cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2023-39949 | 2023-08-11T14:15:13.807 | eprosima Fast DDS is a C++ implementation of the Data Distribution Service standard of the Object Management Group. Prior to versions 2.9.1 and 2.6.5, improper validation of sequence numbers may lead to remotely reachable assertion failure. This can remotely crash any Fast-DDS process. Versions 2.9.1 and 2.6.5 contain ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/eProsima/Fast-DDS/blob/v2.9.0/src/cpp/rtps/messages/MessageReceiver.cpp#L1059"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eprosima:fast_dds:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A5F6650B-AD38-4E23-94EC-691A17D787EB",
"versionEndExcluding": "2.6.5",
"versionEndIncluding": null,
"versionStartExclu... | [
"617"
] | 617 | https://github.com/eProsima/Fast-DDS/issues/3236 | [
"Third Party Advisory"
] | github.com | [
"eProsima",
"Fast-DDS"
] | ### Is there an already existing issue for this?
- [X] I have searched the existing issues
### Expected behavior
Malformed submessages handled gracefully.
### Current behavior
I came across two following issues.
1. An SPDP payload with a malformed heartbeat submessage triggers an assertion failure at `f... | Assertion failure in SequenceNumber.h via malformed SPDP packet only when compiled in logging-enabled (Debug) mode | https://api.github.com/repos/eProsima/Fast-DDS/issues/3236/comments | 5 | 2023-01-19T23:10:09Z | 2023-08-11T20:45:06Z | https://github.com/eProsima/Fast-DDS/issues/3236 | 1,550,082,318 | 3,236 | 5,490 |
CVE-2023-40274 | 2023-08-14T01:15:47.307 | An issue was discovered in zola 0.13.0 through 0.17.2. The custom implementation of a web server, available via the "zola serve" command, allows directory traversal. The handle_request function, used by the server to process HTTP requests, does not account for sequences of special path control characters (../) in the U... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/getzola/zola/issues/2257"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/getzola/zola/pull/2258"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:getzola:zola:*:*:*:*:*:*:*:*",
"matchCriteriaId": "046BF830-C166-436E-BB74-0468599AD03C",
"versionEndExcluding": null,
"versionEndIncluding": "0.17.2",
"versionStartExcluding... | [
"22"
] | 22 | https://github.com/getzola/zola/issues/2257 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"getzola",
"zola"
] | # Bug Report
## Environment
OS: MacOS 13.4.1; Windows 11; Ubuntu 20.04
Zola version: 0.17.2
## Expected Behavior
Application should only search & serve files within the webserver's root folder.
## Current Behavior
Custom implementation of a web server, used for development purposes & available via `zola s... | LFI in zola serve | https://api.github.com/repos/getzola/zola/issues/2257/comments | 1 | 2023-07-24T19:55:18Z | 2024-05-27T18:56:05Z | https://github.com/getzola/zola/issues/2257 | 1,819,042,790 | 2,257 | 5,491 |
CVE-2023-40294 | 2023-08-14T04:15:11.337 | libboron in Boron 2.0.8 has a heap-based buffer overflow in ur_parseBlockI at i_parse_blk.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/0branch/boron/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/0branch/bo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:0branch:boron:2.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "82303CD4-FB83-4A0E-8F7E-0FEB740E4C03",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/0branch/boron/issues/3 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"0branch",
"boron"
] |
Hi!
While I was running boron in my environment, I happened to stumble upon 2 heap buffer overflows in the libboron library (libboron.so.2 version 2.0.8) when processing slightly malformed input. I have included reproduction files and tried my best to pinpoint the location of both heap buffer overflows. I tested... | Heap Overflows in Libboron v2.0.8 | https://api.github.com/repos/0branch/boron/issues/3/comments | 3 | 2023-08-04T17:49:28Z | 2023-12-12T14:30:30Z | https://github.com/0branch/boron/issues/3 | 1,837,133,829 | 3 | 5,492 |
CVE-2023-40296 | 2023-08-14T04:15:11.467 | async-sockets-cpp through 0.3.1 has a stack-based buffer overflow in ReceiveFrom and Receive in udpsocket.hpp when processing malformed UDP packets. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/eminfedar/async-sockets-cpp/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Ve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eminfedar:async-sockets-cpp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8D30067E-9487-412A-BA73-8755F07C5F58",
"versionEndExcluding": null,
"versionEndIncluding": "0.3.1",
"version... | [
"787"
] | 787 | https://github.com/eminfedar/async-sockets-cpp/issues/32 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"eminfedar",
"async-sockets-cpp"
] | Hi!
It appears that async-sockets-cpp (through 0.3.1) contains a remote buffer overflow vulnerability in static void ReceiveFrom(UDPSocket* udpSocket) at udpsocket.hpp, around lines 160-167. The buffer overflow affects all corresponding UDP servers. The remote buffer overflow can be triggered by connecting to a UD... | Stack Buffer Overflow in static void ReceiveFrom(UDPSocket* udpSocket) at udpsocket.hpp | https://api.github.com/repos/eminfedar/async-sockets-cpp/issues/32/comments | 5 | 2023-07-30T23:51:29Z | 2023-09-12T12:19:16Z | https://github.com/eminfedar/async-sockets-cpp/issues/32 | 1,828,132,520 | 32 | 5,493 |
CVE-2023-38850 | 2023-08-15T17:15:10.480 | Buffer Overflow vulnerability in Michaelrsweet codedoc v.3.7 allows an attacker to cause a denial of service via the codedoc.c:1742 comppnent. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/michaelrsweet/codedoc/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/mic... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:msweet:codedoc:3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "9B20B4BC-4E97-4EA9-AD35-BD6481E6062C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"120"
] | 120 | https://github.com/michaelrsweet/codedoc/issues/15 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"michaelrsweet",
"codedoc"
] | ./codedoc poc225
version 3.7
```
=================================================================
==43141==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60200000012f at pc 0x55e9e1ae8aa6 bp 0x7ffefd45f8d0 sp 0x7ffefd45f8c0
READ of size 1 at 0x60200000012f thread T0
#0 0x55e9e1ae8aa5 in highlight... | AddressSanitizer: heap-buffer-overflow | https://api.github.com/repos/michaelrsweet/codedoc/issues/15/comments | 1 | 2023-07-13T00:28:10Z | 2024-03-23T01:12:02Z | https://github.com/michaelrsweet/codedoc/issues/15 | 1,801,942,021 | 15 | 5,494 |
CVE-2023-38851 | 2023-08-15T17:15:10.603 | Buffer Overflow vulnerability in libxlsv.1.6.2 allows a remote attacker to execute arbitrary code and cause a denial of service via a crafted XLS file to the xls_parseWorkBook function in xls.c:1018. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/libxls/libxls/issues/124"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/libxls/lib... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libxls_project:libxls:1.6.2:*:*:*:*:*:*:*",
"matchCriteriaId": "716193D2-B36C-4AED-BB10-43E8E89E2E0A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/libxls/libxls/issues/124 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"libxls",
"libxls"
] | Hi, developers of libxls:
In the test of the binary `test2_libxls` instrumented with ASAN. There are 6 heap-buffer-overflow and 1 SEGV vulnerabilities in
`src/xls.c:1015`, `src/xls.c:1018`, `src/xlstool.c:266`, `src/xlstool.c:411`, `src/xlstool.c:395`, and `src/xlstool.c:296`. Here is the ASAN mode output (I omit s... | There are multiple heap-buffer-overflow vulnerability found in libxls | https://api.github.com/repos/libxls/libxls/issues/124/comments | 0 | 2023-07-13T06:31:34Z | 2024-02-04T15:16:49Z | https://github.com/libxls/libxls/issues/124 | 1,802,290,400 | 124 | 5,495 |
CVE-2023-38857 | 2023-08-15T17:15:11.420 | Buffer Overflow vulnerability infaad2 v.2.10.1 allows a remote attacker to execute arbitrary code and cause a denial of service via the stcoin function in mp4read.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/knik0/faad2/issues/171"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.gentoo.org/glsa/202401-13"
},
{
"source": "af854a3a-2127-422b-91ae-364da... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "49A2F342-2F20-4146-8972-7FFE7B524B0A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/171 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"knik0",
"faad2"
] | Hi, developers of faad2:
In the test of the binary faad([1d53978](https://github.com/knik0/faad2/commit/1d539788397713968d9660fe9f4e68af526bab73)) instrumented with ASAN. There is a heap-buffer-overflow vulnerability in `faad`, `/faad2/frontend/mp4read.c:449:63` in `static int stcoin(int size)`. Here is the ASAN mode ... | A heap-buffer-overflow vulnerability found in mp4read.c:449:63 | https://api.github.com/repos/knik0/faad2/issues/171/comments | 1 | 2023-07-18T04:19:21Z | 2023-08-21T10:23:34Z | https://github.com/knik0/faad2/issues/171 | 1,809,050,783 | 171 | 5,496 |
CVE-2023-38858 | 2023-08-15T17:15:11.597 | Buffer Overflow vulnerability infaad2 v.2.10.1 allows a remote attacker to execute arbitrary code and cause a denial of service via the mp4info function in mp4read.c:1039. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/knik0/faad2/issues/173"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.gentoo.org/glsa/202401-13"
},
{
"source": "af854a3a-2127-422b-91ae-364da... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "49A2F342-2F20-4146-8972-7FFE7B524B0A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/173 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"knik0",
"faad2"
] | Hi, developers of faad2:
In the test of the binary faad([1d53978](https://github.com/knik0/faad2/commit/1d539788397713968d9660fe9f4e68af526bab73)) instrumented with ASAN. There is a SEGV vulnerability in `faad`, `/faad2/frontend/mp4read.c:1039:67` in `mp4info`. Here is the ASAN mode output:
========================... | A SEGV vulnerability found in faad2 | https://api.github.com/repos/knik0/faad2/issues/173/comments | 4 | 2023-07-24T02:37:19Z | 2023-08-22T00:10:02Z | https://github.com/knik0/faad2/issues/173 | 1,817,487,438 | 173 | 5,497 |
CVE-2023-38860 | 2023-08-15T17:15:11.737 | An issue in LangChain v.0.0.231 allows a remote attacker to execute arbitrary code via the prompt parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/hwchase17/langchain/issues/7641"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/hwc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.231:*:*:*:*:*:*:*",
"matchCriteriaId": "F477D71B-7192-463A-94B4-99EB77D322C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"94"
] | 94 | https://github.com/hwchase17/langchain/issues/7641 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"hwchase17",
"langchain"
] | ### System Info
LangChain 0.0.231, Windows 10, Python 3.10.11
### Who can help?
_No response_
### Information
- [X] The official example notebooks/scripts
- [ ] My own modified scripts
### Related Components
- [ ] LLMs/Chat Models
- [ ] Embedding Models
- [ ] Prompts / Prompt Templates / Prompt Selectors
- [ ] O... | RCE vulnerability in CPAL (causal program-aided language) chain | https://api.github.com/repos/langchain-ai/langchain/issues/7641/comments | 1 | 2023-07-13T07:26:31Z | 2023-08-29T18:44:50Z | https://github.com/langchain-ai/langchain/issues/7641 | 1,802,378,837 | 7,641 | 5,498 |
CVE-2023-38889 | 2023-08-15T17:15:11.887 | An issue in Alluxio v.2.9.3 and before allows an attacker to execute arbitrary code via a crafted script to the username parameter of lluxio.util.CommonUtils.getUnixGroups(java.lang.String). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/Alluxio/alluxio/issues/17766"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alluxio:alluxio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "554323A8-5D2F-4D7D-AFE1-218ECC971A45",
"versionEndExcluding": null,
"versionEndIncluding": "2.9.3",
"versionStartExcludi... | [
"94"
] | 94 | https://github.com/Alluxio/alluxio/issues/17766 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"Alluxio",
"alluxio"
] | **Affected Alluxio Version:**
All the version before the latest(2.9.3).
**Describe the vulnerability**
Passing username with special characters of unix shell as parameter of `alluxio.util.CommonUtils.getUnixGroups(java.lang.String)` can inject malicious commands. For example, the following code
CommonUtils.ge... | There's code injection vulnerability of alluxio.util.CommonUtils.getUnixGroups | https://api.github.com/repos/Alluxio/alluxio/issues/17766/comments | 1 | 2023-07-12T19:55:35Z | 2023-07-13T20:08:58Z | https://github.com/Alluxio/alluxio/issues/17766 | 1,801,657,773 | 17,766 | 5,499 |
CVE-2023-38916 | 2023-08-15T17:15:12.457 | SQL Injection vulnerability in eVotingSystem-PHP v.1.0 allows a remote attacker to execute arbitrary code and obtain sensitive information via the user input fields. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Mohammad-Ajazuddin/eVotingSytem-PHP/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mohammad-ajazuddin:evotingsystem-php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3919AED0-8948-4EA6-A3D6-4F7081B73C90",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/Mohammad-Ajazuddin/eVotingSytem-PHP/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Mohammad-Ajazuddin",
"eVotingSytem-PHP"
] |
**1. SQL Injection Vulnerability**
*Vulnerability Description:* The code directly inserts user input into an SQL query, which can lead to SQL injection attacks. Malicious users can manipulate, delete, or disclose data from the database by injecting malicious SQL code through input fields.
*Code Location:*
```p... | SQL Injection Vulnerability | https://api.github.com/repos/Mohammad-Ajazuddin/eVotingSytem-PHP/issues/1/comments | 1 | 2023-07-12T10:50:35Z | 2023-07-14T06:25:35Z | https://github.com/Mohammad-Ajazuddin/eVotingSytem-PHP/issues/1 | 1,800,708,680 | 1 | 5,500 |
CVE-2023-39659 | 2023-08-15T17:15:12.930 | An issue in langchain langchain-ai v.0.0.232 and before allows a remote attacker to execute arbitrary code via a crafted script to the PythonAstREPLTool._run component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/langchain-ai/langchain/issues/7700"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BAFE4797-0C2C-4BBF-87A5-8747A3539923",
"versionEndExcluding": null,
"versionEndIncluding": "0.0.232",
"versionStartE... | [
"74"
] | 74 | https://github.com/langchain-ai/langchain/issues/7700 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"langchain-ai",
"langchain"
] | ### System Info
langchain: 0.0.232
os: ubuntu 20.04
python: 3.9.13
### Who can help?
_No response_
### Information
- [ ] The official example notebooks/scripts
- [X] My own modified scripts
### Related Components
- [ ] LLMs/Chat Models
- [ ] Embedding Models
- [ ] Prompts / Prompt Templates / ... | Prompt injection which leads to arbitrary code execution | https://api.github.com/repos/langchain-ai/langchain/issues/7700/comments | 5 | 2023-07-14T10:11:00Z | 2023-10-27T19:17:54Z | https://github.com/langchain-ai/langchain/issues/7700 | 1,804,604,289 | 7,700 | 5,501 |
CVE-2023-39661 | 2023-08-15T17:15:13.133 | An issue in pandas-ai v.0.9.1 and before allows a remote attacker to execute arbitrary code via the _is_jailbreak function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gventuri/pandas-ai/issues/410"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gabrieleventuri:pandasai:*:*:*:*:*:python:*:*",
"matchCriteriaId": "B20DF392-01BD-403C-B22F-54FD7BF3841F",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.1",
"versi... | [
"74"
] | 74 | https://github.com/gventuri/pandas-ai/issues/410 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gventuri",
"pandas-ai"
] | ### 🐛 Describe the bug
Hi Team!
In `pandasai 0.8.1`, despite there is a syntax-level fix to [#399](https://github.com/gventuri/pandas-ai/issues/399), it seems that this fix does not work as intended, and although the PoC mentioned in [#399](https://github.com/gventuri/pandas-ai/issues/399) is no longer attackable,... | The fix of #issue399 (RCE from prompt) can be bypassed. | https://api.github.com/repos/sinaptik-ai/pandas-ai/issues/410/comments | 4 | 2023-07-29T06:55:31Z | 2024-06-01T00:20:01Z | https://github.com/sinaptik-ai/pandas-ai/issues/410 | 1,827,352,294 | 410 | 5,502 |
CVE-2023-39662 | 2023-08-15T17:15:13.313 | An issue in llama_index v.0.7.13 and before allows a remote attacker to execute arbitrary code via the `exec` parameter in PandasQueryEngine function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryjliu/llama_index/issues/7054"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:llamaindex_project:llamaindex:*:*:*:*:*:python:*:*",
"matchCriteriaId": "C4B705CE-A0F1-407E-97A8-CEEC3B2D2C08",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.13",
... | [
"74"
] | 74 | https://github.com/jerryjliu/llama_index/issues/7054 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryjliu",
"llama_index"
] | ### Bug Description
In `PandasQueryEngine` (a agent like module to help user query pandas file or data structure), dangerous function `exec` is used which will lead to code execution. If the code is running on a server, it will lead to RCE by the attacker, with just one line prompt.
### Version
0.7.13
###... | [Bug]: Prompt injection which will lead to RCE | https://api.github.com/repos/run-llama/llama_index/issues/7054/comments | 6 | 2023-07-27T08:02:27Z | 2023-11-28T08:00:19Z | https://github.com/run-llama/llama_index/issues/7054 | 1,823,831,779 | 7,054 | 5,503 |
CVE-2023-38905 | 2023-08-17T19:15:12.873 | SQL injection vulnerability in Jeecg-boot v.3.5.0 and before allows a local attacker to cause a denial of service via the Benchmark, PG_Sleep, DBMS_Lock.Sleep, Waitfor, DECODE, and DBMS_PIPE.RECEIVE_MESSAGE functions. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/wealeson1/e24fc8575f4e051320d69e9a75080642"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jeec... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7CCC4761-FDE8-4C1D-99BA-74DB3DEB267A",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExclud... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/4737 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
3.5.0
##### 前端版本:vue3版?还是 vue2版?
vue3版
##### 问题描述:
/sys/duplicate/check 接口SQL注入,checksql可以被绕过。
##### 截图&代码:
延时10秒。
<img width="1165" alt="image" src="https://user-images.githubusercontent.com/46522822/226792979-cf92d1d9-4579-433e-af85-1cb901480015.png">
不延时。
<img width="1173" alt="image" src=... | [CVE-2023-38905] sys/duplicate/check SQL注入 | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/4737/comments | 4 | 2023-03-22T03:23:48Z | 2023-09-04T09:30:59Z | https://github.com/jeecgboot/JeecgBoot/issues/4737 | 1,634,994,366 | 4,737 | 5,504 |
CVE-2023-39741 | 2023-08-17T19:15:12.977 | lrzip v0.651 was discovered to contain a heap overflow via the libzpaq::PostProcessor::write(int) function at /libzpaq/libzpaq.cpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://gist.github.com/huanglei3/ec9090096aa92445cf0a8baa8e929084"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ckolivas/lrzip/issues/246"
},
{
"source": "cv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:long_range_zip_project:long_range_zip:0.651:*:*:*:*:*:*:*",
"matchCriteriaId": "052FD35D-AAF5-4D09-8F2A-E56F6C3B63D7",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/ckolivas/lrzip/issues/246 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ckolivas",
"lrzip"
] | project : lrzip 0.651
exec : ./lrzip -t file
Decompressing...
=================================================================
==641214==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6140000001ec at pc 0x0000005260ac bp 0x7f4b526e35d0 sp 0x7f4b526e35c8
WRITE of size 1 at 0x6140000001ec thread T2... | heap-buffer-overflow in libzpaq/libzpaq.cpp:1208:25 libzpaq::PostProcessor::write(int) | https://api.github.com/repos/ckolivas/lrzip/issues/246/comments | 3 | 2023-08-01T07:36:42Z | 2023-08-18T12:57:00Z | https://github.com/ckolivas/lrzip/issues/246 | 1,830,650,019 | 246 | 5,505 |
CVE-2023-39743 | 2023-08-17T19:15:13.077 | lrzip-next LZMA v23.01 was discovered to contain an access violation via the component /bz3_decode_block src/libbz3.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://gist.github.com/huanglei3/ec9090096aa92445cf0a8baa8e929084"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://github.com/huanglei3/lrzip-next-poc/tree/main"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pete4abw:lzma_software_development_kit:23.01:*:*:*:*:*:*:*",
"matchCriteriaId": "7E666D44-321E-4DDC-9A5E-522B7809C86B",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"284"
] | 284 | https://github.com/pete4abw/lrzip-next/issues/132 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"pete4abw",
"lrzip-next"
] | ### lrzip-next Version
lzma 23.01(default)
### lrzip-next command line
./lrzip-next -vvt file
### What happened?
./lrzip-next -vvt poc
The following options are in effect for this INTEGRITY TEST.
Threading is ENABLED. Number of CPUs detected: 4
Detected 8,287,764,480 bytes ram
Nice Value: 19
Show Progress
Ma... | Read zero page memory | https://api.github.com/repos/pete4abw/lrzip-next/issues/132/comments | 1 | 2023-08-05T02:20:36Z | 2023-08-05T11:29:47Z | https://github.com/pete4abw/lrzip-next/issues/132 | 1,837,526,801 | 132 | 5,506 |
CVE-2023-2318 | 2023-08-19T06:15:46.883 | DOM-based XSS in src/muya/lib/contentState/pasteCtrl.js in MarkText 0.17.1 and before on Windows, Linux and macOS allows arbitrary JavaScript code to run in the context of MarkText main window. This vulnerability can be exploited if a user copies text from a malicious webpage and paste it into MarkText. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 8.6,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "info@starlabs.sg",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/marktext/marktext/issues/3618"
},
{
"source": "info@starlabs.sg",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://starlabs.sg/advisories/23/2... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:marktext:marktext:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB68239C-90DB-4BD3-AF7E-5A79E97A7093",
"versionEndExcluding": null,
"versionEndIncluding": "0.17.1",
"versionStartExcl... | [
"79"
] | 79 | https://github.com/marktext/marktext/issues/3618 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"marktext",
"marktext"
] | ## Summary:
There is a DOM-based XSS in MarkText allowing arbitrary JavaScript code to run in the context of MarkText main window. This vulnerability can be exploited if a user copies text from a malicious webpage and paste it into MarkText.
## Vulnerability Details:
When the user performs paste operations, ... | Security Issue: DOM-Based XSS leading to RCE | https://api.github.com/repos/marktext/marktext/issues/3618/comments | 2 | 2023-04-28T03:43:30Z | 2023-05-13T21:32:54Z | https://github.com/marktext/marktext/issues/3618 | 1,687,847,262 | 3,618 | 5,508 |
CVE-2023-4446 | 2023-08-21T01:15:10.320 | A vulnerability, which was classified as critical, was found in OpenRapid RapidCMS 1.3.1. This affects an unknown part of the file template/default/category.php. The manipulation of the argument id leads to sql injection. The exploit has been disclosed to the public and may be used. The associated identifier of this vu... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.2,
"confidentialityImpact... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/OpenRapid/rapidcms/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/OpenRapid/rapidcms/issues/3 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in `template/default/category.php` .
For more details, see:
[RapidCMS-SQLi-1.pdf](https://github.com/OpenRapid/rapidcms/files/12329060/RapidCMS-SQLi-1.pdf)
| SQL injection vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/3/comments | 0 | 2023-08-13T08:23:15Z | 2023-08-13T08:24:48Z | https://github.com/OpenRapid/rapidcms/issues/3 | 1,848,481,794 | 3 | 5,509 |
CVE-2023-4447 | 2023-08-21T02:15:10.120 | A vulnerability has been found in OpenRapid RapidCMS 1.3.1 and classified as critical. This vulnerability affects unknown code of the file admin/article-chat.php. The manipulation of the argument id leads to sql injection. The attack can be initiated remotely. The exploit has been disclosed to the public and may be use... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/OpenRapid/rapidcms/issues/4"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.com/?cti... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/OpenRapid/rapidcms/issues/4 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain SQL injection vulnerability in `admin/article-chat.php` .
For more details, see:
[RapidCMS-SQLi-2.pdf](https://github.com/OpenRapid/rapidcms/files/12329065/RapidCMS-SQLi-2.pdf)
| SQL injection vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/4/comments | 0 | 2023-08-13T08:26:23Z | 2023-08-13T08:26:23Z | https://github.com/OpenRapid/rapidcms/issues/4 | 1,848,482,818 | 4 | 5,510 |
CVE-2023-4448 | 2023-08-21T02:15:10.227 | A vulnerability was found in OpenRapid RapidCMS 1.3.1 and classified as critical. This issue affects some unknown processing of the file admin/run-movepass.php. The manipulation of the argument password/password2 leads to weak password recovery. The attack may be initiated remotely. The exploit has been disclosed to th... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch"
],
"url": "https://github.com/OpenRapid/rapidcms/commit/4dff387283060961c362d50105ff8da8ea40bcbe#diff-fc57d4c69cf5912c6edb5233c6df069a91106ebd481c115faf1ea124478b26d0"
},
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrapid:rapidcms:1.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "D66CF166-4A08-45F5-9577-38D3CE25AFBA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"640"
] | 640 | https://github.com/OpenRapid/rapidcms/issues/5 | [
"Issue Tracking",
"Patch"
] | github.com | [
"OpenRapid",
"rapidcms"
] | RapidCMS Dev.1.3.1 was discovered to contain Administrator password reset vulnerability in `admin/run-movepass.php`.
For more details, see:
[RapidCMS-PasswordReset.pdf](https://github.com/OpenRapid/rapidcms/files/12329073/RapidCMS-PasswordReset.pdf)
| Administrator password reset vulnerability exists in RapidCMS Dev.1.3.1 | https://api.github.com/repos/OpenRapid/rapidcms/issues/5/comments | 1 | 2023-08-13T08:32:42Z | 2023-08-14T06:42:27Z | https://github.com/OpenRapid/rapidcms/issues/5 | 1,848,485,398 | 5 | 5,511 |
CVE-2023-38899 | 2023-08-21T12:15:08.483 | SQL injection vulnerability in berkaygediz O_Blog v.1.0 allows a local attacker to escalate privileges via the secure_file_priv component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://o.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/berkaygediz/O_Blog"
},
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:berkaygediz:o_blog:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B207331-2B17-4DEC-8DD7-8351A3D1822F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/berkaygediz/O_Blog/issues/2 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"berkaygediz",
"O_Blog"
] | SQL injection bypass login:
POST /O_Blog-main/ HTTP/1.1
Host: 192.168.150.131
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, de... | sql sql injection | https://api.github.com/repos/berkaygediz/O_Blog/issues/2/comments | 1 | 2023-07-14T03:51:40Z | 2023-07-14T17:12:50Z | https://github.com/berkaygediz/O_Blog/issues/2 | 1,804,111,647 | 2 | 5,512 |
CVE-2023-38836 | 2023-08-21T17:15:47.633 | File Upload vulnerability in BoidCMS v.2.0.0 allows a remote attacker to execute arbitrary code by adding a GIF header to bypass MIME type checks. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://boidcms.com"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/175026/BoidCMS-2.0.0-Shell-Upload.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boidcms:boidcms:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9CA34CF5-1C33-4846-B9C0-718CD2A9766A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/BoidCMS/BoidCMS/issues/27 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"BoidCMS",
"BoidCMS"
] | # Overview
By default, an authenticated user cannot upload a PHP file due to mime type checks but it can be bypassed by adding a GIF header at the beginning of the PHP file. **"finfo"** considers a PHP file with GIF header as a GIF file instead of PHP.
```php
// shell.php
GIF89a;
<?php system($_GET["cmd"]); ?>
``... | [VULNERABILITY] Authenticated file upload vulnerability - [leading to shell command execution] | https://api.github.com/repos/BoidCMS/BoidCMS/issues/27/comments | 9 | 2023-07-13T09:28:41Z | 2023-07-15T23:44:08Z | https://github.com/BoidCMS/BoidCMS/issues/27 | 1,802,608,596 | 27 | 5,513 |
CVE-2023-38961 | 2023-08-21T17:15:47.973 | Buffer Overflwo vulnerability in JerryScript Project jerryscript v.3.0.0 allows a remote attacker to execute arbitrary code via the scanner_is_context_needed component in js-scanner-until.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5092"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/5092 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: https://github.com/jerryscript-project/jerryscript/commit/05dbbd134c3b9e2482998f267857dd3722001cd7
Version: v3.0.0
###### Build platform
Ubuntu 20.04.5 LTS (Linux 5.4.0-144-generic x86_64)
###### Build steps
```sh
python ./tools/build.py --clean --compile-flag=-m32 --compi... | heap-buffer-overflow in scanner_is_context_needed | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5092/comments | 1 | 2023-06-24T08:32:20Z | 2024-11-22T09:32:26Z | https://github.com/jerryscript-project/jerryscript/issues/5092 | 1,772,536,756 | 5,092 | 5,514 |
CVE-2023-38976 | 2023-08-21T17:15:48.127 | An issue in weaviate v.1.20.0 allows a remote attacker to cause a denial of service via the handleUnbatchedGraphQLRequest function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://aisec.today/Weaviate-26981c6c5f794077bd51d24c88cebf7a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/weaviate/weaviate/issues/3258"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:weaviate:weaviate:1.20.0:*:*:*:*:*:*:*",
"matchCriteriaId": "78FD46DA-F678-421E-878B-A2C6F5B94714",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/weaviate/weaviate/issues/3258 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"weaviate",
"weaviate"
] | version : 1.20.0
1. run `AUTHENTICATION_ANONYMOUS_ACCESS_ENABLED=true PERSISTENCE_DATA_PATH=/r3p/vdb/wea/ ./weaviate-server --port=8080 --scheme=http`
2. send `curl -X POST -H 'Content-Type: application/json' -d '[{"operationName":"r3","query":"r3","variables":[1337]}]' http://127.0.0.1:8080/v1/graphql/batch`
... | panic when type assertions in function handleUnbatchedGraphQLRequest | https://api.github.com/repos/weaviate/weaviate/issues/3258/comments | 1 | 2023-07-13T06:52:11Z | 2023-08-22T16:20:58Z | https://github.com/weaviate/weaviate/issues/3258 | 1,802,328,314 | 3,258 | 5,515 |
CVE-2023-39094 | 2023-08-21T17:15:48.437 | Cross Site Scripting vulnerability in ZeroWdd studentmanager v.1.0 allows a remote attacker to execute arbitrary code via the username parameter in the student list function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ZeroWdd/studentmanager/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zerowdd:studentmanager:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2375E47D-661D-4707-AC3E-A71C23BEF7FB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/ZeroWdd/studentmanager/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ZeroWdd",
"studentmanager"
] | After logging in, modifying the 'username' parameter of the [student list] can cause a Stored XSS (Cross-Site Scripting) attack.
<img width="1352" alt="image" src="https://github.com/ZeroWdd/studentmanager/assets/56468203/3d3a1e96-5eef-44c6-ac98-a73da625b122">
<img width="957" alt="image" src="https://github.com/Zero... | There is a Stored-XSS vulnerability in studentmanager | https://api.github.com/repos/ZeroWdd/studentmanager/issues/12/comments | 0 | 2023-07-20T16:41:13Z | 2023-07-20T16:41:13Z | https://github.com/ZeroWdd/studentmanager/issues/12 | 1,814,409,959 | 12 | 5,516 |
CVE-2023-39106 | 2023-08-21T17:15:48.587 | An issue in Nacos Group Nacos Spring Project v.1.1.1 and before allows a remote attacker to execute arbitrary code via the SnakeYamls Constructor() component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/nacos-group/nacos-spring-project/issues/314"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alibabacloud:nacos_spring_project:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E5503D03-947F-4623-8E7B-C0F3BA4B456E",
"versionEndExcluding": null,
"versionEndIncluding": "1.1.1",
"v... | [
"502"
] | 502 | https://github.com/nacos-group/nacos-spring-project/issues/314 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"nacos-group",
"nacos-spring-project"
] | ## Issue Description
The SnakeYaml's Constructor() class is used in the component nacos-spring-context, but it does not restrict types that can be instantiated during deserialization.
### Describe what happened (or what feature you want)
Deserializing yaml content provided by an attacker can lead to remote co... | YAML deserialization vulnerability leads to RCE | https://api.github.com/repos/nacos-group/nacos-spring-project/issues/314/comments | 1 | 2023-05-29T03:23:07Z | 2023-11-30T02:00:20Z | https://github.com/nacos-group/nacos-spring-project/issues/314 | 1,729,944,198 | 314 | 5,517 |
CVE-2023-39660 | 2023-08-21T17:15:48.797 | An issue in Gaberiele Venturi pandasai v.0.8.0 and before allows a remote attacker to execute arbitrary code via a crafted request to the prompt function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/gventuri/pandas-ai/issues/399"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/gventuri/pandas... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gabrieleventuri:pandasai:*:*:*:*:*:python:*:*",
"matchCriteriaId": "B67616D2-0664-414C-B545-438A4BA2F0FE",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.0",
"versi... | [
"94"
] | 94 | https://github.com/gventuri/pandas-ai/issues/399 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"gventuri",
"pandas-ai"
] | ### 🐛 Describe the bug
Hi, Team
Today, while I'm reading the source code of pandasai, I found there is a RCE vulnerability which can be triggered by just one line of prompt.
I've seen that there are already some issues that pointed out the security concern about using `exec` such as https://github.com/gventuri/... | Bypass the security check, RCE again with prompt injection. | https://api.github.com/repos/sinaptik-ai/pandas-ai/issues/399/comments | 3 | 2023-07-27T14:44:24Z | 2023-07-28T23:47:03Z | https://github.com/sinaptik-ai/pandas-ai/issues/399 | 1,824,535,343 | 399 | 5,518 |
CVE-2020-18378 | 2023-08-22T19:15:55.143 | A NULL pointer dereference was discovered in SExpressionWasmBuilder::makeBlock in wasm/wasm-s-parser.c in Binaryen 1.38.26. A crafted wasm input can cause a segmentation fault, leading to denial-of-service, as demonstrated by wasm-as. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1900"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:1.38.26:*:*:*:*:*:*:*",
"matchCriteriaId": "DFEC4DA4-B057-4B2A-8126-17D04D8A66A5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"476"
] | 476 | https://github.com/WebAssembly/binaryen/issues/1900 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi, there.
A Heap-buffer-overflow problem was discovered in wasm::WasmBinaryBuilder::visitBlock(wasm::Block*) function in simple_ast.h in /src/wasm/wasm-binary.cpp, as distributed in Binaryen 1.38.26. A crafted wasm input can cause segment faults and I have confirmed them with address sanitizer too.
Here are the ... | Heap-buffer-overflow in /src/wasm/wasm-binary.cpp in wasm::WasmBinaryBuilder::visitBlock(wasm::Block*) in Binaryen 1.38.26 | https://api.github.com/repos/WebAssembly/binaryen/issues/1900/comments | 8 | 2019-02-06T07:37:30Z | 2023-08-25T16:48:04Z | https://github.com/WebAssembly/binaryen/issues/1900 | 407,112,198 | 1,900 | 5,519 |
CVE-2020-18770 | 2023-08-22T19:15:55.550 | An issue was discovered in function zzip_disk_entry_to_file_header in mmapped.c in zziplib 0.13.69, which will lead to a denial-of-service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gdraheim/zziplib/issues/69"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zziplib_project:zziplib:0.13.69:*:*:*:*:*:*:*",
"matchCriteriaId": "82DA4CCB-B3C3-4298-9277-8C295AAAD14A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"400"
] | 400 | https://github.com/gdraheim/zziplib/issues/69 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gdraheim",
"zziplib"
] | POC:
[zip_poc.zip](https://github.com/gdraheim/zziplib/files/3001317/zip_poc.zip)
There exisits one invalid memroy access issue in zzip_disk_entry_to_file_header in mmapped.c in zziplib 0.13.69, which will lead to a denial-of-service. This bug can be triggered by the executable unzzip-mem.
$ unzzip-mem $poc
A... | one invalid memroy access issue in zzip_disk_entry_to_file_header in mmapped.c | https://api.github.com/repos/gdraheim/zziplib/issues/69/comments | 4 | 2019-03-25T03:02:30Z | 2024-11-23T09:00:48Z | https://github.com/gdraheim/zziplib/issues/69 | 424,703,318 | 69 | 5,520 |
CVE-2020-18781 | 2023-08-22T19:15:56.027 | Heap buffer overflow vulnerability in FilePOSIX::read in File.cpp in audiofile 0.3.6 may cause denial-of-service via a crafted wav file, this bug can be triggered by the executable sfconvert. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mpruett/audiofile/issues/56"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:audiofile:audiofile:0.3.6:*:*:*:*:*:*:*",
"matchCriteriaId": "3C7E74B2-432B-4CCD-873F-AA7E012D8C7F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/mpruett/audiofile/issues/56 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mpruett",
"audiofile"
] | one heap buffer overflow in FilePOSIX::read in File.cpp in master branch.
[poc.zip](https://github.com/mpruett/audiofile/files/3901168/poc.zip)
$uname -a
Linux ubuntu 4.15.0-70-generic #79~16.04.1-Ubuntu SMP Tue Nov 12 14:01:10 UTC 2019 x86_64 GNU/Linux
$./sfconvert poc.wav output format wave
asan:
========... | one heap buffer overflow in FilePOSIX::read in File.cpp | https://api.github.com/repos/mpruett/audiofile/issues/56/comments | 2 | 2019-11-28T10:32:34Z | 2023-11-07T19:28:03Z | https://github.com/mpruett/audiofile/issues/56 | 529,827,358 | 56 | 5,521 |
CVE-2020-18831 | 2023-08-22T19:15:56.220 | Buffer Overflow vulnerability in tEXtToDataBuf function in pngimage.cpp in Exiv2 0.27.1 allows remote attackers to cause a denial of service and other unspecified impacts via use of crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/828"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://www.exiv2.org/download.htm... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:0.27.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9E196C7D-A075-43E0-A620-C2D7C0EB559F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/Exiv2/exiv2/issues/828 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **Describe the bug**
An issue was discovered in Exiv2 0.27.1. There is reading beyond buffer at tEXtToDataBuf in the file pngimage.cpp. This can be triggered by a crafted file. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
**To Reproduce**
Steps to r... | Segmentation fault in pngimage.cpp:329. | https://api.github.com/repos/Exiv2/exiv2/issues/828/comments | 2 | 2019-05-06T06:22:34Z | 2023-08-24T12:18:28Z | https://github.com/Exiv2/exiv2/issues/828 | 440,554,840 | 828 | 5,522 |
CVE-2020-19725 | 2023-08-22T19:16:04.567 | There is a use-after-free vulnerability in file pdd_simplifier.cpp in Z3 before 4.8.8. It occurs when the solver attempt to simplify the constraints and causes unexpected memory access. It can cause segmentation faults or arbitrary code execution. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Z3Prover/z3/issues/3363"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:z3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6D8EF4B1-776B-4405-896B-9C0EC073D347",
"versionEndExcluding": "4.8.8",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"416"
] | 416 | https://github.com/Z3Prover/z3/issues/3363 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Z3Prover",
"z3"
] | Hi, there.
There is a use after free issue that causes segmentation fault using z3.
To reproduce this issue, simply run
z3 poc.smt2
[z3-uaf_pdd_simplified.smt2.zip](https://github.com/Z3Prover/z3/files/4337612/z3-uaf_pdd_simplified.smt2.zip)
OS: Ubuntu 16.06
commit 6ad261e
Here is the trace reported by... | use after free in ../src/math/grobner/pdd_simplifier.cpp:131 | https://api.github.com/repos/Z3Prover/z3/issues/3363/comments | 0 | 2020-03-16T10:43:10Z | 2020-03-16T18:45:17Z | https://github.com/Z3Prover/z3/issues/3363 | 582,187,536 | 3,363 | 5,523 |
CVE-2020-22217 | 2023-08-22T19:16:19.050 | Buffer overflow vulnerability in c-ares before 1_16_1 thru 1_17_0 via function ares_parse_soa_reply in ares_parse_soa_reply.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/c-ares/c-ares/issues/333"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/d... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c-ares:c-ares:1.16.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F414AE45-51A4-439A-9522-74D765564707",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/c-ares/c-ares/issues/333 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"c-ares",
"c-ares"
] | we found read-heap-buffer-overflow by fuzzing c-ares master-branch

lenth unchecked before read aptr
 | https://api.github.com/repos/c-ares/c-ares/issues/333/comments | 6 | 2020-05-21T13:13:41Z | 2023-09-07T18:42:30Z | https://github.com/c-ares/c-ares/issues/333 | 622,490,646 | 333 | 5,524 |
CVE-2020-22219 | 2023-08-22T19:16:19.190 | Buffer Overflow vulnerability in function bitwriter_grow_ in flac before 1.4.0 allows remote attackers to run arbitrary code via crafted input to the encoder. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xiph/flac/issues/215"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/09/msg00028.html"
},
{
"source": "cve@mit... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flac_project:flac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "13B55CB3-C5B9-46DF-B36A-EB50126F50C7",
"versionEndExcluding": "1.4.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"120"
] | 120 | https://github.com/xiph/flac/issues/215 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"xiph",
"flac"
] | we found wild-addr-write by fuzzing flac-master:
```
==217==ERROR: AddressSanitizer: SEGV on unknown address 0xb6029a2c (pc 0x0822a2ae bp 0xffeb31e8 sp 0xffeb30a0 T0)
==217==The signal is caused by a WRITE memory access.
SCARINESS: 30 (wild-addr-write)
#0 0x822a2ad in FLAC__bitwriter_write_raw_uint32_nocheck /... | wild-addr-write found by fuzz | https://api.github.com/repos/xiph/flac/issues/215/comments | 18 | 2020-06-02T03:09:10Z | 2023-09-11T13:32:44Z | https://github.com/xiph/flac/issues/215 | 628,865,332 | 215 | 5,525 |
CVE-2020-22570 | 2023-08-22T19:16:19.297 | Memcached 1.6.0 before 1.6.3 allows remote attackers to cause a denial of service (daemon crash) via a crafted meta command. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/memcached/memcached/issues/636"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/memc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:memcached:memcached:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9CDEE25B-32D1-4097-BDAB-3C5673C6CE5B",
"versionEndExcluding": "1.6.3",
"versionEndIncluding": null,
"versionStartExc... | [
"77"
] | 77 | https://github.com/memcached/memcached/issues/636 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"memcached",
"memcached"
] | memcached maintainer,
I found a NULL pointer reference bug in code of memcached, which could conduct DoS by remote artificial command.
The affected memcached version: >1.6.0.
The bug location is at file: memcached.c, detailed information as the following:
In the function "process_mget_command", the local v... | NULL pointer reference conduct DoS | https://api.github.com/repos/memcached/memcached/issues/636/comments | 3 | 2020-03-27T09:47:10Z | 2020-03-28T22:29:36Z | https://github.com/memcached/memcached/issues/636 | 589,010,832 | 636 | 5,526 |
CVE-2020-22628 | 2023-08-22T19:16:19.353 | Buffer Overflow vulnerability in LibRaw::stretch() function in libraw\src\postprocessing\aspect_ratio.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibRaw/LibRaw/issues/269"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libraw:libraw:*:*:*:*:*:*:*:*",
"matchCriteriaId": "27DFF8C5-9D6E-46BE-AC83-B1CFA0EC18E9",
"versionEndExcluding": null,
"versionEndIncluding": "0.19.5",
"versionStartExcludin... | [
"120"
] | 120 | https://github.com/LibRaw/LibRaw/issues/269 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibRaw",
"LibRaw"
] | **Description**
An out-of-bounds read vulnerability exists within the "LibRaw::stretch()" function (libraw\src\postprocessing\aspect_ratio.cpp) when parsing a crafted CRW file.
**Steps to Reproduce**
(poc archive password= girlelecta):
https://drive.google.com/open?id=1Y70DxvWYfsNS7DBu4cuoUVOoMOyheA8O
cmd:... | "LibRaw::stretch()" Out-of-bounds read vulnerability | https://api.github.com/repos/LibRaw/LibRaw/issues/269/comments | 2 | 2020-03-25T18:57:59Z | 2023-08-24T14:09:40Z | https://github.com/LibRaw/LibRaw/issues/269 | 587,920,532 | 269 | 5,527 |
CVE-2020-25887 | 2023-08-22T19:16:19.887 | Buffer overflow in mg_resolve_from_hosts_file in Mongoose 6.18, when reading from a crafted hosts file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cesanta/mongoose/issues/1140"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cesant... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cesanta:mongoose:6.18:*:*:*:*:*:*:*",
"matchCriteriaId": "1F4949BC-D04D-4DB8-9E7E-4459648D712E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/cesanta/mongoose/issues/1140 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"cesanta",
"mongoose"
] | Buffer overflow in mg_resolve_from_hosts_file function (line 124) in mongoose/src/mg_resolv.c in Mongoose 6.18, where sscanf copies data from p to alias without limiting the size of the copied data not to exceed the alias array size, which is 256. Note that p can be up to 1024 (minus the IP digits) and is copied from a... | Buffer overflow in mg_resolve_from_hosts_file function | https://api.github.com/repos/cesanta/mongoose/issues/1140/comments | 1 | 2020-08-20T00:41:18Z | 2020-12-18T13:45:42Z | https://github.com/cesanta/mongoose/issues/1140 | 682,268,829 | 1,140 | 5,528 |
CVE-2020-26652 | 2023-08-22T19:16:19.943 | An issue was discovered in function nl80211_send_chandef in rtl8812au v5.6.4.2 allows attackers to cause a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/aircrack-ng/rtl8812au/issues/730"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ai... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:realtek:rtl8812au_firmware:5.6.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "957AECA6-1567-42B3-996E-0786C82DCB84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"400"
] | 400 | https://github.com/aircrack-ng/rtl8812au/issues/730 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"aircrack-ng",
"rtl8812au"
] | **testing environment**
root@kali:~# uname -r
5.6.0-kali2-amd64
**poc:**
`
#!/usr/bin/env python
#coding=utf-8
import time
import socket
AP_MAC = "00:22:66:88:22:00"
STA_MAC = "00:13:ef:f1:04:ef"
ETH_P_ALL = 3
IFACE = "wlan0"
def mac2str(mac):
return "".join(map(lambda x: chr(int(x, 16)), mac.... | fuzzing wifi ,network will down, result is net/wireless/nl80211.c:3159 nl80211_send_chandef+0x14b/0x160 [cfg80211] | https://api.github.com/repos/aircrack-ng/rtl8812au/issues/730/comments | 0 | 2020-09-27T02:40:40Z | 2020-09-27T09:04:46Z | https://github.com/aircrack-ng/rtl8812au/issues/730 | 709,652,419 | 730 | 5,529 |
CVE-2021-32292 | 2023-08-22T19:16:20.350 | An issue was discovered in json-c from 20200420 (post 0.14 unreleased code) through 0.15-20200726. A stack-buffer-overflow exists in the auxiliary sample program json_parse which is located in the function parseit. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/json-c/json-c/issues/654"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.netapp.com/advisory/ntap-20230929-0010/"
},
{
"source": "cve@mitre.org... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:json-c_project:json-c:0.15-20200726:*:*:*:*:*:*:*",
"matchCriteriaId": "5C367D32-8FA6-49E0-A6D5-2D86473F5E75",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"787"
] | 787 | https://github.com/json-c/json-c/issues/654 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"json-c",
"json-c"
] | ## System info
Ubuntu X64, clang 6.0, json_parse (latest master [56a89f](https://github.com/json-c/json-c/commit/56a89f902f360c91a80ac0c7419d2ba1aa8e8634))
## Configure
cmake ..-DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address"
##... | A stack-buffer-overflow in json_parse.c:89:44 | https://api.github.com/repos/json-c/json-c/issues/654/comments | 5 | 2020-08-05T02:18:37Z | 2020-08-07T14:19:02Z | https://github.com/json-c/json-c/issues/654 | 673,200,701 | 654 | 5,530 |
CVE-2021-40211 | 2023-08-22T19:16:21.427 | An issue was discovered with ImageMagick 7.1.0-4 via Division by zero in function ReadEnhMetaFile of coders/emf.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/4097"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.1.0-4:*:*:*:*:*:*:*",
"matchCriteriaId": "7C1767C6-89C1-4D1E-93E0-AC04EF098E16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"369"
] | 369 | https://github.com/ImageMagick/ImageMagick/issues/4097 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### ImageMagick version
7.1.0
### Operating system
All system
### Operating system, version and so on
All system,the latest version
### Description
pBits can be controlled by an attacker,a division-by-zero exception can happen in function ReadEnhMetaFile() of coders/emf.c at line 428,431.
![222]... | Division by zero in ReadEnhMetaFile() of coders/emf.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/4097/comments | 0 | 2021-08-21T07:53:53Z | 2021-08-21T11:34:44Z | https://github.com/ImageMagick/ImageMagick/issues/4097 | 976,075,255 | 4,097 | 5,531 |
CVE-2021-46179 | 2023-08-22T19:16:21.883 | Reachable Assertion vulnerability in upx before 4.0.0 allows attackers to cause a denial of service via crafted file passed to the the readx function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/upx/upx/issues/545"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/upx/upx/issues/545"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1E4C95CD-E2A9-47E3-9866-FD4B7ECF14AA",
"versionEndExcluding": "4.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"617"
] | 617 | https://github.com/upx/upx/issues/545 | [
"Issue Tracking",
"Patch"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggest... | Assertion `(unsigned)len <= buf->getSize()' failed in file.cpp:275 | https://api.github.com/repos/upx/upx/issues/545/comments | 1 | 2021-12-09T14:42:36Z | 2021-12-27T03:43:07Z | https://github.com/upx/upx/issues/545 | 1,075,652,035 | 545 | 5,532 |
CVE-2022-25024 | 2023-08-22T19:16:22.173 | The json2xml package through 3.12.0 for Python allows an error in typecode decoding enabling a remote attack that can lead to an exception, causing a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/vinitkumar/json2xml/issues/106"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/vinitkumar/jso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vinitkumar:json2xml:*:*:*:*:*:python:*:*",
"matchCriteriaId": "FD4849CA-C0B1-486D-B26D-E383B997A949",
"versionEndExcluding": null,
"versionEndIncluding": "3.12.0",
"versionSt... | [
"754"
] | 754 | https://github.com/vinitkumar/json2xml/issues/106 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"vinitkumar",
"json2xml"
] | **Describe the bug**
I found out that theJson2xml(data).to_xml() method can raise a UnicodeDecodeError leading to a crash of the running program.
This could be problematic if users of the library are dealing with untrusted data since this issue will lead to a DoS. This should be detected and an execption should be ... | [Uncaught exception] UnicodeDecodeError when calling to_xml with arbitrary data | https://api.github.com/repos/vinitkumar/json2xml/issues/106/comments | 7 | 2022-02-07T11:54:32Z | 2022-02-10T17:28:28Z | https://github.com/vinitkumar/json2xml/issues/106 | 1,125,887,018 | 106 | 5,533 |
CVE-2022-26592 | 2023-08-22T19:16:22.240 | Stack Overflow vulnerability in libsass 3.6.5 via the CompoundSelector::has_real_parent_ref function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/sass/libsass/issues/3174"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/sass/libsa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sass-lang:libsass:3.6.5:*:*:*:*:*:*:*",
"matchCriteriaId": "945F5630-C5D9-4A40-AF30-E994FC017A72",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/sass/libsass/issues/3174 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"sass",
"libsass"
] | I use AFL to fuzz libsass, and it finds a stack-overflow on the target.
**version**: **3.6.4, 3.6.5**
**POC**:[**poc**](https://github.com/lmm-1997/libsass/blob/main/id%EF%80%BA000013%2Csig%EF%80%BA11%2Csrc%EF%80%BA013228%2B013477%2Cop%EF%80%BAsplice%2Crep%EF%80%BA2)
**CMD**:**./sassc poc**
### ASAN has rep... | AddressSanitizer: stack-overflow on address 0x7ffff3e46ff8 (pc 0x7f13120dddd5 bp 0x615000000be8 sp 0x7ffff3e47000 T0) | https://api.github.com/repos/sass/libsass/issues/3174/comments | 2 | 2022-02-25T08:20:47Z | 2023-12-21T08:31:37Z | https://github.com/sass/libsass/issues/3174 | 1,150,168,432 | 3,174 | 5,534 |
CVE-2022-34038 | 2023-08-22T19:16:23.000 | Etcd v3.5.4 allows remote attackers to cause a denial of service via function PageWriter.write in pagewriter.go. NOTE: the vendor's position is that this is not a vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/etcd-io/etcd/pull/14022"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/etcd-io/etcd/pull/14452"
},
{
"source": "cve@mitre.org",
"tags": null,
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:etcd:etcd:3.5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "40857CA1-2C0D-4602-91D3-45CFC0472736",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/golang/vulndb/issues/2016#issuecomment-1698677762 | null | github.com | [
"golang",
"vulndb"
] | CVE-2022-34038 references [github.com/etcd-io/etcd](https://github.com/etcd-io/etcd), which may be a Go module.
Description:
Etcd v3.5.4 allows remote attackers to cause a denial of service via function PageWriter.write in pagewriter.go
References:
- NIST: https://nvd.nist.gov/vuln/detail/CVE-2022-34038
- JSON: https... | x/vulndb: potential Go vuln in github.com/etcd-io/etcd: CVE-2022-34038 | https://api.github.com/repos/golang/vulndb/issues/2016/comments | 5 | 2023-08-22T19:02:47Z | 2023-08-30T16:10:57Z | https://github.com/golang/vulndb/issues/2016 | 1,862,033,789 | 2,016 | 5,535 |
CVE-2022-43357 | 2023-08-22T19:16:29.527 | Stack overflow vulnerability in ast_selectors.cpp in function Sass::CompoundSelector::has_real_parent_ref in libsass:3.6.5-8-g210218, which can be exploited by attackers to causea denial of service (DoS). Also affects the command line driver for libsass, sassc 3.6.2. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Permissions Required",
"Third Party Advisory"
],
"url": "https://drive.google.com/file/d/1aC5q3czen0atI91fuBIoCBFkS30_OSWX/"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sass-lang:libsass:3.6.5-8-g210218:*:*:*:*:*:*:*",
"matchCriteriaId": "DD554F0E-70F8-4860-8F1A-292E60E0F9A3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"787"
] | 787 | https://github.com/sass/libsass/issues/3177 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"sass",
"libsass"
] |
### **1. Description**
A stack-overflow has occurred in `Sass::CompoundSelector::has_real_parent_ref()` of `src/ast_selectors.cpp:557` when running program `./sassc/bin/sassc`, this can reproduce on the lattest commit.
### **2. Software version info**
```shell
$ git log -1
commit 2102188d21d2b7577c2b3edb1... | A stack-overflow src/ast_selectors.cpp:557 in Sass::CompoundSelector::has_real_parent_ref() const | https://api.github.com/repos/sass/libsass/issues/3177/comments | 7 | 2022-10-16T02:22:39Z | 2023-12-21T08:31:34Z | https://github.com/sass/libsass/issues/3177 | 1,410,349,151 | 3,177 | 5,536 |
CVE-2022-43358 | 2023-08-22T19:16:29.603 | Stack overflow vulnerability in ast_selectors.cpp: in function Sass::ComplexSelector::has_placeholder in libsass:3.6.5-8-g210218, which can be exploited by attackers to cause a denial of service (DoS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://drive.google.com/file/d/1j5fkPjWH9zQeTdO_4dMcZ-FpOBzP0MaI/"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/sass/libsass"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sass-lang:libsass:3.6.5-8-g210218:*:*:*:*:*:*:*",
"matchCriteriaId": "DD554F0E-70F8-4860-8F1A-292E60E0F9A3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"787"
] | 787 | https://github.com/sass/libsass/issues/3178 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"sass",
"libsass"
] |
### **1. Description**
A stack-overflow has occurred in `Sass::ComplexSelector::has_placeholder()` of `src/ast_selectors.cpp:464` when running program `./sassc/bin/sassc`, this can reproduce on the lattest commit.
### **2. Software version info**
```shell
$ git log -1
commit 2102188d21d2b7577c2b3edb12832e... | AddressSanitizer: stack-overflow src/ast_selectors.cpp:464 in Sass::ComplexSelector::has_placeholder() const | https://api.github.com/repos/sass/libsass/issues/3178/comments | 2 | 2022-10-16T02:32:36Z | 2023-12-21T08:31:28Z | https://github.com/sass/libsass/issues/3178 | 1,410,350,701 | 3,178 | 5,537 |
CVE-2022-47022 | 2023-08-22T19:16:30.547 | An issue was discovered in open-mpi hwloc 2.1.0 allows attackers to cause a denial of service or other unspecified impacts via glibc-cpuset in topology-linux.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/open-mpi/hwloc/issues/544"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open-mpi:hwloc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B915E20D-5CE9-4E0A-A624-9066F29A512C",
"versionEndExcluding": null,
"versionEndIncluding": "2.9.2",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/open-mpi/hwloc/issues/544 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"open-mpi",
"hwloc"
] | Hi, I found a potential null pointer dereference bug in the project source code of hwloc, and I have shown the execution sequence of the program that may generate the bug on the graph below. The red text illustrates the steps that generate the bug, the green text represents some additional information to help understan... | potential NULL glibc-cpuset dereferences in topology-linux.c | https://api.github.com/repos/open-mpi/hwloc/issues/544/comments | 3 | 2022-08-31T02:15:57Z | 2023-08-23T20:19:27Z | https://github.com/open-mpi/hwloc/issues/544 | 1,356,650,175 | 544 | 5,538 |
CVE-2022-48538 | 2023-08-22T19:16:31.230 | In Cacti 1.2.19, there is an authentication bypass in the web login functionality because of improper validation in the PHP code: cacti_ldap_auth() allows a zero as the password. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://docs.cacti.net/Settings-Auth-LDAP.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/Cacti/cacti/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:1.2.19:*:*:*:*:*:*:*",
"matchCriteriaId": "A4BB8CCB-5F52-4248-947C-3F4F1211EF53",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"863"
] | 863 | https://github.com/Cacti/cacti/issues/5189 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Cacti",
"cacti"
] | This is basically the same issue as #5140 just with LDAP.
2023.01.24 08:40:11 - CMDPHP PHP ERROR Backtrace: (/index.php[25]:include(), /include/auth.php[158]:require_once(), /auth_login.php[99]:ldap_login_process(), /lib/auth.php[3513]:cacti_ldap_auth(), /lib/ldap.php[74]:CactiErrorHandler())
2023.01.24 08:40:11 - ... | 1.2.23 - Cacti PHP 8.2 LDAP Errors with php-ldap Installed | https://api.github.com/repos/Cacti/cacti/issues/5189/comments | 4 | 2023-01-24T08:43:44Z | 2023-04-25T00:02:00Z | https://github.com/Cacti/cacti/issues/5189 | 1,554,547,887 | 5,189 | 5,539 |
CVE-2022-48541 | 2023-08-22T19:16:31.443 | A memory leak in ImageMagick 7.0.10-45 and 6.9.11-22 allows remote attackers to perform a denial of service via the "identify -help" command. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/2889"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2024/03/msg000... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:6.9.11-22:*:*:*:*:*:*:*",
"matchCriteriaId": "C5EDF13D-9DE8-4890-82CD-E6977434E531",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/2889 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Memory leak in identify -help | https://api.github.com/repos/ImageMagick/ImageMagick/issues/2889/comments | 1 | 2020-11-30T15:25:48Z | 2020-11-30T17:44:27Z | https://github.com/ImageMagick/ImageMagick/issues/2889 | 753,571,210 | 2,889 | 5,540 |
CVE-2022-48547 | 2023-08-22T19:16:31.647 | A reflected cross-site scripting (XSS) vulnerability in Cacti 0.8.7g and earlier allows unauthenticated remote attackers to inject arbitrary web script or HTML in the "ref" parameter at auth_changepassword.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/Cacti/cacti/issues/1882"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:*:*:*:*:*:*:*:*",
"matchCriteriaId": "921BD859-6432-492B-887B-B9A172ED2113",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.7g",
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/Cacti/cacti/issues/1882 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Cacti",
"cacti"
] | ### v1.1.38 Stored XSS in user_admin.php
When creating a new user on /cacti/user_admin.php, using the “copy” method, it is possible to bypass user input validation. This allows for the creation of a user called ```<script>alert(1)</script>```.
*This username just meets the max characters allowed. However, this res... | Bypass output validation in select cases | https://api.github.com/repos/Cacti/cacti/issues/1882/comments | 4 | 2018-08-30T13:26:18Z | 2020-06-30T05:46:00Z | https://github.com/Cacti/cacti/issues/1882 | 355,584,656 | 1,882 | 5,541 |
CVE-2022-48570 | 2023-08-22T19:16:32.157 | Crypto++ through 8.4 contains a timing side channel in ECDSA signature generation. Function FixedSizeAllocatorWithCleanup could write to memory outside of the allocation if the allocated memory was not 16-byte aligned. NOTE: this issue exists because the CVE-2019-14318 fix was intentionally removed for functionality re... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/weidai11/cryptopp/issues/992"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/weidai1... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cryptopp:crypto\\+\\+:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BFA9C8B3-FB1A-4E7F-A316-DACCCF660D08",
"versionEndExcluding": null,
"versionEndIncluding": "8.4.0",
"versionStartE... | [
"787"
] | 787 | https://github.com/weidai11/cryptopp/issues/992 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"weidai11",
"cryptopp"
] | @dwmcrobb discovered a latent bug in `FixedSizeSecBlock`. It was reported at [GH #988](https://github.com/weidai11/cryptopp/issues/988). In the 988 bug we fixed the pointer problem and cleaned up the class.
Since the `FixedSizeSecBlock` overhaul we started seeing failures on AppVeyor, which tests the Windows gear. F... | AppVeyor failures after fixing FixedSizeSecBlock | https://api.github.com/repos/weidai11/cryptopp/issues/992/comments | 29 | 2020-12-28T11:39:40Z | 2021-03-17T22:01:10Z | https://github.com/weidai11/cryptopp/issues/992 | 775,357,638 | 992 | 5,542 |
CVE-2023-36281 | 2023-08-22T19:16:36.457 | An issue in langchain v.0.0.171 allows a remote attacker to execute arbitrary code via a JSON file to load_prompt. This is related to __subclasses__ or a template. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://aisec.today/LangChain-2e6244a313dd46139c5ef28cbcab9e55"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.171:*:*:*:*:*:*:*",
"matchCriteriaId": "D8235D79-2666-4DEE-B6A2-A5DE48FB42C6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"94"
] | 94 | https://github.com/hwchase17/langchain/issues/4394 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"hwchase17",
"langchain"
] | ### System Info
windows 11
### Who can help?
_No response_
### Information
- [X] The official example notebooks/scripts
- [ ] My own modified scripts
### Related Components
- [ ] LLMs/Chat Models
- [ ] Embedding Models
- [X] Prompts / Prompt Templates / Prompt Selectors
- [ ] Output Parsers
- ... | Template injection to arbitrary code execution | https://api.github.com/repos/langchain-ai/langchain/issues/4394/comments | 4 | 2023-05-09T12:28:24Z | 2023-10-10T15:15:44Z | https://github.com/langchain-ai/langchain/issues/4394 | 1,701,910,416 | 4,394 | 5,543 |
CVE-2023-38666 | 2023-08-22T19:16:39.170 | Bento4 v1.6.0-639 was discovered to contain a segmentation violation via the AP4_Processor::ProcessFragments function in mp4encrypt. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/784"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-639:*:*:*:*:*:*:*",
"matchCriteriaId": "A003FBD1-339C-409D-A304-7FEE97E23250",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/784 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | # Summary
Hi, developers of Bento4:
I tested the binary mp4encrypt with my fuzzer, and a crash incurred—SEGV on unknown address. The following is the details.
# Bug
Detected SEGV on unknown address in mp4encrypt.
```
root@2e47aa8b3277:/fuzz-mp4encrypt-ACBC/mp4encrypt# ./mp4encrypt --method MARLIN-IPMP-ACBC ..... | SEGV on unknown address 0x000000000028 in mp4encrypt | https://api.github.com/repos/axiomatic-systems/Bento4/issues/784/comments | 0 | 2022-10-02T04:35:03Z | 2023-05-29T02:51:17Z | https://github.com/axiomatic-systems/Bento4/issues/784 | 1,393,638,825 | 784 | 5,544 |
CVE-2023-41105 | 2023-08-23T07:15:08.590 | An issue was discovered in Python 3.11 through 3.11.4. If a path containing '\0' bytes is passed to os.path.normpath(), the path will be truncated unexpectedly at the first '\0' byte. There are plausible cases in which an application would have rejected a filename for security reasons in Python 3.10.x or earlier, but t... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/python/cpython/issues/106242"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/python/cpython/pull/107981"
},
{
"source": "cve@m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "445B042E-9410-42E8-8749-A5EAEF2FF93D",
"versionEndExcluding": null,
"versionEndIncluding": "3.11.4",
"versionStartExcludin... | [
"426"
] | 426 | https://github.com/python/cpython/issues/106242 | [
"Issue Tracking",
"Patch"
] | github.com | [
"python",
"cpython"
] | # Bug report
Looks like `posix._path_normpath` has slightly different behaviour to the python implementation of `normpath` defined in `posixpath`, as such `os.path.normpath` behaves differently on Python 3.11 (where `posix._path_normpath` is used if it exists) vs 3.10 on posix systems:
Python 3.10:
```python
>>... | os.path.normpath truncates input on null bytes in 3.11, but not 3.10 | https://api.github.com/repos/python/cpython/issues/106242/comments | 9 | 2023-06-29T12:51:07Z | 2023-08-28T14:00:55Z | https://github.com/python/cpython/issues/106242 | 1,780,762,234 | 106,242 | 5,545 |
CVE-2023-39834 | 2023-08-24T18:15:07.540 | PbootCMS below v3.2.0 was discovered to contain a command injection vulnerability via create_function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Pbootcms/Pbootcms/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Pbootcms... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbootcms:pbootcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2DAA4DFB-3BBF-4476-A91E-7E9E602D3A7F",
"versionEndExcluding": "3.2.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"77"
] | 77 | https://github.com/Pbootcms/Pbootcms/issues/8 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Pbootcms",
"Pbootcms"
] | CVE-2022-32417后
在3.2.0以下的版本依然可以进行RCE | PbootCMS 3.2.0以下版本存在前台RCE漏洞 | https://api.github.com/repos/Pbootcms/Pbootcms/issues/8/comments | 2 | 2023-08-05T06:33:11Z | 2023-12-04T07:26:47Z | https://github.com/Pbootcms/Pbootcms/issues/8 | 1,837,606,018 | 8 | 5,546 |
CVE-2023-4508 | 2023-08-24T23:15:09.380 | A user able to control file input to Gerbv, between versions 2.4.0 and 2.10.0, can cause a crash and cause denial-of-service with a specially crafted Gerber RS-274X file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security@ubuntu.com",
"tags": [
"Third Party Advisory"
],
"url": "https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-4508"
},
{
"source": "security@ubuntu.com",
"tags": null,
"url": "https://github.com/gerbv/gerbv/commit/5517e22250e935dc7f86f64ad414aeae3dbcb36... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gerbv_project:gerbv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BAF64AAF-1393-4283-BB0C-3C0502600456",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.0",
"versionStartEx... | [
"824"
] | 824 | https://github.com/gerbv/gerbv/issues/191 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gerbv",
"gerbv"
] | ### Summary
Error or warning while processing an included image may result in a crash of Gerbv.
### CWEs
- CWE-824: Access of uninitialized pointer
### Details
The Gerber RS-274X format defines the `IF` command (`INCLUDE FILE`, for referencing an external file) in its [User's Guide](https://www2.pv.infn.... | Denial of Service in Gerbv | https://api.github.com/repos/gerbv/gerbv/issues/191/comments | 17 | 2023-07-11T07:22:22Z | 2023-08-23T22:55:35Z | https://github.com/gerbv/gerbv/issues/191 | 1,798,287,524 | 191 | 5,547 |
CVE-2023-36198 | 2023-08-25T20:15:08.193 | Buffer Overflow vulnerability in skalenetwork sgxwallet v.1.9.0 allows an attacker to cause a denial of service via the trustedBlsSignMessage function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/skalenetwork/sgxwallet/issues/419"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:skale:sgxwallet:1.9.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AE703687-AEA5-4907-A024-416EFA865D05",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/skalenetwork/sgxwallet/issues/419 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"skalenetwork",
"sgxwallet"
] | # NULL Pointer De-reference
A null-pointer de-reference in [trustedGenerateEcdsaKey](https://github.com/skalenetwork/sgxwallet/blob/22d6c98caa3b581a651ba31bd5cfd789201f9df8/secure_enclave/secure_enclave.c#L382). The global variable `curve` could be null if `trustedGenerateEcdsaKey` was called before [trustedEnclaveI... | Two bugs on SGXWallet | https://api.github.com/repos/skalenetwork/sgxwallet/issues/419/comments | 2 | 2023-05-29T03:51:50Z | 2023-10-30T01:29:48Z | https://github.com/skalenetwork/sgxwallet/issues/419 | 1,729,973,749 | 419 | 5,548 |
CVE-2023-39562 | 2023-08-28T19:15:07.747 | GPAC v2.3-DEV-rev449-g5948e4f70-master was discovered to contain a heap-use-after-free via the gf_bs_align function at bitstream.c. This vulnerability allows attackers to cause a Denial of Service (DoS) via supplying a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ChanStormstout/Pocs/blob/master/gpac_POC/id%3A000000%2Csig%3A06%2Csrc%3A003771%2Ctime%3A328254%2Cexecs%3A120473%2Cop%3Ahavoc%2Crep%3A8"
},
{
"source": "cve@mitre.org",
"tags": [
"Explo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3:2.3-dev-rev449-g5948e4f70-master:*:*:*:*:*:*",
"matchCriteriaId": "EE4D79B3-5867-4201-AB50-8CF590E4260B",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2537 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gpac",
"gpac"
] | # Description
While fuzzing yasm, a "heap-use-after-free" crash occurs,which was positioned in /gpac/src/utils/bitstream.c:1225:19 in gf_bs_align.
This bug may allow attackers to cause remote malicious code execution and denial of service via crafted files.
# Software version info
```
/AFLplusplus/my_test/fuzz_g... | A `heap-use-after-free` crash in bitstream.c:1225:19 in gf_bs_align | https://api.github.com/repos/gpac/gpac/issues/2537/comments | 0 | 2023-07-24T13:14:16Z | 2023-07-24T14:34:56Z | https://github.com/gpac/gpac/issues/2537 | 1,818,405,399 | 2,537 | 5,549 |
CVE-2023-39578 | 2023-08-28T20:15:08.207 | A stored cross-site scripting (XSS) vulnerability in the Create function of Zenario CMS v9.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Menu navigation text field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/anh91/Zenario-xss/issues/1"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://panda002.hashnode.dev/a-stored-cross-site-scripting-xss-vuln... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tribalsystems:zenario:9.4:*:*:*:*:*:*:*",
"matchCriteriaId": "D286E7B5-A87E-4B50-8BCD-DDD571CBD8C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/anh91/Zenario-xss/issues/1 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"anh91",
"Zenario-xss"
] | Summary
hi team,
I found a small Stored XSS
Info
Zenario 9.4
Step 1:
Login to account https://demo.zenar.io/admin

Step 2:
In the tab menu click on event and create a new event

## Steps to reproduce
1. compile libming with ASAN
```
$ CC="clang -fsanitize=address,fuzzer-no-link -g" CFLAGS+=" -fcommon" ./configu... | heap-buffer-overflow in r_readc() at fromswf.c:264 | https://api.github.com/repos/libming/libming/issues/288/comments | 0 | 2023-08-09T02:43:36Z | 2023-08-09T02:43:36Z | https://github.com/libming/libming/issues/288 | 1,842,363,544 | 288 | 5,551 |
CVE-2023-40825 | 2023-08-28T22:15:09.293 | An issue in Perfree PerfreeBlog v.3.1.2 allows a remote attacker to execute arbitrary code via crafted plugin listed in admin/plugin/access/list. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/perfree/PerfreeBlog/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/perfr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:perfree:perfreeblog:3.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "8D85BC31-3119-4CC1-89DD-CF50428AEAD0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"434"
] | 434 | https://github.com/perfree/PerfreeBlog/issues/15 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"perfree",
"PerfreeBlog"
] | ## Vulnerability information
PerfreeBlog implements the extension plug-in function based on SpringBoot and pf4j. After the plug-in is developed, it is packaged as a jar package, which can be directly installed and used online through the plug-in management of PerfreeBlog background. If an attacker develops a plug-in a... | The uploaded malicious plug-in is parsed and the command is executed | https://api.github.com/repos/PerfreeBlog/PerfreeBlog/issues/15/comments | 1 | 2023-08-12T06:35:20Z | 2023-09-21T03:00:59Z | https://github.com/PerfreeBlog/PerfreeBlog/issues/15 | 1,847,801,012 | 15 | 5,552 |
CVE-2023-40826 | 2023-08-28T22:15:09.433 | An issue in pf4j pf4j v.3.9.0 and before allows a remote attacker to obtain sensitive information and execute arbitrary code via the zippluginPath parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/pf4j/pf4j/issues/536"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pf4j_project:pf4j:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DB85990D-5588-477E-ADF2-EB0D1DCBC83B",
"versionEndExcluding": null,
"versionEndIncluding": "3.9.0",
"versionStartExclu... | [
"22"
] | 22 | https://github.com/pf4j/pf4j/issues/536 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"pf4j",
"pf4j"
] | ## description
Dear project developers, I use SpringBoot and pf4j to implement the system's extension plug-in function, the use of zip or jar package format is very easy to expand the system. When I was using pf4j, I found that the pluginPath value was not verified securely when loading plug-ins. If the developers usi... | The method of extracting the zip file has a path traversal vulnerability | https://api.github.com/repos/pf4j/pf4j/issues/536/comments | 2 | 2023-08-12T11:48:08Z | 2023-08-13T09:29:45Z | https://github.com/pf4j/pf4j/issues/536 | 1,847,959,785 | 536 | 5,553 |
CVE-2023-40857 | 2023-08-28T22:15:09.870 | Buffer Overflow vulnerability in VirusTotal yara v.4.3.2 allows a remote attacker to execute arbtirary code via the yr_execute_cod function in the exe.c component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/VirusTotal/yara/issues/1945"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:virustotal:yara:4.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C9EEF587-BE65-40E9-AE81-5F7FA989A74A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/VirusTotal/yara/issues/1945 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"VirusTotal",
"yara"
] | **Describe the bug**
AddressSanitizer: heap-buffer-overflow libyara/exec.c:1426 in yr_execute_code
**To Reproduce**
Steps to reproduce the behavior:
1, compile yara with asan: ./configure CC=gcc CXX=g++ CFLAGS="-g -O0 -fsanitize=address" CXXFLAGS="-g -O0 -fsanitize=address" LDFLAGS="-g -O0 -fsanitize=address"
2,... | heap-buffer-overflow libyara/exec.c:1426 in yr_execute_code | https://api.github.com/repos/VirusTotal/yara/issues/1945/comments | 1 | 2023-08-10T08:11:16Z | 2023-08-14T20:37:14Z | https://github.com/VirusTotal/yara/issues/1945 | 1,844,655,627 | 1,945 | 5,554 |
CVE-2023-41005 | 2023-08-28T22:15:10.307 | An issue in Pagekit pagekit v.1.0.18 alows a remote attacker to execute arbitrary code via thedownloadAction and updateAction functions in UpdateController.php | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/pagekit/pagekit/issues/977"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pagekit:pagekit:1.0.18:*:*:*:*:*:*:*",
"matchCriteriaId": "A1E39691-604C-42A3-BA30-80433E0E09EA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"94"
] | 94 | https://github.com/pagekit/pagekit/issues/977 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"pagekit",
"pagekit"
] | <!--
Before submitting an issue, please try some troubleshooting steps:
- Enabled debug mode: https://pagekit.com/docs/troubleshooting/debug-mode
- Verify the server requirements: https://pagekit.com/docs/getting-started/requirements
- Disable all installed extensions
- Check the browser developer console for ... | There is a logical flaw that leads to obtaining shell access. | https://api.github.com/repos/pagekit/pagekit/issues/977/comments | 0 | 2023-08-20T17:13:21Z | 2023-08-20T17:13:21Z | https://github.com/pagekit/pagekit/issues/977 | 1,858,202,758 | 977 | 5,555 |
CVE-2023-39663 | 2023-08-29T20:15:09.990 | Mathjax up to v2.7.9 was discovered to contain two Regular expression Denial of Service (ReDoS) vulnerabilities in MathJax.js via the components pattern and markdownPattern. NOTE: the vendor disputes this because the regular expressions are not applied to user input; thus, there is no risk. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/mathjax/MathJax/issues/3074"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mathjax:mathjax:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD9A61A5-6BB3-47A3-ACF7-5FBF93EEC1A1",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.9",
"versionStartExcludi... | [
"1333"
] | 1333 | https://github.com/mathjax/MathJax/issues/3074 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"mathjax",
"MathJax"
] | **Replace the text below with the details of the issue you are facing.
DO NOT simply erase the form and type a free-form response.**
-----
### Issue Summary
MathJax v2 contains two highly vulnerable regex patterns in `MathJax.js`: `pattern` and `markdownPattern`.
`pattern`: ``/%(\d+|\{\d+\}|\{[a-z]+:\%\d+(?... | Vulnerable regex in MathJax v2 could potentially lead to a ReDoS attack | https://api.github.com/repos/mathjax/MathJax/issues/3074/comments | 1 | 2023-07-29T09:46:01Z | 2023-08-11T14:29:25Z | https://github.com/mathjax/MathJax/issues/3074 | 1,827,424,525 | 3,074 | 5,556 |
CVE-2023-38975 | 2023-08-29T22:15:08.980 | * Buffer Overflow vulnerability in qdrant v.1.3.2 allows a remote attacker cause a denial of service via the chucnked_vectors.rs component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://aisec.today/Qdrant-56dd05e12ca94d75a5e798b3fee80fa3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qdrant:qdrant:1.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "0B45F198-D213-48C3-9946-197FECCC6C2B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"120"
] | 120 | https://github.com/qdrant/qdrant/issues/2268 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"qdrant",
"qdrant"
] | Wrong dim when create collection may cause db service down
## Current Behavior
Denial of Service, Users can not use the vector database normally
## Steps to Reproduce
some bugs related with the dim of vector when create collection, which can cause DoS
Details
version: 1.3.2
FPE
at https://github.c... | Wrong dim when create collection may cause db service down | https://api.github.com/repos/qdrant/qdrant/issues/2268/comments | 5 | 2023-07-17T03:57:04Z | 2023-08-31T13:11:38Z | https://github.com/qdrant/qdrant/issues/2268 | 1,806,900,854 | 2,268 | 5,557 |
CVE-2023-39135 | 2023-08-30T22:15:08.920 | An issue in Zip Swift v2.1.2 allows attackers to execute a path traversal attack via a crafted zip entry. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://blog.ostorlab.co/zip-packages-exploitation.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:marmelroy:zip:2.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "BA37A87A-CC3E-41F3-92EB-A0E2F141C0E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"22"
] | 22 | https://github.com/marmelroy/Zip/issues/245 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"marmelroy",
"Zip"
] | **Description:**
The package does not validate paths coming from zip entries, hence allowing for path traversal
**Technical details:**
Below is a code snippet from the `unzipFile` function used to extract zip files, you can notice that `pathString` coming from our zip entry is appended to the `destination` di... | Path traversal vulnerability | https://api.github.com/repos/marmelroy/Zip/issues/245/comments | 2 | 2023-07-24T08:54:44Z | 2024-02-14T09:50:35Z | https://github.com/marmelroy/Zip/issues/245 | 1,817,954,724 | 245 | 5,558 |
CVE-2023-39136 | 2023-08-30T22:15:08.977 | An unhandled edge case in the component _sanitizedPath of ZipArchive v2.5.4 allows attackers to cause a Denial of Service (DoS) via a crafted zip file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://blog.ostorlab.co/zip-packages-exploitation.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ziparchive_project:ziparchive:2.5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "588B005C-A0E6-4EC3-AD83-F65BD3E3A4FF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"703"
] | 703 | https://github.com/ZipArchive/ZipArchive/issues/680 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"ZipArchive",
"ZipArchive"
] | **Description:**
There is an unhandeled edge case where we can crash the application when it tries to unzip a specially crafted zip file
**Technical details:**
Below is a code snippet from the `_sanitizedPath` function used to sanitize file paths coming from zip entries before extraction to prevent path trav... | Unhandled edge case in _sanitizedPath | https://api.github.com/repos/ZipArchive/ZipArchive/issues/680/comments | 1 | 2023-07-10T10:58:18Z | 2023-07-24T08:59:28Z | https://github.com/ZipArchive/ZipArchive/issues/680 | 1,796,509,070 | 680 | 5,559 |
CVE-2023-39137 | 2023-08-30T22:15:09.030 | An issue in Archive v3.3.7 allows attackers to spoof zip filenames which can lead to inconsistent filename parsing. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://blog.ostorlab.co/zip-packages-exploitation.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/brendan-duncan/archive/issues/266"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:archive_project:archive:3.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "310DCB5F-FF27-4496-9CCC-5730A2BC0BB1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"20"
] | 20 | https://github.com/brendan-duncan/archive/issues/266 | [
"Issue Tracking"
] | github.com | [
"brendan-duncan",
"archive"
] | Hi,
This is a follow up of the previous issue report, we noticed that when `archive` tries to parse the filename from the zip header, it only considers the filename from the `Local File Header` and does not match it against `Central Directory Entry` filename, this can pose a security risk as the `Local File Header` ... | Archive package is vulnerable to zip filename spoofing | https://api.github.com/repos/brendan-duncan/archive/issues/266/comments | 2 | 2023-06-20T17:23:24Z | 2023-09-03T02:43:09Z | https://github.com/brendan-duncan/archive/issues/266 | 1,765,832,957 | 266 | 5,560 |
CVE-2023-39138 | 2023-08-30T22:15:09.083 | An issue in ZIPFoundation v0.9.16 allows attackers to execute a path traversal via extracting a crafted zip file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://blog.ostorlab.co/zip-packages-exploitation.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/weichsel/ZIPFoundation/issues/282"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:peakstep:zipfoundation:0.9.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D80F1168-A141-4F13-8964-9FAEB4370CA6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/weichsel/ZIPFoundation/issues/282 | [
"Issue Tracking"
] | github.com | [
"weichsel",
"ZIPFoundation"
] | # Summary
The package does not check if symlinks are pointing to paths outside the extraction directory
# Steps to Reproduce
1- Generate `payload.zip` using the following code:
```python
import zipfile
def compress_file(filename):
zipInfo = zipfile.ZipInfo(".")
zipInfo.create_system = 3
zipIn... | Symlink path traversal vulnerability | https://api.github.com/repos/weichsel/ZIPFoundation/issues/282/comments | 3 | 2023-07-24T08:52:35Z | 2024-01-25T11:16:47Z | https://github.com/weichsel/ZIPFoundation/issues/282 | 1,817,951,182 | 282 | 5,561 |
CVE-2023-39139 | 2023-08-30T22:15:09.300 | An issue in Archive v3.3.7 allows attackers to execute a path traversal via extracting a crafted zip file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://blog.ostorlab.co/zip-packages-exploitation.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/brendan-duncan/archive/issues/265"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:archive_project:archive:3.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "310DCB5F-FF27-4496-9CCC-5730A2BC0BB1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/brendan-duncan/archive/issues/265 | [
"Issue Tracking"
] | github.com | [
"brendan-duncan",
"archive"
] | Hello,
while doing some security testing on `archive` package, we noticed that it supports symlinks, while symlinks might be an intended functionality of your package, we do believe that symlinks pointing outside the extraction directory are more of a security risk than a feature, below is an example where we creat... | Archive is vulnerable to symlink path traversal | https://api.github.com/repos/brendan-duncan/archive/issues/265/comments | 2 | 2023-06-20T17:09:28Z | 2023-09-05T11:35:12Z | https://github.com/brendan-duncan/archive/issues/265 | 1,765,811,320 | 265 | 5,562 |
CVE-2023-39685 | 2023-09-01T10:15:08.217 | An issue in hjson-java up to v3.0.0 allows attackers to cause a Denial of Service (DoS) via supplying a crafted JSON string. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/hjson/hjson-java/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hjson:hjson:*:*:*:*:*:*:*:*",
"matchCriteriaId": "213D947D-3AF3-4D5B-8503-AFE86807AEB6",
"versionEndExcluding": null,
"versionEndIncluding": "3.0.0",
"versionStartExcluding":... | [
"94"
] | 94 | https://github.com/hjson/hjson-java/issues/27 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"hjson",
"hjson-java"
] | ## Description
The utilization of hjson to interpret untrusted JSON strings could potentially expose to significant security risks, specifically denial of service (DOS) attacks. This vulnerability arises when the parser operates on input provided by users, which could be manipulated by malicious actors. They could c... | java.lang.StringIndexOutOfBoundsException error caused by hjson parsing of untrusted JSON String | https://api.github.com/repos/hjson/hjson-java/issues/27/comments | 4 | 2023-07-30T12:15:58Z | 2023-08-12T14:42:06Z | https://github.com/hjson/hjson-java/issues/27 | 1,827,914,114 | 27 | 5,563 |
CVE-2023-40969 | 2023-09-01T11:15:42.800 | Senayan Library Management Systems SLIMS 9 Bulian v9.6.1 is vulnerable to Server Side Request Forgery (SSRF) via admin/modules/bibliography/pop_p2p.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/komangsughosa/CVE-ID-not-yet/blob/main/slims/slims9_bulian-9.6.1-SSRF-pop_p2p.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:slims:senayan_library_management_system:9.6.1:*:*:*:*:*:*:*",
"matchCriteriaId": "548C3132-1CC1-446F-90FC-3411038DFAAB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"918"
] | 918 | https://github.com/slims/slims9_bulian/issues/204 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"slims",
"slims9_bulian"
] | # The bug
A Server Side Request Forgery exists in `admin/modules/bibliography/pop_p2p.php` at the code below
```php
$detail_uri = $_GET['uri'] . "/index.php?p=show_detail&inXML=true&id=" . $_GET['biblioID'];
// parse XML
$data = modsXMLsenayan($detail_uri, 'uri');
```
# To Reproduce
**Steps to reproduce t... | [Security Bugs] Server Side Request Forgery at pop_p2p.php | https://api.github.com/repos/slims/slims9_bulian/issues/204/comments | 2 | 2023-08-17T17:57:57Z | 2023-08-30T07:30:34Z | https://github.com/slims/slims9_bulian/issues/204 | 1,855,462,115 | 204 | 5,564 |
CVE-2023-40970 | 2023-09-01T11:15:42.923 | Senayan Library Management Systems SLIMS 9 Bulian v 9.6.1 is vulnerable to SQL Injection via admin/modules/circulation/loan_rules.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/komangsughosa/CVE-ID-not-yet/blob/main/slims/slims9_bulian-9.6.1-SQLI-loan_rules.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:slims:senayan_library_management_system:9.6.1:*:*:*:*:*:*:*",
"matchCriteriaId": "548C3132-1CC1-446F-90FC-3411038DFAAB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/slims/slims9_bulian/issues/205 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"slims",
"slims9_bulian"
] | # The bug
A SQL Injection exists in `admin/modules/circulation/loan_rules.php` at the code below
```php
/* RECORD OPERATION */
if (isset($_POST['saveData'])) {
$data['member_type_id'] = $_POST['memberTypeID'];
$data['coll_type_id'] = $_POST['collTypeID'];
$data['gmd_id'] = $_POST['gmdID'];
$da... | [Security Bugs] SQL Injection at loan_rules.php | https://api.github.com/repos/slims/slims9_bulian/issues/205/comments | 3 | 2023-08-18T14:09:37Z | 2023-09-01T06:50:58Z | https://github.com/slims/slims9_bulian/issues/205 | 1,856,790,763 | 205 | 5,565 |
CVE-2023-36076 | 2023-09-01T16:15:07.857 | SQL Injection vulnerability in smanga version 3.1.9 and earlier, allows remote attackers to execute arbitrary code and gain sensitive information via mediaId, mangaId, and userId parameters in php/history/add.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/lkw199711/smanga/issues/100"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pocketmanga:smanga:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2CDB3ADC-6AC1-4E1F-B95D-237A07B5124E",
"versionEndExcluding": null,
"versionEndIncluding": "3.1.9",
"versionStartExcl... | [
"89"
] | 89 | https://github.com/lkw199711/smanga/issues/100 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"lkw199711",
"smanga"
] | ## 测试环境说明
* 版本:3.2.7(最新版)
* 环境:docker
docker搭建所使用的命令:
```
docker run -itd --name smanga \
-p 3333:3306 \
-p 8097:80 \
-v /mnt:/mnt \
-v /route/smanga:/data \
-v /route/compress:/compress \
lkw199711/smanga;
```
### 1、未授权远程代码执行
* 漏洞描述
**/php/manga/delete.php**接口处存在未授权远程代码执行漏洞,攻击者可在目标主机执行任意命令,获取服... | 3个高危漏洞 | https://api.github.com/repos/lkw199711/smanga/issues/100/comments | 1 | 2023-06-07T16:00:08Z | 2023-06-18T10:14:11Z | https://github.com/lkw199711/smanga/issues/100 | 1,746,228,624 | 100 | 5,566 |
CVE-2023-36088 | 2023-09-01T16:15:07.910 | Server Side Request Forgery (SSRF) vulnerability in NebulaGraph Studio version 3.7.0, allows remote attackers to gain sensitive information. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://nebulagraph.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/vesoft-inc/nebula-studio"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vesoft:nebulagraph_studio:3.7.0:*:*:*:*:*:*:*",
"matchCriteriaId": "10E246F7-BEED-4EDB-898B-09599EA9A6A2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"918"
] | 918 | https://github.com/vesoft-inc/nebula-studio/issues/571 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vesoft-inc",
"nebula-studio"
] | **Describe the bug (__must be provided__)**
The NebulaGraph Studio login interface provides the function of connecting to NebulaGraph. Unauthorized users can request the IP address and port of the intranet host through the target website for intranet detection.
**Your Environments (__must be provided__)**
* Ne... | NebulaGraph Studio has SSRF vulnerability | https://api.github.com/repos/vesoft-inc/nebula-studio/issues/571/comments | 1 | 2023-06-08T05:38:09Z | 2023-09-25T11:14:09Z | https://github.com/vesoft-inc/nebula-studio/issues/571 | 1,747,118,267 | 571 | 5,567 |
CVE-2023-36100 | 2023-09-01T16:15:07.967 | An issue was discovered in IceCMS version 2.0.1, allows attackers to escalate privileges and gain sensitive information via UserID parameter in api/User/ChangeUser. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Thecosy/IceCMS/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:macwk:icecms:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C8043F07-E915-49DC-A4D8-DC34AC2B9770",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"269"
] | 269 | https://github.com/Thecosy/IceCMS/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Thecosy",
"IceCMS"
] | api:/api/User/ChangeUser/(self_token)
Calling this interface, we can modify the information of any user by modifying the UserID field.there will be no validation

Try to log in to user test39, it goes well
 function eventually calls eval() on the data provided. [eval() is extremely dangerous when supplied with user input](https://nedbatchelder.com/blog/201206/eval_really_is_dangerous.html) and to my knowledge it isn't mentioned that the function does this. I would add a warning in the documentation about th... | Warn that evaluate() should not be used on user input | https://api.github.com/repos/pydata/numexpr/issues/442/comments | 60 | 2023-07-07T21:32:16Z | 2025-02-08T06:30:36Z | https://github.com/pydata/numexpr/issues/442 | 1,794,402,008 | 442 | 5,570 |
CVE-2023-40771 | 2023-09-01T16:15:08.423 | SQL injection vulnerability in DataEase v.1.18.9 allows a remote attacker to obtain sensitive information via a crafted string outside of the blacklist function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dataease/dataease/issues/5861"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dataease:dataease:1.18.9:*:*:*:*:*:*:*",
"matchCriteriaId": "D1AE6464-BAA2-474D-AE65-EB1AA6CE2EDC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/dataease/dataease/issues/5861 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dataease",
"dataease"
] | Impact
DataEase has a SQL injection vulnerability that Not affected by SQL injection blacklists
The SQL statement is located in the following file location, using the ${} symbol.
https://github.com/dataease/dataease/blob/dev/backend/src/main/java/io/dataease/ext/query/GridSql.xml
 2016..2023 Henner Zeller. This program is free software; license GPL 2.0.
Image decoding GraphicsMagick 1.3... | Detected Crash: AddressSanitizer: heap-buffer-overflow | https://api.github.com/repos/hzeller/timg/issues/115/comments | 7 | 2023-08-16T14:09:55Z | 2023-09-09T18:05:29Z | https://github.com/hzeller/timg/issues/115 | 1,853,331,422 | 115 | 5,572 |
CVE-2023-40980 | 2023-09-01T16:15:08.523 | File Upload vulnerability in DWSurvey DWSurvey-OSS v.3.2.0 and before allows a remote attacker to execute arbitrary code via the saveimage method and savveFile in the action/UploadAction.java file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wkeyuan/DWSurvey/issues/107"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:diaowen:dwsurvey:*:*:*:*:*:*:*:*",
"matchCriteriaId": "28413AA7-B86B-47F2-B3ED-E77F485F24E2",
"versionEndExcluding": null,
"versionEndIncluding": "3.2.0",
"versionStartExclud... | [
"434"
] | 434 | https://github.com/wkeyuan/DWSurvey/issues/107 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wkeyuan",
"DWSurvey"
] | ``The saveimage method and saveFile in the com/key/common/base/action/UploadAction.java file can directly upload any type of file without authorization
For the saveimage method, this method can be directly called without authorization to upload any specified type of file to the /file/images/ directory, and this dire... | Arbitrary file uploads exist | https://api.github.com/repos/wkeyuan/DWSurvey/issues/107/comments | 1 | 2023-08-18T09:28:16Z | 2023-08-18T09:28:41Z | https://github.com/wkeyuan/DWSurvey/issues/107 | 1,856,382,882 | 107 | 5,573 |
CVE-2023-36308 | 2023-09-05T04:15:08.703 | disintegration Imaging 1.6.2 allows attackers to cause a panic (because of an integer index out of range during a Grayscale call) via a crafted TIFF file to the scan function of scanner.go. NOTE: it is unclear whether there are common use cases in which this panic could have any security consequence | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/disintegration/imaging/issues/165"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://github.com/disintegrati... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:disintegration:imaging:1.6.2:*:*:*:*:go:*:*",
"matchCriteriaId": "585534FE-4333-40AD-BA0E-17DCFEDD1AD0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"129"
] | 129 | https://github.com/disintegration/imaging/issues/165 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"disintegration",
"imaging"
] | When we use the imaging library to parse a maliciously constructed graph, the `scan` function of the `scanner.go` file will have an index out of bounds problem. The verification procedure is as follows:
```
package main
import (
"image"
"os"
"runtime"
"github.com/disintegration/imaging"
)
func main... | Specific image will cause the index of the scan function in scanner.go to go out of bounds | https://api.github.com/repos/disintegration/imaging/issues/165/comments | 0 | 2023-07-14T05:43:43Z | 2023-07-15T13:53:25Z | https://github.com/disintegration/imaging/issues/165 | 1,804,214,116 | 165 | 5,574 |
CVE-2023-40918 | 2023-09-05T18:15:11.317 | KnowStreaming 3.3.0 is vulnerable to Escalation of Privileges. Unauthorized users can create a new user with an admin role. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/didi/KnowStreaming/issues/1128"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:knowstreaming_project:knowstreaming:3.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E4F7FED8-1125-4851-AC50-8EAC3290E77C",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"269"
] | 269 | https://github.com/didi/KnowStreaming/issues/1128 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"didi",
"KnowStreaming"
] | - [Y ] 我已经在 [issues](https://github.com/didi/KnowStreaming/issues) 搜索过相关问题了,并没有重复的。
你是否希望来认领这个Bug。
### Env
* KnowStreaming version : <font size=4 color =red> 3.0.0 </font>
* Operating System version :
* Java version :
This issue is tested on the website https://demo.knowstreaming.com
### Step... | [Escalation of Privileges] Unauthorized users can create a new user with admin role | https://api.github.com/repos/didi/KnowStreaming/issues/1128/comments | 0 | 2023-08-15T11:12:37Z | 2023-08-24T19:31:47Z | https://github.com/didi/KnowStreaming/issues/1128 | 1,851,266,832 | 1,128 | 5,575 |
CVE-2021-36646 | 2023-09-06T17:15:49.873 | A Cross Site Scrtpting (XSS) vulnerability in KodExplorer 4.45 allows remote attackers to run arbitrary code via /index.php page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kalcaddle/KodExplorer/issues/482"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kodcloud:kodexplorer:4.45:*:*:*:*:*:*:*",
"matchCriteriaId": "2DDC782B-E8E9-4B75-AF51-2F3A90B7A6A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/kalcaddle/KodExplorer/issues/482 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kalcaddle",
"KodExplorer"
] | # Analyse
file: app/template/api/view.html
```
G.shareInfo = {
path:"<?php echo $_GET['path'];?>",
name:"<?php echo get_path_this($_GET['path']);?>",
mtime:0,
size:0
}
```
No any safety check for variable(path), it direct to echo in the page.
Attacker can use this bug to send fish email to ad... | New Reflected XSS in KodExplorer | https://api.github.com/repos/kalcaddle/KodExplorer/issues/482/comments | 1 | 2021-07-08T07:20:41Z | 2021-07-08T11:33:16Z | https://github.com/kalcaddle/KodExplorer/issues/482 | 939,553,431 | 482 | 5,576 |
CVE-2023-36184 | 2023-09-08T02:15:08.080 | CMysten Labs Sui blockchain v1.2.0 was discovered to contain a stack overflow via the component /spec/openrpc.json. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/MystenLabs/sui/commit/8b681515c0cf435df2a54198a28ab4ef574d202b"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/aptos-labs/aptos-core/commit/47a0391c612407fe0b... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:aptosfoundation:aptos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "23231A97-68C3-43D6-AC2C-C2B45D157B44",
"versionEndExcluding": "1.4.3",
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/move-language/move/issues/1059 | [
"Issue Tracking",
"Patch"
] | github.com | [
"move-language",
"move"
] | There is a critical Move VM vulnerability that has been fixed by Sui move and Aptos move, but this project has not fix that vulnerability.
In addition to Sui and Aptos, some blockchains are also using the Move virtual machine.
Sui move patch link
https://github.com/MystenLabs/sui/commit/8b681515c0cf435df2a5419... | [Bug] A patch for a DoS vulnerability needs to be applied | https://api.github.com/repos/move-language/move/issues/1059/comments | 1 | 2023-06-09T08:31:11Z | 2024-01-16T08:46:57Z | https://github.com/move-language/move/issues/1059 | 1,749,410,371 | 1,059 | 5,577 |
CVE-2023-39584 | 2023-09-08T13:15:07.990 | Hexo up to v7.0.0 (RC2) was discovered to contain an arbitrary file read vulnerability. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hexojs/hexo/blob/a3e68e7576d279db22bd7481914286104e867834/lib/plugins/tag/include_code.js#L49"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hexo:hexo:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "2F494D7D-4DEC-47D1-9D57-FD22F923AD68",
"versionEndExcluding": null,
"versionEndIncluding": "6.3.0",
"versionStartExcludi... | [
"22"
] | 22 | https://github.com/hexojs/hexo/issues/5250 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hexojs",
"hexo"
] | ## Check
- I have already read [Docs page](https://hexo.io/docs/)
- I have already searched existing issues
## Feature Request
When browsing the project code, I found a vulnerability fix for arbitrary file reading:
[security check: do not allow ../ in path](https://github.com/hexojs/hexo/blob/a3e68e7576d279... | By pass security check: do not allow ../ in path | https://api.github.com/repos/hexojs/hexo/issues/5250/comments | 1 | 2023-07-26T07:34:19Z | 2024-04-16T15:58:48Z | https://github.com/hexojs/hexo/issues/5250 | 1,821,769,026 | 5,250 | 5,578 |
CVE-2023-41578 | 2023-09-08T19:15:44.147 | Jeecg boot up to v3.5.3 was discovered to contain an arbitrary file read vulnerability via the interface /testConnection. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Snakinya/Bugs/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Snakinya/Bug... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB2E1EE1-D408-4689-8A4F-CDF2C09DAC83",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.3",
"versionStartExclud... | [
"22"
] | 22 | https://github.com/Snakinya/Bugs/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Snakinya",
"Bugs"
] | In the /testConnection route, a MySQL connection can be constructed to cause arbitrary file reading.
```java
@PostMapping({"/testConnection"})
public Result a(@RequestBody JmreportDynamicDataSourceVo var1) {
Connection var2 = null;
String var3 = var1.toString();
a.info(" local cache ... | Jeecg-boot <=3.5.3 Arbitrary File Read | https://api.github.com/repos/Snakinya/Bugs/issues/1/comments | 0 | 2023-08-26T13:44:49Z | 2023-08-27T05:30:54Z | https://github.com/Snakinya/Bugs/issues/1 | 1,868,103,181 | 1 | 5,579 |
CVE-2023-42268 | 2023-09-08T19:15:44.200 | Jeecg boot up to v3.5.3 was discovered to contain a SQL injection vulnerability via the component /jeecg-boot/jmreport/show. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/5311"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/je... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB2E1EE1-D408-4689-8A4F-CDF2C09DAC83",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.3",
"versionStartExclud... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/5311 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
3.5.3
##### 前端版本:vue3版?还是 vue2版?
vue3
##### 问题描述:
/jeecg-boot/jmreport/show接口存在sql注入,攻击者可以利用布尔盲注绕过防护。
##### 截图&代码:
org/jeecg/modules/jmreport/common/b/i.class
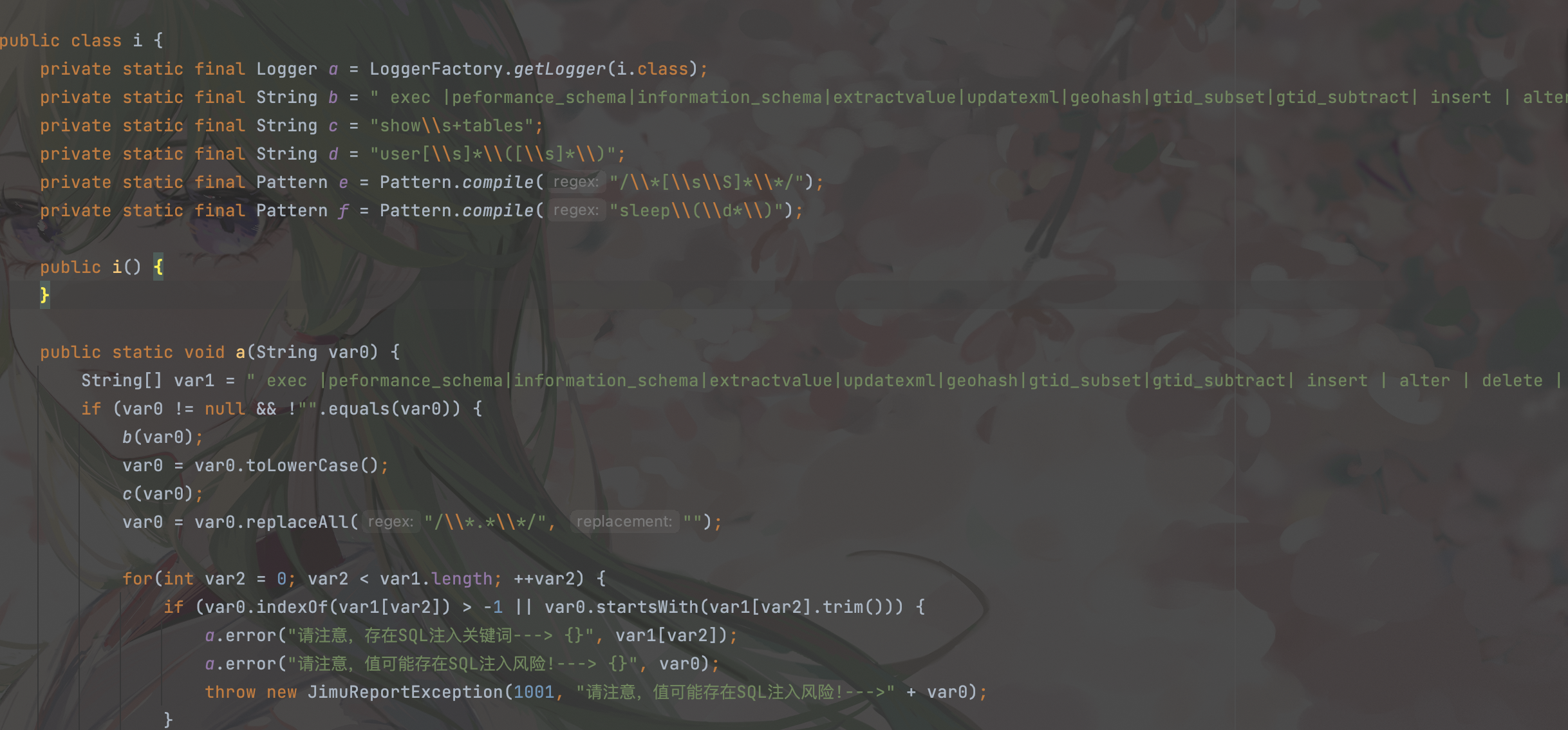
黑名单如下:" exec |peformance_s... | jeecgboot3.5.3 存在未授权sql注入(布尔盲注绕过) | https://api.github.com/repos/jeecgboot/JeecgBoot/issues/5311/comments | 5 | 2023-08-25T14:24:01Z | 2023-09-21T03:43:26Z | https://github.com/jeecgboot/JeecgBoot/issues/5311 | 1,867,152,632 | 5,311 | 5,580 |
CVE-2023-42276 | 2023-09-08T22:15:11.740 | hutool v5.8.21 was discovered to contain a buffer overflow via the component jsonArray. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3286"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.21:*:*:*:*:*:*:*",
"matchCriteriaId": "EBFA93D9-F18F-4939-BF26-89603CD7148D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/dromara/hutool/issues/3286 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dromara",
"hutool"
] |
### 版本情况
JDK版本: 1.8.0_362
hutool版本: 5.8.21
### 问题描述(包括截图)
1. 复现代码
```java
import cn.hutool.json.JSONObject;
public class JSONObjectTest {
public static void main(String[] args) {
JSONArray jSONArray = new JSONArray();
Object element = new Object();
jSONArray.add(1... | `JSONArray`的`add()`方法抛出OutOfMemory异常 | https://api.github.com/repos/chinabugotech/hutool/issues/3286/comments | 2 | 2023-08-30T09:51:25Z | 2023-09-12T03:28:46Z | https://github.com/chinabugotech/hutool/issues/3286 | 1,873,333,053 | 3,286 | 5,581 |
CVE-2023-42277 | 2023-09-08T22:15:11.863 | hutool v5.8.21 was discovered to contain a buffer overflow via the component jsonObject.putByPath. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3285"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.21:*:*:*:*:*:*:*",
"matchCriteriaId": "EBFA93D9-F18F-4939-BF26-89603CD7148D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/dromara/hutool/issues/3285 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: 1.8.0_362
hutool版本: 5.8.21
### 问题描述(包括截图)
1. 复现代码
```java
import cn.hutool.json.JSONObject;
public class JSONObjectTest {
public static void main(String[] args) {
JSONObject jSONObject = new JSONObject();
Object value = new Object();
jSONObject.putBy... | `putByPath()`方法抛出OutOfMemory异常 | https://api.github.com/repos/chinabugotech/hutool/issues/3285/comments | 1 | 2023-08-30T08:22:07Z | 2023-08-30T13:52:31Z | https://github.com/chinabugotech/hutool/issues/3285 | 1,873,179,897 | 3,285 | 5,582 |
CVE-2023-42278 | 2023-09-08T22:15:12.037 | hutool v5.8.21 was discovered to contain a buffer overflow via the component JSONUtil.parse(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/dromara/hutool/issues/3289"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hutool:hutool:5.8.21:*:*:*:*:*:*:*",
"matchCriteriaId": "EBFA93D9-F18F-4939-BF26-89603CD7148D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/dromara/hutool/issues/3289 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"dromara",
"hutool"
] | ### 版本情况
JDK版本: 1.8.0_362
hutool版本: 5.8.21
### 问题描述(包括截图)
1. 复现代码
```java
import cn.hutool.json.JSONUtil;
public class JSONOUtilTest {
public static void main(String[] args) {
String s = "{\"G\":00,[,,[0E5,6E9,6E5,6E9,6E5,6E9,6E5,6E9,6E9,6E5,true,6E5,6E9,6E5,6E9,6956,EE,5E9,6E5,RE,6E9... | `JSONUtil.parse()`方法解析特定输入时,会导致服务挂起和崩溃,存在安全隐患 | https://api.github.com/repos/chinabugotech/hutool/issues/3289/comments | 5 | 2023-09-04T02:58:25Z | 2023-09-14T07:12:52Z | https://github.com/chinabugotech/hutool/issues/3289 | 1,879,420,551 | 3,289 | 5,583 |
CVE-2023-41000 | 2023-09-11T15:16:02.307 | GPAC through 2.2.1 has a use-after-free vulnerability in the function gf_bifs_flush_command_list in bifs/memory_decoder.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2550"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "047BC15F-5E51-48D9-B751-9DC9311FEBCF",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.1",
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2550 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [Y ] I looked for a similar issue and couldn't find any.
- [Y] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [Y] I give enough information for contributors to reproduce my issue
**Description**
There is a Null Pointer Dereference detected by Ad... | Null Pointer Dereference in function BS_ReadByte | https://api.github.com/repos/gpac/gpac/issues/2550/comments | 4 | 2023-08-08T07:09:38Z | 2023-09-11T12:40:06Z | https://github.com/gpac/gpac/issues/2550 | 1,840,701,677 | 2,550 | 5,584 |
CVE-2023-41609 | 2023-09-11T18:15:10.993 | An open redirect vulnerability in the sanitize_url() parameter of CouchCMS v2.3 allows attackers to redirect a victim user to an arbitrary web site via a crafted URL. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/CouchCMS/CouchCMS/issues/190"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:couchcms:couchcms:2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "54DC5B84-C10C-47C8-8168-FCBC27DB17ED",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"601"
] | 601 | https://github.com/CouchCMS/CouchCMS/issues/190 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"CouchCMS",
"CouchCMS"
] | Exploit Title: CouchCMS v2.3 exists an open redirect vulnerability
Product: CouchCMS
Versio: v2.3
Software Link: https://github.com/CouchCMS/CouchCMS
+ Vulnerability Description
The server does not strictly filter the incoming jump url variables, resulting in malicious construction of any malicious... | CouchCMS v2.3 exists an open redirect vulnerability | https://api.github.com/repos/CouchCMS/CouchCMS/issues/190/comments | 2 | 2023-08-28T12:47:12Z | 2023-08-28T20:52:35Z | https://github.com/CouchCMS/CouchCMS/issues/190 | 1,869,697,810 | 190 | 5,585 |
CVE-2023-41423 | 2023-09-12T22:15:08.107 | Cross Site Scripting vulnerability in WP Githuber MD plugin v.1.16.2 allows a remote attacker to execute arbitrary code via a crafted payload to the new article function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/terrylinooo/githuber-md/issues/316"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:terryl:wp_githuber_md:1.16.2:*:*:*:*:wordpress:*:*",
"matchCriteriaId": "FFE3EA4A-3E74-4943-8E77-9CAAD05A2677",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"79"
] | 79 | https://github.com/terrylinooo/githuber-md/issues/316 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"terrylinooo",
"githuber-md"
] | When I used this plugin to write MD articles, I encountered a stored XSS vulnerability
Steps to reproduce the behavior:
1. Enable WP Githuber MD v1.16.2 plugin
2. Write new articles (via MD editor of this plugin)
3. Insert the following JS code:(Note that I added Tab spaces!!!)
</textarea><script>alert('a... | There is a stored XSS vulnerability | https://api.github.com/repos/terrylinooo/githuber-md/issues/316/comments | 2 | 2023-08-21T12:31:03Z | 2023-10-23T01:03:47Z | https://github.com/terrylinooo/githuber-md/issues/316 | 1,859,273,206 | 316 | 5,586 |
CVE-2023-42405 | 2023-09-14T23:15:08.277 | SQL injection vulnerability in FIT2CLOUD RackShift v1.7.1 allows attackers to execute arbitrary code via the `sort` parameter to taskService.list(), bareMetalService.list(), and switchService.list(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/fit2cloud/rackshift/issues/79"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fit2cloud:rackshift:1.7.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E08D3D59-714E-4B00-992B-59158730E58B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"89"
] | 89 | https://github.com/fit2cloud/rackshift/issues/79 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"fit2cloud",
"rackshift"
] | ## Description
Multiple SQL injection vulnerabilities in RackShift v1.7.1 allow attacker to execute arbitrary SQL commands via the `sort` parameter to taskService.list(), bareMetalService.list(), switchService.list() and so on.
## Detail
Multiple controllers have SQL injection vulnerabilities, and I will use TaskCon... | [BUG] SQL injection vulnerability in list() method across multiple controllers | https://api.github.com/repos/fit2cloud/rackshift/issues/79/comments | 0 | 2023-09-06T15:54:55Z | 2023-12-12T06:50:34Z | https://github.com/fit2cloud/rackshift/issues/79 | 1,884,310,101 | 79 | 5,587 |
CVE-2023-4984 | 2023-09-15T14:15:11.457 | A vulnerability was found in didi KnowSearch 0.3.2/0.3.1.2. It has been rated as problematic. This issue affects some unknown processing of the file /api/es/admin/v3/security/user/1. The manipulation leads to unprotected storage of credentials. The attack may be initiated remotely. The exploit has been disclosed to the... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit"
],
"url": "https://github.com/didi/KnowSearch/files/12135597/ad1aa7b3-ecee-44b0-a22a-80917ca0fe71.pdf4398935202801712312.pdf"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:didiglobal:knowsearch:0.3.1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "61BF4201-C7AE-403F-87ED-292387FE8F4A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"256"
] | 256 | https://github.com/didi/KnowSearch/issues/86 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"didi",
"KnowSearch"
] | [ad1aa7b3-ecee-44b0-a22a-80917ca0fe71.pdf4398935202801712312.pdf](https://github.com/didi/KnowSearch/files/12135597/ad1aa7b3-ecee-44b0-a22a-80917ca0fe71.pdf4398935202801712312.pdf)
| KnowSearch 用户认证安全风险修复 | https://api.github.com/repos/didi/KnowSearch/issues/86/comments | 1 | 2023-07-22T02:59:33Z | 2024-02-19T10:32:17Z | https://github.com/didi/KnowSearch/issues/86 | 1,816,576,234 | 86 | 5,588 |
CVE-2023-39612 | 2023-09-16T01:15:07.397 | A cross-site scripting (XSS) vulnerability in FileBrowser before v2.23.0 allows an authenticated attacker to escalate privileges to Administrator via user interaction with a crafted HTML file or URL. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://febin0x4e4a.wordpress.com/2023/09/15/xss-in-filebrowser-leads-to-admin-account-takeover-in-filebrowser/"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:filebrowser:filebrowser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B368F96D-05ED-446B-BA42-68FC7F8A2269",
"versionEndExcluding": "2.23.0",
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/filebrowser/filebrowser/issues/2570 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"filebrowser",
"filebrowser"
] | ### Description
A Cross-Site Scripting vulnerability is discovered in FileBrowser in which an attacker with a non-admin user account inside the FileBrowser instance can create malicious HTML & JS files, craft them in a specific way and send the HTML file's link to the Admin to achieve Account takeover via XSS bypass... | Potential XSS in FileBrowser leads to Admin account takeover in Filebrowser | https://api.github.com/repos/filebrowser/filebrowser/issues/2570/comments | 4 | 2023-07-25T06:55:22Z | 2023-07-27T10:14:57Z | https://github.com/filebrowser/filebrowser/issues/2570 | 1,819,677,416 | 2,570 | 5,589 |
CVE-2023-5015 | 2023-09-17T02:15:07.430 | A vulnerability was found in UCMS 1.4.7. It has been classified as problematic. Affected is an unknown function of the file ajax.php?do=strarraylist. The manipulation of the argument strdefault leads to cross site scripting. It is possible to launch the attack remotely. The exploit has been disclosed to the public and ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/3"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ucms_project:ucms:1.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "5498798F-9AC7-4309-B2E9-90B8959E70F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Num-Nine/CVE/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | 1.Download address: https://github.com/forget-code/ucms
2.Vulnerability file location: http://127.0.0.1/CVE-Target/ucms-master/ucms/ajax.php? do=strarraylist
3.You need to manually create the cache and uploadfile directories during program installation
4.Ucms-master /ucms/ajax.php installed successfully? do=st... | The ucms has xss | https://api.github.com/repos/QianGeG/CVE/issues/3/comments | 0 | 2023-09-06T03:31:30Z | 2023-09-06T03:31:30Z | https://github.com/QianGeG/CVE/issues/3 | 1,883,115,340 | 3 | 5,590 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.