cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-36594 | 2022-09-02T04:15:11.363 | Mapper v4.0.0 to v4.2.0 was discovered to contain a SQL injection vulnerability via the ids parameter at the selectByIds function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/abel533/Mapper/issues/862"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mybatis:mapper:*:*:*:*:*:*:*:*",
"matchCriteriaId": "94A446F8-F70E-404C-B30D-B85F686F37C0",
"versionEndExcluding": null,
"versionEndIncluding": "4.2.0",
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/abel533/Mapper/issues/862 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"abel533",
"Mapper"
] | Write the following test demo:
1、UserController.java:
@Controller
public class UserController {
@Autowired
UserService userService;
@RequestMapping("gets")
@ResponseBody
public List<User> getUser(String ids) {
List<String> idList = Arrays.asList(ids.split(","));
retur... | selectByIds function sql injection | https://api.github.com/repos/abel533/Mapper/issues/862/comments | 3 | 2022-07-20T06:58:52Z | 2022-07-21T00:53:13Z | https://github.com/abel533/Mapper/issues/862 | 1,310,540,938 | 862 | 4,083 |
CVE-2022-36600 | 2022-09-02T05:15:07.417 | BlogEngine v3.3.8.0 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /blogengine/api/posts. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Description field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/BlogEngine/BlogEngine.NET/issues/254"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blogengine:blogengine.net:3.3.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C215046E-4B0C-44AD-B0C4-D055FE17A873",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/BlogEngine/BlogEngine.NET/issues/254 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"BlogEngine",
"BlogEngine.NET"
] | A Cross Site Scripting vulnerabilty exists in BlogEngine via the Description field in /blogengine/api/posts
Step to exploit:
1. Login as admin.
2. Navigate to http://127.0.0.1/blogengine/admin/#/content/posts and click on "NEW".
3. Insert XSS payload `<img src=1 onerror=alert('XSS')>` in the "Description" field a... | Cross-Site Scripting (XSS) in "/blogengine/api/posts" | https://api.github.com/repos/BlogEngine/BlogEngine.NET/issues/254/comments | 0 | 2022-07-20T15:46:07Z | 2022-08-01T03:49:37Z | https://github.com/BlogEngine/BlogEngine.NET/issues/254 | 1,311,382,952 | 254 | 4,084 |
CVE-2022-37679 | 2022-09-02T05:15:07.610 | Miniblog.Core v1.0 was discovered to contain a cross-site scripting (XSS) vulnerability in the component /blog/edit. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Excerpt field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/madskristensen/Miniblog.Core/issues/178"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniblog.core_project:miniblog.core:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "49DAF53E-1D8A-41BA-8408-5B4590DE33B4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"79"
] | 79 | https://github.com/madskristensen/Miniblog.Core/issues/178 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"madskristensen",
"Miniblog.Core"
] | A Cross Site Scripting vulnerabilty exists in Miniblog.Core via the Excerpt field in "/posts"
Step to exploit:
1. Login as admin.
2. Navigate to https://miniblogcore.azurewebsites.net/blog/edit.
3. Insert XSS payload `<img src=1 onerror=alert('XSS')>` in the "Excerpt" field and click on Save.
4. Go to Home page.... | Cross-Site Scripting (XSS) in "/posts" | https://api.github.com/repos/madskristensen/Miniblog.Core/issues/178/comments | 0 | 2022-08-01T03:39:09Z | 2022-08-01T03:39:09Z | https://github.com/madskristensen/Miniblog.Core/issues/178 | 1,323,762,815 | 178 | 4,085 |
CVE-2020-22669 | 2022-09-02T18:15:11.607 | Modsecurity owasp-modsecurity-crs 3.2.0 (Paranoia level at PL1) has a SQL injection bypass vulnerability. Attackers can use the comment characters and variable assignments in the SQL syntax to bypass Modsecurity WAF protection and implement SQL injection attacks on Web applications. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/SpiderLabs/owasp-modsecurity-crs/issues/1727"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:owasp:owasp_modsecurity_core_rule_set:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2DABE2C3-F827-4B87-8051-7EE4C536FE0F",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/SpiderLabs/owasp-modsecurity-crs/issues/1727 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"SpiderLabs",
"owasp-modsecurity-crs"
] | ### Description
Fuzz found that the following request can bypass modesecurity rules and implement SQLi injection.
sample code:`user.php`(id parameter has SQL injection security issues)
```
<?php
echo "<head><title>SQL injection demo</title></head>";
$id=$_GET['id'];
$conn=new mysqli('127.0.0.1','root','root','... | SQLi bypass at PL1(CRS 3.2.0) | https://api.github.com/repos/SpiderLabs/owasp-modsecurity-crs/issues/1727/comments | 1 | 2020-03-28T15:47:00Z | 2020-04-03T23:31:41Z | https://github.com/SpiderLabs/owasp-modsecurity-crs/issues/1727 | 589,601,789 | 1,727 | 4,086 |
CVE-2021-27693 | 2022-09-02T18:15:11.687 | Server-side Request Forgery (SSRF) vulnerability in PublicCMS before 4.0.202011.b via /publiccms/admin/ueditor when the action is catchimage. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/sanluan/PublicCMS/commit/0f4c4872914b6a71305e121a7d9a19c07cde0338"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:publiccms:publiccms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C947C87C-1E2D-4732-9A7A-84652BCF240E",
"versionEndExcluding": "4.0.202011.b",
"versionEndIncluding": null,
"versionS... | [
"918"
] | 918 | https://github.com/sanluan/PublicCMS/issues/51 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sanluan",
"PublicCMS"
] | Hello,I found a SSRF in the lastest version of PublicCMS-V4.0.202011.b
The vulnerability is triggered by visiting the following address after logging in the management background
http://192.168.6.237:8081/publiccms/admin/ueditor?action=catchimage&file%5b%5d=http://192.168.103.3
http://192.168.6.237:8081/publiccms/... | There is a SSRF vulnerability via /publiccms/admin/ueditor | https://api.github.com/repos/sanluan/PublicCMS/issues/51/comments | 1 | 2021-02-23T09:33:07Z | 2021-10-28T04:55:16Z | https://github.com/sanluan/PublicCMS/issues/51 | 814,280,961 | 51 | 4,087 |
CVE-2022-36071 | 2022-09-02T18:15:12.150 | SFTPGo is configurable SFTP server with optional HTTP/S, FTP/S and WebDAV support. SFTPGo WebAdmin and WebClient support login using TOTP (Time-based One Time Passwords) as a secondary authentication factor. Because TOTPs are often configured on mobile devices that can be lost, stolen or damaged, SFTPGo also supports r... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 8.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integri... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/drakkan/sftpgo/issues/965"
},
{
"source": "security-advisories@github.com",
"tags": [
"Mitigation",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sftpgo_project:sftpgo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "154C23FB-9676-4167-A174-476FB50A6C06",
"versionEndExcluding": "2.3.4",
"versionEndIncluding": null,
"versionStartE... | [
"916"
] | 916 | https://github.com/drakkan/sftpgo/issues/965 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"drakkan",
"sftpgo"
] | **Area**
Web Client MFA /web/client/mfa
**Summary**
Not sure if this is the expected behaviour, but a user required to use MFA has the option to generate recovery codes
even before configuring and enabling it on account . This option is available after logging in with username / password. This means an atta... | TOTP Generate Recovery Codes MFA | https://api.github.com/repos/drakkan/sftpgo/issues/965/comments | 1 | 2022-08-30T16:36:09Z | 2022-09-01T14:23:52Z | https://github.com/drakkan/sftpgo/issues/965 | 1,356,032,979 | 965 | 4,088 |
CVE-2022-36647 | 2022-09-02T22:15:08.523 | PKUVCL davs2 v1.6.205 was discovered to contain a global buffer overflow via the function parse_sequence_header() at source/common/header.cc:269. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pkuvcl/davs2/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:davs2_project:davs2:1.6.205:*:*:*:*:*:*:*",
"matchCriteriaId": "BC996119-1C77-46E0-AC3D-AB460FB614CC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"120"
] | 120 | https://github.com/pkuvcl/davs2/issues/29 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pkuvcl",
"davs2"
] | **Describe the bug**
Bug Relevant code as follows:
====================================================================================
static
int parse_sequence_header(davs2_mgr_t *mgr, davs2_seq_t *seq, davs2_bs_t *bs)
{
......
seq->head.bitrate = ((seq->bit_rate_upper << 18) + seq->bit_ra... | Global-buffer-overflow in parse_sequence_header() --> source/common/header.cc:269 | https://api.github.com/repos/pkuvcl/davs2/issues/29/comments | 3 | 2022-07-21T10:50:43Z | 2022-09-03T13:39:10Z | https://github.com/pkuvcl/davs2/issues/29 | 1,313,064,467 | 29 | 4,089 |
CVE-2022-39829 | 2022-09-05T04:15:08.790 | There is a NULL pointer dereference in aes256_encrypt in Samsung mTower through 0.3.0 due to a missing check on the return value of EVP_CIPHER_CTX_new. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/mTower/blob/18f4b592a8a973ce5972f4e2658ea0f6e3686284/tools/ecdsa_keygen.c#L135"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samsung:mtower:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C72C53B-9CF2-4F9A-90C1-3A1FE236BA5B",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.0",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/Samsung/mTower/issues/75 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Samsung",
"mTower"
] | # Affected components
affected source code file: tools/ecdsa_keygen.c
# Attack vector(s)
Lacking a check for the return value of EVP_CIPHER_CTX_new.
EVP_CIPHER_CTX_new() returns a pointer to a newly created EVP_CIPHER_CTX for success and NULL for failure.
# Suggested description of the vulnerability for u... | Security: NULL Pointer Dereference in the function aes256_encrypt() | https://api.github.com/repos/Samsung/mTower/issues/75/comments | 1 | 2022-09-02T03:29:31Z | 2022-09-05T20:21:41Z | https://github.com/Samsung/mTower/issues/75 | 1,359,661,025 | 75 | 4,090 |
CVE-2022-39839 | 2022-09-05T06:15:18.417 | Cotonti Siena 0.9.20 allows admins to conduct stored XSS attacks via a forum post. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Technical Description"
],
"url": "https://github.com/Cotonti/Cotonti/issues/1661"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Techni... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cotonti:cotonti_siena:0.9.20:*:*:*:*:*:*:*",
"matchCriteriaId": "F3269E7D-8B8A-4991-A712-3F629FF84779",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/Cotonti/Cotonti/issues/1661 | [
"Exploit",
"Issue Tracking",
"Technical Description"
] | github.com | [
"Cotonti",
"Cotonti"
] | Hello, we found the stored xss on forum.
Tested on latest version 0.9.20.
Poc:
1. Create new topic with poll
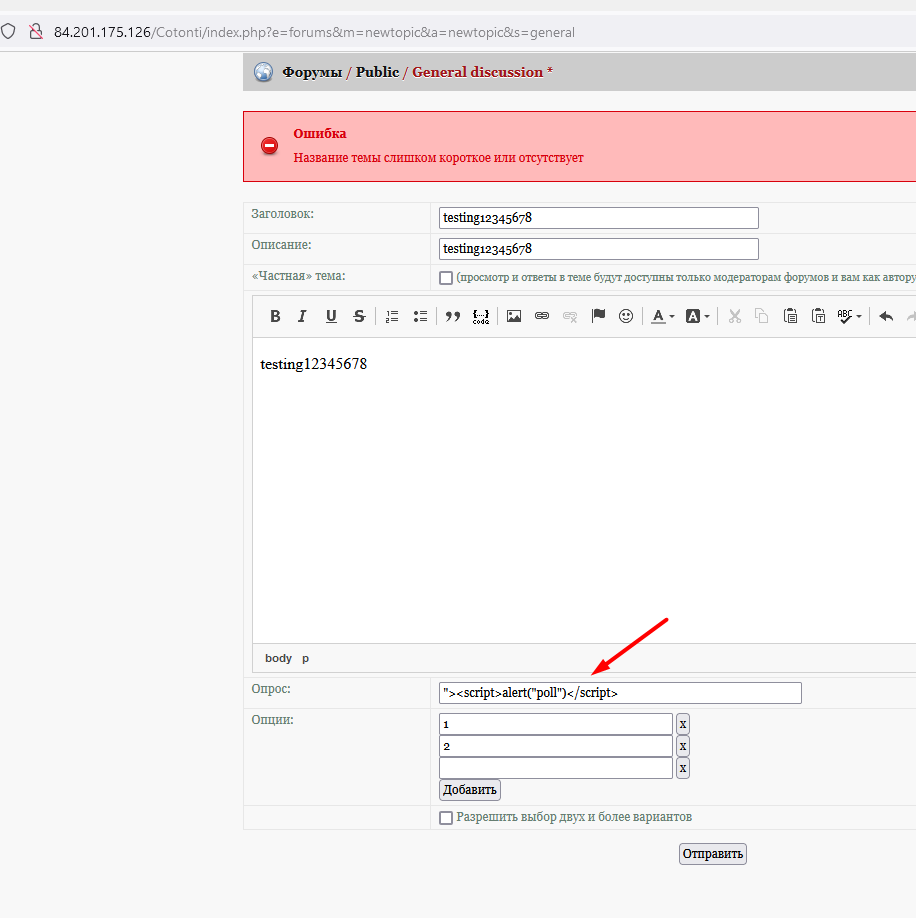
2. XSS execute
. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cotonti/Cotonti/issues/1660"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cotonti:cotonti_siena:0.9.20:*:*:*:*:*:*:*",
"matchCriteriaId": "F3269E7D-8B8A-4991-A712-3F629FF84779",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/Cotonti/Cotonti/issues/1660 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cotonti",
"Cotonti"
] | Hello, we found the stored xss.
Tested on latest version 0.9.20.
Poc:
1. Write a DM to any user
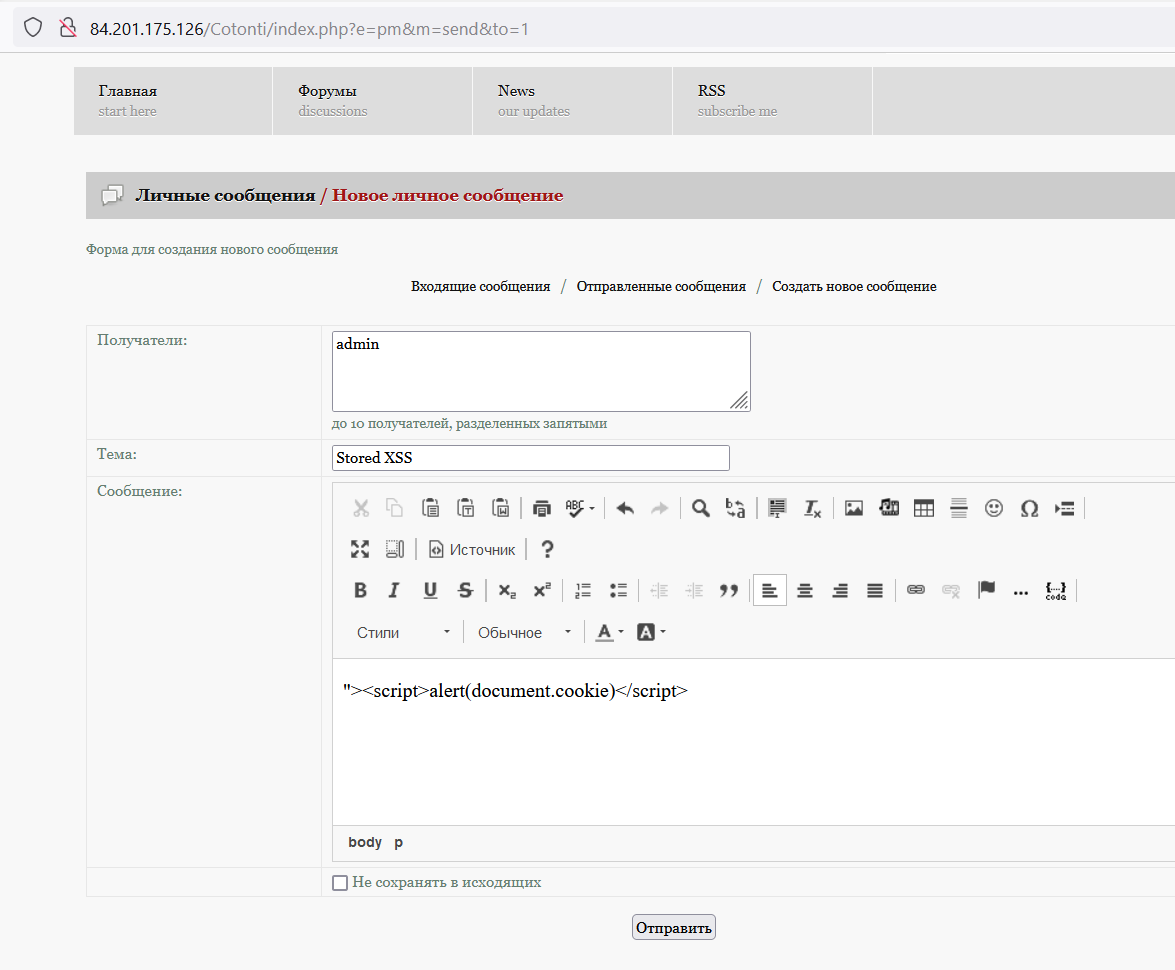
2. Then read the incoming message and press "quote" to quote the message with payload. Press the bu... | Stored XSS | https://api.github.com/repos/Cotonti/Cotonti/issues/1660/comments | 4 | 2022-08-30T18:58:49Z | 2022-09-04T11:00:02Z | https://github.com/Cotonti/Cotonti/issues/1660 | 1,356,177,543 | 1,660 | 4,092 |
CVE-2022-39843 | 2022-09-05T07:15:08.207 | 123elf Lotus 1-2-3 before 1.0.0rc3 for Linux, and Lotus 1-2-3 R3 for UNIX and other platforms through 9.8.2, allow attackers to execute arbitrary code via a crafted worksheet. This occurs because of a stack-based buffer overflow in the cell format processing routines, as demonstrated by a certain function call from pro... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taviso/123elf/issues/103"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lotus_1-2-3_project:lotus_1-2-3:1.0.0:rc1:*:*:*:*:*:*",
"matchCriteriaId": "8E852959-16B3-469D-9F65-E614E6E25C8E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"787"
] | 787 | https://github.com/taviso/123elf/issues/103 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taviso",
"123elf"
] | The unnamed function at 0x80bb148 is used to copy data into a buffer and lacks a destination length check. This function is called in two places - by `process_fmt()` and `fmt_cell_combine()`. The call by `process_fmt()` is reachable using a `w3r_format` element (0x13) in a wk3 file, where user-controlled data from th... | Exploitable Stack Overflow | https://api.github.com/repos/taviso/123elf/issues/103/comments | 6 | 2022-09-04T00:40:42Z | 2022-09-11T17:48:15Z | https://github.com/taviso/123elf/issues/103 | 1,360,997,448 | 103 | 4,093 |
CVE-2022-3008 | 2022-09-05T09:15:10.110 | The tinygltf library uses the C library function wordexp() to perform file path expansion on untrusted paths that are provided from the input file. This function allows for command injection by using backticks. An attacker could craft an untrusted path input that would result in a path expansion. We recommend upgrading... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve-coordination@google.com",
"tags": [
"Exploit",
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=49053"
},
{
"source": "cve-coordination@google.com",
"tags": [
"Product"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinygltf_project:tinygltf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "078C039E-D2B4-44A7-BEC7-7B77F794FB1D",
"versionEndExcluding": "2.6.0",
"versionEndIncluding": null,
"versionSt... | [
"77"
] | 77 | https://github.com/syoyo/tinygltf/issues/368 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"syoyo",
"tinygltf"
] | **Describe the issue**
This is a security vulnerability. The `wordexp` call here allows arbitrary code execution https://github.com/syoyo/tinygltf/blob/0fa56e239c77cc864dc248842e8887d985cf8e3f/tiny_gltf.h#L2640 when parsing a gltf file.
**To Reproduce**
- OS: Linux
- Compiler, compiler version, compile options... | Command injection via wordexp call. | https://api.github.com/repos/syoyo/tinygltf/issues/368/comments | 6 | 2022-08-16T06:57:34Z | 2022-09-05T23:23:45Z | https://github.com/syoyo/tinygltf/issues/368 | 1,339,900,556 | 368 | 4,094 |
CVE-2022-25308 | 2022-09-06T18:15:11.437 | A stack-based buffer overflow flaw was found in the Fribidi package. This flaw allows an attacker to pass a specially crafted file to the Fribidi application, which leads to a possible memory leak or a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-25308"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:fribidi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A9E50E4E-F644-4B2F-8972-60E055F52B68",
"versionEndExcluding": "1.0.12",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"121"
] | 121 | https://github.com/fribidi/fribidi/issues/181 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"fribidi",
"fribidi"
] | Hi, I found a bug, stack-buffer-overflow.
- SUMMARY:
AddressSanitizer: stack-buffer-overflow (/home/lin/fribidi/bin/fribidi+0x5ab4) in main
- Version
```
➜ bin git:(master) ✗ ./fribidi --version
fribidi (GNU FriBidi) 1.0.11
interface version 4,
Unicode Character Database version 14.0.0,
Configure opt... | stack-buffer-overflow on address 0x7ffda2c0112f at pc 0x5580929d7ab5 bp 0x7ffda2bc1820 sp 0x7ffda2bc1810 | https://api.github.com/repos/fribidi/fribidi/issues/181/comments | 1 | 2021-12-22T09:03:41Z | 2022-03-25T05:09:43Z | https://github.com/fribidi/fribidi/issues/181 | 1,086,605,471 | 181 | 4,095 |
CVE-2022-25309 | 2022-09-06T18:15:11.493 | A heap-based buffer overflow flaw was found in the Fribidi package and affects the fribidi_cap_rtl_to_unicode() function of the fribidi-char-sets-cap-rtl.c file. This flaw allows an attacker to pass a specially crafted file to the Fribidi application with the '--caprtl' option, leading to a crash and causing a denial o... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-25309"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bug... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:fribidi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A9E50E4E-F644-4B2F-8972-60E055F52B68",
"versionEndExcluding": "1.0.12",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"122"
] | 122 | https://github.com/fribidi/fribidi/issues/182 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"fribidi",
"fribidi"
] | Hi, I found a bug, heap-buffer-overflow.
- SUMMARY:
SUMMARY: AddressSanitizer: heap-buffer-overflow (/home/lin/fribidi/bin/fribidi+0x108fe) in fribidi_cap_rtl_to_unicode
- Version
```
➜ bin git:(master) ✗ ./fribidi --version
fribidi (GNU FriBidi) 1.0.11
interface version 4,
Unicode Character Database v... | heap-buffer-overflow (/home/lin/fribidi/bin/fribidi+0x108fe) in fribidi_cap_rtl_to_unicode | https://api.github.com/repos/fribidi/fribidi/issues/182/comments | 3 | 2021-12-22T09:07:41Z | 2022-04-19T19:55:33Z | https://github.com/fribidi/fribidi/issues/182 | 1,086,608,926 | 182 | 4,096 |
CVE-2022-25310 | 2022-09-06T18:15:11.557 | A segmentation fault (SEGV) flaw was found in the Fribidi package and affects the fribidi_remove_bidi_marks() function of the lib/fribidi.c file. This flaw allows an attacker to pass a specially crafted file to Fribidi, leading to a crash and causing a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-25310"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bug... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:fribidi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A9E50E4E-F644-4B2F-8972-60E055F52B68",
"versionEndExcluding": "1.0.12",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/fribidi/fribidi/issues/183 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"fribidi",
"fribidi"
] | Hi, I found a bug, SEGV.
- SUMMARY:
SUMMARY: AddressSanitizer: SEGV (/home/lin/fribidi/bin/fribidi+0x66a5) in fribidi_remove_bidi_marks
- Version
```
➜ bin git:(master) ✗ ./fribidi --version
fribidi (GNU FriBidi) 1.0.11
interface version 4,
Unicode Character Database version 14.0.0,
Configure options.... | SEGV on unknown address 0x000000000000 (pc 0x55cc8b6086a6 bp 0x7ffed6538790 sp 0x7ffed6538740 T0) | https://api.github.com/repos/fribidi/fribidi/issues/183/comments | 1 | 2021-12-22T09:10:25Z | 2022-03-30T19:03:07Z | https://github.com/fribidi/fribidi/issues/183 | 1,086,611,188 | 183 | 4,097 |
CVE-2020-21516 | 2022-09-06T19:15:08.290 | There is an arbitrary file upload vulnerability in FeehiCMS 2.0.8 at the head image upload, that allows attackers to execute relevant PHP code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/46"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:2.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "4AEB1B4F-33FF-4363-BB98-B7151666907B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/liufee/cms/issues/46 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | There is an arbitrary file upload vulnerability in the background avatar upload.
The CMS only verified the suffix of the file in the front end by js, and we found that we could upload the PHP scripts directly after using Burp Suite for package capture modification.
 files. A user opening a malicious PYC file could be affected by this vulnerability, allowing an attacker to execute code on the user's machine... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rizinorg/rizin/commit/68948017423a12786704e54227b8b2f918c2fd27"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rizin:rizin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5E797DF4-7DCA-46AA-9A36-5C0064FE79CA",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.0",
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/rizinorg/rizin/issues/2963 | [
"Third Party Advisory"
] | github.com | [
"rizinorg",
"rizin"
] | Hi! We've been fuzzing your project and found the following errors in `librz/bin/format/pyc/marshal.c`
### Work environment
OS: Ubuntu 20.04
File format: -
rizin version: https://github.com/rizinorg/rizin/commit/4b385978a1a33252c4f829d3db59fb3056afadb9
### Bug description
Heap out-of-bounds write (segv) o... | Multiple heap out-of-bounds writes of size 1 in marshal.c | https://api.github.com/repos/rizinorg/rizin/issues/2963/comments | 1 | 2022-08-22T11:08:29Z | 2022-08-24T00:26:43Z | https://github.com/rizinorg/rizin/issues/2963 | 1,346,224,089 | 2,963 | 4,100 |
CVE-2022-36041 | 2022-09-06T20:15:08.673 | Rizin is a UNIX-like reverse engineering framework and command-line toolset. Versions 0.4.0 and prior are vulnerable to an out-of-bounds write when parsing Mach-O files. A user opening a malicious Mach-O file could be affected by this vulnerability, allowing an attacker to execute code on the user's machine. Commit num... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rizinorg/rizin/commit/7323e64d68ecccfb0ed3ee480f704384c38676b2"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rizin:rizin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5E797DF4-7DCA-46AA-9A36-5C0064FE79CA",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.0",
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/rizinorg/rizin/issues/2956 | [
"Third Party Advisory"
] | github.com | [
"rizinorg",
"rizin"
] | Hi! We've been fuzzing your project and found the following error in `librz/bin/format/mach0/mach0.c`
### Work environment
OS: Ubuntu 20.04
File format: -
rizin version: https://github.com/rizinorg/rizin/commit/4b385978a1a33252c4f829d3db59fb3056afadb9
### Bug description
Heap out-of-bounds write of size 2... | Heap out-of-bounds write in mach0.c | https://api.github.com/repos/rizinorg/rizin/issues/2956/comments | 2 | 2022-08-22T10:50:17Z | 2022-08-24T00:26:44Z | https://github.com/rizinorg/rizin/issues/2956 | 1,346,201,672 | 2,956 | 4,101 |
CVE-2022-36043 | 2022-09-06T20:15:08.740 | Rizin is a UNIX-like reverse engineering framework and command-line toolset. Versions 0.4.0 and prior are vulnerable to a double free in bobj.c:rz_bin_reloc_storage_free() when freeing relocations generated from qnx binary plugin. A user opening a malicious qnx binary could be affected by this vulnerability, allowing a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rizinorg/rizin/commit/a3d50c1ea185f3f642f2d8180715f82d98840784"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rizin:rizin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5E797DF4-7DCA-46AA-9A36-5C0064FE79CA",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.0",
"versionStartExcluding":... | [
"415"
] | 415 | https://github.com/rizinorg/rizin/issues/2964 | [
"Third Party Advisory"
] | github.com | [
"rizinorg",
"rizin"
] | Hi! We've been fuzzing your project and found the following error in `librz/bin/bobj.c:142`
### Work environment
OS: Ubuntu 20.04
File format: -
rizin version: https://github.com/rizinorg/rizin/commit/4b385978a1a33252c4f829d3db59fb3056afadb9
### Bug description
Heap double-free in `librz/bin/bobj.c:142:3`... | double-free in bobj.c | https://api.github.com/repos/rizinorg/rizin/issues/2964/comments | 2 | 2022-08-22T11:11:15Z | 2022-08-24T00:26:42Z | https://github.com/rizinorg/rizin/issues/2964 | 1,346,227,624 | 2,964 | 4,102 |
CVE-2022-36067 | 2022-09-06T22:15:09.207 | vm2 is a sandbox that can run untrusted code with whitelisted Node's built-in modules. In versions prior to version 3.9.11, a threat actor can bypass the sandbox protections to gain remote code execution rights on the host running the sandbox. This vulnerability was patched in the release of version 3.9.11 of vm2. Ther... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 10,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/patriksimek/vm2/blob/master/lib/setup-sandbox.js#L71"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vm2_project:vm2:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3CB151FD-32BF-4CED-93D3-F07D6F62E4DC",
"versionEndExcluding": "3.9.11",
"versionEndIncluding": null,
"versionStart... | [
"913"
] | 913 | https://github.com/patriksimek/vm2/issues/467 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"patriksimek",
"vm2"
] | Hello 👋
The [Oxeye](https://www.oxeye.io/) research team has found a sandbox breakout vulnerability in VM2. We would like to share the in-depth analysis with you so the vulnerability can be fixed. We tried to contact `security@integromat.com` but didn't get any response.
Could you please share with me an email ad... | Sandbox Breakout in VM2 | https://api.github.com/repos/patriksimek/vm2/issues/467/comments | 18 | 2022-08-28T09:52:15Z | 2022-09-15T02:53:51Z | https://github.com/patriksimek/vm2/issues/467 | 1,353,303,106 | 467 | 4,103 |
CVE-2022-38528 | 2022-09-06T23:15:08.880 | Open Asset Import Library (assimp) commit 3c253ca was discovered to contain a segmentation violation via the component Assimp::XFileImporter::CreateMeshes. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Technical Description",
"Third Party Advisory"
],
"url": "https://github.com/assimp/assimp/issues/4662"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:assimp:assimp:5.2.5:*:*:*:*:*:*:*",
"matchCriteriaId": "19513059-3423-47C9-B7A3-38B8ACA2A7B2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"125"
] | 125 | https://github.com/assimp/assimp/issues/4662 | [
"Exploit",
"Issue Tracking",
"Technical Description",
"Third Party Advisory"
] | github.com | [
"assimp",
"assimp"
] | # Describe the bug
SEGV on unknown address still exists in Assimp::XFileImporter::CreateMeshes.
***This is similar to issue https://github.com/assimp/assimp/issues/1728. Note that #1728 reported wrong type of the vulnerability, as it is not a NULL pointer dereference. Patch https://github.com/assimp/assimp/commit/... | Bug: SEGV on unknown address still exists in Assimp::XFileImporter::CreateMeshes | https://api.github.com/repos/assimp/assimp/issues/4662/comments | 2 | 2022-07-26T13:16:46Z | 2025-05-23T16:56:35Z | https://github.com/assimp/assimp/issues/4662 | 1,318,230,977 | 4,662 | 4,104 |
CVE-2022-38529 | 2022-09-06T23:15:08.920 | tinyexr commit 0647fb3 was discovered to contain a heap-buffer overflow via the component rleUncompress. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/syoyo/tinyexr/issues/169"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyexr_project:tinyexr:2022-06-28:*:*:*:*:*:*:*",
"matchCriteriaId": "DB72586A-37D9-4C6D-8CED-D429A2BD5C1C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"787"
] | 787 | https://github.com/syoyo/tinyexr/issues/169 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"syoyo",
"tinyexr"
] | # Describe the issue
Heap-buffer-overflow still exists in the `rleUncompress`.
***This is similar to issue https://github.com/syoyo/tinyexr/issues/112, but it seems that the patch https://github.com/syoyo/tinyexr/commit/58a625894cfbb76da1d599e4f9768f099058e0e4 has not fully fixed them.***
# To Reproduce
*E... | Heap-buffer-overflow still exists in the rleUncompress | https://api.github.com/repos/syoyo/tinyexr/issues/169/comments | 3 | 2022-07-06T03:10:33Z | 2022-07-14T07:32:10Z | https://github.com/syoyo/tinyexr/issues/169 | 1,295,059,789 | 169 | 4,105 |
CVE-2022-38530 | 2022-09-06T23:15:09.010 | GPAC v2.1-DEV-rev232-gfcaa01ebb-master was discovered to contain a stack overflow when processing ISOM_IOD. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2216"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2216 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | **version info:**
```
root:# MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev232-gfcaa01ebb-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.114... | AddressSanitizer: stack-overflow when processing ISOM_IOD | https://api.github.com/repos/gpac/gpac/issues/2216/comments | 0 | 2022-07-02T17:45:58Z | 2022-07-12T17:13:10Z | https://github.com/gpac/gpac/issues/2216 | 1,292,105,535 | 2,216 | 4,106 |
CVE-2022-40023 | 2022-09-07T13:15:09.953 | Sqlalchemy mako before 1.2.2 is vulnerable to Regular expression Denial of Service when using the Lexer class to parse. This also affects babelplugin and linguaplugin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sqlalchemy/mako/blob/c2f392e0be52dc67d1b9770ab8cce6a9c736d547/mako/ext/extract.py#L21"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sqlalchemy:mako:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A85380F0-0A58-4E13-B3E3-3DC01E7ABF3F",
"versionEndExcluding": "1.2.2",
"versionEndIncluding": null,
"versionStartExcludi... | [
"1333"
] | 1333 | https://github.com/sqlalchemy/mako/issues/366 | [
"Issue Tracking",
"Patch"
] | github.com | [
"sqlalchemy",
"mako"
] | this will crash the Lexer due to the regex:
```py
from mako.lexer import Lexer
template = "<%0" + '"' * 3000
Lexer(template).parse
``` | quoted sections in tag not grouped correctly | https://api.github.com/repos/sqlalchemy/mako/issues/366/comments | 1 | 2022-08-29T15:48:22Z | 2022-08-29T18:06:27Z | https://github.com/sqlalchemy/mako/issues/366 | 1,354,517,220 | 366 | 4,107 |
CVE-2022-36079 | 2022-09-07T21:15:08.560 | Parse Server is an open source backend that can be deployed to any infrastructure that can run Node.js. Internal fields (keys used internally by Parse Server, prefixed by `_`) and protected fields (user defined) can be used as query constraints. Internal and protected fields are removed by Parse Server and are only ret... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.6,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/parse-community/parse-server/commit/634c44acd18f6ee6ec60fac89a2b602d92799bec"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parseplatform:parse-server:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "55B47674-02C1-4BE5-B962-AF328A4F99B5",
"versionEndExcluding": "4.10.14",
"versionEndIncluding": null,
"... | [
"200"
] | 200 | https://github.com/parse-community/parse-server/issues/8143 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"parse-community",
"parse-server"
] | Fixes https://github.com/parse-community/parse-server/security/advisories/GHSA-2m6g-crv8-p3c6 | fix: brute force guessing of user sensitive data via search patterns (GHSA-2m6g-crv8-p3c6) | https://api.github.com/repos/parse-community/parse-server/issues/8143/comments | 4 | 2022-09-02T17:52:12Z | 2022-09-03T09:25:15Z | https://github.com/parse-community/parse-server/pull/8143 | 1,360,469,071 | 8,143 | 4,108 |
CVE-2022-36079 | 2022-09-07T21:15:08.560 | Parse Server is an open source backend that can be deployed to any infrastructure that can run Node.js. Internal fields (keys used internally by Parse Server, prefixed by `_`) and protected fields (user defined) can be used as query constraints. Internal and protected fields are removed by Parse Server and are only ret... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.6,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/parse-community/parse-server/commit/634c44acd18f6ee6ec60fac89a2b602d92799bec"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parseplatform:parse-server:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "55B47674-02C1-4BE5-B962-AF328A4F99B5",
"versionEndExcluding": "4.10.14",
"versionEndIncluding": null,
"... | [
"200"
] | 200 | https://github.com/parse-community/parse-server/issues/8144 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"parse-community",
"parse-server"
] | Fixes https://github.com/parse-community/parse-server/security/advisories/GHSA-2m6g-crv8-p3c6 | fix: brute force guessing of user sensitive data via search patterns (GHSA-2m6g-crv8-p3c6) | https://api.github.com/repos/parse-community/parse-server/issues/8144/comments | 3 | 2022-09-02T17:52:58Z | 2022-09-03T09:24:10Z | https://github.com/parse-community/parse-server/pull/8144 | 1,360,469,671 | 8,144 | 4,109 |
CVE-2022-25897 | 2022-09-08T05:15:07.410 | The package org.eclipse.milo:sdk-server before 0.6.8 are vulnerable to Denial of Service (DoS) when bypassing the limitations for excessive memory consumption by sending multiple CloseSession requests with the deleteSubscription parameter equal to False. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/eclipse/milo/commit/4534381760d7d9f0bf00cbf6a8449bb0d13c6ce5"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:milo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "21638D30-0B3C-4457-BEBC-022ACACE81A5",
"versionEndExcluding": "0.6.8",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"770"
] | 770 | https://github.com/eclipse/milo/issues/1030 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"eclipse",
"milo"
] | The server should allow the maximum number of MonitoredItems that can be created to be configurable via the `OpcUaServerConfigLimits` interface. To best maintain backwards compatibility with the previous server the default value will be `Integer.MAX_VALUE`, which is effectively unlimited. | Allow max MonitoredItems to be configured | https://api.github.com/repos/eclipse-milo/milo/issues/1030/comments | 0 | 2022-08-23T17:26:44Z | 2022-08-24T11:12:05Z | https://github.com/eclipse-milo/milo/issues/1030 | 1,348,292,957 | 1,030 | 4,110 |
CVE-2022-40280 | 2022-09-08T22:15:08.800 | An issue was discovered in Samsung TizenRT through 3.0_GBM (and 3.1_PRE). createDB in security/provisioning/src/provisioningdatabasemanager.c has a missing sqlite3_close after sqlite3_open_v2, leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Samsung/TizenRT/blob/f8f776dd183246ad8890422c1ee5e8f33ab2aaaf/external/iotivity/iotivity_1.2-rel/resource/csdk/security/provisioning/src/provisioningdatabasemanager.c#L100"
},
{
"source": "cve@m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:samsung:tizenrt:1.0:m1:*:*:*:*:*:*",
"matchCriteriaId": "6B59E31E-7082-4719-97B6-3ADA43058E65",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"772"
] | 772 | https://github.com/Samsung/TizenRT/issues/5627 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Samsung",
"TizenRT"
] | # Affected components
affected source code file: external/iotivity/iotivity_1.2-rel/resource/csdk/security/provisioning/src/provisioningdatabasemanager.c
# Attack vector(s)
Missing sqlite3_close after sqlite3_open_v2.
Whether or not an error occurs when it is opened, resources associated with the [database co... | Security: DoS vulnerability in function createDB() | https://api.github.com/repos/Samsung/TizenRT/issues/5627/comments | 0 | 2022-09-02T04:54:05Z | 2022-09-02T05:14:28Z | https://github.com/Samsung/TizenRT/issues/5627 | 1,359,701,920 | 5,627 | 4,114 |
CVE-2022-40281 | 2022-09-08T22:15:08.843 | An issue was discovered in Samsung TizenRT through 3.0_GBM (and 3.1_PRE). cyassl_connect_step2 in curl/vtls/cyassl.c has a missing X509_free after SSL_get_peer_certificate, leading to information disclosure. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Samsung/TizenRT/blob/f8f776dd183246ad8890422c1ee5e8f33ab2aaaf/external/curl/vtls/cyassl.c#L545"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:samsung:tizenrt:1.0:m1:*:*:*:*:*:*",
"matchCriteriaId": "6B59E31E-7082-4719-97B6-3ADA43058E65",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"401"
] | 401 | https://github.com/Samsung/TizenRT/issues/5626 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Samsung",
"TizenRT"
] | # Affected components
affected source code file: external/curl/vtls/cyassl.c
# Attack vector(s)
Missing X509_free() after SSL_get_peer_certificate().
The X509 object must be explicitly freed using X509_free().
# Suggested description of the vulnerability for use in the CVE
Privacy leakage vulnerability ... | Security: Privacy leakage in function cyassl_connect_step2() | https://api.github.com/repos/Samsung/TizenRT/issues/5626/comments | 0 | 2022-09-02T04:44:13Z | 2022-09-02T05:15:36Z | https://github.com/Samsung/TizenRT/issues/5626 | 1,359,697,306 | 5,626 | 4,115 |
CVE-2022-40299 | 2022-09-09T01:15:07.853 | In Singular before 4.3.1, a predictable /tmp pathname is used (e.g., by sdb.cc), which allows local users to gain the privileges of other users via a procedure in a file under /tmp. NOTE: this CVE Record is about sdb.cc and similar files in the Singular interface that have predictable /tmp pathnames; this CVE Record is... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://michael.orlitzky.com/cves/cve-2022-40299.xhtml"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Singular/Sing... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:singular:singular:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3FE9F514-BE4C-43B5-AAF5-30D4AE629E20",
"versionEndExcluding": "4.3.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"330"
] | 330 | https://github.com/Singular/Singular/issues/1137 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Singular",
"Singular"
] | I just noticed commit https://github.com/Singular/Singular/commit/ed2fd9bb8a4241c386b59a55bd8bbfb1d66ac174 which led me to `git grep /tmp` in the codebase. There are several places where a fixed (or at least predictable) path under `/tmp` is used for temporary storage. This creates a [general class of vulnerability](ht... | Insecure /tmp usage due to predictable paths | https://api.github.com/repos/Singular/Singular/issues/1137/comments | 5 | 2022-05-18T14:08:48Z | 2024-08-20T12:16:19Z | https://github.com/Singular/Singular/issues/1137 | 1,240,027,736 | 1,137 | 4,116 |
CVE-2020-10735 | 2022-09-09T14:15:08.660 | A flaw was found in python. In algorithms with quadratic time complexity using non-binary bases, when using int("text"), a system could take 50ms to parse an int string with 100,000 digits and 5s for 1,000,000 digits (float, decimal, int.from_bytes(), and int() for binary bases 2, 4, 8, 16, and 32 are not affected). Th... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/09/21/1"
},
{
"source": "secalert@redhat.com",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0743C1B3-D44D-4940-AAF4-25DEFB46AC74",
"versionEndExcluding": "3.7.14",
"versionEndIncluding": null,
"versionStartExcludin... | [
"704"
] | 704 | https://github.com/python/cpython/issues/95778 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"python",
"cpython"
] | ## Problem
A Denial Of Service (DoS) issue was identified in CPython because we use binary bignum’s for our `int` implementation. A huge integer will always consume a near-quadratic amount of CPU time in conversion to or from a base 10 (decimal) string with a large number of digits. No efficient algorithm exists to ... | CVE-2020-10735: Prevent DoS by large int<->str conversions | https://api.github.com/repos/python/cpython/issues/95778/comments | 24 | 2022-08-08T07:53:39Z | 2023-02-07T04:35:46Z | https://github.com/python/cpython/issues/95778 | 1,331,477,062 | 95,778 | 4,117 |
CVE-2022-38272 | 2022-09-09T14:15:08.777 | JFinal CMS 5.1.0 is vulnerable to SQL Injection via /admin/article/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/51"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jflyfox/jfinal_cms/issues/51 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | Administrator login is required. The default account password is admin:admin123
## admin/article/list
There is a SQLI vul in background mode.The route is as following

vulnerable argument passing is as following
![ima... | Some SQL injection vulnerabilities exists in JFinal CMS 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/51/comments | 0 | 2022-08-09T09:43:40Z | 2022-08-09T09:46:05Z | https://github.com/jflyfox/jfinal_cms/issues/51 | 1,332,993,619 | 51 | 4,118 |
CVE-2022-38282 | 2022-09-09T14:15:09.267 | JFinal CMS 5.1.0 is vulnerable to SQL Injection via /admin/videoalbum/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/52"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jflyfox/jfinal_cms/issues/52 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | Administrator login is required. The default account password is admin:admin123
## admin/videoalbum/list
There is a SQLI vul in background mode.The route is as following
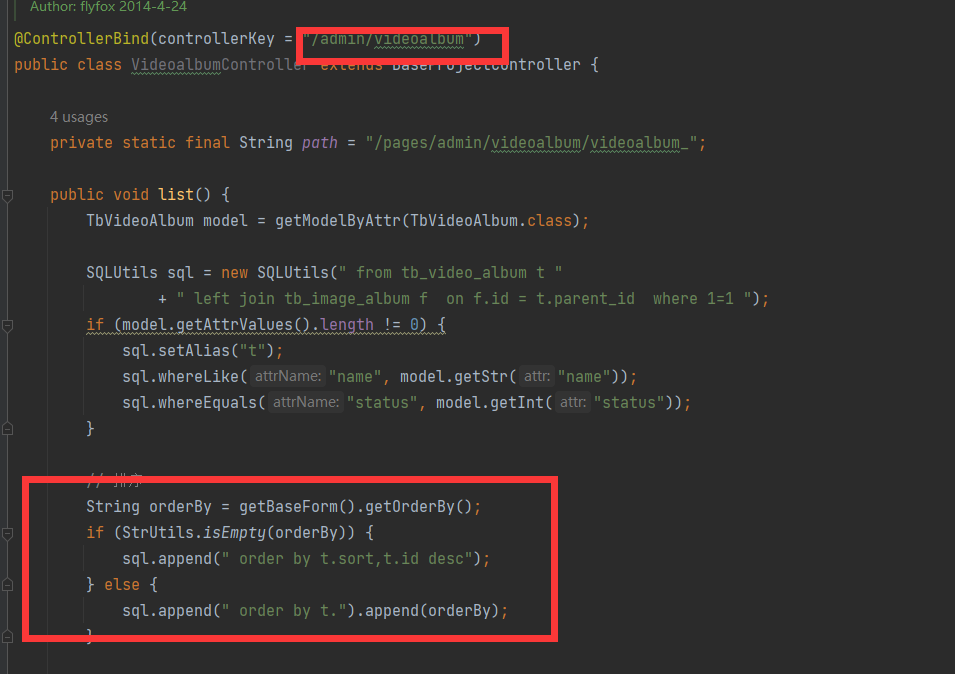
vulnerable argument passing is as following
![ima... | Some SQL injection vulnerabilities exists in JFinal CMS 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/52/comments | 0 | 2022-08-09T10:01:49Z | 2022-08-09T10:01:49Z | https://github.com/jflyfox/jfinal_cms/issues/52 | 1,333,015,169 | 52 | 4,119 |
CVE-2022-38639 | 2022-09-09T19:15:08.313 | A cross-site scripting (XSS) vulnerability in Markdown-Nice v1.8.22 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Community Posting field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mdnice/markdown-nice/issues/327"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:inkdrop:markdown_nice:1.8.22:*:*:*:*:*:*:*",
"matchCriteriaId": "88A634C2-783D-495C-AE35-B9675EF1E397",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/mdnice/markdown-nice/issues/327 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mdnice",
"markdown-nice"
] | The markdown preview executes the xss vector, and the stored xss occurs in the community posting, which can be fixed by the [DOMPurify](https://github.com/cure53/DOMPurify) project.
`<img src=1 onerror=alert(1)>`
 allows attackers to cause an arithmetic exception leading to a Denial of Service (DoS) via a crafted JPEG file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/DanBloomberg/leptonica/commit/f062b42c0ea8dddebdc6a152fd16152de215d614"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tesseract_project:tesseract:5.0.0:alpha-20210401:*:*:*:*:*:*",
"matchCriteriaId": "D83B1B84-78AE-4CFD-B425-509B29AF243B",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"369"
] | 369 | https://github.com/tesseract-ocr/tesseract/issues/3498 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tesseract-ocr",
"tesseract"
] | ### **System Configuration**
- tesseract version: 5.0.0-alpha-20210401
- linked library version:
leptonica-1.79.0
libgif 5.1.4 : libjpeg 8d (libjpeg-turbo 2.0.3) : libpng 1.6.37 : libtiff 4.1.0 : zlib 1.2.11 : libwebp 0.6.1 : libopenjp2 2.3.1
Found AVX512BW
Found AVX512F
Found AVX2
Found AVX
Found FMA
Found... | While processing, division by zero causes an arithmetic exception | https://api.github.com/repos/tesseract-ocr/tesseract/issues/3498/comments | 13 | 2021-07-15T09:34:01Z | 2022-11-21T16:44:14Z | https://github.com/tesseract-ocr/tesseract/issues/3498 | 945,189,724 | 3,498 | 4,123 |
CVE-2022-37767 | 2022-09-12T14:15:09.110 | Pebble Templates 3.1.5 allows attackers to bypass a protection mechanism and implement arbitrary code execution with springbok. NOTE: the vendor disputes this because input to the Pebble templating engine is intended to include arbitrary Java code, and thus either the input should not arrive from an untrusted source, o... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PebbleTemplates/pebble/issues/625#issuecomment-1282138635"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pebbletemplates:pebble_templates:3.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "9A45A63E-6BB7-4C65-9557-4516199DE5C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"863"
] | 863 | https://github.com/PebbleTemplates/pebble/issues/625#issuecomment-1282138635 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PebbleTemplates",
"pebble"
] | Hello,
since this morning security checks in our projects are reporting new critical vulnerability in the current pebble version 3.1.5:
NVD: https://nvd.nist.gov/vuln/detail/CVE-2022-37767
Original report: https://github.com/Y4tacker/Web-Security/issues/3
Any short-term workaround to mitigate the vulnerabilit... | Vulnerability CVE-2022-37767 | https://api.github.com/repos/PebbleTemplates/pebble/issues/625/comments | 38 | 2022-09-15T07:30:44Z | 2023-03-23T16:02:53Z | https://github.com/PebbleTemplates/pebble/issues/625 | 1,374,064,812 | 625 | 4,124 |
CVE-2022-37767 | 2022-09-12T14:15:09.110 | Pebble Templates 3.1.5 allows attackers to bypass a protection mechanism and implement arbitrary code execution with springbok. NOTE: the vendor disputes this because input to the Pebble templating engine is intended to include arbitrary Java code, and thus either the input should not arrive from an untrusted source, o... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PebbleTemplates/pebble/issues/625#issuecomment-1282138635"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pebbletemplates:pebble_templates:3.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "9A45A63E-6BB7-4C65-9557-4516199DE5C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"863"
] | 863 | https://github.com/Y4tacker/Web-Security/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Y4tacker",
"Web-Security"
] | # Pebble 3.1.5 Bypass
Pebble Templates 3.1.5 allows attackers to bypass a protection mechanism and implement arbitrary code execution with springboot.
First, simply set up an environment with the official documentation:https://pebbletemplates.io/
Pom.xml
```xml
<?xml version="1.0" encoding="UTF-8"?>
<proj... | command execution vulnerability in pebble 3.1.5(latest) | https://api.github.com/repos/Y4tacker/Web-Security/issues/3/comments | 0 | 2022-08-03T12:51:58Z | 2022-09-20T01:19:30Z | https://github.com/Y4tacker/Web-Security/issues/3 | 1,327,173,676 | 3 | 4,125 |
CVE-2022-38291 | 2022-09-12T21:15:11.143 | SLiMS Senayan Library Management System v9.4.2 was discovered to contain a cross-site scripting (XSS) vulnerability via the Search function. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Search bar. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/slims/slims9_bulian/issues/156"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:slims:senayan_library_management_system:9.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "EDC3FA43-9AED-4115-B41B-61587D7D784F",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/slims/slims9_bulian/issues/156 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"slims",
"slims9_bulian"
] | **Describe the bug**
XSS in search bar
**To Reproduce**
Steps to reproduce the behavior:
1. Go to the website and make sure it has more than 10 bibliography/books
2. put this payload (`<IMG SRC="jav&x09;ascript:alert('XSS');"><script>alert("xss by 0xdc9");</script>`) in the search bar and enter
3. an alert tha... | XSS in search bar | https://api.github.com/repos/slims/slims9_bulian/issues/156/comments | 0 | 2022-08-09T18:44:51Z | 2022-09-24T03:27:21Z | https://github.com/slims/slims9_bulian/issues/156 | 1,333,651,959 | 156 | 4,126 |
CVE-2022-38292 | 2022-09-12T21:15:11.193 | SLiMS Senayan Library Management System v9.4.2 was discovered to contain multiple Server-Side Request Forgeries via the components /bibliography/marcsru.php and /bibliography/z3950sru.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/slims/slims9_bulian/issues/158"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:slims:senayan_library_management_system:9.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "EDC3FA43-9AED-4115-B41B-61587D7D784F",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"918"
] | 918 | https://github.com/slims/slims9_bulian/issues/158 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"slims",
"slims9_bulian"
] | **The bug**
A Server Side Request Forgery exists in `admin/modules/bibliography/marcsru.php` and `admin/modules/bibliography/z3950sru.php` due to the class in `lib/marc/XMLParser.inc.php`
**Reproduce**
Steps to reproduce the behavior:
1. Go to `http://127.0.0.1:8008/slims9_bulian-9.4.2/admin/index.php?mod=bibli... | [Security Bugs] Server Side Request Forgery | https://api.github.com/repos/slims/slims9_bulian/issues/158/comments | 0 | 2022-08-11T21:31:20Z | 2022-11-24T07:56:26Z | https://github.com/slims/slims9_bulian/issues/158 | 1,336,516,748 | 158 | 4,127 |
CVE-2022-38295 | 2022-09-12T21:15:11.243 | Cuppa CMS v1.0 was discovered to contain a cross-site scripting vulnerability at /table_manager/view/cu_user_groups. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Name field under the Add New Group function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/34"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/CuppaCMS/CuppaCMS/issues/34 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | Cross-Site Scripting exists in Cuppa CMS in Users tap.
Discoverer : **Team Am0namiss**(Members : [hoseongJ](https://github.com/hoseongJ), [studdcat](https://github.com/studdcat), [AnonyMousStu](https://github.com/AnonyMousStu), [GuJiseung](https://github.com/GuJiseung), [4dministrat0r](https://github.com/4dministrat0r... | XSS Vulnerability exists in Cuppa CMS in Users | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/34/comments | 0 | 2022-08-09T12:30:41Z | 2022-09-13T11:02:46Z | https://github.com/CuppaCMS/CuppaCMS/issues/34 | 1,333,188,097 | 34 | 4,128 |
CVE-2022-38296 | 2022-09-12T21:15:11.297 | Cuppa CMS v1.0 was discovered to contain an arbitrary file upload vulnerability via the File Manager. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/33"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/CuppaCMS/CuppaCMS/issues/33 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | File upload vulnerability exists in Cuppa CMS in File Manager tap.
Discoverer : **Team Am0namiss**(Members : [hoseongJ](https://github.com/hoseongJ), [studdcat](https://github.com/studdcat), [AnonyMousStu](https://github.com/AnonyMousStu), [GuJiseung](https://github.com/GuJiseung), [4dministrat0r](https://github.com/4... | File Upload Vulnerability exists in Cuppa CMS in File Manager | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/33/comments | 0 | 2022-08-09T12:17:02Z | 2022-09-13T11:02:31Z | https://github.com/CuppaCMS/CuppaCMS/issues/33 | 1,333,171,744 | 33 | 4,129 |
CVE-2022-38537 | 2022-09-13T15:15:08.973 | Archery v1.4.5 to v1.8.5 was discovered to contain multiple SQL injection vulnerabilities via the start_file, end_file, start_time, and stop_time parameters in the binlog2sql interface. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://announcements.bybit.com/en-US/article/bybit-improves-the-security-of-the-open-source-community-blt626818c0ee8c48a6/"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:archerydms:archery:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F38198C3-79F6-4978-8227-0D784F625903",
"versionEndExcluding": "1.9.0",
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/hhyo/Archery/issues/1842 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hhyo",
"Archery"
] | ### 重现步骤
https://github.com/hhyo/Archery/blob/v1.8.5/sql/plugins/my2sql.py#L36
Plugin my2sql has a problem with the filtering method of start_time and stop_time parameters, which leads to injection system command execution, resulting in a remote command execution vulnerability.
https://github.com/hhyo/Archery/blob... | Multiple Remote Code Executioin | https://api.github.com/repos/hhyo/Archery/issues/1842/comments | 0 | 2022-09-19T02:30:23Z | 2022-09-19T13:45:32Z | https://github.com/hhyo/Archery/issues/1842 | 1,377,303,744 | 1,842 | 4,130 |
CVE-2022-38538 | 2022-09-13T15:15:09.023 | Archery v1.7.0 to v1.8.5 was discovered to contain a SQL injection vulnerability via the checksum parameter in the report module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://announcements.bybit.com/en-US/article/bybit-improves-the-security-of-the-open-source-community-blt626818c0ee8c48a6/"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:archerydms:archery:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AF3B860B-7F06-4778-9FCD-7A153778CE30",
"versionEndExcluding": "1.9.0",
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/hhyo/Archery/issues/1841 | [
"Third Party Advisory"
] | github.com | [
"hhyo",
"Archery"
] | ### 重现步骤
https://github.com/hhyo/Archery/blob/v1.8.5/sql/slowlog.py#L167
The checksum parameter of the report interface is not escaped, and it is pass into the SQL statement for execution, results in SQL injection. Any logged-in user can execute SQL injection and steal other user's django session_key from database an... | Multiple SQL injection | https://api.github.com/repos/hhyo/Archery/issues/1841/comments | 1 | 2022-09-19T02:27:58Z | 2022-09-19T13:47:02Z | https://github.com/hhyo/Archery/issues/1841 | 1,377,302,318 | 1,841 | 4,131 |
CVE-2022-38306 | 2022-09-13T21:15:09.427 | LIEF commit 5d1d643 was discovered to contain a heap-buffer overflow in the component /core/CorePrPsInfo.tcc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/763"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2B9842CE-CF1E-43E6-B3DF-9701F5DFE1DF",
"versionEndExcluding": "0.12.1",
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/lief-project/LIEF/issues/763 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | ###### version
```
latest master [5d1d643](https://github.com/lief-project/LIEF/commit/5d1d643a0c46437b57d35654690e03d26d189070)
```
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.13.0-52-generic x86_64)
###### Build step
```
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=... | heap-buffer-overflow in elf_reader | https://api.github.com/repos/lief-project/LIEF/issues/763/comments | 1 | 2022-08-09T08:23:03Z | 2022-08-10T06:05:42Z | https://github.com/lief-project/LIEF/issues/763 | 1,332,896,530 | 763 | 4,132 |
CVE-2022-38307 | 2022-09-13T21:15:09.480 | LIEF commit 5d1d643 was discovered to contain a segmentation violation via the function LIEF::MachO::SegmentCommand::file_offset() at /MachO/SegmentCommand.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/764"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2B9842CE-CF1E-43E6-B3DF-9701F5DFE1DF",
"versionEndExcluding": "0.12.1",
"versionEndIncluding": null,
"versionStartExcl... | [
"476"
] | 476 | https://github.com/lief-project/LIEF/issues/764 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | ###### version
```
latest master 5d1d643
```
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.13.0-52-generic x86_64)
###### Build step
```
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address"
```
###### Run
```
./b... | SEGV in SegmentCommand.cpp:149 | https://api.github.com/repos/lief-project/LIEF/issues/764/comments | 0 | 2022-08-09T09:54:15Z | 2022-08-10T05:27:03Z | https://github.com/lief-project/LIEF/issues/764 | 1,333,006,398 | 764 | 4,133 |
CVE-2022-38329 | 2022-09-13T21:15:09.537 | An issue was discovered in Shopxian CMS 3.0.0. There is a CSRF vulnerability that can delete the specified column via index.php/contents-admin_cat-finderdel-model-ContentsCat.html?id=17. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://albert5888.github.io/posts/CVE-2022-38329/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zhangqiquan/shopxian_cms/issues/4"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shopxian:shopxian_cms:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C3E351B5-8095-4F9D-B555-EBD4349D1985",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"352"
] | 352 | https://github.com/zhangqiquan/shopxian_cms/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zhangqiquan",
"shopxian_cms"
] | Vulnerability details:
When the administrator logs in, click the button will delete the specified column.
Vulnerability POC:
```<input type ="button" onclick="javascript:location.href='http://127.0.0.1/index.php/contents-admin_cat-finderdel-model-ContentsCat.html?id=17'" value="Click Me!!!"></input>```
CSRF HTM... | CSRF vulnerable | https://api.github.com/repos/zhangqiquan/shopxian_cms/issues/4/comments | 0 | 2022-08-11T18:49:55Z | 2022-08-11T18:49:55Z | https://github.com/zhangqiquan/shopxian_cms/issues/4 | 1,336,357,318 | 4 | 4,134 |
CVE-2022-38495 | 2022-09-13T21:15:09.590 | LIEF commit 365a16a was discovered to contain a heap-buffer overflow via the function print_binary at /c/macho_reader.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/767"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B2A9F55D-96B8-4830-A6DB-5D04F75406E4",
"versionEndExcluding": null,
"versionEndIncluding": "0.12.1",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/lief-project/LIEF/issues/767 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | ###### Version
```
latest master 365a16a
```
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.13.0-52-generic x86_64)
###### Build step
```
cmake -DLIEF_ASAN=ON ../
```
###### Run
```
./build/examples/c/macho_reader poc
```
[poc.zip](https://github.com/lief-project/LIEF/files/9299163/poc.zip)
... | heap-buffer-overflow in macho_reader.c | https://api.github.com/repos/lief-project/LIEF/issues/767/comments | 1 | 2022-08-10T10:26:03Z | 2022-08-13T05:01:09Z | https://github.com/lief-project/LIEF/issues/767 | 1,334,409,301 | 767 | 4,135 |
CVE-2022-38496 | 2022-09-13T21:15:09.647 | LIEF commit 365a16a was discovered to contain a reachable assertion abort via the component BinaryStream.hpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/765"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B2A9F55D-96B8-4830-A6DB-5D04F75406E4",
"versionEndExcluding": null,
"versionEndIncluding": "0.12.1",
"versionStartExcl... | [
"617"
] | 617 | https://github.com/lief-project/LIEF/issues/765 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | ###### version
```
latest master 365a16a
```
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.13.0-52-generic x86_64)
###### Build step
```
cmake -DLIEF_ASAN=ON ../
```
###### Run
```
./build/examples/c/macho_reader poc
```
[poc.zip](https://github.com/lief-project/LIEF/files/9299006/poc.zip)
##... | Abort in BinaryStream.hpp | https://api.github.com/repos/lief-project/LIEF/issues/765/comments | 0 | 2022-08-10T10:05:20Z | 2022-08-13T05:00:36Z | https://github.com/lief-project/LIEF/issues/765 | 1,334,384,359 | 765 | 4,136 |
CVE-2022-38497 | 2022-09-13T21:15:09.703 | LIEF commit 365a16a was discovered to contain a segmentation violation via the component CoreFile.tcc:69. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/766"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B2A9F55D-96B8-4830-A6DB-5D04F75406E4",
"versionEndExcluding": null,
"versionEndIncluding": "0.12.1",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/lief-project/LIEF/issues/766 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | ###### version
```
latest master 365a16a
```
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.13.0-52-generic x86_64)
###### Build step
```
cmake -DLIEF_ASAN=ON ../
```
###### Run
```
./build/examples/c/elf_reader poc
```
[poc.zip](https://github.com/lief-project/LIEF/files/9299058/poc.zip)
##... | SEGV in CoreFile.tcc:69 | https://api.github.com/repos/lief-project/LIEF/issues/766/comments | 0 | 2022-08-10T10:09:19Z | 2022-08-13T05:00:37Z | https://github.com/lief-project/LIEF/issues/766 | 1,334,389,058 | 766 | 4,137 |
CVE-2022-37191 | 2022-09-13T23:15:08.667 | The component "cuppa/api/index.php" of CuppaCMS v1.0 is Vulnerable to LFI. An authenticated user can read system files via crafted POST request using [function] parameter value as LFI payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/20"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"829"
] | 829 | https://github.com/CuppaCMS/CuppaCMS/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | There is a serious Local File Inclusion vulnerability exists in **"cuppa/api/index.php"** via **POST** requests "**function**" parameter.
**PoC:**

Reference: https://github.com/badru8612/Cuppa... | Authenticated Local File Inclusion vulnerability in cuppa api. | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/20/comments | 0 | 2022-01-24T07:59:02Z | 2022-01-25T23:08:06Z | https://github.com/CuppaCMS/CuppaCMS/issues/20 | 1,112,291,001 | 20 | 4,138 |
CVE-2022-40365 | 2022-09-14T21:15:10.583 | Cross site scripting (XSS) vulnerability in ouqiang gocron through 1.5.3, allows attackers to execute arbitrary code via scope.row.hostname in web/vue/src/pages/taskLog/list.vue. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/ouqiang/gocron"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gocron_project:gocron:*:*:*:*:*:*:*:*",
"matchCriteriaId": "556143D0-A8C7-4901-80C8-1F0FDA88554C",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.3",
"versionStartE... | [
"79"
] | 79 | https://github.com/ouqiang/gocron/issues/362 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ouqiang",
"gocron"
] | ### Introduction
> `gocron/web/vue/src/pages/taskLog/list.vue` line 91 host will be parsed by the browser as html, which leads to xss vulnerability
### Proof

<img width="1776" alt="image" src="https://use... | There is an xss vulnerability in the front end | https://api.github.com/repos/ouqiang/gocron/issues/362/comments | 0 | 2022-08-06T11:30:51Z | 2022-08-06T11:30:51Z | https://github.com/ouqiang/gocron/issues/362 | 1,330,728,479 | 362 | 4,139 |
CVE-2022-40438 | 2022-09-14T21:15:10.627 | Buffer overflow vulnerability in function AP4_MemoryByteStream::WritePartial in mp42aac in Bento4 v1.6.0-639, allows attackers to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/751"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/axiomatic-systems/Bento4/issues/751 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42aac instrumented with ASAN. There are some inputs causing heap-buffer-overflow. Here is the ASAN mode output:
=================================================================
==4695==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6190000027a0 at ... | Heap-buffer-overflow with ASAN in mp42aac | https://api.github.com/repos/axiomatic-systems/Bento4/issues/751/comments | 0 | 2022-09-07T02:21:29Z | 2022-09-18T23:10:27Z | https://github.com/axiomatic-systems/Bento4/issues/751 | 1,364,000,633 | 751 | 4,140 |
CVE-2022-40439 | 2022-09-14T21:15:10.670 | An memory leak issue was discovered in AP4_StdcFileByteStream::Create in mp42ts in Bento4 v1.6.0-639, allows attackers to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/750"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/axiomatic-systems/Bento4/issues/750 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, developers of Bento4:
In the test of the binary mp42ts instrumented with ASAN. There are some inputs causing memory leaks. Here is the ASAN mode output:
=================================================================
==18321==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 48 byte(s) in 1 objec... | Memory leaks with ASAN in mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/750/comments | 0 | 2022-09-06T14:00:13Z | 2023-05-29T02:53:17Z | https://github.com/axiomatic-systems/Bento4/issues/750 | 1,363,336,565 | 750 | 4,141 |
CVE-2022-40734 | 2022-09-14T23:15:09.583 | UniSharp laravel-filemanager (aka Laravel Filemanager) before 2.6.4 allows download?working_dir=%2F.. directory traversal to read arbitrary files, as exploited in the wild in June 2022. This is related to league/flysystem before 2.0.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/UniSharp/laravel-filemanager/issues/1150"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/UniSharp/laravel-filemanager/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:unisharp:laravel_filemanager:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F55D5755-7EE5-4205-A976-12D1DBAB33B0",
"versionEndExcluding": null,
"versionEndIncluding": "2.5.1",
"versio... | [
"22"
] | 22 | https://github.com/UniSharp/laravel-filemanager/issues/1150 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"UniSharp",
"laravel-filemanager"
] | I do not use this package, but I seen this in our firewall blocked list. My guess is that there is some sort of vulnerability.

| Directory traversal vulnerability (CVE-2022-40734) | https://api.github.com/repos/UniSharp/laravel-filemanager/issues/1150/comments | 19 | 2022-06-22T04:18:30Z | 2024-03-28T15:31:00Z | https://github.com/UniSharp/laravel-filemanager/issues/1150 | 1,279,489,454 | 1,150 | 4,142 |
CVE-2022-40734 | 2022-09-14T23:15:09.583 | UniSharp laravel-filemanager (aka Laravel Filemanager) before 2.6.4 allows download?working_dir=%2F.. directory traversal to read arbitrary files, as exploited in the wild in June 2022. This is related to league/flysystem before 2.0.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/UniSharp/laravel-filemanager/issues/1150"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/UniSharp/laravel-filemanager/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:unisharp:laravel_filemanager:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F55D5755-7EE5-4205-A976-12D1DBAB33B0",
"versionEndExcluding": null,
"versionEndIncluding": "2.5.1",
"versio... | [
"22"
] | 22 | https://github.com/UniSharp/laravel-filemanager/issues/1150#issuecomment-1320186966 | null | github.com | [
"UniSharp",
"laravel-filemanager"
] | I do not use this package, but I seen this in our firewall blocked list. My guess is that there is some sort of vulnerability.

| Directory traversal vulnerability (CVE-2022-40734) | https://api.github.com/repos/UniSharp/laravel-filemanager/issues/1150/comments | 19 | 2022-06-22T04:18:30Z | 2024-03-28T15:31:00Z | https://github.com/UniSharp/laravel-filemanager/issues/1150 | 1,279,489,454 | 1,150 | 4,143 |
CVE-2022-40734 | 2022-09-14T23:15:09.583 | UniSharp laravel-filemanager (aka Laravel Filemanager) before 2.6.4 allows download?working_dir=%2F.. directory traversal to read arbitrary files, as exploited in the wild in June 2022. This is related to league/flysystem before 2.0.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/UniSharp/laravel-filemanager/issues/1150"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/UniSharp/laravel-filemanager/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:unisharp:laravel_filemanager:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F55D5755-7EE5-4205-A976-12D1DBAB33B0",
"versionEndExcluding": null,
"versionEndIncluding": "2.5.1",
"versio... | [
"22"
] | 22 | https://github.com/UniSharp/laravel-filemanager/issues/1150#issuecomment-1825310417 | null | github.com | [
"UniSharp",
"laravel-filemanager"
] | I do not use this package, but I seen this in our firewall blocked list. My guess is that there is some sort of vulnerability.

| Directory traversal vulnerability (CVE-2022-40734) | https://api.github.com/repos/UniSharp/laravel-filemanager/issues/1150/comments | 19 | 2022-06-22T04:18:30Z | 2024-03-28T15:31:00Z | https://github.com/UniSharp/laravel-filemanager/issues/1150 | 1,279,489,454 | 1,150 | 4,144 |
CVE-2018-25047 | 2022-09-15T00:15:09.580 | In Smarty before 3.1.47 and 4.x before 4.2.1, libs/plugins/function.mailto.php allows XSS. A web page that uses smarty_function_mailto, and that could be parameterized using GET or POST input parameters, could allow injection of JavaScript code by a user. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.gentoo.org/870100"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:smarty:smarty:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2C07B998-ABE8-4F99-8A25-EEEBBC27599E",
"versionEndExcluding": "3.1.47",
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/smarty-php/smarty/issues/454 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"smarty-php",
"smarty"
] | I found a bug in the **Smarty package**, specifically in the **smarty_function_mailto($params)** function.
Remote exploitation of such vulnerability is unlikely, but it is still advisable to take it into account.
A web page that uses this function and that could be parameterized using GET or POST input parameters... | smarty_function_mailto - JavaScript injection in eval function | https://api.github.com/repos/smarty-php/smarty/issues/454/comments | 3 | 2018-06-18T16:31:00Z | 2022-12-27T11:00:26Z | https://github.com/smarty-php/smarty/issues/454 | 333,345,886 | 454 | 4,145 |
CVE-2022-38352 | 2022-09-15T02:15:09.223 | ThinkPHP v6.0.13 was discovered to contain a deserialization vulnerability via the component League\Flysystem\Cached\Storage\Psr6Cache. This vulnerability allows attackers to execute arbitrary code via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/top-think/framework/issues/2749"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkphp:thinkphp:6.0.13:*:*:*:*:*:*:*",
"matchCriteriaId": "DDD39D80-F4FD-4FDA-B294-E26CF148F865",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"502"
] | 502 | https://github.com/top-think/framework/issues/2749 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"top-think",
"framework"
] | Any method of any class, where eval is called to execute php code, thereby executing php and writing to a file.
```php
<?php
namespace League\Flysystem\Cached\Storage{
class Psr6Cache{
private $pool;
protected $autosave = false;
public function __construct($exp)
{
... | There is a new exploit chain for the deserialization vulnerability of thinkphp 6.0.13 | https://api.github.com/repos/top-think/framework/issues/2749/comments | 0 | 2022-08-14T15:26:02Z | 2024-03-01T08:25:01Z | https://github.com/top-think/framework/issues/2749 | 1,338,277,889 | 2,749 | 4,146 |
CVE-2022-40737 | 2022-09-15T04:15:24.610 | An issue was discovered in Bento4 through 1.6.0-639. A buffer over-read exists in the function AP4_StdcFileByteStream::WritePartial located in System/StdC/Ap4StdCFileByteStream.cpp, called from AP4_ByteStream::Write and AP4_HdlrAtom::WriteFields. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/756"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/756 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hello, I use fuzzer to test bianry mp4split, and found some vulnerabilities,the following is the details.
# Bug1
```
root@c511e4bf49bc:/mp4split/mp4split# ./mp4split FishFuzz/crashes/id:000000,sig:06,src:000011,op:flip1,pos:31240,1216870
=================================================================
==258946... | there are some vulnerabilities in binary mp4split | https://api.github.com/repos/axiomatic-systems/Bento4/issues/756/comments | 2 | 2022-09-14T11:20:27Z | 2023-06-26T06:40:26Z | https://github.com/axiomatic-systems/Bento4/issues/756 | 1,372,814,057 | 756 | 4,147 |
CVE-2022-31735 | 2022-09-15T05:15:08.883 | OpenAM Consortium Edition version 14.0.0 provided by OpenAM Consortium contains an open redirect vulnerability (CWE-601). When accessing an affected server through some specially crafted URL, the user may be redirected to an arbitrary website. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "vultures@jpcert.or.jp",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/openam-jp/openam/issues/259"
},
{
"source": "vultures@jpcert.or.jp",
"tags": [
"Third Party Advisory"
],
"url": "https://jvn.jp/e... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:osstech:openam:*:*:*:*:consortium:*:*:*",
"matchCriteriaId": "1E5893F0-D7DF-46D8-A751-E965D6ADAC4A",
"versionEndExcluding": null,
"versionEndIncluding": "13.0.0-183",
"versio... | [
"601"
] | 601 | https://github.com/openam-jp/openam/issues/259 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"openam-jp",
"openam"
] | ## Description
OpenAM (OpenAM Consortium Edition) has an open redirect vulnerability in logout URL.
After performing some steps, accessing the logout URL with a malformed parameter can redirect the user to an arbitrary URL. | Open Redirect Vulnerability | https://api.github.com/repos/openam-jp/openam/issues/259/comments | 0 | 2022-09-13T01:23:52Z | 2022-09-15T02:04:45Z | https://github.com/openam-jp/openam/issues/259 | 1,370,718,149 | 259 | 4,148 |
CVE-2022-37257 | 2022-09-15T13:15:09.653 | Prototype pollution vulnerability in function convertLater in npm-convert.js in stealjs steal 2.2.4 via the requestedVersion variable in npm-convert.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://steal.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://stealjs.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1321"
] | 1321 | https://github.com/stealjs/steal/issues/1526 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | Prototype pollution vulnerability in function convertLater in npm-convert.js in stealjs steal 2.2.4 via the requestedVersion variable in npm-convert.js.
The prototype pollution vulnerability can be mitigated with several best practices described here:
https://learn.snyk.io/lessons/prototype-pollution/javascript/ | [CVE-2022-37257]/prototype-pollution found in npm-convert.js | https://api.github.com/repos/stealjs/steal/issues/1526/comments | 0 | 2022-09-14T09:08:10Z | 2022-09-14T09:08:10Z | https://github.com/stealjs/steal/issues/1526 | 1,372,628,760 | 1,526 | 4,149 |
CVE-2022-37266 | 2022-09-15T13:15:09.697 | Prototype pollution vulnerability in function extend in babel.js in stealjs steal 2.2.4 via the key variable in babel.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/ext/babel.js#L29165"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1321"
] | 1321 | https://github.com/stealjs/steal/issues/1535 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | Prototype pollution vulnerability in function extend in babel.js in stealjs steal 2.2.4 via the key variable in babel.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [CVE-2022-37266] Prototype pollution found in babel.js | https://api.github.com/repos/stealjs/steal/issues/1535/comments | 0 | 2022-09-14T09:49:39Z | 2022-09-14T09:49:39Z | https://github.com/stealjs/steal/issues/1535 | 1,372,688,015 | 1,535 | 4,150 |
CVE-2022-37262 | 2022-09-15T16:15:10.323 | A Regular Expression Denial of Service (ReDoS) flaw was found in stealjs steal 2.2.4 via the source and sourceWithComments variable in main.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/main.js#L3497"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1333"
] | 1333 | https://github.com/stealjs/steal/issues/1531 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | A Regular Expression Denial of Service (ReDoS) flaw was found in stealjs steal 2.2.4 via the source and sourceWithComments variable in main.js.
The ReDoS vulnerability can be mitigated with several best practices described here: https://snyk.io/blog/redos-and-catastrophic-backtracking/
| [CVE-2022-37262]/ReDos found in main.js | https://api.github.com/repos/stealjs/steal/issues/1531/comments | 0 | 2022-09-14T09:33:46Z | 2022-09-14T09:33:46Z | https://github.com/stealjs/steal/issues/1531 | 1,372,664,571 | 1,531 | 4,151 |
CVE-2022-37264 | 2022-09-15T16:15:10.387 | Prototype pollution vulnerability in stealjs steal 2.2.4 via the optionName variable in main.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/main.js#L2194"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1321"
] | 1321 | https://github.com/stealjs/steal/issues/1533 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | Prototype pollution vulnerability in stealjs steal 2.2.4 via the optionName variable in main.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [CVE-2022-37264]/ Prototype pollution found in main.js | https://api.github.com/repos/stealjs/steal/issues/1533/comments | 0 | 2022-09-14T09:40:44Z | 2022-09-14T09:40:44Z | https://github.com/stealjs/steal/issues/1533 | 1,372,674,742 | 1,533 | 4,152 |
CVE-2022-38890 | 2022-09-15T16:15:10.687 | Nginx NJS v0.7.7 was discovered to contain a segmentation violation via njs_utf8_next at src/njs_utf8.h | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/569"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.7:*:*:*:*:*:*:*",
"matchCriteriaId": "B99556AB-3BAC-4553-8CDC-17292CF06AA8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"125"
] | 125 | https://github.com/nginx/njs/issues/569 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | the call stack is different with https://github.com/nginx/njs/issues/522
```
Environment
commit: 569292e0a74f2b1ec09566f3329f82bdd0d58e87
version: 0.7.7
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Poc
```js
function placeholder(){}
function main() {
var v2 = String... | Another way to trigger SEGV in njs_utf8_next cause oob read | https://api.github.com/repos/nginx/njs/issues/569/comments | 2 | 2022-08-25T02:58:03Z | 2022-09-02T00:51:09Z | https://github.com/nginx/njs/issues/569 | 1,350,249,226 | 569 | 4,153 |
CVE-2022-37260 | 2022-09-15T19:15:09.847 | A Regular Expression Denial of Service (ReDoS) flaw was found in stealjs steal 2.2.4 via the input variable in main.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/main.js#L2490"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealj... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1333"
] | 1333 | https://github.com/stealjs/steal/issues/1529 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | A Regular Expression Denial of Service (ReDoS) flaw was found in stealjs steal 2.2.4 via the input variable in main.js.
The ReDoS vulnerability can be mitigated with several best practices described here:
https://snyk.io/blog/redos-and-catastrophic-backtracking/
| [CVE-2022-37260]/ReDos found in main.js | https://api.github.com/repos/stealjs/steal/issues/1529/comments | 0 | 2022-09-14T09:25:55Z | 2022-09-14T09:25:55Z | https://github.com/stealjs/steal/issues/1529 | 1,372,653,654 | 1,529 | 4,154 |
CVE-2022-29240 | 2022-09-15T22:15:11.220 | Scylla is a real-time big data database that is API-compatible with Apache Cassandra and Amazon DynamoDB. When decompressing CQL frame received from user, Scylla assumes that user-provided uncompressed length is correct. If user provides fake length, that is greater than the real one, part of decompression buffer won't... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/scylladb/scylla/security/advisories/GHSA-25pq-rrqm-6fmr"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scylladb:scylla:*:*:*:*:open_source:*:*:*",
"matchCriteriaId": "62049391-A8C3-4963-B692-B9D0EBD24754",
"versionEndExcluding": "4.6.7",
"versionEndIncluding": null,
"versionSt... | [
"908"
] | 908 | https://github.com/scylladb/scylladb/issues/11476 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"scylladb",
"scylladb"
] | We return the wrong size, which can lead to crashes or other undefined behavior.
This is [CVE-2022-29240](https://github.com/scylladb/scylladb/security/advisories/GHSA-25pq-rrqm-6fmr). | Undefined behavior in transport decompression code | https://api.github.com/repos/scylladb/scylladb/issues/11476/comments | 1 | 2022-09-07T07:57:30Z | 2022-11-16T19:23:33Z | https://github.com/scylladb/scylladb/issues/11476 | 1,364,252,689 | 11,476 | 4,155 |
CVE-2022-39215 | 2022-09-15T22:15:11.527 | Tauri is a framework for building binaries for all major desktop platforms. Due to missing canonicalization when `readDir` is called recursively, it was possible to display directory listings outside of the defined `fs` scope. This required a crafted symbolic link or junction folder inside an allowed path of the `fs` s... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 8.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tauri-apps/tauri/issues/4882"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tauri:tauri:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BE5A2510-1D82-4D06-BFDC-08FA3942EDC8",
"versionEndExcluding": "1.0.6",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"59"
] | 59 | https://github.com/tauri-apps/tauri/issues/4882 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tauri-apps",
"tauri"
] | ### Describe the bug
When a junction is created in the $APP Base directory on windows
eg. `mklink /J C:\Users\<user>\AppData\Roaming\<identifier>\TestFolder C:\Dev\TestFolder`)
The folder is accessible together with all files and folders inside using fs if read from the root directory
`const entries = await readD... | [bug] Accessing junction folder from within $APP folder on Windows | https://api.github.com/repos/tauri-apps/tauri/issues/4882/comments | 0 | 2022-08-07T18:06:13Z | 2022-09-08T13:59:07Z | https://github.com/tauri-apps/tauri/issues/4882 | 1,331,083,809 | 4,882 | 4,156 |
CVE-2022-40149 | 2022-09-16T10:15:09.677 | Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve-coordination@google.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=46538"
},
{
"source": "cve-coordination@google.com",
"tags": [
"Issue Tracking",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jettison_project:jettison:*:*:*:*:*:*:*:*",
"matchCriteriaId": "56D361BD-D04F-425F-A8EB-4D389BD32429",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.0",
"versionSt... | [
"787"
] | 787 | https://github.com/jettison-json/jettison/issues/45 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jettison-json",
"jettison"
] | Dear Jettison maintainers,
Multiple bugs were found during fuzzing by [Jazzer](https://github.com/CodeIntelligenceTesting/jazzer) in Jettison, for example [[Out of memory](https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=46549) and [Stackoverflow](https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=46538)]. W... | New OSS-Fuzz Findings in Jettison | https://api.github.com/repos/jettison-json/jettison/issues/45/comments | 10 | 2022-08-03T14:40:56Z | 2023-01-01T12:41:39Z | https://github.com/jettison-json/jettison/issues/45 | 1,327,327,641 | 45 | 4,157 |
CVE-2022-40151 | 2022-09-16T10:15:09.817 | Those using Xstream to seralize XML data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve-coordination@google.com",
"tags": [
"Exploit",
"Permissions Required",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=47367"
},
{
"source": "cve-coordination@google.com",
"tags": [
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xstream_project:xstream:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A6DDFDA0-5B71-4DEF-98C5-216EE4042401",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.19",
"versionSta... | [
"787"
] | 787 | https://github.com/x-stream/xstream/issues/304 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"x-stream",
"xstream"
] | Dear xstream maintainers,
Multiple bugs(Stackoverflows) were found during fuzzing by [Jazzer](https://github.com/CodeIntelligenceTesting/jazzer) in xstream. We would like to provide you with access to the bugs at Google OSS-Fuzz before they get publicly disclosed.
What do we need from you?
We need an emai... | New OSS-Fuzz Findings in xstream | https://api.github.com/repos/x-stream/xstream/issues/304/comments | 45 | 2022-08-04T12:20:17Z | 2022-12-23T22:37:34Z | https://github.com/x-stream/xstream/issues/304 | 1,328,536,856 | 304 | 4,158 |
CVE-2022-37258 | 2022-09-16T22:15:12.097 | Prototype pollution vulnerability in function convertLater in npm-convert.js in stealjs steal 2.2.4 via the packageName variable in npm-convert.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/ext/npm-convert.js#L362"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:*:*:*",
"matchCriteriaId": "F01F1B6C-0486-4C61-A8F0-5ABAC7B0E168",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"1321"
] | 1321 | https://github.com/stealjs/steal/issues/1527 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | Prototype pollution vulnerability in function convertLater in npm-convert.js in stealjs steal 2.2.4 via the packageName variable in npm-convert.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [CVE-2022-37258]/Prototype pollution found in npm-convert.js | https://api.github.com/repos/stealjs/steal/issues/1527/comments | 0 | 2022-09-14T09:17:00Z | 2022-09-14T09:17:00Z | https://github.com/stealjs/steal/issues/1527 | 1,372,641,337 | 1,527 | 4,159 |
CVE-2022-40755 | 2022-09-16T22:15:12.303 | JasPer 3.0.6 allows denial of service via a reachable assertion in the function inttobits in libjasper/base/jas_image.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jasper-software/jasper/issues/338"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jasper_project:jasper:3.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "CD0938AD-12F3-4B02-899A-A54286B9FFEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"617"
] | 617 | https://github.com/jasper-software/jasper/issues/338 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jasper-software",
"jasper"
] | ## summary
Hello, I was testing my fuzzer and found a reachable assertion in imginfo. An assertion in function inttobits can be reached when parsing a crafted jp2 file, when running `./imginfo -f $POC`, as shown in the attachment
## Environment
* Ubuntu 22.04 (docker)
* gcc/g++ 11.2.0
* jasper latest commit 0c2a... | [BUG] Reachable assertion in inttobits, jas_image.c | https://api.github.com/repos/jasper-software/jasper/issues/338/comments | 10 | 2022-09-13T07:26:35Z | 2022-11-04T16:13:07Z | https://github.com/jasper-software/jasper/issues/338 | 1,370,986,252 | 338 | 4,160 |
CVE-2022-40757 | 2022-09-16T22:15:12.347 | A Buffer Access with Incorrect Length Value vulnerablity in the TEE_MACComputeFinal function in Samsung mTower through 0.3.0 allows a trusted application to trigger a Denial of Service (DoS) by invoking the function TEE_MACComputeFinal with an excessive size value of messageLen. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/mTower/blob/efd36709306a9afcca5b4782499d01be0c7a02a5/tee/lib/libutee/tee_api_operations.c#L1031"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samsung:mtower:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C72C53B-9CF2-4F9A-90C1-3A1FE236BA5B",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.0",
"versionStartExcludin... | [
"119"
] | 119 | https://github.com/Samsung/mTower/issues/81 | [
"Third Party Advisory"
] | github.com | [
"Samsung",
"mTower"
] | Buffer Access with Incorrect Length Value in the function TEE_MACUpdate
**Affected components:**
affected source code file: /tee/lib/libutee/tee_api_objects.c, affected functions: TEE_MACUpdate
**Attack vector(s)**
To exploit the vulnerability, invoke the function TEE_MACUpdate and pass an excessive size v... | Security: Buffer Access with Incorrect Length Value in TEE_MACUpdate, TEE_MACComputeFinal and TEE_CipherUpdate | https://api.github.com/repos/Samsung/mTower/issues/81/comments | 0 | 2022-09-16T14:10:07Z | 2022-11-28T10:30:30Z | https://github.com/Samsung/mTower/issues/81 | 1,376,007,292 | 81 | 4,161 |
CVE-2022-40759 | 2022-09-16T22:15:12.430 | A NULL pointer dereference issue in the TEE_MACCompareFinal function in Samsung mTower through 0.3.0 allows a trusted application to trigger a Denial of Service (DoS) by invoking the function TEE_MACCompareFinal with a NULL pointer for the parameter operation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/mTower/blob/efd36709306a9afcca5b4782499d01be0c7a02a5/tee/lib/libutee/tee_api_operations.c#L1249"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samsung:mtower:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C72C53B-9CF2-4F9A-90C1-3A1FE236BA5B",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.0",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/Samsung/mTower/issues/80 | [
"Third Party Advisory"
] | github.com | [
"Samsung",
"mTower"
] | **Affected components:**
affected source code file: /tee/lib/libutee/tee_api_objects.c, affected functions: TEE_MACCompareFinal
**Attack vector(s)**
To exploit the vulnerability, invoke the function TEE_MACCompareFinal and pass a NULL pointer to the parameter "operation".
**Suggested description of the vul... | Security: NULL Pointer Dereference in the function TEE_MACCompareFinal | https://api.github.com/repos/Samsung/mTower/issues/80/comments | 0 | 2022-09-16T14:06:28Z | 2022-11-21T11:13:40Z | https://github.com/Samsung/mTower/issues/80 | 1,376,002,655 | 80 | 4,162 |
CVE-2022-40761 | 2022-09-16T22:15:12.517 | The function tee_obj_free in Samsung mTower through 0.3.0 allows a trusted application to trigger a Denial of Service (DoS) by invoking the function TEE_AllocateOperation with a disturbed heap layout, related to utee_cryp_obj_alloc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/mTower/blob/efd36709306a9afcca5b4782499d01be0c7a02a5/tee/tee/tee_obj.c#L109"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samsung:mtower:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C72C53B-9CF2-4F9A-90C1-3A1FE236BA5B",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.0",
"versionStartExcludin... | [
"1284"
] | 1284 | https://github.com/Samsung/mTower/issues/83 | [
"Third Party Advisory"
] | github.com | [
"Samsung",
"mTower"
] | **Affected components:**
affected source code file: /tee/tee/tee_svc_cryp.c, affected functions: utee_cryp_obj_alloc
affected source code file: /tee/tee/tee_obj.c, affected functions: tee_obj_alloc and tee_obj_free
**Attack vector(s)**
One way to exploit the vulnerability, invoking the function `TEE_AllocateO... | Security: Improper Input Validation in the function utee_cryp_obj_alloc | https://api.github.com/repos/Samsung/mTower/issues/83/comments | 0 | 2022-09-16T14:14:28Z | 2022-11-24T19:39:39Z | https://github.com/Samsung/mTower/issues/83 | 1,376,012,858 | 83 | 4,163 |
CVE-2022-40762 | 2022-09-16T22:15:12.557 | A Memory Allocation with Excessive Size Value vulnerablity in the TEE_Realloc function in Samsung mTower through 0.3.0 allows a trusted application to trigger a Denial of Service (DoS) by invoking the function TEE_Realloc with an excessive number for the parameter len. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Samsung/mTower/blob/efd36709306a9afcca5b4782499d01be0c7a02a5/tee/lib/libutee/tee_api.c#L319"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samsung:mtower:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C72C53B-9CF2-4F9A-90C1-3A1FE236BA5B",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.0",
"versionStartExcludin... | [
"770"
] | 770 | https://github.com/Samsung/mTower/issues/82 | [
"Third Party Advisory"
] | github.com | [
"Samsung",
"mTower"
] | **Affected components:**
affected source code file: /tee/lib/libutee/tee_api.c, affected functions: TEE_Realloc
**Attack vector(s)**
To exploit the vulnerability, invoke the function TEE_Realloc and pass a large number to the parameter "len".
**Suggested description of the vulnerability for use in the CVE**... | Security: Memory Allocation with Excessive Size Value in the function TEE_Realloc | https://api.github.com/repos/Samsung/mTower/issues/82/comments | 0 | 2022-09-16T14:12:09Z | 2022-10-25T13:47:21Z | https://github.com/Samsung/mTower/issues/82 | 1,376,009,885 | 82 | 4,164 |
CVE-2022-36027 | 2022-09-16T23:15:11.430 | TensorFlow is an open source platform for machine learning. When converting transposed convolutions using per-channel weight quantization the converter segfaults and crashes the Python process. We have patched the issue in GitHub commit aa0b852a4588cea4d36b74feb05d93055540b450. The fix will be included in TensorFlow 2.... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/commit/aa0b852a4588cea4d36b74feb05d93055540b450"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C6622D95-1C86-45C5-AB55-E6EEEA0996DF",
"versionEndExcluding": "2.7.2",
"versionEndIncluding": null,
"versionStartExclu... | [
"20"
] | 20 | https://github.com/tensorflow/tensorflow/issues/53767 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | When converting transposed convolutions using per-channel weight quantization the converter segfaults and crashes the Python process. Per-channel quantization is supported by TFLite Transposed convolutions:
https://github.com/tensorflow/tensorflow/blob/f87be6c7de847017c48520649e3d771e5d6b81b6/tensorflow/lite/kernels/t... | TFLite Converter segfaults when trying to convert per-channel quantized transposed convolutions | https://api.github.com/repos/tensorflow/tensorflow/issues/53767/comments | 9 | 2022-01-14T18:55:01Z | 2024-11-01T02:08:27Z | https://github.com/tensorflow/tensorflow/issues/53767 | 1,104,010,260 | 53,767 | 4,165 |
CVE-2022-25873 | 2022-09-18T15:15:09.660 | The package vuetify from 2.0.0-beta.4 and before 2.6.10 are vulnerable to Cross-site Scripting (XSS) due to improper input sanitization in the 'eventName' function within the VCalendar component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://codepen.io/5v3n-08/pen/MWGKEjY"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vuetifyjs/vuetify/commit/a... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vuetifyjs:vuetify:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5717CAE6-B23D-4EE0-88A8-5A98FF6D68E2",
"versionEndExcluding": "2.6.10",
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/vuetifyjs/vuetify/issues/15757 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vuetifyjs",
"vuetify"
] | ### Environment
**Vuetify Version:** 2.6.9
**Vue Version:** 2.6.14
**Browsers:** Chrome 105.0.0.0
**OS:** Mac OS 10.15.7
### Steps to reproduce
Open the link and see the alert with xss.
### Expected Behavior
Not use plain html
### Actual Behavior
html is used and open an alert
### Reproduction Link
... | [Bug Report][2.6.9] xss in v-calendar | https://api.github.com/repos/vuetifyjs/vuetify/issues/15757/comments | 0 | 2022-09-08T11:29:39Z | 2022-09-08T14:43:19Z | https://github.com/vuetifyjs/vuetify/issues/15757 | 1,366,110,081 | 15,757 | 4,166 |
CVE-2022-40769 | 2022-09-18T17:15:09.667 | profanity through 1.60 has only four billion possible RNG initializations. Thus, attackers can recover private keys from Ethereum vanity addresses and steal cryptocurrency, as exploited in the wild in June 2022. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://blog.1inch.io/a-vulnerability-disclosed-in-profanity-an-ethereum-vanity-address-tool-68ed7455fc8c"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:profanity_project:profanity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "16E1CC96-F6AE-40E6-8DEE-1FAD971A615B",
"versionEndExcluding": null,
"versionEndIncluding": "1.60",
"versionS... | [
"338"
] | 338 | https://github.com/johguse/profanity/issues/61 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"johguse",
"profanity"
] | Hi, could you elaborate on how private keys are being generated and brute forced? It seems like a reliable random number generator `std::mt19937_64` is being fully initialized by `unsigned int` (https://en.cppreference.com/w/cpp/numeric/random/random_device), which could make it less reliable:
https://github.com/johgu... | Private key safety | https://api.github.com/repos/johguse/profanity/issues/61/comments | 4 | 2022-01-17T08:50:54Z | 2022-09-15T07:42:49Z | https://github.com/johguse/profanity/issues/61 | 1,105,545,328 | 61 | 4,167 |
CVE-2022-40774 | 2022-09-18T19:15:09.277 | An issue was discovered in Bento4 through 1.6.0-639. There is a NULL pointer dereference in AP4_StszAtom::GetSampleSize. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/757"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/757 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi There,
I tested the binary mp42ts with my fuzzer, and a crash incurred, i.e., SEGV on an unknown address error. Here are the details:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==6287==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x... | SEGV at AP4_StszAtom::GetSampleSize(unsigned int, unsigned int&) in binary mp42ts | https://api.github.com/repos/axiomatic-systems/Bento4/issues/757/comments | 2 | 2022-09-17T03:04:47Z | 2023-06-26T09:40:27Z | https://github.com/axiomatic-systems/Bento4/issues/757 | 1,376,646,543 | 757 | 4,168 |
CVE-2022-40775 | 2022-09-18T19:15:09.323 | An issue was discovered in Bento4 through 1.6.0-639. A NULL pointer dereference occurs in AP4_StszAtom::WriteFields. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/758"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "180AEBD6-AF89-4F0F-856E-D8B977C762C0",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-639",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/758 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi there, I use my fuzzer for fuzzing the binary mp4decrypt, and this binary crashes with the following:
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==24087==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x000000702ee8 bp 0x7ffcf40a75f0 s... | SEGV error | https://api.github.com/repos/axiomatic-systems/Bento4/issues/758/comments | 0 | 2022-09-17T06:02:37Z | 2023-06-26T09:41:06Z | https://github.com/axiomatic-systems/Bento4/issues/758 | 1,376,678,566 | 758 | 4,169 |
CVE-2022-38881 | 2022-09-19T16:15:11.540 | The d8s-archives for python, as distributed on PyPI, included a potential code-execution backdoor inserted by a third party. The backdoor is the democritus-strings package. The affected version is 0.1.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/democritus-project/d8s-archives/issues/12"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://pypi.org/project/d8s-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:d8s-archives_project:d8s-archives:0.1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "83A7837F-25C6-41FC-ADB1-B4FDD9C884F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/democritus-project/d8s-archives/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"democritus-project",
"d8s-archives"
] | We discovered a potential code execution backdoor in version 0.1.0 of the project, the backdoor is the democritus-strings package. Attackers can upload democritus-strings packages containing arbitrary malicious code. For the safety of this project, the democritus-strings package has been uploaded by us.
 function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tinyproxy/tinyproxy"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/tinyproxy/tinyproxy/blob/84f203fb1c4733608c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyproxy_project:tinyproxy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3E51FD82-DAE3-49BD-A817-91A131CE6525",
"versionEndExcluding": null,
"versionEndIncluding": "1.11.1",
"versio... | [
"1188"
] | 1188 | https://github.com/tinyproxy/tinyproxy/issues/457 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tinyproxy",
"tinyproxy"
] | > ubuntu 22.04
> GNU C Library (Ubuntu GLIBC 2.35-0ubuntu3.1) stable release version 2.35.
1. Clone & Compile
```
git clone https://github.com/tinyproxy/tinyproxy
cd tinyproxy
./autogen.sh
./configure
make
```
2. Create a config file
```
vi ./1.conf
Port 8888
Listen 0.0.0.0
Bind 0.0.0.0
Timeou... | Potential runtime system sensitive information disclosure through special HTTP requests. | https://api.github.com/repos/tinyproxy/tinyproxy/issues/457/comments | 5 | 2022-09-08T13:25:39Z | 2024-05-05T18:20:33Z | https://github.com/tinyproxy/tinyproxy/issues/457 | 1,366,329,471 | 457 | 4,179 |
CVE-2022-40468 | 2022-09-19T17:15:14.700 | Potential leak of left-over heap data if custom error page templates containing special non-standard variables are used. Tinyproxy commit 84f203f and earlier use uninitialized buffers in process_request() function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tinyproxy/tinyproxy"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/tinyproxy/tinyproxy/blob/84f203fb1c4733608c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyproxy_project:tinyproxy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3E51FD82-DAE3-49BD-A817-91A131CE6525",
"versionEndExcluding": null,
"versionEndIncluding": "1.11.1",
"versio... | [
"1188"
] | 1188 | https://github.com/tinyproxy/tinyproxy/issues/457#issuecomment-1264176815 | null | github.com | [
"tinyproxy",
"tinyproxy"
] | > ubuntu 22.04
> GNU C Library (Ubuntu GLIBC 2.35-0ubuntu3.1) stable release version 2.35.
1. Clone & Compile
```
git clone https://github.com/tinyproxy/tinyproxy
cd tinyproxy
./autogen.sh
./configure
make
```
2. Create a config file
```
vi ./1.conf
Port 8888
Listen 0.0.0.0
Bind 0.0.0.0
Timeou... | Potential runtime system sensitive information disclosure through special HTTP requests. | https://api.github.com/repos/tinyproxy/tinyproxy/issues/457/comments | 5 | 2022-09-08T13:25:39Z | 2024-05-05T18:20:33Z | https://github.com/tinyproxy/tinyproxy/issues/457 | 1,366,329,471 | 457 | 4,180 |
CVE-2022-38545 | 2022-09-19T23:15:09.203 | Valine v1.4.18 was discovered to contain a remote code execution (RCE) vulnerability which allows attackers to execute arbitrary code via a crafted POST request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xCss/Valine/issues/400"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:valine.js:valine:1.4.18:*:*:*:*:*:*:*",
"matchCriteriaId": "71726106-9C57-4CCA-9A8C-34B1ACB32642",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/xCss/Valine/issues/400 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xCss",
"Valine"
] | 如果您想报告错误,请提供以下信息 If you want to report a bug, please provide the following information:
- [x] 可复现问题的步骤 The steps to reproduce.
- [x] 可复现问题的网页地址 A minimal demo of the problem via https://jsfiddle.net or http://codepen.io/pen if possible.
- [x] 受影响的Valine版本、操作系统,以及浏览器信息 Which versions of Valine, and which browser / ... | A XSS bug that can execute code(用户恶意修改 评论 的ua可触发XSS执行代码) | https://api.github.com/repos/xCss/Valine/issues/400/comments | 3 | 2022-06-21T06:13:26Z | 2022-10-11T08:44:36Z | https://github.com/xCss/Valine/issues/400 | 1,277,942,586 | 400 | 4,181 |
CVE-2022-38550 | 2022-09-19T23:15:09.247 | A stored cross-site scripting (XSS) vulnerability in the /weibo/list component of Jeesns v2.0.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Pick-program/JEESNS/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6771ECEB-00AE-4D70-BCEA-E6040665827E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/Pick-program/JEESNS/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Pick-program",
"JEESNS"
] | Tools required: BurpSuite, IDEA (Eclipse)
Required source download address:
https://github.com/zchuanzhao/jeesns/releases
Deployment Instructions:
https://gitee.com/zchuanzhao/jeesns#%E9%83%A8%E7%BD%B2%E8%AF%B4%E6%98%8E
 flaw was found in stealjs steal 2.2.4 via the string variable in babel.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/ext/babel.js#L54124"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1333"
] | 1333 | https://github.com/stealjs/steal/issues/1528 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | A Regular Expression Denial of Service (ReDoS) flaw was found in stealjs steal 2.2.4 via the string variable in babel.js.
The ReDoS vulnerability can be mitigated with several best practices described here: https://snyk.io/blog/redos-and-catastrophic-backtracking/
| [CVE-2022-37259]/ReDos found in babel.js | https://api.github.com/repos/stealjs/steal/issues/1528/comments | 0 | 2022-09-14T09:21:22Z | 2022-09-14T09:21:22Z | https://github.com/stealjs/steal/issues/1528 | 1,372,647,305 | 1,528 | 4,184 |
CVE-2022-37265 | 2022-09-20T18:15:10.270 | Prototype pollution vulnerability in stealjs steal 2.2.4 via the alias variable in babel.js. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/stealjs/steal/blob/c9dd1eb19ed3f97aeb93cf9dcea5d68ad5d0ced9/ext/babel.js#L4216"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stealjs:steal:2.2.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3819AF82-351A-415D-B7D8-60208158D5E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"1321"
] | 1321 | https://github.com/stealjs/steal/issues/1534 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stealjs",
"steal"
] | Prototype pollution vulnerability in stealjs steal 2.2.4 via the alias variable in babel.js.
The prototype pollution vulnerability can be mitigated with several best practices described here: https://learn.snyk.io/lessons/prototype-pollution/javascript/
| [CVE-2022-37265]/ Prototype pollution found in babel.js | https://api.github.com/repos/stealjs/steal/issues/1534/comments | 0 | 2022-09-14T09:47:08Z | 2022-09-14T09:47:08Z | https://github.com/stealjs/steal/issues/1534 | 1,372,684,258 | 1,534 | 4,185 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.