cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-27477 | 2022-04-10T21:15:09.243 | Newbee-Mall v1.0.0 was discovered to contain an arbitrary file upload via the Upload function at /admin/goods/edit. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/newbee-ltd/newbee-mall/issues/63"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:newbee-mall_project:newbee-mall:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2D0A6046-1A4C-488F-B8BF-6E0A3A50E5DC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"434"
] | 434 | https://github.com/newbee-ltd/newbee-mall/issues/63 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"newbee-ltd",
"newbee-mall"
] | [Suggested description]
A file upload vulnerability exists in NewBee mall. Because the upload method of uploadcontroller can bypass the upload restriction by modifying the file format suffix.
[Vulnerability Type]
File upload vulnerability
[Vendor of Product]
https://github.com/newbee-ltd/newbee-mall
[Aff... | There is a File upload vulnerability exists in newbee-mall | https://api.github.com/repos/newbee-ltd/newbee-mall/issues/63/comments | 0 | 2022-03-03T02:35:48Z | 2022-11-03T08:53:39Z | https://github.com/newbee-ltd/newbee-mall/issues/63 | 1,157,900,793 | 63 | 3,480 |
CVE-2022-27041 | 2022-04-11T14:15:09.227 | Due to lack of protection, parameter student_id in OpenSIS Classic 8.0 /modules/eligibility/Student.php can be used to inject SQL queries to extract information from databases. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/OS4ED/openSIS-Classic/issues/248"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Track... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:os4ed:opensis:8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "20B5286C-4CFF-4710-8D23-C76669FADFE7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/OS4ED/openSIS-Classic/issues/248 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"OS4ED",
"openSIS-Classic"
] | Due to lack of protection, parameter `student_id` in /modules/eligibility/Student.php can be abused to injection SQL queries to extract information from databases.
**POC:**
---
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (original value)
Payload: /openSIS-Classic-8.0/Ajax... | SQL Injection in /modules/eligibility/Student.php | https://api.github.com/repos/OS4ED/openSIS-Classic/issues/248/comments | 1 | 2022-03-07T15:07:24Z | 2022-03-31T12:10:21Z | https://github.com/OS4ED/openSIS-Classic/issues/248 | 1,161,541,811 | 248 | 3,481 |
CVE-2022-27115 | 2022-04-11T15:15:09.187 | In Studio-42 elFinder 2.1.60, there is a vulnerability that causes remote code execution through file name bypass for file upload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Studio-42/elFinder/issues/3458"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:std42:elfinder:2.1.60:*:*:*:*:*:*:*",
"matchCriteriaId": "183D9350-7C50-462D-A351-EBC1752B4C02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/Studio-42/elFinder/issues/3458 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Studio-42",
"elFinder"
] | **Describe the bug**
Filename bypass leading to Remote Code Execution
**To Reproduce**
Steps to reproduce the behavior:
1. Upload a file with `a<?php phpinfo();?>` named shell.php, Note: the letter 'a' at the beginning of the content cannot be omitted.
2. Add two dots after the file name like this `shell.php..`... | Filename bypass leading to RCE | https://api.github.com/repos/Studio-42/elFinder/issues/3458/comments | 2 | 2022-02-20T17:25:31Z | 2022-03-09T15:05:25Z | https://github.com/Studio-42/elFinder/issues/3458 | 1,145,083,051 | 3,458 | 3,482 |
CVE-2022-27156 | 2022-04-11T15:15:09.223 | Daylight Studio Fuel CMS 1.5.1 is vulnerable to HTML Injection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/593"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F3A806A2-582F-49B6-B9EC-C0FB4B13ED3D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/daylightstudio/FUEL-CMS/issues/593 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | A HTML Injection issue is affecting the application.
STEP 1:

STEP 2:

| HTML Injection Issue | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/593/comments | 2 | 2022-03-13T16:39:35Z | 2022-07-30T22:42:59Z | https://github.com/daylightstudio/FUEL-CMS/issues/593 | 1,167,630,562 | 593 | 3,483 |
CVE-2022-24815 | 2022-04-11T20:15:20.217 | JHipster is a development platform to quickly generate, develop, & deploy modern web applications & microservice architectures. SQL Injection vulnerability in entities for applications generated with the option "reactive with Spring WebFlux" enabled and an SQL database using r2dbc. Applications created without "reactiv... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jhipster/generator-jhipster/commit/c220a210fd7742c53eea72bd5fadbb96220faa98"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jhipster:generator-jhipster:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "056A57BE-F484-4FE0-B0A0-A4ADB5DCEBE0",
"versionEndExcluding": "7.8.1",
"versionEndIncluding": null,
"v... | [
"89"
] | 89 | https://github.com/jhipster/generator-jhipster/issues/18269 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jhipster",
"generator-jhipster"
] | I don't know whether this is the right place to ask this though...
In a reactive spring project with r2dbc, I found that SQL injection is actually possible. This may happen because of me, lacking knowledge on how to use r2dbc correctly. If it is case please let me know the correct usage.
#### Setup
- Jhipster 7.... | SQL Injection in Reactive project | https://api.github.com/repos/jhipster/generator-jhipster/issues/18269/comments | 35 | 2022-04-03T23:08:46Z | 2022-04-07T16:08:27Z | https://github.com/jhipster/generator-jhipster/issues/18269 | 1,191,074,778 | 18,269 | 3,484 |
CVE-2022-24837 | 2022-04-11T21:15:08.703 | HedgeDoc is an open-source, web-based, self-hosted, collaborative markdown editor. Images uploaded with HedgeDoc version 1.9.1 and later have an enumerable filename after the upload, resulting in potential information leakage of uploaded documents. This is especially relevant for private notes and affects all upload ba... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/hedgedoc/hedgedoc/commit/9e2f9e21e904c4a319e84265da7ef03b0a8e343a"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hedgedoc:hedgedoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5ED58E51-742B-41E3-8526-5CA73D46E4FE",
"versionEndExcluding": "1.9.3",
"versionEndIncluding": null,
"versionStartExclu... | [
"434"
] | 434 | https://github.com/node-formidable/formidable/issues/808 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"node-formidable",
"formidable"
] | Whenever i encounter a "need to generate a uniq filename" and including dependencies and so forth like hexoid to generate them https://github.com/node-formidable/formidable/blob/1618ea060326d8c510cf19f06600b79186c84f98/package.json#L34
and seeing stuff like:
https://github.com/node-formidable/formidable/blob/1618ea06... | uniq filenames | https://api.github.com/repos/node-formidable/formidable/issues/808/comments | 3 | 2022-01-02T21:39:54Z | 2022-04-02T23:49:04Z | https://github.com/node-formidable/formidable/issues/808 | 1,092,106,352 | 808 | 3,485 |
CVE-2022-29080 | 2022-04-12T05:15:07.447 | The npm-dependency-versions package through 0.3.0 for Node.js allows command injection if an attacker is able to call dependencyVersions with a JSON object in which pkgs is a key, and there are shell metacharacters in a value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/barneycarroll/npm-dependency-versions/issues/6"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:npm-dependency-versions_project:npm-dependency-versions:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D19A9D7F-8667-48BA-9460-526BCD8557B6",
"versionEndExcluding": null,
"versionEndIncludi... | [
"78"
] | 78 | https://github.com/barneycarroll/npm-dependency-versions/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"barneycarroll",
"npm-dependency-versions"
] | Hi,
Thanks for devloping this great npm package! We find a potential command injection vulnerabilty from it. The bug is caused by the fact that package-exported method fail to sanitize `pkgs` parameter and let it flow into a sensitive command execution API.
Here is the proof of concept.
```javascript
const depe... | Potential command injection vulnerability in npm-dependency-versions | https://api.github.com/repos/barneycarroll/npm-dependency-versions/issues/6/comments | 0 | 2022-04-06T19:49:43Z | 2022-04-06T19:49:43Z | https://github.com/barneycarroll/npm-dependency-versions/issues/6 | 1,195,102,405 | 6 | 3,486 |
CVE-2022-27161 | 2022-04-12T16:15:08.777 | Csz Cms 1.2.2 is vulnerable to SQL Injection via cszcms_admin_Members_viewUsers | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/43"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "00DCD2B8-2F52-4BF9-8404-06760D8F6647",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/43 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | Exploit Title: SQL Injection vulnerability on cszcms_admin_Members_viewUsers
Date: 11-March-2022
Exploit Author: [@Limerence9](https://github.com/Limerence9)
Software Link: https://github.com/cskaza/cszcms/archive/refs/tags/1.2.2.zip
Version: 1.2.2
Description:
SQL Injection allows an attacker to run malicious ... | SQL Injection vulnerability on cszcms_admin_Members_viewUsers | https://api.github.com/repos/cskaza/cszcms/issues/43/comments | 0 | 2022-03-14T03:38:29Z | 2022-04-13T08:35:33Z | https://github.com/cskaza/cszcms/issues/43 | 1,167,844,791 | 43 | 3,487 |
CVE-2022-27162 | 2022-04-12T16:15:08.830 | CSZ CMS 1.2.2 is vulnerable to SQL Injection via cszcms_admin_Members_editUser | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/44"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "00DCD2B8-2F52-4BF9-8404-06760D8F6647",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/44 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | Exploit Title: SQL Injection vulnerability on cszcms_admin_Members_editUser
Date: 11-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/cskaza/cszcms/archive/refs/tags/1.2.2.zip
Version: 1.2.2
Description:
SQL Injection allows an attacker to run malicious... | SQL Injection vulnerability on cszcms_admin_Members_editUser | https://api.github.com/repos/cskaza/cszcms/issues/44/comments | 0 | 2022-03-14T03:39:56Z | 2022-04-13T12:51:48Z | https://github.com/cskaza/cszcms/issues/44 | 1,167,845,366 | 44 | 3,488 |
CVE-2022-27163 | 2022-04-12T16:15:08.877 | CSZ CMS 1.2.2 is vulnerable to SQL Injection via cszcms_admin_Users_editUser | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/45"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "00DCD2B8-2F52-4BF9-8404-06760D8F6647",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/45 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | Exploit Title: SQL Injection vulnerability on cszcms_admin_Users_editUser
Date: 11-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/cskaza/cszcms/archive/refs/tags/1.2.2.zip
Version: 1.2.2
Description:
SQL Injection allows an attacker to run malicious S... | SQL Injection vulnerability on cszcms_admin_Users_editUser | https://api.github.com/repos/cskaza/cszcms/issues/45/comments | 0 | 2022-03-14T03:44:05Z | 2022-04-13T12:51:35Z | https://github.com/cskaza/cszcms/issues/45 | 1,167,846,925 | 45 | 3,489 |
CVE-2022-27164 | 2022-04-12T16:15:08.923 | CSZ CMS 1.2.2 is vulnerable to SQL Injection via cszcms_admin_Users_viewUsers | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/42"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "00DCD2B8-2F52-4BF9-8404-06760D8F6647",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/42 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | Exploit Title: SQL Injection vulnerability on cszcms_admin_Users_viewUsers
Date: 11-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/cskaza/cszcms/archive/refs/tags/1.2.2.zip
Version: 1.2.2
Description:
SQL Injection allows an attacker to run malicious ... | SQL Injection vulnerability on cszcms_admin_Users_viewUsers | https://api.github.com/repos/cskaza/cszcms/issues/42/comments | 0 | 2022-03-14T03:37:15Z | 2022-04-13T12:52:05Z | https://github.com/cskaza/cszcms/issues/42 | 1,167,844,254 | 42 | 3,490 |
CVE-2022-27165 | 2022-04-12T16:15:08.980 | CSZ CMS 1.2.2 is vulnerable to SQL Injection via cszcms_admin_Plugin_manager_setstatus | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/41"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "00DCD2B8-2F52-4BF9-8404-06760D8F6647",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/41 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | Exploit Title: SQL Injection vulnerability on cszcms_admin_Plugin_manager_setstatus
Date: 11-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/cskaza/cszcms/archive/refs/tags/1.2.2.zip
Version: 1.2.2
Description:
SQL Injection allows an attacker to run m... | SQL Injection vulnerability on cszcms_admin_Plugin_manager_setstatus | https://api.github.com/repos/cskaza/cszcms/issues/41/comments | 0 | 2022-03-14T03:35:23Z | 2022-04-13T12:52:14Z | https://github.com/cskaza/cszcms/issues/41 | 1,167,843,413 | 41 | 3,491 |
CVE-2022-28032 | 2022-04-12T16:15:09.207 | AtomCMS 2.0 is vulnerable to SQL Injection via Atom.CMS_admin_ajax_pages.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thedigicraft/Atom.CMS/issues/263"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedigitalcraft:atomcms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8949C5AC-7D10-43A8-929D-B6FCFE9F2DC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/thedigicraft/Atom.CMS/issues/263 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thedigicraft",
"Atom.CMS"
] | Exploit Title: SQL Injection vulnerability on Atom.CMS_admin_ajax_pages.php
Date: 21-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/thedigicraft/Atom.CMS
Version: AtomCMS 2.0
Description:
SQL Injection allows an attacker to run malicious SQL statement... | SQL Injection vulnerability on Atom.CMS_admin_ajax_pages.php | https://api.github.com/repos/thedigicraft/Atom.CMS/issues/263/comments | 2 | 2022-03-21T09:10:59Z | 2022-12-22T21:13:05Z | https://github.com/thedigicraft/Atom.CMS/issues/263 | 1,175,091,417 | 263 | 3,492 |
CVE-2022-28033 | 2022-04-12T16:15:09.257 | Atom.CMS 2.0 is vulnerable to SQL Injection via Atom.CMS_admin_uploads.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thedigicraft/Atom.CMS/issues/259"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedigitalcraft:atomcms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8949C5AC-7D10-43A8-929D-B6FCFE9F2DC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/thedigicraft/Atom.CMS/issues/259 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thedigicraft",
"Atom.CMS"
] | Exploit Title: SQL Injection vulnerability on Atom.CMS_admin_uploads.php
Date: 21-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/thedigicraft/Atom.CMS
Version: AtomCMS 2.0
Description:
SQL Injection allows an attacker to run malicious SQL statements o... | SQL Injection vulnerability on Atom.CMS_admin_uploads.php | https://api.github.com/repos/thedigicraft/Atom.CMS/issues/259/comments | 2 | 2022-03-21T08:09:03Z | 2022-12-22T21:14:24Z | https://github.com/thedigicraft/Atom.CMS/issues/259 | 1,175,031,558 | 259 | 3,493 |
CVE-2022-28034 | 2022-04-12T16:15:09.307 | AtomCMS 2.0 is vulnerabie to SQL Injection via Atom.CMS_admin_ajax_list-sort.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thedigicraft/Atom.CMS/issues/261"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedigitalcraft:atomcms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8949C5AC-7D10-43A8-929D-B6FCFE9F2DC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/thedigicraft/Atom.CMS/issues/261 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thedigicraft",
"Atom.CMS"
] | Exploit Title: SQL Injection vulnerability on Atom.CMS_admin_ajax_list-sort.php
Date: 21-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/thedigicraft/Atom.CMS
Version: AtomCMS 2.0
Description:
SQL Injection allows an attacker to run malicious SQL state... | SQL Injection vulnerability on Atom.CMS_admin_ajax_list-sort.php | https://api.github.com/repos/thedigicraft/Atom.CMS/issues/261/comments | 2 | 2022-03-21T08:36:04Z | 2022-12-22T21:14:02Z | https://github.com/thedigicraft/Atom.CMS/issues/261 | 1,175,057,949 | 261 | 3,494 |
CVE-2022-28035 | 2022-04-12T16:15:09.520 | Atom.CMS 2.0 is vulnerable to SQL Injection via Atom.CMS_admin_ajax_blur-save.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thedigicraft/Atom.CMS/issues/260"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedigitalcraft:atomcms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8949C5AC-7D10-43A8-929D-B6FCFE9F2DC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/thedigicraft/Atom.CMS/issues/260 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thedigicraft",
"Atom.CMS"
] | Exploit Title: SQL Injection vulnerability on Atom.CMS_admin_ajax_blur-save.php
Date: 21-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/thedigicraft/Atom.CMS
Version: AtomCMS 2.0
Description:
SQL Injection allows an attacker to run malicious SQL state... | SQL Injection vulnerability on Atom.CMS_admin_ajax_blur-save.php | https://api.github.com/repos/thedigicraft/Atom.CMS/issues/260/comments | 2 | 2022-03-21T08:20:19Z | 2022-12-22T21:14:14Z | https://github.com/thedigicraft/Atom.CMS/issues/260 | 1,175,044,266 | 260 | 3,495 |
CVE-2022-28036 | 2022-04-12T16:15:09.870 | AtomCMS 2.0 is vulnerable to SQL Injection via Atom.CMS_admin_ajax_navigation.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thedigicraft/Atom.CMS/issues/262"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedigitalcraft:atomcms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8949C5AC-7D10-43A8-929D-B6FCFE9F2DC7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"89"
] | 89 | https://github.com/thedigicraft/Atom.CMS/issues/262 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thedigicraft",
"Atom.CMS"
] | Exploit Title: SQL Injection vulnerability on Atom.CMS_admin_ajax_navigation.php
Date: 21-March-2022
Exploit Author: [@Limerence](https://github.com/xuehaobaobao)
Software Link: https://github.com/thedigicraft/Atom.CMS
Version: AtomCMS 2.0
Description:
SQL Injection allows an attacker to run malicious SQL stat... | SQL Injection vulnerability on Atom.CMS_admin_ajax_navigation.php | https://api.github.com/repos/thedigicraft/Atom.CMS/issues/262/comments | 2 | 2022-03-21T08:58:14Z | 2022-12-22T21:13:45Z | https://github.com/thedigicraft/Atom.CMS/issues/262 | 1,175,077,768 | 262 | 3,496 |
CVE-2022-27140 | 2022-04-12T17:15:09.887 | An arbitrary file upload vulnerability in the file upload module of express-fileupload 1.3.1 allows attackers to execute arbitrary code via a crafted PHP file. NOTE: the vendor's position is that the observed behavior can only occur with "intentional misusing of the API": the express-fileupload middleware is not respon... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/richardgirges/express-fileupload/issues/312#issuecomment-1134912967"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/richardgirge... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:express-fileupload_project:express-fileupload:1.3.1:*:*:*:*:node.js:*:*",
"matchCriteriaId": "C2BDDDE8-6D13-4146-93A1-0C5D16D85FF2",
"versionEndExcluding": null,
"versionEndIncluding": n... | [
"434"
] | 434 | https://github.com/richardgirges/express-fileupload/issues/312#issuecomment-1134912967 | [
"Third Party Advisory"
] | github.com | [
"richardgirges",
"express-fileupload"
] | Please have a look at CVE-2022-27261 and CVE-2022-27140 | Major security threats | https://api.github.com/repos/richardgirges/express-fileupload/issues/312/comments | 15 | 2022-04-15T08:01:56Z | 2022-05-24T01:22:49Z | https://github.com/richardgirges/express-fileupload/issues/312 | 1,205,367,038 | 312 | 3,497 |
CVE-2022-27140 | 2022-04-12T17:15:09.887 | An arbitrary file upload vulnerability in the file upload module of express-fileupload 1.3.1 allows attackers to execute arbitrary code via a crafted PHP file. NOTE: the vendor's position is that the observed behavior can only occur with "intentional misusing of the API": the express-fileupload middleware is not respon... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/richardgirges/express-fileupload/issues/312#issuecomment-1134912967"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/richardgirge... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:express-fileupload_project:express-fileupload:1.3.1:*:*:*:*:node.js:*:*",
"matchCriteriaId": "C2BDDDE8-6D13-4146-93A1-0C5D16D85FF2",
"versionEndExcluding": null,
"versionEndIncluding": n... | [
"434"
] | 434 | https://github.com/richardgirges/express-fileupload/issues/329#issuecomment-1387288644 | [
"Third Party Advisory"
] | github.com | [
"richardgirges",
"express-fileupload"
] | This package has a CVSS Score: of 9.8, which is very high.
An arbitrary file upload vulnerability in the file upload module of Express-Fileupload v1.3.1 allows attackers to execute arbitrary code via a crafted PHP file. | Unrestricted Upload of File with Dangerous Type | https://api.github.com/repos/richardgirges/express-fileupload/issues/329/comments | 9 | 2022-09-07T11:41:05Z | 2025-04-21T14:35:27Z | https://github.com/richardgirges/express-fileupload/issues/329 | 1,364,535,565 | 329 | 3,498 |
CVE-2022-27416 | 2022-04-12T20:15:08.957 | Tcpreplay v4.4.1 was discovered to contain a double-free via __interceptor_free. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.1,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/702"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://securi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"415"
] | 415 | https://github.com/appneta/tcpreplay/issues/702 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | [Bug] Double-free | https://api.github.com/repos/appneta/tcpreplay/issues/702/comments | 2 | 2022-02-05T08:53:25Z | 2022-02-11T21:36:05Z | https://github.com/appneta/tcpreplay/issues/702 | 1,124,875,048 | 702 | 3,499 |
CVE-2022-27418 | 2022-04-12T20:15:08.997 | Tcpreplay v4.4.1 has a heap-based buffer overflow in do_checksum_math at /tcpedit/checksum.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.1,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/703"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://securi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/703 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | You are opening a _bug report_ against the Tcpreplay project: we use
GitHub Issues for tracking bug reports and feature requests.
If you have a question about how to use Tcpreplay, you are at the wrong
site. You can ask a question on the [tcpreplay-users mailing list](https://sourceforge.net/p/tcpreplay/mailman/tc... | Heap-buffer-overflow in tcpreplay | https://api.github.com/repos/appneta/tcpreplay/issues/703/comments | 1 | 2022-02-05T10:45:27Z | 2022-02-12T17:56:43Z | https://github.com/appneta/tcpreplay/issues/703 | 1,124,896,906 | 703 | 3,500 |
CVE-2022-27419 | 2022-04-12T20:15:09.037 | rtl_433 21.12 was discovered to contain a stack overflow in the function acurite_00275rm_decode at /devices/acurite.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/merbanan/rtl_433/issues/2012"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rtl_433_project:rtl_433:21.12:*:*:*:*:*:*:*",
"matchCriteriaId": "9A498702-4055-4160-A6A1-E2F893BF3C47",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/merbanan/rtl_433/issues/2012 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"merbanan",
"rtl_433"
] |
# Command
```
./rtl_433 -d0 -H5 -H20 -f 433.70M -f 433.80M -f 433.90M POC1
```
[POC1.zip](https://github.com/merbanan/rtl_433/files/8297582/POC1.zip)
# ASAN
```
SUMMARY: AddressSanitizer: stack-buffer-overflow /home/zxq/CVE_testing/ASAN-install/rtl_433/src/devices/acurite.c:1244 in acurite_00275rm_decode
S... | Stack-based Buffer Overflow in rtl_433 | https://api.github.com/repos/merbanan/rtl_433/issues/2012/comments | 1 | 2022-03-18T01:29:06Z | 2022-03-18T07:10:49Z | https://github.com/merbanan/rtl_433/issues/2012 | 1,173,087,627 | 2,012 | 3,501 |
CVE-2015-20107 | 2022-04-13T16:15:08.937 | In Python (aka CPython) up to 3.10.8, the mailcap module does not add escape characters into commands discovered in the system mailcap file. This may allow attackers to inject shell commands into applications that call mailcap.findmatch with untrusted input (if they lack validation of user-provided filenames or argumen... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 8,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugs.python.org/issue24778"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pyth... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "16A21965-681C-4815-94DA-5B8EBC5EDA68",
"versionEndExcluding": null,
"versionEndIncluding": "3.7.15",
"versionStartExcludin... | [
"77"
] | 77 | https://github.com/python/cpython/issues/68966 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"python",
"cpython"
] | BPO | [24778](https://bugs.python.org/issue24778)
--- | :---
Nosy | @vstinner, @bitdancer
Files | <li>[screenshot.png](https://bugs.python.org/file40099/screenshot.png "Uploaded as image/png at 2015-08-02.08:25:06 by TheRegRunner")</li><li>[The Quote Problem.py](https://bugs.python.org/file40116/The%20Quote%20Problem.p... | [CVE-2015-20107] mailcap.findmatch: document shell command Injection danger in filename parameter | https://api.github.com/repos/python/cpython/issues/68966/comments | 55 | 2015-08-02T08:25:07Z | 2023-06-05T03:40:08Z | https://github.com/python/cpython/issues/68966 | 1,198,939,118 | 68,966 | 3,502 |
CVE-2022-24843 | 2022-04-13T22:15:08.203 | Gin-vue-admin is a backstage management system based on vue and gin, which separates the front and rear of the full stack. Gin-vue-admin 2.50 has arbitrary file read vulnerability due to a lack of parameter validation. This has been resolved in version 2.5.1. There are no known workarounds for this issue. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flipped-aurora/gin-vue-admin/issues/1002"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gin-vue-admin_project:gin-vue-admin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "750A0815-5D4A-4594-BA38-676B926FA2E4",
"versionEndExcluding": "2.5.1",
"versionEndIncluding": null,
... | [
"22"
] | 22 | https://github.com/flipped-aurora/gin-vue-admin/issues/1002 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flipped-aurora",
"gin-vue-admin"
] | ### gin-vue-admin 版本
V2.5.0b
### Node 版本
v16.3.0
### Golang 版本
go1.16.6
### 是否依旧存在
可以
### bug描述
发现了一个任意文件读取/下载安全漏洞,wx联系~
### 修改建议
参数校验下即可。 | [Bug]: Security Issues-20220402-luckyt0mat0 | https://api.github.com/repos/flipped-aurora/gin-vue-admin/issues/1002/comments | 1 | 2022-04-02T07:25:03Z | 2022-05-30T14:20:24Z | https://github.com/flipped-aurora/gin-vue-admin/issues/1002 | 1,190,537,576 | 1,002 | 3,503 |
CVE-2022-27007 | 2022-04-14T15:15:08.163 | nginx njs 0.7.2 is affected suffers from Use-after-free in njs_function_frame_alloc() when it try to invoke from a restored frame saved with njs_function_frame_save(). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/ad48705bf1f04b4221a5f5b07715ac48b3160d53"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"416"
] | 416 | https://github.com/nginx/njs/issues/469 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | This UAF was introduced in a patch for a similar bug #451, which shows that njs_await_fulfilled is still flawed.
### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 7bd570b39297d3d91902c93a624c89b08be7a6fe
Version... | Patch bypass for njs_await_fulfilled, causing UAF again | https://api.github.com/repos/nginx/njs/issues/469/comments | 3 | 2022-02-15T08:42:02Z | 2022-02-21T18:58:48Z | https://github.com/nginx/njs/issues/469 | 1,138,362,403 | 469 | 3,504 |
CVE-2022-27008 | 2022-04-14T15:15:08.207 | nginx njs 0.7.2 is vulnerable to Buffer Overflow. Type confused in Array.prototype.concat() when a slow array appended element is fast array. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/e673ae41a998d1391bd562edb2ed6d49db7cc716"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"120"
] | 120 | https://github.com/nginx/njs/issues/471 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | ### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 7bd570b39297d3d91902c93a624c89b08be7a6fe
Version : 0.7.2
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -... | SEGV njs_array.c:335:41 in njs_array_add | https://api.github.com/repos/nginx/njs/issues/471/comments | 0 | 2022-02-15T09:26:33Z | 2022-02-21T16:55:07Z | https://github.com/nginx/njs/issues/471 | 1,138,411,189 | 471 | 3,505 |
CVE-2022-28041 | 2022-04-15T14:15:07.570 | stb_image.h v2.27 was discovered to contain an integer overflow via the function stbi__jpeg_decode_block_prog_dc. This vulnerability allows attackers to cause a Denial of Service (DoS) via unspecified vectors. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nothings/stb/issues/1292"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nothings:stb_image.h:2.27:*:*:*:*:*:*:*",
"matchCriteriaId": "026BA031-EE47-451B-8A8C-1CE5F0233D27",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"190"
] | 190 | https://github.com/nothings/stb/issues/1292 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nothings",
"stb"
] | **Describe the bug**
`UBSAN: runtime error: signed integer overflow: -126340289 * 17 cannot be represented in type 'int'`
and
`UBSAN: runtime error: signed integer overflow: -2147450975 + -32767 cannot be represented in type 'int'`
**To Reproduce**
Built stb according to [the oss-fuzz script](https://github.com/... | UBSAN: integer overflow | https://api.github.com/repos/nothings/stb/issues/1292/comments | 2 | 2022-02-17T15:52:07Z | 2023-01-29T23:47:29Z | https://github.com/nothings/stb/issues/1292 | 1,141,520,739 | 1,292 | 3,506 |
CVE-2022-28042 | 2022-04-15T14:15:07.617 | stb_image.h v2.27 was discovered to contain an heap-based use-after-free via the function stbi__jpeg_huff_decode. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nothings/stb/issues/1289"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nothings:stb_image.h:2.27:*:*:*:*:*:*:*",
"matchCriteriaId": "026BA031-EE47-451B-8A8C-1CE5F0233D27",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"416"
] | 416 | https://github.com/nothings/stb/issues/1289 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nothings",
"stb"
] | **Describe the bug**
UndefinedBehaviorSanitizer: undefined-behavior: index out of bounds + AddressSanitizer: heap-use-after-free in stbi__jpeg_huff_decode.
**To Reproduce**
Built stb according to [the oss-fuzz script](https://github.com/nothings/stb/blob/master/tests/ossfuzz.sh) with `CXXFLAGS='-O1 -fsanitize=addr... | AddressSanitizer: heap-use-after-free in stbi__jpeg_huff_decode | https://api.github.com/repos/nothings/stb/issues/1289/comments | 3 | 2022-02-17T11:13:28Z | 2023-01-29T23:47:59Z | https://github.com/nothings/stb/issues/1289 | 1,141,200,788 | 1,289 | 3,507 |
CVE-2022-28044 | 2022-04-15T14:15:07.660 | Irzip v0.640 was discovered to contain a heap memory corruption via the component lrzip.c:initialise_control. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ckolivas/lrzip/commit/5faf80cd53ecfd16b636d653483144cd12004f46"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:irzip_project:irzip:0.640:*:*:*:*:*:*:*",
"matchCriteriaId": "F5AAC36E-7E82-4270-8613-147AA67393E8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/ckolivas/lrzip/issues/216 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ckolivas",
"lrzip"
] | The `suffix` field in the `static rzip_control` structure is initialized to point to global memory in [initialize_control](https://github.com/ckolivas/lrzip/blob/64eb4a8c37aead0b473a06d515bc348f23f3a1e7/lrzip.c#L1341)
https://github.com/ckolivas/lrzip/blob/64eb4a8c37aead0b473a06d515bc348f23f3a1e7/lrzip.c#L1341
a... | Deallocation of control->suffix corrupts Heap Memory | https://api.github.com/repos/ckolivas/lrzip/issues/216/comments | 5 | 2022-02-24T18:06:02Z | 2022-05-12T23:53:00Z | https://github.com/ckolivas/lrzip/issues/216 | 1,149,589,254 | 216 | 3,508 |
CVE-2022-28048 | 2022-04-15T14:15:07.703 | STB v2.27 was discovered to contain an integer shift of invalid size in the component stbi__jpeg_decode_block_prog_ac. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nothings/stb/issues/1293"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:stb_project:stb:2.27:*:*:*:*:*:*:*",
"matchCriteriaId": "4EE9CD8E-67B3-4D15-A7D3-FD54FEE21B79",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"682"
] | 682 | https://github.com/nothings/stb/issues/1293 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nothings",
"stb"
] | **Describe the bug**
Several `UBSAN runtime error: shift exponent 32 is too large for 32-bit type 'unsigned int'` and similar
**To Reproduce**
Built stb according to [the oss-fuzz script](https://github.com/nothings/stb/blob/master/tests/ossfuzz.sh) with `CXXFLAGS='-O1 -fsanitize=address -fsanitize=array-bounds,bo... | UBSAN: shift exponent is too large | https://api.github.com/repos/nothings/stb/issues/1293/comments | 4 | 2022-02-17T15:56:39Z | 2023-06-30T00:36:04Z | https://github.com/nothings/stb/issues/1293 | 1,141,526,489 | 1,293 | 3,509 |
CVE-2022-28049 | 2022-04-15T14:15:07.747 | NGINX NJS 0.7.2 was discovered to contain a NULL pointer dereference via the component njs_vmcode_array at /src/njs_vmcode.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/f65981b0b8fcf02d69a40bc934803c25c9f607ab"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nul... | [
"476"
] | 476 | https://github.com/nginx/njs/issues/473 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nginx",
"njs"
] | Hi,
this bug was found by fuzzing the current master branch, to reproduce build the OSS-Fuzz harness with ASan and UBSan.
The bug is a write to a NULL pointer, this is the sanitizer report:
```
INFO: Seed: 2125423890
INFO: Loaded 1 modules (53334 inline 8-bit counters): 53334 [0x95f010, 0x96c066),
INFO: Lo... | Null pointer dereference in src/njs_vmcode.c:1049:17 | https://api.github.com/repos/nginx/njs/issues/473/comments | 0 | 2022-02-17T15:51:14Z | 2022-02-21T16:55:08Z | https://github.com/nginx/njs/issues/473 | 1,141,519,666 | 473 | 3,510 |
CVE-2022-27365 | 2022-04-15T18:15:10.330 | Cscms Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the component dance_Dance.php_del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/12#issue-1170440183"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1865339A-4927-439D-9D16-D38C8330CB92",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/12#issue-1170440183 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | ##### SQL injection vulnerability exists in Cscms music portal system v4.2
There is a SQL blind injection vulnerability in dance_Dance.php_del
#### Details
Add a song after administrator login

POC
```
... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/12/comments | 0 | 2022-03-16T01:45:29Z | 2022-03-16T01:45:29Z | https://github.com/chshcms/cscms/issues/12 | 1,170,440,183 | 12 | 3,511 |
CVE-2022-27366 | 2022-04-15T18:15:10.383 | Cscms Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the component dance_Dance.php_hy. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/13#issue-1170447891"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1865339A-4927-439D-9D16-D38C8330CB92",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/13#issue-1170447891 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### There is a SQL blind injection vulnerability in dance_Dance.php_hy
#### Details
Add a song after administrator login

Add songs first and then delete them into the trash

```
POST /admin.php/dance/admin/topic/save HTT... | SQL injection vulnerability exists in Cscms music portal system v4.2(dance_Topic.php_del) | https://api.github.com/repos/chshcms/cscms/issues/14/comments | 0 | 2022-03-16T02:17:57Z | 2022-03-16T02:17:57Z | https://github.com/chshcms/cscms/issues/14 | 1,170,457,945 | 14 | 3,513 |
CVE-2022-27368 | 2022-04-15T18:15:10.497 | Cscms Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the component dance_Lists.php_zhuan. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1865339A-4927-439D-9D16-D38C8330CB92",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### SQL injection vulnerability exists in Cscms music portal system v4.2 (dance_Lists.php_zhuan)
#### Details
After the administrator logs in, the following data package is constructed
```
POST /admin.php/dance/admin/lists/zhuan HTTP/1.1
Host: cscms.test
Content-Length: 23
Accept: application/json, text/javas... | SQL injection vulnerability exists in Cscms music portal system v4.2 | https://api.github.com/repos/chshcms/cscms/issues/15/comments | 0 | 2022-03-16T02:25:23Z | 2022-03-16T02:25:23Z | https://github.com/chshcms/cscms/issues/15 | 1,170,461,847 | 15 | 3,514 |
CVE-2022-27369 | 2022-04-15T18:15:10.557 | Cscms Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the component news_News.php_hy. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1865339A-4927-439D-9D16-D38C8330CB92",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | #### There is a SQL blind injection vulnerability in news_News.php_hy
#### Details
After the administrator is logged in, a news needs to be added

```
POST /admin.php/news/admin/news/save HTTP/1.1... | SQL injection vulnerability exists in Cscms music portal system v4.2(news_News.php_hy) | https://api.github.com/repos/chshcms/cscms/issues/16/comments | 0 | 2022-03-16T02:46:24Z | 2022-03-16T02:55:29Z | https://github.com/chshcms/cscms/issues/16 | 1,170,472,919 | 16 | 3,515 |
CVE-2022-24851 | 2022-04-15T19:15:12.383 | LDAP Account Manager (LAM) is an open source web frontend for managing entries stored in an LDAP directory. The profile editor tool has an edit profile functionality, the parameters on this page are not properly sanitized and hence leads to stored XSS attacks. An authenticated user can store XSS payloads in the profile... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LDAPAccountManager/lam/commit/3c6f09a3579e048e224eb5a4c4e3eefaa8bccd49"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Pat... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ldap-account-manager:ldap_account_manager:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7FA2D90C-50A8-451A-97D2-7BAC063193F4",
"versionEndExcluding": "7.9.1",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/LDAPAccountManager/lam/issues/170 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"LDAPAccountManager",
"lam"
] | Hello..
I am a security researcher, and with my friend Manthan(@netsectuna), We reviewed the application and discovered multiple vulnerabilities.
1. Stored XSS
Description - The profile editor tool has an edit profile functionality, the parameters on this page are not properly sanitized and hence leads to stor... | Multiple vulnerabilities in LDAP Account Manager | https://api.github.com/repos/LDAPAccountManager/lam/issues/170/comments | 1 | 2022-04-10T18:07:59Z | 2022-04-11T18:43:12Z | https://github.com/LDAPAccountManager/lam/issues/170 | 1,199,128,924 | 170 | 3,516 |
CVE-2022-29020 | 2022-04-16T00:15:09.487 | ForestBlog through 2022-02-16 allows admin/profile/save userAvatar XSS during addition of a user avatar. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saysky/ForestBlog/issues/76"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:forestblog_project:forestblog:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2497593A-8430-4A7E-A483-1DB9F12D403F",
"versionEndExcluding": null,
"versionEndIncluding": "2022-02-16",
"... | [
"79"
] | 79 | https://github.com/saysky/ForestBlog/issues/76 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"saysky",
"ForestBlog"
] | 1.Edit user information and save it

2.The profile picture address in the packet capture request is changed
payload:1" onerror=alert('xss') class="1
. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wasm3/wasm3/issues/320"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wasm3_project:wasm3:0.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3189DB65-6E31-4059-A460-75F502C0B948",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/wasm3/wasm3/issues/320 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wasm3",
"wasm3"
] | I found a heap overflow vulnerability.
Wasm3 0.5.0 has an out-of-bounds write in NewCodePage (called from Compile_BranchTable).
Recommended Security Severity: High
Poc: [poc.zip](https://github.com/wasm3/wasm3/files/8499030/poc.zip)
```
$ ./wasm3 --func fib poc.wasm
Error: invalid block depth
free(): cor... | [security] Heap Overflow in NewCodePage m3_code.c:25:29 | https://api.github.com/repos/wasm3/wasm3/issues/320/comments | 2 | 2022-04-07T06:41:07Z | 2022-08-29T10:30:19Z | https://github.com/wasm3/wasm3/issues/320 | 1,195,587,768 | 320 | 3,518 |
CVE-2021-3652 | 2022-04-18T17:15:15.443 | A flaw was found in 389-ds-base. If an asterisk is imported as password hashes, either accidentally or maliciously, then instead of being inactive, any password will successfully match during authentication. This flaw allows an attacker to successfully authenticate as a user whose password was disabled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1982782"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:port389:389-ds-base:*:*:*:*:*:*:*:*",
"matchCriteriaId": "694C5EA5-0CC5-45D7-9059-1D29DBF8066D",
"versionEndExcluding": "2.0.7",
"versionEndIncluding": null,
"versionStartExc... | [
"287"
] | 287 | https://github.com/389ds/389-ds-base/issues/4817 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"389ds",
"389-ds-base"
] | **Issue Description**
If an entry contains an asterisk as the crypted password hash, binding is possible with any password for this entry
userPassword: {CRYPT}*
**Package Version and Platform:**
- Platform: openSUSE Leap 15.2
- Package and version: 389-ds-1.4.3.23~git0.f53d0132b-lp152.2.15.1.x86_64
- Browser... | CRYPT password hash with asterisk | https://api.github.com/repos/389ds/389-ds-base/issues/4817/comments | 8 | 2021-06-29T12:56:33Z | 2022-01-13T21:09:01Z | https://github.com/389ds/389-ds-base/issues/4817 | 932,630,405 | 4,817 | 3,519 |
CVE-2021-3681 | 2022-04-18T17:15:15.507 | A flaw was found in Ansible Galaxy Collections. When collections are built manually, any files in the repository directory that are not explicitly excluded via the ``build_ignore`` list in "galaxy.yml" include files in the ``.tar.gz`` file. This contains sensitive info, such as the user's Ansible Galaxy API key and any... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1989407"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ansible/galaxy/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible_automation_platform:1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "CBA4F8F3-6FC3-4ADD-BB96-A707E94AB0AB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"v... | [
"522"
] | 522 | https://github.com/ansible/galaxy/issues/1977 | [
"Third Party Advisory"
] | github.com | [
"ansible",
"galaxy"
] | From the Galaxy Admin site an admin user should be able to:
- Deprecate a Collection
- Delete a Collection Version
| Add Collection management features to Galaxy Admin site | https://api.github.com/repos/ansible/galaxy/issues/1977/comments | 3 | 2019-08-07T14:36:37Z | 2022-02-19T16:10:47Z | https://github.com/ansible/galaxy/issues/1977 | 477,968,808 | 1,977 | 3,520 |
CVE-2022-1341 | 2022-04-18T17:15:16.440 | An issue was discovered in in bwm-ng v0.6.2. An arbitrary null write exists in get_cmdln_options() function in src/options.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vgropp/bwm-ng/commit/9774f23bf78a6e6d3ae4cfe3d73bad34f2fdcd17"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bwm-ng_project:bwm-ng:0.6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "89AE42EB-83E6-49A5-8A39-E4E88777C1E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"476"
] | 476 | https://github.com/vgropp/bwm-ng/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vgropp",
"bwm-ng"
] | Hi,
In src/options.c, line 337.
// malloc() may fail, and str will be NULL.
str=(char*)malloc(strlen(pwd_entry->pw_dir)+14);
// write to Null
snprintf(str,strlen(pwd_entry->pw_dir)+14,"%s/.bwm-ng.conf",pwd_entry->pw_dir);
I think this is a vulnerability, and maybe we can patch it as following?
str=(char... | Vulnerability? Bug? Null write in the get_cmdln_options function in src/options.c. | https://api.github.com/repos/vgropp/bwm-ng/issues/26/comments | 5 | 2020-04-27T04:26:24Z | 2020-09-29T17:47:29Z | https://github.com/vgropp/bwm-ng/issues/26 | 607,222,269 | 26 | 3,521 |
CVE-2022-24859 | 2022-04-18T19:15:09.757 | PyPDF2 is an open source python PDF library capable of splitting, merging, cropping, and transforming the pages of PDF files. In versions prior to 1.27.5 an attacker who uses this vulnerability can craft a PDF which leads to an infinite loop if the PyPDF2 if the code attempts to get the content stream. The reason is th... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/py-pdf/PyPDF2/issues/329"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pypdf2_project:pypdf2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8A55FA8A-9A2D-4317-9B8E-22112A79840E",
"versionEndExcluding": "1.27.5",
"versionEndIncluding": null,
"versionStart... | [
"835"
] | 835 | https://github.com/py-pdf/PyPDF2/issues/329 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"py-pdf",
"PyPDF2"
] | When you try to get the content stream of [this attached PDF](https://github.com/mstamy2/PyPDF2/files/783085/malicious.pdf), PyPDF2 will end up in an infinite loop. So this is probably a security issue because it might be possible to denial-of-service applications using PyPDF2.
The reason is that the last while-loop... | Manipulated inline images can force PyPDF2 into an infinite loop | https://api.github.com/repos/py-pdf/pypdf/issues/329/comments | 0 | 2017-02-17T11:55:45Z | 2022-04-15T11:55:29Z | https://github.com/py-pdf/pypdf/issues/329 | 208,420,591 | 329 | 3,522 |
CVE-2022-27055 | 2022-04-19T17:15:11.497 | ecjia-daojia 1.38.1-20210202629 is vulnerable to information leakage via content/apps/installer/classes/Helper.php. When the web program is installed, a new environment file is created, and the database information is recorded, including the database record password. NOTE: the vendor disputes this because the environme... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ecjia/ecjia-daojia/blob/dfb322387e8d3d50719e44d23d793072616ff789/content/apps/installer/classes/Controllers/IndexController.php#L74-L78"
},
{
"source": "cve@mitre.org",
"tag... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ecjia:daojia:1.38.1-20210202629:*:*:*:*:*:*:*",
"matchCriteriaId": "38BF9352-2371-4A14-89B2-028410AE3AB2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"863"
] | 863 | https://github.com/ecjia/ecjia-daojia/issues/20 | [
"Third Party Advisory"
] | github.com | [
"ecjia",
"ecjia-daojia"
] | helper.php file line 315 creates the .env file Content is:$envPath = base_path() . DIRECTORY_SEPARATOR . '.env';
Its content is to create a .env file in the root directory and write the database account, password, and database name | information leakage | https://api.github.com/repos/ecjia/ecjia-daojia/issues/20/comments | 2 | 2022-03-08T11:32:51Z | 2022-04-16T10:14:43Z | https://github.com/ecjia/ecjia-daojia/issues/20 | 1,162,546,895 | 20 | 3,523 |
CVE-2022-29537 | 2022-04-20T23:15:08.777 | gp_rtp_builder_do_hevc in ietf/rtp_pck_mpeg4.c in GPAC 2.0.0 has a heap-based buffer over-read, as demonstrated by MP4Box. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2173"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7AEE044-50E9-4230-B492-A5FF18653115",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/2173 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | [BUG] heap buffer overflow in gp_rtp_builder_do_hevc | https://api.github.com/repos/gpac/gpac/issues/2173/comments | 0 | 2022-04-16T08:01:38Z | 2022-08-03T09:45:02Z | https://github.com/gpac/gpac/issues/2173 | 1,206,048,984 | 2,173 | 3,524 |
CVE-2022-29498 | 2022-04-21T05:15:06.940 | Blazer before 2.6.0 allows SQL Injection. In certain circumstances, an attacker could get a user to run a query they would not have normally run. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/ankane/blazer/issues/392"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blazer_project:blazer:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1880074A-0182-4024-82CA-26B56333D0AA",
"versionEndExcluding": "2.6.0",
"versionEndIncluding": null,
"versionStartE... | [
"89"
] | 89 | https://github.com/ankane/blazer/issues/392 | [
"Mitigation",
"Third Party Advisory"
] | github.com | [
"ankane",
"blazer"
] | Blazer queries with variables are vulnerable to SQL injection in certain cases. This vulnerability has been assigned the CVE identifier CVE-2022-29498.
Versions Affected: 2.5.0 and below
Fixed Versions: 2.6.0
## Impact
For some queries, specific variable values can modify the query rather than just the variab... | SQL injection for certain queries with variables | https://api.github.com/repos/ankane/blazer/issues/392/comments | 0 | 2022-04-20T21:38:03Z | 2022-04-20T21:38:12Z | https://github.com/ankane/blazer/issues/392 | 1,210,236,778 | 392 | 3,525 |
CVE-2022-28074 | 2022-04-22T14:15:09.587 | Halo-1.5.0 was discovered to contain a stored cross-site scripting (XSS) vulnerability via \admin\index.html#/system/tools. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/1769"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fit2cloud:halo:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C370E382-F3E0-4D9A-A9BF-C74F6695C69D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/1769 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | ### What is version of Halo has the issue?
1.5.0
### What database are you using?
Other
### What is your deployment method?
Fat Jar
### Your site address.
_No response_
### What happened?
作者你好,在部署环境的过程中,发现了一些问题。
希望在下一个版本中,能够进行一些安全的升级。
如下:
导出的文件未加密,可以修改内容,安全隐患:
用户将博客备份开源到互联网,遭到修改,可能导致存储型xss
 via el-table-column. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/asjdf/element-table-xss-test/"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/asjdf/ele... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:element-plus:element-plus:2.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "ED98E47C-4621-43A9-B9B3-82FAD54614C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/asjdf/element-table-xss-test/issues/1 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"asjdf",
"element-table-xss-test"
] | https://cs.github.com/element-plus/element-plus/blob/b8c38a9fe5365c1af99a0b2cb0ea9f9e3f68021a/packages/components/table/src/table-column/render-helper.ts#L148
They render the html as the code.
All Frontend Program used show-overflow-tooltips = true attr and concat the backend feedback into this column seems has thi... | vuln location seems like there. | https://api.github.com/repos/asjdf/element-table-xss-test/issues/1/comments | 1 | 2022-03-10T06:13:23Z | 2022-04-26T15:59:51Z | https://github.com/asjdf/element-table-xss-test/issues/1 | 1,164,797,966 | 1 | 3,527 |
CVE-2022-27103 | 2022-04-25T13:15:49.383 | element-plus 2.0.5 is vulnerable to Cross Site Scripting (XSS) via el-table-column. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/asjdf/element-table-xss-test/"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/asjdf/ele... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:element-plus:element-plus:2.0.5:*:*:*:*:*:*:*",
"matchCriteriaId": "ED98E47C-4621-43A9-B9B3-82FAD54614C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/element-plus/element-plus/issues/6514 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"element-plus",
"element-plus"
] | <!-- generated by https://issue.element-plus.org/ DO NOT REMOVE -->
Bug Type: **`Component`**
## Environment
- Vue Version: `3.2.13`
- Element Plus Version: `2.0.5`
- Browser / OS: `UserAgent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/96.0.4664.110 Safari/5... | [Bug Report] [Component] [table-column] table-column 中对于 属性 show-overflow-tooltip 处理存在问题 可以导致 XSS | https://api.github.com/repos/element-plus/element-plus/issues/6514/comments | 8 | 2022-03-10T07:47:54Z | 2022-04-10T16:18:17Z | https://github.com/element-plus/element-plus/issues/6514 | 1,164,868,186 | 6,514 | 3,528 |
CVE-2022-27428 | 2022-04-25T13:15:49.593 | A stored cross-site scripting (XSS) vulnerability in /index.php/album/add of GalleryCMS v2.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the album_name parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bensonarts/GalleryCMS/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gallerycms_project:gallerycms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "20997B61-13E1-4409-B120-2959AA893308",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/bensonarts/GalleryCMS/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bensonarts",
"GalleryCMS"
] | Alert users who are still using the project
* Conditions: Common user
The POST parameter "album_name" in the path "/index.php/album/add" has storage XSS. This can result in arbitrary JS code execution, obtaining administrator cookies to obtain administrator permissions, etc
The album name can inject XSS ```<s... | v2.0: stored XSS Vulnerability | https://api.github.com/repos/bensonarts/GalleryCMS/issues/20/comments | 0 | 2022-03-18T05:30:44Z | 2022-03-18T05:39:10Z | https://github.com/bensonarts/GalleryCMS/issues/20 | 1,173,204,267 | 20 | 3,529 |
CVE-2022-27429 | 2022-04-25T13:15:49.640 | Jizhicms v1.9.5 was discovered to contain a Server-Side Request Forgery (SSRF) vulnerability via /admin.php/Plugins/update.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/67"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:1.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "07898D32-45C7-4692-AABE-5D7728D8B8B7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"918"
] | 918 | https://github.com/Cherry-toto/jizhicms/issues/67 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | SSRF vulnerability with echo exists in the CMS background, and attackers can use this vulnerability to scan local and Intranet ports and attack local and Intranet Jizhicms background. Attackers can use this vulnerability to scan local and Intranet ports, attack local and Intranet services, or carry out DOS attacks
... | V1.9.5: SSRF Vulnerability | https://api.github.com/repos/Cherry-toto/jizhicms/issues/67/comments | 2 | 2022-03-18T13:32:51Z | 2022-04-02T01:42:09Z | https://github.com/Cherry-toto/jizhicms/issues/67 | 1,173,597,157 | 67 | 3,530 |
CVE-2022-28053 | 2022-04-25T13:15:49.683 | Typemill v1.5.3 was discovered to contain an arbitrary file upload vulnerability via the upload function. This vulnerability allows attackers to execute arbitrary code via a crafted PHP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/typemill/typemill/issues/325"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:typemill:typemill:1.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "BF856DAC-17C1-450B-8DE1-E5BA45F2DDBB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"434"
] | 434 | https://github.com/typemill/typemill/issues/325 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"typemill",
"typemill"
] | See PDF for details:
[typemill-1.5.3-backstage.UploadVul.pdf](https://github.com/typemill/typemill/files/8310642/typemill-1.5.3-backstage.UploadVul.pdf)
| V1.5.3: Unrestricted File Upload Vulnerability | https://api.github.com/repos/typemill/typemill/issues/325/comments | 7 | 2022-03-20T02:42:15Z | 2022-04-06T17:19:09Z | https://github.com/typemill/typemill/issues/325 | 1,174,422,966 | 325 | 3,531 |
CVE-2022-28586 | 2022-04-25T13:15:49.773 | XSS in edit page of Hoosk 1.8.0 allows attacker to execute javascript code in user browser via edit page with XSS payload bypass filter some special chars. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/havok89/Hoosk/issues/63"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hoosk:hoosk:1.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "82154F24-2E08-490F-8040-1E8D19AD554C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/havok89/Hoosk/issues/63 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"havok89",
"Hoosk"
] | This vulnerability in `edit page` function

Exploit with using "heading" attribute, we can custom HTML tag lead to inject `img` tag with `onerror` event, and use `HTML encoding` to bypass filter some spe... | XSS on Hoosk v1.8 | https://api.github.com/repos/havok89/Hoosk/issues/63/comments | 0 | 2022-04-01T05:25:15Z | 2022-04-01T05:25:15Z | https://github.com/havok89/Hoosk/issues/63 | 1,189,256,433 | 63 | 3,532 |
CVE-2022-1441 | 2022-04-25T17:15:36.547 | MP4Box is a component of GPAC-2.0.0, which is a widely-used third-party package on RPM Fusion. When MP4Box tries to parse a MP4 file, it calls the function `diST_box_read()` to read from video. In this function, it allocates a buffer `str` with fixed length. However, content read from `bs` is controllable by user, so i... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/3dbe11b37d65c8472faf0654410068e5500b3adb"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7AEE044-50E9-4230-B492-A5FF18653115",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/2175 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | # Description
When GPAC tries to parse a MP4 file, it calls the function `diST_box_read()` to read from video. In this funtion, it allocates a buffer `str` with fixed length. However, content read from `bs` is controllable by user, so is the length, which causes a buffer overflow.
```
char str[1024];
i=0;
... | GPAC-2.0.0 MP4Box: stack overflow with unlimited length and controllable content in diST_box_read | https://api.github.com/repos/gpac/gpac/issues/2175/comments | 1 | 2022-04-16T08:21:46Z | 2022-04-22T18:29:03Z | https://github.com/gpac/gpac/issues/2175 | 1,206,053,267 | 2,175 | 3,533 |
CVE-2022-27984 | 2022-04-26T14:15:41.557 | CuppaCMS v1.0 was discovered to contain a SQL injection vulnerability via the menu_filter parameter at /administrator/templates/default/html/windows/right.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://cuppa.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/30"
},
{
"source": "nvd@nist.gov",
"t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/CuppaCMS/CuppaCMS/issues/30 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | * VULNERABLE: SQL injection vulnerability exists in CuppaCMS. An attacker can inject query in
“/administrator/templates/default/html/windows/right.php" via the "menu_filter=2" parameters.
* Contact me:wanghu29570@gmail.com
* Product:CuppaCMS
* Payload Boolean true: menu_filter=2' and '1'='1
* Payload Boolean false... | SQL injection vulnerability exists in CuppaCMS /administrator/templates/default/html/windows/right.php | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/30/comments | 0 | 2022-03-21T16:24:23Z | 2022-03-21T16:24:23Z | https://github.com/CuppaCMS/CuppaCMS/issues/30 | 1,175,630,195 | 30 | 3,534 |
CVE-2022-27985 | 2022-04-26T14:15:41.763 | CuppaCMS v1.0 was discovered to contain a SQL injection vulnerability via /administrator/alerts/alertLightbox.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://cuppa.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/31"
},
{
"source": "nvd@nist.gov",
"t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/CuppaCMS/CuppaCMS/issues/31 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"CuppaCMS",
"CuppaCMS"
] | * VULNERABLE: SQL injection vulnerability exists in CuppaCMS. An attacker can inject query in
“/administrator/alerts/alertLightbox.php" via the "params%5Bgroup%5D=2" parameters.
* Github: https://github.com/JiuBanSec
* Product: CuppaCMS
* Impact: Allow attacker inject query and access , disclosure of all data on th... | SQL injection vulnerability exists in CuppaCMS /administrator/alerts/alertLightbox.php | https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/31/comments | 0 | 2022-03-22T16:24:01Z | 2022-03-22T16:24:01Z | https://github.com/CuppaCMS/CuppaCMS/issues/31 | 1,177,004,325 | 31 | 3,535 |
CVE-2022-24881 | 2022-04-26T16:15:47.737 | Ballcat Codegen provides the function of online editing code to generate templates. In versions prior to 1.0.0.beta.2, attackers can implement remote code execution through malicious code injection of the template engine. This happens because Velocity and freemarker templates are introduced but input verification is no... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ballcat-projects/ballcat-codegen/commit/84a7cb38daf0295b93aba21d562ec627e4eb463b"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Trac... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ballcat:codegen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "41037930-63CD-4494-BE0B-3F616730F684",
"versionEndExcluding": "1.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"20"
] | 20 | https://github.com/ballcat-projects/ballcat-codegen/issues/5 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ballcat-projects",
"ballcat-codegen"
] | 已使用wx联系~ | ballcat-codegen template engine injection RCE | https://api.github.com/repos/ballcat-projects/ballcat-codegen/issues/5/comments | 1 | 2022-04-25T07:01:20Z | 2022-04-26T08:01:33Z | https://github.com/ballcat-projects/ballcat-codegen/issues/5 | 1,214,059,441 | 5 | 3,536 |
CVE-2022-28448 | 2022-04-26T20:15:35.780 | nopCommerce 4.50.1 is vulnerable to Cross Site Scripting (XSS). An attacker (role customer) can inject javascript code to First name or Last name at Customer Info. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nopSolutions/nopCommerce/issues/6191"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nopcommerce:nopcommerce:4.50.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DE1F8366-57AA-4EB3-AF01-0260B561A966",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/nopSolutions/nopCommerce/issues/6191 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nopSolutions",
"nopCommerce"
] | nopCommerce version: 4.50.1
Steps to reproduce the problem:
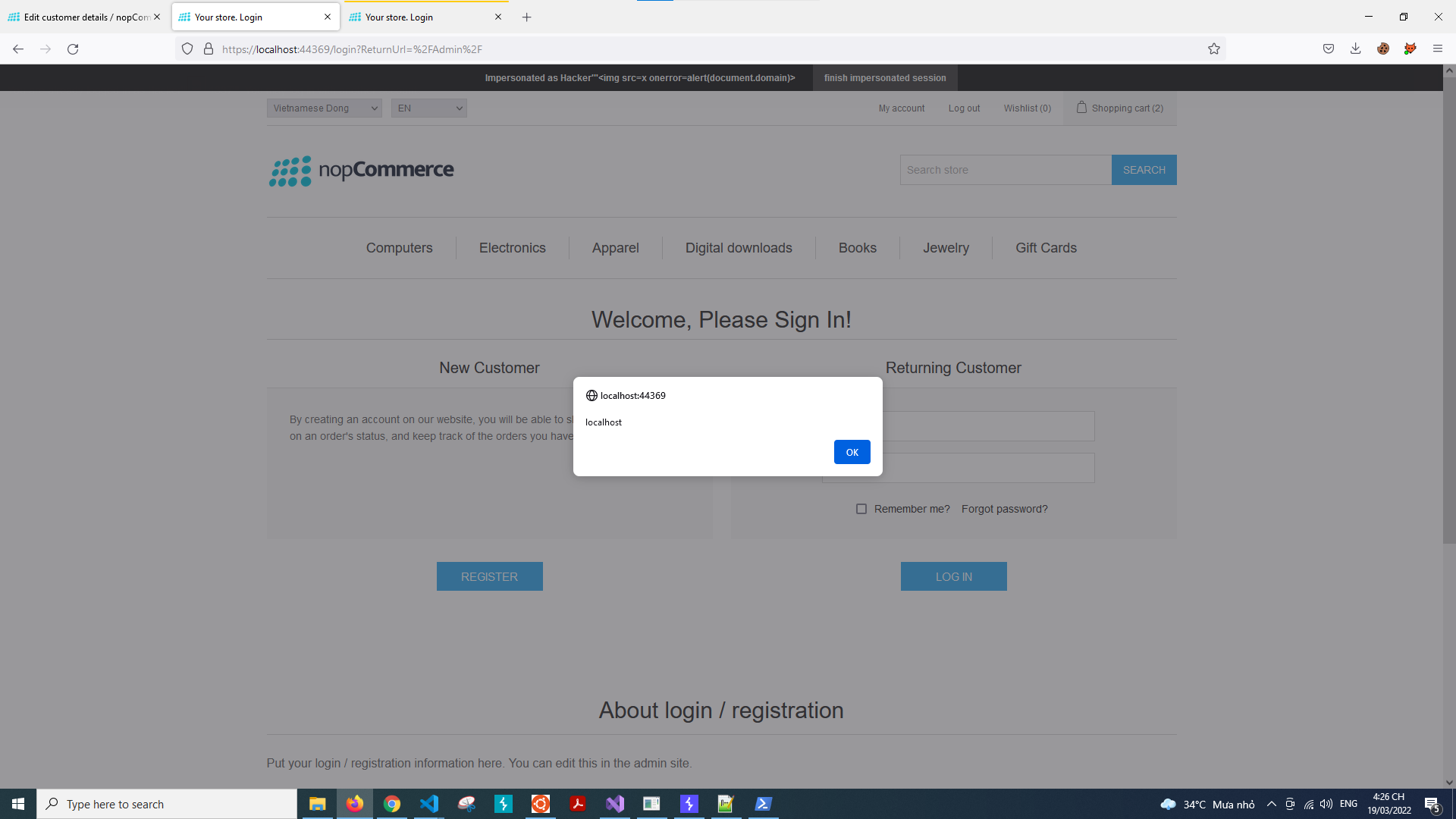
- Inject javascript code to First name or Last name at Customer Info
- When customer accesses deny resources, for exa... | Stored XSS in customer name when customer accessed deny resource and redirect to login page | https://api.github.com/repos/nopSolutions/nopCommerce/issues/6191/comments | 1 | 2022-03-19T09:32:47Z | 2022-03-22T11:01:29Z | https://github.com/nopSolutions/nopCommerce/issues/6191 | 1,174,221,161 | 6,191 | 3,537 |
CVE-2022-28058 | 2022-04-26T21:15:45.190 | Verydows v2.0 was discovered to contain an arbitrary file deletion vulnerability via \backend\file_controller.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Verytops/verydows/issues/20"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zhendezuile/bug_re... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:verydows:verydows:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "297496BD-F73F-4240-B58D-4C01A4FD9474",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"22"
] | 22 | https://github.com/Verytops/verydows/issues/20 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Verytops",
"verydows"
] | Vulnerability file: \protected\controller\backend\file_controller.php
It can be seen that the deleted file or directory is received through the path parameter, and is directly deleted without security filtering, so we can use this vulnerability to delete any file

.... | Verydows Exists Arbitrary File Deletion Vulnerability | https://api.github.com/repos/Verytops/verydows/issues/21/comments | 0 | 2022-03-23T13:54:45Z | 2022-03-23T14:06:39Z | https://github.com/Verytops/verydows/issues/21 | 1,178,157,993 | 21 | 3,539 |
CVE-2022-28449 | 2022-04-26T21:15:45.343 | nopCommerce 4.50.1 is vulnerable to Cross Site Scripting (XSS). At Apply for vendor account feature, an attacker can upload an arbitrary file to the system. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/nopSolutions/nopCommerce/issues/6192"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nopcommerce:nopcommerce:4.50.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DE1F8366-57AA-4EB3-AF01-0260B561A966",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/nopSolutions/nopCommerce/issues/6192 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"nopSolutions",
"nopCommerce"
] | nopCommerce version: 4.50.1
Steps to reproduce the problem:
- At **Apply for vendor account** feature, customer could upload arbitrary file, for example file **script.html** and content of submitted form as below:
```
-----------------------------353170076619137176562598160618
Content-Disposition: form-data; na... | Unrestricted File Upload in Apply for vendor account feature | https://api.github.com/repos/nopSolutions/nopCommerce/issues/6192/comments | 1 | 2022-03-20T08:35:25Z | 2022-03-23T13:34:18Z | https://github.com/nopSolutions/nopCommerce/issues/6192 | 1,174,474,913 | 6,192 | 3,540 |
CVE-2022-28450 | 2022-04-26T21:15:45.390 | nopCommerce 4.50.1 is vulnerable to Cross Site Scripting (XSS) via the "Text" parameter (forums) when creating a new post, which allows a remote attacker to execute arbitrary JavaScript code at client browser. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/nopSolutions/nopCommerce/issues/6194"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nopcommerce:nopcommerce:4.50.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DE1F8366-57AA-4EB3-AF01-0260B561A966",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/nopSolutions/nopCommerce/issues/6194 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"nopSolutions",
"nopCommerce"
] | nopCommerce version: 4.50.1
Description: A stored cross-site scripting (XSS) vulnerability exists when creating a new post of nopCommerce version 4.50.1 that allows a remote attacker to execute arbitrary JavaScript code at client browser
Steps to reproduce the problem:
- Step 1: Create new topic or reply topic wi... | XSS issue in the "Text" parameter (forums) | https://api.github.com/repos/nopSolutions/nopCommerce/issues/6194/comments | 4 | 2022-03-20T12:30:36Z | 2022-03-22T11:11:54Z | https://github.com/nopSolutions/nopCommerce/issues/6194 | 1,174,532,370 | 6,194 | 3,541 |
CVE-2022-28522 | 2022-04-26T21:15:45.480 | ZCMS v20170206 was discovered to contain a stored cross-site scripting (XSS) vulnerability via index.php?m=home&c=message&a=add. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jorycn/thinkphp-zcms/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zhendezuile/bug_... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zcms_project:zcms:20170206:*:*:*:*:*:*:*",
"matchCriteriaId": "E49CF457-6231-48AF-B3DA-C96BD47E6776",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/jorycn/thinkphp-zcms/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jorycn",
"thinkphp-zcms"
] | Vulnerability file:\Application\Home\Controller\MessageController.class.php
You can see that the xss vulnerability is not filtered here

Vulnerability to reproduce:
1、Visit url: http://www.xxx.com/index.... | There is a stored xss vulnerability here: /index.php?m=home&c=message&a=add | https://api.github.com/repos/jorycn/thinkphp-zcms/issues/5/comments | 0 | 2022-03-30T06:01:31Z | 2022-03-30T06:06:40Z | https://github.com/jorycn/thinkphp-zcms/issues/5 | 1,185,926,372 | 5 | 3,542 |
CVE-2022-28523 | 2022-04-26T21:15:45.527 | HongCMS 3.0.0 allows arbitrary file deletion via the component /admin/index.php/template/ajax?action=delete. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Neeke/HongCMS/issues/17"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hongcms_project:hongcms:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "5B8D6DB5-CC3D-4315-92A2-72E06A9AB4F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/Neeke/HongCMS/issues/17 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Neeke",
"HongCMS"
] | Vulnerability file: \admin\controllers\template.php
The vulnerability code is as follows:

Arbitrary file deletion vulnerability could lead to system reinstallation
Vulnerability to reproduce:
1、First l... | There is an arbitrary file deletion vulnerability here: /admin/index.php/template/ajax?action=delete | https://api.github.com/repos/Neeke/HongCMS/issues/17/comments | 0 | 2022-03-31T09:16:53Z | 2022-03-31T09:18:25Z | https://github.com/Neeke/HongCMS/issues/17 | 1,187,764,370 | 17 | 3,543 |
CVE-2022-28527 | 2022-04-26T21:15:45.663 | dhcms v20170919 was discovered to contain an arbitrary folder deletion vulnerability via /admin.php?r=admin/AdminBackup/del. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ShaoGongBra/dhcms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dhcms_project:dhcms:2017-09-19:*:*:*:*:*:*:*",
"matchCriteriaId": "E036CF96-6F25-499B-AB54-6439CF6EFAA6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"22"
] | 22 | https://github.com/ShaoGongBra/dhcms/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ShaoGongBra",
"dhcms"
] | Vulnerability file: \framework\ext\Util.php
You can see that the following code does not filter ../ or ..\\, it just filters . or .., which will cause any folder to be deleted

Vulnerability to reproduce:... | There is an arbitrary folder deletion vulnerability here:/admin.php?r=admin/AdminBackup/del | https://api.github.com/repos/ShaoGongBra/dhcms/issues/5/comments | 0 | 2022-04-01T08:51:20Z | 2022-04-01T08:51:20Z | https://github.com/ShaoGongBra/dhcms/issues/5 | 1,189,470,171 | 5 | 3,544 |
CVE-2022-28528 | 2022-04-26T21:15:45.707 | bloofoxCMS v0.5.2.1 was discovered to contain an arbitrary file upload vulnerability via /admin/index.php?mode=content&page=media&action=edit. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alexlang24/bloofoxCMS/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C12BED64-DA1B-4FB8-A196-B414759D79C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"434"
] | 434 | https://github.com/alexlang24/bloofoxCMS/issues/14 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alexlang24",
"bloofoxCMS"
] | Vulnerability file: \functions.php
You can see that the file is uploaded directly without the verification file suffix.
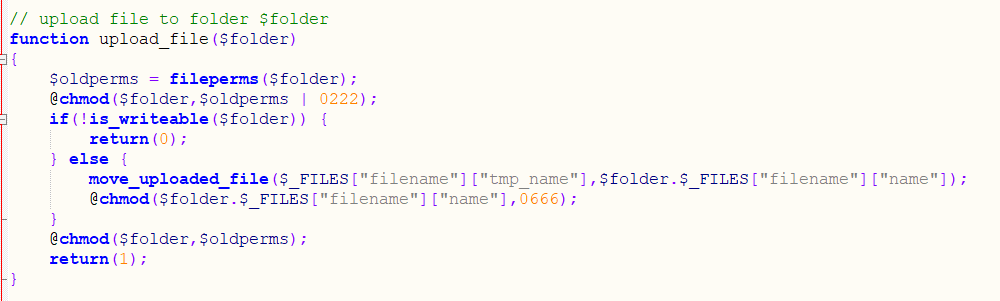
Vulnerability to reproduce:
1、First log in to the backend of the website
2、Visit ... | There is a file upload vulnerability here: /admin/index.php?mode=content&page=media&action=edit | https://api.github.com/repos/alexlang24/bloofoxCMS/issues/14/comments | 0 | 2022-04-01T16:12:30Z | 2022-04-01T16:13:54Z | https://github.com/alexlang24/bloofoxCMS/issues/14 | 1,190,012,664 | 14 | 3,545 |
CVE-2022-28085 | 2022-04-27T03:15:39.650 | A flaw was found in htmldoc commit 31f7804. A heap buffer overflow in the function pdf_write_names in ps-pdf.cxx may lead to arbitrary code execution and Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/46c8ec2b9bccb8ccabff52d998c5eee77a228348"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AF5FC4A4-81ED-4559-9ABE-B689F001E877",
"versionEndExcluding": "1.9.16",
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/michaelrsweet/htmldoc/issues/480 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | # Description
Whilst experimenting with `htmldoc`, built from commit [31f7804](https://github.com/michaelrsweet/htmldoc/tree/31f780487e5ddc426888638786cdc47631687275), we are able to induce a vulnerability in function `pdf_write_names` , using a harness compiled from `htmldoc/htmldoc.cxx`.
Because there is no bo... | AddressSanitizer: heap-buffer-overflow in function pdf_write_names | https://api.github.com/repos/michaelrsweet/htmldoc/issues/480/comments | 7 | 2022-03-24T12:44:48Z | 2022-05-19T16:24:33Z | https://github.com/michaelrsweet/htmldoc/issues/480 | 1,179,466,461 | 480 | 3,546 |
CVE-2021-41945 | 2022-04-28T14:15:07.617 | Encode OSS httpx < 0.23.0 is affected by improper input validation in `httpx.URL`, `httpx.Client` and some functions using `httpx.URL.copy_with`. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "http://encode.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/lebr0nli/4edb76bbd3b5ff993cf44f2fbce5e571"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:encode:httpx:*:*:*:*:*:python:*:*",
"matchCriteriaId": "984D81ED-5C7E-493D-9CDD-8F4B0A85BFD1",
"versionEndExcluding": "0.23.0",
"versionEndIncluding": null,
"versionStartExcl... | [
"20"
] | 20 | https://github.com/encode/httpx/issues/2184 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"encode",
"httpx"
] | After some research, I found that `httpx.Client` and `httpx.Proxy` may implicit parse wrong URL because of the improper implement of `httpx.URL().copy_with`.
And this issue may lead to some blacklist bypass.
For example:
- `httpx.Client`
```python
user_input_from_http_request = 'http:////admin-dashboard/se... | Some URL can make httpx use URL with wrong info | https://api.github.com/repos/encode/httpx/issues/2184/comments | 11 | 2022-04-21T03:46:42Z | 2022-05-23T16:41:02Z | https://github.com/encode/httpx/issues/2184 | 1,210,457,678 | 2,184 | 3,547 |
CVE-2022-28101 | 2022-04-28T14:15:07.720 | Turtlapp Turtle Note v0.7.2.6 does not filter the <meta> tag during markdown parsing, allowing attackers to execute HTML injection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/turtl/tracker/issues/404"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.cybe... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lyonbros:turtl:0.7.2.6:*:*:*:-:android:*:*",
"matchCriteriaId": "3A22E008-510E-45EA-B9B0-D238EEA7CF4B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/turtl/tracker/issues/404 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"turtl",
"tracker"
] | Notes allow `<meta>` tag injection. Ie, a note with the content
```
<META HTTP-EQUIV="refresh" CONTENT="0; URL=https://google.com">
```
opens a new browser window to Google. While this problem would happen over person-to-person sharing and thus the severity is limited (because you generally only share with thos... | Filter <meta> tags from notes | https://api.github.com/repos/turtl/tracker/issues/404/comments | 2 | 2021-12-13T21:49:44Z | 2022-07-26T13:59:13Z | https://github.com/turtl/tracker/issues/404 | 1,079,064,966 | 404 | 3,548 |
CVE-2022-28102 | 2022-04-28T14:15:07.763 | A cross-site scripting (XSS) vulnerability in PHP MySQL Admin Panel Generator v1 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected at /edit-db.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"URL Repurposed"
],
"url": "http://php-mysql-admin-panel-generator.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php_mysql_admin_panel_generator_project:php_mysql_admin_panel_generator:-:*:*:*:*:*:*:*",
"matchCriteriaId": "A4B95705-4B91-4EE5-A33D-4F625C369E4C",
"versionEndExcluding": null,
"version... | [
"79"
] | 79 | https://github.com/housamz/php-mysql-admin-panel-generator/issues/19 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"housamz",
"php-mysql-admin-panel-generator"
] | Affected software : php-mysql-admin-panel-generator
Version : N/A
Type of vulnerability : XSS (Cross-Site Scripting)
Author : s7safe
Description:
php-mysql-admin-panel-generator is susceptible to cross-site scripting attacks, allowing malicious users to inject code into web pages, and other users will be a... | Cross-Site Scripting (XSS) - Security Issue | https://api.github.com/repos/housamz/php-mysql-admin-panel-generator/issues/19/comments | 0 | 2022-03-25T20:50:21Z | 2022-03-25T20:51:01Z | https://github.com/housamz/php-mysql-admin-panel-generator/issues/19 | 1,181,257,328 | 19 | 3,549 |
CVE-2021-41948 | 2022-04-29T14:15:08.363 | A cross-site scripting (XSS) vulnerability exists in the "contact us" plugin for Subrion CMS <= 4.2.1 version via "List of subjects". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/intelliants/subrion-plugin-contact_us/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:intelliants:subrion:*:*:*:*:*:*:*:*",
"matchCriteriaId": "32A3677D-242A-4B1D-8ADB-9C4313D76A8D",
"versionEndExcluding": null,
"versionEndIncluding": "4.2.1",
"versionStartExc... | [
"79"
] | 79 | https://github.com/intelliants/subrion-plugin-contact_us/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"intelliants",
"subrion-plugin-contact_us"
] | Login into admin panel
Go to `http://localhost/panel/configuration/contact_us/`
Insert into `List of subjects` `1111" onclick="alert(1)`
Go to `http://192.168.1.100/contacts/`
Click `subject`
 aims to access files and directories that are stored outside the web root folder. By manipulating variables that reference files with “dot-dot-slash (../)” sequences and its variations or by u... | Security Vulnerability Found | https://api.github.com/repos/onlaj/Piano-LED-Visualizer/issues/350/comments | 0 | 2022-04-28T20:25:57Z | 2022-04-29T13:11:57Z | https://github.com/onlaj/Piano-LED-Visualizer/issues/350 | 1,219,248,648 | 350 | 3,551 |
CVE-2022-1227 | 2022-04-29T16:15:08.753 | A privilege escalation flaw was found in Podman. This flaw allows an attacker to publish a malicious image to a public registry. Once this image is downloaded by a potential victim, the vulnerability is triggered after a user runs the 'podman top' command. This action gives the attacker access to the host filesystem, l... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2070368"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:podman_project:podman:*:*:*:*:*:*:*:*",
"matchCriteriaId": "027F4117-F10C-4D9A-9977-BEB6146AA10A",
"versionEndExcluding": "4.0.0",
"versionEndIncluding": null,
"versionStartE... | [
"269"
] | 269 | https://github.com/containers/podman/issues/10941 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"containers",
"podman"
] | **Is this a BUG REPORT or FEATURE REQUEST? (leave only one on its own line)**
/kind bug
**Description**
**Steps to reproduce the issue:**
1.
top with --userns=keep-id container
```
[mike@x240 podman]$ podman run --name redis1 -d --userns=keep-id redis
d2f77ab7b4ebbd22a36b9853d28f6bdcdc452a7544f54... | podman top not work with userns=keep-id container | https://api.github.com/repos/containers/podman/issues/10941/comments | 37 | 2021-07-15T12:56:50Z | 2023-09-20T14:05:02Z | https://github.com/containers/podman/issues/10941 | 945,351,800 | 10,941 | 3,552 |
CVE-2022-25854 | 2022-04-29T20:15:07.580 | This affects the package @yaireo/tagify before 4.9.8. The package is used for rendering UI components inside the input or text fields, and an attacker can pass a malicious placeholder value to it to fire the XSS payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://bsg.tech/blog/cve-2022-25854-stored-xss-in-yaireo-tagify-npm-module/"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tagify_project:tagify:*:*:*:*:*:*:*:*",
"matchCriteriaId": "135622D7-7891-420D-81D9-C078AD572C78",
"versionEndExcluding": "4.9.8",
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/yairEO/tagify/issues/988 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yairEO",
"tagify"
] | ## Prerequisites
- [x] I am running the latest version
- [x] I checked the documentation and found no answer
- [x] I checked to make sure that this issue has not already been filed
### 💥 Demo Page
***React*** issue template:
[tagify-react-wrapper-forked](https://codesandbox.io/s/tagify-react-wrapper-forked-l... | XSS in tagify's template wrapper | https://api.github.com/repos/yairEO/tagify/issues/988/comments | 7 | 2022-02-16T15:50:15Z | 2022-04-05T18:20:21Z | https://github.com/yairEO/tagify/issues/988 | 1,140,233,339 | 988 | 3,553 |
CVE-2022-28481 | 2022-05-01T15:15:07.683 | CSV-Safe gem < 3.0.0 doesn't filter out special characters which could trigger CSV Injection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/zvory/csv-safe"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zvory/c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:csv-safe_project:csv-safe:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "90FF4066-FE73-42AB-8A71-1DD61B5788FA",
"versionEndExcluding": "3.0.0",
"versionEndIncluding": null,
"versio... | [
"1236"
] | 1236 | https://github.com/zvory/csv-safe/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zvory",
"csv-safe"
] | **Older versions of CSV-Safe gem doesn't filter out special characters which could trigger CSV Injection. (< 3.0.0)**
**Vulnerability Type**
CSV Injection
**Product**
csv-safe
**Affected Product Code Base**
CSV-safe - <3.0.0 are effected
**Affected Component**
Sanitization of CSV Injection vectors.
... | Older versions of CSV-Safe gem doesn't filter out special characters which could trigger CSV Injection. (< 3.0.0) [CVE-2022-28481] | https://api.github.com/repos/zvory/csv-safe/issues/7/comments | 7 | 2022-03-10T17:08:57Z | 2022-05-02T10:40:29Z | https://github.com/zvory/csv-safe/issues/7 | 1,165,494,657 | 7 | 3,554 |
CVE-2022-25301 | 2022-05-01T17:15:07.697 | All versions of package jsgui-lang-essentials are vulnerable to Prototype Pollution due to allowing all Object attributes to be altered, including their magical attributes such as proto, constructor and prototype. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/metabench/jsgui-lang-essentials/issues/1"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsgui-lang-essentials_project:jsgui-lang-essentials:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4EF99A25-9608-4D5B-8818-0112EFE6CF9A",
"versionEndExcluding": null,
"versionEndIncluding": null,... | [
"1321"
] | 1321 | https://github.com/metabench/jsgui-lang-essentials/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"metabench",
"jsgui-lang-essentials"
] | jsgui-lang-essentials runs the risk of prototype contamination when using inherited attributes in the function ll_set()
the risk locate is in here
https://github.com/lelecolacola123/jsgui-lang-essentials/blob/473b8daa94fda22a17d7d7bfe514f18e8d60e33e/jsgui-lang-essentials.js#L1418 | Prototype pollution in function jsgui-lang-essentials.ll_set() | https://api.github.com/repos/metabench/jsgui-lang-essentials/issues/1/comments | 1 | 2021-12-13T10:20:18Z | 2021-12-14T05:25:10Z | https://github.com/metabench/jsgui-lang-essentials/issues/1 | 1,078,340,462 | 1 | 3,555 |
CVE-2022-28451 | 2022-05-02T00:15:08.197 | nopCommerce 4.50.1 is vulnerable to Directory Traversal via the backup file in the Maintenance feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nopSolutions/nopCommerce/commit/47ff9a241243db9359f10216bcf401baaa36d0b4"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nopcommerce:nopcommerce:4.50.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DE1F8366-57AA-4EB3-AF01-0260B561A966",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"22"
] | 22 | https://github.com/nopSolutions/nopCommerce/issues/6203 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nopSolutions",
"nopCommerce"
] | nopCommerce version: 4.50
The Maintenance feature in nopCommerce version 4.50.1 is vulnerable to path traversal, an user can send the wrong value of parameter "backupFileName" when sending POST request manually
| Possible issue with database backup filenames | https://api.github.com/repos/nopSolutions/nopCommerce/issues/6203/comments | 1 | 2022-03-28T08:57:13Z | 2022-03-28T08:58:03Z | https://github.com/nopSolutions/nopCommerce/issues/6203 | 1,183,112,184 | 6,203 | 3,556 |
CVE-2021-46790 | 2022-05-02T12:16:26.260 | ntfsck in NTFS-3G through 2021.8.22 has a heap-based buffer overflow involving buffer+512*3-2. NOTE: the upstream position is that ntfsck is deprecated; however, it is shipped by some Linux distributions. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/05/26/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/tuxe... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tuxera:ntfs-3g:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A0ECB2C7-D4AA-4221-B95E-63117C4B328C",
"versionEndExcluding": null,
"versionEndIncluding": "2021.8.22",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/tuxera/ntfs-3g/issues/16 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tuxera",
"ntfs-3g"
] | Hello.
I have found a vulnerability in the NTFS-3G driver, specifically in the ntfsck tool (see: [_ntfsprogs/ntfsck.c_](https://github.com/tuxera/ntfs-3g/blob/92b9fbc6fe5aaa940a401b8f5ff2ed8cac6d5cc6/ntfsprogs/ntfsck.c)).
In the _check_file_record_ function, the update sequence array is applied, but no proper b... | Heap overflow in ntfsck | https://api.github.com/repos/tuxera/ntfs-3g/issues/16/comments | 3 | 2021-11-25T22:42:53Z | 2022-05-26T11:55:11Z | https://github.com/tuxera/ntfs-3g/issues/16 | 1,063,952,534 | 16 | 3,557 |
CVE-2022-29973 | 2022-05-02T12:16:28.117 | relan exFAT 1.3.0 allows local users to obtain sensitive information (data from deleted files in the filesystem) in certain situations involving offsets beyond ValidDataLength. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 1.9,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/relan/exfat/issues/185"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exfat_project:exfat:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C1CF85C8-472F-480A-B6E3-C023593774F1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"770"
] | 770 | https://github.com/relan/exfat/issues/185 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"relan",
"exfat"
] | Affected versions: 1.3.0 and latest code (11e4f03).
Details:
In the exFAT file system, each file has a stream extension with the following fields defined (among others): DataLength and ValidDataLength (https://docs.microsoft.com/en-us/windows/win32/fileio/exfat-specification#76-stream-extension-directory-entry). T... | Information disclosure in fuse-exfat | https://api.github.com/repos/relan/exfat/issues/185/comments | 5 | 2022-05-01T23:02:44Z | 2023-03-02T20:34:26Z | https://github.com/relan/exfat/issues/185 | 1,222,319,176 | 185 | 3,558 |
CVE-2022-27466 | 2022-05-02T14:15:07.837 | MCMS v5.2.27 was discovered to contain a SQL injection vulnerability in the orderBy parameter at /dict/list.do. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ming-soft/MCMS/issues/90"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mingsoft:mcms:5.2.27:*:*:*:*:*:*:*",
"matchCriteriaId": "F21B5945-3958-4CB1-927C-C93A0071E880",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/ming-soft/MCMS/issues/90 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ming-soft",
"MCMS"
] | A suspicious point was found in the IDictDao.xml file in the lib,ms-mdiy-2.1.12
.net.mingsoft.mdiy.dao.IDictDao.xml#145
<img width="1067" alt="image" src="https://user-images.githubusercontent.com/32029400/159149858-c22125dd-3299-499a-b02c-d45c7e0bf6b1.png">
Since the query maps to a method in Java, and this XML ... | MCMS 5.2.7 SQLI | https://api.github.com/repos/ming-soft/MCMS/issues/90/comments | 1 | 2022-03-20T06:17:38Z | 2022-09-09T01:41:23Z | https://github.com/ming-soft/MCMS/issues/90 | 1,174,451,572 | 90 | 3,559 |
CVE-2022-1515 | 2022-05-02T19:15:09.027 | A memory leak was discovered in matio 1.5.21 and earlier in Mat_VarReadNextInfo5() in mat5.c via a crafted file. This issue can potentially result in DoS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=2079986"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matio_project:matio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "52BC06EA-02DC-49AB-87F1-39A83AE066DD",
"versionEndExcluding": "1.5.22",
"versionEndIncluding": null,
"versionStartEx... | [
"401"
] | 401 | https://github.com/tbeu/matio/issues/186 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"tbeu",
"matio"
] | Hi,
this is an issue found by fuzzing the current master branch, use the OSS-Fuzz harness compiled with ASan and UBSan to reproduce.
The memory leak is in Mat_VarReadNextInfo5, the reported sanitizer error is the following:
```
INFO: Seed: 117854221
INFO: Loaded 1 modules (269217 inline 8-bit counters): 2692... | Memory leaks in Mat_VarReadNextInfo5 | https://api.github.com/repos/tbeu/matio/issues/186/comments | 2 | 2022-02-17T16:21:15Z | 2022-04-28T17:03:13Z | https://github.com/tbeu/matio/issues/186 | 1,141,556,988 | 186 | 3,560 |
CVE-2021-41959 | 2022-05-03T11:15:07.130 | JerryScript Git version 14ff5bf does not sufficiently track and release allocated memory via jerry-core/ecma/operations/ecma-regexp-object.c after RegExp, which causes a memory leak. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4781"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:-:*:*:*:*:*:*:*",
"matchCriteriaId": "4EB495C8-348F-4B04-B31F-1F4EE471CC22",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"401"
] | 401 | https://github.com/jerryscript-project/jerryscript/issues/4781 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
14ff5bf
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.11.0-34-generic x86_64)
###### Build steps
```sh
./tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--clean --debug --strip=off --logging=on --error-messages=on \
--compile-flag=-fsanitize=address --sta... | Unfreed float causing memory leak in ecma-regexp-object | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4781/comments | 2 | 2021-09-27T07:23:09Z | 2021-10-04T11:12:53Z | https://github.com/jerryscript-project/jerryscript/issues/4781 | 1,007,794,199 | 4,781 | 3,561 |
CVE-2021-42218 | 2022-05-03T11:15:07.180 | OMPL v1.5.2 contains a memory leak in VFRRT.cpp | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ompl/ompl/issues/839"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rice:open_motion_planning_library:1.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D03D3844-605B-454C-8690-5CBA05D5C2A3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"401"
] | 401 | https://github.com/ompl/ompl/issues/839 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ompl",
"ompl"
] | When I’m testing ompl, here is a memory leak occured. After positioning,we found that the error is caused by the following code in VFRRT.cpp:
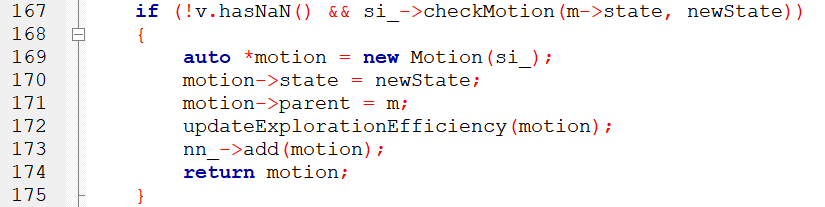
In line 169.A motion object was requested with it’s construct... | A memory leak in VFRRT | https://api.github.com/repos/ompl/ompl/issues/839/comments | 2 | 2021-10-07T07:30:39Z | 2022-05-09T19:17:30Z | https://github.com/ompl/ompl/issues/839 | 1,019,712,046 | 839 | 3,562 |
CVE-2021-39390 | 2022-05-03T13:15:07.567 | Stored XSS in PartKeepr 1.4.0 Edit section in multiple api endpoints via name parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://demo.partkeepr.org/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/partkeepr/PartKeepr/issues/1237"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:partkeepr:partkeepr:1.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BB940D93-DB3C-4E3C-BFD5-6B87C971BD74",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/partkeepr/PartKeepr/issues/1237 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"partkeepr",
"PartKeepr"
] | ## Description
Stored XSS in PartKeepr 1.4.0 Edit section in multiple api endpoints via name parameter
## Reproduction Steps
Browsing to Edit tab, select project and add new project.
There, insert the following payload `<img src=x onerror=alert(1)>` in name field.
<img width="1440" alt="payload" src="https://... | Stored XSS in PartKeepr | https://api.github.com/repos/partkeepr/PartKeepr/issues/1237/comments | 0 | 2022-02-22T12:47:49Z | 2022-02-22T12:47:49Z | https://github.com/partkeepr/PartKeepr/issues/1237 | 1,146,869,446 | 1,237 | 3,563 |
CVE-2022-28589 | 2022-05-03T14:15:08.643 | A stored cross-site scripting (XSS) vulnerability in Pixelimity 1.0 allows attackers to execute arbitrary web scripts or HTML via the Title field in admin/pages.php?action=add_new | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pixelimity/pixelimity/issues/23"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pixelimity:pixelimity:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1F0EADD1-0D88-4392-A4EF-B273DA08E9AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/pixelimity/pixelimity/issues/23 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pixelimity",
"pixelimity"
] | A Cross Site Scripting vulnerabilty exists in Pixelimity via the Page Title field in pixelimity/admin/pages.php?action=add_new
Step to exploit:
1. Login as admin.
2. Navigate to http://127.0.0.1/pixelimity/admin/pages.php and click on Add New.
3. Insert XSS payload (<script>alert(1)</script>) in the "Title" field... | Cross-Site Scripting (XSS) in "admin/pages.php?action=add_new" | https://api.github.com/repos/pixelimity/pixelimity/issues/23/comments | 0 | 2022-04-01T13:22:07Z | 2022-04-01T13:22:07Z | https://github.com/pixelimity/pixelimity/issues/23 | 1,189,790,686 | 23 | 3,564 |
CVE-2022-28505 | 2022-05-03T17:15:07.730 | Jfinal_cms 5.1.0 is vulnerable to SQL Injection via com.jflyfox.system.log.LogController.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/33"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/jflyfox/jfinal_cms/issues/33 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jflyfox",
"jfinal_cms"
] | # SQL injection vulnerability exists in JFinal CMS 5.1.0
# Analysis
The vulnerability appears in lines 23-47 of the **com.jflyfox.system.log.LogController.java**

Here call **SQLUtils** to query with th... | [CVE-2022-28505] SQL injection vulnerability exists in JFinal CMS 5.1.0 | https://api.github.com/repos/jflyfox/jfinal_cms/issues/33/comments | 0 | 2022-03-29T08:03:30Z | 2022-05-03T17:07:15Z | https://github.com/jflyfox/jfinal_cms/issues/33 | 1,184,471,428 | 33 | 3,565 |
CVE-2022-28585 | 2022-05-03T18:15:08.900 | EmpireCMS 7.5 has a SQL injection vulnerability in AdClass.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/leadscloud/EmpireCMS/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phome:empirecms:7.5:*:*:*:*:*:*:*",
"matchCriteriaId": "E98F3E40-61C8-4876-AF5B-BA3786690439",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/leadscloud/EmpireCMS/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"leadscloud",
"EmpireCMS"
] | ## **Brief of this vulnerability**
EmpireCMS v7.5 has sql injection vulnerability in adding advertisement category
## **Test Environment**
- Windows10
- PHP 5.5.9+Apache/2.4.39
## **Affect version**
EmpireCMS 7.5
## **Vulnerable Code**
e\admin\tool\AdClass.php line 30
The variable $add passed i... | EmpireCMS v7.5 has sql injection vulnerability | https://api.github.com/repos/leadscloud/EmpireCMS/issues/5/comments | 0 | 2022-04-01T08:10:06Z | 2022-04-01T08:10:06Z | https://github.com/leadscloud/EmpireCMS/issues/5 | 1,189,426,211 | 5 | 3,566 |
CVE-2022-28588 | 2022-05-03T18:15:08.943 | In SpringBootMovie <=1.2 when adding movie names, malicious code can be stored because there are no filtering parameters, resulting in stored XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/lkmc2/SpringBootMovie/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:springbootmovie_project:springbootmovie:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C9323BE2-F97F-4E03-A288-3DA1DBA7D5E7",
"versionEndExcluding": null,
"versionEndIncluding": "1.2",
... | [
"79"
] | 79 | https://github.com/lkmc2/SpringBootMovie/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"lkmc2",
"SpringBootMovie"
] | When adding movie names, malicious code can be stored because there is no filtering of parameters
Affected version:<=1.2
test:

The trigger:
 vulnerability exists in FUEL-CMS 1.5.1 that allows an authenticated user to upload a malicious .pdf file which acts as a stored XSS payload. If this stored XSS payload is triggered by an administrator it will trigger a XSS attack. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/595"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F3A806A2-582F-49B6-B9EC-C0FB4B13ED3D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/daylightstudio/FUEL-CMS/issues/595 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | A stored cross-site scripting (XSS) vulnerability exists in FUEL-CMS-1.5.1 that allows an authenticated user authorized to upload a malicious .pdf file which acts as a stored XSS payload. If this stored XSS payload is triggered by an administrator it will trigger a XSS attack.
1、login as admin .in the Assets page
![i... | A stored cross-site scripting (XSS) vulnerability exists in FUEL-CMS-1.5.1 | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/595/comments | 0 | 2022-04-02T09:29:18Z | 2022-04-02T09:38:57Z | https://github.com/daylightstudio/FUEL-CMS/issues/595 | 1,190,577,090 | 595 | 3,568 |
CVE-2022-29001 | 2022-05-03T18:15:09.023 | In SpringBootMovie <=1.2, the uploaded file suffix parameter is not filtered, resulting in arbitrary file upload vulnerability | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/lkmc2/SpringBootMovie/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:springbootmovie_project:springbootmovie:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C9323BE2-F97F-4E03-A288-3DA1DBA7D5E7",
"versionEndExcluding": null,
"versionEndIncluding": "1.2",
... | [
"434"
] | 434 | https://github.com/lkmc2/SpringBootMovie/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"lkmc2",
"SpringBootMovie"
] | Affected version:<=1.2
Upload a compromised file with the suffix .php

Published successfully
... | Arbitrary file upload vulnerability | https://api.github.com/repos/lkmc2/SpringBootMovie/issues/4/comments | 1 | 2022-04-08T08:49:20Z | 2023-03-07T17:01:39Z | https://github.com/lkmc2/SpringBootMovie/issues/4 | 1,197,028,639 | 4 | 3,569 |
CVE-2022-27420 | 2022-05-04T03:15:07.307 | Hospital Management System v1.0 was discovered to contain a SQL injection vulnerability via the patient_contact parameter in patientsearch.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kishan0725/Hospital-Management-System/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Track... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hospital_management_system_project:hospital_management_system:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "36653204-5E38-44E3-B8FD-580F2D27E958",
"versionEndExcluding": null,
"versionEndInclu... | [
"89"
] | 89 | https://github.com/kishan0725/Hospital-Management-System/issues/19 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kishan0725",
"Hospital-Management-System"
] | I found an SQL Injection in your project
Pls Follow these steps to reproduce:
1. Create a request to 'patientsearch.php':

2. Save this request to 1.txt file:
 {
if(isset($GLOBALS['groupid']) && $GLOBALS['groupid']) {
if(is_array($GLOBALS['groupid'])) {
$where = ' IN ('.implode(',', $GLOBALS['groupid']).')';
foreach($GLOBALS['groupid'] as $gid) {
$this... | Wuzhicms v4.1.0 /coreframe/app/member/admin/group.php hava a SQL Injection Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/200/comments | 0 | 2022-03-18T07:58:14Z | 2022-03-18T07:58:14Z | https://github.com/wuzhicms/wuzhicms/issues/200 | 1,173,293,142 | 200 | 3,571 |
CVE-2022-27470 | 2022-05-04T03:15:07.627 | SDL_ttf v2.0.18 and below was discovered to contain an arbitrary memory write via the function TTF_RenderText_Solid(). This vulnerability is triggered via a crafted TTF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libsdl-org/SDL_ttf/commit/db1b41ab8bde6723c24b866e466cad78c2fa0448"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsdl:sdl_ttf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "030E0F2C-3446-4732-8E66-FF2818FEF632",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.18",
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/libsdl-org/SDL_ttf/issues/187 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libsdl-org",
"SDL_ttf"
] |
Hello, I found a vulnerability in this project.
### Summary
Arbitrary memory overwrite occurs when loading glyphs and rendering text with a malformed TTF file.
### System Info
- Operating System: Ubuntu 20.04
### Detailed Description
When the function `TTF_RenderText_Solid()` is executed... | Arbitrary memory overwrite occurs when loading glyphs and rendering text with a malformed TTF file. | https://api.github.com/repos/libsdl-org/SDL_ttf/issues/187/comments | 2 | 2022-03-19T11:11:01Z | 2022-05-07T10:16:07Z | https://github.com/libsdl-org/SDL_ttf/issues/187 | 1,174,240,535 | 187 | 3,572 |
CVE-2022-28111 | 2022-05-04T13:15:08.643 | MyBatis PageHelper v1.x.x-v3.7.0 v4.0.0-v5.0.0,v5.1.0-v5.3.0 was discovered to contain a time-blind SQL injection vulnerability via the orderBy parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/pagehelper/Mybatis-PageHelper"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/pagehelper/Mybat... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pagehelper_project:pagehelper:*:*:*:*:*:*:*:*",
"matchCriteriaId": "16FCD77F-3941-458E-A12D-29665FEEB137",
"versionEndExcluding": null,
"versionEndIncluding": "3.7.0",
"versi... | [
"89"
] | 89 | https://github.com/pagehelper/Mybatis-PageHelper/issues/674 | [
"Third Party Advisory"
] | github.com | [
"pagehelper",
"Mybatis-PageHelper"
] | 这种漏洞应该在调用方通过正则或者白名单处理,有些人的需求会用到函数等各种复杂排序,因此分页插件不做校验。
### 如果你从前端传递一个 SQL 用 JDBC 原生方式执行,你是不是发现了一个天大的漏洞?
### 如果JDBC不做处理,是不是就不用 JDBC 了?
如果这个漏洞会影响你们项目选择分页插件,可以在当前 issues 留言,如果留言人数很多,下个版本可以把 `order by` 功能去掉。
### 影响所有版本?瞎写!!!
下面是和排序有关的更新日志。
### 3.6.0 - 2015-02-03
- PageHelper增加了startPage(int pageNum, int p... | 关于 CVE-2022-28111漏洞!!! | https://api.github.com/repos/pagehelper/Mybatis-PageHelper/issues/674/comments | 15 | 2022-06-02T07:20:42Z | 2023-11-02T12:07:47Z | https://github.com/pagehelper/Mybatis-PageHelper/issues/674 | 1,257,793,797 | 674 | 3,573 |
CVE-2022-28487 | 2022-05-04T15:15:12.863 | Tcpreplay version 4.4.1 contains a memory leakage flaw in fix_ipv6_checksums() function. The highest threat from this vulnerability is to data confidentiality. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/723"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/appneta/tcpreplay/issues/723 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
Tcpreplay version 4.4.1 contains a memory leakage flaw, CWE-134 vulnerability in fix_ipv6_checksums() function. The highest threat from this vulnerability is to data confidentiality. The inputs required to exploit the vulnerability is unknown.
https://github.com/appneta/tcpreplay/blob/09f07748d... | [Bug] Format string vulnerability in fix_ipv6_checksums() function | https://api.github.com/repos/appneta/tcpreplay/issues/723/comments | 2 | 2022-03-28T20:35:50Z | 2025-05-07T07:19:50Z | https://github.com/appneta/tcpreplay/issues/723 | 1,183,961,497 | 723 | 3,574 |
CVE-2022-28488 | 2022-05-04T15:15:12.910 | The function wav_format_write in libwav.c in libwav through 2017-04-20 has an Use of Uninitialized Variable vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/marc-q/libwav/issues/29"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libwav_project:libwav:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0B1ADCA2-142E-4BE6-997F-4549F987C0E1",
"versionEndExcluding": null,
"versionEndIncluding": "2017-04-20",
"versionS... | [
"908"
] | 908 | https://github.com/marc-q/libwav/issues/29 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"marc-q",
"libwav"
] | ***Describe the bug***
An unitialized variable is used in function wav_format_write. The highest threat from this vulnerability is to data confidentiality.
The unitialized variable `format` is copied to the stream pointed by `f` variable, as illustrated below.
https://github.com/marc-q/libwav/blob/5cc874635f4e5a3... | [Bug] Use of uninitialized value in function wav_format_write in libwav.c | https://api.github.com/repos/marc-q/libwav/issues/29/comments | 0 | 2022-03-27T22:15:14Z | 2022-03-28T21:12:09Z | https://github.com/marc-q/libwav/issues/29 | 1,182,681,183 | 29 | 3,575 |
CVE-2022-28552 | 2022-05-04T15:15:12.997 | Cscms 4.1 is vulnerable to SQL Injection. Log into the background, open the song module, create a new song, delete it to the recycle bin, and SQL injection security problems will occur when emptying the recycle bin. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1DCFB098-04A8-43FE-AF93-0BE46815BAA3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | Log in to the background, open the song module, create a new song, delete it to the recycle bin, and SQL injection security problems will occur when emptying the recycle bin.
```
POST /admin.php/dance/admin/dance/save HTTP/1.1
Host: cscms.test
Content-Length: 292
Accept: application/json, text/javascript, */*; q=0... | Cscms V4.1 has sqlinjection | https://api.github.com/repos/chshcms/cscms/issues/10/comments | 0 | 2022-01-18T08:12:55Z | 2022-01-18T08:12:55Z | https://github.com/chshcms/cscms/issues/10 | 1,106,596,877 | 10 | 3,576 |
CVE-2022-28471 | 2022-05-05T13:15:07.877 | In ffjpeg (commit hash: caade60), the function bmp_load() in bmp.c contains an integer overflow vulnerability, which eventually results in the heap overflow in jfif_encode() in jfif.c. This is due to the incomplete patch for issue 38 | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/49"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:2021-12-06:*:*:*:*:*:*:*",
"matchCriteriaId": "A3438805-CAF0-41AE-BC2A-3A11A252D8E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"190"
] | 190 | https://github.com/rockcarry/ffjpeg/issues/49 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | **version**: master (commit [caade60](https://github.com/rockcarry/ffjpeg/commit/caade60a69633d74100bd3c2528bddee0b6a1291))
**poc**: [poc](https://github.com/dandanxu96/PoC/blob/main/ffjpeg/ffjpeg-bmp_load-integer-overflow)
**command**: ./ffjpeg -e $poc$
Here is the trace reported by ASAN:
```
user@c3ae4d510abb:... | Integer overflow in bmp_load() resulting in heap overflow in jfif_encode() at jfif.c:763 | https://api.github.com/repos/rockcarry/ffjpeg/issues/49/comments | 7 | 2022-03-25T10:42:12Z | 2022-05-21T02:29:45Z | https://github.com/rockcarry/ffjpeg/issues/49 | 1,180,627,632 | 49 | 3,577 |
CVE-2022-29339 | 2022-05-05T13:15:07.927 | In GPAC 2.1-DEV-rev87-g053aae8-master, function BS_ReadByte() in utils/bitstream.c has a failed assertion, which causes a Denial of Service. This vulnerability was fixed in commit 9ea93a2. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/9ea93a2ec8f555ceed1ee27294cf94822f14f10f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A97931ED-0014-4D2C-969E-5B41DDFF9DD2",
"versionEndExcluding": "2022-04-12",
"versionEndIncluding": null,
"versionStartExcludin... | [
"617"
] | 617 | https://github.com/gpac/gpac/issues/2165 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | **version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://do... | Assertion failed in BS_ReadByte, utils/bitstream.c:383 | https://api.github.com/repos/gpac/gpac/issues/2165/comments | 0 | 2022-04-08T08:28:19Z | 2022-04-12T09:01:22Z | https://github.com/gpac/gpac/issues/2165 | 1,197,007,820 | 2,165 | 3,578 |
CVE-2022-29340 | 2022-05-05T13:15:07.967 | GPAC 2.1-DEV-rev87-g053aae8-master. has a Null Pointer Dereference vulnerability in gf_isom_parse_movie_boxes_internal due to improper return value handling of GF_SKIP_BOX, which causes a Denial of Service. This vulnerability was fixed in commit 37592ad. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/37592ad86c6ca934d34740012213e467acc4a3b0"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A97931ED-0014-4D2C-969E-5B41DDFF9DD2",
"versionEndExcluding": "2022-04-12",
"versionEndIncluding": null,
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2163 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | **version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://do... | NULL Pointer Dereference still exists in gf_isom_parse_movie_boxes_internal | https://api.github.com/repos/gpac/gpac/issues/2163/comments | 1 | 2022-04-01T12:17:54Z | 2022-04-12T09:01:21Z | https://github.com/gpac/gpac/issues/2163 | 1,189,714,047 | 2,163 | 3,579 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.