cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-35490 | 2020-12-17T19:15:14.417 | FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.PerUserPoolDataSource. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Technical Description",
"Third Party Advisory"
],
"url": "https://cowtowncoder.medium.com/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "49F38029-9D32-499B-B5D4-C4FFDD9B1728",
"versionEndExcluding": "2.9.10.8",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2986 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `org.apache.commons:commons-dbcp2`. library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): Al1ex@knownsec
Mitre ids:
* CVE-2020-35490
* ... | Block 2 more gadget types (commons-dbcp2, CVE-2020-35490/CVE-2020-35491) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2986/comments | 0 | 2020-12-14T21:48:07Z | 2021-06-22T04:04:11Z | https://github.com/FasterXML/jackson-databind/issues/2986 | 766,957,739 | 2,986 | 1,567 |
CVE-2020-35545 | 2020-12-17T20:15:14.027 | Time-based SQL injection exists in Spotweb 1.4.9 via the query string. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/spotweb/spotweb/issues/629"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/spotweb/spotweb/issues/629"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:spotweb_project:spotweb:1.4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "F2CE0FCC-C8CF-4C39-A8D7-C0799862E585",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/spotweb/spotweb/issues/629 | [
"Third Party Advisory"
] | github.com | [
"spotweb",
"spotweb"
] | Hi there,
I was using your web application and noticed that it's vulnerable to SQL injection attack. any unauthenticated user can send malicious payload on the query string and trigger a time-based SQL injection attack to the underling database service.
you can test it by sending the following HTTP request and no... | Security issue | https://api.github.com/repos/spotweb/spotweb/issues/629/comments | 2 | 2020-12-17T09:48:10Z | 2020-12-20T14:47:02Z | https://github.com/spotweb/spotweb/issues/629 | 769,784,585 | 629 | 1,568 |
CVE-2020-26284 | 2020-12-21T23:15:12.157 | Hugo is a fast and Flexible Static Site Generator built in Go. Hugo depends on Go's `os/exec` for certain features, e.g. for rendering of Pandoc documents if these binaries are found in the system `%PATH%` on Windows. In Hugo before version 0.79.1, if a malicious file with the same name (`exe` or `bat`) is found in the... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 8.5,
"confidentialityImpact": "COM... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gohugoio/hugo/security/advisories/GHSA-8j34-9876-pvfq"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Patch",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gohugo:hugo:*:*:*:*:*:windows:*:*",
"matchCriteriaId": "E9F3B098-63C6-44CD-A08B-876C6CBC8BDF",
"versionEndExcluding": "0.79.1",
"versionEndIncluding": null,
"versionStartExcl... | [
"78"
] | 78 | https://github.com/golang/go/issues/38736 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | <!--
Please answer these questions before submitting your issue. Thanks!
For questions please use one of our forums: https://github.com/golang/go/wiki/Questions
-->
### What version of Go are you using (`go version`)?
<pre>
$ go version
go version go1.14.1 windows/amd64
</pre>
Originally noticed with Go 1.... | proposal: os/exec: make LookPath not look in dot implicitly on Windows | https://api.github.com/repos/golang/go/issues/38736/comments | 31 | 2020-04-29T00:09:12Z | 2022-07-08T14:09:14Z | https://github.com/golang/go/issues/38736 | 608,691,699 | 38,736 | 1,569 |
CVE-2018-15632 | 2020-12-22T17:15:12.487 | Improper input validation in database creation logic in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier, allows remote attackers to initialize an empty database on which they can connect with default credentials. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 8.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63700"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "D9126A1A-FA35-4127-91B3-A3FA8B26FABB",
"versionEndExcluding": null,
"versionEndIncluding": "11.0",
"versionStartExclud... | [
"20"
] | 20 | https://github.com/odoo/odoo/issues/63700 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2018-15632
**Affects**: Odoo 11.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2018-15632](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15632)
**Component**: Framework
**Credits**: P. Valov (SoCyber)
Improper input validation in database creation logic in Odoo ... | [SEC] CVE-2018-15632 - Affects: Odoo 11.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63700/comments | 0 | 2020-12-22T15:30:55Z | 2020-12-22T15:30:57Z | https://github.com/odoo/odoo/issues/63700 | 773,033,276 | 63,700 | 1,570 |
CVE-2018-15633 | 2020-12-22T17:15:12.690 | Cross-site scripting (XSS) issue in "document" module in Odoo Community 11.0 and earlier and Odoo Enterprise 11.0 and earlier, allows remote attackers to inject arbitrary web script in the browser of a victim via crafted attachment filenames. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63701"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "D9126A1A-FA35-4127-91B3-A3FA8B26FABB",
"versionEndExcluding": null,
"versionEndIncluding": "11.0",
"versionStartExclud... | [
"79"
] | 79 | https://github.com/odoo/odoo/issues/63701 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2018-15633
**Affects**: Odoo 11.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2018-15633](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15633)
**Component**: "document" module
**Credits**: Nathanael ROTA (Capgemini), Lauri Vakkala (Silverskin),
Tomas Ca... | [SEC] CVE-2018-15633 - Affects: Odoo 11.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63701/comments | 0 | 2020-12-22T15:30:57Z | 2020-12-22T15:30:59Z | https://github.com/odoo/odoo/issues/63701 | 773,033,314 | 63,701 | 1,571 |
CVE-2018-15634 | 2020-12-22T17:15:12.783 | Cross-site scripting (XSS) issue in attachment management in Odoo Community 14.0 and earlier and Odoo Enterprise 14.0 and earlier, allows remote attackers to inject arbitrary web script in the browser of a victim via a crafted link. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63702"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "2DBCA075-326A-4F0F-89B9-1437744D0FFC",
"versionEndExcluding": null,
"versionEndIncluding": "14.0",
"versionStartExclud... | [
"79"
] | 79 | https://github.com/odoo/odoo/issues/63702 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2018-15634
**Affects**: Odoo 14.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2018-15634](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15634)
**Component**: Framework
**Credits**: Nathanael ROTA (Capgemini) and Alessandro Innocenti
Cross-site scripting (XSS) i... | [SEC] CVE-2018-15634 - Affects: Odoo 14.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63702/comments | 0 | 2020-12-22T15:30:59Z | 2020-12-22T15:31:01Z | https://github.com/odoo/odoo/issues/63702 | 773,033,341 | 63,702 | 1,572 |
CVE-2018-15638 | 2020-12-22T17:15:12.847 | Cross-site scripting (XSS) issue in mail module in Odoo Community 13.0 and earlier and Odoo Enterprise 13.0 and earlier, allows remote attackers to inject arbitrary web script in the browser of a victim via crafted channel names. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63703"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "97EB1578-CFCC-4301-AEE7-DBBC6A92BC25",
"versionEndExcluding": null,
"versionEndIncluding": "13.0",
"versionStartExclud... | [
"79"
] | 79 | https://github.com/odoo/odoo/issues/63703 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2018-15638
**Affects**: Odoo 13.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2018-15638](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15638)
**Component**: Discuss
**Credits**: Subash SN and Bharath Kumar (Appsecco), Dipanshu Agrawal
Cross-site scripting (XSS... | [SEC] CVE-2018-15638 - Affects: Odoo 13.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63703/comments | 0 | 2020-12-22T15:31:01Z | 2020-12-22T15:31:03Z | https://github.com/odoo/odoo/issues/63703 | 773,033,360 | 63,703 | 1,573 |
CVE-2018-15641 | 2020-12-22T17:15:12.940 | Cross-site scripting (XSS) issue in web module in Odoo Community 11.0 through 14.0 and Odoo Enterprise 11.0 through 14.0, allows remote authenticated internal users to inject arbitrary web script in the browser of a victim via crafted calendar event attributes. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63704"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "4ED3084D-DF4C-486F-A161-ADCC24FF61F4",
"versionEndExcluding": null,
"versionEndIncluding": "14.0",
"versionStartExclud... | [
"79"
] | 79 | https://github.com/odoo/odoo/issues/63704 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2018-15641
**Affects**: Odoo 11.0 through 14.0 (Community and Enterprise Editions)
**CVE ID**: [CVE-2018-15641](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15641)
**Component**: Framework
**Credits**: msg systems ag, Lauri Vakkala (Silverskin),
Bharath Kumar (Appsecco), A... | [SEC] CVE-2018-15641 - Affects: Odoo 11.0 through 14.0 (Community a... | https://api.github.com/repos/odoo/odoo/issues/63704/comments | 0 | 2020-12-22T15:31:04Z | 2020-12-22T15:31:05Z | https://github.com/odoo/odoo/issues/63704 | 773,033,386 | 63,704 | 1,574 |
CVE-2018-15645 | 2020-12-22T17:15:13.033 | Improper access control in message routing in Odoo Community 12.0 and earlier and Odoo Enterprise 12.0 and earlier allows remote authenticated users to create arbitrary records via crafted payloads, which may allow privilege escalation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63705"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "A958BCBB-C656-44A5-A9A9-66A66AEA67A0",
"versionEndExcluding": null,
"versionEndIncluding": "12.0",
"versionStartExclud... | [
"732"
] | 732 | https://github.com/odoo/odoo/issues/63705 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2018-15645
**Affects**: Odoo 12.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2018-15645](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15645)
**Component**: Discuss
**Credits**: Nils Hamerlinck (Trobz)
Improper access control in message routing in Odoo Communi... | [SEC] CVE-2018-15645 - Affects: Odoo 12.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63705/comments | 0 | 2020-12-22T15:31:05Z | 2020-12-22T15:31:07Z | https://github.com/odoo/odoo/issues/63705 | 773,033,411 | 63,705 | 1,575 |
CVE-2019-11781 | 2020-12-22T17:15:13.127 | Improper input validation in portal component in Odoo Community 12.0 and earlier and Odoo Enterprise 12.0 and earlier, allows remote attackers to trick victims into modifying their account via crafted links, leading to privilege escalation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "security@odoo.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63706"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63706"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "A958BCBB-C656-44A5-A9A9-66A66AEA67A0",
"versionEndExcluding": null,
"versionEndIncluding": "12.0",
"versionStartExclud... | [
"20"
] | 20 | https://github.com/odoo/odoo/issues/63706 | [
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2019-11781
**Affects**: Odoo 12.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2019-11781](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11781)
**Component**: Portal
**Credits**: "[iamsushi](https://github.com/sushiwushi)"
Improper input validation in por... | [SEC] CVE-2019-11781 - Affects: Odoo 12.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63706/comments | 0 | 2020-12-22T15:31:07Z | 2021-02-05T12:25:28Z | https://github.com/odoo/odoo/issues/63706 | 773,033,435 | 63,706 | 1,576 |
CVE-2019-11782 | 2020-12-22T17:15:13.190 | Improper access control in Odoo Community 14.0 and earlier and Odoo Enterprise 14.0 and earlier, allows remote authenticated users with access to contact management to modify user accounts, leading to privilege escalation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63707"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63707"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "2DBCA075-326A-4F0F-89B9-1437744D0FFC",
"versionEndExcluding": null,
"versionEndIncluding": "14.0",
"versionStartExclud... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/63707 | [
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2019-11782
**Affects**: Odoo 14.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2019-11782](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11782)
**Component**: Portal
**Credits**: Damien LESCOS
Improper access control in Odoo Community 14.0 and earlier and Odoo E... | [SEC] CVE-2019-11782 - Affects: Odoo 14.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63707/comments | 0 | 2020-12-22T15:31:09Z | 2020-12-22T15:31:10Z | https://github.com/odoo/odoo/issues/63707 | 773,033,453 | 63,707 | 1,577 |
CVE-2019-11783 | 2020-12-22T17:15:13.267 | Improper access control in mail module (channel partners) in Odoo Community 14.0 and earlier and Odoo Enterprise 14.0 and earlier, allows remote authenticated users to subscribe to arbitrary mail channels uninvited. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security@odoo.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63708"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63708"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "2DBCA075-326A-4F0F-89B9-1437744D0FFC",
"versionEndExcluding": null,
"versionEndIncluding": "14.0",
"versionStartExclud... | [
"862"
] | 862 | https://github.com/odoo/odoo/issues/63708 | [
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2019-11783
**Affects**: Odoo 14.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2019-11783](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11783)
**Component**: Discuss
**Credits**: Nils Hamerlinck (Trobz), Christopher Riis Bubeck Eriksen,
Alexandre Diaz, ... | [SEC] CVE-2019-11783 - Affects: Odoo 14.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63708/comments | 0 | 2020-12-22T15:31:11Z | 2020-12-22T15:31:12Z | https://github.com/odoo/odoo/issues/63708 | 773,033,474 | 63,708 | 1,578 |
CVE-2019-11784 | 2020-12-22T17:15:13.330 | Improper access control in mail module (notifications) in Odoo Community 14.0 and earlier and Odoo Enterprise 14.0 and earlier, allows remote authenticated users to obtain access to arbitrary messages in conversations they were not a party to. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security@odoo.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63709"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63709"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "2DBCA075-326A-4F0F-89B9-1437744D0FFC",
"versionEndExcluding": null,
"versionEndIncluding": "14.0",
"versionStartExclud... | [
"862"
] | 862 | https://github.com/odoo/odoo/issues/63709 | [
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2019-11784
**Affects**: Odoo 14.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2019-11784](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11784)
**Component**: Discuss
Improper access control in mail module (notifications) in Odoo Community
14.0 and earlier and O... | [SEC] CVE-2019-11784 - Affects: Odoo 14.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63709/comments | 0 | 2020-12-22T15:31:12Z | 2020-12-22T15:31:13Z | https://github.com/odoo/odoo/issues/63709 | 773,033,497 | 63,709 | 1,579 |
CVE-2019-11785 | 2020-12-22T17:15:13.393 | Improper access control in mail module (followers) in Odoo Community 13.0 and earlier and Odoo Enterprise 13.0 and earlier, allows remote authenticated users to obtain access to messages posted on business records there were not given access to, and subscribe to receive future messages. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security@odoo.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63710"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63710"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "97EB1578-CFCC-4301-AEE7-DBBC6A92BC25",
"versionEndExcluding": null,
"versionEndIncluding": "13.0",
"versionStartExclud... | [
"862"
] | 862 | https://github.com/odoo/odoo/issues/63710 | [
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2019-11785
**Affects**: Odoo 13.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2019-11785](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11785)
**Component**: Discuss
**Credits**: Nils Hamerlinck (Trobz)
Improper access control in mail module (followers) in Odoo... | [SEC] CVE-2019-11785 - Affects: Odoo 13.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63710/comments | 0 | 2020-12-22T15:31:14Z | 2020-12-22T15:31:16Z | https://github.com/odoo/odoo/issues/63710 | 773,033,517 | 63,710 | 1,580 |
CVE-2019-11786 | 2020-12-22T17:15:13.457 | Improper access control in Odoo Community 13.0 and earlier and Odoo Enterprise 13.0 and earlier, allows remote authenticated users to modify translated terms, which may lead to arbitrary content modification on translatable elements. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "security@odoo.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63711"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63711"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "97EB1578-CFCC-4301-AEE7-DBBC6A92BC25",
"versionEndExcluding": null,
"versionEndIncluding": "13.0",
"versionStartExclud... | [
"284"
] | 284 | https://github.com/odoo/odoo/issues/63711 | [
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2019-11786
**Affects**: Odoo 13.0 and earlier (Community and Enterprise Editions)
**CVE ID**: [CVE-2019-11786](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11786)
**Component**: Core
**Credits**: Martin Trigaux, Alexandre Diaz
Improper access control in Odoo Community 13.0 and ear... | [SEC] CVE-2019-11786 - Affects: Odoo 13.0 and earlier (Community an... | https://api.github.com/repos/odoo/odoo/issues/63711/comments | 0 | 2020-12-22T15:31:16Z | 2020-12-22T15:31:18Z | https://github.com/odoo/odoo/issues/63711 | 773,033,547 | 63,711 | 1,581 |
CVE-2020-29396 | 2020-12-22T17:15:13.550 | A sandboxing issue in Odoo Community 11.0 through 13.0 and Odoo Enterprise 11.0 through 13.0, when running with Python 3.6 or later, allows remote authenticated users to execute arbitrary code, leading to privilege escalation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/odoo/odoo/issues/63712"
},
{
"source": "security@odoo.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://www.oracle.com/security-alerts... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:odoo:odoo:*:*:*:*:community:*:*:*",
"matchCriteriaId": "C1269963-1DD6-4B28-A33F-B8C2F69AEF4C",
"versionEndExcluding": null,
"versionEndIncluding": "13.0",
"versionStartExclud... | [
"267"
] | 267 | https://github.com/odoo/odoo/issues/63712 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"odoo",
"odoo"
] | # Security Advisory - CVE-2020-29396
**Affects**: Odoo 11.0 through 13.0 (Community and Enterprise Editions)
**CVE ID**: [CVE-2020-29396](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29396)
**Component**: Core
**Credits**: Toufik Ben Jaa, Stéphane Debauche, Benoît FONTAINE
A sandboxing issue in Odoo Commun... | [SEC] CVE-2020-29396 - Affects: Odoo 11.0 through 14.0 (Community a... | https://api.github.com/repos/odoo/odoo/issues/63712/comments | 0 | 2020-12-22T15:31:19Z | 2020-12-22T15:31:20Z | https://github.com/odoo/odoo/issues/63712 | 773,033,581 | 63,712 | 1,582 |
CVE-2020-35666 | 2020-12-23T20:15:12.927 | Steedos Platform through 1.21.24 allows NoSQL injection because the /api/collection/findone implementation in server/packages/steedos_base.js mishandles req.body validation, as demonstrated by MongoDB operator attacks such as an X-User-Id[$ne]=1 value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/steedos/steedos-platform/issues/1245"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:steedos:steedos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "74A7D344-88BB-463F-A267-480CE9237176",
"versionEndExcluding": null,
"versionEndIncluding": "1.21.24",
"versionStartExclu... | [
"89"
] | 89 | https://github.com/steedos/steedos-platform/issues/1245 | [
"Exploit",
"Vendor Advisory"
] | github.com | [
"steedos",
"steedos-platform"
] | 接口对mongodb nosql操作验证不严,可能导致nosql注入。详细可参考
https://owasp.org/www-pdf-archive/GOD16-NOSQL.pdf
大多数接口存在鉴权所以未登录无法利用,这里仅仅举一个例子
**漏洞产生原因**
例如在 server/packages/steedos_base.js 中,存在如下代码:
```
JsonRoutes.add("post", "/api/collection/findone", function (req, res, next) {
...
if (req.body) {
userId = req.b... | Mongodb NoSQL 注入问题 | https://api.github.com/repos/steedos/steedos-platform/issues/1245/comments | 2 | 2020-12-22T02:37:45Z | 2021-01-14T06:40:21Z | https://github.com/steedos/steedos-platform/issues/1245 | 772,591,577 | 1,245 | 1,583 |
CVE-2020-35668 | 2020-12-23T23:15:12.270 | RedisGraph 2.x through 2.2.11 has a NULL Pointer Dereference that leads to a server crash because it mishandles an unquoted string, such as an alias that has not yet been introduced. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/RedisGraph/RedisGraph/issues/1502"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/RedisGraph/Red... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redislabs:redisgraph:*:*:*:*:*:*:*:*",
"matchCriteriaId": "038A8817-60E1-4367-90B6-C7EDEE21DD70",
"versionEndExcluding": "2.2.11",
"versionEndIncluding": null,
"versionStartE... | [
"476"
] | 476 | https://github.com/RedisGraph/RedisGraph/issues/1502 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"RedisGraph",
"RedisGraph"
] | ## Bug impact
Redis Graph crashes and server downs
## Bug explained
It's appear that Redis Graph doesn't processes well list of unknown data types. Typing this in the CLI, server crashes:
```
> GRAPH.QUERY "myGraph" "CYPHER A=[a]"
```
It also crashes with any invalid values in `A`.
## Redis Bug rep... | DoS (Denial Of Service) Bug | https://api.github.com/repos/RedisGraph/RedisGraph/issues/1502/comments | 4 | 2020-12-21T14:41:21Z | 2021-01-04T09:42:01Z | https://github.com/RedisGraph/RedisGraph/issues/1502 | 772,219,124 | 1,502 | 1,584 |
CVE-2020-35669 | 2020-12-24T03:15:12.530 | An issue was discovered in the http package through 0.12.2 for Dart. If the attacker controls the HTTP method and the app is using Request directly, it's possible to achieve CRLF injection in an HTTP request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/dart-lang/http/blob/master/CHANGELOG.md#0133"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dart:http:*:*:*:*:*:dart:*:*",
"matchCriteriaId": "16C1D167-1153-490E-B0EA-015D9D8CFB9F",
"versionEndExcluding": null,
"versionEndIncluding": "0.12.2",
"versionStartExcluding... | [
"74"
] | 74 | https://github.com/dart-lang/http/issues/511 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"dart-lang",
"http"
] | I believe there is a security issue with the current implementation of `Request`.
The full example can be found [here](https://github.com/n0npax/dart-test-http)
## What's wrong:
`Request` is passing method verb as is to the stream without any kind of validation.
basically:
```dart
var r = Request(
"G... | Header injection and path forgery [security issue] | https://api.github.com/repos/dart-lang/http/issues/511/comments | 1 | 2020-12-23T11:07:32Z | 2021-04-30T00:50:56Z | https://github.com/dart-lang/http/issues/511 | 773,674,973 | 511 | 1,585 |
CVE-2020-28169 | 2020-12-24T15:15:12.950 | The td-agent-builder plugin before 2020-12-18 for Fluentd allows attackers to gain privileges because the bin directory is writable by a user account, but a file in bin is executed as NT AUTHORITY\SYSTEM. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 6.9,
"confidentialityImpact": "COMPL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/160791/Fluentd-TD-agent-4.0.1-Insecure-Folder-Permission.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Vendor ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:td-agent-builder_project:td-agent-builder:*:*:*:*:*:fluentd:*:*",
"matchCriteriaId": "C502E5D4-3955-4C31-97EB-602E13683A50",
"versionEndExcluding": "2020-12-18",
"versionEndIncluding": n... | [
"732"
] | 732 | https://github.com/fluent/fluentd/issues/3201 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fluent",
"fluentd"
] |
[POC.docx](https://github.com/fluent/fluentd/files/5680500/POC.docx)
**Describe the bug**
Inappropriate folder permissions, possible escalation of privileges' on Windows
**To Reproduce**
Download URL:
http://packages.treasuredata.com.s3.amazonaws.com/4/windows/td-agent-4.0.1-x64.msi
Vulnerable Path:
C:\opt\t... | Possible Vulnerability | https://api.github.com/repos/fluent/fluentd/issues/3201/comments | 7 | 2020-12-11T16:55:44Z | 2021-03-18T04:30:48Z | https://github.com/fluent/fluentd/issues/3201 | 762,621,950 | 3,201 | 1,586 |
CVE-2020-35709 | 2020-12-25T19:15:13.130 | bloofoxCMS 0.5.2.1 allows admins to upload arbitrary .php files (with "Content-Type: application/octet-stream") to ../media/images/ via the admin/index.php?mode=tools&page=upload URI, aka directory traversal. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alexlang24/bloofoxCMS/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bloofox:bloofoxcms:0.5.2.1:*:*:*:*:*:*:*",
"matchCriteriaId": "C12BED64-DA1B-4FB8-A196-B414759D79C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"22"
] | 22 | https://github.com/alexlang24/bloofoxCMS/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alexlang24",
"bloofoxCMS"
] | I want to report an arbitrary file upload vulnerability that I found in bloofoxcms 0.5.2.1, through which we can upload webshell and control the web server.
After entering the web management background, we can use the upload function to upload files:

Crash reason : Access violation (invalid address 0x41107f92=????????)
Crashed thread : ntdll_77570000!RtlpFreeHeap+0x2a2
-------------------------------------------------------------------------------------------
0:000> g
WARNING: Continuing a non-continuable exception
(4868.6e3c):... | StepMania 5.0.12 crash report | https://api.github.com/repos/stepmania/stepmania/issues/1890/comments | 6 | 2019-09-10T06:39:53Z | 2020-12-28T14:26:28Z | https://github.com/stepmania/stepmania/issues/1890 | 491,480,189 | 1,890 | 1,588 |
CVE-2020-35284 | 2020-12-26T06:15:12.537 | Flamingo (aka FlamingoIM) through 2020-09-29 allows ../ directory traversal because the only ostensibly unpredictable part of a file-transfer request is an MD5 computation; however, this computation occurs on the client side, and the computation details can be easily determined because the product's source code is avai... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/balloonwj/flamingo/issues/48"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flamingoim_project:flamingoim:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9BDFDAE1-F9AA-479B-AB74-D8E45F0D9E9F",
"versionEndExcluding": null,
"versionEndIncluding": "2020-09-29",
"... | [
"22"
] | 22 | https://github.com/balloonwj/flamingo/issues/48 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"balloonwj",
"flamingo"
] | ## Directory traversal
Through code audit, it is found that the file download function in flamingo has a problem with directory traversal. Through this vulnerability, files can be downloaded anywhere on the server through the directory.
### Test environment
```
mysql> select version();
+-------------------... | Directory traversal vulnerability exists in uploaded and downloaded files | https://api.github.com/repos/balloonwj/flamingo/issues/48/comments | 1 | 2020-12-01T06:20:12Z | 2020-12-01T06:28:15Z | https://github.com/balloonwj/flamingo/issues/48 | 754,055,626 | 48 | 1,589 |
CVE-2020-28759 | 2020-12-26T20:15:12.997 | The serializer module in OAID Tengine lite-v1.0 has a Buffer Overflow and crash. NOTE: another person has stated "I don't think there is an proof of overflow so far. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/OAID/Tengine/issues/476"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tengine_project:tengine:1.0:*:*:*:lite:*:*:*",
"matchCriteriaId": "324AB9BB-BF23-43BD-B339-239B776D51E9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"120"
] | 120 | https://github.com/OAID/Tengine/issues/476 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"OAID",
"Tengine"
] | # Vulnerability analysis
We found that in the seriliazer module, there is a buffer overflow problem
Link:https://github.com/OAID/Tengine/blob/tengine-lite/src/serializer/tm/tm2_serializer.c
The problem is in the `load_model` function starting at line 798, which calls the `get_tm_file_model` function at line 84... | A buffer overflow is found in serializer | https://api.github.com/repos/OAID/Tengine/issues/476/comments | 1 | 2020-11-11T07:31:30Z | 2021-03-03T08:07:34Z | https://github.com/OAID/Tengine/issues/476 | 740,541,113 | 476 | 1,590 |
CVE-2020-29203 | 2020-12-26T20:15:13.077 | struct2json before 2020-11-18 is affected by a Buffer Overflow because strcpy is used for S2J_STRUCT_GET_string_ELEMENT. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/armink/struct2json/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struct2json_project:struct2json:*:*:*:*:*:*:*:*",
"matchCriteriaId": "33FF87F3-92E7-43E6-8E74-E80F500553A9",
"versionEndExcluding": "2020-11-18",
"versionEndIncluding": null,
... | [
"120"
] | 120 | https://github.com/armink/struct2json/issues/13 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"armink",
"struct2json"
] | # struct2json
## Vulnerability Analysis
An unsafe operation is found in the `S2J_STRUCT_GET_string_ELEMENTfunction`. The `strcpy` function is used to copy `JSON->value` to the `struct`, which may cause overflow when `JSON->value` is longer than structure defined array size.
 through 2020-09-29 has a SQL injection vulnerability in UserManager::updateUserTeamInfoInDbAndMemory. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/balloonwj/flamingo/issues/47"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:flamingo_project:flamingo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4023A85E-B9F2-4439-923D-302C005647AE",
"versionEndExcluding": null,
"versionEndIncluding": "2020-09-29",
"vers... | [
"89"
] | 89 | https://github.com/balloonwj/flamingo/issues/47 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"balloonwj",
"flamingo"
] | # issue 1
## Vulnerability
There is a SQL injection vulnerability in the `UserManager::addUser` method.
The related business corresponding to the method is the registered account.
`userid`,`username`, `nickname` can be controlled, no filtering measures, and directly execute the entire SQL statement.
Looking ... | There are security risks in the operation of the server on the database | https://api.github.com/repos/balloonwj/flamingo/issues/47/comments | 1 | 2020-11-27T10:59:59Z | 2020-12-01T06:27:48Z | https://github.com/balloonwj/flamingo/issues/47 | 752,168,260 | 47 | 1,592 |
CVE-2020-35728 | 2020-12-27T05:15:11.590 | FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.oracle.wls.shaded.org.apache.xalan.lib.sql.JNDIConnectionPool (aka embedded Xalan in org.glassfish.web/javax.servlet.jsp.jstl). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2999"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DB440540-715A-4764-9F9B-6181D32CE07C",
"versionEndExcluding": "2.9.10.8",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2999 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `org.glassfish.web/javax.servlet.jsp.jstl` library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): bu5yer (of Sangfor FarSight Security Lab)
Mitre ... | Block one more gadget type (org.glassfish.web/javax.servlet.jsp.jstl, CVE-2020-35728) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2999/comments | 2 | 2020-12-23T04:30:19Z | 2021-06-22T04:06:00Z | https://github.com/FasterXML/jackson-databind/issues/2999 | 773,477,032 | 2,999 | 1,593 |
CVE-2020-29204 | 2020-12-27T06:15:12.387 | XXL-JOB 2.2.0 allows Stored XSS (in Add User) to bypass the 20-character limit via xxl-job-admin/src/main/java/com/xxl/job/admin/controller/UserController.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/xuxueli/xxl-job/issues/2083"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:xuxueli:xxl-job:2.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "C7AE69F1-6781-47B8-933D-989F4EF5ED19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/xuxueli/xxl-job/issues/2083 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"xuxueli",
"xxl-job"
] | Please answer some questions before submitting your issue. Thanks!
### Which version of XXL-JOB do you using?
v2.2.0
### Expected behavior
Add User。
### Actual behavior
Add User Stored XSS vulnerabilities . Escape 20 length limit
### Steps to reproduce the behavior
url:https://github.com/xuxueli/xxl-job/blob/... | v2.2.0 Add User Stored XSS vulnerabilities . Escape 20 length limit | https://api.github.com/repos/xuxueli/xxl-job/issues/2083/comments | 1 | 2020-11-18T09:38:37Z | 2025-03-09T08:46:00Z | https://github.com/xuxueli/xxl-job/issues/2083 | 745,495,627 | 2,083 | 1,594 |
CVE-2020-35736 | 2020-12-27T20:15:12.400 | GateOne 1.1 allows arbitrary file download without authentication via /downloads/.. directory traversal because os.path.join is misused. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/liftoff/GateOne/issues/747"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://rmb122.com/2019/08/28/Ogeek-Ea... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liftoffsoftware:gateone:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "382A8ABB-28F2-4B96-A0DB-A542FD68B61A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/liftoff/GateOne/issues/747 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"liftoff",
"GateOne"
] | Gateone has a vulnerability that allows arbitrary file download without authentication, which can traverse the directory and read arbitrary files on the target system.
> Code auditing
View the file [gateone/core/server.py](https://github.com/liftoff/GateOne/blob/master/gateone/core/server.py) In line 3692, you ca... | An Arbitrary File Download Vulnerability | https://api.github.com/repos/liftoff/GateOne/issues/747/comments | 2 | 2020-12-27T09:05:04Z | 2020-12-30T11:07:24Z | https://github.com/liftoff/GateOne/issues/747 | 775,003,018 | 747 | 1,595 |
CVE-2020-29242 | 2020-12-28T08:15:11.670 | dhowden tag before 2020-11-19 allows "panic: runtime error: index out of range" via readPICFrame. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dhowden/tag/issues/77"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tag_project:tag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B41EEA04-8974-4BB1-ABCB-A44C6413E45C",
"versionEndExcluding": "2020-11-19",
"versionEndIncluding": null,
"versionStartEx... | [
"129"
] | 129 | https://github.com/dhowden/tag/issues/77 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"dhowden",
"tag"
] | Hello, I found some vulnerability in this respository, they are could be used to cause a denial of service via decode some evil file.
This is the first vulnerability in [id3v2frames.go](https://github.com/dhowden/tag/blob/master/id3v2frames.go#L563-L568).
In readPICFrame function, you don't check the size of b pa... | some vulnerability - 0x01 an out-of-bound vulnerability in readPICFrame function | https://api.github.com/repos/dhowden/tag/issues/77/comments | 3 | 2020-11-19T13:15:59Z | 2021-01-04T19:12:38Z | https://github.com/dhowden/tag/issues/77 | 746,574,172 | 77 | 1,597 |
CVE-2020-29243 | 2020-12-28T08:15:11.710 | dhowden tag before 2020-11-19 allows "panic: runtime error: index out of range" via readAPICFrame. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dhowden/tag/issues/80"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tag_project:tag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B41EEA04-8974-4BB1-ABCB-A44C6413E45C",
"versionEndExcluding": "2020-11-19",
"versionEndIncluding": null,
"versionStartEx... | [
"129"
] | 129 | https://github.com/dhowden/tag/issues/80 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"dhowden",
"tag"
] | This is the fourth vulnerability in [id3v2frames.go](https://github.com/dhowden/tag/blob/master/id3v2frames.go#L603-L608).
In readAPICFrame function, you don't check the size of b parameter. If the b parameter don't end with double zero, the size of mimeDataSplit is one after bytes.SplitN and then program will happe... | some vulnerability - 0x04 an out-of-bound vulnerability in readAPICFrame function | https://api.github.com/repos/dhowden/tag/issues/80/comments | 0 | 2020-11-19T13:44:09Z | 2020-11-19T19:32:33Z | https://github.com/dhowden/tag/issues/80 | 746,597,891 | 80 | 1,598 |
CVE-2020-29244 | 2020-12-28T08:15:11.757 | dhowden tag before 2020-11-19 allows "panic: runtime error: slice bounds out of range" via readTextWithDescrFrame. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dhowden/tag/issues/79"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tag_project:tag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B41EEA04-8974-4BB1-ABCB-A44C6413E45C",
"versionEndExcluding": "2020-11-19",
"versionEndIncluding": null,
"versionStartEx... | [
"129"
] | 129 | https://github.com/dhowden/tag/issues/79 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"dhowden",
"tag"
] | This is the third vulnerability in [id3v2frames.go](https://github.com/dhowden/tag/blob/master/id3v2frames.go#L454-L460)
In readTextWithDescrFrame function, you don't check the size of b , program will happen panic when the size of b is 2 or less than 2 .
testcase [8eff69ad26a59a05ec11e38f3ca6c592f08dcc54.zip](ht... | some vulnerability - 0x03 an out-of-bound vulnerability in readTextWithDescrFrame function | https://api.github.com/repos/dhowden/tag/issues/79/comments | 7 | 2020-11-19T13:29:16Z | 2020-11-20T10:24:23Z | https://github.com/dhowden/tag/issues/79 | 746,586,802 | 79 | 1,599 |
CVE-2020-29245 | 2020-12-28T08:15:11.803 | dhowden tag before 2020-11-19 allows "panic: runtime error: slice bounds out of range" via readAtomData. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dhowden/tag/issues/78"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tag_project:tag:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B41EEA04-8974-4BB1-ABCB-A44C6413E45C",
"versionEndExcluding": "2020-11-19",
"versionEndIncluding": null,
"versionStartEx... | [
"129"
] | 129 | https://github.com/dhowden/tag/issues/78 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"dhowden",
"tag"
] | This is the second vulnerability in [mp4.go](https://github.com/dhowden/tag/blob/master/id3v2frames.go#L152-L155).
In readAtomData function, although you check the size of b , program also will happen panic when the size of b is 3 .
testcase [8a27ec34f36eb99f06de03422f00340f091b7b67.zip](https://github.com/dhowde... | some vulnerability - 0x02 an out-of-bound vulnerability in readAtomData function | https://api.github.com/repos/dhowden/tag/issues/78/comments | 0 | 2020-11-19T13:24:16Z | 2020-11-19T19:32:33Z | https://github.com/dhowden/tag/issues/78 | 746,583,003 | 78 | 1,600 |
CVE-2020-35766 | 2020-12-28T20:15:13.260 | The test suite in libopendkim in OpenDKIM through 2.10.3 allows local users to gain privileges via a symlink attack against the /tmp/testkeys file (related to t-testdata.h, t-setup.c, and t-cleanup.c). NOTE: this is applicable to persons who choose to engage in the "A number of self-test programs are included here for ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.4,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/trusteddomainproject/OpenDKIM/issues/113"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opendkim:opendkim:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0B747EF7-FA4F-4C72-8008-B595EBA29911",
"versionEndExcluding": null,
"versionEndIncluding": "2.10.3",
"versionStartExcl... | [
"59"
] | 59 | https://github.com/trusteddomainproject/OpenDKIM/issues/113 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"trusteddomainproject",
"OpenDKIM"
] | In https://github.com/trusteddomainproject/OpenDKIM/blob/develop/libopendkim/tests/t-testdata.h#L15 a fixed path under `/tmp` is used for the test keys.
This is not a _huge_ vulnerability, but it is a silly one since it is so well-known and easy to avoid: https://owasp.org/www-community/vulnerabilities/Insecure_Temp... | CVE-2020-35766: Insecure temporary key path /tmp/testkeys | https://api.github.com/repos/trusteddomainproject/OpenDKIM/issues/113/comments | 10 | 2020-12-28T16:05:55Z | 2020-12-30T02:06:01Z | https://github.com/trusteddomainproject/OpenDKIM/issues/113 | 775,471,702 | 113 | 1,601 |
CVE-2020-26287 | 2020-12-29T00:15:12.673 | HedgeDoc is a collaborative platform for writing and sharing markdown. In HedgeDoc before version 1.7.1 an attacker can inject arbitrary `script` tags in HedgeDoc notes using mermaid diagrams. Our content security policy prevents loading scripts from most locations, but `www.google-analytics.com` is allowed. Using Goog... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Alemmi/ctf-writeups/blob/main/hxpctf-2020/hackme/solution.md"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hedgedoc:hedgedoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DB55BE58-3D3F-40C5-89FE-2AACEA56F4E0",
"versionEndExcluding": "1.7.1",
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/hackmdio/codimd/issues/1630 | [
"Third Party Advisory"
] | github.com | [
"hackmdio",
"codimd"
] | Hi,
This weekend I played hxpctf, during competition there was a challenge called hackme. It was a Docker with codimd. My solution was unintended: I use google analytics to exploit a stored xss bug in mermaid.
Here is my [PoC](https://github.com/Alemmi/ctf-writeups/blob/main/hxpctf-2020/hackme/solution.md)
The bug... | Stored XSS in mermaid | https://api.github.com/repos/hackmdio/codimd/issues/1630/comments | 0 | 2020-12-20T21:27:54Z | 2020-12-25T09:22:57Z | https://github.com/hackmdio/codimd/issues/1630 | 771,710,540 | 1,630 | 1,602 |
CVE-2020-35850 | 2020-12-30T02:15:12.680 | An SSRF issue was discovered in cockpit-project.org Cockpit 234. NOTE: this is unrelated to the Agentejo Cockpit product. NOTE: the vendor states "I don't think [it] is a big real-life issue. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cockpit-project/cockpit/issues/15077"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/passtheti... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cockpit-project:cockpit:234:*:*:*:*:*:*:*",
"matchCriteriaId": "25671439-8E36-442D-917D-559660F25947",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"918"
] | 918 | https://github.com/cockpit-project/cockpit/issues/15077 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cockpit-project",
"cockpit"
] | Cockpit version: 234
OS: Ubuntu 18.04
Page: login
User can detect open ssh port or another open ports on server that services Cockpit last version. This is a vulnerability that allows an user send request to internal hosts for detecting open ports. So that firewall configuration can be bypassed or the server can b... | unauthenticated server-side request forgery - login page allows ssh to to localhost [CVE-2020-35850] | https://api.github.com/repos/cockpit-project/cockpit/issues/15077/comments | 14 | 2020-12-28T16:28:11Z | 2023-04-07T04:41:18Z | https://github.com/cockpit-project/cockpit/issues/15077 | 775,481,483 | 15,077 | 1,603 |
CVE-2020-35240 | 2020-12-30T15:15:13.027 | FluxBB 1.5.11 is affected by cross-site scripting (XSS in the Blog Content component. This vulnerability can allow an attacker to inject the XSS payload in "Blog Content" and each time any user will visit the blog, the XSS triggers and the attacker can able to steal the cookie according to the crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://fluxbb.org/downloads/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hemantsolo/CVE-Reference/blob/main/CVE-2020-35240.md"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fluxbb:fluxbb:1.5.11:*:*:*:*:*:*:*",
"matchCriteriaId": "4294CBC2-85BA-4C0F-90D3-E655F78495DF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/hemantsolo/CVE-Reference/issues/1 | [
"Third Party Advisory"
] | github.com | [
"hemantsolo",
"CVE-Reference"
] | Your example is not reproducible:
>payload in "Blog Content"
FluxBB doesn't have "Blog Content"
>Now go to the URL: https://127.0.0.1/fluxbb/post.php?action=post&fid=1
>Put the payload in Content:
post.php on its form does not contain Content field
> and the attacker can able to steal the cookie accordi... | CVE-2020-35240: Your example is not reproducible | https://api.github.com/repos/hemantsolo/CVE-Reference/issues/1/comments | 1 | 2021-01-08T02:46:00Z | 2021-02-09T13:31:05Z | https://github.com/hemantsolo/CVE-Reference/issues/1 | 781,799,411 | 1 | 1,604 |
CVE-2020-27848 | 2020-12-30T19:15:13.123 | dotCMS before 20.10.1 allows SQL injection, as demonstrated by the /api/v1/containers orderby parameter. The PaginatorOrdered classes that are used to paginate results of a REST endpoints do not sanitize the orderBy parameter and in some cases it is vulnerable to SQL injection attacks. A user must be an authenticated m... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/core/compare/v5.3.8.1...v20.10.1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotcms:dotcms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "329E2530-4026-4A5B-B21C-487197C91666",
"versionEndExcluding": "20.10.1",
"versionEndIncluding": null,
"versionStartExcludi... | [
"89"
] | 89 | https://github.com/dotCMS/core/issues/19500 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"dotCMS",
"core"
] | **api : /api/v1/containers
Is vulnerable to SQL injection, by the parameter ‘orderby’ in url.**
<img width="990" alt="截屏2020-09-3017 36 27" src="https://user-images.githubusercontent.com/19262732/97246207-c0180680-1837-11eb-98fe-a4b4d711e1ba.png">
<img width="978" alt="截屏2020-09-3017 37 48" src="https://user-images.... | SQL Injection Vulnerability in api /api/v1/containers | https://api.github.com/repos/dotCMS/core/issues/19500/comments | 3 | 2020-10-27T01:40:55Z | 2021-10-26T15:58:40Z | https://github.com/dotCMS/core/issues/19500 | 730,028,213 | 19,500 | 1,605 |
CVE-2020-28734 | 2020-12-30T19:15:13.263 | Plone before 5.2.3 allows XXE attacks via a feature that is explicitly only available to the Manager role. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://dist.plone.org/release/5.2.3/RELEASE-NOTES.txt"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/plone/Produ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:plone:plone:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5BD82FD3-BE50-4B23-AF04-9FDF79E5B748",
"versionEndExcluding": "5.2.3",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"611"
] | 611 | https://github.com/plone/Products.CMFPlone/issues/3209 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"plone",
"Products.CMFPlone"
] | Hi, I found several security issues in the background, please pay attention to deal with it
address: https://www.misakikata.com/codes/plone/python-en.html | Security issues in the background | https://api.github.com/repos/plone/Products.CMFPlone/issues/3209/comments | 7 | 2020-11-10T09:41:27Z | 2020-11-18T20:51:48Z | https://github.com/plone/Products.CMFPlone/issues/3209 | 739,749,558 | 3,209 | 1,606 |
CVE-2020-26296 | 2020-12-30T23:15:15.233 | Vega is a visualization grammar, a declarative format for creating, saving, and sharing interactive visualization designs. Vega in an npm package. In Vega before version 5.17.3 there is an XSS vulnerability in Vega expressions. Through a specially crafted Vega expression, an attacker could execute arbitrary javascript ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/vega/vega/issues/3018"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/vega/vega/pull/3019"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vega_project:vega:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "7A1B602E-B94B-4BD0-ADF7-2582C27105D2",
"versionEndExcluding": "5.17.3",
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/vega/vega/issues/3018 | [
"Third Party Advisory"
] | github.com | [
"vega",
"vega"
] | This was found during the hxp ctf.
### Credit
@cgvwzq and his [writeup](https://gist.github.com/cgvwzq/0392d64fe1aed82f65c1648b71df1a37)
- Describe how to reproduce the bug / the goal of the feature request:
Paste the below JSON in the [Vega Editor](https://vega.github.io/editor/#/custom/vega-lite).
[Worki... | XSS in transform filter | https://api.github.com/repos/vega/vega/issues/3018/comments | 6 | 2020-12-21T10:54:25Z | 2020-12-21T20:22:35Z | https://github.com/vega/vega/issues/3018 | 772,072,655 | 3,018 | 1,607 |
CVE-2019-25011 | 2020-12-31T20:15:12.570 | NetBox through 2.6.2 allows an Authenticated User to conduct an XSS attack against an admin via a GFM-rendered field, as demonstrated by /dcim/sites/add/ comments. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://www.cinquino.eu/NetBox.htm"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/netbox-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netbox:netbox:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D0628336-45B1-4EAF-A12A-D2F1FD5AB06B",
"versionEndExcluding": null,
"versionEndIncluding": "2.6.2",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/netbox-community/netbox/issues/3471 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"netbox-community",
"netbox"
] | Netbox is vulnerable to stored XSS due to lack of filtration of user-supplied [Autenticated User]
### Environment
* Python version: 3.7.4
* NetBox version: 2.6.1 -2.6.2
Parameter:
name="comments" [ works on all pages where the parameter is present ]
**PoC**
```
POST /dcim/sites/add/ HTTP/1.1
Host: xx... | XSS possible through GFM-rendered fields | https://api.github.com/repos/netbox-community/netbox/issues/3471/comments | 4 | 2019-08-31T09:47:44Z | 2020-01-15T15:50:46Z | https://github.com/netbox-community/netbox/issues/3471 | 487,752,640 | 3,471 | 1,608 |
CVE-2020-35930 | 2020-12-31T20:15:12.663 | Seo Panel 4.8.0 allows stored XSS by an Authenticated User via the url parameter, as demonstrated by the seo/seopanel/websites.php URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/seopanel/Seo-Panel/issues/201"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seopanel:seo_panel:4.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA338EF9-AC8B-411D-8BE3-9F9A2E68F8E0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/seopanel/Seo-Panel/issues/201 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"seopanel",
"Seo-Panel"
] | SeoPanel is vulnerable to stored XSS due to lack of filtration of user-supplied [Autenticated User]
Environment
SeoPanel version: 4.8.0 Last Version
Parameter:
name="url" [ works on all pages where the parameter is present ]
PoC
POST /seo/seopanel/websites.php HTTP/1.1
Host: xxx
User-Agent: Mozilla/5.... | [BUG] Xss Stored | https://api.github.com/repos/seopanel/Seo-Panel/issues/201/comments | 1 | 2020-12-30T10:49:42Z | 2021-03-22T11:11:44Z | https://github.com/seopanel/Seo-Panel/issues/201 | 776,393,582 | 201 | 1,609 |
CVE-2021-3002 | 2021-01-01T19:15:11.077 | Seo Panel 4.8.0 allows reflected XSS via the seo/seopanel/login.php?sec=forgot email parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://www.cinquino.eu/SeoPanelReflect.htm"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seopanel:seo_panel:4.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "FA338EF9-AC8B-411D-8BE3-9F9A2E68F8E0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/seopanel/Seo-Panel/issues/202 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"seopanel",
"Seo-Panel"
] | SeoPanel is vulnerable to reflect XSS due to lack of filtration of user-supplied [NO Autenticated User]
Environment
SeoPanel version: 4.8.0 Last Version
Parameter:
name="email"
PoC
POST /seo/seopanel/login.php?sec=forgot HTTP/1.1
Host: xxx
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Ge... | [BUG] Xss Reflect | https://api.github.com/repos/seopanel/Seo-Panel/issues/202/comments | 1 | 2021-01-01T11:31:37Z | 2021-03-22T10:29:18Z | https://github.com/seopanel/Seo-Panel/issues/202 | 777,269,687 | 202 | 1,610 |
CVE-2020-28851 | 2021-01-02T06:15:12.380 | In x/text in Go 1.15.4, an "index out of range" panic occurs in language.ParseAcceptLanguage while parsing the -u- extension. (x/text/language is supposed to be able to parse an HTTP Accept-Language header.) | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/golang/go/issues/42535"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.netapp.com/advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:1.15.4:*:*:*:*:*:*:*",
"matchCriteriaId": "57427CF7-E136-4F17-BBBA-1AAAA7333825",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"129"
] | 129 | https://github.com/golang/go/issues/42535 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | <!-- Please answer these questions before submitting your issue. Thanks! -->
### What version of Go are you using (`go version`)?
<pre>
$ go version
go version go1.15.4 linux/amd64
</pre>
### Does this issue reproduce with the latest release?
### What operating system and processor architecture are you... | x/text: panic in language.ParseAcceptLanguage while parsing -u- extension | https://api.github.com/repos/golang/go/issues/42535/comments | 16 | 2020-11-12T11:07:01Z | 2022-03-26T11:38:47Z | https://github.com/golang/go/issues/42535 | 741,505,618 | 42,535 | 1,611 |
CVE-2020-28852 | 2021-01-02T06:15:13.100 | In x/text in Go before v0.3.5, a "slice bounds out of range" panic occurs in language.ParseAcceptLanguage while processing a BCP 47 tag. (x/text/language is supposed to be able to parse an HTTP Accept-Language header.) | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/golang/go/issues/42536"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://security.netapp.com/advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:text:*:*:*:*:*:*:*:*",
"matchCriteriaId": "248279D3-C3A0-439B-8772-09373DA59099",
"versionEndExcluding": "0.3.5",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"129"
] | 129 | https://github.com/golang/go/issues/42536 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"golang",
"go"
] | <!-- Please answer these questions before submitting your issue. Thanks! -->
### What version of Go are you using (`go version`)?
<pre>
$ go version
go version go1.15.4 linux/amd64
</pre>
### Does this issue reproduce with the latest release?
### What operating system and processor architecture are you... | x/text: panic in language.ParseAcceptLanguage while processing bcp47 tag | https://api.github.com/repos/golang/go/issues/42536/comments | 8 | 2020-11-12T11:12:42Z | 2022-01-08T15:21:49Z | https://github.com/golang/go/issues/42536 | 741,509,514 | 42,536 | 1,612 |
CVE-2021-3019 | 2021-01-05T05:15:10.907 | ffay lanproxy 0.1 allows Directory Traversal to read /../conf/config.properties to obtain credentials for a connection to the intranet. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ffay/lanproxy/commits/master"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/maybe-why-not/lanpr... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lanproxy_project:lanproxy:0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "BCCBA214-90E3-4C0B-85F4-C6A96FC75AC9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/maybe-why-not/lanproxy/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"maybe-why-not",
"lanproxy"
] | Vendor of the product: https://github.com/ffay/lanproxy
Payload: http://192.168.5.43:8090/../conf/config.properties
Read configuration file

Configure the proxy to connect to the intranet after logging... | Path traversal vulnerability in lanproxy leads to connection to the intranet | https://api.github.com/repos/maybe-why-not/lanproxy/issues/1/comments | 0 | 2021-01-05T02:36:29Z | 2021-01-05T02:36:29Z | https://github.com/maybe-why-not/lanproxy/issues/1 | 778,523,449 | 1 | 1,613 |
CVE-2020-26045 | 2021-01-05T15:15:13.657 | FUEL CMS 1.4.11 allows SQL Injection via parameter 'name' in /fuel/permissions/create/. Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://getfuelcms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/575"
},
{
"source": "cve@mitre.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.4.11:*:*:*:*:*:*:*",
"matchCriteriaId": "5128D2F0-4C37-4010-946C-00364B1EB496",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"89"
] | 89 | https://github.com/daylightstudio/FUEL-CMS/issues/575 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"daylightstudio",
"FUEL-CMS"
] | FUEL CMS 1.4.11 allows SQL Injection via parameter 'name' in /fuel/permissions/create/
Exploiting this issue could allow an attacker to compromise the application, access or modify data, or exploit latent vulnerabilities in the underlying database.

Refresh the page, it will trigger below "Recently Viewed" menu

Fr... | Stored XSS in Blocks/Navigation/Site Variables (release/1.4.11) | https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/574/comments | 0 | 2020-09-23T07:36:11Z | 2020-09-23T16:43:02Z | https://github.com/daylightstudio/FUEL-CMS/issues/574 | 707,124,307 | 574 | 1,615 |
CVE-2020-29437 | 2021-01-05T21:15:14.773 | SQL injection in the Buzz module of OrangeHRM through 4.6 allows remote authenticated attackers to execute arbitrary SQL commands via the orangehrmBuzzPlugin/lib/dao/BuzzDao.php loadMorePostsForm[profileUserId] parameter to the buzz/loadMoreProfile endpoint. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/issues/695"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/orangehrm/orangehrm/pull/699"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:orangehrm:orangehrm:*:*:*:*:*:*:*:*",
"matchCriteriaId": "86BE7F8F-2131-4E66-867C-20CC62DF6FE4",
"versionEndExcluding": "4.6.0.1",
"versionEndIncluding": null,
"versionStartE... | [
"89"
] | 89 | https://github.com/orangehrm/orangehrm/issues/695 | [
"Third Party Advisory"
] | github.com | [
"orangehrm",
"orangehrm"
] | Hi, I would like to report a security issue, can I please get a point of contact?
Thanks! | security issue | https://api.github.com/repos/orangehrm/orangehrm/issues/695/comments | 2 | 2020-11-28T19:16:33Z | 2021-01-04T06:06:07Z | https://github.com/orangehrm/orangehrm/issues/695 | 752,748,953 | 695 | 1,616 |
CVE-2020-36067 | 2021-01-05T21:15:15.053 | GJSON <=v1.6.5 allows attackers to cause a denial of service (panic: runtime error: slice bounds out of range) via a crafted GET call. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tidwall/gjson/issues/196"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/tidwall/gjson/issues/196"
}
] | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gjson_project:gjson:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F57067B1-32E3-49A2-98E4-686C6BB14CC1",
"versionEndExcluding": null,
"versionEndIncluding": "1.6.5",
"versionStartExc... | [
"129"
] | 129 | https://github.com/tidwall/gjson/issues/196 | [
"Third Party Advisory"
] | github.com | [
"tidwall",
"gjson"
] | https://play.golang.org/p/of9fapZ8vMs
| panic: runtime error: slice bounds out of range | https://api.github.com/repos/tidwall/gjson/issues/196/comments | 1 | 2020-12-24T02:40:47Z | 2021-01-06T13:40:11Z | https://github.com/tidwall/gjson/issues/196 | 774,141,896 | 196 | 1,617 |
CVE-2020-36051 | 2021-01-05T22:15:14.313 | Directory traversal vulnerability in page_edit.php in MiniCMS V1.10 allows remote attackers to read arbitrary files via the state parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/bg5sbk/MiniCMS/issues/39"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:1234n:minicms:1.10:*:*:*:*:*:*:*",
"matchCriteriaId": "1EAC73A0-FD32-4344-A4F5-BB6D3D1B7DA7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"22"
] | 22 | https://github.com/bg5sbk/MiniCMS/issues/39 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"bg5sbk",
"MiniCMS"
] | post_edit and page_edit.php
line99
$index_file = '../mc-files/posts/index/'.$post_state.'.php';
line102
$index_file = '../mc-files/pages/index/'.$post_state.'.php';
post_state is controllable and there is no filtering limit
We can use ../ to loop through all files
 library was reported as possible gadget type and should be blocked.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): Al1ex@knownsec
Mitre id(s... | Block some more DBCP-related potential gadget classes (CVE-2020-36179 - CVE-2020-36182) | https://api.github.com/repos/FasterXML/jackson-databind/issues/3004/comments | 1 | 2021-01-01T01:03:14Z | 2021-06-22T04:05:38Z | https://github.com/FasterXML/jackson-databind/issues/3004 | 777,170,349 | 3,004 | 1,620 |
CVE-2020-36184 | 2021-01-06T23:15:13.017 | FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.datasources.PerUserPoolDataSource. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Technical Description",
"Third Party Advisory"
],
"url": "https://cowtowncoder.medium.com/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netapp:cloud_backup:-:*:*:*:*:*:*:*",
"matchCriteriaId": "5C2089EE-5D7F-47EC-8EA5-0F69790564C4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2998 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `org.apache.tomcat/tomcat-dbcp` library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): Al1ex@knownsec
Mitre id(s):
* [CVE-2020-36184](CVE-2020... | Block 2 more gadget types (org.apache.tomcat/tomcat-dbcp, CVE-2020-36184/CVE-2020-36185) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2998/comments | 1 | 2020-12-23T04:18:43Z | 2021-01-07T21:18:05Z | https://github.com/FasterXML/jackson-databind/issues/2998 | 773,473,261 | 2,998 | 1,621 |
CVE-2020-36186 | 2021-01-06T23:15:13.123 | FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Technical Description",
"Third Party Advisory"
],
"url": "https://cowtowncoder.medium.com/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4892ABAA-57A0-43D3-965C-2D7F4A8A6024",
"versionEndExcluding": "2.6.7.5",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2997 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `tomcat:naming-factory-dbcp` library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): Al1ex@knownsec
Mitre id(s):
* [CVE-2020-36186](CVE-2020-... | Block 2 more gadget types (tomcat/naming-factory-dbcp, CVE-2020-36186/CVE-2020-36187) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2997/comments | 1 | 2020-12-23T04:18:08Z | 2021-06-22T04:04:42Z | https://github.com/FasterXML/jackson-databind/issues/2997 | 773,473,087 | 2,997 | 1,622 |
CVE-2020-36188 | 2021-01-06T23:15:13.233 | FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to com.newrelic.agent.deps.ch.qos.logback.core.db.JNDIConnectionSource. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Technical Description",
"Third Party Advisory"
],
"url": "https://cowtowncoder.medium.com/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4892ABAA-57A0-43D3-965C-2D7F4A8A6024",
"versionEndExcluding": "2.6.7.5",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2996 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `com.newrelic.agent.java:newrelic-agent` library (version 3.x).
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): Al1ex@knownsec
Mitre id(s):
* [C... | Block 2 more gadget types (newrelic-agent, CVE-2020-36188/CVE-2020-36189) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2996/comments | 1 | 2020-12-23T04:09:48Z | 2021-06-22T04:04:28Z | https://github.com/FasterXML/jackson-databind/issues/2996 | 773,470,448 | 2,996 | 1,623 |
CVE-2020-36183 | 2021-01-07T00:15:15.023 | FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.docx4j.org.apache.xalan.lib.sql.JNDIConnectionPool. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Technical Description",
"Third Party Advisory"
],
"url": "https://cowtowncoder.medium.com/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "959574F9-E7A4-4738-A609-031488012274",
"versionEndExcluding": "2.6.7.5",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/3003 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `org.docx4j.org.apache:xalan-interpretive` library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Reporter(s): differ (of Zorelworld iLab team)
Mitre id: [CVE-... | Block one more gadget type (org.docx4j.org.apache:xalan-interpretive, CVE-2020-36183) | https://api.github.com/repos/FasterXML/jackson-databind/issues/3003/comments | 1 | 2021-01-01T00:43:41Z | 2021-06-22T04:05:49Z | https://github.com/FasterXML/jackson-databind/issues/3003 | 777,167,854 | 3,003 | 1,624 |
CVE-2020-26768 | 2021-01-07T13:15:11.623 | Formstone <=1.4.16 is vulnerable to a Reflected Cross-Site Scripting (XSS) vulnerability caused by improper validation of user supplied input in the upload-target.php and upload-chunked.php files. A remote attacker could exploit this vulnerability using a specially crafted URL to execute a script in a victim's Web brow... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Formstone/Formstone/issues/286"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Formstone/Formstone/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:formstone:formstone:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FFE042F2-14FC-45DD-8048-5522F0C4F215",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.16",
"versionStartEx... | [
"79"
] | 79 | https://github.com/Formstone/Formstone/issues/286 | [
"Third Party Advisory"
] | github.com | [
"Formstone",
"Formstone"
] | Hi Formstone team.
We are BRZTEC, a offensive information security firm from Brazil.
When performed a pentest in one of our customers we found a XSS vulnerability that affect default installation of Formstone.
Please, do you can tell us a secure channel to send to yours more details about this vulnerability?... | XSS Vulnerability | https://api.github.com/repos/Formstone/Formstone/issues/286/comments | 4 | 2020-10-02T22:56:01Z | 2020-10-06T17:09:20Z | https://github.com/Formstone/Formstone/issues/286 | 713,942,143 | 286 | 1,625 |
CVE-2020-13449 | 2021-01-07T22:15:10.817 | A directory traversal vulnerability in the Markdown engine of Gotenberg through 6.2.1 allows an attacker to read any container files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/160744/Gotenberg-6.2.0-Traversal-Code-Execution-Insecure-Permissions.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thecodingmachine:gotenberg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B023F305-FA25-4E60-AA64-C7327F034F9F",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.1",
"versionS... | [
"22"
] | 22 | https://github.com/thecodingmachine/gotenberg/issues/199 | [
"Third Party Advisory"
] | github.com | [
"thecodingmachine",
"gotenberg"
] | Hi there,
I have identified several vulnerabilities in Gotenberg which all lead to arbitrary code execution in the container.
Following responsible disclosure model I would like to give contributors more details so that you could fix this.
@gulien : please provide some e-mail and pgp key so that I can contact... | Critical vulnerability | https://api.github.com/repos/gotenberg/gotenberg/issues/199/comments | 4 | 2020-05-25T07:00:23Z | 2020-06-22T08:58:02Z | https://github.com/gotenberg/gotenberg/issues/199 | 624,090,792 | 199 | 1,626 |
CVE-2020-28468 | 2021-01-08T12:15:12.687 | This affects the package pwntools before 4.3.1. The shellcraft generator for affected versions of this module are vulnerable to Server-Side Template Injection (SSTI), which can lead to remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Gallopsled/pwntools/issues/1427"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pwntools_project:pwntools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B5FEFD1B-2E07-42C6-9665-4A77128F511A",
"versionEndExcluding": "4.3.1",
"versionEndIncluding": null,
"versionSt... | [
"74"
] | 74 | https://github.com/Gallopsled/pwntools/issues/1427 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Gallopsled",
"pwntools"
] | PoC||GTFO:
```
In [161]: print(shellcraft.amd64.write(0, '*/', 2))
/* write(fd=0, buf='*/', n=2) */
/* push '*/\x00' */
push 0x1010101 ^ 0x2f2a
xor dword ptr [rsp], 0x1010101
mov rsi, rsp
xor edi, edi /* 0 */
push 2
pop rdx
/* call write() */
push SYS_write /* 1 */
... | Shellcraft generation fails with strings that contains end of multiline comment | https://api.github.com/repos/Gallopsled/pwntools/issues/1427/comments | 1 | 2020-02-08T23:06:53Z | 2020-11-29T23:44:35Z | https://github.com/Gallopsled/pwntools/issues/1427 | 562,091,521 | 1,427 | 1,627 |
CVE-2020-26800 | 2021-01-11T13:15:13.260 | A stack overflow vulnerability in Aleth Ethereum C++ client version <= 1.8.0 using a specially crafted a config.json file may result in a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://ethereum.org/en/about/"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ethereum/aleth"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ethereum:aleth:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BB30748E-D2BA-4956-AC11-E49FFA9A93F2",
"versionEndExcluding": null,
"versionEndIncluding": "1.8.0",
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/ethereum/aleth/issues/5917 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ethereum",
"aleth"
] | ### Short description
Stack based buffer overflow while parsing JSON file Leads to DoS
### Attack scenario
An attacker can supply a specially crafted config.json file, consisting of 3764 left square brackets or more, which results in segmentation fault by the application. This immediately results in Denial of Ser... | [CVE-2020-26800] Stack based buffer overflow while parsing JSON file | https://api.github.com/repos/ethereum/aleth/issues/5917/comments | 2 | 2021-01-10T22:07:33Z | 2021-04-21T15:07:29Z | https://github.com/ethereum/aleth/issues/5917 | 782,919,279 | 5,917 | 1,628 |
CVE-2020-23643 | 2021-01-11T14:15:12.890 | XSS exists in JIZHICMS 1.7.1 via index.php/Wechat/checkWeixin?signature=1&echostr={XSS] to Home/c/WechatController.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:1.7.1:*:*:*:*:*:*:*",
"matchCriteriaId": "694A0DBA-00B6-46BA-81C4-D50F430CD863",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Cherry-toto/jizhicms/issues/29 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | A xss vulnerability was discovered in jizhicms 1.7.1
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the msg parameter of /index.php/Wechat/checkWeixin?signature=1&echostr=1
Vulnerability file: `Home/c/WechatController.php`
```php
public functi... | XSS vulnerability jizhicms v1.7.1 Wechat reflected xss vulnerability | https://api.github.com/repos/Cherry-toto/jizhicms/issues/29/comments | 1 | 2020-06-15T14:56:07Z | 2020-06-15T15:49:24Z | https://github.com/Cherry-toto/jizhicms/issues/29 | 638,919,919 | 29 | 1,629 |
CVE-2020-23644 | 2021-01-11T14:15:12.953 | XSS exists in JIZHICMS 1.7.1 via index.php/Error/index?msg={XSS] to Home/c/ErrorController.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Cherry-toto/jizhicms/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jizhicms:jizhicms:1.7.1:*:*:*:*:*:*:*",
"matchCriteriaId": "694A0DBA-00B6-46BA-81C4-D50F430CD863",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/Cherry-toto/jizhicms/issues/28 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Cherry-toto",
"jizhicms"
] | A xss vulnerability was discovered in jizhicms 1.7.1
There is a reflected XSS vulnerability which allows remote attackers to inject arbitrary web script or HTML via the msg parameter of /index.php/Error/index?msg=1
Vulnerability file: `Home/c/ErrorController.php`
```php
class ErrorController extends Controll... | jizhicms v1.7.1 msg reflected xss vulnerability | https://api.github.com/repos/Cherry-toto/jizhicms/issues/28/comments | 3 | 2020-06-15T14:40:14Z | 2021-01-14T16:36:31Z | https://github.com/Cherry-toto/jizhicms/issues/28 | 638,908,140 | 28 | 1,630 |
CVE-2020-23849 | 2021-01-11T14:15:13.000 | Stored XSS was discovered in the tree mode of jsoneditor before 9.0.2 through injecting and executing JavaScript. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/josdejong/jsoneditor/issues/1029"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsoneditoronline:jsoneditor:*:*:*:*:*:*:*:*",
"matchCriteriaId": "54399FE4-3A39-4823-87D1-27B98374940F",
"versionEndExcluding": "9.0.2",
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/josdejong/jsoneditor/issues/1029 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"josdejong",
"jsoneditor"
] | Insert a poc
https://jsoneditoronline.org/#right=local.xobutu&left=local.pawuqa

click the Drop-down list box
. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://zzcms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Pandora1m2/"
},
{
"source": "cve@mitre.org",
"tags": [
"Expl... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:201910:*:*:*:*:*:*:*",
"matchCriteriaId": "783BABB9-58F7-458E-B214-5CE4B34239FA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"89"
] | 89 | https://github.com/Pandora1m2/zzcms201910/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Pandora1m2",
"zzcms201910"
] | ### Software download address:
http://www.zzcms.net/download/zzcms201910.zip
### Operation environment requirements:
Apache, IIS, etc
PHP4 / PHP5 / PHP7
MySQL 4/5
### Here is a global filter at /inc/config.php
`define('stopwords','select|update|and|or|delete|insert|truncate|char... | zzcms.ver201910 Blind SQL injection vulnerability based on time | https://api.github.com/repos/Pandora1m2/zzcms201910/issues/1/comments | 0 | 2020-06-12T11:16:02Z | 2020-06-12T11:16:02Z | https://github.com/Pandora1m2/zzcms201910/issues/1 | 637,678,903 | 1 | 1,632 |
CVE-2020-35701 | 2021-01-11T16:15:15.600 | An issue was discovered in Cacti 1.2.x through 1.2.16. A SQL injection vulnerability in data_debug.php allows remote authenticated attackers to execute arbitrary SQL commands via the site_id parameter. This can lead to remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://asaf.me/2020/12/15/cacti-1-2-0-to-1-2-16-sql-injection/"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Cacti/cacti/issues... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F2A8BC37-F5C4-4940-BE4E-2114CAA44B5F",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.16",
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/Cacti/cacti/issues/4022 | [
"Third Party Advisory"
] | github.com | [
"Cacti",
"cacti"
] | # Describe the bug
Due to a lack of validation, data_debug.php can be the source of a SQL injection.
## Expected behavior
Cacti should be safe from SQL injections | SQL Injection was possible due to incorrect validation order (CVE-2020-35701) | https://api.github.com/repos/Cacti/cacti/issues/4022/comments | 2 | 2020-12-24T15:37:03Z | 2021-04-30T22:50:28Z | https://github.com/Cacti/cacti/issues/4022 | 774,491,101 | 4,022 | 1,633 |
CVE-2020-36191 | 2021-01-13T04:15:13.073 | JupyterHub 1.1.0 allows CSRF in the admin panel via a request that lacks an _xsrf field, as demonstrated by a /hub/api/user request (to add or remove a user account). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jupyterhub/jupyterhub/issues/3304"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jupyterhub/jupyterhub/release... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jupyter:jupyterhub:1.1.0:-:*:*:*:*:*:*",
"matchCriteriaId": "BE8F96E9-B97E-4ECD-93B7-AE60F2E75B7F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"352"
] | 352 | https://github.com/jupyterhub/jupyterhub/issues/3304 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jupyterhub",
"jupyterhub"
] | ### Bug description
In JupyterHub's Admin panel, the _xsrf token is not working for add/delete user features.
Current mechanism to protect add/delete user features against CSRF attack is solely rely on checking the Referer header value.
Although current referer header examination seems to be strict enough, it could... | Anti-CSRF token is not working in Admin panel | https://api.github.com/repos/jupyterhub/jupyterhub/issues/3304/comments | 2 | 2020-12-11T02:02:14Z | 2022-09-09T07:25:04Z | https://github.com/jupyterhub/jupyterhub/issues/3304 | 761,789,976 | 3,304 | 1,634 |
CVE-2020-35687 | 2021-01-13T17:15:12.853 | PHPFusion version 9.03.90 is vulnerable to CSRF attack which leads to deletion of all shoutbox messages by the attacker on behalf of the logged in victim. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PHPFusion/PHPFusion/issues/2347"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:phpfusion:9.03.90:*:*:*:*:*:*:*",
"matchCriteriaId": "B99CC43B-BBB6-46CC-8263-D55D51169212",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"352"
] | 352 | https://github.com/PHPFusion/PHPFusion/issues/2347 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PHPFusion",
"PHPFusion"
] | **Describe the bug**
PHP-Fusion version 9.03.90 is vulnerable to CSRF attack which leads to deletion of shoutbox messages by the attacker on behalf of the logged in victim..
**Version**
PHP-Fusion version 9.03.90.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'https://v9.demos.php-fusion.co.uk/ho... | CSRF attack leads to deletion of shoutbox messages | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2347/comments | 11 | 2020-12-21T16:21:03Z | 2021-01-19T07:57:11Z | https://github.com/PHPFusion/PHPFusion/issues/2347 | 772,287,114 | 2,347 | 1,635 |
CVE-2020-23653 | 2021-01-13T18:15:14.040 | An insecure unserialize vulnerability was discovered in ThinkAdmin versions 4.x through 6.x in app/admin/controller/api/Update.php and app/wechat/controller/api/Push.php, which may lead to arbitrary remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zoujingli/ThinkAdmin/issues/238"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkadmin:thinkadmin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "24F3812E-3B21-4FDE-A007-9B5259FE8A17",
"versionEndExcluding": null,
"versionEndIncluding": "6.0",
"versionStartExc... | [
"502"
] | 502 | https://github.com/zoujingli/ThinkAdmin/issues/238 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zoujingli",
"ThinkAdmin"
] | Hi, this is Tencent **Xcheck** team. Our code safety check tool Xcheck has found several unserialize vulnerabilities in this project(v4, v5, v6). It leads to remote code execution. Here are the details.
**v6**
1. app/admin/controller/api/Update.php
line: 46 `$this->rules = unserialize($this->request->post('rule... | Remote code execution vulnerability | https://api.github.com/repos/zoujingli/ThinkAdmin/issues/238/comments | 1 | 2020-06-02T02:38:06Z | 2023-10-11T07:04:38Z | https://github.com/zoujingli/ThinkAdmin/issues/238 | 628,854,976 | 238 | 1,636 |
CVE-2020-29587 | 2021-01-14T16:15:18.227 | SimplCommerce 1.0.0-rc uses the Bootbox.js library, which allows creation of programmatic dialog boxes using Bootstrap modals. The Bootbox.js library intentionally does not perform any sanitization of user input, which results in a DOM XSS, because it uses the jQuery .html() function to directly append the payload to a... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/simplcommerce/SimplCommerce/issues/969"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simplcommerce:simplcommerce:1.0.0:rc:*:*:*:*:*:*",
"matchCriteriaId": "51050C05-11AE-43C0-890E-A81CF04EFA5C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"79"
] | 79 | https://github.com/simplcommerce/SimplCommerce/issues/969 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"simplcommerce",
"SimplCommerce"
] | Opened this issue because there is not a security advisory or a response from the repo maintainers after sending a report by email.
The POC described here used the docker continuous deployment instance (https://ci.simplcommerce.com).
### POC
The following POC is just an example of many others that are prone to D... | Admin dashboard vulnerable to DOM XSS | https://api.github.com/repos/simplcommerce/SimplCommerce/issues/969/comments | 0 | 2021-01-13T12:36:40Z | 2021-01-18T23:39:23Z | https://github.com/simplcommerce/SimplCommerce/issues/969 | 785,068,620 | 969 | 1,637 |
CVE-2020-27219 | 2021-01-14T23:15:12.977 | In all version of Eclipse Hawkbit prior to 0.3.0M7, the HTTP 404 (Not Found) JSON response body returned by the REST API may contain unsafe characters within the path attribute. Sending a POST request to a non existing resource will return the full path from the given URL unescaped to the client. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "emo@eclipse.org",
"tags": [
"Vendor Advisory"
],
"url": "https://bugs.eclipse.org/bugs/show_bug.cgi?id=570289"
},
{
"source": "emo@eclipse.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/eclipse/hawkbit/issues/1067"
},
{
"sour... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclipse:hawkbit:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AECE2400-B719-4F2D-A67B-2C75E2686EBB",
"versionEndExcluding": null,
"versionEndIncluding": "0.2.5",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/eclipse/hawkbit/issues/1067 | [
"Third Party Advisory"
] | github.com | [
"eclipse",
"hawkbit"
] | Hi,
our security team reported an issue with our Hawkbit instance:
Request:
POST to /cgi-bin/<script>xss-test<script>.asp
Response:
{"timestamp":"2021-01-11T07:18:10.650+0000","status":404,"error":"Not Found","message":"Not Found","path":"/cgi-bin/<script>xss-test</script>.asp"}
I was able to reproduce ... | Mgmt API error page vulnerable to cross-site scripting attack | https://api.github.com/repos/eclipse-hawkbit/hawkbit/issues/1067/comments | 4 | 2021-01-11T07:26:25Z | 2021-01-15T07:42:50Z | https://github.com/eclipse-hawkbit/hawkbit/issues/1067 | 783,135,215 | 1,067 | 1,638 |
CVE-2020-23522 | 2021-01-19T13:15:11.963 | Pixelimity 1.0 has cross-site request forgery via the admin/setting.php data [Password] parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/161276/Pixelimity-1.0-Cross-Site-Request-Forgery.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pixelimity:pixelimity:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1F0EADD1-0D88-4392-A4EF-B273DA08E9AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"352"
] | 352 | https://github.com/pixelimity/pixelimity/issues/20 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pixelimity",
"pixelimity"
] | Affected software: Pixelimity CMS
Type of vulnerability: CSRF (Cross-Site Request Forgery)
Version : v1.0
Discovered by: Noth
Author: Noth
Description:
Pixelimity CMS is vulnerable to persistent Cross-Site Request Forgery attacks, which allow malicious users to inject HTML or scripts and forge user pe... | CSRF Vulnerability V1.0 | https://api.github.com/repos/pixelimity/pixelimity/issues/20/comments | 1 | 2020-06-02T17:11:23Z | 2020-07-27T14:38:14Z | https://github.com/pixelimity/pixelimity/issues/20 | 629,370,184 | 20 | 1,639 |
CVE-2020-28481 | 2021-01-19T15:15:12.060 | The package socket.io before 2.4.0 are vulnerable to Insecure Defaults due to CORS Misconfiguration. All domains are whitelisted by default. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/socketio/socket.io/issues/3671"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://snyk.io/vuln/SNYK-JAVA-ORGWEBJARSBOWER-10... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:socket:socket.io:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "C44F71AC-EC7A-4F4A-A047-841D2BFA3E08",
"versionEndExcluding": "2.4.0",
"versionEndIncluding": null,
"versionStart... | [
"346"
] | 346 | https://github.com/socketio/socket.io/issues/3671 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"socketio",
"socket.io"
] | **Note:** This issue was originally reported to https://try.nodebb.org but as per them this issue has to be fixed by you guys, thus raising it here. The details which was shared with them is given below:
While testing https://try.nodebb.org I found a security issue at socket.io endpoint, description for the same i... | CORS Misconfiguration in socket.io | https://api.github.com/repos/socketio/socket.io/issues/3671/comments | 7 | 2020-10-29T20:20:39Z | 2021-01-05T09:04:55Z | https://github.com/socketio/socket.io/issues/3671 | 732,631,646 | 3,671 | 1,640 |
CVE-2021-20190 | 2021-01-19T17:15:13.427 | A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 8.3,
"confidentialityImpact": "PARTI... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1916633"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "92CF0272-B961-44D2-95F6-162A23169E1D",
"versionEndExcluding": "2.6.7.5",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2854 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) has been reported regarding a class(es) of JDK Swing.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2021-20190 (see https://nvd.nist.gov/vuln/detail/CVE-2021-20190)
Reporter(s... | Block one more gadget type (javax.swing, CVE-2020-20190) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2854/comments | 0 | 2020-09-16T15:32:43Z | 2023-01-12T04:03:45Z | https://github.com/FasterXML/jackson-databind/issues/2854 | 702,866,300 | 2,854 | 1,641 |
CVE-2020-8554 | 2021-01-21T17:15:13.843 | Kubernetes API server in all versions allow an attacker who is able to create a ClusterIP service and set the spec.externalIPs field, to intercept traffic to that IP address. Additionally, an attacker who is able to patch the status (which is considered a privileged operation and should not typically be granted to user... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/97076"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "044D3402-749F-4BEA-9F7E-16F7839654FE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"283"
] | 283 | https://github.com/kubernetes/kubernetes/issues/97076 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: **Medium** ([CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:L](https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:L))
This issue affects multitenant clusters. If a potential attacker can already create or edit services and pods, then they may be able to intercept traffic f... | CVE-2020-8554: Man in the middle using LoadBalancer or ExternalIPs | https://api.github.com/repos/kubernetes/kubernetes/issues/97076/comments | 36 | 2020-12-04T20:02:15Z | 2021-12-14T21:23:22Z | https://github.com/kubernetes/kubernetes/issues/97076 | 757,368,290 | 97,076 | 1,642 |
CVE-2020-8567 | 2021-01-21T17:15:14.063 | Kubernetes Secrets Store CSI Driver Vault Plugin prior to v0.0.6, Azure Plugin prior to v0.0.10, and GCP Plugin prior to v0.2.0 allow an attacker who can create specially-crafted SecretProviderClass objects to write to arbitrary file paths on the host filesystem, including /var/lib/kubelet/pods. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes-sigs/secrets-store-csi-driver/issues/384"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:secret_manager_provider_for_secret_store_csi_driver:*:*:*:*:*:kubernetes:*:*",
"matchCriteriaId": "FF1065B6-815D-49AC-9071-2366DFD8918C",
"versionEndExcluding": "0.2.0",
"versionE... | [
"22"
] | 22 | https://github.com/kubernetes-sigs/secrets-store-csi-driver/issues/384 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes-sigs",
"secrets-store-csi-driver"
] | CVSS Rating: Medium(4.9) [CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:C/C:N/I:L/A:L](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:C/C:N/I:L/A:L)
Specially crafted `SecretProviderClass` can write to arbitrary file paths on the host filesystem, including `/var/lib/kubelet/pods`.
## Am I vulnerable?
... | CVE-2020-8567: Plugin directory traversals | https://api.github.com/repos/kubernetes-sigs/secrets-store-csi-driver/issues/384/comments | 2 | 2020-11-16T17:36:27Z | 2020-11-16T17:46:40Z | https://github.com/kubernetes-sigs/secrets-store-csi-driver/issues/384 | 744,029,690 | 384 | 1,643 |
CVE-2020-8568 | 2021-01-21T17:15:14.157 | Kubernetes Secrets Store CSI Driver versions v0.0.15 and v0.0.16 allow an attacker who can modify a SecretProviderClassPodStatus/Status resource the ability to write content to the host filesystem and sync file contents to Kubernetes Secrets. This includes paths under var/lib/kubelet/pods that contain other Kubernetes ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes-sigs/secrets-store-csi-driver/issues/378"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:secrets_store_csi_driver:0.0.15:*:*:*:*:*:*:*",
"matchCriteriaId": "5567203F-A177-45D9-B39F-6AC0911958AD",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"22"
] | 22 | https://github.com/kubernetes-sigs/secrets-store-csi-driver/issues/378 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes-sigs",
"secrets-store-csi-driver"
] | CVSS Rating: Medium(5.8) [CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:N/A:N](https://www.first.org/cvss/calculator/3.1#CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:N/A:N)
Modification of `SecretProviderClassPodStatus/Status` resource could result in writing content to the host filesystem and syncing file contents to Kubernetes... | CVE-2020-8568: Secrets sync/rotate directory traversal | https://api.github.com/repos/kubernetes-sigs/secrets-store-csi-driver/issues/378/comments | 2 | 2020-11-10T23:10:13Z | 2020-11-14T01:48:21Z | https://github.com/kubernetes-sigs/secrets-store-csi-driver/issues/378 | 740,309,251 | 378 | 1,644 |
CVE-2020-8569 | 2021-01-21T17:15:14.250 | Kubernetes CSI snapshot-controller prior to v2.1.3 and v3.0.2 could panic when processing a VolumeSnapshot custom resource when: - The VolumeSnapshot referenced a non-existing PersistentVolumeClaim and the VolumeSnapshot did not reference any VolumeSnapshotClass. - The snapshot-controller crashes, is automatically rest... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes-csi/external-snapshotter/issues/380"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:container_storage_interface_snapshotter:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1609D4D8-E5EF-418C-B81E-22066045A439",
"versionEndExcluding": "2.1.3",
"versionEndIncluding": nul... | [
"476"
] | 476 | https://github.com/kubernetes-csi/external-snapshotter/issues/380 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"kubernetes-csi",
"external-snapshotter"
] | When taking a snapshot of a non-existing PVC, snapshot controller panics:
```
E0929 06:42:38.147021 1 snapshot_controller_base.go:338] checkAndUpdateSnapshotClass failed to setDefaultClass the snapshot source PVC name is not specified
E0929 06:42:38.147118 1 runtime.go:78] Observed a panic: "invalid me... | snapshot-controller panics when source PVC does not exist | https://api.github.com/repos/kubernetes-csi/external-snapshotter/issues/380/comments | 1 | 2020-09-29T13:00:51Z | 2020-09-30T19:52:56Z | https://github.com/kubernetes-csi/external-snapshotter/issues/380 | 711,090,028 | 380 | 1,645 |
CVE-2020-8570 | 2021-01-21T17:15:14.327 | Kubernetes Java client libraries in version 10.0.0 and versions prior to 9.0.1 allow writes to paths outside of the current directory when copying multiple files from a remote pod which sends a maliciously crafted archive. This can potentially overwrite any files on the system of the process executing the client code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes-client/java/issues/1491"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:java:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CDE8B8B0-BFEA-4097-B229-633ED83338B4",
"versionEndExcluding": "9.0.2",
"versionEndIncluding": null,
"versionStartExcludi... | [
"22"
] | 22 | https://github.com/kubernetes-client/java/issues/1491 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes-client",
"java"
] | There is a defect in the copy implementation in `Copy.java` that was fixed in #1450
The summary of the issue is that you copy a file from a malicious pod with a specially crafted tarball, it may extract to any file that your user has permission to write.
This issue was fixed in release `9.0.2`, `10.0.1` and `11.... | CVE-2020-8570: Path Traversal bug in the Java Kubernetes Client | https://api.github.com/repos/kubernetes-client/java/issues/1491/comments | 1 | 2021-01-11T23:09:47Z | 2021-03-15T01:23:24Z | https://github.com/kubernetes-client/java/issues/1491 | 783,772,361 | 1,491 | 1,646 |
CVE-2021-21259 | 2021-01-22T17:15:12.867 | HedgeDoc is open source software which lets you create real-time collaborative markdown notes. In HedgeDoc before version 1.7.2, an attacker can inject arbitrary JavaScript into a HedgeDoc note, which is executed when the note is viewed in slide mode. Depending on the configuration of the instance, the attacker may not... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/hackmdio/codimd/issues/1648"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hedgedoc:hedgedoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6EF4EA31-5B63-4C26-A744-E8A8B03D8DEC",
"versionEndExcluding": "1.7.2",
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/hackmdio/codimd/issues/1648 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"hackmdio",
"codimd"
] | There is a (quite convoluted) stored XSS vulnerability in the slides feature:
- The presentation's YAML options allow specifying JavaScript files as dependencies. Any JS file specified by the `dependency` option is loaded and executed (when viewed via the presentation mode, `/p/...`), subject to the server's CSP an... | Stored XSS in slide mode (via reveal-markdown) | https://api.github.com/repos/hackmdio/codimd/issues/1648/comments | 0 | 2021-01-13T11:01:12Z | 2021-01-25T08:50:24Z | https://github.com/hackmdio/codimd/issues/1648 | 785,005,148 | 1,648 | 1,647 |
CVE-2020-28487 | 2021-01-22T18:15:12.517 | This affects the package vis-timeline before 7.4.4. An attacker with the ability to control the items of a Timeline element can inject additional script code into the generated application. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/visjs/vis-timeline/issues/838"
},
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/visjs/vis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:visjs:vis-timeline:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "FF25E313-3368-4ED4-945A-E568DA016BFA",
"versionEndExcluding": "7.4.4",
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/visjs/vis-timeline/issues/838 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"visjs",
"vis-timeline"
] | @yotamberk For details about this issue see email. | Security Cleanup | https://api.github.com/repos/visjs/vis-timeline/issues/838/comments | 4 | 2020-12-18T11:09:53Z | 2021-04-27T07:36:55Z | https://github.com/visjs/vis-timeline/issues/838 | 770,798,704 | 838 | 1,648 |
CVE-2020-21146 | 2021-01-26T18:15:42.037 | Feehi CMS 2.0.8 is affected by a cross-site scripting (XSS) vulnerability. When the user name is inserted as JavaScript code, browsing the post will trigger the XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/43"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehi_cms:2.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "17D944DF-8EBC-468F-BDA9-CC930094EAD4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/liufee/cms/issues/43 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | This is a Cross Site Scripting vulnerability. When the user name is <script>alert(1)<script> or js code, the pop-up alert will be triggered when browsing the post. Details are as follows:
POC example:
registered:
```
POST /index.php?r=site%2Fsignup HTTP/1.1
Host: demo.cms.feehi.com
Content-Length: 283
Cache-... | XSS vulnerability in feehicms v2.0.8 | https://api.github.com/repos/liufee/cms/issues/43/comments | 1 | 2019-11-01T10:27:58Z | 2019-11-03T14:55:45Z | https://github.com/liufee/cms/issues/43 | 516,032,979 | 43 | 1,649 |
CVE-2020-22643 | 2021-01-26T18:15:42.160 | Feehi CMS 2.1.0 is affected by an arbitrary file upload vulnerability, potentially resulting in remote code execution. After an administrator logs in, open the administrator image upload page to potentially upload malicious files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/liufee/cms/issues/51"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:feehi:feehi_cms:2.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "A793CD95-EEE8-408B-808B-F8EF860AF4AE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/liufee/cms/issues/51 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"liufee",
"cms"
] | 1. The administrator will use the beforSave function in the /common/models/AdminUser.php file to modify the avatar.
This function will call Util's handleModelSingleFileUpload function

2. We continue to use the ... | 后台头像管理模块存在任意文件上传getshell | https://api.github.com/repos/liufee/cms/issues/51/comments | 1 | 2020-03-27T10:09:42Z | 2020-04-07T01:20:25Z | https://github.com/liufee/cms/issues/51 | 589,023,361 | 51 | 1,650 |
CVE-2020-23262 | 2021-01-26T18:15:42.520 | An issue was discovered in ming-soft MCMS v5.0, where a malicious user can exploit SQL injection without logging in through /mcms/view.do. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ming-soft/MCMS/issues/45"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mingsoft:mcms:5.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9DF05EFA-0CE0-4BEB-A7B7-35775CD6EB9B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"89"
] | 89 | https://github.com/ming-soft/MCMS/issues/45 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ming-soft",
"MCMS"
] | The vulnerable query is in IContentDao.xml .
src/main/java/net/mingsoft/cms/dao/IContentDao.xml:
```xml
<!-- 根据站点编号、开始、结束时间和栏目编号查询文章编号集合 -->
<select id="queryIdsByCategoryIdForParser" resultMap="resultBean">
select
cms_content.id article_id,c.*
FROM cms_content
LEFT JOIN cms_category c ON content_c... | Security issue - SQL injection in /mcms/view.do | https://api.github.com/repos/ming-soft/MCMS/issues/45/comments | 1 | 2020-05-12T14:03:18Z | 2020-09-10T06:45:51Z | https://github.com/ming-soft/MCMS/issues/45 | 616,683,265 | 45 | 1,651 |
CVE-2020-23447 | 2021-01-26T18:15:42.660 | newbee-mall 1.0 is affected by cross-site scripting in shop-cart/settle. Users only need to write xss payload in their address information when buying goods, which is triggered when viewing the "View Recipient Information" of this order in "Order Management Office". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/newbee-ltd/newbee-mall/issues/33"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:newbee-mall_project:newbee-mall:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2D0A6046-1A4C-488F-B8BF-6E0A3A50E5DC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"79"
] | 79 | https://github.com/newbee-ltd/newbee-mall/issues/33 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"newbee-ltd",
"newbee-mall"
] | 1、Build an environment to simulate users selecting products at the front desk——add to cart——confirm order-pay:
http://127.0.0.1:28089/shop-cart/settle
Insert the payload here at the harvest information:
<script> alert (document.cookie) </ script>

2、The corresponding code is as follows:
).
I build openjpeg with ASAN, this is ASAN report.
POC picture : 
https://revive.com/www/delivery/ck.php?oadest=https://evil.com -> it will be redirect to url destination
we read this url https://packetstormsecurity.com/files/152671/REVIVE-SA-2019-001.txt
that we should upgrade version, but this bug (as we thin... | open redirect (oadest url) ck.php revive 4.2.1 | https://api.github.com/repos/revive-adserver/revive-adserver/issues/1068/comments | 4 | 2019-06-24T06:42:33Z | 2020-12-23T09:06:10Z | https://github.com/revive-adserver/revive-adserver/issues/1068 | 459,716,086 | 1,068 | 1,656 |
CVE-2021-25863 | 2021-01-26T18:16:21.850 | Open5GS 2.1.3 listens on 0.0.0.0:3000 and has a default password of 1423 for the admin account. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 8.3,
"confidentialityImpact": ... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/open5gs/open5gs/issues/764"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:open5gs:open5gs:2.1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "4DF29C51-0BC2-4C66-9AF7-E22CD138D6FF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"287"
] | 287 | https://github.com/open5gs/open5gs/issues/764 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"open5gs",
"open5gs"
] | ## Details
The configuration of `webui` might result in the control panel being taken over by arbitrary user via default username and password.
The lines of code below indicate that, if not specified, the server will listen on `0.0.0.0:3000`, which means the control panel could be accessed via WAN.
```
https:/... | Security flaw in default configuration of webui | https://api.github.com/repos/open5gs/open5gs/issues/764/comments | 10 | 2021-01-15T11:49:05Z | 2023-03-21T22:36:27Z | https://github.com/open5gs/open5gs/issues/764 | 786,835,811 | 764 | 1,657 |
CVE-2021-25864 | 2021-01-26T18:16:21.897 | node-red-contrib-huemagic 3.0.0 is affected by hue/assets/..%2F Directory Traversal.in the res.sendFile API, used in file hue-magic.js, to fetch an arbitrary file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/Foddy/node-red-contrib-huemagic/issues/217"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Mitigation",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dgtl:huemagic:3.0.0:*:*:*:*:node.js:*:*",
"matchCriteriaId": "34B7DCCF-571F-4971-B41A-7B83E207C803",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"22"
] | 22 | https://github.com/Foddy/node-red-contrib-huemagic/issues/217 | [
"Exploit",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"Foddy",
"node-red-contrib-huemagic"
] | **Describe the bug**
The `res.sendFile` API, used in file `hue-magic.js`, introduces a `Path Traversal` vulnerability.
https://github.com/Foddy/node-red-contrib-huemagic/blob/4cb9d2e32bd4fcbf7b04642bbcc80cdc2f3356dd/huemagic/hue-magic.js#L277
**Flow to Reproduce**
Since the path isn't protected by `RED.auth.... | Security bug in hue-magic.js | https://api.github.com/repos/Foddy/node-red-contrib-huemagic/issues/217/comments | 1 | 2021-01-17T11:35:47Z | 2022-01-09T20:01:00Z | https://github.com/Foddy/node-red-contrib-huemagic/issues/217 | 787,686,627 | 217 | 1,658 |
CVE-2021-3195 | 2021-01-26T18:16:28.427 | bitcoind in Bitcoin Core through 0.21.0 can create a new file in an arbitrary directory (e.g., outside the ~/.bitcoin directory) via a dumpwallet RPC call. NOTE: this reportedly does not violate the security model of Bitcoin Core, but can violate the security model of a fork that has implemented dumpwallet restrictions | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bitcoin/bitcoin/issues/20866"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bitcoin:bitcoin_core:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1F64E80F-21E7-4CCB-B18C-439B8864BAE5",
"versionEndExcluding": null,
"versionEndIncluding": "0.21.0",
"versionStartE... | [
"20"
] | 20 | https://github.com/bitcoin/bitcoin/issues/20866 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bitcoin",
"bitcoin"
] | Currently `dumpwallet` (and other RPCs that create server-side files) can scribble all over the file system, at least as the user running `bitcoind` permits.
It would be better if these were at the least limited to the data directory, or even a specific directory within the data directory, say, `~/.bitcoin/dumpwalle... | Restrict RPCs that make server-side files | https://api.github.com/repos/bitcoin/bitcoin/issues/20866/comments | 20 | 2021-01-06T10:39:23Z | 2025-05-16T08:30:42Z | https://github.com/bitcoin/bitcoin/issues/20866 | 780,450,193 | 20,866 | 1,659 |
CVE-2021-3223 | 2021-01-26T18:16:28.757 | Node-RED-Dashboard before 2.26.2 allows ui_base/js/..%2f directory traversal to read files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/node-red/node-red-dashboard/issues/669"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/node-red/node-red-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nodered:node-red-dashboard:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "F56DC439-AA58-48A1-9FE7-33422246B5DA",
"versionEndExcluding": "2.26.2",
"versionEndIncluding": null,
"v... | [
"22"
] | 22 | https://github.com/node-red/node-red-dashboard/issues/669 | [
"Third Party Advisory"
] | github.com | [
"node-red",
"node-red-dashboard"
] | In /nodes/ui_base.js, the URL is matched with'/ui_base/js/*' and then passed to path.join,
The lack of verification of the final path leads to a path traversal vulnerability.
We can use this vulnerability to read sensitive data on the server, such as settings.js.
### What are the steps to reproduce?
1. Instal... | Path traversal | https://api.github.com/repos/node-red/node-red-dashboard/issues/669/comments | 0 | 2021-01-11T04:39:02Z | 2021-01-11T12:00:39Z | https://github.com/node-red/node-red-dashboard/issues/669 | 783,057,647 | 669 | 1,660 |
CVE-2021-3286 | 2021-01-26T18:16:29.567 | SQL injection exists in Spotweb 1.4.9 because the notAllowedCommands protection mechanism is inadequate, e.g., a variation of the payload may be used. NOTE: this issue exists because of an incomplete fix for CVE-2020-35545. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/spotweb/spotweb/issues/653"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:spotweb_project:spotweb:1.4.9:*:*:*:*:*:*:*",
"matchCriteriaId": "F2CE0FCC-C8CF-4C39-A8D7-C0799862E585",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"89"
] | 89 | https://github.com/spotweb/spotweb/issues/653 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"spotweb",
"spotweb"
] | **Describe the bug/issue**
Hi, I'm part of the Debian LTS Team and I'm investigating CVE-2020-35545, reported under #629, describes an SQL injection.
The fix from fefb39ad143caad021ad496427617db79c42aff2 / 25c1f89f0202af5d5d224b906ff9d9313f017aa6 introduces a black list and a regex to attempt to filter out the malici... | CVE-2021-3286 - SQL injection incomplete fix | https://api.github.com/repos/spotweb/spotweb/issues/653/comments | 12 | 2021-01-21T18:18:48Z | 2022-02-03T14:58:51Z | https://github.com/spotweb/spotweb/issues/653 | 791,388,318 | 653 | 1,661 |
CVE-2021-3309 | 2021-01-26T21:15:13.063 | packages/wekan-ldap/server/ldap.js in Wekan before 4.87 can process connections even though they are not authorized by the Certification Authority trust store, | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wekan/wekan/issues/3482"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wekan_project:wekan:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FD5D1800-99E6-4E68-B5B9-B22CF9E6CCE3",
"versionEndExcluding": "4.87",
"versionEndIncluding": null,
"versionStartExcl... | [
"295"
] | 295 | https://github.com/wekan/wekan/issues/3482 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wekan",
"wekan"
] | As of writing, Wekan disables the SSL/TLS certificate validation for LDAP by default [unless `LDAP_REJECT_UNAUTHORIZED=true`](https://github.com/wekan/wekan/blob/master/packages/wekan-ldap/server/ldap.js#L22) is explicitly set. Thus, by default, Wekan is effectively vulnerable to MITM attacks, even when using SSL/TLS f... | Security: SSL/TLS certificate validation for LDAP disabled by default | https://api.github.com/repos/wekan/wekan/issues/3482/comments | 5 | 2021-01-25T22:42:05Z | 2021-02-02T23:31:24Z | https://github.com/wekan/wekan/issues/3482 | 793,779,879 | 3,482 | 1,662 |
CVE-2020-23774 | 2021-01-26T22:15:11.887 | A reflected XSS vulnerability exists in tohtml/convert.php of Winmail 6.5, which can cause JavaScript code to be executed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zhonghaozhao/winmail/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:winmail_project:winmail:6.5:*:*:*:*:*:*:*",
"matchCriteriaId": "AAEB4B7E-9C6C-4319-9A6D-A6E60594E96A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/zhonghaozhao/winmail/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zhonghaozhao",
"winmail"
] | #### Reflected XSS Vulnerability exists in the file of Winmail 6.5, which can cause javascript code executed
[winmail_xss.docx](https://github.com/zhonghaozhao/winmail/files/4841596/winmail_xss.docx)
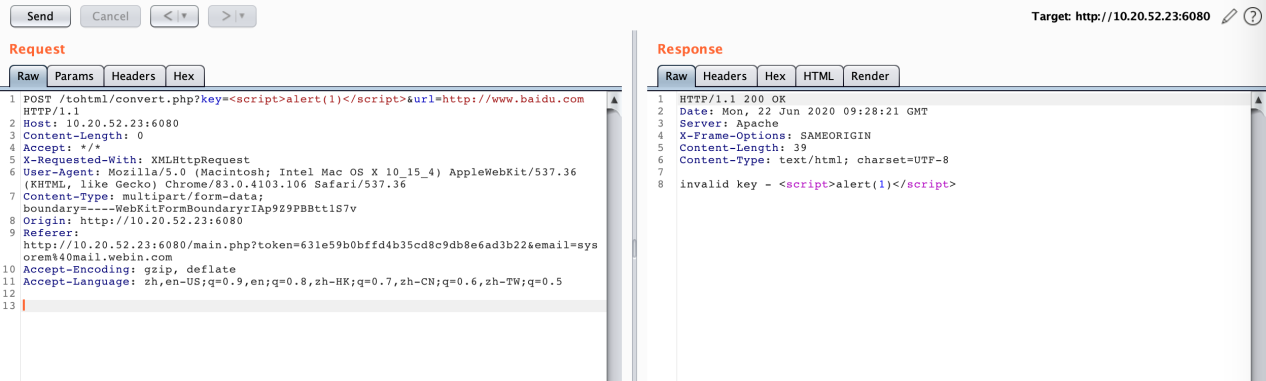
![图片2]... | Reflected XSS Vulnerability exists in the file of Winmail 6.5, which can cause javascript code executed | https://api.github.com/repos/zhonghaozhao/winmail/issues/2/comments | 0 | 2020-06-28T02:42:40Z | 2020-06-28T02:42:40Z | https://github.com/zhonghaozhao/winmail/issues/2 | 646,819,924 | 2 | 1,663 |
CVE-2020-23776 | 2021-01-26T22:15:11.950 | A SSRF vulnerability exists in Winmail 6.5 in app.php in the key parameter when HTTPS is on. An attacker can use this vulnerability to cause the server to send a request to a specific URL. An attacker can modify the request header 'HOST' value to cause the server to send the request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zhonghaozhao/winmail/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:winmail_project:winmail:6.5:*:*:*:*:*:*:*",
"matchCriteriaId": "AAEB4B7E-9C6C-4319-9A6D-A6E60594E96A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"918"
] | 918 | https://github.com/zhonghaozhao/winmail/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zhonghaozhao",
"winmail"
] | SSRF Vulnerability exists in the file of Winmail 6.5 when HTTPS is on
The attacker can use this vulnerability to cause the server send the request to the specific url.
[winmail_ssrf.docx](https://github.com/zhonghaozhao/winmail/files/4850745/winmail_ssrf.docx)
| SSRF Vulnerability exists in the file of Winmail 6.5 when HTTPS is on | https://api.github.com/repos/zhonghaozhao/winmail/issues/3/comments | 0 | 2020-06-30T09:17:45Z | 2020-06-30T09:17:45Z | https://github.com/zhonghaozhao/winmail/issues/3 | 648,012,188 | 3 | 1,664 |
CVE-2021-3272 | 2021-01-27T08:15:10.483 | jp2_decode in jp2/jp2_dec.c in libjasper in JasPer 2.0.24 has a heap-based buffer over-read when there is an invalid relationship between the number of channels and the number of image components. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jasper-software/jasper/issues/259"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-an... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jasper_project:jasper:2.0.24:*:*:*:*:*:*:*",
"matchCriteriaId": "E84A82E5-EB56-4E02-9880-D1FC90E9DB9A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"125"
] | 125 | https://github.com/jasper-software/jasper/issues/259 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jasper-software",
"jasper"
] | I found a heap buffer overflow vulnerability in the current master branch (release version 2.0.24)
poc file : [hoob_8.zip](https://github.com/jasper-software/jasper/files/5774086/hoob_8.zip)
ASAN report
```
appl git:(master) ✗ ./jasper --input ../../../hoob_8 --output test.jp2
warning: not enough tile data (25 b... | Heap buffer overflow in libjasper/jp2/jp2_dec.c:434:4 | https://api.github.com/repos/jasper-software/jasper/issues/259/comments | 1 | 2021-01-06T05:48:40Z | 2021-01-27T08:49:39Z | https://github.com/jasper-software/jasper/issues/259 | 780,074,381 | 259 | 1,665 |
CVE-2020-23359 | 2021-01-27T16:15:13.013 | WeBid 1.2.2 admin/newuser.php has an issue with password rechecking during registration because it uses a loose comparison to check the identicalness of two passwords. Two non-identical passwords can still bypass the check. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/renlok/WeBid/issues/530"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webidsupport:webid:1.2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6C5E4CA0-910D-4E6C-AAAA-7487B5F0AECE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"697"
] | 697 | https://github.com/renlok/WeBid/issues/530 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"renlok",
"WeBid"
] | WeBid 1.2.2 has the problem of password rechecking during registration because it uses a loose comparison to check the identicalness of two passwords. Two non-identical passwords can still bypass the check. `$password1 = "0e1111"` and `$password2 = "0e2222"` are loosely compared and return `bool(true)`. A lot of other... | Funcational bugs in password rechecking during registration related processes | https://api.github.com/repos/renlok/WeBid/issues/530/comments | 0 | 2020-05-25T08:11:30Z | 2020-05-25T08:17:56Z | https://github.com/renlok/WeBid/issues/530 | 624,126,116 | 530 | 1,666 |
CVE-2020-23360 | 2021-01-27T16:15:13.060 | oscommerce v2.3.4.1 has a functional problem in user registration and password rechecking, where a non-identical password can bypass the checks in /catalog/admin/administrators.php and /catalog/password_reset.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/osCommerce/oscommerce2/issues/658"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:oscommerce:oscommerce:2.3.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "3D8A496B-7F43-478C-8A75-C3CF3688067C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"697"
] | 697 | https://github.com/osCommerce/oscommerce2/issues/658 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"osCommerce",
"oscommerce2"
] | Hi,
I just find that, in many places of oscommerce v2.3.4.1, the username and password recheck during registration and other processes can be bypassed easily through the `magic string` in loose comparison, for example `"0e11111" == "0e22222"` returns `Bool(True)`. If the user sets the username or password to such m... | Username and password recheck bypassed | https://api.github.com/repos/osCommerce/oscommerce2/issues/658/comments | 0 | 2020-05-26T05:59:06Z | 2023-02-21T10:31:28Z | https://github.com/osCommerce/oscommerce2/issues/658 | 624,620,472 | 658 | 1,667 |
CVE-2021-3318 | 2021-01-27T18:15:14.150 | attach/ajax.php in DzzOffice through 2.02.1 allows XSS via the editorid parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162314/DzzOffice-2.02.1-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dzzoffice:dzzoffice:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A7BB379C-21F1-4859-9305-6C3C0686CA07",
"versionEndExcluding": null,
"versionEndIncluding": "2.02.1",
"versionStartEx... | [
"79"
] | 79 | https://github.com/zyx0814/dzzoffice/issues/173 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zyx0814",
"dzzoffice"
] | There is a potential XSS vulnerability in dzz/attach/ajax.php using the 'editorid' parameter.
| Potential XSS Vulnerability | https://api.github.com/repos/zyx0814/dzzoffice/issues/173/comments | 0 | 2021-01-27T12:58:49Z | 2021-01-27T12:58:49Z | https://github.com/zyx0814/dzzoffice/issues/173 | 795,079,764 | 173 | 1,668 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.