cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-33363 | 2021-09-13T20:15:08.567 | Memory leak in the infe_box_read function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/ec64c7b8966d7e4642d12debb888be5acf18efb9"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/1786 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box infe_box_read | https://api.github.com/repos/gpac/gpac/issues/1786/comments | 0 | 2021-05-08T05:17:05Z | 2023-09-22T06:13:34Z | https://github.com/gpac/gpac/issues/1786 | 880,299,345 | 1,786 | 2,475 |
CVE-2021-33365 | 2021-09-13T20:15:08.627 | Memory leak in the gf_isom_get_root_od function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/984787de3d414a5f7d43d0b4584d9469dff2a5a5"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/1784 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box gf_isom_get_root_od | https://api.github.com/repos/gpac/gpac/issues/1784/comments | 0 | 2021-05-08T05:14:42Z | 2023-09-22T06:08:59Z | https://github.com/gpac/gpac/issues/1784 | 880,296,904 | 1,784 | 2,476 |
CVE-2020-20670 | 2021-09-13T22:15:07.437 | An arbitrary file upload vulnerability in /admin/media/upload of ZKEACMS V3.2.0 allows attackers to execute arbitrary code via a crafted HTML file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yilezhu/Czar.Cms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zkea:zkeacms:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8BE5639E-3AAD-49E8-B7F9-855537544440",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"434"
] | 434 | https://github.com/yilezhu/Czar.Cms/issues/6 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yilezhu",
"Czar.Cms"
] | Can upload Html
Cause fishing attacks , JavaScript Code execution

url :http://demo.zkea.net/admin/media/upload
poc :
-----------------------------189153225812082
Content-Disposition: form-data; name="file";... | Arbitrary file upload vulnerability exists in the background | https://api.github.com/repos/yilezhu/Czar.Cms/issues/6/comments | 0 | 2019-10-11T08:36:25Z | 2019-10-11T08:36:25Z | https://github.com/yilezhu/Czar.Cms/issues/6 | 505,716,018 | 6 | 2,477 |
CVE-2020-20671 | 2021-09-13T22:15:10.077 | A cross-site request forgery (CSRF) in KiteCMS V1.1 allows attackers to arbitrarily add an administrator account. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Kitesky/KiteCMS/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kitesky:kitecms:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "206854A6-CDE7-4607-B768-79570E16AE42",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/Kitesky/KiteCMS/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Kitesky",
"KiteCMS"
] | SCRF : add administrator user
Edit Upload options
Upload php file getshell
CSRF POC:

Edit Upload options
 via a crafted PSD file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://bitbucket.org/netbsd/pkgsrc/commits/970a81d31ec7498e04d09b6b7771cef35f63cd28"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8C9591E2-D3E9-40F7-82E8-EAA2FB78FD4D",
"versionEndExcluding": "1.8.5",
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/saitoha/libsixel/issues/74 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Our fuzzer detected several crashes when converting PSD file against 2df6437 (compiled with Address Sanitizer). The command to trigger that is `img2sixel $POC -o /tmp/test.six` where $POC is:
https://github.com/ntu-sec/pocs/blob/master/libsixel-2df6437/crashes/read_stb_image.h%3A5669_1.psd
gdb output:
```
Read... | Address Sanitizer: invalid read at stb_image.h:5669 | https://api.github.com/repos/saitoha/libsixel/issues/74/comments | 3 | 2018-07-28T12:00:04Z | 2020-01-03T01:34:42Z | https://github.com/saitoha/libsixel/issues/74 | 345,443,147 | 74 | 2,480 |
CVE-2020-21050 | 2021-09-14T16:15:08.987 | Libsixel prior to v1.8.3 contains a stack buffer overflow in the function gif_process_raster at fromgif.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://bitbucket.org/netbsd/pkgsrc/commits/a27113e21179cbfbfae0c35f6a9edd6aa498faae"
},
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/12... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A5CB650-56E4-4DF9-9310-080C174E1528",
"versionEndExcluding": "1.8.3",
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/saitoha/libsixel/issues/75 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Our fuzzer detected several crashes when converting gif file against 2df6437 (compiled with Address Sanitizer). The command to trigger that is `img2sixel $POC -o /tmp/test.six` where $POC can be:
https://github.com/ntu-sec/pocs/blob/master/libsixel-2df6437/crashes/so_fromgif.c%3A310_1.gif
https://github.com/ntu-sec/... | AddressSanitizer: stack-buffer-overflow at fromgif.c:310 | https://api.github.com/repos/saitoha/libsixel/issues/75/comments | 2 | 2018-07-28T12:04:34Z | 2019-12-15T08:31:39Z | https://github.com/saitoha/libsixel/issues/75 | 345,443,459 | 75 | 2,481 |
CVE-2020-21081 | 2021-09-14T16:15:09.197 | A cross-site request forgery (CSRF) in Maccms 8.0 causes administrators to add and modify articles without their knowledge via clicking on a crafted URL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/magicblack/maccms8/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maccms:maccms:8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93D75918-25B5-4D87-8C9E-112C215DDEE6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"352"
] | 352 | https://github.com/magicblack/maccms8/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"magicblack",
"maccms8"
] | # xss
XSS vulnerability exists in the background administrator article management office when adding and modifying
Where Chinese and English names are entered, enter
`" onmousemove=alert(document.cookie) src=x`,Following chart
 vulnerability exists in the admin panel in Beego v2.0.1 via the URI path in an HTTP request, which is activated by administrators viewing the "Request Statistics" page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/beego/beego"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/beego/beego/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:beego:beego:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "3B58EC25-E45E-4F44-9EAC-CE89FFE0D709",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/beego/beego/issues/4727 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"beego",
"beego"
] | When navigating to a page, the path is not sanitized in the "Request statistics" in the admin panel, leading to an XSS.
For example, navigating to ```http://beego-site/<script>alert(1)</script>``` leads to an alert when viewed on the admin panel:

... | SQL Injection Vulerable. | https://api.github.com/repos/Kliqqi-CMS/Kliqqi-CMS/issues/259/comments | 0 | 2019-10-31T09:41:21Z | 2019-10-31T09:41:21Z | https://github.com/Kliqqi-CMS/Kliqqi-CMS/issues/259 | 515,291,262 | 259 | 2,485 |
CVE-2020-21122 | 2021-09-15T17:15:08.607 | UReport v2.2.9 contains a Server-Side Request Forgery (SSRF) in the designer page which allows attackers to detect intranet device ports. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/youseries/ureport/issues/483"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ureport_project:ureport:2.2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "10CADB94-5E0B-48FD-8430-516DAF5FD34C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"918"
] | 918 | https://github.com/youseries/ureport/issues/483 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"youseries",
"ureport"
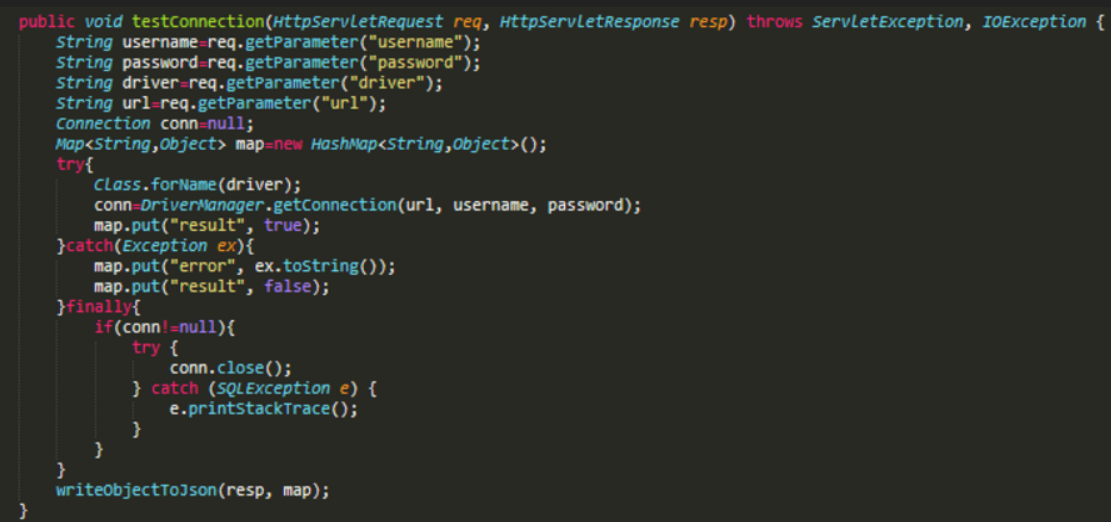
] | In this part of source code, we find that users can make connection requests to any IP address.
Then we found that the designer page did not verify the access user's permission.
So we can directly implement... | An unauthorized SSRF vulnerability in the designer page. | https://api.github.com/repos/youseries/ureport/issues/483/comments | 0 | 2019-11-29T04:20:17Z | 2019-11-29T04:20:17Z | https://github.com/youseries/ureport/issues/483 | 530,148,729 | 483 | 2,486 |
CVE-2020-21124 | 2021-09-15T17:15:08.730 | UReport 2.2.9 allows attackers to execute arbitrary code due to a lack of access control to the designer page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/youseries/ureport/issues/484"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ureport_project:ureport:2.2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "10CADB94-5E0B-48FD-8430-516DAF5FD34C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"863"
] | 863 | https://github.com/youseries/ureport/issues/484 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"youseries",
"ureport"
] | With the following source code, we can easily find that the 'class. Forname' method can load malicious classes.

'Class.forname' is a method for JVM to retrieve and load into memory. In this process, the ... | Local malicious class loading and code execution vulnerability due to unauthorized access to designer page. | https://api.github.com/repos/youseries/ureport/issues/484/comments | 0 | 2019-11-29T05:25:46Z | 2019-11-29T05:25:46Z | https://github.com/youseries/ureport/issues/484 | 530,161,732 | 484 | 2,487 |
CVE-2020-21126 | 2021-09-15T17:15:08.957 | MetInfo 7.0.0 contains a Cross-Site Request Forgery (CSRF) via admin/?n=admin&c=index&a=doSaveInfo. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Echox1/metinfo_csrf/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:-:*:*:*:*:*:*",
"matchCriteriaId": "65A2CB16-CC11-4C8B-9CCC-7241BDD92E0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/Echox1/metinfo_csrf/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Echox1",
"metinfo_csrf"
] | There is a csrf via admin/?n=admin&c=index&a=doSaveInfo to update the admin user account
request:
```POST /MetInfo7.0.0/admin/?n=admin&c=index&a=doSaveInfo HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: application/json, text/javascript, ... | There is a csrf in MetInfo 7.0.0 via admin/?n=admin&c=index&a=doSaveInfo to update the admin user | https://api.github.com/repos/Echox1/metinfo_csrf/issues/1/comments | 0 | 2019-12-02T08:00:27Z | 2019-12-02T08:01:46Z | https://github.com/Echox1/metinfo_csrf/issues/1 | 530,957,069 | 1 | 2,488 |
CVE-2020-21127 | 2021-09-15T17:15:09.037 | MetInfo 7.0.0 contains a SQL injection vulnerability via admin/?n=logs&c=index&a=dodel. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/T3qui1a/metinfo_sqlinjection/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:-:*:*:*:*:*:*",
"matchCriteriaId": "65A2CB16-CC11-4C8B-9CCC-7241BDD92E0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"89"
] | 89 | https://github.com/T3qui1a/metinfo_sqlinjection/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"T3qui1a",
"metinfo_sqlinjection"
] | Vulnerability Name: Metinfo7.0 CMS Background SQL Blind Injection
Product Homepage: https://www.metinfo.cn/
Software link: https://u.mituo.cn/api/metinfo/download/7.0.0beta
Version: V7.0.0
## Vulnerability code
logs/index.class.php
line32-line45

 {
$siteid = get_cookie('siteid');
$page = isset($GLOBALS['page']) ? intval($GLOBALS['page']) : 1;
$page = max($page,1);
$fieldtype = $GLOBALS['fieldtype'];
$keywords = $GLOBALS['key... | Wuzhicms v4.1.0 /coreframe/app/promote/admin/index.php hava a SQL Injection Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/196/comments | 0 | 2021-09-05T14:05:26Z | 2021-09-05T14:05:26Z | https://github.com/wuzhicms/wuzhicms/issues/196 | 988,517,784 | 196 | 2,493 |
CVE-2021-40670 | 2021-09-16T19:15:07.977 | SQL Injection vulnerability exists in Wuzhi CMS 4.1.0 via the keywords iparameter under the /coreframe/app/order/admin/card.php file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/197"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/wuzhicms/wuzhicms/issues/197 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | ## Vulnerability file:
`/coreframe/app/order/admin/card.php:21-45`
```php
public function listing() {
$page = isset($GLOBALS['page']) ? intval($GLOBALS['page']) : 1;
$page = max($page,1);
$batchid = isset($GLOBALS['batchid']) ? $GLOBALS['batchid'] : 0;
$keytype = isse... | Wuzhicms v4.1.0 /coreframe/app/order/admin/card.php hava a SQL Injection Vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/197/comments | 0 | 2021-09-06T02:43:30Z | 2021-09-06T02:59:23Z | https://github.com/wuzhicms/wuzhicms/issues/197 | 988,686,922 | 197 | 2,494 |
CVE-2020-21594 | 2021-09-16T22:15:07.587 | libde265 v1.0.4 contains a heap buffer overflow in the put_epel_hv_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/233"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
},
{
"source": "af854a3a-212... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/233 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_epel_hv_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.... | heap-buffer-overflow in put_epel_hv_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/233/comments | 4 | 2019-12-24T08:25:45Z | 2023-01-24T17:42:58Z | https://github.com/strukturag/libde265/issues/233 | 542,042,456 | 233 | 2,495 |
CVE-2020-21595 | 2021-09-16T22:15:07.697 | libde265 v1.0.4 contains a heap buffer overflow in the mc_luma function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/239"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/239 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in mc_luma when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Rel... | heap-buffer-overflow in mc_luma when decoding file | https://api.github.com/repos/strukturag/libde265/issues/239/comments | 2 | 2019-12-24T11:28:20Z | 2023-01-24T18:06:05Z | https://github.com/strukturag/libde265/issues/239 | 542,098,946 | 239 | 2,496 |
CVE-2020-21596 | 2021-09-16T22:15:07.743 | libde265 v1.0.4 contains a global buffer overflow in the decode_CABAC_bit function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/236"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"120"
] | 120 | https://github.com/strukturag/libde265/issues/236 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # global buffer overflow in decode_CABAC_bit when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04... | global buffer overflow in decode_CABAC_bit when decoding file | https://api.github.com/repos/strukturag/libde265/issues/236/comments | 2 | 2019-12-24T11:22:38Z | 2023-01-24T18:01:46Z | https://github.com/strukturag/libde265/issues/236 | 542,097,369 | 236 | 2,497 |
CVE-2020-21597 | 2021-09-16T22:15:07.793 | libde265 v1.0.4 contains a heap buffer overflow in the mc_chroma function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/238"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/238 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in mc_chroma when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
R... | heap-buffer-overflow in mc_chroma when decoding file | https://api.github.com/repos/strukturag/libde265/issues/238/comments | 4 | 2019-12-24T11:26:58Z | 2023-01-24T18:04:53Z | https://github.com/strukturag/libde265/issues/238 | 542,098,570 | 238 | 2,498 |
CVE-2020-21598 | 2021-09-16T22:15:07.837 | libde265 v1.0.4 contains a heap buffer overflow in the ff_hevc_put_unweighted_pred_8_sse function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/237 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in ff_hevc_put_unweighted_pred_8_sse when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: ... | heap-buffer-overflow in ff_hevc_put_unweighted_pred_8_sse when decoding file | https://api.github.com/repos/strukturag/libde265/issues/237/comments | 3 | 2019-12-24T11:25:26Z | 2023-01-24T18:03:54Z | https://github.com/strukturag/libde265/issues/237 | 542,098,137 | 237 | 2,499 |
CVE-2020-21599 | 2021-09-16T22:15:07.880 | libde265 v1.0.4 contains a heap buffer overflow in the de265_image::available_zscan function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/235"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/235 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | # heap overflow in de265_image::available_zscan when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16... | heap overflow in de265_image::available_zscan when decoding file | https://api.github.com/repos/strukturag/libde265/issues/235/comments | 4 | 2019-12-24T11:18:40Z | 2023-01-24T17:46:14Z | https://github.com/strukturag/libde265/issues/235 | 542,096,202 | 235 | 2,500 |
CVE-2020-21600 | 2021-09-16T22:15:07.920 | libde265 v1.0.4 contains a heap buffer overflow in the put_weighted_pred_avg_16_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/struktura... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/243 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_weighted_pred_avg_16_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: ... | heap-buffer-overflow in put_weighted_pred_avg_16_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/243/comments | 4 | 2019-12-24T11:35:38Z | 2023-01-24T18:10:24Z | https://github.com/strukturag/libde265/issues/243 | 542,100,957 | 243 | 2,501 |
CVE-2020-21601 | 2021-09-16T22:15:07.963 | libde265 v1.0.4 contains a stack buffer overflow in the put_qpel_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/241"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/241 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # stack-buffer-overflow in put_qpel_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04... | stack-buffer-overflow in put_qpel_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/241/comments | 3 | 2019-12-24T11:32:05Z | 2023-01-24T18:08:34Z | https://github.com/strukturag/libde265/issues/241 | 542,100,005 | 241 | 2,502 |
CVE-2020-21602 | 2021-09-16T22:15:08.007 | libde265 v1.0.4 contains a heap buffer overflow in the put_weighted_bipred_16_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/122.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/struktura... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/242 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_weighted_bipred_16_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: ... | heap-buffer-overflow in put_weighted_bipred_16_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/242/comments | 2 | 2019-12-24T11:33:52Z | 2023-01-24T18:09:22Z | https://github.com/strukturag/libde265/issues/242 | 542,100,475 | 242 | 2,503 |
CVE-2020-21603 | 2021-09-16T22:15:08.050 | libde265 v1.0.4 contains a heap buffer overflow in the put_qpel_0_0_fallback_16 function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/240"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/240 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_qpel_0_0_fallback_16 when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu... | heap-buffer-overflow in put_qpel_0_0_fallback_16 when decoding file | https://api.github.com/repos/strukturag/libde265/issues/240/comments | 3 | 2019-12-24T11:29:40Z | 2023-01-24T18:07:17Z | https://github.com/strukturag/libde265/issues/240 | 542,099,323 | 240 | 2,504 |
CVE-2020-21604 | 2021-09-16T22:15:08.093 | libde265 v1.0.4 contains a heap buffer overflow fault in the _mm_loadl_epi64 function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/231"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/231 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in decode file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.04.6 LTS
Release: 16... | heap-buffer-overflow in decode file | https://api.github.com/repos/strukturag/libde265/issues/231/comments | 3 | 2019-12-24T03:25:24Z | 2023-01-24T17:40:29Z | https://github.com/strukturag/libde265/issues/231 | 541,973,882 | 231 | 2,505 |
CVE-2020-21606 | 2021-09-16T22:15:08.177 | libde265 v1.0.4 contains a heap buffer overflow fault in the put_epel_16_fallback function, which can be exploited via a crafted a file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/strukturag/libde265/issues/232"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5346"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "4F5331C0-3C70-42CB-AC2C-4E8B7FA1328F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/232 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"strukturag",
"libde265"
] | # heap-buffer-overflow in put_epel_16_fallback when decoding file
I found some problems during fuzzing
## Test Version
dev version, git clone https://github.com/strukturag/libde265
## Test Environment
root@ubuntu:~# lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 16.... | heap-buffer-overflow in put_epel_16_fallback when decoding file | https://api.github.com/repos/strukturag/libde265/issues/232/comments | 5 | 2019-12-24T08:22:59Z | 2023-01-24T17:39:38Z | https://github.com/strukturag/libde265/issues/232 | 542,041,601 | 232 | 2,506 |
CVE-2021-23442 | 2021-09-17T10:15:07.437 | This affects all versions of package @cookiex/deep. The global proto object can be polluted using the __proto__ object. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tony-tsx/cookiex-deep/commit/b5bea2b7f34a5fa9abb4446cbd038ecdbcd09c88"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cookiex-deep_project:cookiex-deep:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "F007AA1F-4D44-4CAE-8BF5-CA7707EDB1B1",
"versionEndExcluding": "0.0.6",
"versionEndIncluding": null,
... | [
"1321"
] | 1321 | https://github.com/tony-tsx/cookiex-deep/issues/1 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"tony-tsx",
"cookiex-deep"
] | [@cookiex/deep](https://www.npmjs.com/package/@cookiex/deep) npm package is vulnerable to **prototype pollution** vulnerability prior to version 0.0.6. | @cookiex/deep npm package is vulnerable to prototype pollution vulnerability prior to version 0.0.6. | https://api.github.com/repos/tony-tsx/cookiex-deep/issues/1/comments | 0 | 2021-09-06T06:29:37Z | 2021-09-14T12:21:35Z | https://github.com/tony-tsx/cookiex-deep/issues/1 | 988,815,265 | 1 | 2,507 |
CVE-2020-21547 | 2021-09-17T21:15:07.313 | Libsixel 1.8.2 contains a heap-based buffer overflow in the dither_func_fs function in tosixel.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/114"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.2:*:*:*:*:*:*:*",
"matchCriteriaId": "BAFCC979-2F4E-46A5-AC18-B6452E752D90",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/saitoha/libsixel/issues/114 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | version : img2sixel 1.8.2
There is a heap-buffer-overflow in dither_func_fs at tosixel.c:861
please run following cmd to reproduce it.
```
img2sixel --high-color $PoC
```
[poc](https://drive.google.com/file/d/1Zbn3EFlTBY7dBozOSegrchWQ0F8MEO7I/view?usp=sharing)
ASAN LOG
```
==39700==ERROR: AddressSanitizer: h... | heap-buffer-overflow in dither_func_fs at tosixel.c:861 | https://api.github.com/repos/saitoha/libsixel/issues/114/comments | 1 | 2019-12-13T13:53:59Z | 2019-12-16T14:40:25Z | https://github.com/saitoha/libsixel/issues/114 | 537,562,433 | 114 | 2,508 |
CVE-2020-21548 | 2021-09-17T21:15:07.360 | Libsixel 1.8.3 contains a heap-based buffer overflow in the sixel_encode_highcolor function in tosixel.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/116"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75488CEA-3C52-4C9C-97F2-83B652FD701D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/saitoha/libsixel/issues/116 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | img2sixel 1.8.3
There is a heap-buffer-overflow in sixel_encode_highcolor at tosixel.c:1361
please run following cmd to reproduce it.
```
img2sixel --high-color $PoC
```
[poc](https://drive.google.com/file/d/1Hdpq1fEL_DgGeEqXyKD0YIcTOICjoGgS/view?usp=sharing)
ASAN LOG
```
==28051==ERROR: AddressSanitizer: he... | heap-buffer-overflow in sixel_encode_highcolor at tosixel.c:1361 | https://api.github.com/repos/saitoha/libsixel/issues/116/comments | 1 | 2019-12-16T04:32:36Z | 2019-12-18T20:32:53Z | https://github.com/saitoha/libsixel/issues/116 | 538,179,086 | 116 | 2,509 |
CVE-2021-41392 | 2021-09-17T22:15:08.163 | static/main-preload.js in Boost Note through 0.22.0 allows remote command execution. A remote attacker may send a crafted IPC message to the exposed vulnerable ipcRenderer IPC interface, which invokes the dangerous openExternal Electron API. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/BoostIO/BoostNote-App/issues/856"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boostnote:boostnote:*:*:*:*:*:*:*:*",
"matchCriteriaId": "608C136E-55B4-49D2-A188-3A98619F4DCA",
"versionEndExcluding": null,
"versionEndIncluding": "0.22.0",
"versionStartEx... | [
"74"
] | 74 | https://github.com/BoostIO/BoostNote-App/issues/856 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"BoostIO",
"BoostNote-App"
] | Hi,
We found that `static/main-preload.js` introduces dangerous API openShellExternal for arbitrary access on unsafe renderer process.
This may lead to remote command execution.
We suggest that a URL check should be enforced at L15, which enforces an allowlist on trusted URLs.
https://github.com/BoostIO/BoostNo... | Potential Command Execution vulnerabilities introduced by main-preload.js | https://api.github.com/repos/BoostIO/BoostNote-App/issues/856/comments | 2 | 2021-03-09T15:02:25Z | 2022-06-04T18:54:59Z | https://github.com/BoostIO/BoostNote-App/issues/856 | 826,066,955 | 856 | 2,510 |
CVE-2021-40674 | 2021-09-20T15:15:08.990 | An SQL injection vulnerability exists in Wuzhi CMS v4.1.0 via the KeyValue parameter in coreframe/app/order/admin/index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/198"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/wuzhicms/wuzhicms/issues/198 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | # There are 3 SQL injections in Wuzhicms v4.1.0 background
# one
## Wuzhicms v4.1.0 /coreframe/app/pay/admin/index.php hava a SQL Injection Vulnerability
## Vulnerability file:
`/coreframe/app/pay/admin/index.php 30-98`
```php
public function listing(){
$fieldtypes = array('订单号', '手机号'... | There are 3 SQL injections in Wuzhicms v4.1.0 background | https://api.github.com/repos/wuzhicms/wuzhicms/issues/198/comments | 0 | 2021-09-06T13:00:49Z | 2021-09-21T06:49:49Z | https://github.com/wuzhicms/wuzhicms/issues/198 | 989,149,160 | 198 | 2,511 |
CVE-2021-32265 | 2021-09-20T16:15:09.913 | An issue was discovered in Bento4 through v1.6.0-637. A global-buffer-overflow exists in the function AP4_MemoryByteStream::WritePartial() located in Ap4ByteStream.cpp. It allows an attacker to cause code execution or information disclosure. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/545"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9684D8EA-E280-40A0-BB75-E7AFB950B234",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-637",
"versionStartExcl... | [
"120"
] | 120 | https://github.com/axiomatic-systems/Bento4/issues/545 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | ## System info
Ubuntu x86_64, clang 6.0, mp42aac (latest master [174b94](https://github.com/axiomatic-systems/Bento4/commit/174b948be29b69009b235ae0aa92884d05bcea49))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=add... | A global-buffer-overflow in Ap4ByteStream.cpp:783:5 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/545/comments | 1 | 2020-08-22T01:47:18Z | 2022-05-01T20:31:46Z | https://github.com/axiomatic-systems/Bento4/issues/545 | 683,904,034 | 545 | 2,512 |
CVE-2021-32268 | 2021-09-20T16:15:09.960 | Buffer overflow vulnerability in function gf_fprintf in os_file.c in gpac before 1.0.1 allows attackers to execute arbitrary code. The fixed version is 1.0.1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/388ecce75d05e11fc8496aa4857b91245007d26e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1587 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [5a884e](https://github.com/gpac/gpac/commit/5a884e376e1f67b3d40ec91c0b70ab49219fe3cd))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A heap-buffer-overflow in box_dump.c:350 | https://api.github.com/repos/gpac/gpac/issues/1587/comments | 0 | 2020-09-04T15:05:21Z | 2020-09-07T07:20:45Z | https://github.com/gpac/gpac/issues/1587 | 693,270,293 | 1,587 | 2,513 |
CVE-2021-32269 | 2021-09-20T16:15:10.003 | An issue was discovered in gpac through 20200801. A NULL pointer dereference exists in the function ilst_item_box_dump located in box_dump.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1574"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1574 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A Segmentation fault in box_dump.c:3641 | https://api.github.com/repos/gpac/gpac/issues/1574/comments | 0 | 2020-08-13T03:20:26Z | 2020-09-01T16:00:16Z | https://github.com/gpac/gpac/issues/1574 | 678,118,496 | 1,574 | 2,514 |
CVE-2021-32270 | 2021-09-20T16:15:10.053 | An issue was discovered in gpac through 20200801. A NULL pointer dereference exists in the function vwid_box_del located in box_code_base.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1586"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1586 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [5a884e](https://github.com/gpac/gpac/commit/5a884e376e1f67b3d40ec91c0b70ab49219fe3cd))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A Segmentation fault in box_code_base.c:11579 | https://api.github.com/repos/gpac/gpac/issues/1586/comments | 0 | 2020-09-04T14:58:11Z | 2020-09-07T07:20:45Z | https://github.com/gpac/gpac/issues/1586 | 693,262,344 | 1,586 | 2,515 |
CVE-2021-32271 | 2021-09-20T16:15:10.100 | An issue was discovered in gpac through 20200801. A stack-buffer-overflow exists in the function DumpRawUIConfig located in odf_dump.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1575"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1575 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A stack-buffer-overflow in odf_dump.c:887 | https://api.github.com/repos/gpac/gpac/issues/1575/comments | 0 | 2020-08-15T01:36:37Z | 2020-09-01T16:03:15Z | https://github.com/gpac/gpac/issues/1575 | 679,475,781 | 1,575 | 2,516 |
CVE-2021-32272 | 2021-09-20T16:15:10.143 | An issue was discovered in faad2 before 2.10.0. A heap-buffer-overflow exists in the function stszin located in mp4read.c. It allows an attacker to cause Code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/knik0/faad2/commit/1b71a6ba963d131375f5e489b3b25e36f19f3f24"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AF3BA5A2-CCE7-471A-B083-FD9557B427A9",
"versionEndExcluding": "2.10.0",
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/57 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knik0",
"faad2"
] | ## System info
Ubuntu x86_64, clang 6.0, faad (latest master [1073ae](https://github.com/knik0/faad2/commit/1073aeef823cafd844704389e9a497c257768e2f))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-shared=no
## Command line
./frontend/faad -w -b 5 @@
## A... | A heap-buffer-overflow in mp4read.c:355:29 | https://api.github.com/repos/knik0/faad2/issues/57/comments | 0 | 2020-08-30T15:27:09Z | 2020-08-31T08:55:06Z | https://github.com/knik0/faad2/issues/57 | 688,738,712 | 57 | 2,517 |
CVE-2021-32273 | 2021-09-20T16:15:10.187 | An issue was discovered in faad2 through 2.10.0. A stack-buffer-overflow exists in the function ftypin located in mp4read.c. It allows an attacker to cause Code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/knik0/faad2/issues/56"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://www.debian.org/security/2022... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "473E94D7-49A2-4FA4-82CD-726B2B84FF95",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.0",
"versionStartEx... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/56 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knik0",
"faad2"
] |
## System info
Ubuntu x86_64, clang 6.0, faad (latest master [eb19fa](https://github.com/knik0/faad2/commit/eb19fa58e08ffad79fe4af09abc0b5a584b4e6e6))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-shared=no
## Command line
./frontend/faad -w -b 5 @@
##... | A stack-buffer-overflow in mp4read.c:141:9 | https://api.github.com/repos/knik0/faad2/issues/56/comments | 0 | 2020-08-16T07:27:58Z | 2020-08-17T05:37:21Z | https://github.com/knik0/faad2/issues/56 | 679,706,876 | 56 | 2,518 |
CVE-2021-32274 | 2021-09-20T16:15:10.230 | An issue was discovered in faad2 through 2.10.0. A heap-buffer-overflow exists in the function sbr_qmf_synthesis_64 located in sbr_qmf.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/knik0/faad2/issues/60"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "473E94D7-49A2-4FA4-82CD-726B2B84FF95",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.0",
"versionStartEx... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/60 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knik0",
"faad2"
] | ## System info
Ubuntu x86_64, clang 6.0, faad (latest master [1073ae](https://github.com/knik0/faad2/commit/1073aeef823cafd844704389e9a497c257768e2f))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-shared=no
## Command line
./frontend/faad -w -b 5 @@
## A... | A heap-buffer-overflow in sbr_qmf.c:614:27 | https://api.github.com/repos/knik0/faad2/issues/60/comments | 1 | 2020-08-30T15:53:54Z | 2020-10-07T19:28:39Z | https://github.com/knik0/faad2/issues/60 | 688,743,058 | 60 | 2,519 |
CVE-2021-32275 | 2021-09-20T16:15:10.277 | An issue was discovered in faust through v2.30.5. A NULL pointer dereference exists in the function CosPrim::computeSigOutput() located in cosprim.hh. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/grame-cncm/faust/issues/482"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grame:faust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4DFD6F44-9ABE-4A8E-823E-7A45DE62126E",
"versionEndExcluding": null,
"versionEndIncluding": "2.30.5",
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/grame-cncm/faust/issues/482 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"grame-cncm",
"faust"
] | ## System info
Ubuntu x86_64, clang 6.0, faust (latest master [c236d2](https://github.com/grame-cncm/faust/commit/c236d23526de80c410f8014d36bb803af1da18b8))
## Configure
cmake . -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DINC... | A Segmentation fault in cosprim.hh:49:13 | https://api.github.com/repos/grame-cncm/faust/issues/482/comments | 7 | 2020-08-26T02:30:17Z | 2021-10-18T17:33:05Z | https://github.com/grame-cncm/faust/issues/482 | 685,956,370 | 482 | 2,520 |
CVE-2021-32276 | 2021-09-20T16:15:10.317 | An issue was discovered in faad2 through 2.10.0. A NULL pointer dereference exists in the function get_sample() located in output.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/knik0/faad2/issues/58"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "473E94D7-49A2-4FA4-82CD-726B2B84FF95",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.0",
"versionStartEx... | [
"476"
] | 476 | https://github.com/knik0/faad2/issues/58 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knik0",
"faad2"
] | ## System info
Ubuntu x86_64, clang 6.0, faad (latest master [1073ae](https://github.com/knik0/faad2/commit/1073aeef823cafd844704389e9a497c257768e2f))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-shared=no
## Command line
./frontend/faad -w -b 5 @@
## A... | A Segmentation fault in output.c:49:16 | https://api.github.com/repos/knik0/faad2/issues/58/comments | 0 | 2020-08-30T15:29:51Z | 2020-10-09T15:48:34Z | https://github.com/knik0/faad2/issues/58 | 688,739,153 | 58 | 2,521 |
CVE-2021-32277 | 2021-09-20T16:15:10.363 | An issue was discovered in faad2 through 2.10.0. A heap-buffer-overflow exists in the function sbr_qmf_analysis_32 located in sbr_qmf.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/knik0/faad2/issues/59"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "473E94D7-49A2-4FA4-82CD-726B2B84FF95",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.0",
"versionStartEx... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/59 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knik0",
"faad2"
] | ## System info
Ubuntu x86_64, clang 6.0, faad (latest master [1073ae](https://github.com/knik0/faad2/commit/1073aeef823cafd844704389e9a497c257768e2f))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-shared=no
## Command line
./frontend/faad -w -b 5 @@
## A... | A heap-buffer-overflow in sbr_qmf.c:96:77 | https://api.github.com/repos/knik0/faad2/issues/59/comments | 0 | 2020-08-30T15:32:46Z | 2020-10-06T04:45:45Z | https://github.com/knik0/faad2/issues/59 | 688,739,598 | 59 | 2,522 |
CVE-2021-32278 | 2021-09-20T16:15:10.413 | An issue was discovered in faad2 through 2.10.0. A heap-buffer-overflow exists in the function lt_prediction located in lt_predict.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/knik0/faad2/issues/62"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:faad2_project:faad2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "473E94D7-49A2-4FA4-82CD-726B2B84FF95",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.0",
"versionStartEx... | [
"787"
] | 787 | https://github.com/knik0/faad2/issues/62 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"knik0",
"faad2"
] | ## System info
Ubuntu x86_64, clang 6.0, faad (latest master [f71b5e](https://github.com/knik0/faad2/commit/f71b5e81f563d94fa284977a326520d269d8353e))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-shared=no
## Command line
./frontend/faad -w -b 5 @@
## A... | A heap-buffer-overflow in lt_predict.c:108:36 | https://api.github.com/repos/knik0/faad2/issues/62/comments | 0 | 2020-09-04T14:47:28Z | 2020-10-06T04:45:45Z | https://github.com/knik0/faad2/issues/62 | 693,250,265 | 62 | 2,523 |
CVE-2021-32281 | 2021-09-20T16:15:10.517 | An issue was discovered in gravity through 0.8.1. A heap-buffer-overflow exists in the function gnode_function_add_upvalue located in gravity_ast.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marcobambini/gravity/issues/313"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creolabs:gravity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B07F7D2C-1B83-4D51-89BE-CDDCD836BA20",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.1",
"versionStartExclud... | [
"787"
] | 787 | https://github.com/marcobambini/gravity/issues/313 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcobambini",
"gravity"
] | ## System info
Ubuntu x86_64, clang 6.0, gravity (latest master [ecbee9f](https://github.com/marcobambini/gravity/commit/ecbee9f06e0168b17ddb953fb08adb4b9bb19fca))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=addres... | A heap-buffer-overflow in gravity_ast.c:90:41 can cause abort | https://api.github.com/repos/marcobambini/gravity/issues/313/comments | 1 | 2020-08-07T04:58:06Z | 2020-08-31T08:19:43Z | https://github.com/marcobambini/gravity/issues/313 | 674,757,661 | 313 | 2,524 |
CVE-2021-32282 | 2021-09-20T16:15:10.563 | An issue was discovered in gravity through 0.8.1. A NULL pointer dereference exists in the function ircode_add_check() located in gravity_ircode.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marcobambini/gravity/issues/315"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creolabs:gravity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B07F7D2C-1B83-4D51-89BE-CDDCD836BA20",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.1",
"versionStartExclud... | [
"476"
] | 476 | https://github.com/marcobambini/gravity/issues/315 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcobambini",
"gravity"
] | ## System info
Ubuntu x86_64, clang 6.0, gravity (latest master [ecbee9f](https://github.com/marcobambini/gravity/commit/ecbee9f06e0168b17ddb953fb08adb4b9bb19fca))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=addres... | A Segmentation fault in gravity_ircode.c:428:20 | https://api.github.com/repos/marcobambini/gravity/issues/315/comments | 1 | 2020-08-07T14:09:43Z | 2020-08-31T08:20:03Z | https://github.com/marcobambini/gravity/issues/315 | 675,041,848 | 315 | 2,525 |
CVE-2021-32283 | 2021-09-20T16:15:10.607 | An issue was discovered in gravity through 0.8.1. A NULL pointer dereference exists in the function gravity_string_to_value() located in gravity_value.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marcobambini/gravity/issues/314"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creolabs:gravity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B07F7D2C-1B83-4D51-89BE-CDDCD836BA20",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.1",
"versionStartExclud... | [
"476"
] | 476 | https://github.com/marcobambini/gravity/issues/314 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcobambini",
"gravity"
] | ## System info
Ubuntu x86_64, clang 6.0, gravity (latest master [ecbee9f](https://github.com/marcobambini/gravity/commit/ecbee9f06e0168b17ddb953fb08adb4b9bb19fca))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=addres... | A Segmentation fault in gravity_value.c:2382:44 | https://api.github.com/repos/marcobambini/gravity/issues/314/comments | 1 | 2020-08-07T14:07:36Z | 2020-08-31T08:19:54Z | https://github.com/marcobambini/gravity/issues/314 | 675,040,528 | 314 | 2,526 |
CVE-2021-32284 | 2021-09-20T16:15:10.647 | An issue was discovered in gravity through 0.8.1. A NULL pointer dereference exists in the function ircode_register_pop_context_protect() located in gravity_ircode.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marcobambini/gravity/issues/321"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creolabs:gravity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B07F7D2C-1B83-4D51-89BE-CDDCD836BA20",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.1",
"versionStartExclud... | [
"476"
] | 476 | https://github.com/marcobambini/gravity/issues/321 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcobambini",
"gravity"
] | ## System info
Ubuntu x86_64, clang 6.0, gravity (latest master [c79e18](https://github.com/marcobambini/gravity/commit/c79e185158a2b5d8f94eec599459d9a5355993c5))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address... | A Segmentation fault in gravity_ircode.c | https://api.github.com/repos/marcobambini/gravity/issues/321/comments | 1 | 2020-08-30T16:46:44Z | 2020-08-31T08:20:39Z | https://github.com/marcobambini/gravity/issues/321 | 688,751,618 | 321 | 2,527 |
CVE-2021-32285 | 2021-09-20T16:15:10.690 | An issue was discovered in gravity through 0.8.1. A NULL pointer dereference exists in the function list_iterator_next() located in gravity_core.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/marcobambini/gravity/issues/319"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:creolabs:gravity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B07F7D2C-1B83-4D51-89BE-CDDCD836BA20",
"versionEndExcluding": null,
"versionEndIncluding": "0.8.1",
"versionStartExclud... | [
"476"
] | 476 | https://github.com/marcobambini/gravity/issues/319 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"marcobambini",
"gravity"
] | ## System info
Ubuntu x86_64, clang 6.0, gravity (latest master [c79e18](https://github.com/marcobambini/gravity/commit/c79e185158a2b5d8f94eec599459d9a5355993c5))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address... | A Segmentation fault in gravity_core.c:1100:5 | https://api.github.com/repos/marcobambini/gravity/issues/319/comments | 1 | 2020-08-30T16:37:45Z | 2020-08-31T08:20:23Z | https://github.com/marcobambini/gravity/issues/319 | 688,750,158 | 319 | 2,528 |
CVE-2021-32286 | 2021-09-20T16:15:10.737 | An issue was discovered in hcxtools through 6.1.6. A global-buffer-overflow exists in the function pcapngoptionwalk located in hcxpcapngtool.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ZerBea/hcxtools/issues/155"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hcxtools_project:hcxtoold:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2464705C-CFC5-4E7E-AC0C-9402A0838E32",
"versionEndExcluding": null,
"versionEndIncluding": "6.1.6",
"versionSt... | [
"787"
] | 787 | https://github.com/ZerBea/hcxtools/issues/155 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ZerBea",
"hcxtools"
] | ## System info
Ubuntu x86_64, clang 6.0, hcxpcapngtool (latest master [e6b738](https://github.com/ZerBea/hcxtools/commit/e6b738c0fb905c40fae14c03b64fccf69919356e))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" make
## Command line
./hcxpcapngtool --all -o /dev/null @@
## Add... | A global-buffer-overflow in hcxpcapngtool.c:3789:4 | https://api.github.com/repos/ZerBea/hcxtools/issues/155/comments | 7 | 2020-08-12T03:09:27Z | 2021-09-21T15:30:32Z | https://github.com/ZerBea/hcxtools/issues/155 | 677,347,117 | 155 | 2,529 |
CVE-2021-32287 | 2021-09-20T16:15:10.783 | An issue was discovered in heif through v3.6.2. A global-buffer-overflow exists in the function HevcDecoderConfigurationRecord::getPicWidth() located in hevcdecoderconfigrecord.cpp. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nokiatech/heif/issues/86"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nokia:heif:*:*:*:*:*:*:*:*",
"matchCriteriaId": "665D3535-EF3B-45AF-9DE9-8A7AF5A34D4F",
"versionEndExcluding": null,
"versionEndIncluding": "3.6.2",
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/nokiatech/heif/issues/86 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"nokiatech",
"heif"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), heif (latest master [2fc78e](https://github.com/nokiatech/heif/commit/2fc78e4c80e9dbd22b5b0e09c137985d21d75512))
## Configure
cmake ../srcs -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsani... | A global-buffer-overflow in hevcdecoderconfigrecord.cpp:311:37 | https://api.github.com/repos/nokiatech/heif/issues/86/comments | 1 | 2020-08-04T07:58:10Z | 2020-08-12T09:12:35Z | https://github.com/nokiatech/heif/issues/86 | 672,589,184 | 86 | 2,530 |
CVE-2021-32288 | 2021-09-20T16:15:10.827 | An issue was discovered in heif through v3.6.2. A global-buffer-overflow exists in the function HevcDecoderConfigurationRecord::getPicHeight() located in hevcdecoderconfigrecord.cpp. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nokiatech/heif/issues/87"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nokia:heif:*:*:*:*:*:*:*:*",
"matchCriteriaId": "665D3535-EF3B-45AF-9DE9-8A7AF5A34D4F",
"versionEndExcluding": null,
"versionEndIncluding": "3.6.2",
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/nokiatech/heif/issues/87 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nokiatech",
"heif"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), heif (latest master [2fc78e](https://github.com/nokiatech/heif/commit/2fc78e4c80e9dbd22b5b0e09c137985d21d75512))
## Configure
cmake ../srcs -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsani... | A global-buffer-overflow in hevcdecoderconfigrecord.cpp:317:38 | https://api.github.com/repos/nokiatech/heif/issues/87/comments | 1 | 2020-08-04T14:03:20Z | 2020-08-12T09:13:08Z | https://github.com/nokiatech/heif/issues/87 | 672,818,230 | 87 | 2,531 |
CVE-2021-32289 | 2021-09-20T16:15:10.870 | An issue was discovered in heif through through v3.6.2. A NULL pointer dereference exists in the function convertByteStreamToRBSP() located in nalutil.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nokiatech/heif/issues/85"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nokia:heif:*:*:*:*:*:*:*:*",
"matchCriteriaId": "665D3535-EF3B-45AF-9DE9-8A7AF5A34D4F",
"versionEndExcluding": null,
"versionEndIncluding": "3.6.2",
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/nokiatech/heif/issues/85 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nokiatech",
"heif"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), heif (latest master [2fc78e](https://github.com/nokiatech/heif/commit/2fc78e4c80e9dbd22b5b0e09c137985d21d75512))
## Configure
cmake ../srcs -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsani... | A Segmentation fault in nalutil.cpp:49:10 | https://api.github.com/repos/nokiatech/heif/issues/85/comments | 1 | 2020-08-04T07:55:57Z | 2020-08-12T09:10:38Z | https://github.com/nokiatech/heif/issues/85 | 672,587,806 | 85 | 2,532 |
CVE-2021-32294 | 2021-09-20T16:15:10.917 | An issue was discovered in libgig through 20200507. A heap-buffer-overflow exists in the function RIFF::List::GetSubList located in RIFF.cpp. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/drbye78/libgig/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxsampler:libgig:*:*:*:*:*:*:*:*",
"matchCriteriaId": "292FD88A-E0C8-4C09-AE90-24952EC922FE",
"versionEndExcluding": null,
"versionEndIncluding": "20200507",
"versionStart... | [
"787"
] | 787 | https://github.com/drbye78/libgig/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"drbye78",
"libgig"
] | The User account creation has been disabled in Bugzilla, so I have to report it here.
## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), gigextract (latest master [237fd8](https://github.com/drbye78/libgig/commit/237fd8a12825717eaa648fb12e6b8bddd93032e6))
## Command line
./src/tools/gigextract @@ /... | A heap-buffer-overflow in RIFF.cpp:1151 | https://api.github.com/repos/drbye78/libgig/issues/1/comments | 0 | 2020-08-15T14:27:18Z | 2020-08-15T14:27:18Z | https://github.com/drbye78/libgig/issues/1 | 679,583,552 | 1 | 2,533 |
CVE-2021-32297 | 2021-09-20T16:15:10.963 | An issue was discovered in LIEF through 0.11.4. A heap-buffer-overflow exists in the function main located in pe_reader.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/lief-project/LIEF/issues/449"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lief-project:lief:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DE7CEECE-1180-4112-B47D-5DDC6362F33E",
"versionEndExcluding": null,
"versionEndIncluding": "0.11.4",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/lief-project/LIEF/issues/449 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"lief-project",
"LIEF"
] | ## System info
Ubuntu x86_64, gcc, pe_reader (latest master [4bbe410](https://github.com/lief-project/LIEF/commit/4bbe410333c0d727df6bc1f3bc92d4d5adc4726e))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address"
#... | A heap overflow in pe_reader.c:133 (not issue in the library) | https://api.github.com/repos/lief-project/LIEF/issues/449/comments | 1 | 2020-08-07T13:04:22Z | 2020-08-27T09:19:16Z | https://github.com/lief-project/LIEF/issues/449 | 675,002,426 | 449 | 2,534 |
CVE-2021-32298 | 2021-09-20T16:15:11.007 | An issue was discovered in libiff through 20190123. A global-buffer-overflow exists in the function IFF_errorId located in error.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/svanderburg/libiff/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libiff_project:libiff:*:*:*:*:*:*:*:*",
"matchCriteriaId": "60CE841D-B2B4-44B1-BF11-6C326887388D",
"versionEndExcluding": null,
"versionEndIncluding": "20190123",
"versionSta... | [
"787"
] | 787 | https://github.com/svanderburg/libiff/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"svanderburg",
"libiff"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), iffpp (latest master [0290be4](https://github.com/svanderburg/libiff/commit/0290be4ed3df0c1b8e8f5c24012cc75ba8870570))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./src/iffpp/.libs/lt-iffpp @... | A global-buffer-overflow in error.c:46:18 | https://api.github.com/repos/svanderburg/libiff/issues/10/comments | 0 | 2020-08-04T06:53:28Z | 2020-08-04T06:53:28Z | https://github.com/svanderburg/libiff/issues/10 | 672,552,072 | 10 | 2,535 |
CVE-2021-32299 | 2021-09-20T16:15:11.050 | An issue was discovered in pbrt through 20200627. A stack-buffer-overflow exists in the function pbrt::ParamSet::ParamSet() located in paramset.h. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mmp/pbrt-v3/issues/296"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbrt_project:pbrt:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5593DE2A-56F7-46F9-8A52-64281B9F2CD5",
"versionEndExcluding": null,
"versionEndIncluding": "20200627",
"versionStartEx... | [
"787"
] | 787 | https://github.com/mmp/pbrt-v3/issues/296 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mmp",
"pbrt-v3"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pbrt (latest master [aaa552](https://github.com/mmp/pbrt-v3/commit/aaa552a4b9cbf9dccb71450f47b268e0ed6370e2))
## Configure
cmake ../srcs -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitiz... | A stack-buffer-overflow in paramset.h:56 with default test case | https://api.github.com/repos/mmp/pbrt-v3/issues/296/comments | 0 | 2020-08-04T08:57:10Z | 2020-08-04T08:57:10Z | https://github.com/mmp/pbrt-v3/issues/296 | 672,626,915 | 296 | 2,536 |
CVE-2021-39514 | 2021-09-20T16:15:11.557 | An issue was discovered in libjpeg through 2020021. An uncaught floating point exception in the function ACLosslessScan::ParseMCU() located in aclosslessscan.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/36"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"697"
] | 697 | https://github.com/thorfdbg/libjpeg/issues/36 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Frame::ParseTrailer, line 1083, file ... | A heap overflow in aclosslessscan.cpp:349 causes segment fault | https://api.github.com/repos/thorfdbg/libjpeg/issues/36/comments | 2 | 2020-08-04T02:48:57Z | 2021-10-08T06:24:14Z | https://github.com/thorfdbg/libjpeg/issues/36 | 672,464,794 | 36 | 2,537 |
CVE-2021-39515 | 2021-09-20T16:15:11.597 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function SampleInterleavedLSScan::ParseMCU() located in sampleinterleavedlsscan.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/37"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/thorfdbg/libjpeg/issues/37 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
Segmentation fault
```
## AddressSanitizer output
`... | Segmentation fault in sampleinterleavedlsscan.cpp:133 | https://api.github.com/repos/thorfdbg/libjpeg/issues/37/comments | 3 | 2020-08-04T12:51:56Z | 2020-09-25T07:07:23Z | https://github.com/thorfdbg/libjpeg/issues/37 | 672,768,766 | 37 | 2,538 |
CVE-2021-39516 | 2021-09-20T16:15:11.640 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function HuffmanDecoder::Get() located in huffmandecoder.hpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/42"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/thorfdbg/libjpeg/issues/42 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## AddressSanitizer output
```
ASAN:SIGSEGV
======================... | Segmentation fault in refinementscan.cpp:644 | https://api.github.com/repos/thorfdbg/libjpeg/issues/42/comments | 1 | 2020-08-13T04:27:58Z | 2020-08-28T18:07:17Z | https://github.com/thorfdbg/libjpeg/issues/42 | 678,140,262 | 42 | 2,539 |
CVE-2021-39517 | 2021-09-20T16:15:11.683 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function BlockBitmapRequester::ReconstructUnsampled() located in blockbitmaprequester.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/33"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/thorfdbg/libjpeg/issues/33 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Tables::ParseTables, line 1384, file ... | Segmentation fault in blockbitmaprequester.cpp:1047 | https://api.github.com/repos/thorfdbg/libjpeg/issues/33/comments | 1 | 2020-08-04T01:54:43Z | 2020-08-29T07:47:06Z | https://github.com/thorfdbg/libjpeg/issues/33 | 672,446,762 | 33 | 2,540 |
CVE-2021-39518 | 2021-09-20T16:15:11.730 | An issue was discovered in libjpeg through 2020021. LineBuffer::FetchRegion() in linebuffer.cpp has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/35"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/thorfdbg/libjpeg/issues/35 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Tables::ParseTables, line 1384, file ta... | A heap overflow in linebuffer.cpp:322 causes segment fault | https://api.github.com/repos/thorfdbg/libjpeg/issues/35/comments | 1 | 2020-08-04T02:45:44Z | 2020-08-29T07:30:07Z | https://github.com/thorfdbg/libjpeg/issues/35 | 672,463,749 | 35 | 2,541 |
CVE-2021-39519 | 2021-09-20T16:15:11.773 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function BlockBitmapRequester::PullQData() located in blockbitmaprequester.cpp It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/thorfdbg/libjpeg/issues/28 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
For license conditions, see README.license for details.
*... | Segmentation fault in blockbitmaprequester.cpp:1100 | https://api.github.com/repos/thorfdbg/libjpeg/issues/28/comments | 1 | 2020-08-01T14:34:03Z | 2020-08-29T08:26:13Z | https://github.com/thorfdbg/libjpeg/issues/28 | 670,921,724 | 28 | 2,542 |
CVE-2021-39520 | 2021-09-20T16:15:11.813 | An issue was discovered in libjpeg through 2020021. A NULL pointer dereference exists in the function BlockBitmapRequester::PushReconstructedData() located in blockbitmaprequester.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/34"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A34FCBC-1BCC-4595-9283-0986879CDFDD",
"versionEndExcluding": null,
"versionEndIncluding": "2020021",
"versionStartExcludin... | [
"476"
] | 476 | https://github.com/thorfdbg/libjpeg/issues/34 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"thorfdbg",
"libjpeg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), jpeg (latest master [e52406](https://github.com/thorfdbg/libjpeg/commit/e524066cc8f532e37cf2360c9c33852b8b64f1da))
## Command line
./jpeg -oz -h -s 1x1,2x2,2x2 @@ /dev/null
## Output
```
*** Warning -1038 in Frame::ParseTrailer, line 1088, file ... | Segmentation fault in blockbitmaprequester.cpp:1182 | https://api.github.com/repos/thorfdbg/libjpeg/issues/34/comments | 1 | 2020-08-04T02:30:41Z | 2020-08-29T07:31:47Z | https://github.com/thorfdbg/libjpeg/issues/34 | 672,458,755 | 34 | 2,543 |
CVE-2021-39521 | 2021-09-20T16:15:11.857 | An issue was discovered in libredwg through v0.10.1.3751. A NULL pointer dereference exists in the function bit_read_BB() located in bits.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/262"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/LibreDWG/libredwg/issues/262 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [bacd017](https://github.com/LibreDWG/libredwg/commit/bacd01778d20b7b79f28541ea7a60cafe25175aa))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwg2dxf -b -m ./SE... | A Segmentation fault in bits.c:186 | https://api.github.com/repos/LibreDWG/libredwg/issues/262/comments | 2 | 2020-08-03T14:19:33Z | 2020-08-04T09:51:29Z | https://github.com/LibreDWG/libredwg/issues/262 | 672,111,174 | 262 | 2,544 |
CVE-2021-39522 | 2021-09-20T16:15:11.900 | An issue was discovered in libredwg through v0.10.1.3751. bit_wcs2len() in bits.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/255"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/255 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [aee0ea](https://github.com/LibreDWG/libredwg/commit/aee0ea1f52ef9603b981362c83b3fec324ebb199))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwg2dxf -b -m ./h... | A heap buffer overflow in bit_wcs2len at bits.c:1634 | https://api.github.com/repos/LibreDWG/libredwg/issues/255/comments | 1 | 2020-07-31T12:13:06Z | 2020-08-01T09:34:29Z | https://github.com/LibreDWG/libredwg/issues/255 | 669,753,229 | 255 | 2,545 |
CVE-2021-39523 | 2021-09-20T16:15:11.947 | An issue was discovered in libredwg through v0.10.1.3751. A NULL pointer dereference exists in the function check_POLYLINE_handles() located in decode.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/251"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/LibreDWG/libredwg/issues/251 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info:
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [aee0ea](https://github.com/LibreDWG/libredwg/commit/aee0ea1f52ef9603b981362c83b3fec324ebb199))
## Command line
./programs/dwg2dxf -b -m ./SEGV-check_POLYLINE_handles-decode-5110 -o /dev/null
## Output
```
Reading DWG file ./... | A Segmentation fault error in check_POLYLINE_handles at decode.c:5110 | https://api.github.com/repos/LibreDWG/libredwg/issues/251/comments | 0 | 2020-07-31T08:53:01Z | 2020-08-01T09:34:28Z | https://github.com/LibreDWG/libredwg/issues/251 | 669,581,382 | 251 | 2,546 |
CVE-2021-39525 | 2021-09-20T16:15:11.990 | An issue was discovered in libredwg through v0.10.1.3751. bit_read_fixed() in bits.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/261"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/261 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [39ef943](https://github.com/LibreDWG/libredwg/commit/39ef9439f35111170258cf57cc0c58eabc4748c7))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwg2dxf -b -m ./... | A heap overflow in bits.c:1424 | https://api.github.com/repos/LibreDWG/libredwg/issues/261/comments | 1 | 2020-08-02T04:51:37Z | 2020-08-02T12:15:30Z | https://github.com/LibreDWG/libredwg/issues/261 | 671,508,299 | 261 | 2,547 |
CVE-2021-39527 | 2021-09-20T16:15:12.037 | An issue was discovered in libredwg through v0.10.1.3751. appinfo_private() in decode.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/252"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/252 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info:
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwg2dxf (latest master [aee0ea](https://github.com/LibreDWG/libredwg/commit/aee0ea1f52ef9603b981362c83b3fec324ebb199))
## Command line
./programs/dwg2dxf -b -m ./heap-buffer-overflow-appinfo_private-decode-2993 -o /dev/null
## AddressSanitizer output
... | A heap buffer overflow in appinfo_private at decode.c:2993 | https://api.github.com/repos/LibreDWG/libredwg/issues/252/comments | 0 | 2020-07-31T08:58:03Z | 2020-08-01T09:34:29Z | https://github.com/LibreDWG/libredwg/issues/252 | 669,586,008 | 252 | 2,548 |
CVE-2021-39528 | 2021-09-20T16:15:12.077 | An issue was discovered in libredwg through v0.10.1.3751. dwg_free_MATERIAL_private() in dwg.spec has a double free. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/256"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"415"
] | 415 | https://github.com/LibreDWG/libredwg/issues/256 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwgbmp (latest master [4b99ed](https://github.com/LibreDWG/libredwg/commit/4b99edb0ea26e99ef65c5fe68670e6b1f9382d44))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwgbmp ./double-fr... | A double free in dwg.spec:7662 | https://api.github.com/repos/LibreDWG/libredwg/issues/256/comments | 1 | 2020-08-01T12:56:26Z | 2020-08-01T21:07:33Z | https://github.com/LibreDWG/libredwg/issues/256 | 670,848,928 | 256 | 2,549 |
CVE-2021-39530 | 2021-09-20T16:15:12.163 | An issue was discovered in libredwg through v0.10.1.3751. bit_wcs2nlen() in bits.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/258"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "937A8147-F4AB-4717-9E3F-4CFDF8194421",
"versionEndExcluding": null,
"versionEndIncluding": "0.10.1.3751",
"versionStartExcl... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/258 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), dwgbmp (latest master [39ef943](https://github.com/LibreDWG/libredwg/commit/39ef9439f35111170258cf57cc0c58eabc4748c7))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./programs/dwgbmp ./heap-ove... | Heap overflow due to incomplete fix for issues #255 | https://api.github.com/repos/LibreDWG/libredwg/issues/258/comments | 0 | 2020-08-02T02:25:59Z | 2020-08-02T12:15:29Z | https://github.com/LibreDWG/libredwg/issues/258 | 671,412,127 | 258 | 2,550 |
CVE-2021-39531 | 2021-09-20T16:15:12.210 | An issue was discovered in libslax through v0.22.1. slaxLexer() in slaxlexer.c has a stack-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Juniper/libslax/issues/53"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:juniper:libslax:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6D5523A4-6902-49B4-BD77-FD58DFA71EA1",
"versionEndExcluding": null,
"versionEndIncluding": "0.22.1",
"versionStartExclud... | [
"787"
] | 787 | https://github.com/Juniper/libslax/issues/53 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Juniper",
"libslax"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), slaxproc (latest master [45d88a](https://github.com/Juniper/libslax/commit/45d88a103c315519cd7e3566eec10dceb4ce9bdc))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./build/slaxproc/slaxproc -o ... | A dynamic-stack-buffer-overflow in slaxlexer.c:955:4 | https://api.github.com/repos/Juniper/libslax/issues/53/comments | 1 | 2020-08-03T16:29:31Z | 2025-01-02T05:23:03Z | https://github.com/Juniper/libslax/issues/53 | 672,196,824 | 53 | 2,551 |
CVE-2021-39532 | 2021-09-20T16:15:12.253 | An issue was discovered in libslax through v0.22.1. A NULL pointer dereference exists in the function slaxLexer() located in slaxlexer.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Juniper/libslax/issues/50"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:juniper:libslax:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6D5523A4-6902-49B4-BD77-FD58DFA71EA1",
"versionEndExcluding": null,
"versionEndIncluding": "0.22.1",
"versionStartExclud... | [
"476"
] | 476 | https://github.com/Juniper/libslax/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Juniper",
"libslax"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), slaxproc (latest master [45d88a](https://github.com/Juniper/libslax/commit/45d88a103c315519cd7e3566eec10dceb4ce9bdc))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./build/slaxproc/slaxproc -o ... | A Segmentation fault in slaxlexer.c:1107:13 | https://api.github.com/repos/Juniper/libslax/issues/50/comments | 2 | 2020-08-02T14:01:43Z | 2025-01-02T05:26:14Z | https://github.com/Juniper/libslax/issues/50 | 671,621,842 | 50 | 2,552 |
CVE-2021-39533 | 2021-09-20T16:15:12.300 | An issue was discovered in libslax through v0.22.1. slaxLexer() in slaxlexer.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Juniper/libslax/issues/51"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:juniper:libslax:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6D5523A4-6902-49B4-BD77-FD58DFA71EA1",
"versionEndExcluding": null,
"versionEndIncluding": "0.22.1",
"versionStartExclud... | [
"787"
] | 787 | https://github.com/Juniper/libslax/issues/51 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Juniper",
"libslax"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), slaxproc (latest master [45d88a](https://github.com/Juniper/libslax/commit/45d88a103c315519cd7e3566eec10dceb4ce9bdc))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./build/slaxproc/slaxproc -o ... | A heap-buffer-overflow in slaxlexer.c:986:11 | https://api.github.com/repos/Juniper/libslax/issues/51/comments | 1 | 2020-08-02T14:04:56Z | 2025-01-02T05:25:35Z | https://github.com/Juniper/libslax/issues/51 | 671,622,400 | 51 | 2,553 |
CVE-2021-39534 | 2021-09-20T16:15:12.347 | An issue was discovered in libslax through v0.22.1. slaxIsCommentStart() in slaxlexer.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Juniper/libslax/issues/52"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:juniper:libslax:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6D5523A4-6902-49B4-BD77-FD58DFA71EA1",
"versionEndExcluding": null,
"versionEndIncluding": "0.22.1",
"versionStartExclud... | [
"787"
] | 787 | https://github.com/Juniper/libslax/issues/52 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Juniper",
"libslax"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), slaxproc (latest master [45d88a](https://github.com/Juniper/libslax/commit/45d88a103c315519cd7e3566eec10dceb4ce9bdc))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure
## Command line
./build/slaxproc/slaxproc -o ... | A heap-buffer-overflow in slaxlexer.c:751:13 | https://api.github.com/repos/Juniper/libslax/issues/52/comments | 1 | 2020-08-02T14:07:30Z | 2025-01-02T05:24:31Z | https://github.com/Juniper/libslax/issues/52 | 671,622,806 | 52 | 2,554 |
CVE-2021-39544 | 2021-09-20T16:15:12.787 | An issue was discovered in sela through 20200412. file::WavFile::writeToFile() in wav_file.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"787"
] | 787 | https://github.com/sahaRatul/sela/issues/25 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | A heap-buffer-overflow in wav_file.cpp:262:32 | https://api.github.com/repos/sahaRatul/sela/issues/25/comments | 0 | 2020-08-14T04:52:18Z | 2020-08-14T04:52:18Z | https://github.com/sahaRatul/sela/issues/25 | 678,895,603 | 25 | 2,555 |
CVE-2021-39545 | 2021-09-20T16:15:12.827 | An issue was discovered in sela through 20200412. A NULL pointer dereference exists in the function rice::RiceDecoder::process() located in rice_decoder.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"476"
] | 476 | https://github.com/sahaRatul/sela/issues/31 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | Segmentation fault in rice_decoder.cpp:58:5 | https://api.github.com/repos/sahaRatul/sela/issues/31/comments | 0 | 2020-08-14T05:04:52Z | 2020-08-14T05:04:52Z | https://github.com/sahaRatul/sela/issues/31 | 678,900,221 | 31 | 2,556 |
CVE-2021-39546 | 2021-09-20T16:15:12.873 | An issue was discovered in sela through 20200412. rice::RiceDecoder::process() in rice_decoder.cpp has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"787"
] | 787 | https://github.com/sahaRatul/sela/issues/29 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | A heap-buffer-overflow in rice_decoder.cpp:39 | https://api.github.com/repos/sahaRatul/sela/issues/29/comments | 0 | 2020-08-14T05:00:32Z | 2020-08-14T05:00:32Z | https://github.com/sahaRatul/sela/issues/29 | 678,898,461 | 29 | 2,557 |
CVE-2021-39547 | 2021-09-20T16:15:12.917 | An issue was discovered in sela through 20200412. A NULL pointer dereference exists in the function lpc::SampleGenerator::process() located in sample_generator.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"476"
] | 476 | https://github.com/sahaRatul/sela/issues/32 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | Segmentation fault in sample_generator.cpp:15:18 | https://api.github.com/repos/sahaRatul/sela/issues/32/comments | 0 | 2020-08-14T05:06:36Z | 2020-08-14T05:06:36Z | https://github.com/sahaRatul/sela/issues/32 | 678,900,888 | 32 | 2,558 |
CVE-2021-39548 | 2021-09-20T16:15:12.963 | An issue was discovered in sela through 20200412. A NULL pointer dereference exists in the function frame::FrameDecoder::process() located in frame_decoder.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"476"
] | 476 | https://github.com/sahaRatul/sela/issues/28 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | Segmentation fault in frame_decoder.cpp:65:35 | https://api.github.com/repos/sahaRatul/sela/issues/28/comments | 0 | 2020-08-14T04:58:45Z | 2020-08-14T04:58:45Z | https://github.com/sahaRatul/sela/issues/28 | 678,897,858 | 28 | 2,559 |
CVE-2021-39549 | 2021-09-20T16:15:13.007 | An issue was discovered in sela through 20200412. A NULL pointer dereference exists in the function file::WavFile::WavFile() located in wav_file.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"476"
] | 476 | https://github.com/sahaRatul/sela/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | Segmentation fault in wav_file.cpp:13:46 | https://api.github.com/repos/sahaRatul/sela/issues/27/comments | 0 | 2020-08-14T04:56:57Z | 2020-08-14T04:56:57Z | https://github.com/sahaRatul/sela/issues/27 | 678,897,262 | 27 | 2,560 |
CVE-2021-39550 | 2021-09-20T16:15:13.057 | An issue was discovered in sela through 20200412. file::SelaFile::readFromFile() in sela_file.cpp has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/30"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"787"
] | 787 | https://github.com/sahaRatul/sela/issues/30 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | A heap-buffer-overflow in sela_file.cpp:90:53 | https://api.github.com/repos/sahaRatul/sela/issues/30/comments | 0 | 2020-08-14T05:02:24Z | 2020-08-14T05:02:24Z | https://github.com/sahaRatul/sela/issues/30 | 678,899,213 | 30 | 2,561 |
CVE-2021-39551 | 2021-09-20T16:15:13.103 | An issue was discovered in sela through 20200412. file::SelaFile::readFromFile() in sela_file.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"787"
] | 787 | https://github.com/sahaRatul/sela/issues/26 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | A heap-buffer-overflow in sela_file.cpp:78:67 | https://api.github.com/repos/sahaRatul/sela/issues/26/comments | 0 | 2020-08-14T04:54:33Z | 2020-08-14T04:54:33Z | https://github.com/sahaRatul/sela/issues/26 | 678,896,429 | 26 | 2,562 |
CVE-2021-39552 | 2021-09-20T16:15:13.143 | An issue was discovered in sela through 20200412. file::WavFile::readFromFile() in wav_file.c has a heap-based buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sahaRatul/sela/issues/23"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sela_project:sela:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9EFCB451-9AB9-4111-B4C8-3F9283520F9C",
"versionEndExcluding": null,
"versionEndIncluding": "2020-04-12",
"versionStart... | [
"787"
] | 787 | https://github.com/sahaRatul/sela/issues/23 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sahaRatul",
"sela"
] | ## System info
Ubuntu x86_64, clang 6.0, sela (latest master [ca09cb](https://github.com/sahaRatul/sela/commit/ca09cbd80bd6084bca08288d980c7f6928571bbb))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE... | A heap-buffer-overflow in wav_file.cpp:160:40 | https://api.github.com/repos/sahaRatul/sela/issues/23/comments | 0 | 2020-08-14T02:49:47Z | 2020-08-14T04:50:32Z | https://github.com/sahaRatul/sela/issues/23 | 678,857,762 | 23 | 2,563 |
CVE-2021-39553 | 2021-09-20T16:15:13.187 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function grealloc() located in gmem.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Technical Description"
],
"url": "https://github.com/matthiaskramm/swftools/issues/103"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/103 | [
"Exploit",
"Issue Tracking",
"Technical Description"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./stack-overflow-grealloc-gmem-156
## Output
```
Error: PDF file is damaged -... | A Segmentation fault in xpdf/gmem.cc:156 | https://api.github.com/repos/swftools/swftools/issues/103/comments | 0 | 2020-08-01T06:55:27Z | 2020-08-01T06:55:27Z | https://github.com/swftools/swftools/issues/103 | 670,596,306 | 103 | 2,564 |
CVE-2021-39554 | 2021-09-20T16:15:13.227 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function Lexer::Lexer() located in Lexer.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/100"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/100 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./stack-overflow-Lexer-Lexer-53
## Output
```
Segmentation fault (core dumped... | A Segmentation fault in xpdf/Lexer.cc:53 | https://api.github.com/repos/swftools/swftools/issues/100/comments | 0 | 2020-08-01T02:16:31Z | 2020-08-01T02:16:31Z | https://github.com/swftools/swftools/issues/100 | 670,435,303 | 100 | 2,565 |
CVE-2021-39555 | 2021-09-20T16:15:13.270 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function InfoOutputDev::type3D0() located in InfoOutputDev.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/99"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/99 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./SEGV-type3D0-InfoOutputDev-880
## Output
```
Segmentation fault (core dumpe... | A Segmentation fault in InfoOutputDev.cc:880 | https://api.github.com/repos/swftools/swftools/issues/99/comments | 0 | 2020-08-01T02:10:19Z | 2020-08-01T02:10:19Z | https://github.com/swftools/swftools/issues/99 | 670,432,001 | 99 | 2,566 |
CVE-2021-39556 | 2021-09-20T16:15:13.313 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function InfoOutputDev::type3D1() located in InfoOutputDev.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/105"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/105 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./SEGV-type3D1-InfoOutputDev-887
## Output
```
Segmentation fault (core dumpe... | A Segmentation fault in InfoOutputDev.cc:887 | https://api.github.com/repos/swftools/swftools/issues/105/comments | 0 | 2020-08-01T07:01:24Z | 2020-08-01T07:01:24Z | https://github.com/swftools/swftools/issues/105 | 670,599,501 | 105 | 2,567 |
CVE-2021-39557 | 2021-09-20T16:15:13.357 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function copyString() located in gmem.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/97"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/97 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./stack-overflow-gmalloc-gmem-101
## Output
```
Segmentation fault (core dump... | Segmentation fault error in xpdf/gmem.cc:101 | https://api.github.com/repos/swftools/swftools/issues/97/comments | 0 | 2020-07-31T14:00:06Z | 2020-08-01T02:37:17Z | https://github.com/swftools/swftools/issues/97 | 669,847,515 | 97 | 2,568 |
CVE-2021-39558 | 2021-09-20T16:15:13.397 | An issue was discovered in swftools through 20200710. A stack-buffer-overflow exists in the function VectorGraphicOutputDev::drawGeneralImage() located in VectorGraphicOutputDev.cc. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/106"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/106 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./stack-overflow-drawGeneralImage-VectorGraphicOutputDev-1158
## AddressSanitizer... | A stack-buffer-overflow in VectorGraphicOutputDev.cc:1158 | https://api.github.com/repos/swftools/swftools/issues/106/comments | 0 | 2020-08-02T03:17:40Z | 2020-08-02T03:17:40Z | https://github.com/swftools/swftools/issues/106 | 671,446,394 | 106 | 2,569 |
CVE-2021-39559 | 2021-09-20T16:15:13.440 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function GString::~GString() located in GString.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/101"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/101 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./SEGV-GString-GString-173
## AddressSanitizer output
```
Error: Type 4 funct... | A SEGV in xpdf/GString.cc:173 | https://api.github.com/repos/swftools/swftools/issues/101/comments | 0 | 2020-08-01T02:18:46Z | 2020-08-01T02:18:46Z | https://github.com/swftools/swftools/issues/101 | 670,436,539 | 101 | 2,570 |
CVE-2021-39561 | 2021-09-20T16:15:13.480 | An issue was discovered in swftools through 20200710. A stack-buffer-overflow exists in the function Gfx::opSetFillColorN() located in Gfx.cc. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/102"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/102 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null
## AddressSanitizer output
```
Error (492): Unknown operator 'P0'
==========... | A stack overflow in xpdf/Gfx.cc:1258 | https://api.github.com/repos/swftools/swftools/issues/102/comments | 0 | 2020-08-01T02:31:55Z | 2020-08-01T02:31:55Z | https://github.com/swftools/swftools/issues/102 | 670,444,172 | 102 | 2,571 |
CVE-2021-39562 | 2021-09-20T16:15:13.527 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function FileStream::makeSubStream() located in Stream.cc. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/98"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/98 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), pdf2swf (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./pdf2swf -qq -z -o /dev/null ./stack-overflow-Stream-598
## Output
```
Segmentation fault (core dumped)
`... | A Segmentation fault in xpdf/Stream.cc:598 | https://api.github.com/repos/swftools/swftools/issues/98/comments | 0 | 2020-08-01T02:04:36Z | 2020-08-01T02:06:51Z | https://github.com/swftools/swftools/issues/98 | 670,428,844 | 98 | 2,572 |
CVE-2021-39563 | 2021-09-20T16:15:13.567 | An issue was discovered in swftools through 20200710. A NULL pointer dereference exists in the function swf_DumpActions() located in swfaction.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/115"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"476"
] | 476 | https://github.com/matthiaskramm/swftools/issues/115 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## Output
```
Segmentation fault (core dumped)
```
## AddressSanitizer output
```
ASAN:SIGSEGV
... | A Segmentation fault in swfaction.c:483 | https://api.github.com/repos/swftools/swftools/issues/115/comments | 0 | 2020-08-05T07:02:23Z | 2020-08-05T07:09:34Z | https://github.com/swftools/swftools/issues/115 | 673,305,336 | 115 | 2,573 |
CVE-2021-39564 | 2021-09-20T16:15:13.607 | An issue was discovered in swftools through 20200710. A heap-buffer-overflow exists in the function swf_DumpActions() located in swfaction.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/116"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/116 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## AddressSanitizer output
```
=================================================================
==114... | A heap-buffer-overflow in swfaction.c:398 | https://api.github.com/repos/swftools/swftools/issues/116/comments | 0 | 2020-08-05T07:06:56Z | 2020-08-05T07:09:11Z | https://github.com/swftools/swftools/issues/116 | 673,307,783 | 116 | 2,574 |
CVE-2021-39569 | 2021-09-20T16:15:13.650 | An issue was discovered in swftools through 20200710. A heap-buffer-overflow exists in the function OpAdvance() located in swfaction.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/114"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/114 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## AddressSanitizer output
```
=================================================================
==201... | A heap-buffer-overflow in swfaction.c:254 | https://api.github.com/repos/swftools/swftools/issues/114/comments | 0 | 2020-08-05T06:59:30Z | 2020-08-05T07:09:59Z | https://github.com/swftools/swftools/issues/114 | 673,303,749 | 114 | 2,575 |
CVE-2021-39574 | 2021-09-20T16:15:13.693 | An issue was discovered in swftools through 20200710. A heap-buffer-overflow exists in the function pool_read() located in pool.c. It allows an attacker to cause code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/124"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "192BB2B1-5CB5-4E87-AAB7-51ACC07D8934",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-10",
"versionStart... | [
"787"
] | 787 | https://github.com/matthiaskramm/swftools/issues/124 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"matthiaskramm",
"swftools"
] | ## System info
Ubuntu x86_64, clang 6.0, swfdump (latest master [fad6c2](https://github.com/matthiaskramm/swftools/commit/fad6c2e7505efa62e68375d061a508f802c3e77c))
## Command line
./src/swfdump -D @@
## AddressSanitizer output
```
/home/seviezhou/swftools/lib/rfxswf.c:520
#1 0x55e4357ac829 in pool... | A heap-buffer-overflow in rfxswf.c:520 | https://api.github.com/repos/swftools/swftools/issues/124/comments | 0 | 2020-08-05T07:40:08Z | 2020-08-05T07:40:08Z | https://github.com/swftools/swftools/issues/124 | 673,326,905 | 124 | 2,576 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.