cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-33034 | 2022-06-23T17:15:14.270 | LibreDWG v0.12.4.4608 was discovered to contain a stack overflow via the function copy_bytes at decode_r2007.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/494"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.4.4608:*:*:*:*:*:*:*",
"matchCriteriaId": "205AD0A5-0F64-4F38-A208-B41F8C1E8952",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/494 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==9543==ERROR: AddressSanitizer: stack-buffer-overflow on address 0x7fffffffc8f0 at pc 0x00000072... | stack-buffer-overflow exists in the function copy_bytes in decode_r2007.c | https://api.github.com/repos/LibreDWG/libredwg/issues/494/comments | 3 | 2022-06-08T01:51:23Z | 2022-12-15T08:47:23Z | https://github.com/LibreDWG/libredwg/issues/494 | 1,264,082,849 | 494 | 3,782 |
CVE-2022-33068 | 2022-06-23T17:15:14.350 | An integer overflow in the component hb-ot-shape-fallback.cc of Harfbuzz v4.3.0 allows attackers to cause a Denial of Service (DoS) via unspecified vectors. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/harfbuzz/harfbuzz/commit/62e803b36173fd096d7ad460dd1d1db9be542593"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:harfbuzz_project:harfbuzz:4.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "4A67E5B9-F189-4A12-9BA2-D9135C21AD24",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"190"
] | 190 | https://github.com/harfbuzz/harfbuzz/issues/3557 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"harfbuzz",
"harfbuzz"
] | ##### **Describe the bug**
UndefinedBehaviorSanitizer: signed integer overflow in hb-ot-shape-fallback.cc
##### **To Reproduce**
Built harfbuzz-shape-fuzzer using clang-10 according to [the oss-fuzz script](https://github.com/google/oss-fuzz/blob/master/projects/harfbuzz/build.sh) with `CXXFLAGS='-O1 -fsanitize=... | UndefinedBehaviorSanitizer: signed integer overflow | https://api.github.com/repos/harfbuzz/harfbuzz/issues/3557/comments | 0 | 2022-04-29T15:03:57Z | 2022-06-01T13:40:26Z | https://github.com/harfbuzz/harfbuzz/issues/3557 | 1,221,037,217 | 3,557 | 3,783 |
CVE-2022-33069 | 2022-06-23T17:15:14.390 | Ethereum Solidity v0.8.14 contains an assertion failure via SMTEncoder::indexOrMemberAssignment() at SMTEncoder.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ethereum/solidity/issues/12973"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trackin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:soliditylang:solidity:0.8.13:*:*:*:*:*:*:*",
"matchCriteriaId": "2404611E-1F7A-4574-A34B-D4BA13B45B19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"617"
] | 617 | https://github.com/ethereum/solidity/issues/12973 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ethereum",
"solidity"
] | ##### **Describe the bug**
The attached testcase crashes the solidity compiler solc with an InternalCompilerError: Solidity assertion failed in in solidity::frontend::SMTEncoder::indexOrMemberAssignment
https://github.com/ethereum/solidity/blob/b35cda5998ac7bc28a58f23480f2f82a440d6fa2/libsolidity/formal/SMTEncoder.... | [SMTChecker] ICE in `SMTEncoder::indexOrMemberAssignment()` with public state variable with invalid double initialization | https://api.github.com/repos/ethereum/solidity/issues/12973/comments | 2 | 2022-04-29T16:12:49Z | 2022-11-29T10:58:37Z | https://github.com/ethereum/solidity/issues/12973 | 1,221,177,514 | 12,973 | 3,784 |
CVE-2022-33113 | 2022-06-23T17:15:14.793 | Jfinal CMS v5.1.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the keyword text field under the publish blog module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/39"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/jflyfox/jfinal_cms/issues/39 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | There is a stored XSS vulnerability in JFinal_cms 's publish blog module. An attacker can insert malicious XSS code into the keyword field. When the user views the content of the article in the foreground, the malicious XSS code is triggered successfully.
payload: `" onmouseover="alert(document.cookie)`
<img widt... | XSS vulnerability stored in the publish blog module of Jfinal_cms V5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/39/comments | 1 | 2022-06-10T14:54:45Z | 2022-07-11T10:09:49Z | https://github.com/jflyfox/jfinal_cms/issues/39 | 1,267,664,722 | 39 | 3,785 |
CVE-2022-33114 | 2022-06-23T17:15:14.833 | Jfinal CMS v5.1.0 was discovered to contain a SQL injection vulnerability via the attrVal parameter at /jfinal_cms/system/dict/list. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/38"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jflyfox/jfinal_cms/issues/38 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | # Vulnerability Analysis
The vulnerability appears in lines 23-28 of the **com.jflyfox.system.dict.DictController.java**
<img width="951" alt="image-20220610104610536" src="https://user-images.githubusercontent.com/30547070/172980296-78159fe2-2e0d-4e2c-aae3-cf1bd3095253.png">
<img width="1079" alt="image-2022061... | SQL injection vulnerability exists in JFinal CMS 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/38/comments | 0 | 2022-06-10T02:49:09Z | 2022-06-14T20:59:46Z | https://github.com/jflyfox/jfinal_cms/issues/38 | 1,266,938,033 | 38 | 3,786 |
CVE-2022-34299 | 2022-06-23T17:15:18.410 | There is a heap-based buffer over-read in libdwarf 0.4.0. This issue is related to dwarf_global_formref_b. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/davea42/libdwarf-code/commit/7ef09e1fc9ba07653dd078edb2408631c7969162"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libdwarf_project:libdwarf:0.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "448D8623-0083-42B9-A9D1-60A5BF2F6DE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"125"
] | 125 | https://github.com/davea42/libdwarf-code/issues/119 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"davea42",
"libdwarf-code"
] |
asan output:
```
=================================================================
==3946410==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61b000000697 at pc 0x0000005d9f2d bp 0x7fffffff94f0 sp 0x7fffffff94e8
READ of size 8 at 0x61b000000697 thread T0
#0 0x5d9f2c in dwarf_global_formref_b /libd... | heap overflow in dwarf_global_formref_b | https://api.github.com/repos/davea42/libdwarf-code/issues/119/comments | 1 | 2022-06-15T12:36:15Z | 2022-06-16T00:08:41Z | https://github.com/davea42/libdwarf-code/issues/119 | 1,272,170,737 | 119 | 3,787 |
CVE-2022-34300 | 2022-06-23T17:15:18.460 | In tinyexr 1.0.1, there is a heap-based buffer over-read in tinyexr::DecodePixelData. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/syoyo/tinyexr/issues/167"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyexr_project:tinyexr:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C2BE6DA6-577F-4392-9F51-7BB9A0782440",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"125"
] | 125 | https://github.com/syoyo/tinyexr/issues/167 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"syoyo",
"tinyexr"
] | ## desc
There is a heap based buffer overflow in tinyexr::DecodePixelData before 20220506 that could cause remote code execution depending on the usage of this program.
## asan output
```
==2363537==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x629000009210 at pc 0x000000563bd4 bp 0x7fffffffc4b0 sp 0... | heap overflow in tinyexr::DecodePixelData | https://api.github.com/repos/syoyo/tinyexr/issues/167/comments | 8 | 2022-06-14T16:06:34Z | 2022-06-28T10:56:54Z | https://github.com/syoyo/tinyexr/issues/167 | 1,271,032,557 | 167 | 3,788 |
CVE-2022-33121 | 2022-06-24T21:15:08.357 | A Cross-Site Request Forgery (CSRF) in MiniCMS v1.11 allows attackers to arbitrarily delete local .dat files via clicking on a malicious link. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bg5sbk/MiniCMS/issues/45"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:1234n:minicms:1.11:*:*:*:*:*:*:*",
"matchCriteriaId": "EFF126BA-FB8A-4D2A-8B51-D19BF0F8C301",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"352"
] | 352 | https://github.com/bg5sbk/MiniCMS/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bg5sbk",
"MiniCMS"
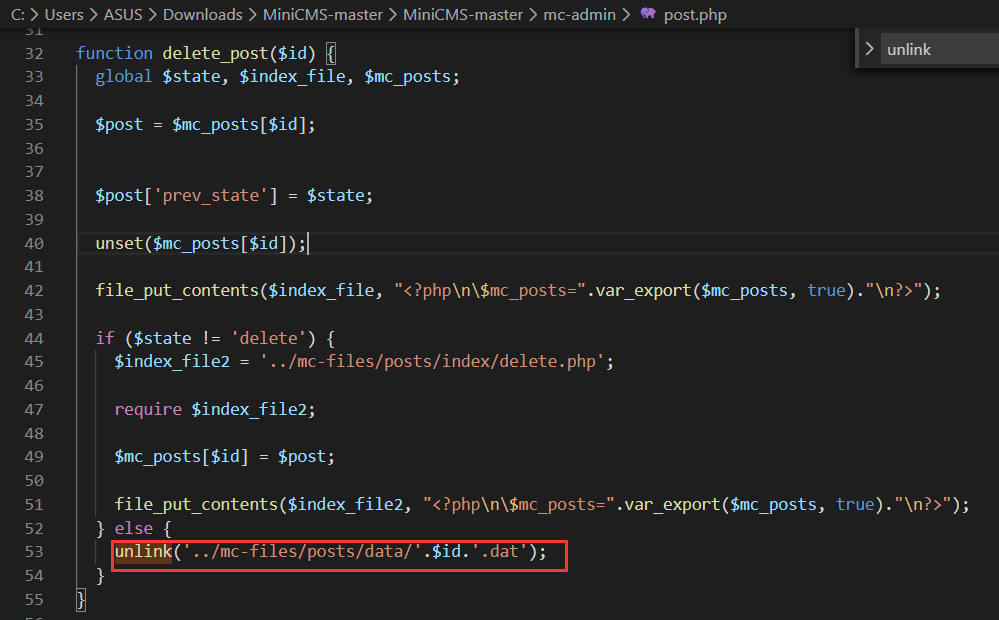
] | Software Link : https://github.com/bg5sbk/MiniCMS After the installation is complete, log in as administrator, open the page
In post.php, user can delete any local .dat files without filter
[](https://imgtu.com/i/XgVxl6)
Create 1.dat in the parent directo... | There is CSRF vulnerabilities that can lead to deleting local .dat files | https://api.github.com/repos/bg5sbk/MiniCMS/issues/45/comments | 3 | 2022-06-11T12:37:22Z | 2024-09-06T05:43:24Z | https://github.com/bg5sbk/MiniCMS/issues/45 | 1,268,263,919 | 45 | 3,789 |
CVE-2021-40941 | 2022-06-27T18:15:08.803 | In Bento4 1.6.0-638, there is an allocator is out of memory in the function AP4_Array<AP4_TrunAtom::Entry>::EnsureCapacity in Ap4Array.h:172, as demonstrated by GPAC. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/644"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-638:*:*:*:*:*:*:*",
"matchCriteriaId": "2122DA5E-A523-4D07-B017-982DF2B8B829",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/644 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | How to reproduce:
```
1.check out latest code, 5922ba762a
2.compile with asan,
set(CMAKE_C_FLAGS "${CMAKE_C_FLAGS} -fsanitize=address -g")
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -fsanitize=address -g")
3.run ./mp4dump --verbosity 3 --format text poc1
```
[poc1.zip](https://github.com/axiomatic-sy... | allocator is out of memory in Ap4Array.h:172 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/644/comments | 0 | 2021-08-25T02:03:31Z | 2021-09-08T02:36:45Z | https://github.com/axiomatic-systems/Bento4/issues/644 | 978,628,921 | 644 | 3,790 |
CVE-2021-40942 | 2022-06-27T21:15:07.900 | In GPAC MP4Box v1.1.0, there is a heap-buffer-overflow in the function filter_parse_dyn_args function in filter_core/filter.c:1454, as demonstrated by GPAC. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1908"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1908 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | heap-buffer-overflow in MP4Box at filter_core/filter.c:1454 | https://api.github.com/repos/gpac/gpac/issues/1908/comments | 1 | 2021-09-07T10:07:06Z | 2021-09-07T12:49:31Z | https://github.com/gpac/gpac/issues/1908 | 989,818,036 | 1,908 | 3,791 |
CVE-2022-31103 | 2022-06-27T23:15:08.170 | lettersanitizer is a DOM-based HTML email sanitizer for in-browser email rendering. All versions of lettersanitizer below 1.0.2 are affected by a denial of service issue when processing a CSS at-rule `@keyframes`. This package is depended on by [react-letter](https://github.com/mat-sz/react-letter), therefore everyone ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mat-sz/lettersanitizer/commit/96d3dfe2ef0465d47324ed4d13e91ba0816a173f"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lettersanitizer_project:lettersanitizer:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "7996CE4F-0FF7-4D5F-A65D-99A97283CE50",
"versionEndExcluding": "1.0.2",
"versionEndIncluding": null,
... | [
"754"
] | 754 | https://github.com/mat-sz/react-letter/issues/17 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mat-sz",
"react-letter"
] | In production I have issue with this html.
If use dangerouslySetInnerHTML, there is no error, but if use react-letter CPU will hold on 100% and the browser will be unresponded
Please check
[error.zip](https://github.com/mat-sz/react-letter/files/8954131/error.zip)
. | 100% cpu cost and lagging | https://api.github.com/repos/mat-sz/react-letter/issues/17/comments | 14 | 2022-06-22T03:19:11Z | 2025-03-10T19:06:48Z | https://github.com/mat-sz/react-letter/issues/17 | 1,279,434,802 | 17 | 3,792 |
CVE-2022-32994 | 2022-06-27T23:15:08.233 | Halo CMS v1.5.3 was discovered to contain an arbitrary file upload vulnerability via the component /api/admin/attachments/upload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zongdeiqianxing/cve-reports/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "97A6AD19-974E-4BB4-8B49-E88E9B3179B6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"434"
] | 434 | https://github.com/zongdeiqianxing/cve-reports/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zongdeiqianxing",
"cve-reports"
] | https://github.com/halo-dev/halo/
Halo cms v1.5.3 has an arbitrary format file upload vulnerability at /api/admin/attachments/upload. Attackers can upload files in formats such as jsp、html etc.
### Proof of Concept
```
POST /api/admin/attachments/upload HTTP/1.1
Host: 127.0.0.1:8090
Content-Length: 219
Ad... | Halo cms v1.5.3 has an arbitrary format file upload vulnerability at /api/admin/attachments/upload | https://api.github.com/repos/zongdeiqianxing/cve-reports/issues/1/comments | 0 | 2022-06-06T06:43:34Z | 2022-06-06T07:21:21Z | https://github.com/zongdeiqianxing/cve-reports/issues/1 | 1,261,422,307 | 1 | 3,793 |
CVE-2022-32995 | 2022-06-27T23:15:08.273 | Halo CMS v1.5.3 was discovered to contain a Server-Side Request Forgery (SSRF) via the template remote download function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zongdeiqianxing/cve-reports/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "97A6AD19-974E-4BB4-8B49-E88E9B3179B6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"918"
] | 918 | https://github.com/zongdeiqianxing/cve-reports/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zongdeiqianxing",
"cve-reports"
] | https://github.com/halo-dev/halo/
There is an ssrf vulnerability in the template remote download function in halo cms v1.5.3. The attacker needs to enter a link that ends with a zip , such as http://127.0.0.1:40001/1.zip
### Proof of Concept
```
POST /api/admin/themes/fetching?uri=http://127.0.0.1:40000/1.zip... | There is an ssrf vulnerability in the template remote download function in halo cms v1.5.3 in halo-dev/halo | https://api.github.com/repos/zongdeiqianxing/cve-reports/issues/2/comments | 0 | 2022-06-06T07:47:20Z | 2022-06-06T07:47:20Z | https://github.com/zongdeiqianxing/cve-reports/issues/2 | 1,261,479,417 | 2 | 3,794 |
CVE-2022-33009 | 2022-06-27T23:15:08.313 | A stored cross-site scripting (XSS) vulnerability in LightCMS v1.3.11 allows attackers to execute arbitrary web scripts or HTML via uploading a crafted PDF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://lightcms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/eddy8/LightCMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lightcms_project:lightcms:1.3.11:*:*:*:*:*:*:*",
"matchCriteriaId": "839D2756-08AD-46B0-9B7B-694C35D3B6CE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/eddy8/LightCMS/issues/30 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"eddy8",
"LightCMS"
] | A stored cross-site scripting (XSS) vulnerability exists in LightCMS that allows an user authorized to upload a malicious .pdf file which acts as a stored XSS payload. If this stored XSS payload is triggered by an administrator it will trigger a XSS attack.
1. login as admin in the article page
 vulnerability exists in LightCMS "contents" field | https://api.github.com/repos/eddy8/LightCMS/issues/30/comments | 2 | 2022-06-06T16:26:44Z | 2022-06-09T03:57:15Z | https://github.com/eddy8/LightCMS/issues/30 | 1,262,073,812 | 30 | 3,795 |
CVE-2022-34132 | 2022-06-28T00:15:08.313 | Benjamin BALET Jorani v1.0 was discovered to contain a SQL injection vulnerability via the id parameter at application/controllers/Leaves.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/bbalet/jorani/commit/c5c42e29e6a9e59a3c82450bef48b67b8dd48333"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jorani:jorani:1.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CE8B2D2D-7CCC-4688-9C1C-5C2512F140E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/bbalet/jorani/issues/369 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bbalet",
"jorani"
] | Hello,
Several vulnerabilites were found when peeking into Jorani webapp.
An email containing details about those issues was sended.
Best regards,
| Several vulnerabilities | https://api.github.com/repos/bbalet/jorani/issues/369/comments | 2 | 2022-06-05T19:17:08Z | 2022-06-06T19:24:39Z | https://github.com/bbalet/jorani/issues/369 | 1,261,137,598 | 369 | 3,796 |
CVE-2021-40606 | 2022-06-28T13:15:09.740 | The gf_bs_write_data function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1885"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1885 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Bug: Memcpy from unknown addrees in MP4BOX at src/utils/bitstream.c:1028 | https://api.github.com/repos/gpac/gpac/issues/1885/comments | 0 | 2021-08-24T02:45:45Z | 2021-08-30T15:33:43Z | https://github.com/gpac/gpac/issues/1885 | 977,647,480 | 1,885 | 3,797 |
CVE-2021-40607 | 2022-06-28T13:15:09.797 | The schm_box_size function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1879"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"770"
] | 770 | https://github.com/gpac/gpac/issues/1879 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | BUG: heap-buffer-overflow in MP4Box at src/isomedia/schm_box_size:179 | https://api.github.com/repos/gpac/gpac/issues/1879/comments | 0 | 2021-08-19T02:52:37Z | 2021-08-30T15:33:42Z | https://github.com/gpac/gpac/issues/1879 | 974,213,413 | 1,879 | 3,798 |
CVE-2021-40608 | 2022-06-28T13:15:09.840 | The gf_hinter_track_finalize function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1883"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"908"
] | 908 | https://github.com/gpac/gpac/issues/1883 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | BUG : free on unknown addrees in MP4BOX at gf_hinter_track_finalize media_tools/isom_hinter.c:956 | https://api.github.com/repos/gpac/gpac/issues/1883/comments | 0 | 2021-08-20T05:15:45Z | 2021-08-30T15:33:43Z | https://github.com/gpac/gpac/issues/1883 | 975,274,297 | 1,883 | 3,799 |
CVE-2021-40609 | 2022-06-28T13:15:09.880 | The GetHintFormat function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1894"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"770"
] | 770 | https://github.com/gpac/gpac/issues/1894 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] |
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ... | heap-buffer-overflow in MP4BOX at souce file src/isomedia/hint_track.c:46 | https://api.github.com/repos/gpac/gpac/issues/1894/comments | 0 | 2021-08-26T04:44:12Z | 2021-08-30T15:33:44Z | https://github.com/gpac/gpac/issues/1894 | 979,828,664 | 1,894 | 3,800 |
CVE-2021-40943 | 2022-06-28T13:15:09.920 | In Bento4 1.6.0-638, there is a null pointer reference in the function AP4_DescriptorListInspector::Action function in Ap4Descriptor.h:124 , as demonstrated by GPAC. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/643"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-638:*:*:*:*:*:*:*",
"matchCriteriaId": "2122DA5E-A523-4D07-B017-982DF2B8B829",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/643 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | How to reproduce:
```
1.check out latest code, 5922ba762a
2.compile with asan,
set(CMAKE_C_FLAGS "${CMAKE_C_FLAGS} -fsanitize=address -g")
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -fsanitize=address -g")
3.run ./mp4dump --verbosity 3 --format text poc
```
You can see the asan information below:
... | Null pointer reference in Ap4Descriptor.h:124 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/643/comments | 0 | 2021-08-25T02:00:03Z | 2021-08-25T02:00:03Z | https://github.com/axiomatic-systems/Bento4/issues/643 | 978,627,371 | 643 | 3,801 |
CVE-2021-40944 | 2022-06-28T13:15:09.963 | In GPAC MP4Box 1.1.0, there is a Null pointer reference in the function gf_filter_pid_get_packet function in src/filter_core/filter_pid.c:5394, as demonstrated by GPAC. This can cause a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1906"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:-:*:*:*:*:*:*",
"matchCriteriaId": "13133329-701B-4D4B-BA02-F2DF80638668",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1906 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null pointer reference in GPAC at src/filter_core/filter_pid.c:5394 | https://api.github.com/repos/gpac/gpac/issues/1906/comments | 4 | 2021-09-01T07:25:03Z | 2021-09-07T15:18:06Z | https://github.com/gpac/gpac/issues/1906 | 984,803,968 | 1,906 | 3,802 |
CVE-2020-19897 | 2022-06-28T22:15:07.810 | A reflected Cross Site Scripting (XSS) in wuzhicms v4.1.0 allows remote attackers to execute arbitrary web script or HTML via the imgurl parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/183"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/183 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A xss vulnerability was discovered in WUZHI CMS 4.1.0
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the imgurl parameter of /index.php?m=core&f=index&_su=wuzhicms.
POC
ji</textarea> <img/src=1 onerror=alert(document.cookie)>
Vulnerability trigg... | wuzhicms v4.1.0 statcode reflected xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/183/comments | 0 | 2019-08-01T08:29:05Z | 2019-08-01T08:30:33Z | https://github.com/wuzhicms/wuzhicms/issues/183 | 475,546,565 | 183 | 3,803 |
CVE-2022-33021 | 2022-06-29T12:15:07.887 | CVA6 commit 909d85a accesses invalid memory when reading the value of MHPMCOUNTER30. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/884"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"125"
] | 125 | https://github.com/openhwgroup/cva6/issues/884 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Hi,
CVA6 RTL is returning unknown value ("xxxxxxxx") when reading the value of MHPMCOUNTER30. This is happening because the csr reg data (```csr_rdata```) is being read from ``perf_counter_d`` array in the perf_counters.sv module with an array index outside its range. The range of ``perf_counter_d`` is [riscv::CSR_M... | [Bug Report] Out of bound array access | https://api.github.com/repos/openhwgroup/cva6/issues/884/comments | 7 | 2022-05-24T22:43:58Z | 2023-12-13T21:43:08Z | https://github.com/openhwgroup/cva6/issues/884 | 1,247,200,381 | 884 | 3,804 |
CVE-2022-33023 | 2022-06-29T12:15:07.937 | CVA6 commit 909d85a gives incorrect permission to use special multiplication units when the format of instructions is wrong. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/885"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"276"
] | 276 | https://github.com/openhwgroup/cva6/issues/885 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
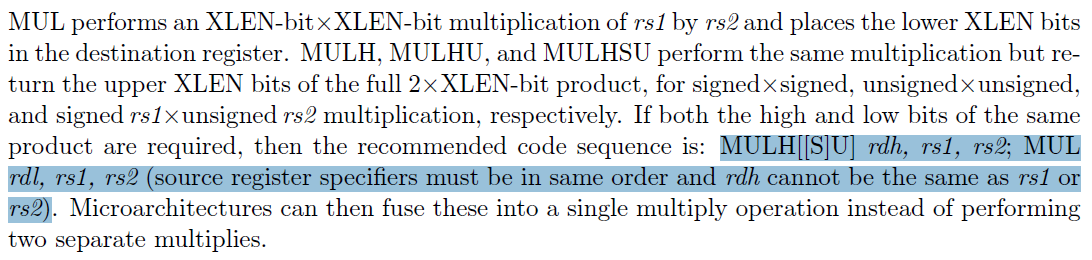
] | Hi,
The RISC-V ISA Volume I, 20190608, page 43 mentions: "MULH[[S]U] rdh, rs1, rs2; MUL
rdl, rs1, rs2 (source register specifiers must be in same order and rdh cannot be the same as rs1 or rs2)"
Our t... | [Bug report] miss illegal instruction exception when rd of MULHU is the same as rs1 or rs2 | https://api.github.com/repos/openhwgroup/cva6/issues/885/comments | 12 | 2022-05-25T00:52:21Z | 2023-11-02T13:49:10Z | https://github.com/openhwgroup/cva6/issues/885 | 1,247,271,466 | 885 | 3,805 |
CVE-2022-33107 | 2022-06-29T12:15:07.983 | ThinkPHP v6.0.12 was discovered to contain a deserialization vulnerability via the component vendor\league\flysystem-cached-adapter\src\Storage\AbstractCache.php. This vulnerability allows attackers to execute arbitrary code via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/top-think/framework/issues/2717"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkphp:thinkphp:6.0.12:*:*:*:*:*:*:*",
"matchCriteriaId": "F3201EB1-17FE-4E3C-86F5-6821F5D17FA8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"502"
] | 502 | https://github.com/top-think/framework/issues/2717 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"top-think",
"framework"
] | # ThinkPHP RCE链子
**Environment installation**
test version:Thinkphp6.0.12
Environment configuration:(tp6只支持用composer安装)
composer create-project topthink/think=6.0.12 tp612
Add deserialization entry point
```php
<?php
namespace app\controller;
use app\BaseController;
use think\facade\Request;
... | ThinkPHP 6.0.12 Unserialize RCE | https://api.github.com/repos/top-think/framework/issues/2717/comments | 18 | 2022-05-24T07:16:25Z | 2024-02-26T09:20:26Z | https://github.com/top-think/framework/issues/2717 | 1,246,093,065 | 2,717 | 3,806 |
CVE-2022-31110 | 2022-06-29T18:15:08.973 | RSSHub is an open source, extensible RSS feed generator. In commits prior to 5c4177441417 passing some special values to the `filter` and `filterout` parameters can cause an abnormally high CPU. This results in an impact on the performance of the servers and RSSHub services which may lead to a denial of service. This i... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/DIYgod/RSSHub/commit/5c4177441417b44a6e45c3c63e9eac2504abeb5b"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rsshub:rsshub:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "9AA9F16E-B0E9-4D3B-8303-B1FD35978982",
"versionEndExcluding": "2022-06-21",
"versionEndIncluding": null,
"versionSta... | [
"1333"
] | 1333 | https://github.com/DIYgod/RSSHub/issues/10045 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"DIYgod",
"RSSHub"
] | **The vulnerability has been fixed (refer to the [security advisory](https://github.com/DIYgod/RSSHub/security/advisories/GHSA-jvxx-v45p-v5vf)).** According to the consultation with @DIYgod, this is a complete disclosure of the vulnerability report, disclosed 120 hours after the fix commit.
[**For a better reading e... | [Vulnerability Report Disclosure: ReDoS] Catastrophic Backtracking in User-supplied Regular Expression | https://api.github.com/repos/DIYgod/RSSHub/issues/10045/comments | 2 | 2022-06-26T18:02:17Z | 2023-11-16T14:28:44Z | https://github.com/DIYgod/RSSHub/issues/10045 | 1,284,990,825 | 10,045 | 3,807 |
CVE-2021-40663 | 2022-06-30T12:15:08.297 | deep.assign npm package 0.0.0-alpha.0 is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution'). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/janbialostok/deep-assign/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.netapp.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:deep.assign_project:deep.assign:0.0.0:alpha0:*:*:*:node.js:*:*",
"matchCriteriaId": "A7CA3464-30FF-4360-901F-888E3B2C9A64",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"1321"
] | 1321 | https://github.com/janbialostok/deep-assign/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"janbialostok",
"deep-assign"
] | ✍️ Description
[deep.assign](https://www.npmjs.com/package/deep.assign) npm package is vulnerable to prototype pollution vulnerability prior to version 0.0.0-alpha.0.
🕵️♂️ Proof of Concept
[LIVE POC LINK](https://runkit.com/embed/hxpxvkppf5x5)
```
var deepAssign = require("deep.assign@0.0.0-alpha.0")
var ob... | Prototype Pollution in deep.assign npm package | https://api.github.com/repos/janbialostok/deep-assign/issues/1/comments | 1 | 2021-09-06T04:52:21Z | 2022-07-02T01:50:42Z | https://github.com/janbialostok/deep-assign/issues/1 | 988,764,102 | 1 | 3,808 |
CVE-2021-37770 | 2022-06-30T15:15:07.947 | Nucleus CMS v3.71 is affected by a file upload vulnerability. In this vulnerability, we can use upload to change the upload path to the path without the Htaccess file. Upload an Htaccess file and write it to AddType application / x-httpd-php.jpg. In this way, an attacker can upload a picture with shell, treat it as PHP... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/NucleusCMS/NucleusCMS/issues/96"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nucleuscms:nucleus_cms:3.71:*:*:*:*:*:*:*",
"matchCriteriaId": "4419BE1B-193F-4EB5-A88B-B20D647D0215",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"434"
] | 434 | https://github.com/NucleusCMS/NucleusCMS/issues/96 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"NucleusCMS",
"NucleusCMS"
] | Description: I found a file upload vulnerability. In this vulnerability, we can use upload to change the upload path to the path without. Htaccess file. Upload an. Htaccess file and write it to AddType application / x-httpd-php.jpg. In this way, we can upload a picture with shell, treat it as PHP, execute our commands,... | File upload vulnerability in Nucleus CMS v3.71 | https://api.github.com/repos/NucleusCMS/NucleusCMS/issues/96/comments | 2 | 2019-12-02T16:20:24Z | 2021-07-26T02:28:29Z | https://github.com/NucleusCMS/NucleusCMS/issues/96 | 531,236,423 | 96 | 3,809 |
CVE-2021-37778 | 2022-06-30T15:15:07.993 | There is a buffer overflow in gps-sdr-sim v1.0 when parsing long command line parameters, which can lead to DoS or code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/osqzss/gps-sdr-sim/issues/294"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gps-sdr-sim_project:gps-sdr-sim:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F330E7D7-76B4-49E0-A661-EF68376EDFC6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"120"
] | 120 | https://github.com/osqzss/gps-sdr-sim/issues/294 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"osqzss",
"gps-sdr-sim"
] | Hi friends!
When the parameter length is greater than 100 characters of MAX_CHAR, the strcpy function overflows. A length check can be performed to fix the problem.
```c
#define MAX_CHAR (100)
char umfile[MAX_CHAR];
char navfile[MAX_CHAR];
char outfile[MAX_CHAR];
```
```c
while ((result=getopt(argc,argv,... | There is a buffer overflow when parsing command line parameters | https://api.github.com/repos/osqzss/gps-sdr-sim/issues/294/comments | 1 | 2021-07-23T13:23:33Z | 2023-10-20T10:06:57Z | https://github.com/osqzss/gps-sdr-sim/issues/294 | 951,577,485 | 294 | 3,810 |
CVE-2022-31112 | 2022-06-30T17:15:07.977 | Parse Server is an open source backend that can be deployed to any infrastructure that can run Node.js. In affected versions parse Server LiveQuery does not remove protected fields in classes, passing them to the client. The LiveQueryController now removes protected fields from the client response. Users are advised to... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/parse-community/parse-server/commit/309f64ced8700321df056fb3cc97f15007a00df1"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parseplatform:parse-server:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "9C3D4EDC-0BE1-411C-93E3-2351A4E7B3D6",
"versionEndExcluding": "4.10.13",
"versionEndIncluding": null,
"... | [
"212"
] | 212 | https://github.com/parse-community/parse-server/issues/8073 | [
"Issue Tracking",
"Patch",
"Release Notes",
"Third Party Advisory"
] | github.com | [
"parse-community",
"parse-server"
] | null | fix: protected fields exposed via LiveQuery (GHSA-crrq-vr9j-fxxh) | https://api.github.com/repos/parse-community/parse-server/issues/8073/comments | 3 | 2022-06-26T20:40:03Z | 2022-07-02T09:21:17Z | https://github.com/parse-community/parse-server/pull/8073 | 1,285,025,776 | 8,073 | 3,811 |
CVE-2013-4144 | 2022-06-30T18:15:08.557 | There is an object injection vulnerability in swfupload plugin for wordpress. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wordpress/secure-swfupload/issues/1"
},
{
"source": "secalert@redhat.com",
"tags": [
"Mailing List"
],
"url": "https://www.openwall.com/lists/oss-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swfupload_project:swfupload:3.5.2:*:*:*:*:wordpress:*:*",
"matchCriteriaId": "C077E743-7719-429C-8D0B-F2BC3CE43B2C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"74"
] | 74 | https://github.com/wordpress/secure-swfupload/issues/1 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wordpress",
"secure-swfupload"
] | I've received a few reports today of an image object injection problem in swfupload affecting WordPress. I'm filing this public issue here after contacting swfupload-security@wordpress.org and being asked to do so (as this issue is already public knowledge).
There's an object injection "vulnerability" in swfupload, as... | Image object injection vulnerability via 'buttonImageURL' parameter | https://api.github.com/repos/WordPress/secure-swfupload/issues/1/comments | 11 | 2013-07-03T18:00:54Z | 2015-03-22T07:21:12Z | https://github.com/WordPress/secure-swfupload/issues/1 | 16,332,126 | 1 | 3,812 |
CVE-2022-2274 | 2022-07-01T08:15:07.687 | The OpenSSL 3.0.4 release introduced a serious bug in the RSA implementation for X86_64 CPUs supporting the AVX512IFMA instructions. This issue makes the RSA implementation with 2048 bit private keys incorrect on such machines and memory corruption will happen during the computation. As a consequence of the memory corr... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "openssl-security@openssl.org",
"tags": null,
"url": "https://git.openssl.org/gitweb/?p=openssl.git%3Ba=commitdiff%3Bh=4d8a88c134df634ba610ff8db1eb8478ac5fd345"
},
{
"source": "openssl-security@openssl.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openssl:openssl:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "064E8433-3B62-4C85-868C-58BFD3E8FD49",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/openssl/openssl/issues/18625 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openssl",
"openssl"
] | Build OpenSSL-3.0.4 on a CPU with AVX512 (my CPU is a Core i7-1065G7) with:
```
CFLAGS="-O3 -g -fsanitize=address" ./config
make
```
Run a test:
```
make V=1 TESTS=test_exp test
```
The sanitizer complains:
```
==481618==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60c000089400 at pc ... | AVX512-specific heap buffer overflow with 3.0.4 release | https://api.github.com/repos/openssl/openssl/issues/18625/comments | 27 | 2022-06-22T08:51:51Z | 2022-07-18T15:16:57Z | https://github.com/openssl/openssl/issues/18625 | 1,279,803,279 | 18,625 | 3,813 |
CVE-2022-25758 | 2022-07-01T20:15:07.847 | All versions of package scss-tokenizer are vulnerable to Regular Expression Denial of Service (ReDoS) via the loadAnnotation() function, due to the usage of insecure regex. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sasstools/scss-tokenizer/issues/45"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scss-tokenizer_project:scss-tokenizer:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "341E73F1-2D99-4B4E-8497-A126A3FA9F1C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"1333"
] | 1333 | https://github.com/sasstools/scss-tokenizer/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sasstools",
"scss-tokenizer"
] | Dear SCSS-Tokenizer Team,
In scanning my node_modules for [Regular Expression Denial of Service (ReDoS) Affecting org.webjars.npm:postcss](https://security.snyk.io/vuln/SNYK-JAVA-ORGWEBJARSNPM-1255641) and [CVE-2021-23382](https://nvd.nist.gov/vuln/detail/CVE-2021-23382)
I encountered scss-tokenizer with [previo... | CVE-2021-23382 Might apply? | https://api.github.com/repos/sasstools/scss-tokenizer/issues/45/comments | 2 | 2022-01-12T21:11:06Z | 2022-08-10T01:30:25Z | https://github.com/sasstools/scss-tokenizer/issues/45 | 1,100,793,167 | 45 | 3,814 |
CVE-2022-25876 | 2022-07-01T20:15:07.917 | The package link-preview-js before 2.1.16 are vulnerable to Server-side Request Forgery (SSRF) which allows attackers to send arbitrary requests to the local network and read the response. This is due to flawed DNS rebinding protection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ospfranco/link-preview-js/issues/115"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:link-preview-js_project:link-preview-js:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "17008C45-5881-498A-B129-01ACA4E82F0D",
"versionEndExcluding": "2.1.16",
"versionEndIncluding": null,
... | [
"918"
] | 918 | https://github.com/ospfranco/link-preview-js/issues/115 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ospfranco",
"link-preview-js"
] | **Describe**
There is a way to bypass your regex to validate private & local networks.
If we use http://127.0.0.1/ or http://localhost/ to link preview, we don't see it (`Error: link-preview-js did not receive a valid a url or text`), but if we use a domain that resolved to 127.0.0.1, we can. For example: localtest... | SSRF | https://api.github.com/repos/OP-Engineering/link-preview-js/issues/115/comments | 17 | 2022-05-25T07:33:47Z | 2022-06-27T05:53:03Z | https://github.com/OP-Engineering/link-preview-js/issues/115 | 1,247,683,812 | 115 | 3,815 |
CVE-2022-31943 | 2022-07-01T21:15:08.147 | MCMS v5.2.8 was discovered to contain an arbitrary file upload vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ming-soft/MCMS/issues/95"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mingsoft:mcms:5.2.8:*:*:*:*:*:*:*",
"matchCriteriaId": "7C5B845C-EA6C-4362-B197-7C58FE4C8129",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/ming-soft/MCMS/issues/95 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ming-soft",
"MCMS"
] | 1.代码分析
从铭飞官网https://gitee.com/mingSoft/MCMS把源码考下来之后
经过审计找到上传点,form.ftl这里有个文章缩略图上传点看他有没有做过滤然后根据action找到上传接口
<img width="415" alt="1" src="https://user-images.githubusercontent.com/106334576/170712617-eed47160-7a48-47b7-81e2-04c5e7837b39.png">
经过查找在FileAction.class这里只判断了../防止目录跳跃,继续往下看点击继承的那个类
<img width="416" alt... | Mcms v5.2.8文件上传漏洞 | https://api.github.com/repos/ming-soft/MCMS/issues/95/comments | 3 | 2022-05-27T15:05:46Z | 2022-10-11T07:27:35Z | https://github.com/ming-soft/MCMS/issues/95 | 1,250,873,195 | 95 | 3,816 |
CVE-2022-32324 | 2022-07-01T22:15:07.927 | PDFAlto v0.4 was discovered to contain a heap buffer overflow via the component /pdfalto/src/pdfalto.cc. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kermitt2/pdfalto/issues/144"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdfalto_project:pdfalto:0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "0F175631-FB59-4AC3-80E9-0BE1F7D088D6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/kermitt2/pdfalto/issues/144 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kermitt2",
"pdfalto"
] | sample here:
[heap-bufferoverflow-pos-)%at pdfalto.zip](https://github.com/kermitt2/pdfalto/files/8811939/heap-bufferoverflow-pos-.at.pdfalto.zip)
Describe info:
```
$ ./pdfalto heap-bufferoverflow-pos-\>at\ pdfalto.cc\:190\:5
==43072==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6040000000f1 at... | heap-buffer-overflow found? | https://api.github.com/repos/kermitt2/pdfalto/issues/144/comments | 0 | 2022-06-01T07:31:05Z | 2024-12-26T16:31:14Z | https://github.com/kermitt2/pdfalto/issues/144 | 1,255,225,282 | 144 | 3,817 |
CVE-2022-32325 | 2022-07-01T22:15:07.993 | JPEGOPTIM v1.4.7 was discovered to contain a segmentation violation which is caused by a READ memory access at jpegoptim.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tjko/jpegoptim/issues/107"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%4... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpegoptim_project:jpegoptim:1.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "3E659588-F2F1-4FD5-9851-287D91B13B64",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"125"
] | 125 | https://github.com/tjko/jpegoptim/issues/107 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tjko",
"jpegoptim"
] | hi, with the help of fuzzing ,I found some crash sample in this repo, here is the sample, are they new bugs?
crash position jpegoptim.c:631:3
crash sample: crash1_SEGV_caused_by_READ_memory_access_at_jpegoptim.c:631:3
sample here:
[crash1_SEGV_caused_by_READ_memory_access_at_jpegoptim.zip](https://github.com/tjk... | SEGV caused by a READ memory access | https://api.github.com/repos/tjko/jpegoptim/issues/107/comments | 6 | 2022-06-02T01:51:47Z | 2023-01-05T04:40:37Z | https://github.com/tjko/jpegoptim/issues/107 | 1,257,496,511 | 107 | 3,818 |
CVE-2021-43116 | 2022-07-05T14:15:08.767 | An Access Control vulnerability exists in Nacos 2.0.3 in the access prompt page; enter username and password, click on login to capture packets and then change the returned package, which lets a malicious user login. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/171638/Nacos-2.0.3-Access-Control.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/alibaba/nacos/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alibaba:nacos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "92C071B9-CC45-4164-986C-9DDE011EAB15",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.3",
"versionStartExcluding... | [
"287"
] | 287 | https://github.com/alibaba/nacos/issues/7127 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"alibaba",
"nacos"
] | <!-- Here is for bug reports and feature requests ONLY!
If you're looking for help, please check our mail list、WeChat group and the Gitter room.
Please try to use English to describe your issue, or at least provide a snippet of English translation.
我们鼓励使用英文,如果不能直接使用,可以使用翻译软件,您仍旧可以保留中文原文。
-->
**Describe the ... | A vulnerability was found that could cause any existing user to log in | https://api.github.com/repos/alibaba/nacos/issues/7127/comments | 0 | 2021-10-26T10:13:19Z | 2021-11-05T07:23:20Z | https://github.com/alibaba/nacos/issues/7127 | 1,036,102,526 | 7,127 | 3,819 |
CVE-2021-43116 | 2022-07-05T14:15:08.767 | An Access Control vulnerability exists in Nacos 2.0.3 in the access prompt page; enter username and password, click on login to capture packets and then change the returned package, which lets a malicious user login. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/171638/Nacos-2.0.3-Access-Control.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/alibaba/nacos/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alibaba:nacos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "92C071B9-CC45-4164-986C-9DDE011EAB15",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.3",
"versionStartExcluding... | [
"287"
] | 287 | https://github.com/alibaba/nacos/issues/7182 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"alibaba",
"nacos"
] | The steps to reproduce.可复现问题的步骤 1.Download the latest version of NacOS
https://github.com/alibaba/nacos/
2.Follow the steps for installation
3.After the installation is successful, access the default login ... | Found a login background vulnerability | https://api.github.com/repos/alibaba/nacos/issues/7182/comments | 5 | 2021-11-05T07:48:43Z | 2022-10-10T07:34:31Z | https://github.com/alibaba/nacos/issues/7182 | 1,045,534,980 | 7,182 | 3,820 |
CVE-2022-31836 | 2022-07-05T15:15:08.750 | The leafInfo.match() function in Beego v2.0.3 and below uses path.join() to deal with wildcardvalues which can lead to cross directory risk. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/advisories/GHSA-95f9-94vc-665h"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/beego/beego/issues/4961"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:beego:beego:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6F33069D-EE29-428D-A087-595B51047BEB",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.3",
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/beego/beego/issues/4961 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"beego",
"beego"
] | Function leafInfo.match() use path.join() to deal with `wildcardValues`, which may lead to cross directory risk.
- **poc1: route end with `*.*` can use `../` to cross directory and set evil value for `:path` .**
https://github.com/beego/beego/blob/64cf44d725c8cc35d782327d333df9cbeb1bf2dd/server/web/tree.go#L414... | Function leafInfo.match() use path.join() to deal with `wildcardValues`, which may lead to cross directory risk. | https://api.github.com/repos/beego/beego/issues/4961/comments | 4 | 2022-05-23T12:59:50Z | 2022-06-02T02:12:06Z | https://github.com/beego/beego/issues/4961 | 1,245,131,363 | 4,961 | 3,821 |
CVE-2021-44915 | 2022-07-05T18:15:07.797 | Taocms 3.0.2 was discovered to contain a blind SQL injection vulnerability via the function Edit category. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/taogogo/taocms/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taogogo",
"taocms"
] | Log in to the background as the default account admin.

We click in order and grab packets:

 | https://api.github.com/repos/taogogo/taocms/issues/8/comments | 0 | 2021-12-07T08:51:23Z | 2021-12-07T08:51:23Z | https://github.com/taogogo/taocms/issues/8 | 1,073,082,158 | 8 | 3,822 |
CVE-2022-32413 | 2022-07-05T20:15:08.237 | An arbitrary file upload vulnerability in Dice v4.2.0 allows attackers to execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bihell/Dice/issues/157"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dice_project:dice:4.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "19630FFB-7EB6-4FBE-85A5-61C4D99039DB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/bihell/Dice/issues/157 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bihell",
"Dice"
] | 1、Any file upload vulnerability in the following code can cause RCE

2、Follow up the code、Files are directly uploaded to the server without filtering
-1
### modify admin's password ,mail,phone and head-image.
Technical Description:
file :
` pescms/App/Team/PUT/User.php`
The function of this file is to Modify personal information,but it don't Verify whether the operation is legal.
Through it attackers can modif... | There are some vulnerabilities in cms. | https://api.github.com/repos/lazyphp/PESCMS-TEAM/issues/7/comments | 1 | 2021-04-19T09:20:03Z | 2021-04-19T09:29:30Z | https://github.com/lazyphp/PESCMS-TEAM/issues/7 | 861,094,547 | 7 | 3,824 |
CVE-2021-31677 | 2022-07-06T13:15:09.040 | An issue was discovered in PESCMS-V2.3.3. There is a CSRF vulnerability that can modify admin and other members' passwords. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/RO6OTXX/pescms_vulnerability"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/lazyphp/PESCMS-TEAM/issues/7%2C"
},
{
"source": "cve@mitre... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pescms:pescms_team:2.3.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B86D2EF3-C36E-45D0-BB3E-BCF0111F597F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"352"
] | 352 | https://github.com/lazyphp/PESCMS-TEAM/issues/7%2C | null | github.com | [
"lazyphp",
"PESCMS-TEAM"
] | ## Cross Site Request Forgery(CSRF)-1
### modify admin's password ,mail,phone and head-image.
Technical Description:
file :
` pescms/App/Team/PUT/User.php`
The function of this file is to Modify personal information,but it don't Verify whether the operation is legal.
Through it attackers can modif... | There are some vulnerabilities in cms. | https://api.github.com/repos/lazyphp/PESCMS-TEAM/issues/7/comments | 1 | 2021-04-19T09:20:03Z | 2021-04-19T09:29:30Z | https://github.com/lazyphp/PESCMS-TEAM/issues/7 | 861,094,547 | 7 | 3,825 |
CVE-2015-3172 | 2022-07-06T20:15:07.940 | EidoGo is susceptible to Cross-Site Scripting (XSS) attacks via maliciously crafted SGF input. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jkk/eidogo/issues/27"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eidogo:eidogo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "924144DF-9903-46D1-8926-720D9913E802",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/jkk/eidogo/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jkk",
"eidogo"
] | EidoGo is susceptible to Cross-Site Scripting (XSS) attacks via maliciously crafted SGF input.
There are actually two separate XSS vulnerabilities:
1) Text from comments and game info are unsafely added into the DOM directly via innerHTML.
2) Any file loaded from URL that begins with a left-curly bracket "{" is assume... | XSS Security Vulnerability | https://api.github.com/repos/jkk/eidogo/issues/27/comments | 7 | 2015-06-14T20:15:36Z | 2021-11-02T23:11:09Z | https://github.com/jkk/eidogo/issues/27 | 88,241,816 | 27 | 3,826 |
CVE-2021-35283 | 2022-07-07T21:15:09.847 | SQL Injection vulnerability in product_admin.php in atoms183 CMS 1.0, allows attackers to execute arbitrary commands via the Name, Fname, and ID parameters to search.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/atoms183/CMS/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:atoms183_cms_project:atoms183_cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CE394319-D504-4901-85C9-4FA83BC9DDD7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/atoms183/CMS/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"atoms183",
"CMS"
] | product_ Admin.php
There is SQL injection in line 23
```
$link=mysql_connect($host,$user,$pass);
mysql_select_db($db_name,$link);
//Если переменная Name передана
if (isset($_POST["Name"])) {
//Тут идет запрос
$sql = mysql_query("INSERT INTO `info` (`Name`, `Fname`, `ID`)
VALU... | product_ Admin.php SQL injection | https://api.github.com/repos/atoms183/CMS/issues/1/comments | 0 | 2021-06-09T05:44:41Z | 2021-06-09T05:44:41Z | https://github.com/atoms183/CMS/issues/1 | 915,801,208 | 1 | 3,827 |
CVE-2021-41037 | 2022-07-08T04:15:13.833 | In Eclipse p2, installable units are able to alter the Eclipse Platform installation and the local machine via touchpoints during installation. Those touchpoints can, for example, alter the command-line used to start the application, injecting things like agent or other settings that usually require particular attentio... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "emo@eclipse.org",
"tags": [
"Mailing List",
"Vendor Advisory"
],
"url": "https://bugs.eclipse.org/bugs/show_bug.cgi?id=577029"
},
{
"source": "emo@eclipse.org",
"tags": null,
"url": "https://github.com/eclipse-equinox/p2/issues/235"
},
{
"source": "af... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:equinox_p2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "82D19D5B-3327-4797-A09C-A32EC26D1342",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"829"
] | 829 | https://github.com/eclipse-equinox/p2/issues/235 | null | github.com | [
"eclipse-equinox",
"p2"
] | This issue's description and proposed remediation will be edited as this issue evolves. It is currently a draft work in progress.
Background:
- https://bugs.eclipse.org/bugs/show_bug.cgi?id=577029
- https://nvd.nist.gov/vuln/detail/CVE-2021-41037
The CVE has this description:
> In Eclipse p2, installable ... | CVE-2021-41037: p2 metadata (even without artifacts) can be an attack vector | https://api.github.com/repos/eclipse-equinox/p2/issues/235/comments | 19 | 2023-03-25T10:15:53Z | 2024-07-12T13:49:47Z | https://github.com/eclipse-equinox/p2/issues/235 | 1,640,462,047 | 235 | 3,828 |
CVE-2022-31501 | 2022-07-11T01:15:08.040 | The ChaoticOnyx/OnyxForum repository before 2022-05-04 on GitHub allows absolute path traversal because the Flask send_file function is used unsafely. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ChaoticOnyx/OnyxForum/commit/f25543dfc62a9694d7e4f67eebfa45e3de916053"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onyxforum_project:onyxforum:*:*:*:*:*:*:*:*",
"matchCriteriaId": "20DBF704-0F43-41D2-B854-46441B0944D3",
"versionEndExcluding": null,
"versionEndIncluding": "2022-05-04",
"ve... | [
"22"
] | 22 | https://github.com/github/securitylab/issues/669#issuecomment-1117265726 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"github",
"securitylab"
] | ### CVE(s) ID list
This is a placeholder issue. I plan on sending bulk PR's to approx 100 projects. I will add the CVE once the fixes are merged and identifiers are assigned.
### All For One submission
https://github.com/github/securitylab/issues/407
### Details
TBA
### Are you planning to discuss this vulner... | Python : Flask Path Traversal Vulnerability | https://api.github.com/repos/github/securitylab/issues/669/comments | 54 | 2022-04-28T19:02:52Z | 2022-08-08T18:30:18Z | https://github.com/github/securitylab/issues/669 | 1,219,149,119 | 669 | 3,829 |
CVE-2022-31581 | 2022-07-11T01:15:11.227 | The scorelab/OpenMF repository before 2022-05-03 on GitHub allows absolute path traversal because the Flask send_file function is used unsafely. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/github/securitylab/issues/669#issuecomment-1117265726"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scorelab:openmf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DE5E2491-8B9E-492C-8CD1-C696BBBA7F0E",
"versionEndExcluding": "2022-05-03",
"versionEndIncluding": null,
"versionStartEx... | [
"22"
] | 22 | https://github.com/scorelab/OpenMF/issues/262 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"scorelab",
"OpenMF"
] | # Absolute Path Traversal due to incorrect use of `send_file` call
A path traversal attack (also known as directory traversal) aims to access files and directories that are stored outside the web root folder. By manipulating variables that reference files with “dot-dot-slash (../)” sequences and its variations or by u... | Security Vulnerability Found | https://api.github.com/repos/scorelab/OpenMF/issues/262/comments | 0 | 2022-05-03T12:25:30Z | 2022-05-03T12:27:48Z | https://github.com/scorelab/OpenMF/issues/262 | 1,224,030,169 | 262 | 3,830 |
CVE-2022-2385 | 2022-07-12T19:15:08.487 | A security issue was discovered in aws-iam-authenticator where an allow-listed IAM identity may be able to modify their username and escalate privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes-sigs/aws-iam-authenticator/issues/472"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Mailing List",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:aws-iam-authenticator:*:*:*:*:*:kubernetes:*:*",
"matchCriteriaId": "61C7DCDF-228A-41D4-9336-B6E757616B72",
"versionEndExcluding": "0.5.9",
"versionEndIncluding": null,
... | [
"20"
] | 20 | https://github.com/kubernetes-sigs/aws-iam-authenticator/issues/472 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kubernetes-sigs",
"aws-iam-authenticator"
] | CVSS Rating: [High](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:N)
A security issue was discovered in aws-iam-authenticator where an allow-listed IAM identity may be able to modify their username and escalate privileges.
This issue has been rated **high** (https://www.fir... | CVE-2022-2385: AccessKeyID validation bypass | https://api.github.com/repos/kubernetes-sigs/aws-iam-authenticator/issues/472/comments | 5 | 2022-07-11T16:15:16Z | 2022-07-12T18:23:35Z | https://github.com/kubernetes-sigs/aws-iam-authenticator/issues/472 | 1,300,932,370 | 472 | 3,831 |
CVE-2022-30517 | 2022-07-12T23:15:12.037 | Mogu blog 5.2 is vulnerable to Cross Site Scripting (XSS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/moxi624/mogu_blog_v2/issues/65"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mogublog_project:mogublog:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "BAA6E8F8-A88C-4E75-A0F3-9597FBB3B034",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/moxi624/mogu_blog_v2/issues/65 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"moxi624",
"mogu_blog_v2"
] | Using mogu2021:mogu2021 to log in the Mogu blog.
http://demoweb.moguit.cn/


Choose User Center > ... | Mogu blog has a vulnerability to upload arbitrary files | https://api.github.com/repos/moxi624/mogu_blog_v2/issues/65/comments | 2 | 2022-05-08T11:03:25Z | 2022-06-05T08:47:22Z | https://github.com/moxi624/mogu_blog_v2/issues/65 | 1,228,858,146 | 65 | 3,832 |
CVE-2019-10761 | 2022-07-13T09:15:08.213 | This affects the package vm2 before 3.6.11. It is possible to trigger a RangeError exception from the host rather than the "sandboxed" context by reaching the stack call limit with an infinite recursion. The returned object is then used to reference the mainModule property of the host code running the script allowing i... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 8.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/patriksimek/vm2/commit/4b22d704e4794af63a5a2d633385fd20948f6f90"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vm2_project:vm2:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "E1C137CC-088D-4998-BB3A-DD81B2CCCE79",
"versionEndExcluding": "3.6.11",
"versionEndIncluding": null,
"versionStart... | [
"674"
] | 674 | https://github.com/patriksimek/vm2/issues/197 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"patriksimek",
"vm2"
] | It is possible to almost anywhere generate a RangeError: Maximum call stack size exceeded. Sometimes the RangeError will be a host RangeError which is not Contextified.
I tried to make the code as stable as possible.
```JS
"use strict";
const {VM} = require('vm2');
const untrusted = `
const f = Buffer.prototype.w... | Breakout in v3.6.10 via Maximum call stack size exceeded RangeError | https://api.github.com/repos/patriksimek/vm2/issues/197/comments | 3 | 2019-04-07T08:21:39Z | 2019-12-09T22:43:50Z | https://github.com/patriksimek/vm2/issues/197 | 430,118,407 | 197 | 3,833 |
CVE-2022-32065 | 2022-07-13T15:15:10.707 | An arbitrary file upload vulnerability in the background management module of RuoYi v4.7.3 and below allows attackers to execute arbitrary code via a crafted HTML file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://gitee.com/y_project/RuoYi/commit/d8b2a9a905fb750fa60e2400238cf4750a77c5e6"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ruoyi:ruoyi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1501E3A5-4A4F-4D50-B99A-D553D98C20B2",
"versionEndExcluding": null,
"versionEndIncluding": "4.7.3",
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/yangzongzhuan/RuoYi/issues/118 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yangzongzhuan",
"RuoYi"
] | Vulnerability disclosure
Vulnerability title: The html file can be uploaded where the avatar is uploaded, and its content not be filtered, which resulting in stored XSS in Ruoyi cms
Product: https://github.com/yangzongzhuan/RuoYi
Affected Versions: v4.7.3(the lastest vesion)
Discovery time: 2022.5.16
Fou... | Vulnerability: The html file can be uploaded where the avatar is uploaded, and its content not be filtered, which resulting in stored XSS in Ruoyi cms | https://api.github.com/repos/yangzongzhuan/RuoYi/issues/118/comments | 1 | 2022-05-15T23:58:57Z | 2022-07-12T09:45:58Z | https://github.com/yangzongzhuan/RuoYi/issues/118 | 1,236,468,032 | 118 | 3,834 |
CVE-2020-21967 | 2022-07-13T20:15:08.030 | File upload vulnerability in the Catalog feature in Prestashop 1.7.6.7 allows remote attackers to run arbitrary code via the add new file page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/167742/PrestaShop-1.7.6.7-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:prestashop:prestashop:1.7.6.7:*:*:*:*:*:*:*",
"matchCriteriaId": "7B8C99EA-5A63-4404-AE10-5E4B4652F371",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/PrestaShop/PrestaShop/issues/20306 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PrestaShop",
"PrestaShop"
] | <!--
****************************
DO NOT disclose security issues here, contact security@prestashop.com instead!
****************************
-->
An issue is discovered in PrestaShop version 1.7.6.7 under the Catelog feature when using the file-upload functionality for uploading the Files for various products. ... | Cross Site Scripting Issue in PrestaShop Using File Upload Functionality | https://api.github.com/repos/PrestaShop/PrestaShop/issues/20306/comments | 3 | 2020-07-23T17:29:20Z | 2020-07-24T07:51:28Z | https://github.com/PrestaShop/PrestaShop/issues/20306 | 664,648,405 | 20,306 | 3,835 |
CVE-2022-32308 | 2022-07-13T20:15:08.110 | Cross Site Scripting (XSS) vulnerability in uBlock Origin extension before 1.41.1 allows remote attackers to run arbitrary code via a spoofed 'MessageSender.url' to the browser renderer process. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/uBlockOrigin/uBlock-issues/issues/1992"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ublock_origin_project:ublock_origin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E19CA144-D108-468C-A361-3BA22E3BCB18",
"versionEndExcluding": "1.41.1",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/uBlockOrigin/uBlock-issues/issues/1992 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"uBlockOrigin",
"uBlock-issues"
] | ### Description
Email received at `ubo-security at raymondhill.net` on 2022-02-17:
> Hi,
>
> I'd like to report a security vulnerability in the uBlock Origin extension.
>
> A compromised renderer process of Chrome is able to spoof the URL of a messaging port and send privileged messages.
>
> A compromise... | Use unspoofable Messenger.origin to determine privilege level of ports | https://api.github.com/repos/uBlockOrigin/uBlock-issues/issues/1992/comments | 1 | 2022-02-17T23:03:39Z | 2022-03-03T13:45:44Z | https://github.com/uBlockOrigin/uBlock-issues/issues/1992 | 1,142,031,666 | 1,992 | 3,836 |
CVE-2022-32117 | 2022-07-13T21:15:08.123 | Jerryscript v2.4.0 was discovered to contain a stack buffer overflow via the function jerryx_print_unhandled_exception in /util/print.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5008"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/5008 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
0d4969661810b9e618485c284c361e597144e9b9
master
###### Build platform
Ubuntu 16.04.7 LTS (Linux 4.15.0-142-generic x86_64)
###### Build steps
```sh
./tools/build.py --clean --compile-flag=-fsanitize=address --lto=off --error-message=on --profile=es.next --stack-limit=15 --debug --lo... | Stack-buffer-overflow in jerryx_print_unhandled_exception (jerryscript/jerry-ext/util/print.c) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5008/comments | 1 | 2022-05-29T18:17:00Z | 2022-08-08T06:14:38Z | https://github.com/jerryscript-project/jerryscript/issues/5008 | 1,251,957,111 | 5,008 | 3,837 |
CVE-2022-35857 | 2022-07-13T22:15:09.060 | kvf-admin through 2022-02-12 allows remote attackers to execute arbitrary code because deserialization is mishandled. The rememberMe parameter is encrypted with a hardcoded key from the com.kalvin.kvf.common.shiro.ShiroConfig file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/kalvinGit/kvf-admin/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kvf-admin_project:kvf-admin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2664551A-27E9-4D70-A84A-DA72BD4CF6C7",
"versionEndExcluding": null,
"versionEndIncluding": "2022-02-12",
"ve... | [
"798"
] | 798 | https://github.com/kalvinGit/kvf-admin/issues/16 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"kalvinGit",
"kvf-admin"
] | The author sets a fixed key in the com.kalvin.kvf.common.shiro.ShiroConfig file and uses this key to encrypt the rememberMe parameter in the cookie. This situation can cause a deserialization attack with very serious consequences.
<img width="942" alt="2" src="https://user-images.githubusercontent.com/75016675/1783973... | There is a deserialization vulnerability that can cause RCE | https://api.github.com/repos/kalvinGit/kvf-admin/issues/16/comments | 1 | 2022-07-12T02:50:44Z | 2024-03-28T02:04:03Z | https://github.com/kalvinGit/kvf-admin/issues/16 | 1,301,463,910 | 16 | 3,838 |
CVE-2022-32298 | 2022-07-14T20:15:08.660 | Toybox v0.8.7 was discovered to contain a NULL pointer dereference via the component httpd.c. This vulnerability can lead to a Denial of Service (DoS) via unspecified vectors. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/landley/toybox/issues/346"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:toybox_project:toybox:0.8.7:*:*:*:*:*:*:*",
"matchCriteriaId": "3FFAA4F7-F658-46C8-BB1F-47ED437929F5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"476"
] | 476 | https://github.com/landley/toybox/issues/346 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"landley",
"toybox"
] | ## poc
```bash
GET /tar/tar.tar/.. HTTP/1.1\r\n\r\n
```
## crash scene
```bash
pwndbg> bt
#0 strstart (a=a@entry=0x7fffffffdb58, b=b@entry=0x0) at lib/lib.c:506
#1 0x00005555555749f4 in isunder (dir=0x5555555bb7d4 ".", file=0x5555555cd535 "tar/tar.tar/..") at toys/net/httpd.c:86
#2 handle (infd=<optim... | Null pointer dereference in httpd.c | https://api.github.com/repos/landley/toybox/issues/346/comments | 2 | 2022-05-23T05:44:46Z | 2022-06-09T22:32:49Z | https://github.com/landley/toybox/issues/346 | 1,244,612,012 | 346 | 3,839 |
CVE-2022-32406 | 2022-07-14T21:15:08.613 | GtkRadiant v1.6.6 was discovered to contain a buffer overflow via the component q3map2. This vulnerability can cause a Denial of Service (DoS) via a crafted MAP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/TTimo/GtkRadiant/issues/676"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gtkradiant_project:gtkradiant:1.6.6:*:*:*:*:*:*:*",
"matchCriteriaId": "19DDA161-3459-4772-BCAC-5FE1DEBF7C4D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"120"
] | 120 | https://github.com/TTimo/GtkRadiant/issues/676 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"TTimo",
"GtkRadiant"
] | Hi folks,
A buffer overflow was found while fuzz testing of the q3map2 binary which can be triggered via a malformed MAP file with a large shader image name. Although this malformed file only crashes the program as-is, it could potentially be crafted further and create a security issue where these kinds of files wou... | Buffer overflow in q3map2 when parsing malformed MAP file | https://api.github.com/repos/TTimo/GtkRadiant/issues/676/comments | 0 | 2022-01-12T18:10:15Z | 2022-01-12T18:10:15Z | https://github.com/TTimo/GtkRadiant/issues/676 | 1,100,643,453 | 676 | 3,840 |
CVE-2022-32425 | 2022-07-14T22:15:08.950 | The login function of Mealie v1.0.0beta-2 allows attackers to enumerate existing usernames by timing the server's response time. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hay-kot/mealie/issues/1336"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hay-kot/mealie/issues/1336"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mealie:mealie:1.0.0:beta2:*:*:*:*:*:*",
"matchCriteriaId": "1A87BAAC-D05F-4315-B961-9B4553943D81",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"203"
] | 203 | https://github.com/hay-kot/mealie/issues/1336 | [
"Third Party Advisory"
] | github.com | [
"hay-kot",
"mealie"
] | ### First Check
- [X] This is not a feature request
- [X] I added a very descriptive title to this issue.
- [X] I used the GitHub search to find a similar issue and didn't find it.
- [X] I searched the Mealie documentation, with the integrated search.
- [X] I already read the docs and didn't find an answer.
#... | [v1.0.0b] - Time based user enumeration in the /api/auth/token endpoint | https://api.github.com/repos/mealie-recipes/mealie/issues/1336/comments | 1 | 2022-06-02T17:04:29Z | 2022-06-04T18:27:31Z | https://github.com/mealie-recipes/mealie/issues/1336 | 1,258,460,082 | 1,336 | 3,841 |
CVE-2022-34092 | 2022-07-14T22:15:08.993 | Portal do Software Publico Brasileiro i3geo v7.0.5 was discovered to contain a cross-site scripting (XSS) vulnerability via svg2img.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/edmarmoretti/i3geo/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/saladesituacao/i3g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwarepublico:i3geo:7.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "ADD2D314-E4BD-4399-BC3E-9BDC7A780477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/edmarmoretti/i3geo/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"edmarmoretti",
"i3geo"
] | Boa tarde
A vulnerabilidade em questão está no arquivo svg2img.php.
O nível de severidade da vulnerabilidade é alta, pois é possível a injeção de código html, bem como a execução de código javascript.
Proof of Concept (POC)
O falha pode ser testada da seguinte maneira:
http://.../i3geo/pacotes/svg2img.ph... | Vulnerabilidade - XSS (Cross Site Scripting) or HTML Injection - svg2img.php | https://api.github.com/repos/edmarmoretti/i3geo/issues/3/comments | 0 | 2022-06-14T10:56:46Z | 2022-06-14T10:56:46Z | https://github.com/edmarmoretti/i3geo/issues/3 | 1,270,623,978 | 3 | 3,842 |
CVE-2022-34093 | 2022-07-14T22:15:09.037 | Portal do Software Publico Brasileiro i3geo v7.0.5 was discovered to contain a cross-site scripting (XSS) vulnerability via access_token.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/edmarmoretti/i3geo/issues/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/saladesituacao/i3g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwarepublico:i3geo:7.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "ADD2D314-E4BD-4399-BC3E-9BDC7A780477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/edmarmoretti/i3geo/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"edmarmoretti",
"i3geo"
] | Boa tarde
A vulnerabilidade em questão está no arquivo access_token.php.
O nível de severidade da vulnerabilidade é alta, pois é possível a injeção de código html, bem como a execução de código javascript.
Proof of Concept (POC)
O falha pode ser testada da seguinte maneira:
http://.../i3geo/pacotes/linke... | Vulnerabilidade - XSS (Cross Site Scripting) or HTML Injection - access_token.php | https://api.github.com/repos/edmarmoretti/i3geo/issues/4/comments | 0 | 2022-06-14T10:57:19Z | 2022-06-14T10:57:19Z | https://github.com/edmarmoretti/i3geo/issues/4 | 1,270,624,553 | 4 | 3,843 |
CVE-2022-34094 | 2022-07-14T22:15:09.083 | Portal do Software Publico Brasileiro i3geo v7.0.5 was discovered to contain a cross-site scripting (XSS) vulnerability via request_token.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/edmarmoretti/i3geo/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/saladesituacao/i3g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwarepublico:i3geo:7.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "ADD2D314-E4BD-4399-BC3E-9BDC7A780477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/edmarmoretti/i3geo/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"edmarmoretti",
"i3geo"
] | Boa tarde
A vulnerabilidade em questão está no arquivo request_token.php.
O nível de severidade da vulnerabilidade é alta, pois é possível a injeção de código html, bem como a execução de código javascript.
Proof of Concept (POC)
O falha pode ser testada da seguinte maneira:
http://.../i3geo/pacotes/link... | Vulnerabilidade - XSS (Cross Site Scripting) or HTML Injection - request_token.php | https://api.github.com/repos/edmarmoretti/i3geo/issues/5/comments | 0 | 2022-06-14T10:57:53Z | 2022-06-14T10:57:53Z | https://github.com/edmarmoretti/i3geo/issues/5 | 1,270,625,144 | 5 | 3,844 |
CVE-2021-36461 | 2022-07-15T12:15:08.677 | An Arbitrary File Upload vulnerability exists in Microweber 1.1.3 that allows attackers to getshell via the Settings Upload Picture section by uploading pictures with malicious code, user.ini. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/microweber/microweber/issues/751"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microweber:microweber:1.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26B5B517-157A-416A-8816-98EAC6FBA01B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"434"
] | 434 | https://github.com/microweber/microweber/issues/751 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"microweber",
"microweber"
] | [microweber Background file upload getshell.pdf](https://github.com/microweber/microweber/files/6719464/microweber.Background.file.upload.getshell.pdf)
This pdf file describes the vulnerability in detail
| microweber1.1.3 has background upload getshell | https://api.github.com/repos/microweber/microweber/issues/751/comments | 1 | 2021-06-26T02:24:23Z | 2021-06-29T11:24:19Z | https://github.com/microweber/microweber/issues/751 | 930,595,970 | 751 | 3,845 |
CVE-2022-31153 | 2022-07-15T18:15:08.760 | OpenZeppelin Contracts for Cairo is a library for contract development written in Cairo for StarkNet, a decentralized ZK Rollup. Version 0.2.0 is vulnerable to an error that renders account contracts unusable on live networks. This issue affects all accounts (vanilla and ethereum flavors) in the v0.2.0 release of OpenZ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/OpenZeppelin/cairo-contracts/blob/release-0.2.0/src/openzeppelin/account/library.cairo#L203"
},
{
"source": "security-advisories@github.com",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openzeppelin:contracts:0.2.0:*:*:*:*:cairo:*:*",
"matchCriteriaId": "49289387-3C88-4D7E-9B63-73CFC6729EB5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"863"
] | 863 | https://github.com/OpenZeppelin/cairo-contracts/issues/386 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"OpenZeppelin",
"cairo-contracts"
] | Transactions on goerli fail with the following error message:
```
🛑 The transaction was rejected but no contract address was identified in the error message.
Error message:
Error at pc=0:133:
Got an exception while executing a hint.
Cairo traceback (most recent call last):
Unknown location (pc=0:746)
Unknown... | `ecdsa_ptr` points to reference in Account lib's `execute` | https://api.github.com/repos/OpenZeppelin/cairo-contracts/issues/386/comments | 0 | 2022-07-10T00:00:12Z | 2024-03-29T13:26:38Z | https://github.com/OpenZeppelin/cairo-contracts/issues/386 | 1,299,789,749 | 386 | 3,846 |
CVE-2022-32434 | 2022-07-15T21:15:08.783 | EIPStackGroup OpENer v2.3.0 was discovered to contain a stack overflow via /bin/posix/src/ports/POSIX/OpENer+0x56073d. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/EIPStackGroup/OpENer/issues/374"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/WaterDe... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opener_project:opener:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6672F381-CA65-4595-BD10-AC6B9DED4809",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/EIPStackGroup/OpENer/issues/374 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"EIPStackGroup",
"OpENer"
] | Hi, there is a stack overflow bug in OpENer, which is found by fuzzing.
It can be reproduced by the poc.zip attached (by using `send_testcase.py` script and poc.zip is assumed to be unziped).
[poc.zip](https://github.com/EIPStackGroup/OpENer/files/8818829/poc.zip)
Here is the message output by AddressSanitiz... | A stackoverflow bug | https://api.github.com/repos/EIPStackGroup/OpENer/issues/374/comments | 3 | 2022-06-01T21:19:21Z | 2022-07-16T08:07:58Z | https://github.com/EIPStackGroup/OpENer/issues/374 | 1,257,065,949 | 374 | 3,847 |
CVE-2022-34029 | 2022-07-18T21:15:07.910 | Nginx NJS v0.7.4 was discovered to contain an out-of-bounds read via njs_scope_value at njs_scope.h. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/506"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A12FD5A4-6946-49DD-95D4-154A8DA98F7A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"125"
] | 125 | https://github.com/nginx/njs/issues/506 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Environment
```OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 9f4ebc96148308a8ce12f2b54432c87e6d78b881
Version : 0.7.4
Build :
./configure --cc=clang --address-sanitizer=YES
make
```
Proof of concept
``... | SEGV njs_scope.h:74:12 Out-of-bounds Read in njs_scope_value | https://api.github.com/repos/nginx/njs/issues/506/comments | 2 | 2022-05-30T02:09:28Z | 2022-06-02T23:34:07Z | https://github.com/nginx/njs/issues/506 | 1,252,090,775 | 506 | 3,848 |
CVE-2022-34033 | 2022-07-18T21:15:08.083 | HTMLDoc v1.9.15 was discovered to contain a heap overflow via (write_header) /htmldoc/htmldoc/html.cxx:273. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/a0014be47d614220db111b360fb6170ef6f3937e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:1.9.15:*:*:*:*:*:*:*",
"matchCriteriaId": "7FA48CA3-3C4E-46CA-8B5E-FDBF99FDD55F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/michaelrsweet/htmldoc/issues/425 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | AddressSanitizer: heap-buffer-overflow on (write_header) /htmldoc/htmldoc/html.cxx:273 | https://api.github.com/repos/michaelrsweet/htmldoc/issues/425/comments | 3 | 2021-05-06T02:08:38Z | 2021-05-07T10:37:41Z | https://github.com/michaelrsweet/htmldoc/issues/425 | 877,005,444 | 425 | 3,849 | |
CVE-2022-34035 | 2022-07-18T21:15:08.127 | HTMLDoc v1.9.12 and below was discovered to contain a heap overflow via e_node htmldoc/htmldoc/html.cxx:588. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/a0014be47d614220db111b360fb6170ef6f3937e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B9DD956F-44F8-4CB5-B9FD-9269C3E931F2",
"versionEndExcluding": null,
"versionEndIncluding": "1.9.12",
"versionSta... | [
"787"
] | 787 | https://github.com/michaelrsweet/htmldoc/issues/426 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | Hello, I found a heap-buffer-overflow in write_node
Reporter:
dramthy from Topsec Alpha Lab
test platform:
htmldoc Version :current
OS :Ubuntu 20.04.1 LTS aarch64
kernel: 5.4.0-53-generic
compiler: gcc (Ubuntu 9.3.0-17ubuntu1~20.04) 9.3.0
reproduced:
(htmldoc with asan build option)
./htmldoc-with-as... | AddressSanitizer: heap-buffer-overflow on write_node htmldoc/htmldoc/html.cxx:588 | https://api.github.com/repos/michaelrsweet/htmldoc/issues/426/comments | 2 | 2021-05-07T02:47:11Z | 2021-05-07T10:43:05Z | https://github.com/michaelrsweet/htmldoc/issues/426 | 878,358,961 | 426 | 3,850 |
CVE-2022-34633 | 2022-07-18T23:15:12.677 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a executes crafted or incorrectly formatted sfence.vma instructions rather create an exception. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/876"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/openhwgroup/cva6/issues/876 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Hi, we are currently doing some co-simulation with cva6 and spike, and we found the decoder has an incorrect behavior when meeting a sfence.vma with non-zero rd field.
According to the ISA Specification (Volume II: RISC-V Privileged Architectures V20211203 Page 152) for the SFENCE.VMA format, instr[11:7] should be 5... | [Bug Report] incorrect SFENCE.VMA decoder | https://api.github.com/repos/openhwgroup/cva6/issues/876/comments | 1 | 2022-05-15T08:22:54Z | 2022-07-08T08:24:09Z | https://github.com/openhwgroup/cva6/issues/876 | 1,236,221,321 | 876 | 3,851 |
CVE-2022-34634 | 2022-07-18T23:15:12.733 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a executes crafted or incorrectly formatted det instructions rather create an exception. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/899"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/openhwgroup/cva6/issues/899 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Our co-simulation framework found the decoder has an incorrect behavior when execute a `dret` with non-zero rd field.
According to the Debug Specification Version 1.0.0:
> To resume execution, the debug module sets a flag which causes the hart to execute a `dret`. `dret` is an instruction that only has meaning whil... | [Bug Report] incorrect DRET decoder | https://api.github.com/repos/openhwgroup/cva6/issues/899/comments | 1 | 2022-06-03T14:34:46Z | 2022-07-08T08:23:33Z | https://github.com/openhwgroup/cva6/issues/899 | 1,259,991,150 | 899 | 3,852 |
CVE-2022-34636 | 2022-07-18T23:15:12.863 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a and RISCV-Boom commit ad64c5419151e5e886daee7084d8399713b46b4b implements the incorrect exception type when a PMA violation occurs during address translation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/905"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/openhwgroup/cva6/issues/905 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Our co-simulation framework found that the exception type of address translation PMA violation is incorrect.
In the following test case, we modify a non-leaf (level 2) PTE to zero, which means the level 2 page dictionary is at 0x0000.
0x0000 is not part of the address range of the memory, which clearly violates the... | [Bug Report] Incorrect exception type of PMA violation during address translation | https://api.github.com/repos/openhwgroup/cva6/issues/905/comments | 1 | 2022-06-08T11:33:20Z | 2023-02-07T20:30:25Z | https://github.com/openhwgroup/cva6/issues/905 | 1,264,602,708 | 905 | 3,853 |
CVE-2022-34636 | 2022-07-18T23:15:12.863 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a and RISCV-Boom commit ad64c5419151e5e886daee7084d8399713b46b4b implements the incorrect exception type when a PMA violation occurs during address translation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/905"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/riscv-boom/riscv-boom/issues/606 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"riscv-boom",
"riscv-boom"
] | **Type of issue**: bug report
**Impact**: unknown
**Development Phase**: proposal
**Other information**
Our co-simulation framework found that the exception type of address translation PMA violation is incorrect.
In the following test case, we modify a non-leaf (level 2) PTE to zero, which means the level 2 p... | [Bug Report] Incorrect exception type of PMA violation during address translation | https://api.github.com/repos/riscv-boom/riscv-boom/issues/606/comments | 0 | 2022-06-08T14:17:55Z | 2022-06-08T14:25:14Z | https://github.com/riscv-boom/riscv-boom/issues/606 | 1,264,831,498 | 606 | 3,854 |
CVE-2022-34637 | 2022-07-18T23:15:12.923 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a implements an incorrect exception type when an illegal virtual address is loaded. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/904"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/openhwgroup/cva6/issues/904 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Our co-simulation framework found that the exception type when access/load/store an illegal virtual address is incorrect.
In the following test case, we flipped the MSB of a legal virtual address and load with it at 0x00002980.
cva6 throws an access fault, while spike throws a page fault.
Since page fault has been... | [Bug Report] Incorrect exception type for illegal virtual address access | https://api.github.com/repos/openhwgroup/cva6/issues/904/comments | 1 | 2022-06-07T17:58:21Z | 2023-02-07T20:36:18Z | https://github.com/openhwgroup/cva6/issues/904 | 1,263,672,668 | 904 | 3,855 |
CVE-2022-34639 | 2022-07-18T23:15:12.983 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a treats non-standard fence instructions as illegal which can affect the function of the application. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/900"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openhwgroup:cva6:-:*:*:*:*:*:*:*",
"matchCriteriaId": "D73073CF-1196-4ABF-A8AE-3BE51A34519C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"755"
] | 755 | https://github.com/openhwgroup/cva6/issues/900 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Our co-simulation framework found the decoder has an incorrect behavior when execute a `fence.i`/`fence` with non-zero rd field.
As discussed before [719](https://github.com/openhwgroup/cva6/issues/719), `fence`/`fence.i` should ignores immediate, rs1, rd field. We found the patch [724](https://github.com/openhwgrou... | [Bug Report] incorrect MISC_MEM decoder | https://api.github.com/repos/openhwgroup/cva6/issues/900/comments | 2 | 2022-06-03T15:46:03Z | 2022-07-08T08:23:25Z | https://github.com/openhwgroup/cva6/issues/900 | 1,260,064,333 | 900 | 3,856 |
CVE-2022-34641 | 2022-07-18T23:15:13.087 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a and RISCV-Boom commit ad64c5419151e5e886daee7084d8399713b46b4b implements the incorrect exception type when a PMP violation occurs during address translation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/906"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/openhwgroup... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boom-core:riscvc-boom:-:*:*:*:*:*:*:*",
"matchCriteriaId": "1507C03F-AB2F-4B03-BC3F-29B9B3690AD6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"755"
] | 755 | https://github.com/openhwgroup/cva6/issues/906 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"openhwgroup",
"cva6"
] | Our co-simulation framework found that the exception type of address translation PMP violation is incorrect.
In the following test case, we let a non-leaf (level 2) PTE out of the PMP range.
Next, we will perform a store operation with a special virtual address, during translation processor will try to access the P... | [Bug Report] Incorrect exception type of PMP violation during address translation | https://api.github.com/repos/openhwgroup/cva6/issues/906/comments | 5 | 2022-06-08T13:53:25Z | 2022-06-09T13:17:37Z | https://github.com/openhwgroup/cva6/issues/906 | 1,264,790,945 | 906 | 3,857 |
CVE-2022-34641 | 2022-07-18T23:15:13.087 | CVA6 commit d315ddd0f1be27c1b3f27eb0b8daf471a952299a and RISCV-Boom commit ad64c5419151e5e886daee7084d8399713b46b4b implements the incorrect exception type when a PMP violation occurs during address translation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/openhwgroup/cva6/issues/906"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/openhwgroup... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boom-core:riscvc-boom:-:*:*:*:*:*:*:*",
"matchCriteriaId": "1507C03F-AB2F-4B03-BC3F-29B9B3690AD6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"755"
] | 755 | https://github.com/riscv-boom/riscv-boom/issues/605 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"riscv-boom",
"riscv-boom"
] | **Type of issue**: bug report
**Impact**: unknown
**Development Phase**: proposal
**Other information**
Our co-simulation framework found that the exception type of address translation PMP violation is incorrect.
In the following test case, we let a non-leaf (level 2) PTE out of the PMP range.
Next, we will ... | [Bug Report] Incorrect exception type of PMP violation during address translation | https://api.github.com/repos/riscv-boom/riscv-boom/issues/605/comments | 0 | 2022-06-08T14:10:39Z | 2022-06-08T14:10:39Z | https://github.com/riscv-boom/riscv-boom/issues/605 | 1,264,818,299 | 605 | 3,858 |
CVE-2022-34643 | 2022-07-18T23:15:13.200 | RISCV ISA Sim commit ac466a21df442c59962589ba296c702631e041b5 implements the incorrect exception priotrity when accessing memory. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/riscv-software-src/riscv-isa-sim/issues/971"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:riscv:spike_risc-v_isa_simulator:-:*:*:*:*:*:*:*",
"matchCriteriaId": "CBDDC845-73D1-4788-888D-1F71F54951EF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"755"
] | 755 | https://github.com/riscv-software-src/riscv-isa-sim/issues/971 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"riscv-software-src",
"riscv-isa-sim"
] | Let's take the load instruction as an example:
https://github.com/riscv-software-src/riscv-isa-sim/blob/0f15aa09005a12521c27005515e088cbd1b81629/riscv/mmu.h#L99-L125
At line 101, load will first check if it is aligned, then at line 122 it will try to access the address in the load_slow_path function.
https://g... | [Bug Report] Wrong exception priority during access memory | https://api.github.com/repos/riscv-software-src/riscv-isa-sim/issues/971/comments | 6 | 2022-04-11T13:48:47Z | 2022-12-05T12:43:41Z | https://github.com/riscv-software-src/riscv-isa-sim/issues/971 | 1,200,004,978 | 971 | 3,859 |
CVE-2022-34025 | 2022-07-19T19:15:10.750 | Vesta v1.0.0-5 was discovered to contain a cross-site scripting (XSS) vulnerability via the post function at /web/api/v1/upload/UploadHandler.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/serghey-rodin/vesta/issues/2252"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vestacp:vesta_control_panel:1.0.0-5:*:*:*:*:*:*:*",
"matchCriteriaId": "948D4423-7EA2-4FB2-90A7-B7E5D3BD3B1C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"79"
] | 79 | https://github.com/serghey-rodin/vesta/issues/2252 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"serghey-rodin",
"vesta"
] | Hello,
I would like to report for possible XSS vulnerability.
In file https://github.com/serghey-rodin/vesta/blob/master/web/api/v1/upload/UploadHandler.php
the source in function post
```php
public function post($print_response = true) {
//....
// the source $_FILES[$this->options['par... | Possible XSS Vulnerability | https://api.github.com/repos/outroll/vesta/issues/2252/comments | 6 | 2022-06-06T12:55:48Z | 2022-07-27T10:49:06Z | https://github.com/outroll/vesta/issues/2252 | 1,261,807,957 | 2,252 | 3,860 |
CVE-2022-2476 | 2022-07-19T20:15:11.303 | A null pointer dereference bug was found in wavpack-5.4.0 The results from the ASAN log: AddressSanitizer:DEADLYSIGNAL ===================================================================84257==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x561b47a970c6 bp 0x7fff13952fb0 sp 0x7fff1394fca0 T0) ==84... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dbry/WavPack/issues/121"
},
{
"source": "secalert@redhat.com",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wavpack:wavpack:5.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3FA5388B-91D0-45C6-BEC9-4953666966D7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"476"
] | 476 | https://github.com/dbry/WavPack/issues/121 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dbry",
"WavPack"
] | Hi, I found a null pointer dereference at cli/wvunpack.c:911
Here's ASAN log:
AddressSanitizer:DEADLYSIGNAL
=================================================================
==84257==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x561b47a970c6 bp 0x7fff13952fb0 sp 0x7fff139... | Null pointer dereference at cli/wvunpack.c | https://api.github.com/repos/dbry/WavPack/issues/121/comments | 1 | 2022-07-05T07:09:55Z | 2024-03-16T03:44:06Z | https://github.com/dbry/WavPack/issues/121 | 1,293,883,996 | 121 | 3,861 |
CVE-2022-35569 | 2022-07-20T18:15:08.673 | Blogifier v3.0 was discovered to contain an arbitrary file upload vulnerability at /api/storage/upload/PostImage. This vulnerability allows attackers to execute arbitrary web scripts or HTML via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/blogifierdotnet/Blogifier/issues/316"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blogifier:blogifier:3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AA07869B-835C-41C0-B00C-B776C312BC7B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/blogifierdotnet/Blogifier/issues/316 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"blogifierdotnet",
"Blogifier"
] | **Describe the bug**
Stored XSS exists in Blogifier 3.0 via filename parameter in '/api/storage/upload/PostImage'.
**Steps to reproduce**
1. Login as admin.
2. Click on 'New post'.
3. Click on 'Insert Image' and insert the following payload `<img src=1 onerror=alert(1)>` in filename field.
4. Click on Save... | Stored XSS via filename parameter in '/api/storage/upload/PostImage' | https://api.github.com/repos/blogifierdotnet/Blogifier/issues/316/comments | 1 | 2022-07-07T15:31:55Z | 2022-07-10T02:34:36Z | https://github.com/blogifierdotnet/Blogifier/issues/316 | 1,297,647,655 | 316 | 3,862 |
CVE-2022-31151 | 2022-07-21T04:15:12.157 | Authorization headers are cleared on cross-origin redirect. However, cookie headers which are sensitive headers and are official headers found in the spec, remain uncleared. There are active users using cookie headers in undici. This may lead to accidental leakage of cookie to a 3rd-party site or a malicious attacker w... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 3.7,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nodejs/undici/issues/872"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nodejs:undici:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "6CE17D7F-0014-4379-A243-34EA094A0E05",
"versionEndExcluding": "5.7.1",
"versionEndIncluding": null,
"versionStartExc... | [
"346"
] | 346 | https://github.com/nodejs/undici/issues/872 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nodejs",
"undici"
] | ## Bug Description
Security flaw.
## Reproducible By
```js
const http = require('http');
const undici = require('undici');
const server = http.createServer((request, response) => {
if (request.headers.authorization != 'test') {
response.statusCode = 403;
response.end();
ret... | `authorization` header is not deleted on redirects to third party origins | https://api.github.com/repos/nodejs/undici/issues/872/comments | 0 | 2021-07-11T17:25:59Z | 2021-07-12T07:12:12Z | https://github.com/nodejs/undici/issues/872 | 941,498,406 | 872 | 3,863 |
CVE-2022-34037 | 2022-07-22T15:15:08.580 | An out-of-bounds read in the rewrite function at /modules/caddyhttp/rewrite/rewrite.go in Caddy v2.5.1 allows attackers to cause a Denial of Service (DoS) via a crafted URI. Note: This has been disputed as a bug, not a security vulnerability, in the Caddy web server that emerged when an administrator's bad configuratio... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/caddyserver/caddy/issues/4775"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/caddyserver/caddy/issues/4... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:caddyserver:caddy:2.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CADA4E73-FE23-4494-9BAF-66084596E46F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/caddyserver/caddy/issues/4775 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"caddyserver",
"caddy"
] | It occurs in modules/caddyhttp/rewrite/rewrite.go.
Specifically,this bug locates in `func (rewr Rewrite) rewrite`
```go
func (rewr Rewrite) rewrite(r *http.Request, repl *caddy.Replacer, logger *zap.Logger) bool {
oldMethod := r.Method
oldURI := r.RequestURI
// method
if rewr.Method != "" {
r.Method =... | [panic]: slice OOB caused by illegal uri | https://api.github.com/repos/caddyserver/caddy/issues/4775/comments | 8 | 2022-05-09T06:30:02Z | 2022-08-03T05:25:39Z | https://github.com/caddyserver/caddy/issues/4775 | 1,229,239,444 | 4,775 | 3,864 |
CVE-2022-34037 | 2022-07-22T15:15:08.580 | An out-of-bounds read in the rewrite function at /modules/caddyhttp/rewrite/rewrite.go in Caddy v2.5.1 allows attackers to cause a Denial of Service (DoS) via a crafted URI. Note: This has been disputed as a bug, not a security vulnerability, in the Caddy web server that emerged when an administrator's bad configuratio... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/caddyserver/caddy/issues/4775"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/caddyserver/caddy/issues/4... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:caddyserver:caddy:2.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CADA4E73-FE23-4494-9BAF-66084596E46F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/caddyserver/caddy/issues/4775#issuecomment-1203388116 | null | github.com | [
"caddyserver",
"caddy"
] | It occurs in modules/caddyhttp/rewrite/rewrite.go.
Specifically,this bug locates in `func (rewr Rewrite) rewrite`
```go
func (rewr Rewrite) rewrite(r *http.Request, repl *caddy.Replacer, logger *zap.Logger) bool {
oldMethod := r.Method
oldURI := r.RequestURI
// method
if rewr.Method != "" {
r.Method =... | [panic]: slice OOB caused by illegal uri | https://api.github.com/repos/caddyserver/caddy/issues/4775/comments | 8 | 2022-05-09T06:30:02Z | 2022-08-03T05:25:39Z | https://github.com/caddyserver/caddy/issues/4775 | 1,229,239,444 | 4,775 | 3,865 |
CVE-2022-34502 | 2022-07-22T15:15:08.703 | Radare2 v5.7.0 was discovered to contain a heap buffer overflow via the function consume_encoded_name_new at format/wasm/wasm.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted binary file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/issues/20336"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:5.7.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C3D7A38B-5772-4F2B-AF10-7C79AF2F18FA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/radareorg/radare2/issues/20336 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
Mon Jun 20 03:01:00 PM CST 2022
radare2 5.7.0 28296 @ linux-x86-64 git.5.7.0
commit: 09569c1d5c324df7f23bdc9ad864ac1c25925745 build: 2022-06-20__11:48:07
Linux x86_64
```
## Description
After 5.7.0 release, a heap buffer overflow can be found in function `consume_encoded_name_new` in ... | heap-buffer-overflow in WASM name handling after 5.7.0 release | https://api.github.com/repos/radareorg/radare2/issues/20336/comments | 2 | 2022-06-20T07:52:24Z | 2023-02-10T00:34:07Z | https://github.com/radareorg/radare2/issues/20336 | 1,276,517,429 | 20,336 | 3,866 |
CVE-2022-34503 | 2022-07-22T15:15:08.743 | QPDF v8.4.2 was discovered to contain a heap buffer overflow via the function QPDF::processXRefStream. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted PDF file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/qpdf/qpdf/issues/701"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qpdf_project:qpdf:8.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B51E3AFF-75A5-4484-BCBD-57E06F707375",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/qpdf/qpdf/issues/701 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"qpdf",
"qpdf"
] | Hi, I have found a heap-buffer-overflow in QPDF 8.4.2 using ASAN, which has not been reported yet. But after https://github.com/qpdf/qpdf/commit/d71f05ca07eb5c7cfa4d6d23e5c1f2a800f52e8e, the heap-buffer-overflow seems to disappear. I don't know exactly how the commit mitigate the problem since it was intended to fix si... | heap-buffer-overflow in `QPDF::processXRefStream` found by ASAN | https://api.github.com/repos/qpdf/qpdf/issues/701/comments | 6 | 2022-05-12T01:40:43Z | 2022-07-27T17:57:04Z | https://github.com/qpdf/qpdf/issues/701 | 1,233,342,875 | 701 | 3,867 |
CVE-2022-34520 | 2022-07-22T15:15:08.827 | Radare2 v5.7.2 was discovered to contain a NULL pointer dereference via the function r_bin_file_xtr_load_buffer at bin/bfile.c. This vulnerability allows attackers to cause a Denial of Service (DOS) via a crafted binary file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/issues/20354"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:5.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6E68F1D1-553D-479A-8773-ABCECDD7F1BA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"476"
] | 476 | https://github.com/radareorg/radare2/issues/20354 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
Sat Jun 25 11:13:09 AM CST 2022
radare2 5.7.3 28346 @ linux-x86-64 git.5.6.6-689-gf369ff2de
commit: f369ff2de3c807681ec76df450ee6d4af5e04ce0 build: 2022-06-24__10:39:32
```
## Description
NULL pointer dereference in function `r_bin_file_xtr_load_buffer` in `bin/bfile.c` in Radare2 5.7.... | NULL pointer dereference in `r_bin_file_xtr_load_buffer` | https://api.github.com/repos/radareorg/radare2/issues/20354/comments | 1 | 2022-06-25T03:31:59Z | 2022-06-25T15:08:52Z | https://github.com/radareorg/radare2/issues/20354 | 1,284,427,588 | 20,354 | 3,868 |
CVE-2022-25759 | 2022-07-22T20:15:09.187 | The package convert-svg-core before 0.6.2 are vulnerable to Remote Code Injection via sending an SVG file containing the payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.9,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/neocotic/convert-svg/commit/7e6031ac7427cf82cf312cb4a25040f2e6efe7a5"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:convert-svg-core_project:convert-svg-core:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "8DD21343-DE31-4E60-A591-F972FFEB4C2A",
"versionEndExcluding": "0.6.2",
"versionEndIncluding": null,
... | [
"94"
] | 94 | https://github.com/neocotic/convert-svg/issues/81 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"neocotic",
"convert-svg"
] | Affected versions of this package are vulnerable to Remote Code Injection. Using a specially crafted SVG file, an attacker could read arbitrary files from the file system and then show the file content as a converted PNG file.
<img width="1231" alt="poc" src="https://user-images.githubusercontent.com/18032641/170427... | Remote Code Injection vulnerable | https://api.github.com/repos/neocotic/convert-svg/issues/81/comments | 11 | 2022-05-26T06:05:04Z | 2022-05-29T16:19:21Z | https://github.com/neocotic/convert-svg/issues/81 | 1,249,139,609 | 81 | 3,869 |
CVE-2022-34112 | 2022-07-22T23:15:08.053 | An access control issue in the component /api/plugin/uninstall Dataease v1.11.1 allows attackers to arbitrarily uninstall the plugin, a right normally reserved for the administrator. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dataease/dataease/issues/2429"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease_project:dataease:1.11.1:*:*:*:*:*:*:*",
"matchCriteriaId": "24D016E4-391C-45A7-B7F1-32ADEECD319D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"732"
] | 732 | https://github.com/dataease/dataease/issues/2429 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dataease",
"dataease"
] | **DataEase 版本**
最新版
**运行方式(安装包运行 or 源码运行 ?)**
安装包运行
**浏览器版本**
任意
**Bug 描述**
普通权限越权卸载插件
**Bug 重现步骤(有截图更好)**
普通用户无法对插件进行处理,但是通过调用接口可对插件进行卸载:
```
POST /api/plugin/uninstall/1 HTTP/1.1
Host: xxx
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:101.0) Gecko/20100101 Firefox/101.0
Accept: ap... | [Bug]普通权限越权卸载插件 | https://api.github.com/repos/dataease/dataease/issues/2429/comments | 2 | 2022-06-15T07:59:25Z | 2022-06-17T10:34:21Z | https://github.com/dataease/dataease/issues/2429 | 1,271,826,696 | 2,429 | 3,870 |
CVE-2022-34114 | 2022-07-22T23:15:08.143 | Dataease v1.11.1 was discovered to contain a SQL injection vulnerability via the parameter dataSourceId. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dataease/dataease/issues/2430"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease_project:dataease:1.11.1:*:*:*:*:*:*:*",
"matchCriteriaId": "24D016E4-391C-45A7-B7F1-32ADEECD319D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"89"
] | 89 | https://github.com/dataease/dataease/issues/2430 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"dataease",
"dataease"
] | **DataEase 版本**
最新版
**运行方式(安装包运行 or 源码运行 ?)**
安装包运行
**浏览器版本**
任意
**Bug 描述**
任意SQL代码执行
**Bug 重现步骤(有截图更好)**
普通权限用户可调用 /dataset/table/sqlPreview 接口。
实现过程中主要需要两个参数:DataSourceId和 sql,dataSourceId可通过查看数据源获取。
```
POST /dataset/table/sqlPreview HTTP/1.1
Host: xxx
User-Agent: Mozilla/5.0 (Macintosh; I... | [Bug]任意SQL代码执行 | https://api.github.com/repos/dataease/dataease/issues/2430/comments | 2 | 2022-06-15T08:08:00Z | 2022-06-17T10:34:10Z | https://github.com/dataease/dataease/issues/2430 | 1,271,836,748 | 2,430 | 3,871 |
CVE-2022-34115 | 2022-07-22T23:15:08.183 | DataEase v1.11.1 was discovered to contain a arbitrary file write vulnerability via the parameter dataSourceId. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/dataease/dataease/issues/2428"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease_project:dataease:1.11.1:*:*:*:*:*:*:*",
"matchCriteriaId": "24D016E4-391C-45A7-B7F1-32ADEECD319D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"434"
] | 434 | https://github.com/dataease/dataease/issues/2428 | [
"Exploit",
"Issue Tracking",
"Patch",
"Release Notes",
"Third Party Advisory"
] | github.com | [
"dataease",
"dataease"
] | **DataEase 版本**
最新版
**运行方式(安装包运行 or 源码运行 ?)**
安装包运行
**浏览器版本**
任意
**Bug 描述**
任意文件跨目录写入
**Bug 重现步骤(有截图更好)**
数据源驱动管理处存在文件上传接口:
<img width="965" alt="image" src="https://user-images.githubusercontent.com/76553352/173771456-ddd78e08-1ffd-4023-94f9-b0844b13ffdc.png">
查看源代码:
<img width="901" alt="image" src=... | [Bug]任意文件跨目录写入 | https://api.github.com/repos/dataease/dataease/issues/2428/comments | 2 | 2022-06-15T07:48:58Z | 2022-06-17T10:34:31Z | https://github.com/dataease/dataease/issues/2428 | 1,271,815,035 | 2,428 | 3,872 |
CVE-2020-28471 | 2022-07-25T14:15:09.927 | This affects the package properties-reader before 2.2.0. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/steveukx/properties/commit/0877cc871db9865f58dd9389ce99e61be05380a5"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:properties-reader_project:properties-reader:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "0EAC45CB-5911-4B1E-BE80-0FF86388F09D",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null... | [
"1321"
] | 1321 | https://github.com/steveukx/properties/issues/40 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"steveukx",
"properties"
] | Steps to reproduce:
payload.properties
```
[__proto__]
polluted = polluted
```
poc.js:
```
var propertiesReader = require('properties-reader');
propertiesReader('./payload.properties');
console.log({}.polluted) // logs 'polluted'
```
| Snyk - potential prototype pollution | https://api.github.com/repos/steveukx/properties/issues/40/comments | 1 | 2020-12-30T06:53:37Z | 2020-12-30T07:51:36Z | https://github.com/steveukx/properties/issues/40 | 776,300,399 | 40 | 3,873 |
CVE-2021-23451 | 2022-07-25T14:15:10.260 | The package otp-generator before 3.0.0 are vulnerable to Insecure Randomness due to insecure generation of random one-time passwords, which may allow a brute-force attack. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Maheshkumar-Kakade/otp-generator/commit/b27de1ce439ae7f533cec26677e9698671275b70"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:otp-generator_project:otp-generator:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "9D861DA5-DFB3-4D11-AC8A-B28528D9CF40",
"versionEndExcluding": "3.0.0",
"versionEndIncluding": null,
... | [
"330"
] | 330 | https://github.com/Maheshkumar-Kakade/otp-generator/issues/12 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Maheshkumar-Kakade",
"otp-generator"
] | Hi,
I would like to report to you a security issue within otp-generator and I need some way to disclose it privately. You could open your DMs on Twitter or provide me with an email address. | Security issue | https://api.github.com/repos/Maheshkumar-Kakade/otp-generator/issues/12/comments | 3 | 2021-07-16T12:25:45Z | 2023-03-31T12:56:46Z | https://github.com/Maheshkumar-Kakade/otp-generator/issues/12 | 946,246,538 | 12 | 3,874 |
CVE-2022-21802 | 2022-07-25T14:15:10.817 | The package grapesjs before 0.19.5 are vulnerable to Cross-site Scripting (XSS) due to an improper sanitization of the class name in Selector Manager. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/artf/grapesjs/commit/13e85d152d486b968265c4b8017e8901e7d89ff3"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grapesjs:grapesjs:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "E6B41B38-278B-4B3D-9F4B-4BDD6D9466CD",
"versionEndExcluding": "0.19.5",
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/artf/grapesjs/issues/4411%23issuecomment-1167202709 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"artf",
"grapesjs"
] | ### GrapesJS version
- [X] I confirm to use the latest version of GrapesJS
### What browser are you using?
Chrome v102
### Reproducible demo link
https://jsfiddle.net/szLp8h4n
### Describe the bug
**How to reproduce the bug?**
1. Select any component
2. Add class name to Selector Manager like `<a href="#"oncli... | BUG: XSS when add class name to Selector Manager | https://api.github.com/repos/GrapesJS/grapesjs/issues/4411/comments | 3 | 2022-06-27T10:48:02Z | 2022-06-27T14:34:55Z | https://github.com/GrapesJS/grapesjs/issues/4411 | 1,285,615,447 | 4,411 | 3,875 |
CVE-2021-33437 | 2022-07-26T13:15:08.487 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There are memory leaks in frozen_cb() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"401"
] | 401 | https://github.com/cesanta/mjs/issues/160 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-5794-frozen_cb-memor... | AddressSanitizer: 1 memory leaks of frozen_cb() | https://api.github.com/repos/cesanta/mjs/issues/160/comments | 0 | 2021-05-19T08:38:25Z | 2021-05-19T08:38:25Z | https://github.com/cesanta/mjs/issues/160 | 895,159,181 | 160 | 3,876 |
CVE-2021-33438 | 2022-07-26T13:15:08.630 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is stack buffer overflow in json_parse_array() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/cesanta/mjs/issues/158 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-5fb78-json_parse_arr... | AddressSanitizer: stack-buffer-overflow in json_parse_array() mjs.c:5952 | https://api.github.com/repos/cesanta/mjs/issues/158/comments | 0 | 2021-05-19T08:36:33Z | 2021-05-19T08:36:33Z | https://github.com/cesanta/mjs/issues/158 | 895,156,817 | 158 | 3,877 |
CVE-2021-33440 | 2022-07-26T13:15:08.717 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in mjs_bcode_commit() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/cesanta/mjs/issues/163 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-7954-mjs_bcode_commi... | A NULL pointer dereference in the function mjs_bcode_commit() mjs.c:8051 | https://api.github.com/repos/cesanta/mjs/issues/163/comments | 0 | 2021-05-19T08:40:50Z | 2021-05-19T08:40:50Z | https://github.com/cesanta/mjs/issues/163 | 895,161,871 | 163 | 3,879 |
CVE-2021-33441 | 2022-07-26T13:15:08.757 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in exec_expr() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/cesanta/mjs/issues/165 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-9035-exec_expr-null-... | A NULL pointer dereference in the function exec_expr() mjs.c:9144 | https://api.github.com/repos/cesanta/mjs/issues/165/comments | 0 | 2021-05-19T08:42:37Z | 2021-05-19T08:42:37Z | https://github.com/cesanta/mjs/issues/165 | 895,163,896 | 165 | 3,880 |
CVE-2021-33442 | 2022-07-26T13:15:08.803 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is NULL pointer dereference in json_printf() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/cesanta/mjs/issues/161 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-6368-json_printf-nul... | A NULL pointer dereference in the function json_printf() mjs.c:6396 | https://api.github.com/repos/cesanta/mjs/issues/161/comments | 0 | 2021-05-19T08:39:12Z | 2021-05-19T08:39:12Z | https://github.com/cesanta/mjs/issues/161 | 895,160,290 | 161 | 3,881 |
CVE-2021-33443 | 2022-07-26T13:15:08.847 | An issue was discovered in mjs (mJS: Restricted JavaScript engine), ES6 (JavaScript version 6). There is stack buffer overflow in mjs_execute() in mjs.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/Clingto/bb632c0c463f4b2c97e4f65f751c5e6d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mjs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B1A3EF-A920-4FB4-BD11-F97092B362F7",
"versionEndExcluding": "2.20.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/cesanta/mjs/issues/167 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cesanta",
"mjs"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, mjs (latest master 4c870e5)
Compile Command:
```
$ gcc -fsanitize=address -fno-omit-frame-pointer -DMJS_MAIN mjs.c -ldl -g -o mjs
```
Run Command:
```
$ mjs -f $POC
```
POC file:
https://github.com/Clingto/POC/blob/master/MSA/mjs/mjs-9522-mjs_execute-sta... | AddressSanitizer: stack-buffer-overflow in mjs_execute mjs.c:9650 | https://api.github.com/repos/cesanta/mjs/issues/167/comments | 0 | 2021-05-19T08:44:06Z | 2021-05-19T08:44:06Z | https://github.com/cesanta/mjs/issues/167 | 895,165,377 | 167 | 3,882 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.