cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-44389 | 2022-11-14T20:15:18.593 | EyouCMS V1.5.9-UTF8-SP1 was discovered to contain a Cross-Site Request Forgery (CSRF) via the Edit Admin Profile module. This vulnerability allows attackers to arbitrarily change Administrator account information. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/30"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/30 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | EyouCMS v1.5.9 has a vulnerability, Cross-site request forgery(CSRF).Located in the background, edit the administrator profile. This vulnerability may cause the modification of personal information such as administrator password, mobile phone number, and email address. To exploit this vulnerability, a constructed HTML ... | EyouCMS v1.5.9 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/30/comments | 1 | 2022-10-29T03:58:24Z | 2023-02-21T02:49:11Z | https://github.com/weng-xianhu/eyoucms/issues/30 | 1,428,062,999 | 30 | 4,387 |
CVE-2022-44390 | 2022-11-14T20:15:18.950 | A cross-site scripting (XSS) vulnerability in EyouCMS V1.5.9-UTF8-SP1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Public Security Record Number text field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/31 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | Version:V1.5.9-UTF8-SP1

1、Go to the background --> basic information--> the record number and public security record number, and click the code mode to modify to the code mode.
 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/31/comments | 1 | 2022-10-29T06:04:09Z | 2023-02-21T01:49:51Z | https://github.com/weng-xianhu/eyoucms/issues/31 | 1,428,108,510 | 31 | 4,388 |
CVE-2022-3997 | 2022-11-15T17:15:10.317 | A vulnerability, which was classified as critical, has been found in MonikaBrzica scm. Affected by this issue is some unknown functionality of the file upis_u_bazu.php. The manipulation of the argument email/lozinka/ime/id leads to sql injection. The attack may be launched remotely. The exploit has been disclosed to th... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/MonikaBrzica/scm/issues/2"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/?id.213698"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scm_project:scm:-:*:*:*:*:*:*:*",
"matchCriteriaId": "3B1A4B9C-BE8D-4C83-A9BD-C5D93CE61DCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"707"
] | 707 | https://github.com/MonikaBrzica/scm/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"MonikaBrzica",
"scm"
] | Open source software scm has a storage type cross site script attack vulnerability
Build environment: Aapche2.4.39; MySQL5.7.26; PHP7.3.4
In uredi_ Korisnika.php file, line 42 - line 50,

The information entered by the user is direc... | Open source software scm has a storage type cross site script attack vulnerability | https://api.github.com/repos/MonikaBrzica/scm/issues/2/comments | 0 | 2022-11-15T06:40:48Z | 2022-11-15T13:07:37Z | https://github.com/MonikaBrzica/scm/issues/2 | 1,449,251,439 | 2 | 4,389 |
CVE-2022-3998 | 2022-11-15T17:15:11.177 | A vulnerability, which was classified as critical, was found in MonikaBrzica scm. This affects an unknown part of the file uredi_korisnika.php. The manipulation of the argument id leads to sql injection. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be used. The as... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/MonikaBrzica/scm/issues/1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scm_project:scm:-:*:*:*:*:*:*:*",
"matchCriteriaId": "3B1A4B9C-BE8D-4C83-A9BD-C5D93CE61DCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"707"
] | 707 | https://github.com/MonikaBrzica/scm/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"MonikaBrzica",
"scm"
] |
Build environment: Aapche2.4.39; MySQL5.7.26; PHP7.3.4
From line 22 to line 29, $id gets the get data and then brings it into the database for query
$result returns the database connection results and data query results

... | SQL injection vulnerability exists in scm | https://api.github.com/repos/MonikaBrzica/scm/issues/1/comments | 0 | 2022-11-15T06:06:10Z | 2022-11-15T13:07:21Z | https://github.com/MonikaBrzica/scm/issues/1 | 1,449,221,157 | 1 | 4,390 |
CVE-2022-4006 | 2022-11-15T22:15:19.167 | A vulnerability, which was classified as problematic, has been found in WBCE CMS. Affected by this issue is the function increase_attempts of the file wbce/framework/class.login.php of the component Header Handler. The manipulation of the argument X-Forwarded-For leads to improper restriction of excessive authenticatio... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.7,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS/issues/524"
},
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:-:*:*:*:*:*:*:*",
"matchCriteriaId": "0F44EFA8-B748-450F-A765-E455F227D1E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"307"
] | 307 | https://github.com/WBCE/WBCE_CMS/issues/524 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"WBCE",
"WBCE_CMS"
] | Hi team,
I found a way to bypass account protection (not blocked when brute-force account).
Step: *this is demo some cases
1. If I log in wrongly too many times, it will be locked

2. But i can p... | Bypass account protection | https://api.github.com/repos/WBCE/WBCE_CMS/issues/524/comments | 1 | 2022-11-05T06:01:36Z | 2022-12-03T09:19:58Z | https://github.com/WBCE/WBCE_CMS/issues/524 | 1,436,858,984 | 524 | 4,391 |
CVE-2022-4015 | 2022-11-16T08:15:28.723 | A vulnerability, which was classified as critical, was found in Sports Club Management System 119. This affects an unknown part of the file admin/make_payments.php. The manipulation of the argument m_id/plan leads to sql injection. It is possible to initiate the attack remotely. The exploit has been disclosed to the pu... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/shreyansh225/Sports-Club-Management-System/issues/6"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sports_club_management_system_project:sports_club_management_system:119:*:*:*:*:*:*:*",
"matchCriteriaId": "0629AEBA-BFEA-4404-ACC2-3B21BBB0E1CF",
"versionEndExcluding": null,
"versionEn... | [
"89"
] | 89 | https://github.com/shreyansh225/Sports-Club-Management-System/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"shreyansh225",
"Sports-Club-Management-System"
] | ## Build environment: Aapche2.4.39; MySQL5.5.29; PHP5.6.9
SQL injection vulnerability in Sports Club Management System
In admin/make_ Payments.php, at line 119, the information entered by the user is submitted to submit_ Payments.php, follow up the code, and we can see that the m entered by the user_ The ID is as... | SQL injection vulnerability in Sports Club Management System | https://api.github.com/repos/shreyansh225/Sports-Club-Management-System/issues/6/comments | 0 | 2022-11-16T07:12:28Z | 2022-11-16T08:52:26Z | https://github.com/shreyansh225/Sports-Club-Management-System/issues/6 | 1,451,010,170 | 6 | 4,392 |
CVE-2022-43234 | 2022-11-16T15:15:15.753 | An arbitrary file upload vulnerability in the /attachments component of Hoosk v1.8 allows attackers to execute arbitrary code via a crafted PHP file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/havok89/Hoosk/issues/64"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hoosk:hoosk:1.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "82154F24-2E08-490F-8040-1E8D19AD554C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"434"
] | 434 | https://github.com/havok89/Hoosk/issues/64 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"havok89",
"Hoosk"
] | Vulnerability exists in **/attachments** routing
After logging in to the background, there is an interface for uploading arbitrary files. You can upload php files by building network packages to obtain webshell
 via the Nest library module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tribalsystems:zenario:9.3.57186:*:*:*:*:*:*:*",
"matchCriteriaId": "8CA17362-D750-47F4-AEDA-5A98A74319AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hieuminhnv",
"Zenario-CMS-last-version"
] | **Summary**
hi team,
I found Stored XSS in Nest library
**Info**
Zenario 9.3.57186 last version
FireFox 105.0.3 (64-bit)
**Steps**
Login to account http://xxx.xxx.x.x/admin.php?
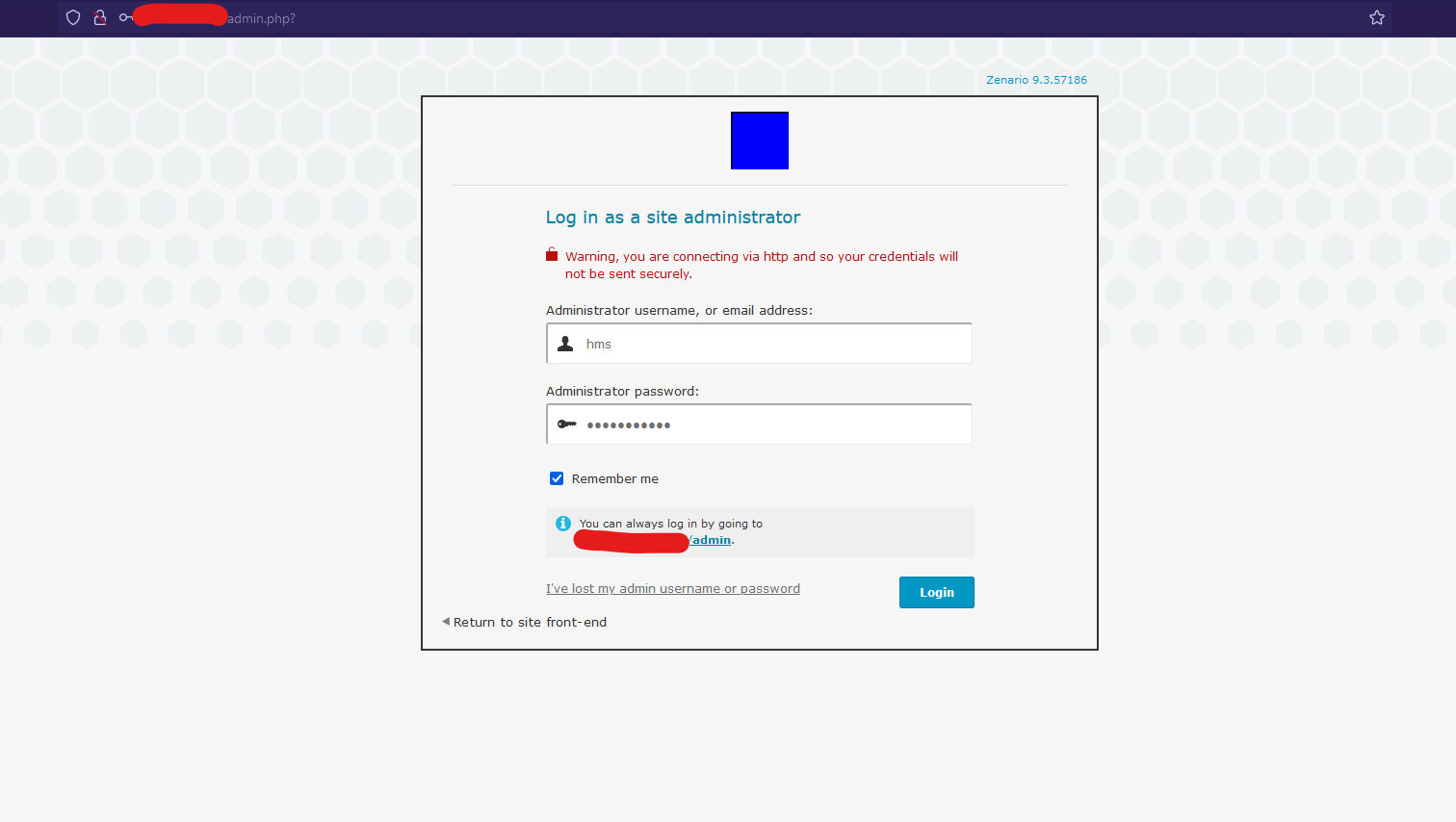
in **Menu**... | Stored XSS in Nest library | https://api.github.com/repos/hieuminhnv/Zenario-CMS-last-version/issues/4/comments | 0 | 2022-10-17T18:44:22Z | 2023-02-09T17:45:41Z | https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/4 | 1,412,045,809 | 4 | 4,395 |
CVE-2022-44070 | 2022-11-16T16:15:10.873 | Zenario CMS 9.3.57186 is vulnerable to Cross Site Scripting (XSS) via News articles. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tribalsystems:zenario:9.3.57186:*:*:*:*:*:*:*",
"matchCriteriaId": "8CA17362-D750-47F4-AEDA-5A98A74319AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hieuminhnv",
"Zenario-CMS-last-version"
] | **Summary**
hi team,
I found small Stored XSS
**Info**
Zenario 9.3.57186 last version
FireFox 105.0.3 (64-bit)
**Steps**
Login to account http://xxx.xxx.x.x/admin.php?
 via profile. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tribalsystems:zenario:9.3.57186:*:*:*:*:*:*:*",
"matchCriteriaId": "8CA17362-D750-47F4-AEDA-5A98A74319AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hieuminhnv",
"Zenario-CMS-last-version"
] | **Summary**
hi team,
I found Stored XSS in profile
**Info**
Zenario 9.3.57186 last version
FireFox 105.0.3 (64-bit)
**Steps**
Login to account http://xxx.xxx.x.x/admin.php?
in profile , at **First name** and **Last name** fill in payload >> save
 via svg,Users & Contacts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tribalsystems:zenario:9.3.57186:*:*:*:*:*:*:*",
"matchCriteriaId": "8CA17362-D750-47F4-AEDA-5A98A74319AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/6 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hieuminhnv",
"Zenario-CMS-last-version"
] | **Summary**
hi team,
I found Stored XSS in upload file svg version 9.0.54156 reported the vulnerability with CVE-2021-41952, in version 9.3.57186 i have bypassed it
visit : https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/1 to view my report
**Info**
Zenario 9.3.57186 last version
FireFox 105.0.3 (... | XSS upload file SVG in Zenario 9.3.57186 | https://api.github.com/repos/hieuminhnv/Zenario-CMS-last-version/issues/6/comments | 0 | 2022-10-18T05:14:47Z | 2023-02-09T17:45:32Z | https://github.com/hieuminhnv/Zenario-CMS-last-version/issues/6 | 1,412,584,959 | 6 | 4,398 |
CVE-2022-42187 | 2022-11-17T04:15:10.950 | Hustoj 22.09.22 has a XSS Vulnerability in /admin/problem_judge.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zhblue/hustoj/issues/866"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hustoj:hustoj:22.09.22:*:*:*:*:*:*:*",
"matchCriteriaId": "7F9D317C-8136-4514-8E07-250E38E47B48",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/zhblue/hustoj/issues/866 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zhblue",
"hustoj"
] | **描述问题**
XSS Vulnerability exists in
https://github.com/zhblue/hustoj/blob/417173dd9b4606251e06e1b9a2e6992db58831a8/trunk/web/admin/problem_judge.php#L138
**如何复现**
Steps to reproduce the behavior:
1. POST text with xss script to submit.php
for example:
```html
id=-1000&language=1&source=asdasdasdasdasd&input_te... | XSS Vulnerability in /admin/problem_judge.php | https://api.github.com/repos/zhblue/hustoj/issues/866/comments | 6 | 2022-09-29T06:19:47Z | 2022-09-30T11:20:38Z | https://github.com/zhblue/hustoj/issues/866 | 1,390,317,684 | 866 | 4,399 |
CVE-2022-42246 | 2022-11-17T04:15:11.103 | Doufox 0.0.4 contains a CSRF vulnerability that can add system administrator account. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/farliy-hacker/Doufoxcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:duofoxtechnologies:duofox_cms:0.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "1D7C3797-3604-4170-BAB9-A9057BD7C09A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"352"
] | 352 | https://github.com/farliy-hacker/Doufoxcms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"farliy-hacker",
"Doufoxcms"
] | After the administrator logs in, open the following page
poc:
add.html---add a user
CSRF link: https://github.com/farliy-hacker/Doufoxcms/blob/main/CSRF-poc
| CSRF vulnerability adding system administrator account | https://api.github.com/repos/farliy-hacker/Doufoxcms/issues/1/comments | 0 | 2022-10-02T06:34:06Z | 2022-10-02T07:28:16Z | https://github.com/farliy-hacker/Doufoxcms/issues/1 | 1,393,660,763 | 1 | 4,400 |
CVE-2022-43140 | 2022-11-17T17:15:13.613 | kkFileView v4.1.0 was discovered to contain a Server-Side Request Forgery (SSRF) via the component cn.keking.web.controller.OnlinePreviewController#getCorsFile. This vulnerability allows attackers to force the application to make arbitrary requests via injection of crafted URLs into the url parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kekingcn/kkFileView/issues/392"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:keking:kkfileview:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3CF7B3A0-ACE8-4EF5-AF51-760E7B2650BF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"918"
] | 918 | https://github.com/kekingcn/kkFileView/issues/392 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kekingcn",
"kkFileView"
] | 问题描述
kkFileview v4.1.0存在SSRF漏洞,攻击者可以利用此漏洞造成服务器端请求伪造(SSRF),远程攻击者可以通过将任意url注入url参数来强制应用程序发出任意请求。
Description
kkFileview v4.1.0 has an SSRF vulnerability, This vulnerability can be leveraged by attackers to cause a Server-Side Request Forgery (SSRF),allows remote attackers to force the application to make arbitr... | kkFileView SSRF Vulnerability | https://api.github.com/repos/kekingcn/kkFileView/issues/392/comments | 1 | 2022-10-08T09:46:30Z | 2022-12-28T06:46:56Z | https://github.com/kekingcn/kkFileView/issues/392 | 1,401,891,198 | 392 | 4,401 |
CVE-2022-4051 | 2022-11-17T17:15:13.847 | A vulnerability has been found in Hostel Searching Project and classified as critical. This vulnerability affects unknown code of the file view-property.php. The manipulation of the argument property_id leads to sql injection. The attack can be initiated remotely. The exploit has been disclosed to the public and may be... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/itzmehedi/Hostel-searching-project-using-PHP-Mysql/issues/1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory",
"VDB Entry... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hostel_searching_project:hostel_searching_project:-:*:*:*:*:*:*:*",
"matchCriteriaId": "F0F144D3-06A9-4B8B-A620-34516045F514",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/itzmehedi/Hostel-searching-project-using-PHP-Mysql/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"itzmehedi",
"Hostel-searching-project-using-PHP-Mysql"
] | # SQL injection vulnerability exists in Hostel searching project
## 1.Build environment
Aapche2.4.39; MySQL5.7.26; PHP8.0.2
## 2.Vulnerability analysis

view-property.php:
property_ ID is assigned to $property_ The ID varia... | SQL injection vulnerability exists in Hostel searching project | https://api.github.com/repos/iammehedi1/Hostel-searching-project-using-PHP-Mysql/issues/1/comments | 0 | 2022-11-17T05:51:46Z | 2022-11-18T12:00:14Z | https://github.com/iammehedi1/Hostel-searching-project-using-PHP-Mysql/issues/1 | 1,452,754,200 | 1 | 4,402 |
CVE-2022-4052 | 2022-11-17T17:15:14.193 | A vulnerability was found in Student Attendance Management System and classified as critical. This issue affects some unknown processing of the file /Admin/createClass.php. The manipulation of the argument Id leads to sql injection. The attack may be initiated remotely. The exploit has been disclosed to the public and ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rickxy/Student-Attendance-Management-System/issues/2"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory",
"VDB Entry"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:student_attendance_management_system_project:student_attendance_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A049D780-8ACB-4734-A45C-AE7EE194690C",
"versionEndExcluding": null,
... | [
"89"
] | 89 | https://github.com/rickxy/Student-Attendance-Management-System/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rickxy",
"Student-Attendance-Management-System"
] | Build environment: Aapche2.4.39; MySQL5.7.26; PHP7.3.4
SQL injection vulnerability in Student Attendance Management System。input admin@mail.com / Password@123 Log in to the background. Then modify the information in createClass Php, the ID is assigned to the variable $ID, and then inserted into the database for quer... | SQL injection vulnerability in Student Attendance Management System | https://api.github.com/repos/rickxy/Student-Attendance-Management-System/issues/2/comments | 0 | 2022-11-17T06:51:39Z | 2022-11-18T00:12:23Z | https://github.com/rickxy/Student-Attendance-Management-System/issues/2 | 1,452,812,879 | 2 | 4,403 |
CVE-2022-4053 | 2022-11-17T17:15:14.467 | A vulnerability was found in Student Attendance Management System. It has been classified as problematic. Affected is an unknown function of the file createClass.php. The manipulation of the argument className leads to cross site scripting. It is possible to launch the attack remotely. The exploit has been disclosed to... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.4,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rickxy/Student-Attendance-Management-System/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory",
"VDB Entry"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:student_attendance_management_system_project:student_attendance_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A049D780-8ACB-4734-A45C-AE7EE194690C",
"versionEndExcluding": null,
... | [
"79"
] | 79 | https://github.com/rickxy/Student-Attendance-Management-System/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rickxy",
"Student-Attendance-Management-System"
] | ## Build environment: Aapche2.4.39; MySQL5.7.26; PHP7.3.4
input admin@mail.com / Password@123 Log in to the background. At manage classes, click create class, enter xsspayload:<script>alert ("ace")</script>, and click save。

and then ref... | Student Attendance Management System has a storage XSS vulnerability | https://api.github.com/repos/rickxy/Student-Attendance-Management-System/issues/3/comments | 0 | 2022-11-17T06:52:34Z | 2022-11-18T00:12:28Z | https://github.com/rickxy/Student-Attendance-Management-System/issues/3 | 1,452,813,739 | 3 | 4,404 |
CVE-2022-41920 | 2022-11-17T18:15:10.100 | Lancet is a general utility library for the go programming language. Affected versions are subject to a ZipSlip issue when using the fileutil package to unzip files. This issue has been addressed and a fix will be included in versions 2.1.10 and 1.3.4. Users are advised to upgrade. There are no known workarounds for th... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/duke-git/lancet/commit/f133b32faa05eb93e66175d01827afa4b7094572"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lancet_project:lancet:*:*:*:*:*:go:*:*",
"matchCriteriaId": "B1C2AAFE-19C2-489A-942C-6F0F833A348D",
"versionEndExcluding": "1.3.4",
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/duke-git/lancet/issues/62 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"duke-git",
"lancet"
] | Hello 👋
I found a potential security issue in lancet, how can I get in touch with you in a private way and submit my security report?
Could you add a SECURITY.md file with an e-mail address for me to send further details to? GitHub [recommends](https://docs.github.com/en/code-security/getting-started/adding-a-se... | How to get in touch regarding a security concern? | https://api.github.com/repos/duke-git/lancet/issues/62/comments | 1 | 2022-11-15T12:14:14Z | 2022-11-17T08:22:38Z | https://github.com/duke-git/lancet/issues/62 | 1,449,687,711 | 62 | 4,405 |
CVE-2022-43183 | 2022-11-17T21:15:15.837 | XXL-Job before v2.3.1 contains a Server-Side Request Forgery (SSRF) via the component /admin/controller/JobLogController.java. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/3002"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B9117C48-ADBB-4018-8476-F291CA8A2BF4",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.1",
"versionStartExcludi... | [
"918"
] | 918 | https://github.com/xuxueli/xxl-job/issues/3002 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | xxl-job =< 2.3.1 version (latest version) has SSRF vulnerability, which causes low-privileged users to control executor to execute arbitrary commands
1. Vulnerability description
XXL-JOB is a distributed task scheduling platform based on java language in the XXL (XXL-JOB) community.
There is an SSRF vulnerabi... | xxl-job =< 2.3.1 version (latest version) has SSRF vulnerability, which causes low-privileged users to control executor to execute arbitrary commands | https://api.github.com/repos/xuxueli/xxl-job/issues/3002/comments | 5 | 2022-10-10T06:59:34Z | 2023-03-23T10:51:45Z | https://github.com/xuxueli/xxl-job/issues/3002 | 1,402,687,023 | 3,002 | 4,406 |
CVE-2022-39389 | 2022-11-17T22:15:10.547 | Lightning Network Daemon (lnd) is an implementation of a lightning bitcoin overlay network node. All lnd nodes before version `v0.15.4` are vulnerable to a block parsing bug that can cause a node to enter a degraded state once encountered. In this degraded state, nodes can continue to make payments and forward HTLCs, a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lightningnetwork/lnd/issues/7096"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:btcd_project:btcd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4C76213E-2BE3-4BF3-B5D1-2AA9B6BB0A95",
"versionEndExcluding": "0.23.3",
"versionEndIncluding": null,
"versionStartExcl... | [
"20"
] | 20 | https://github.com/lightningnetwork/lnd/issues/7096 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lightningnetwork",
"lnd"
] | ### Background
lnd does not process new blocks.
lnd:
```
2022-11-01 12:02:54.658 [ERR] LNWL: Unable to process chain reorg: unable to get block 000000000000000000070742427fa10ec3c66d006160155a704d9f56d090a3ea: MsgTx.BtcDecode: too many witness items to fit into max message size [count 500003, max 500000]
```
... | [bug]: CRITICAL! Unable to process chain reorg / too many witness items to fit into max message size | https://api.github.com/repos/lightningnetwork/lnd/issues/7096/comments | 19 | 2022-11-01T11:12:11Z | 2022-11-02T10:37:15Z | https://github.com/lightningnetwork/lnd/issues/7096 | 1,431,260,386 | 7,096 | 4,407 |
CVE-2022-43171 | 2022-11-17T23:15:23.883 | A heap buffer overflow in the LIEF::MachO::BinaryParser::parse_dyldinfo_generic_bind function of LIEF v0.12.1 allows attackers to cause a Denial of Service (DoS) via a crafted MachO file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/782"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:0.12.1:*:*:*:*:*:*:*",
"matchCriteriaId": "BC60B6E0-1155-48A0-9CB4-1A6201D420C7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/lief-project/LIEF/issues/782 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | **Describe the bug**
A bad macho file which can lead LIEF::MachO::Parser::parse() to a heap-buffer-overflow(read) issue.
Poc here :
[poc1.zip](https://github.com/lief-project/LIEF/files/9542081/poc1.zip)
**To Reproduce**
1. Build the whole project with **ASAN**
2. Drive program (compile it with **ASAN** too):
... | Heap-buffer-overflow in LIEF::MachO::BinaryParser::parse_dyldinfo_generic_bind at MachO/BinaryParser.tcc:1629 | https://api.github.com/repos/lief-project/LIEF/issues/782/comments | 0 | 2022-09-11T08:44:50Z | 2022-09-12T08:45:03Z | https://github.com/lief-project/LIEF/issues/782 | 1,368,876,839 | 782 | 4,408 |
CVE-2022-45474 | 2022-11-18T18:15:10.767 | drachtio-server 0.8.18 has a request-handler.cpp event_cb use-after-free for any request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/drachtio/drachtio-server/commit/860f025468feb31c43227153d8fb3f34210a522e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:drachtio:drachtio-server:0.8.18:*:*:*:*:*:*:*",
"matchCriteriaId": "D4953169-9FF9-4362-A9E7-25416AC7FF45",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"416"
] | 416 | https://github.com/drachtio/drachtio-server/issues/240 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"drachtio",
"drachtio-server"
] | Hello,
this is a follow-up after the private disclosure.
When `drachtio-server` receives a call, if you run it via a debugger (valgrind in this case), you will see a use-after-free that happens by default.
```
valgrind /usr/local/bin/drachtio --contact 'sip:PUBLIC_IP;transport=udp' --contact 'sip:PUBLIC_IP;tr... | CVE-2022-45474: Use-after-free in event_cb when drachtio-server receives a call | https://api.github.com/repos/drachtio/drachtio-server/issues/240/comments | 2 | 2022-11-18T14:59:47Z | 2022-11-25T15:41:06Z | https://github.com/drachtio/drachtio-server/issues/240 | 1,455,282,743 | 240 | 4,409 |
CVE-2022-38871 | 2022-11-18T23:15:20.117 | In Free5gc v3.0.5, the AMF breaks due to malformed NAS messages. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/free5gc/free5gc/issues/198"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:free5gc:free5gc:3.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "7AC5244A-13E0-4776-A4C6-58A9784FDAFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"400"
] | 400 | https://github.com/free5gc/free5gc/issues/198 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"free5gc",
"free5gc"
] | ## Describe the bug
While testing the free5gc AMF for some NAS basic security features and fuzzing, I could trigger several crashes, while sending malformed NAS message. This means those issues are relatively exposed as they can be trigger by any 5G subscriber, in the principle.
Here, all memory issues due to mishand... | [Bugs] AMF breaks due to malformed NAS message | https://api.github.com/repos/free5gc/free5gc/issues/198/comments | 4 | 2021-04-26T13:42:33Z | 2023-12-04T08:48:27Z | https://github.com/free5gc/free5gc/issues/198 | 867,719,689 | 198 | 4,410 |
CVE-2022-4064 | 2022-11-19T19:15:09.780 | A vulnerability was found in Dalli. It has been classified as problematic. Affected is the function self.meta_set of the file lib/dalli/protocol/meta/request_formatter.rb of the component Meta Protocol Handler. The manipulation leads to injection. The exploit has been disclosed to the public and may be used. The name o... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.1,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/petergoldstein/dalli/commit/48d594dae55934476fec61789e7a7c3700e0f50d"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dalli_project:dalli:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "1E4D2EAA-00C7-487E-9FCF-0C454555528E",
"versionEndExcluding": "3.2.3",
"versionEndIncluding": null,
"versionStart... | [
"74"
] | 74 | https://github.com/petergoldstein/dalli/issues/932 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"petergoldstein",
"dalli"
] | Hi there,
I'm a security researcher currently doing research on Memcached wrappers vulnerabilities. I was doing some source code reviewing on your wrapper and noticed that the `flush_all` method on the meta protocol takes a delay value and passes it to the server without any checks, which can be used to smuggle comman... | Meta protocol flush_all method is vulnerable to code injection (Lack of input type check) | https://api.github.com/repos/petergoldstein/dalli/issues/932/comments | 7 | 2022-10-25T17:09:25Z | 2022-10-29T13:32:37Z | https://github.com/petergoldstein/dalli/issues/932 | 1,422,799,445 | 932 | 4,411 |
CVE-2022-45012 | 2022-11-21T15:15:11.537 | A cross-site scripting (XSS) vulnerability in the Modify Page module of WBCE CMS v1.5.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Source field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gozan10/cve"
},
{
"source": "cve@mitre.org",
"tags": [... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5322A587-93A1-48C2-99A5-6E83A8858684",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.4",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/gozan10/cve/issues/1 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gozan10",
"cve"
] | Exploit Title: XSS Stored Vulnerability in WBCE Version: 1.5.4
Date: 03/11/2022
Exploit Author: Gozan
Contact: https://github.com/gozan10
Product: WBCE CMS (https://github.com/WBCE/WBCE_CMS)
Vendor: WBCE CMS
Description: XSS Stored exitst in Section name field allow attacker excute arbitrary web script
First... | CVE_WBCE | https://api.github.com/repos/gozan10/cve/issues/1/comments | 0 | 2022-11-03T13:47:25Z | 2022-11-03T15:24:48Z | https://github.com/gozan10/cve/issues/1 | 1,434,692,988 | 1 | 4,412 |
CVE-2022-45013 | 2022-11-21T15:15:11.783 | A cross-site scripting (XSS) vulnerability in the Show Advanced Option module of WBCE CMS v1.5.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Section Header field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gozan10"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5322A587-93A1-48C2-99A5-6E83A8858684",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.4",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/gozan10/cve/issues/2 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gozan10",
"cve"
] | Exploit Title: XSS Stored Vulnerability in WBCE Version: 1.5.4
Date: 04/11/2022
Exploit Author: Gozan
Contact: https://github.com/gozan10
Product: WBCE CMS (https://github.com/WBCE/WBCE_CMS)
Vendor: WBCE CMS
Description: XSS Stored exitst in Section Header field allow attacker excute arbitrary web script
First... | CVE_WBCE_1 | https://api.github.com/repos/gozan10/cve/issues/2/comments | 0 | 2022-11-04T02:34:32Z | 2022-11-04T02:48:02Z | https://github.com/gozan10/cve/issues/2 | 1,435,463,262 | 2 | 4,413 |
CVE-2022-45014 | 2022-11-21T15:15:12.023 | A cross-site scripting (XSS) vulnerability in the Search Settings module of WBCE CMS v1.5.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Results Header field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gozan10"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5322A587-93A1-48C2-99A5-6E83A8858684",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.4",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/gozan10/cve/issues/3 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gozan10",
"cve"
] | Exploit Title: XSS Stored Vulnerability in WBCE Version: 1.5.4
Date: 04/11/2022
Exploit Author: Gozan
Contact: https://github.com/gozan10
Product: WBCE CMS (https://github.com/WBCE/WBCE_CMS)
Vendor: WBCE CMS
Description: XSS Stored exitst in Section Results Header field allow attacker excute arbitrary web script
... | CVE_WBCE_2 | https://api.github.com/repos/gozan10/cve/issues/3/comments | 0 | 2022-11-04T03:04:55Z | 2022-11-04T03:14:06Z | https://github.com/gozan10/cve/issues/3 | 1,435,479,175 | 3 | 4,414 |
CVE-2022-45015 | 2022-11-21T15:15:12.247 | A cross-site scripting (XSS) vulnerability in the Search Settings module of WBCE CMS v1.5.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Results Footer field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gozan10"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5322A587-93A1-48C2-99A5-6E83A8858684",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.4",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/gozan10/cve/issues/4 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gozan10",
"cve"
] | Exploit Title: XSS Stored Vulnerability in WBCE Version: 1.5.4
Date: 04/11/2022
Exploit Author: Gozan
Contact: https://github.com/gozan10
Product: WBCE CMS (https://github.com/WBCE/WBCE_CMS)
Vendor: WBCE CMS
Description: XSS Stored exitst in Section Results Footer field allow attacker excute arbitrary web script
... | CVE_WBCE_3 | https://api.github.com/repos/gozan10/cve/issues/4/comments | 0 | 2022-11-04T03:22:32Z | 2022-11-04T03:22:32Z | https://github.com/gozan10/cve/issues/4 | 1,435,489,408 | 4 | 4,415 |
CVE-2022-45016 | 2022-11-21T15:15:12.320 | A cross-site scripting (XSS) vulnerability in the Search Settings module of WBCE CMS v1.5.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Footer field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gozan10"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5322A587-93A1-48C2-99A5-6E83A8858684",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.4",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/gozan10/cve/issues/5 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gozan10",
"cve"
] | Exploit Title: XSS Stored Vulnerability in WBCE Version: 1.5.4
Date: 04/11/2022
Exploit Author: Gozan
Contact: https://github.com/gozan10
Product: WBCE CMS (https://github.com/WBCE/WBCE_CMS)
Vendor: WBCE CMS
Description: XSS Stored exitst in Section Footer field allow attacker excute arbitrary web script
First... | CVE WBCE_4 | https://api.github.com/repos/gozan10/cve/issues/5/comments | 0 | 2022-11-04T03:27:07Z | 2022-11-04T07:41:54Z | https://github.com/gozan10/cve/issues/5 | 1,435,492,527 | 5 | 4,416 |
CVE-2022-45017 | 2022-11-21T15:15:12.393 | A cross-site scripting (XSS) vulnerability in the Overview Page settings module of WBCE CMS v1.5.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Post Loop field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/WBCE/WBCE_CMS/issues/525"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wbce:wbce_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5322A587-93A1-48C2-99A5-6E83A8858684",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.4",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/WBCE/WBCE_CMS/issues/525 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"WBCE",
"WBCE_CMS"
] | Hi team,
I find XSS via modul post loop in Pages
Step:
1. add section in manage sections

 vulnerability in Beekeeper Studio v3.6.6 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the error modal container. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/beekeeper-studio/beekeeper-studio/issues/1393"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:beekeeperstudio:beekeeper-studio:3.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE808B7-9E7E-4F47-8726-A9B210429081",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"79"
] | 79 | https://github.com/beekeeper-studio/beekeeper-studio/issues/1393 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"beekeeper-studio",
"beekeeper-studio"
] | **Author: [bob11.devranger@gmail.com](mailto:bob11.devranger@gmail.com)**
**Date: 2022-10-07**
**OS: Windows, Linux, MacOS**
**Beekeeper Studio Version: 3.6.6**
**DB Type&Version: MySQL 5.7 and 8.0 Also**
---
## Summary
It has been possible to trigger remote code execution via Beekeeper’s **Modal C... | BUG: Beekeeper Remote Code Execution via XSS | https://api.github.com/repos/beekeeper-studio/beekeeper-studio/issues/1393/comments | 2 | 2022-10-08T08:52:49Z | 2022-11-21T15:46:13Z | https://github.com/beekeeper-studio/beekeeper-studio/issues/1393 | 1,401,877,047 | 1,393 | 4,418 |
CVE-2022-36227 | 2022-11-22T02:15:11.003 | In libarchive before 3.6.2, the software does not check for an error after calling calloc function that can return with a NULL pointer if the function fails, which leads to a resultant NULL pointer dereference. NOTE: the discoverer cites this CWE-476 remark but third parties dispute the code-execution impact: "In rare ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.gentoo.org/882521"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/libarchive/libarchive/blob/v3... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libarchive:libarchive:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89B15E48-C18C-4FD9-8797-BBA59F4E3C3B",
"versionEndExcluding": "3.6.2",
"versionEndIncluding": null,
"versionStartE... | [
"476"
] | 476 | https://github.com/libarchive/libarchive/issues/1754 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libarchive",
"libarchive"
] | The software does not check for an error after calling `calloc` function that can return with a NULL pointer if the function fails, which leads to a resultant NULL pointer dereference or, in some cases, even arbitrary code execution.
The vulnerability is here:
```
f = calloc(1, sizeof(*f));
f->archive = _a;
... | There is a NULL pointer dereference vulnerability | https://api.github.com/repos/libarchive/libarchive/issues/1754/comments | 9 | 2022-07-11T06:25:04Z | 2023-02-21T07:36:29Z | https://github.com/libarchive/libarchive/issues/1754 | 1,300,264,871 | 1,754 | 4,419 |
CVE-2021-46854 | 2022-11-23T07:15:09.057 | mod_radius in ProFTPD before 1.3.7c allows memory disclosure to RADIUS servers because it copies blocks of 16 characters. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "http://www.proftpd.org/docs/RELEASE_NOTES-1.3.7e"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.gentoo.org/811... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:proftpd:proftpd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D1FF45EB-7C4A-4CBF-A03B-661546B087E7",
"versionEndExcluding": "1.3.7c",
"versionEndIncluding": null,
"versionStartExclud... | [
"401"
] | 401 | https://github.com/proftpd/proftpd/issues/1284 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"proftpd",
"proftpd"
] | ### What I Did
We have noticed a disclosure of memory contents from mod_radius to RADIUS servers.
mod_radius copies the client-supplied password into a temporary
buffer to encrypt it with the RADIUS shared secret. However, it
does so obeying some padding rules: i.e. it is expected that the
password has a leng... | mod_radius: memory disclosure to radius server | https://api.github.com/repos/proftpd/proftpd/issues/1284/comments | 1 | 2021-08-04T18:06:14Z | 2021-08-05T03:16:31Z | https://github.com/proftpd/proftpd/issues/1284 | 960,816,974 | 1,284 | 4,420 |
CVE-2021-35284 | 2022-11-23T18:15:11.063 | SQL Injection vulnerability in function get_user in login_manager.php in rizalafani cms-php v1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rizalafani/cms-php/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cms-php_project:cms-php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AA4C1813-639F-4FF1-B4ED-E70CC588103D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/rizalafani/cms-php/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rizalafani",
"cms-php"
] | Login page : login.php
judge : login_manager.php
function : get_user()
`function.php` Execute SQL query
```
function get_user($where = ""){
$koneksi = connection();
$data = mysql_query("select * from userapp $where;") or die ("query error");
destroy_connection($koneksi);
return to_array($data);
... | Login page SQL injection | https://api.github.com/repos/rizalafani/cms-php/issues/1/comments | 0 | 2021-06-10T05:17:04Z | 2021-06-10T05:17:04Z | https://github.com/rizalafani/cms-php/issues/1 | 916,909,676 | 1 | 4,421 |
CVE-2022-44140 | 2022-11-23T20:15:10.333 | Jizhicms v2.3.3 was discovered to contain a SQL injection vulnerability via the /Member/memberedit.html component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/81"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:2.3.3:*:*:*:*:*:*:*",
"matchCriteriaId": "6FDCCC0D-710D-49F8-BBE7-50FC638428E2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/Cherry-toto/jizhicms/issues/81 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | ### Issue
SQL injection vulnerabilities exist under the function nodes of new members, and attackers can operate on databases
### Steps to reproduce
1. Log in to the background
2. Click User Management>Member List>Add Member or Edit


Problematic packets:
> POST ... | jizhicms v2.3.3 has a vulnerability, SQL injection | https://api.github.com/repos/Cherry-toto/jizhicms/issues/83/comments | 1 | 2022-11-10T09:53:18Z | 2022-11-18T08:29:48Z | https://github.com/Cherry-toto/jizhicms/issues/83 | 1,443,586,440 | 83 | 4,423 |
CVE-2022-45280 | 2022-11-23T21:15:11.310 | A cross-site scripting (XSS) vulnerability in the Url parameter in /login.php of EyouCMS v1.6.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EB987CAE-6D4D-417A-8E0D-9DCC47F986EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/32 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | name:EyouCMS
version: EyouCMS-V1.6.0-UTF8-SP1
Installation package [download:](https://www.eyoucms.com/rizhi/2022/1102/28642.html)
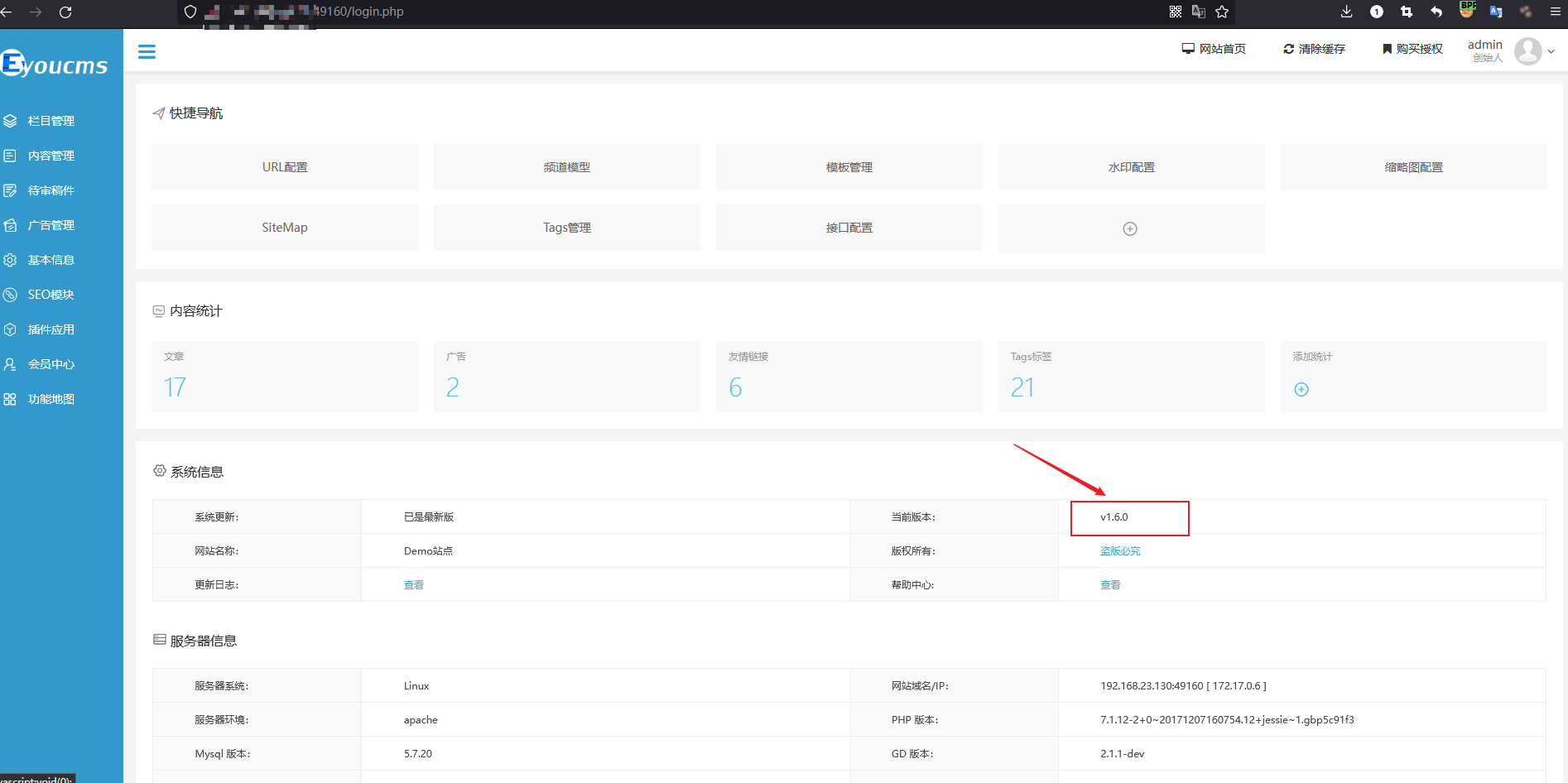
Problematic packets:
> POST /login.php?m=admin&c=Links&a=add&_ajax=1... | EyouCMS v1.6.0 existence stored cross-site scripting (XSS) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/32/comments | 1 | 2022-11-10T12:16:56Z | 2023-02-21T01:34:50Z | https://github.com/weng-xianhu/eyoucms/issues/32 | 1,443,805,273 | 32 | 4,424 |
CVE-2022-45868 | 2022-11-23T21:15:11.360 | The web-based admin console in H2 Database Engine before 2.2.220 can be started via the CLI with the argument -webAdminPassword, which allows the user to specify the password in cleartext for the web admin console. Consequently, a local user (or an attacker that has obtained local access through some means) would be ab... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 8.4,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/advisories/GHSA-22wj-vf5f-wrvj"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/h2database/h2database/blob/96832bf5a97cdc0adc1f2066ed61c54990d66ab5/h2/src/main/o... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:h2database:h2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EFEFD20F-4B01-42B0-BD3A-F8FCA9AE9DD5",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.214",
"versionStartExcludi... | [
"312"
] | 312 | https://github.com/h2database/h2database/issues/3686 | null | github.com | [
"h2database",
"h2database"
] | Dependabot and `org.owasp:dependency-check-maven` have been reporting CVE-2022-45868 (see https://github.com/advisories/GHSA-22wj-vf5f-wrvj) to me. I didn't find this CVE referenced from any issue in the issue tracker here, so I'm creating this one.
Since the CVE has already been published (possibly as a zero day??)... | CVE-2022-45868: Password exposure in H2 Database (not an issue) | https://api.github.com/repos/h2database/h2database/issues/3686/comments | 13 | 2022-12-01T14:27:16Z | 2024-04-02T09:11:15Z | https://github.com/h2database/h2database/issues/3686 | 1,471,413,455 | 3,686 | 4,425 |
CVE-2022-4088 | 2022-11-24T10:15:11.103 | A vulnerability was found in rickxy Stock Management System and classified as critical. Affected by this issue is some unknown functionality of the file /pages/processlogin.php. The manipulation of the argument user/password leads to sql injection. The attack may be launched remotely. The exploit has been disclosed to ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rickxy/Stock-Management-System/issues/2"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stock_management_system_project:stock_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A57E1F1C-75BF-46D8-987E-98223ED68D41",
"versionEndExcluding": null,
"versionEndIncluding": n... | [
"89"
] | 89 | https://github.com/rickxy/Stock-Management-System/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rickxy",
"Stock-Management-System"
] | Build environment: Apache 2.4.39; MySQL5.7.26; PHP7.3.4
## SQL injection vulnerability in Stock Management System
```
In processlogin PHP, in lines 7 to 9 of the code, the back-end receives the user and password parameters passed through by the front-end, and encrypts the password with sha1; In lines 18 to 25 of th... | SQL injection vulnerability in Stock Management System | https://api.github.com/repos/rickxy/Stock-Management-System/issues/2/comments | 0 | 2022-11-21T11:48:39Z | 2022-11-24T12:40:57Z | https://github.com/rickxy/Stock-Management-System/issues/2 | 1,457,808,295 | 2 | 4,426 |
CVE-2022-4089 | 2022-11-24T10:15:11.197 | A vulnerability was found in rickxy Stock Management System. It has been declared as problematic. This vulnerability affects unknown code of the file /pages/processlogin.php. The manipulation of the argument user leads to cross site scripting. The attack can be initiated remotely. The exploit has been disclosed to the ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rickxy/Stock-Management-System/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stock_management_system_project:stock_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A57E1F1C-75BF-46D8-987E-98223ED68D41",
"versionEndExcluding": null,
"versionEndIncluding": n... | [
"79"
] | 79 | https://github.com/rickxy/Stock-Management-System/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rickxy",
"Stock-Management-System"
] | ## Reflective XSS vulnerability in Stock Management System
```php+HTML
In processlogin PHP, in lines 18-25 of the code, the parameters entered by the front end are brought into the database for associated table query, and then the results of database execution are returned. After the 27th line of code, judge the re... | Reflective XSS vulnerability in Stock Management System | https://api.github.com/repos/rickxy/Stock-Management-System/issues/3/comments | 0 | 2022-11-21T11:49:10Z | 2022-11-24T12:40:49Z | https://github.com/rickxy/Stock-Management-System/issues/3 | 1,457,808,895 | 3 | 4,427 |
CVE-2022-4090 | 2022-11-24T13:15:10.467 | A vulnerability was found in rickxy Stock Management System and classified as problematic. This issue affects some unknown processing of the file us_transac.php?action=add. The manipulation leads to cross-site request forgery. The attack may be initiated remotely. The exploit has been disclosed to the public and may be... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rickxy/Stock-Management-System/issues/4"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stock_management_system_project:stock_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A57E1F1C-75BF-46D8-987E-98223ED68D41",
"versionEndExcluding": null,
"versionEndIncluding": n... | [
"352"
] | 352 | https://github.com/rickxy/Stock-Management-System/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rickxy",
"Stock-Management-System"
] | ## The Stock Management System has a CSRF vulnerability
```html
In use_ In add.php, add user information and send it to us via post request_ transac. Php, and then stored the new user information in the database without cookie or session verification or referer verification, resulting in a CSRF vulnerability. Simil... | The Stock Management System has a CSRF vulnerability | https://api.github.com/repos/rickxy/Stock-Management-System/issues/4/comments | 0 | 2022-11-21T11:49:34Z | 2022-11-24T12:40:33Z | https://github.com/rickxy/Stock-Management-System/issues/4 | 1,457,809,383 | 4 | 4,428 |
CVE-2022-45205 | 2022-11-25T17:15:11.007 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/dict/queryTableData. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4128"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4128 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | # SysDictMapper.xml
queryDictTablePageList。You can see that no precompiling is performed
<img width="960" alt="截屏2022-10-25 15 24 58" src="https://user-images.githubusercontent.com/60163868/197709842-99880e4f-25e4-4f5a-a2cb-4fa8dcca4db2.png">
# SysDictController.java
<img width="1192" alt="截屏2022-10-25 15 25 29" ... | [CVE-2022-45205]/sys/dict/queryTableData is affected by sql injection | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4128/comments | 2 | 2022-10-25T07:31:16Z | 2022-12-01T07:35:33Z | https://github.com/jeecgboot/JeecgBoot/issues/4128 | 1,421,998,736 | 4,128 | 4,429 |
CVE-2022-45206 | 2022-11-25T17:15:11.060 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/duplicate/check. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4129"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4129 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | [jeecg-boot漏洞.pdf](https://github.com/jeecgboot/jeecg-boot/files/9858362/jeecg-boot.pdf)
| [CVE-2022-45206]/sys/duplicate/check存在sql注入漏洞 | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4129/comments | 12 | 2022-10-25T08:10:59Z | 2024-04-21T07:44:09Z | https://github.com/jeecgboot/JeecgBoot/issues/4129 | 1,422,048,340 | 4,129 | 4,430 |
CVE-2022-45207 | 2022-11-25T17:15:11.117 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component updateNullByEmptyString. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4127"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4127 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | java提供了原生的预编译sql语句,这样可以防止sql注入问题
# queryListWithPermission
下图没有进行预编译处理,建议换成#{},虽然项目现在没有使用这条语句,但不排除以后的可能,建议修复
<img width="1532" alt="截屏2022-10-25 10 48 22" src="https://user-images.githubusercontent.com/60163868/197670494-95f85eb2-ce58-43ee-9aef-02b9e07ba2b1.png">
# updateNullByEmptyString
下图也使用的是${}
<img width="1... | [CVE-2022-45207]这里有几处没有换成预编译,但个人建议修复 | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4127/comments | 6 | 2022-10-25T06:07:32Z | 2022-12-07T00:59:38Z | https://github.com/jeecgboot/JeecgBoot/issues/4127 | 1,421,911,807 | 4,127 | 4,431 |
CVE-2022-45208 | 2022-11-25T17:15:11.173 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/user/putRecycleBin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4126"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4126 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | # sysUserMapper.xml
revertLogicDeleted. You can see that no precompiling is performed
<img width="1048" alt="截屏2022-10-25 11 40 04" src="https://user-images.githubusercontent.com/60163868/197676949-8016d0d1-9874-45fd-ba3f-89c63d8a2c90.png">
# SysUserController.java
<img width="1278" alt="截屏2022-10-25 11 40 32" sr... | [CVE-2022-45208]/sys/user/putRecycleBin is affected by sql injection | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4126/comments | 2 | 2022-10-25T03:44:24Z | 2022-12-07T01:05:07Z | https://github.com/jeecgboot/JeecgBoot/issues/4126 | 1,421,795,524 | 4,126 | 4,432 |
CVE-2022-45210 | 2022-11-25T17:15:11.230 | Jeecg-boot v3.4.3 was discovered to contain a SQL injection vulnerability via the component /sys/user/deleteRecycleBin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jeecg-boot.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/4125"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "49DF84AE-6D1A-4065-AB0B-CB6926D6C5F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4125 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | # sysUserMapper.xml
deleteLogicDeleted. You can see that no precompiling is performed
<img width="617" alt="截屏2022-10-25 11 04 50" src="https://user-images.githubusercontent.com/60163868/197672626-fb8257e3-ca86-484e-a4aa-e878ebb31c34.png">
# SysUserController.java
<img width="811" alt="截屏2022-10-25 11 06 04" src="... | [CVE-2022-45210]/sys/user/deleteRecycleBin is affected by sql injection | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4125/comments | 2 | 2022-10-25T03:12:40Z | 2022-12-07T01:16:36Z | https://github.com/jeecgboot/JeecgBoot/issues/4125 | 1,421,774,671 | 4,125 | 4,433 |
CVE-2022-39334 | 2022-11-25T19:15:11.350 | Nextcloud also ships a CLI utility called nextcloudcmd which is sometimes used for automated scripting and headless servers. Versions of nextcloudcmd prior to 3.6.1 would incorrectly trust invalid TLS certificates, which may enable a Man-in-the-middle attack that exposes sensitive data or credentials to a network attac... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 3.9,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integrityI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nextcloud/desktop/issues/4927"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nextcloud:desktop:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A7633B29-D30E-483A-BDB1-41514D9358A6",
"versionEndExcluding": "3.6.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"295"
] | 295 | https://github.com/nextcloud/desktop/issues/4927 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nextcloud",
"desktop"
] | ### ⚠️ Before submitting, please verify the following: ⚠️
- [X] This is a **bug**, not a question or a configuration issue.
- [X] This issue is **not** already reported on Github (I've searched it).
- [X] Nextcloud Server and Desktop Client are **up to date**. See [Server Maintenance and Release Schedule](https://gith... | [Bug]: nextcloudcmd incorrectly trusts bad TLS certs | https://api.github.com/repos/nextcloud/desktop/issues/4927/comments | 3 | 2022-09-10T19:46:57Z | 2025-01-17T06:07:19Z | https://github.com/nextcloud/desktop/issues/4927 | 1,368,715,169 | 4,927 | 4,434 |
CVE-2022-45907 | 2022-11-26T02:15:10.253 | In PyTorch before trunk/89695, torch.jit.annotations.parse_type_line can cause arbitrary code execution because eval is used unsafely. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pytorch/pytorch/commit/767f6aa49fe20a2766b9843d01e3b7f7793df6a3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:pytorch:*:*:*:*:*:python:*:*",
"matchCriteriaId": "17B8827A-469E-484D-845F-8DA235DB1BBA",
"versionEndExcluding": "1.13.1",
"versionEndIncluding": null,
"versi... | [
"94"
] | 94 | https://github.com/pytorch/pytorch/issues/88868 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"pytorch",
"pytorch"
] | ### 🐛 Describe the bug
In `torch.jit.annotations`, it looks like there are some functions that are deprecated, but still retain code, which may lead to some backdoors, especially since some of these functions still use eval while implementing.
But now I'm not sure if there are some features (jit decorator) in some ... | `torch.jit.annotations.parse_type_line` is not safe (command injection) even it seems already deprecated. | https://api.github.com/repos/pytorch/pytorch/issues/88868/comments | 16 | 2022-11-11T04:09:54Z | 2022-12-16T21:06:00Z | https://github.com/pytorch/pytorch/issues/88868 | 1,444,898,821 | 88,868 | 4,435 |
CVE-2022-45933 | 2022-11-27T03:15:11.180 | KubeView through 0.1.31 allows attackers to obtain control of a Kubernetes cluster because api/scrape/kube-system does not require authentication, and retrieves certificate files that can be used for authentication as kube-admin. NOTE: the vendor's position is that KubeView was a "fun side project and a learning exerci... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/benc-uk/kubeview/issues/95"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubeview_project:kubeview:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5E7E24E4-AA8C-4708-98D2-C991863DBB12",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.31",
"versionS... | [
"306"
] | 306 | https://github.com/benc-uk/kubeview/issues/95 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"benc-uk",
"kubeview"
] | Hello,
may you please consider **adding authentication** to **KubeView?**
a `curl` to the the API for the `kube-system` namespace would return certificate files that can be used for authentication and **ultimately lead to taking full control over the k8s cluster!**
the request would be like this:
```bash
... | [CVE-2022-45933] Critical Security Issue that could lead to full cluster takeover | https://api.github.com/repos/benc-uk/kubeview/issues/95/comments | 5 | 2022-11-20T15:38:34Z | 2025-05-31T17:00:05Z | https://github.com/benc-uk/kubeview/issues/95 | 1,456,946,197 | 95 | 4,436 |
CVE-2022-38900 | 2022-11-28T13:15:10.033 | decode-uri-component 0.2.0 is vulnerable to Improper Input Validation resulting in DoS. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/SamVerschueren/decode-uri-component/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:decode-uri-component_project:decode-uri-component:0.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E5FAEFE5-8016-43E2-A600-46EC2CCAD87E",
"versionEndExcluding": null,
"versionEndIncluding": nul... | [
"20"
] | 20 | https://github.com/SamVerschueren/decode-uri-component/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"SamVerschueren",
"decode-uri-component"
] | Crash occured when `%ea%ba%5a%ba` is parsed by `decodeUriComponent`
This function is used in some other nodejs projects for decoding query strings and hash strings in url, for example the hash `# kun%ea%ba%5a%ba` is valid and should be parsed correctly as `{ ' kun%ea%ba%5a%ba': null }`
For example in chrome's d... | TypeError: decodeComponents(...).join is not a function | https://api.github.com/repos/SamVerschueren/decode-uri-component/issues/5/comments | 2 | 2022-08-24T09:32:21Z | 2022-12-01T21:48:16Z | https://github.com/SamVerschueren/decode-uri-component/issues/5 | 1,349,145,334 | 5 | 4,437 |
CVE-2022-38900 | 2022-11-28T13:15:10.033 | decode-uri-component 0.2.0 is vulnerable to Improper Input Validation resulting in DoS. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/SamVerschueren/decode-uri-component/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:decode-uri-component_project:decode-uri-component:0.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E5FAEFE5-8016-43E2-A600-46EC2CCAD87E",
"versionEndExcluding": null,
"versionEndIncluding": nul... | [
"20"
] | 20 | https://github.com/sindresorhus/query-string/issues/345 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sindresorhus",
"query-string"
] | Version: `v7.1.1`
Crash occured when `# kun%ea%ba%5a%ba` is parsed by `queryString.parse`
This hash is valid and should be parsed correctly as `{ ' kun%ea%ba%5a%ba': null }`
For example in chrome's development tools' console the url `https://google.com# kun%ea%ba%5a%ba` can be parsed without problems:
```
c... | TypeError: decodeComponents(...).join is not a function | https://api.github.com/repos/sindresorhus/query-string/issues/345/comments | 12 | 2022-08-24T08:20:26Z | 2022-12-02T08:04:34Z | https://github.com/sindresorhus/query-string/issues/345 | 1,349,056,021 | 345 | 4,438 |
CVE-2022-44937 | 2022-11-28T21:15:10.617 | Bosscms v2.0.0 was discovered to contain a Cross-Site Request Forgery (CSRF) via the Add function under the Administrator List module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/5497lvren/Zhenhao/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bosscms:bosscms:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3515006B-917D-420E-A026-3341F59BA61F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/5497lvren/Zhenhao/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"5497lvren",
"Zhenhao"
] | Download link:
https://gitee.com/Greenpeas/BOSSCMS/repository/archive/V2.0202210100920.zip
version:v2.0.0
The issue in the background - > User - > administrator list -> add
![The issue in the b... | Bosscms v2.0.0 a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/5497lvren/Zhenhao/issues/1/comments | 0 | 2022-11-02T07:04:23Z | 2022-11-02T07:09:59Z | https://github.com/5497lvren/Zhenhao/issues/1 | 1,432,609,817 | 1 | 4,439 |
CVE-2022-45921 | 2022-11-28T21:15:10.747 | FusionAuth before 1.41.3 allows a file outside of the application root to be viewed or retrieved using an HTTP request. To be specific, an attacker may be able to view or retrieve any file readable by the user running the FusionAuth process. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://fusionauth.io/docs/v1/tech/release-notes"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FusionAu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fusionauth:fusionauth:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9E1FF535-F9FA-4576-99AA-F43450B7229E",
"versionEndExcluding": "1.41.3",
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/FusionAuth/fusionauth-issues/issues/1983 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FusionAuth",
"fusionauth-issues"
] | ## Mitigate traversal attack
### Description
A potential exists for a traversal attack.
### Affects versions
Versions greater than or equal to `1.37.0` and less than `1.41.3` are affected.
### Related
CVE-2022-45921
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=2022-45921
### Community guidelines... | Mitigate traversal attack - CVE-2022-45921 | https://api.github.com/repos/FusionAuth/fusionauth-issues/issues/1983/comments | 0 | 2022-11-28T15:28:05Z | 2022-11-28T15:29:49Z | https://github.com/FusionAuth/fusionauth-issues/issues/1983 | 1,466,625,921 | 1,983 | 4,440 |
CVE-2022-45202 | 2022-11-29T04:15:11.207 | GPAC v2.1-DEV-rev428-gcb8ae46c8-master was discovered to contain a stack overflow via the function dimC_box_read at isomedia/box_code_3gpp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2296"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2296 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Stack buffer overflow in function dimC_box_read at isomedia/box_code_3gpp.c:1070
### System info
ubuntu 20.04 lts
### version info:
···
/MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev428-gcb8ae46c8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please ... | Stack buffer overflow in function dimC_box_read at isomedia/box_code_3gpp.c:1070 | https://api.github.com/repos/gpac/gpac/issues/2296/comments | 1 | 2022-10-31T01:21:46Z | 2022-11-04T08:28:44Z | https://github.com/gpac/gpac/issues/2296 | 1,429,110,423 | 2,296 | 4,441 |
CVE-2022-45204 | 2022-11-29T04:15:11.253 | GPAC v2.1-DEV-rev428-gcb8ae46c8-master was discovered to contain a memory leak via the function dimC_box_read at isomedia/box_code_3gpp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2307"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/2307 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Memory Leak in dimC_box_read at isomedia/box_code_3gpp.c:1060
### System info
ubuntu 20.04 lts
###
version info:
```
./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev460-g9d963dc62-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in y... | Memory Leak in dimC_box_read at isomedia/box_code_3gpp.c:1060 | https://api.github.com/repos/gpac/gpac/issues/2307/comments | 1 | 2022-11-07T12:35:15Z | 2022-11-08T02:28:56Z | https://github.com/gpac/gpac/issues/2307 | 1,438,293,014 | 2,307 | 4,442 |
CVE-2022-45343 | 2022-11-29T16:15:09.293 | GPAC v2.1-DEV-rev478-g696e6f868-master was discovered to contain a heap use-after-free via the Q_IsTypeOn function at /gpac/src/bifs/unquantize.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2315"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2315 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | # Description
Heap use after free in Q_IsTypeOn at gpac/src/bifs/unquantize.c:175:12
# System info
Ubuntu 20.04 lts
# Version info
```shell
MP4Box - GPAC version 2.1-DEV-rev478-g696e6f868-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your r... | Heap use after free in Q_IsTypeOn at gpac/src/bifs/unquantize.c | https://api.github.com/repos/gpac/gpac/issues/2315/comments | 0 | 2022-11-14T01:55:34Z | 2022-11-14T13:45:21Z | https://github.com/gpac/gpac/issues/2315 | 1,447,239,893 | 2,315 | 4,443 |
CVE-2022-45332 | 2022-11-30T03:15:13.973 | LibreDWG v0.12.4.4643 was discovered to contain a heap buffer overflow via the function decode_preR13_section_hdr at decode_r11.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/524"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.4.4643:*:*:*:*:*:*:*",
"matchCriteriaId": "8B1D693A-7DFD-40CC-B3E7-D2B6E5F5ADD1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/524 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | **System info**
Ubuntu x86_64, clang 10.0
version: 0.12.4.4643, last commit [93c2512](https://github.com/LibreDWG/libredwg/commit/93c25124c191987af168ace9fe4b5623061874bd)
**Command line**
./dwg2dxf poc
**Poc**
poc: [poc](https://github.com/iorra-cifer/Poc/blob/main/libredwg/heap-buffer-overflow?raw=true)
... | heap-buffer-overflow exists in the function decode_preR13_section_hdr in decode_r11.c | https://api.github.com/repos/LibreDWG/libredwg/issues/524/comments | 1 | 2022-11-13T04:23:10Z | 2022-11-30T12:14:12Z | https://github.com/LibreDWG/libredwg/issues/524 | 1,446,725,478 | 524 | 4,444 |
CVE-2022-44096 | 2022-11-30T05:15:11.187 | Sanitization Management System v1.0 was discovered to contain hardcoded credentials which allows attackers to escalate privileges and access the admin panel. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upasvi/CVE-/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sanitization_management_system_project:sanitization_management_system:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9FB7FB55-B294-42EB-8C91-5B0106071352",
"versionEndExcluding": null,
"version... | [
"798"
] | 798 | https://github.com/upasvi/CVE-/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upasvi",
"CVE-"
] | Sanitization Management System — Use of Hard-coded Credentials in Source Code Leads to Admin Panel Access
Exploit Author: Upasana Bohra
Vendor Homepage: https://www.sourcecodester.com/php-project
Software Link: https://www.sourcecodester.com/php/15770/sanitization-management-system-project-php-and-mysql-fre... | Sanitization Management System — Use of Hard-coded Credentials in Source Code Leads to Admin Panel Access | https://api.github.com/repos/Upasanabohra/CVE-/issues/1/comments | 0 | 2022-10-18T06:32:33Z | 2022-10-18T06:32:33Z | https://github.com/Upasanabohra/CVE-/issues/1 | 1,412,648,121 | 1 | 4,445 |
CVE-2022-44097 | 2022-11-30T05:15:11.257 | Book Store Management System v1.0 was discovered to contain hardcoded credentials which allows attackers to escalate privileges and access the admin panel. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upasvi/CVE-/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:book_store_management_system_project:book_store_management_system:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "7E1BB334-C4F4-456D-B55F-61A06A11757D",
"versionEndExcluding": null,
"versionEndI... | [
"798"
] | 798 | https://github.com/upasvi/CVE-/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upasvi",
"CVE-"
] | Book Store Management System— Use of Hard-coded Credentials in Source Code Leads to Admin Panel Access
Exploit Author: Upasana Bohra
Vendor Homepage: https://www.sourcecodester.com/php-project
Software Link: https://www.sourcecodester.com/php/15748/book-store-management-system-project-using-php-codeigniter-3-f... | Book Store Management System— Use of Hard-coded Credentials in Source Code Leads to Admin Panel Access | https://api.github.com/repos/Upasanabohra/CVE-/issues/2/comments | 0 | 2022-10-18T07:04:27Z | 2022-10-18T07:04:27Z | https://github.com/Upasanabohra/CVE-/issues/2 | 1,412,682,326 | 2 | 4,446 |
CVE-2022-40489 | 2022-12-01T05:15:11.730 | ThinkCMF version 6.0.7 is affected by a Cross Site Request Forgery (CSRF) vulnerability that allows a Super Administrator user to be injected into administrative users. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinkcmf/thinkcmf/issues/736"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkcmf:thinkcmf:6.0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "3F02595D-FE6B-481C-87D7-E31A5C955FED",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/thinkcmf/thinkcmf/issues/736 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinkcmf",
"thinkcmf"
] | Hi,
I found a CSRF in ThinkCMF version 6.0.7 that allows a remote user to add a Super Admin account by taking advantage of the session of an administrator who is logged into the system. Below are the steps to reproduce this issue.
1. The remote user tricks the logged in administrator into visiting a malicious site.... | I found a CSRF that creates a Super Admin account. | https://api.github.com/repos/thinkcmf/thinkcmf/issues/736/comments | 0 | 2022-09-14T16:45:34Z | 2022-10-04T17:17:52Z | https://github.com/thinkcmf/thinkcmf/issues/736 | 1,373,294,253 | 736 | 4,447 |
CVE-2022-40849 | 2022-12-01T05:15:11.890 | ThinkCMF version 6.0.7 is affected by Stored Cross-Site Scripting (XSS). An attacker who successfully exploited this vulnerability could inject a Persistent XSS payload in the Slideshow Management section that execute arbitrary JavaScript code on the client side, e.g., to steal the administrator's PHP session token (PH... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinkcmf/thinkcmf/issues/737"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkcmf:thinkcmf:6.0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "3F02595D-FE6B-481C-87D7-E31A5C955FED",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/thinkcmf/thinkcmf/issues/737 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinkcmf",
"thinkcmf"
] | ThinkCMF version 6.0.7 is vulnerable to Stored Cross-Site Scripting. More precisely, the component that manages the slideshows allows you to insert HTML tags and JavaScript code in the Name field.
Here are the steps to reproduce the issue.
1. A remote user tricks the logged in administrator into visiting a maliciou... | XSS Stored in the Slideshow Management component. | https://api.github.com/repos/thinkcmf/thinkcmf/issues/737/comments | 0 | 2022-09-14T17:27:15Z | 2022-10-04T17:17:42Z | https://github.com/thinkcmf/thinkcmf/issues/737 | 1,373,343,106 | 737 | 4,448 |
CVE-2022-4247 | 2022-12-01T08:15:09.370 | A vulnerability classified as critical was found in Movie Ticket Booking System. This vulnerability affects unknown code of the file booking.php. The manipulation of the argument id leads to sql injection. The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aman05382/movie_ticket_booking_system_php/issues/1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:movie_ticket_booking_system_project:movie_ticket_booking_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BD1CC14F-D9F9-4E98-9CD1-69C3BECFF808",
"versionEndExcluding": null,
"versionEndInclu... | [
"707"
] | 707 | https://github.com/aman05382/movie_ticket_booking_system_php/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aman05382",
"movie_ticket_booking_system_php"
] | # Building environment:Apache2.4.49;MySQL5.7.26;PHP7.3.4
## 1.Movie Ticket Booking System-PHP SQL injection vulnerability exists
In Booking Php, from line 4 to line 12 of the code,the value of id is passed to the backend through the get request, and is assigned to the variable $id, then $id is substituted into th... | Movie Ticket Booking System-PHP SQL injection vulnerability exists | https://api.github.com/repos/aman05382/movie_ticket_booking_system_php/issues/1/comments | 0 | 2022-12-01T02:06:51Z | 2022-12-01T07:24:57Z | https://github.com/aman05382/movie_ticket_booking_system_php/issues/1 | 1,470,541,722 | 1 | 4,449 |
CVE-2022-4248 | 2022-12-01T08:15:09.470 | A vulnerability, which was classified as critical, has been found in Movie Ticket Booking System. This issue affects some unknown processing of the file editBooking.php. The manipulation of the argument id leads to sql injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aman05382/movie_ticket_booking_system_php/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:movie_ticket_booking_system_project:movie_ticket_booking_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BD1CC14F-D9F9-4E98-9CD1-69C3BECFF808",
"versionEndExcluding": null,
"versionEndInclu... | [
"707"
] | 707 | https://github.com/aman05382/movie_ticket_booking_system_php/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aman05382",
"movie_ticket_booking_system_php"
] | # Building environment:Apache2.4.49;MySQL5.7.26;PHP7.3.4
## 1.Movie Ticket Booking System-PHP SQL injection vulnerability exists
At editBooking In PHP, in lines 30-38 of the code, the parameters requested by the front-end POST include first, last, number, email, and amount, while the variable $id is controllable.... | Movie Ticket Booking System-PHP SQL injection vulnerability exists | https://api.github.com/repos/aman05382/movie_ticket_booking_system_php/issues/3/comments | 0 | 2022-12-01T02:08:01Z | 2022-12-01T07:25:15Z | https://github.com/aman05382/movie_ticket_booking_system_php/issues/3 | 1,470,542,890 | 3 | 4,450 |
CVE-2022-4249 | 2022-12-01T08:15:09.560 | A vulnerability, which was classified as problematic, was found in Movie Ticket Booking System. Affected is an unknown function of the component POST Request Handler. The manipulation of the argument ORDER_ID leads to cross site scripting. It is possible to launch the attack remotely. The exploit has been disclosed to ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aman05382/movie_ticket_booking_system_php/issues/5"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:movie_ticket_booking_system_project:movie_ticket_booking_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BD1CC14F-D9F9-4E98-9CD1-69C3BECFF808",
"versionEndExcluding": null,
"versionEndInclu... | [
"79"
] | 79 | https://github.com/aman05382/movie_ticket_booking_system_php/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aman05382",
"movie_ticket_booking_system_php"
] | # Building environment:Apache2.4.49;MySQL5.7.26;PHP7.3.4
## 1.Movie Ticket Booking System-PHP XSS vulnerability
inTxnStatus. Php, code line 17: ORDER_ The variable $ORDER whose ID is input by the user and assigned through POST request_ The ID is then directly output in line 44 of the code. Value="<? Php echo $ORD... | Movie Ticket Booking System-PHP XSS vulnerability | https://api.github.com/repos/aman05382/movie_ticket_booking_system_php/issues/5/comments | 0 | 2022-12-01T02:09:03Z | 2022-12-01T07:24:47Z | https://github.com/aman05382/movie_ticket_booking_system_php/issues/5 | 1,470,543,844 | 5 | 4,451 |
CVE-2022-4250 | 2022-12-01T08:15:09.660 | A vulnerability has been found in Movie Ticket Booking System and classified as problematic. Affected by this vulnerability is an unknown functionality of the file booking.php. The manipulation of the argument id leads to cross site scripting. The attack can be launched remotely. The exploit has been disclosed to the p... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aman05382/movie_ticket_booking_system_php/issues/2"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:movie_ticket_booking_system_project:movie_ticket_booking_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BD1CC14F-D9F9-4E98-9CD1-69C3BECFF808",
"versionEndExcluding": null,
"versionEndInclu... | [
"707"
] | 707 | https://github.com/aman05382/movie_ticket_booking_system_php/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aman05382",
"movie_ticket_booking_system_php"
] | # Building environment:Apache2.4.49;MySQL5.7.26;PHP7.3.4
## 1.Movie Ticket Booking System-PHP XSS vulnerability
There is an XSS vulnerability in Booking In PHP, at line 111, we can see that the value is equal to the value of the variable $id, and the $id controllable variable is determined by user input and outpu... | Movie Ticket Booking System-PHP XSS vulnerability | https://api.github.com/repos/aman05382/movie_ticket_booking_system_php/issues/2/comments | 0 | 2022-12-01T02:07:31Z | 2022-12-01T07:25:22Z | https://github.com/aman05382/movie_ticket_booking_system_php/issues/2 | 1,470,542,393 | 2 | 4,452 |
CVE-2022-4251 | 2022-12-01T08:15:09.760 | A vulnerability was found in Movie Ticket Booking System and classified as problematic. Affected by this issue is some unknown functionality of the file editBooking.php. The manipulation leads to cross site scripting. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. The... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.4,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aman05382/movie_ticket_booking_system_php/issues/4"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:movie_ticket_booking_system_project:movie_ticket_booking_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BD1CC14F-D9F9-4E98-9CD1-69C3BECFF808",
"versionEndExcluding": null,
"versionEndInclu... | [
"707"
] | 707 | https://github.com/aman05382/movie_ticket_booking_system_php/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aman05382",
"movie_ticket_booking_system_php"
] | # Building environment:Apache2.4.49;MySQL5.7.26;PHP7.3.4
Movie Ticket Booking System-PHP-There is a storage XSS vulnerability
At editBooking In PHP, from the 63rd line of code to the 70th line of code, the content entered by the user is directly stored in the database without filtering, and then displayed and... | Movie Ticket Booking System-PHP-There is a storage XSS vulnerability | https://api.github.com/repos/aman05382/movie_ticket_booking_system_php/issues/4/comments | 0 | 2022-12-01T02:08:30Z | 2022-12-01T07:25:07Z | https://github.com/aman05382/movie_ticket_booking_system_php/issues/4 | 1,470,543,332 | 4 | 4,453 |
CVE-2022-44290 | 2022-12-02T20:15:13.880 | webTareas 2.4p5 was discovered to contain a SQL injection vulnerability via the id parameter in deleteapprovalstages.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/2"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"89"
] | 89 | https://github.com/anhdq201/webtareas/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
The id parameter appears to be vulnerable to SQL injection attacks.
# Proof of Concept
**Step 1:** Go to "/approvals/deleteapprovalstages.php?id=1", add payload '+and+1=1' to id parameter and see response have return data
---
 vulnerability in the Add Announcement function at /index.php?module=help_pages/pages&entities_id=24. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Title field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in "Add announcement" function in the "Help System" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=help_pages/pages&entities_id=24", click "Add announcement" and insert payload "`<im... | Stored Cross Site Scripting Vulnerability on "Help system" in "Add announcement" function in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/14/comments | 1 | 2022-11-02T15:18:02Z | 2022-12-09T03:50:13Z | https://github.com/anhdq201/rukovoditel/issues/14 | 1,433,334,314 | 14 | 4,456 |
CVE-2022-44945 | 2022-12-02T20:15:14.103 | Rukovoditel v3.2.1 was discovered to contain a SQL injection vulnerability via the heading_field_id parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/anhdq201/rukovoditel/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
The heading_field_id parameter appears to be vulnerable to SQL injection attacks. A single quote was submitted in the heading_field_id parameter, and a database error message was returned. Two single quotes were then submitted and the error message disappeared.
# Proof of Concept
... | SQL injection Vulnerability on "heading_field_id" in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/16/comments | 2 | 2022-11-02T15:43:14Z | 2022-12-09T03:53:49Z | https://github.com/anhdq201/rukovoditel/issues/16 | 1,433,375,562 | 16 | 4,457 |
CVE-2022-44946 | 2022-12-02T20:15:14.180 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the Add Page function at /index.php?module=help_pages/pages&entities_id=24. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Title field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in "Add page" function in the "Help System" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=help_pages/pages&entities_id=24", click "Add page" and insert payload "`<img src=1 onerror=... | Stored Cross Site Scripting Vulnerability on "Help system" in "Add page" function in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/15/comments | 1 | 2022-11-02T15:20:58Z | 2022-12-09T03:56:50Z | https://github.com/anhdq201/rukovoditel/issues/15 | 1,433,340,558 | 15 | 4,458 |
CVE-2022-44947 | 2022-12-02T20:15:14.257 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the Highlight Row feature at /index.php?module=entities/listing_types&entities_id=24. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Note field after cl... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Permissions Required",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in "Note" field in the "Highlight row" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=entities/listing_types&entities_id=24", click "Add" and insert payload "`<img src=1 onerror='ale... | Stored Cross Site Scripting Vulnerability on "Highlight row" in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/13/comments | 1 | 2022-11-02T15:15:30Z | 2022-12-09T03:58:05Z | https://github.com/anhdq201/rukovoditel/issues/13 | 1,433,328,656 | 13 | 4,459 |
CVE-2022-44948 | 2022-12-02T20:15:14.320 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the Entities Group feature at/index.php?module=entities/entities_groups. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field after clicking "Add". | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Entities groups" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=entities/entities_groups", click "Add" and insert payload "`<img src=1 onerror='alert(document.coookie)'/>`" i... | Stored Cross Site Scripting Vulnerability on "Entities groups" in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/8/comments | 1 | 2022-11-02T13:26:05Z | 2022-12-09T03:58:58Z | https://github.com/anhdq201/rukovoditel/issues/8 | 1,433,146,115 | 8 | 4,460 |
CVE-2022-44949 | 2022-12-02T20:15:14.397 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the Add New Field function at /index.php?module=entities/fields&entities_id=24. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Short Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in "Short Name" field in the "Fields Configuration" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=entities/fields&entities_id=24", click "Add New Field" and insert payload "`<img sr... | Stored Cross Site Scripting Vulnerability on "Fields Configuration" in "Short Name" field in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/12/comments | 1 | 2022-11-02T15:06:25Z | 2022-12-09T03:59:25Z | https://github.com/anhdq201/rukovoditel/issues/12 | 1,433,309,977 | 12 | 4,461 |
CVE-2022-44950 | 2022-12-02T20:15:14.463 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the Add New Field function at /index.php?module=entities/fields&entities_id=24. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in "Name" field in the "Fields Configuration" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=entities/fields&entities_id=24", click "Add New Field" and insert payload "`<img src=1 on... | Stored Cross Site Scripting Vulnerability on "Fields Configuration" in "Name" field in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/10/comments | 1 | 2022-11-02T14:54:55Z | 2022-12-09T04:00:03Z | https://github.com/anhdq201/rukovoditel/issues/10 | 1,433,291,930 | 10 | 4,462 |
CVE-2022-44951 | 2022-12-02T20:15:14.523 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in the Add New Form tab function at /index.php?module=entities/forms&entities_id=24. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Form Configuration" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=entities/forms&entities_id=24", click "Add New Form Tab" and insert payload "`<img src=1 onerror='alert(doc... | Stored Cross Site Scripting Vulnerability on "Form Configuration" in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/11/comments | 1 | 2022-11-02T14:57:10Z | 2022-12-09T04:00:32Z | https://github.com/anhdq201/rukovoditel/issues/11 | 1,433,296,033 | 11 | 4,463 |
CVE-2022-44952 | 2022-12-02T20:15:14.583 | Rukovoditel v3.2.1 was discovered to contain a stored cross-site scripting (XSS) vulnerability in /index.php?module=configuration/application. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Copyright Text field after clicking "Add". | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable",
"URL Repurposed"
],
"url": "http://rukovoditel.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:3.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "AF93014A-D2CB-48B2-AB57-692E95E5702D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/anhdq201/rukovoditel/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"rukovoditel"
] | # Version: 3.2.1
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Application Settings" feature.
# Proof of Concept
**Step 1:** Go to "/index.php?module=configuration/application", click "Add" and insert payload "`<img src=1 onerror='alert(document.cookie)'/... | Stored Cross Site Scripting Vulnerability on "Application Settings" in rukovoditel 3.2.1 | https://api.github.com/repos/anhdq201/rukovoditel/issues/9/comments | 1 | 2022-11-02T13:26:15Z | 2022-12-09T04:01:05Z | https://github.com/anhdq201/rukovoditel/issues/9 | 1,433,146,355 | 9 | 4,464 |
CVE-2022-44953 | 2022-12-02T20:15:14.647 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /linkedcontent/listfiles.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field after clicking "Add". | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/8"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Files" feature.
# Proof of Concept
**Step 1:** Go to "/linkedcontent/listfiles.php?doc_type=0&id=0", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`" in "Name... | Stored Cross Site Scripting Vulnerability Bypass filter on "Files" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/8/comments | 1 | 2022-11-02T17:40:23Z | 2022-12-09T04:07:02Z | https://github.com/anhdq201/webtareas/issues/8 | 1,433,539,867 | 8 | 4,465 |
CVE-2022-44954 | 2022-12-02T20:15:14.703 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /contacts/listcontacts.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Last Name field after clicking "Add". | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/10"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Contacts" feature.
# Proof of Concept
**Step 1:** Go to "/contacts/listcontacts.php?", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`" in "Last Name" field.
... | Stored Cross Site Scripting Vulnerability Bypass filter on "Contacts" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/10/comments | 1 | 2022-11-02T17:46:44Z | 2022-12-09T04:07:48Z | https://github.com/anhdq201/webtareas/issues/10 | 1,433,547,467 | 10 | 4,466 |
CVE-2022-44955 | 2022-12-02T20:15:14.767 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the Chat function. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Messages field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/5"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Chat" feature.
# Proof of Concept
**Step 1:** Go to "Chat" feature, insert payload "`<details/open/ontoggle=alert(document.cookie)>`" and click "Enter" in "Messages" field.
---
 vulnerability in the component /projects/listprojects.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/3"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in "Add projects" function in the "Projects" feature.
# Proof of Concept
**Step 1:** Go to "/projects/listprojects.php?", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)... | Stored Cross Site Scripting Vulnerability Bypass filter on "Projects" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/3/comments | 1 | 2022-11-02T16:56:12Z | 2022-12-09T04:08:56Z | https://github.com/anhdq201/webtareas/issues/3 | 1,433,482,717 | 3 | 4,468 |
CVE-2022-44957 | 2022-12-02T20:15:14.897 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /clients/listclients.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/11"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Clients" feature.
# Proof of Concept
**Step 1:** Go to "/clients/listclients.php?", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`" in "Name" field.
---
![... | Stored Cross Site Scripting Vulnerability Bypass filter on "Clients" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/11/comments | 1 | 2022-11-02T17:48:51Z | 2022-12-09T04:09:22Z | https://github.com/anhdq201/webtareas/issues/11 | 1,433,549,869 | 11 | 4,469 |
CVE-2022-44959 | 2022-12-02T20:15:14.967 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /meetings/listmeetings.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/6"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Meetings" feature.
# Proof of Concept
**Step 1:** Go to "/meetings/listmeetings.php?", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`" in "Name" field.
---
... | Stored Cross Site Scripting Vulnerability Bypass filter on "Meetings" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/6/comments | 1 | 2022-11-02T17:34:26Z | 2022-12-09T04:09:56Z | https://github.com/anhdq201/webtareas/issues/6 | 1,433,532,834 | 6 | 4,470 |
CVE-2022-44960 | 2022-12-02T20:15:15.023 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /general/search.php?searchtype=simple. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Search field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/4"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Search" feature.
# Proof of Concept
**Step 1:** Go to "/general/search.php?searchtype=simple", click "Search" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`".
---
![ima... | Reflect Cross Site Scripting Vulnerability Bypass filter on "Search" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/4/comments | 1 | 2022-11-02T17:15:31Z | 2022-12-09T04:11:42Z | https://github.com/anhdq201/webtareas/issues/4 | 1,433,508,329 | 4 | 4,471 |
CVE-2022-44961 | 2022-12-02T20:15:15.077 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /forums/editforum.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/7"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Forums" feature.
# Proof of Concept
**Step 1:** Go to "/forums/editforum.php?", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`" in "Name" field.
---
![imag... | Stored Cross Site Scripting Vulnerability Bypass filter on "Forums" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/7/comments | 1 | 2022-11-02T17:38:14Z | 2022-12-09T04:12:11Z | https://github.com/anhdq201/webtareas/issues/7 | 1,433,537,422 | 7 | 4,472 |
CVE-2022-44962 | 2022-12-02T20:15:15.133 | webtareas 2.4p5 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /calendar/viewcalendar.php. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Subject field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://webtareas.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/anhdq201/webtareas/issues/12"
},
{
"so... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webtareas_project:webtareas:2.4:p5:*:*:*:*:*:*",
"matchCriteriaId": "94C4D4FE-5B6C-48AA-AFCC-C0BEDF27E9D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/anhdq201/webtareas/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"anhdq201",
"webtareas"
] | # Version: 2.4p5
# Description
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Calendar" feature.
# Proof of Concept
**Step 1:** Go to "/calendar/viewcalendar.php?", click "Add" and insert payload "`<details/open/ontoggle=alert(document.cookie)>`" in "Subject" field.
-... | Stored Cross Site Scripting Vulnerability Bypass filter on "Calendar" feature in webtareas 2.4p5 | https://api.github.com/repos/anhdq201/webtareas/issues/12/comments | 3 | 2022-11-02T17:50:45Z | 2022-12-09T04:20:17Z | https://github.com/anhdq201/webtareas/issues/12 | 1,433,551,961 | 12 | 4,473 |
CVE-2022-4272 | 2022-12-03T09:15:08.950 | A vulnerability, which was classified as critical, has been found in FeMiner wms. Affected by this issue is some unknown functionality of the file /product/savenewproduct.php?flag=1. The manipulation of the argument upfile leads to unrestricted upload. The attack may be launched remotely. The exploit has been disclosed... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": null,
"url": "http://www.openwall.com/lists/oss-security/2023/04/26/1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FeMiner/wms/issues/14"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:warehouse_management_system_project:warehouse_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "C2B64B6B-5234-4C15-99B3-8B195D20872A",
"versionEndExcluding": null,
"versionEndInclu... | [
"266"
] | 266 | https://github.com/FeMiner/wms/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FeMiner",
"wms"
] | ## WMS has a file upload code execution vulnerability
## Build environment: Apache 2.4.39; MySQL5.0.96; PHP5.3.29
### 1.in /src/product/addproduct.php,On lines 242-246 of the code

Upfile is a parameter for uploading picture... | WMS has a file upload code execution vulnerability | https://api.github.com/repos/FeMiner/wms/issues/14/comments | 0 | 2022-11-29T14:50:54Z | 2022-12-03T07:49:00Z | https://github.com/FeMiner/wms/issues/14 | 1,468,199,248 | 14 | 4,474 |
CVE-2022-4274 | 2022-12-03T16:15:09.917 | A vulnerability, which was classified as critical, was found in House Rental System. Affected is an unknown function of the file /view-property.php. The manipulation of the argument property_id leads to sql injection. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nikeshtiwari1/House-Rental-System/issues/6"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:house_rental_system_project:house_rental_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CCFC3381-1E5A-43F1-8930-099904962A98",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/nikeshtiwari1/House-Rental-System/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nikeshtiwari1",
"House-Rental-System"
] | # Build environment: Apache 2.4.39; MySQL5.7.26; PHP7.3.4
## SQL injection vulnerability in House Rental System
In view property In PHP, from line 32 to line 34 of the code, property_ The ID is passed to the backend through get and assigned to the variable $property_ ID, and then executed the SQL statement query,... | SQL injection vulnerability in House Rental System | https://api.github.com/repos/nikeshtiwari1/House-Rental-System/issues/6/comments | 0 | 2022-12-02T01:45:04Z | 2022-12-17T07:11:58Z | https://github.com/nikeshtiwari1/House-Rental-System/issues/6 | 1,472,190,546 | 6 | 4,475 |
CVE-2022-4275 | 2022-12-03T16:15:10.047 | A vulnerability has been found in House Rental System and classified as critical. Affected by this vulnerability is an unknown functionality of the file search-property.php of the component POST Request Handler. The manipulation of the argument search_property leads to sql injection. The attack can be launched remotely... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nikeshtiwari1/House-Rental-System/issues/7"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:house_rental_system_project:house_rental_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CCFC3381-1E5A-43F1-8930-099904962A98",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/nikeshtiwari1/House-Rental-System/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nikeshtiwari1",
"House-Rental-System"
] | # Build environment: Apache 2.4.39; MySQL5.7.26; PHP7.3.4
## SQL injection vulnerability exists in search-property.php
In search property In PHP, in lines 52-54 of the code, search_ The property is transferred to the backend through the post request and assigned to the variable $q_ String, and then it is substitu... | SQL injection vulnerability exists in search-property.php | https://api.github.com/repos/nikeshtiwari1/House-Rental-System/issues/7/comments | 0 | 2022-12-02T01:45:49Z | 2022-12-17T07:11:51Z | https://github.com/nikeshtiwari1/House-Rental-System/issues/7 | 1,472,190,983 | 7 | 4,476 |
CVE-2022-4276 | 2022-12-03T16:15:10.143 | A vulnerability was found in House Rental System and classified as critical. Affected by this issue is some unknown functionality of the file tenant-engine.php of the component POST Request Handler. The manipulation of the argument id_photo leads to unrestricted upload. The attack may be launched remotely. The exploit ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nikeshtiwari1/House-Rental-System/issues/8"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:house_rental_system_project:house_rental_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CCFC3381-1E5A-43F1-8930-099904962A98",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/nikeshtiwari1/House-Rental-System/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nikeshtiwari1",
"House-Rental-System"
] | Build environment: Apache 2.4.39; MySQL5.7.26; PHP7.3.4
1. Tenst-register.php has a file upload vulnerability
```php+HTML
<form method="POST" action="tenant-engine.php" enctype="multipart/form-data">
```
tenant-register. PHP, the ninth line of code. The information filled in by the front end includes the u... | Tenst-register.php has a file upload vulnerability | https://api.github.com/repos/nikeshtiwari1/House-Rental-System/issues/8/comments | 0 | 2022-12-02T01:46:42Z | 2022-12-17T07:11:39Z | https://github.com/nikeshtiwari1/House-Rental-System/issues/8 | 1,472,191,544 | 8 | 4,477 |
CVE-2022-41642 | 2022-12-05T04:15:09.857 | OS command injection vulnerability in Nadesiko3 (PC Version) v3.3.61 and earlier allows a remote attacker to execute an arbitrary OS command when processing compression and decompression on the product. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "vultures@jpcert.or.jp",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kujirahand/nadesiko3/issues/1325"
},
{
"source": "vultures@jpcert.or.jp",
"tags": [
"Issue Tracking",
"Patch",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kujirahand:nadesiko3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C5A044E7-2248-4B46-9E15-F65F69F61CB6",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.68",
"versionStartE... | [
"78"
] | 78 | https://github.com/kujirahand/nadesiko3/issues/1325 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kujirahand",
"nadesiko3"
] | なでしこ3のPC版(Node.js版)において「圧縮」「解凍」について、コマンドインジェクションの問題がありました。
以下のコミットで修正済みです。
- 56ccfb2f9cceaec83e6a9d3024c3ba8c54ebe1a4
- 61a70792752a75b7f71df214e98a236721ea3fa6
- 124871c064cfc65cdcd83205637e84fc246c76df
このバグに気付いてもらえただけでも、セキュリティネクストキャンプで講師やって良かったです!!
@satoki
報告、ありがとうございました!
| cnako3の圧縮解凍の問題 | https://api.github.com/repos/kujirahand/nadesiko3/issues/1325/comments | 1 | 2022-08-24T04:27:39Z | 2022-10-07T05:19:34Z | https://github.com/kujirahand/nadesiko3/issues/1325 | 1,348,845,959 | 1,325 | 4,478 |
CVE-2022-41642 | 2022-12-05T04:15:09.857 | OS command injection vulnerability in Nadesiko3 (PC Version) v3.3.61 and earlier allows a remote attacker to execute an arbitrary OS command when processing compression and decompression on the product. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "vultures@jpcert.or.jp",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kujirahand/nadesiko3/issues/1325"
},
{
"source": "vultures@jpcert.or.jp",
"tags": [
"Issue Tracking",
"Patch",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kujirahand:nadesiko3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C5A044E7-2248-4B46-9E15-F65F69F61CB6",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.68",
"versionStartE... | [
"78"
] | 78 | https://github.com/kujirahand/nadesiko3/issues/1347 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kujirahand",
"nadesiko3"
] | - appkeyが短かったため総当たりでキーが取得される可能性があった
- appkeyが取得された場合、nako3editにおいてファイル名経由で任意のコマンドを実行される問題があった。
- (例) http://localhost:8888/html/edit.html?file=`xeyes`.nako&appkey=K8078c3
- 以下コード中のdecodeURIComponentに不正な値が渡ることでサーバ機能が強制終了する問題があった
- (例) http://localhost:8888/html/edit.html?file=%
| nako3editのファイルの扱いの問題 | https://api.github.com/repos/kujirahand/nadesiko3/issues/1347/comments | 1 | 2022-10-07T04:00:42Z | 2022-10-07T05:42:16Z | https://github.com/kujirahand/nadesiko3/issues/1347 | 1,400,586,471 | 1,347 | 4,479 |
CVE-2022-45283 | 2022-12-06T00:15:10.257 | GPAC MP4box v2.0.0 was discovered to contain a stack overflow in the smil_parse_time_list parameter at /scenegraph/svg_attributes.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2295"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7AEE044-50E9-4230-B492-A5FF18653115",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2295 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [X] I looked for a similar issue and couldn't find any.
- [X] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [X] I give enough info... | GPAC-2.0.0 MP4Box: stack overflow with unlimited length and controllable content in smil_parse_time_list | https://api.github.com/repos/gpac/gpac/issues/2295/comments | 0 | 2022-10-29T18:52:22Z | 2022-11-04T08:28:14Z | https://github.com/gpac/gpac/issues/2295 | 1,428,405,742 | 2,295 | 4,480 |
CVE-2022-44289 | 2022-12-06T16:15:11.337 | Thinkphp 5.1.41 and 5.0.24 has a code logic error which causes file upload getshell. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/top-think/framework/issues/2772"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkphp:thinkphp:5.0.24:*:*:*:*:*:*:*",
"matchCriteriaId": "A396FB8E-3328-435E-998E-70426F1F5FFA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"434"
] | 434 | https://github.com/top-think/framework/issues/2772 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"top-think",
"framework"
] | **Code logic error causes file upload getshell**
Verify version:Thinkphp5.1.41/Thinkphp5.0.24
Install:composer create-project topthink/think tp 5.xxx
test version:Thinkphp5.1.41
If the user directly uses the move method of thinkphp
like this:Add an upload controller like the official documentation:[https://www... | Code logic error causes file upload getshell | https://api.github.com/repos/top-think/framework/issues/2772/comments | 5 | 2022-10-23T06:53:23Z | 2024-10-08T01:50:16Z | https://github.com/top-think/framework/issues/2772 | 1,419,671,628 | 2,772 | 4,481 |
CVE-2022-44942 | 2022-12-07T02:15:09.497 | Casdoor before v1.126.1 was discovered to contain an arbitrary file deletion vulnerability via the uploadFile function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/casdoor/casdoor/issues/1171"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:casbin:casdoor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "61CC9797-6380-4BAC-B4CD-18F04197D310",
"versionEndExcluding": "1.126.1",
"versionEndIncluding": null,
"versionStartExclud... | [
"22"
] | 22 | https://github.com/casdoor/casdoor/issues/1171 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"casdoor",
"casdoor"
] | Hi,
I was looking at the fix to https://github.com/casdoor/casdoor/issues/1035:
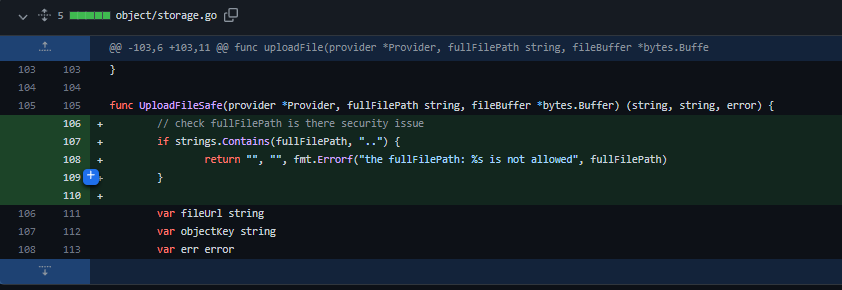
And I noticed it only fixes the path traversal in file upload, while file deletion is still vulnerable.
Thus, it's possi... | Arbitrary file delete vulnerability | https://api.github.com/repos/casdoor/casdoor/issues/1171/comments | 2 | 2022-09-30T10:05:05Z | 2022-09-30T16:39:26Z | https://github.com/casdoor/casdoor/issues/1171 | 1,392,193,950 | 1,171 | 4,482 |
CVE-2022-45025 | 2022-12-07T02:15:10.223 | Markdown Preview Enhanced v0.6.5 and v0.19.6 for VSCode and Atom was discovered to contain a command injection vulnerability via the PDF file import function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/shd101wyy/vscode-markdown-preview-enhanced/issues/639"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:markdown_preview_enhanced_project:markdown_preview_enhanced:0.6.5:*:*:*:*:atom:*:*",
"matchCriteriaId": "267A6438-0CAF-4A16-8FB9-9A734FD0E7F7",
"versionEndExcluding": null,
"versionEndIn... | [
"78"
] | 78 | https://github.com/shd101wyy/vscode-markdown-preview-enhanced/issues/639 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"shd101wyy",
"vscode-markdown-preview-enhanced"
] | Video PoC for VSCode on [YouTube](https://www.youtube.com/watch?v=bnK5DPdb5JU):
[](https://www.youtube.com/watch?v=bnK5DPdb5JU)
Original issue: [shd101wyy/mume, OS command injection in PDF import functionality](https://github.com/shd101wyy/mume/issues/273)
S... | [Vulnerability] Code exection via markdown preview | https://api.github.com/repos/shd101wyy/vscode-markdown-preview-enhanced/issues/639/comments | 1 | 2022-11-22T20:44:14Z | 2022-12-07T20:22:03Z | https://github.com/shd101wyy/vscode-markdown-preview-enhanced/issues/639 | 1,460,527,375 | 639 | 4,483 |
CVE-2022-45026 | 2022-12-07T02:15:10.410 | An issue in Markdown Preview Enhanced v0.6.5 and v0.19.6 for VSCode and Atom allows attackers to execute arbitrary commands during the GFM export process. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/shd101wyy/vscode-markdown-preview-enhanced/issues/640"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:markdown_preview_enhanced_project:markdown_preview_enhanced:0.6.5:*:*:*:*:atom:*:*",
"matchCriteriaId": "267A6438-0CAF-4A16-8FB9-9A734FD0E7F7",
"versionEndExcluding": null,
"versionEndIn... | [
"78"
] | 78 | https://github.com/shd101wyy/vscode-markdown-preview-enhanced/issues/640 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"shd101wyy",
"vscode-markdown-preview-enhanced"
] | Video PoC for VSCode on [YouTube](https://www.youtube.com/watch?v=D0HdwtDoFXs):
[](https://www.youtube.com/watch?v=D0HdwtDoFXs)
Original issue: [shd101wyy/mume, OS command injection via Memraid PNG export](https://github.com/shd101wyy/mume/issues/274)
STR (ple... | [Vulnerability] Code execution via GitHub Flavored Markdown export | https://api.github.com/repos/shd101wyy/vscode-markdown-preview-enhanced/issues/640/comments | 1 | 2022-11-22T20:44:39Z | 2022-12-07T20:23:41Z | https://github.com/shd101wyy/vscode-markdown-preview-enhanced/issues/640 | 1,460,527,817 | 640 | 4,484 |
CVE-2022-44371 | 2022-12-07T17:15:10.967 | hope-boot 1.0.0 has a deserialization vulnerability that can cause Remote Code Execution (RCE). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/java-aodeng/hope-boot/issues/83"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hope-boot_project:hope-boot:1.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83023A51-1288-480A-97A1-43CCFDCF1CCE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/java-aodeng/hope-boot/issues/83 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"java-aodeng",
"hope-boot"
] | The author has set a fixed key in the com.hope.shiro.config.ShiroConfig under the hope-admin package and uses this key to encrypt the rememberMe parameter in the cookie. This situation can lead to a deserialisation attack with very serious consequences.
![1](https://user-images.githubusercontent.com/75016675/198077595... | There is a deserialization vulnerability that can cause RCE | https://api.github.com/repos/java-aodeng/hope-boot/issues/83/comments | 0 | 2022-10-26T16:06:26Z | 2022-10-26T16:18:55Z | https://github.com/java-aodeng/hope-boot/issues/83 | 1,424,310,612 | 83 | 4,485 |
CVE-2022-44351 | 2022-12-07T19:15:09.853 | Skycaiji v2.5.1 was discovered to contain a deserialization vulnerability via /SkycaijiApp/admin/controller/Mystore.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zorlan/skycaiji/issues/46"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:skycaiji:skycaiji:2.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D42AD2A1-FD75-4B28-A11D-3635BB32D06D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"502"
] | 502 | https://github.com/zorlan/skycaiji/issues/46 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zorlan",
"skycaiji"
] | I found a deserialization vulnerability in v2.5.1
URL: http://localhost/index.php?s=/admin/mystore/upload
<img width="1512" alt="" src="https://user-images.githubusercontent.com/72502573/197928307-eb1f204b-0551-4b40-83e1-b1d2465c068b.png">
unserialize's parameter can control by uploading the file contains the payloa... | Skycaiji has a deserialization vulnerability in v2.5.1 | https://api.github.com/repos/zorlan/skycaiji/issues/46/comments | 0 | 2022-10-26T03:45:52Z | 2023-01-26T10:43:33Z | https://github.com/zorlan/skycaiji/issues/46 | 1,423,392,464 | 46 | 4,486 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.