cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-38238 | 2022-08-16T21:15:14.123 | XPDF commit ffaf11c was discovered to contain a heap-buffer overflow via DCTStream::lookChar() at /xpdf/Stream.cc. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jhcloos/xpdf/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xpdf_project:xpdf:3.04:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD71528-E16D-42E8-A422-05AAD924A832",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/jhcloos/xpdf/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jhcloos",
"xpdf"
] | Hi, in the lastest version of this code [ ps: commit id [ffaf11c](https://github.com/jhcloos/xpdf/commit/ffaf11c4f9ee0c4a124ec454f96c0f99ee699f10)] I found something unusual.
### crash sample
[8id148_heap_buffer_overflow_in_lookChar.zip](https://github.com/jhcloos/xpdf/files/9278233/8id148_heap_buffer_overflow_in_l... | heap_buffer_overflow_in_lookChar | https://api.github.com/repos/jhcloos/xpdf/issues/15/comments | 1 | 2022-08-08T02:40:13Z | 2022-08-13T04:34:46Z | https://github.com/jhcloos/xpdf/issues/15 | 1,331,243,403 | 15 | 3,983 |
CVE-2022-25799 | 2022-08-16T22:15:08.147 | An open redirect vulnerability exists in CERT/CC VINCE software prior to 1.50.0. An attacker could send a link that has a specially crafted URL and convince the user to click the link. When an authenticated user clicks the link, the authenticated user's browser could be redirected to a malicious site that is designed t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cret@cert.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://cheatsheetseries.owasp.org/cheatsheets/Unvalidated_Redirects_and_Forwards_Cheat_Sheet.html"
},
{
"source": "cret@cert.org",
"tags": [
"Issue Tracking",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cert:vince:*:*:*:*:*:*:*:*",
"matchCriteriaId": "996A047E-B6BD-4CA2-AFFE-25FD35000D66",
"versionEndExcluding": "1.50.0",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"601"
] | 601 | https://github.com/CERTCC/VINCE/issues/45 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CERTCC",
"VINCE"
] | @JLLeitschuh (with help from CodeQL) reported this open redirect, which was fixed in 1.50.0:
https://www.kb.cert.org/vince/comm/login/?next=https%3A%2F%2Fexample.com
https://github.com/CERTCC/VINCE/blob/b986a8637b57c5cd8b2c5722f29f9893aef3f04c/cogauth/views.py#L768
https://github.com/CERTCC/VINCE/commit/b986a8... | assign CVE ID for open redirect fixed in 1.50.0 | https://api.github.com/repos/CERTCC/VINCE/issues/45/comments | 4 | 2022-08-15T19:42:17Z | 2022-08-17T14:42:42Z | https://github.com/CERTCC/VINCE/issues/45 | 1,339,408,309 | 45 | 3,984 |
CVE-2022-36186 | 2022-08-17T15:15:08.480 | A Null Pointer dereference vulnerability exists in GPAC 2.1-DEV-revUNKNOWN-master via the function gf_filter_pid_set_property_full () at filter_core/filter_pid.c:5250,which causes a Denial of Service (DoS). This vulnerability was fixed in commit b43f9d1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2223"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.1:dev:*:*:*:*:*:*",
"matchCriteriaId": "2963671B-FA29-45DB-80B0-92F9E55F5159",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2223 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | A NULL pointer dereference in gf_filter_pid_set_property_full | https://api.github.com/repos/gpac/gpac/issues/2223/comments | 0 | 2022-07-07T10:26:55Z | 2022-07-12T17:13:11Z | https://github.com/gpac/gpac/issues/2223 | 1,297,164,642 | 2,223 | 3,985 |
CVE-2022-36190 | 2022-08-17T15:15:08.543 | GPAC mp4box 2.1-DEV-revUNKNOWN-master has a use-after-free vulnerability in function gf_isom_dovi_config_get. This vulnerability was fixed in commit fef6242. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2220"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2220 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Heap Use After Free in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/2220/comments | 1 | 2022-07-06T03:36:02Z | 2022-07-12T17:13:50Z | https://github.com/gpac/gpac/issues/2220 | 1,295,074,577 | 2,220 | 3,986 |
CVE-2022-36191 | 2022-08-17T16:15:07.920 | A heap-buffer-overflow had occurred in function gf_isom_dovi_config_get of isomedia/avc_ext.c:2490, as demonstrated by MP4Box. This vulnerability was fixed in commit fef6242. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2218"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4D3D58A-C3C9-4441-A84A-FB91FD19985C",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2218 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | heap-buffer-overflow in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/2218/comments | 0 | 2022-07-04T10:10:00Z | 2022-07-12T17:13:10Z | https://github.com/gpac/gpac/issues/2218 | 1,292,941,893 | 2,218 | 3,987 |
CVE-2022-2870 | 2022-08-17T19:15:07.497 | A vulnerability was found in laravel 5.1 and classified as problematic. This issue affects some unknown processing. The manipulation leads to deserialization. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier VDB-206501 was assigned to this vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 4.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/beicheng-maker/vulns/issues/2"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/?id.206501... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laravel:laravel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3794CF34-E1D7-4E1A-808E-D5AA4C2154E0",
"versionEndExcluding": null,
"versionEndIncluding": "5.1.46",
"versionStartExclud... | [
"502"
] | 502 | https://github.com/beicheng-maker/vulns/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"beicheng-maker",
"vulns"
] | # Laravel 5.1 POP Chain
`composer create-project --prefer-dist laravel/laravel laravel5.1 "5.1.*"`
`app/Http/Controllers/UsersController.php adding a controller UsersController`
```php
<?php
namespace App\Http\Controllers;
use Illuminate\Http\Request;
class UsersController extends Controller
{
/**
... | Laravel5.1 Unserialize RCE | https://api.github.com/repos/beicheng-maker/vulns/issues/2/comments | 4 | 2022-08-17T03:15:09Z | 2022-08-26T04:08:54Z | https://github.com/beicheng-maker/vulns/issues/2 | 1,341,109,531 | 2 | 3,988 |
CVE-2022-35147 | 2022-08-17T21:15:09.520 | DoraCMS v2.18 and earlier allows attackers to bypass login authentication via a crafted HTTP request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/doramart/DoraCMS/issues/256"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:html-js:doracms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B936DD6A-24A5-44AB-965B-5F9D26E1714A",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.8",
"versionStartExcludi... | [
"200"
] | 200 | https://github.com/doramart/DoraCMS/issues/256 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"doramart",
"DoraCMS"
] | There is login bypass in doracms2.18 and earlier versions. When logging in, you can bypass the login user authentication by replacing the return package with the return package after a system successfully logs in.
[Vulnerability proof]
Step 1:Log in to the system through the default account doracms and record the ret... | There is login bypass in doracms | https://api.github.com/repos/doramart/DoraCMS/issues/256/comments | 1 | 2022-07-01T05:50:13Z | 2022-08-23T08:23:40Z | https://github.com/doramart/DoraCMS/issues/256 | 1,290,941,924 | 256 | 3,989 |
CVE-2022-35148 | 2022-08-17T21:15:09.563 | maccms10 v2021.1000.1081 to v2022.1000.3031 was discovered to contain a SQL injection vulnerability via the table parameter at database/columns.html. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/magicblack/maccms10/issues/931"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trackin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maccms:maccms:10.0:2021.1000.1081:*:*:*:*:*:*",
"matchCriteriaId": "A7049FDA-9118-418C-9816-E2627C341D8F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"89"
] | 89 | https://github.com/magicblack/maccms10/issues/931 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"magicblack",
"maccms10"
] | Vulnerability name:SQL injection
Vulnerability level:Medium risk
Affected version:v2021.1000.1081<=v2022.1000.3031
Vulnerability location:
Log in to the background and click the database function module to select the data batch replacement function
 vulnerabilities via the urls and currentUrl parameters at /controller/OnlinePreviewController.java. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kekingcn/kkFileView/issues/366"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trackin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:keking:kkfileview:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3CF7B3A0-ACE8-4EF5-AF51-760E7B2650BF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/kekingcn/kkFileView/issues/366 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kekingcn",
"kkFileView"
] | 问题描述Description
kkFileview v4.1.0存在XSS漏洞,可能导致网站cookies泄露。
kkFileview v4.1.0 has an XSS vulnerability, which may lead to the leakage of website cookies.
漏洞位置vulerable code location
kkFileView/server/src/main/java/cn/keking/web/controller/OnlinePreviewController.java文件71行、86行,"urls"、"currentUrl"参数用户可控,且没有过滤特殊... | kkFileView XSS Vulnerability | https://api.github.com/repos/kekingcn/kkFileView/issues/366/comments | 2 | 2022-07-01T09:12:24Z | 2022-07-29T08:34:36Z | https://github.com/kekingcn/kkFileView/issues/366 | 1,291,138,782 | 366 | 3,991 |
CVE-2022-35598 | 2022-08-18T02:15:08.633 | A SQL injection vulnerability in ConnectionFactoryDAO.java in sazanrjb InventoryManagementSystem 1.0 allows attackers to execute arbitrary SQL commands via parameter username. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sazanrjb/InventoryManagementSystem"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sazanrjb/InventoryMan... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:inventorymanagementsystem_project:inventorymanagementsystem:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "85B0AF3A-0FEC-4DE4-A207-67A3BA34AE18",
"versionEndExcluding": null,
"versionEndIncludi... | [
"89"
] | 89 | https://github.com/sazanrjb/InventoryManagementSystem/issues/14 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sazanrjb",
"InventoryManagementSystem"
] | Hey, I find few parameters are vulnerable to SQL injection vulnerability.
A list of affected files:
UserDAO.java
Stocks.java
SupplierDAO.java
ProductDAO.java
CustomerDAO.java
ConnectionFactory.java | Sql Injection Security Issues | https://api.github.com/repos/sajxraj/InventoryManagementSystem/issues/14/comments | 2 | 2022-07-09T02:23:14Z | 2022-07-14T17:14:05Z | https://github.com/sajxraj/InventoryManagementSystem/issues/14 | 1,299,549,051 | 14 | 3,992 |
CVE-2022-35164 | 2022-08-18T05:15:07.603 | LibreDWG v0.12.4.4608 & commit f2dea29 was discovered to contain a heap use-after-free via bit_copy_chain. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/497"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A8152A2-6867-4B31-8F47-A1A655A49EFF",
"versionEndExcluding": "0.12.4.4608",
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/LibreDWG/libredwg/issues/497 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | # Vulnerability description
version: [0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608) & latest commit [f2dea29](https://github.com/LibreDWG/libredwg/commit/f2dea296a0a3bb16afdae8d2ca16749a617a4383)
poc: [poc](https://github.com/0xdd96/PoC/raw/main/libredwg/UAF-bit_copy_chain)
command: ./... | Heap use-after-free still exists in the bit_copy_chain | https://api.github.com/repos/LibreDWG/libredwg/issues/497/comments | 2 | 2022-06-17T12:04:26Z | 2023-06-27T10:19:27Z | https://github.com/LibreDWG/libredwg/issues/497 | 1,274,949,181 | 497 | 3,993 |
CVE-2022-35165 | 2022-08-18T05:15:07.657 | An issue in AP4_SgpdAtom::AP4_SgpdAtom() of Bento4-1.6.0-639 allows attackers to cause a Denial of Service (DoS) via a crafted mp4 input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/712"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"835"
] | 835 | https://github.com/axiomatic-systems/Bento4/issues/712 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Vulnerability description
**version:** Bento4-1.6.0-639
**command:** ./mp42aac $POC /dev/null
**Download:** [poc](https://github.com/0xdd96/PoC/raw/main/Bento4/AP4_SgpdAtom::AP4_SgpdAtom-out-of-memory)
Here is the trace reported by ASAN:
```
$ mp42aac poc /dev/null
AddressSanitizer: Out of memory. The proc... | Possible memory exhuastion in AP4_SgpdAtom::AP4_SgpdAtom(). The process has exhausted 65536MB memory. | https://api.github.com/repos/axiomatic-systems/Bento4/issues/712/comments | 0 | 2022-05-31T14:44:43Z | 2022-06-04T17:16:23Z | https://github.com/axiomatic-systems/Bento4/issues/712 | 1,253,977,287 | 712 | 3,994 |
CVE-2022-35166 | 2022-08-18T05:15:07.700 | libjpeg commit 842c7ba was discovered to contain an infinite loop via the component JPEG::ReadInternal. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/76"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:2022-06-15:*:*:*:*:*:*:*",
"matchCriteriaId": "CDECFA58-57FC-4227-A771-A74B47C7C502",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"835"
] | 835 | https://github.com/thorfdbg/libjpeg/issues/76 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | **version:** latest commit https://github.com/thorfdbg/libjpeg/commit/842c7baef7808f12cad19b49b2efcfa9575dbc78
**poc:** [poc](https://github.com/0xdd96/PoC/raw/main/libjpeg/infinite-loop-ReadInternal)
**command:** ./jpeg poc /dev/null
Here is the backtrace in GDB:
```
pwndbg> backtrace
#0 0x000055555558fa8a in... | Infinite loop in JPEG::ReadInternal | https://api.github.com/repos/thorfdbg/libjpeg/issues/76/comments | 1 | 2022-06-26T04:17:35Z | 2022-06-27T18:59:25Z | https://github.com/thorfdbg/libjpeg/issues/76 | 1,284,796,852 | 76 | 3,995 |
CVE-2022-35173 | 2022-08-18T06:15:07.280 | An issue was discovered in Nginx NJS v0.7.5. The JUMP offset for a break instruction was not set to a correct offset during code generation, leading to a segmentation violation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "http://hg.nginx.org/njs/rev/b7c4e0f714a9"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/40455389679... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:0.7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "AFF53793-2148-4A4F-AA75-6D9B959E9B7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"754"
] | 754 | https://github.com/nginx/njs/issues/553 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Hi, the following PoC triggers a crash (related to string fmt?) in the latest commit.
```js
(function() {
while ([])
try {
break
try {
return } catch (a) {}
} catch (b) {}
}())
```
Environment:
```
Commit: e008f7ae22834ff1173b7a0067b14c821102018d
System: Ubuntu 18.04.6 LTS
`... | SEGV in njs_sprintf.c:424:19 | https://api.github.com/repos/nginx/njs/issues/553/comments | 0 | 2022-06-20T21:18:10Z | 2024-07-20T00:35:11Z | https://github.com/nginx/njs/issues/553 | 1,277,395,914 | 553 | 3,996 |
CVE-2022-2876 | 2022-08-18T08:15:07.563 | A vulnerability, which was classified as critical, was found in SourceCodester Student Management System. Affected is an unknown function of the file index.php. The manipulation of the argument id leads to sql injection. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integr... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/beicheng-maker/vulns/issues/4"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/?id.206634... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:student_management_system_project:student_management_system:-:*:*:*:*:*:*:*",
"matchCriteriaId": "8A7EC412-2363-438C-8AE6-6483F8FF7D15",
"versionEndExcluding": null,
"versionEndIncluding... | [
"89"
] | 89 | https://github.com/beicheng-maker/vulns/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"beicheng-maker",
"vulns"
] | Sql injection vulnerability exists in the page ID code parameter of Student Management System, which can be exploited by attackers to obtain sensitive information and cause data leakage.

Sqlmap attack
![im... | Sql injection exists for Student Management System page ID | https://api.github.com/repos/beicheng-maker/vulns/issues/4/comments | 0 | 2022-08-17T14:18:09Z | 2022-08-17T14:18:09Z | https://github.com/beicheng-maker/vulns/issues/4 | 1,341,838,521 | 4 | 3,997 |
CVE-2020-27787 | 2022-08-18T19:15:14.210 | A Segmentaation fault was found in UPX in invert_pt_dynamic() function in p_lx_elf.cpp. An attacker with a crafted input file allows invalid memory address access that could lead to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/commit/e2f60adc95334f47e286838dac33160819c5d74d"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A4A2432-18AE-4B27-A527-030DD9D34F93",
"versionEndExcluding": "3.96",
"versionEndIncluding": null,
"versionStartExcludin... | [
"119"
] | 119 | https://github.com/upx/upx/issues/333 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | ## Environment
A crafted input will lead to crash in p_lx_elf.cpp at UPX 3.96(latest version,git clone from branch devel)
upx 3.96-git-1bb93d4fce9f+
UCL data compression library 1.03
zlib data compression library 1.2.8
LZMA SDK version 4.43
Copyright (C) 1996-2020 Markus Franz Xaver Johannes Oberhumer
Copyrigh... | Segmentation fault in PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5173 | https://api.github.com/repos/upx/upx/issues/333/comments | 4 | 2020-01-14T07:02:22Z | 2022-08-18T21:41:23Z | https://github.com/upx/upx/issues/333 | 549,373,236 | 333 | 3,998 |
CVE-2020-27790 | 2022-08-18T19:15:14.270 | A floating point exception issue was discovered in UPX in PackLinuxElf64::invert_pt_dynamic() function of p_lx_elf.cpp file. An attacker with a crafted input file could trigger this issue that could cause a crash leading to a denial of service. The highest impact is to Availability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/commit/eb90eab6325d009004ffb155e3e33f22d4d3ca26"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A4A2432-18AE-4B27-A527-030DD9D34F93",
"versionEndExcluding": "3.96",
"versionEndIncluding": null,
"versionStartExcludin... | [
"369"
] | 369 | https://github.com/upx/upx/issues/331 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | ## The environment
A crafted input will lead to crash in p_lx_elf.cpp at UPX 3.96(latest version,git clone from branch devel)
root@ubuntu:/home/upx_cp_2/src# ./upx.out --version
upx 3.96-git-0f4975fd7ffb+
UCL data compression library 1.03
zlib data compression library 1.2.8
LZMA SDK version 4.43
Copyright (C) ... | SIGFPE divide by zero in PackLinuxElf64::invert_pt_dynamic at p_lx_elf.cpp:5108 | https://api.github.com/repos/upx/upx/issues/331/comments | 2 | 2020-01-13T07:11:42Z | 2022-08-18T21:42:09Z | https://github.com/upx/upx/issues/331 | 548,744,640 | 331 | 3,999 |
CVE-2022-35204 | 2022-08-18T19:15:14.550 | Vitejs Vite before v2.9.13 was discovered to allow attackers to perform a directory traversal via a crafted URL to the victim's service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vitejs/vite/issues/8498"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vitejs:vite:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "BA74D018-9C42-4064-99A8-59E31BAB5856",
"versionEndExcluding": "2.9.13",
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/vitejs/vite/issues/8498 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"vitejs",
"vite"
] | ### Describe the bug
The vulnerability found at https://github.com/vitejs/vite/issues/2820 was found to be not fixed properly, which leads to the unrestricted directory traversal.
Currently the `@fs` directory does check for the allowed path, but it does not check for encoded paths.
For example, assuming that ... | Unrestricted directory traversal with `@fs` (Bypass) | https://api.github.com/repos/vitejs/vite/issues/8498/comments | 4 | 2022-06-08T04:16:20Z | 2022-07-23T00:24:39Z | https://github.com/vitejs/vite/issues/8498 | 1,264,168,583 | 8,498 | 4,000 |
CVE-2020-27788 | 2022-08-18T20:15:08.947 | An out-of-bounds read access vulnerability was discovered in UPX in PackLinuxElf64::canPack() function of p_lx_elf.cpp file. An attacker with a crafted input file could trigger this issue that could cause a crash leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/commit/1bb93d4fce9f1d764ba57bf5ac154af515b3fc83"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2A4A2432-18AE-4B27-A527-030DD9D34F93",
"versionEndExcluding": "3.96",
"versionEndIncluding": null,
"versionStartExcludin... | [
"125"
] | 125 | https://github.com/upx/upx/issues/332 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | ## Environment
A crafted input will lead to crash in p_lx_elf.cpp at UPX 3.96(latest version,git clone from branch devel)
root@ubuntu:/home/upx_cp_2/src# ./upx.out --version
upx 3.96-git-0f4975fd7ffb+
UCL data compression library 1.03
zlib data compression library 1.2.8
LZMA SDK version 4.43
Copyright (C) 1996... | heap-buffer-overflow in PackLinuxElf64::canPack() at p_lx_elf.cpp:2385 | https://api.github.com/repos/upx/upx/issues/332/comments | 2 | 2020-01-13T08:10:55Z | 2022-08-18T22:37:18Z | https://github.com/upx/upx/issues/332 | 548,768,610 | 332 | 4,001 |
CVE-2022-35213 | 2022-08-18T20:15:11.573 | Ecommerce-CodeIgniter-Bootstrap before commit 56465f was discovered to contain a cross-site scripting (XSS) vulnerability via the function base_url() at /blog/blogpublish.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kirilkirkov/Ecommerce-CodeIgniter-Bootstrap/commit/56465fb6a83aaa934a76615a8579100938b790a1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ecommerce-codeigniter-bootstrap_project:ecommerce-codeigniter-bootstrap:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A2060B33-D99A-4D99-8D54-6AB28E1EE59A",
"versionEndExcluding": "2021-08-21",
... | [
"79"
] | 79 | https://github.com/kirilkirkov/Ecommerce-CodeIgniter-Bootstrap/issues/219 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kirilkirkov",
"Ecommerce-CodeIgniter-Bootstrap"
] | We found multiple XSS vulnerabilities in the latest version of Ecommerce-CodeIgniter-Bootstrap.
Technique details:
The vulnerabilities occur at base_url() function. We notice the user inputs (e.g., $_POST) are used as the parameter of base_url() function in many places (e.g., the 45th line in /application/modules/... | XSS vulnerabilities | https://api.github.com/repos/kirilkirkov/Ecommerce-CodeIgniter-Bootstrap/issues/219/comments | 0 | 2021-08-22T11:13:03Z | 2021-08-23T18:27:29Z | https://github.com/kirilkirkov/Ecommerce-CodeIgniter-Bootstrap/issues/219 | 976,349,920 | 219 | 4,002 |
CVE-2022-37047 | 2022-08-18T20:15:11.837 | The component tcprewrite in Tcpreplay v4.4.1 was discovered to contain a heap-based buffer overflow in get_ipv6_next at common/get.c:713. NOTE: this is different from CVE-2022-27940. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/734"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/734 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get.c:713 | https://api.github.com/repos/appneta/tcpreplay/issues/734/comments | 1 | 2022-07-24T02:43:39Z | 2022-08-07T02:02:04Z | https://github.com/appneta/tcpreplay/issues/734 | 1,315,792,459 | 734 | 4,003 |
CVE-2022-37048 | 2022-08-18T20:15:11.880 | The component tcprewrite in Tcpreplay v4.4.1 was discovered to contain a heap-based buffer overflow in get_l2len_protocol at common/get.c:344. NOTE: this is different from CVE-2022-27941. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/735"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/735 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get.c:344 | https://api.github.com/repos/appneta/tcpreplay/issues/735/comments | 1 | 2022-07-24T07:35:35Z | 2022-08-07T02:55:11Z | https://github.com/appneta/tcpreplay/issues/735 | 1,315,833,757 | 735 | 4,004 |
CVE-2022-37049 | 2022-08-18T20:15:11.927 | The component tcpprep in Tcpreplay v4.4.1 was discovered to contain a heap-based buffer overflow in parse_mpls at common/get.c:150. NOTE: this is different from CVE-2022-27942. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/736"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/736 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get.c:150 | https://api.github.com/repos/appneta/tcpreplay/issues/736/comments | 1 | 2022-07-24T14:40:26Z | 2022-08-07T03:03:15Z | https://github.com/appneta/tcpreplay/issues/736 | 1,315,924,974 | 736 | 4,005 |
CVE-2022-37768 | 2022-08-18T20:15:11.970 | libjpeg commit 281daa9 was discovered to contain an infinite loop via the component Frame::ParseTrailer. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/77"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "43E4B6B8-F045-4BF3-AC73-8F5596EA703C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"835"
] | 835 | https://github.com/thorfdbg/libjpeg/issues/77 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | version: latest commit 14bf94c
poc: [poc.zip](https://github.com/thorfdbg/libjpeg/files/9191143/poc.zip)
command: ./jpeg poc /dev/null
The backtrace in gdb:
```
(gdb) bt
#0 ByteStream::Get (this=0x790ae0) at bytestream.cpp:223
#1 0x000000000042331e in IOStream::PeekWord (this=0x790ae0)
at iostream.cpp:... | Infinite loop in Frame::ParseTrailer | https://api.github.com/repos/thorfdbg/libjpeg/issues/77/comments | 1 | 2022-07-26T15:59:16Z | 2022-08-03T12:22:36Z | https://github.com/thorfdbg/libjpeg/issues/77 | 1,318,449,876 | 77 | 4,006 |
CVE-2022-37769 | 2022-08-18T20:15:12.013 | libjpeg commit 281daa9 was discovered to contain a segmentation fault via HuffmanDecoder::Get at huffmandecoder.hpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/78"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "43E4B6B8-F045-4BF3-AC73-8F5596EA703C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"119"
] | 119 | https://github.com/thorfdbg/libjpeg/issues/78 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | Hi, there.
There is a segmentation fault in the newest master branch.
Here is the reproducing command:
`jpeg poc /dev/null`
```
Program received signal SIGSEGV, Segmentation fault.
HuffmanDecoder::Get (this=0x0, io=0x7933c8)
at /home/users/chluo/libjpeg/codestream/../coding/huffmandecoder.hpp:112
warn... | Segmentation fault in HuffmanDecoder::Get | https://api.github.com/repos/thorfdbg/libjpeg/issues/78/comments | 1 | 2022-07-27T04:04:02Z | 2022-08-03T12:23:15Z | https://github.com/thorfdbg/libjpeg/issues/78 | 1,318,990,797 | 78 | 4,007 |
CVE-2022-37770 | 2022-08-18T20:15:12.060 | libjpeg commit 281daa9 was discovered to contain a segmentation fault via LineMerger::GetNextLowpassLine at linemerger.cpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/79"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "43E4B6B8-F045-4BF3-AC73-8F5596EA703C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"119"
] | 119 | https://github.com/thorfdbg/libjpeg/issues/79 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | Hi, there.
There is a segmentation fault in the newest master branch.
Here is the reproducing command:
`jpeg poc /dev/null`
```
(gdb) bt
#0 0x00007ffff7f31270 in ?? () from /lib/x86_64-linux-gnu/libc.so.6
#1 0x0000000000711b6f in LineMerger::GetNextLowpassLine (this=0x85ed20, comp=2 '\002')
at linem... | Segmentation fault in LineMerger::GetNextLowpassLine | https://api.github.com/repos/thorfdbg/libjpeg/issues/79/comments | 3 | 2022-07-28T04:17:56Z | 2022-08-03T12:22:57Z | https://github.com/thorfdbg/libjpeg/issues/79 | 1,320,369,822 | 79 | 4,008 |
CVE-2022-35540 | 2022-08-18T23:15:08.293 | Hardcoded JWT Secret in AgileConfig <1.6.8 Server allows remote attackers to use the generated JWT token to gain administrator access. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dotnetcore/AgileConfig/issues/91"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotnetcore:agileconfig:*:*:*:*:*:*:*:*",
"matchCriteriaId": "839201E6-FD66-4BD5-954D-0A92390A5B8C",
"versionEndExcluding": "1.6.8",
"versionEndIncluding": null,
"versionStart... | [
"798"
] | 798 | https://github.com/dotnetcore/AgileConfig/issues/91 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dotnetcore",
"AgileConfig"
] | The hard-coded JWT Secret in the source code allows remote attackers to gain administrator access in AgileConfig Server.
Details and POC have been emailed.
源代码中存在JWT key 硬编码,导致原有的登录限制可能被绕过,直接以管理员权限访问系统
详细信息和POC已发送至邮箱
| security vulnerability (存在安全漏洞) | https://api.github.com/repos/dotnetcore/AgileConfig/issues/91/comments | 4 | 2022-07-06T16:15:01Z | 2022-09-01T05:41:10Z | https://github.com/dotnetcore/AgileConfig/issues/91 | 1,296,073,627 | 91 | 4,009 |
CVE-2022-2886 | 2022-08-19T12:15:08.140 | A vulnerability, which was classified as critical, was found in Laravel 5.1. Affected is an unknown function. The manipulation leads to deserialization. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-206688. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/beicheng-maker/vulns/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://vuldb.com/?id.206688... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laravel:laravel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3794CF34-E1D7-4E1A-808E-D5AA4C2154E0",
"versionEndExcluding": null,
"versionEndIncluding": "5.1.46",
"versionStartExclud... | [
"502"
] | 502 | https://github.com/beicheng-maker/vulns/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"beicheng-maker",
"vulns"
] | # Laravel5.1 POP4 RCE
`composer create-project --prefer-dist laravel/laravel laravel5.1 "5.1.*"`
`app/Http/Controllers/UsersController.php adding a controller UsersController`
```php
<?php
namespace App\Http\Controllers;
use Illuminate\Http\Request;
class UsersController extends Controller
{
/**
... | Laravel5.1 POP4 RCE | https://api.github.com/repos/beicheng-maker/vulns/issues/3/comments | 0 | 2022-08-17T05:08:35Z | 2022-08-17T05:08:35Z | https://github.com/beicheng-maker/vulns/issues/3 | 1,341,174,463 | 3 | 4,010 |
CVE-2022-36605 | 2022-08-19T15:15:08.507 | Yimioa v6.1 was discovered to contain a SQL injection vulnerability via the orderbyGET parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cloudwebsoft/ywoa/issues/24"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yimihome:ywoa:6.1:*:*:*:*:*:*:*",
"matchCriteriaId": "EB7ABBCC-CAE9-442D-8084-176F08DBBAC0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/cloudwebsoft/ywoa/issues/24 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cloudwebsoft",
"ywoa"
] | # ywoaSQL-Inject-Bypass
# Environment build
## Windows build
Recommended to use Windows build, because idea build is very troublesome, and report a lot of errors, Windows is a one-click deployment
http://partner.yimihome.com/static/index.html#/index/sys_env
## 1, personnel - personnel information - orderbyG... | ywoa SQL inject Bypass and Analysis of the article | https://api.github.com/repos/cloudwebsoft/ywoa/issues/24/comments | 0 | 2022-07-21T02:54:36Z | 2023-09-07T13:28:46Z | https://github.com/cloudwebsoft/ywoa/issues/24 | 1,312,410,083 | 24 | 4,011 |
CVE-2022-36606 | 2022-08-19T15:15:08.550 | Ywoa before v6.1 was discovered to contain a SQL injection vulnerability via /oa/setup/checkPool?database. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cloudwebsoft/ywoa/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yimihome:ywoa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "70ADA123-C9C3-426E-A8EA-94CD3E377B74",
"versionEndExcluding": "6.1",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/cloudwebsoft/ywoa/issues/25 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cloudwebsoft",
"ywoa"
] | # Environment construction
http://partner.yimihome.com/static/index.html#/index/sys_env

Direct one-click installation can be started, and then login on the account admin password 1111111... | yimiYWOA<6.1 version foreground unauthorized SQL injection | https://api.github.com/repos/cloudwebsoft/ywoa/issues/25/comments | 0 | 2022-07-22T02:52:22Z | 2023-09-07T13:28:46Z | https://github.com/cloudwebsoft/ywoa/issues/25 | 1,314,075,554 | 25 | 4,012 |
CVE-2022-36224 | 2022-08-19T17:15:07.817 | XunRuiCMS V4.5.6 is vulnerable to Cross Site Request Forgery (CSRF). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/dayrui/xunruicms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xunruicms:xunruicms:4.5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "4E022B5A-17F8-4F5A-9154-747F0EDD4B6D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"352"
] | 352 | https://github.com/dayrui/xunruicms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"dayrui",
"xunruicms"
] | 本地搭建4.5.6版本
在后台,内容->文章管理->删除功能存在csrf

选择一个内容进行删除操作,弹出框点击确认并抓包

发送到csrf poc,并扔掉此包
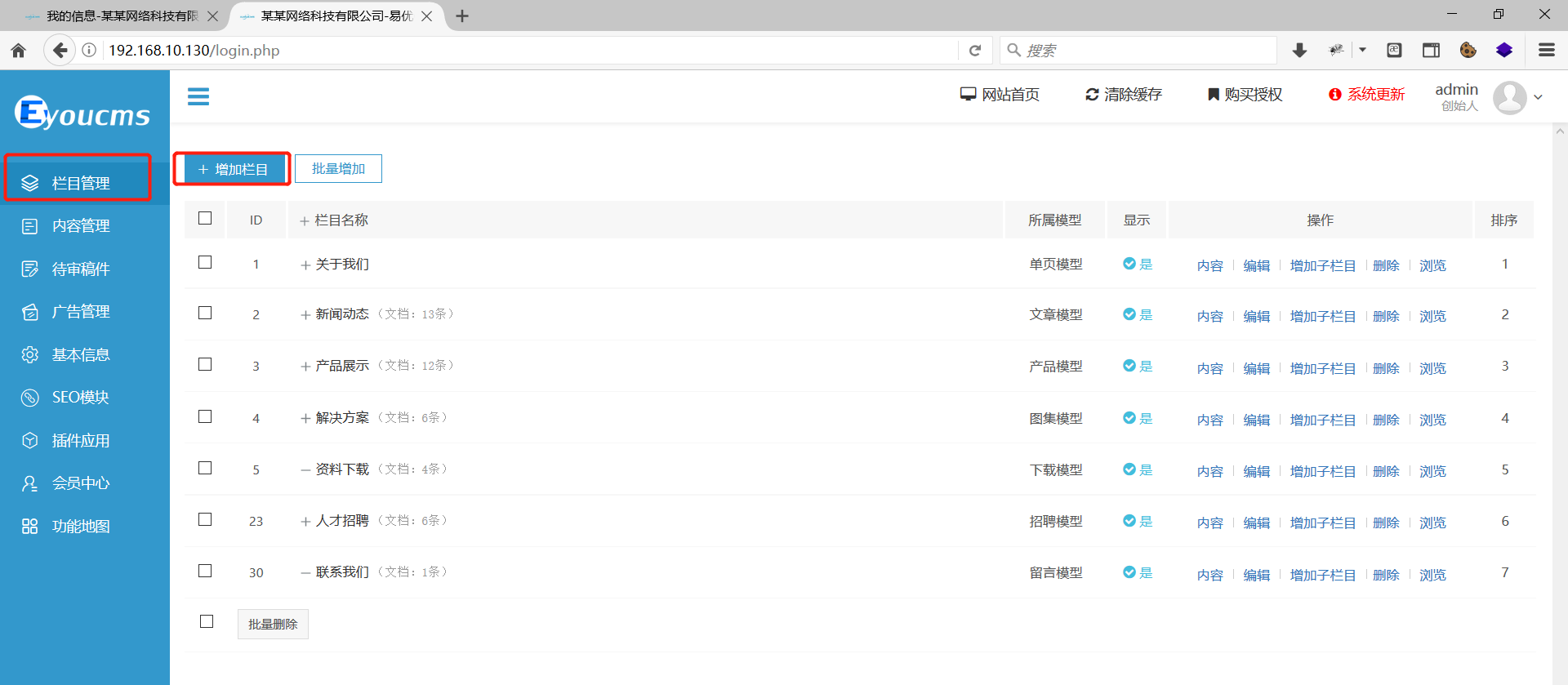
 via the background, column management function and add. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.5.8:*:*:*:*:*:*:*",
"matchCriteriaId": "82E421EB-ECC8-42A4-8384-4187474D1AC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/weng-xianhu/eyoucms/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | version:V1.5.8-UTF8-SP1

In the background, column management function and add.
Add test data... | EyouCMS v1.5.8 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/weng-xianhu/eyoucms/issues/26/comments | 2 | 2022-07-17T13:08:03Z | 2023-02-28T08:54:23Z | https://github.com/weng-xianhu/eyoucms/issues/26 | 1,307,093,003 | 26 | 4,014 |
CVE-2022-36577 | 2022-08-19T17:15:08.010 | An issue was discovered in jizhicms v2.3.1. There is a CSRF vulnerability that can add a admin. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/77"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F7444555-03D3-42CC-88CA-4BDE28C9CFC8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/Cherry-toto/jizhicms/issues/77 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | version:v2.3.1

The issue in the background - > User Management - > administrator list

add a ... | jizhicms v2.3.1 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/Cherry-toto/jizhicms/issues/77/comments | 1 | 2022-07-19T13:44:25Z | 2022-07-19T14:43:30Z | https://github.com/Cherry-toto/jizhicms/issues/77 | 1,309,547,815 | 77 | 4,015 |
CVE-2022-36578 | 2022-08-19T17:15:08.050 | jizhicms v2.3.1 has SQL injection in the background. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/78"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F7444555-03D3-42CC-88CA-4BDE28C9CFC8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/Cherry-toto/jizhicms/issues/78 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | version: v2.3.1
Problematic packets:
```
POST /index.php/admins/Fields/get_fields.html HTTP/1.1
Host: 192.168.10.130
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:54.0) Gecko/20100101 Firefox/54.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content... | jizhicms v2.3.1 has a vulnerability, SQL injection | https://api.github.com/repos/Cherry-toto/jizhicms/issues/78/comments | 1 | 2022-07-19T14:21:25Z | 2022-07-19T15:06:41Z | https://github.com/Cherry-toto/jizhicms/issues/78 | 1,309,598,383 | 78 | 4,016 |
CVE-2022-36579 | 2022-08-19T17:15:08.090 | Wellcms 2.2.0 is vulnerable to Cross Site Request Forgery (CSRF). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wellcms/wellcms/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wellcms:wellcms:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9D30FB54-27CB-4ADF-80A1-372F7BA7C082",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/wellcms/wellcms/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wellcms",
"wellcms"
] | version:2.2.0
position:Background - > manage users - > create users


add a new users, and gra... | wellcms v2.2.0 has a vulnerability, Cross-site request forgery(CSRF) | https://api.github.com/repos/wellcms/wellcms/issues/11/comments | 1 | 2022-07-23T12:56:19Z | 2022-07-23T14:50:06Z | https://github.com/wellcms/wellcms/issues/11 | 1,315,652,867 | 11 | 4,017 |
CVE-2022-37254 | 2022-08-19T17:15:08.133 | DolphinPHP 1.5.1 is vulnerable to Cross Site Scripting (XSS) via Background - > System - > system function - > configuration management. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/caiweiming/DolphinPHP/issues/42"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dolphinphp_project:dolphinphp:1.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6CF0D652-3247-4BBA-8070-026C39EBAEE1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"79"
] | 79 | https://github.com/caiweiming/DolphinPHP/issues/42 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"caiweiming",
"DolphinPHP"
] | version:1.5.1
Vulnerability location:Background - > System - > system function - > configuration management.

 | https://api.github.com/repos/caiweiming/DolphinPHP/issues/42/comments | 1 | 2022-07-29T15:08:41Z | 2024-07-10T09:50:07Z | https://github.com/caiweiming/DolphinPHP/issues/42 | 1,322,367,864 | 42 | 4,018 |
CVE-2022-36157 | 2022-08-19T22:15:09.017 | XXL-JOB all versions as of 11 July 2022 are vulnerable to Insecure Permissions resulting in the ability to execute admin function with low Privilege account. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Richard-Muzi/vulnerability/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B9117C48-ADBB-4018-8476-F291CA8A2BF4",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.1",
"versionStartExcludi... | [
"269"
] | 269 | https://github.com/Richard-Muzi/vulnerability/issues/1 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Richard-Muzi",
"vulnerability"
] | XXL-JOB is a distributed task scheduling framework, the core design goal is to develop quickly, learning simple, lightweight, easy to expand. Is now open source and access to a number of companies online product line.
https://www.xuxueli.com/xxl-job/en/
https://github.com/xuxueli/xxl-job/
A Escalation of Privilege... | XXL-JOB Escalation of Privileges vulnerability | https://api.github.com/repos/Richard-Muzi/vulnerability/issues/1/comments | 0 | 2022-07-11T06:39:47Z | 2022-07-11T07:59:53Z | https://github.com/Richard-Muzi/vulnerability/issues/1 | 1,300,276,528 | 1 | 4,019 |
CVE-2020-27793 | 2022-08-19T23:15:08.367 | An off-by-one overflow flaw was found in radare2 due to mismatched array length in core_java.c. This could allow an attacker to cause a crash, and perform a denail of service attack. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/commit/ced0223c7a1b3b5344af315715cd28fe7c0d9ebc"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE8DA49-FB7A-4416-8942-56DD67E62CD9",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | [
"193"
] | 193 | https://github.com/radareorg/radare2/issues/16304 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | unmatched array length in core_java.c | https://api.github.com/repos/radareorg/radare2/issues/16304/comments | 1 | 2020-03-25T04:35:41Z | 2020-03-26T11:02:44Z | https://github.com/radareorg/radare2/issues/16304 | 587,435,992 | 16,304 | 4,020 |
CVE-2020-27794 | 2022-08-19T23:15:08.427 | A double free issue was discovered in radare2 in cmd_info.c:cmd_info(). Successful exploitation could lead to modification of unexpected memory locations and potentially causing a crash. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "NONE",
"in... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/commit/cb8b683758edddae2d2f62e8e63a738c39f92683"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE8DA49-FB7A-4416-8942-56DD67E62CD9",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | [
"415"
] | 415 | https://github.com/radareorg/radare2/issues/16303 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | invalid free in cmd_info.c:cmd_info() | https://api.github.com/repos/radareorg/radare2/issues/16303/comments | 1 | 2020-03-25T04:31:50Z | 2020-03-26T11:28:51Z | https://github.com/radareorg/radare2/issues/16303 | 587,434,855 | 16,303 | 4,021 |
CVE-2020-27795 | 2022-08-19T23:15:08.487 | A segmentation fault was discovered in radare2 with adf command. In libr/core/cmd_anal.c, when command "adf" has no or wrong argument, anal_fcn_data (core, input + 1) --> RAnalFunction *fcn = r_anal_get_fcn_in (core->anal, core->offset, -1); returns null pointer for fcn causing segmentation fault later in ensure_fcn_ra... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/commit/4d3811681a80f92a53e795f6a64c4b0fc2c8dd22"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EEE8DA49-FB7A-4416-8942-56DD67E62CD9",
"versionEndExcluding": "4.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | [
"908"
] | 908 | https://github.com/radareorg/radare2/issues/16215 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ### Work environment
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) | Ubuntu x86 64
| File format of the file you reverse (mandatory) | ELF
| Architecture/bit... | command "adf" Segmentation fault | https://api.github.com/repos/radareorg/radare2/issues/16215/comments | 1 | 2020-03-14T07:54:59Z | 2020-03-16T16:03:23Z | https://github.com/radareorg/radare2/issues/16215 | 581,094,359 | 16,215 | 4,022 |
CVE-2022-24298 | 2022-08-23T05:15:07.760 | All versions of package freeopcua/freeopcua are vulnerable to Denial of Service (DoS) when bypassing the limitations for excessive memory consumption by sending multiple CloseSession requests with the deleteSubscription parameter equal to False. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FreeOpcUa/freeopcua/issues/391"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://security.snyk.io/vuln/SNYK-UNMANAG... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:freeopcua_project:freeopcua:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7F2A8BC2-6B2D-47B0-8268-77AA65032C5B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"770"
] | 770 | https://github.com/FreeOpcUa/freeopcua/issues/391 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FreeOpcUa",
"freeopcua"
] | We would like to responsibly report on a vulnerability we found in freeopcua (cpp). Where should we send our detailed report?
Additionally I would like to suggest adding a security policy to the repository to help other security researchers reach out to you properly.
Thanks!
Team82 Claroty Research
https://clar... | How to report a security issue? | https://api.github.com/repos/FreeOpcUa/freeopcua/issues/391/comments | 0 | 2022-05-23T13:01:50Z | 2022-05-23T13:01:50Z | https://github.com/FreeOpcUa/freeopcua/issues/391 | 1,245,134,139 | 391 | 4,023 |
CVE-2022-25304 | 2022-08-23T05:15:07.987 | All versions of package opcua; all versions of package asyncua are vulnerable to Denial of Service (DoS) due to a missing limitation on the number of received chunks - per single session or in total for all concurrent sessions. An attacker can exploit this vulnerability by sending an unlimited number of huge chunks (e.... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FreeOpcUa/python-opcua/issues/1466"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://security.snyk.io/vuln/SNYK-PYT... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:asyncua_project:asyncua:*:*:*:*:*:python:*:*",
"matchCriteriaId": "515536F5-025D-4947-A517-339AE3019B7C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"770"
] | 770 | https://github.com/FreeOpcUa/python-opcua/issues/1466 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FreeOpcUa",
"python-opcua"
] | We would like to responsibly report on a vulnerability we found in python opcua. Where should we send our detailed report?
Additionally I would like to suggest adding a security policy to the repository to help other security researchers reach out to you properly.
Thanks!
Team82 Claroty Research
https://claroty... | How to report a security issue? | https://api.github.com/repos/FreeOpcUa/python-opcua/issues/1466/comments | 6 | 2022-05-23T12:59:14Z | 2022-05-26T11:34:46Z | https://github.com/FreeOpcUa/python-opcua/issues/1466 | 1,245,130,623 | 1,466 | 4,024 |
CVE-2022-37199 | 2022-08-23T13:15:08.520 | JFinal CMS 5.1.0 is vulnerable to SQL Injection via /jfinal_cms/system/user/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/48"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jflyfox/jfinal_cms/issues/48 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | the route is /jfinal_cms/system/user/list


| There is a SQL injection vulnerability exists in JFinal CMS 5.1.0 again | https://api.github.com/repos/jflyfox/jfinal_cms/issues/49/comments | 0 | 2022-07-28T23:48:08Z | 2022-07-28T23:48:08Z | https://github.com/jflyfox/jfinal_cms/issues/49 | 1,321,600,614 | 49 | 4,026 |
CVE-2021-23177 | 2022-08-23T16:15:09.280 | An improper link resolution flaw while extracting an archive can lead to changing the access control list (ACL) of the target of the link. An attacker may provide a malicious archive to a victim user, who would trigger this flaw when trying to extract the archive. A local attacker may use this flaw to change the ACL of... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-23177"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libarchive:libarchive:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A55FBDE8-F405-4C72-BCDC-756873D578C9",
"versionEndExcluding": "3.5.2",
"versionEndIncluding": null,
"versionStartE... | [
"59"
] | 59 | https://github.com/libarchive/libarchive/issues/1565 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libarchive",
"libarchive"
] | When an archive entry contains a symbolic link that has defined ACLs on Linux, on extraction the ACLs of the link target are modified. This is because the function acl_set_file() is used without a prior check if the file is not a symbolic link.
FreeBSD and MacOS use acl_set_link_np() that does not follow symbolic li... | [SECURITY] Linux: extracting a symlink with ACLs modifies ACLs of target | https://api.github.com/repos/libarchive/libarchive/issues/1565/comments | 3 | 2021-08-21T17:41:51Z | 2021-12-17T07:33:13Z | https://github.com/libarchive/libarchive/issues/1565 | 976,185,621 | 1,565 | 4,027 |
CVE-2021-31566 | 2022-08-23T16:15:09.337 | An improper link resolution flaw can occur while extracting an archive leading to changing modes, times, access control lists, and flags of a file outside of the archive. An attacker may provide a malicious archive to a victim user, who would trigger this flaw when trying to extract the archive. A local attacker may us... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-31566"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libarchive:libarchive:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A55FBDE8-F405-4C72-BCDC-756873D578C9",
"versionEndExcluding": "3.5.2",
"versionEndIncluding": null,
"versionStartE... | [
"59"
] | 59 | https://github.com/libarchive/libarchive/issues/1566 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libarchive",
"libarchive"
] | Some modes, times, ACLs and file flags especially on directories are set on archive_write_close() time. An archive can contain multiple entries with the same path. If a directory entry is marked for post-processing and a symlink entry with the same path "replaces" the directory with the symlink, the "fixup" postprocess... | [SECURITY] Processing fixup entries may follow symbolic links | https://api.github.com/repos/libarchive/libarchive/issues/1566/comments | 4 | 2021-08-22T04:09:32Z | 2021-12-17T07:37:45Z | https://github.com/libarchive/libarchive/issues/1566 | 976,279,379 | 1,566 | 4,028 |
CVE-2021-3701 | 2022-08-23T16:15:09.500 | A flaw was found in ansible-runner where the default temporary files configuration in ansible-2.0.0 are written to world R/W locations. This flaw allows an attacker to pre-create the directory, resulting in reading private information or forcing ansible-runner to write files as the legitimate user in a place they did n... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 6.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Vendor Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-3701"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible_runner:2.0.0:-:*:*:*:*:*:*",
"matchCriteriaId": "1470BAF6-3B08-42DB-AD44-B5887D24D787",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"276"
] | 276 | https://github.com/ansible/ansible-runner/issues/738 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible-runner"
] | related to: https://github.com/ansible/ansible-runner/pull/722
| ansible-runner writes artifacts to world rw location by default | https://api.github.com/repos/ansible/ansible-runner/issues/738/comments | 2 | 2021-06-24T20:55:44Z | 2021-06-29T13:01:34Z | https://github.com/ansible/ansible-runner/issues/738 | 929,605,116 | 738 | 4,029 |
CVE-2021-3905 | 2022-08-23T16:15:10.177 | A memory leak was found in Open vSwitch (OVS) during userspace IP fragmentation processing. An attacker could use this flaw to potentially exhaust available memory by keeping sending packet fragments. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-3905"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzil... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openvswitch:openvswitch:*:*:*:*:*:*:*:*",
"matchCriteriaId": "59369EE4-B970-4222-AA4E-276928B1016B",
"versionEndExcluding": "2.17.0",
"versionEndIncluding": null,
"versionSta... | [
"401"
] | 401 | https://github.com/openvswitch/ovs-issues/issues/226 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"openvswitch",
"ovs-issues"
] | Hi,
This commit introduce a mempool memleak.
[640d4db788eda96bb904abcfc7de2327107bafe1](https://github.com/openvswitch/ovs/commit/640d4db788eda96bb904abcfc7de2327107bafe1)
If I keep sending first fragment as an attack, the mempool would be exhausted.
I think revert it and respect the dnsteal flag as @ Wang L... | ipf memleak | https://api.github.com/repos/openvswitch/ovs-issues/issues/226/comments | 10 | 2021-09-29T09:58:10Z | 2021-10-12T05:47:39Z | https://github.com/openvswitch/ovs-issues/issues/226 | 1,010,749,369 | 226 | 4,030 |
CVE-2022-37111 | 2022-08-23T16:15:11.677 | BlueCMS 1.6 has SQL injection in line 132 of admin/article.php | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/seizer-zyx/Vulnerability/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bluecms_project:bluecms:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "6A26806A-9CB5-4262-BAD1-049659C2CE2C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/seizer-zyx/Vulnerability/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"seizer-zyx",
"Vulnerability"
] | # Bluecms_v1.6
## Download
http://lp.downcode.com/j_14/j_14745_bluecms.rar
## vulnerability code:
in admin/article.php line132:
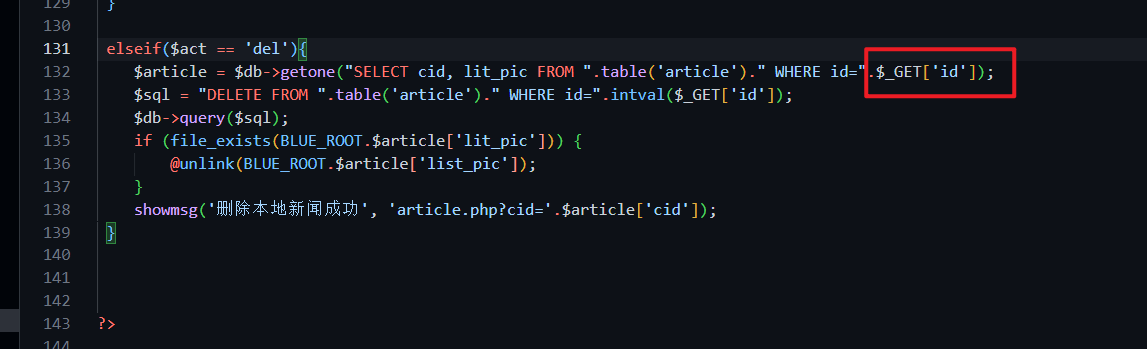
There is numeric injection for $_GET['id']
Because there is no echo, you ... | Bluecms V1.6 has SQL injection in line 132 of admin/article.php | https://api.github.com/repos/seizer-zyx/Vulnerability/issues/1/comments | 0 | 2022-07-26T02:16:33Z | 2022-07-26T06:37:09Z | https://github.com/seizer-zyx/Vulnerability/issues/1 | 1,317,605,361 | 1 | 4,031 |
CVE-2022-37112 | 2022-08-23T16:15:11.717 | BlueCMS 1.6 has SQL injection in line 55 of admin/model.php | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/seizer-zyx/Vulnerability/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bluecms_project:bluecms:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "6A26806A-9CB5-4262-BAD1-049659C2CE2C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/seizer-zyx/Vulnerability/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"seizer-zyx",
"Vulnerability"
] | ## Download
http://lp.downcode.com/j_14/j_14745_bluecms.rar
## vulnerability code:
in admin/model.php line 55:
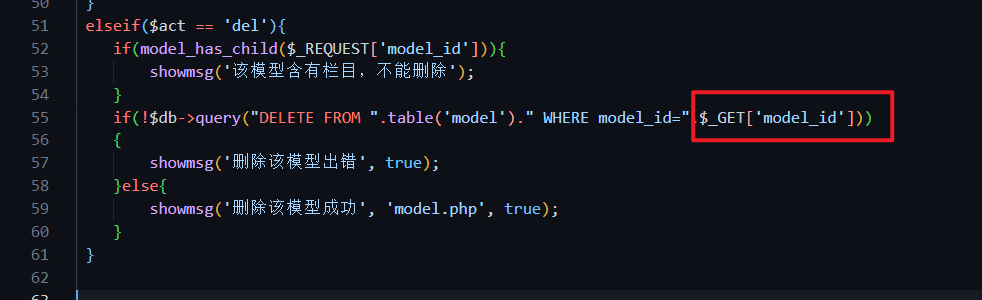
There is numeric injection for $_GET['model_id']
Because there is no echo, you can blind SQ... | Bluecms V1.6 has SQL injection in line 55 of admin/model.php | https://api.github.com/repos/seizer-zyx/Vulnerability/issues/2/comments | 0 | 2022-07-26T07:07:06Z | 2022-07-26T07:07:06Z | https://github.com/seizer-zyx/Vulnerability/issues/2 | 1,317,796,057 | 2 | 4,032 |
CVE-2022-37113 | 2022-08-23T16:15:11.757 | Bluecms 1.6 has SQL injection in line 132 of admin/area.php | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/seizer-zyx/Vulnerability/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bluecms_project:bluecms:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "6A26806A-9CB5-4262-BAD1-049659C2CE2C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/seizer-zyx/Vulnerability/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"seizer-zyx",
"Vulnerability"
] | # Bluecms_v1.6
## Download
http://lp.downcode.com/j_14/j_14745_bluecms.rar
## vulnerability code:
in admin/area.php line 36:
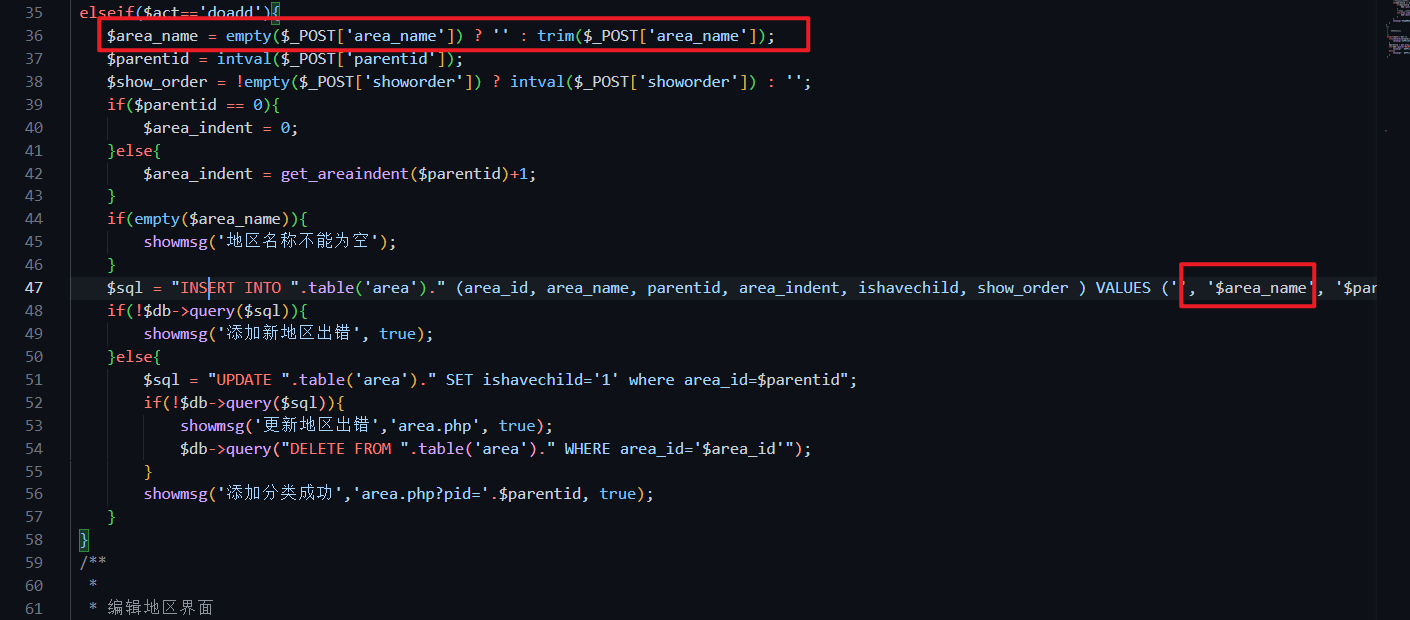
Line 36 of admin/area.php is not heavily filtered, and in... | Bluecms V1.6 has SQL injection in line 132 of admin/area.php | https://api.github.com/repos/seizer-zyx/Vulnerability/issues/3/comments | 0 | 2022-07-26T09:22:51Z | 2022-07-26T09:22:51Z | https://github.com/seizer-zyx/Vulnerability/issues/3 | 1,317,952,065 | 3 | 4,033 |
CVE-2021-3917 | 2022-08-23T20:15:08.360 | A flaw was found in the coreos-installer, where it writes the Ignition config to the target system with world-readable access permissions. This flaw allows a local attacker to have read access to potentially sensitive data. The highest threat from this vulnerability is to confidentiality. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Vendor Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-3917"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:coreos-installer:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A5FB7948-D4C7-4806-A707-B1F4FC340F97",
"versionEndExcluding": "0.10.0",
"versionEndIncluding": null,
"versionSta... | [
"276"
] | 276 | https://github.com/coreos/fedora-coreos-tracker/issues/889 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"coreos",
"fedora-coreos-tracker"
] | In the ignition file sometimes contains secrets and the best option maybe for this is denied access to unauthorized users.
The only way to access has to be through `sudo` or with the root account. | Change `/boot/ignition/config.ign` permissions to 0600 and delete it after provisioning | https://api.github.com/repos/coreos/fedora-coreos-tracker/issues/889/comments | 19 | 2021-07-06T13:02:39Z | 2021-11-23T05:22:02Z | https://github.com/coreos/fedora-coreos-tracker/issues/889 | 937,874,394 | 889 | 4,034 |
CVE-2021-4178 | 2022-08-24T16:15:09.770 | A arbitrary code execution flaw was found in the Fabric 8 Kubernetes client affecting versions 5.0.0-beta-1 and above. Due to an improperly configured YAML parsing, this will allow a local and privileged attacker to supply malicious YAML. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 6.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Vendor Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-4178"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cg... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:fabric8-kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9C5E8807-F660-4409-A21C-754651357607",
"versionEndExcluding": "5.0.3",
"versionEndIncluding": null,
"versionSt... | [
"502"
] | 502 | https://github.com/fabric8io/kubernetes-client/issues/3653 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fabric8io",
"kubernetes-client"
] | ### Describe the bug
Hi team,
I think I found a security issue in the kubernetes-client library which can cause code execution depending on where the input is coming from. If a malicious config string or Kubernetes resource string is passed to a specific function in the library, this will execute arbitrary Java cod... | Security issue in kubernetes-client | https://api.github.com/repos/fabric8io/kubernetes-client/issues/3653/comments | 5 | 2021-12-16T15:03:31Z | 2022-03-03T09:28:59Z | https://github.com/fabric8io/kubernetes-client/issues/3653 | 1,082,300,494 | 3,653 | 4,035 |
CVE-2021-4214 | 2022-08-24T16:15:10.037 | A heap overflow flaw was found in libpngs' pngimage.c program. This flaw allows an attacker with local network access to pass a specially crafted PNG file to the pngimage utility, causing an application to crash, leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2021-4214"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugz... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libpng:libpng:1.6.0:-:*:*:*:*:*:*",
"matchCriteriaId": "42882881-6827-4123-B217-FC9B4C36702A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"120"
] | 120 | https://github.com/glennrp/libpng/issues/302 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"glennrp",
"libpng"
] | Hi, I find a potential heap overflow issue in contrib/libtests/pngimage.c, function compare_read.
The code version is commit https://github.com/glennrp/libpng/commit/301f7a14295a3bdfaf406dbb5004d0784dc137ea
The compile command is
`CFLAGS="-O0 -g -fsanitize=address,leak,undefined" ./configure --disable-shared`
... | A potential heap overflow issue | https://api.github.com/repos/pnggroup/libpng/issues/302/comments | 3 | 2019-06-25T14:50:55Z | 2022-01-26T06:39:19Z | https://github.com/pnggroup/libpng/issues/302 | 460,472,662 | 302 | 4,036 |
CVE-2022-37178 | 2022-08-24T17:15:08.290 | An issue was discovered in 72crm 9.0. There is a SQL Injection vulnerability in View the task calendar. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/72wukong/72crm-9.0-PHP/issues/34"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:72crm:wukong_crm:9.0:*:*:*:*:*:*:*",
"matchCriteriaId": "7FD0E887-2558-4A21-B67E-D5E2B722ABEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/72wukong/72crm-9.0-PHP/issues/34 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"72wukong",
"72crm-9.0-PHP"
] | ## **Brief of this vulnerability**
72crm v9 has sql injection vulnerability in View the task calendar
## **Test Environment**
- Windows10
- PHP 5.6.9+Apache/2.4.39
## **Affect version**
72crm v9
## **Vulnerable Code**
application\work\controller\Task.php line 506
The $param parameter is passed ... | 72crm v9 has sql injection vulnerability | https://api.github.com/repos/WuKongOpenSource/WukongCRM-9.0-PHP/issues/34/comments | 0 | 2022-07-28T04:35:24Z | 2022-07-28T04:35:24Z | https://github.com/WuKongOpenSource/WukongCRM-9.0-PHP/issues/34 | 1,320,380,250 | 34 | 4,037 |
CVE-2022-37181 | 2022-08-24T17:15:08.343 | 72crm 9.0 has an Arbitrary file upload vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/72wukong/72crm-9.0-PHP/issues/35"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:72crm:wukong_crm:9.0:*:*:*:*:*:*:*",
"matchCriteriaId": "7FD0E887-2558-4A21-B67E-D5E2B722ABEE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/72wukong/72crm-9.0-PHP/issues/35 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"72wukong",
"72crm-9.0-PHP"
] | ## **Brief of this vulnerability**
72crm v9 has Arbitrary file upload vulnerability Where to upload the logo
## **Test Environment**
- Windows10
- PHP 5.6.9+Apache/2.4.39
## **Affect version**
72crm v9
## **Vulnerable Code**
application\admin\controller\System.php line 51
我花费了 2-4 小时自查,发现可能的原因是:Weak password vulnerability in the management system
### 复现步骤
 on error message strings returned through the 5th parameter of sqlite3_exec() after the error message string is no longer needed."
https://github.com/hughsie/colord/blob/1572d92bb69de7632841bf17f3cb81534881c3c6... | potential memory leak: forgetting to free error message of libsqlite3 API 'sqlite3_exec' -1 | https://api.github.com/repos/hughsie/colord/issues/110/comments | 5 | 2020-03-21T15:10:44Z | 2022-08-26T07:40:04Z | https://github.com/hughsie/colord/issues/110 | 585,517,804 | 110 | 4,040 |
CVE-2021-43766 | 2022-08-25T18:15:09.317 | Odyssey passes to server unencrypted bytes from man-in-the-middle When Odyssey is configured to use certificate Common Name for client authentication, a man-in-the-middle attacker can inject arbitrary SQL queries when a connection is first established, despite the use of SSL certificate verification and encryption. Thi... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integ... | [
{
"source": "patrick@puiterwijk.org",
"tags": null,
"url": "https://github.com/yandex/odyssey/issues/376%2C"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Not Applicable"
],
"url": "https://www.postgresql.org/support/security/CVE-2021-23214/"
},
{
"source": "af854... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odyssey_project:odyssey:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "34DBBE36-E704-416B-B8C1-CCF6D8F2B865",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"295"
] | 295 | https://github.com/yandex/odyssey/issues/376%2C | null | github.com | [
"yandex",
"odyssey"
] | When Odyssey is configured to use certificate Common Name for client authentication, a man-in-the-middle attacker can inject arbitrary SQL queries when a connection is first established, despite the use of SSL certificate verification and encryption. This is similar to CVE-2021-23214 for PostgreSQL.
This issue was f... | CVE-2021-43766: Odyssey passes to server unencrypted bytes from man-in-the-middle | https://api.github.com/repos/yandex/odyssey/issues/376/comments | 0 | 2021-12-06T06:42:53Z | 2021-12-06T06:42:56Z | https://github.com/yandex/odyssey/issues/376 | 1,071,787,095 | 376 | 4,041 |
CVE-2021-43767 | 2022-08-25T18:15:09.377 | Odyssey passes to client unencrypted bytes from man-in-the-middle When Odyssey storage is configured to use the PostgreSQL server using 'trust' authentication with a 'clientcert' requirement or to use 'cert' authentication, a man-in-the-middle attacker can inject false responses to the client's first few queries. Despi... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "patrick@puiterwijk.org",
"tags": null,
"url": "https://github.com/yandex/odyssey/issues/377%2C"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Not Applicable",
"Vendor Advisory"
],
"url": "https://www.postgresql.org/support/security/CVE-2021-23222/"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:postgresql:postgresql:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2E950ED8-CA9E-4C53-BD86-7E1BEF561E9A",
"versionEndExcluding": "9.6.24",
"versionEndIncluding": null,
"versionStart... | [
"295"
] | 295 | https://github.com/yandex/odyssey/issues/377%2C | null | github.com | [
"yandex",
"odyssey"
] | When Odyssey storage is configured to use the PostgreSQL server using `trust` authentication with a `clientcert` requirement or to use `cert` authentication, a man-in-the-middle attacker can inject false responses to the client's first few queries. Despite the use of SSL certificate verification and encryption, Odyssey... | CVE-2021-43767: Odyssey passes to client unencrypted bytes from man-in-the-middle | https://api.github.com/repos/yandex/odyssey/issues/377/comments | 0 | 2021-12-06T06:43:37Z | 2021-12-06T06:43:40Z | https://github.com/yandex/odyssey/issues/377 | 1,071,787,462 | 377 | 4,042 |
CVE-2021-4022 | 2022-08-25T18:15:09.443 | A vulnerability was found in rizin. The bug involves an ELF64 binary for the HPPA architecture. When a specially crafted binarygets analysed by rizin, it causes rizin to crash by freeing an uninitialized (and potentially user controlled, depending on the build) memory address. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rizinorg/rizin/issues/2015"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rizin:rizin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DDF54820-3CA2-49DC-9B65-DF480E8AF596",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.1",
"versionStartExcluding":... | [
"416"
] | 416 | https://github.com/rizinorg/rizin/issues/2015 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rizinorg",
"rizin"
] | ### Work environment
With @ogianatiempo we discovered a bug which makes rizin crash when analyzing certain kind of binaries.
| Questions | Answers
|------------------------------------------------------|--------------------
| OS/arch/bits (mandatory) ... | CVE-2021-4022: Segfault when analyzing an ELF64 for HPPA architecture | https://api.github.com/repos/rizinorg/rizin/issues/2015/comments | 9 | 2021-11-23T15:46:59Z | 2021-11-29T12:15:17Z | https://github.com/rizinorg/rizin/issues/2015 | 1,061,438,966 | 2,015 | 4,043 |
CVE-2022-36527 | 2022-08-25T19:15:08.483 | Jfinal CMS v5.1.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the post title text field under the publish blog module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/45"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/jflyfox/jfinal_cms/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | There is a stored XSS vulnerability in JFinal_cms 's publish blog module. An attacker could insert malicious XSS code into the post title. When users and administrators view the blog post, the malicious XSS code is triggered successfully.
First register a user to test it, then go to the submit blog post page and ins... | XSS vulnerability1 in jfinal_cms 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/45/comments | 0 | 2022-07-18T04:43:11Z | 2022-07-18T04:43:11Z | https://github.com/jflyfox/jfinal_cms/issues/45 | 1,307,399,442 | 45 | 4,044 |
CVE-2020-27796 | 2022-08-25T20:15:08.487 | A heap-based buffer over-read was discovered in the invert_pt_dynamic function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/392"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/upx/upx/issues/392 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow in the latest commit of the devel branch
ASAN reports:
```
==21202==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x62f00000c530 at pc 0x00000058b076 bp 0x7ffdc9ecf670 sp 0x7ffdc9ecf668
READ of... | Heap buffer overflow in PackLinuxElf32::invert_pt_dynamic | https://api.github.com/repos/upx/upx/issues/392/comments | 1 | 2020-07-23T08:29:53Z | 2020-08-06T06:29:46Z | https://github.com/upx/upx/issues/392 | 664,292,638 | 392 | 4,045 |
CVE-2020-27797 | 2022-08-25T20:15:08.537 | An invalid memory address reference was discovered in the elf_lookup function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/390"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"763"
] | 763 | https://github.com/upx/upx/issues/390 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
Segmentation fault in PackLinuxElf32::elf_lookup(char const*) of /src/p_lx_elf.cpp in the latest commit of the devel branch
code link : [p_lx_elf.cpp#L5486](https://github.com/upx/upx/blob/87b73e5cfdc12da94c251b2cd83bb01c7d9f616... | Segmentation fault in PackLinuxElf32::elf_lookup(char const*) of /src/p_lx_elf.cpp | https://api.github.com/repos/upx/upx/issues/390/comments | 2 | 2020-07-23T08:06:10Z | 2020-08-06T06:28:39Z | https://github.com/upx/upx/issues/390 | 664,279,490 | 390 | 4,046 |
CVE-2020-27798 | 2022-08-25T20:15:08.583 | An invalid memory address reference was discovered in the adjABS function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/396"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"763"
] | 763 | https://github.com/upx/upx/issues/396 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
Segmentation fault in PackLinuxElf64::adjABS of p_lx_elf.cpp in the latest commit of the devel branch
code:
```
────────────────────────────────────────────────────────────────────────────────[ REGISTERS ]──────────────────────... | Segmentation fault in PackLinuxElf64::adjABS of p_lx_elf.cpp | https://api.github.com/repos/upx/upx/issues/396/comments | 1 | 2020-07-24T09:28:47Z | 2020-08-06T06:30:09Z | https://github.com/upx/upx/issues/396 | 665,044,143 | 396 | 4,047 |
CVE-2020-27799 | 2022-08-25T20:15:08.630 | A heap-based buffer over-read was discovered in the acc_ua_get_be32 function in miniacc.h in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/391"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/upx/upx/issues/391 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit of the devel branch
ASAN reports:
```
==21053==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6160000014bb at pc 0x000000755961 bp 0x7ffe38d0c080 sp 0x7ffe38d0c078
... | Heap buffer overflow in acc_ua_get_be32() | https://api.github.com/repos/upx/upx/issues/391/comments | 1 | 2020-07-23T08:13:04Z | 2020-08-06T06:29:39Z | https://github.com/upx/upx/issues/391 | 664,283,181 | 391 | 4,048 |
CVE-2020-27800 | 2022-08-25T20:15:08.677 | A heap-based buffer over-read was discovered in the get_le32 function in bele.h in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/395"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/upx/upx/issues/395 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit of the devel branch
ASAN reports:
```
==5614==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x624000007da0 at pc 0x000000757233 bp 0x7ffe125eb8e0 sp 0x7ffe125eb8d8
REA... | Another heap buffer overflow in get_le32() | https://api.github.com/repos/upx/upx/issues/395/comments | 1 | 2020-07-24T08:10:02Z | 2020-08-06T06:30:04Z | https://github.com/upx/upx/issues/395 | 664,994,296 | 395 | 4,049 |
CVE-2020-27801 | 2022-08-25T20:15:08.727 | A heap-based buffer over-read was discovered in the get_le64 function in bele.h in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/394"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/upx/upx/issues/394 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit of the devel branch
ASAN reports:
```
==4525==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x7fab6ae5cdd8 at pc 0x000000757297 bp 0x7fff2d255a60 sp 0x7fff2d255a58
REA... | Heap buffer overflow in get_le64() | https://api.github.com/repos/upx/upx/issues/394/comments | 1 | 2020-07-24T06:42:22Z | 2020-08-06T06:29:58Z | https://github.com/upx/upx/issues/394 | 664,953,164 | 394 | 4,050 |
CVE-2020-27802 | 2022-08-25T20:15:08.777 | An floating point exception was discovered in the elf_lookup function in p_lx_elf.cpp in UPX 4.0.0 via a crafted Mach-O file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/upx/upx/issues/393"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"369"
] | 369 | https://github.com/upx/upx/issues/393 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
Floating point exception was found in PackLinuxElf32::elf_lookup of p_lx_elf.cpp (the latest commit of the devel branch)
through debugging,because of div 0
```
────────────────────────────────────────────────────────────[ DISA... | Floating point exception in PackLinuxElf32::elf_lookup | https://api.github.com/repos/upx/upx/issues/393/comments | 1 | 2020-07-23T09:02:02Z | 2020-08-06T06:29:52Z | https://github.com/upx/upx/issues/393 | 664,311,420 | 393 | 4,051 |
CVE-2022-36168 | 2022-08-26T00:15:09.237 | A directory traversal vulnerability was discovered in Wuzhicms 4.1.0. via /coreframe/app/attachment/admin/index.php: | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.7,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cigar-Fasion/CVE/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/Cigar-Fasion/CVE/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cigar-Fasion",
"CVE"
] | A directory traversal vulnerability was discovered in WUZHI CMS 4.1.0.
Directory traversal allows authenticated remote attackers to list files in any directory.
Vulnerability in /coreframe/app/attachment/admin/index.php:
```
public function dir()
{
$dir = isset($GLOBALS['dir']) && trim($GLOBALS['d... | Wuzhicms v4.1.0 /coreframe/app/attachment/admin/index.php hava a directory traversal Vulnerability | https://api.github.com/repos/f4s1on/CVE/issues/1/comments | 0 | 2022-07-12T03:17:32Z | 2022-07-12T03:17:32Z | https://github.com/f4s1on/CVE/issues/1 | 1,301,479,795 | 1 | 4,052 |
CVE-2022-36168 | 2022-08-26T00:15:09.237 | A directory traversal vulnerability was discovered in Wuzhicms 4.1.0. via /coreframe/app/attachment/admin/index.php: | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 2.7,
"baseSeverity": "LOW",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cigar-Fasion/CVE/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/wuzhicms/wuzhicms/issues/202 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A directory traversal vulnerability was discovered in WUZHI CMS 4.1.0.
Directory traversal allows authenticated remote attackers to list files in any directory.
Vulnerability in /coreframe/app/attachment/admin/index.php:
```
public function dir()
{
$dir = isset($GLOBALS['dir']) && trim($GLOBALS['d... | Wuzhicms v4.1.0 /coreframe/app/attachment/admin/index.php hava a directory traversal Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/202/comments | 1 | 2022-07-12T03:28:46Z | 2023-01-08T02:20:43Z | https://github.com/wuzhicms/wuzhicms/issues/202 | 1,301,485,949 | 202 | 4,053 |
CVE-2021-39393 | 2022-08-26T13:15:08.300 | mm-wiki v0.2.1 was discovered to contain a cross-site scripting (XSS) vulnerability via the markdown editor. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/phachon/mm-wiki/issues/315"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mm-wiki_project:mm-wiki:0.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "B14C3277-7618-436B-B961-C0A2673B87CC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/phachon/mm-wiki/issues/315 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"phachon",
"mm-wiki"
] | xxxxxHere is the problem descriptionxxxx
1. The version number in use
vx0.2.1
2. Whether the version has been upgraded to the new version
yes
3. Current problems encountered:
The markdown editor exist a XSS
4. Error logs or screenshots
Insert the XSS-payload into it
 which allows attackers to arbitrarily add user accounts and modify user information. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phachon/mm-wiki/issues/316"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mm-wiki_project:mm-wiki:0.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "B14C3277-7618-436B-B961-C0A2673B87CC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"352"
] | 352 | https://github.com/phachon/mm-wiki/issues/316 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phachon",
"mm-wiki"
] | xxxxxHere is the problem descriptionxxxx
The version number in use
vx0.2.1
Whether the version has been upgraded to the new version
yes
Current problems encountered:
CSRF vulnerabilities
Error logs or screenshots
1. Click to modify personal information and capture it
 and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to ensure it has not already been reported
I have verified that I am using the latest ... | AddressSanitizer report LeakSanitizer: detected memory leaks when executing convert command | https://api.github.com/repos/ImageMagick/ImageMagick/issues/3540/comments | 11 | 2021-04-13T14:50:19Z | 2022-11-30T17:19:10Z | https://github.com/ImageMagick/ImageMagick/issues/3540 | 857,040,605 | 3,540 | 4,058 |
CVE-2022-38794 | 2022-08-27T21:15:08.890 | Zaver through 2020-12-15 allows directory traversal via the GET /.. substring. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zyearn/zaver/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zaver_project:zaver:*:*:*:*:*:*:*:*",
"matchCriteriaId": "33AAE9C2-8D4D-4DCB-A971-79C8C4B29291",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-15",
"versionSta... | [
"22"
] | 22 | https://github.com/zyearn/zaver/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zyearn",
"zaver"
] | Directory traversal.
Hackers can gain access to a wealth of sensitive information including configuration files.

For example, here I can read my `.bashrc` and `zaver.conf`
 vulnerability in Pagekit CMS v1.0.18 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Markdown text box under /blog/post/edit. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pagekit/pagekit/issues/968"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pagekit:pagekit:1.0.18:*:*:*:*:*:*:*",
"matchCriteriaId": "A1E39691-604C-42A3-BA30-80433E0E09EA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/pagekit/pagekit/issues/968 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pagekit",
"pagekit"
] |
## Problem
An attacker can insert a constructed statement into the article. When a user visits this page, it will trigger (XSS) cross site scripting attack

## EXP
<svg/onrandom=random onload=confirm... | There is an XSS vulnerability in the place where the article is edited | https://api.github.com/repos/pagekit/pagekit/issues/968/comments | 1 | 2022-07-20T14:19:05Z | 2022-07-20T14:19:55Z | https://github.com/pagekit/pagekit/issues/968 | 1,311,207,979 | 968 | 4,060 |
CVE-2022-0284 | 2022-08-29T15:15:09.183 | A heap-based-buffer-over-read flaw was found in ImageMagick's GetPixelAlpha() function of 'pixel-accessor.h'. This vulnerability is triggered when an attacker passes a specially crafted Tagged Image File Format (TIFF) image to convert it into a PICON file format. This issue can potentially lead to a denial of service a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-0284"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "90A073A6-900F-44EE-B29F-05CB65058078",
"versionEndExcluding": "7.1.0-20",
"versionEndIncluding": null,
"versionS... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/4729 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-20
### Operating system
Linux
### Operating system, version and so on
Linux ubuntu 5.4.0-73-generic #82~18.04.1-Ubuntu SMP Fri Apr 16 15:10:02 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
### Description
Hi, ImageMagick security team
This is ZhangJiaxing (@r0fm1a) from Codesafe Team of ... | Heap Buffer Overflow | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4729/comments | 4 | 2022-01-19T07:07:49Z | 2022-02-19T13:35:53Z | https://github.com/ImageMagick/ImageMagick/issues/4729 | 1,107,736,894 | 4,729 | 4,061 |
CVE-2022-0367 | 2022-08-29T15:15:09.370 | A heap-based buffer overflow flaw was found in libmodbus in function modbus_reply() in src/modbus.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2045571"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libmodbus:libmodbus:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4A63A4C-595F-494C-9F53-ED458E91FFE0",
"versionEndExcluding": "3.1.7",
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/stephane/libmodbus/issues/614 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"stephane",
"libmodbus"
] | ## libmodbus version
ebc4f4788678eda8d99e23be87c61a662a9d26b7
## OS and/or distribution
Ubuntu 20.04 focal
## Environment
,AMD EPYC 7742 64-Core @ 16x 2.25GHz
## Description
Heap-based Buffer Overflow in _modbus_receive_msg
## Expected behaviour
no crash.
## Actual behaviour
double free... | Heap-based Buffer Overflow in modbus_reply | https://api.github.com/repos/stephane/libmodbus/issues/614/comments | 14 | 2021-12-22T10:46:59Z | 2023-02-11T02:24:21Z | https://github.com/stephane/libmodbus/issues/614 | 1,086,695,047 | 614 | 4,062 |
CVE-2022-0480 | 2022-08-29T15:15:09.477 | A flaw was found in the filelock_init in fs/locks.c function in the Linux kernel. This issue can lead to host memory exhaustion due to memcg not limiting the number of Portable Operating System Interface (POSIX) file locks. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-0480"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "037A6DFB-B41D-4CC7-86C1-A201809B79C4",
"versionEndExcluding": "5.15",
"versionEndIncluding": null,
"versionStartExclu... | [
"770"
] | 770 | https://github.com/kata-containers/kata-containers/issues/3373 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kata-containers",
"kata-containers"
] | This is Yutian Yang from Zhejiang University. Our team have discovered
a new attack from inside Kata containers, leading to host memory
exhaustion.
The root cause lies in the Linux kernel, even in the latest version.
Briefly speaking, the kernel memcg does not charge posix locks
allocated by user processes. The... | Host Memory Exhaustion Attack from Inside Kata Containers | https://api.github.com/repos/kata-containers/kata-containers/issues/3373/comments | 16 | 2022-01-03T12:33:47Z | 2022-02-03T11:09:36Z | https://github.com/kata-containers/kata-containers/issues/3373 | 1,092,474,299 | 3,373 | 4,063 |
CVE-2022-0496 | 2022-08-29T15:15:09.597 | A vulnerbiility was found in Openscad, where a DXF-format drawing with particular (not necessarily malformed!) properties may cause an out-of-bounds memory access when imported using import(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2050695"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openscad:openscad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B1CAB560-2A16-496D-8216-1EC6B102BB0A",
"versionEndExcluding": "2022-02-04",
"versionEndIncluding": null,
"versionStart... | [
"125"
] | 125 | https://github.com/openscad/openscad/issues/4037 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"openscad",
"openscad"
] | ### Summary
A DXF-format drawing with particular (not necessarily malformed!) properties may cause an out-of-bounds memory access when imported using `import()`.
### Vulnerable versions
* OpenSCAD Linux (commit eedf37059ca9ce81c09b9270c99257c3d7f74c43)
* OpenSCAD Windows x64 (2021.01)
### Steps to reproduce
... | Out-of-bounds memory access in DXF loader (path identification) | https://api.github.com/repos/openscad/openscad/issues/4037/comments | 9 | 2022-01-05T19:57:35Z | 2022-02-05T01:53:54Z | https://github.com/openscad/openscad/issues/4037 | 1,094,696,669 | 4,037 | 4,064 |
CVE-2022-0497 | 2022-08-29T15:15:09.650 | A vulnerbiility was found in Openscad, where a .scad file with no trailing newline could cause an out-of-bounds read during parsing of annotations. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2050699"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openscad:openscad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "715D4AF8-E090-42D2-BE4E-125F287BD9FF",
"versionEndExcluding": "2022-01-09",
"versionEndIncluding": null,
"versionStart... | [
"125"
] | 125 | https://github.com/openscad/openscad/issues/4043 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"openscad",
"openscad"
] | ### Summary
A .scad file with no trailing newline may cause an out-of-bounds read during parsing of annotations.
### Vulnerable versions
* OpenSCAD (commit 374fa5853faeadf48afb55a0e4482f7b14b4f280)
### Steps to reproduce
1. Unzip the [provided proof-of-concept file](https://github.com/openscad/openscad/fil... | Out-of-bounds memory access in comment parser (file without trailing newline) | https://api.github.com/repos/openscad/openscad/issues/4043/comments | 2 | 2022-01-09T17:08:37Z | 2022-02-04T13:50:30Z | https://github.com/openscad/openscad/issues/4043 | 1,097,250,051 | 4,043 | 4,065 |
CVE-2022-1115 | 2022-08-29T15:15:10.297 | A heap-buffer-overflow flaw was found in ImageMagick’s PushShortPixel() function of quantum-private.h file. This vulnerability is triggered when an attacker passes a specially crafted TIFF image file to ImageMagick for conversion, potentially leading to a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-1115"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "62ED872E-70D8-4736-9876-F307A77839D4",
"versionEndExcluding": "6.9.12-44",
"versionEndIncluding": null,
"version... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/4974 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-28
### Operating system
Linux
### Operating system, version and so on
OS: Ubuntu 20.04.3 LTS
Version: ImageMagick 7.1.0-28 Q16-HDRI x86_64 2022-03-04 https://imagemagick.org
Copyright: (C) 1999 ImageMagick Studio LLC
License: https://imagemagick.org/script/license.php ... | heap-buffer-overflow in magick at quantum-private.h PushShortPixel | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4974/comments | 1 | 2022-03-22T02:10:38Z | 2022-03-24T01:28:05Z | https://github.com/ImageMagick/ImageMagick/issues/4974 | 1,176,173,021 | 4,974 | 4,066 |
CVE-2022-25646 | 2022-08-30T05:15:07.607 | All versions of package x-data-spreadsheet are vulnerable to Cross-site Scripting (XSS) due to missing sanitization of values inserted into the cells. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/myliang/x-spreadsheet/issues/580"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:x-data-spreadsheet_project:x-data-spreadsheet:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "EAB5CA5D-367A-4344-8151-1C2C41E9CD2D",
"versionEndExcluding": null,
"versionEndIncluding": null,... | [
"79"
] | 79 | https://github.com/myliang/x-spreadsheet/issues/580 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"myliang",
"x-spreadsheet"
] | xss found
PoC: https://ibb.co/XbdMNVV
Payload: `"><img src=1 onerror=alert(document.domain)>` | xss bug found | https://api.github.com/repos/myliang/x-spreadsheet/issues/580/comments | 1 | 2022-03-18T06:45:03Z | 2022-07-16T01:50:21Z | https://github.com/myliang/x-spreadsheet/issues/580 | 1,173,239,466 | 580 | 4,067 |
CVE-2022-36747 | 2022-08-30T22:15:09.537 | Razor v0.8.0 was discovered to contain a cross-site scripting (XSS) vulnerability via the function uploadchannel(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/enferas/b00038c9add210ab639c13e0729425c9"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cobub:razor:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "685B8616-266E-4588-BB94-748233156F4B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/cobub/razor/issues/176 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cobub",
"razor"
] | Hello,
I would like to report for XSS vulnerability.
In file https://github.com/cobub/razor/blob/2c991aff4a9c83f99e77a03e26056715706f15c0/web/application/controllers/manage/product.php
```php
//line 98
function uploadchannel()
{
$platform = $_POST['platform'];
$channel = $this->channel... | XSS vulnerability | https://api.github.com/repos/cobub/razor/issues/176/comments | 1 | 2022-07-18T16:02:27Z | 2022-09-13T17:53:35Z | https://github.com/cobub/razor/issues/176 | 1,308,172,462 | 176 | 4,068 |
CVE-2022-36748 | 2022-08-30T22:15:09.583 | PicUploader v2.6.3 was discovered to contain a cross-site scripting (XSS) vulnerability via the component /master/index.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xiebruce/PicUploader/issues/80"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:picuploader_project:picuploader:2.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "9FBB4CBD-45D3-4117-8510-4048A5E321B7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/xiebruce/PicUploader/issues/80 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xiebruce",
"PicUploader"
] | Hello,
I would like to report for possible XSS vulnerability.
In file https://github.com/xiebruce/PicUploader/blob/master/index.php
```php
$data = [
'code' => 'success',
'data' => [
'filename' => $_FILES['file']['name'],
'url' => $isWeb ? $link['formatLink'] : $link,
//专用于web上传,其它客户端上... | XX vulnerability in index.php | https://api.github.com/repos/xiebruce/PicUploader/issues/80/comments | 9 | 2022-07-22T20:45:18Z | 2023-06-25T13:45:44Z | https://github.com/xiebruce/PicUploader/issues/80 | 1,315,403,588 | 80 | 4,069 |
CVE-2022-36749 | 2022-08-30T22:15:09.630 | RPi-Jukebox-RFID v2.3.0 was discovered to contain a command injection vulnerability via the component /htdocs/utils/Files.php. This vulnerability is exploited via a crafted payload injected into the file name of an uploaded file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MiczFlor/RPi-Jukebox-RFID/issues/1859"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sourcefabric:rpi-jukebox-rfid:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D564CC8A-AFE5-48C3-910C-08BDEF93FBEA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"78"
] | 78 | https://github.com/MiczFlor/RPi-Jukebox-RFID/issues/1859 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"MiczFlor",
"RPi-Jukebox-RFID"
] | Hello,
I would like to report for possible vulnerability.
In file https://github.com/MiczFlor/RPi-Jukebox-RFID/blob/develop/htdocs/trackEdit.php
```php
//line 136
if(isset($_GET['folder']) && $_GET['folder'] != "") {
$post['folder'] = $_GET['folder'];
} else {
if(isset($_POST['folder']) && $_POST... | 🐛 | Command Injection and XSS vulnerabilities reports | https://api.github.com/repos/MiczFlor/RPi-Jukebox-RFID/issues/1859/comments | 4 | 2022-07-18T14:10:45Z | 2024-09-15T09:50:33Z | https://github.com/MiczFlor/RPi-Jukebox-RFID/issues/1859 | 1,308,022,012 | 1,859 | 4,070 |
CVE-2020-35538 | 2022-08-31T16:15:09.040 | A crafted input file could cause a null pointer dereference in jcopy_sample_rows() when processed by libjpeg-turbo. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libjpeg-turbo/libjpeg-turbo/commit/9120a247436e84c0b4eea828cb11e8f665fcde30"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg-turbo:libjpeg-turbo:2.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "5130BD31-63BD-48B0-9B1C-E01B3484FD05",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"476"
] | 476 | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/441 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libjpeg-turbo",
"libjpeg-turbo"
] | **Have you searched the existing issues (both open and closed) in the libjpeg-turbo issue tracker to ensure that this bug report is not a duplicate?**
Yes
**Does this bug report describe one of the [two known and unsolvable issues with the JPEG format](https://libjpeg-turbo.org/pmwiki/uploads/About/TwoIssueswiththe... | jcopy_sample_rows() causes SIGSEGV | https://api.github.com/repos/libjpeg-turbo/libjpeg-turbo/issues/441/comments | 4 | 2020-07-06T07:45:09Z | 2021-12-23T16:23:45Z | https://github.com/libjpeg-turbo/libjpeg-turbo/issues/441 | 651,322,599 | 441 | 4,071 |
CVE-2022-1325 | 2022-08-31T16:15:09.467 | A flaw was found in Clmg, where with the help of a maliciously crafted pandore or bmp file with modified dx and dy header field values it is possible to trick the application into allocating huge buffer sizes like 64 Gigabyte upon reading the file from disk or from a virtual buffer. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Broken Link"
],
"url": "https://access.redhat.com/security/cve/CVE-2022-1325"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cimg:cimg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5BC6B9AC-0442-4A13-BE55-DC1B28A0700B",
"versionEndExcluding": "3.1.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"770"
] | 770 | https://github.com/GreycLab/CImg/issues/343 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GreycLab",
"CImg"
] | # Description
Via a maliciously crafted pandore or bmp file with modified dx and dy header field values it is possible to trick the application into allocating huge buffer sizes like 64 Gigabyte upon reading the file from disk or from a virtual buffer.
# Version
This does affect the newest Version of Cimg which i... | Denial of service via RAM exhaustion in _load_bmp | https://api.github.com/repos/GreycLab/CImg/issues/343/comments | 18 | 2022-04-02T13:56:36Z | 2022-09-27T09:01:50Z | https://github.com/GreycLab/CImg/issues/343 | 1,190,640,729 | 343 | 4,072 |
CVE-2022-2466 | 2022-08-31T16:15:10.943 | It was found that Quarkus 2.10.x does not terminate HTTP requests header context which may lead to unpredictable behavior. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/quarkusio/quarkus/issues/26748"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:quarkus:quarkus:*:*:*:*:*:*:*:*",
"matchCriteriaId": "10673B6C-4242-4C0A-9CC2-888ACF185D66",
"versionEndExcluding": "2.10.4",
"versionEndIncluding": null,
"versionStartExclud... | [
"444"
] | 444 | https://github.com/quarkusio/quarkus/issues/26748 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"quarkusio",
"quarkus"
] |
### Describe the bug
~~Upgrading from Quarkus 2.9.x to 2.10.x whenever i try to access `RoutingContext` request from a bean i get always the headers of the first request that have been made to the app.~~
~~This happens on both @GraphQLApi endpoints and event in any CDI bean that consumes `RoutingContext` or `Ht... | CVE-2022-2466 - Request Context not terminated with GraphQL | https://api.github.com/repos/quarkusio/quarkus/issues/26748/comments | 28 | 2022-07-15T07:32:30Z | 2022-07-26T14:51:35Z | https://github.com/quarkusio/quarkus/issues/26748 | 1,305,687,135 | 26,748 | 4,073 |
CVE-2022-36566 | 2022-08-31T18:15:08.607 | Rengine v1.3.0 was discovered to contain a command injection vulnerability via the scan engine function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zongdeiqianxing/rengine/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yogeshojha:rengine:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7EC7544-DE01-459C-AAEE-BA6815D98AFB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"78"
] | 78 | https://github.com/zongdeiqianxing/rengine/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zongdeiqianxing",
"rengine"
] | https://github.com/yogeshojha/rengine
The rce vulnerability is caused by the code reading the value from the yaml file and splicing it directly into the os.system statement.
[ github permark](https://github.com/yogeshojha/rengine/blob/67ca0a4350c4fb4b3d9a25c01db7024e170ff12a/web/reNgine/tasks.py#L1692-L1708)
!... | There is an OS Command Injection vulnerability in the scan engine function configuration of rengine 1.3.0 | https://api.github.com/repos/zongdeiqianxing/rengine/issues/2/comments | 0 | 2022-07-19T03:10:43Z | 2022-07-19T03:22:33Z | https://github.com/zongdeiqianxing/rengine/issues/2 | 1,308,916,097 | 2 | 4,074 |
CVE-2020-35530 | 2022-09-01T18:15:08.770 | In LibRaw, there is an out-of-bounds write vulnerability within the "new_node()" function (libraw\src\x3f\x3f_utils_patched.cpp) that can be triggered via a crafted X3F file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/11c4db253ef2c9bb44247b578f5caa57c66a1eeb"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E00F0C8F-11AC-42B2-8D85-27028B41EBF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/LibRaw/LibRaw/issues/272 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description**
There is an out-of-bounds write vulnerability within the "new_node()" function (libraw\src\x3f\x3f_utils_patched.cpp).
**Steps to Reproduce**
poc (password: 0xfoxone):
https://drive.google.com/open?id=1SGItp-hBZXEgrPErI6URiRkqUOT5J9In
cmd:
magick.exe convert poc.X3F new.png
Upon running... | Libraw "new_node()" Out-of-bounds Write Vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/272/comments | 1 | 2020-04-03T17:35:32Z | 2020-06-15T14:40:35Z | https://github.com/LibRaw/LibRaw/issues/272 | 593,536,465 | 272 | 4,075 |
CVE-2020-35531 | 2022-09-01T18:15:08.820 | In LibRaw, an out-of-bounds read vulnerability exists within the get_huffman_diff() function (libraw\src\x3f\x3f_utils_patched.cpp) when reading data from an image file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/d75af00681a74dcc8b929207eb895611a6eceb68"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E00F0C8F-11AC-42B2-8D85-27028B41EBF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/LibRaw/LibRaw/issues/270 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description**
An out-of-bounds read vulnerability exists within the "get_huffman_diff()" function (libraw\src\x3f\x3f_utils_patched.cpp) when parsing a crafted X3F file.
**Steps to Reproduce**
(poc archive password= girlelecta):
https://drive.google.com/file/d/1Yhqo6idPqWMisvPKrlzjsUKRApHmz2M_/view
cmd:
... | LibRaw "get_huffman_diff()" Out-of-bounds read vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/270/comments | 4 | 2020-04-02T12:03:57Z | 2020-06-17T13:12:10Z | https://github.com/LibRaw/LibRaw/issues/270 | 592,578,946 | 270 | 4,076 |
CVE-2020-35532 | 2022-09-01T18:15:08.870 | In LibRaw, an out-of-bounds read vulnerability exists within the "simple_decode_row()" function (libraw\src\x3f\x3f_utils_patched.cpp) which can be triggered via an image with a large row_stride field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/5ab45b085898e379fedc6b113e2e82a890602b1e"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E00F0C8F-11AC-42B2-8D85-27028B41EBF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/LibRaw/LibRaw/issues/271 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description**
An out-of-bounds read vulnerability exists within the "simple_decode_row()" function (libraw\src\x3f\x3f_utils_patched.cpp) which can be triggered via an image with a large "row_stride" field.
**Steps to Reproduce**
(poc archive password= girlelecta):
https://drive.google.com/file/d/12pjib7aED... | LibRaw "simple_decode_row()" Out-of-bounds read vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/271/comments | 3 | 2020-04-02T12:14:58Z | 2020-06-17T12:49:47Z | https://github.com/LibRaw/LibRaw/issues/271 | 592,585,243 | 271 | 4,077 |
CVE-2020-35533 | 2022-09-01T18:15:08.920 | In LibRaw, an out-of-bounds read vulnerability exists within the "LibRaw::adobe_copy_pixel()" function (libraw\src\decoders\dng.cpp) when reading data from the image file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/a6937d4046a7c4742b683a04c8564605fd9be4fb"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E00F0C8F-11AC-42B2-8D85-27028B41EBF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/LibRaw/LibRaw/issues/273 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description**
An out-of-bounds read vulnerability exists within the "LibRaw::adobe_copy_pixel()" function (libraw\src\decoders\dng.cpp) when parsing a crafted DNG file.
**Steps to Reproduce**
(poc archive password= girlelecta):
https://drive.google.com/file/d/1kDMhDwfxoZBa31_vrsA2TfQI45FG8NRW/view
cmd:
... | "LibRaw::adobe_copy_pixel()" Out-of-bounds read vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/273/comments | 2 | 2020-04-08T15:45:46Z | 2020-06-15T15:00:04Z | https://github.com/LibRaw/LibRaw/issues/273 | 596,678,080 | 273 | 4,078 |
CVE-2020-35534 | 2022-09-01T18:15:08.970 | In LibRaw, there is a memory corruption vulnerability within the "crxFreeSubbandData()" function (libraw\src\decoders\crx.cpp) when processing cr3 files. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/e41f331e90b383e3208cefb74e006df44bf3a4b8"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E00F0C8F-11AC-42B2-8D85-27028B41EBF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"770"
] | 770 | https://github.com/LibRaw/LibRaw/issues/279 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description:**
There is a memory corruption vulnerability within the "crxFreeSubbandData()" function (libraw\src\decoders\crx.cpp) when processing cr3 files.
**Steps to Reproduce:**
poc (password: 0xfoxone):
https://drive.google.com/open?id=10pjqVx6mItzmvovgqF-8IHi3jnnKQ6fD
cmd:
magick.exe convert poc.c... | Libraw "crxFreeSubbandData()" Memory Corruption Vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/279/comments | 1 | 2020-04-26T13:13:45Z | 2020-04-26T15:50:32Z | https://github.com/LibRaw/LibRaw/issues/279 | 607,009,739 | 279 | 4,079 |
CVE-2020-35535 | 2022-09-01T18:15:09.027 | In LibRaw, there is an out-of-bounds read vulnerability within the "LibRaw::parseSonySRF()" function (libraw\src\metadata\sony.cpp) when processing srf files. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/commit/c243f4539233053466c1309bde606815351bee81"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:0.20.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E00F0C8F-11AC-42B2-8D85-27028B41EBF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/LibRaw/LibRaw/issues/283 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description:**
There is an out-of-bounds read vulnerability within the "LibRaw::parseSonySRF()" function (libraw\src\metadata\sony.cpp) when processing srf files.
**Steps to Reproduce:**
poc (password: 0xfoxone):
https://drive.google.com/open?id=1r0wig5pSGUFhP3mDycIUcKMvnHamYaGJ
cmd:
magick.exe convert ... | Libraw "LibRaw::parseSonySRF()" Out-of-bounds Read Vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/283/comments | 1 | 2020-05-10T17:30:28Z | 2020-05-10T18:24:18Z | https://github.com/LibRaw/LibRaw/issues/283 | 615,438,367 | 283 | 4,080 |
CVE-2022-39170 | 2022-09-02T03:15:07.527 | libdwarf 0.4.1 has a double free in _dwarf_exec_frame_instr in dwarf_frame.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/davea42/libdwarf-code/commit/60303eb80ecc7747bf29776d545e2a5c5a76f6f8"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libdwarf_project:libdwarf:0.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DE7E818D-510D-47B1-8DB9-299F4344D6D8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"415"
] | 415 | https://github.com/davea42/libdwarf-code/issues/132 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"davea42",
"libdwarf-code"
] | Hello, I was testing my fuzzer and found a double free in dwarfdump, _dwarf_exec_frame_instr bug. A double free will be triggered when parsing a crafted file, when running ./dwarfdump -vv -a $POC, as shown in the attachment
## Environment
Ubuntu 22.04
gcc 11.2.0
libdwarf latest commit 271cc04a1bdd1f47d641ab9219fb... | [BUG] double free in _dwarf_exec_frame_instr | https://api.github.com/repos/davea42/libdwarf-code/issues/132/comments | 1 | 2022-08-27T08:23:55Z | 2022-08-29T22:20:39Z | https://github.com/davea42/libdwarf-code/issues/132 | 1,352,982,801 | 132 | 4,081 |
CVE-2022-36593 | 2022-09-02T04:15:11.267 | kkFileView v4.0.0 was discovered to contain an arbitrary file deletion vulnerability via the fileName parameter at /controller/FileController.java. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kekingcn/kkFileView/issues/370"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:keking:kkfileview:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "14029A50-34F9-451F-800A-5A21EE2822A0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/kekingcn/kkFileView/issues/370 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kekingcn",
"kkFileView"
] | 问题描述Description
kkFileview v4.0.0存在任意文件删除漏洞,可能导致系统任意文件被删除。
kkFileview v4.0.0 has an arbitrary file deletion vulnerability, which may lead to arbitrary file being deleted.
漏洞位置vulerable code location
src/main/java/cn/keking/web/controller/FileController.java文件78行,fileName参数用户可控,由于只截取"/"后面的内容作为文件名,导致可以利用“..\"... | kkFileView arbitrary file deletion vulnerability | https://api.github.com/repos/kekingcn/kkFileView/issues/370/comments | 2 | 2022-07-20T05:59:04Z | 2022-07-25T10:33:59Z | https://github.com/kekingcn/kkFileView/issues/370 | 1,310,483,184 | 370 | 4,082 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.