cve_id stringlengths 13 16 | cve_published stringdate 2019-01-01 16:29:00 2025-02-25 20:15:37 | cve_descriptions stringlengths 34 2.6k | cve_metrics dict | cve_references listlengths 1 281 | cve_configurations listlengths 1 70 | cve_cwe_list listlengths 1 1 | cve_primary_cwe stringclasses 164
values | url stringlengths 36 97 | cve_tags listlengths 1 5 ⌀ | domain stringclasses 1
value | issue_owner_repo listlengths 2 2 | issue_body stringlengths 0 198k ⌀ | issue_title stringlengths 1 335 | issue_comments_url stringlengths 55 116 | issue_comments_count int64 0 338 | issue_created_at stringdate 2012-06-06 09:34:24 2025-04-02 09:37:20 | issue_updated_at stringdate 2014-04-01 20:16:21 2025-06-16 12:26:58 | issue_html_url stringlengths 36 97 | issue_github_id int64 4.93M 2.97B | issue_number int64 1 199k | __index_level_0__ int64 0 6.55k |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2014-2906 | 2020-01-28T16:15:12.133 | The psub function in fish (aka fish-shell) 1.16.0 before 2.1.1 does not properly create temporary files, which allows local users to execute arbitrary commands via a temporary file with a predictable name. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.4,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2014/04/28/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/fish-shell/fish-shell... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fishshell:fish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "97A46CC4-CAF5-4ECB-8025-5FC5AC4068EA",
"versionEndExcluding": "2.1.1",
"versionEndIncluding": null,
"versionStartExcludin... | [
"362"
] | 362 | https://github.com/fish-shell/fish-shell/issues/1437 | [
"Third Party Advisory"
] | github.com | [
"fish-shell",
"fish-shell"
] | `psub` and `funced` both create temporary files using reasonably predictable names and are vulnerable to a race condition.
For `funced`, the file is sourced directly, allowing privilege escalation (CVE-2014-3856).
For `psub`, the file is given as an argument to other programs, allowing incorrect input to these progra... | psub and funced don't protect tempfiles (CVE-2014-2906 and CVE-2014-3856) | https://api.github.com/repos/fish-shell/fish-shell/issues/1437/comments | 0 | 2014-04-28T02:42:09Z | 2020-04-19T02:03:40Z | https://github.com/fish-shell/fish-shell/issues/1437 | 32,327,861 | 1,437 | 1,044 |
CVE-2014-2914 | 2020-01-28T16:15:12.197 | fish (aka fish-shell) 2.0.0 before 2.1.1 does not restrict access to the configuration service (aka fish_config), which allows remote attackers to execute arbitrary code via unspecified vectors, as demonstrated by set_prompt. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2014/04/28/4"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/fish-shell/fish-shell... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fishshell:fish:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8DF37E4B-7053-4B60-AFA9-A364954804C9",
"versionEndExcluding": "2.1.1",
"versionEndIncluding": null,
"versionStartExcludin... | [
"20"
] | 20 | https://github.com/fish-shell/fish-shell/issues/1438 | [
"Third Party Advisory"
] | github.com | [
"fish-shell",
"fish-shell"
] | Before 6d749789ce and 44b35f773 anyone\* could connect to a running fish_config server and send code to (e.g.) set_prompt, which is obviously bad.
That's been clamped down to localhost-only now, which helps, but it's still possible for someone on your local machine to wait for you to start fish_config and then talk to... | Restrict fish_config socket connections (CVE-2014-2914) | https://api.github.com/repos/fish-shell/fish-shell/issues/1438/comments | 6 | 2014-04-28T02:43:07Z | 2020-04-19T03:03:23Z | https://github.com/fish-shell/fish-shell/issues/1438 | 32,327,897 | 1,438 | 1,045 |
CVE-2020-8112 | 2020-01-28T18:15:11.743 | opj_t1_clbl_decode_processor in openjp2/t1.c in OpenJPEG 2.3.1 through 2020-01-28 has a heap-based buffer overflow in the qmfbid==1 case, a different issue than CVE-2020-6851. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2020:0550"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://access.redhat.com/errata/RHSA-2020:0569"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://access.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uclouvain:openjpeg:2.3.1:*:*:*:*:*:*:*",
"matchCriteriaId": "22C33617-4369-4A1B-9C49-27BAE05D8BAE",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"787"
] | 787 | https://github.com/uclouvain/openjpeg/issues/1231 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"uclouvain",
"openjpeg"
] | Hi,
This overflow looks similar to #1228 but still works on latest master (b63a433ba168bad5fa10e83de04d6305e6a222e2):
```
$ build_afl/bin/opj_decompress -i ../openjpeg/afl_symcc_5_out/afl-slave/crashes/id:000000,sig:06,sync:symcc,src:002975 -o /tmp/image_verification.pgm
====================================... | Another heap buffer overflow in libopenjp2 | https://api.github.com/repos/uclouvain/openjpeg/issues/1231/comments | 2 | 2020-01-28T11:05:53Z | 2020-01-30T12:28:26Z | https://github.com/uclouvain/openjpeg/issues/1231 | 556,135,856 | 1,231 | 1,046 |
CVE-2019-20444 | 2020-01-29T21:15:11.047 | HttpObjectDecoder.java in Netty before 4.1.44 allows an HTTP header that lacks a colon, which might be interpreted as a separate header with an incorrect syntax, or might be interpreted as an "invalid fold." | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0497"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0567"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netty:netty:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3D374B9C-E87A-47F2-AF0C-25D2A6D03E89",
"versionEndExcluding": "4.1.44",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"444"
] | 444 | https://github.com/netty/netty/issues/9866 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"netty",
"netty"
] | ### Expected behavior
Netty shouldn't allow the invalid fold. According to RFC7230, https://tools.ietf.org/html/rfc7230#section-3.2.
```
header-field = field-name ":" OWS field-value OWS
field-name = token
field-value = *( field-content / obs-fold )
field-content = field-vchar [ 1*( SP ... | Netty shouldn't allow the invalid fold. | https://api.github.com/repos/netty/netty/issues/9866/comments | 12 | 2019-12-10T12:38:14Z | 2020-02-17T05:11:47Z | https://github.com/netty/netty/issues/9866 | 535,703,297 | 9,866 | 1,047 |
CVE-2019-20445 | 2020-01-29T21:15:11.110 | HttpObjectDecoder.java in Netty before 4.1.44 allows a Content-Length header to be accompanied by a second Content-Length header, or by a Transfer-Encoding header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0497"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0567"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netty:netty:*:*:*:*:*:*:*:*",
"matchCriteriaId": "3D374B9C-E87A-47F2-AF0C-25D2A6D03E89",
"versionEndExcluding": "4.1.44",
"versionEndIncluding": null,
"versionStartExcluding"... | [
"444"
] | 444 | https://github.com/netty/netty/issues/9861 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"netty",
"netty"
] | ### Expected behavior
1.Only accept one Content-Length.RFC 7230 says `duplicate Content-Length header fields have been generated or combined by an upstream message processor, then the recipient MUST either reject the message as invalid or replace the duplicated field-values with a single valid Content-Length`.
2.Only... | Non-proper handling of Content-Length and Transfer-Encoding: chunked headers | https://api.github.com/repos/netty/netty/issues/9861/comments | 24 | 2019-12-09T18:54:41Z | 2020-02-24T09:13:05Z | https://github.com/netty/netty/issues/9861 | 535,148,204 | 9,861 | 1,048 |
CVE-2020-8442 | 2020-01-30T01:15:10.713 | In OSSEC-HIDS 2.7 through 3.5.0, the server component responsible for log analysis (ossec-analysisd) is vulnerable to a heap-based buffer overflow in the rootcheck decoder component via an authenticated client. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1820"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/ossec/ossec-hids/issues/1820 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | The `ossec-analysisd` rootcheck decoder (`src/analysisd/decoders/rootcheck.c`) allocates two fixed size heap buffers via global static vars. One, `rk_agent_ips` is an array of `*char` size `MAX_AGENTS`. The other `rk_agent_fps` is an array of `*FILE`, also size `MAX_AGENTS`. In a default build MAX_AGENTS is 2048.
ht... | CVE-2020-8442: analysisd rootcheck decoder: heap overflow in DB_File. | https://api.github.com/repos/ossec/ossec-hids/issues/1820/comments | 1 | 2020-01-15T21:01:47Z | 2020-01-30T14:35:31Z | https://github.com/ossec/ossec-hids/issues/1820 | 550,427,271 | 1,820 | 1,049 |
CVE-2020-8442 | 2020-01-30T01:15:10.713 | In OSSEC-HIDS 2.7 through 3.5.0, the server component responsible for log analysis (ossec-analysisd) is vulnerable to a heap-based buffer overflow in the rootcheck decoder component via an authenticated client. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1820"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/is... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"787"
] | 787 | https://github.com/ossec/ossec-hids/issues/1821 | [
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | Hi folks,
I spent some free time recently auditing OSSEC. I was primarily focused on a threat model where an OSSEC agent is compromised (e.g. the agent key and assoc. counters are known) and used to attack the OSSEC server (primarily `ossec-remoted` and `ossec-analysisd`). Given the problem domain of OSSEC and HIDS ... | OSSEC-HIDS Security Audit Findings | https://api.github.com/repos/ossec/ossec-hids/issues/1821/comments | 5 | 2020-01-15T21:02:37Z | 2020-10-03T14:29:23Z | https://github.com/ossec/ossec-hids/issues/1821 | 550,427,631 | 1,821 | 1,050 |
CVE-2020-8444 | 2020-01-30T01:15:10.837 | In OSSEC-HIDS 2.7 through 3.5.0, the server component responsible for log analysis (ossec-analysisd) is vulnerable to a use-after-free during processing of ossec-alert formatted msgs (received from authenticated remote agents and delivered to the analysisd processing queue by ossec-remoted). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1817"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1821"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"416"
] | 416 | https://github.com/ossec/ossec-hids/issues/1817 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | The `ossec-analysisd`'s `OS_ReadMSG` function calls `OS_CleanMSG` at the start of processing a received message from the ossec queue UNIX domain socket.
In `src/analysisd/cleanevent.c` the `OS_CleanMSG` function populates the `lf` struct, setting fields like `log`, `hostname` and `program_name` to substrings of the ... | CVE-2020-8444: analysisd: OS_ReadMSG heap use-after-free with ossec-alert msgs. | https://api.github.com/repos/ossec/ossec-hids/issues/1817/comments | 4 | 2020-01-15T21:00:51Z | 2021-03-05T21:04:09Z | https://github.com/ossec/ossec-hids/issues/1817 | 550,426,873 | 1,817 | 1,052 |
CVE-2020-8445 | 2020-01-30T01:15:10.917 | In OSSEC-HIDS 2.7 through 3.5.0, the OS_CleanMSG function in ossec-analysisd doesn't remove or encode terminal control characters or newlines from processed log messages. In many cases, those characters are later logged. Because newlines (\n) are permitted in messages processed by ossec-analysisd, it may be possible to... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 10,
"confidentialityImpact": "COMPLETE"... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1814"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1821"
},
{
"source"... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"20"
] | 20 | https://github.com/ossec/ossec-hids/issues/1814 | [
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | The `ossec-analysisd`'s `OS_CleanMSG` function doesn't remove or encode terminal control characters or newlines from processed log messages. In many cases those control characters/newline are later logged.
There have been cases where allowing arbitrary control characters in log messages has led to command execution ... | CVE-2020-8445: analysisd: OS_CleanMSG allows control characters in msg. | https://api.github.com/repos/ossec/ossec-hids/issues/1814/comments | 1 | 2020-01-15T20:59:57Z | 2020-01-30T14:37:12Z | https://github.com/ossec/ossec-hids/issues/1814 | 550,426,476 | 1,814 | 1,053 |
CVE-2020-8446 | 2020-01-30T01:15:10.993 | In OSSEC-HIDS 2.7 through 3.5.0, the server component responsible for log analysis (ossec-analysisd) is vulnerable to path traversal (with write access) via crafted syscheck messages written directly to the analysisd UNIX domain socket by a local user. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1813"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1821"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"22"
] | 22 | https://github.com/ossec/ossec-hids/issues/1813 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | The `ossec-analysisd`'s syscheck decoder (`src/analysisd/decoders/syscheck.c`) performs unsafe path handling using the received agent name when trying to get the agent file. The `DB_File` function uses the agent name unsanitized when building a file name to be used with `fopen`.
https://github.com/ossec/ossec-hids/b... | CVE-2020-8446: analysisd: syscheck decoder location path injection. | https://api.github.com/repos/ossec/ossec-hids/issues/1813/comments | 1 | 2020-01-15T20:59:40Z | 2020-01-30T14:37:32Z | https://github.com/ossec/ossec-hids/issues/1813 | 550,426,349 | 1,813 | 1,054 |
CVE-2020-8447 | 2020-01-30T01:15:11.070 | In OSSEC-HIDS 2.7 through 3.5.0, the server component responsible for log analysis (ossec-analysisd) is vulnerable to a use-after-free during processing of syscheck formatted msgs (received from authenticated remote agents and delivered to the analysisd processing queue by ossec-remoted). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1818"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1821"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"416"
] | 416 | https://github.com/ossec/ossec-hids/issues/1818 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | The `ossec-analysisd`'s `OS_ReadMSG` function calls `OS_CleanMSG` at the start of processing a message read from the ossec queue UNIX domain socket.
In `src/analysisd/cleanevent.c` the `OS_CleanMSG` function populates the `lf` struct, setting fields like `log`, `hostname` and `program_name` to substrings of the `lf-... | CVE-2020-8447: analysisd: OS_ReadMSG heap use-after-free decoding syscheck msgs. | https://api.github.com/repos/ossec/ossec-hids/issues/1818/comments | 2 | 2020-01-15T21:01:03Z | 2020-01-30T14:35:52Z | https://github.com/ossec/ossec-hids/issues/1818 | 550,426,963 | 1,818 | 1,055 |
CVE-2020-8448 | 2020-01-30T01:15:11.133 | In OSSEC-HIDS 2.7 through 3.5.0, the server component responsible for log analysis (ossec-analysisd) is vulnerable to a denial of service (NULL pointer dereference) via crafted messages written directly to the analysisd UNIX domain socket by a local user. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1815"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ossec/ossec-hids/issues/1821"
},... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:ossec:ossec:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B349E3E6-F70E-41A0-843D-202A82473ABD",
"versionEndExcluding": null,
"versionEndIncluding": "3.5.0",
"versionStartExcluding":... | [
"476"
] | 476 | https://github.com/ossec/ossec-hids/issues/1815 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ossec",
"ossec-hids"
] | In `src/analysisd/cleanevent.c` the `ossec-analysisd`'s `OS_CleanMSG` function handles the location portion of a message differently when the first character after a 2 digit ID is `(`, indicating it came from a remote agent via `ossec-remoted`.
When remote agent locations are processed `OS_CleanMSG` tries to null te... | CVE-2020-8448: analysisd: OS_CleanMSG segfault processing invalid msg location. | https://api.github.com/repos/ossec/ossec-hids/issues/1815/comments | 1 | 2020-01-15T21:00:12Z | 2020-01-30T14:36:54Z | https://github.com/ossec/ossec-hids/issues/1815 | 550,426,613 | 1,815 | 1,056 |
CVE-2020-7218 | 2020-01-31T13:15:10.533 | HashiCorp Nomad and Nonad Enterprise up to 0.10.2 HTTP/RPC services allowed unbounded resource usage, and were susceptible to unauthenticated denial of service. Fixed in 0.10.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/hashicorp/nomad/issues/7002"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://www.hashicorp.com/blog/c... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:nomad:*:*:*:*:-:*:*:*",
"matchCriteriaId": "3997DB3C-4BE4-40DF-A321-3010EAF570A4",
"versionEndExcluding": "0.10.3",
"versionEndIncluding": null,
"versionStartExclud... | [
"770"
] | 770 | https://github.com/hashicorp/nomad/issues/7002 | [
"Issue Tracking",
"Mitigation",
"Third Party Advisory"
] | github.com | [
"hashicorp",
"nomad"
] | **Vulnerability ID:** CVE-2020-7218
**Versions:** Previous versions of Nomad and Nomad Enterprise; fixed in 0.10.3.
A vulnerability was identified in Nomad such that unbounded resource usage, triggered by the establishment of many unauthenticated HTTP or RPC connections, may generate excessive load and/or crash the... | HTTP/RPC Unbounded Resource Usage, Susceptible to Unauthenticated DoS | https://api.github.com/repos/hashicorp/nomad/issues/7002/comments | 1 | 2020-01-28T19:12:17Z | 2022-11-11T02:33:55Z | https://github.com/hashicorp/nomad/issues/7002 | 556,410,311 | 7,002 | 1,057 |
CVE-2020-7219 | 2020-01-31T13:15:10.627 | HashiCorp Consul and Consul Enterprise up to 1.6.2 HTTP/RPC services allowed unbounded resource usage, and were susceptible to unauthenticated denial of service. Fixed in 1.6.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hashicorp/consul/issues/7159"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://www.hashicorp.com/blog/category/consul/"
},
{
"source": "af... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:consul:*:*:*:*:*:*:*:*",
"matchCriteriaId": "860E97FE-158E-4C5E-9FBE-6AD01C64EAC5",
"versionEndExcluding": "1.6.2",
"versionEndIncluding": null,
"versionStartExclud... | [
"770"
] | 770 | https://github.com/hashicorp/consul/issues/7159 | [
"Third Party Advisory"
] | github.com | [
"hashicorp",
"consul"
] | **Vulnerability ID:** CVE-2020-7219
**Release Date:** January 29, 2020
**Affected Products/Versions:** Previous versions of Consul and Consul Enterprise; fixed in 1.6.3.
A vulnerability was identified in Consul and Consul Enterprise (“Consul”) such that unbounded resource usage, triggered by the establishment of m... | HTTP/RPC Services Allow Unbounded Resource Usage, Susceptible to Unauthenticated Denial of Service | https://api.github.com/repos/hashicorp/consul/issues/7159/comments | 0 | 2020-01-28T23:54:20Z | 2020-01-30T18:47:54Z | https://github.com/hashicorp/consul/issues/7159 | 556,558,525 | 7,159 | 1,058 |
CVE-2020-7955 | 2020-01-31T13:15:10.813 | HashiCorp Consul and Consul Enterprise 1.4.1 through 1.6.2 did not uniformly enforce ACLs across all API endpoints, resulting in potential unintended information disclosure. Fixed in 1.6.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hashicorp/consul/issues/7160"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://www.hashicorp.com/blog/category/consul/"
},
{
"source": "af... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:consul:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2E0F3B04-5FA5-48EB-BA4A-E698F6790499",
"versionEndExcluding": "1.6.2",
"versionEndIncluding": null,
"versionStartExclud... | [
"863"
] | 863 | https://github.com/hashicorp/consul/issues/7160 | [
"Third Party Advisory"
] | github.com | [
"hashicorp",
"consul"
] | **Vulnerability ID:** CVE-2020-7955
**Release Date:** January 29, 2020
**Affected Products/Versions:** Previous versions of Consul and Consul Enterprise; fixed in 1.6.3.
A low risk vulnerability was identified in Consul and Consul Enterprise (“Consul”) HTTP API such that the endpoints `v1/agent/health/service/*` d... | Add ACL enforcement to the v1/agent/health/service/* endpoints | https://api.github.com/repos/hashicorp/consul/issues/7160/comments | 0 | 2020-01-28T23:54:33Z | 2020-01-30T18:47:57Z | https://github.com/hashicorp/consul/issues/7160 | 556,558,587 | 7,160 | 1,059 |
CVE-2020-7956 | 2020-01-31T13:15:10.877 | HashiCorp Nomad and Nomad Enterprise up to 0.10.2 incorrectly validated role/region associated with TLS certificates used for mTLS RPC, and were susceptible to privilege escalation. Fixed in 0.10.3. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/hashicorp/nomad/issues/7003"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "https://www.hashicorp.com/blog/category/nomad/"
},
{
"source": "af85... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:hashicorp:nomad:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9AD77DCB-A98E-4BB4-89E6-3984A6617B2C",
"versionEndExcluding": "0.10.3",
"versionEndIncluding": null,
"versionStartExclud... | [
"295"
] | 295 | https://github.com/hashicorp/nomad/issues/7003 | [
"Third Party Advisory"
] | github.com | [
"hashicorp",
"nomad"
] | Vulnerability ID: CVE-2020-7956
Versions: Previous versions of Nomad and Nomad Enterprise; fixed in 0.10.3.
Nomad 0.10.3 includes a fix for a privilege escalation vulnerability in validating TLS certificates for RPC with mTLS. Nomad RPC endpoints validated that TLS client certificates had not expired and were signe... | CVE-2020-7956: Privilege escalation due to incorrect certificate validation for role/region | https://api.github.com/repos/hashicorp/nomad/issues/7003/comments | 1 | 2020-01-28T19:12:39Z | 2022-11-11T02:33:53Z | https://github.com/hashicorp/nomad/issues/7003 | 556,410,504 | 7,003 | 1,060 |
CVE-2020-8440 | 2020-01-31T14:15:12.077 | controllers/page_apply.php in Simplejobscript.com SJS through 1.66 is prone to unauthenticated Remote Code Execution by uploading a PHP script as a resume. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/niteosoft/simplejobscript/issues/10"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simplejobscript:simplejobscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CD8EF221-6FAC-49F7-9589-168A8294E29A",
"versionEndExcluding": null,
"versionEndIncluding": "1.66",
"vers... | [
"434"
] | 434 | https://github.com/niteosoft/simplejobscript/issues/10 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"niteosoft",
"simplejobscript"
] | **Description:** `controllers/page_apply.php` in simplejobscript.com SJS <=1.66 is prone to unauthenticated Remote Code Execution by uploading a PHP script as a resume.
**Environment:**
Version: 1.64
OS: Ubuntu 16.10
Web server: Apache 2.4.18
PHP: 5.6.40
Database: MySQL 5.7.28
URL: `/apply`
**Steps to Rep... | [security] CVE-2020-8440, Unrestricted file upload | https://api.github.com/repos/niteosoft/simplejobscript/issues/10/comments | 2 | 2020-01-19T13:19:49Z | 2020-01-29T22:55:43Z | https://github.com/niteosoft/simplejobscript/issues/10 | 551,921,250 | 10 | 1,061 |
CVE-2011-4116 | 2020-01-31T18:15:11.343 | _is_safe in the File::Temp module for Perl does not properly handle symlinks. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2011/11/04/2"
},
{
"source": "secalert@redhat.com",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cpan:file\\:\\:temp:-:*:*:*:*:*:*:*",
"matchCriteriaId": "E4523EB2-5331-47E5-BE50-1624EF987D81",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"59"
] | 59 | https://github.com/Perl-Toolchain-Gang/File-Temp/issues/14 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"Perl-Toolchain-Gang",
"File-Temp"
] | https://rt.cpan.org/Ticket/Display.html?id=69106
```
Example...
As user "attacker":
ln -s /tmp /tmp/exploit
As user "victim":
perl -MFile::Temp -e 'File::Temp->safe_level(File::Temp::HIGH); print
File::Temp::tempdir("/tmp/exploit/meXXXX") . "\n";'
The temporary directory path that is returned includes the symlink... | File:Temp::_is_safe() allows unsafe traversal of symlinks [rt.cpan.org #69106] | https://api.github.com/repos/Perl-Toolchain-Gang/File-Temp/issues/14/comments | 5 | 2016-04-03T03:41:22Z | 2023-07-09T15:50:06Z | https://github.com/Perl-Toolchain-Gang/File-Temp/issues/14 | 145,448,983 | 14 | 1,062 |
CVE-2020-5234 | 2020-01-31T18:15:11.860 | MessagePack for C# and Unity before version 1.9.11 and 2.1.90 has a vulnerability where untrusted data can lead to DoS attack due to hash collisions and stack overflow. Review the linked GitHub Security Advisory for more information and remediation steps. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 6.8,
"confidentialityImpact": "NONE... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/neuecc/MessagePack-CSharp/commit/56fa86219d01d0a183babbbbcb34abbdea588a02"
},
{
"source": "security-advisories@github.com",
"tags": null,
"url": "https://... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:messagepack:messagepack:*:*:*:*:*:c\\#:*:*",
"matchCriteriaId": "6E3E3D7A-9BC4-4387-9EBD-EE1DEE62266D",
"versionEndExcluding": "1.9.3",
"versionEndIncluding": null,
"versionS... | [
"787"
] | 787 | https://github.com/neuecc/MessagePack-CSharp/issues/810 | null | github.com | [
"neuecc",
"MessagePack-CSharp"
] | When a `MessagePackSecurity` instance is mutated, the copy constructor doesn't initialize its `objectFallbackEqualityComparer` field, leading to future calls to `MessagePackSecurity.GetEqualityComparer<object>` to return null.
What's particularly hazardous about this is that `null` is interpreted by `Dictionary<K,V>... | MessagePackSecurity.GetEqualityComparer<object> returns null on copied instances | https://api.github.com/repos/MessagePack-CSharp/MessagePack-CSharp/issues/810/comments | 0 | 2020-02-07T23:25:01Z | 2020-02-10T13:46:21Z | https://github.com/MessagePack-CSharp/MessagePack-CSharp/issues/810 | 561,922,221 | 810 | 1,063 |
CVE-2019-11251 | 2020-02-03T16:15:11.140 | The Kubernetes kubectl cp command in versions 1.1-1.12, and versions prior to 1.13.11, 1.14.7, and 1.15.4 allows a combination of two symlinks provided by tar output of a malicious container to place a file outside of the destination directory specified in the kubectl cp invocation. This could be used to allow an attac... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/87773"
},
{
"source": "jordan@liggitt.net",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.google.com/d/msg/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "8E20ECB8-B503-4DB2-BCDB-D28E53523C9E",
"versionEndExcluding": "1.13.11",
"versionEndIncluding": null,
"versionStar... | [
"59"
] | 59 | https://github.com/kubernetes/kubernetes/issues/87773 | [
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | A security issue was discovered in kubectl versions v1.13.10, v1.14.6, and v1.15.3. The issue is of a medium severity and upgrading of kubectl is encouraged to fix the vulnerability.
**Am I vulnerable?**
Run kubectl version --client and if it returns versions v1.13.10, v1.14.6, and v1.15.3, you are running a vuln... | CVE-2019-11251: kubectl cp symlink vulnerability | https://api.github.com/repos/kubernetes/kubernetes/issues/87773/comments | 3 | 2020-02-03T15:12:22Z | 2022-10-14T02:00:16Z | https://github.com/kubernetes/kubernetes/issues/87773 | 559,146,411 | 87,773 | 1,064 |
CVE-2020-8116 | 2020-02-04T20:15:13.353 | Prototype pollution vulnerability in dot-prop npm package versions before 4.2.1 and versions 5.x before 5.1.1 allows an attacker to add arbitrary properties to JavaScript language constructs such as objects. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "support@hackerone.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/advisories/GHSA-ff7x-qrg7-qggm"
},
{
"source": "support@hackerone.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:dot-prop_project:dot-prop:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "9EFF2C93-F28E-47DE-A654-0B614FB1D5B8",
"versionEndExcluding": "4.2.1",
"versionEndIncluding": null,
"ver... | [
"1321"
] | 1321 | https://github.com/sindresorhus/dot-prop/issues/63 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"sindresorhus",
"dot-prop"
] | Based on the severity of [CVE-2020-8116](https://nvd.nist.gov/vuln/detail/CVE-2020-8116) and the fact that 4.x is still very commonly used as a dependency, I would like to kindly request for the [fix](https://github.com/sindresorhus/dot-prop/commit/3039c8c07f6fdaa8b595ec869ae0895686a7a0f2) to be backported to 4.x and r... | Please backport CVE-2020-8116 security fix to 4.x. | https://api.github.com/repos/sindresorhus/dot-prop/issues/63/comments | 9 | 2020-08-12T09:55:49Z | 2020-08-21T22:33:08Z | https://github.com/sindresorhus/dot-prop/issues/63 | 677,559,188 | 63 | 1,065 |
CVE-2016-7523 | 2020-02-06T14:15:10.737 | coders/meta.c in ImageMagick allows remote attackers to cause a denial of service (out-of-bounds read) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security@debian.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2016/09/22/2"
},
{
"source": "security@debian.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://bug... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CFC2C780-A54E-4426-9C52-46A20216339E",
"versionEndExcluding": "6.9.4-0",
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/94 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | https://bugs.launchpad.net/ubuntu/+source/imagemagick/+bug/1537420
| heap-buffer-overflow in coders/meta.c:496 | https://api.github.com/repos/ImageMagick/ImageMagick/issues/94/comments | 2 | 2016-01-24T01:29:08Z | 2016-01-25T00:23:16Z | https://github.com/ImageMagick/ImageMagick/issues/94 | 128,365,381 | 94 | 1,067 |
CVE-2016-7524 | 2020-02-06T14:15:10.830 | coders/meta.c in ImageMagick allows remote attackers to cause a denial of service (out-of-bounds read) via a crafted file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "security@debian.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2016/09/22/2"
},
{
"source": "security@debian.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://bug... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CFC2C780-A54E-4426-9C52-46A20216339E",
"versionEndExcluding": "6.9.4-0",
"versionEndIncluding": null,
"versionSt... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/96 | [
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | https://bugs.launchpad.net/ubuntu/+source/imagemagick/+bug/1537422
| heap-buffer-overflow in coders/meta.c:465 | https://api.github.com/repos/ImageMagick/ImageMagick/issues/96/comments | 3 | 2016-01-24T01:29:30Z | 2020-02-10T03:00:49Z | https://github.com/ImageMagick/ImageMagick/issues/96 | 128,365,398 | 96 | 1,068 |
CVE-2020-8645 | 2020-02-07T00:15:09.443 | An issue was discovered in Simplejobscript.com SJS through 1.66. There is an unauthenticated SQL injection via the job applications search function. The vulnerable parameter is job_id. The function is getJobApplicationsByJobId(). The file is _lib/class.JobApplication.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/niteosoft/simplejobscript/issues/9"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:simplejobscript:simplejobscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CD8EF221-6FAC-49F7-9589-168A8294E29A",
"versionEndExcluding": null,
"versionEndIncluding": "1.66",
"vers... | [
"89"
] | 89 | https://github.com/niteosoft/simplejobscript/issues/9 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"niteosoft",
"simplejobscript"
] | **Description:** An issue was discovered in Simplejobscript.com SJS through 1.66. There is an unauthenticated SQL injection via the job applications search function. The vulnerable parameter is `job_id`. The function is `getJobApplicationsByJobId()`. The file is `_lib/class.JobApplication.php`.
**Environment:**
V... | [security] CVE-2020-8645, SQL injection in job applications search function | https://api.github.com/repos/niteosoft/simplejobscript/issues/9/comments | 3 | 2020-01-19T13:01:39Z | 2020-02-05T21:57:37Z | https://github.com/niteosoft/simplejobscript/issues/9 | 551,919,038 | 9 | 1,069 |
CVE-2020-8654 | 2020-02-07T00:15:09.520 | An issue was discovered in EyesOfNetwork 5.3. An authenticated web user with sufficient privileges could abuse the AutoDiscovery module to run arbitrary OS commands via the /module/module_frame/index.php autodiscovery.php target field. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/156266/EyesOfNetwork-5.3-Remote-Code-Execution.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyesofnetwork:eyesofnetwork:5.3-0:*:*:*:*:*:*:*",
"matchCriteriaId": "569CE2B4-B9FF-44FB-8550-FED2DBCFA749",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"78"
] | 78 | https://github.com/EyesOfNetworkCommunity/eonweb/issues/50 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"EyesOfNetworkCommunity",
"eonweb"
] | Bonjour,
Il est possible d’exécuter des commandes arbitraires sur le système d'exploitation pour un utilisateur d'EON ayant les droits suffisant pour utiliser le module d'AutoDiscovery.
Le champ 'Target' n'est pas filtré est il est possible d’exécuter des commandes arbitraires.
Voici un exemple de valeur de Target... | Execution de commandes arbitraires sur le module AutoDiscovery | https://api.github.com/repos/EyesOfNetworkCommunity/eonweb/issues/50/comments | 3 | 2020-02-05T13:27:51Z | 2020-03-03T09:51:20Z | https://github.com/EyesOfNetworkCommunity/eonweb/issues/50 | 560,371,847 | 50 | 1,070 |
CVE-2020-8656 | 2020-02-07T00:15:09.723 | An issue was discovered in EyesOfNetwork 5.3. The EyesOfNetwork API 2.4.2 is prone to SQL injection, allowing an unauthenticated attacker to perform various tasks such as authentication bypass via the username field to getApiKey in include/api_functions.php. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/156266/EyesOfNetwork-5.3-Remote-Code-Execution.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyesofnetwork:eyesofnetwork:5.3-0:*:*:*:*:*:*:*",
"matchCriteriaId": "569CE2B4-B9FF-44FB-8550-FED2DBCFA749",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"89"
] | 89 | https://github.com/EyesOfNetworkCommunity/eonapi/issues/16 | [
"Third Party Advisory"
] | github.com | [
"EyesOfNetworkCommunity",
"eonapi"
] | Bonjour,
Il est possible de réaliser une injection SQL sur le champ username de la fonction getApiKey.
Exemple d'injection de code utilisant la fonction sleep(3):
`/eonapi/getApiKey?username=' union select sleep(3),0,0,0,0,0,0,0 or '`
Ceci a été testé sur une installation de EON 5.3 classique téléchargée à pa... | Injection SQL sur le champ username de getApiKey | https://api.github.com/repos/EyesOfNetworkCommunity/eonapi/issues/16/comments | 4 | 2020-02-05T13:20:52Z | 2020-03-03T10:42:27Z | https://github.com/EyesOfNetworkCommunity/eonapi/issues/16 | 560,367,803 | 16 | 1,071 |
CVE-2019-17268 | 2020-02-07T14:15:11.343 | The omniauth-weibo-oauth2 gem 0.4.6 for Ruby, as distributed on RubyGems.org, included a code-execution backdoor inserted by a third party. Versions through 0.4.5, and 0.5.1 and later, are unaffected. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://diff.coditsu.io/diffs/09a05c37-1b34-49e1-ac94-d4dda40d1ad1#d2h-971595"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://gi... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:omniauth-weibo-oauth2_project:omniauth-weibo-oauth2:0.4.6:*:*:*:*:ruby:*:*",
"matchCriteriaId": "10A1A9B2-0128-4CA3-99C3-817C91267631",
"versionEndExcluding": null,
"versionEndIncluding"... | [
"94"
] | 94 | https://github.com/beenhero/omniauth-weibo-oauth2/issues/36 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"beenhero",
"omniauth-weibo-oauth2"
] | Hey,
I took courtesy of reporting the malicious code injection in `0.4.6` into the CVE database.
https://diff.coditsu.io/gems/omniauth-weibo-oauth2/0.4.3/0.4.6
Just wanted to let you know. They initially assigned the `CVE-2019-17268`. | CVE-2019-17268 report for omniauth-weibo-oauth2 | https://api.github.com/repos/beenhero/omniauth-weibo-oauth2/issues/36/comments | 4 | 2019-10-09T12:17:49Z | 2019-10-14T14:46:19Z | https://github.com/beenhero/omniauth-weibo-oauth2/issues/36 | 504,613,423 | 36 | 1,072 |
CVE-2020-8788 | 2020-02-07T14:15:11.437 | Synaptive Medical ClearCanvas ImageServer 3.0 Alpha allows XSS (and HTML injection) via the Default.aspx UserName parameter. NOTE: the issues/227 reference does not imply that the affected product can be downloaded from GitHub. It was simply a convenient location for a public bug report. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/ClearCanvas/ClearCanvas/issues/227"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https:/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:synaptivemedical:clearcanvas:3.0:alpha:*:*:*:*:*:*",
"matchCriteriaId": "E65043C8-07DE-49E3-BFB6-E018EA8A4497",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ver... | [
"79"
] | 79 | https://github.com/ClearCanvas/ClearCanvas/issues/227 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ClearCanvas",
"ClearCanvas"
] | Hello,
I found two vulnerabilities that affect to ClearCanvas ImageServer 3.0 Alpha:
- Cross-site Scripting (XSS) reflected
- HTML Injection
You can reproduce both with the following details,
1. Payload: <p/onclick=alert(1)>xss
2. Vulnerable POST data: &UserName=<p/onclick=alert(1)>xss
3. Output: <span i... | Cross-site Scripting (XSS) and HTML Injection on ClearCanvas ImageServer 3.0 Alpha | https://api.github.com/repos/ClearCanvas/ClearCanvas/issues/227/comments | 3 | 2019-07-24T21:37:53Z | 2020-02-11T15:40:13Z | https://github.com/ClearCanvas/ClearCanvas/issues/227 | 472,547,338 | 227 | 1,073 |
CVE-2020-8811 | 2020-02-07T23:15:10.823 | ajax/profile-picture-upload.php in Bludit 3.10.0 allows authenticated users to change other users' profile pictures. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1131"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Par... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.10.0:*:*:*:*:*:*:*",
"matchCriteriaId": "94D51A63-EB8D-4BE4-82B0-E877D79F0C18",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"862"
] | 862 | https://github.com/bludit/bludit/issues/1131 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"bludit",
"bludit"
] | ### Describe
This vulnerability allows authenticated users to change other user's profile pictures.
### Steps to reproduce the vulnerability
1. Tried to login via Administrator privilege. We found 3 accounts.
 vulnerability in the loadForm function in Frontend/Modules/Search/Actions/Index.php in Fork CMS before 3.8.4 allows remote attackers to inject arbitrary web script or HTML via the q_widget parameter to en/search. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Mailing List",
"Third Party Advisory"
],
"url": "http://seclists.org/fulldisclosure/2015/Jan/38"
},
{
"source": "cve@mitre.org",
"tags": [
"Vendor Advisory"
],
"url": "http://www.fork-cms.com/blog/detail/f... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fork-cms:fork_cms:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AE88F534-F422-464E-B76D-6C52F6ACD4B9",
"versionEndExcluding": "3.8.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"79"
] | 79 | https://github.com/forkcms/forkcms/issues/1018s | [
"Broken Link"
] | github.com | [
"forkcms",
"forkcms"
] | Link: http://demo.fork-cms.com/en/search?form=search&q_widget="onmouseover="alert(111)"&submit=Search
::REQUEST:: Using a proxy to request
GET /en/search?form=search&q_widget="onmouseover="alert('XSS')"&submit=Search HTTP/1.1
Host: demo.fork-cms.com
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:34.0) Gecko/20100... | XSS vulnerability | https://api.github.com/repos/forkcms/forkcms/issues/1018/comments | 1 | 2014-12-25T10:31:18Z | 2014-12-26T07:13:57Z | https://github.com/forkcms/forkcms/issues/1018 | 52,858,198 | 1,018 | 1,076 |
CVE-2020-8823 | 2020-02-10T03:15:10.677 | htmlfile in lib/transport/htmlfile.js in SockJS before 0.3.0 is vulnerable to Reflected XSS via the /htmlfile c (aka callback) parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/theyiyibest/Reflected-XSS-on-SockJS"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/theyiyibest/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sockjs_project:sockjs:*:*:*:*:*:node.js:*:*",
"matchCriteriaId": "CD2CDBA3-3C78-4479-9D2F-C1F5892D1076",
"versionEndExcluding": "0.3.0",
"versionEndIncluding": null,
"version... | [
"79"
] | 79 | https://github.com/theyiyibest/Reflected-XSS-on-SockJS/issues/1 | [
"Third Party Advisory"
] | github.com | [
"theyiyibest",
"Reflected-XSS-on-SockJS"
] | I'm concerned the public text of CVE-2020-8823 isn't well defined enough for development teams to patch the affected library. Can you provide more details to help? Specifically the concern is that product name and version number do not match clearly with SockJS.
SockJS seems to be a product family and not a single... | Affected version and product name accurate? | https://api.github.com/repos/theyiyibest/Reflected-XSS-on-SockJS/issues/1/comments | 1 | 2020-02-14T14:57:10Z | 2020-11-12T18:46:29Z | https://github.com/theyiyibest/Reflected-XSS-on-SockJS/issues/1 | 565,377,653 | 1 | 1,077 |
CVE-2020-8089 | 2020-02-10T16:15:14.267 | Piwigo 2.10.1 is affected by stored XSS via the Group Name Field to the group_list page. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1150"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Vendor Advisory"
],
"url": "https://piwigo... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8E8B6457-1AF4-4B29-AF6E-9682E45BB2A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/Piwigo/Piwigo/issues/1150 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | Description:
Piwigo version 2.10.1 is affected by stored cross site scripting vulnerability. This vulnerability exists in "Group Name" Field in "group_list" page.
How to reproduce:
1. Login into the application.
2. Go to the "Users" -> "Groups" page from life navigation menu.
3. Click on "Add Group" button a... | Stored Cross-Site Scripting vulnerability in Piwigo CMS | https://api.github.com/repos/Piwigo/Piwigo/issues/1150/comments | 1 | 2020-01-20T13:47:13Z | 2020-03-25T14:32:53Z | https://github.com/Piwigo/Piwigo/issues/1150 | 552,310,420 | 1,150 | 1,078 |
CVE-2020-8840 | 2020-02-10T21:56:10.653 | FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "http://www.huawei.com/en/psirt/security-advisories/huawei-sa-20200610-01-fastjason-en"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jac... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2F87CF67-6994-43F1-BEC3-DD7D122D0146",
"versionEndExcluding": "2.7.9.7",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2620 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget (*) type reported related to JNDI access.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-8840
Original discoverer: @threedr3am
Fixed in:
* 2.9.10.3 (`jackson-bom` version `2.9... | Block one more gadget type (xbean-reflect/JNDI - CVE-2020-8840) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2620/comments | 6 | 2020-02-09T22:50:59Z | 2020-07-16T17:23:57Z | https://github.com/FasterXML/jackson-databind/issues/2620 | 562,253,349 | 2,620 | 1,079 |
CVE-2014-9748 | 2020-02-11T17:15:11.780 | The uv_rwlock_t fallback implementation for Windows XP and Server 2003 in libuv before 1.7.4 does not properly prevent threads from releasing the locks of other threads, which allows attackers to cause a denial of service (deadlock) or possibly have unspecified other impact by leveraging a race condition. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libuv/libuv/issues/515"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/libuv/libuv/pull/516"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libuv:libuv:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9BC7386D-7909-47FB-9B43-E02D9B01A16F",
"versionEndExcluding": "1.7.4",
"versionEndIncluding": null,
"versionStartExcluding":... | [
"362"
] | 362 | https://github.com/libuv/libuv/issues/515 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"libuv",
"libuv"
] | It was pointed out by Zhou Ran that the fallback write mutex can end up getting unlocked by a different thread than the one that locked it, resulting in undefined behavior. Consider a rwlock that is initially unlocked:
Thread A: increments reader count at t0 -> acquires write lock at t0 -> decrements reader count at ... | windows: xp rwlock fallback is unsound | https://api.github.com/repos/libuv/libuv/issues/515/comments | 2 | 2015-09-07T13:02:14Z | 2015-09-11T09:50:26Z | https://github.com/libuv/libuv/issues/515 | 105,211,877 | 515 | 1,080 |
CVE-2019-19921 | 2020-02-12T15:15:12.210 | runc through 1.0.0-rc9 has Incorrect Access Control leading to Escalation of Privileges, related to libcontainer/rootfs_linux.go. To exploit this, an attacker must be able to spawn two containers with custom volume-mount configurations, and be able to run custom images. (This vulnerability does not affect Docker due to... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.4,
"confidentialityImpact": "PARTIA... | [
{
"source": "cve@mitre.org",
"tags": [
"Broken Link",
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-02/msg00018.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:linuxfoundation:runc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D522E8C1-E7F0-4A3D-AF68-6D962944A0E5",
"versionEndExcluding": null,
"versionEndIncluding": "0.1.1",
"versionStartEx... | [
"706"
] | 706 | https://github.com/opencontainers/runc/issues/2197 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"opencontainers",
"runc"
] | Disclosed in https://github.com/opencontainers/runc/pull/2190.
Here's the original report to security@opencontainers.org:
Hi all,
an attacker who controls the container image for two containers that share a volume can race volume mounts during container initialization, by adding a symlink to the rootfs that po... | [CVE-2019-19921]: Volume mount race condition with shared mounts | https://api.github.com/repos/opencontainers/runc/issues/2197/comments | 12 | 2020-01-01T13:07:23Z | 2023-04-24T11:30:03Z | https://github.com/opencontainers/runc/issues/2197 | 544,355,271 | 2,197 | 1,081 |
CVE-2020-5239 | 2020-02-13T01:15:11.047 | In Mailu before version 1.7, an authenticated user can exploit a vulnerability in Mailu fetchmail script and gain full access to a Mailu instance. Mailu servers that have open registration or untrusted users are most impacted. The master and 1.7 branches are patched on our git repository. All Docker images published on... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Mailu/Mailu/issues/1354"
},
{
"source": "security-advisories@github.com",
"tags": [
"Mitigation",
"Third Party Advisory"
],
"url": "https://github.com/Ma... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mailu:mailu:*:*:*:*:*:*:*:*",
"matchCriteriaId": "5CD1E230-BB0F-4184-84B0-A67EAA9D97B0",
"versionEndExcluding": "1.7",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"863"
] | 863 | https://github.com/Mailu/Mailu/issues/1354 | [
"Third Party Advisory"
] | github.com | [
"Mailu",
"Mailu"
] | On 02/07, we discovered a bug in the Fetchmail script for Mailu that has serious security consequences. If you are using the fetchmail container for Mailu (which is optional), **please apply the following instructions as soon as possible**.
The vulnerability requires authenticated access for exploitation, so patchi... | WARNING - Fetchmail security update to all branches, update ASAP | https://api.github.com/repos/Mailu/Mailu/issues/1354/comments | 1 | 2020-02-08T09:30:20Z | 2020-09-25T10:41:02Z | https://github.com/Mailu/Mailu/issues/1354 | 561,995,268 | 1,354 | 1,082 |
CVE-2020-8981 | 2020-02-13T17:15:29.930 | A cross-site scripting (XSS) vulnerability was discovered in the Source Integration plugin before 1.6.2 and 2.x before 2.3.1 for MantisBT. The repo_delete.php Delete Repository page allows execution of arbitrary code via a repo name (if CSP settings permit it). This is related to CVE-2018-16362. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/mantisbt-plugins/source-integration/commit/270675c964c675829fe010f9f0830521dc0835f0"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mantisbt:source_integration:*:*:*:*:*:mantisbt:*:*",
"matchCriteriaId": "8B60D2AF-47DF-4216-B941-DB4F41E31E5B",
"versionEndExcluding": "1.6.2",
"versionEndIncluding": null,
"... | [
"79"
] | 79 | https://github.com/mantisbt-plugins/source-integration/issues/338 | [
"Third Party Advisory"
] | github.com | [
"mantisbt-plugins",
"source-integration"
] | This is related to #286.
Steps to reproduce:
1. Create a new repository, set repo name to `<script>alert('XSS');</script>`
2. Update and go back to Manage Repository page
3. Click on _Delete Repository_
CVE request 841560 pending. | CVE-2020-8981: XSS in Delete Repository page | https://api.github.com/repos/mantisbt-plugins/source-integration/issues/338/comments | 1 | 2020-02-13T13:33:38Z | 2020-02-13T23:33:47Z | https://github.com/mantisbt-plugins/source-integration/issues/338 | 564,685,646 | 338 | 1,083 |
CVE-2012-6685 | 2020-02-19T15:15:11.723 | Nokogiri before 1.5.4 is vulnerable to XXE attacks | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=1178970"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "h... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nokogiri:nokogiri:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CB203B5A-2979-4C08-8E90-EEA32EE5ACB0",
"versionEndExcluding": "1.5.4",
"versionEndIncluding": null,
"versionStartExclu... | [
"776"
] | 776 | https://github.com/sparklemotion/nokogiri/issues/693 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sparklemotion",
"nokogiri"
] | Using external xml entities you can specify URLs (e.g. HTTP) to be contacted when attacker-supplied XML is parsed. This can be used to trigger URLs on the internal network of a XML parsing service and potentially leak their responses.
External xml entities should be completely (file, http, etc.) disabled.
```
$ cat ... | nokogiri vulnerable to XXE attack when used under c ruby | https://api.github.com/repos/sparklemotion/nokogiri/issues/693/comments | 18 | 2012-06-06T09:34:24Z | 2020-09-23T12:15:38Z | https://github.com/sparklemotion/nokogiri/issues/693 | 4,925,753 | 693 | 1,084 |
CVE-2016-3182 | 2020-02-20T01:15:10.687 | The color_esycc_to_rgb function in bin/common/color.c in OpenJPEG before 2.1.1 allows attackers to cause a denial of service (memory corruption) via a crafted jpeg 2000 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2016/03/16/16"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwa... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:uclouvain:openjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2063942E-E483-4E3C-89FB-1357F9F1189E",
"versionEndExcluding": "2.1.1",
"versionEndIncluding": null,
"versionStartExcl... | [
"119"
] | 119 | https://github.com/uclouvain/openjpeg/issues/725 | [
"Third Party Advisory"
] | github.com | [
"uclouvain",
"openjpeg"
] | # Vulnerability Details
According to AddressSanitizer's output message, the Out-of-Bounds read occurred in function color_esycc_to_rgb. However, there must be also an Out-of-Bounds write circumstance since an exception will be throwed when freeing the heap buffer.
- AddressSanitizer output the following exception info... | CVE-2016-3182 Heap Corruption in opj_free function | https://api.github.com/repos/uclouvain/openjpeg/issues/725/comments | 2 | 2016-03-16T10:05:18Z | 2016-09-13T08:27:02Z | https://github.com/uclouvain/openjpeg/issues/725 | 141,224,897 | 725 | 1,085 |
CVE-2020-9272 | 2020-02-20T16:15:11.857 | ProFTPD 1.3.7 has an out-of-bounds (OOB) read vulnerability in mod_cap via the cap_text.c cap_to_text function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00002.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://cert-portal.s... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:proftpd:proftpd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0CBC9526-A183-4F23-BD9A-4ACE11A4307C",
"versionEndExcluding": "1.3.6c",
"versionEndIncluding": null,
"versionStartExclud... | [
"125"
] | 125 | https://github.com/proftpd/proftpd/issues/902 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"proftpd",
"proftpd"
] | **This vulnerability was previously reported via email to security@proftpd.org and has been made public after the fix has been developed.**
### Credit
This issue was discovered and reported by **GitHub Security Lab** team member @antonio-morales (Antonio Morales).
### Summary:
An out-of-bounds (OOB) read vulne... | Out-of-bounds read in mod_cap getstateflags() function | https://api.github.com/repos/proftpd/proftpd/issues/902/comments | 6 | 2020-02-18T17:15:00Z | 2020-02-21T15:54:52Z | https://github.com/proftpd/proftpd/issues/902 | 567,039,374 | 902 | 1,086 |
CVE-2020-9273 | 2020-02-20T16:15:11.950 | In ProFTPD 1.3.7, it is possible to corrupt the memory pool by interrupting the data transfer channel. This triggers a use-after-free in alloc_pool in pool.c, and possible remote code execution. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00002.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:proftpd:proftpd:1.3.7:*:*:*:*:*:*:*",
"matchCriteriaId": "9840D8DB-F09B-47C2-871E-89247B841871",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExclud... | [
"416"
] | 416 | https://github.com/proftpd/proftpd/issues/903 | [
"Third Party Advisory"
] | github.com | [
"proftpd",
"proftpd"
] | **This vulnerability was previously reported via email to security@proftpd.org and has been made public after the fix has been developed.**
### Credit
This issue was discovered and reported by GitHub Security Lab team member @antonio-morales (Antonio Morales).
### Summary
A use-after-free vulnerability exists i... | Use-after-free vulnerability in memory pools during data transfer | https://api.github.com/repos/proftpd/proftpd/issues/903/comments | 3 | 2020-02-18T17:27:21Z | 2020-02-22T16:10:47Z | https://github.com/proftpd/proftpd/issues/903 | 567,046,320 | 903 | 1,087 |
CVE-2020-9329 | 2020-02-21T22:15:10.880 | Gogs through 0.11.91 allows attackers to violate the admin-specified repo-creation policy due to an internal/db/repo.go race condition. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gogs/gogs/issues/5926"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gogs:gogs:*:*:*:*:*:*:*:*",
"matchCriteriaId": "EA2B75BE-EE0C-4E9B-8ACD-DD233A9EBAA7",
"versionEndExcluding": null,
"versionEndIncluding": "0.11.91",
"versionStartExcluding":... | [
"362"
] | 362 | https://github.com/gogs/gogs/issues/5926 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"gogs",
"gogs"
] | ## Description
Users could potentially create more repos than specified in MaxCreationLimit as NumRepos field is not updated in a race-condition-safe cavalier (i.e. row is not locked). Such logic error could be fatal in some specific settings.
## Reason
internal/db/repo.go:1108
```go
func CreateRepository(doer, ... | Race condition can make MaxCreationLimit useless | https://api.github.com/repos/gogs/gogs/issues/5926/comments | 7 | 2020-02-19T18:09:37Z | 2022-08-15T12:41:56Z | https://github.com/gogs/gogs/issues/5926 | 567,743,100 | 5,926 | 1,088 |
CVE-2020-8813 | 2020-02-22T02:15:10.553 | graph_realtime.php in Cacti 1.2.8 allows remote attackers to execute arbitrary OS commands via shell metacharacters in a cookie, if a guest user has the graph real-time privilege. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "COMPLETE",
"baseScore": 9.3,
"confidentialityImpact": "COMPL... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-04/msg00042.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "http... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cacti:cacti:1.2.8:*:*:*:*:*:*:*",
"matchCriteriaId": "2D05824B-4E66-44CA-A862-0DDDB23C8C88",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding"... | [
"78"
] | 78 | https://github.com/Cacti/cacti/issues/3285 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Cacti",
"cacti"
] | **Describe the bug**
Mohammad Askar of iSecurity has reported that graph_realtime.php prior to 1.2.10 allows remote attackers to execute arbitrary OS commands via shell metacharacters in a cookie if a guest user has the graph real-time privilege.
**To Reproduce**
Steps to reproduce the behavior:
1. Enable the gue... | When guest users have access to realtime graphs, remote code could be executed (CVE-2020-8813) | https://api.github.com/repos/Cacti/cacti/issues/3285/comments | 3 | 2020-02-23T06:03:06Z | 2020-06-30T12:30:28Z | https://github.com/Cacti/cacti/issues/3285 | 569,444,022 | 3,285 | 1,089 |
CVE-2020-9369 | 2020-02-24T18:15:22.960 | Sympa 6.2.38 through 6.2.52 allows remote attackers to cause a denial of service (disk consumption from temporary files, and a flood of notifications to listmasters) via a series of requests with malformed parameters. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/sympa-community/sympa/issues/886"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fed... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sympa:sympa:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AD0CD227-C6CC-426C-B13E-A3BE86861467",
"versionEndExcluding": null,
"versionEndIncluding": "6.2.52",
"versionStartExcluding"... | [
"400"
] | 400 | https://github.com/sympa-community/sympa/issues/886 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"sympa-community",
"sympa"
] | <!--- ↑↑ Provide a general summary of the issue in the Title above ↑↑ -->
Version
-------
<!-- Versions of Sympa and related software -->
6.2.38 to 6.2.52.
Installation method
-------------------
<!-- How you installed Sympa: deb, rpm, ports, ... or source package -->
Any.
Expected behavior
------------... | [SA 2020-001] Security flaws in CSRF prevension, CVE-2020-9369 | https://api.github.com/repos/sympa-community/sympa/issues/886/comments | 2 | 2020-02-24T04:26:11Z | 2020-02-25T06:47:53Z | https://github.com/sympa-community/sympa/issues/886 | 569,629,228 | 886 | 1,090 |
CVE-2020-8818 | 2020-02-25T02:15:12.097 | An issue was discovered in the CardGate Payments plugin through 2.0.30 for Magento 2. Lack of origin authentication in the IPN callback processing function in Controller/Payment/Callback.php allows an attacker to remotely replace critical plugin settings (merchant ID, secret key, etc.) and therefore bypass the payment ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/156505/Magento-WooCommerce-CardGate-Payment-Gateway-2.0.30-Bypass.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cardgate:cardgate_payments:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7BD035FF-55DF-417A-99B2-8D6B574A8010",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.30",
"version... | [
"346"
] | 346 | https://github.com/cardgate/magento2/issues/54 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cardgate",
"magento2"
] | ### [CVE-2020-8818](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8818)
Lack of origin authentication ([CWE-346](https://cwe.mitre.org/data/definitions/346.html)) at IPN callback processing function allow (**even _unauthorized_**) attacker to remotely replace critical plugin settings (merchant id, secret key... | Public disclosure on CVE-2020-8818 [Unauthorized Payments Hijacking + Order Status Spoofing] | https://api.github.com/repos/cardgate/magento2/issues/54/comments | 1 | 2020-02-24T18:42:21Z | 2020-03-04T07:18:02Z | https://github.com/cardgate/magento2/issues/54 | 570,050,974 | 54 | 1,091 |
CVE-2020-8819 | 2020-02-25T02:15:12.160 | An issue was discovered in the CardGate Payments plugin through 3.1.15 for WooCommerce. Lack of origin authentication in the IPN callback processing function in cardgate/cardgate.php allows an attacker to remotely replace critical plugin settings (merchant ID, secret key, etc.) and therefore bypass the payment process ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 5.5,
"confidentialityImpact": "PARTIAL"... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/156504/WordPress-WooCommerce-CardGate-Payment-Gateway-3.1.15-Bypass.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cardgate:cardgate_payments:*:*:*:*:*:woocommerce:*:*",
"matchCriteriaId": "8C39B515-59B8-47BB-BE73-FDB32F1392E9",
"versionEndExcluding": null,
"versionEndIncluding": "3.1.15",
... | [
"346"
] | 346 | https://github.com/cardgate/woocommerce/issues/18 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"cardgate",
"woocommerce"
] | ### [CVE-2020-8819](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8819)
Lack of origin authentication ([CWE-346](https://cwe.mitre.org/data/definitions/346.html)) at IPN callback processing function allow (**even _unauthorized_**) attacker to remotely replace critical plugin settings (merchant id, secret key... | Public disclosure on CVE-2020-8819 [Unauthorized Payments Hijacking + Order Status Spoofing] | https://api.github.com/repos/cardgate/woocommerce/issues/18/comments | 1 | 2020-02-24T18:40:59Z | 2020-03-04T07:18:28Z | https://github.com/cardgate/woocommerce/issues/18 | 570,050,115 | 18 | 1,092 |
CVE-2017-6363 | 2020-02-27T05:15:11.007 | In the GD Graphics Library (aka LibGD) through 2.2.5, there is a heap-based buffer over-read in tiffWriter in gd_tiff.c. NOTE: the vendor says "In my opinion this issue should not have a CVE, since the GD and GD2 formats are documented to be 'obsolete, and should only be used for development and testing purposes.' | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/libgd/libgd/issues/383"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libgd:libgd:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1C8F4811-034F-41ED-B690-188B0BE7D7DD",
"versionEndExcluding": null,
"versionEndIncluding": "2.2.5",
"versionStartExcluding":... | [
"125"
] | 125 | https://github.com/libgd/libgd/issues/383 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"libgd",
"libgd"
] | Description
========
Hi, when I fuzz the libgd, a invalid read occurs within the function tiffWriter of gd_tiff.c, it can be triggered by the
[gdfile.txt](https://github.com/libgd/libgd/files/783796/gdfile.txt)
Valgrind tracker
========
```
➜ Bin git:(master) ✗ valgrind --leak-check=yes ./test_gd2_bug00209 .... | Invalid read when call gdImageTiffPtr (CVE-2017-6363) | https://api.github.com/repos/libgd/libgd/issues/383/comments | 7 | 2017-02-17T16:51:11Z | 2018-02-04T15:49:30Z | https://github.com/libgd/libgd/issues/383 | 208,496,906 | 383 | 1,093 |
CVE-2020-7041 | 2020-02-27T18:15:11.483 | An issue was discovered in openfortivpn 1.11.0 when used with OpenSSL 1.0.2 or later. tunnel.c mishandles certificate validation because an X509_check_host negative error code is interpreted as a successful return value. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://lists.opensuse.org/opensuse-security-announce/2020-03/msg00009.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openfortivpn_project:openfortivpn:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9676ABA1-E073-4E5E-A583-9661F9220F98",
"versionEndExcluding": "1.12.0",
"versionEndIncluding": null,
"... | [
"295"
] | 295 | https://github.com/adrienverge/openfortivpn/issues/536 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"adrienverge",
"openfortivpn"
] | Dear mantainers,
As part of my work at GitHub's Security Lab, I have identified some security issues in openfortivpn and I would like to know the preferred way of communicating said issues.
Best regards. | Security Contact | https://api.github.com/repos/adrienverge/openfortivpn/issues/536/comments | 12 | 2020-01-14T13:12:17Z | 2020-03-04T14:30:19Z | https://github.com/adrienverge/openfortivpn/issues/536 | 549,558,420 | 536 | 1,094 |
CVE-2020-9447 | 2020-02-28T16:15:11.087 | There is an XSS (cross-site scripting) vulnerability in GwtUpload 1.0.3 in the file upload functionality. Someone can upload a file with a malicious filename, which contains JavaScript code, which would result in XSS. Cross-site scripting enables attackers to steal data, change the appearance of a website, and perform ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/manolo/gwtupload/issues/32"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://www.co... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gwtupload_project:gwtupload:1.0.3:*:*:*:*:*:*:*",
"matchCriteriaId": "83DF83B6-87E9-4C19-8616-59B0CE2A0364",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versio... | [
"79"
] | 79 | https://github.com/manolo/gwtupload/issues/32 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"manolo",
"gwtupload"
] | There is an XSS(Cross-site scripting) present in the file upload functionality, where someone can upload a file with malicious filename, which contains JavaScript code, which would results in XSS.
Example: https://github.com/manolo/gwtupload/blob/master/samples/src/main/java/gwtuploadsample/client/SingleUploadSample.... | XSS in the file upload functionality | https://api.github.com/repos/manolo/gwtupload/issues/32/comments | 9 | 2020-02-12T17:14:35Z | 2022-06-15T08:05:15Z | https://github.com/manolo/gwtupload/issues/32 | 564,144,989 | 32 | 1,095 |
CVE-2020-9465 | 2020-02-28T20:15:11.787 | An issue was discovered in EyesOfNetwork eonweb 5.1 through 5.3 before 5.3-3. The eonweb web interface is prone to a SQL injection, allowing an unauthenticated attacker to perform various tasks such as authentication bypass via the user_id field in a cookie. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/EyesOfNetworkCommunity/eonweb/issues/51"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:eyesofnetwork:eyesofnetwork:*:*:*:*:*:*:*:*",
"matchCriteriaId": "33CD9C65-C80F-4334-976A-184CAC52CA0E",
"versionEndExcluding": "5.3-3",
"versionEndIncluding": null,
"version... | [
"89"
] | 89 | https://github.com/EyesOfNetworkCommunity/eonweb/issues/51 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"EyesOfNetworkCommunity",
"eonweb"
] | Bonjour,
Il est possible de réaliser une injection SQL sur le cookie `user_id`. Il a été observé que cette injection est possible sur les pages `index.php`, `login.php` et `logout.php` sans authentification préalable.
Exemple d'injection de code utilisant la fonction sleep(3):
`Cookie: user_id=1' union select sl... | Injection SQL sur le cookie user_id | https://api.github.com/repos/EyesOfNetworkCommunity/eonweb/issues/51/comments | 1 | 2020-02-26T17:32:06Z | 2020-02-28T12:40:58Z | https://github.com/EyesOfNetworkCommunity/eonweb/issues/51 | 571,545,509 | 51 | 1,096 |
CVE-2020-9546 | 2020-03-02T04:15:10.843 | FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2631"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.apache.org/thread.html/r35d30db00440ef63b791c4b7f7acb036e14d4a2... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "29BC94E0-FEBC-4E86-825C-0101DC339852",
"versionEndExcluding": "2.7.9.7",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2631 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | (note: placeholder until verified/validated, fix provided)
Another gadget type reported regarding a class of [TO BE ADDED].
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-9546
Reporters: three... | Block one more gadget type (shaded-hikari-config, CVE-2020-9546) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2631/comments | 8 | 2020-02-27T21:17:02Z | 2020-03-23T21:00:52Z | https://github.com/FasterXML/jackson-databind/issues/2631 | 572,364,748 | 2,631 | 1,097 |
CVE-2020-9547 | 2020-03-02T04:15:11.017 | FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2634"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.apache.org/thread.html/r35d30db00440ef63b791c4b7f7acb036e14d4a2... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2F87CF67-6994-43F1-BEC3-DD7D122D0146",
"versionEndExcluding": "2.7.9.7",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2634 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another 2 gadget type reported regarding a classes of `ibatis-sqlmap` and `Anteros-Core` packages.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-9547, CVE-2020-9548
Reporters: threedr3am & V1ZkR... | Block two more gadget types (ibatis-sqlmap, anteros-core; CVE-2020-9547 / CVE-2020-9548) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2634/comments | 8 | 2020-03-01T01:02:31Z | 2020-04-08T02:18:13Z | https://github.com/FasterXML/jackson-databind/issues/2634 | 573,448,185 | 2,634 | 1,098 |
CVE-2020-9549 | 2020-03-02T05:15:13.870 | In PDFResurrect 0.12 through 0.19, get_type in pdf.c has an out-of-bounds write via a crafted PDF document. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/enferex/pdfresurrect/issues/8"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debia... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:pdfresurrect_project:pdfresurrect:*:*:*:*:*:*:*:*",
"matchCriteriaId": "E6D12F79-6ECE-4422-8A8C-D04B40B72615",
"versionEndExcluding": null,
"versionEndIncluding": "0.19",
"ve... | [
"787"
] | 787 | https://github.com/enferex/pdfresurrect/issues/8 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"enferex",
"pdfresurrect"
] | ## Description
In v0.12 and newer, the function `get_type()` in `pdf.c` has the following logic:
https://github.com/enferex/pdfresurrect/blob/e4de3228b617e6467cb74185eb4a3ff0a9471c8a/pdf.c#L1299-L1304
If `buf` does not contain one of the expected terminating characters (whitespace, `/`, `>`), `c` can point to ... | Bug: Buffer Overflow into Out-of-Bounds Write | https://api.github.com/repos/enferex/pdfresurrect/issues/8/comments | 7 | 2020-02-28T18:57:24Z | 2020-03-05T05:10:03Z | https://github.com/enferex/pdfresurrect/issues/8 | 572,942,394 | 8 | 1,099 |
CVE-2019-14892 | 2020-03-02T17:15:17.813 | A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0729"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.re... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "7036DA13-110D-40B3-8494-E361BBF4AFCD",
"versionEndExcluding": "2.6.7.3",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2462 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget (*) type report regarding a class of `commons-configuration` (and later `commons-configuration2`) package(s)
Mitre id: not yet allocated
Reporter: @ybhou1993
Fixed in:
* 2.9.10 and later
* 2.8.11.5
* 2.6.7.3
* does not affect 2.10.0 and later
-----
(*) See https://medium.com/@cowtownco... | Block two more gadget types (commons-configuration/-2) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2462/comments | 9 | 2019-09-19T06:22:53Z | 2020-02-10T22:12:43Z | https://github.com/FasterXML/jackson-databind/issues/2462 | 495,597,365 | 2,462 | 1,100 |
CVE-2018-19599 | 2020-03-02T20:15:11.320 | Monstra CMS 1.6 allows XSS via an uploaded SVG document to the admin/index.php?id=filesmanager&path=uploads/ URI. NOTE: this is a discontinued product. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://anh.im/image/lG1"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://github.com/monstra-cms/monstra/issues/467"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:monstra:monstra_cms:1.6:*:*:*:*:*:*:*",
"matchCriteriaId": "316EFE6D-54F6-4928-B2D3-C803D7A4FD7C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcl... | [
"79"
] | 79 | https://github.com/monstra-cms/monstra/issues/467 | null | github.com | [
"monstra-cms",
"monstra"
] | **Describe the bug**
An authenticated malicious user can take advantage of a Stored XSS vulnerability in the "Files" feature.
Monstra application allows the upload of a SVG file extension (which is also an image type).
** Reproduce**
Steps to reproduce the behavior:
1. Login into the panel Monstra
2. Go to "/admi... | Cross Site Scripting Vulnerability on "Files" upload file SVG in Monstra 3.0.4 | https://api.github.com/repos/monstra-cms/monstra/issues/467/comments | 0 | 2020-05-25T03:57:37Z | 2020-05-25T03:59:29Z | https://github.com/monstra-cms/monstra/issues/467 | 624,029,113 | 467 | 1,101 |
CVE-2019-14893 | 2020-03-02T21:15:17.520 | A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://access.redhat.com/errata/RHSA-2020:0729"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.re... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "BF323F3D-B2A4-41E7-94F9-5539C9B7025E",
"versionEndExcluding": "2.8.11.5",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2469 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget (*) type report regarding a class of `xalan`.
Mitre id: not yet allocated
Reporter: @ybhou1993 (via #2462 originally)
* 2.9.10
* 2.8.11.5
* does not affect 2.10.0 and later
-----
(*) See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 ... | Block one more gadget type (xalan2) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2469/comments | 1 | 2019-09-20T06:20:34Z | 2020-02-10T22:13:16Z | https://github.com/FasterXML/jackson-databind/issues/2469 | 496,168,396 | 2,469 | 1,102 |
CVE-2020-1734 | 2020-03-03T22:15:10.843 | A flaw was found in the pipe lookup plugin of ansible. Arbitrary commands can be run, when the pipe lookup plugin uses subprocess.Popen() with shell=True, by overwriting ansible facts and the variable is not escaped by quote plugin. An attacker could take advantage and run arbitrary commands by overwriting the ansible ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 3.7,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1734"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ansib... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible_engine:*:*:*:*:*:*:*:*",
"matchCriteriaId": "2E713A0F-6AD3-409E-87AA-DE7EB5B7525C",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.16",
"versionStart... | [
"78"
] | 78 | https://github.com/ansible/ansible/issues/67792 | [
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | ##### SUMMARY
<!--- Explain the problem briefly below -->
CVE-2020-1734
The `pipe` lookup plugin should use `shell=False` be default to avoid potential privilege escalation. A new option should provide a way to enable `shell=True`.
If a variable is passed to the `pipe` lookup, that variable could be overriden v... | pipe lookup plugin enables shell by default | https://api.github.com/repos/ansible/ansible/issues/67792/comments | 4 | 2020-02-26T19:48:32Z | 2020-05-14T13:00:07Z | https://github.com/ansible/ansible/issues/67792 | 571,616,203 | 67,792 | 1,103 |
CVE-2020-10212 | 2020-03-07T00:15:13.117 | upload.php in Responsive FileManager 9.13.4 and 9.14.0 allows SSRF via the url parameter because file-extension blocking is mishandled and because it is possible for a DNS hostname to resolve to an internal IP address. For example, an SSRF attempt may succeed if a .ico filename is added to the PATH_INFO. Also, an attac... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/trippo/ResponsiveFilemanager/issues/598"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tecrail:responsive_filemanager:9.13.4:*:*:*:*:*:*:*",
"matchCriteriaId": "6E5817FB-89FD-4B34-A47F-F42E3B5756A1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"918"
] | 918 | https://github.com/trippo/ResponsiveFilemanager/issues/598 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"trippo",
"ResponsiveFilemanager"
] | Good afternoon ResponsiveFilemanager,
When i was doing a security test for a client of mine i noticed in your newest version of
ResponsiveFilemanager 9.13.4 ( in 9.14.0 the url upload is completly broken but it also exist there ) internal server side request forgery by adding to any php "/image.ico".
to reproduc... | server side request forgery vulnerability in url uploader bypass CVE-2018-14728 by adding /favicon.ico to end of php file. | https://api.github.com/repos/trippo/ResponsiveFilemanager/issues/598/comments | 6 | 2020-03-05T05:14:14Z | 2020-09-07T14:01:06Z | https://github.com/trippo/ResponsiveFilemanager/issues/598 | 575,998,259 | 598 | 1,104 |
CVE-2020-10233 | 2020-03-09T00:15:10.893 | In version 4.8.0 and earlier of The Sleuth Kit (TSK), there is a heap-based buffer over-read in ntfs_dinode_lookup in fs/ntfs.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/sleuthkit/sleuthkit/issues/1829"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40li... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sleuthkit:the_sleuth_kit:*:*:*:*:*:*:*:*",
"matchCriteriaId": "82607605-9F72-4A99-9704-09E58BA042E0",
"versionEndExcluding": null,
"versionEndIncluding": "4.8.0",
"versionSta... | [
"125"
] | 125 | https://github.com/sleuthkit/sleuthkit/issues/1829 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"sleuthkit",
"sleuthkit"
] | Hello sleuthkit team,
As part of our fuzzing efforts at Google, we have identified an issue affecting
sleuthkit (tested with revision * develop c05a93a7ce7d40ab203216bb035e3567d8ce68ec).
To reproduce, we are attaching a Dockerfile which compiles the project with
LLVM, taking advantage of the sanitizers that it ... | Heap-buffer-overflow in ntfs_dinode_lookup | https://api.github.com/repos/sleuthkit/sleuthkit/issues/1829/comments | 2 | 2020-02-14T15:42:50Z | 2020-04-01T11:10:27Z | https://github.com/sleuthkit/sleuthkit/issues/1829 | 565,404,605 | 1,829 | 1,105 |
CVE-2020-1737 | 2020-03-09T16:15:12.407 | A flaw was found in Ansible 2.7.17 and prior, 2.8.9 and prior, and 2.9.6 and prior when using the Extract-Zip function from the win_unzip module as the extracted file(s) are not checked if they belong to the destination folder. An attacker could take advantage of this flaw by crafting an archive anywhere in the file sy... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.6,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1737"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ansible/an... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible_engine:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D55D4795-99E8-4097-B704-1CC2BAD67148",
"versionEndExcluding": "2.7.17",
"versionEndIncluding": null,
"versionStart... | [
"22"
] | 22 | https://github.com/ansible/ansible/issues/67795 | [
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
CVE-2020-1737
<!--- Explain the problem briefly below -->
A sp... | win_unzip path traversal with specially crafted archive | https://api.github.com/repos/ansible/ansible/issues/67795/comments | 2 | 2020-02-26T19:55:42Z | 2020-03-27T17:41:28Z | https://github.com/ansible/ansible/issues/67795 | 571,620,016 | 67,795 | 1,106 |
CVE-2020-10251 | 2020-03-10T04:15:11.533 | In ImageMagick 7.0.9, an out-of-bounds read vulnerability exists within the ReadHEICImageByID function in coders\heic.c. It can be triggered via an image with a width or height value that exceeds the actual size of the image. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/1859"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Patch",
"Third Party Advis... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.0.9:*:*:*:*:*:*:*",
"matchCriteriaId": "5A044015-839F-4D63-A002-1F7806C41365",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionSta... | [
"125"
] | 125 | https://github.com/ImageMagick/ImageMagick/issues/1859 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"ImageMagick",
"ImageMagick"
] | ### Prerequisites
- [Y] I have written a descriptive issue title
- [Y] I have verified that I am using the latest version of ImageMagick
- [Y] I have searched [open](https://github.com/ImageMagick/ImageMagick/issues) and [closed](https://github.com/ImageMagick/ImageMagick/issues?q=is%3Aissue+is%3Aclosed) issues to... | ImageMagick "ReadHEICImageByID()" Out-of-bounds read vulnerability | https://api.github.com/repos/ImageMagick/ImageMagick/issues/1859/comments | 6 | 2020-03-03T19:01:32Z | 2020-06-17T12:24:04Z | https://github.com/ImageMagick/ImageMagick/issues/1859 | 574,875,269 | 1,859 | 1,107 |
CVE-2020-1733 | 2020-03-11T19:15:13.030 | A race condition flaw was found in Ansible Engine 2.7.17 and prior, 2.8.9 and prior, 2.9.6 and prior when running a playbook with an unprivileged become user. When Ansible needs to run a module with become user, the temporary directory is created in /var/tmp. This directory is created with "umask 77 && mkdir -p <dir>";... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 3.7,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1733"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://gith... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89338CDC-A956-4F24-A2A2-EA5CFD78F235",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.16",
"versionStartExcludi... | [
"362"
] | 362 | https://github.com/ansible/ansible/issues/67791 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | ##### SUMMARY
<!--- Explain the problem briefly below -->
CVE-2020-1733
We create a temporary directory for the `become_user` with `umask 077` in `/var/tmp` without first checking if the directory exists and that it has the expected permissions.
**Relevant code**
https://github.com/ansible/ansible/blob/79dfa... | Insecure creation of temporary directory for become_user | https://api.github.com/repos/ansible/ansible/issues/67791/comments | 5 | 2020-02-26T19:46:31Z | 2020-05-11T13:00:03Z | https://github.com/ansible/ansible/issues/67791 | 571,615,146 | 67,791 | 1,108 |
CVE-2020-1739 | 2020-03-12T18:15:12.337 | A flaw was found in Ansible 2.7.16 and prior, 2.8.8 and prior, and 2.9.5 and prior when a password is set with the argument "password" of svn module, it is used on svn command line, disclosing to other users within the same node. An attacker could take advantage by reading the cmdline file from that particular PID on t... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 3.3,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1739"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89338CDC-A956-4F24-A2A2-EA5CFD78F235",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.16",
"versionStartExcludi... | [
"200"
] | 200 | https://github.com/ansible/ansible/issues/67797 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
CVE-2020-1739
<!--- Explain the problem briefly below -->
The ... | Command used in subversion module is problematic | https://api.github.com/repos/ansible/ansible/issues/67797/comments | 2 | 2020-02-26T19:58:52Z | 2020-05-11T13:00:03Z | https://github.com/ansible/ansible/issues/67797 | 571,621,996 | 67,797 | 1,109 |
CVE-2020-10544 | 2020-03-13T15:15:11.263 | An XSS issue was discovered in tooltip/tooltip.js in PrimeTek PrimeFaces 7.0.11. In a web application using PrimeFaces, an attacker can provide JavaScript code in an input field whose data is later used as a tooltip title without any input validation. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/primefaces/primefaces/issues/5642"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/primefaces/primefaces/i... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:primetek:primefaces:7.0.11:*:*:*:*:*:*:*",
"matchCriteriaId": "BB928810-1C50-4DDA-A273-4A3E9AB409DA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartE... | [
"79"
] | 79 | https://github.com/primefaces/primefaces/issues/5642 | [
"Third Party Advisory"
] | github.com | [
"primefaces",
"primefaces"
] | ## 1) Environment
- PrimeFaces version: 7.0.11
- Does it work on the newest released PrimeFaces version? No
- Does it work on the newest sources in GitHub? No
- Affected browsers: all
## 2) Expected behavior
Proper escaping of title referenced by p:tooltip for .
## 3) Actual behavior
Target title not escape... | Tooltip: XSS in target title | https://api.github.com/repos/primefaces/primefaces/issues/5642/comments | 7 | 2020-03-04T12:09:20Z | 2024-01-23T20:15:31Z | https://github.com/primefaces/primefaces/issues/5642 | 575,351,426 | 5,642 | 1,110 |
CVE-2020-10567 | 2020-03-14T14:15:11.310 | An issue was discovered in Responsive Filemanager through 9.14.0. In the ajax_calls.php file in the save_img action in the name parameter, there is no validation of what kind of extension is sent. This makes it possible to execute PHP code if a legitimate JPEG image contains this code in the EXIF data, and the .php ext... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/171280/ZwiiCMS-12.2.04-Remote-Code-Execution.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/trippo/ResponsiveFilemanage... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:tecrail:responsive_filemanager:*:*:*:*:*:*:*:*",
"matchCriteriaId": "54CD0F21-D4B5-4F0A-87ED-FA0D20A9D73C",
"versionEndExcluding": null,
"versionEndIncluding": "9.14.0",
"ver... | [
"20"
] | 20 | https://github.com/trippo/ResponsiveFilemanager/issues/600 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"trippo",
"ResponsiveFilemanager"
] | after taking another look at your application i noticed in the ajax_calls.php file in the "save_img" action that the "name" parameter doesn't validate the extension of the file.
this makes it possible to upload php files to the server even when this normaly should not be allowed.
there was a miner validation to check... | remote code execution vulnerability in ajax_calls.php in save_img action because of no validation on extension name. | https://api.github.com/repos/trippo/ResponsiveFilemanager/issues/600/comments | 14 | 2020-03-13T20:06:55Z | 2024-06-13T22:42:57Z | https://github.com/trippo/ResponsiveFilemanager/issues/600 | 580,818,981 | 600 | 1,111 |
CVE-2020-10594 | 2020-03-15T22:15:14.130 | An issue was discovered in drf-jwt 1.15.x before 1.15.1. It allows attackers with access to a notionally invalidated token to obtain a new, working token via the refresh endpoint, because the blacklist protection mechanism is incompatible with the token-refresh feature. NOTE: drf-jwt is a fork of jpadilla/django-rest-f... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Styria-Digital/django-rest-framework-jwt/issues/36"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:styria:django-rest-framework-json_web_tokens:*:*:*:*:*:*:*:*",
"matchCriteriaId": "22200040-522F-4DC6-81C5-5AA358FCF8BF",
"versionEndExcluding": "1.15.1",
"versionEndIncluding": null,
... | [
"287"
] | 287 | https://github.com/Styria-Digital/django-rest-framework-jwt/issues/36 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Styria-Digital",
"django-rest-framework-jwt"
] | If you configure an app to allow blacklisting tokens and turn `JWT_ALLOW_REFRESH` on, then you can still operate the refresh endpoint using a blacklisted token, which allows you to side-step the fact that the token is invalidated. | Blacklisted tokens can still be refreshed | https://api.github.com/repos/Styria-Digital/django-rest-framework-jwt/issues/36/comments | 3 | 2020-03-02T20:17:34Z | 2020-03-12T09:01:27Z | https://github.com/Styria-Digital/django-rest-framework-jwt/issues/36 | 574,221,165 | 36 | 1,112 |
CVE-2020-10594 | 2020-03-15T22:15:14.130 | An issue was discovered in drf-jwt 1.15.x before 1.15.1. It allows attackers with access to a notionally invalidated token to obtain a new, working token via the refresh endpoint, because the blacklist protection mechanism is incompatible with the token-refresh feature. NOTE: drf-jwt is a fork of jpadilla/django-rest-f... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Styria-Digital/django-rest-framework-jwt/issues/36"
},
{
"source": "cve@mitre.org",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:styria:django-rest-framework-json_web_tokens:*:*:*:*:*:*:*:*",
"matchCriteriaId": "22200040-522F-4DC6-81C5-5AA358FCF8BF",
"versionEndExcluding": "1.15.1",
"versionEndIncluding": null,
... | [
"287"
] | 287 | https://github.com/jpadilla/django-rest-framework-jwt/issues/484 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"jpadilla",
"django-rest-framework-jwt"
] | Hello there,
For a long time now I've honestly thought I'd have the time and energy to come back and work on this project, and I think I still don't. I've not worked on any project recently needing it, which makes it harder to find time to come back.
At some point I also noticed I no longer liked how the project ... | Status | https://api.github.com/repos/jpadilla/django-rest-framework-jwt/issues/484/comments | 12 | 2019-07-08T11:01:47Z | 2020-03-19T05:54:09Z | https://github.com/jpadilla/django-rest-framework-jwt/issues/484 | 465,192,457 | 484 | 1,113 |
CVE-2020-1735 | 2020-03-16T16:15:13.890 | A flaw was found in the Ansible Engine when the fetch module is used. An attacker could intercept the module, inject a new path, and then choose a new destination path on the controller node. All versions in 2.7.x, 2.8.x and 2.9.x branches are believed to be vulnerable. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 3.6,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1735"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Ad... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1AA398A0-5DCC-4202-BB11-B2871FB796B4",
"versionEndExcluding": "2.7.17",
"versionEndIncluding": null,
"versionStartExcludi... | [
"22"
] | 22 | https://github.com/ansible/ansible/issues/67793 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
CVE-2020-1735
<!--- Explain the problem briefly below -->
Poss... | fetch module path traversal | https://api.github.com/repos/ansible/ansible/issues/67793/comments | 2 | 2020-02-26T19:50:23Z | 2020-05-06T13:00:11Z | https://github.com/ansible/ansible/issues/67793 | 571,617,198 | 67,793 | 1,114 |
CVE-2020-1736 | 2020-03-16T16:15:13.983 | A flaw was found in Ansible Engine when a file is moved using atomic_move primitive as the file mode cannot be specified. This sets the destination files world-readable if the destination file does not exist and if the file exists, the file could be changed to have less restrictive permissions before the move. This cou... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 2.1,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1736"
},
{
"source": "secalert@redhat.com",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89338CDC-A956-4F24-A2A2-EA5CFD78F235",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.16",
"versionStartExcludi... | [
"732"
] | 732 | https://github.com/ansible/ansible/issues/67794 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
CVE-2020-1736
<!--- Explain the problem briefly below -->
If a... | The default permissions used by atomic_move can create files that are world readable | https://api.github.com/repos/ansible/ansible/issues/67794/comments | 20 | 2020-02-26T19:54:05Z | 2022-07-27T13:00:01Z | https://github.com/ansible/ansible/issues/67794 | 571,619,142 | 67,794 | 1,115 |
CVE-2020-1738 | 2020-03-16T16:15:14.093 | A flaw was found in Ansible Engine when the module package or service is used and the parameter 'use' is not specified. If a previous task is executed with a malicious user, the module sent can be selected by the attacker using the ansible facts file. All versions in 2.7.x, 2.8.x and 2.9.x branches are believed to be v... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.6,
"confidentialityImpact": "NONE",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1738"
},
{
"source": "secalert@redhat.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/ansible/an... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible:*:*:*:*:*:*:*:*",
"matchCriteriaId": "89338CDC-A956-4F24-A2A2-EA5CFD78F235",
"versionEndExcluding": null,
"versionEndIncluding": "2.7.16",
"versionStartExcludi... | [
"88"
] | 88 | https://github.com/ansible/ansible/issues/67796 | [
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
CVE-2020-1738
Both `package` and `service` modules use facts to... | package and service modules allow arbitrary modules to be executed | https://api.github.com/repos/ansible/ansible/issues/67796/comments | 2 | 2020-02-26T19:57:02Z | 2020-05-14T13:00:08Z | https://github.com/ansible/ansible/issues/67796 | 571,620,850 | 67,796 | 1,116 |
CVE-2020-1740 | 2020-03-16T16:15:14.217 | A flaw was found in Ansible Engine when using Ansible Vault for editing encrypted files. When a user executes "ansible-vault edit", another user on the same computer can read the old and new secret, as it is created in a temporary file with mkstemp and the returned file descriptor is closed and the method write_data is... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 1.9,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Vendor Advisory"
],
"url": "https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-1740"
},
{
"source": "secalert@redhat.com",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:redhat:ansible:*:*:*:*:*:*:*:*",
"matchCriteriaId": "1AA398A0-5DCC-4202-BB11-B2871FB796B4",
"versionEndExcluding": "2.7.17",
"versionEndIncluding": null,
"versionStartExcludi... | [
"377"
] | 377 | https://github.com/ansible/ansible/issues/67798 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"ansible",
"ansible"
] | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
CVE-2020-1740
A race condition exists in `ansible-vault edit` w... | ansible-vault edit race condition | https://api.github.com/repos/ansible/ansible/issues/67798/comments | 2 | 2020-02-26T20:00:23Z | 2020-05-01T13:00:18Z | https://github.com/ansible/ansible/issues/67798 | 571,622,922 | 67,798 | 1,117 |
CVE-2018-21037 | 2020-03-17T15:15:12.643 | Subrion CMS 4.1.5 (and possibly earlier versions) allow CSRF to change the administrator password via the panel/members/edit/1 URI. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/intelliants/subrion/issues/638"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:intelliants:subrion:*:*:*:*:*:*:*:*",
"matchCriteriaId": "6B85D0B5-A4C7-4405-BE56-E90E20F3678E",
"versionEndExcluding": null,
"versionEndIncluding": "4.1.5",
"versionStartExc... | [
"352"
] | 352 | https://github.com/intelliants/subrion/issues/638 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"intelliants",
"subrion"
] | Hi Team,
The application is vulnerable to CSRF attack.
Affected Application Version: Subrion CMS 4.1.5
The attacker can change the administrator password by sending a crafted request to the application on change password field.
The application is not validating the source origin of the request is coming from also... | CSRF Attack On Change Password! | https://api.github.com/repos/intelliants/subrion/issues/638/comments | 2 | 2018-02-13T07:26:55Z | 2018-05-18T12:36:32Z | https://github.com/intelliants/subrion/issues/638 | 296,637,859 | 638 | 1,118 |
CVE-2020-10596 | 2020-03-17T15:15:14.253 | OpenCart 3.0.3.2 allows remote authenticated users to conduct XSS attacks via a crafted filename in the users' image upload section. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": null,
"url": "http://packetstormsecurity.com/files/157908/OpenCart-3.0.3.2-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ope... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:opencart:opencart:3.0.3.2:*:*:*:*:*:*:*",
"matchCriteriaId": "7F78529D-B518-4ACB-8107-C210EE4A6FEF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartEx... | [
"79"
] | 79 | https://github.com/opencart/opencart/issues/7810 | [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"opencart",
"opencart"
] | **What version of OpenCart are you reporting this for?**
Opencart 3.0.3.2
**Describe the bug**
Stored Cross Site Scripting (XSS) - Authenticated is found in users image upload section in opencart admin panel. Opencart is accepting filenames with arbitrary code in it and not escaping them so the JavaScript get execut... | Stored Cross Site Scripting - (Authenticated) on Opencart Admin Dashboard | https://api.github.com/repos/opencart/opencart/issues/7810/comments | 13 | 2020-01-09T04:23:52Z | 2020-12-23T20:14:26Z | https://github.com/opencart/opencart/issues/7810 | 547,239,674 | 7,810 | 1,119 |
CVE-2020-10672 | 2020-03-18T22:15:12.313 | FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.aries.transaction.jms.internal.XaPooledConnectionFactory (aka aries.transaction.jms). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2659"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "77F8EDB1-5890-4054-84FF-2034C7D2ED96",
"versionEndExcluding": "2.9.10.4",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2659 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding class(es) of `org.apache.aries.transaction.jms`.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
CVE id: CVE-2020-10672
Reporter: Srikanth Ramu, threedr3am'follower, (concurr... | Block one more gadget type (aries.transaction.jms, CVE-2020-10672) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2659/comments | 0 | 2020-03-16T00:52:40Z | 2020-03-26T16:33:53Z | https://github.com/FasterXML/jackson-databind/issues/2659 | 581,901,777 | 2,659 | 1,120 |
CVE-2020-10673 | 2020-03-18T22:15:12.407 | FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.caucho.config.types.ResourceRef (aka caucho-quercus). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2660"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-an... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "9FB021E3-0529-4F99-B880-66FDAC2F889D",
"versionEndExcluding": "2.6.7.4",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2660 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding a class of `caucho-quercus` library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-10673
Reporter: threedr3am'follower
Fix is included in:
* 2.9.10... | Block one more gadget type (caucho-quercus, CVE-2020-10673) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2660/comments | 1 | 2020-03-18T01:32:04Z | 2021-02-23T19:52:40Z | https://github.com/FasterXML/jackson-databind/issues/2660 | 583,400,227 | 2,660 | 1,121 |
CVE-2020-10675 | 2020-03-19T14:15:12.287 | The Library API in buger jsonparser through 2019-12-04 allows attackers to cause a denial of service (infinite loop) via a Delete call. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/buger/jsonparser/issues/188"
},
{
"source": "cve@mitre.org",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jsonparser_project:jsonparser:*:*:*:*:*:*:*:*",
"matchCriteriaId": "514A5230-F052-4276-8CD1-6B82B6350428",
"versionEndExcluding": "1.0.0",
"versionEndIncluding": null,
"versi... | [
"835"
] | 835 | https://github.com/buger/jsonparser/issues/188 | [
"Exploit",
"Patch",
"Third Party Advisory"
] | github.com | [
"buger",
"jsonparser"
] | Hi. A call to function `Delete` may cause infinite loop. I wish you could take a look.
https://play.golang.org/p/kzKY-Z9ty_j
```
package main
import (
"fmt"
"github.com/buger/jsonparser"
)
func main() {
data1 := []byte("^_�^C^A^@[")
data2 := ""
// sink: this function leads to an inifinite loo... | infinite loop in Delete | https://api.github.com/repos/buger/jsonparser/issues/188/comments | 3 | 2020-03-09T10:40:07Z | 2021-09-14T06:24:28Z | https://github.com/buger/jsonparser/issues/188 | 577,810,888 | 188 | 1,122 |
CVE-2020-10799 | 2020-03-20T23:15:12.863 | The svglib package through 0.9.3 for Python allows XXE attacks via an svg2rlg call. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/deeplook/svglib/issues/229"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Issue Tracking",
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:svglib_project:svglib:*:*:*:*:*:*:*:*",
"matchCriteriaId": "AC597EC8-A947-4752-9AC2-4E455871C207",
"versionEndExcluding": null,
"versionEndIncluding": "0.9.3",
"versionStartE... | [
"611"
] | 611 | https://github.com/deeplook/svglib/issues/229 | [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"deeplook",
"svglib"
] | Hi! I found that I can perform XXE attack (https://en.wikipedia.org/wiki/XML_external_entity_attack) when using svg2rlg function
Code:
```
saved_image_path = 'test_png.png'
with open("./test.svg", "wb") as f:
f.write(image)
drawing = svg2rlg(image_path)
renderPM.drawToFile(drawing, saved_image_pat... | No disabling external entity expansion (XXE) | https://api.github.com/repos/deeplook/svglib/issues/229/comments | 9 | 2020-02-25T11:18:21Z | 2020-03-22T16:13:59Z | https://github.com/deeplook/svglib/issues/229 | 570,497,104 | 229 | 1,123 |
CVE-2020-10807 | 2020-03-22T16:15:12.417 | auth_svc in Caldera before 2.6.5 allows authentication bypass (for REST API requests) via a forged "localhost" string in the HTTP Host header. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/mitre/caldera/compare/2.6.4...2.6.5"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/mitre/caldera/issues/1405"
},
{
"sou... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mitre:caldera:*:*:*:*:*:*:*:*",
"matchCriteriaId": "B89E7BC3-A4A3-4A5B-89C4-19CC70BAFE75",
"versionEndExcluding": "2.6.5",
"versionEndIncluding": null,
"versionStartExcluding... | [
"290"
] | 290 | https://github.com/mitre/caldera/issues/1405 | [
"Third Party Advisory"
] | github.com | [
"mitre",
"caldera"
] | Hi guys,
While checking our your API I've found a serious security flaw, which allows any unauthenticated user to perform any kind of API requests, which basically makes the whole tool and therefore any agents on end hosts exposable to anyone having access to the Caldera REST API.
The following function is respo... | Serious Security Flaw: API Requests from localhost | https://api.github.com/repos/mitre/caldera/issues/1405/comments | 3 | 2020-03-18T15:12:57Z | 2020-03-19T13:55:50Z | https://github.com/mitre/caldera/issues/1405 | 583,800,223 | 1,405 | 1,124 |
CVE-2020-10870 | 2020-03-23T20:15:11.807 | Zim through 0.72.1 creates temporary directories with predictable names. A malicious user could predict and create Zim's temporary directories and prevent other users from being able to start Zim, resulting in a denial of service. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/zim-desktop-wiki/zim-desktop-wiki/issues/1028"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/zim-desktop... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:zim-wiki:zim:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A838A5FB-70E7-4A1A-A723-48DEF9494599",
"versionEndExcluding": null,
"versionEndIncluding": "0.72.1",
"versionStartExcluding... | [
"330"
] | 330 | https://github.com/zim-desktop-wiki/zim-desktop-wiki/issues/1028 | [
"Third Party Advisory"
] | github.com | [
"zim-desktop-wiki",
"zim-desktop-wiki"
] | **Description**
Zim creates temporary directories with predictable names. A malicious user could predict and create Zim's temporary directories and prevent other users from being able to start Zim, resulting in a denial of service.
**Steps to Reproduce**
1. Create two users: user1 and user2.
1. As user1:
`mk... | Predictable /tmp/zim-USER directory allows for denial of service | https://api.github.com/repos/zim-desktop-wiki/zim-desktop-wiki/issues/1028/comments | 1 | 2020-03-06T22:22:48Z | 2020-06-06T13:20:48Z | https://github.com/zim-desktop-wiki/zim-desktop-wiki/issues/1028 | 577,207,106 | 1,028 | 1,125 |
CVE-2020-10871 | 2020-03-23T20:15:11.917 | In OpenWrt LuCI git-20.x, remote unauthenticated attackers can retrieve the list of installed packages and services. NOTE: the vendor disputes the significance of this report because, for instances reachable by an unauthenticated actor, the same information is available in other (more complex) ways, and there is no pla... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/openwrt/luci/issues/3563#issuecomment-578522860"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openwrt:luci:git-20.049.11521-bebfe20:*:*:*:*:*:*:*",
"matchCriteriaId": "2E22DB7F-4E58-4783-A9FA-72786FB1E0C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"200"
] | 200 | https://github.com/openwrt/luci/issues/3563#issuecomment-578522860 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"openwrt",
"luci"
] | LuCI pages with sysauth=false (e.g. status pages that should work even for an user that is not logged in) are broken on LuCI master.
The symptom is that when you access the page with "sysauth=false" attribute, the menu disappears, as in: not even nodes that are also sysauth=false show up.
What should happen: the ... | luci-base: menu and i18n plays very BADLY with sysauth=false in master | https://api.github.com/repos/openwrt/luci/issues/3563/comments | 7 | 2020-01-25T21:59:41Z | 2020-04-13T16:01:25Z | https://github.com/openwrt/luci/issues/3563 | 555,144,202 | 3,563 | 1,126 |
CVE-2020-10871 | 2020-03-23T20:15:11.917 | In OpenWrt LuCI git-20.x, remote unauthenticated attackers can retrieve the list of installed packages and services. NOTE: the vendor disputes the significance of this report because, for instances reachable by an unauthenticated actor, the same information is available in other (more complex) ways, and there is no pla... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/openwrt/luci/issues/3563#issuecomment-578522860"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openwrt:luci:git-20.049.11521-bebfe20:*:*:*:*:*:*:*",
"matchCriteriaId": "2E22DB7F-4E58-4783-A9FA-72786FB1E0C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"200"
] | 200 | https://github.com/openwrt/luci/issues/3653#issue-567892007 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"openwrt",
"luci"
] | On commit r11655-a283b1788a the topmenu "<header>" is shown while no user logged in.
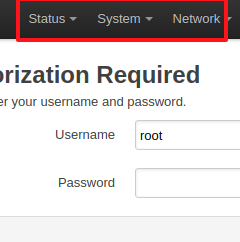
Any idea how to solve this issue?
Thank you. | Header topmenu shown logged out | https://api.github.com/repos/openwrt/luci/issues/3653/comments | 8 | 2020-02-19T22:37:08Z | 2020-02-26T11:39:46Z | https://github.com/openwrt/luci/issues/3653 | 567,892,007 | 3,653 | 1,127 |
CVE-2020-10871 | 2020-03-23T20:15:11.917 | In OpenWrt LuCI git-20.x, remote unauthenticated attackers can retrieve the list of installed packages and services. NOTE: the vendor disputes the significance of this report because, for instances reachable by an unauthenticated actor, the same information is available in other (more complex) ways, and there is no pla... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/openwrt/luci/issues/3563#issuecomment-578522860"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:openwrt:luci:git-20.049.11521-bebfe20:*:*:*:*:*:*:*",
"matchCriteriaId": "2E22DB7F-4E58-4783-A9FA-72786FB1E0C5",
"versionEndExcluding": null,
"versionEndIncluding": null,
"ve... | [
"200"
] | 200 | https://github.com/openwrt/luci/issues/3766 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"openwrt",
"luci"
] | Recent openwrt builds show the administration menu to unauthenticated guests: an attacker would be able to know the presence of installed packages and services on the box.
version banner: _Powered by LuCI Master (git-20.078.22902-0ed0d42) / OpenWrt SNAPSHOT r12643-213250b56b_
 via a crafted binary protocol header to try_read_command_binary in memcached.c. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/memcached/memcached/commit/02c6a2b62ddcb6fa4569a591d3461a156a636305"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": ... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:memcached:memcached:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4B224531-B654-4A70-A6B9-476B6A03D1DF",
"versionEndExcluding": "1.6.2",
"versionEndIncluding": null,
"versionStartExc... | [
"120"
] | 120 | https://github.com/memcached/memcached/issues/629 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"memcached",
"memcached"
] | Hi, Memcached team,
Recently, I revealed a buffer overflow vulnerability which may cause DOS attack. The exploit details can be found as following.
### Affect Version
memcached-1.6.0
memcached-1.6.1
### Root cause
file location: memcached.c:6156-6187
 0day buffer overflow vulnerability reveal | https://api.github.com/repos/memcached/memcached/issues/629/comments | 6 | 2020-03-23T09:21:26Z | 2020-03-24T01:07:22Z | https://github.com/memcached/memcached/issues/629 | 586,054,883 | 629 | 1,129 |
CVE-2019-20628 | 2020-03-24T19:15:20.947 | An issue was discovered in libgpac.a in GPAC before 0.8.0, as demonstrated by MP4Box. It contains a Use-After-Free vulnerability in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/1ab4860609f2e7a35634930571e7d0531297e090"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://git... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"416"
] | 416 | https://github.com/gpac/gpac/issues/1269 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found an UAF on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_uaf_mpegts.c:2183
Command: MP4Box -info $PoC
ASAN says:
~~~
==12341==ERROR: AddressSanitizer: heap-use-after-free on address 0x60300000efb0 at pc 0x00000098190d bp 0... | Use After Free (mpegts.c:2183) | https://api.github.com/repos/gpac/gpac/issues/1269/comments | 1 | 2019-07-06T00:10:37Z | 2019-07-07T15:59:17Z | https://github.com/gpac/gpac/issues/1269 | 464,799,448 | 1,269 | 1,130 |
CVE-2019-20629 | 2020-03-24T19:15:21.007 | An issue was discovered in libgpac.a in GPAC before 0.8.0, as demonstrated by MP4Box. It contains a heap-based buffer over-read in gf_m2ts_process_pmt in media_tools/mpegts.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/2320eb73afba753b39b7147be91f7be7afc0eeb7"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1264 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master) due to a heap buffer overflow on function gf_m2ts_process_pmt.
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_hbo_gf_m2ts_process_pmt
Command: MP4Box -info $PoC
ASAN says:
~~~
==19178==ERROR: AddressSanitizer: he... | SEGV (heap-buffer-overflow) on gf_m2ts_process_pmt | https://api.github.com/repos/gpac/gpac/issues/1264/comments | 1 | 2019-07-05T22:57:04Z | 2019-07-07T15:57:21Z | https://github.com/gpac/gpac/issues/1264 | 464,791,707 | 1,264 | 1,131 |
CVE-2019-20630 | 2020-03-24T19:15:21.070 | An issue was discovered in libgpac.a in GPAC before 0.8.0, as demonstrated by MP4Box. It contains a heap-based buffer over-read in BS_ReadByte (called from gf_bs_read_bit) in utils/bitstream.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/1ab4860609f2e7a35634930571e7d0531297e090"
},
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"125"
] | 125 | https://github.com/gpac/gpac/issues/1268 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a buffer overflow on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_hbo_BS_ReadByte
Command: MP4Box -info $PoC
ASAN says:
~~~
==27934==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60b00000a236 at pc 0x0000004... | heap-buffer-overflow on BS_ReadByte | https://api.github.com/repos/gpac/gpac/issues/1268/comments | 1 | 2019-07-06T00:10:13Z | 2019-07-07T15:59:28Z | https://github.com/gpac/gpac/issues/1268 | 464,799,415 | 1,268 | 1,132 |
CVE-2019-20631 | 2020-03-24T19:15:21.133 | An issue was discovered in libgpac.a in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid pointer dereference in gf_list_count in utils/list.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1270"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"763"
] | 763 | https://github.com/gpac/gpac/issues/1270 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found an UAF on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_segv_gf_list_count
Command: MP4Box -info $PoC
ASAN says:
~~~
==19963==ERROR: AddressSanitizer: SEGV on unknown address 0x00047fff8001 (pc 0x00000047a43d bp 0x6080000... | SEGV on unknown address on gf_list_count | https://api.github.com/repos/gpac/gpac/issues/1270/comments | 1 | 2019-07-06T00:11:01Z | 2019-07-07T16:00:40Z | https://github.com/gpac/gpac/issues/1270 | 464,799,484 | 1,270 | 1,133 |
CVE-2019-20632 | 2020-03-24T19:15:21.180 | An issue was discovered in libgpac.a in GPAC before 0.8.0, as demonstrated by MP4Box. It contains an invalid pointer dereference in gf_odf_delete_descriptor in odf/desc_private.c that can cause a denial of service via a crafted MP4 file. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1271"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/g... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "123D0430-86B1-40BF-9B43-C782CC2EDDE8",
"versionEndExcluding": "0.8.0",
"versionEndIncluding": null,
"versionStartExcluding": n... | [
"763"
] | 763 | https://github.com/gpac/gpac/issues/1271 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"gpac",
"gpac"
] | Hi,
Our fuzzer found a crash on MP4Box (the latest commit 987169b on master).
PoC: https://github.com/strongcourage/PoCs/blob/master/gpac_987169b/PoC_segv_gf_odf_delete_descriptor
Command: MP4Box -diso $PoC
ASAN says:
~~~
==26490==ERROR: AddressSanitizer: SEGV on unknown address 0x00000000ff00 (pc 0x000000c3ef6d ... | SEGV on unknown addres on gf_odf_delete_descriptor | https://api.github.com/repos/gpac/gpac/issues/1271/comments | 1 | 2019-07-06T00:25:31Z | 2019-07-07T16:01:07Z | https://github.com/gpac/gpac/issues/1271 | 464,800,676 | 1,271 | 1,134 |
CVE-2020-5261 | 2020-03-25T02:15:11.427 | Saml2 Authentication services for ASP.NET (NuGet package Sustainsys.Saml2) greater than 2.0.0, and less than version 2.5.0 has a faulty implementation of Token Replay Detection. Token Replay Detection is an important defence in depth measure for Single Sign On solutions. The 2.5.0 version is patched. Note that version ... | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"confidentialityImpact": "PARTI... | [
{
"source": "security-advisories@github.com",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Sustainsys/Saml2/commit/e58e0a1aff2b1ead6aca080b7cdced55ee6d5241"
},
{
"source": "security-advisories@github.com",
"tags": [
"Issue Tracking",
"Th... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:sustainsys:saml2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "74E6577A-B61E-43AD-BE8E-CC0CAC83C4F2",
"versionEndExcluding": "2.5.0",
"versionEndIncluding": null,
"versionStartExclud... | [
"294"
] | 294 | https://github.com/Sustainsys/Saml2/issues/711 | [
"Issue Tracking",
"Third Party Advisory"
] | github.com | [
"Sustainsys",
"Saml2"
] | Token Replay detection was not properly implemented in the migration to .Net Core.
The security implications are described in: https://github.com/Sustainsys/Saml2/security/advisories/GHSA-g6j2-ch25-5mmv and published as CVE-2020-5261 | Missing Token Replay Detection in 2.X | https://api.github.com/repos/Sustainsys/Saml2/issues/711/comments | 0 | 2017-05-09T17:07:47Z | 2020-04-22T08:46:37Z | https://github.com/Sustainsys/Saml2/issues/711 | 227,434,852 | 711 | 1,135 |
CVE-2020-10968 | 2020-03-26T13:15:12.970 | FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy). | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2662"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.or... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "77F8EDB1-5890-4054-84FF-2034C7D2ED96",
"versionEndExcluding": "2.9.10.4",
"versionEndIncluding": null,
"versi... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2662 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type(s) reported regarding a class of `aoju/bus-proxy` library.
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-10968
Reporter: XuYuanzhen (of Alibaba Cloud Security Team)
Fix wil... | Block one more gadget type (bus-proxy, CVE-2020-10968) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2662/comments | 0 | 2020-03-23T01:31:30Z | 2020-03-26T16:29:54Z | https://github.com/FasterXML/jackson-databind/issues/2662 | 585,867,685 | 2,662 | 1,136 |
CVE-2020-10969 | 2020-03-26T13:15:13.077 | FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PART... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/FasterXML/jackson-databind/issues/2642"
},
{
"source": "cve@mitre.org",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-an... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:fasterxml:jackson-databind:*:*:*:*:*:*:*:*",
"matchCriteriaId": "29BC94E0-FEBC-4E86-825C-0101DC339852",
"versionEndExcluding": "2.7.9.7",
"versionEndIncluding": null,
"versio... | [
"502"
] | 502 | https://github.com/FasterXML/jackson-databind/issues/2642 | [
"Third Party Advisory"
] | github.com | [
"FasterXML",
"jackson-databind"
] | Another gadget type reported regarding a class in `javax.swing` package..
See https://medium.com/@cowtowncoder/on-jackson-cves-dont-panic-here-is-what-you-need-to-know-54cd0d6e8062 for description of the general problem.
Mitre id: CVE-2020-10969
Reporters: threedr3am
Fix will be included in:
* 2.9.10.4
* 2... | Block one more gadget type (javax.swing, CVE-2020-10969) | https://api.github.com/repos/FasterXML/jackson-databind/issues/2642/comments | 5 | 2020-03-04T00:05:00Z | 2020-04-02T00:24:11Z | https://github.com/FasterXML/jackson-databind/issues/2642 | 575,038,970 | 2,642 | 1,137 |
CVE-2020-9467 | 2020-03-26T20:15:11.427 | Piwigo 2.10.1 has stored XSS via the file parameter in a /ws.php request because of the pwg.images.setInfo function. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory",
"VDB Entry"
],
"url": "http://packetstormsecurity.com/files/159191/Piwigo-2.10.1-Cross-Site-Scripting.html"
},
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.10.1:*:*:*:*:*:*:*",
"matchCriteriaId": "8E8B6457-1AF4-4B29-AF6E-9682E45BB2A9",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcludi... | [
"79"
] | 79 | https://github.com/Piwigo/Piwigo/issues/1168 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"Piwigo",
"Piwigo"
] | on `file` param. No worry with an admin, but this method can be used by a community user as well.
Originally reported by Zak S. see CVE-2020-9467 | stored XSS with pwg.images.setInfo | https://api.github.com/repos/Piwigo/Piwigo/issues/1168/comments | 1 | 2020-03-24T13:03:01Z | 2020-03-28T05:54:16Z | https://github.com/Piwigo/Piwigo/issues/1168 | 586,943,552 | 1,168 | 1,138 |
CVE-2020-9468 | 2020-03-26T20:15:11.473 | The Community plugin 2.9.e-beta for Piwigo allows users to set image information on images in albums for which they do not have permission, by manipulating the image_id parameter. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/plegall/Piwigo-community/issues/49"
},
{
"source": "cve@mitre.org",
"tags": [
"Release Notes"
],
"url": "https://piwigo.org/ext/extension_view.php?eid=303"
},
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.0:e-beta:*:*:*:*:*:*",
"matchCriteriaId": "43076B11-9615-4DB5-9C54-7105AD92F0AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExc... | [
"639"
] | 639 | https://github.com/plegall/Piwigo-community/issues/49 | [
"Patch",
"Third Party Advisory"
] | github.com | [
"plegall",
"Piwigo-community"
] | CVE-2020-9468 reported by Zak S.
> Further, a malicious user can modify the value of the 'image_id' parameter to any existing image id. There are no access controls to prevent a user from manipulating information on images that are in albums to which they do not have access. | [security] ability to by-pass protection on photo edition | https://api.github.com/repos/plegall/Piwigo-community/issues/49/comments | 1 | 2020-03-24T13:19:57Z | 2020-04-01T14:24:09Z | https://github.com/plegall/Piwigo-community/issues/49 | 586,954,137 | 49 | 1,139 |
CVE-2020-10990 | 2020-03-27T00:15:11.230 | An XXE issue exists in Accenture Mercury before 1.12.28 because of the platformlambda/core/serializers/SimpleXmlParser.java component. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Patch"
],
"url": "https://github.com/Accenture/mercury/commit/f647a01347485d2afe3a0b735eab3d0121d61f46"
},
{
"source": "cve@mitre.org",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/Accenture/mercury/issues/13"
... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:accenture:mercury:*:*:*:*:*:*:*:*",
"matchCriteriaId": "FF086E55-CE2C-4263-8F20-DEC1D8118949",
"versionEndExcluding": "1.12.28",
"versionEndIncluding": null,
"versionStartExc... | [
"611"
] | 611 | https://github.com/Accenture/mercury/issues/13 | [
"Third Party Advisory"
] | github.com | [
"Accenture",
"mercury"
] | @n33dle and I found a security vulnerability within the mercury project. We were hoping to get a core maintainer's contact details to responsibly disclose this vulnerability. | Security Contact Requested | https://api.github.com/repos/Accenture/mercury/issues/13/comments | 4 | 2020-01-06T00:12:35Z | 2020-02-26T18:21:09Z | https://github.com/Accenture/mercury/issues/13 | 545,486,919 | 13 | 1,140 |
CVE-2020-10991 | 2020-03-27T00:15:11.310 | Mulesoft APIkit through 1.3.0 allows XXE because of validation/RestXmlSchemaValidator.java | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/mulesoft/apikit/issues/547"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:mulesoft:aplkit:*:*:*:*:*:*:*:*",
"matchCriteriaId": "D36CCEC3-85DA-40B8-9508-D8B0C355FC52",
"versionEndExcluding": null,
"versionEndIncluding": "1.3.0",
"versionStartExcludi... | [
"611"
] | 611 | https://github.com/mulesoft/apikit/issues/547 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"mulesoft",
"apikit"
] | While reading the code in the apikit project we (@n33dle and I) identified a vulnerability we wanted to raise. The vulnerability is an XXE vulnerability (https://owasp.org/www-community/vulnerabilities/XML_External_Entity_(XXE)_Processing) and can be identified in the lines of code below:
https://github.com/mulesoft... | XXE in apikit | https://api.github.com/repos/mulesoft/apikit/issues/547/comments | 1 | 2020-03-25T08:01:53Z | 2020-07-17T13:49:52Z | https://github.com/mulesoft/apikit/issues/547 | 587,511,988 | 547 | 1,141 |
CVE-2020-10992 | 2020-03-27T00:15:11.370 | Azkaban through 3.84.0 allows XXE, related to validator/XmlValidatorManager.java and user/XmlUserManager.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/azkaban/azkaban/issues/2478"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:azkaban_project:azkaban:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4D087C92-3261-4503-814E-C3D422789367",
"versionEndExcluding": null,
"versionEndIncluding": "3.84.0",
"versionSta... | [
"611"
] | 611 | https://github.com/azkaban/azkaban/issues/2478 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"azkaban",
"azkaban"
] | While reading the code in the Azkaban project we (@n33dle and I) identified a vulnerability we wanted to raise. The vulnerability is an XXE vulnerability (https://owasp.org/www-community/vulnerabilities/XML_External_Entity_(XXE)_Processing) and can be identified in the lines of code below:
https://github.com/azkaban... | XXE in Azkaban | https://api.github.com/repos/azkaban/azkaban/issues/2478/comments | 1 | 2020-03-25T08:03:26Z | 2020-03-30T02:00:01Z | https://github.com/azkaban/azkaban/issues/2478 | 587,512,802 | 2,478 | 1,142 |
CVE-2020-10993 | 2020-03-27T00:15:11.717 | Osmand through 2.0.0 allow XXE because of binary/BinaryMapIndexReader.java. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.4,
"confidentialityImpact": "PARTIAL... | [
{
"source": "cve@mitre.org",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/osmandapp/Osmand/issues/8711"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://githu... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:osmand:osmand:*:*:*:*:*:*:*:*",
"matchCriteriaId": "512C2377-8AA5-41DD-A571-61D210621890",
"versionEndExcluding": null,
"versionEndIncluding": "2.0.0",
"versionStartExcluding... | [
"611"
] | 611 | https://github.com/osmandapp/Osmand/issues/8711 | [
"Exploit",
"Third Party Advisory"
] | github.com | [
"osmandapp",
"Osmand"
] | While reading the code in the Osmand project we (@n33dle and I) identified a vulnerability we wanted to raise. The vulnerability is an XXE vulnerability (https://owasp.org/www-community/vulnerabilities/XML_External_Entity_(XXE)_Processing) and can be identified in the lines of code below:
https://github.com/osmandap... | XXE in Osmand | https://api.github.com/repos/osmandapp/OsmAnd/issues/8711/comments | 1 | 2020-03-25T08:02:39Z | 2020-05-08T22:41:09Z | https://github.com/osmandapp/OsmAnd/issues/8711 | 587,512,395 | 8,711 | 1,143 |
CVE-2020-8551 | 2020-03-27T15:15:12.647 | The Kubelet component in versions 1.15.0-1.15.9, 1.16.0-1.16.6, and 1.17.0-1.17.2 has been found to be vulnerable to a denial of service attack via the kubelet API, including the unauthenticated HTTP read-only API typically served on port 10255, and the authenticated HTTPS API typically served on port 10250. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "ADJACENT_NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 3.3,
"confidentialityImpact": "N... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/89377"
},
{
"source": "jordan@liggitt.net",
"tags": null,
"url": "https://groups.google.com/forum/#%21topic/kuber... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "44ECF71D-7483-45B0-8BF5-92284C11696C",
"versionEndExcluding": null,
"versionEndIncluding": "1.15.9",
"versionStart... | [
"770"
] | 770 | https://github.com/kubernetes/kubernetes/issues/89377 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.0/AV:A/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L](https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:A/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L) (Medium)
The Kubelet has been found to be vulnerable to a denial of service attack via the kubelet API, including the unauthenticated HTTP read-only API typically served... | CVE-2020-8551: Kubelet DoS via API | https://api.github.com/repos/kubernetes/kubernetes/issues/89377/comments | 7 | 2020-03-23T18:34:40Z | 2021-12-02T22:55:29Z | https://github.com/kubernetes/kubernetes/issues/89377 | 586,428,637 | 89,377 | 1,144 |
CVE-2020-8552 | 2020-03-27T15:15:12.757 | The Kubernetes API server component in versions prior to 1.15.9, 1.16.0-1.16.6, and 1.17.0-1.17.2 has been found to be vulnerable to a denial of service attack via successful API requests. | {
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "NONE",
... | [
{
"source": "jordan@liggitt.net",
"tags": [
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/kubernetes/kubernetes/issues/89378"
},
{
"source": "jordan@liggitt.net",
"tags": null,
"url": "https://groups.google.com/forum/#%21topic/kuber... | [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:kubernetes:kubernetes:*:*:*:*:*:*:*:*",
"matchCriteriaId": "07761E41-21F4-466F-A602-4DC9BD1257CE",
"versionEndExcluding": null,
"versionEndIncluding": "1.15.9",
"versionStart... | [
"770"
] | 770 | https://github.com/kubernetes/kubernetes/issues/89378 | [
"Issue Tracking",
"Patch",
"Third Party Advisory"
] | github.com | [
"kubernetes",
"kubernetes"
] | CVSS Rating: [CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L](https://www.first.org/cvss/calculator/3.0#CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:L) (Medium)
The Kubernetes API server has been found to be vulnerable to a denial of service attack via authorized API requests.
### Am I vulnerable?
If an attacker t... | CVE-2020-8552: apiserver DoS (oom) | https://api.github.com/repos/kubernetes/kubernetes/issues/89378/comments | 4 | 2020-03-23T18:35:34Z | 2021-12-02T22:55:22Z | https://github.com/kubernetes/kubernetes/issues/89378 | 586,429,123 | 89,378 | 1,145 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.